| File name: | 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe |
| Full analysis: | https://app.any.run/tasks/f978c329-0d86-457e-811c-0c6d0f2fac50 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | July 19, 2025, 23:42:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 76E3B78E3FDDA7EA92024EF2CE8E30D4 |
| SHA1: | 3C12B9ED0F58AC8AC3C645E0344B82C4FFD88EE0 |
| SHA256: | 58D0C65AB1F16E4AB35A06A7A8F4BCDC82CE2A8D672A85BD223D6259D8A8B6D5 |
| SSDEEP: | 98304:byi3/nstDqRwYXwa7vwY0G8xncoKogj0YjlPuxNc64MGwQhysLBVvISXaroKbyKt:BangCiC |
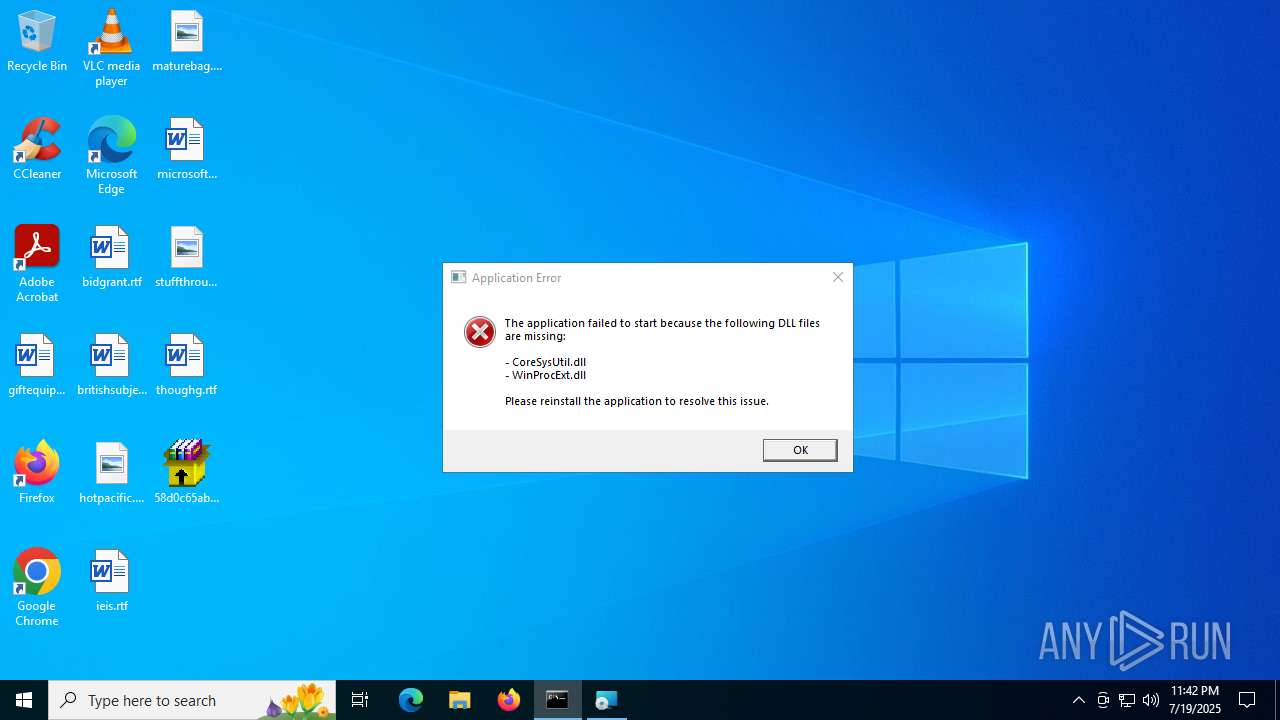
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3148)
- cmd.exe (PID: 8320)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3732)
Bypass execution policy to execute commands
- powershell.exe (PID: 5460)
AMADEY mutex has been found
- suker.exe (PID: 5628)
- ZJ9IFZso.exe (PID: 7052)
- suker.exe (PID: 4196)
- suker.exe (PID: 3936)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 4820)
- NSudoLG.exe (PID: 2504)
- TDxFgx3DG08K.exe (PID: 5548)
Changes Windows Defender settings
- NSudoLG.exe (PID: 2504)
- TDxFgx3DG08K.exe (PID: 5548)
Connects to the CnC server
- suker.exe (PID: 5628)
- Qalae.exe (PID: 7804)
- svchost.exe (PID: 2200)
AMADEY has been detected (SURICATA)
- suker.exe (PID: 5628)
- Qalae.exe (PID: 7804)
AMADEY has been detected (YARA)
- suker.exe (PID: 5628)
Steals credentials from Web Browsers
- sample_app_installer.exe (PID: 2972)
- MSBuild.exe (PID: 1944)
- C0op6ik.exe (PID: 6356)
Changes the autorun value in the registry
- suker.exe (PID: 5628)
- reg.exe (PID: 8416)
Executing a file with an untrusted certificate
- C0op6ik.exe (PID: 6356)
- XPFix.exe (PID: 7296)
- CHashra.exe (PID: 1044)
- CHashra.exe (PID: 6508)
- SpeRouter.exe (PID: 8932)
STEALC has been detected
- C0op6ik.exe (PID: 6356)
- MSBuild.exe (PID: 4688)
LUMMA mutex has been found
- MSBuild.exe (PID: 1944)
GENERIC has been found (auto)
- UnitNa.exe (PID: 1936)
Actions looks like stealing of personal data
- C0op6ik.exe (PID: 6356)
- MSBuild.exe (PID: 1944)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2200)
Run PowerShell with an invisible window
- powershell.exe (PID: 2148)
Starts CMD.EXE for self-deleting
- C0op6ik.exe (PID: 6356)
- NnBiSeDHKSCN.exe (PID: 4700)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 2028)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 8576)
Changes the Windows auto-update feature
- TDxFgx3DG08K.exe (PID: 5548)
SUSPICIOUS
Reads security settings of Internet Explorer
- 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe (PID: 5552)
- iOA41dyB.exe (PID: 4528)
- ZJ9IFZso.exe (PID: 7052)
- nircmd.exe (PID: 5952)
- suker.exe (PID: 5628)
- Unlocker.exe (PID: 1236)
- Unlocker.exe (PID: 4844)
- sample_app_installer.exe (PID: 2972)
- Unlocker.exe (PID: 7032)
- bananaz_copilot_v0.exe (PID: 4460)
- Unlocker.exe (PID: 7052)
- C0op6ik.exe (PID: 6356)
- MSBuild.exe (PID: 4688)
- Unlocker.exe (PID: 2804)
- 7Un6LSu.exe (PID: 8132)
- hRKvkgT.exe (PID: 424)
Drops 7-zip archiver for unpacking
- 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe (PID: 5552)
- iOA41dyB.exe (PID: 4528)
Executable content was dropped or overwritten
- 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe (PID: 5552)
- KYdVpXHP.exe (PID: 6808)
- iOA41dyB.exe (PID: 4528)
- ZJ9IFZso.exe (PID: 7052)
- suker.exe (PID: 5628)
- 7z.exe (PID: 6536)
- bananaz_copilot_v0.exe (PID: 4460)
- Unlocker.exe (PID: 1236)
- Unlocker.exe (PID: 7032)
- Unlocker.exe (PID: 2804)
- HZhaduP.exe (PID: 7704)
- UnitNa.exe (PID: 3740)
- UnitNa.exe (PID: 1936)
- 7Un6LSu.exe (PID: 8132)
- rw6eMTC.exe (PID: 8196)
- CHashra.exe (PID: 1044)
- CHashra.exe (PID: 6508)
- C0op6ik.exe (PID: 6356)
- OM8hqGX.exe (PID: 8700)
- NnBiSeDHKSCN.exe (PID: 4700)
- hRKvkgT.exe (PID: 424)
Starts CMD.EXE for commands execution
- JN1SLII6.exe (PID: 1508)
- iOA41dyB.exe (PID: 4528)
- nircmd.exe (PID: 5952)
- NSudoLG.exe (PID: 1028)
- cmd.exe (PID: 4820)
- Unlocker.exe (PID: 1236)
- Unlocker.exe (PID: 4844)
- Unlocker.exe (PID: 7032)
- Unlocker.exe (PID: 7052)
- Unlocker.exe (PID: 2804)
- TDxFgx3DG08K.exe (PID: 4020)
- C0op6ik.exe (PID: 6356)
- NnBiSeDHKSCN.exe (PID: 4700)
- powershell.exe (PID: 2148)
- TDxFgx3DG08K.exe (PID: 5548)
The process creates files with name similar to system file names
- iOA41dyB.exe (PID: 4528)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3732)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3732)
- NSudoLG.exe (PID: 2504)
- TDxFgx3DG08K.exe (PID: 4020)
- TDxFgx3DG08K.exe (PID: 5548)
- vRmIR1dag6.exe (PID: 7104)
Executing commands from a ".bat" file
- iOA41dyB.exe (PID: 4528)
- nircmd.exe (PID: 5952)
- NSudoLG.exe (PID: 1028)
Starts itself from another location
- ZJ9IFZso.exe (PID: 7052)
- UnitNa.exe (PID: 3740)
- 7Un6LSu.exe (PID: 8132)
- CHashra.exe (PID: 1044)
The executable file from the user directory is run by the CMD process
- nircmd.exe (PID: 6344)
- nircmd.exe (PID: 5952)
- nircmd.exe (PID: 4372)
- NSudoLG.exe (PID: 1028)
- nircmd.exe (PID: 6812)
- NSudoLG.exe (PID: 2504)
- 7z.exe (PID: 6536)
- Unlocker.exe (PID: 4844)
- Unlocker.exe (PID: 1236)
- Unlocker.exe (PID: 7032)
- Unlocker.exe (PID: 7052)
- Unlocker.exe (PID: 2804)
- TDxFgx3DG08K.exe (PID: 5548)
Starts application with an unusual extension
- cmd.exe (PID: 4984)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 4820)
Reads the date of Windows installation
- nircmd.exe (PID: 5952)
- Unlocker.exe (PID: 4844)
- Unlocker.exe (PID: 1236)
- bananaz_copilot_v0.exe (PID: 4460)
- Unlocker.exe (PID: 7032)
- Unlocker.exe (PID: 7052)
- Unlocker.exe (PID: 2804)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3620)
- cmd.exe (PID: 4820)
- powershell.exe (PID: 1352)
Application launched itself
- cmd.exe (PID: 4820)
- OM8hqGX.exe (PID: 2632)
- updater.exe (PID: 4724)
- updater.exe (PID: 8436)
Get information on the list of running processes
- cmd.exe (PID: 4820)
- cmd.exe (PID: 7080)
Script adds exclusion path to Windows Defender
- NSudoLG.exe (PID: 2504)
- TDxFgx3DG08K.exe (PID: 5548)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 2588)
Contacting a server suspected of hosting an CnC
- suker.exe (PID: 5628)
- Qalae.exe (PID: 7804)
- svchost.exe (PID: 2200)
Connects to the server without a host name
- suker.exe (PID: 5628)
- C0op6ik.exe (PID: 6356)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4820)
Starts SC.EXE for service management
- cmd.exe (PID: 6764)
- cmd.exe (PID: 6164)
- cmd.exe (PID: 984)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 1236)
- cmd.exe (PID: 5468)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 4820)
- TDxFgx3DG08K.exe (PID: 5548)
Windows service management via SC.EXE
- sc.exe (PID: 6304)
- sc.exe (PID: 2276)
- sc.exe (PID: 7016)
- sc.exe (PID: 3288)
- sc.exe (PID: 4708)
- sc.exe (PID: 1800)
- sc.exe (PID: 7016)
- sc.exe (PID: 7380)
- sc.exe (PID: 7280)
- sc.exe (PID: 7488)
- sc.exe (PID: 7616)
- sc.exe (PID: 7636)
- sc.exe (PID: 4164)
- sc.exe (PID: 8496)
- sc.exe (PID: 5992)
- sc.exe (PID: 8276)
- sc.exe (PID: 6220)
- sc.exe (PID: 1352)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 700)
- cmd.exe (PID: 6264)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 7516)
Creates or modifies Windows services
- Unlocker.exe (PID: 1236)
- Unlocker.exe (PID: 7052)
- Unlocker.exe (PID: 2804)
Drops a system driver (possible attempt to evade defenses)
- Unlocker.exe (PID: 1236)
- Unlocker.exe (PID: 7032)
- Unlocker.exe (PID: 2804)
Stops a currently running service
- sc.exe (PID: 1132)
- sc.exe (PID: 4836)
- sc.exe (PID: 4036)
- sc.exe (PID: 7360)
- sc.exe (PID: 7468)
- sc.exe (PID: 8020)
- sc.exe (PID: 3640)
- sc.exe (PID: 8432)
- sc.exe (PID: 7632)
- sc.exe (PID: 5264)
- sc.exe (PID: 4264)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4820)
- cmd.exe (PID: 3148)
- cmd.exe (PID: 8892)
There is functionality for taking screenshot (YARA)
- suker.exe (PID: 5628)
There is functionality for enable RDP (YARA)
- suker.exe (PID: 5628)
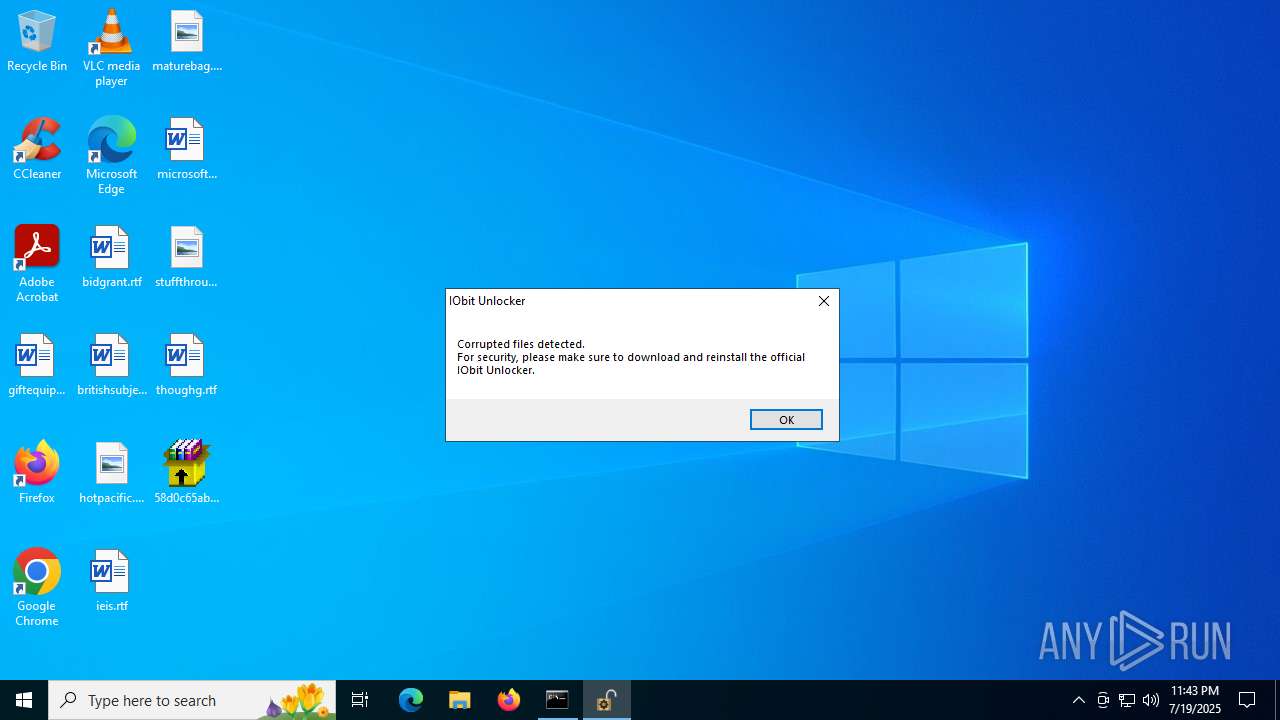
The process verifies whether the antivirus software is installed
- Unlocker.exe (PID: 7032)
- IObitUnlocker.exe (PID: 6524)
Process requests binary or script from the Internet
- suker.exe (PID: 5628)
- C0op6ik.exe (PID: 6356)
Potential Corporate Privacy Violation
- suker.exe (PID: 5628)
- C0op6ik.exe (PID: 6356)
Reads the BIOS version
- C0op6ik.exe (PID: 6356)
- YT1For2.exe (PID: 3896)
- TDxFgx3DG08K.exe (PID: 4020)
- TDxFgx3DG08K.exe (PID: 5548)
Searches for installed software
- C0op6ik.exe (PID: 6356)
- D2pSNtR.exe (PID: 188)
Connects to unusual port
- MSBuild.exe (PID: 6964)
The process executes via Task Scheduler
- suker.exe (PID: 4196)
- suker.exe (PID: 3936)
- Qalae.exe (PID: 6288)
Executes application which crashes
- YT1For2.exe (PID: 3896)
Process drops legitimate windows executable
- HZhaduP.exe (PID: 7704)
- UnitNa.exe (PID: 3740)
- rw6eMTC.exe (PID: 8196)
- CHashra.exe (PID: 1044)
- C0op6ik.exe (PID: 6356)
- NnBiSeDHKSCN.exe (PID: 4700)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- D2pSNtR.exe (PID: 188)
The process drops C-runtime libraries
- rw6eMTC.exe (PID: 8196)
- CHashra.exe (PID: 1044)
Manipulates environment variables
- powershell.exe (PID: 6152)
- powershell.exe (PID: 7680)
- powershell.exe (PID: 2968)
Loads DLL from Mozilla Firefox
- C0op6ik.exe (PID: 6356)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 4788)
- cmd.exe (PID: 4100)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 8368)
- net.exe (PID: 8304)
- cmd.exe (PID: 2596)
- net.exe (PID: 2140)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 8288)
Starts process via Powershell
- powershell.exe (PID: 2148)
- powershell.exe (PID: 3092)
Hides command output
- cmd.exe (PID: 8892)
Process uninstalls Windows update
- wusa.exe (PID: 7204)
The process deletes folder without confirmation
- TDxFgx3DG08K.exe (PID: 5548)
INFO
Checks supported languages
- 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe (PID: 5552)
- JN1SLII6.exe (PID: 1508)
- KYdVpXHP.exe (PID: 6808)
- ZJ9IFZso.exe (PID: 7052)
- iOA41dyB.exe (PID: 4528)
- suker.exe (PID: 5628)
- chcp.com (PID: 6812)
- nircmd.exe (PID: 5952)
- nircmd.exe (PID: 6344)
- NSudoLG.exe (PID: 1028)
- nircmd.exe (PID: 4372)
- chcp.com (PID: 1192)
- chcp.com (PID: 3840)
- nircmd.exe (PID: 6812)
- mode.com (PID: 1964)
- NSudoLG.exe (PID: 2504)
- bananaz_copilot_v0.exe (PID: 4460)
- 7z.exe (PID: 6536)
- Unlocker.exe (PID: 4844)
- Unlocker.exe (PID: 1236)
- sample_app_installer.exe (PID: 2972)
- Unlocker.exe (PID: 7032)
- random2.exe (PID: 6760)
- Unlocker.exe (PID: 7052)
- IObitUnlocker.exe (PID: 6524)
- MSBuild.exe (PID: 1944)
- OT5TCkJ.exe (PID: 4232)
- C0op6ik.exe (PID: 6356)
- QvG0bbo.exe (PID: 6976)
- MSBuild.exe (PID: 6964)
- suker.exe (PID: 4196)
- i8kSMr9.exe (PID: 3624)
- MSBuild.exe (PID: 4688)
- IObitUnlocker.exe (PID: 4012)
- YT1For2.exe (PID: 3896)
- Unlocker.exe (PID: 2804)
- 7Un6LSu.exe (PID: 8132)
- Qalae.exe (PID: 7804)
- suker.exe (PID: 3936)
- Qalae.exe (PID: 6288)
- rw6eMTC.exe (PID: 8196)
- RenT7Wg.exe (PID: 8416)
- MSBuild.exe (PID: 8464)
- SpeRouter.exe (PID: 8932)
- OM8hqGX.exe (PID: 2632)
- OM8hqGX.exe (PID: 8700)
- TDxFgx3DG08K.exe (PID: 4020)
- NnBiSeDHKSCN.exe (PID: 4700)
- updater.exe (PID: 8436)
- TDxFgx3DG08K.exe (PID: 5548)
- updater.exe (PID: 4724)
- vRmIR1dag6.exe (PID: 7104)
- NAqjOgnlZY.exe (PID: 6400)
- updater.exe (PID: 4832)
- hRKvkgT.exe (PID: 424)
- vRmIR1dag6.exe (PID: 8200)
- updater.exe (PID: 2320)
Reads the computer name
- 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe (PID: 5552)
- KYdVpXHP.exe (PID: 6808)
- ZJ9IFZso.exe (PID: 7052)
- nircmd.exe (PID: 5952)
- suker.exe (PID: 5628)
- NSudoLG.exe (PID: 1028)
- iOA41dyB.exe (PID: 4528)
- NSudoLG.exe (PID: 2504)
- bananaz_copilot_v0.exe (PID: 4460)
- 7z.exe (PID: 6536)
- Unlocker.exe (PID: 4844)
- Unlocker.exe (PID: 1236)
- sample_app_installer.exe (PID: 2972)
- Unlocker.exe (PID: 7032)
- random2.exe (PID: 6760)
- Unlocker.exe (PID: 7052)
- MSBuild.exe (PID: 1944)
- C0op6ik.exe (PID: 6356)
- MSBuild.exe (PID: 6964)
- MSBuild.exe (PID: 4688)
- YT1For2.exe (PID: 3896)
- IObitUnlocker.exe (PID: 4012)
- Unlocker.exe (PID: 2804)
- IObitUnlocker.exe (PID: 6524)
- 7Un6LSu.exe (PID: 8132)
- Qalae.exe (PID: 7804)
- TurboMi.exe (PID: 1132)
- rw6eMTC.exe (PID: 8196)
- MSBuild.exe (PID: 8464)
- SpeRouter.exe (PID: 8932)
- NnBiSeDHKSCN.exe (PID: 4700)
- hRKvkgT.exe (PID: 424)
- NAqjOgnlZY.exe (PID: 6400)
Process checks computer location settings
- 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe (PID: 5552)
- iOA41dyB.exe (PID: 4528)
- ZJ9IFZso.exe (PID: 7052)
- nircmd.exe (PID: 5952)
- suker.exe (PID: 5628)
- bananaz_copilot_v0.exe (PID: 4460)
- 7Un6LSu.exe (PID: 8132)
- C0op6ik.exe (PID: 6356)
- hRKvkgT.exe (PID: 424)
The sample compiled with english language support
- 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe (PID: 5552)
- iOA41dyB.exe (PID: 4528)
- Unlocker.exe (PID: 1236)
- Unlocker.exe (PID: 7032)
- Unlocker.exe (PID: 2804)
- HZhaduP.exe (PID: 7704)
- UnitNa.exe (PID: 3740)
- rw6eMTC.exe (PID: 8196)
- CHashra.exe (PID: 1044)
- CHashra.exe (PID: 6508)
- C0op6ik.exe (PID: 6356)
- NnBiSeDHKSCN.exe (PID: 4700)
Reads mouse settings
- JN1SLII6.exe (PID: 1508)
Create files in a temporary directory
- ZJ9IFZso.exe (PID: 7052)
- iOA41dyB.exe (PID: 4528)
- suker.exe (PID: 5628)
- 7z.exe (PID: 6536)
- bananaz_copilot_v0.exe (PID: 4460)
- sample_app_installer.exe (PID: 2972)
- 7Un6LSu.exe (PID: 8132)
- CHashra.exe (PID: 6508)
- rw6eMTC.exe (PID: 8196)
- OM8hqGX.exe (PID: 8700)
- UnitNa.exe (PID: 1936)
NirSoft software is detected
- nircmd.exe (PID: 6344)
- nircmd.exe (PID: 5952)
- nircmd.exe (PID: 4372)
- nircmd.exe (PID: 6812)
Changes the display of characters in the console
- cmd.exe (PID: 4984)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 4820)
Checks operating system version
- cmd.exe (PID: 4820)
Starts MODE.COM to configure console settings
- mode.com (PID: 1964)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5460)
- powershell.exe (PID: 2588)
- powershell.exe (PID: 6152)
- powershell.exe (PID: 2604)
- powershell.exe (PID: 7680)
Reads the machine GUID from the registry
- suker.exe (PID: 5628)
- bananaz_copilot_v0.exe (PID: 4460)
- Unlocker.exe (PID: 4844)
- Unlocker.exe (PID: 1236)
- sample_app_installer.exe (PID: 2972)
- Unlocker.exe (PID: 7032)
- Unlocker.exe (PID: 7052)
- MSBuild.exe (PID: 1944)
- MSBuild.exe (PID: 6964)
- Unlocker.exe (PID: 2804)
- TurboMi.exe (PID: 1132)
Reads the software policy settings
- suker.exe (PID: 5628)
- bananaz_copilot_v0.exe (PID: 4460)
- sample_app_installer.exe (PID: 2972)
- MSBuild.exe (PID: 1944)
- WerFault.exe (PID: 7156)
- TurboMi.exe (PID: 1132)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2588)
- powershell.exe (PID: 6152)
- powershell.exe (PID: 2604)
- powershell.exe (PID: 7680)
Creates files or folders in the user directory
- suker.exe (PID: 5628)
- bananaz_copilot_v0.exe (PID: 4460)
- WerFault.exe (PID: 7156)
- UnitNa.exe (PID: 1936)
- C0op6ik.exe (PID: 6356)
- OM8hqGX.exe (PID: 8700)
- NnBiSeDHKSCN.exe (PID: 4700)
- hRKvkgT.exe (PID: 424)
Checks proxy server information
- suker.exe (PID: 5628)
- bananaz_copilot_v0.exe (PID: 4460)
- C0op6ik.exe (PID: 6356)
- MSBuild.exe (PID: 4688)
- WerFault.exe (PID: 7156)
Reads Environment values
- sample_app_installer.exe (PID: 2972)
Launching a file from a Registry key
- suker.exe (PID: 5628)
- reg.exe (PID: 8416)
Reads CPU info
- C0op6ik.exe (PID: 6356)
Manual execution by a user
- IObitUnlocker.exe (PID: 700)
- IObitUnlocker.exe (PID: 4012)
- WINWORD.EXE (PID: 7372)
- powershell.exe (PID: 6152)
- cmd.exe (PID: 4788)
- powershell.exe (PID: 1352)
- dialer.exe (PID: 8752)
- powershell.exe (PID: 8288)
- cmd.exe (PID: 8324)
- updater.exe (PID: 8436)
- powershell.exe (PID: 7680)
- powershell.exe (PID: 7540)
- cmd.exe (PID: 4100)
- powershell.exe (PID: 2968)
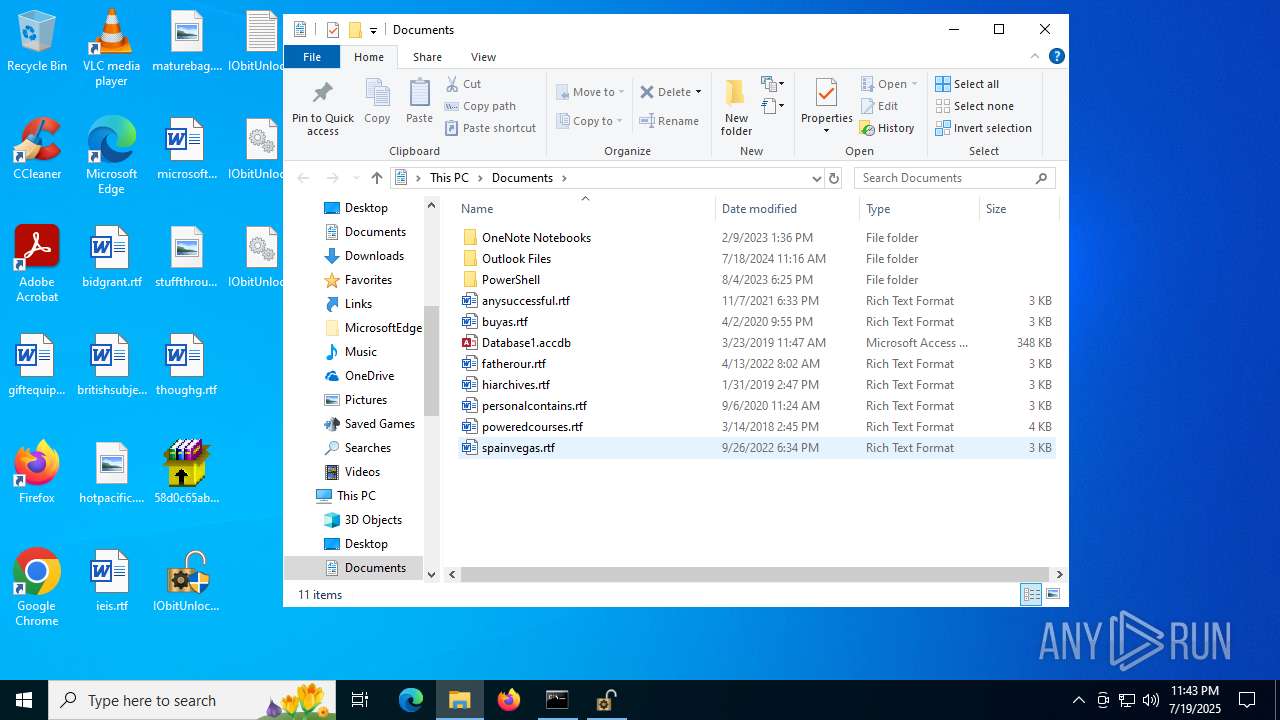
Creates files in the program directory
- IObitUnlocker.exe (PID: 4012)
- C0op6ik.exe (PID: 6356)
- UnitNa.exe (PID: 1936)
Application launched itself
- chrome.exe (PID: 2400)
- chrome.exe (PID: 7452)
- chrome.exe (PID: 1044)
- chrome.exe (PID: 7604)
- msedge.exe (PID: 7976)
- msedge.exe (PID: 5352)
- msedge.exe (PID: 7156)
- msedge.exe (PID: 7668)
- msedge.exe (PID: 7664)
- msedge.exe (PID: 7820)
- chrome.exe (PID: 3288)
The sample compiled with chinese language support
- HZhaduP.exe (PID: 7704)
- UnitNa.exe (PID: 3740)
- UnitNa.exe (PID: 1936)
Process checks whether UAC notifications are on
- TDxFgx3DG08K.exe (PID: 5548)
The executable file from the user directory is run by the Powershell process
- vRmIR1dag6.exe (PID: 8200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(5628) suker.exe
C2176.46.157.50
URLhttp://176.46.157.50/tu3d2rom/index.php
Version5.50
Options
Drop directorybd4cae89c3
Drop namesuker.exe
Strings (125)Rem
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
vs:
un:
ps1
DefaultSettings.XResolution
Content-Type: multipart/form-data; boundary=----
pc:
msi
/Plugins/
\
os:
&unit=
%USERPROFILE%
VideoID
&& Exit"
/k
e3
/tu3d2rom/index.php
.jpg
Keyboard Layout\Preload
bi:
------
------
dm:
AVG
Main
Sophos
GET
2022
Norton
5.50
dll
wb
<c>
00000419
"
Content-Type: application/octet-stream
abcdefghijklmnopqrstuvwxyz0123456789-_
SOFTWARE\Microsoft\Windows NT\CurrentVersion
POST
Powershell.exe
Content-Type: application/x-www-form-urlencoded
st=s
Bitdefender
rb
-unicode-
GetNativeSystemInfo
shutdown -s -t 0
"taskkill /f /im "
|
e2
shell32.dll
sd:
S-%lu-
360TotalSecurity
Kaspersky Lab
exe
/quiet
Content-Disposition: form-data; name="data"; filename="
og:
suker.exe
Programs
ESET
zip
random
clip.dll
r=
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
CurrentBuild
00000423
cred.dll
2019
bd4cae89c3
:::
DefaultSettings.YResolution
ProductName
WinDefender
cmd /C RMDIR /s/q
av:
Doctor Web
2025
" && timeout 1 && del
e1
-executionpolicy remotesigned -File "
0000043f
" && ren
cred.dll|clip.dll|
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
http://
176.46.157.50
&&
"
Startup
0123456789
id:
SYSTEM\ControlSet001\Services\BasicDisplay\Video
ProgramData\
kernel32.dll
#
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
?scr=1
Panda Security
\0000
-%lu
lv:
<d>
--
00000422
ar:
https://
=
Comodo
ComputerName
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
rundll32
2016
%-lu
cmd
+++
AVAST Software
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
\App
rundll32.exe
Avira
d1
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 77312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
537
Monitored processes
384
Malicious processes
33
Suspicious processes
22
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | "C:\Users\admin\AppData\Local\Temp\10137250101\D2pSNtR.exe" | C:\Users\admin\AppData\Local\Temp\10137250101\D2pSNtR.exe | suker.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 320 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | "C:\Users\admin\AppData\Local\Temp\10137290101\hRKvkgT.exe" | C:\Users\admin\AppData\Local\Temp\10137290101\hRKvkgT.exe | suker.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2140,i,5642839600094247807,13712817022039328993,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2184 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 700 | "C:\Windows\System32\cmd.exe" /c taskkill /f /pid "4844" | C:\Windows\System32\cmd.exe | — | Unlocker.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 700 | "C:\Users\admin\Desktop\IObitUnlocker.exe" | C:\Users\admin\Desktop\IObitUnlocker.exe | — | explorer.exe | |||||||||||
User: admin Company: IObit Information Technology Integrity Level: MEDIUM Description: Unlocker Exit code: 3221226540 Version: 1.6.0.16 Modules
| |||||||||||||||
| 700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4204,i,6962515140738735758,7992621193860428498,262144 --variations-seed-version --mojo-platform-channel-handle=4228 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 828 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
144 124
Read events
143 618
Write events
470
Delete events
36
Modification events
| (PID) Process: | (5952) nircmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (5952) nircmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (2120) reg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize |
| Operation: | write | Name: | AppsUseLightTheme |
Value: 0 | |||
| (PID) Process: | (5288) reg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize |
| Operation: | write | Name: | AppsUseLightTheme |
Value: 0 | |||
| (PID) Process: | (5628) suker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5628) suker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5628) suker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4460) bananaz_copilot_v0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4460) bananaz_copilot_v0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4460) bananaz_copilot_v0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
142
Suspicious files
643
Text files
332
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4528 | iOA41dyB.exe | C:\Users\admin\AppData\Local\Temp\Work\7z.exe | executable | |
MD5:426CCB645E50A3143811CFA0E42E2BA6 | SHA256:CF878BFBD9ED93DC551AC038AFF8A8BBA4C935DDF8D48E62122BDDFDB3E08567 | |||
| 5552 | 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe | C:\LeMZVDT\xWEoyEAl.zip | compressed | |
MD5:B0D8B45649AA2DE3E65A99151A9546F9 | SHA256:1D8CAD6B9FE98871D65CA65A5E7654F658C6CE47DF5682F3D2F3D176E92D9F1F | |||
| 5552 | 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe | C:\LeMZVDT\KYdVpXHP.exe | executable | |
MD5:426CCB645E50A3143811CFA0E42E2BA6 | SHA256:CF878BFBD9ED93DC551AC038AFF8A8BBA4C935DDF8D48E62122BDDFDB3E08567 | |||
| 6808 | KYdVpXHP.exe | C:\LeMZVDT\iOA41dyB.exe | executable | |
MD5:F92E0CB48B07FDF0E13A19A52341AE82 | SHA256:A331AAEF86BC0B1313A909B9EB7C211839DAEF0F6FCEF1BFD83CB5F1172FFCA6 | |||
| 4528 | iOA41dyB.exe | C:\Users\admin\AppData\Local\Temp\Work\DKT.zip | compressed | |
MD5:18D343413A871834B55B87F9F6D5055E | SHA256:F5C80FC85EBF077392FF6B1EDE4A42E8E891F59BC16CF1292F37FAB05FE9400C | |||
| 4528 | iOA41dyB.exe | C:\Users\admin\AppData\Local\Temp\Work\nircmd.exe | executable | |
MD5:4A9DA765FD91E80DECFD2C9FE221E842 | SHA256:2E81E048AB419FDC6E5F4336A951BD282ED6B740048DC38D7673678EE3490CDA | |||
| 5460 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B41A67598AFB38DEC192EA6258811D07 | SHA256:B35D59B974FD0A19F04219BC1280F570E0003A135DDD99E8A41C2A5FFDCC9F89 | |||
| 5552 | 58d0c65ab1f16e4ab35a06a7a8f4bcdc82ce2a8d672a85bd223d6259d8a8b6d5.exe | C:\LeMZVDT\JN1SLII6.exe | executable | |
MD5:569F166F8A9FA3CFC0B85E93C43341D3 | SHA256:5462D351EED63AD64EA7F21F51743AD53E217F619DEA20B2C24A699486305BBB | |||
| 5460 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_n1cpop4o.flm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4528 | iOA41dyB.exe | C:\Users\admin\AppData\Local\Temp\sjrWp3r.bat | text | |
MD5:F06B802A647D148B7104E382DC0B7ED8 | SHA256:C4B0E7467D03AB117A70EB53478AD27F4E3795678519EBF352D1550A9CB12D1D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
227
TCP/UDP connections
219
DNS requests
152
Threats
68
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
188 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5628 | suker.exe | POST | 200 | 176.46.157.50:80 | http://176.46.157.50/tu3d2rom/index.php | unknown | — | — | malicious |
5628 | suker.exe | POST | 200 | 176.46.157.50:80 | http://176.46.157.50/tu3d2rom/index.php | unknown | — | — | malicious |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5628 | suker.exe | POST | 200 | 176.46.157.50:80 | http://176.46.157.50/tu3d2rom/index.php | unknown | — | — | malicious |
— | — | GET | 200 | 95.217.221.176:443 | https://mybrainscanner.com/assets/web/assets/cookies-alert-plugin/tools/newtools/prioryti/expired/new/versionfiveone/test/bananaz_copilot_v0.1.2_beta.exe | unknown | executable | 163 Kb | unknown |
5628 | suker.exe | GET | 200 | 176.46.157.32:80 | http://176.46.157.32/test/exe/random2.exe | unknown | — | — | malicious |
5628 | suker.exe | POST | 200 | 176.46.157.50:80 | http://176.46.157.50/tu3d2rom/index.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
188 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
188 | RUXIMICS.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
mybrainscanner.com |
| unknown |
cooawbi.top |
| malicious |
thoqp.lat |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
sleaqwad.shop |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5628 | suker.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
5628 | suker.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
5628 | suker.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO Packed Executable Download |
— | — | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
— | — | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO Observed UA-CPU Header |
5628 | suker.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
Process | Message |
|---|---|
IObitUnlocker.exe | PostAction_Delete |
IObitUnlocker.exe | FileCount:263 |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender Advanced Threat Protection-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Security Health-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Storage Health-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender Advanced Threat Protection-------- |
IObitUnlocker.exe | C:\Program Files\Windows Security-------- |
IObitUnlocker.exe | C:\Program Files\PCHealthCheck-------- |