| File name: | hjhg.exe |
| Full analysis: | https://app.any.run/tasks/5956087c-60c6-4578-ae43-24c673f7f63d |
| Verdict: | Malicious activity |
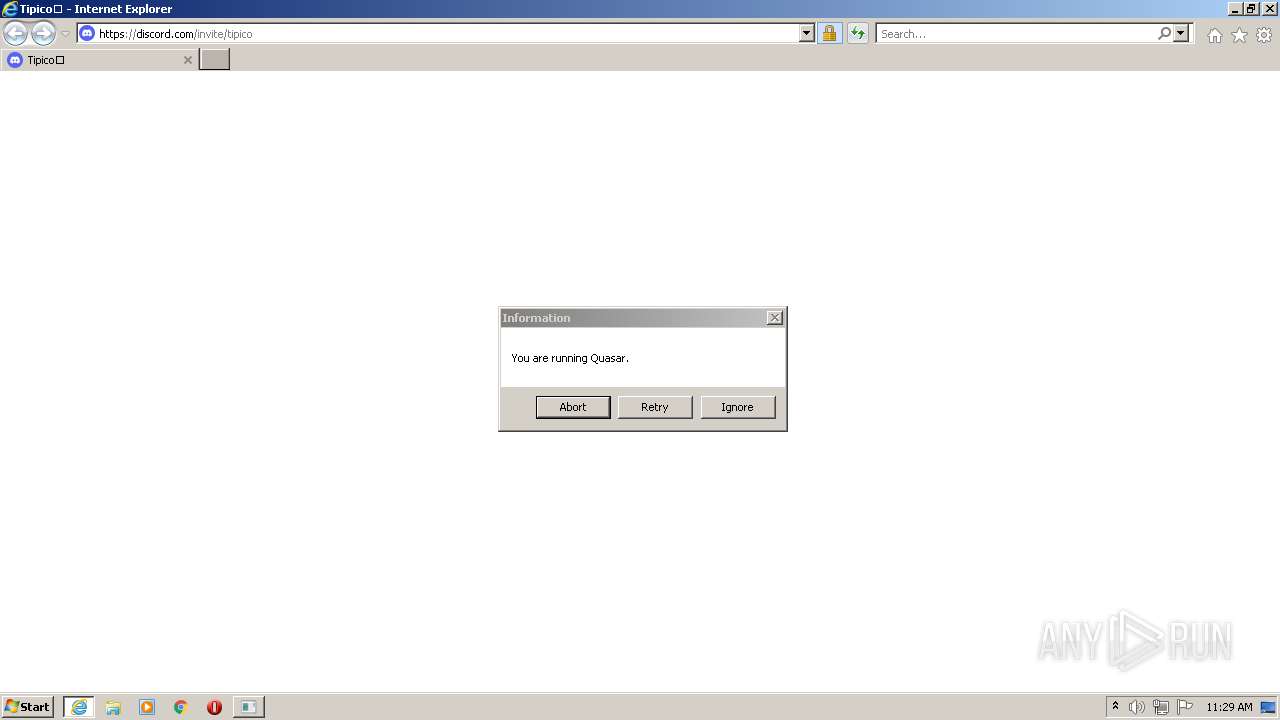
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | June 27, 2022, 10:26:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D6EAF56E261EA4AE68049C9795969269 |
| SHA1: | 6C7B9179F0D62E94E327044D07F221A6817763B1 |
| SHA256: | 59EAD6F9ACADA9C4D0C5A6ED1D6B460C79F835A3462B959CE6F2A5BD9701720B |
| SSDEEP: | 6144:5SncRl6pNHXf500M8knHTWJbO2SbL1CafH60dcCVVFy2:44Yd50ZqJbFa1tH6nCVVFy2 |
MALICIOUS
Drops/Copies Quasar RAT executable
- hjhg.exe (PID: 2220)
- MONACO GUCK.EXE (PID: 4024)
Drops executable file immediately after starts
- hjhg.exe (PID: 2220)
- MONACO GUCK.EXE (PID: 4024)
Application was dropped or rewritten from another process
- Client.exe (PID: 2032)
- MONACO GUCK.EXE (PID: 4024)
Changes the autorun value in the registry
- MONACO GUCK.EXE (PID: 4024)
- Client.exe (PID: 2032)
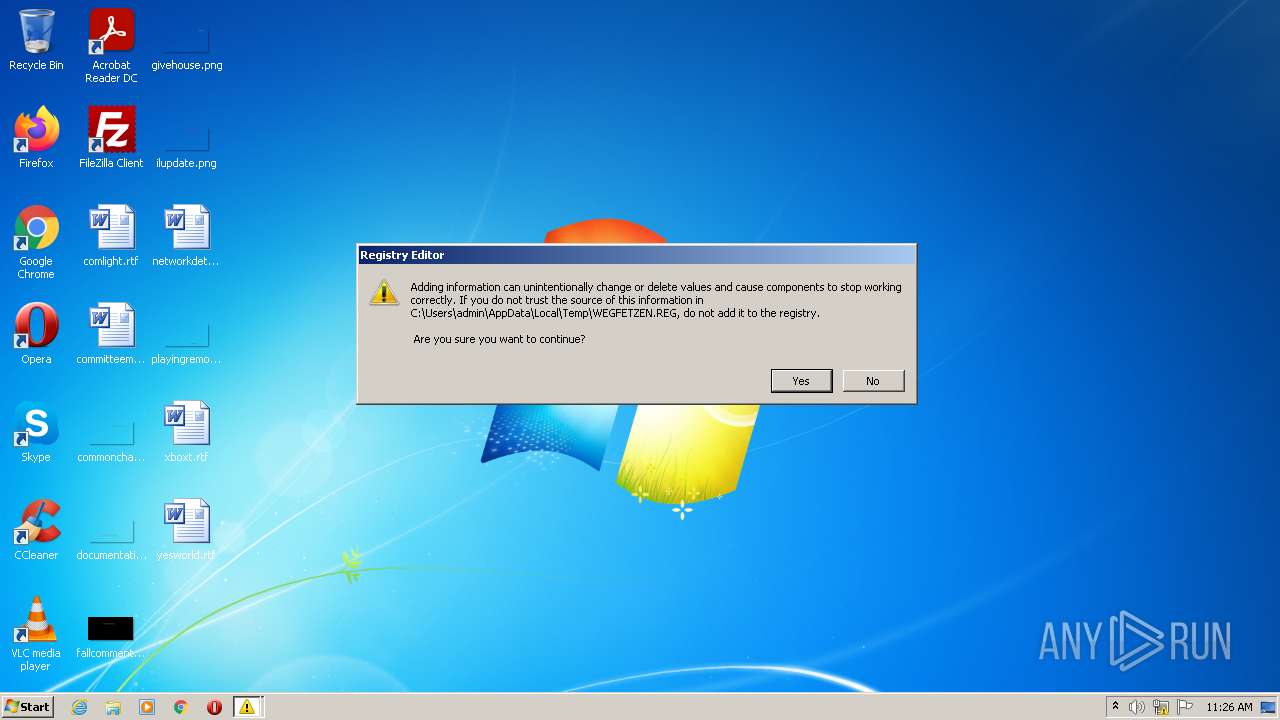
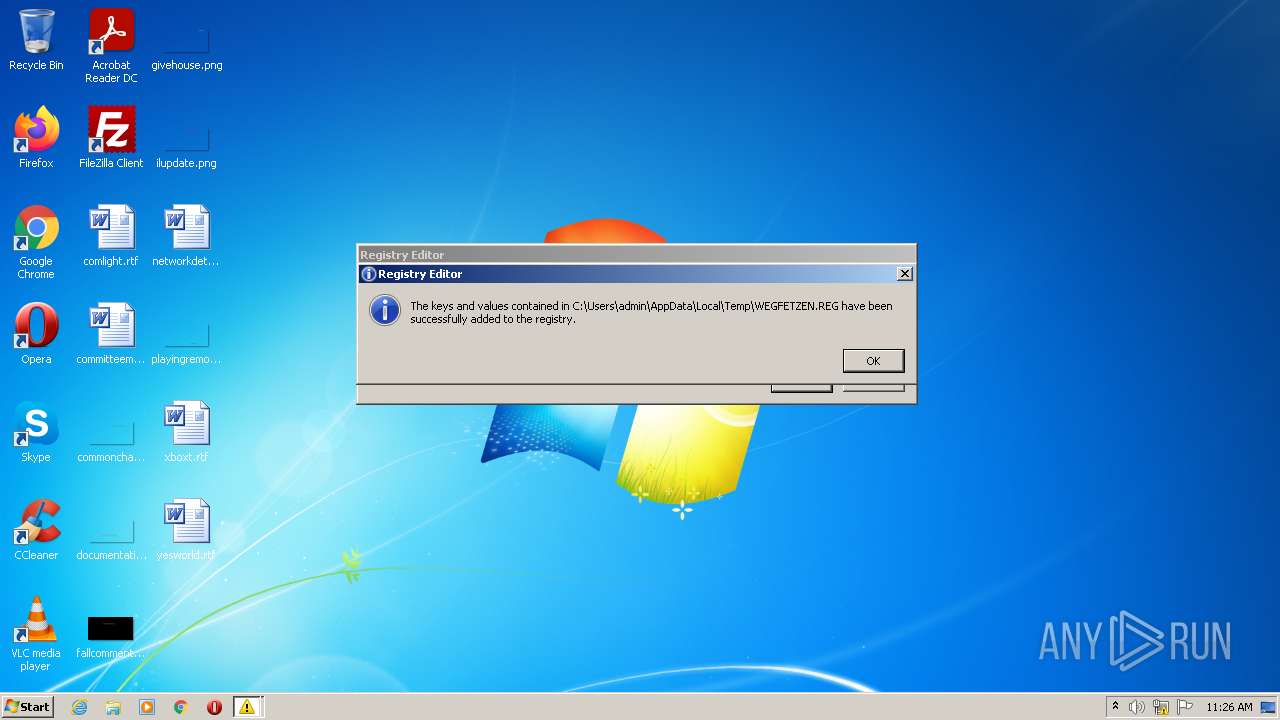
Disables Windows Defender
- regedit.exe (PID: 3468)
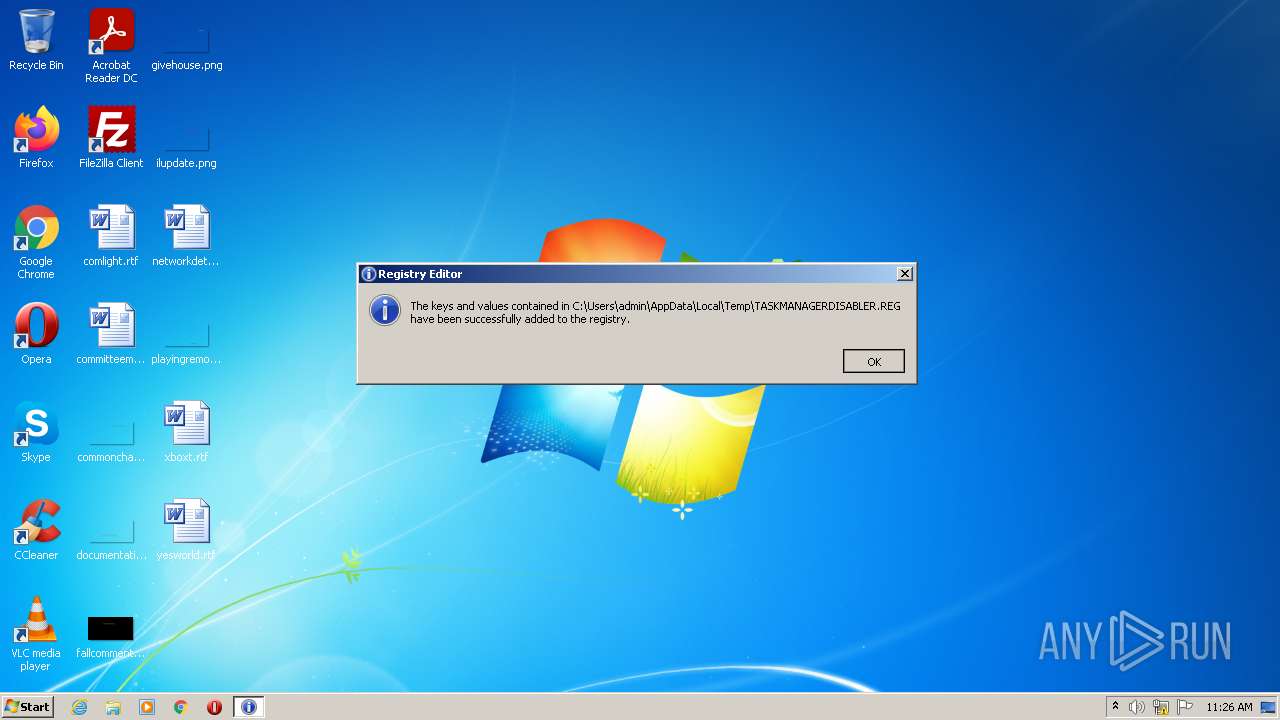
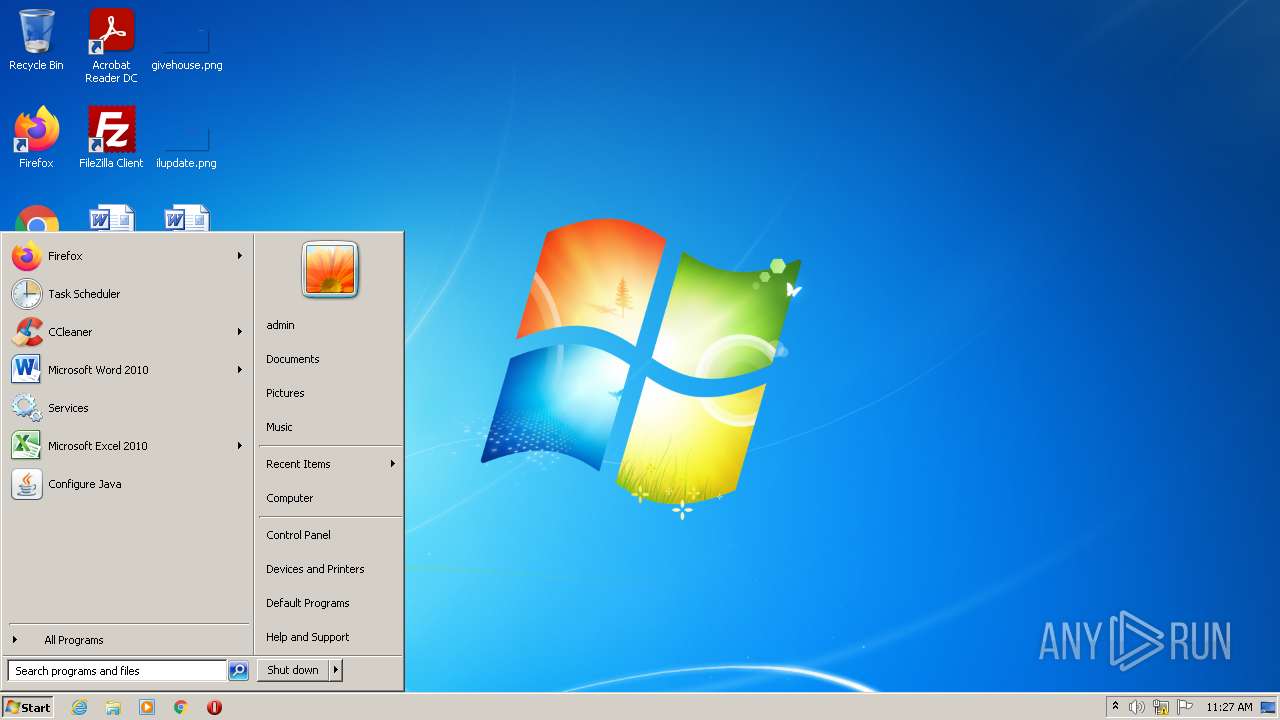
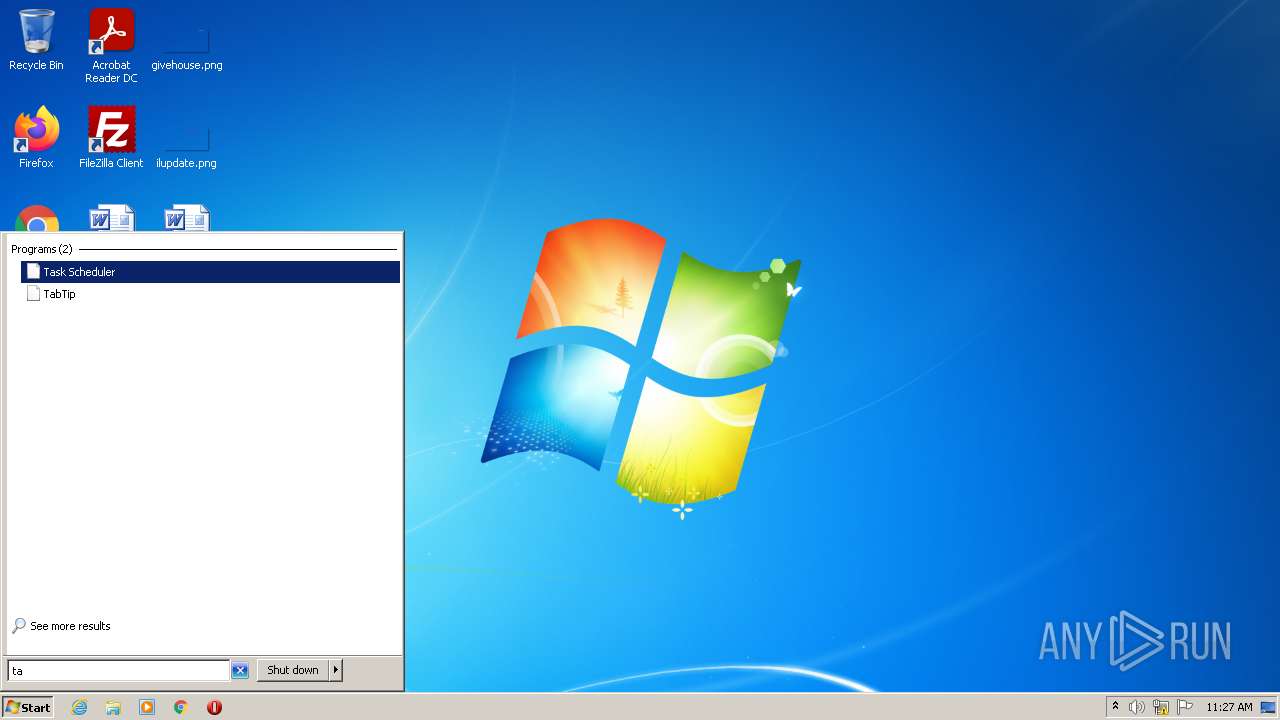
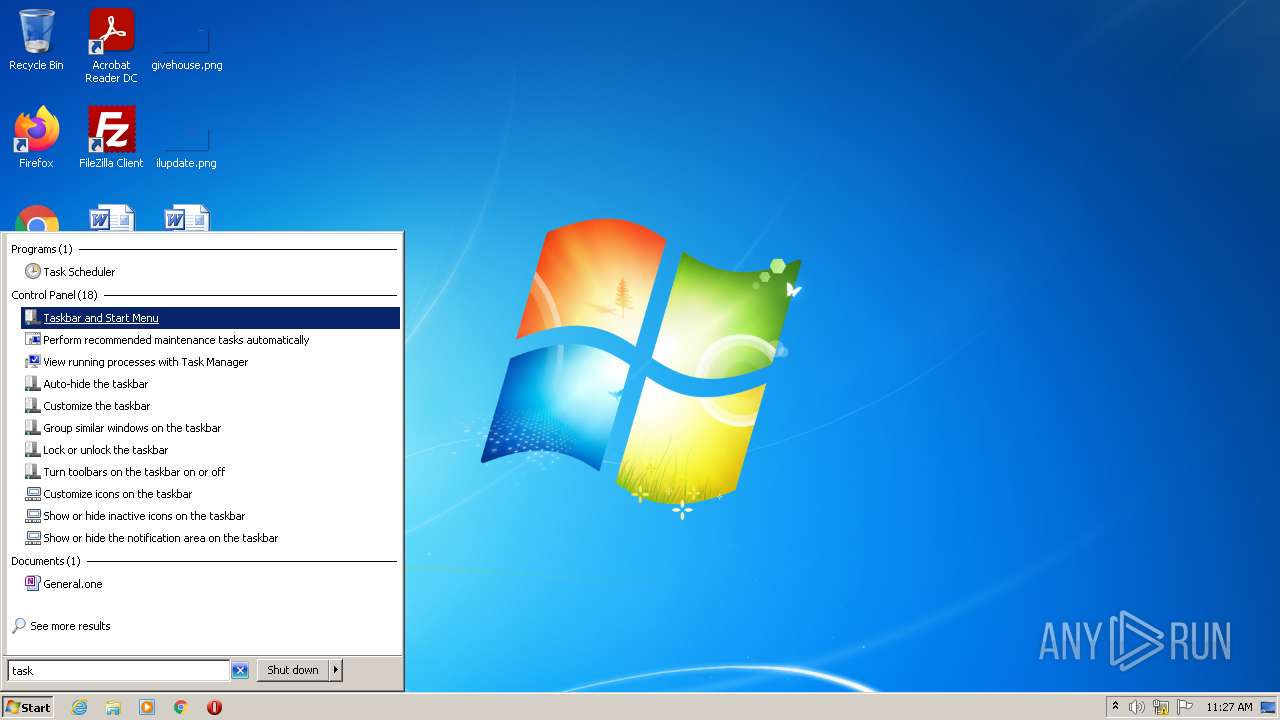
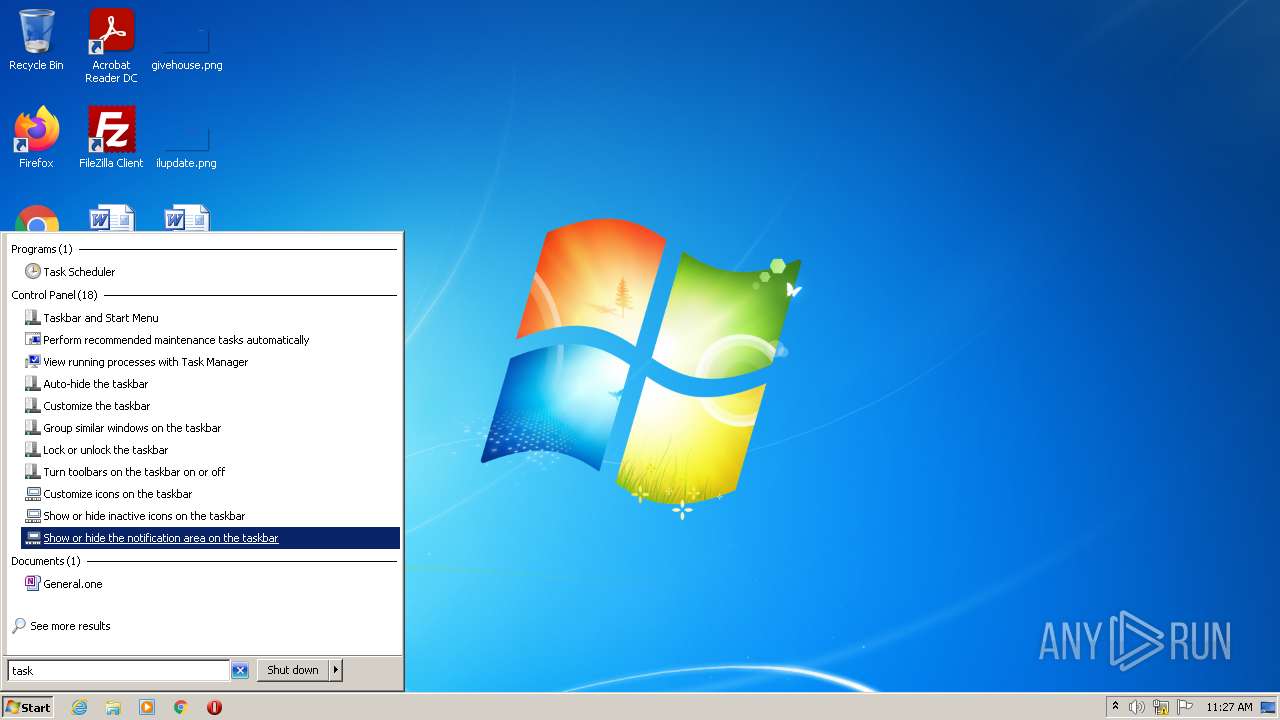
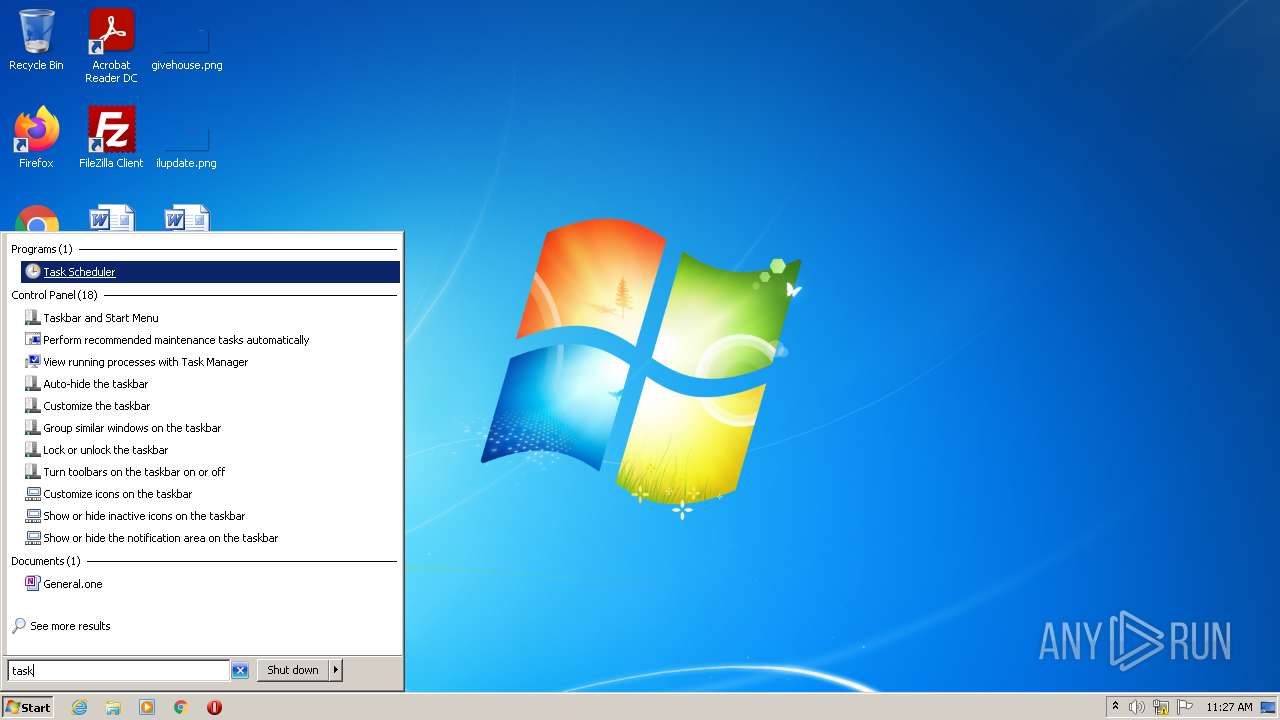
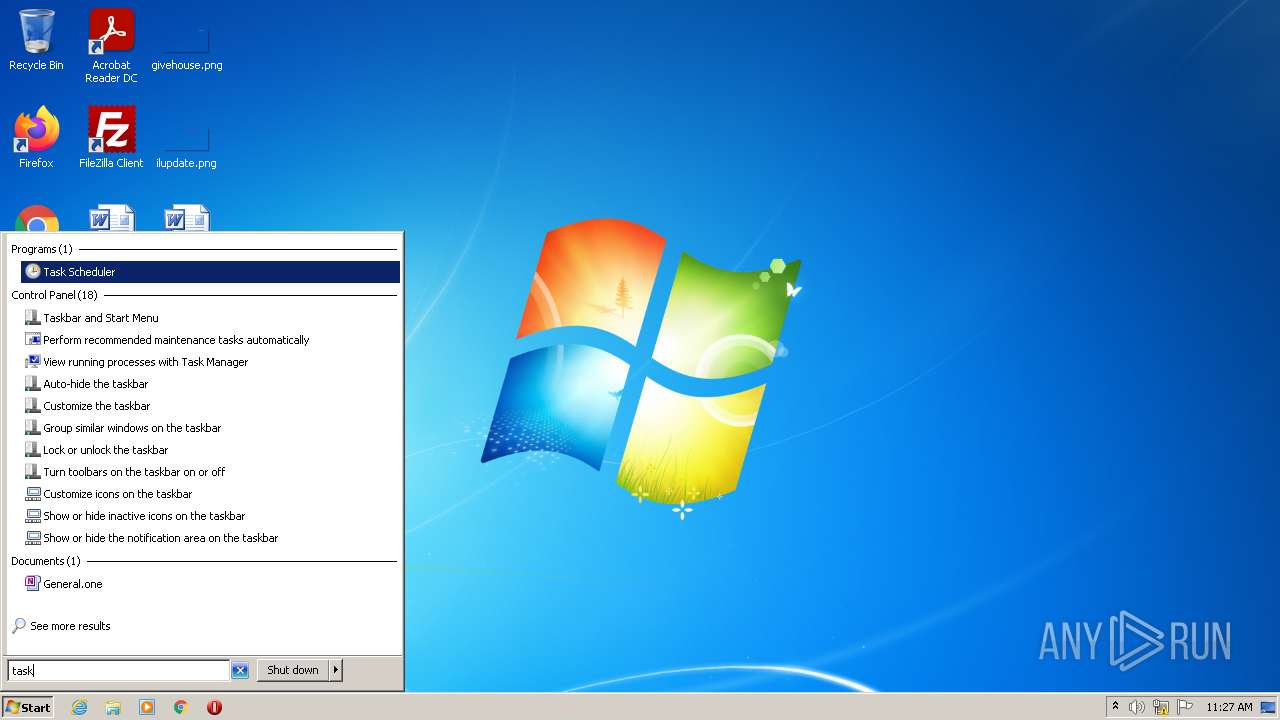
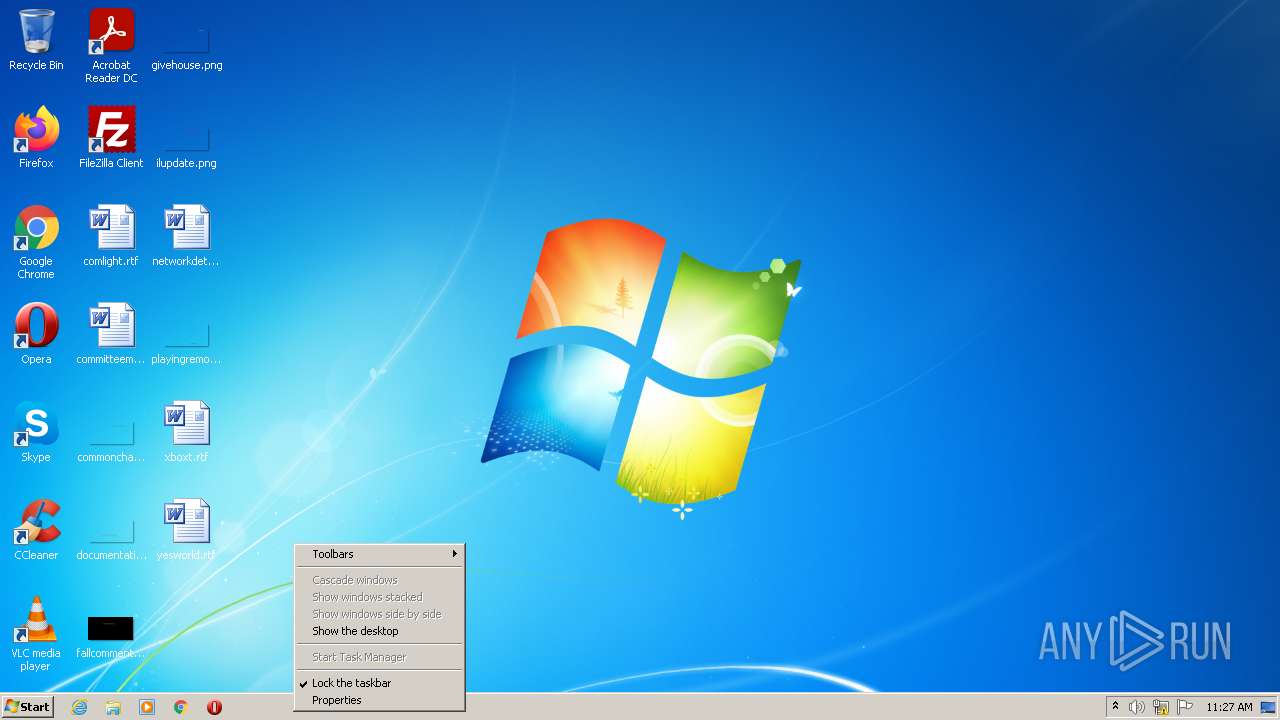
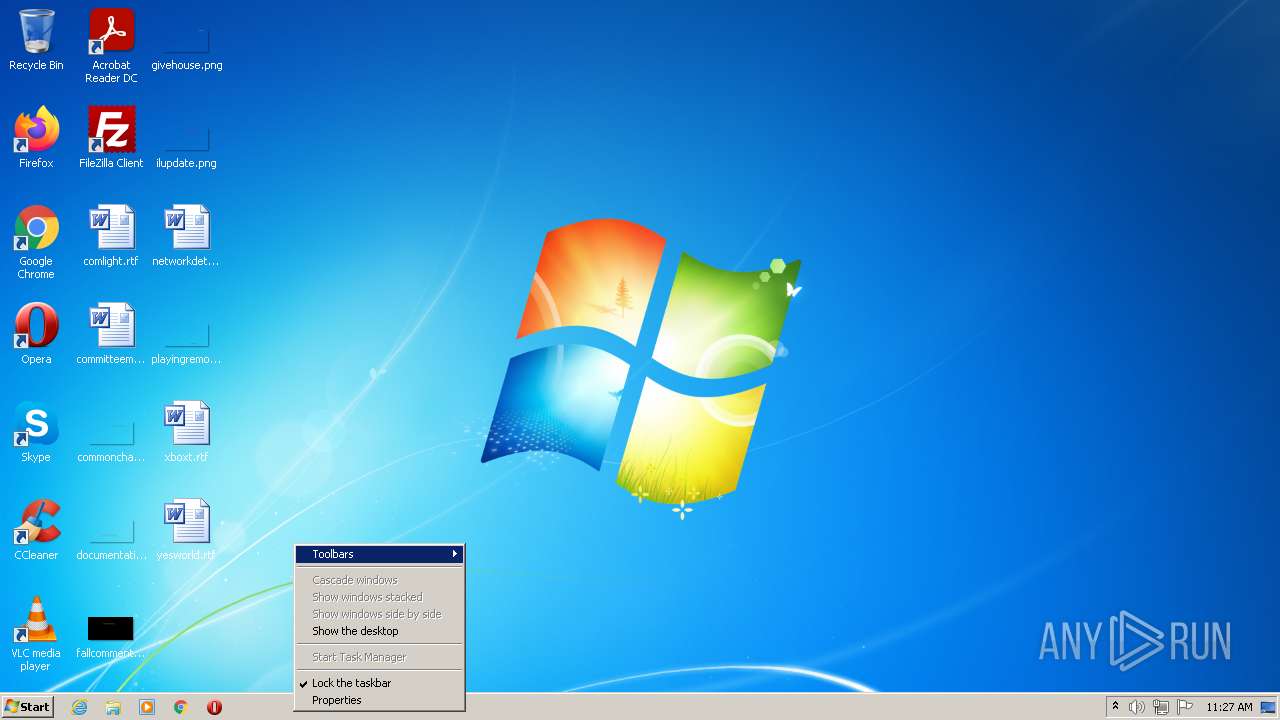
Task Manager has been disabled (taskmgr)
- regedit.exe (PID: 2272)
QUASAR detected by memory dumps
- Client.exe (PID: 2032)
SUSPICIOUS
Executable content was dropped or overwritten
- hjhg.exe (PID: 2220)
- MONACO GUCK.EXE (PID: 4024)
Drops a file with a compile date too recent
- hjhg.exe (PID: 2220)
- MONACO GUCK.EXE (PID: 4024)
Reads the computer name
- hjhg.exe (PID: 2220)
- MONACO GUCK.EXE (PID: 4024)
- Client.exe (PID: 2032)
Checks supported languages
- MONACO GUCK.EXE (PID: 4024)
- hjhg.exe (PID: 2220)
- Client.exe (PID: 2032)
Creates files in the user directory
- MONACO GUCK.EXE (PID: 4024)
- Client.exe (PID: 2032)
Reads Environment values
- MONACO GUCK.EXE (PID: 4024)
- Client.exe (PID: 2032)
Starts itself from another location
- MONACO GUCK.EXE (PID: 4024)
Checks for external IP
- MONACO GUCK.EXE (PID: 4024)
- Client.exe (PID: 2032)
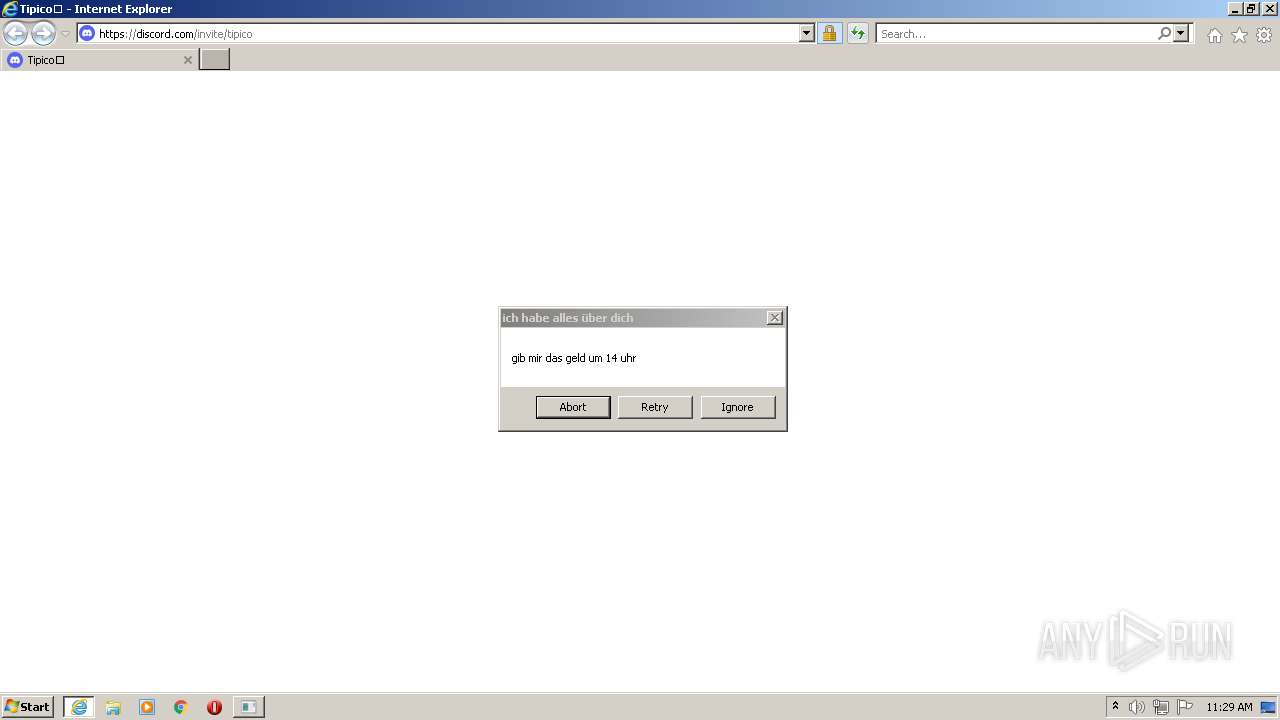
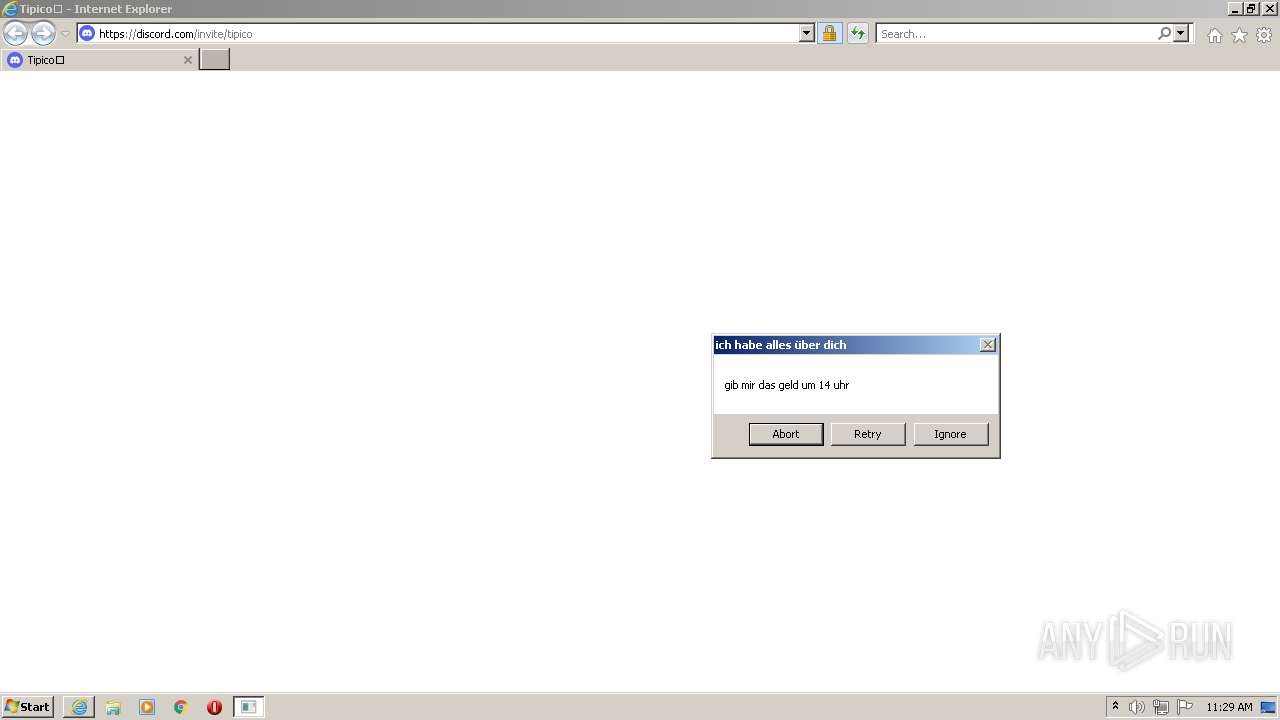
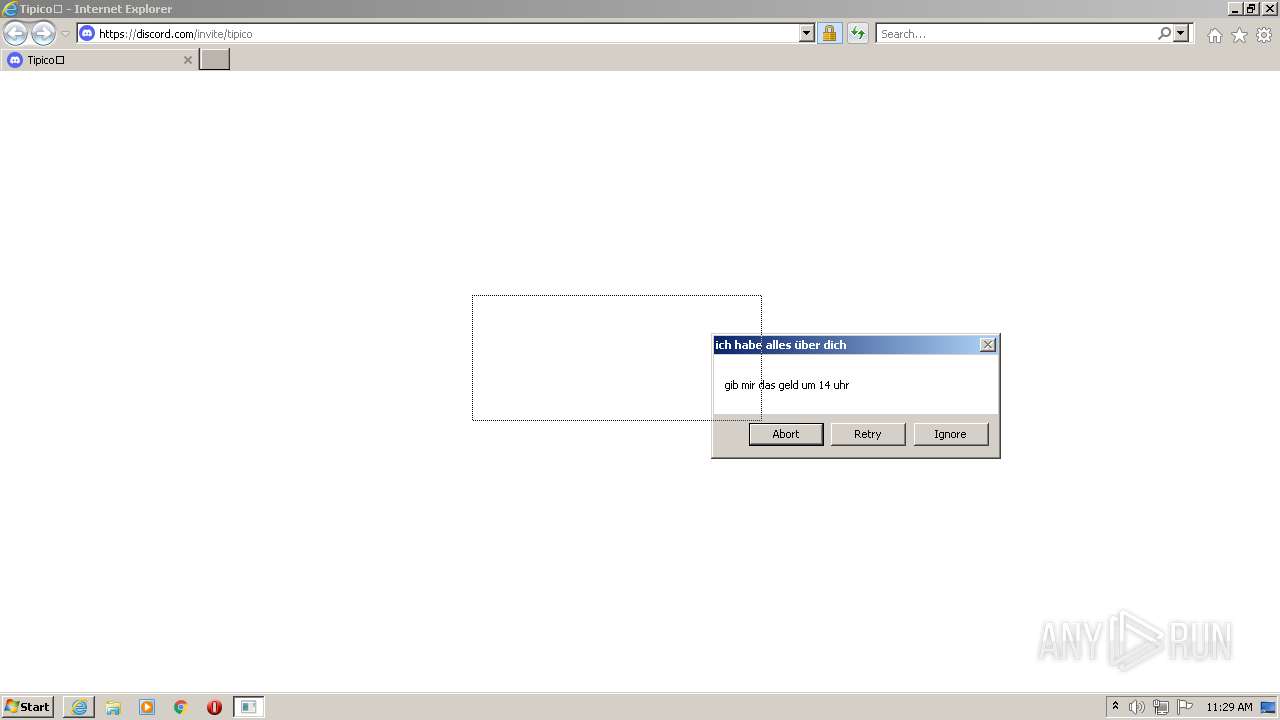
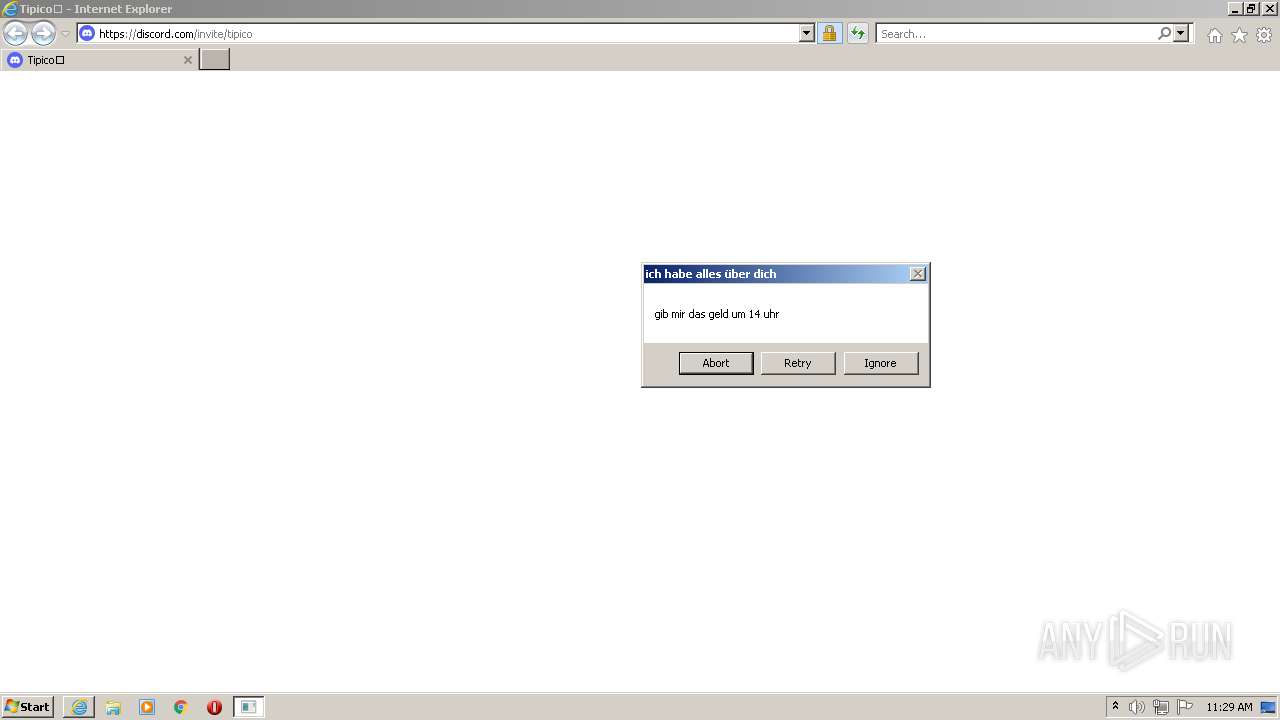
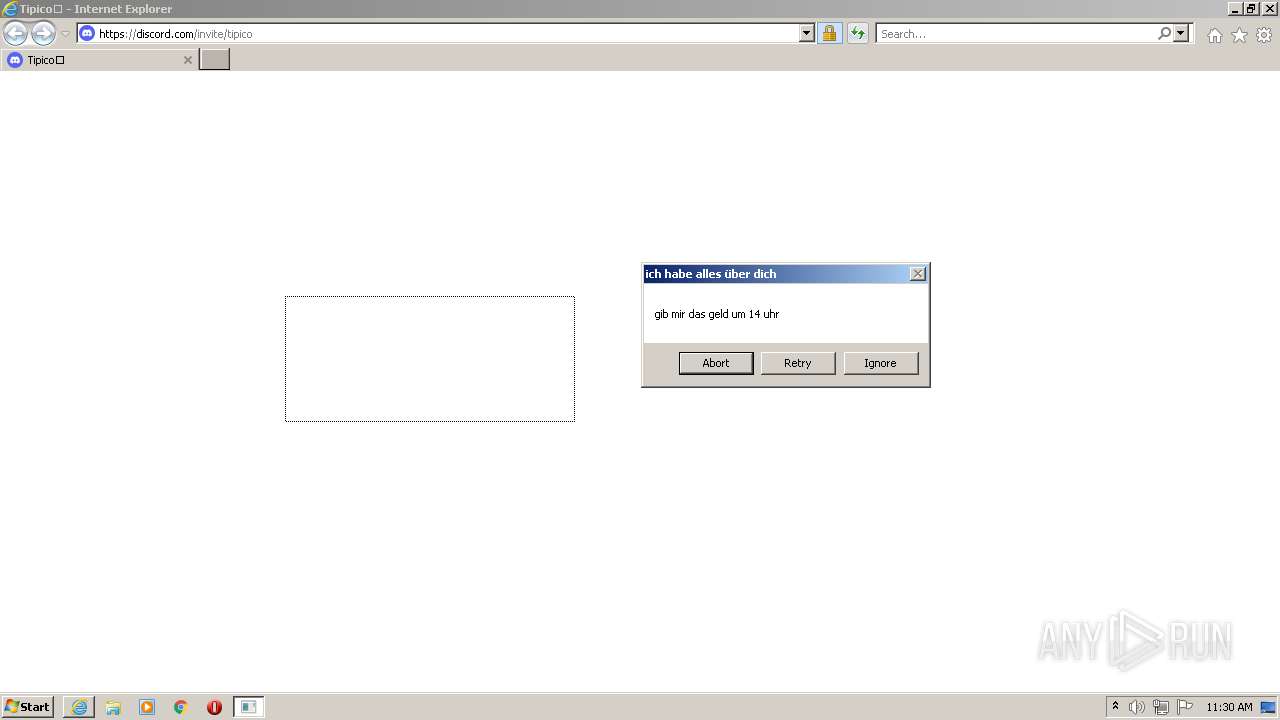
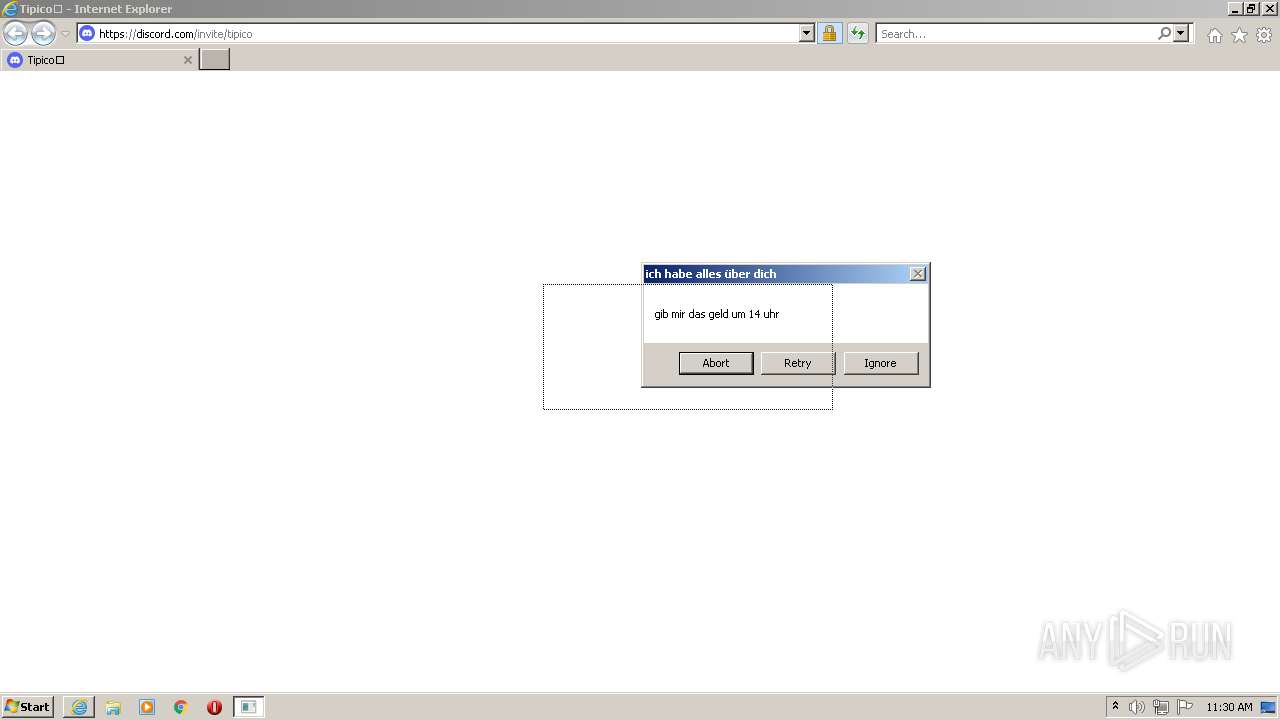
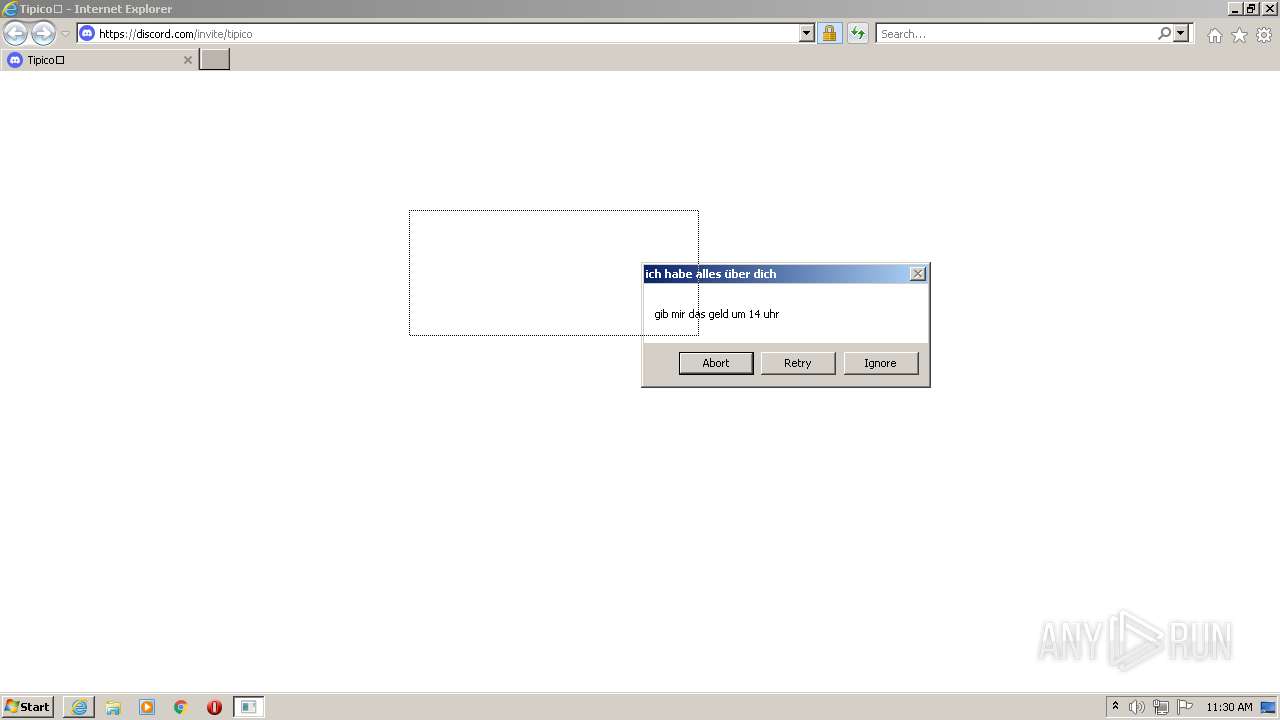
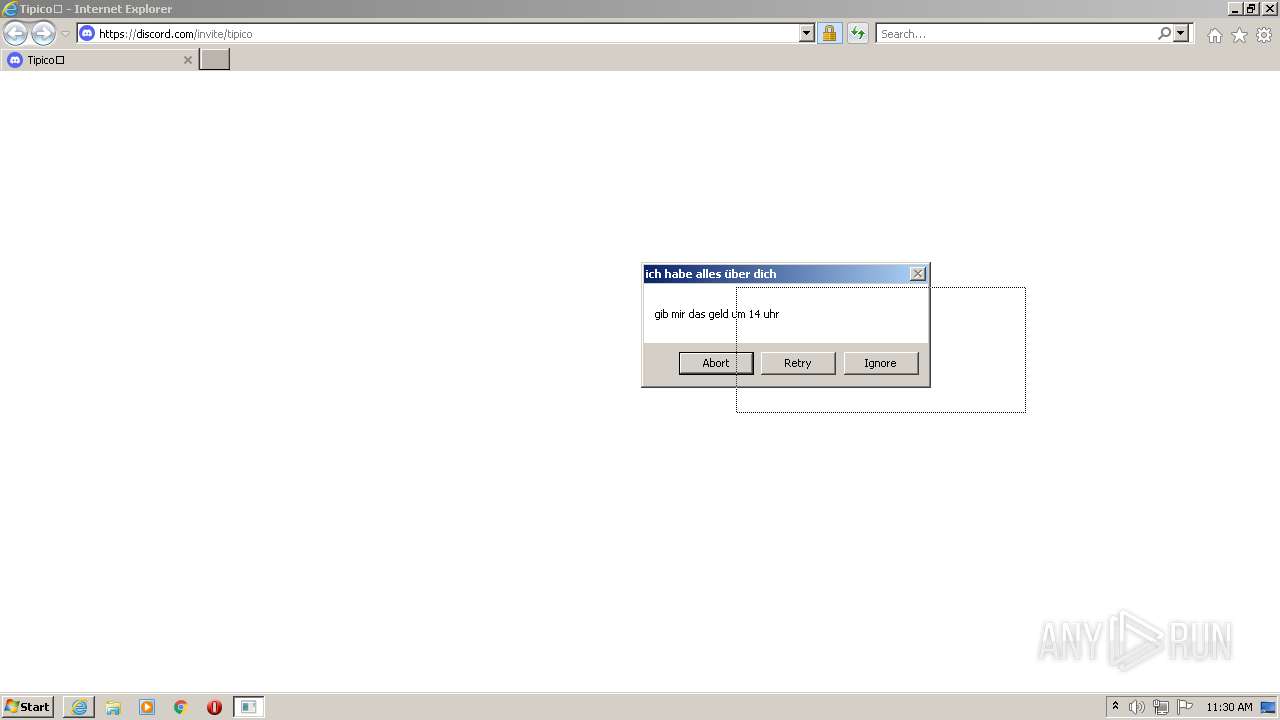
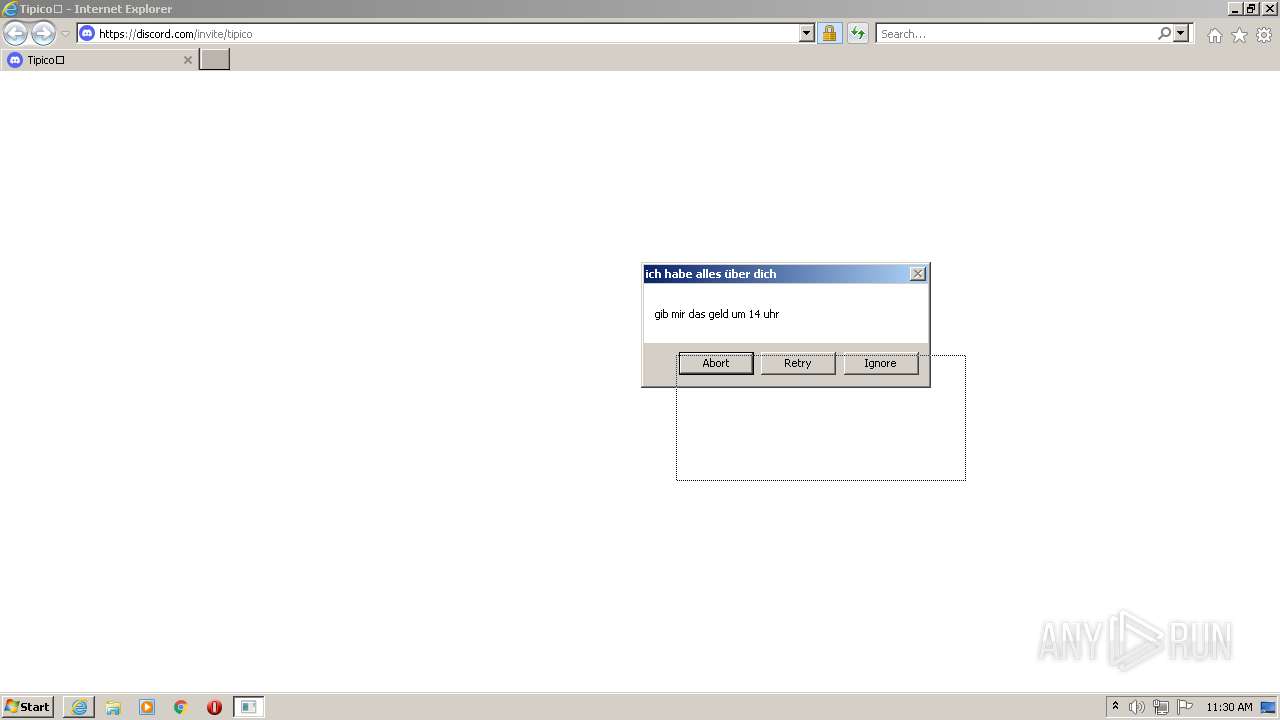
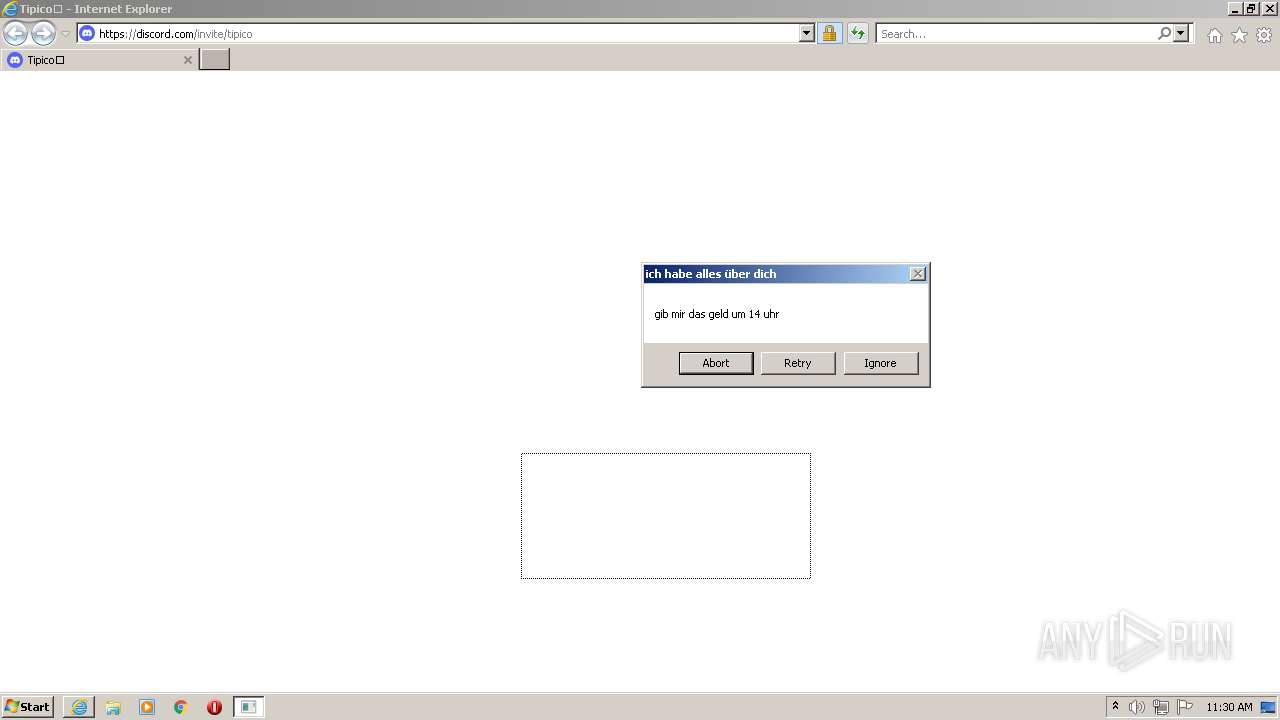
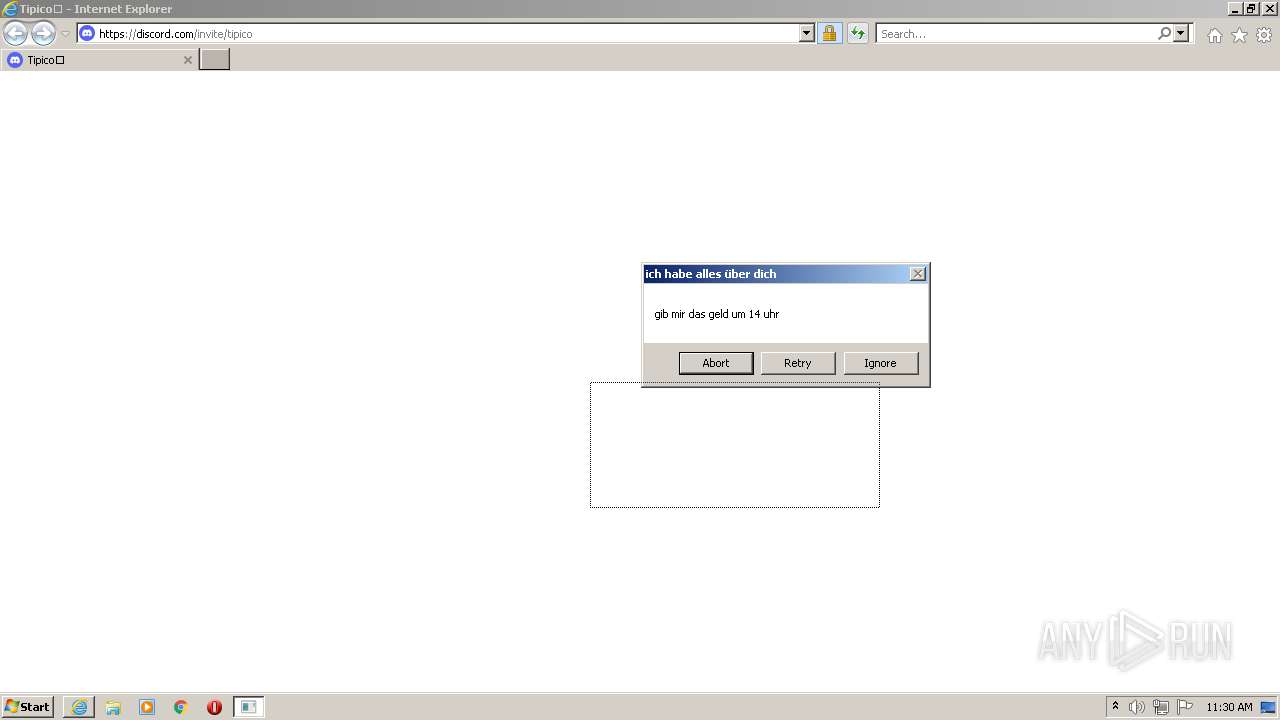
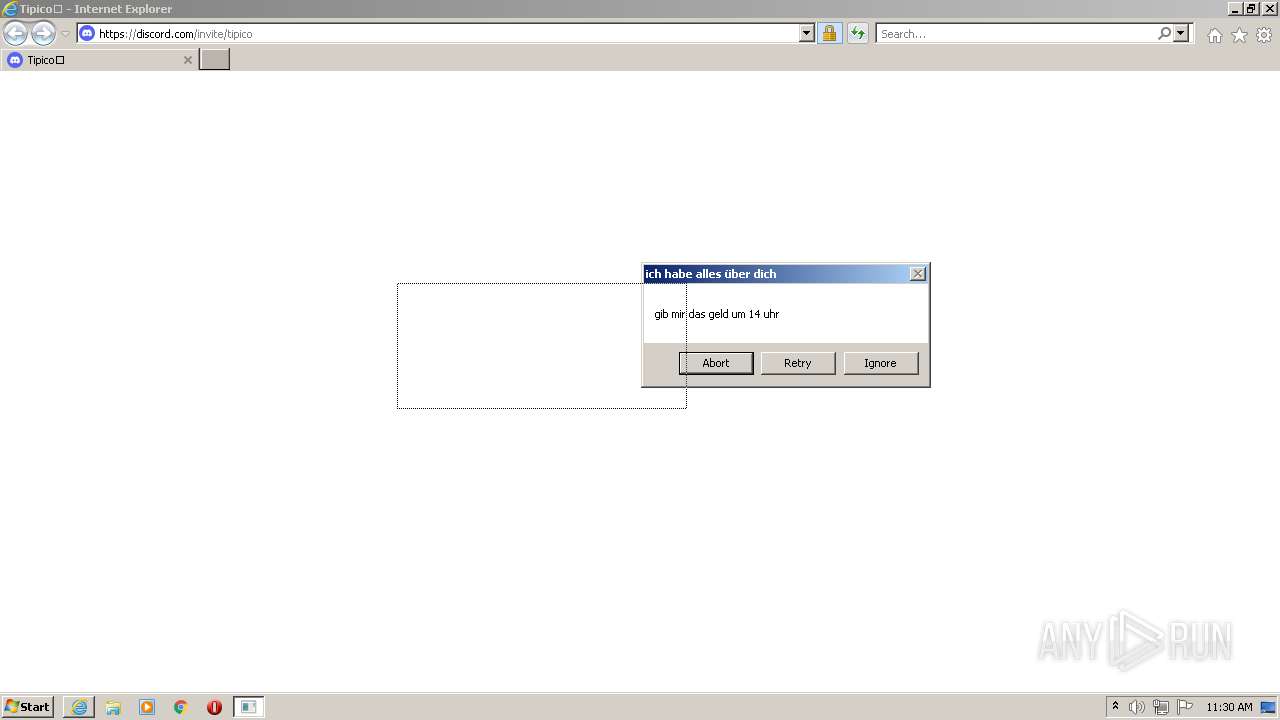
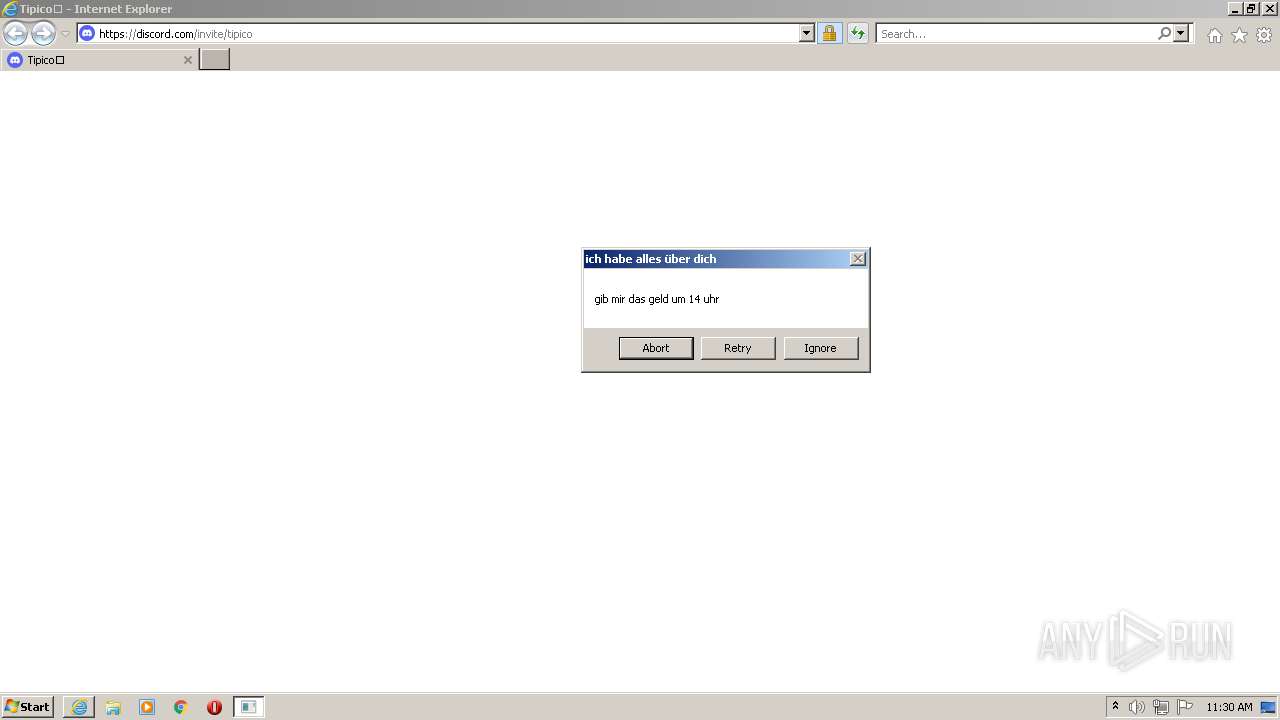
Starts Internet Explorer
- Client.exe (PID: 2032)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 836)
INFO
Checks supported languages
- regedit.exe (PID: 3468)
- regedit.exe (PID: 2272)
- iexplore.exe (PID: 836)
- iexplore.exe (PID: 3764)
Changes internet zones settings
- iexplore.exe (PID: 3764)
Reads the computer name
- iexplore.exe (PID: 3764)
- iexplore.exe (PID: 836)
Application launched itself
- iexplore.exe (PID: 3764)
Reads settings of System Certificates
- iexplore.exe (PID: 836)
- iexplore.exe (PID: 3764)
Checks Windows Trust Settings
- iexplore.exe (PID: 836)
- iexplore.exe (PID: 3764)
Reads internet explorer settings
- iexplore.exe (PID: 836)
Creates files in the user directory
- iexplore.exe (PID: 836)
- iexplore.exe (PID: 3764)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 836)
- iexplore.exe (PID: 3764)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3764)
Changes settings of System certificates
- iexplore.exe (PID: 3764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(2032) Client.exe
Version1.3.0.0
C2 (2)niggahunter88-33934.portmap.io:33934
Sub_DirSubDir
Install_NameClient.exe
MutexQSR_MUTEX_q2Tul7nBUKmd8SX6eg
Startupruntime brocker
Tagwdadsa
LogDirLogs
Signature
Certificate
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x3248 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 379904 |
| CodeSize: | 31232 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2011:07:03 11:05:04+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jul-2011 09:05:04 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Jul-2011 09:05:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00007842 | 0x00007A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48777 |
.rdata | 0x00009000 | 0x0000319E | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92389 |
.data | 0x0000D000 | 0x00001A84 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.57332 |
.rsrc | 0x0000F000 | 0x00057750 | 0x00057800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.42118 |
.reloc | 0x00067000 | 0x000013AA | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.12103 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
MONACO GUCK.EXE | 6.42792 | 356352 | Latin 1 / Western European | UNKNOWN | RBIND |
TASKMANAGERDISABLER.REG | 3.74719 | 880 | Latin 1 / Western European | UNKNOWN | RBIND |
WEGFETZEN.REG | 3.66697 | 532 | Latin 1 / Western European | UNKNOWN | RBIND |
DROPIN | 2.25163 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
EXEC | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.dll |
SHELL32.dll |
Total processes
49
Monitored processes
9
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3764 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1024 | "regedit.exe" "C:\Users\admin\AppData\Local\Temp\WEGFETZEN.REG" | C:\Windows\regedit.exe | — | hjhg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2032 | "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | MONACO GUCK.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.3.0.0 Modules
Quasar(PID) Process(2032) Client.exe Version1.3.0.0 C2 (2)niggahunter88-33934.portmap.io:33934 Sub_DirSubDir Install_NameClient.exe MutexQSR_MUTEX_q2Tul7nBUKmd8SX6eg Startupruntime brocker Tagwdadsa LogDirLogs Signature Certificate | |||||||||||||||
| 2220 | "C:\Users\admin\AppData\Local\Temp\hjhg.exe" | C:\Users\admin\AppData\Local\Temp\hjhg.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2272 | "regedit.exe" "C:\Users\admin\AppData\Local\Temp\TASKMANAGERDISABLER.REG" | C:\Windows\regedit.exe | hjhg.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2940 | "regedit.exe" "C:\Users\admin\AppData\Local\Temp\TASKMANAGERDISABLER.REG" | C:\Windows\regedit.exe | — | hjhg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3468 | "regedit.exe" "C:\Users\admin\AppData\Local\Temp\WEGFETZEN.REG" | C:\Windows\regedit.exe | hjhg.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3764 | "C:\Program Files\Internet Explorer\iexplore.exe" https://discord.gg/tipico | C:\Program Files\Internet Explorer\iexplore.exe | Client.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4024 | "C:\Users\admin\AppData\Local\Temp\MONACO GUCK.EXE" | C:\Users\admin\AppData\Local\Temp\MONACO GUCK.EXE | hjhg.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
Total events
17 533
Read events
17 336
Write events
195
Delete events
2
Modification events
| (PID) Process: | (2220) hjhg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2220) hjhg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2220) hjhg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2220) hjhg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4024) MONACO GUCK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MONACO GUCK_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4024) MONACO GUCK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MONACO GUCK_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4024) MONACO GUCK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MONACO GUCK_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4024) MONACO GUCK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MONACO GUCK_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4024) MONACO GUCK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MONACO GUCK_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4024) MONACO GUCK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MONACO GUCK_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
2
Suspicious files
10
Text files
31
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 836 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\076a8c1a0cc790ebd989[1].js | — | |
MD5:— | SHA256:— | |||
| 2220 | hjhg.exe | C:\Users\admin\AppData\Local\Temp\WEGFETZEN.REG | text | |
MD5:— | SHA256:— | |||
| 2220 | hjhg.exe | C:\Users\admin\AppData\Local\Temp\MONACO GUCK.EXE | executable | |
MD5:— | SHA256:— | |||
| 4024 | MONACO GUCK.EXE | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | executable | |
MD5:— | SHA256:— | |||
| 2220 | hjhg.exe | C:\Users\admin\AppData\Local\Temp\TASKMANAGERDISABLER.REG | text | |
MD5:— | SHA256:— | |||
| 836 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2032 | Client.exe | C:\Users\admin\AppData\Roaming\Logs\06-27-2022 | binary | |
MD5:— | SHA256:— | |||
| 836 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RX377O1O.txt | text | |
MD5:— | SHA256:— | |||
| 836 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 836 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\tipico[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
35
DNS requests
18
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2032 | Client.exe | GET | — | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | malicious |
3764 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
3764 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
836 | iexplore.exe | GET | 200 | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?700ddc42e20e3cb7 | ZA | compressed | 4.70 Kb | whitelisted |
3764 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
4024 | MONACO GUCK.EXE | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | binary | 285 b | malicious |
2032 | Client.exe | GET | 200 | 52.20.78.240:80 | http://api.ipify.org/ | US | text | 12 b | shared |
2032 | Client.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | binary | 285 b | malicious |
836 | iexplore.exe | GET | 200 | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?944f8d817682861a | ZA | compressed | 4.70 Kb | whitelisted |
836 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4024 | MONACO GUCK.EXE | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
2032 | Client.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
2032 | Client.exe | 104.26.14.73:80 | freegeoip.net | Cloudflare Inc | US | shared |
836 | iexplore.exe | 41.63.96.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | ZA | suspicious |
836 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
836 | iexplore.exe | 162.159.133.234:443 | discord.gg | Cloudflare Inc | — | shared |
836 | iexplore.exe | 162.159.138.232:443 | discord.com | Cloudflare Inc | — | malicious |
3764 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3764 | iexplore.exe | 162.159.138.232:443 | discord.com | Cloudflare Inc | — | malicious |
3764 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
freegeoip.net |
| malicious |
api.ipify.org |
| shared |
niggahunter88-33934.portmap.io |
| malicious |
discord.gg |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
discord.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4024 | MONACO GUCK.EXE | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
4024 | MONACO GUCK.EXE | A Network Trojan was detected | ET TROJAN Common RAT Connectivity Check Observed |
4024 | MONACO GUCK.EXE | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2032 | Client.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2032 | Client.exe | A Network Trojan was detected | ET TROJAN Common RAT Connectivity Check Observed |
2032 | Client.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2032 | Client.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to a Reverse Proxy Service Observed |
2032 | Client.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2032 | Client.exe | A Network Trojan was detected | ET TROJAN Common RAT Connectivity Check Observed |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
hjhg.exe | C:\Users\admin\AppData\Local\Temp\MONACO GUCK.EXE |
hjhg.exe | C:\Users\admin\AppData\Local\Temp\TASKMANAGERDISABLER.REG |
hjhg.exe | C:\Users\admin\AppData\Local\Temp\WEGFETZEN.REG |