| File name: | Loader.exe |
| Full analysis: | https://app.any.run/tasks/2a849b8b-205b-4cda-81fa-6252a0b1ff3a |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
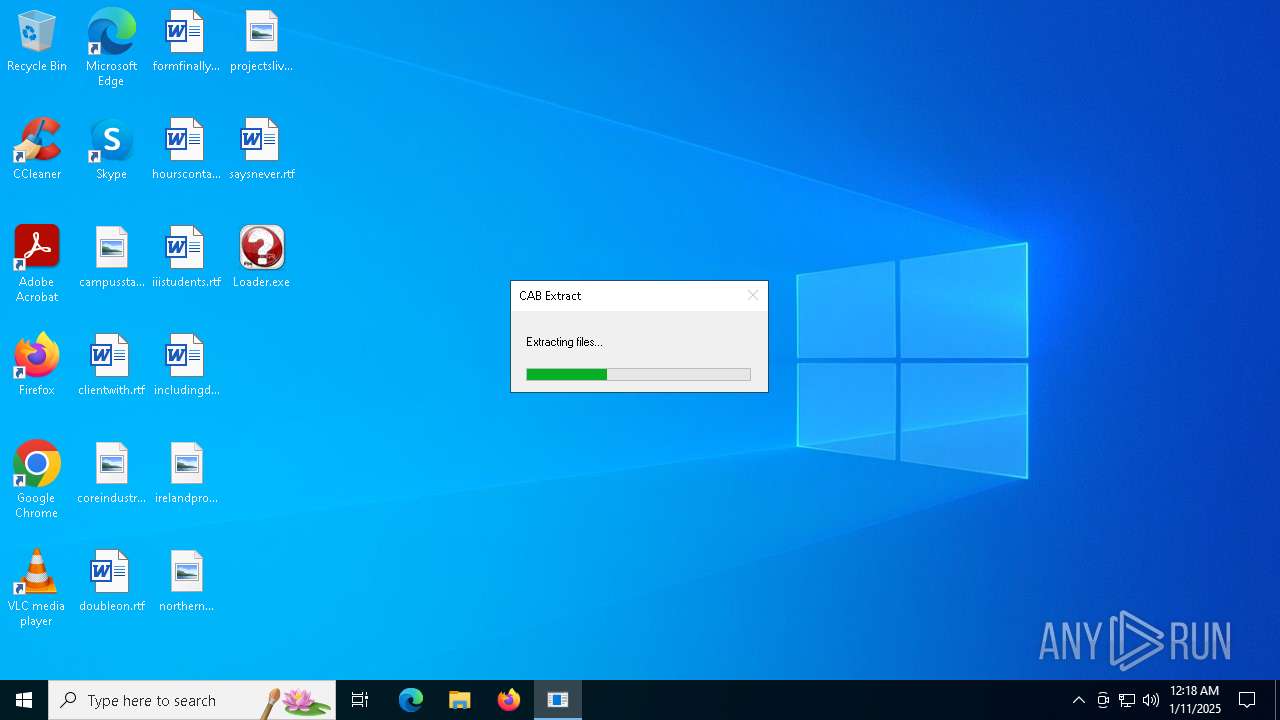
| Analysis date: | January 11, 2025, 00:18:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 16AC36A918C29F1E3F54ADA06BEFDCA9 |
| SHA1: | 69F59CFE33B74FE22864E269D9BB60D932C79001 |
| SHA256: | 5A7A88B315C2A2DC81AC4B5AF5F48B310A13FFD7377A9608BEC5D72717D99343 |
| SSDEEP: | 49152:8N5ZZHd/aY77YLNVE0K+bcODJ0lvBhtQ+KRZ+GuhwI4mOHIdYiBRAkNOknPZEqkY:8t/7fYHbK+bhDmA+KduhwzoCJaOOkXQZ |
MALICIOUS
Executing a file with an untrusted certificate
- Loader.exe (PID: 4384)
AutoIt loader has been detected (YARA)
- Commentary.com (PID: 4428)
LUMMA has been detected (SURICATA)
- Commentary.com (PID: 4428)
SUSPICIOUS
Reads security settings of Internet Explorer
- Loader.exe (PID: 4384)
Starts CMD.EXE for commands execution
- Loader.exe (PID: 4384)
- cmd.exe (PID: 3140)
Get information on the list of running processes
- cmd.exe (PID: 3140)
Executing commands from ".cmd" file
- Loader.exe (PID: 4384)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3140)
Application launched itself
- cmd.exe (PID: 3140)
The executable file from the user directory is run by the CMD process
- Commentary.com (PID: 4428)
Starts the AutoIt3 executable file
- cmd.exe (PID: 3140)
Starts application with an unusual extension
- cmd.exe (PID: 3140)
INFO
Checks supported languages
- Loader.exe (PID: 4384)
- extrac32.exe (PID: 4764)
- Commentary.com (PID: 4428)
Reads the computer name
- Loader.exe (PID: 4384)
- Commentary.com (PID: 4428)
- extrac32.exe (PID: 4764)
Creates files or folders in the user directory
- Loader.exe (PID: 4384)
- extrac32.exe (PID: 4764)
Process checks computer location settings
- Loader.exe (PID: 4384)
Reads the machine GUID from the registry
- Commentary.com (PID: 4428)
Creates a new folder
- cmd.exe (PID: 5308)
Reads mouse settings
- Commentary.com (PID: 4428)
Reads the software policy settings
- Commentary.com (PID: 4428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:09:26 13:21:28+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28160 |
| InitializedDataSize: | 507904 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3883 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
131
Monitored processes
15
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | cmd /c copy /b 672717\Commentary.com + Parts + Favourites + Rochester + Pest + Simulations + Touch + Possess + Analysts + Radar + Sys 672717\Commentary.com | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | "C:\Windows\System32\cmd.exe" /c move Buses Buses.cmd & Buses.cmd | C:\Windows\SysWOW64\cmd.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3816 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4384 | "C:\Users\admin\Desktop\Loader.exe" | C:\Users\admin\Desktop\Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4428 | Commentary.com u | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\672717\Commentary.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 5 Modules
| |||||||||||||||
| 4716 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4764 | extrac32 /Y /E Investigators | C:\Windows\SysWOW64\extrac32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® CAB File Extract Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5004 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 907
Read events
3 907
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
20
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4384 | Loader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Apollo | binary | |
MD5:3D96DE5980245ED8BBFBFBF2E4DB3ACA | SHA256:E724542DDD3CD07735B75CA76843650862F93CDD3728724CB87D39E1F01D60FE | |||
| 3140 | cmd.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Buses.cmd | text | |
MD5:AA42C7FEA6808C0AF9F2F9DC52F07782 | SHA256:BF7E5027AA452490352CD2DF668779D6DC230B7F27E00A504ED032704528AD43 | |||
| 4384 | Loader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Buses | text | |
MD5:AA42C7FEA6808C0AF9F2F9DC52F07782 | SHA256:BF7E5027AA452490352CD2DF668779D6DC230B7F27E00A504ED032704528AD43 | |||
| 4384 | Loader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Investigators | compressed | |
MD5:077C44D8585F7A668F60B3AA75FDFC4A | SHA256:314BDDC458E2195062351B154607523A723A3CC2EC75EFD8F0DA82586840EAF4 | |||
| 4384 | Loader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Name | binary | |
MD5:5E88567E27B1DEDD756E6EF1C5DA17C5 | SHA256:C02F60CAD58451AF445A22FC3E6599CD488413DC7D9C8E11646B9AD50093BE50 | |||
| 4764 | extrac32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Touch | binary | |
MD5:4021E51169BC9A64C2B64783953E5EBB | SHA256:207733202874187A960EB73049ED035A80199823D481FD3BF9264038AE7B5A33 | |||
| 4384 | Loader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Contain | binary | |
MD5:5ABAB600E19A94A84E220FC5220A9B14 | SHA256:C764F0FB99C8F35491898D4331A88B5E17DF2137C9C8981942783316BBDC585B | |||
| 4384 | Loader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Mill | binary | |
MD5:8C1D1B3A4EB8D2AF73EDB3F539B92FAB | SHA256:2324E57AB04AF35764A26F8C49E2193C67F22904603BCE366FF40D195FBE17D2 | |||
| 4384 | Loader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Displays | binary | |
MD5:7D36FFAD89E91436C482D996E1C5A8FF | SHA256:379C3F76F49FFD01F1FCF8EE8C8172BBBA512A4D9E1E5E5F032AA9C2BE2FDD3B | |||
| 4764 | extrac32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Favourites | binary | |
MD5:E8D086062B46F8AC885D9B6ECF1D4129 | SHA256:9049D6C099E773B261D9FE9B877DC12A248513132C8626B86D4E1DAB3CCA42C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
24
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6072 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6072 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.212.216.106:443 | https://steamcommunity.com/profiles/76561199724331900 | unknown | html | 34.3 Kb | whitelisted |
— | — | POST | 200 | 104.21.48.1:443 | https://sailstrangej.cyou/api | unknown | text | 17 b | unknown |
— | — | POST | 200 | 104.21.32.1:443 | https://sputnik-1985.com/api | unknown | text | 17 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6072 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 104.126.37.170:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6072 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6072 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
cTGNwyVSNWCXX.cTGNwyVSNWCXX |
| unknown |
sailstrangej.cyou |
| unknown |
soundtappysk.shop |
| malicious |
femalsabler.shop |
| malicious |
apporholis.shop |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4428 | Commentary.com | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |