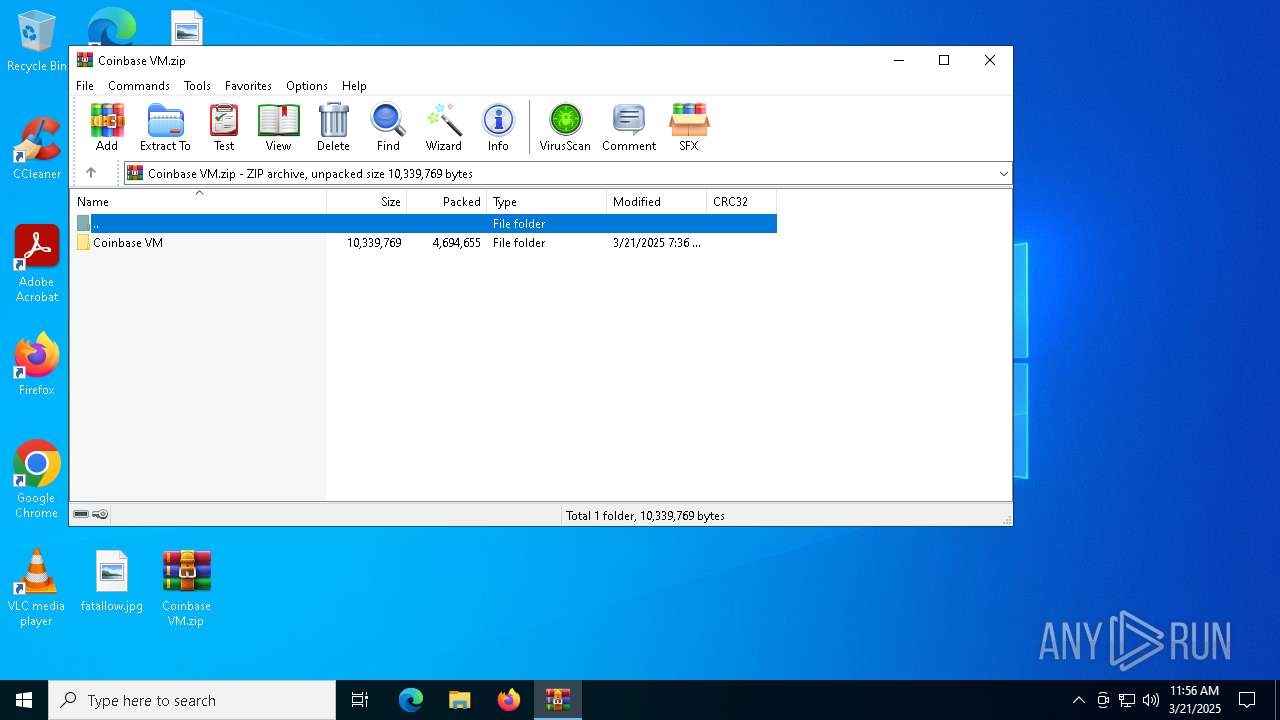
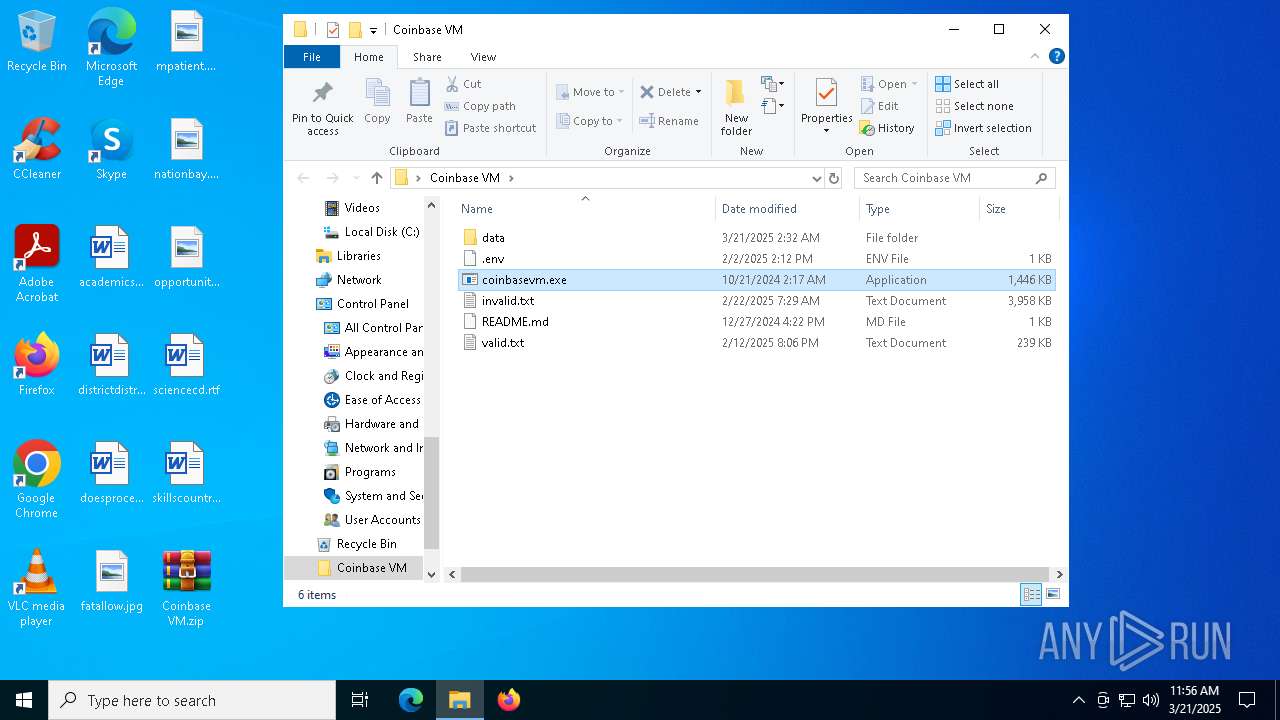
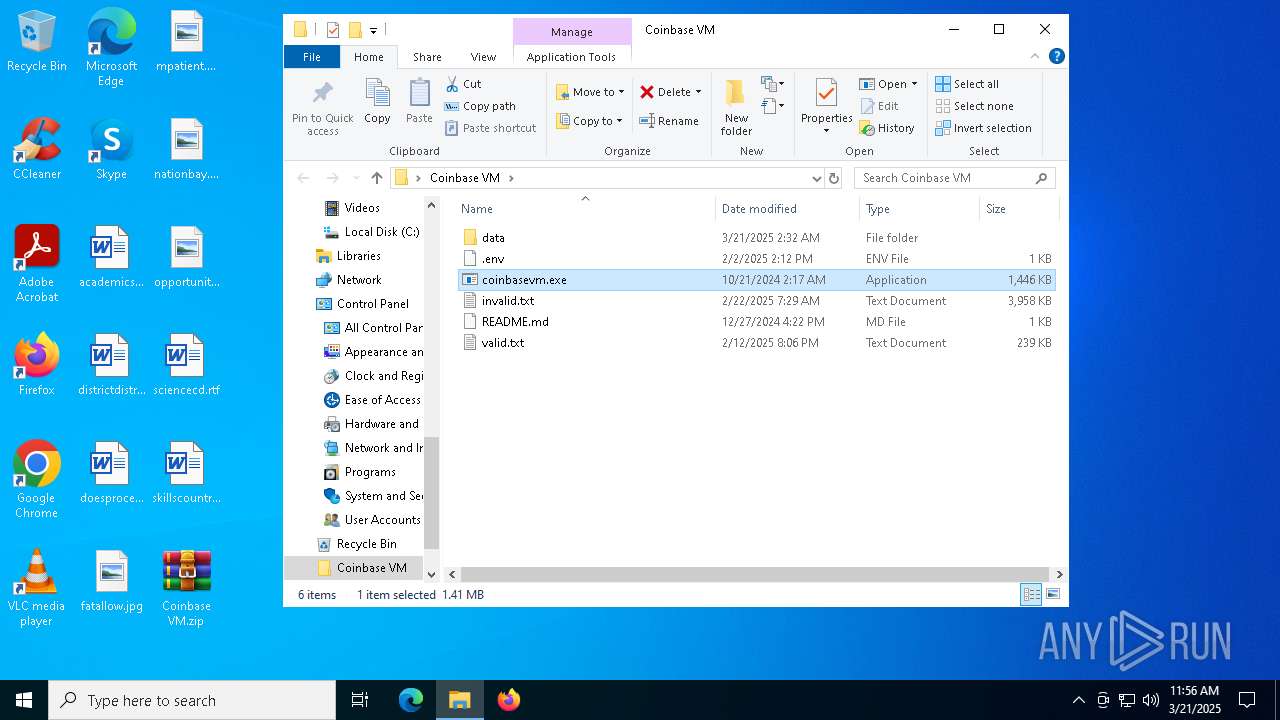
| File name: | Coinbase VM.zip |
| Full analysis: | https://app.any.run/tasks/988414c5-e47f-4630-a9e9-377d2d5e34da |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | March 21, 2025, 11:56:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 18C0A58CB56E4D641B8E0F9AC8C23198 |
| SHA1: | 5C0579BE3388487F1129A612617A6AB2570E844D |
| SHA256: | 5B4485DF7B761A86453EFAD5F38794B7E15AF73CAFD15E252F12A5E615492E4F |
| SSDEEP: | 98304:X35/5eJPBvb98WtY6LVWcHxtJpMxL96rXDYuNeLqpDBLRmxpmI5332upsMe3HIGf:i9D4TDUti40pk |
MALICIOUS
Changes the autorun value in the registry
- coinbasevm.exe (PID: 1912)
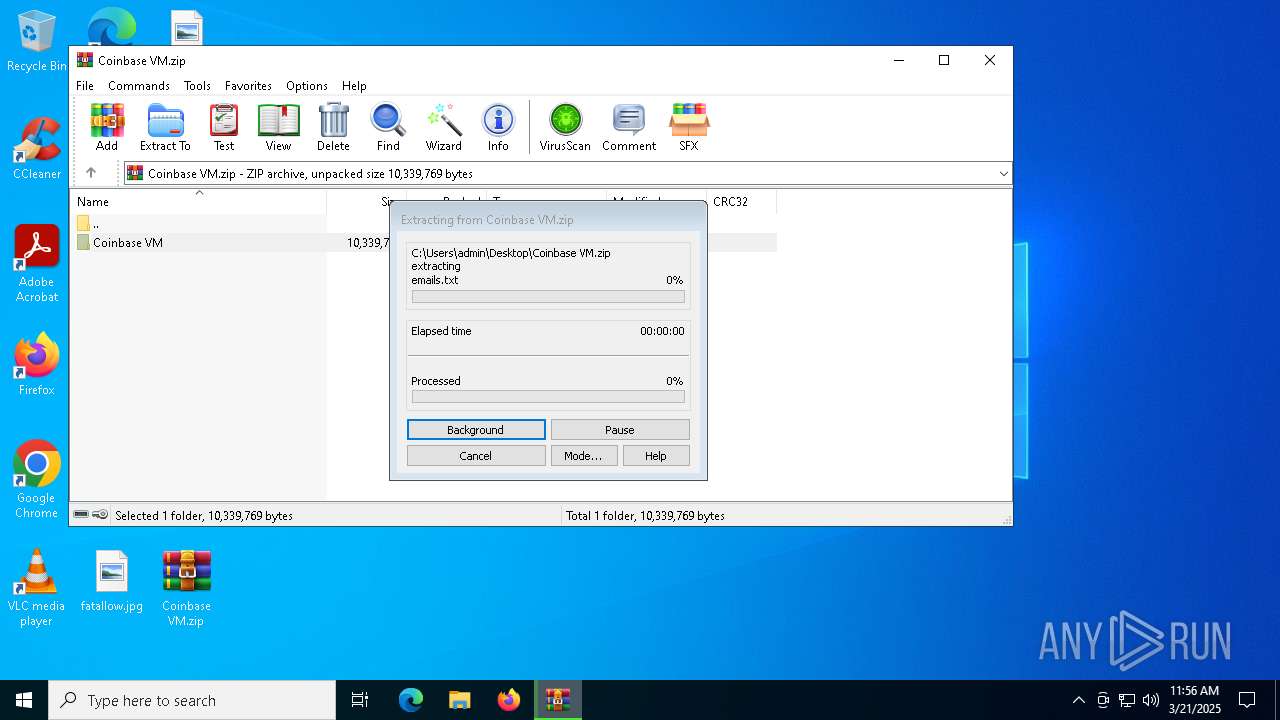
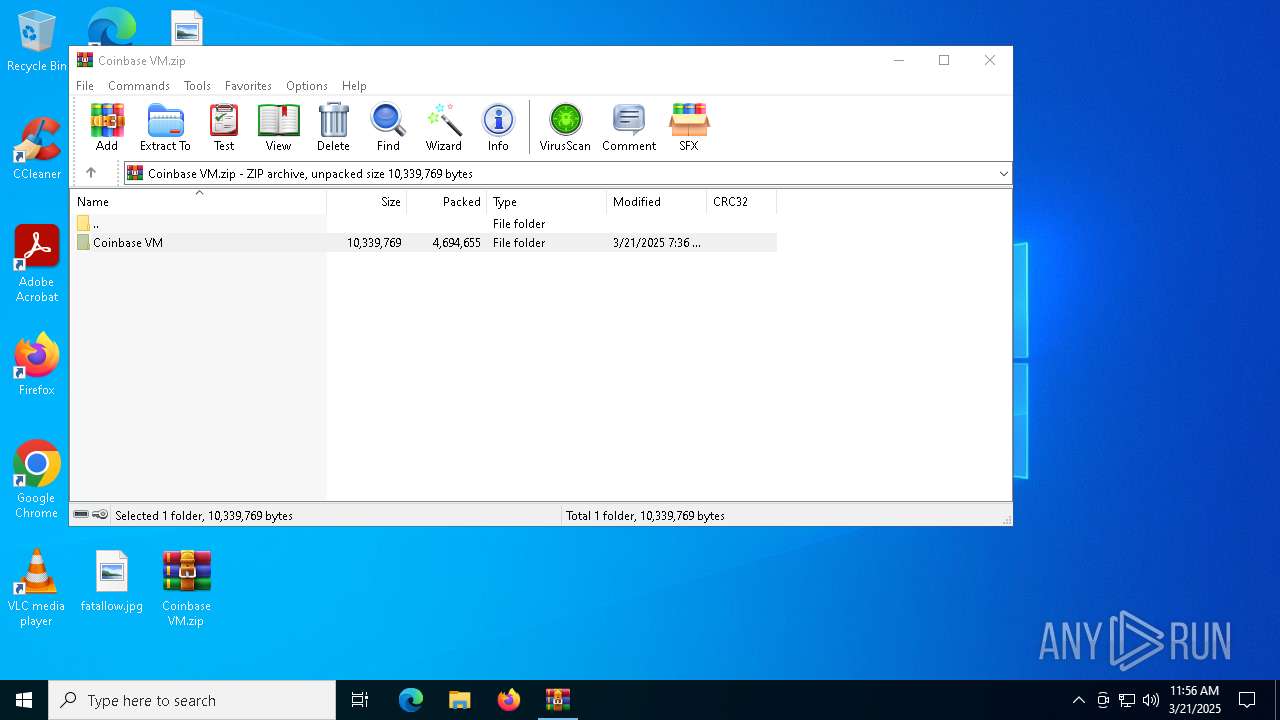
Generic archive extractor
- WinRAR.exe (PID: 4776)
ASYNCRAT has been detected (SURICATA)
- InstallUtil.exe (PID: 1184)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 1184)
SUSPICIOUS
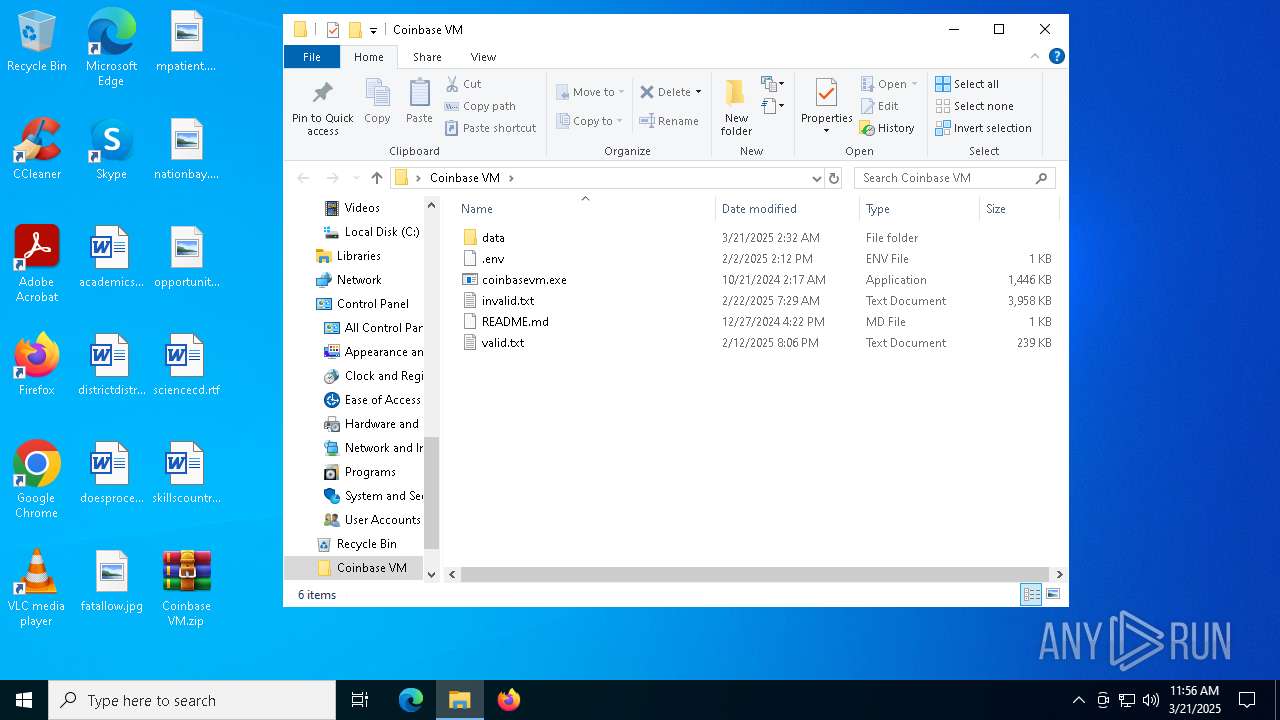
Executable content was dropped or overwritten
- coinbasevm.exe (PID: 1912)
Contacting a server suspected of hosting an CnC
- InstallUtil.exe (PID: 1184)
Connects to unusual port
- InstallUtil.exe (PID: 1184)
INFO
Manual execution by a user
- coinbasevm.exe (PID: 1912)
- InstallUtil.exe (PID: 1184)
Checks supported languages
- coinbasevm.exe (PID: 1912)
- InstallUtil.exe (PID: 1184)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4776)
Create files in a temporary directory
- coinbasevm.exe (PID: 1912)
Reads the machine GUID from the registry
- coinbasevm.exe (PID: 1912)
- InstallUtil.exe (PID: 1184)
Autorun file from Registry key
- coinbasevm.exe (PID: 1912)
Reads the computer name
- coinbasevm.exe (PID: 1912)
- InstallUtil.exe (PID: 1184)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 4560)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 4560)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 4560)
- InstallUtil.exe (PID: 1184)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 1240)
- BackgroundTransferHost.exe (PID: 6268)
- BackgroundTransferHost.exe (PID: 4560)
- BackgroundTransferHost.exe (PID: 4724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:03:21 00:36:10 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Coinbase VM/ |
Total processes
142
Monitored processes
11
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1184 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1240 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\Desktop\Coinbase VM\coinbasevm.exe" | C:\Users\admin\Desktop\Coinbase VM\coinbasevm.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: coinbasevm Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4560 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4724 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4776 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Coinbase VM.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5344 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6268 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6324 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 535
Read events
6 501
Write events
34
Delete events
0
Modification events
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Coinbase VM.zip | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
2
Suspicious files
5
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4776.48410\Coinbase VM\data\emails.txt | — | |
MD5:— | SHA256:— | |||
| 4560 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\62dbb48e-bb8f-4c47-8ec8-365dc5e06023.down_data | — | |
MD5:— | SHA256:— | |||
| 4560 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:94C51D8C82BD56CB3594AF9C8B3ACA44 | SHA256:98928F6E00A695C40733481BBC1BAF6EF7F8FA4210F4F4B2D560792D569CC959 | |||
| 4560 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\200fbbeb-d2bc-4645-a7e4-05cc3ae112b3.2647f4e8-fc0e-4fef-95e8-8b2396f3331d.down_meta | binary | |
MD5:D5D9ED51B6342567CB26E9537EF91CD4 | SHA256:EB7DF603E7D21E6CF393109BD1CF603C556F14533D09D83D21E6F05E41C710A1 | |||
| 4776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4776.48410\Coinbase VM\coinbasevm.exe | executable | |
MD5:FAE797F9E86201D9A803E88E92FE73F0 | SHA256:B0CCF17CA422B577A6C6105BFF444D1F2E005A98076FB45CF404A61F55634186 | |||
| 4776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4776.48410\Coinbase VM\data\proxies.txt | text | |
MD5:EF0A775247C6BEC71A9162DE8C61287B | SHA256:2FAEB0044543EFC84E31965B4A4203040002C6B58E51723F256A3BB4B7A24D40 | |||
| 4776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4776.48410\Coinbase VM\README.md | text | |
MD5:D96A5D7A7C6A485E829B24CDB214A08B | SHA256:2B81E560370EC98A09A69DF26C2BFFBFCC5542AC5369662A2B4AEFE50E59D682 | |||
| 4560 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:B97E400964900BC2D8274B887D5AA1F4 | SHA256:9EE0020FE1FECDEEE0309A80F5EB6BC02AF0793E11C4A230C7931D4C6BC662ED | |||
| 4560 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\200fbbeb-d2bc-4645-a7e4-05cc3ae112b3.up_meta_secure | binary | |
MD5:FFA50B62757D3E48C92DFEB545E73F42 | SHA256:D9272502CF52D7683F1C51515D57D88195C4187DAE2623112500DD4C480BC1DF | |||
| 4776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4776.48410\Coinbase VM\valid.txt | text | |
MD5:1616C21664192EBF2CA2B1C4C9559A6C | SHA256:74BA5FDEC9AF5C9D9ED04214E2131D2221F8BDBE2B1090AE08D86D5AC07B6173 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
15
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5304 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4560 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5228 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5228 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.138:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5304 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1184 | InstallUtil.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
1184 | InstallUtil.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |