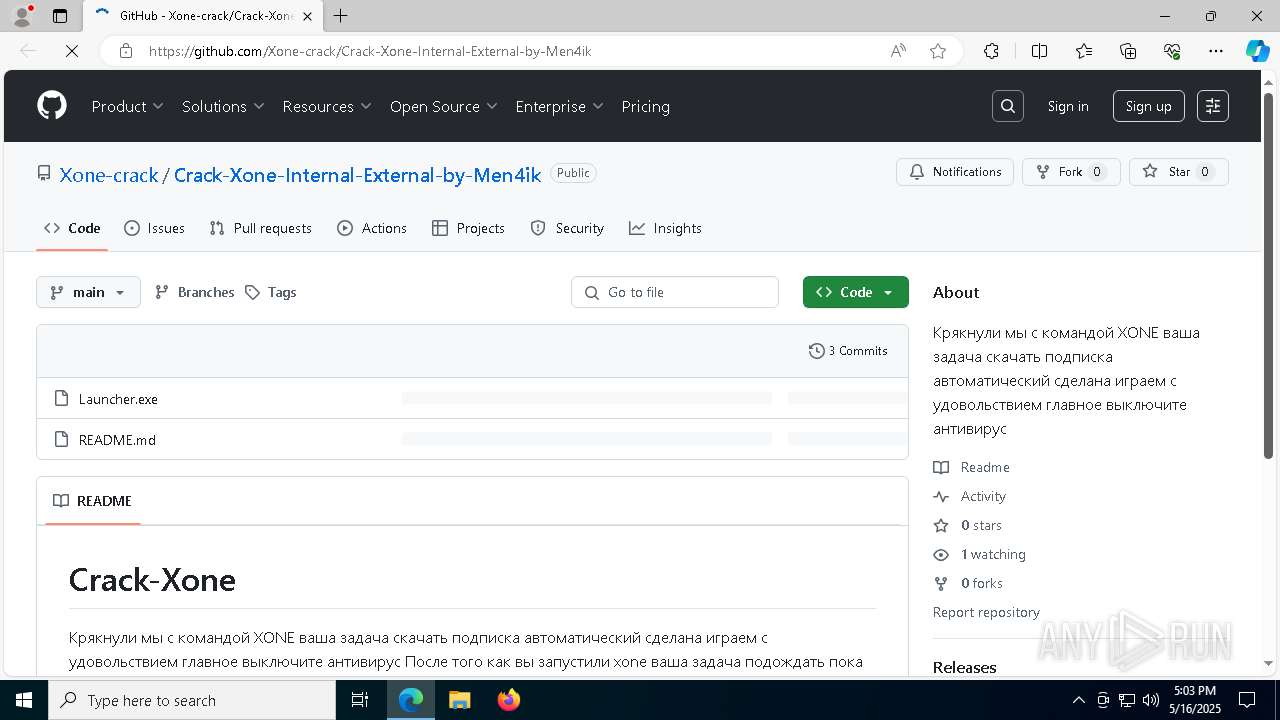
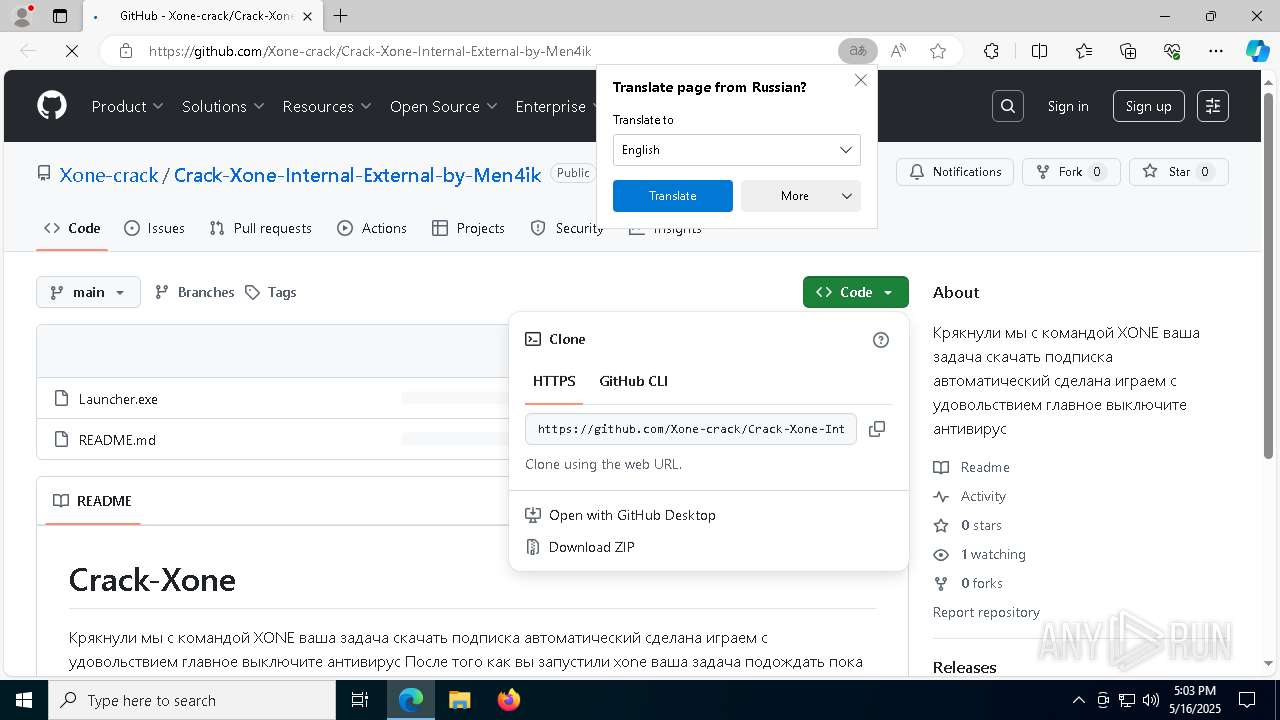
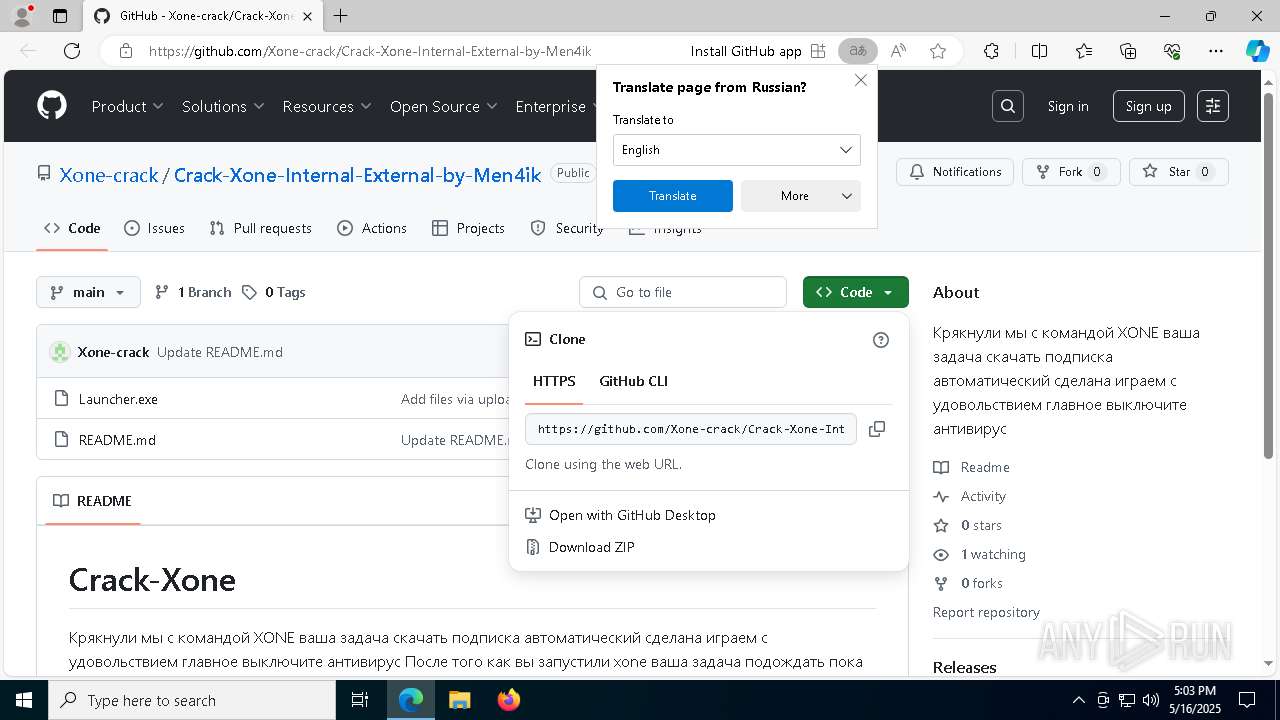
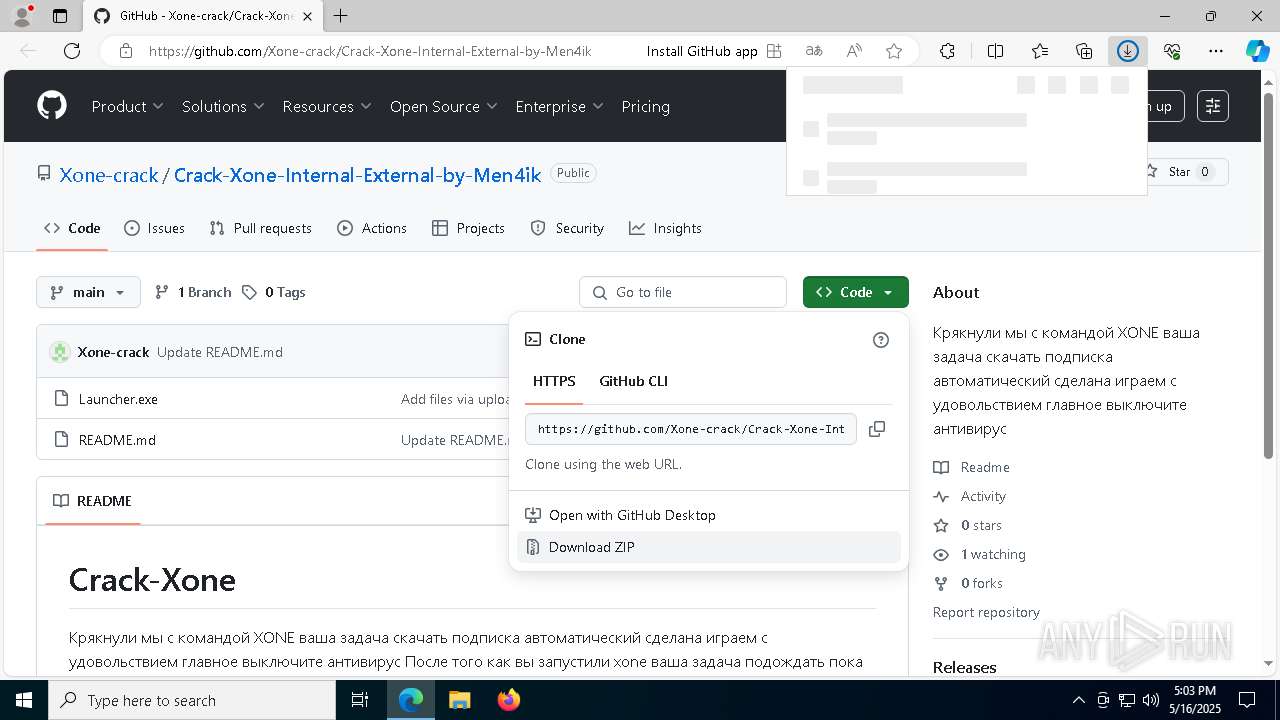
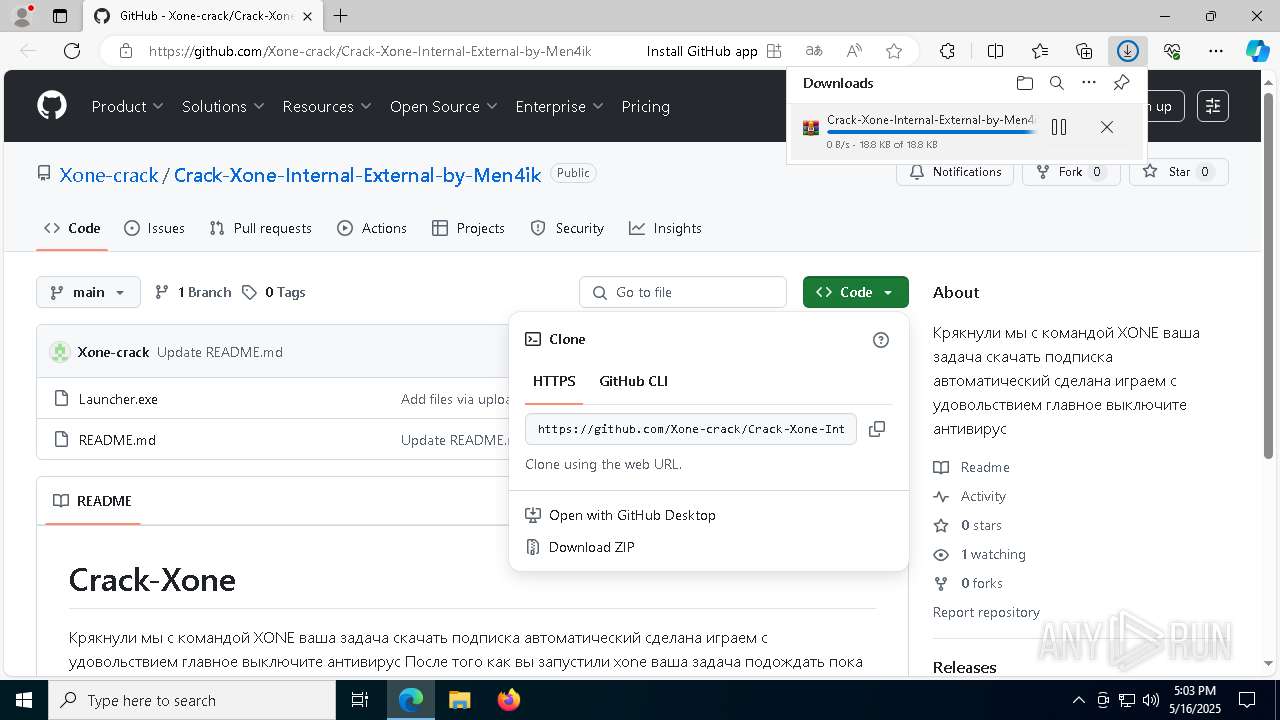
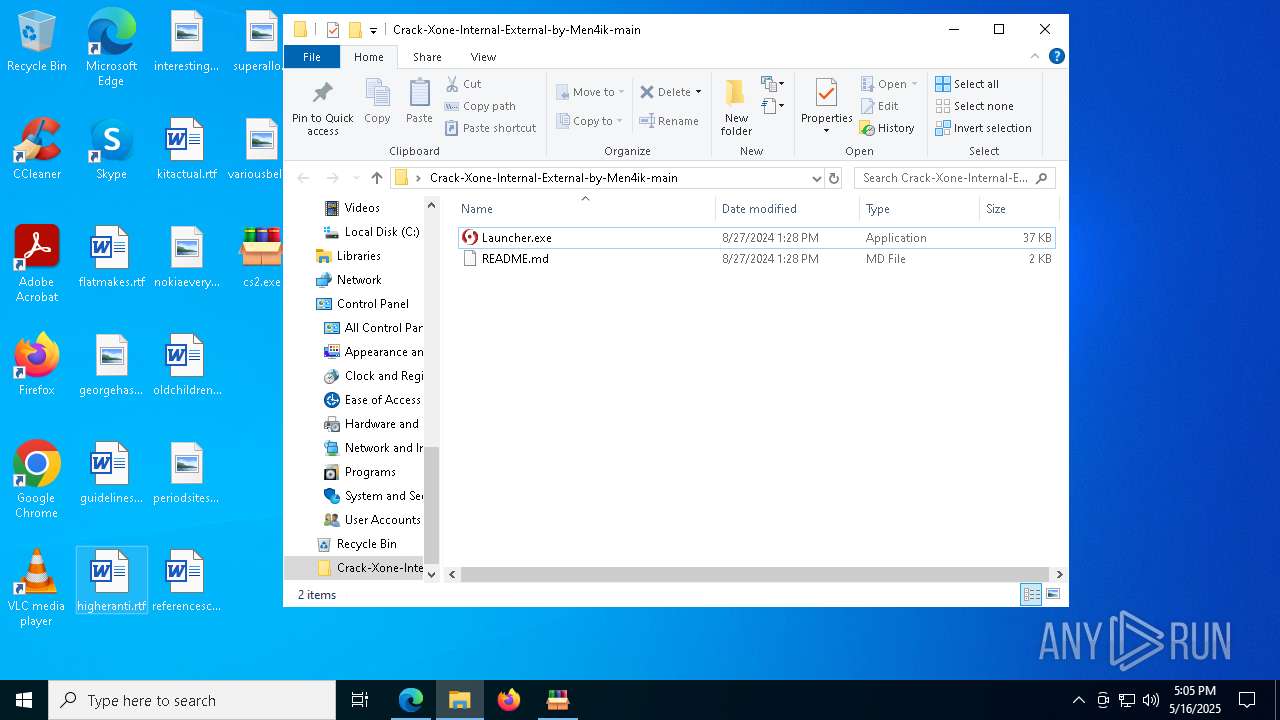
| URL: | https://github.com/Xone-crack/Crack-Xone-Internal-External-by-Men4ik |
| Full analysis: | https://app.any.run/tasks/c85fe2dd-7d0d-4ed2-b897-4f3a1da5a2cd |
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
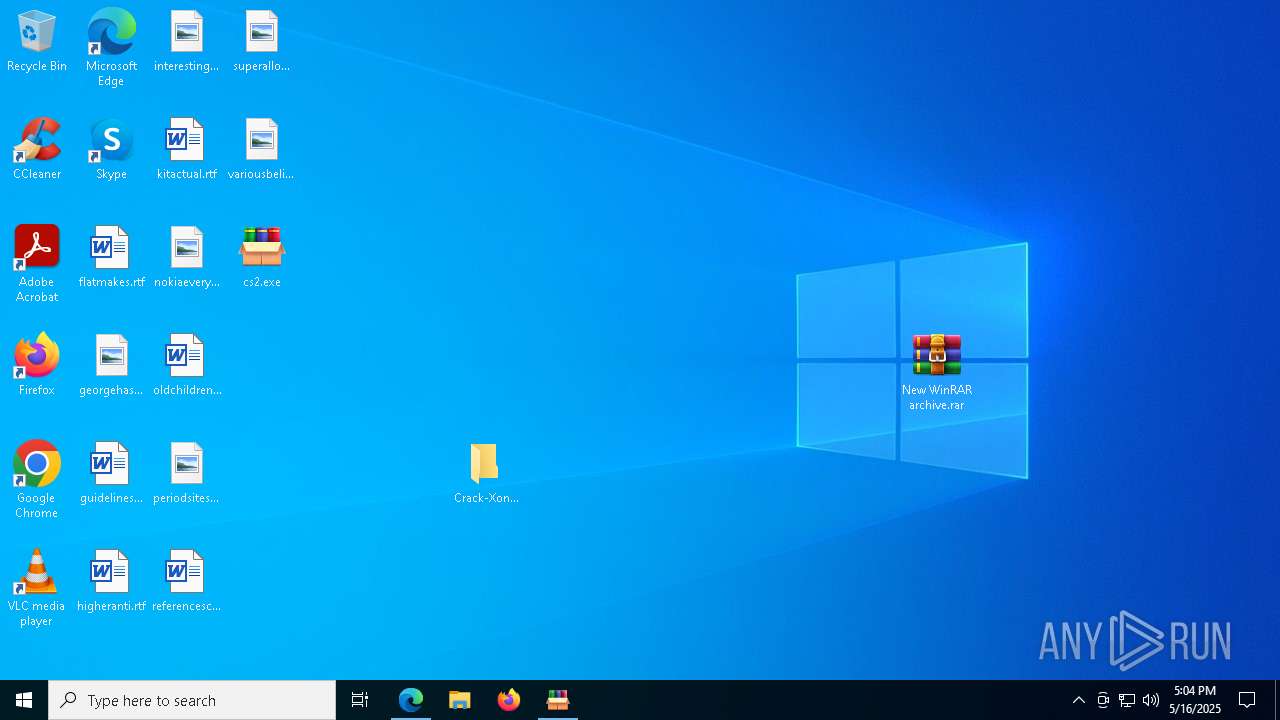
| Analysis date: | May 16, 2025, 17:03:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AB1141C1D4CB23CBB1D092D895605EA2 |
| SHA1: | 2D154B70126050B15C6D4FE69DF03828E0FC7533 |
| SHA256: | 5B121834430A5B42BAD359D5A736C414DE4D77F6A8AA3F4B7931BDD97ED23738 |
| SSDEEP: | 3:N8tEd4b9UGHtOEGYgZ8IHn:2uU9UGOOt0n |
MALICIOUS
Changes the autorun value in the registry
- Launcher.exe (PID: 4152)
NjRAT is detected
- Launcher.exe (PID: 4152)
Create files in the Startup directory
- Launcher.exe (PID: 4152)
NJRAT has been detected (YARA)
- Launcher.exe (PID: 4152)
SUSPICIOUS
Reads Microsoft Outlook installation path
- cs2.exe (PID: 7156)
Reads security settings of Internet Explorer
- cs2.exe (PID: 7156)
Reads Internet Explorer settings
- cs2.exe (PID: 7156)
Uses NETSH.EXE to add a firewall rule or allowed programs
- Launcher.exe (PID: 4152)
There is functionality for taking screenshot (YARA)
- cs2.exe (PID: 7156)
Connects to unusual port
- Launcher.exe (PID: 4152)
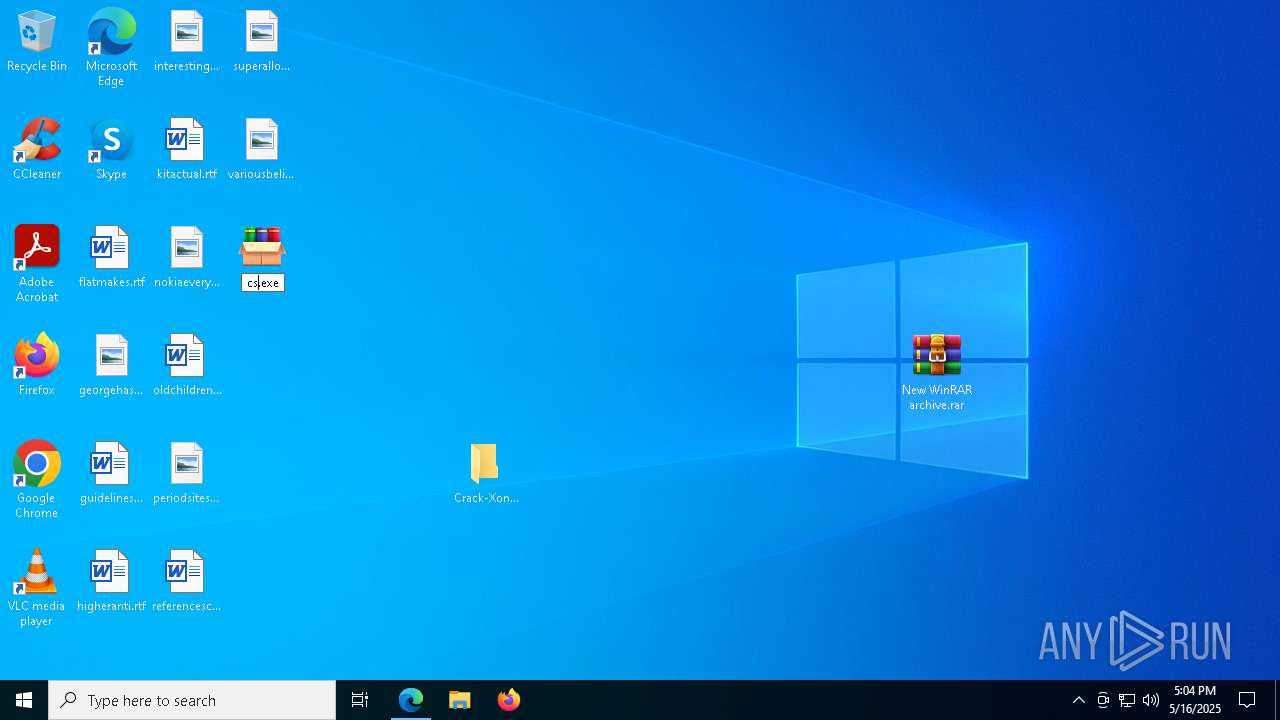
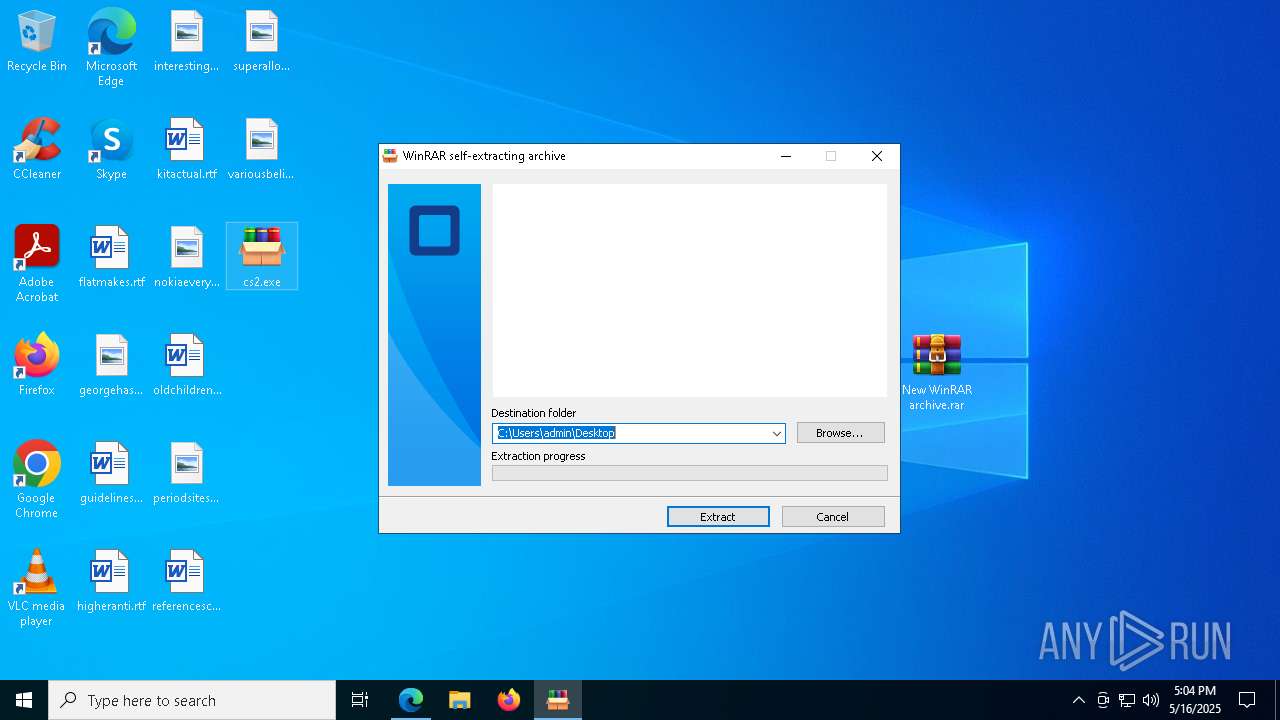
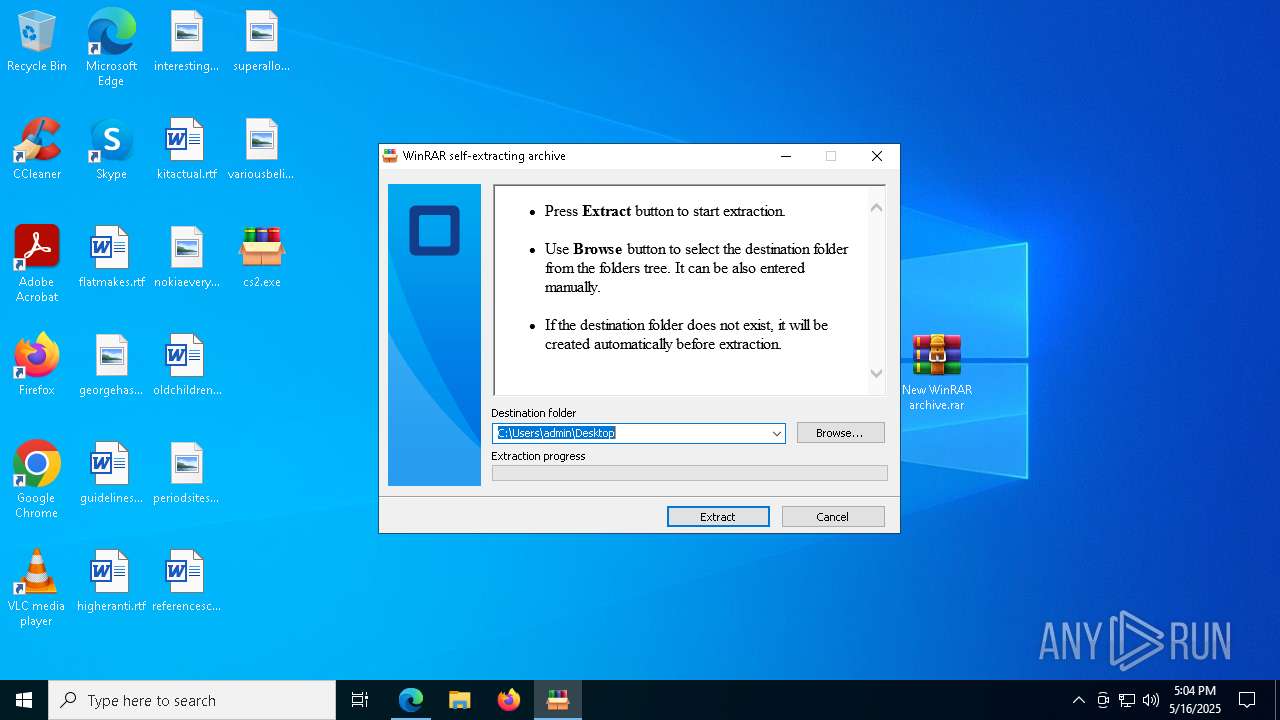
Executable content was dropped or overwritten
- Launcher.exe (PID: 4152)
INFO
Application launched itself
- msedge.exe (PID: 2852)
Reads Environment values
- identity_helper.exe (PID: 4008)
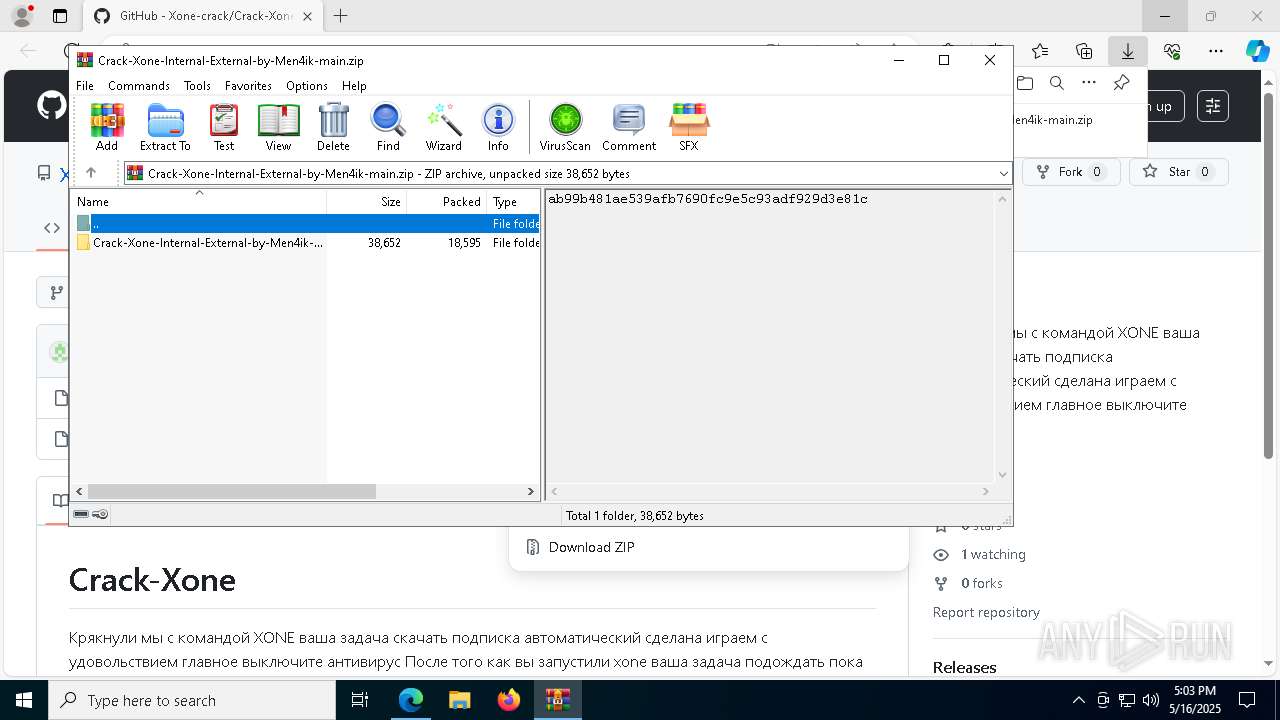
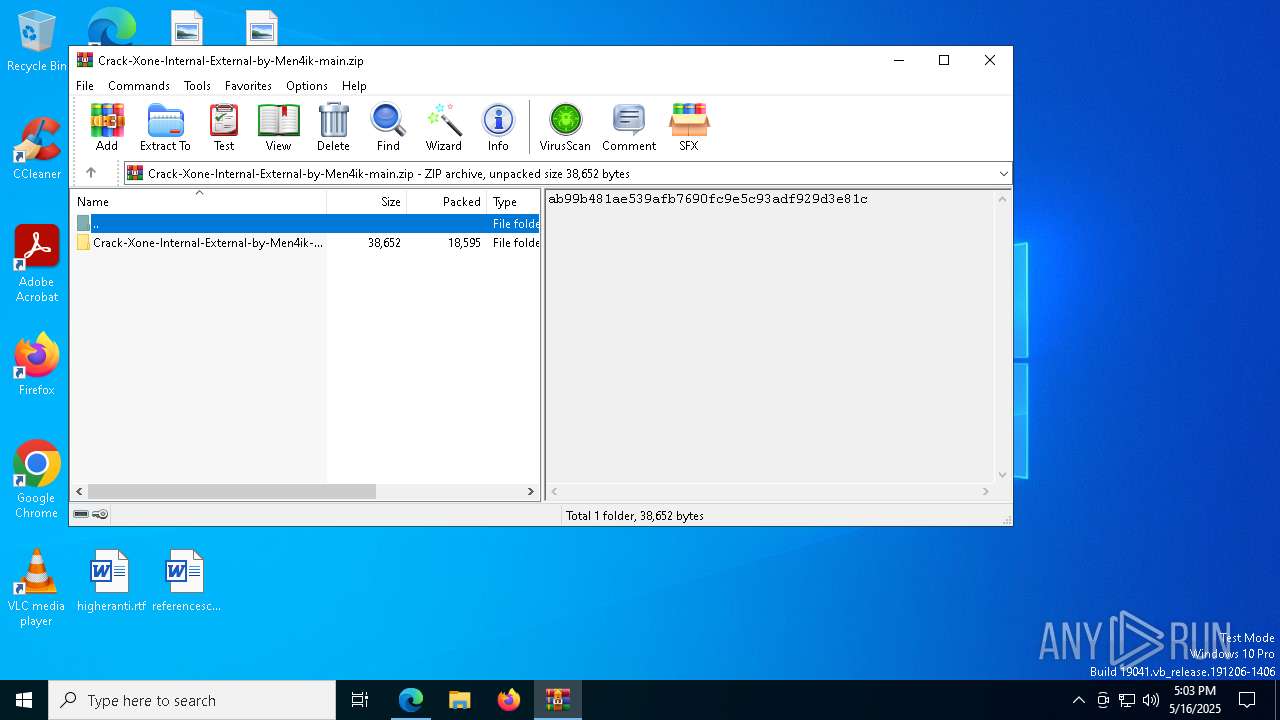
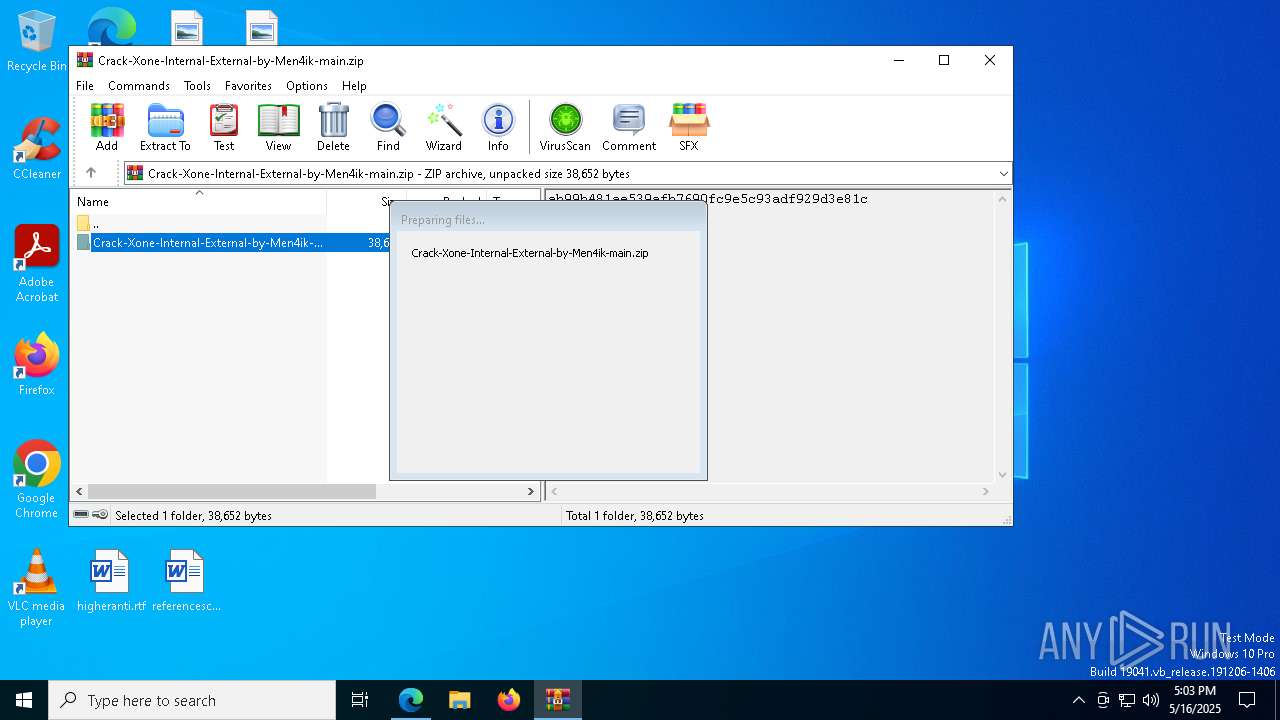
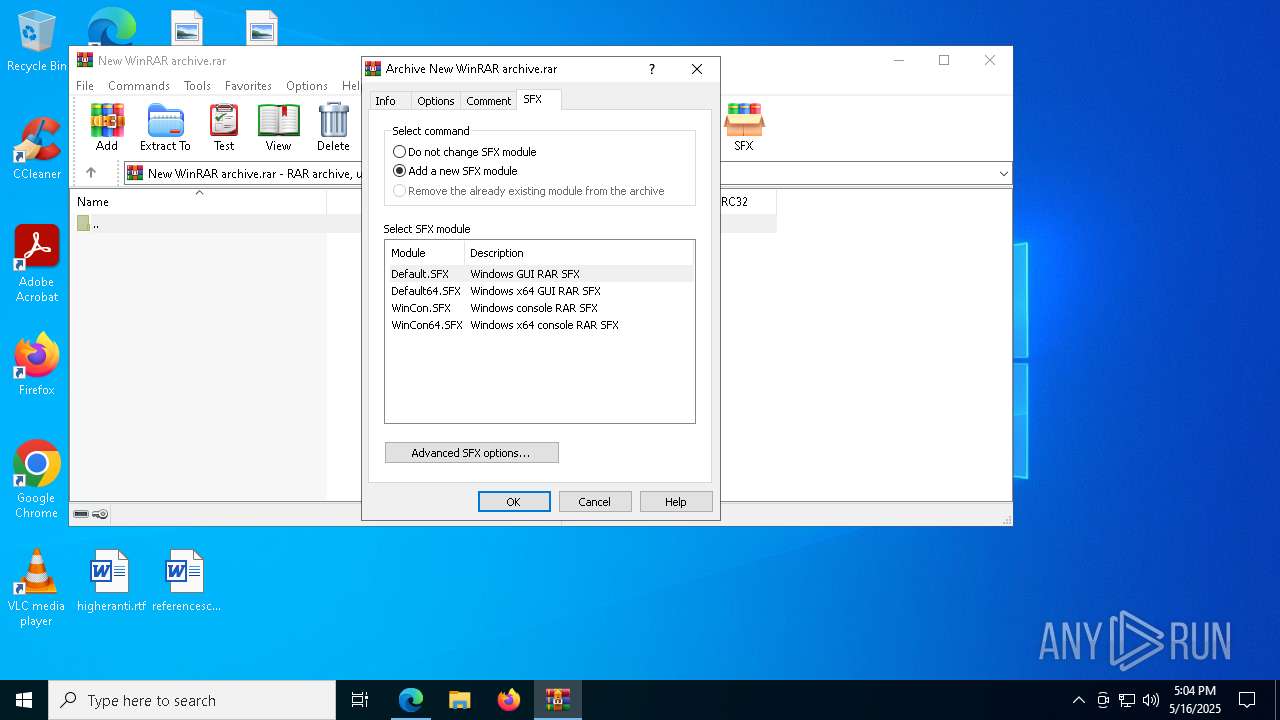
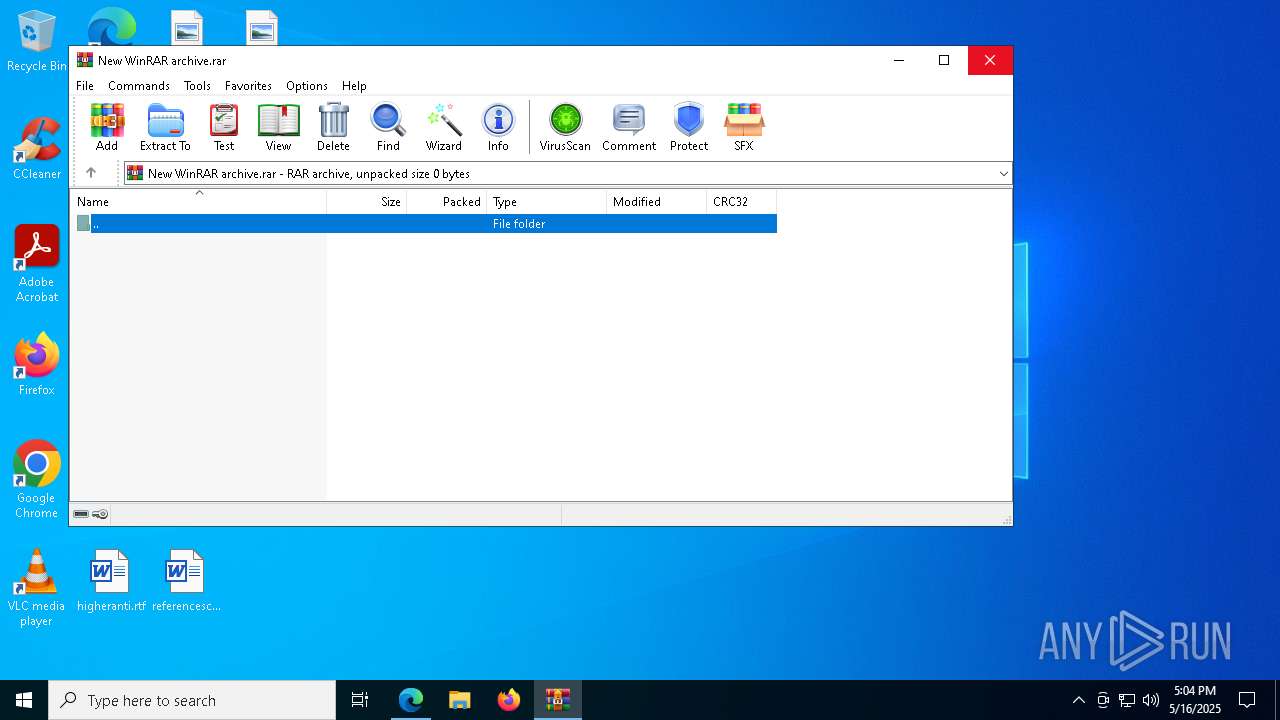
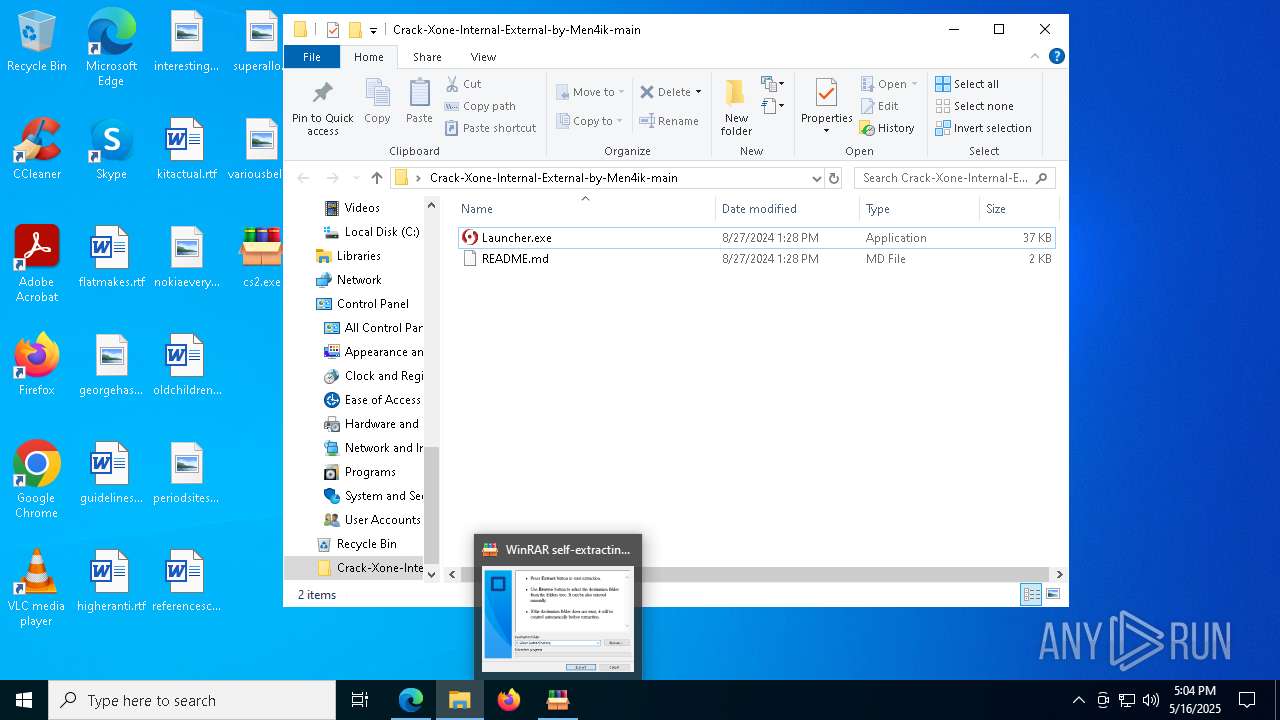
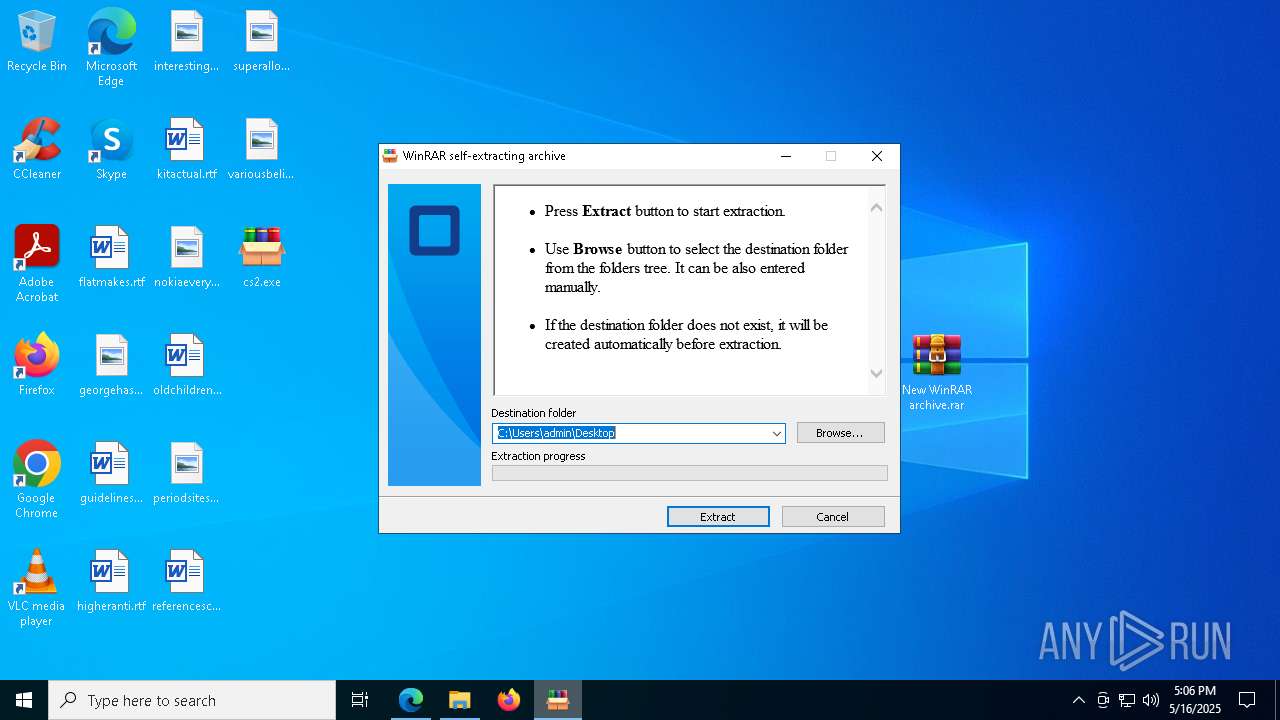
Executable content was dropped or overwritten
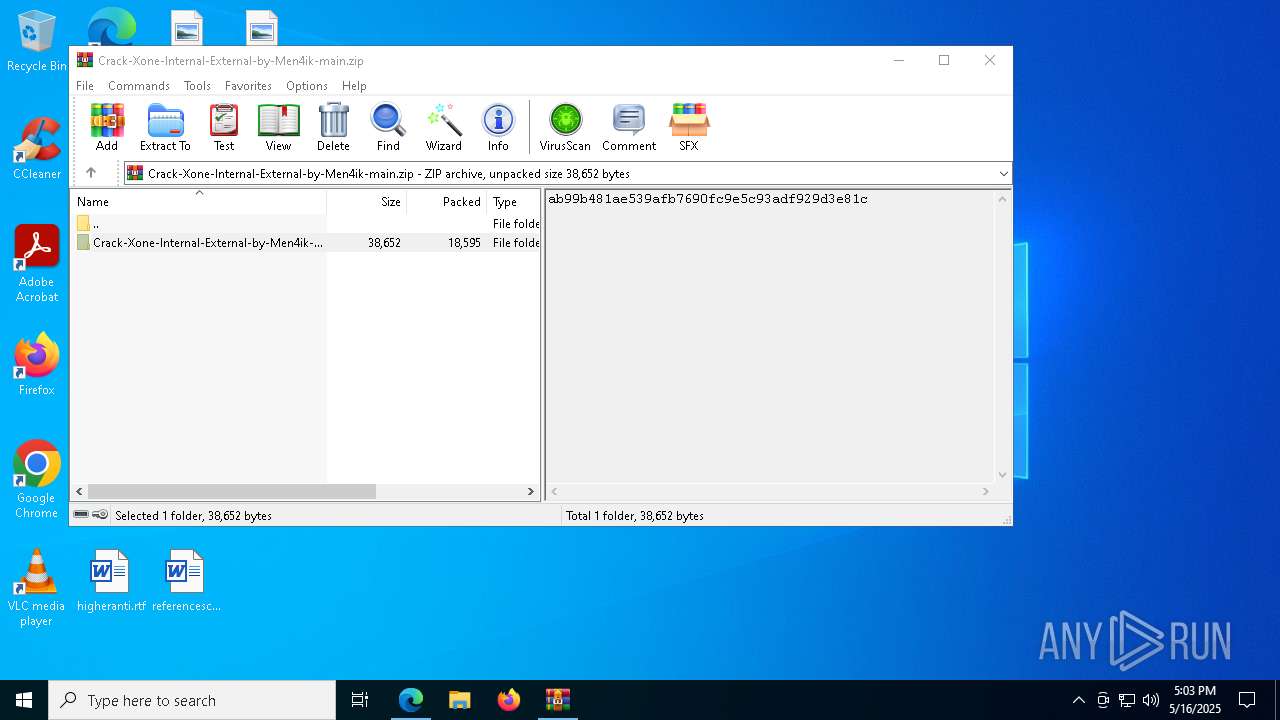
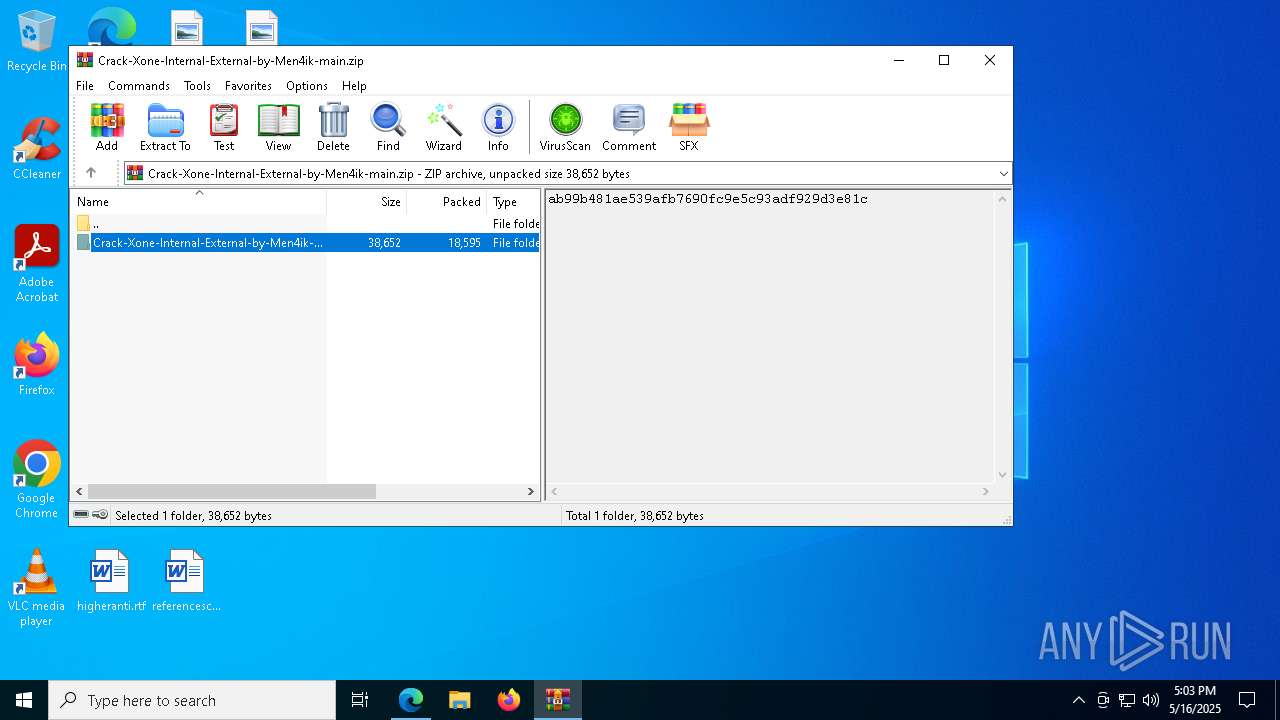
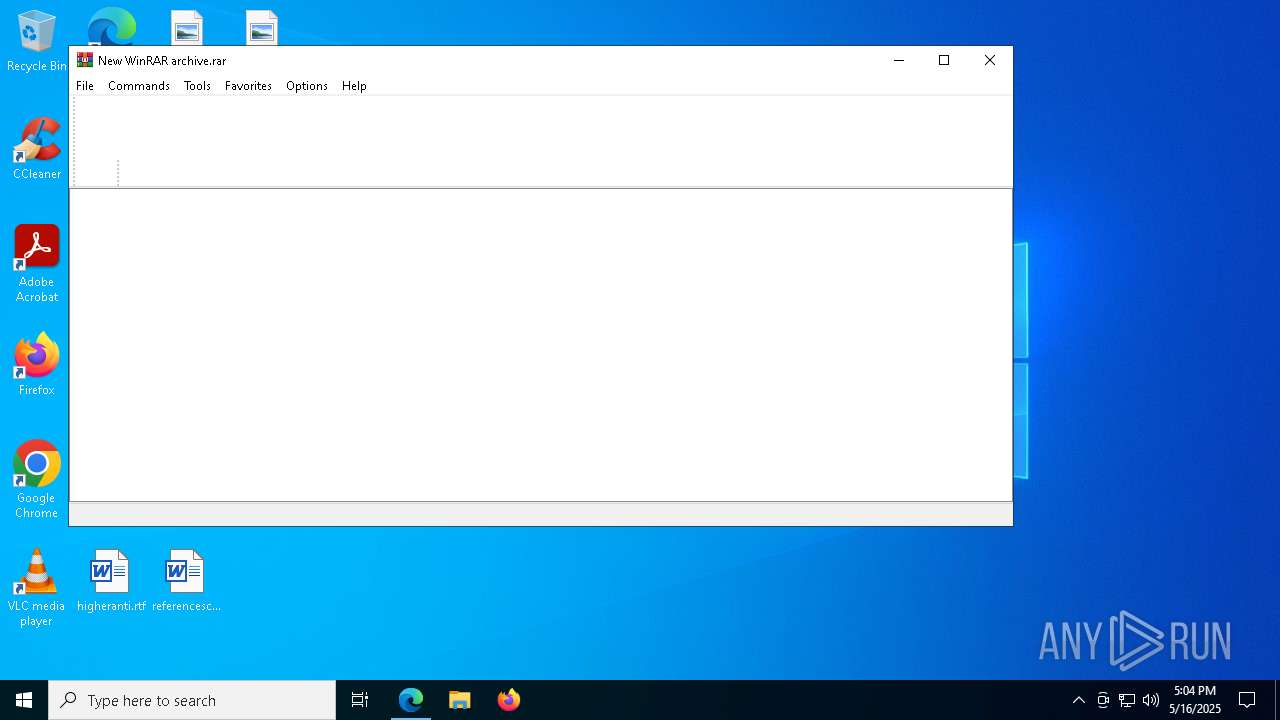
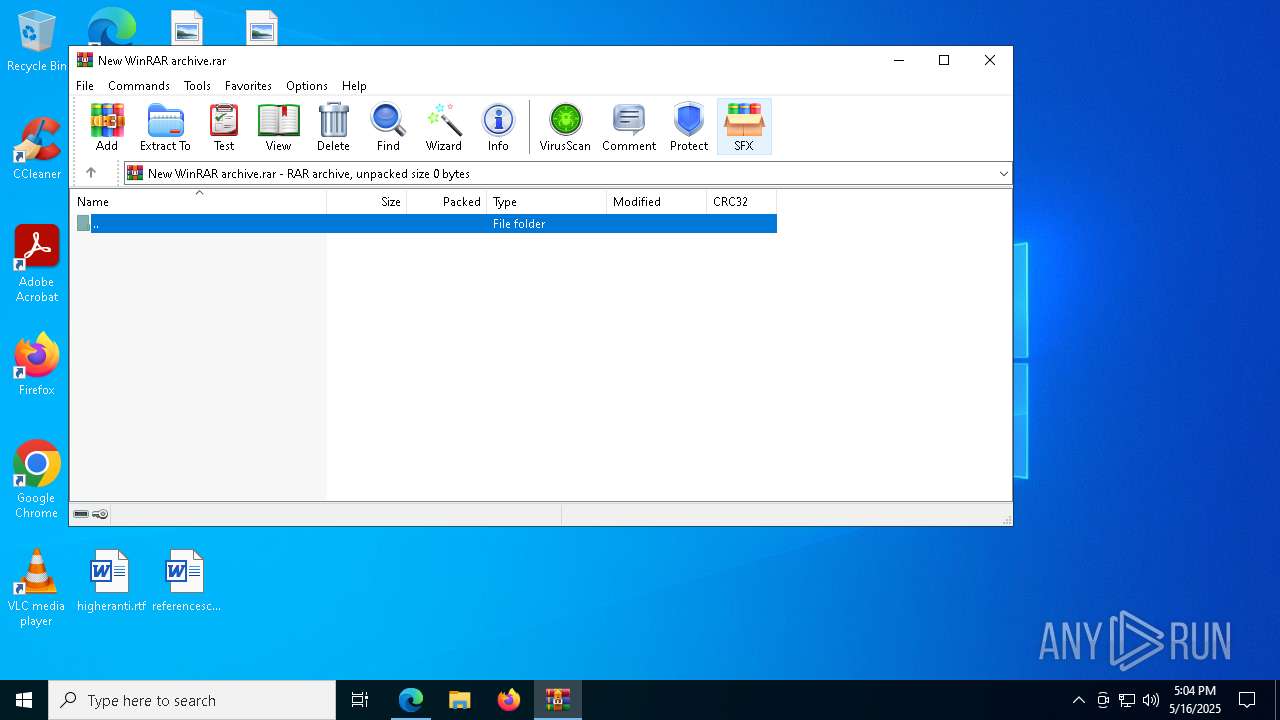
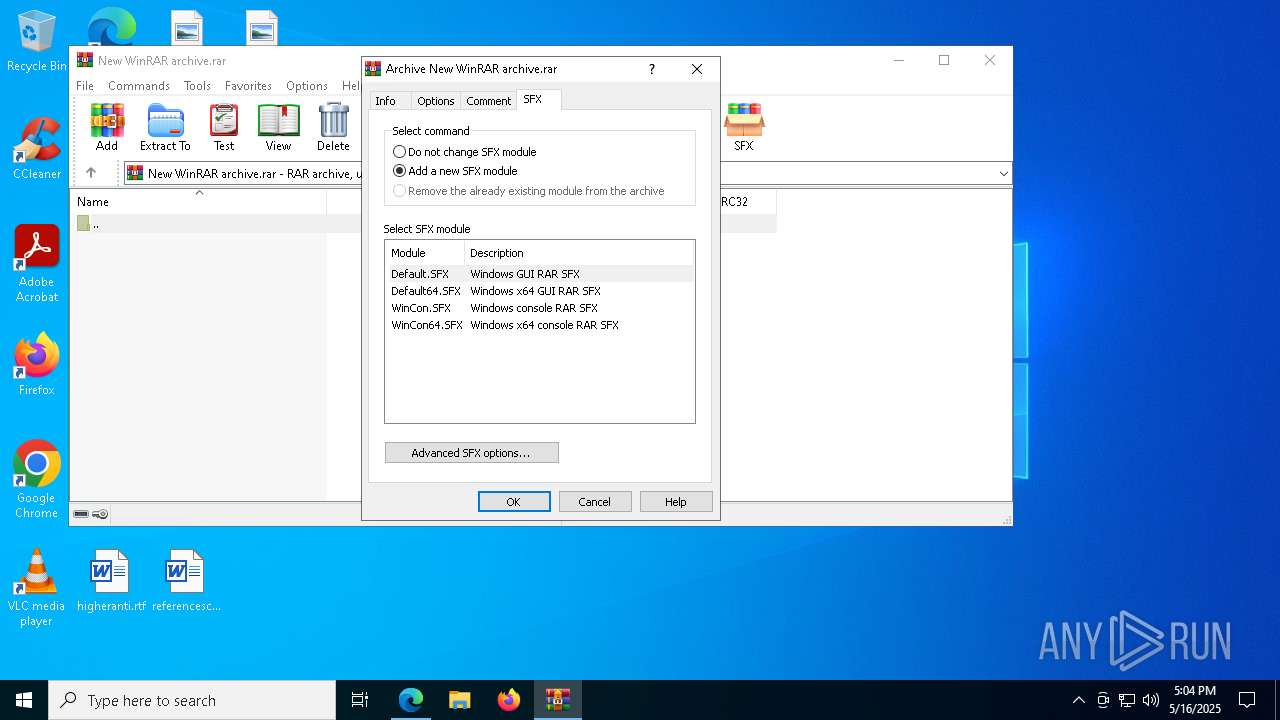
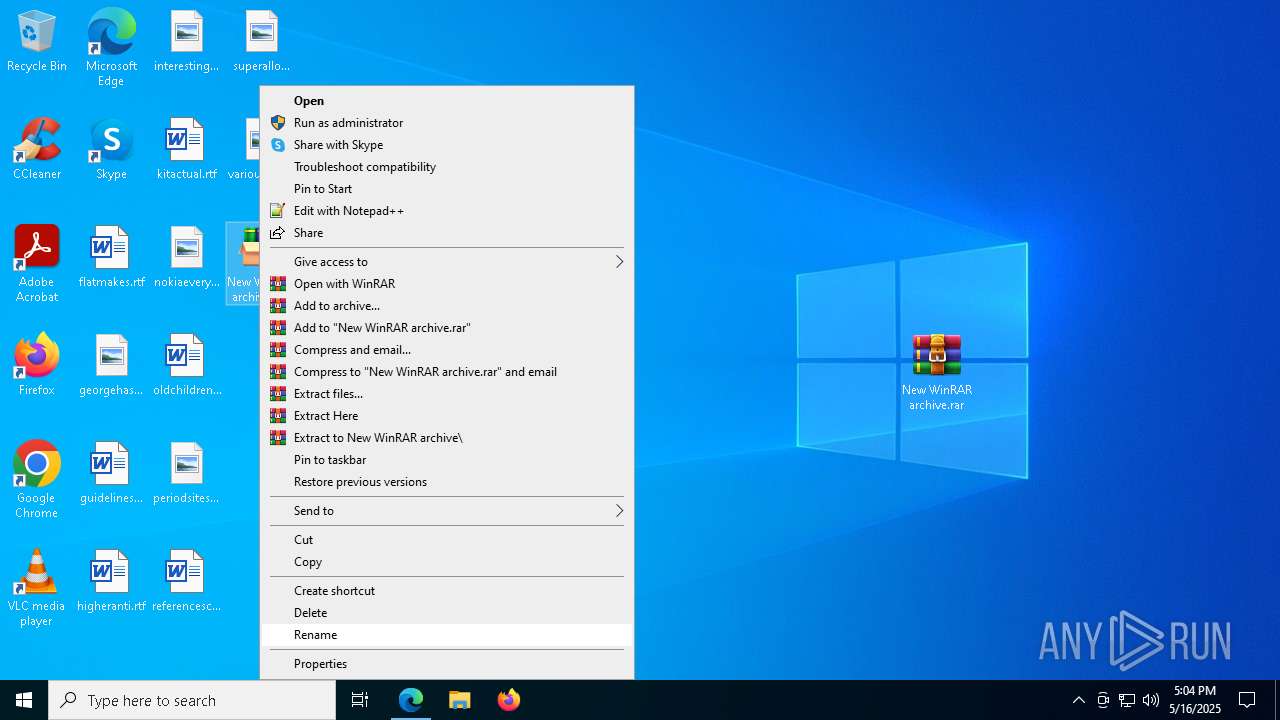
- WinRAR.exe (PID: 2384)
- WinRAR.exe (PID: 6944)
- msedge.exe (PID: 4980)
Reads the computer name
- identity_helper.exe (PID: 4008)
- cs2.exe (PID: 7156)
- Launcher.exe (PID: 4152)
Checks supported languages
- identity_helper.exe (PID: 4008)
- cs2.exe (PID: 7156)
- Launcher.exe (PID: 4152)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2852)
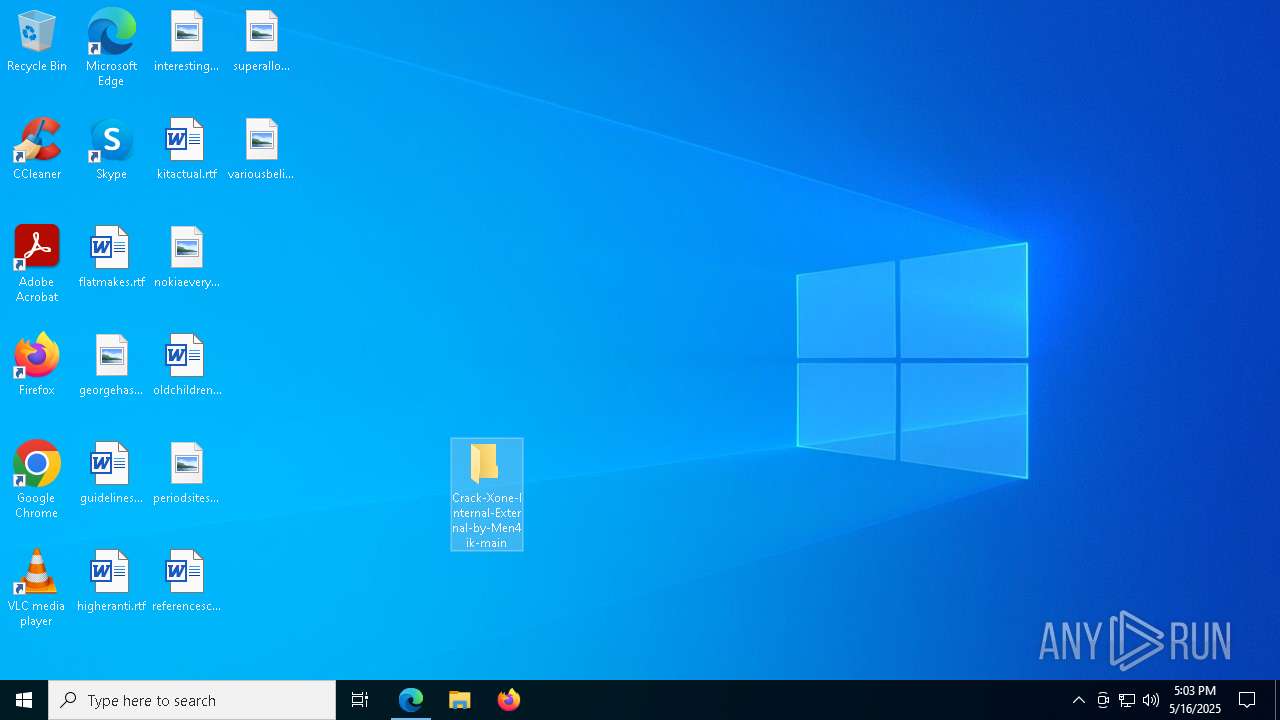
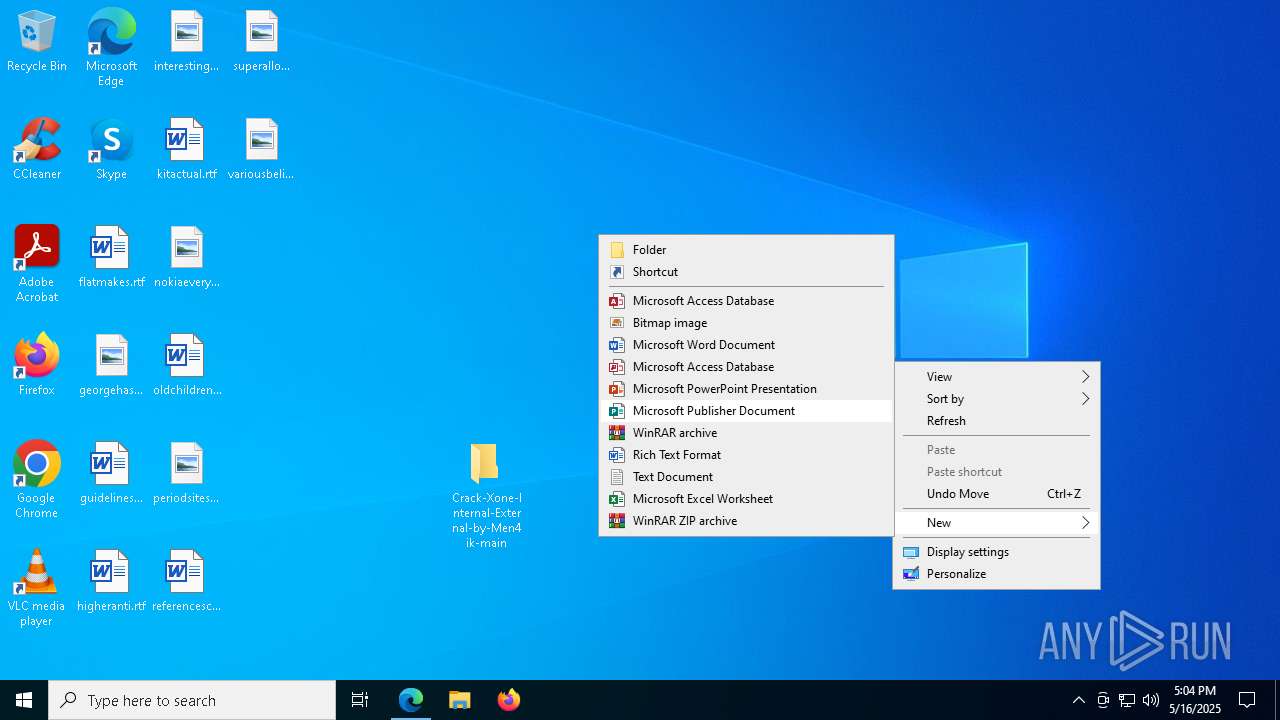
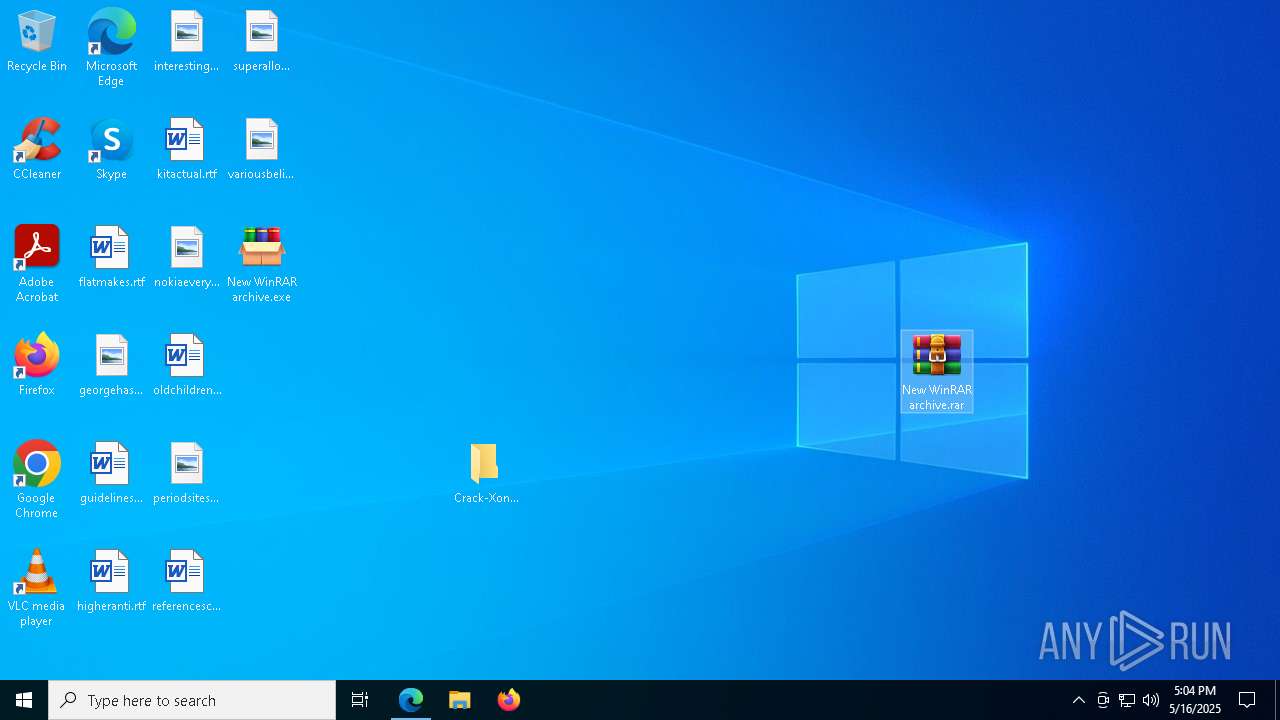
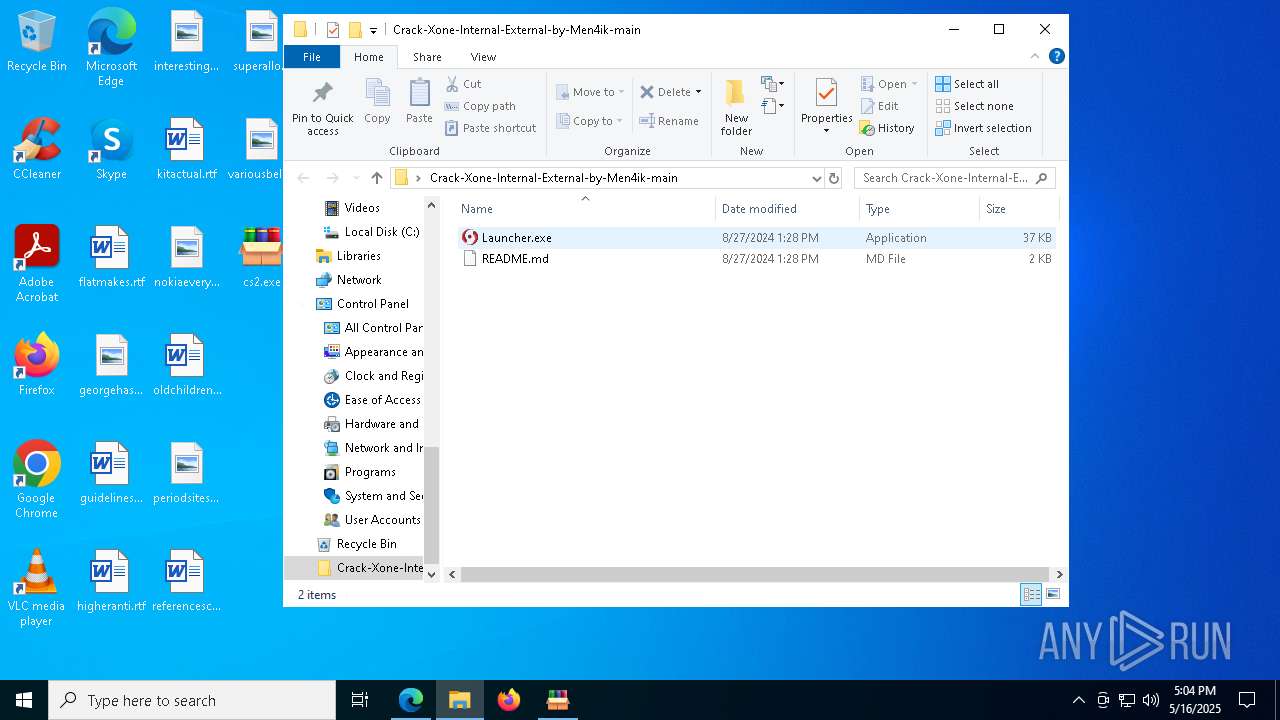
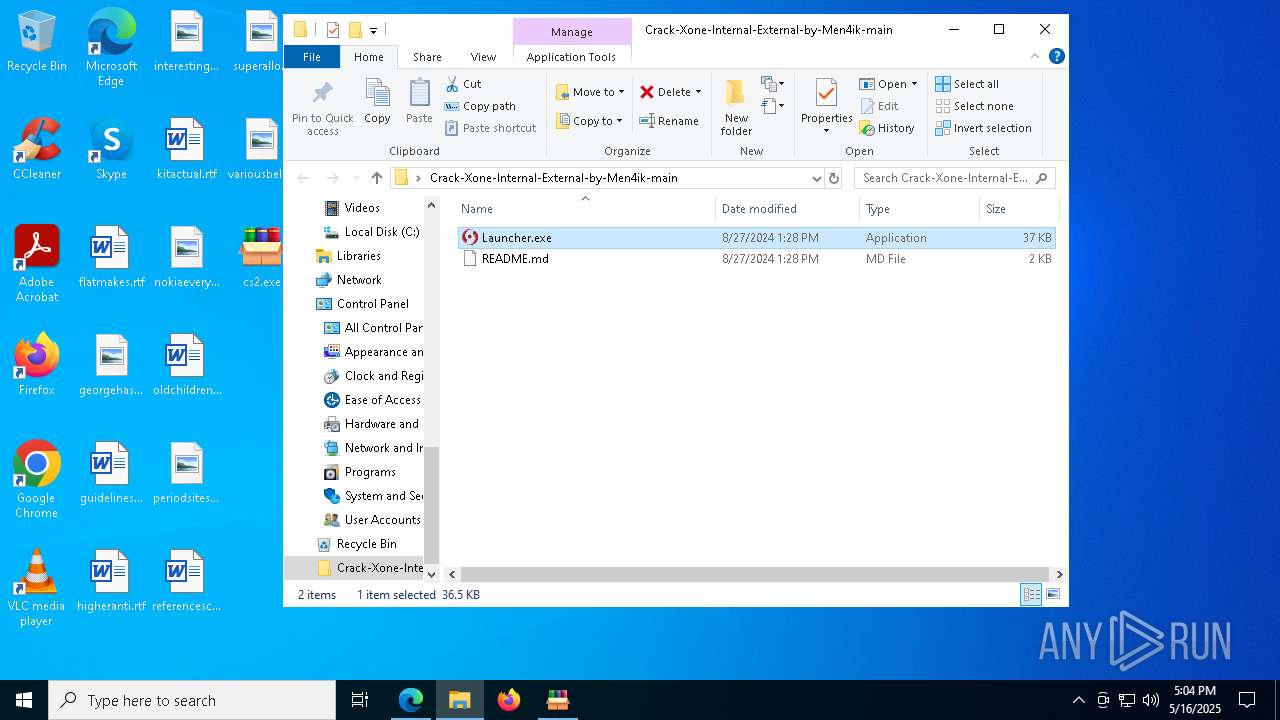
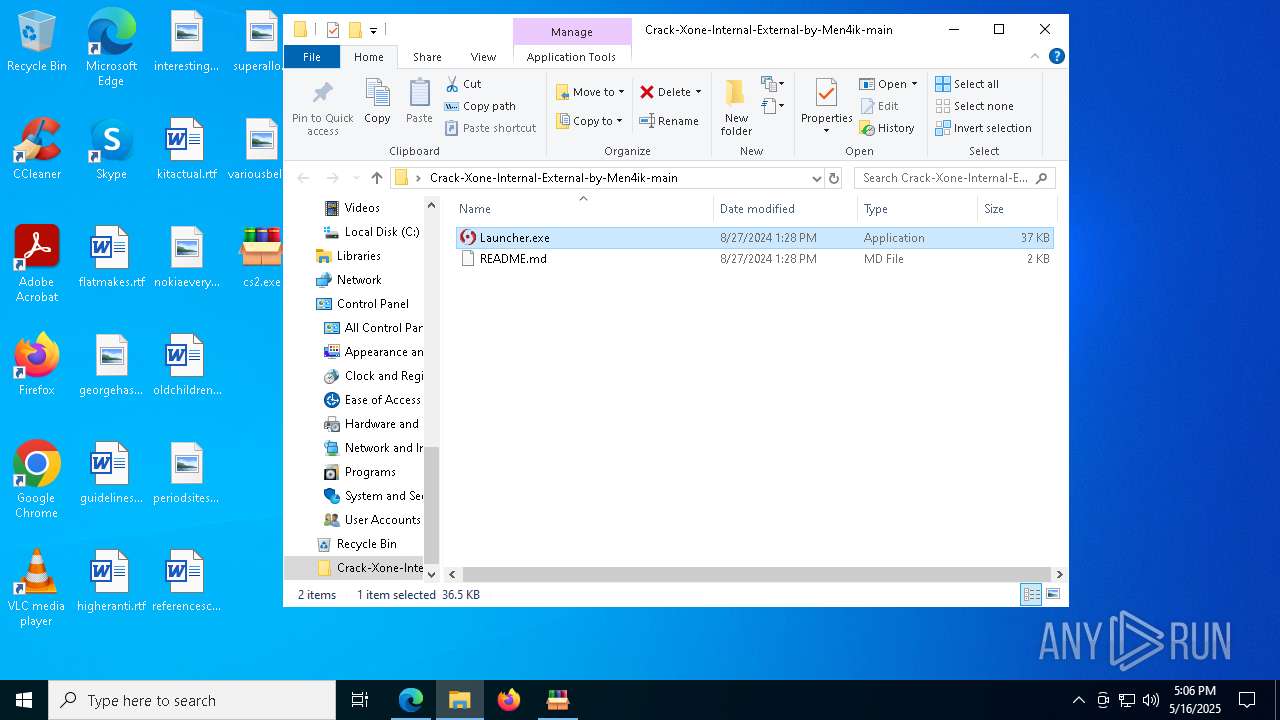
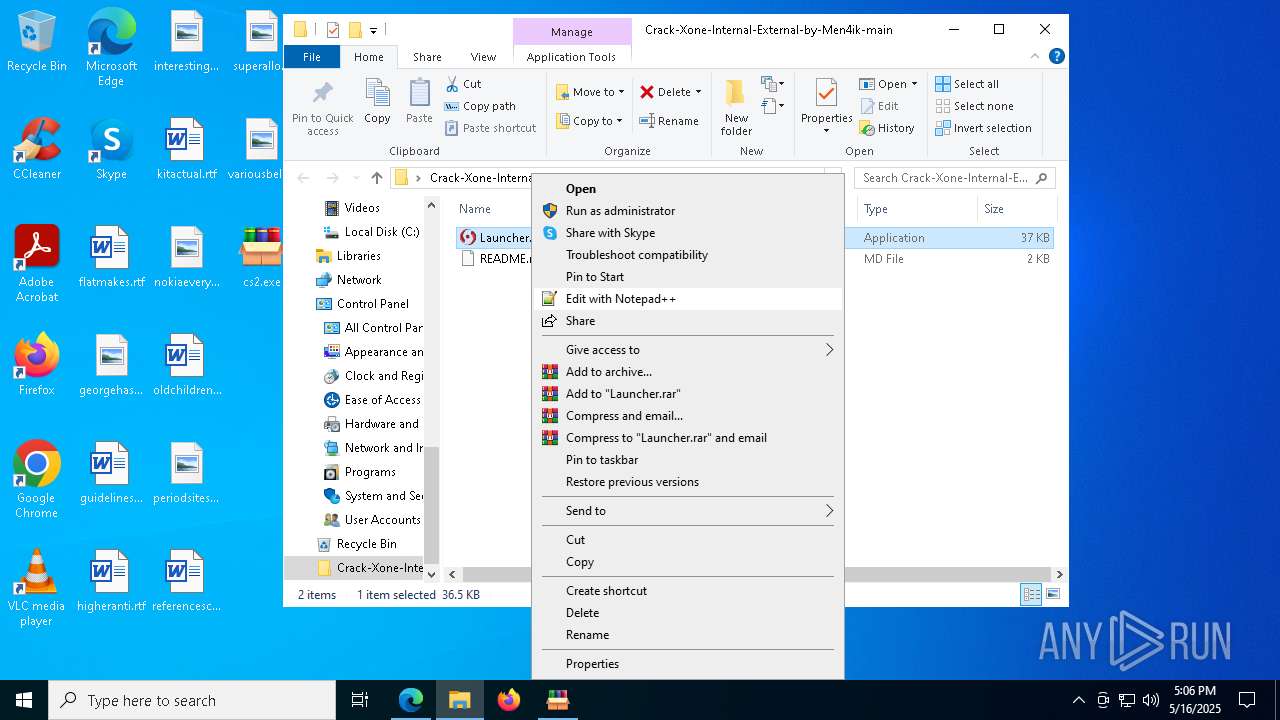
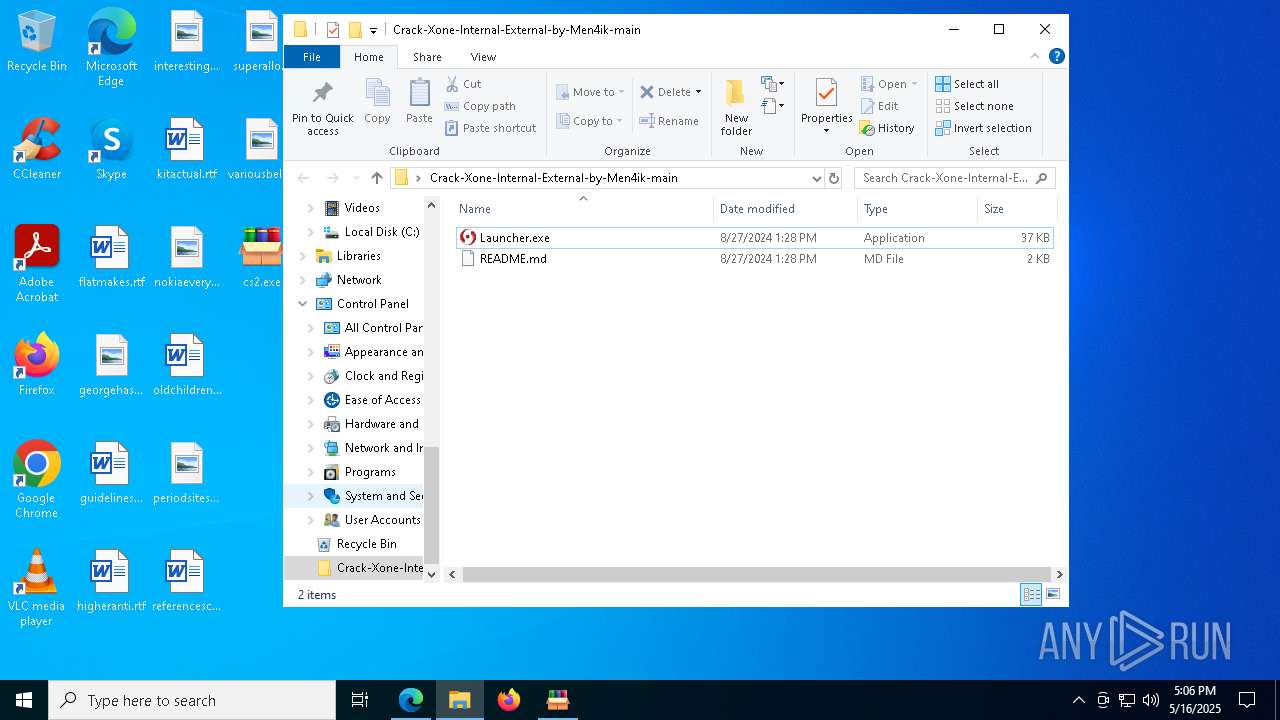
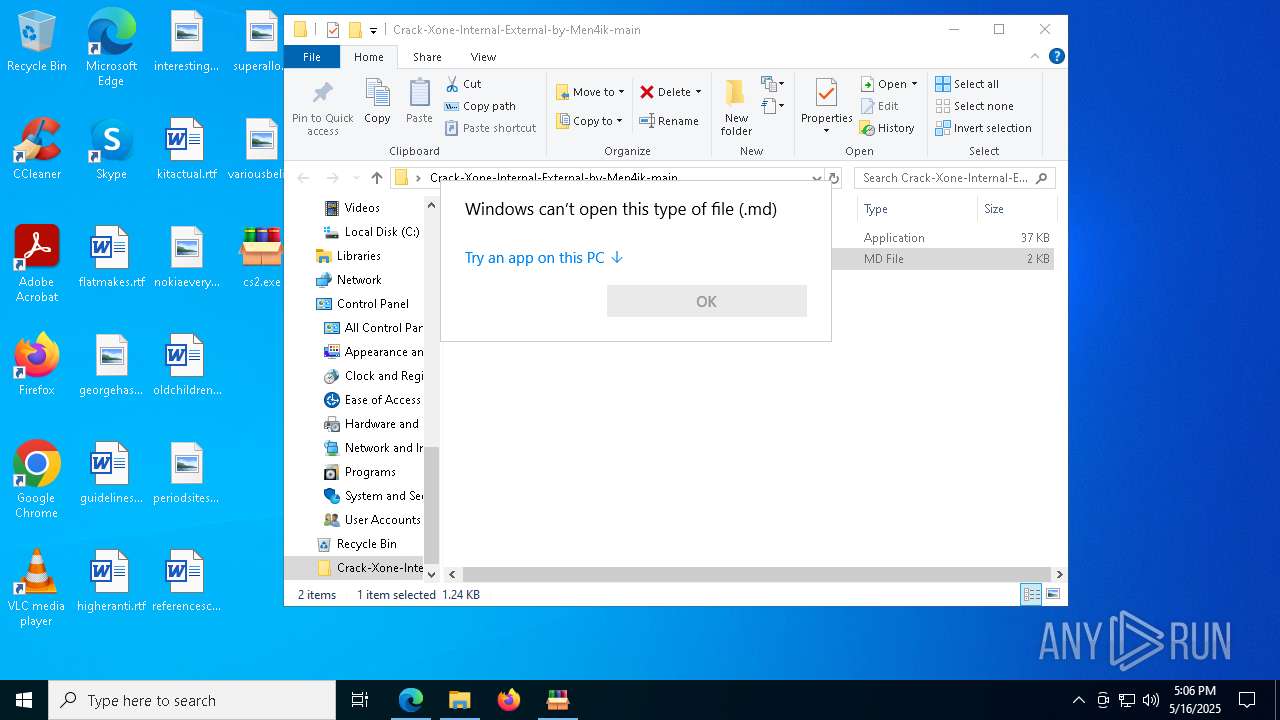
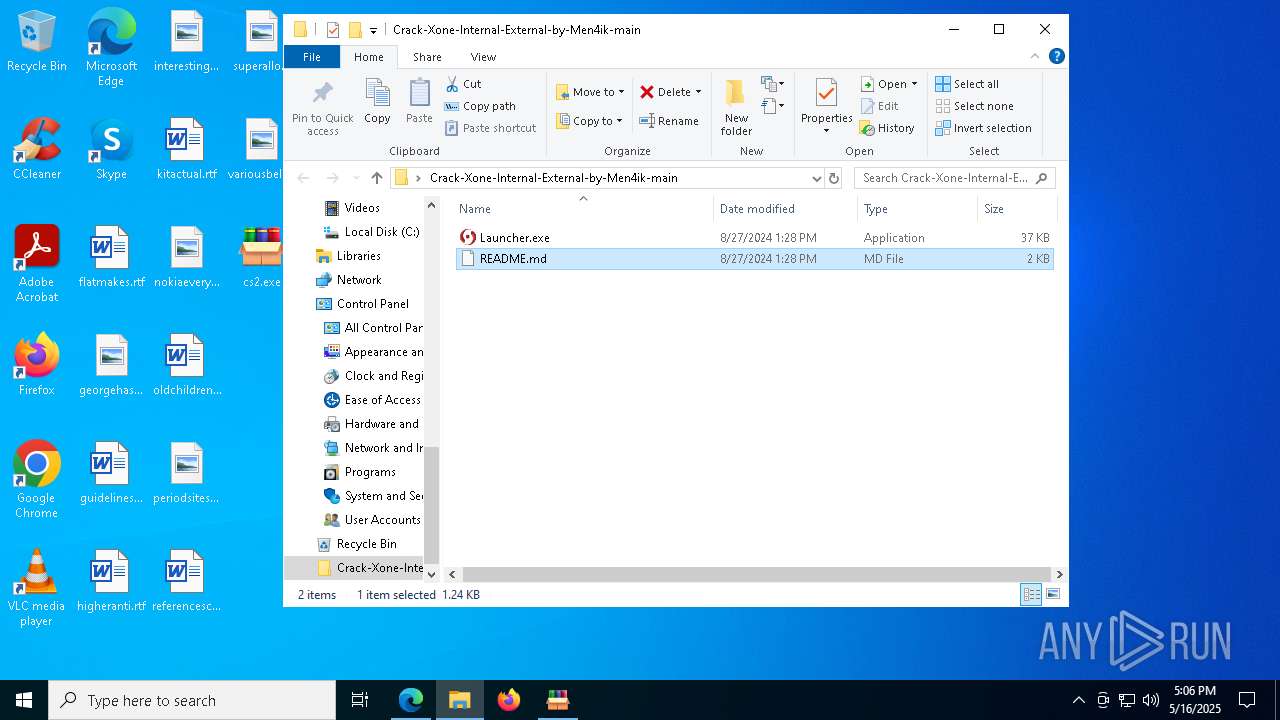
Manual execution by a user
- WinRAR.exe (PID: 6944)
- cs2.exe (PID: 7156)
- Launcher.exe (PID: 4152)
- Launcher.exe (PID: 684)
Checks proxy server information
- cs2.exe (PID: 7156)
Reads the machine GUID from the registry
- Launcher.exe (PID: 4152)
Creates files or folders in the user directory
- Launcher.exe (PID: 4152)
The sample compiled with english language support
- msedge.exe (PID: 4980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
NjRat
(PID) Process(4152) Launcher.exe
C222.ip.gl.ply.gg
Ports14099
BotnetMyBot
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\08d7481f1e10d3c0cd4ba3821958de61
SplitterY262SUCZ4UJJ
Version0.7d
Total processes
189
Monitored processes
56
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | "C:\Users\admin\Desktop\Crack-Xone-Internal-External-by-Men4ik-main\Launcher.exe" | C:\Users\admin\Desktop\Crack-Xone-Internal-External-by-Men4ik-main\Launcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 920 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6628 --field-trial-handle=2512,i,13277390202913927386,15288604352865704083,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1544 --field-trial-handle=2512,i,13277390202913927386,15288604352865704083,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6628 --field-trial-handle=2512,i,13277390202913927386,15288604352865704083,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7436 --field-trial-handle=2512,i,13277390202913927386,15288604352865704083,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Crack-Xone-Internal-External-by-Men4ik-main.zip" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2568 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/Xone-crack/Crack-Xone-Internal-External-by-Men4ik" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
12 352
Read events
12 145
Write events
207
Delete events
0
Modification events
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 31AC310CDA932F00 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 46DE3C0CDA932F00 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {87070425-2C3E-4D67-9F98-2293856DF20D} | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {84D01E48-1D0A-4928-9D07-8CCBFAB7A0F6} | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F9934907-BC18-46FE-B08B-E8725D738267} | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6AD28909-7F1F-4088-9715-6A637F5545A4} | |||
Executable files
8
Suspicious files
230
Text files
45
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10cf0a.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10cf0a.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10cf19.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10cf87.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10cf77.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
75
DNS requests
75
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5112 | svchost.exe | HEAD | 200 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747697096&P2=404&P3=2&P4=gwKlWiOVp1aJeCNdoCYyrndm1XkG7QD7zT8LTGAFgOcC7QRRR%2fwZJzpm6v%2f9fC6i8dTDVznhGDmz5ZpThh38fQ%3d%3d | unknown | — | — | whitelisted |
8116 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8116 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5112 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747697096&P2=404&P3=2&P4=gwKlWiOVp1aJeCNdoCYyrndm1XkG7QD7zT8LTGAFgOcC7QRRR%2fwZJzpm6v%2f9fC6i8dTDVznhGDmz5ZpThh38fQ%3d%3d | unknown | — | — | whitelisted |
5112 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747697096&P2=404&P3=2&P4=gwKlWiOVp1aJeCNdoCYyrndm1XkG7QD7zT8LTGAFgOcC7QRRR%2fwZJzpm6v%2f9fC6i8dTDVznhGDmz5ZpThh38fQ%3d%3d | unknown | — | — | whitelisted |
5112 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747697096&P2=404&P3=2&P4=YS6cDIL4TfJVD6im0GIKyuXCLorqFjpQ2mUcGJht%2buK%2bTsoxOXQv9jwG42Eqlmapkn7f9drZNqJbjClllxtlnQ%3d%3d | unknown | — | — | whitelisted |
5112 | svchost.exe | HEAD | 200 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747697096&P2=404&P3=2&P4=YS6cDIL4TfJVD6im0GIKyuXCLorqFjpQ2mUcGJht%2buK%2bTsoxOXQv9jwG42Eqlmapkn7f9drZNqJbjClllxtlnQ%3d%3d | unknown | — | — | whitelisted |
5112 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747697096&P2=404&P3=2&P4=YS6cDIL4TfJVD6im0GIKyuXCLorqFjpQ2mUcGJht%2buK%2bTsoxOXQv9jwG42Eqlmapkn7f9drZNqJbjClllxtlnQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
7196 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2852 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7196 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7196 | msedge.exe | 13.107.246.53:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7196 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7196 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7196 | msedge.exe | 185.199.108.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |