| File name: | Windows 12.lnk.download |
| Full analysis: | https://app.any.run/tasks/7973c659-3a1d-46a5-a673-8dae853fd49d |
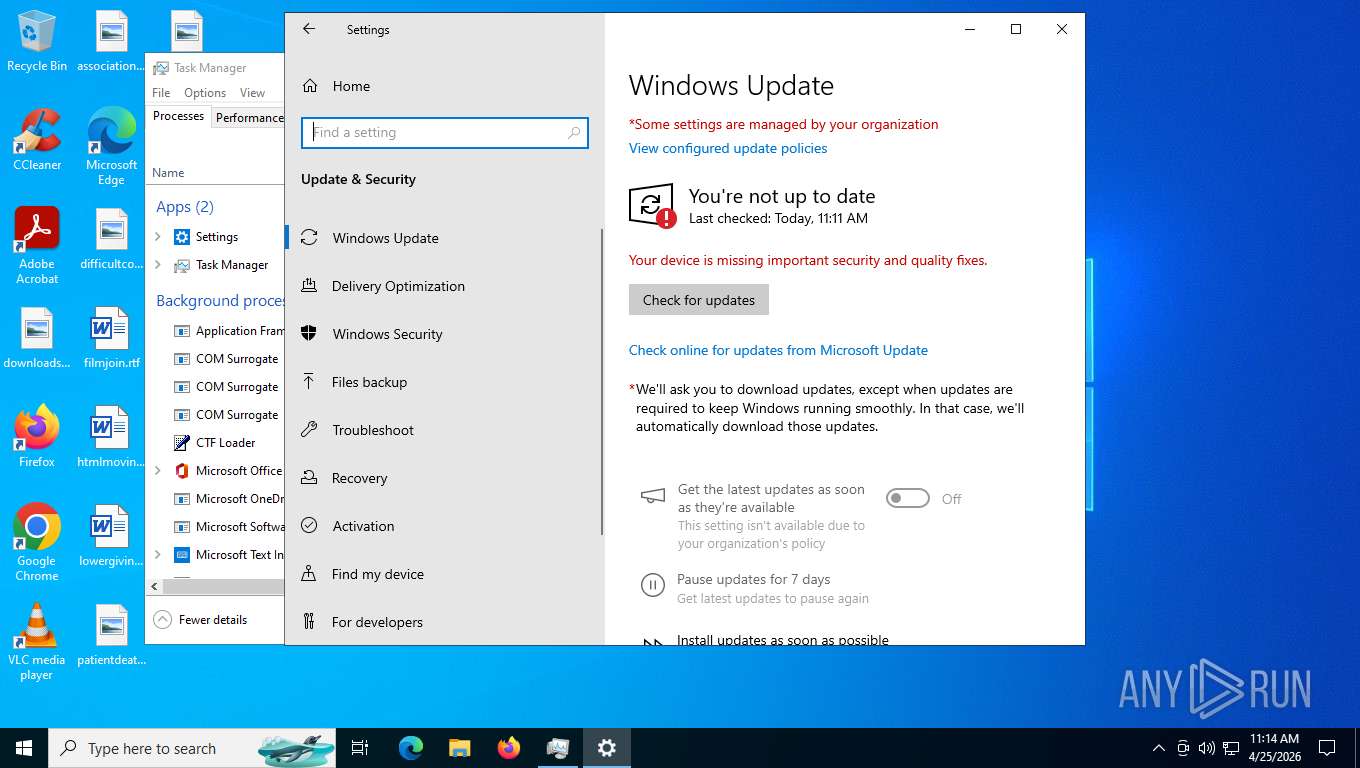
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | April 25, 2026, 15:11:11 |
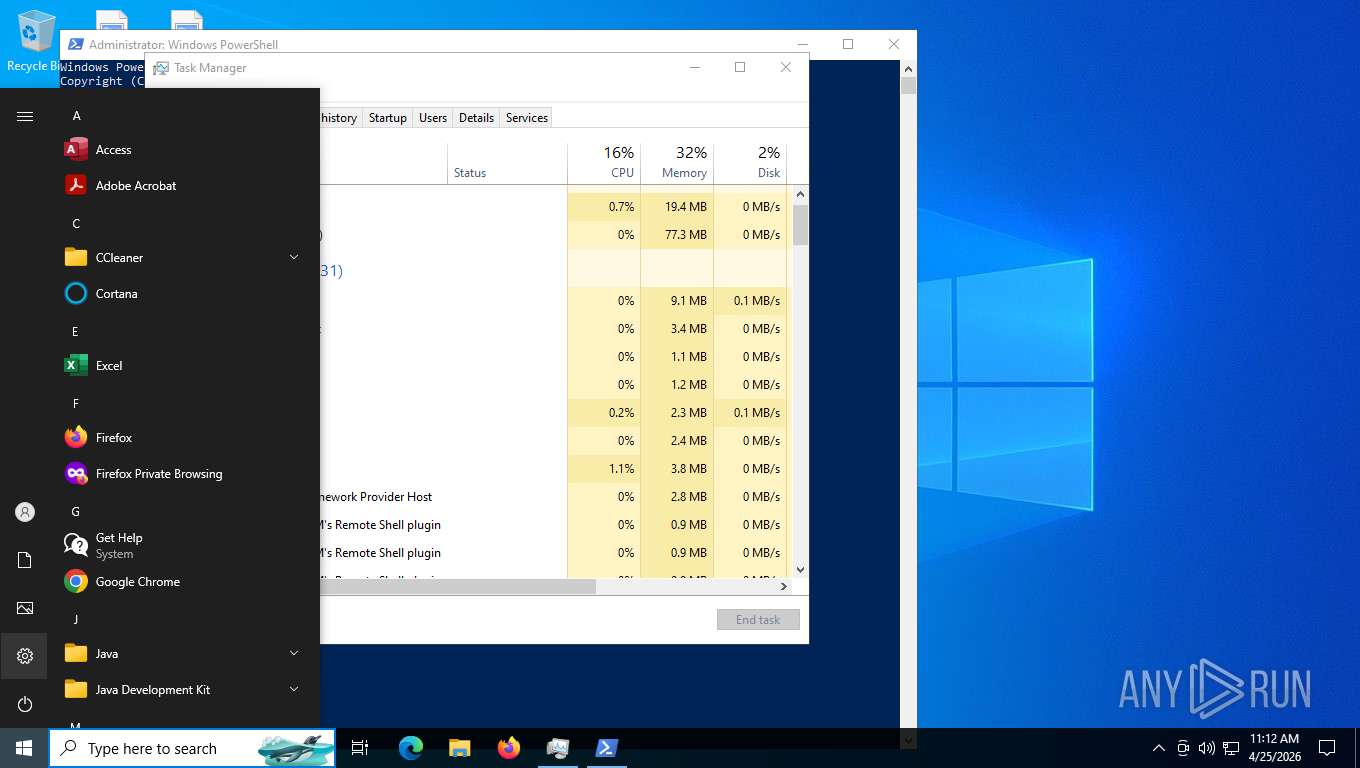
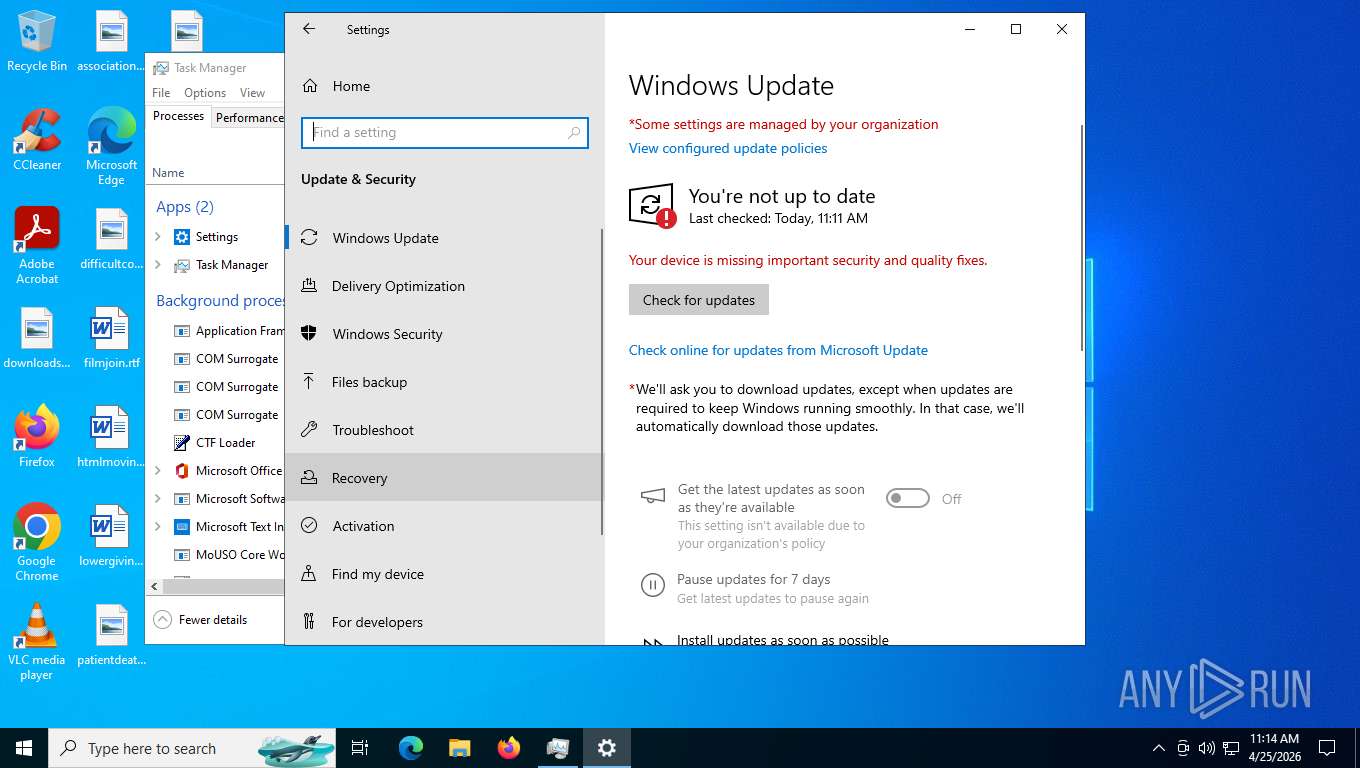
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-ms-shortcut |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has Relative path, Has Working directory, Has command line arguments, Icon number=0, Unicoded, HasExpIcon "%USERPROFILE%\AppData\Local\Microsoft\Edge\User Data\Default\Web Applications\_crx__heapafghjcojljadpkdnfjkifkmfjjdl\Windows 12", Archive, ctime=Fri Mar 6 05:07:43 2026, atime=Mon Apr 20 03:36:26 2026, mtime=Thu Apr 16 03:52:10 2026, length=2366032, window=normal, IDListSize 0x023f, Root folder "20D04FE0-3AEA-1069-A2D8-08002B30309D", Volume "C:\", LocalBasePath "C:\Program Files (x86)\Microsoft\Edge\Application\msedge_proxy.exe" |
| MD5: | CA2DC6E0914FE5822F45577CAF3E261D |
| SHA1: | 3339B3D4B5A82560EE4CF63F37EC6A30A1038ED5 |
| SHA256: | 5AA366AD6AA0882306C830815DBB9F2F6291158AF00BC57D93AF2EF9C051560A |
| SSDEEP: | 48:8QpdODQf86UBU4JfzLlqdqdMl8ubtQlnvid5dKBZDb1RPqid5ddHSafbtQRn:8CxUqyLhElLbqlUa3jGkbKR |
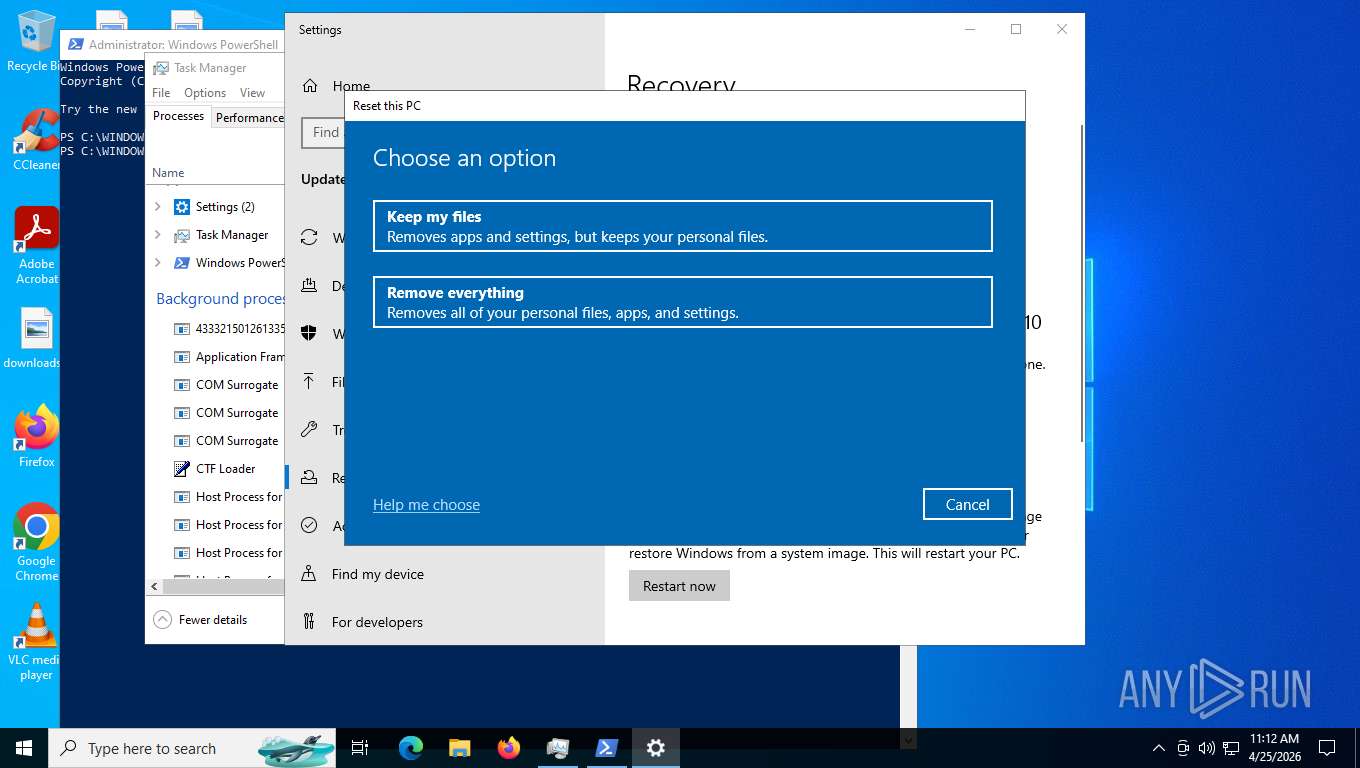
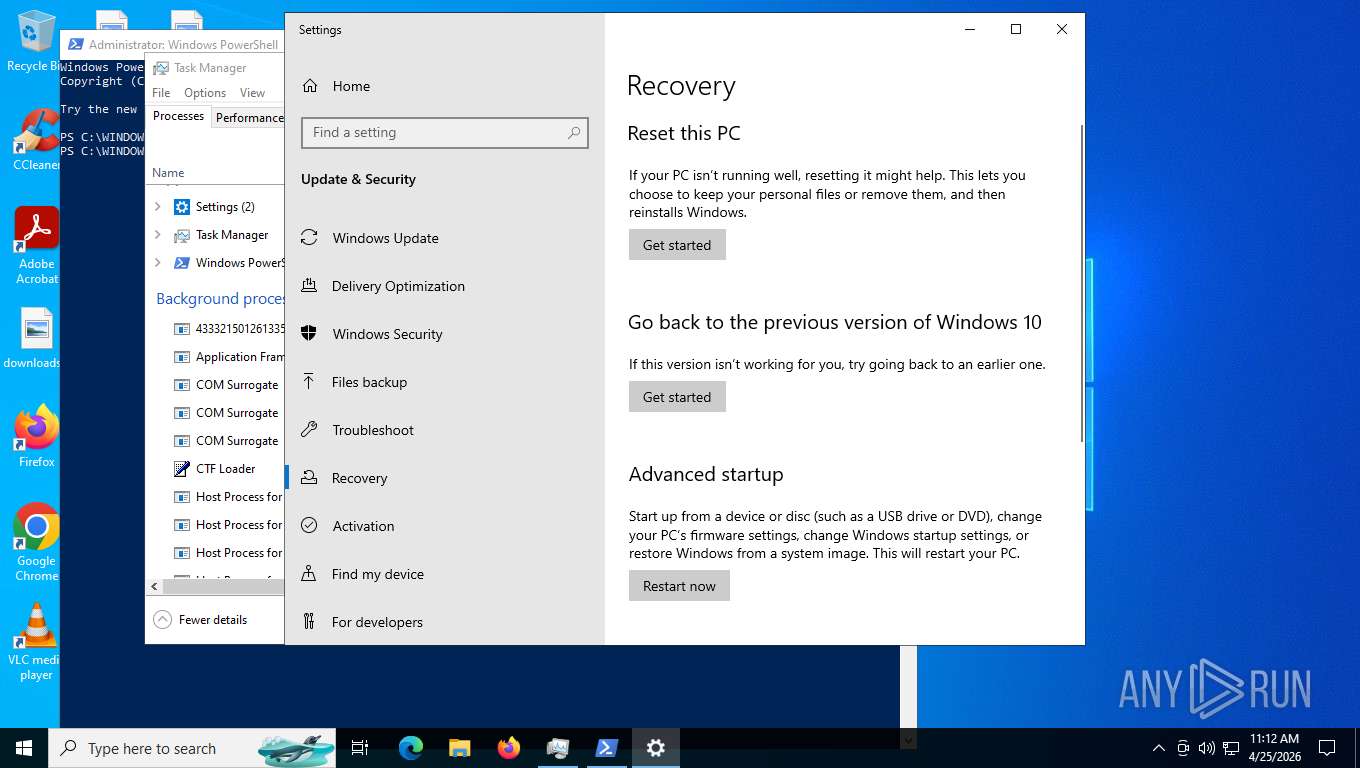
MALICIOUS
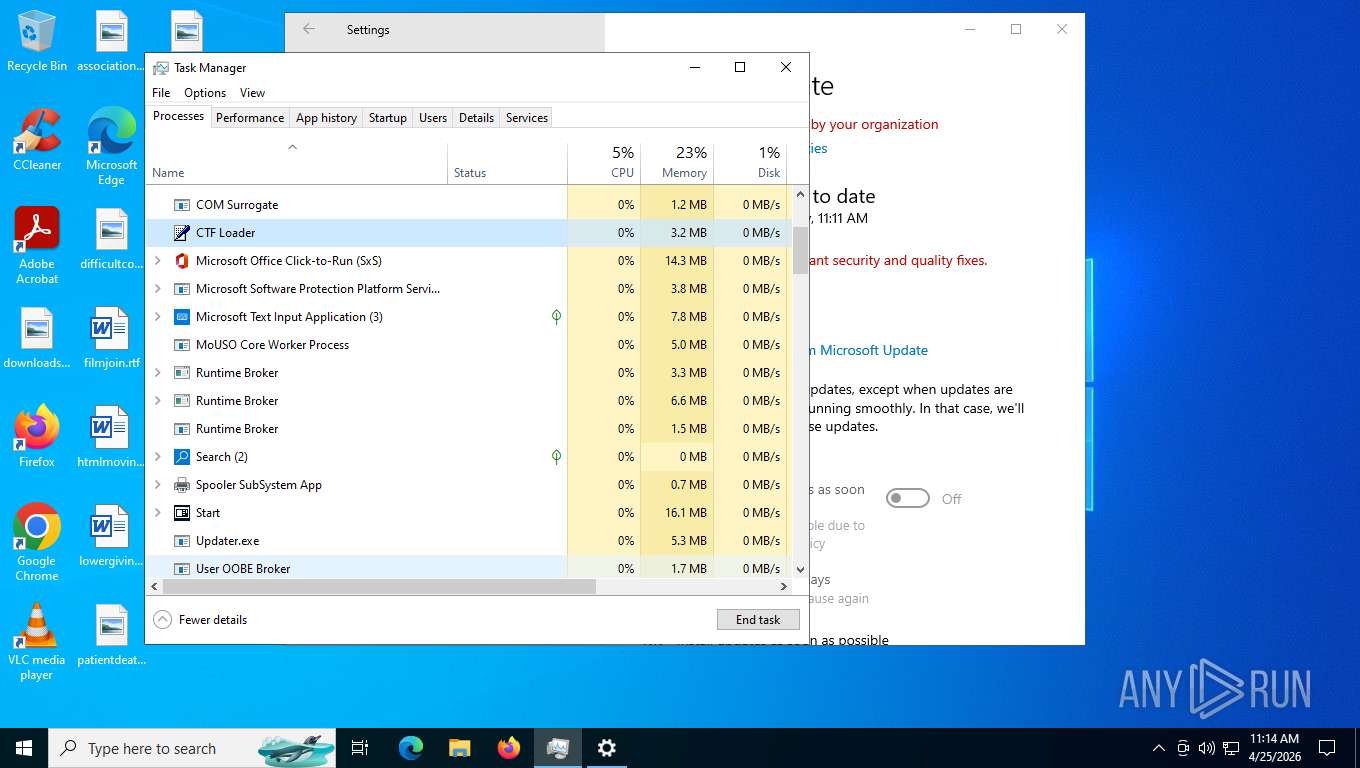
ANDROMEDA mutex has been found
- rename.exe (PID: 2880)
- rename.exe (PID: 3552)
Reads a specific registry key of the VM
- rename.exe (PID: 2880)
- rename.exe (PID: 3552)
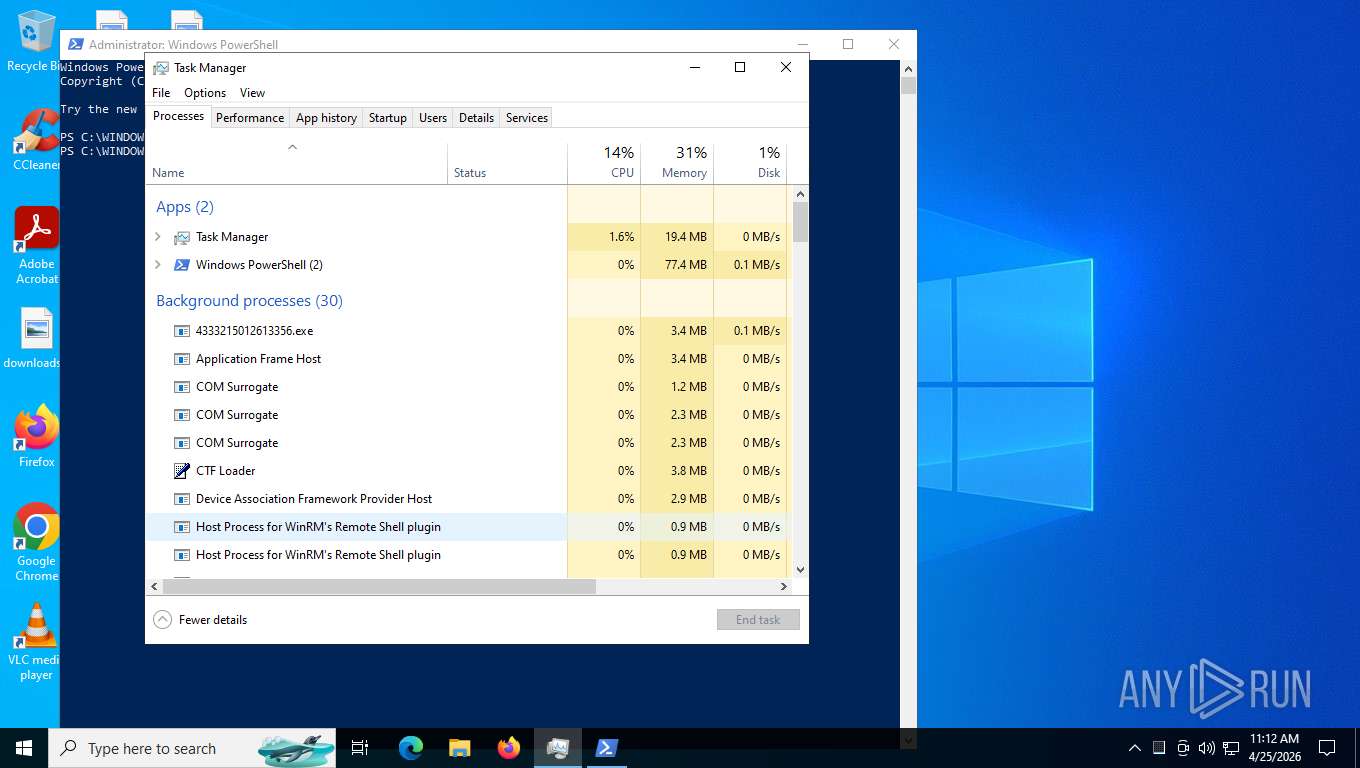
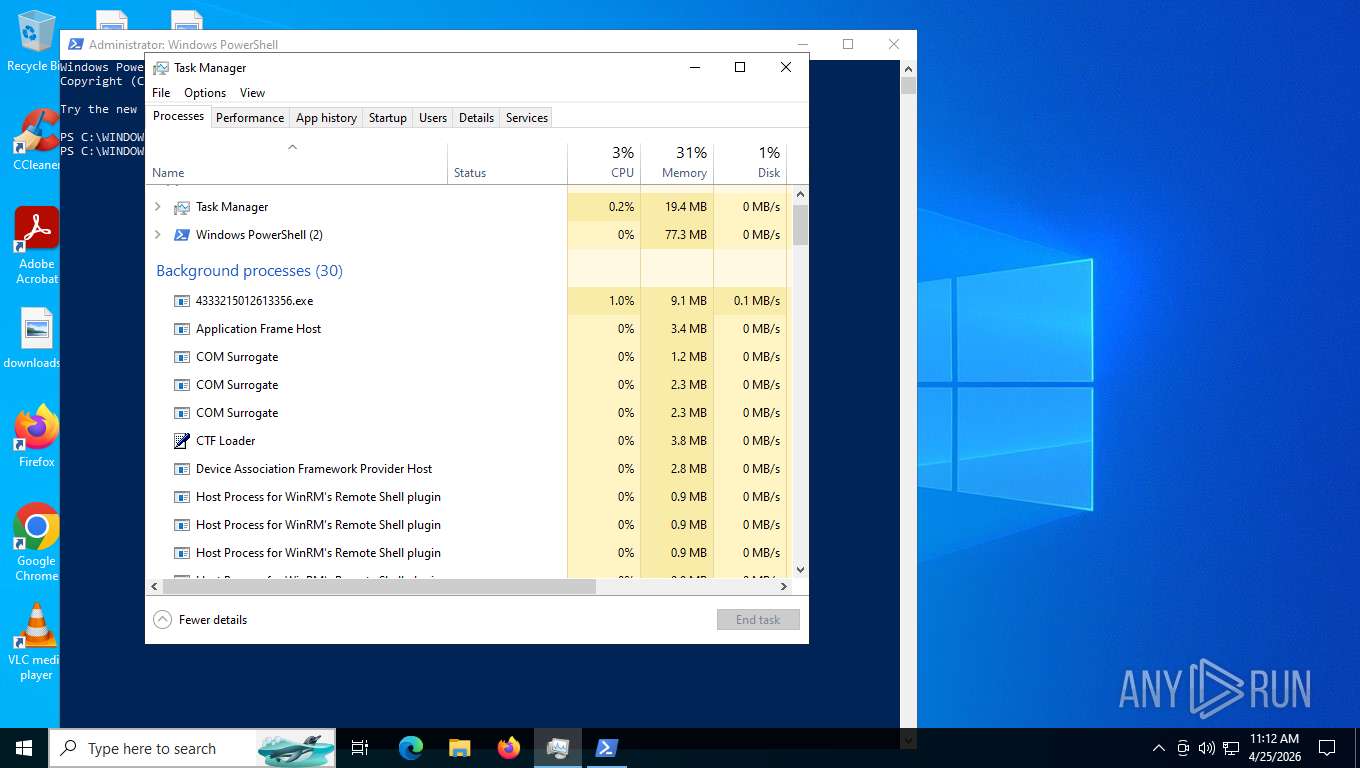
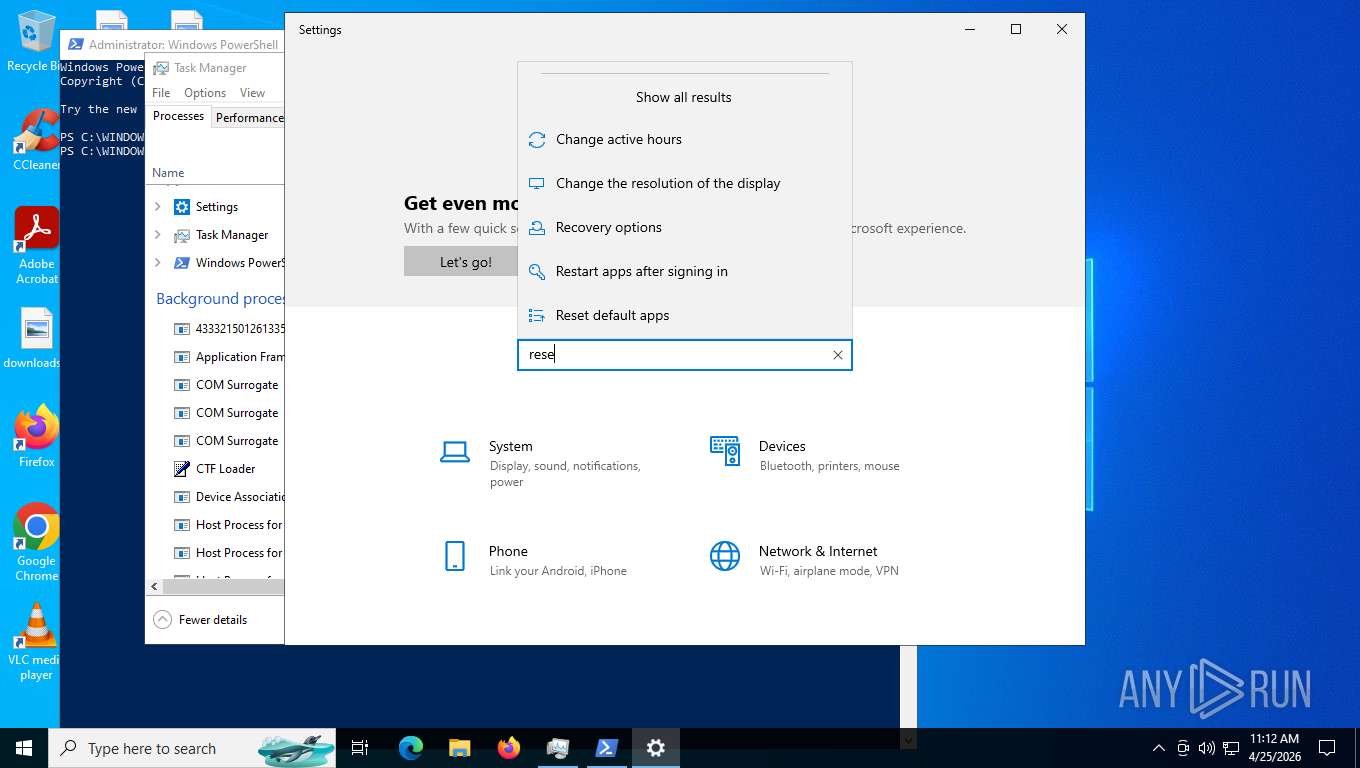
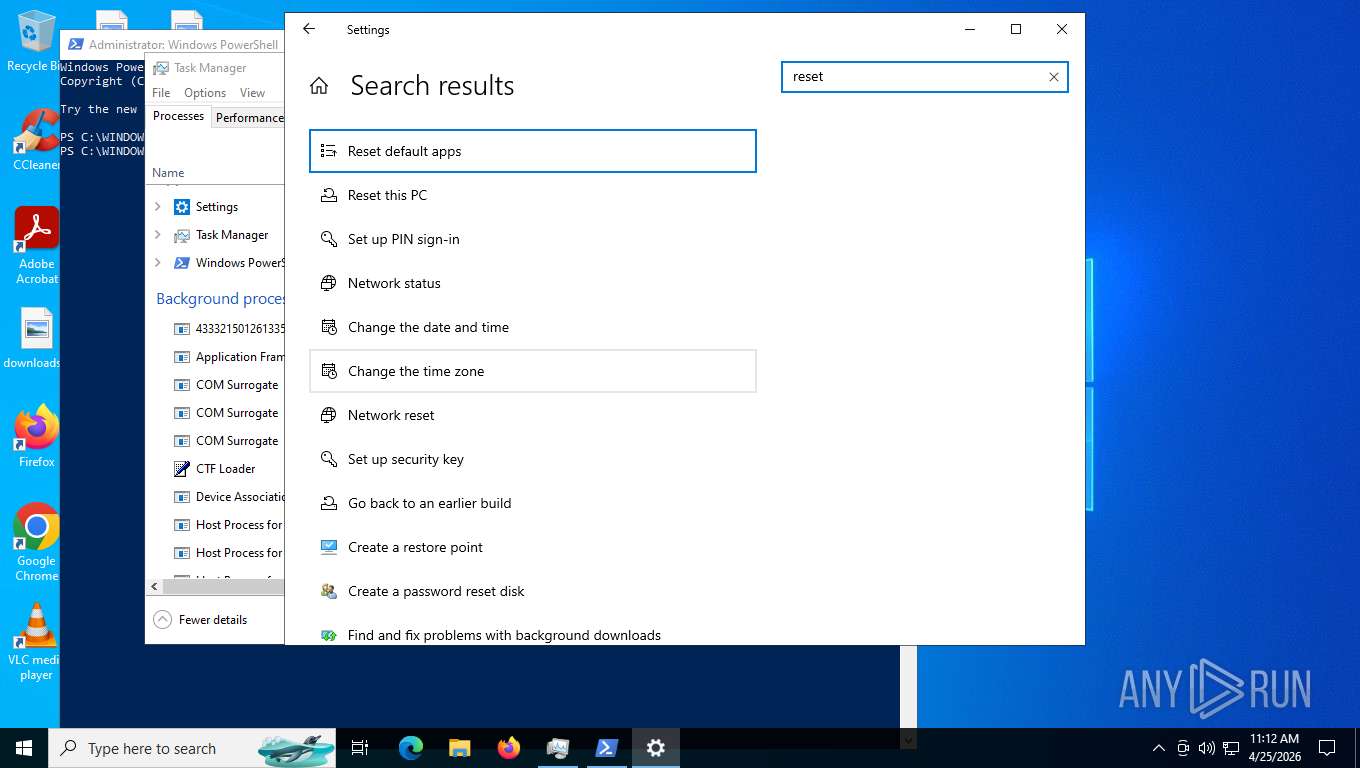
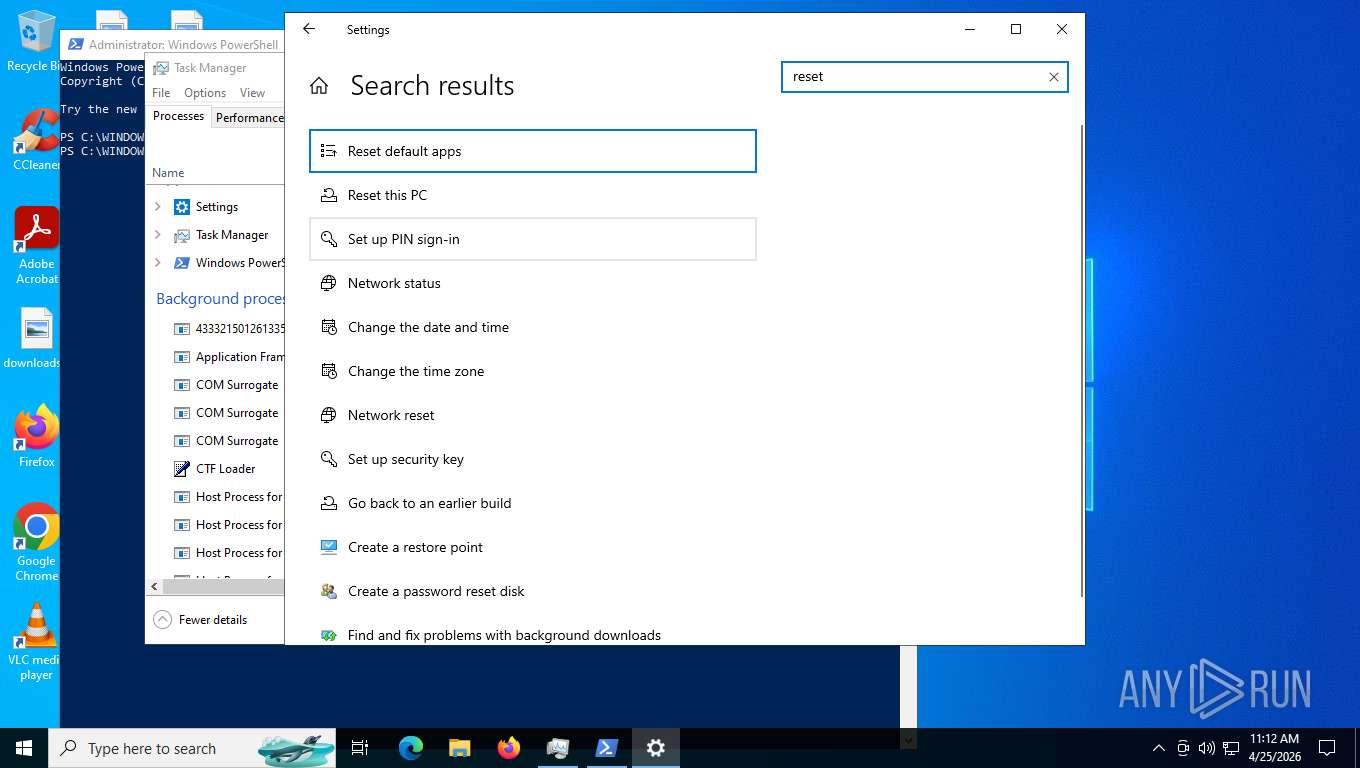
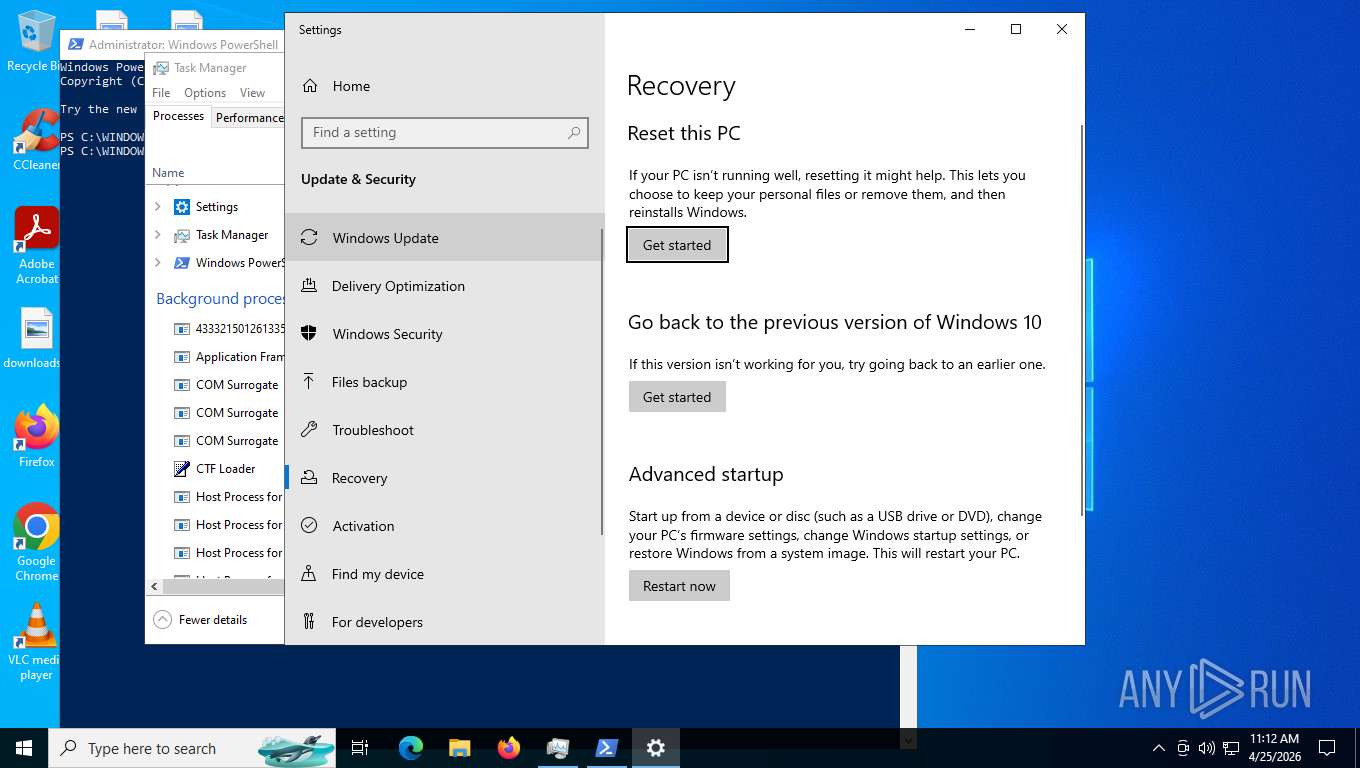
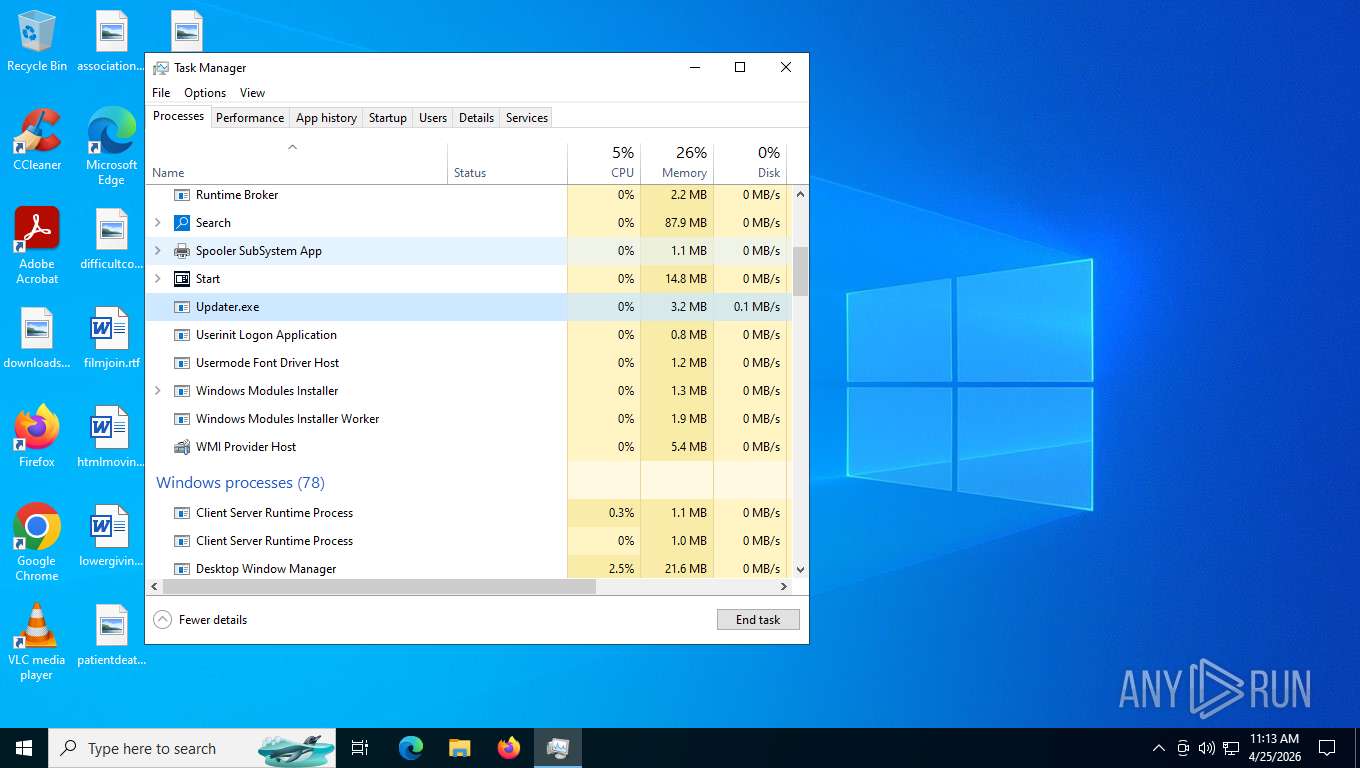
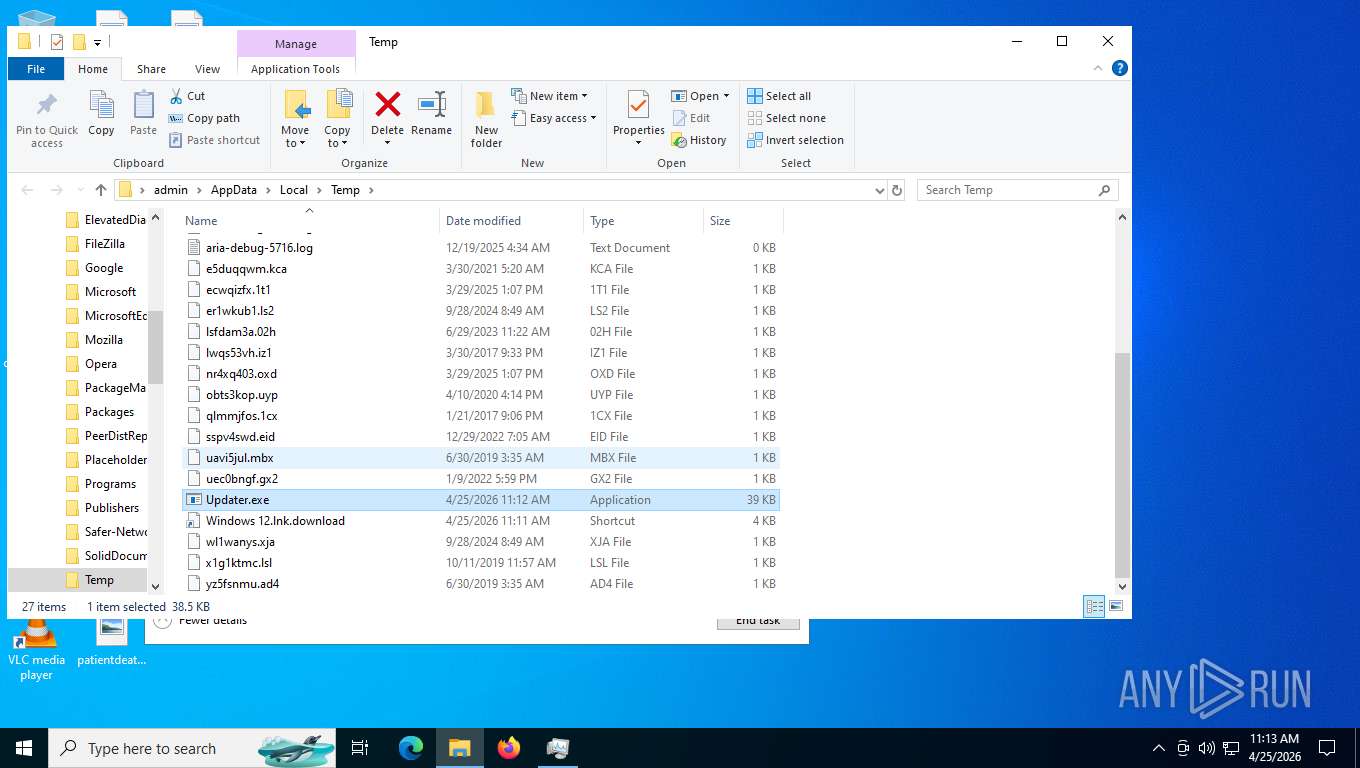
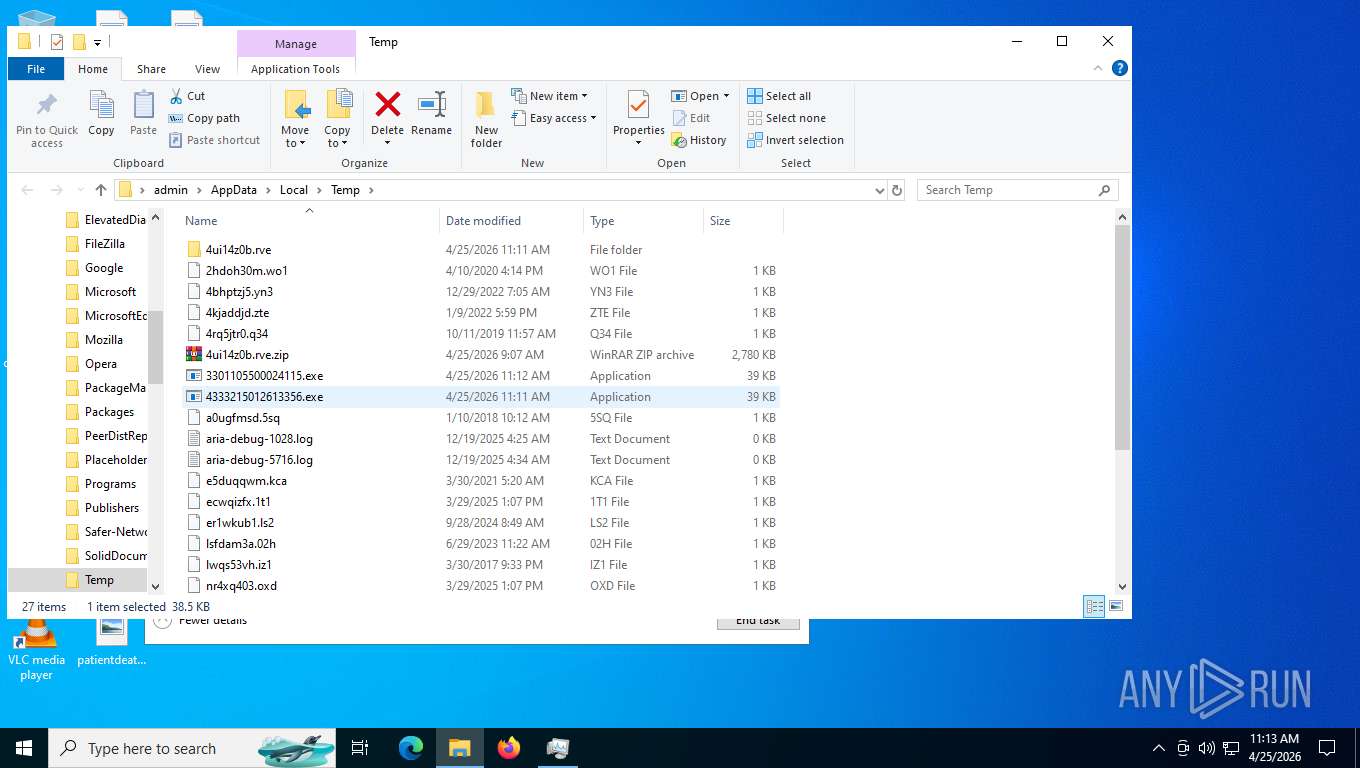
Changes the autorun value in the registry
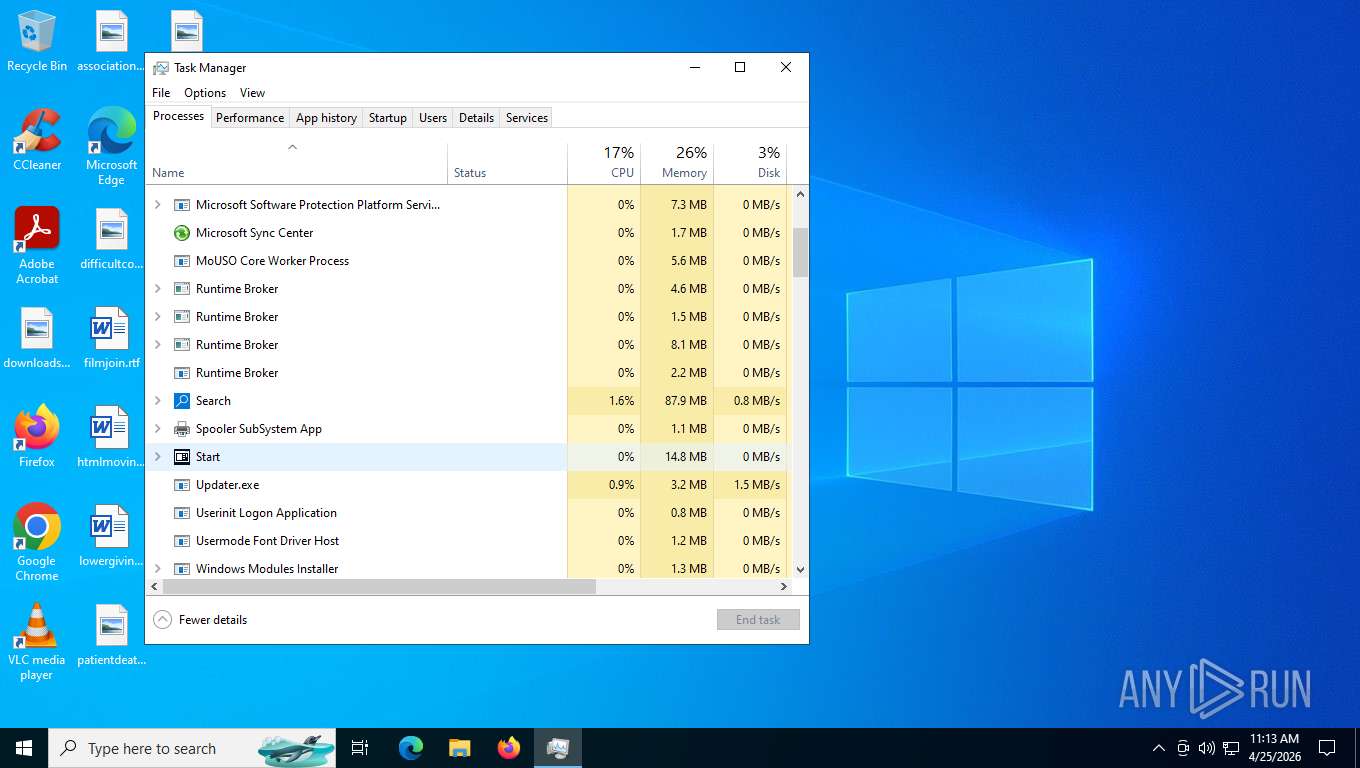
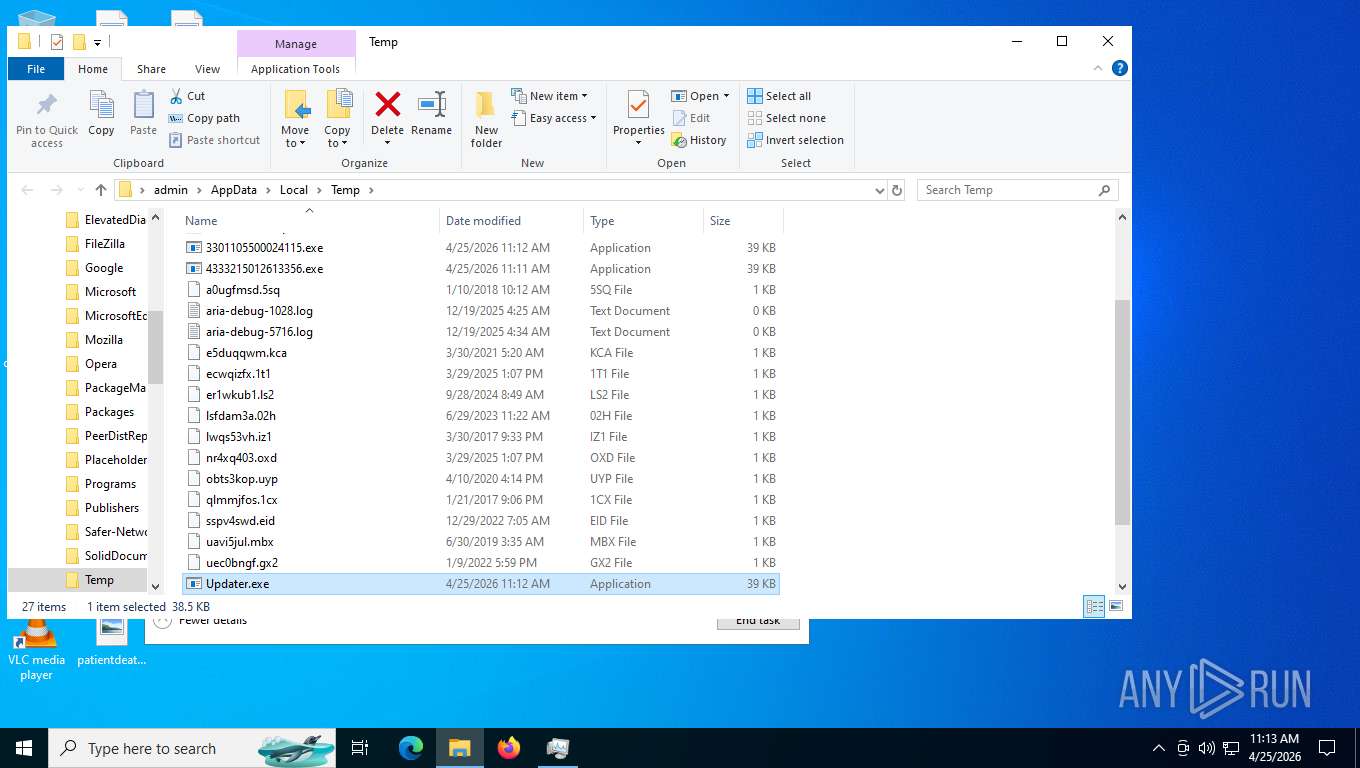
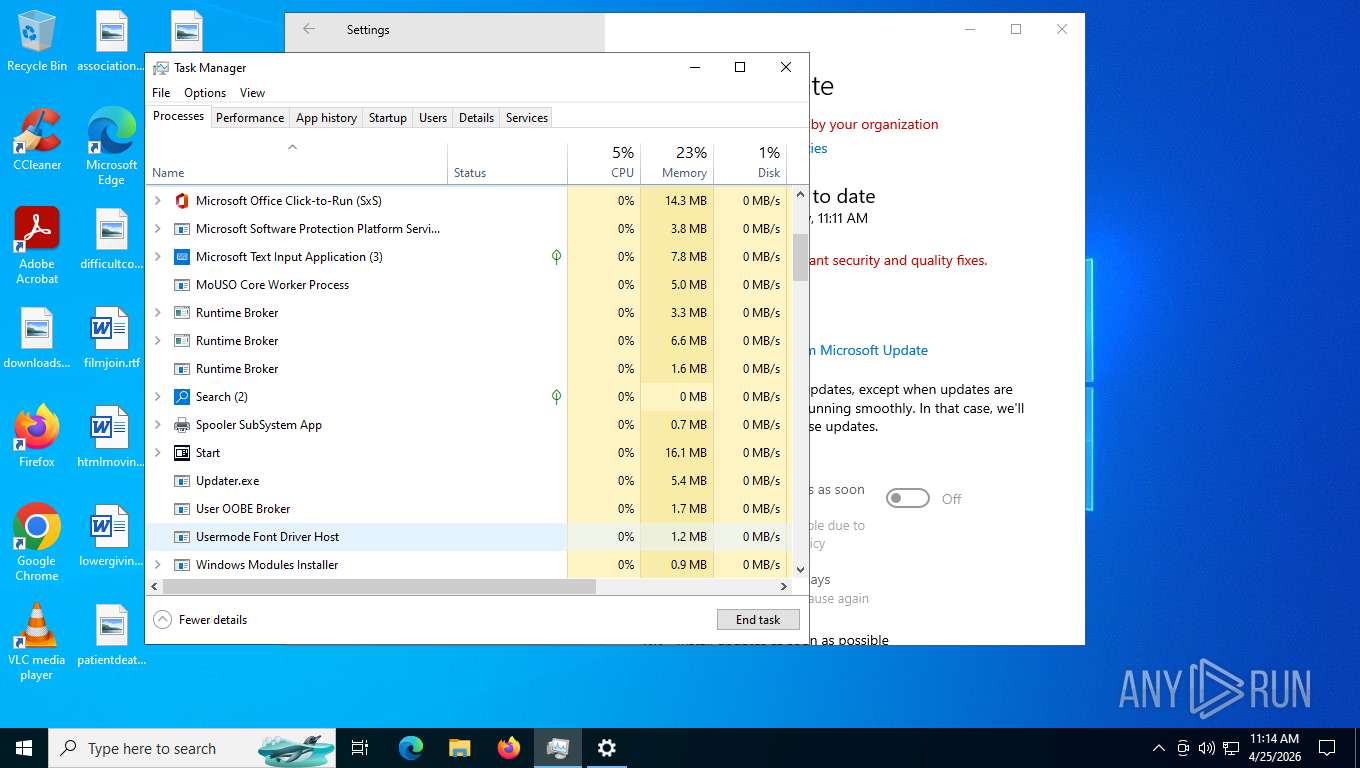
- 4333215012613356.exe (PID: 2340)
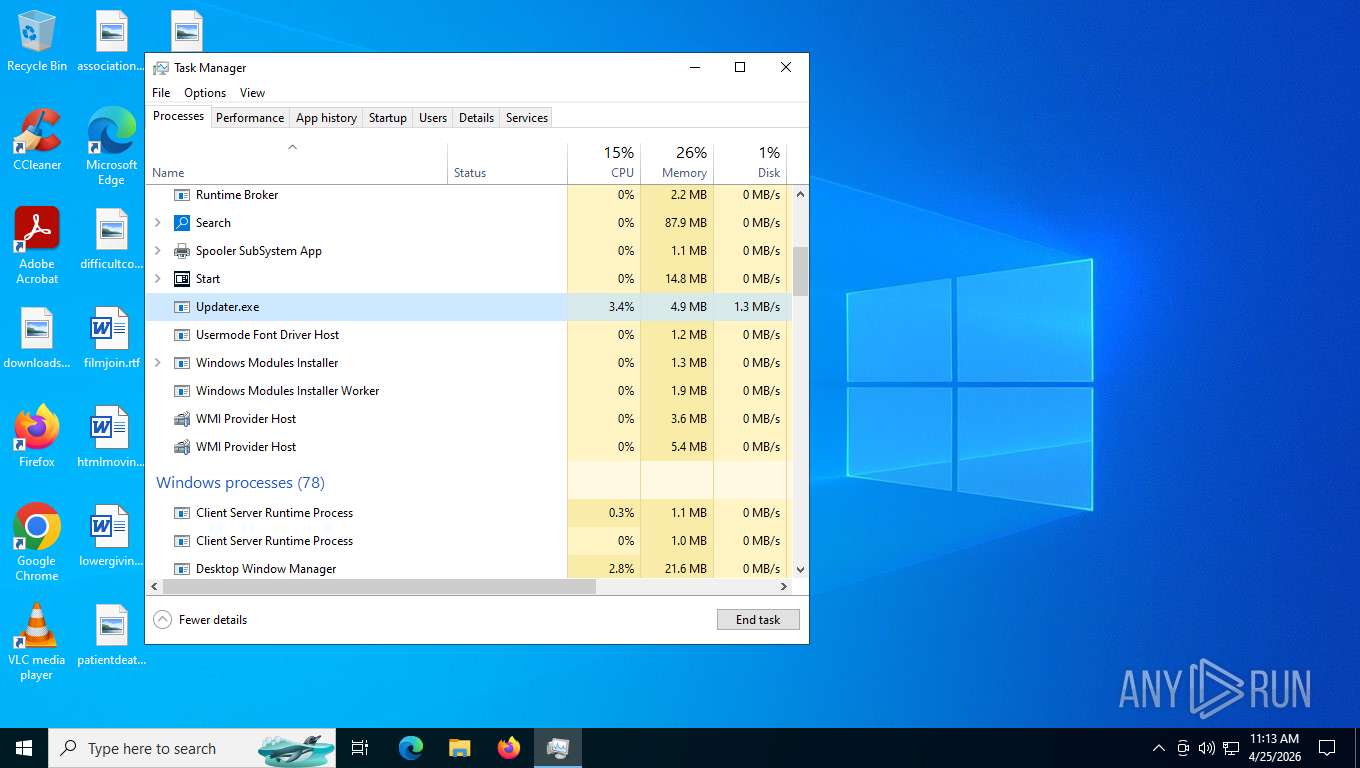
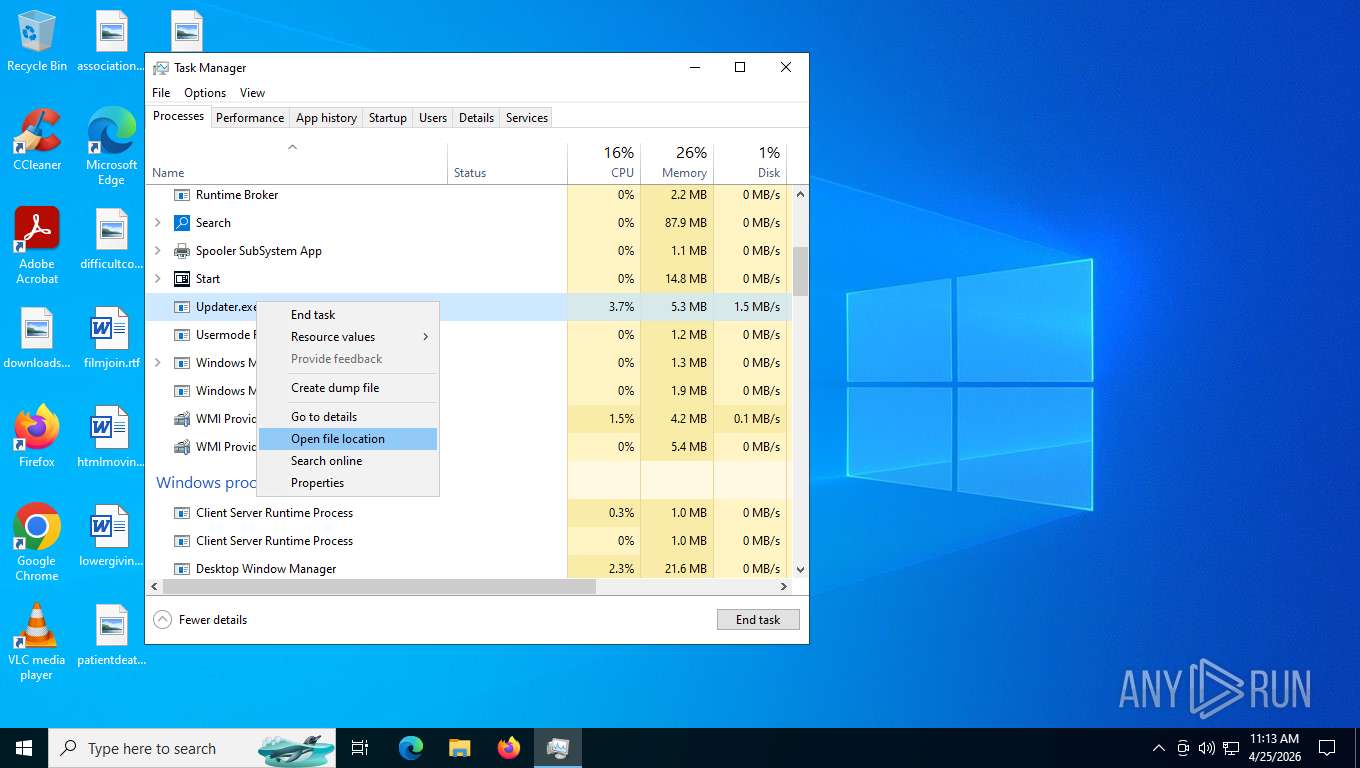
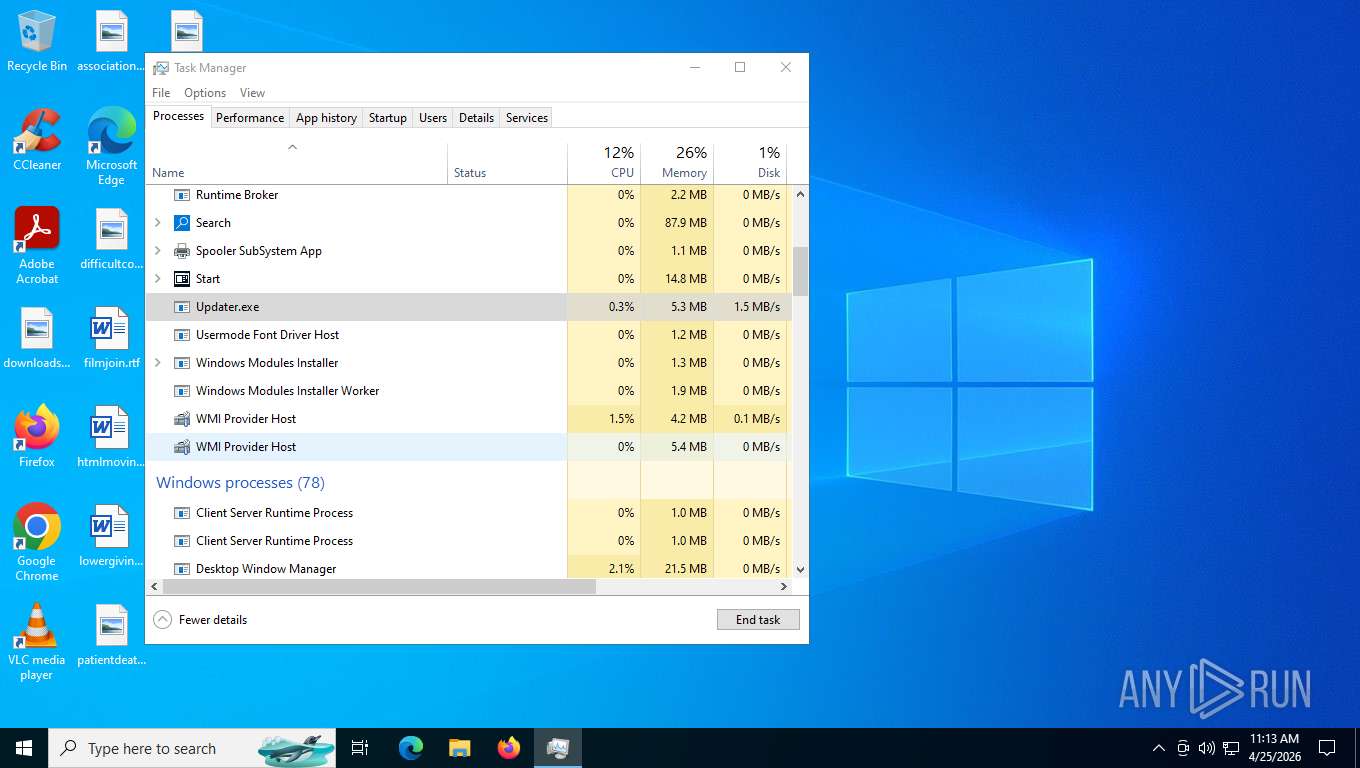
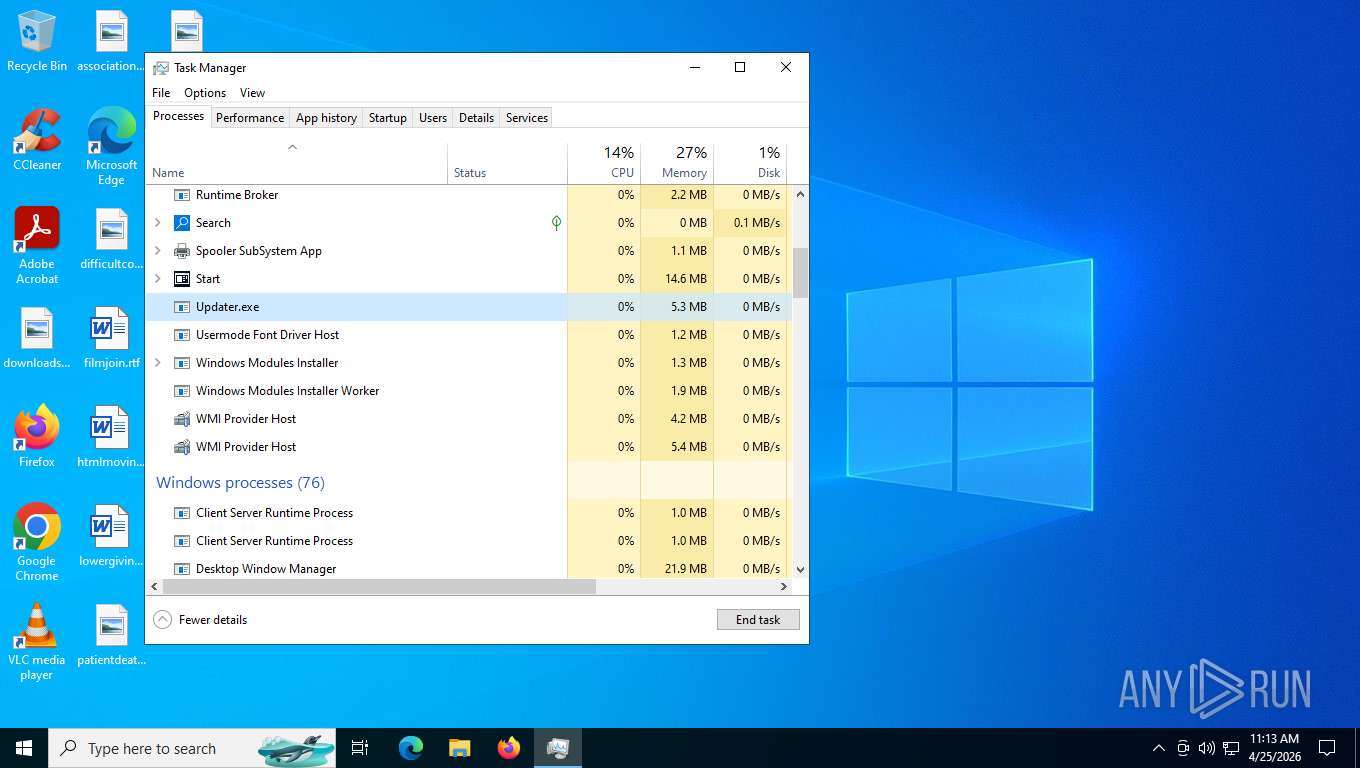
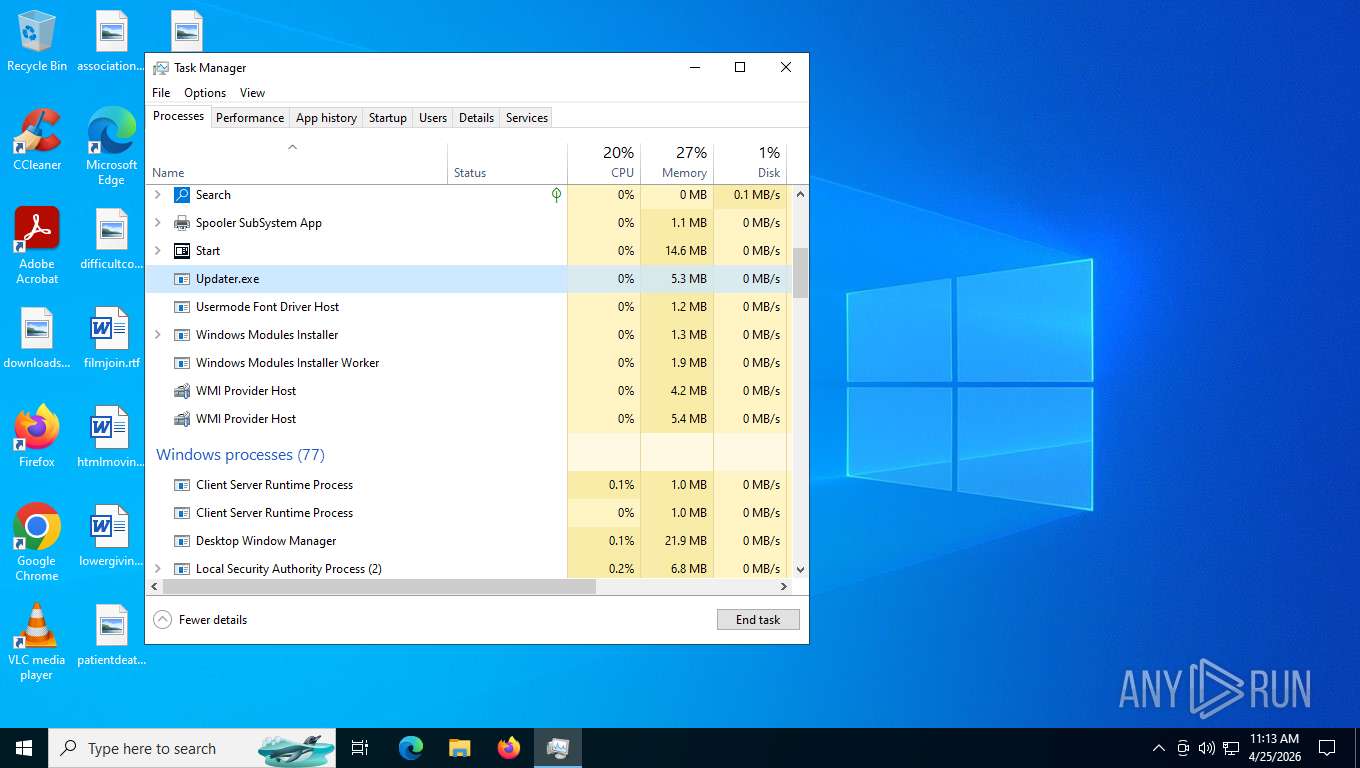
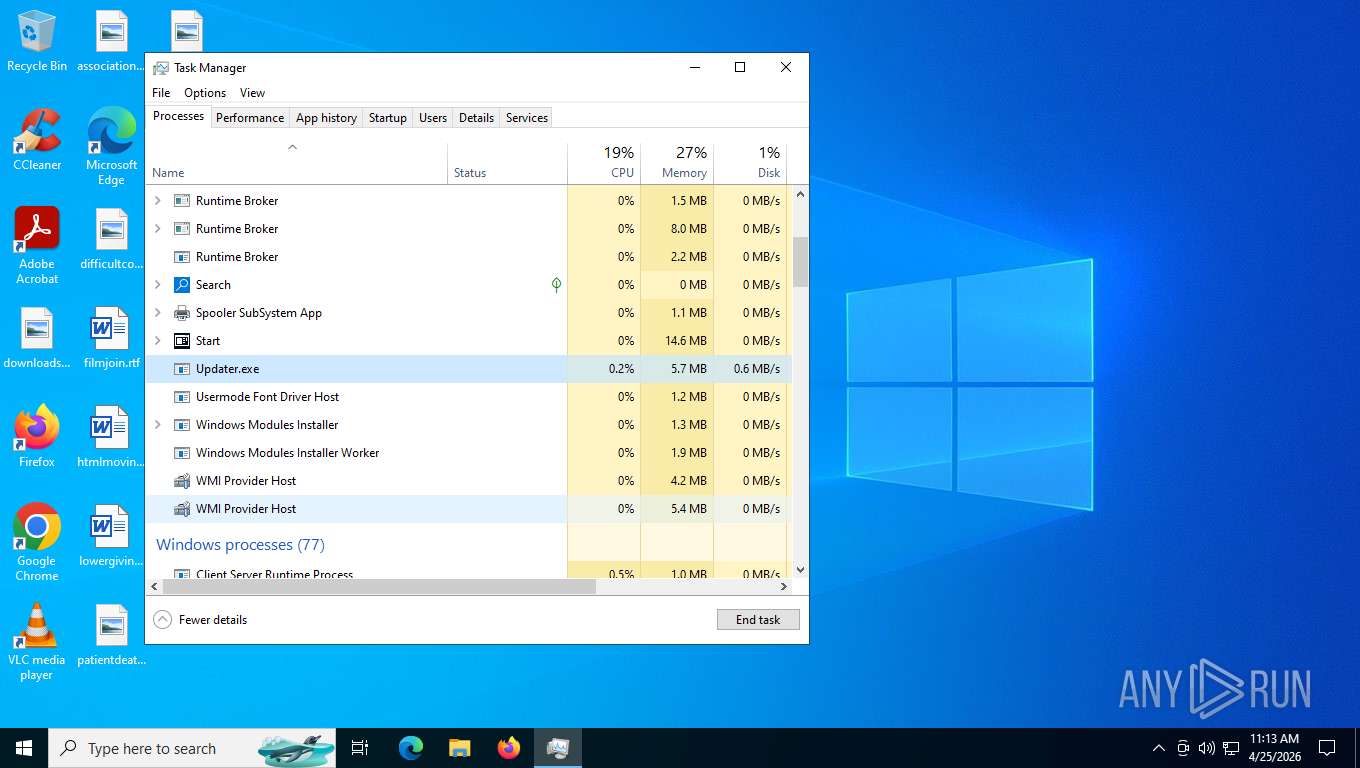
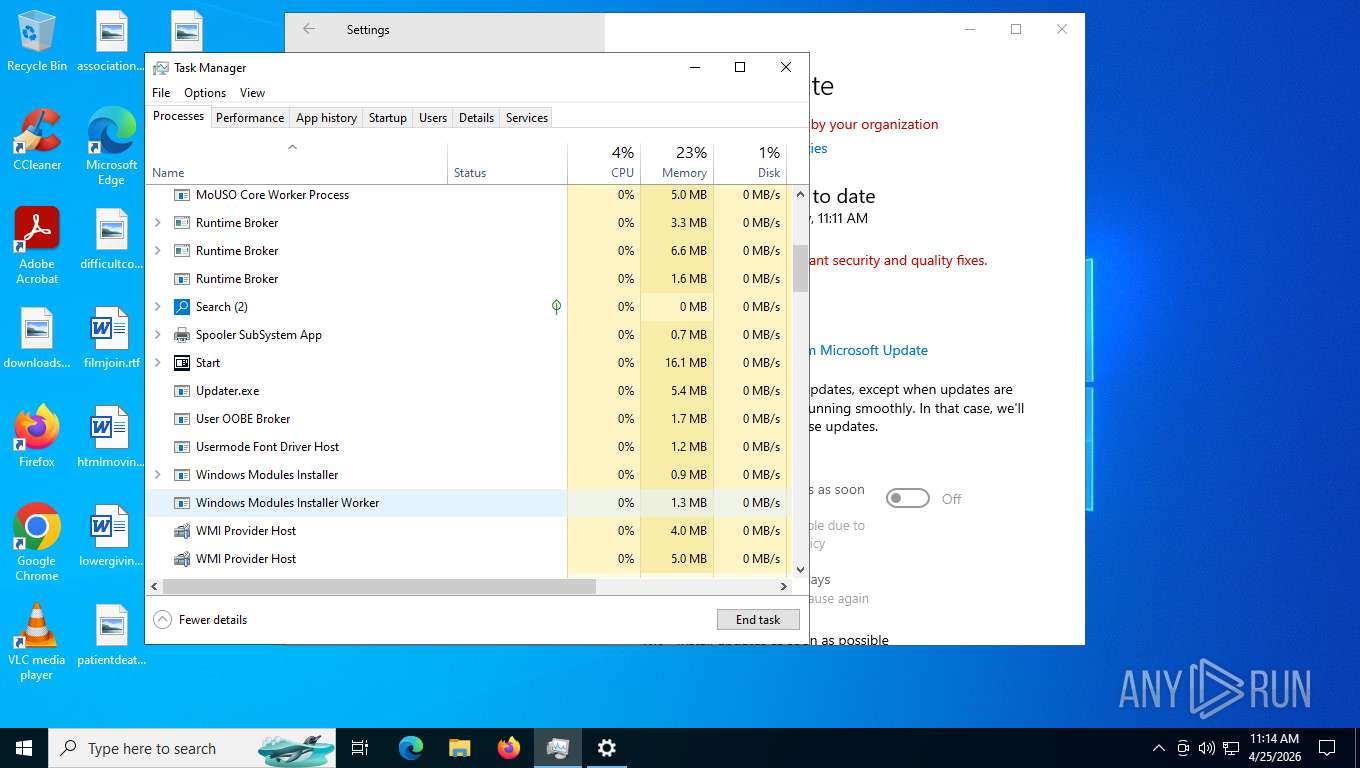
- Updater.exe (PID: 6672)
XWORM has been detected (SURICATA)
- 4333215012613356.exe (PID: 2340)
- Updater.exe (PID: 6672)
XWORM has been detected (YARA)
- 4333215012613356.exe (PID: 2340)
SUSPICIOUS
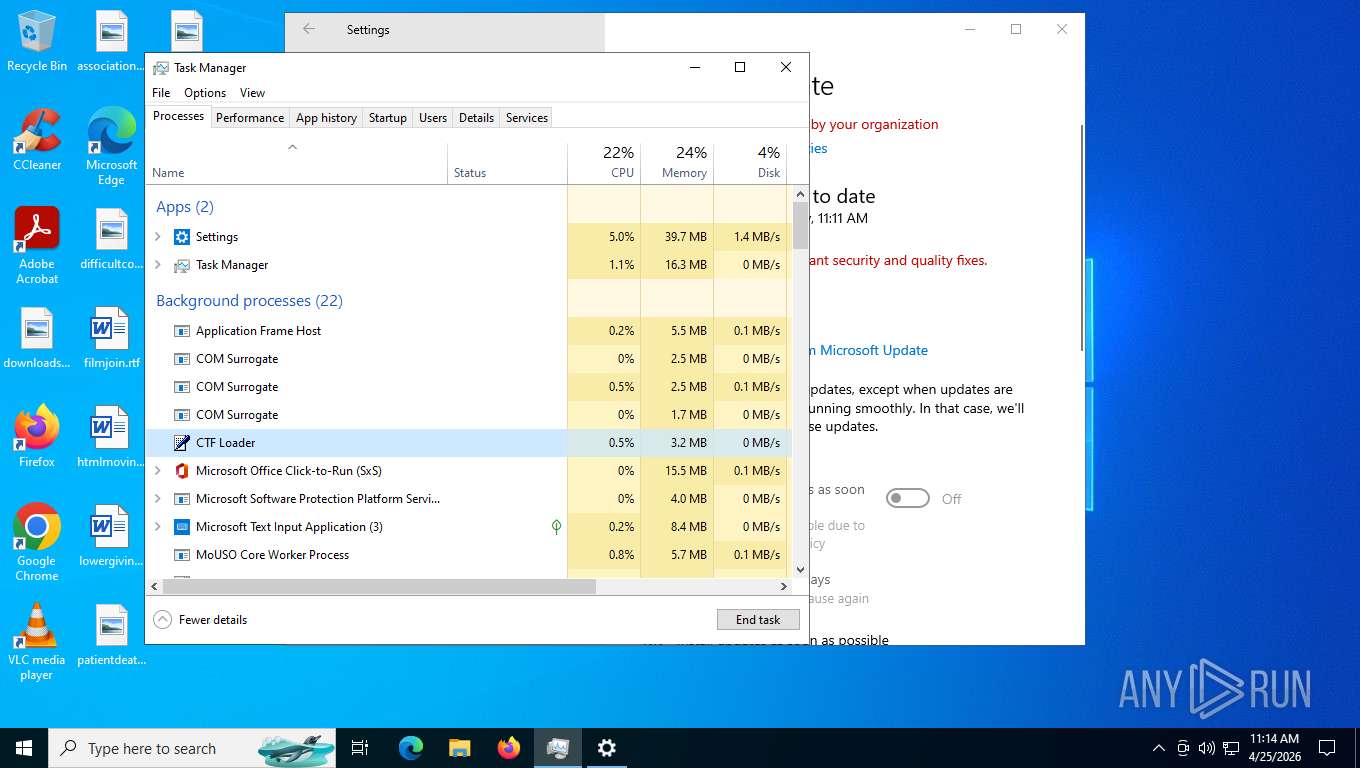
The executable file from the user directory is run by the CMD process
- rename.exe (PID: 2880)
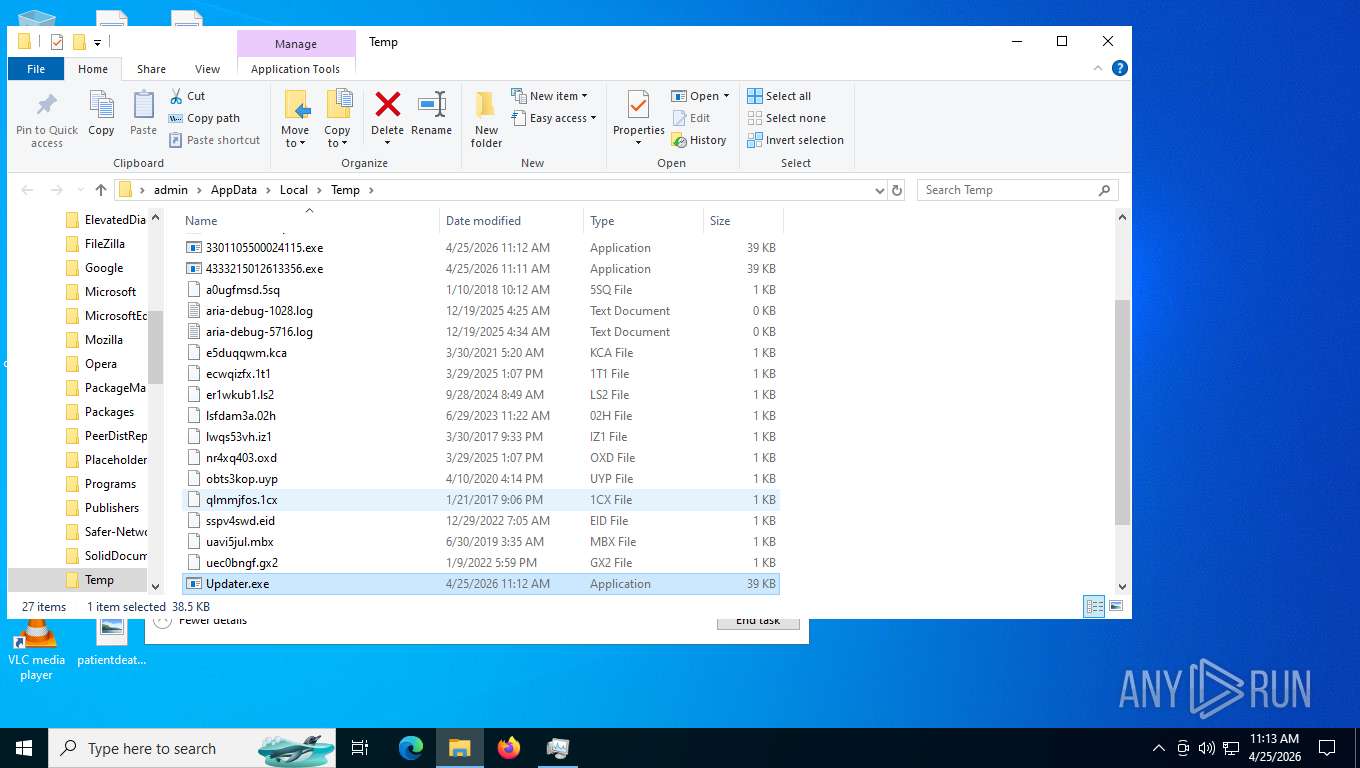
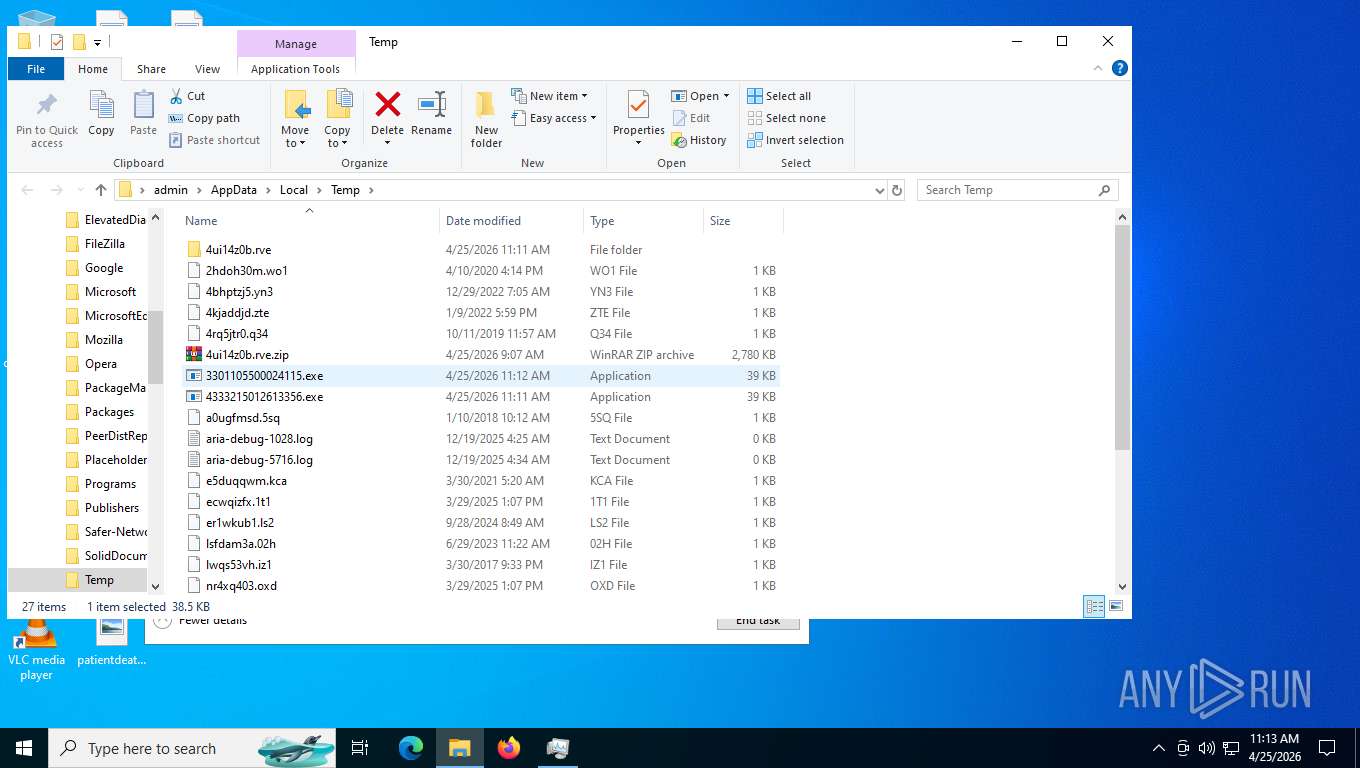
Executable content was dropped or overwritten
- rename.exe (PID: 2880)
- rename.exe (PID: 3552)
- 4333215012613356.exe (PID: 2340)
Reads the date of Windows installation
- rename.exe (PID: 2880)
- rename.exe (PID: 3552)
Reads the BIOS version
- rename.exe (PID: 2880)
- rename.exe (PID: 3552)
Contacting a server suspected of hosting an CnC
- 4333215012613356.exe (PID: 2340)
- Updater.exe (PID: 6672)
INFO
Application launched itself
- msedge.exe (PID: 7844)
- msedge.exe (PID: 6472)
Checks supported languages
- msedge_proxy.exe (PID: 5920)
- rename.exe (PID: 2880)
- 4333215012613356.exe (PID: 2340)
- rename.exe (PID: 3552)
- 3301105500024115.exe (PID: 7788)
- Updater.exe (PID: 4312)
- Updater.exe (PID: 6672)
Reads the machine GUID from the registry
- rename.exe (PID: 2880)
- 4333215012613356.exe (PID: 2340)
- 3301105500024115.exe (PID: 7788)
- rename.exe (PID: 3552)
- Updater.exe (PID: 4312)
- Updater.exe (PID: 6672)
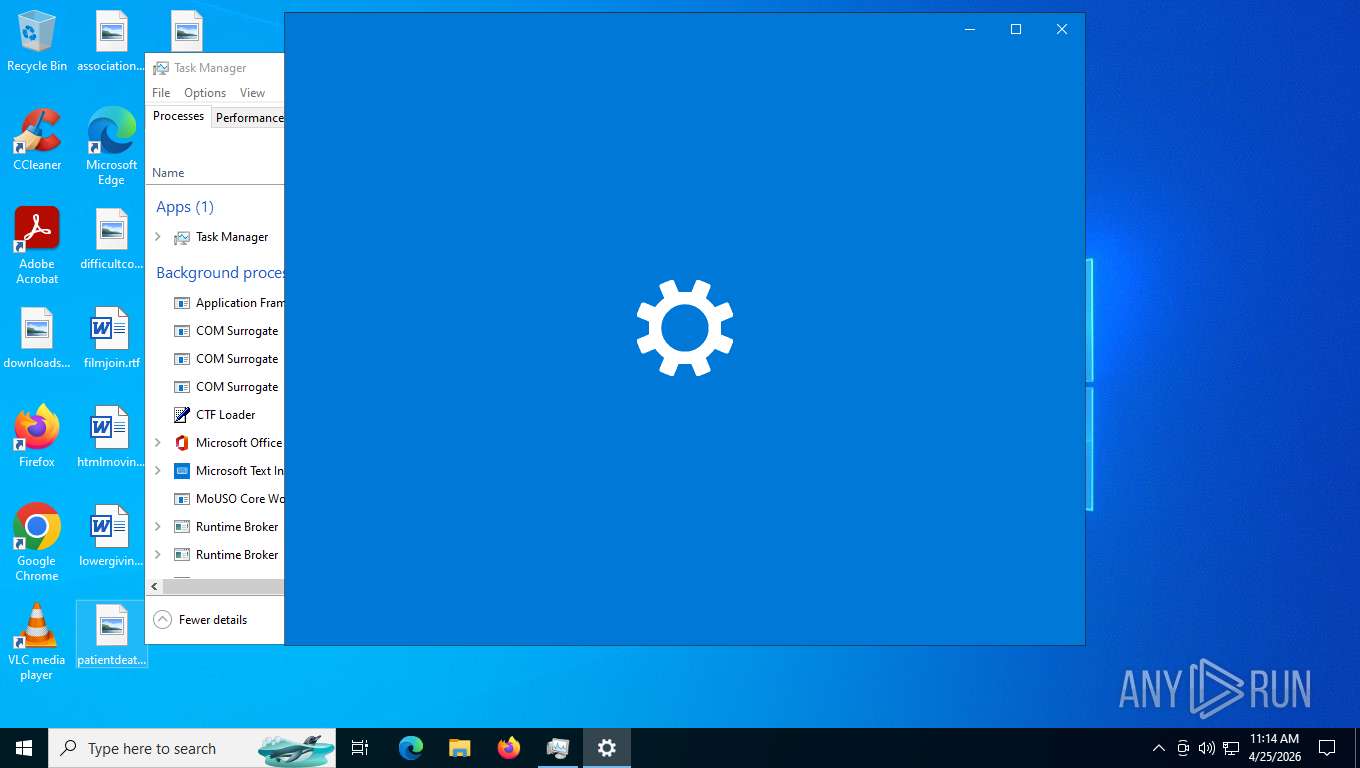
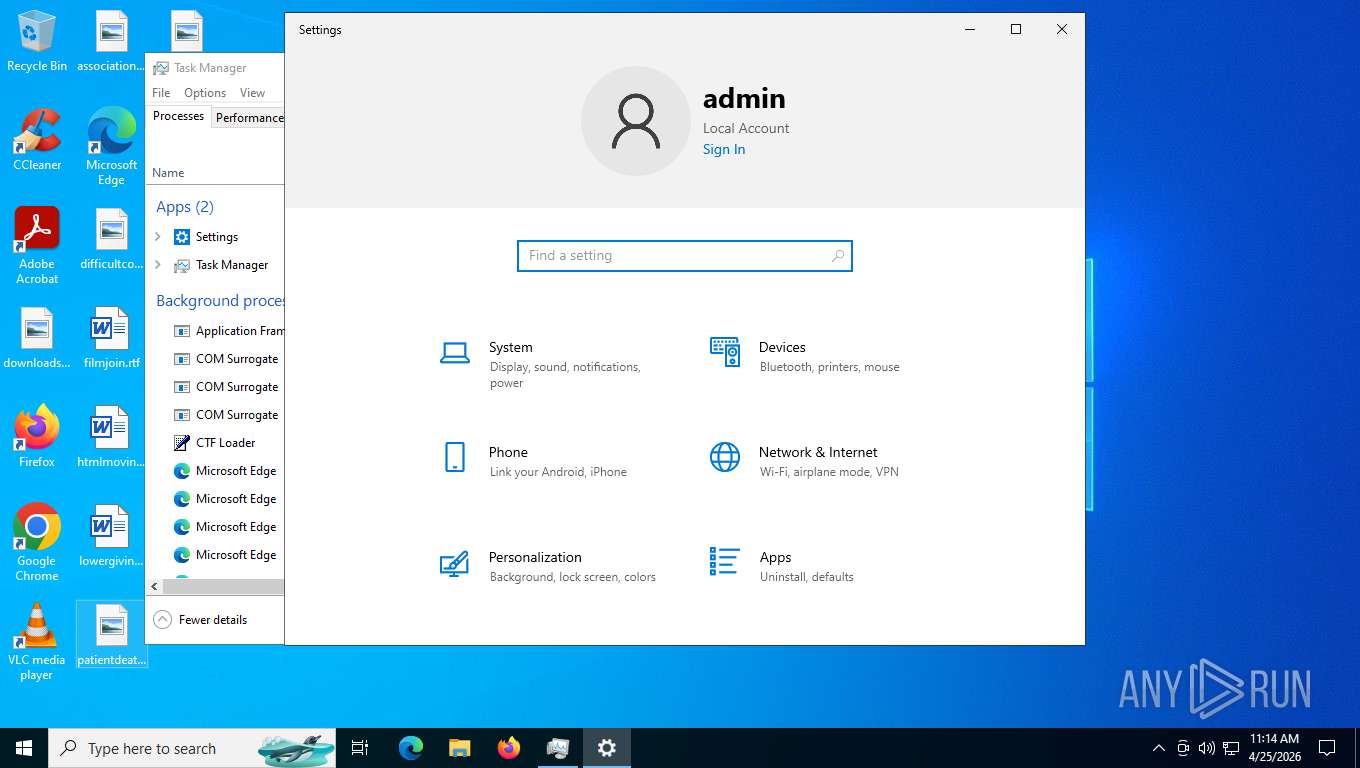
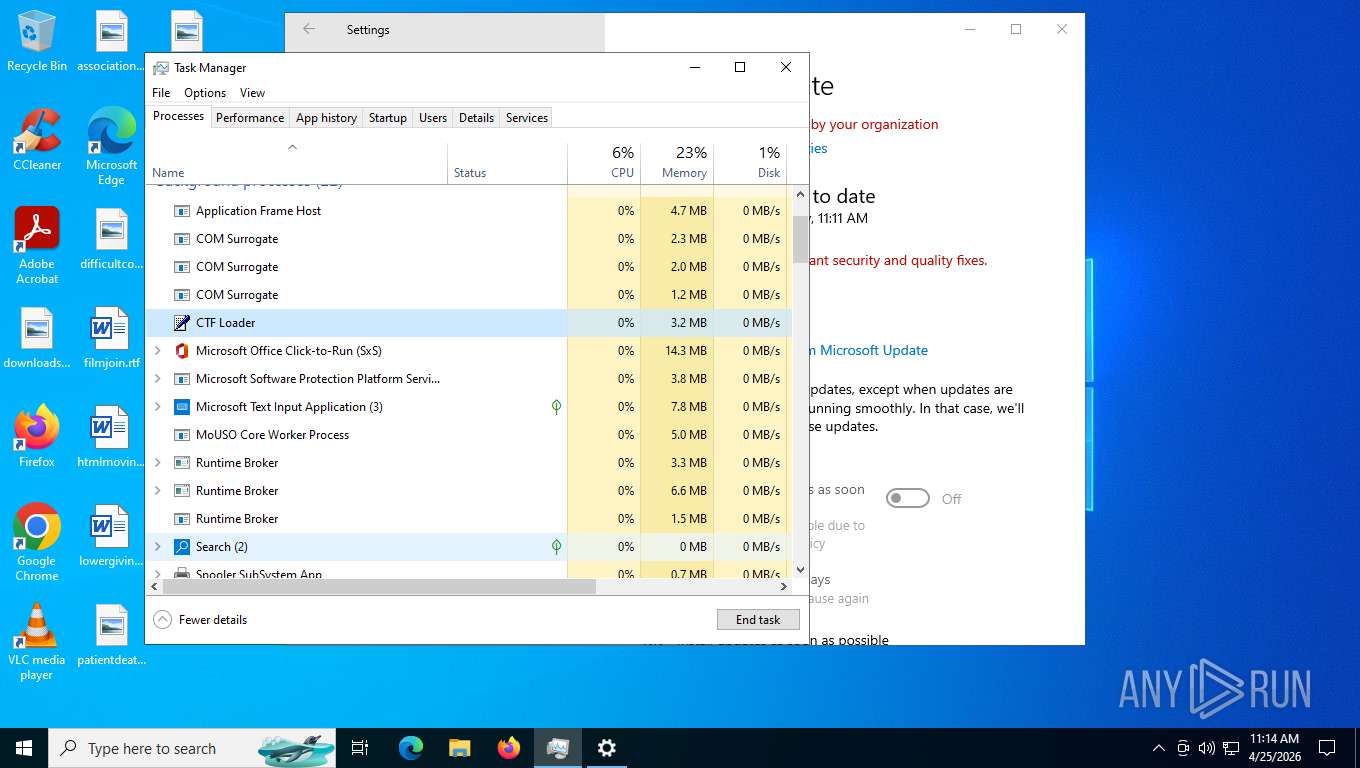
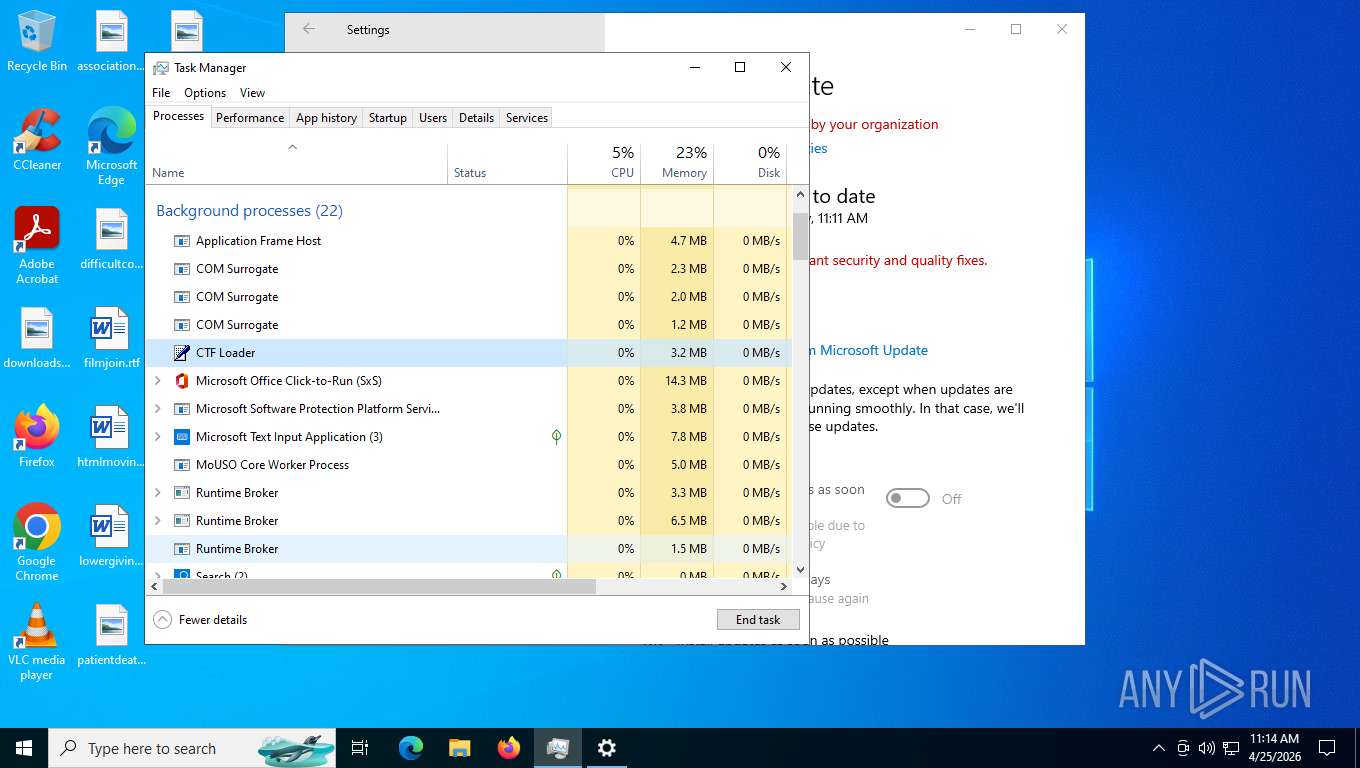
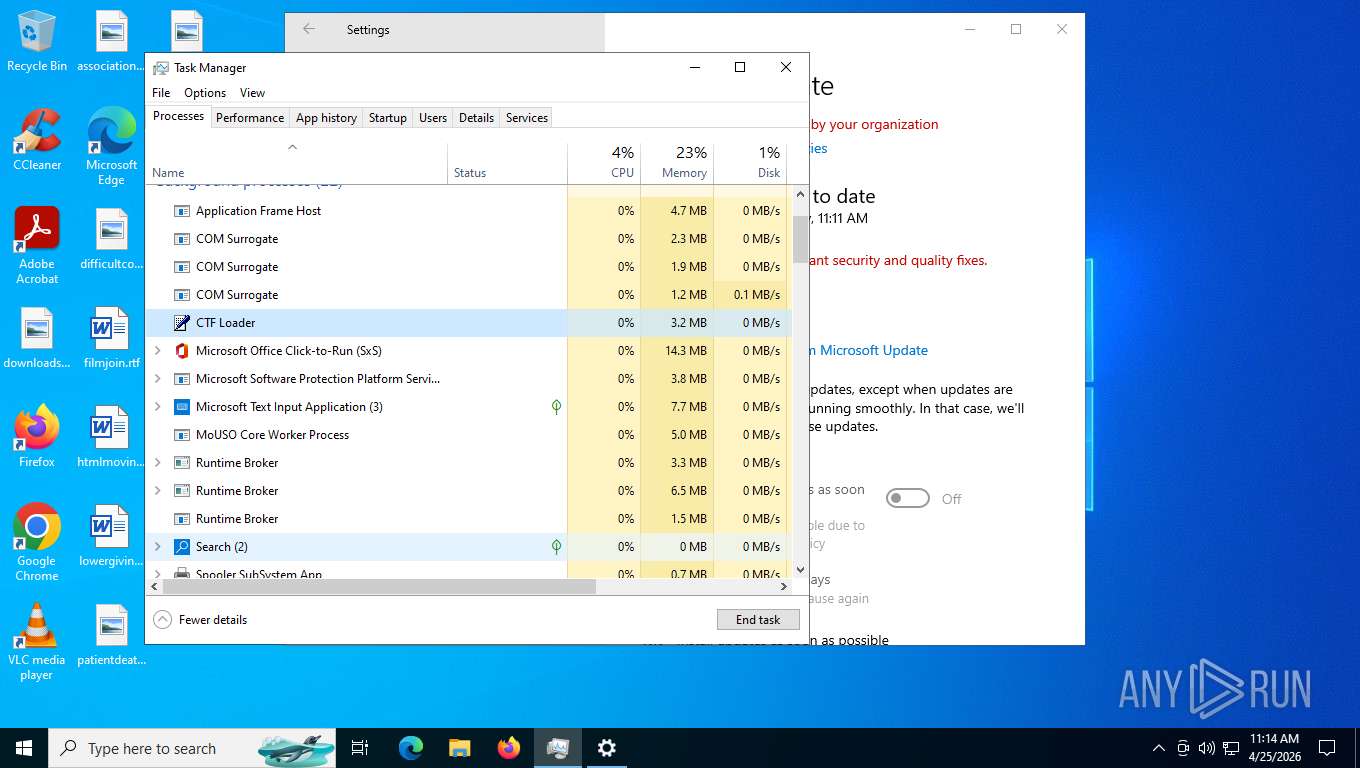
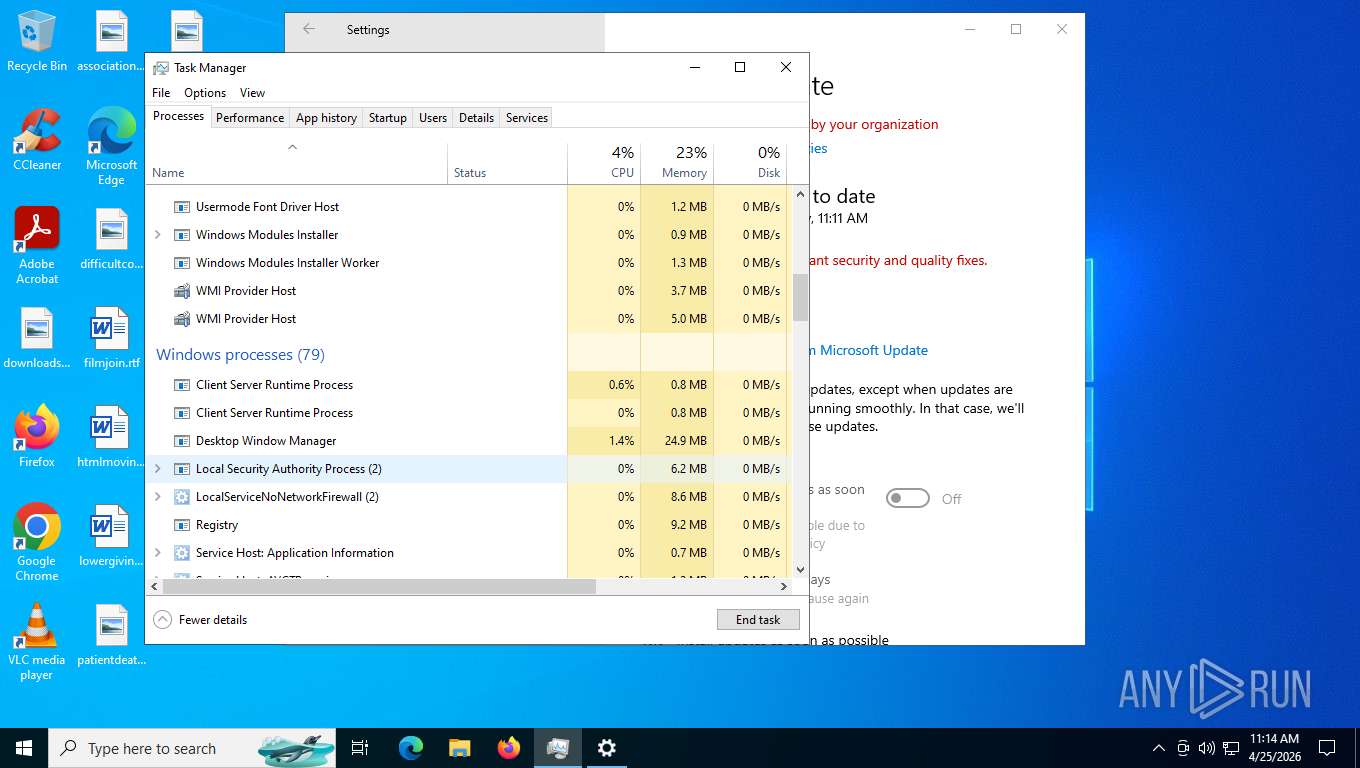
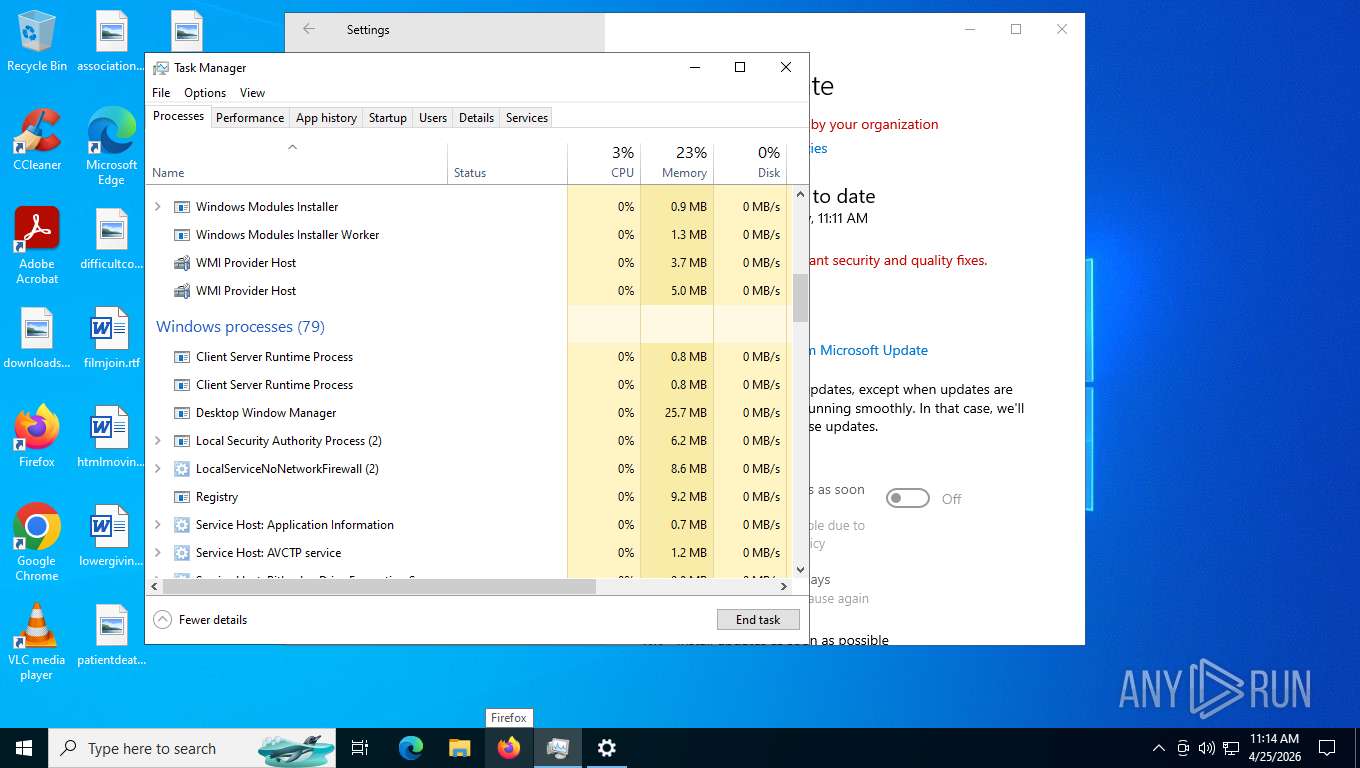
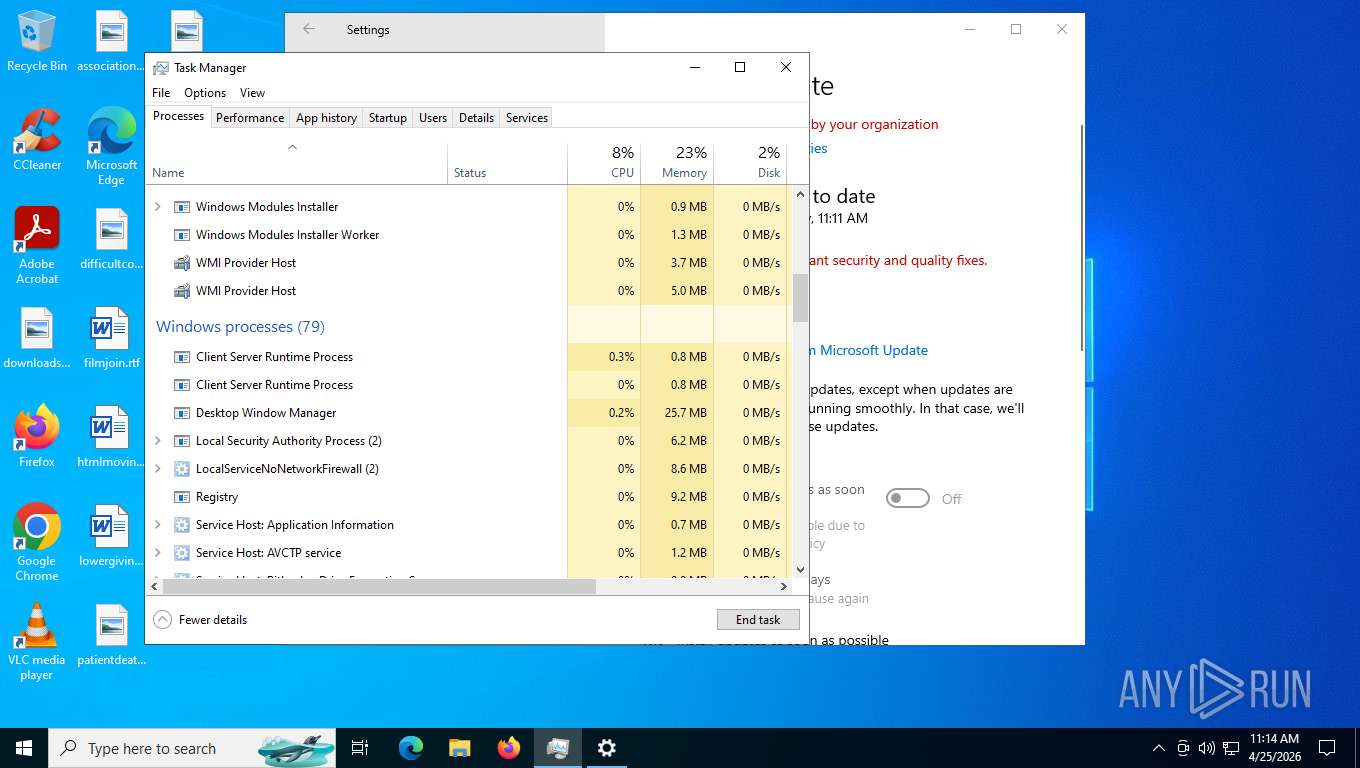
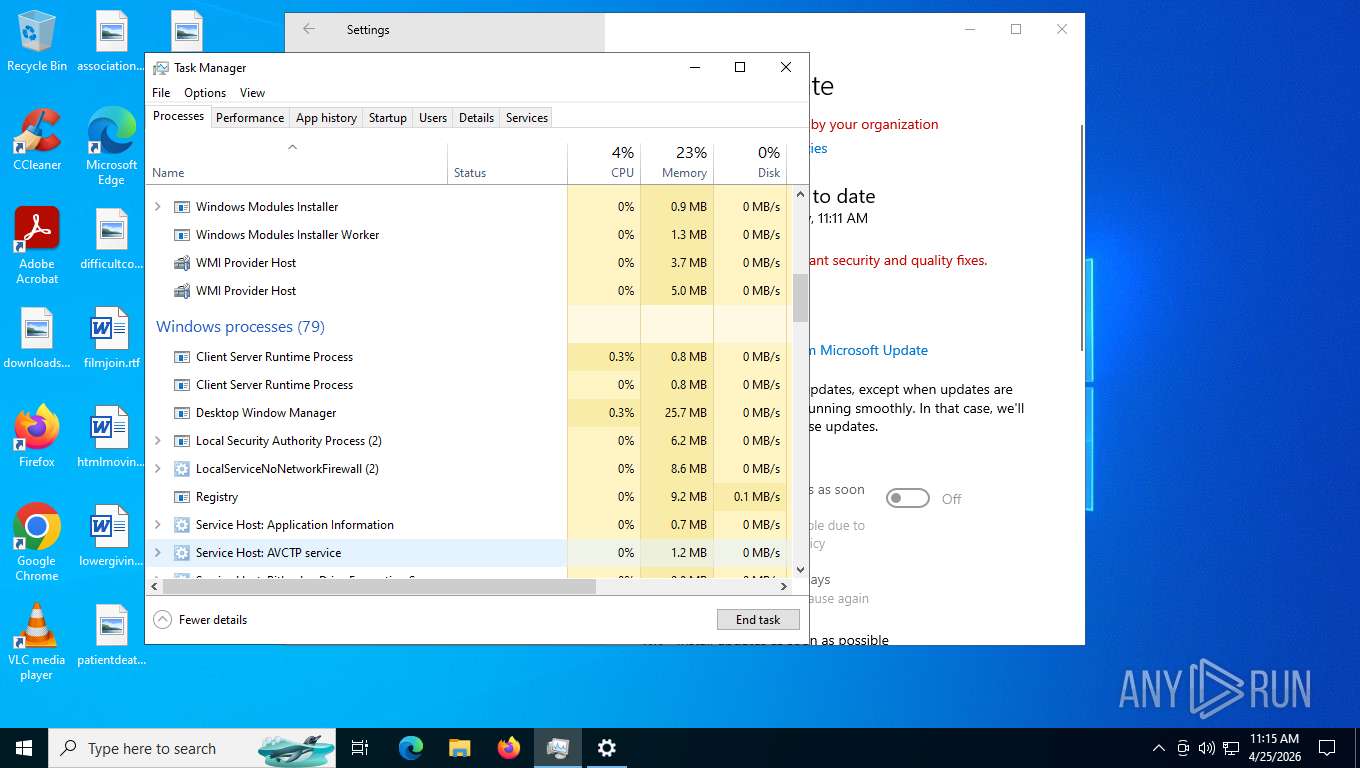
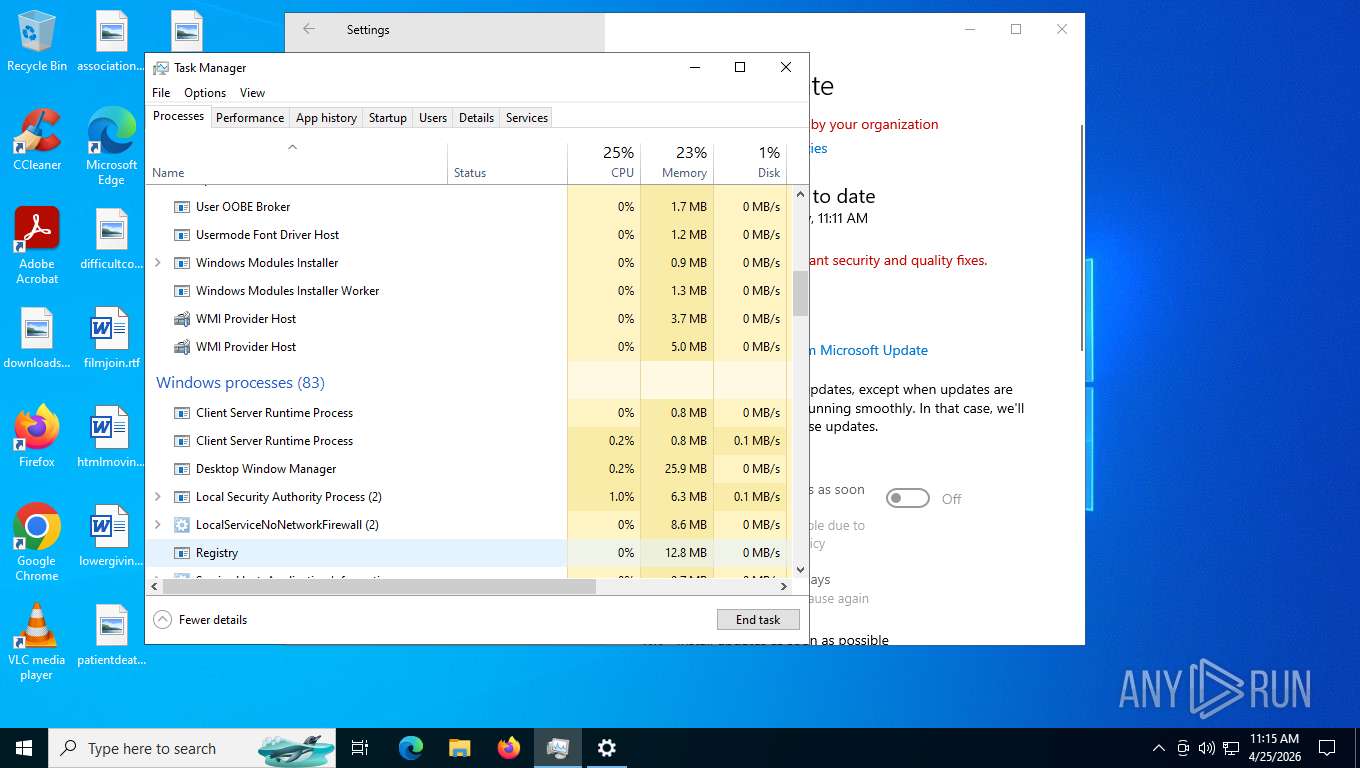
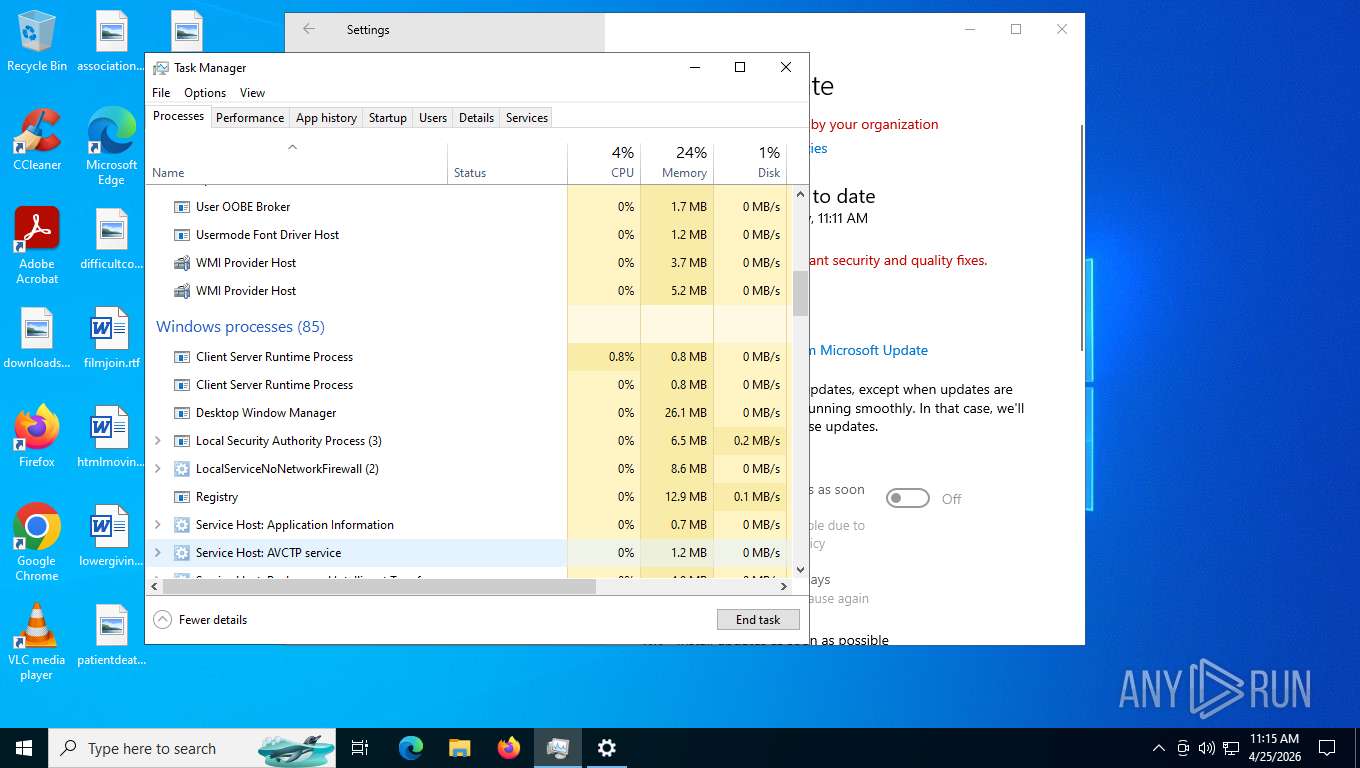
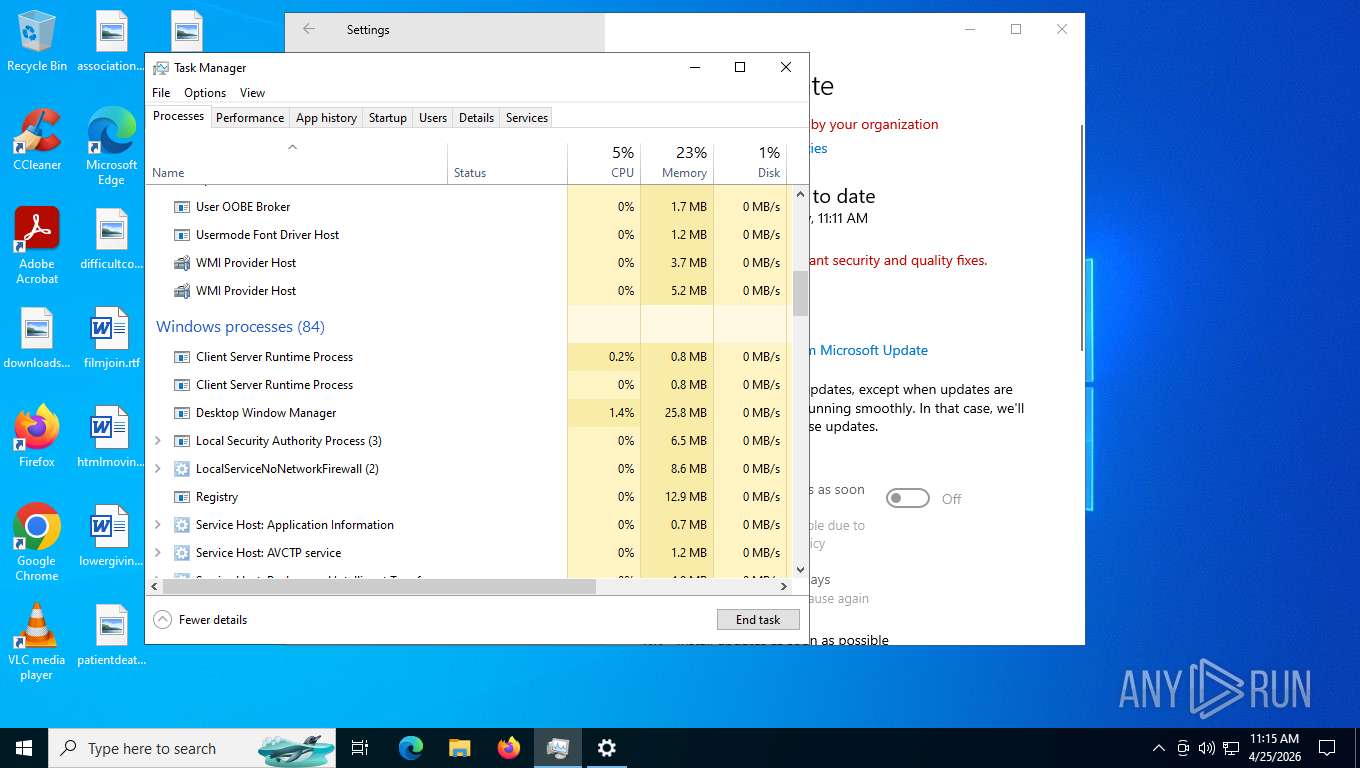
Reads security settings of Internet Explorer
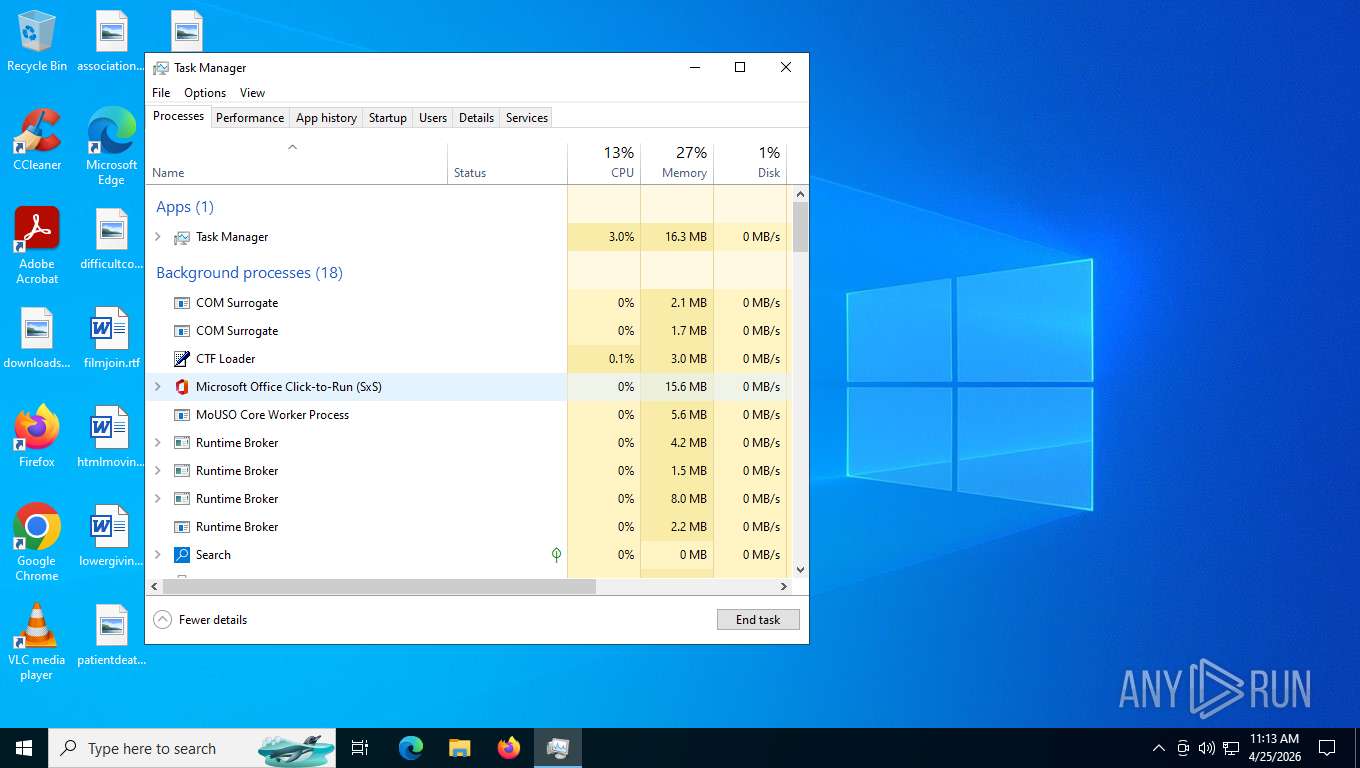
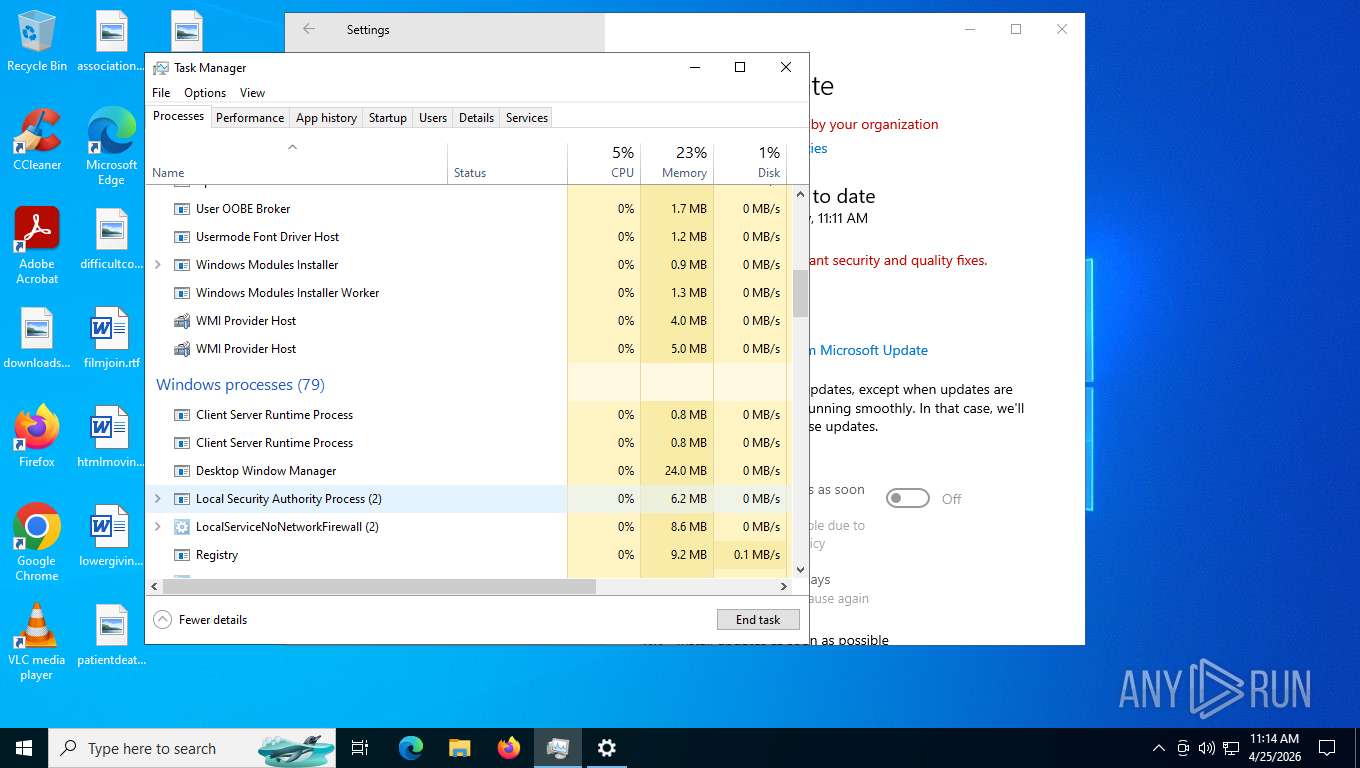
- Taskmgr.exe (PID: 7428)
- rename.exe (PID: 2880)
- rename.exe (PID: 3552)
- Taskmgr.exe (PID: 6580)
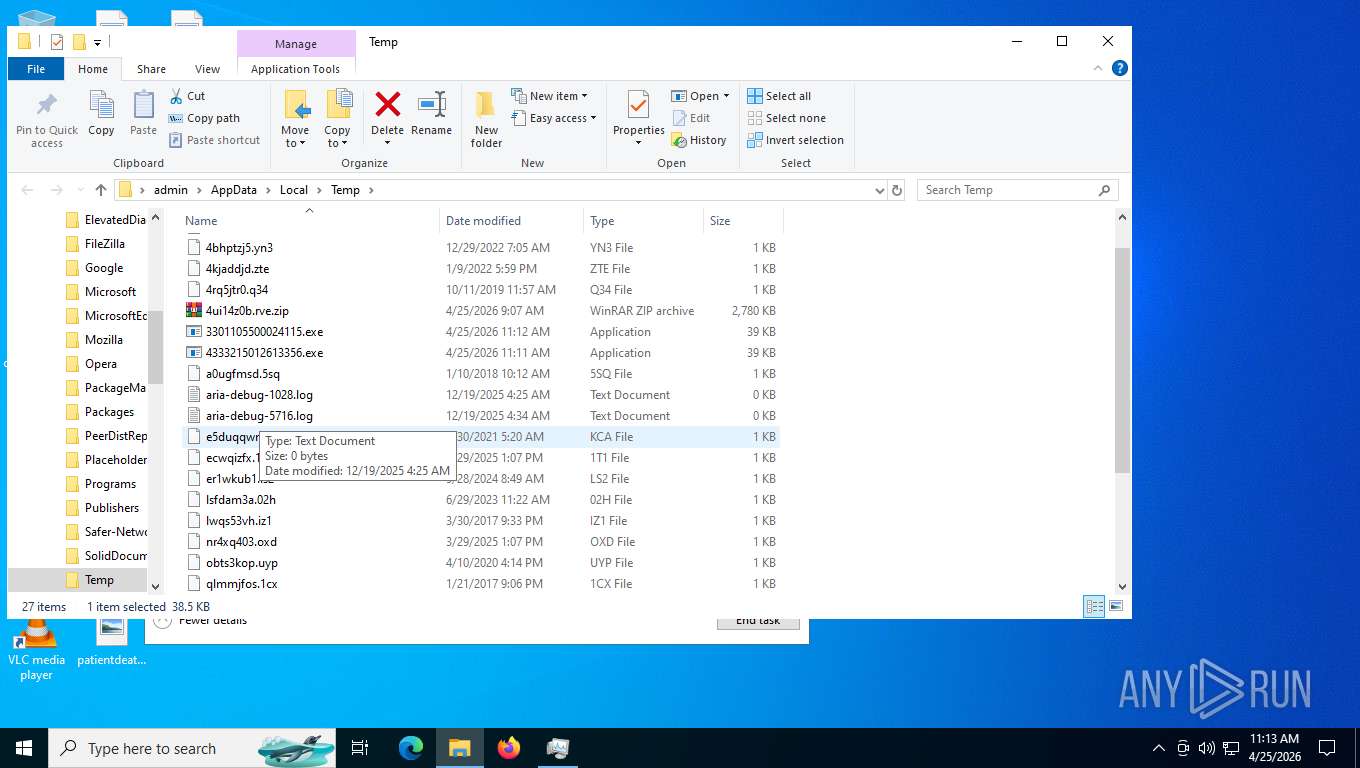
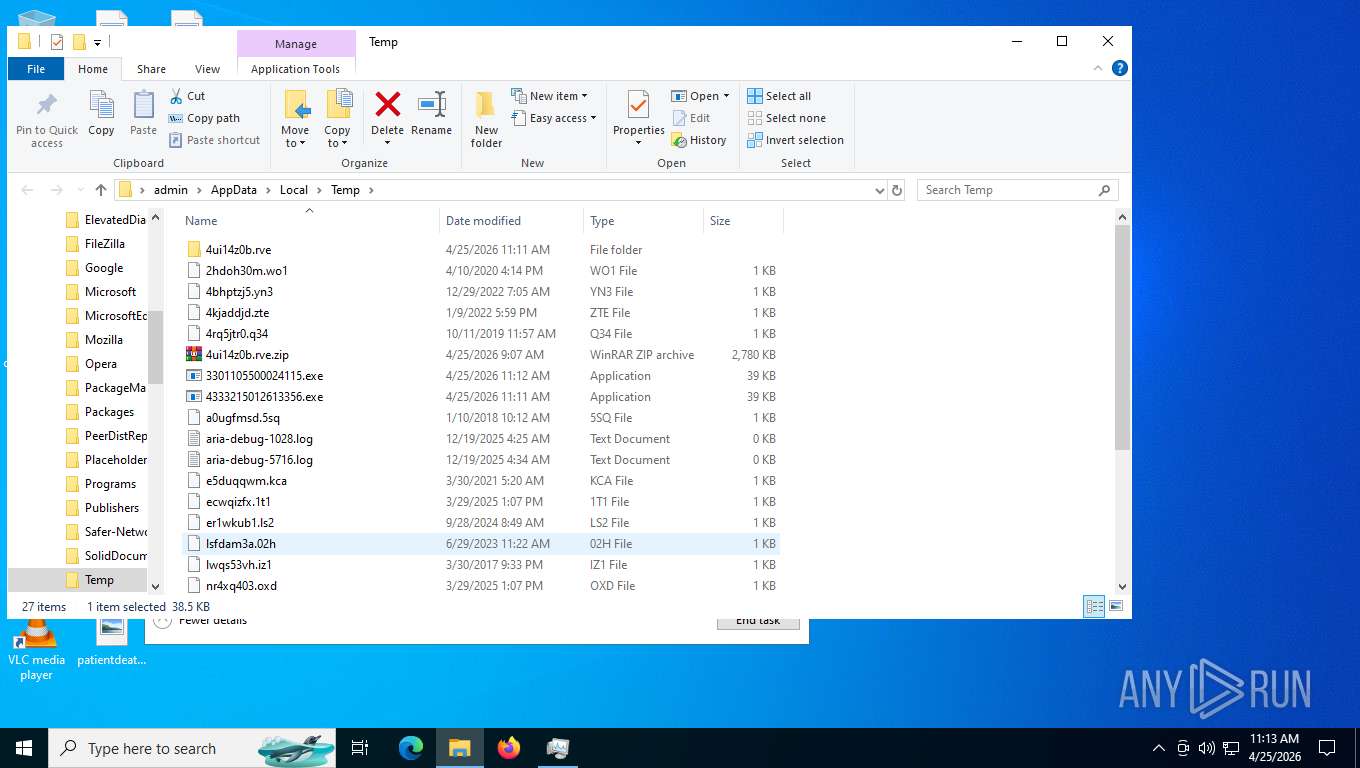
Create files in a temporary directory
- rename.exe (PID: 2880)
- rename.exe (PID: 3552)
- 4333215012613356.exe (PID: 2340)
Reads the computer name
- rename.exe (PID: 2880)
- 4333215012613356.exe (PID: 2340)
- rename.exe (PID: 3552)
- 3301105500024115.exe (PID: 7788)
- Updater.exe (PID: 4312)
- Updater.exe (PID: 6672)
Process checks computer location settings
- rename.exe (PID: 2880)
- rename.exe (PID: 3552)
Reads Windows Product ID
- rename.exe (PID: 2880)
- rename.exe (PID: 3552)
Attempting to use instant messaging service
- rename.exe (PID: 2880)
- rename.exe (PID: 3552)
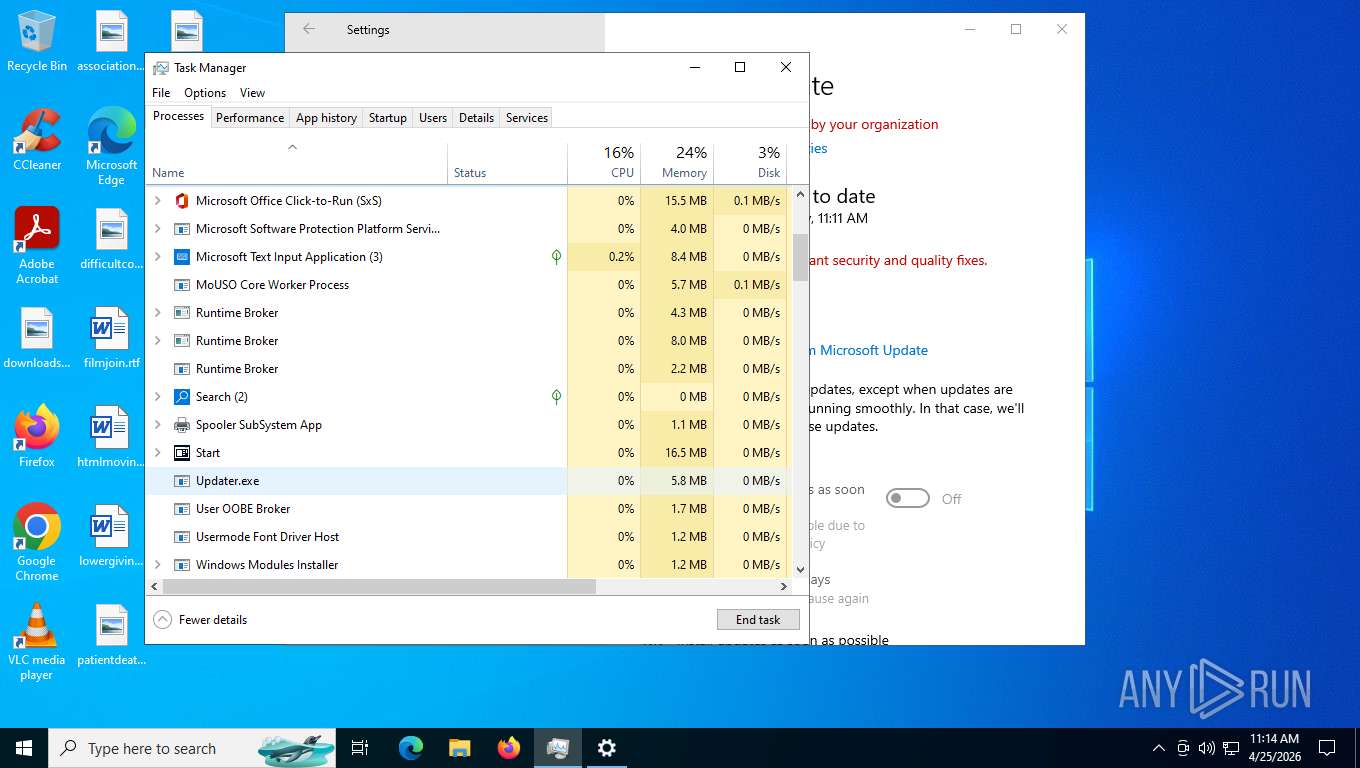
Launching a file from a Registry key
- 4333215012613356.exe (PID: 2340)
- Updater.exe (PID: 6672)
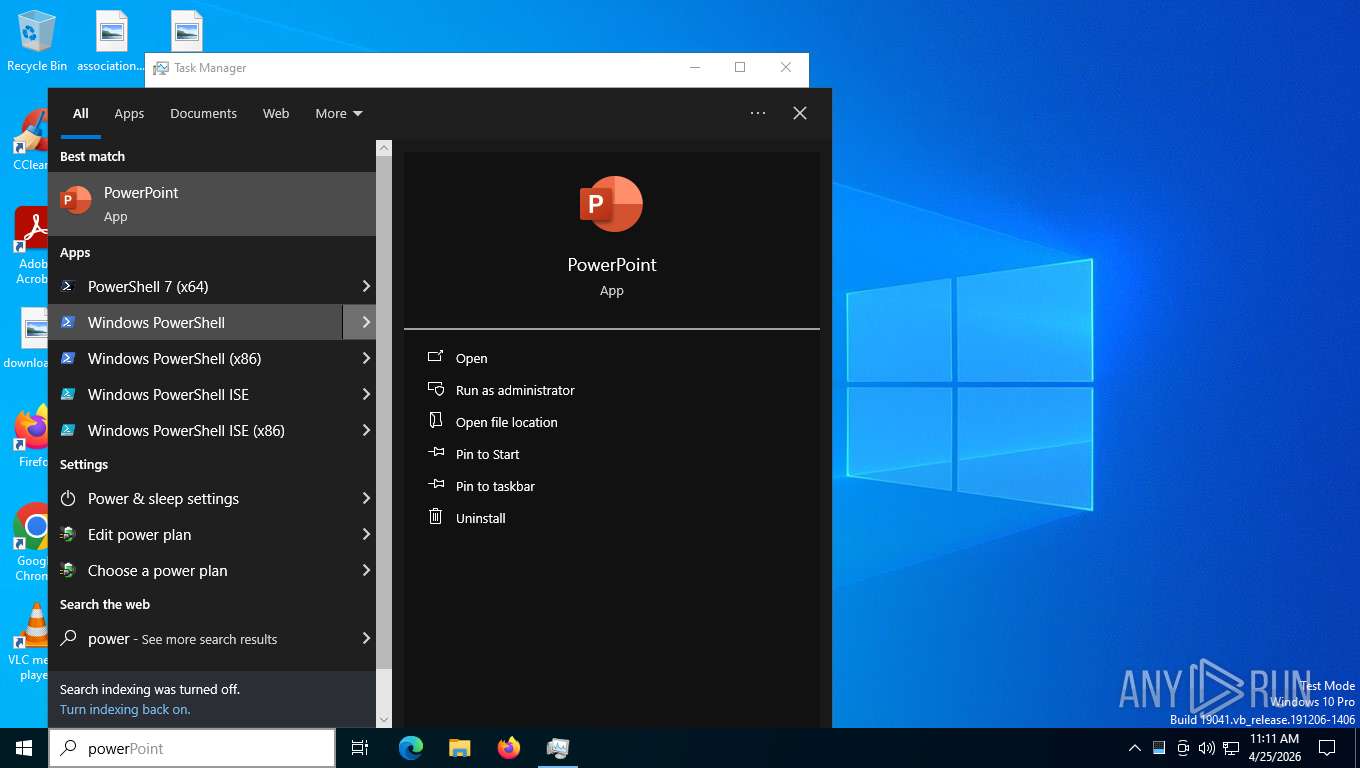
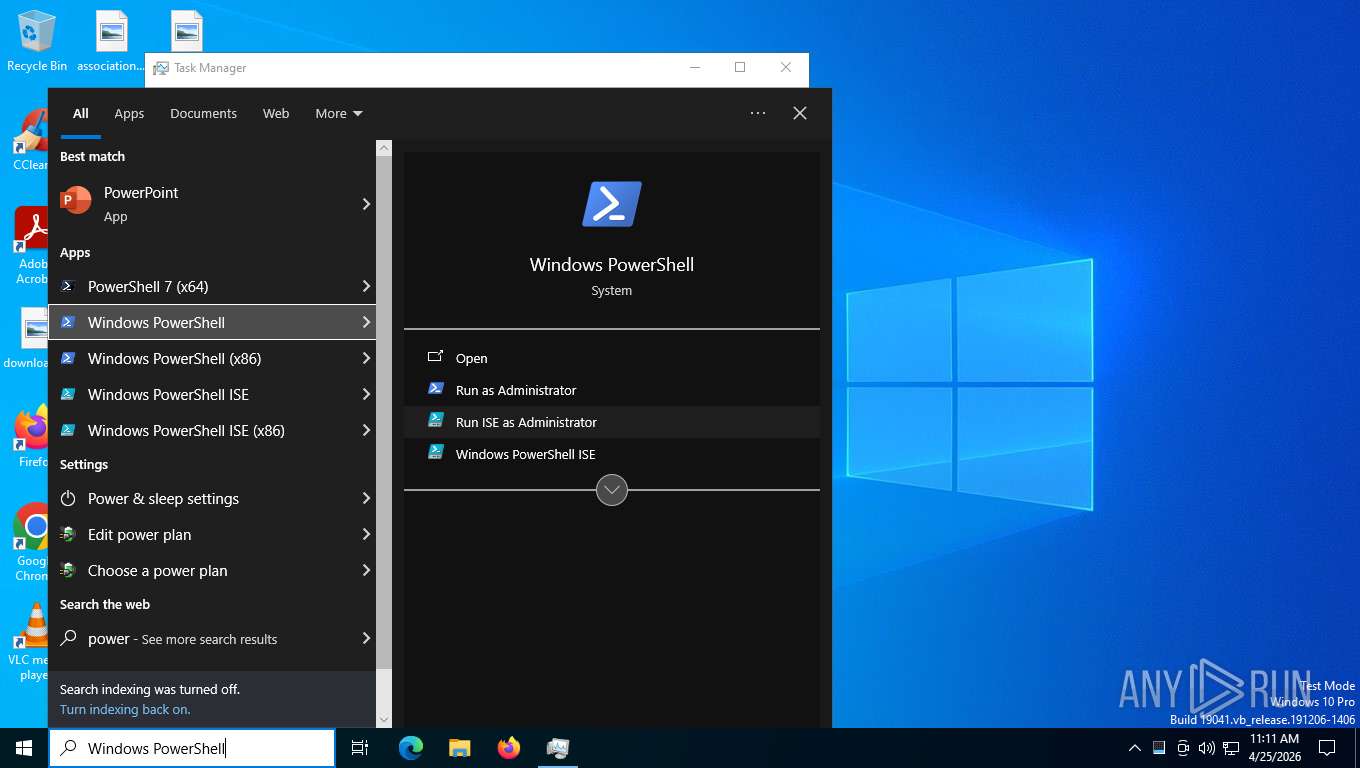
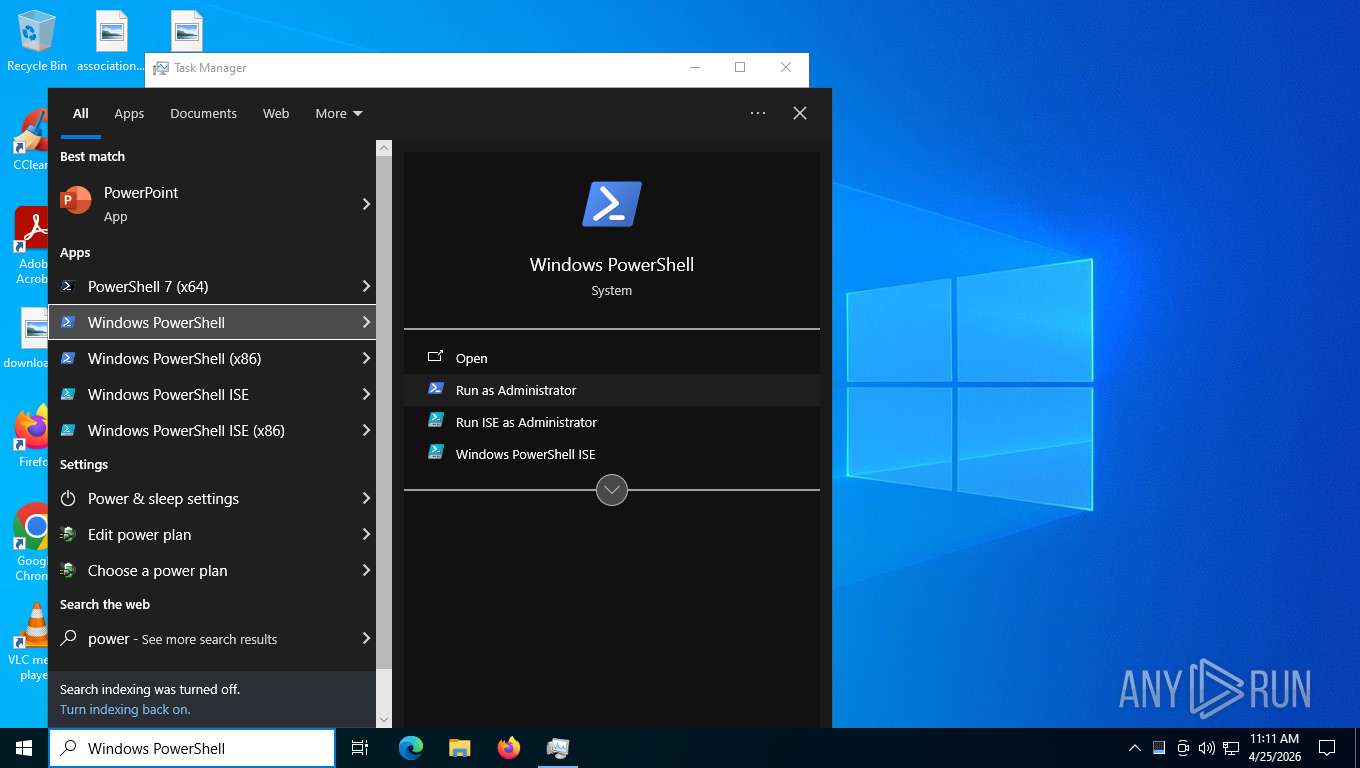
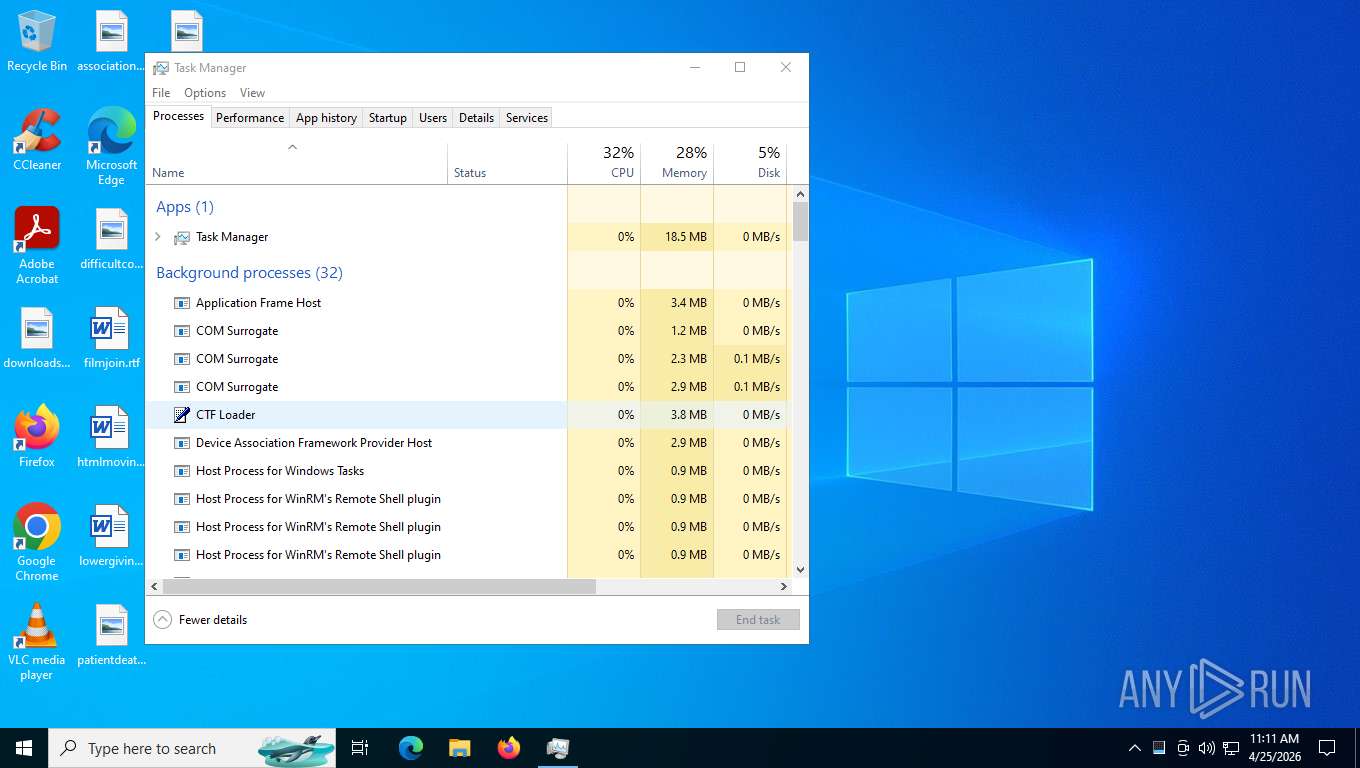
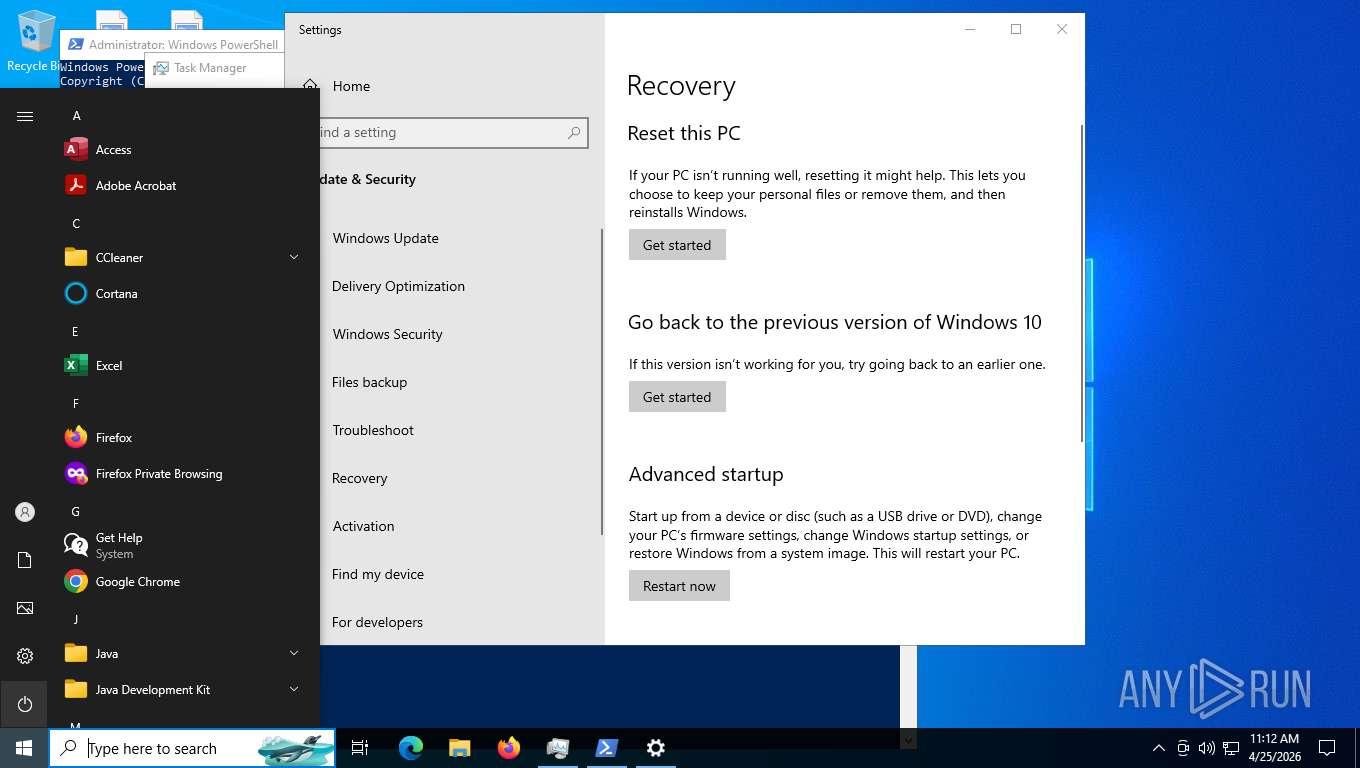
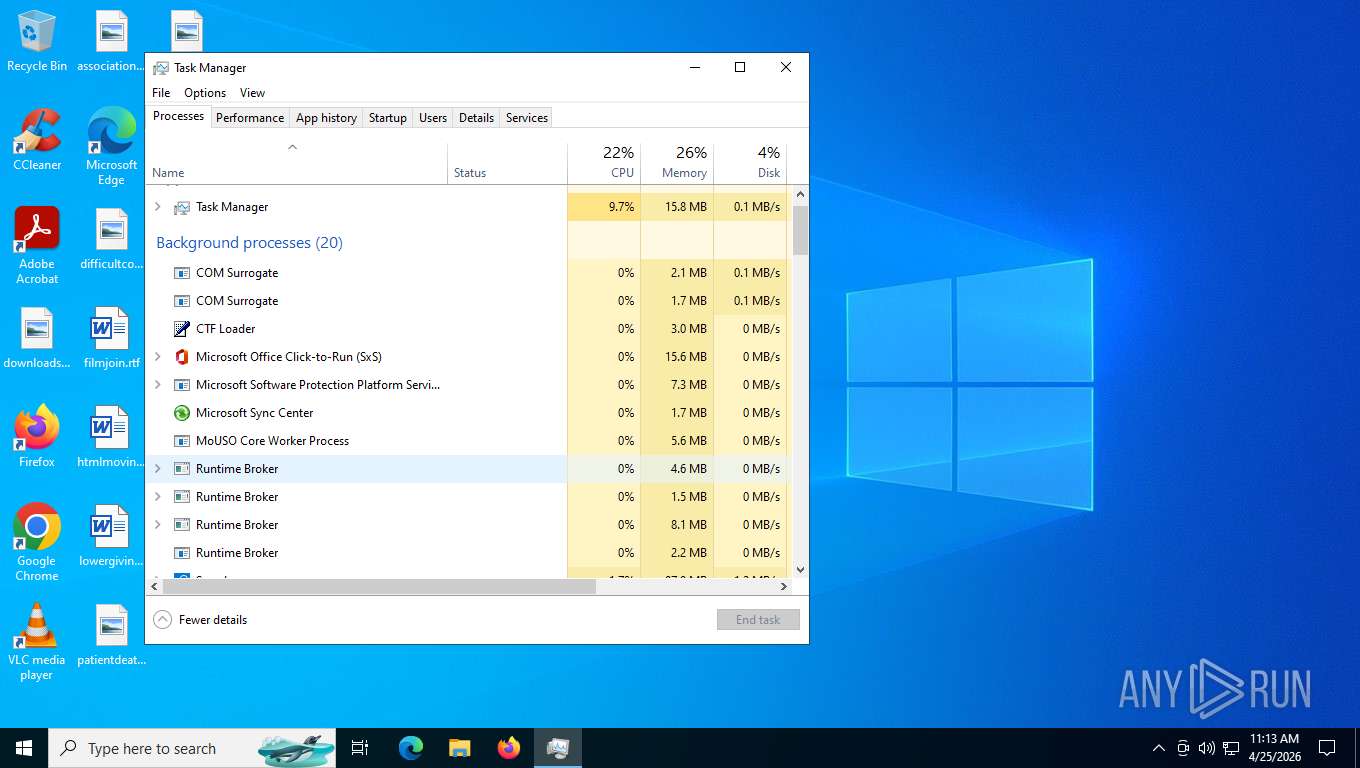
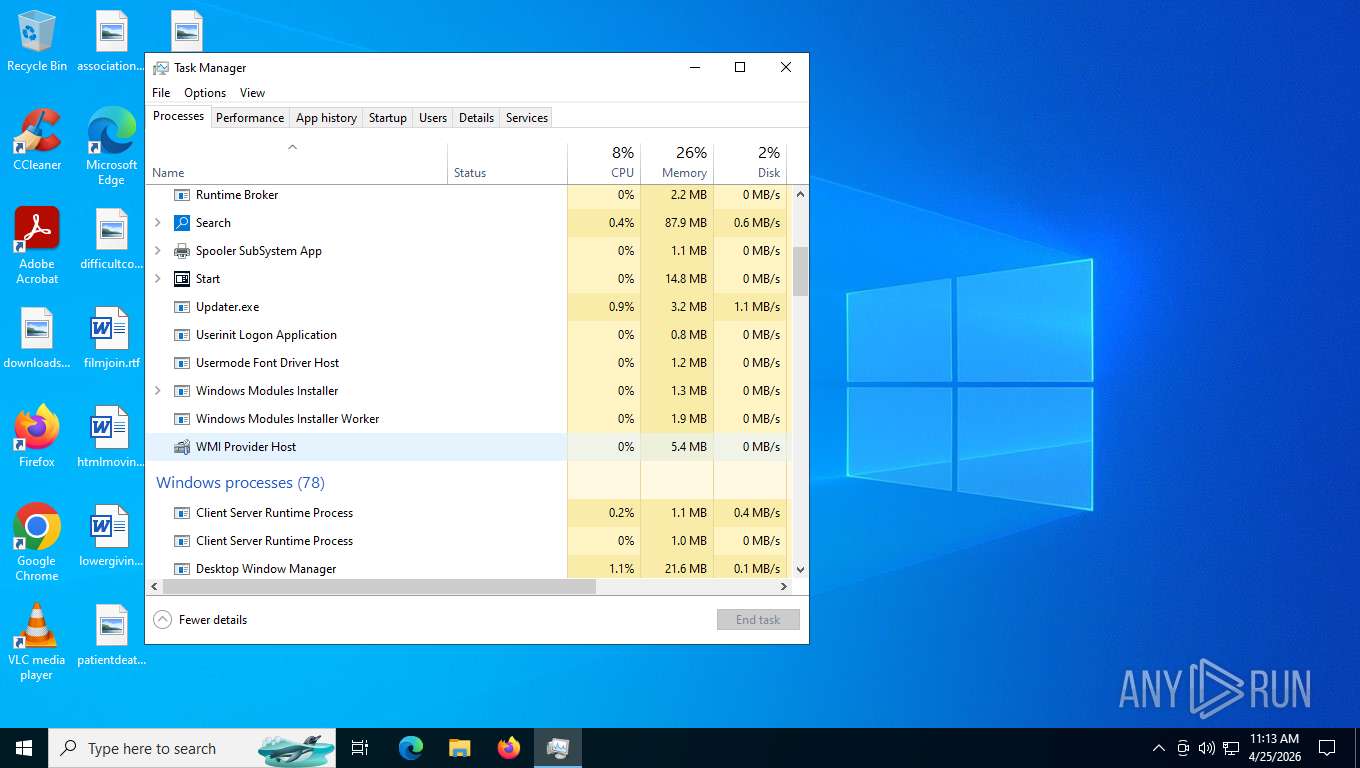
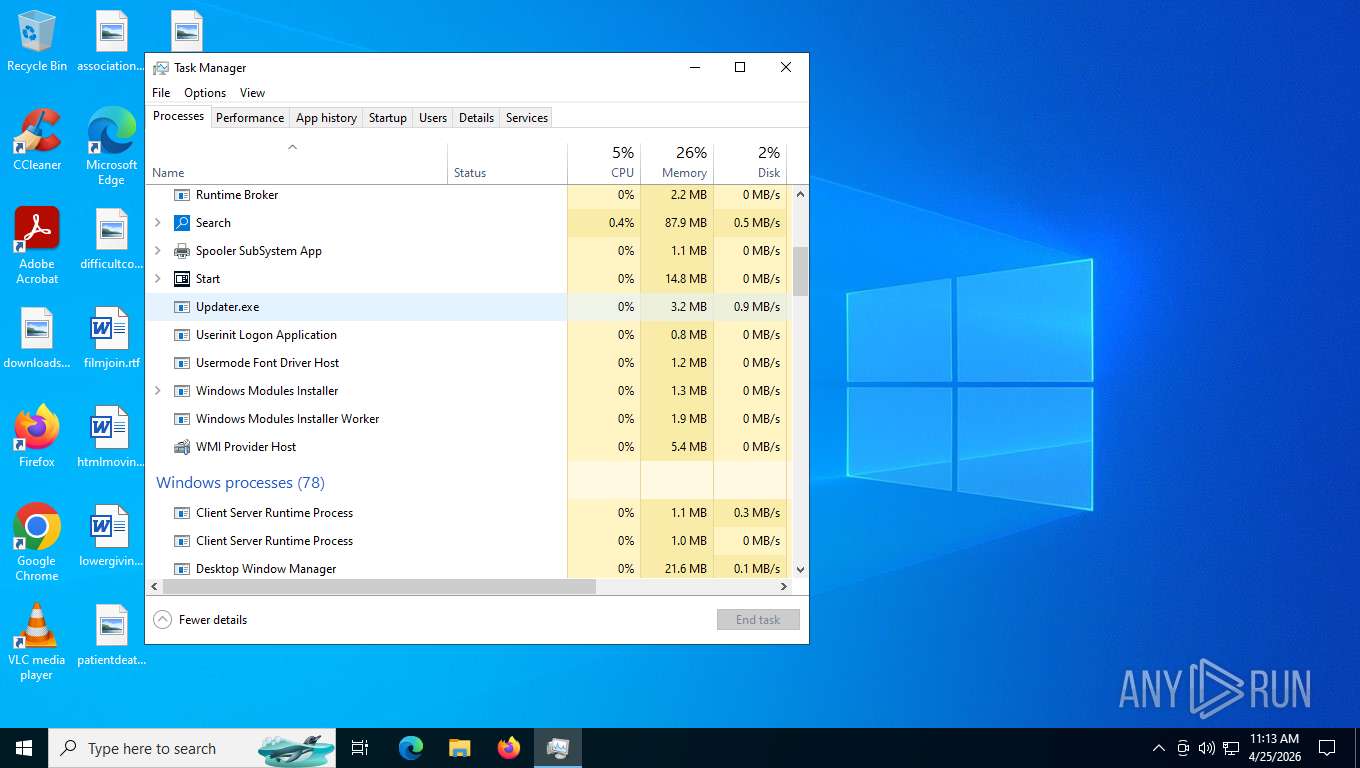
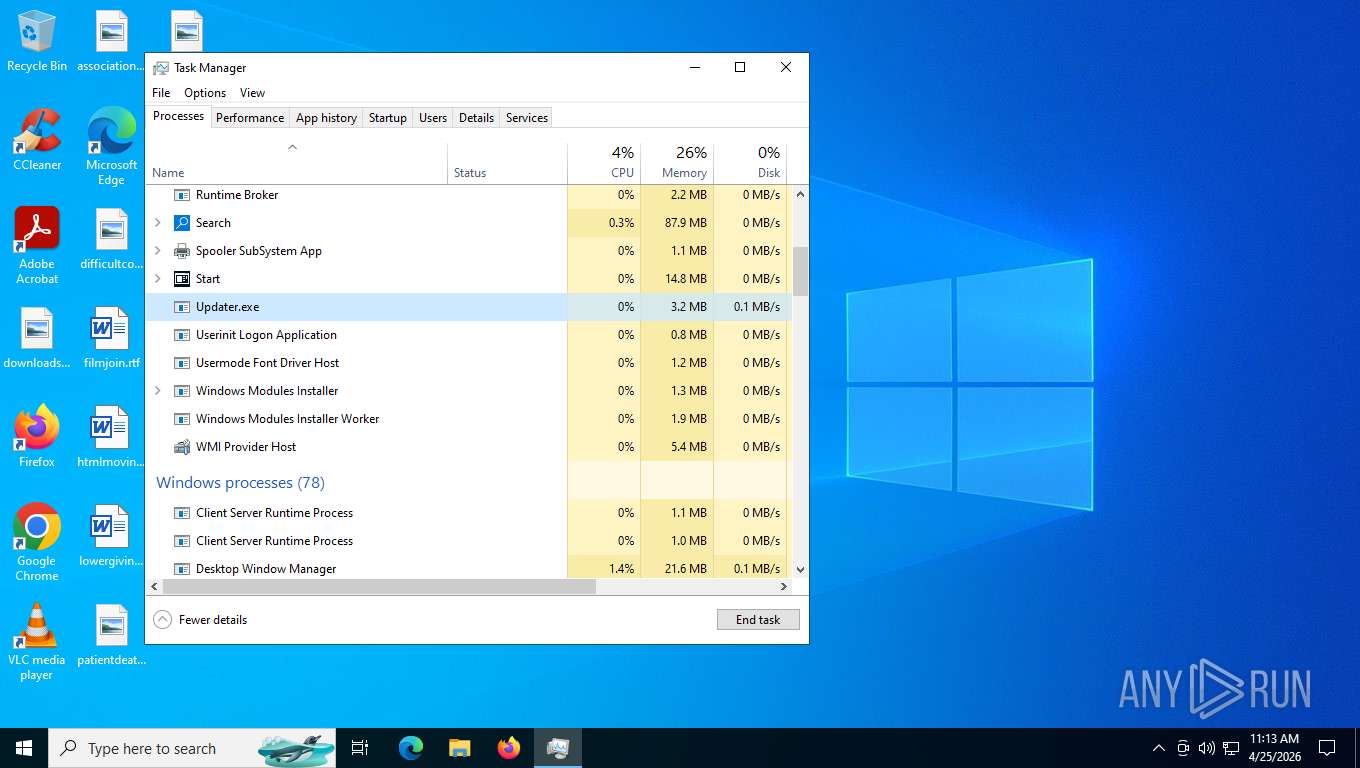
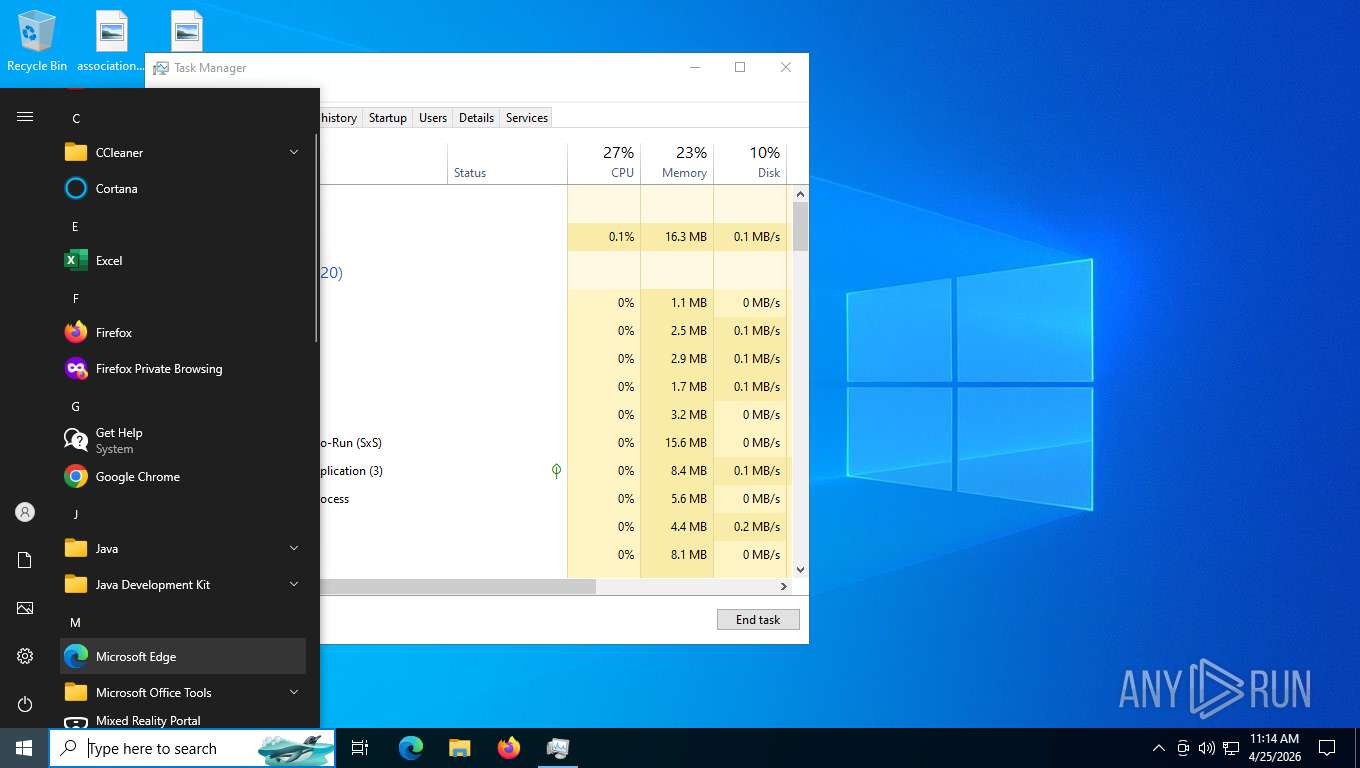
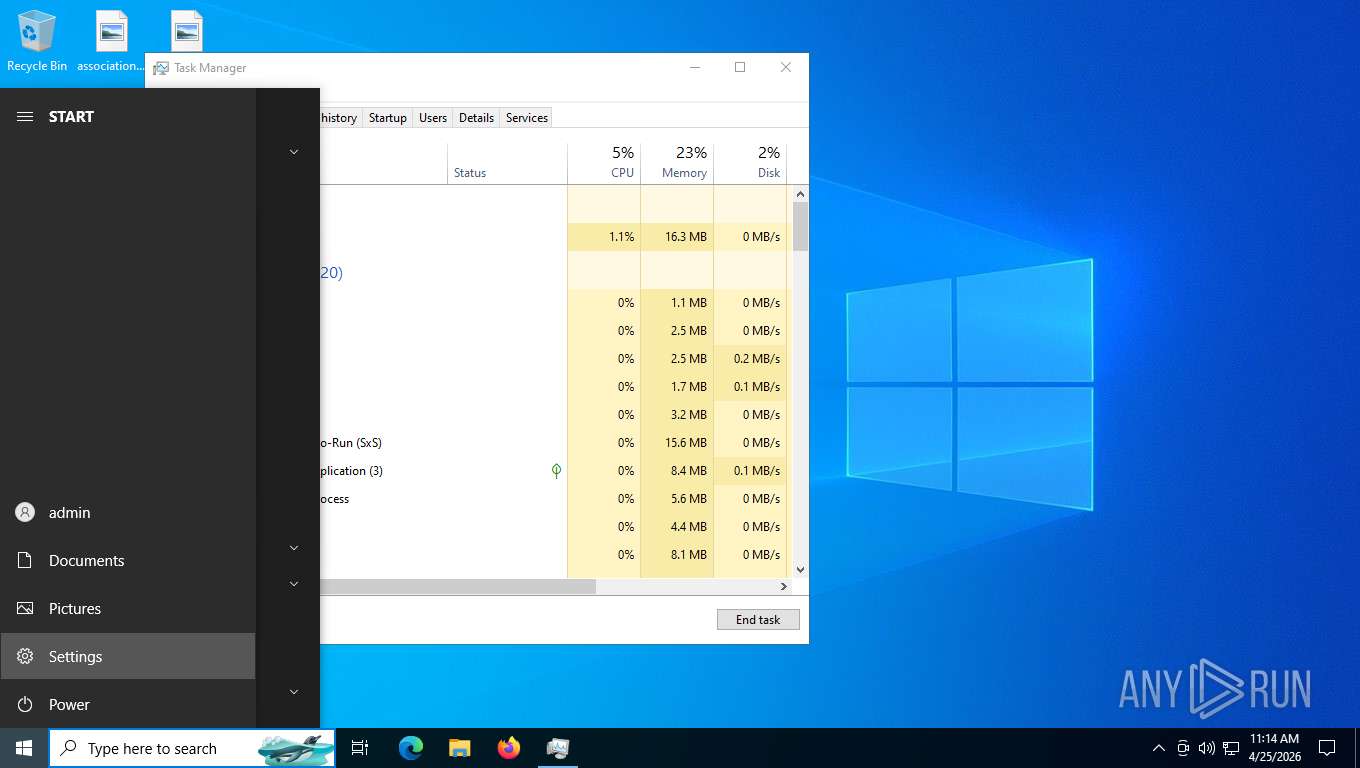
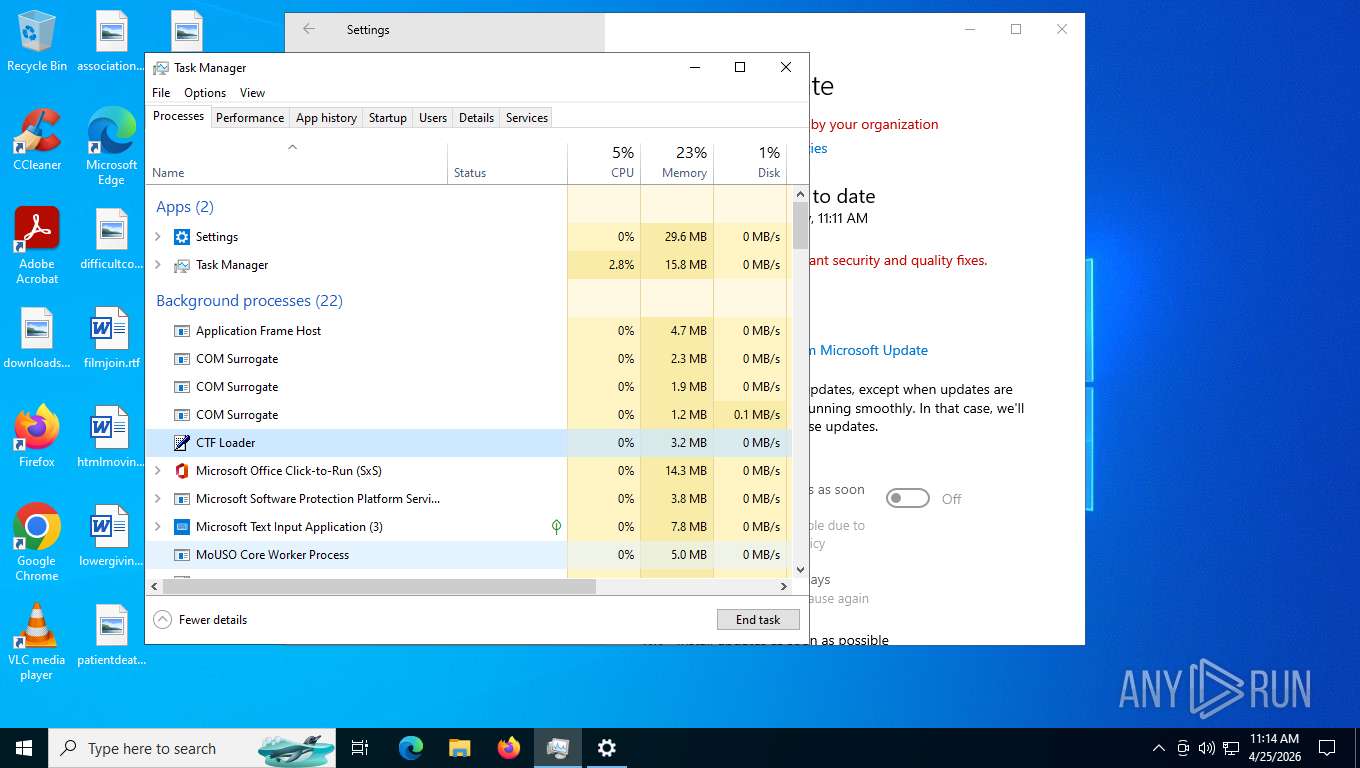
Manual execution by a user
- Updater.exe (PID: 6672)
- Taskmgr.exe (PID: 6460)
- Taskmgr.exe (PID: 6580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Processunknown
C2 (1)87.106.168.15:7004
Keys
AES<V74PV74PV74PV74PV74P>
Options
Splitter<Xwormmm>
Sleep time1
USB drop nameXWorm V7.4
Mutex4Q7xjgv2g6Lr4bFI
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, Description, RelativePath, WorkingDir, CommandArgs, IconFile, Unicode, ExpIcon |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2026:03:06 05:07:43+00:00 |
| AccessDate: | 2026:04:20 03:36:26+00:00 |
| ModifyDate: | 2026:04:16 03:52:10+00:00 |
| TargetFileSize: | 2366032 |
| IconIndex: | (none) |
| RunWindow: | Normal |
| HotKey: | (none) |
| TargetFileDOSName: | MSEDGE~1.EXE |
| DriveType: | Fixed Disk |
| DriveSerialNumber: | 3C41-F1BA |
| VolumeLabel: | Windows 11 |
| LocalBasePath: | C:\Program Files (x86)\Microsoft\Edge\Application\msedge_proxy.exe |
| Description: | This is a browser based clone of the windows with some new design choices. |
| RelativePath: | ..\..\..\..\Program Files (x86)\Microsoft\Edge\Application\msedge_proxy.exe |
| WorkingDirectory: | C:\Program Files (x86)\Microsoft\Edge\Application |
| CommandLineArguments: | --profile-directory=Default --app-id=heapafghjcojljadpkdnfjkifkmfjjdl --app-url=https://windows-12-web.vercel.app/index.html --app-launch-source=4 |
| IconFileName: | C:\Users\marte\AppData\Local\Microsoft\Edge\User Data\Default\Web Applications\_crx__heapafghjcojljadpkdnfjkifkmfjjdl\Windows 12.ico |
| MachineID: | masonsmgpc |
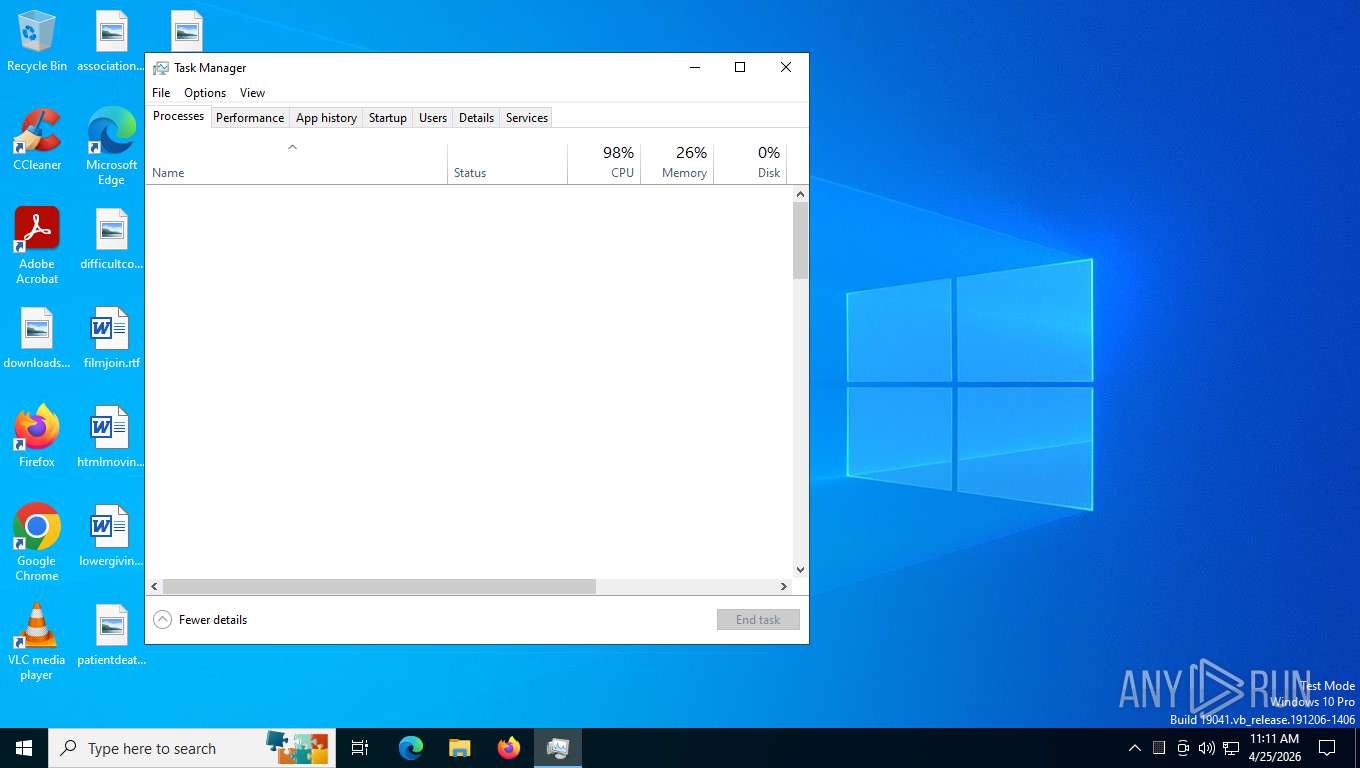
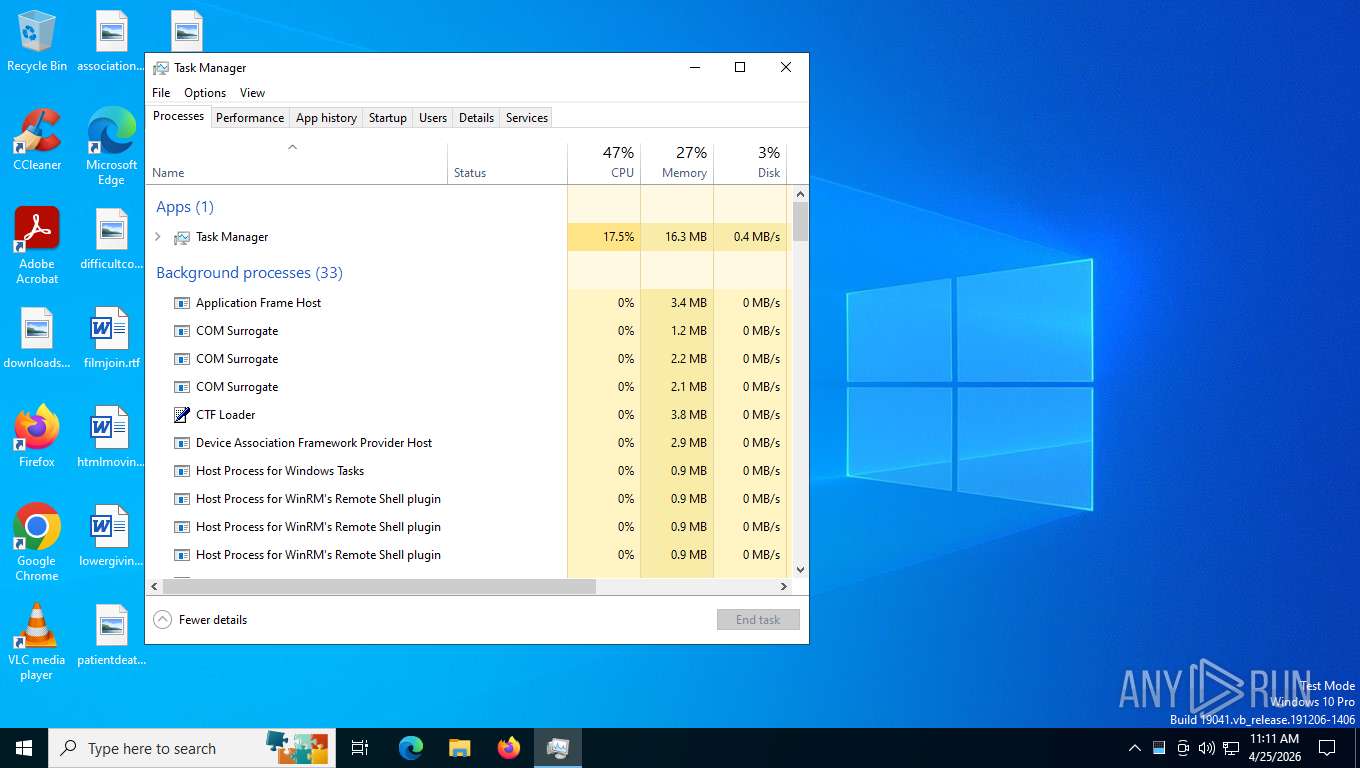
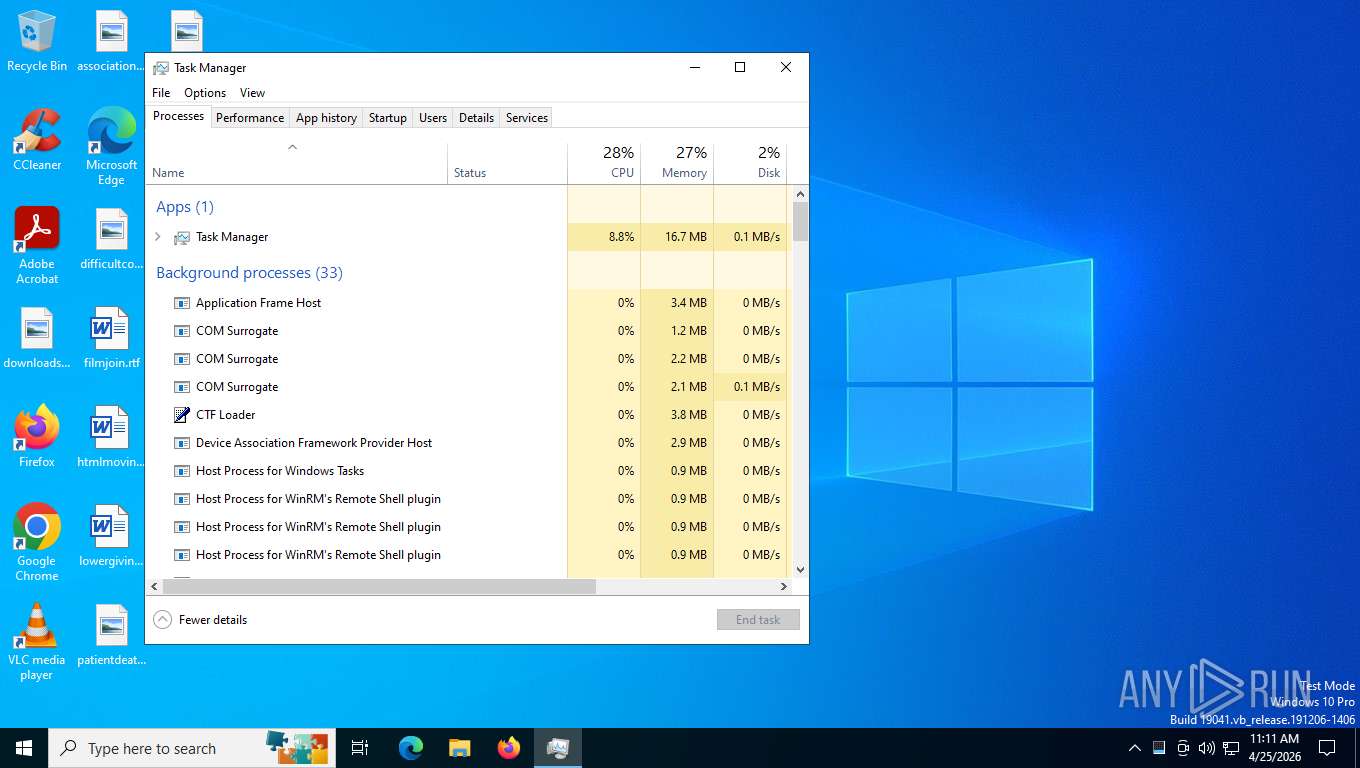
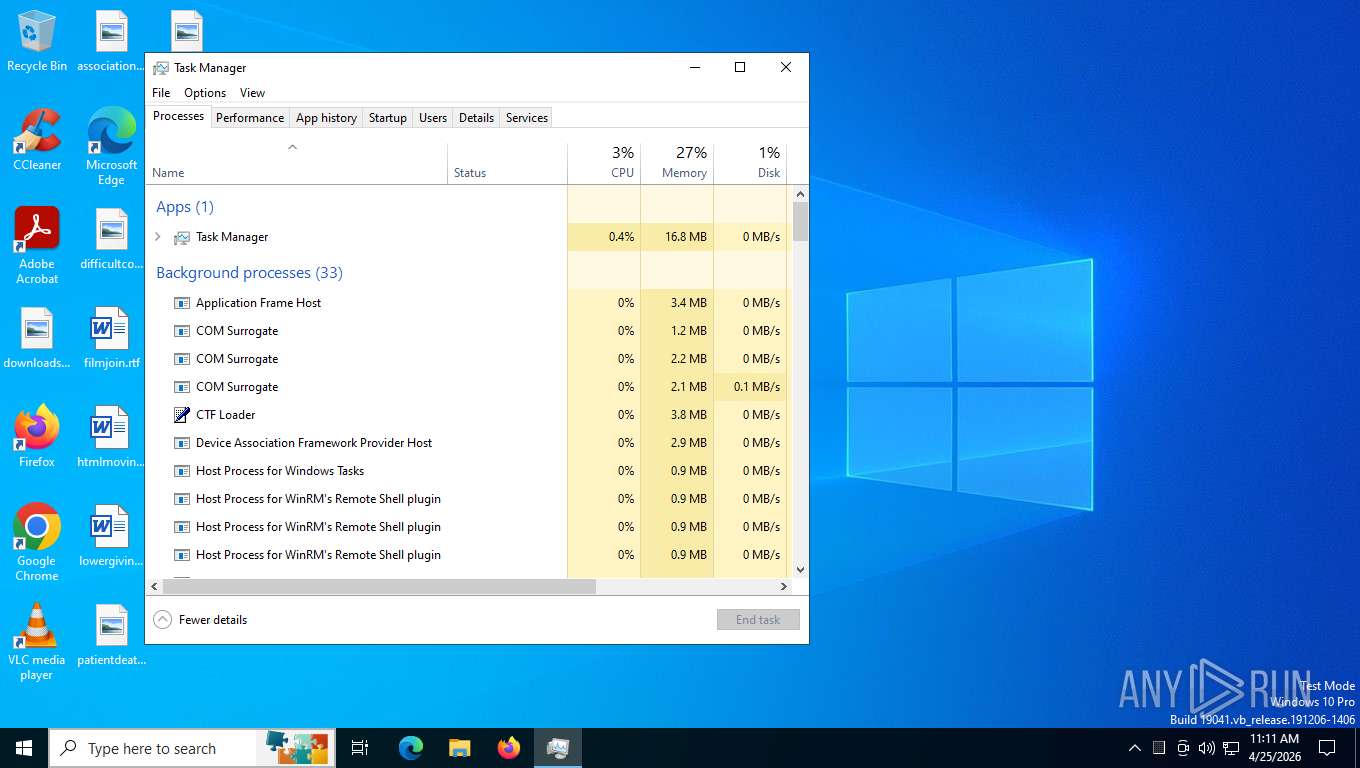
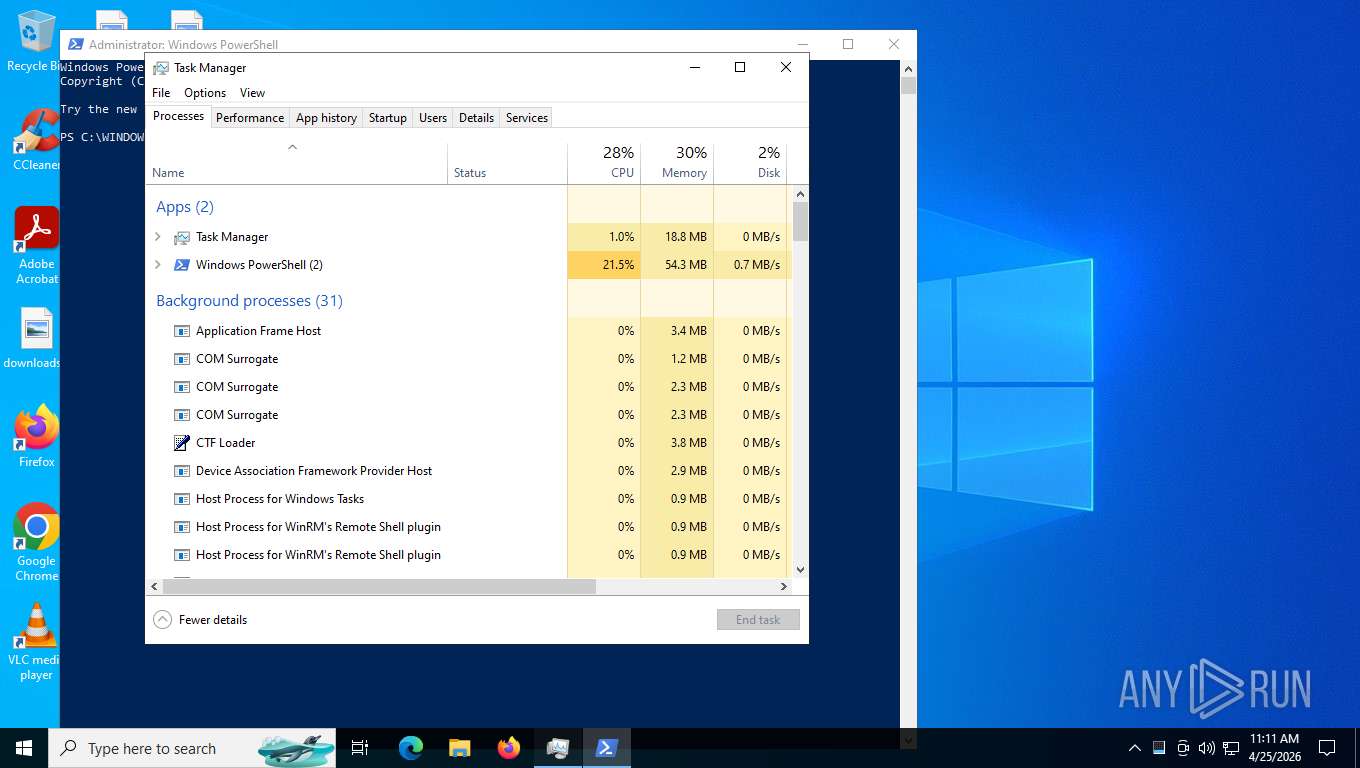
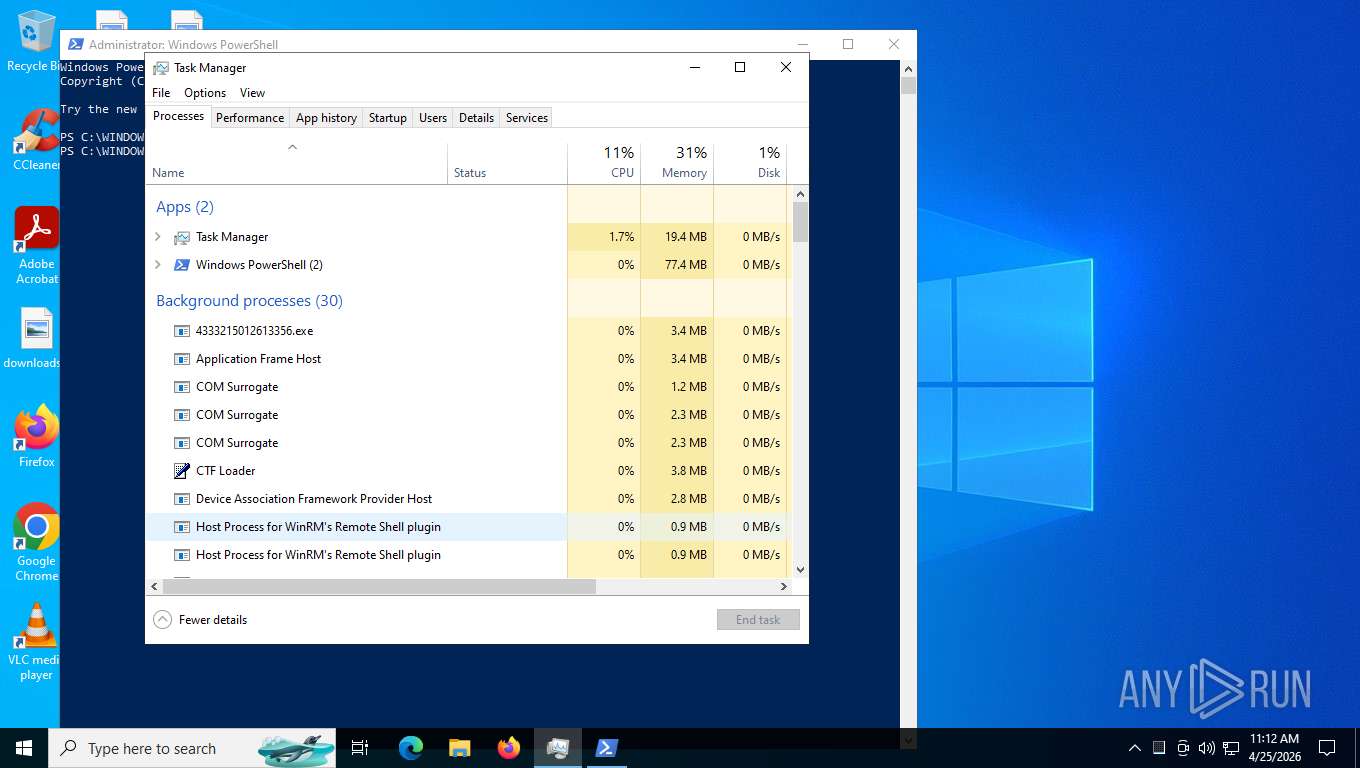
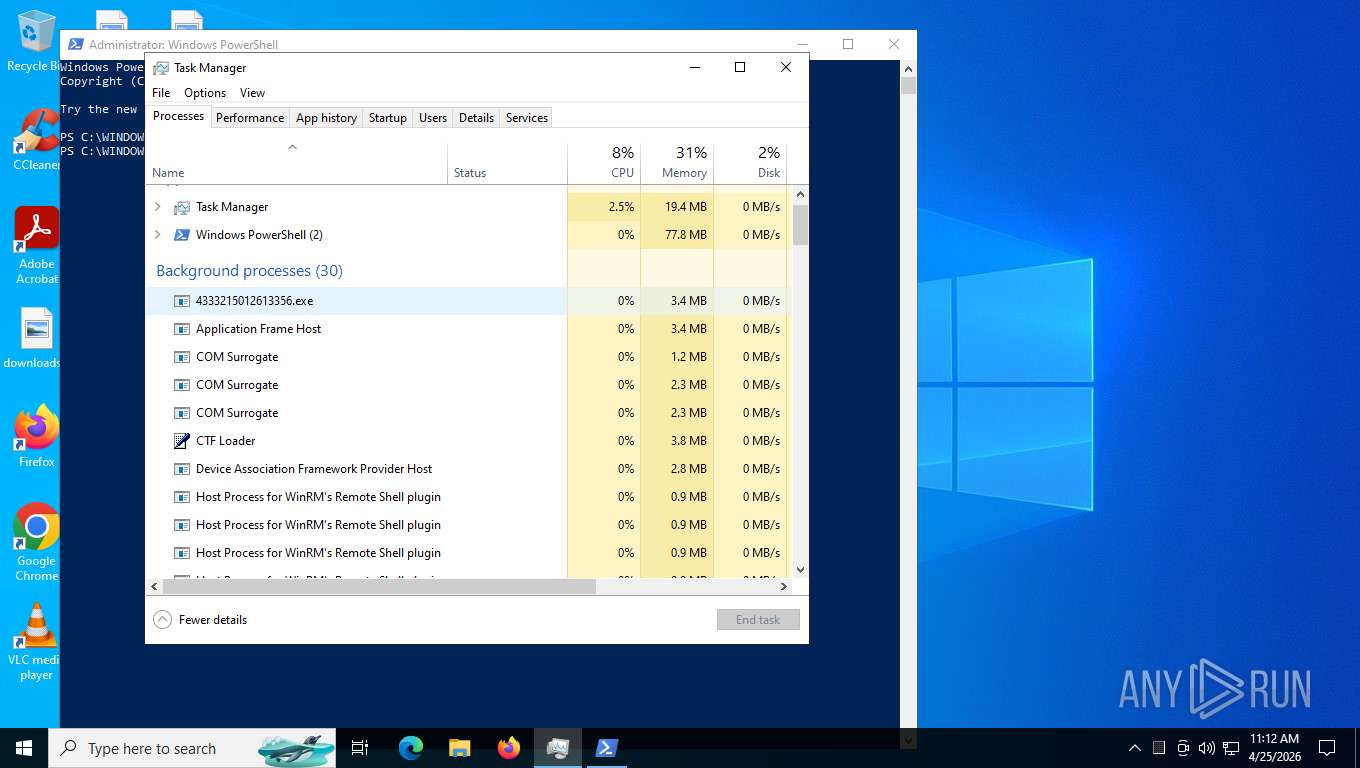
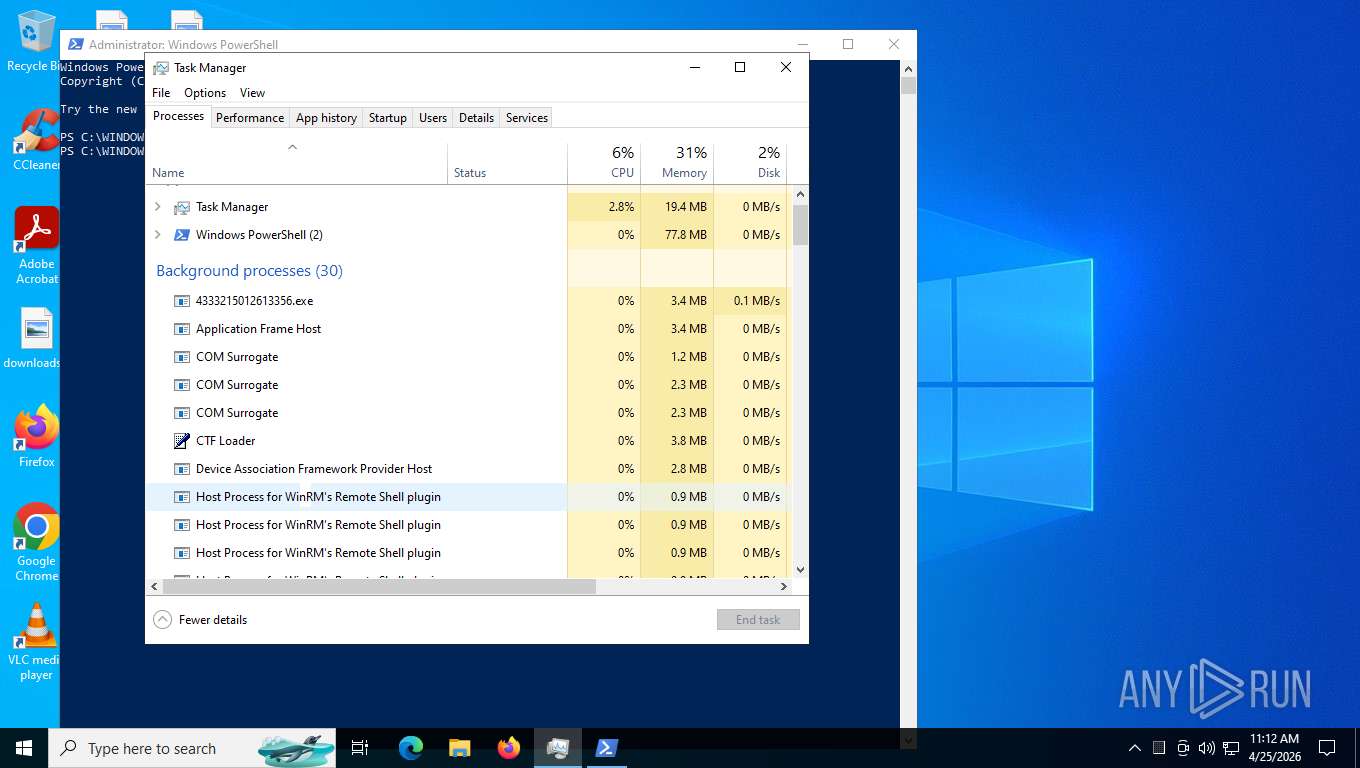
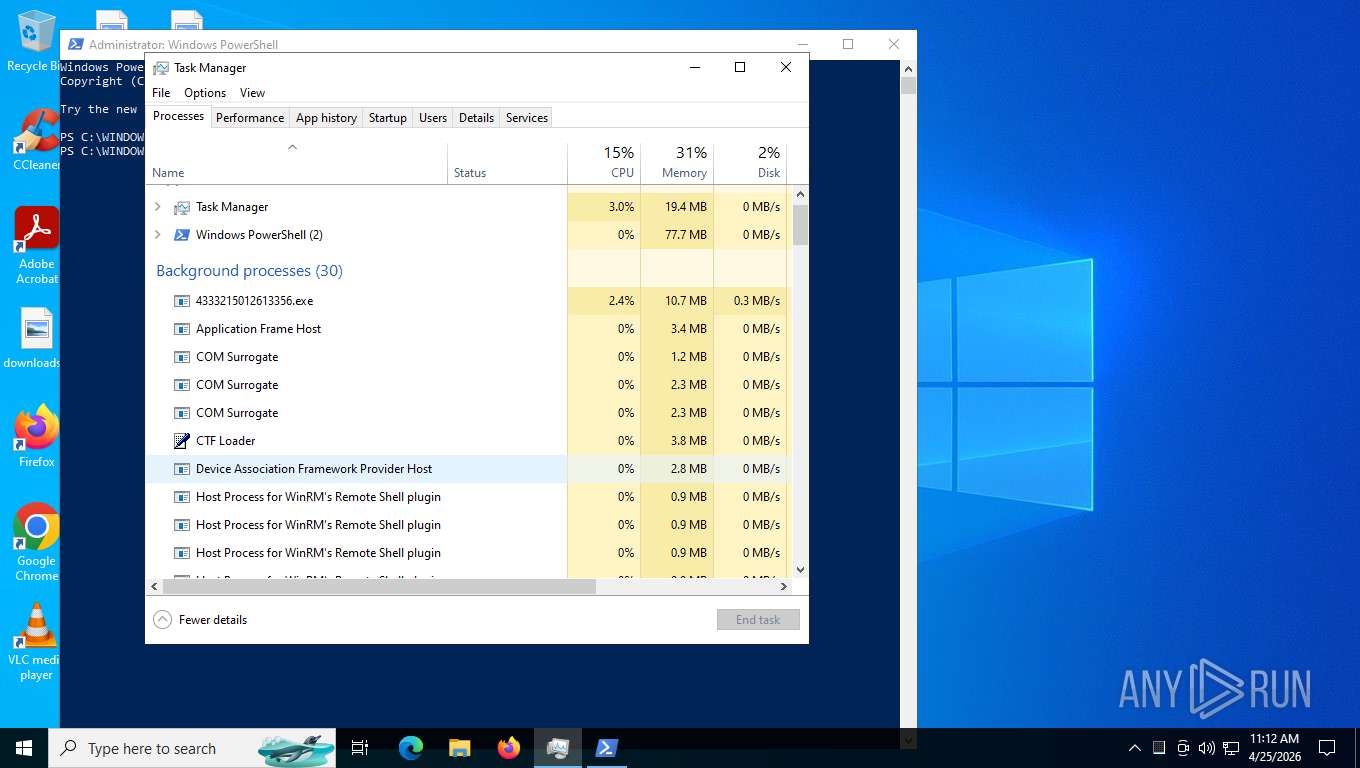
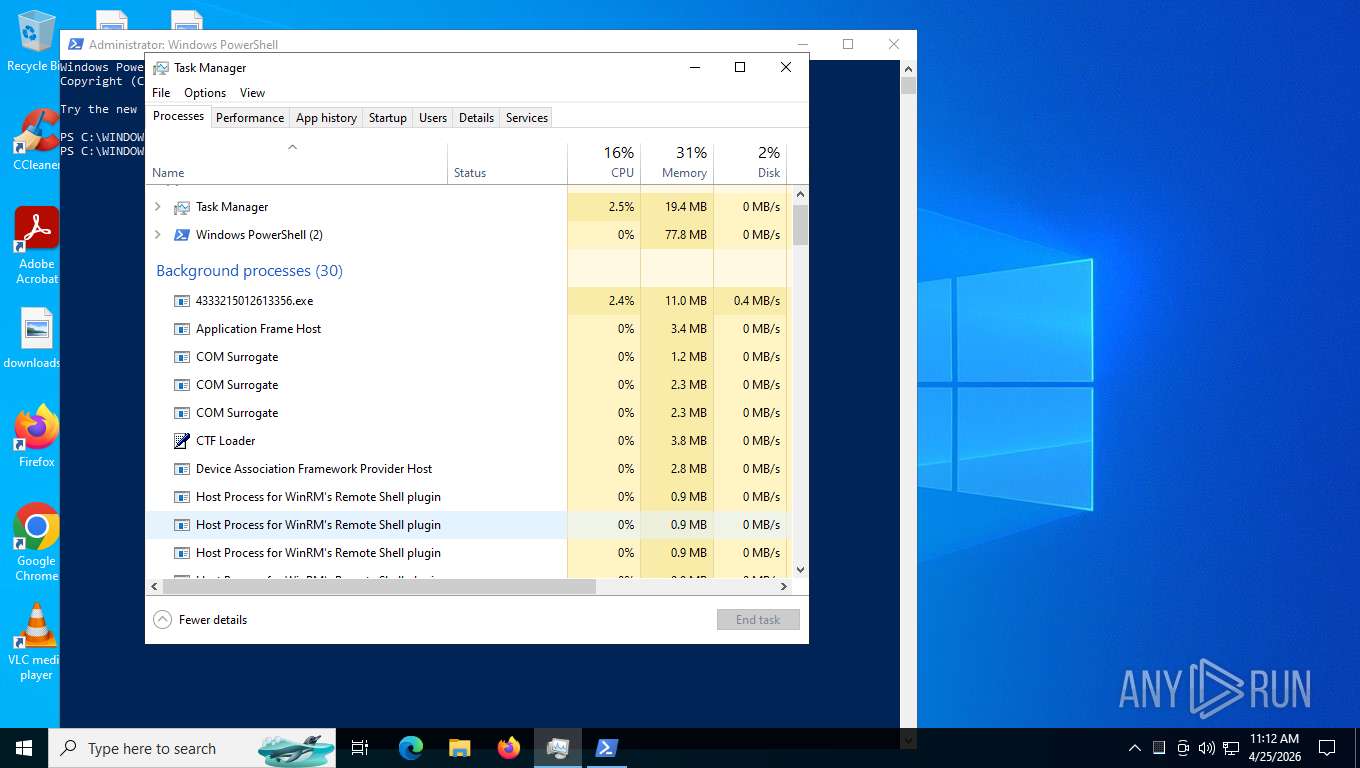
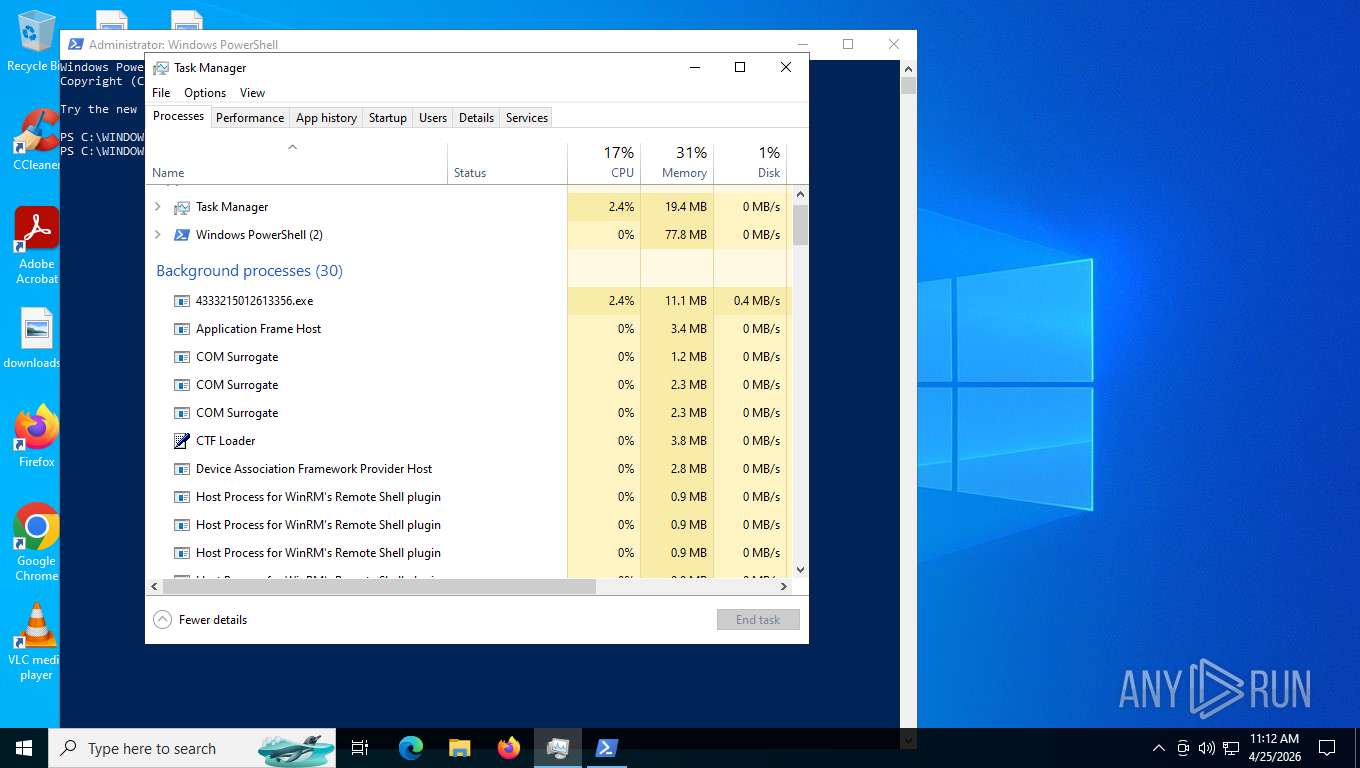
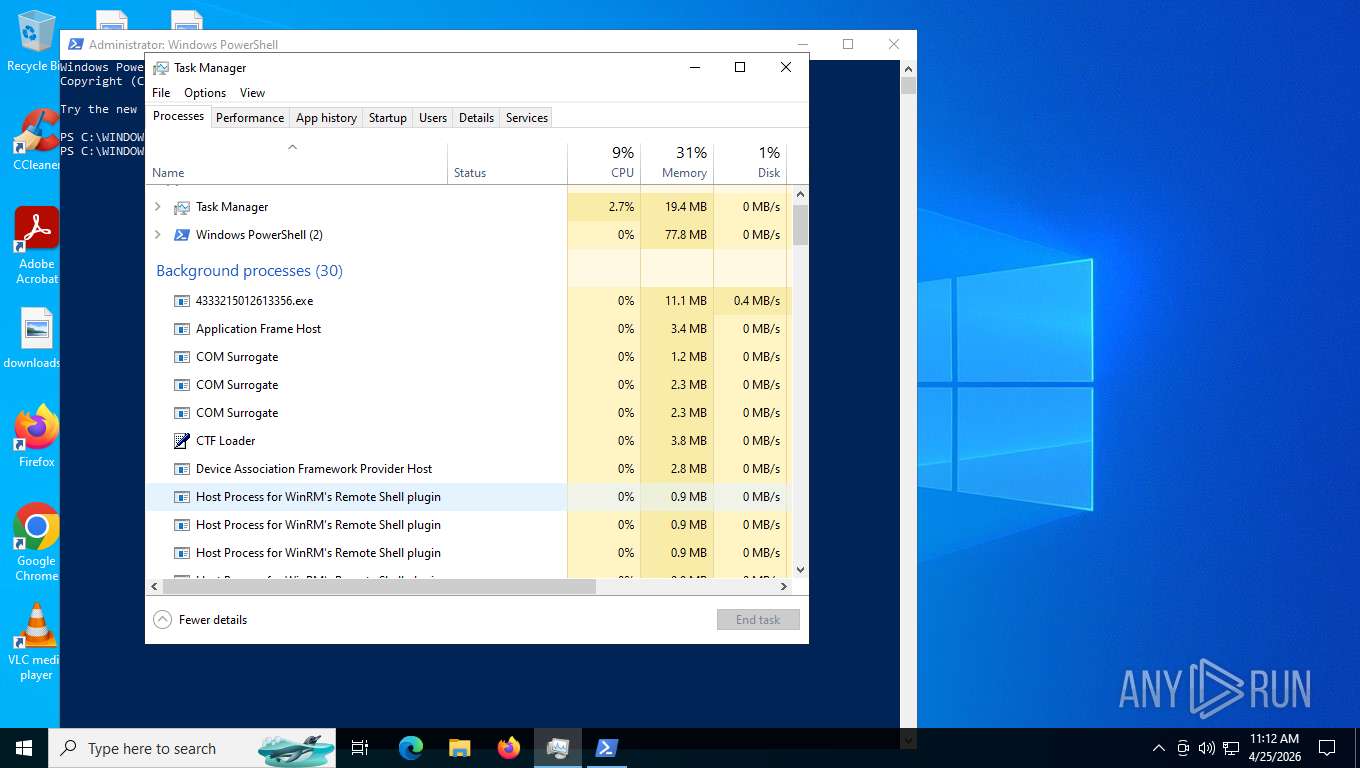
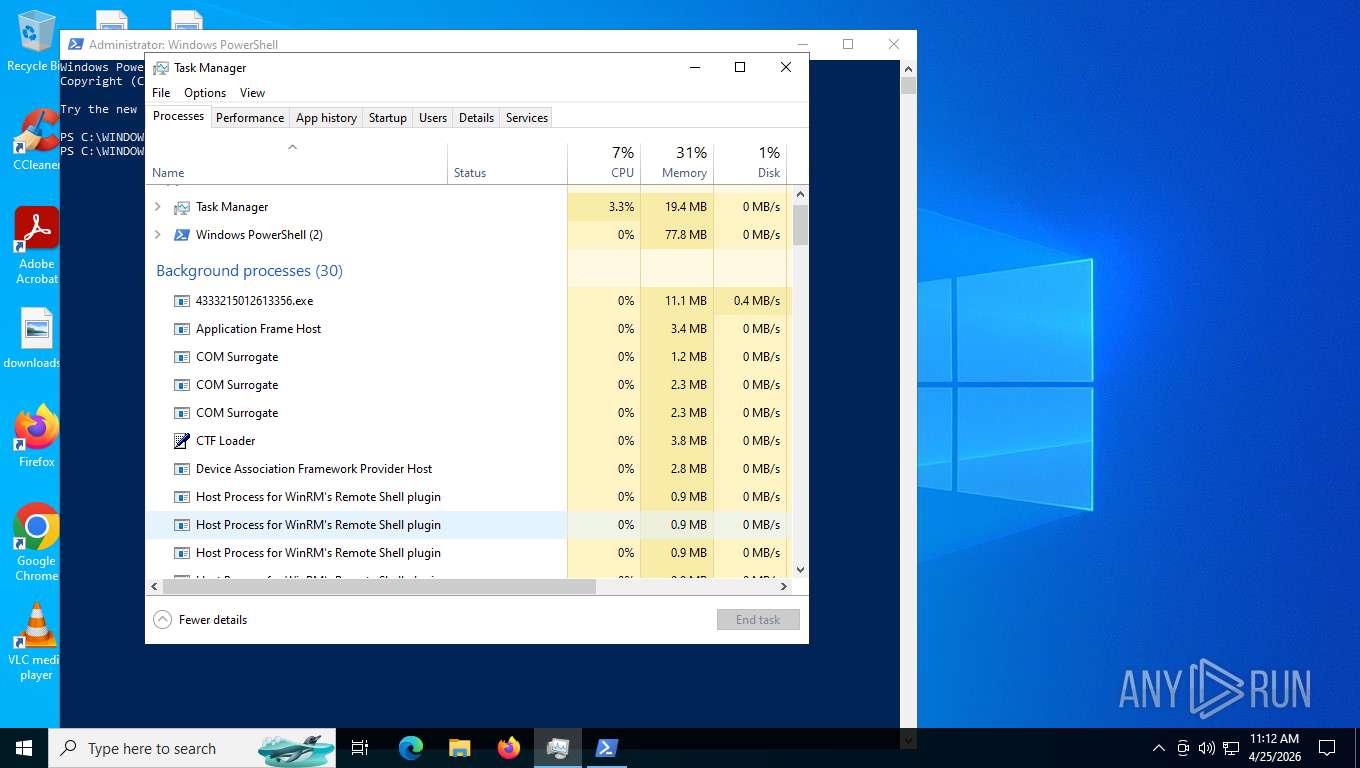
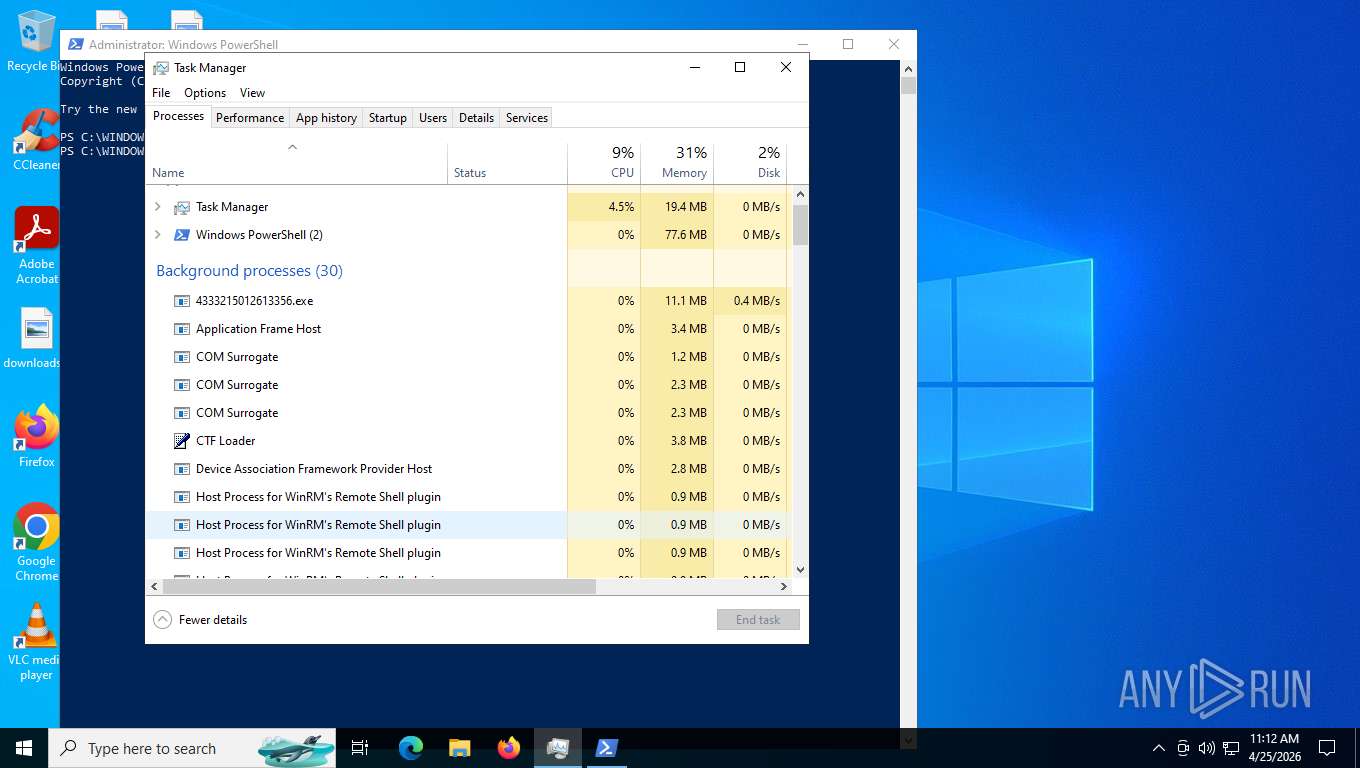
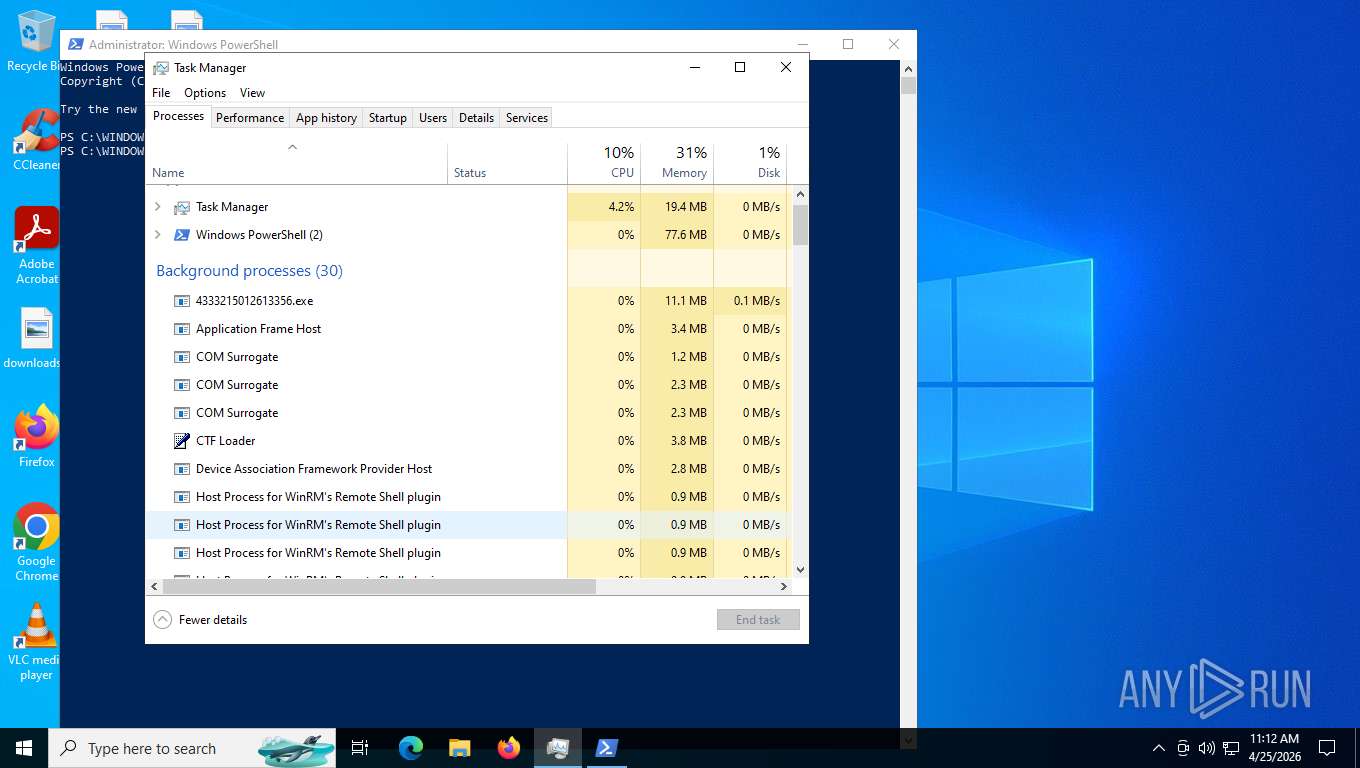
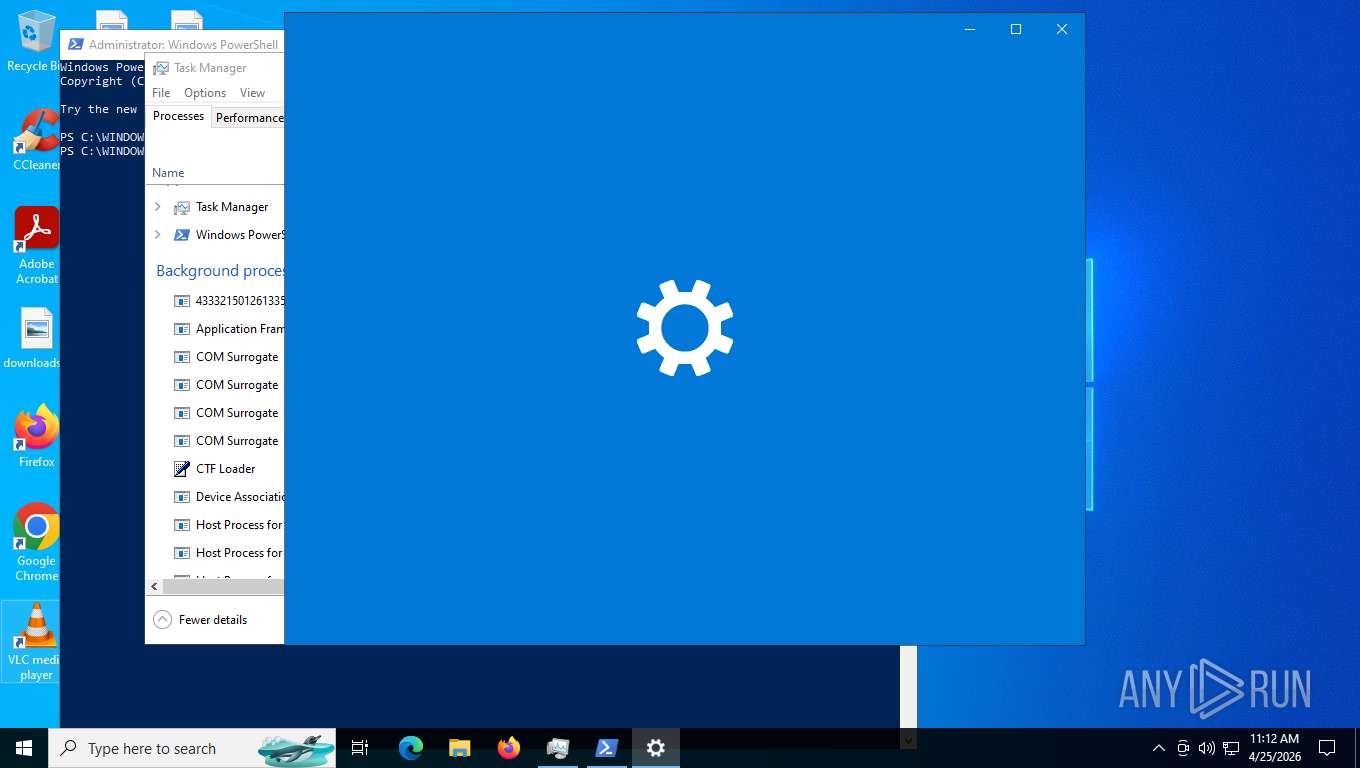
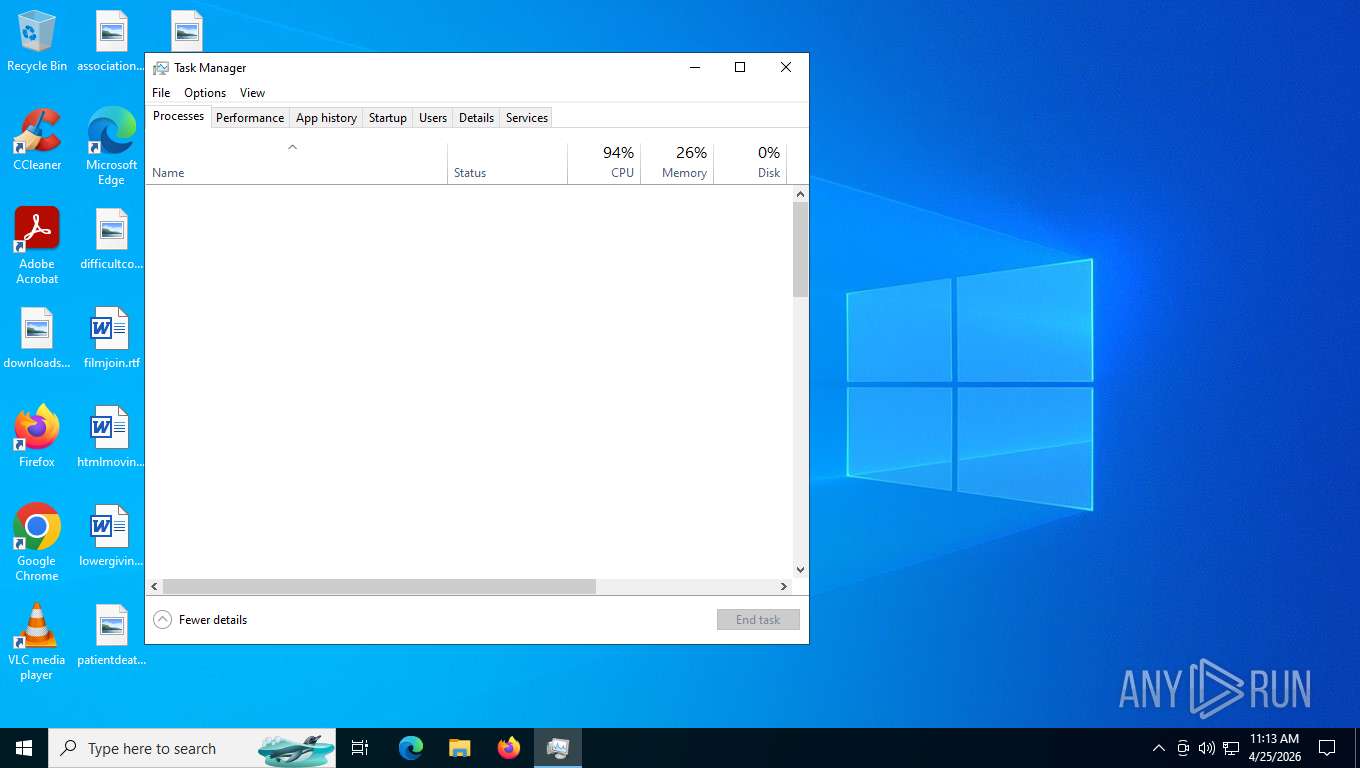
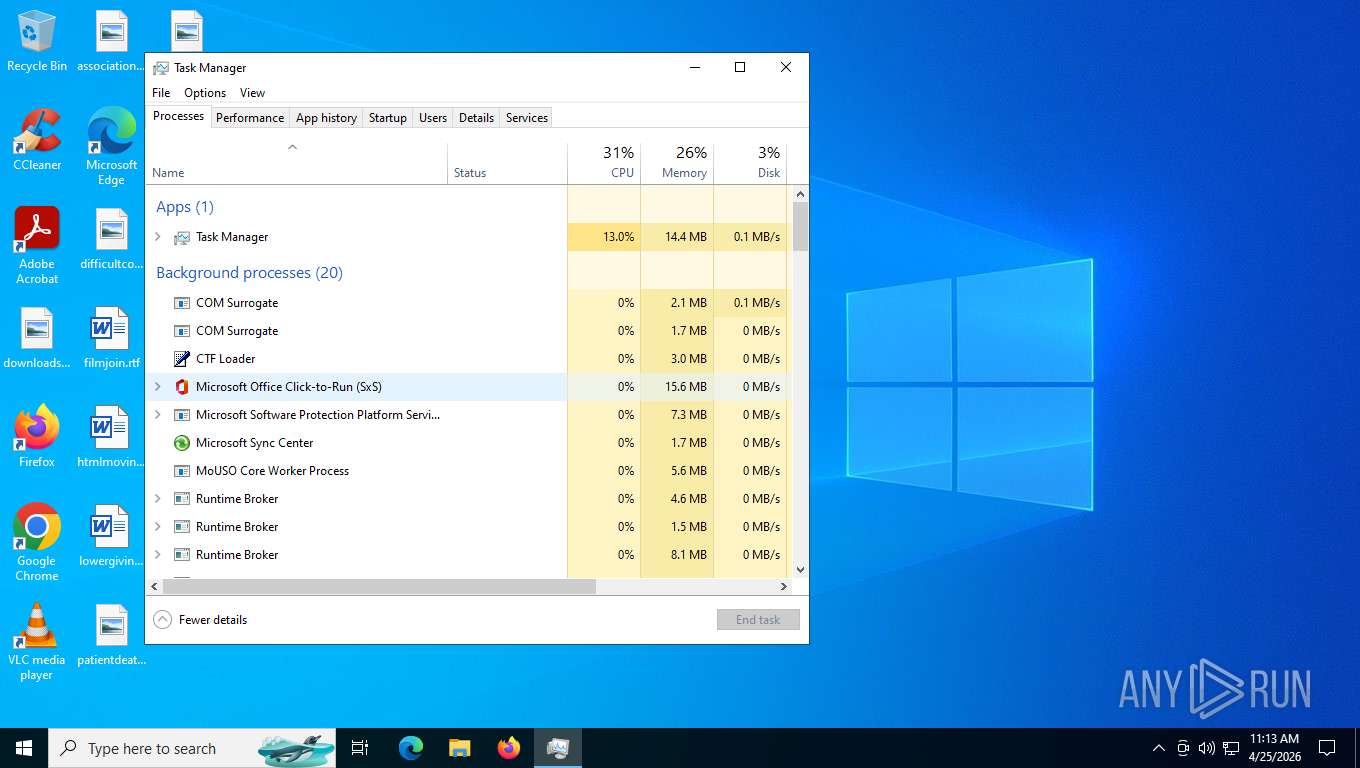
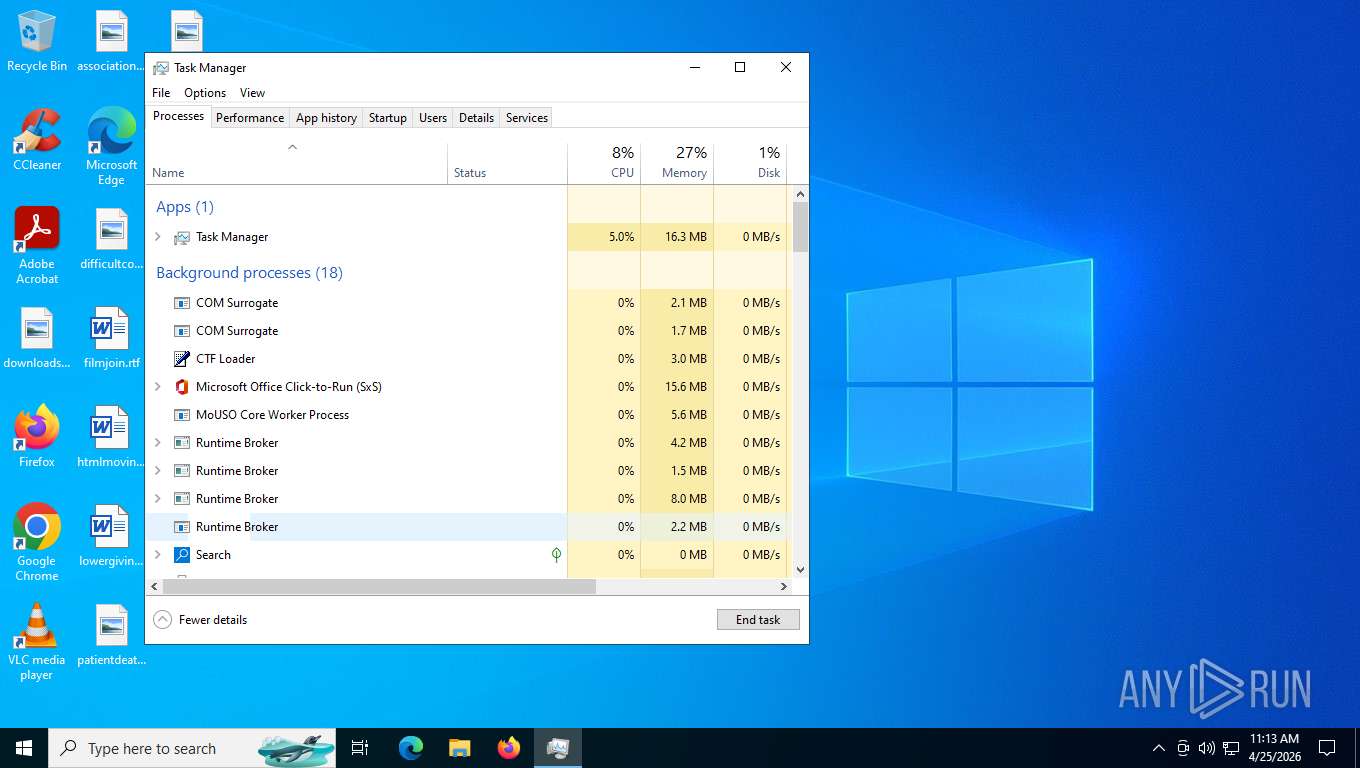
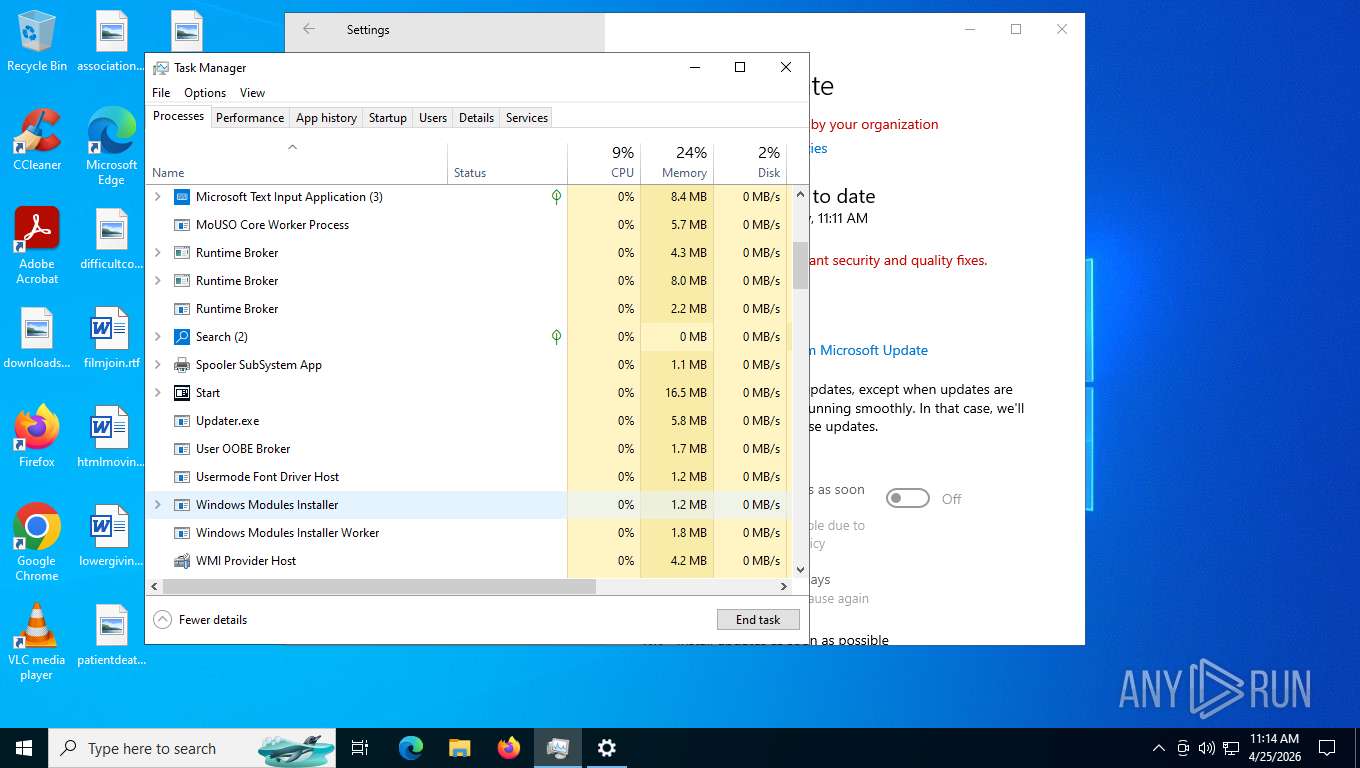
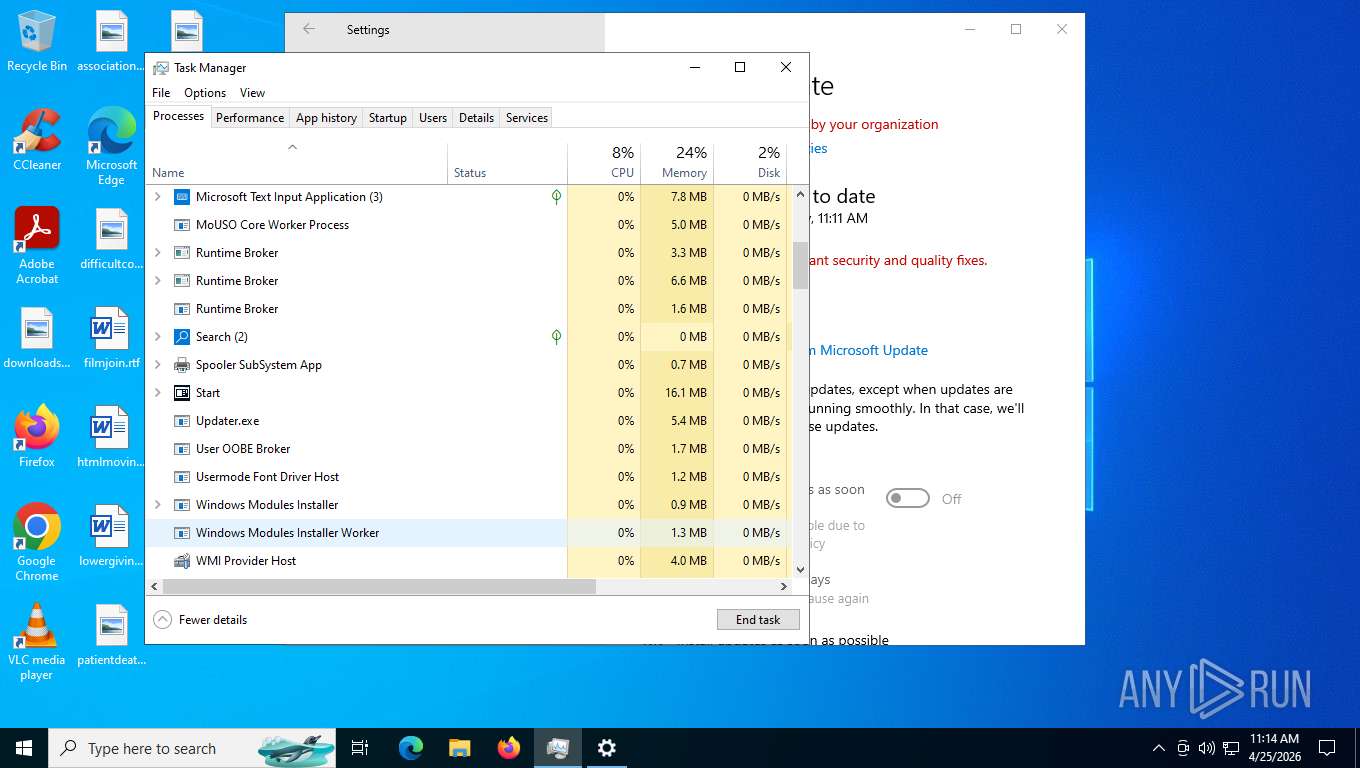
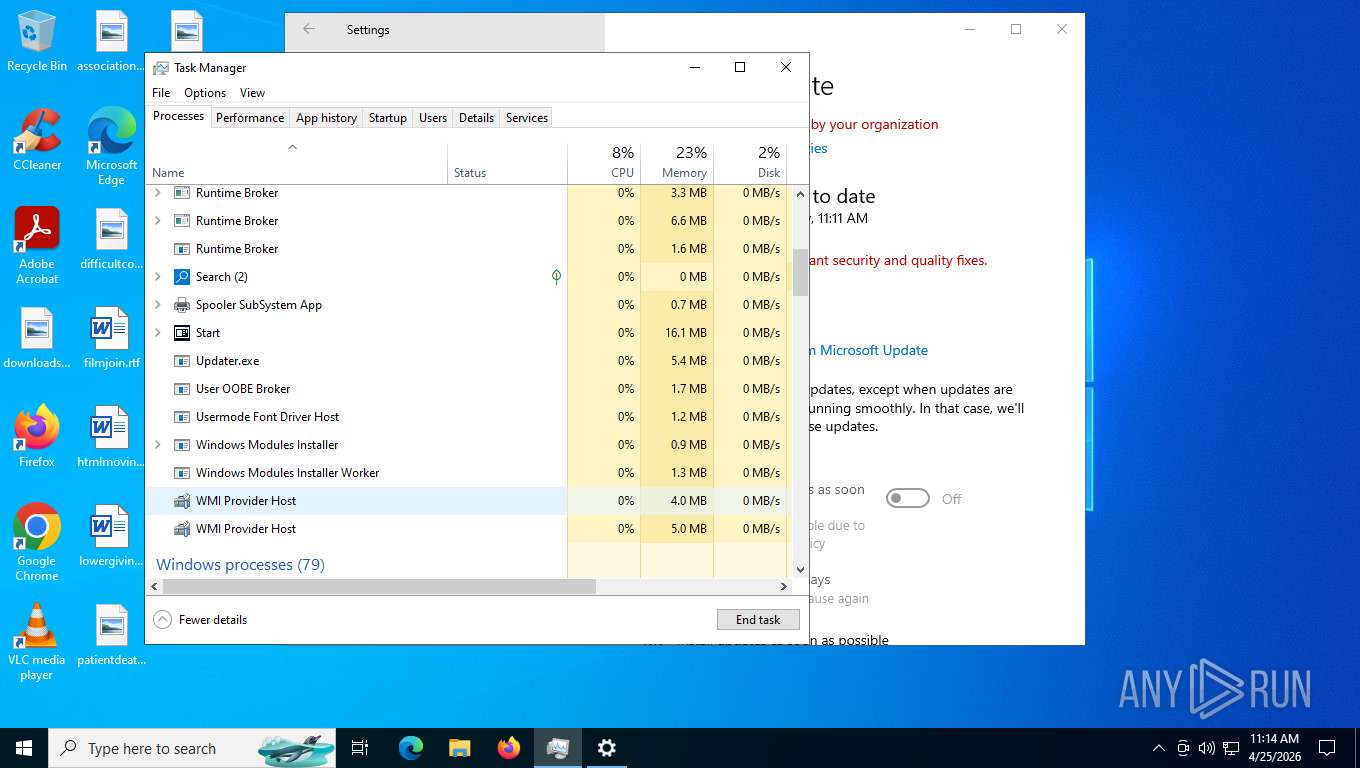
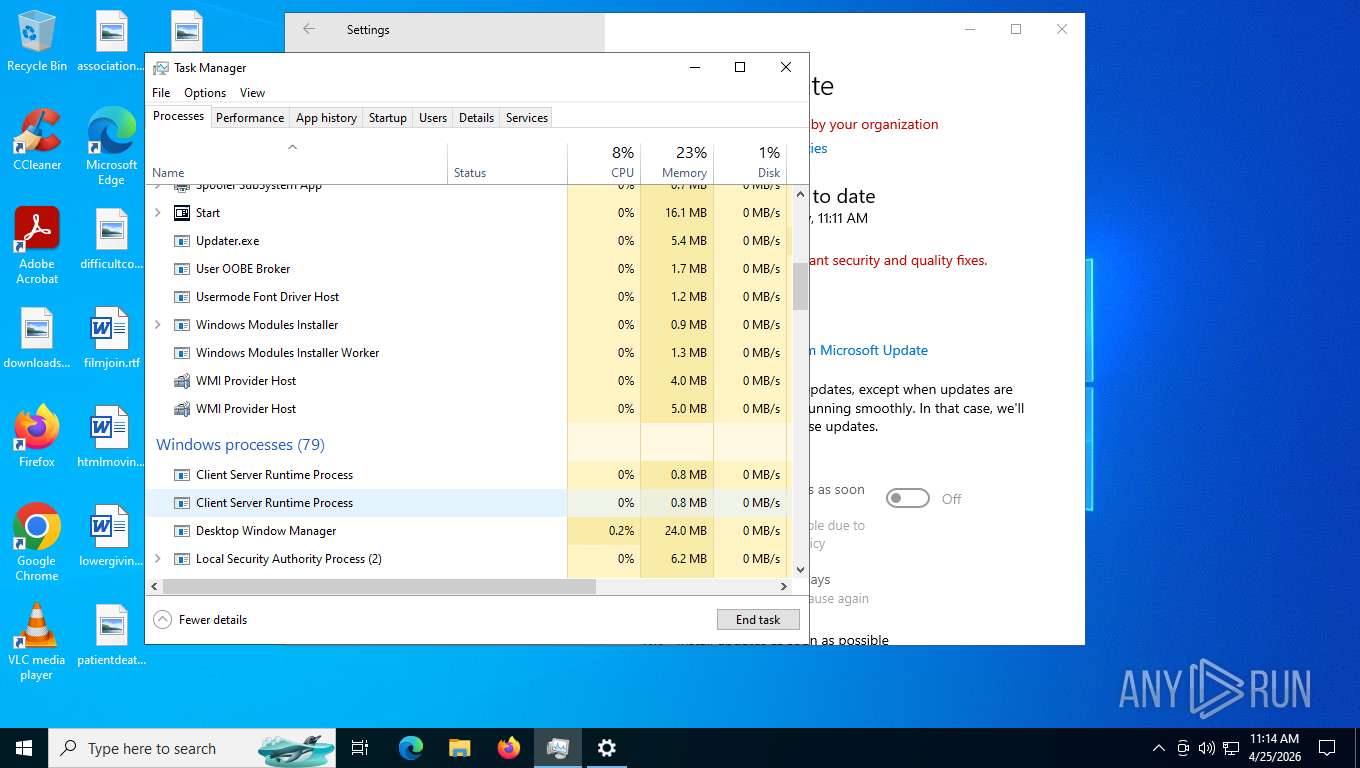
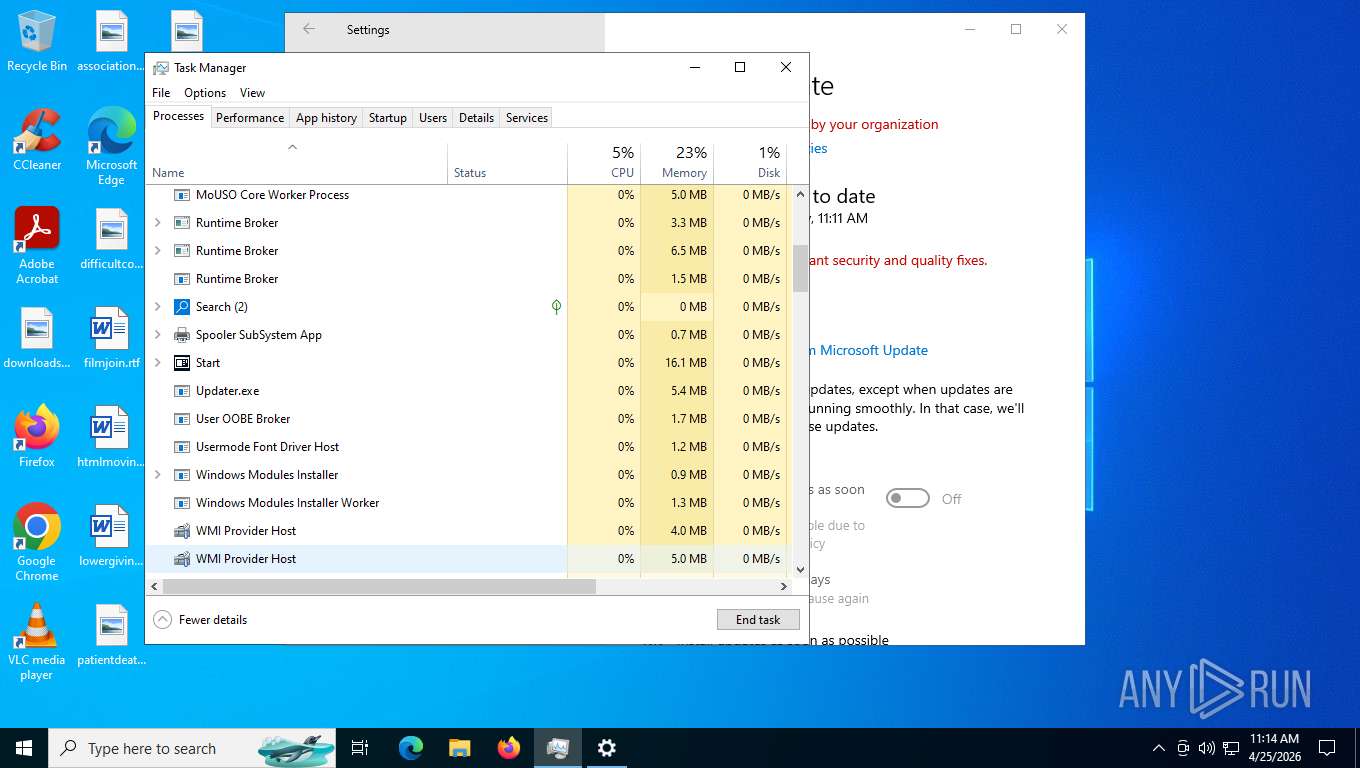
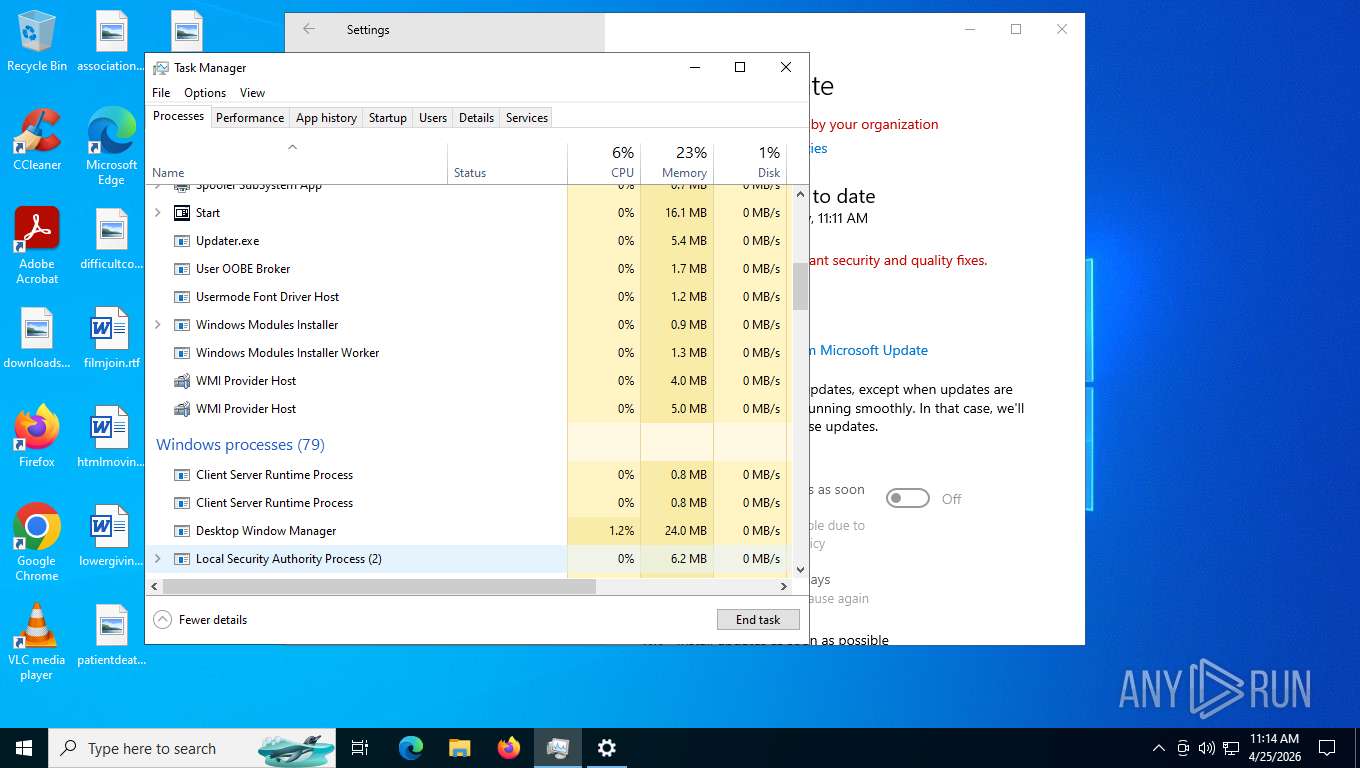
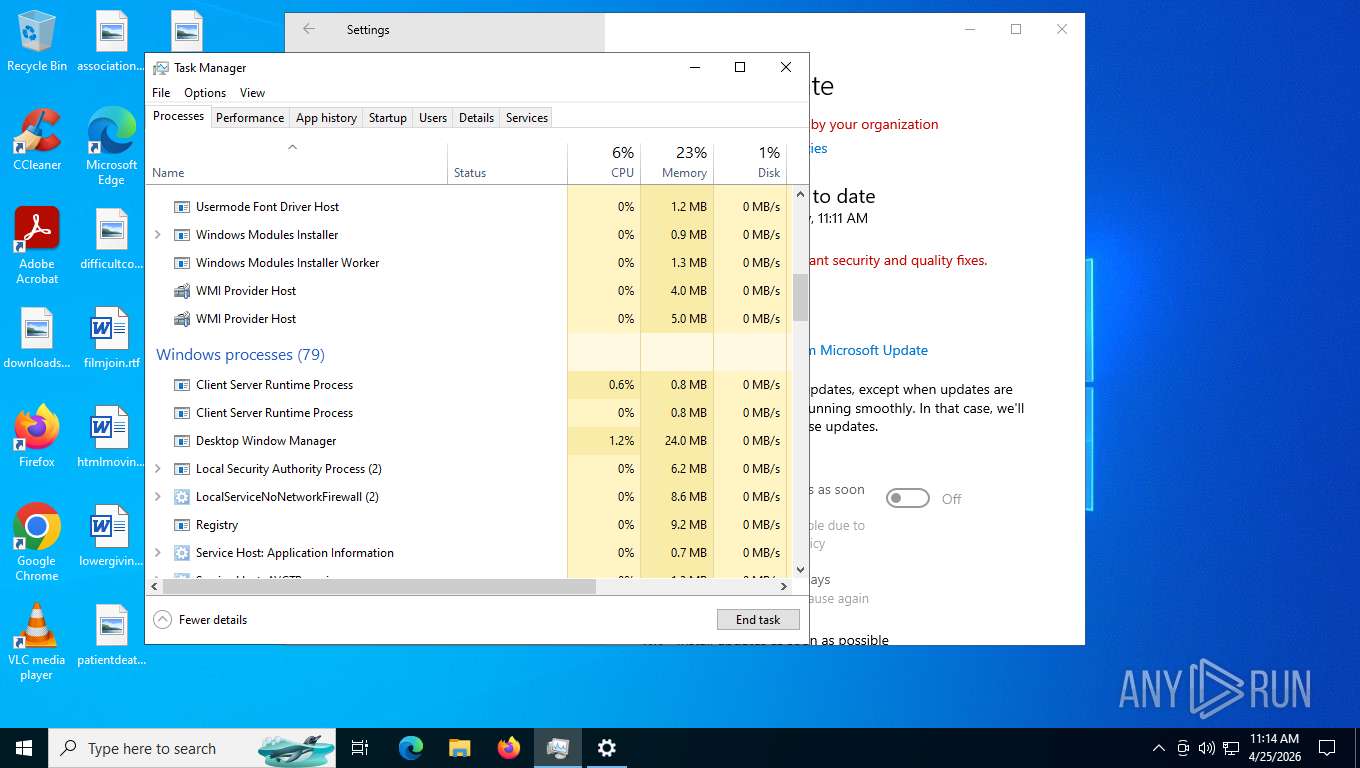
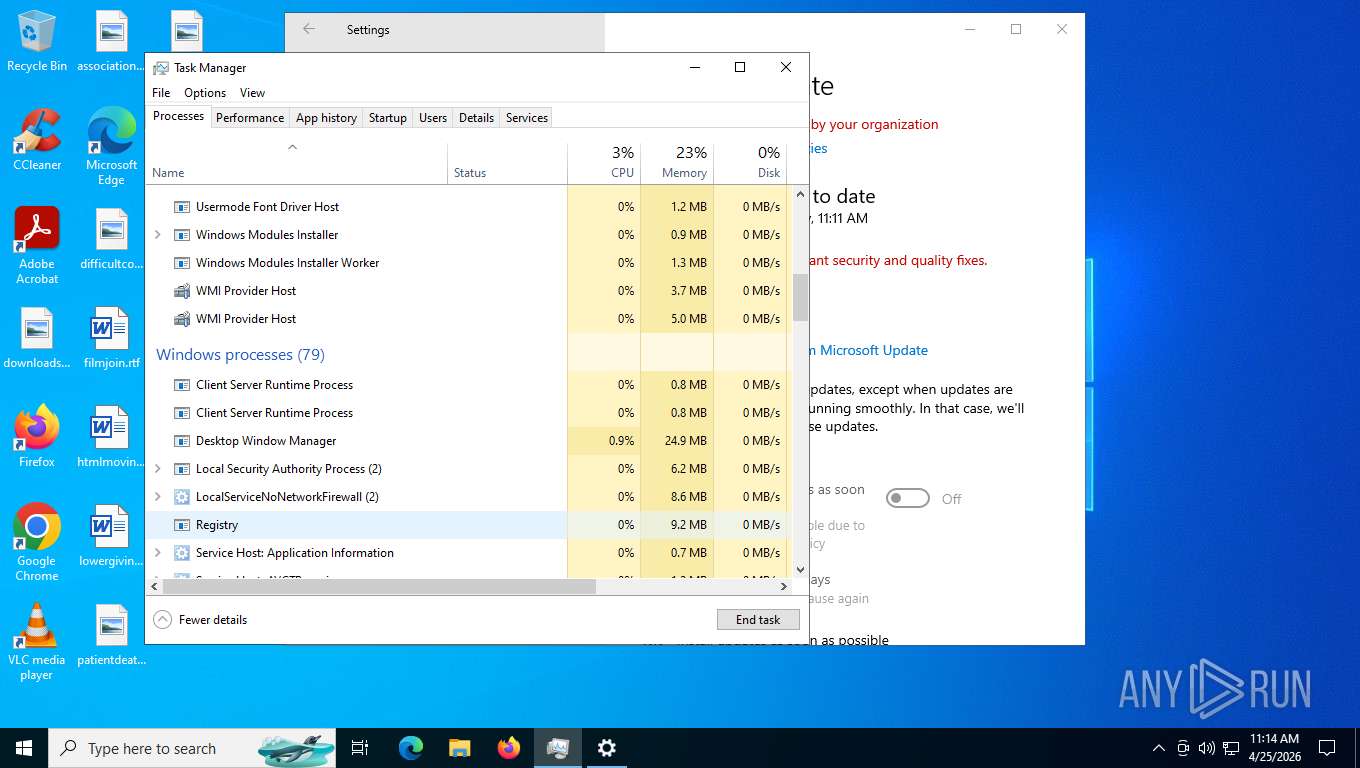
Total processes
313
Monitored processes
18
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2716,i,6058488819488462294,12090040854918117204,262144 --variations-seed-version --mojo-platform-channel-handle=812 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\AppData\Local\Temp\4333215012613356.exe" --binder-child | C:\Users\admin\AppData\Local\Temp\4333215012613356.exe | rename.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 1073807364 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2880 | "rename.exe" | C:\Users\admin\AppData\Local\Temp\4ui14z0b.rve\rename.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3552 | "C:\Users\admin\Desktop\rename.exe" | C:\Users\admin\Desktop\rename.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4312 | C:\Users\admin\AppData\Local\Temp\Updater.exe | C:\Users\admin\AppData\Local\Temp\Updater.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2168,i,6058488819488462294,12090040854918117204,262144 --variations-seed-version --mojo-platform-channel-handle=2160 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge_proxy.exe" --profile-directory=Default --app-id=heapafghjcojljadpkdnfjkifkmfjjdl --app-url=https://windows-12-web.vercel.app/index.html --app-launch-source=4 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge_proxy.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6460 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --source-shortcut="C:\Users\admin\AppData\Local\Temp\Windows 12.lnk.download.lnk" --profile-directory=Default --app-id=heapafghjcojljadpkdnfjkifkmfjjdl --app-url=https://windows-12-web.vercel.app/index.html --app-launch-source=4 --edge-skip-compat-layer-relaunch | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
6 909
Read events
6 903
Write events
4
Delete events
2
Modification events
| (PID) Process: | (7428) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (7428) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100018900000034000000310300008C020000E80300000000000000000000000000000F000000010000000000000058AA1665F67F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AA1665F67F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AA1665F67F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AA1665F67F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AA1665F67F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000AB1665F67F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028AB1665F67F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050AB1665F67F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AA1665F67F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070AB1665F67F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088AB1665F67F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8AB1665F67F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8AB1665F67F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0AB1665F67F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010AC1665F67F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AA1665F67F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AA1665F67F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AA1665F67F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040AC1665F67F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068AC1665F67F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090AC1665F67F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8AC1665F67F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8AC1665F67F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8AC1665F67F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028AB1665F67F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AA1665F67F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020AD1665F67F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040AD1665F67F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068AD1665F67F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AA1665F67F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050AB1665F67F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AA1665F67F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070AB1665F67F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088AB1665F67F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8AB1665F67F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8AB1665F67F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AA1665F67F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088AD1665F67F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8AD1665F67F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0AD1665F67F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AE1665F67F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AE1665F67F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AE1665F67F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AE1665F67F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
| (PID) Process: | (2340) 4333215012613356.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Updater |
Value: C:\Users\admin\AppData\Local\Temp\Updater.exe | |||
| (PID) Process: | (6580) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (6672) Updater.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Updater |
Value: C:\Users\admin\AppData\Local\Temp\Updater.exe | |||
| (PID) Process: | (6580) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100018900000034000000310300008C020000E80300000000000000000000000000000F000000010000000000000058AA36E0F67F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AA36E0F67F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AA36E0F67F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AA36E0F67F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AA36E0F67F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000AB36E0F67F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028AB36E0F67F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050AB36E0F67F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AA36E0F67F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070AB36E0F67F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088AB36E0F67F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8AB36E0F67F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8AB36E0F67F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0AB36E0F67F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010AC36E0F67F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AA36E0F67F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AA36E0F67F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AA36E0F67F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040AC36E0F67F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068AC36E0F67F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090AC36E0F67F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8AC36E0F67F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8AC36E0F67F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8AC36E0F67F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028AB36E0F67F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AA36E0F67F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020AD36E0F67F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040AD36E0F67F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068AD36E0F67F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AA36E0F67F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050AB36E0F67F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AA36E0F67F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070AB36E0F67F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088AB36E0F67F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8AB36E0F67F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8AB36E0F67F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AA36E0F67F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088AD36E0F67F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8AD36E0F67F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0AD36E0F67F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AE36E0F67F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AE36E0F67F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AE36E0F67F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AE36E0F67F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
Executable files
3
Suspicious files
8
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFdff21.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFdff30.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFdff40.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFdff50.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFdff5f.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
160
TCP/UDP connections
76
DNS requests
47
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 312 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
5316 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
5316 | svchost.exe | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
4872 | svchost.exe | GET | 200 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.80 Kb | whitelisted |
4872 | svchost.exe | GET | 200 | 23.216.77.43:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4872 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 2.16.241.205:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5316 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5316 | svchost.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4872 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
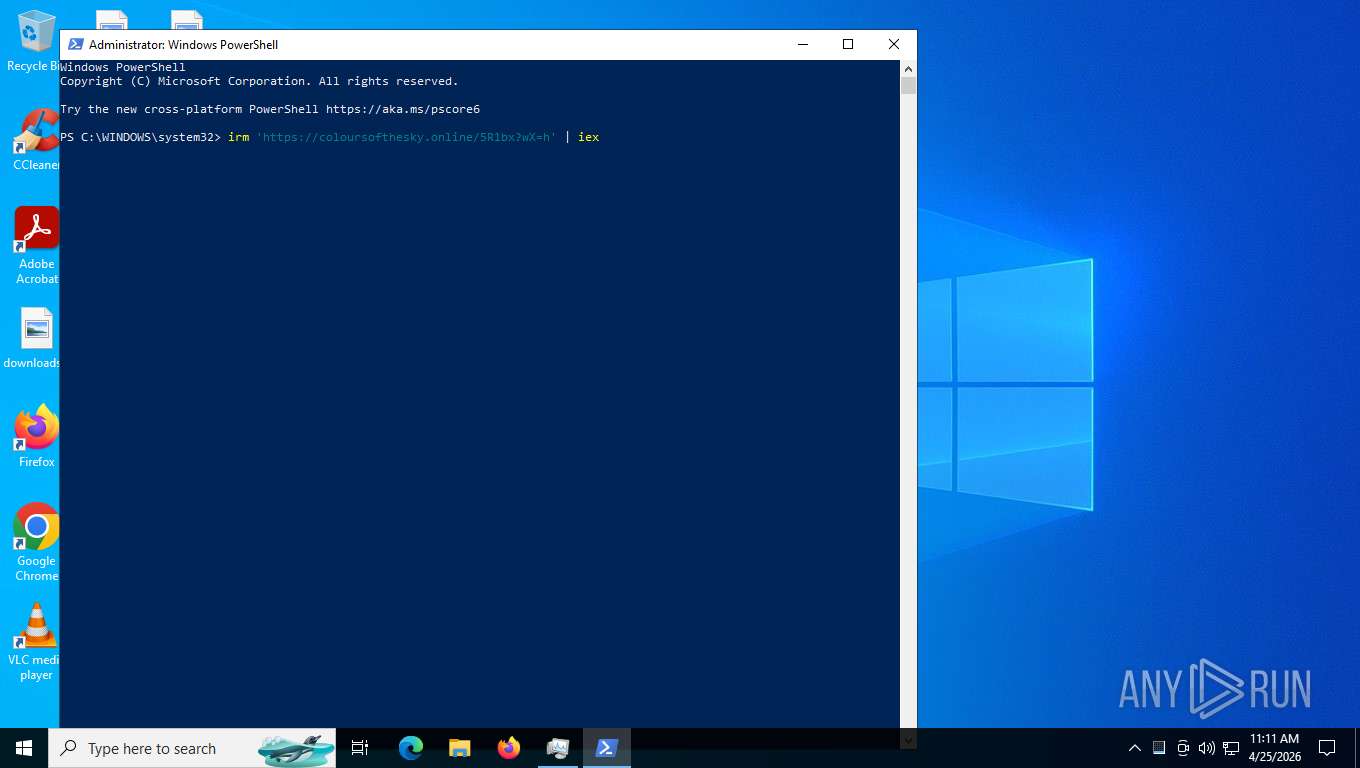
2204 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2880 | rename.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2880 | rename.exe | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |
2880 | rename.exe | A Network Trojan was detected | ET HUNTING Suspicious Fake Windows User-Agent in HTTP Header |
2880 | rename.exe | A Network Trojan was detected | ET HUNTING Suspicious Fake Windows User-Agent in HTTP Header |
3552 | rename.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
3552 | rename.exe | A Network Trojan was detected | ET HUNTING Suspicious Fake Windows User-Agent in HTTP Header |
3552 | rename.exe | A Network Trojan was detected | ET HUNTING Suspicious Fake Windows User-Agent in HTTP Header |
2340 | 4333215012613356.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm TCP Packet |