| File name: | GeneratedInstaller.ps1 |
| Full analysis: | https://app.any.run/tasks/babf8763-1b37-4829-9f3b-9b49cd8f541f |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | March 22, 2025, 22:05:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 (with BOM) text, with very long lines (65483), with CRLF line terminators |
| MD5: | 3524B487C94C169F5075F1B105C57FCF |
| SHA1: | BD8B6B99C5B96F060050B6F44CE52C393679C8B7 |
| SHA256: | 5B0F31D2BF3178514FD0156DA1F7D3B2686BADB7BDBD8D831034EC5B731A127F |
| SSDEEP: | 49152:JYPyt6/IEuTXXQcWvm4H0A6ioeuY2axnUJ3b7nTYaGr7RcWXnFIH+lGkuhMEgXe0:8 |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 2384)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 2384)
Known privilege escalation attack
- dllhost.exe (PID: 7432)
- dllhost.exe (PID: 7544)
Vulnerable driver has been detected
- CiscoCollabHost.exe (PID: 7512)
Actions looks like stealing of personal data
- CiscoCollabHost.exe (PID: 7512)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 7592)
- cmd.exe (PID: 7528)
AMADEY has been detected (YARA)
- Gxtuum.exe (PID: 7736)
SUSPICIOUS
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 2384)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 2384)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2384)
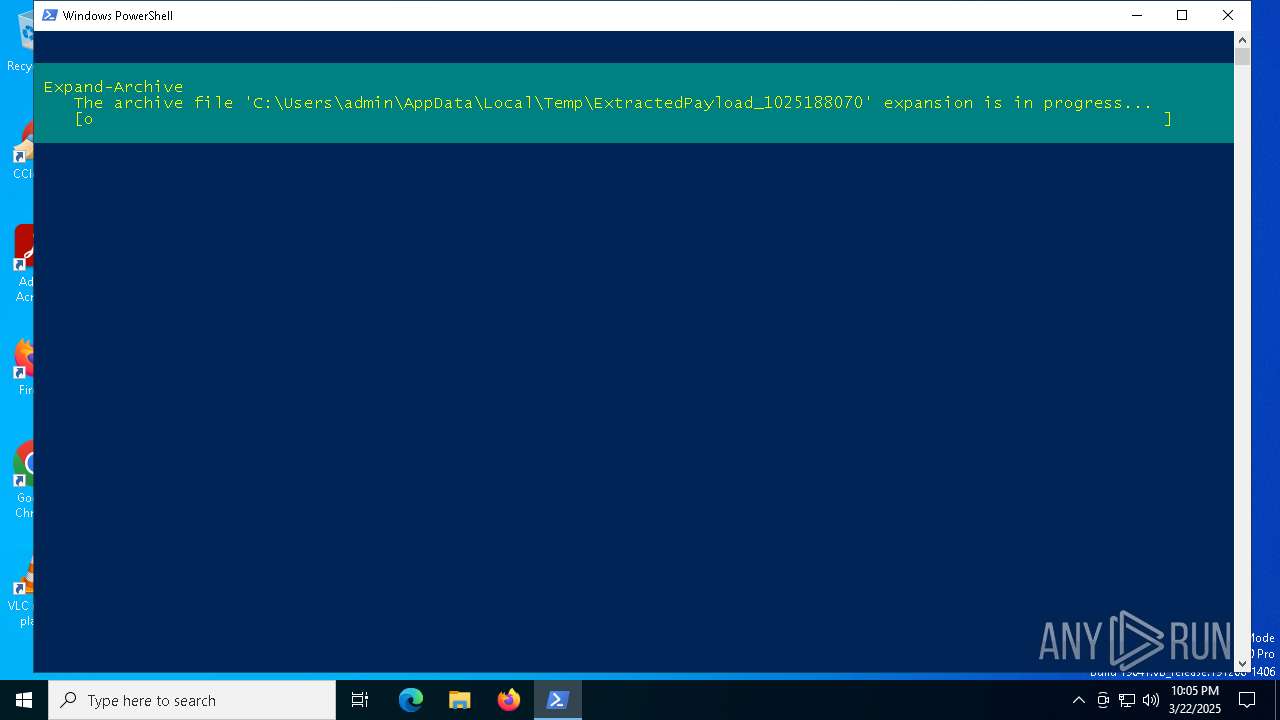
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 2384)
The process creates files with name similar to system file names
- powershell.exe (PID: 2384)
- CiscoCollabHost.exe (PID: 7296)
- CiscoCollabHost.exe (PID: 7512)
- WerFault.exe (PID: 7828)
- WerFault.exe (PID: 8024)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 2384)
Executable content was dropped or overwritten
- powershell.exe (PID: 2384)
- CiscoCollabHost.exe (PID: 7296)
- CiscoCollabHost.exe (PID: 7512)
- svchost.exe (PID: 7684)
Drops a system driver (possible attempt to evade defenses)
- CiscoCollabHost.exe (PID: 7512)
Starts CMD.EXE for commands execution
- CiscoCollabHost.exe (PID: 7512)
- CiscoCollabHost.exe (PID: 3008)
The process verifies whether the antivirus software is installed
- CiscoCollabHost.exe (PID: 7512)
Reads security settings of Internet Explorer
- svchost.exe (PID: 7684)
- Gxtuum.exe (PID: 7736)
Starts itself from another location
- svchost.exe (PID: 7684)
Executes application which crashes
- CiscoCollabHost.exe (PID: 7512)
- CiscoCollabHost.exe (PID: 3008)
There is functionality for enable RDP (YARA)
- Gxtuum.exe (PID: 7736)
There is functionality for taking screenshot (YARA)
- Gxtuum.exe (PID: 7736)
The process executes via Task Scheduler
- Gxtuum.exe (PID: 1616)
- Gxtuum.exe (PID: 7368)
INFO
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2384)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 2384)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2384)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 2384)
The executable file from the user directory is run by the Powershell process
- CiscoCollabHost.exe (PID: 7296)
Checks supported languages
- CiscoCollabHost.exe (PID: 7296)
- CiscoCollabHost.exe (PID: 7512)
- svchost.exe (PID: 7684)
- Gxtuum.exe (PID: 7736)
- CiscoCollabHost.exe (PID: 7924)
- CiscoCollabHost.exe (PID: 7336)
- CiscoCollabHost.exe (PID: 3008)
- svchost.exe (PID: 8128)
- Gxtuum.exe (PID: 1616)
- Gxtuum.exe (PID: 7368)
Reads the computer name
- CiscoCollabHost.exe (PID: 7296)
- CiscoCollabHost.exe (PID: 7512)
- svchost.exe (PID: 7684)
- Gxtuum.exe (PID: 7736)
- CiscoCollabHost.exe (PID: 7924)
- CiscoCollabHost.exe (PID: 7336)
- CiscoCollabHost.exe (PID: 3008)
Reads the machine GUID from the registry
- CiscoCollabHost.exe (PID: 7296)
- CiscoCollabHost.exe (PID: 7336)
Creates files or folders in the user directory
- CiscoCollabHost.exe (PID: 7296)
- WerFault.exe (PID: 7828)
- BackgroundTransferHost.exe (PID: 728)
- WerFault.exe (PID: 8024)
Checks transactions between databases Windows and Oracle
- CiscoCollabHost.exe (PID: 7296)
- CiscoCollabHost.exe (PID: 7336)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 7432)
- BackgroundTransferHost.exe (PID: 7996)
- BackgroundTransferHost.exe (PID: 728)
- BackgroundTransferHost.exe (PID: 7252)
- BackgroundTransferHost.exe (PID: 7408)
- dllhost.exe (PID: 7544)
- BackgroundTransferHost.exe (PID: 7656)
Create files in a temporary directory
- CiscoCollabHost.exe (PID: 7512)
- svchost.exe (PID: 7684)
- CiscoCollabHost.exe (PID: 3008)
The sample compiled with english language support
- CiscoCollabHost.exe (PID: 7512)
Process checks computer location settings
- svchost.exe (PID: 7684)
Manual execution by a user
- CiscoCollabHost.exe (PID: 7924)
- CiscoCollabHost.exe (PID: 7336)
Checks proxy server information
- Gxtuum.exe (PID: 7736)
- BackgroundTransferHost.exe (PID: 728)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 728)
- slui.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(7736) Gxtuum.exe
C2179.43.171.217
URLhttp://179.43.171.217/b9kdj3s3C0/index.php
Version5.20
Options
Drop directoryb9bb355c6f
Drop nameGxtuum.exe
Strings (125)ps1
og:
r=
------
.jpg
rundll32.exe
GET
<c>
WinDefender
&&
pc:
wb
Norton
ProgramData\
rundll32
Powershell.exe
/k
kernel32.dll
5.20
179.43.171.217
Sophos
random
POST
cred.dll|clip.dll|
#
un:
Bitdefender
cred.dll
/Plugins/
shell32.dll
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
|
Doctor Web
e3
2019
Gxtuum.exe
00000419
Kaspersky Lab
st=s
%USERPROFILE%
\0000
VideoID
CurrentBuild
dll
ar:
bi:
Content-Type: multipart/form-data; boundary=----
+++
Startup
Avira
ESET
" && ren
msi
------
Content-Disposition: form-data; name="data"; filename="
Main
<d>
SYSTEM\ControlSet001\Services\BasicDisplay\Video
360TotalSecurity
=
e1
rb
Comodo
?scr=1
/b9kdj3s3C0/index.php
Panda Security
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
" && timeout 1 && del
2025
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
0123456789
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
Programs
00000422
lv:
e2
:::
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
SOFTWARE\Microsoft\Windows NT\CurrentVersion
dm:
AVG
DefaultSettings.YResolution
clip.dll
&unit=
AVAST Software
exe
http://
Keyboard Layout\Preload
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
cmd /C RMDIR /s/q
https://
shutdown -s -t 0
-unicode-
-executionpolicy remotesigned -File "
ComputerName
b9bb355c6f
2022
--
vs:
\
sd:
d1
S-%lu-
"
Content-Type: application/octet-stream
%-lu
GetNativeSystemInfo
&& Exit"
Content-Type: application/x-www-form-urlencoded
/quiet
abcdefghijklmnopqrstuvwxyz0123456789-_
ProductName
"taskkill /f /im "
00000423
Rem
zip
\App
2016
"
0000043f
os:
cmd
id:
av:
-%lu
DefaultSettings.XResolution
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
Total processes
169
Monitored processes
30
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "C:\Users\admin\AppData\Local\Temp\b9bb355c6f\Gxtuum.exe" | C:\Users\admin\AppData\Local\Temp\b9bb355c6f\Gxtuum.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\GeneratedInstaller.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3008 | "C:\Users\admin\AppData\Roaming\CiscoCollabHost.exe" | C:\Users\admin\AppData\Roaming\CiscoCollabHost.exe | dllhost.exe | ||||||||||||
User: admin Company: Cisco Systems, Inc Integrity Level: HIGH Description: Webex Exit code: 3221226356 Version: 1.0.0.2 Modules
| |||||||||||||||
| 4488 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6300 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7252 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7296 | "C:\Users\admin\AppData\Local\Temp\ExtractedPayload_1025188070\CiscoCollabHost.exe" | C:\Users\admin\AppData\Local\Temp\ExtractedPayload_1025188070\CiscoCollabHost.exe | powershell.exe | ||||||||||||
User: admin Company: Cisco Systems, Inc Integrity Level: MEDIUM Description: Webex Exit code: 0 Version: 1.0.0.2 Modules
| |||||||||||||||
Total events
13 240
Read events
13 190
Write events
44
Delete events
6
Modification events
| (PID) Process: | (2384) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MyPayload |
Value: C:\Users\admin\AppData\Local\Temp\ExtractedPayload_1025188070\CiscoCollabHost.exe | |||
| (PID) Process: | (7828) WerFault.exe | Key: | \REGISTRY\A\{4218becc-6fdb-f1a5-4a0f-b1a40c8040bf}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (7828) WerFault.exe | Key: | \REGISTRY\A\{4218becc-6fdb-f1a5-4a0f-b1a40c8040bf}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7828) WerFault.exe | Key: | \REGISTRY\A\{4218becc-6fdb-f1a5-4a0f-b1a40c8040bf}\Root\InventoryApplicationFile\ciscocollabhost.|cf54c41fbf7716ae |
| Operation: | write | Name: | ProgramId |
Value: 000671ea79c17b52c41bb9fde5c1ef5b039500000918 | |||
| (PID) Process: | (7828) WerFault.exe | Key: | \REGISTRY\A\{4218becc-6fdb-f1a5-4a0f-b1a40c8040bf}\Root\InventoryApplicationFile\ciscocollabhost.|cf54c41fbf7716ae |
| Operation: | write | Name: | FileId |
Value: 0000ec2afaf10b78dabfead9e9e485d454789c244188 | |||
| (PID) Process: | (7828) WerFault.exe | Key: | \REGISTRY\A\{4218becc-6fdb-f1a5-4a0f-b1a40c8040bf}\Root\InventoryApplicationFile\ciscocollabhost.|cf54c41fbf7716ae |
| Operation: | write | Name: | LowerCaseLongPath |
Value: c:\users\admin\appdata\roaming\ciscocollabhost.exe | |||
| (PID) Process: | (7828) WerFault.exe | Key: | \REGISTRY\A\{4218becc-6fdb-f1a5-4a0f-b1a40c8040bf}\Root\InventoryApplicationFile\ciscocollabhost.|cf54c41fbf7716ae |
| Operation: | write | Name: | LongPathHash |
Value: ciscocollabhost.|cf54c41fbf7716ae | |||
| (PID) Process: | (7828) WerFault.exe | Key: | \REGISTRY\A\{4218becc-6fdb-f1a5-4a0f-b1a40c8040bf}\Root\InventoryApplicationFile\ciscocollabhost.|cf54c41fbf7716ae |
| Operation: | write | Name: | Name |
Value: CiscoCollabHost.exe | |||
| (PID) Process: | (7828) WerFault.exe | Key: | \REGISTRY\A\{4218becc-6fdb-f1a5-4a0f-b1a40c8040bf}\Root\InventoryApplicationFile\ciscocollabhost.|cf54c41fbf7716ae |
| Operation: | write | Name: | OriginalFileName |
Value: ciscocollabhost.exe | |||
| (PID) Process: | (7828) WerFault.exe | Key: | \REGISTRY\A\{4218becc-6fdb-f1a5-4a0f-b1a40c8040bf}\Root\InventoryApplicationFile\ciscocollabhost.|cf54c41fbf7716ae |
| Operation: | write | Name: | Publisher |
Value: cisco systems, inc | |||
Executable files
10
Suspicious files
17
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1IOFSYEKGW1ILD4P4PBP.temp | binary | |
MD5:3272268A64538D26FA696F2D0F41C785 | SHA256:3D58D33681D7CBDDBBB6DAF0A3E3E314A4D1900DCB916E4E9420094C81C54A73 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ExtractedPayload_1025188070\VERSION.dll | executable | |
MD5:11463F061929FD27C95A765006E6B01F | SHA256:B9467B97B572E6384EDE1638AE7D20CFEB0A74792B8325CD780867BC2CA22C6D | |||
| 7828 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_CiscoCollabHost._d3e82bd29774afc2b2dcac6f4fff4347edf929c_128e8005_b42070a4-973b-43af-b8c0-83c46584b343\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ExtractedPayload_1025188070\CiscoCollabHost.exe | executable | |
MD5:9C521A90653DF5D1EFBD0CEA12318863 | SHA256:85BCFC9DE06BD0751245AD882F7E2141F340CDEDEFCAEFB8DEABBC0792088A58 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:7DF7474378A1329CCB38621449484423 | SHA256:0BD851AD66EFA3CC3B3E4A66C7F8BAB7FC323C4907D81A6146CE130BBA566D12 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_n0321x04.2fj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 728 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\8ed0d081-89cb-4c8f-b185-7f4bfe7dd0ba.down_data | — | |
MD5:— | SHA256:— | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\payload.zip | compressed | |
MD5:C87152A4C77FD0B11490393FFA07BB4C | SHA256:0F8DD92EA4A73846D62FAE3E36C5B24C5D162B2DFE8B0A81781971771FE78B42 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ExtractedPayload_1025188070\CiscoSparkLauncher.dll | executable | |
MD5:E2E01305E938EA378A88658D81C0917F | SHA256:29C3C48F4DC84E7179881BC3767546878B2DB89D418372F687EDBD4A72EF0989 | |||
| 7296 | CiscoCollabHost.exe | C:\Users\admin\AppData\Roaming\CiscoCollabHost.exe | executable | |
MD5:9C521A90653DF5D1EFBD0CEA12318863 | SHA256:85BCFC9DE06BD0751245AD882F7E2141F340CDEDEFCAEFB8DEABBC0792088A58 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
35
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
728 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3284 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4756 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3284 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2108 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2108 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |