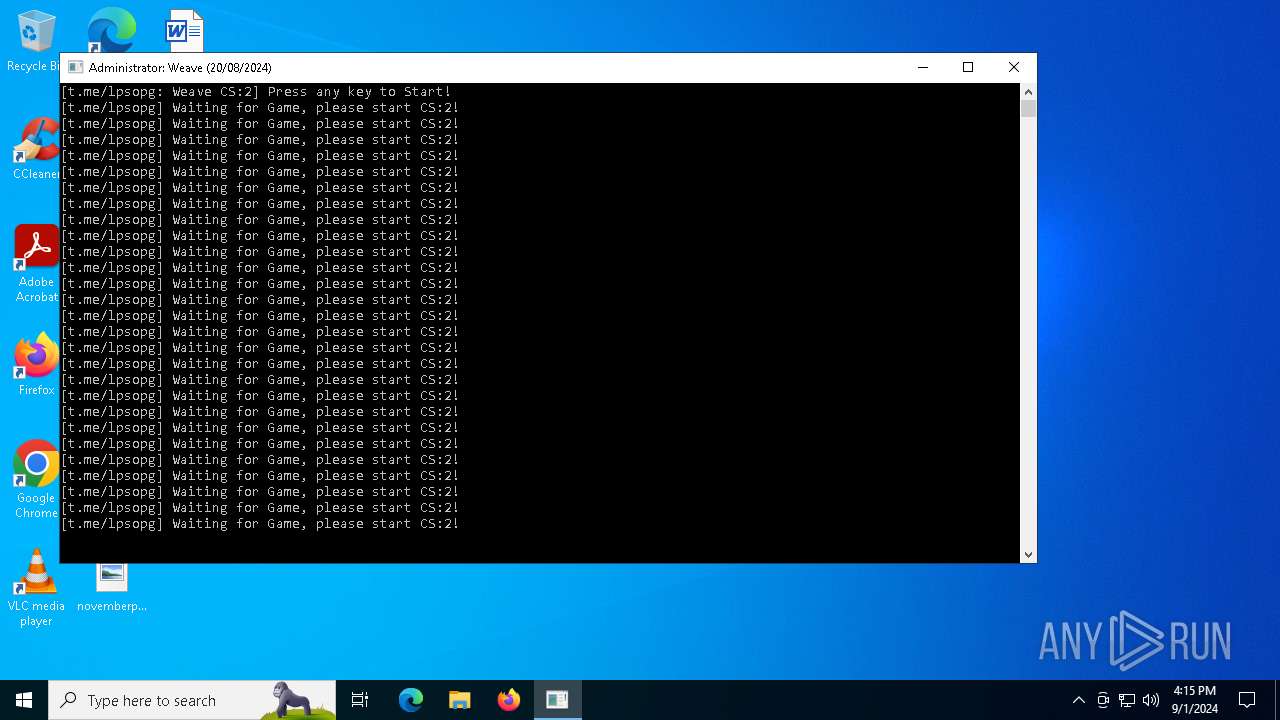
| File name: | weave.exe |
| Full analysis: | https://app.any.run/tasks/6541f4ec-c2bd-4b5a-9dec-2a8daed832c0 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | September 01, 2024, 16:14:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8232AA26C35A5C0E65E5DE1C26DDA123 |
| SHA1: | 3D6B0E100F43DC1A4B8CE4C78CBB03169F5001B1 |
| SHA256: | 5ABFD9A755941262E7C68D0D64A15260810CD9EC73244287C957C316C587A3E1 |
| SSDEEP: | 98304:BPedsAz0NT731lOm/zp0kARodROr8DO6AjVDTkr3jii9c6rTbl5rIx8kbDUAzHsp:EPvk2HkgAKgAnIfYaxCvcmMvA |
MALICIOUS
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 5556)
- explorer.exe (PID: 4552)
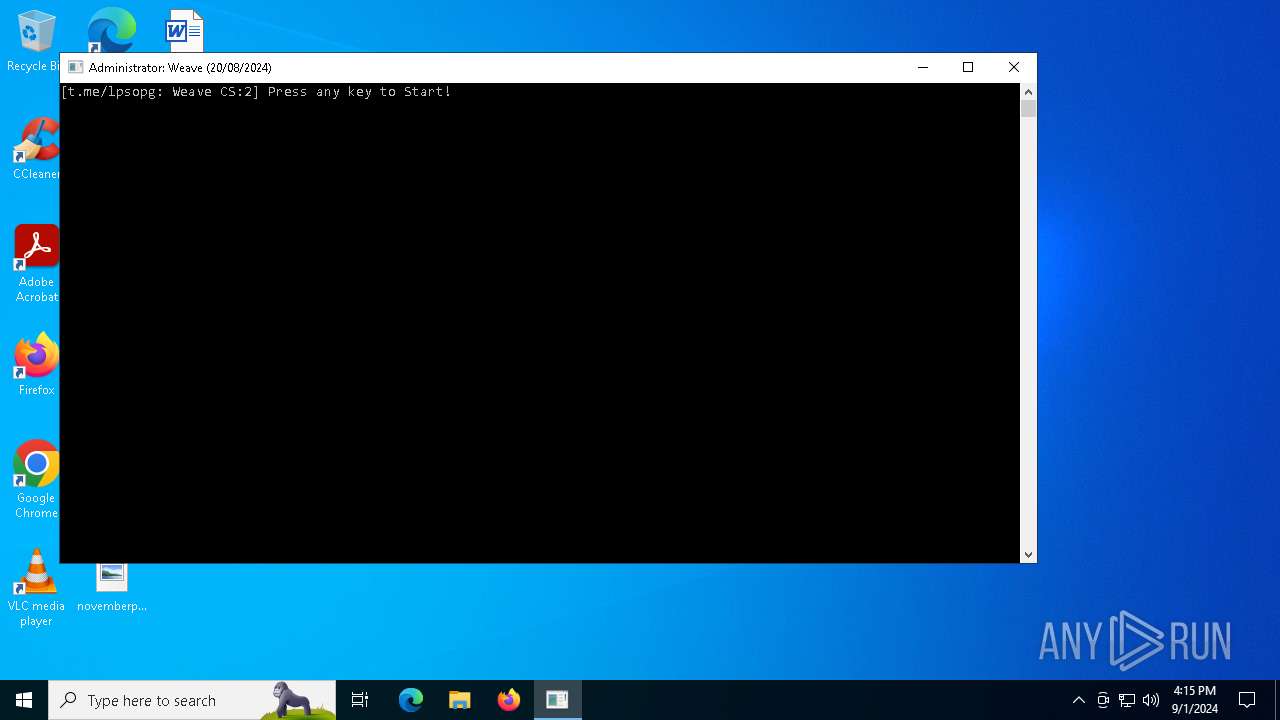
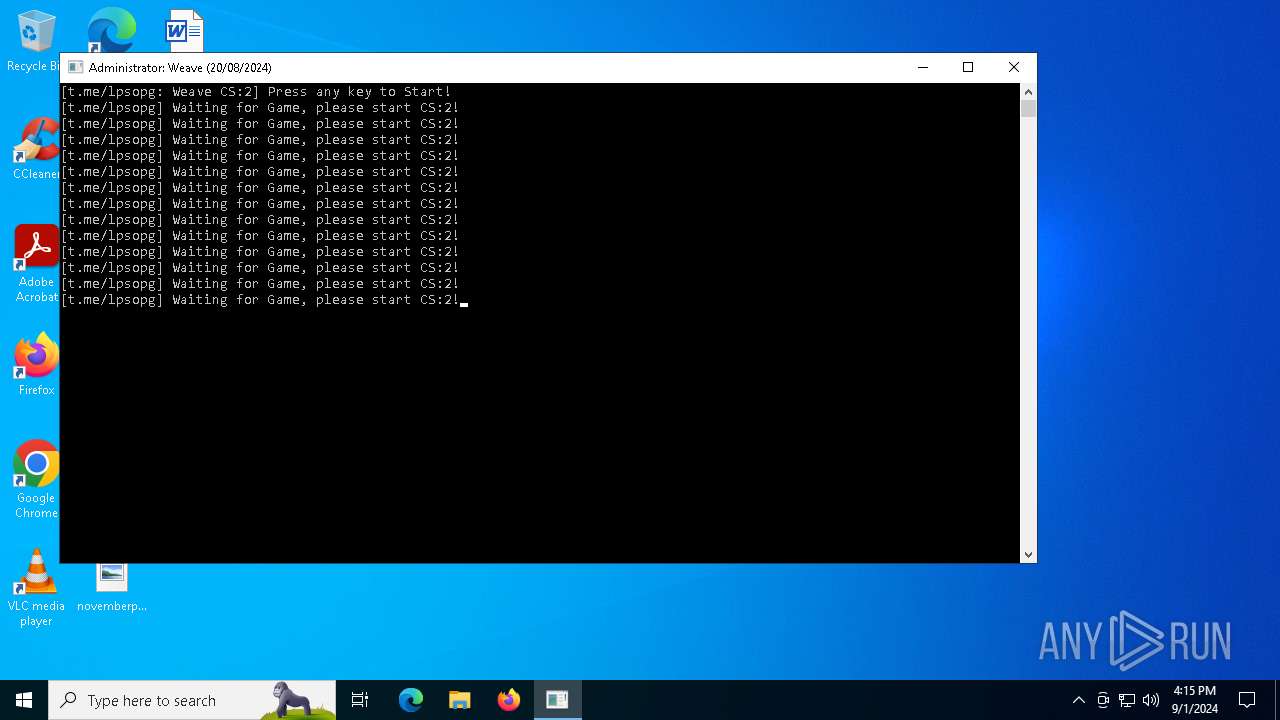
- cli_gui.exe (PID: 4444)
Application was injected by another process
- svchost.exe (PID: 476)
- winlogon.exe (PID: 684)
- lsass.exe (PID: 768)
- dwm.exe (PID: 852)
- svchost.exe (PID: 1316)
- svchost.exe (PID: 1200)
- svchost.exe (PID: 1036)
- svchost.exe (PID: 1364)
- svchost.exe (PID: 1208)
- svchost.exe (PID: 1272)
- svchost.exe (PID: 1620)
- svchost.exe (PID: 1408)
- svchost.exe (PID: 1864)
- svchost.exe (PID: 1588)
- svchost.exe (PID: 1472)
- svchost.exe (PID: 1600)
- svchost.exe (PID: 1628)
- svchost.exe (PID: 1508)
- svchost.exe (PID: 1796)
- svchost.exe (PID: 2072)
- svchost.exe (PID: 1872)
- svchost.exe (PID: 2160)
- svchost.exe (PID: 2304)
- svchost.exe (PID: 2000)
- svchost.exe (PID: 2692)
- svchost.exe (PID: 2312)
- svchost.exe (PID: 2256)
- svchost.exe (PID: 2184)
- svchost.exe (PID: 1816)
- OfficeClickToRun.exe (PID: 2656)
- svchost.exe (PID: 2344)
- svchost.exe (PID: 3012)
- svchost.exe (PID: 2996)
- svchost.exe (PID: 3020)
- svchost.exe (PID: 2968)
- svchost.exe (PID: 2788)
- svchost.exe (PID: 3260)
- svchost.exe (PID: 3056)
- svchost.exe (PID: 3220)
- svchost.exe (PID: 2496)
- spoolsv.exe (PID: 2592)
- svchost.exe (PID: 2412)
- svchost.exe (PID: 3084)
- svchost.exe (PID: 3496)
- svchost.exe (PID: 3200)
- dasHost.exe (PID: 3692)
- svchost.exe (PID: 3408)
- svchost.exe (PID: 3888)
- svchost.exe (PID: 4184)
- svchost.exe (PID: 3548)
- svchost.exe (PID: 4140)
- svchost.exe (PID: 4332)
- svchost.exe (PID: 3340)
- sihost.exe (PID: 4112)
- RuntimeBroker.exe (PID: 4244)
- svchost.exe (PID: 4532)
- svchost.exe (PID: 4808)
- explorer.exe (PID: 4552)
- ctfmon.exe (PID: 4356)
- svchost.exe (PID: 4300)
- dllhost.exe (PID: 5568)
- dllhost.exe (PID: 4424)
- svchost.exe (PID: 5036)
- RuntimeBroker.exe (PID: 776)
- RuntimeBroker.exe (PID: 5560)
- MoUsoCoreWorker.exe (PID: 2120)
- svchost.exe (PID: 4324)
- svchost.exe (PID: 5416)
- dllhost.exe (PID: 3312)
- svchost.exe (PID: 4000)
- uhssvc.exe (PID: 536)
- ApplicationFrameHost.exe (PID: 4052)
- svchost.exe (PID: 1824)
- UserOOBEBroker.exe (PID: 2744)
- svchost.exe (PID: 5236)
- svchost.exe (PID: 6976)
- svchost.exe (PID: 5256)
- svchost.exe (PID: 6812)
- UsoClient.exe (PID: 872)
- RUXIMICS.exe (PID: 6440)
- PLUGScheduler.exe (PID: 6312)
- conhost.exe (PID: 6884)
- taskhostw.exe (PID: 6420)
- WaaSMedicAgent.exe (PID: 5048)
- svchost.exe (PID: 5548)
- RUXIMICS.exe (PID: 7292)
- svchost.exe (PID: 252)
- svchost.exe (PID: 5852)
- MusNotification.exe (PID: 1608)
- svchost.exe (PID: 1492)
Runs injected code in another process
- dialer.exe (PID: 5172)
- dialer.exe (PID: 8172)
XORed URL has been found (YARA)
- dialer.exe (PID: 7288)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2256)
SUSPICIOUS
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 5556)
- explorer.exe (PID: 4552)
Reads security settings of Internet Explorer
- weave.exe (PID: 3784)
Reads the date of Windows installation
- weave.exe (PID: 3784)
Executable content was dropped or overwritten
- weave.exe (PID: 3784)
- updater.exe (PID: 5712)
- updater.exe (PID: 7556)
Drops the executable file immediately after the start
- weave.exe (PID: 3784)
- updater.exe (PID: 5712)
- updater.exe (PID: 7556)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 4552)
- cli_gui.exe (PID: 4444)
Starts POWERSHELL.EXE for commands execution
- explorer.exe (PID: 4552)
- cmd.exe (PID: 5556)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 6608)
- cmd.exe (PID: 8132)
Starts SC.EXE for service management
- cmd.exe (PID: 6660)
- cmd.exe (PID: 7916)
Reads the BIOS version
- cli_gui.exe (PID: 4444)
Hides command output
- cmd.exe (PID: 5556)
The process executes via Task Scheduler
- updater.exe (PID: 7556)
Creates or modifies Windows services
- WaaSMedicAgent.exe (PID: 5048)
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 7556)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2256)
INFO
Reads the computer name
- weave.exe (PID: 3784)
- PLUGScheduler.exe (PID: 6312)
Checks supported languages
- weave.exe (PID: 3784)
- cli_gui.exe (PID: 4444)
- updater.exe (PID: 5712)
- RUXIMICS.exe (PID: 7292)
- RUXIMICS.exe (PID: 6440)
- PLUGScheduler.exe (PID: 6312)
- updater.exe (PID: 7556)
The process uses the downloaded file
- weave.exe (PID: 3784)
- powershell.exe (PID: 7712)
- powershell.exe (PID: 8180)
Create files in a temporary directory
- weave.exe (PID: 3784)
- updater.exe (PID: 5712)
Process checks computer location settings
- weave.exe (PID: 3784)
Process checks whether UAC notifications are on
- cli_gui.exe (PID: 4444)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1224)
- powershell.exe (PID: 4020)
- powershell.exe (PID: 6188)
- powershell.exe (PID: 7712)
- powershell.exe (PID: 8180)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1224)
- powershell.exe (PID: 4020)
- powershell.exe (PID: 7712)
Reads the software policy settings
- WaaSMedicAgent.exe (PID: 5048)
- lsass.exe (PID: 768)
Themida protector has been detected
- cli_gui.exe (PID: 4444)
Manual execution by a user
- powershell.exe (PID: 4020)
- cmd.exe (PID: 6660)
- cmd.exe (PID: 6608)
- dialer.exe (PID: 5172)
- powershell.exe (PID: 6188)
- schtasks.exe (PID: 7484)
- powershell.exe (PID: 7712)
- powershell.exe (PID: 8180)
- cmd.exe (PID: 8132)
- dialer.exe (PID: 8172)
- cmd.exe (PID: 7916)
- dialer.exe (PID: 5188)
- dialer.exe (PID: 7288)
Creates files or folders in the user directory
- dllhost.exe (PID: 5568)
Creates files in the program directory
- RUXIMICS.exe (PID: 7292)
- MoUsoCoreWorker.exe (PID: 2120)
- updater.exe (PID: 5712)
- updater.exe (PID: 7556)
Reads security settings of Internet Explorer
- RuntimeBroker.exe (PID: 5560)
Reads Microsoft Office registry keys
- RuntimeBroker.exe (PID: 5560)
- OfficeClickToRun.exe (PID: 2656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:08:19 22:40:19+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5.16 |
| CodeSize: | 15040000 |
| InitializedDataSize: | 1536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5789a0 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
173
Monitored processes
139
Malicious processes
92
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\WINDOWS\System32\svchost.exe -k LocalServiceNetworkRestricted -p -s lmhosts | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 476 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p -s LSM | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cli_gui.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files\Microsoft Update Health Tools\uhssvc.exe" | C:\Program Files\Microsoft Update Health Tools\uhssvc.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Update Health Service Version: 10.0.19041.3626 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | winlogon.exe | C:\Windows\System32\winlogon.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Logon Application Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | C:\WINDOWS\system32\lsass.exe | C:\Windows\System32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 852 | "dwm.exe" | C:\Windows\System32\dwm.exe | winlogon.exe | ||||||||||||
User: DWM-1 Company: Microsoft Corporation Integrity Level: SYSTEM Description: Desktop Window Manager Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\WINDOWS\system32\usoclient.exe" StartScan | C:\Windows\System32\UsoClient.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: UsoClient Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
63 667
Read events
63 315
Write events
279
Delete events
73
Modification events
| (PID) Process: | (3784) weave.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3784) weave.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3784) weave.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3784) weave.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000503A8 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456033BCEE44DE41B4E8AEC331E84F566D2 | |||
| (PID) Process: | (5236) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Compatibility Assistant\Store |
| Operation: | write | Name: | C:\Users\admin\AppData\Local\Temp\weave.exe |
Value: 534143500100000000000000070000002800000000A2F6008F1DE60001000000000000000000000A5122000050BB64EDDDACD5010000000000000000 | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{614b38e3-6af0-5197-dbd0-cfaa110a112e}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{614b38e3-6af0-5197-dbd0-cfaa110a112e}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{614b38e3-6af0-5197-dbd0-cfaa110a112e}\Root\InventoryApplicationFile\weave.exe|470c3109255a9475 |
| Operation: | write | Name: | ProgramId |
Value: 00061f72c607726eb17521b57088123de82e0000ffff | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{614b38e3-6af0-5197-dbd0-cfaa110a112e}\Root\InventoryApplicationFile\weave.exe|470c3109255a9475 |
| Operation: | write | Name: | FileId |
Value: 00003d6b0e100f43dc1a4b8ce4c78cbb03169f5001b1 | |||
Executable files
8
Suspicious files
52
Text files
22
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1620 | svchost.exe | C:\Windows\Prefetch\HOST.EXE-F5D74C61.pf | binary | |
MD5:0509B99EAC50657C87FE8E7A7ADEF8E3 | SHA256:94533FC7024C0E8FB48F2F1F839264A364EA9F1978A27430BDA7F5B9A4421361 | |||
| 3784 | weave.exe | C:\Users\admin\AppData\Local\Temp\cli_gui.exe | executable | |
MD5:A11C89310149164B7CC9782FB631459B | SHA256:014D7046F92D512642247DF3D442144716451F2E638B60C4685ABA9E0552E154 | |||
| 1620 | svchost.exe | C:\Windows\Prefetch\SVCHOST.EXE-AD0331FB.pf | binary | |
MD5:082816E8F791EF338AB863AC89FD2C8A | SHA256:EE911D9CFE744D9FFE6BF72F5D681178F2D65DD63FB03703522A78346CC5CE93 | |||
| 1224 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zmf2cge4.r1t.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1620 | svchost.exe | C:\Windows\Prefetch\WEAVE.EXE-DAF23D7E.pf | binary | |
MD5:5C28116C521AC50333E18771664F6C4F | SHA256:CF5D6E4FEA68B384AC71FD8DE3575C0D71A78CC2F2FE26C79771E50A9C186C49 | |||
| 3784 | weave.exe | C:\Windows\System32\syscfg.cfg | binary | |
MD5:271EEBC1AB3E0ADD97DCE396FFF66FF2 | SHA256:FA004DB23CC0A76D0E5D846D551339E78542B02BE784DD63262FABC5A08E89D8 | |||
| 4020 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sch2llj5.sw3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1620 | svchost.exe | C:\Windows\Prefetch\POWERSHELL.EXE-920BBA2A.pf | binary | |
MD5:8BA9906E6676A8C008B974EB2AC57C8A | SHA256:1FB702F0DF5791ACA48C7317B66076CBA04698F7D9B82F30657A1372F35FE977 | |||
| 1224 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_maxhvszq.0kf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1620 | svchost.exe | C:\Windows\Prefetch\UPFC.EXE-BDDF79D6.pf | binary | |
MD5:D20D112F20697E520BA9C16EB19032FF | SHA256:32C57032B479DB705BB81A458600EDD734B85874A0DE82564FB352D0EB2F2D7E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
45
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1492 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7620 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7620 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6856 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6440 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6856 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 23.53.43.160:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5336 | SearchApp.exe | 23.37.226.88:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5336 | SearchApp.exe | 23.53.43.178:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5336 | SearchApp.exe | 20.189.173.13:443 | browser.pipe.aria.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |