| File name: | hah.exe |
| Full analysis: | https://app.any.run/tasks/8685f8f6-3ac6-4fcb-b723-f1eb0704d999 |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | August 05, 2023, 07:46:27 |
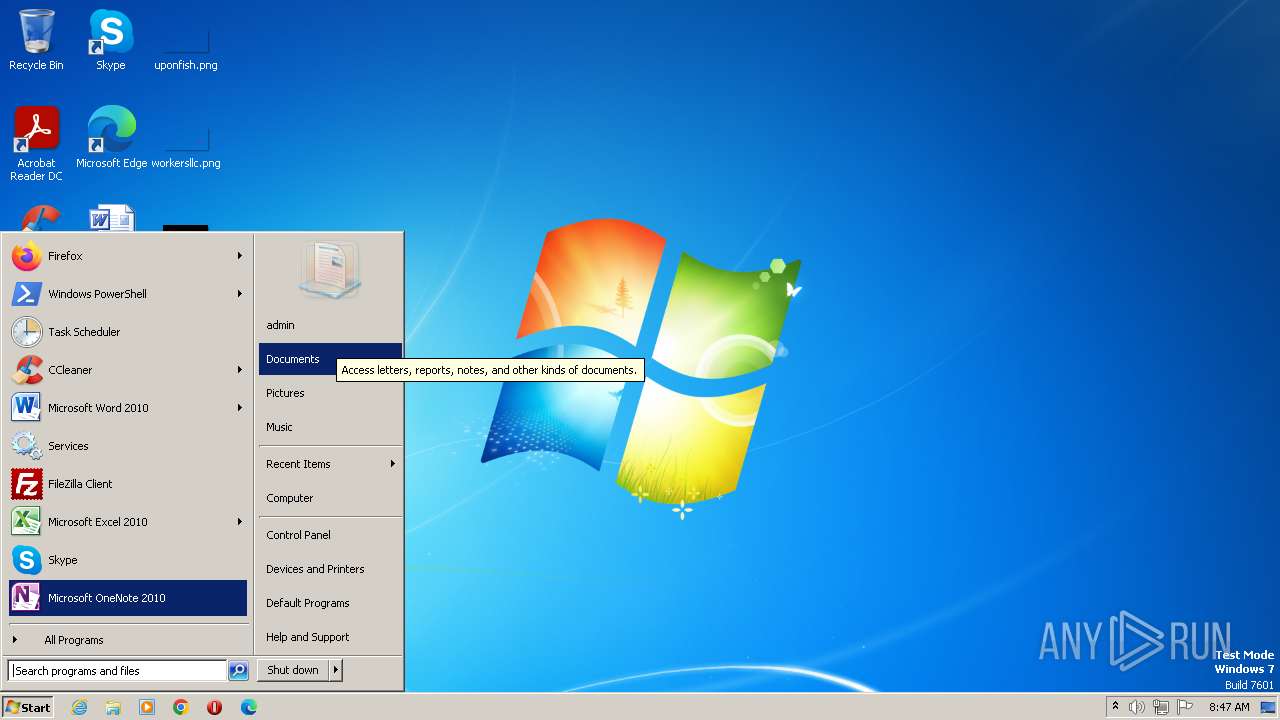
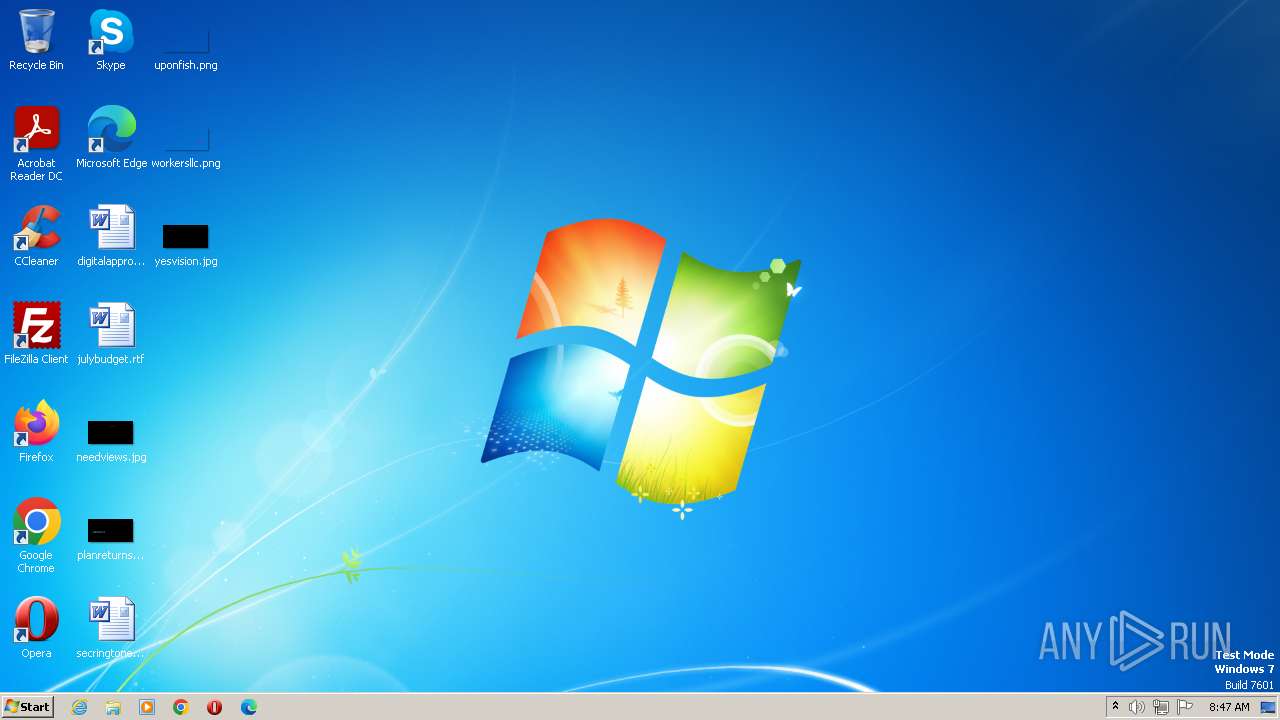
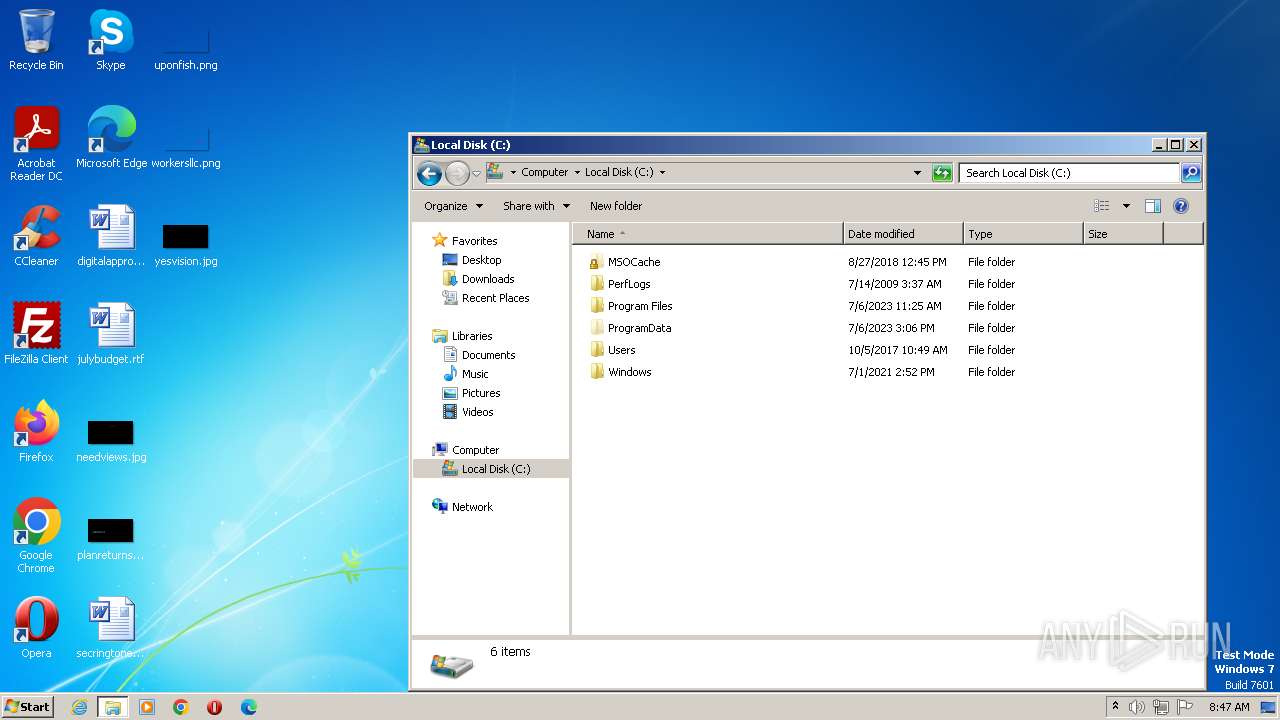
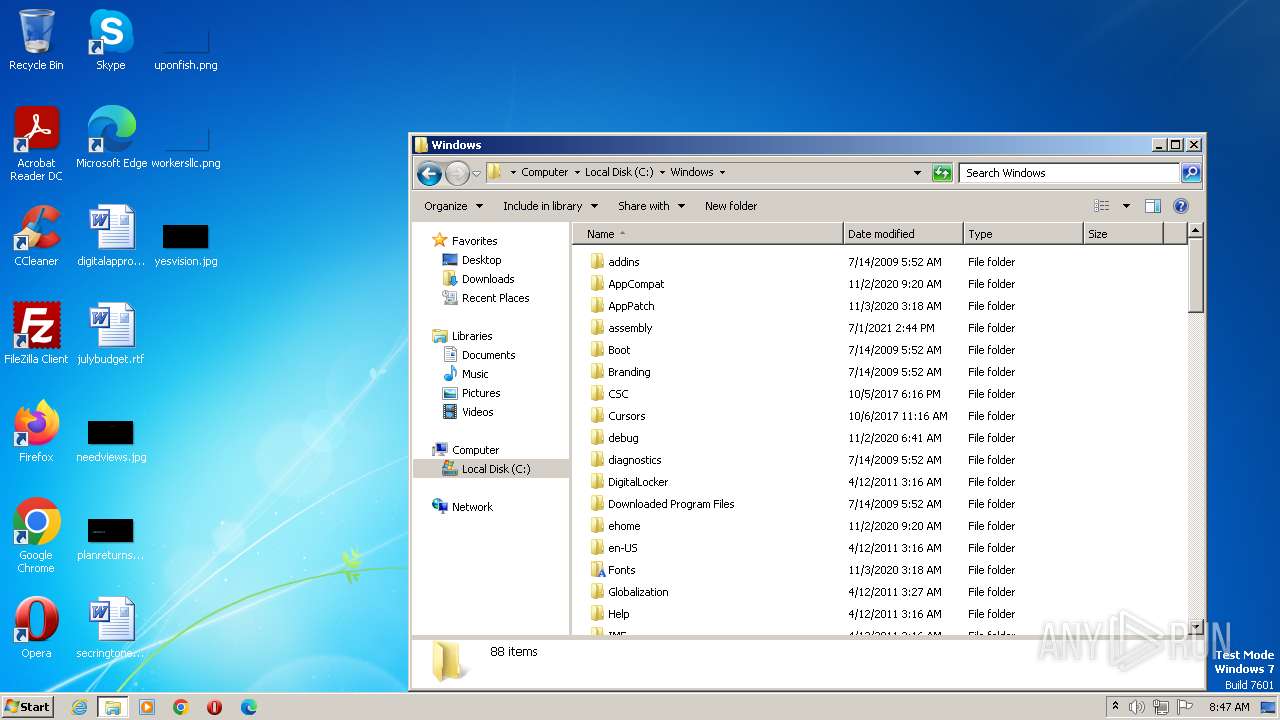
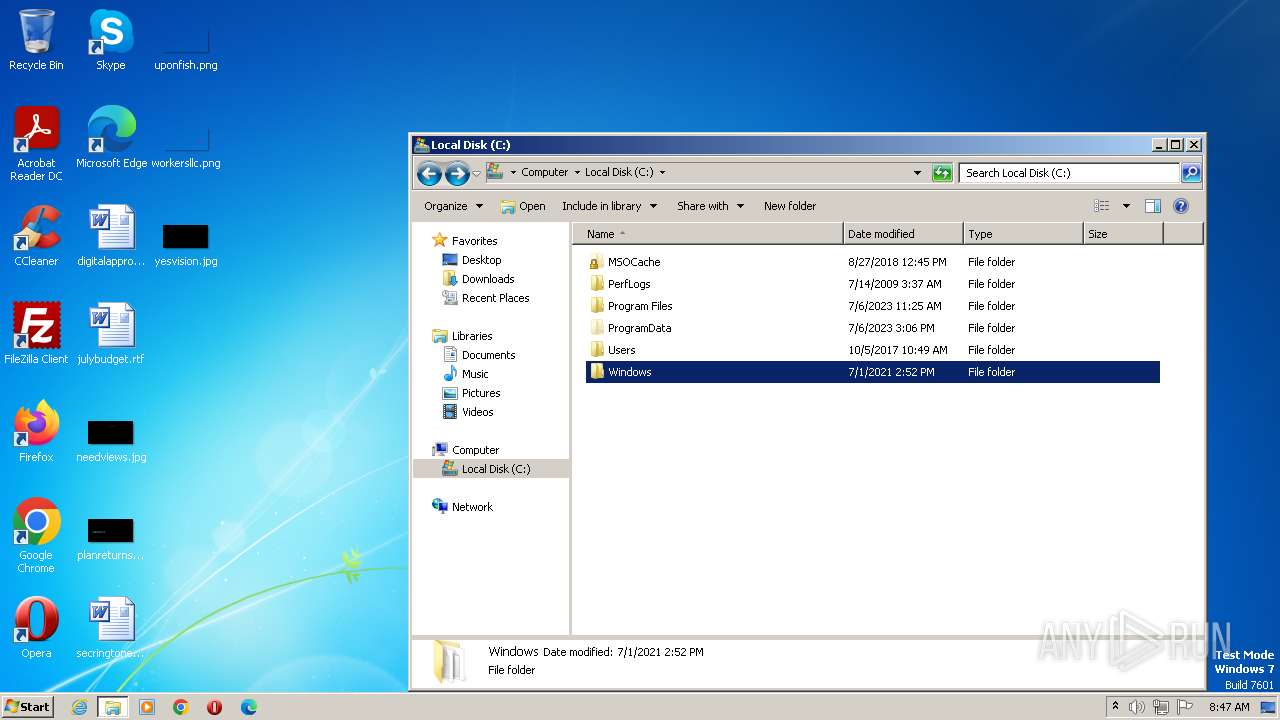
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 51A72CBA85E56E68571F1737A3867248 |
| SHA1: | CD1343921939FB80BA0CC335F6A96E9C25F7F8A4 |
| SHA256: | 57EA66A57F97ECEE958CCA1C7379025750C23BA98EA6DCFAAE17FC5F64C9D1C5 |
| SSDEEP: | 12288:WLshChMwzLdh+fF7dG1lFlWcYT70pxnnaaoawhmm6vgWrJprZNrI0AilFEvxHvB0:mLc4MROxnF664GprZlI0AilFEvxHit1 |
MALICIOUS
Orcus is detected
- hah.exe (PID: 3568)
- javaUpdate.exe (PID: 2804)
- javaUpdate.exe (PID: 3360)
Starts Visual C# compiler
- hah.exe (PID: 3568)
Creates a writable file the system directory
- hah.exe (PID: 3568)
- WindowsInput.exe (PID: 2164)
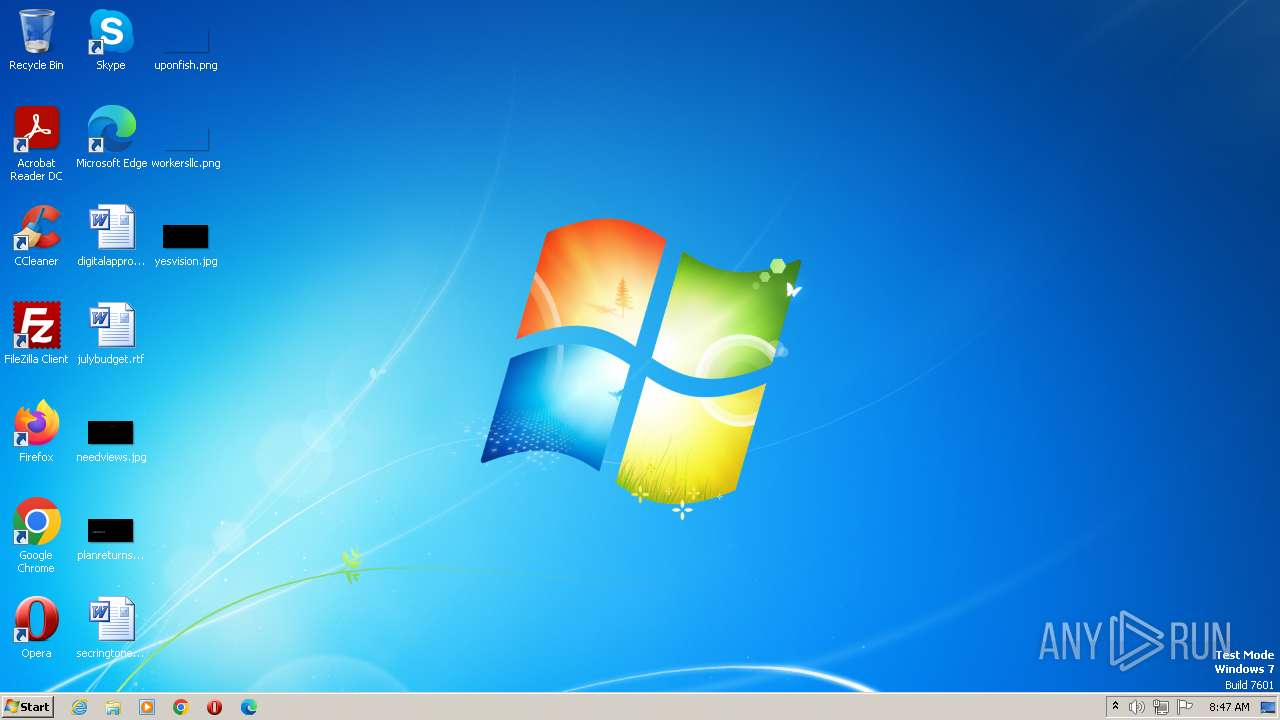
Application was dropped or rewritten from another process
- WindowsInput.exe (PID: 2164)
- WindowsInput.exe (PID: 3908)
ORCUS detected by memory dumps
- javaUpdate.exe (PID: 2804)
SUSPICIOUS
Uses .NET C# to load dll
- hah.exe (PID: 3568)
Executable content was dropped or overwritten
- hah.exe (PID: 3568)
- csc.exe (PID: 1108)
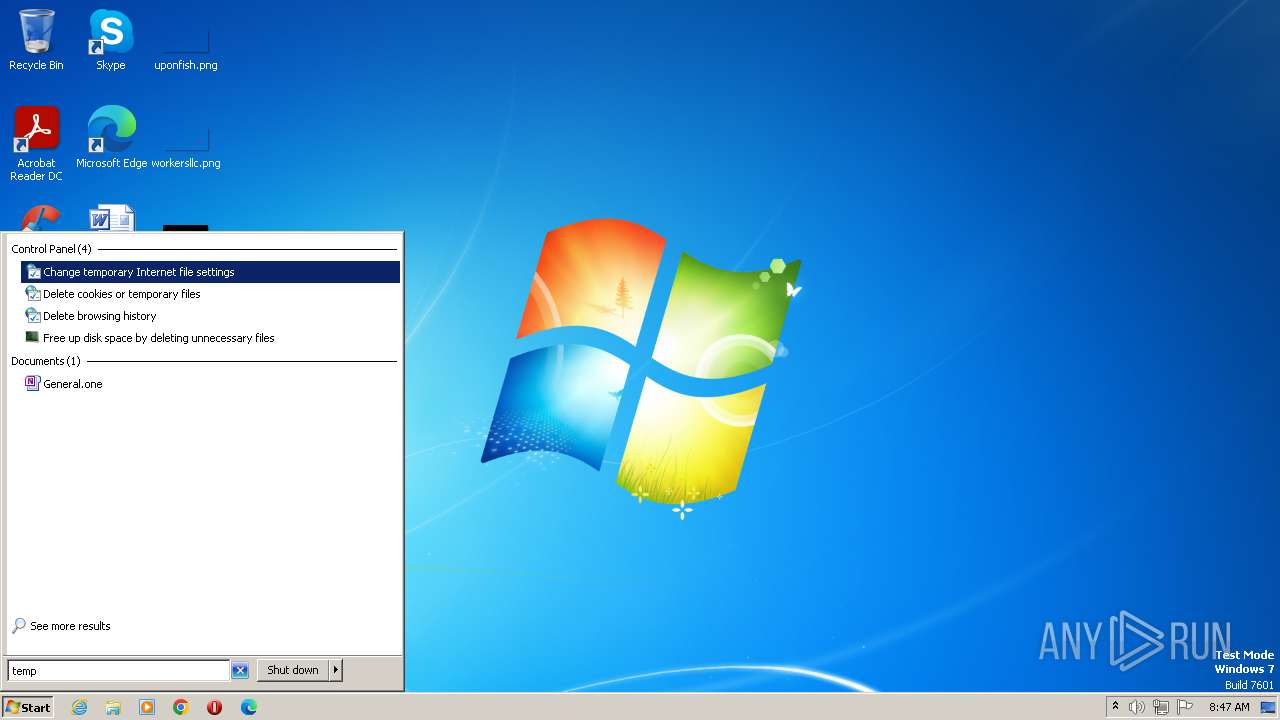
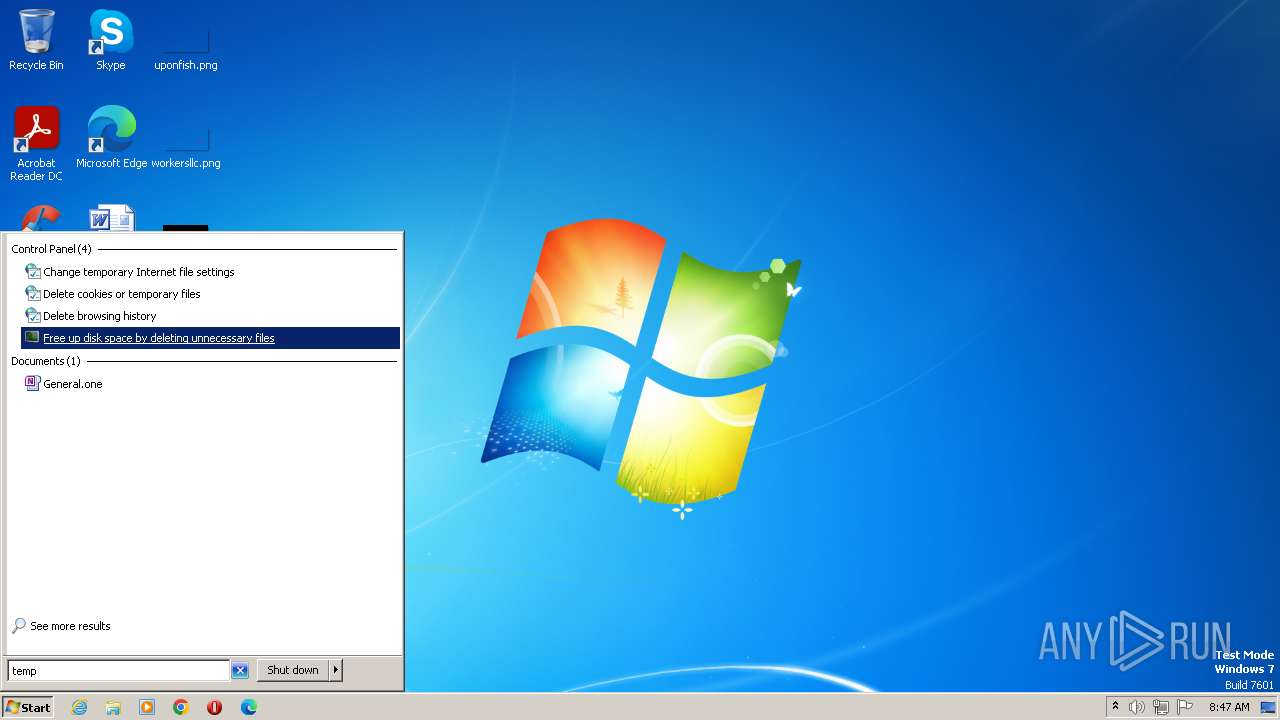
Reads the Internet Settings
- hah.exe (PID: 3568)
- WindowsInput.exe (PID: 2164)
- javaUpdate.exe (PID: 2804)
Starts itself from another location
- hah.exe (PID: 3568)
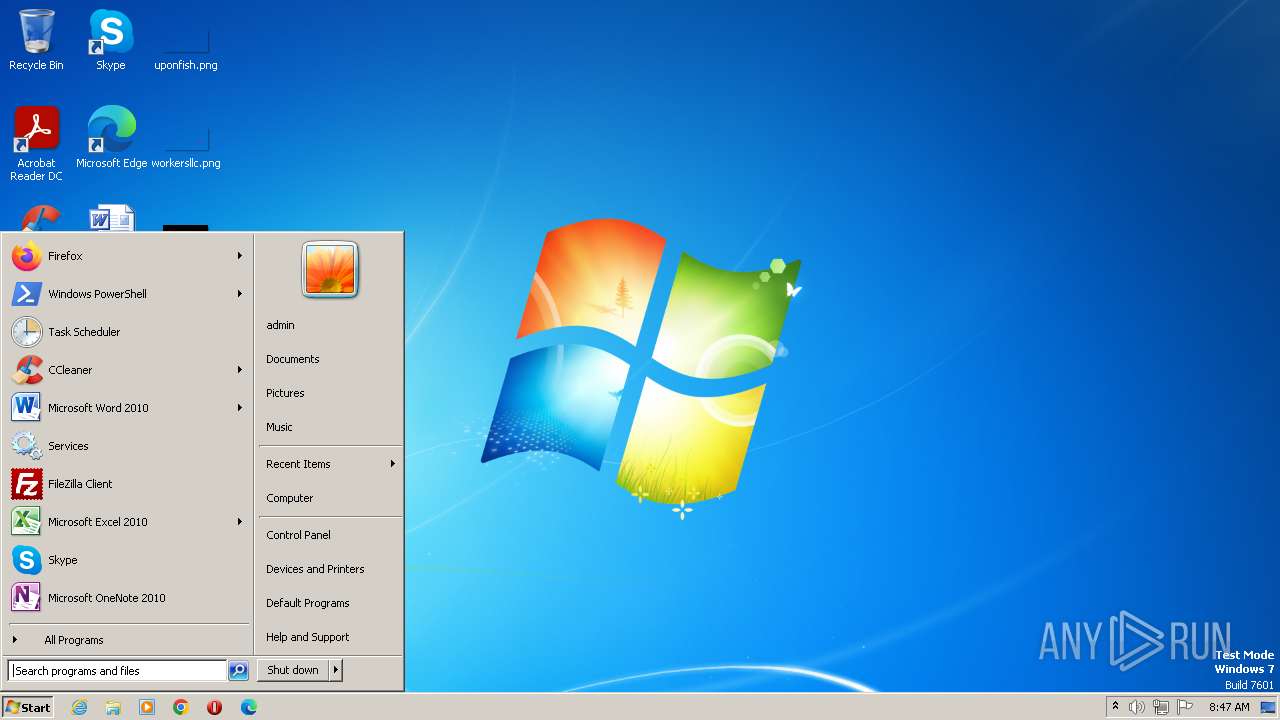
Executes as Windows Service
- WindowsInput.exe (PID: 3908)
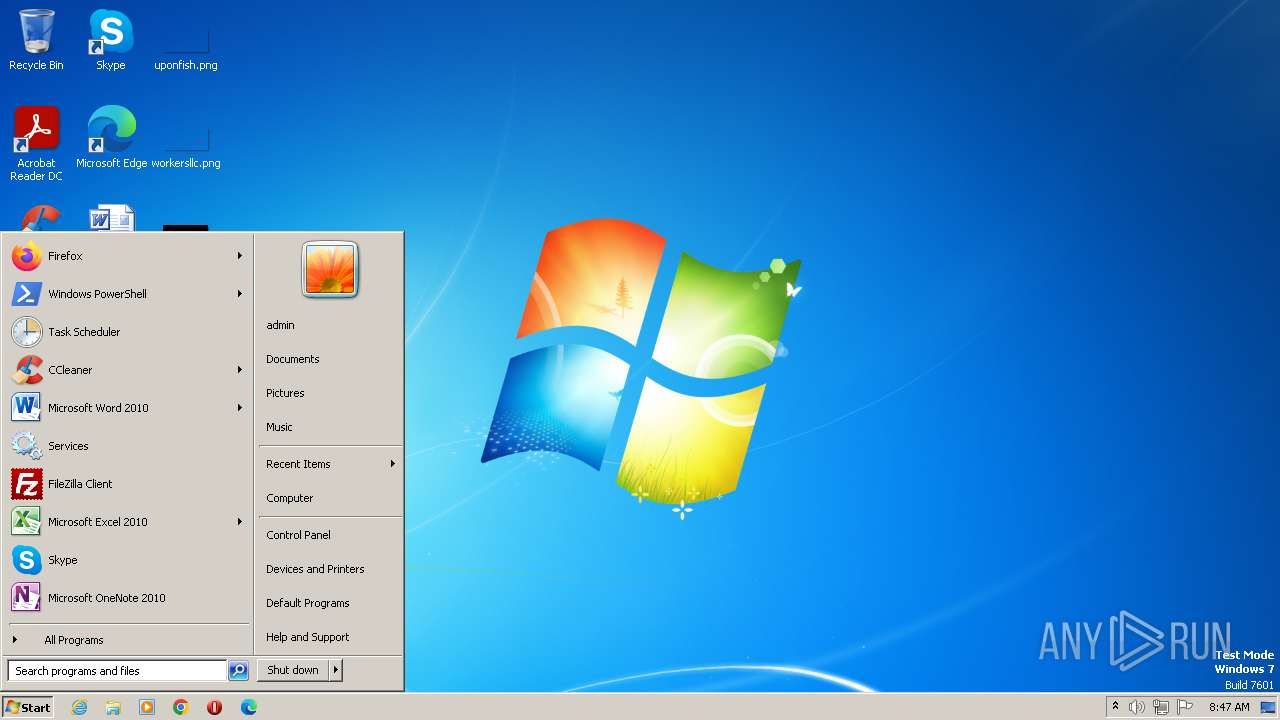
The process executes via Task Scheduler
- javaUpdate.exe (PID: 3360)
Connects to unusual port
- javaUpdate.exe (PID: 2804)
INFO
Checks supported languages
- hah.exe (PID: 3568)
- csc.exe (PID: 1108)
- cvtres.exe (PID: 3024)
- WindowsInput.exe (PID: 2164)
- javaUpdate.exe (PID: 2804)
- WindowsInput.exe (PID: 3908)
- javaUpdate.exe (PID: 3360)
The process checks LSA protection
- hah.exe (PID: 3568)
- csc.exe (PID: 1108)
- cvtres.exe (PID: 3024)
- WindowsInput.exe (PID: 2164)
- WindowsInput.exe (PID: 3908)
- javaUpdate.exe (PID: 2804)
- javaUpdate.exe (PID: 3360)
- dllhost.exe (PID: 3216)
Reads the machine GUID from the registry
- hah.exe (PID: 3568)
- csc.exe (PID: 1108)
- cvtres.exe (PID: 3024)
- WindowsInput.exe (PID: 2164)
- WindowsInput.exe (PID: 3908)
- javaUpdate.exe (PID: 2804)
- javaUpdate.exe (PID: 3360)
Create files in a temporary directory
- hah.exe (PID: 3568)
- cvtres.exe (PID: 3024)
- csc.exe (PID: 1108)
Reads the computer name
- hah.exe (PID: 3568)
- WindowsInput.exe (PID: 2164)
- WindowsInput.exe (PID: 3908)
- javaUpdate.exe (PID: 2804)
- javaUpdate.exe (PID: 3360)
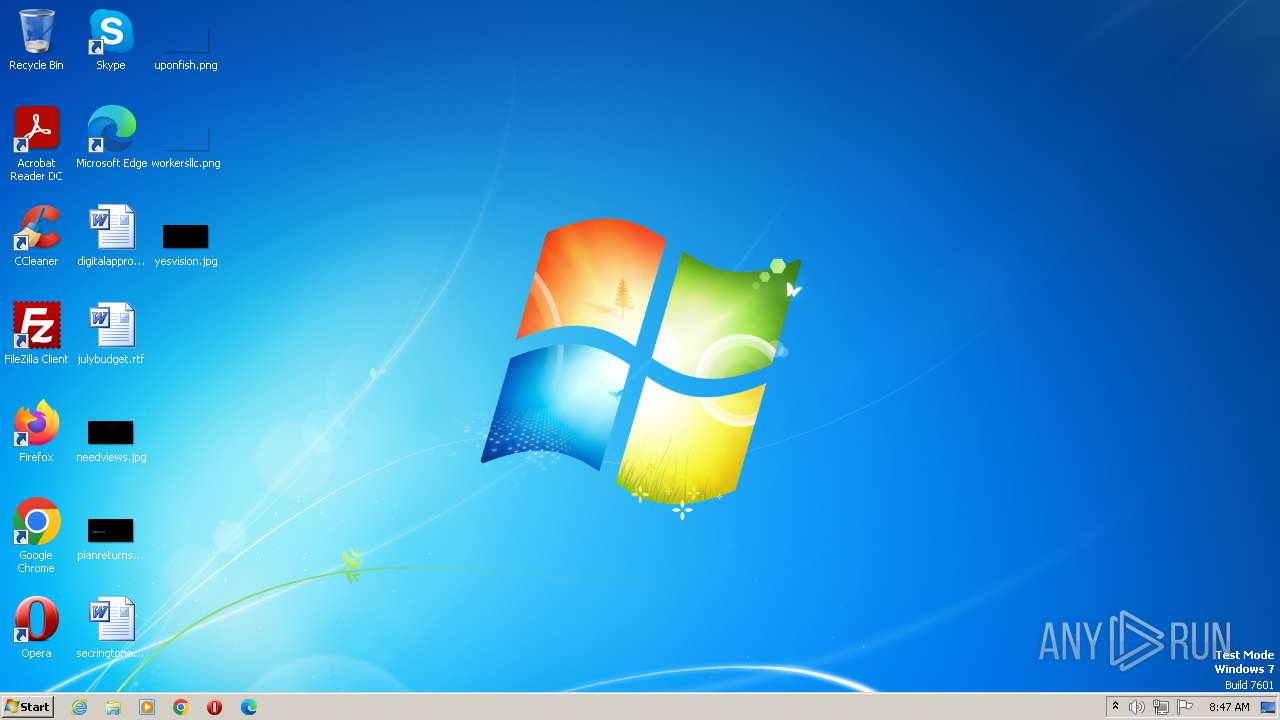
Creates files or folders in the user directory
- hah.exe (PID: 3568)
Checks proxy server information
- javaUpdate.exe (PID: 2804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Orcus
(PID) Process(2804) javaUpdate.exe
C2 (1)s7vety-64001.portmap.io:64001
Keys
AES9be6604a9d1844c20eb2e39f8ed3d10cb26e46b1697b0151bb7446c13a4fd377
Salt
Options
AutostartBuilderProperty
AutostartMethodTaskScheduler
TaskSchedulerTaskNameJavaUpate
TaskHighestPrivilegestrue
RegistryHiddenStarttrue
RegistryKeyNameJavaUpate
TryAllAutostartMethodsOnFailtrue
ChangeAssemblyInformationBuilderProperty
ChangeAssemblyInformationtrue
AssemblyTitleJava Update
AssemblyDescriptionJava Up to date
AssemblyCompanyNameJava
AssemblyProductNamenull
AssemblyCopyrightnull
AssemblyTrademarksnull
AssemblyProductVersion1.0.0.0
AssemblyFileVersion1.0.0.0
ChangeCreationDateBuilderProperty
IsEnabledfalse
NewCreationDate2020-07-31T06:20:28
ChangeIconBuilderProperty
ChangeIconfalse
IconPathnull
ClientTagBuilderProperty
ClientTagnull
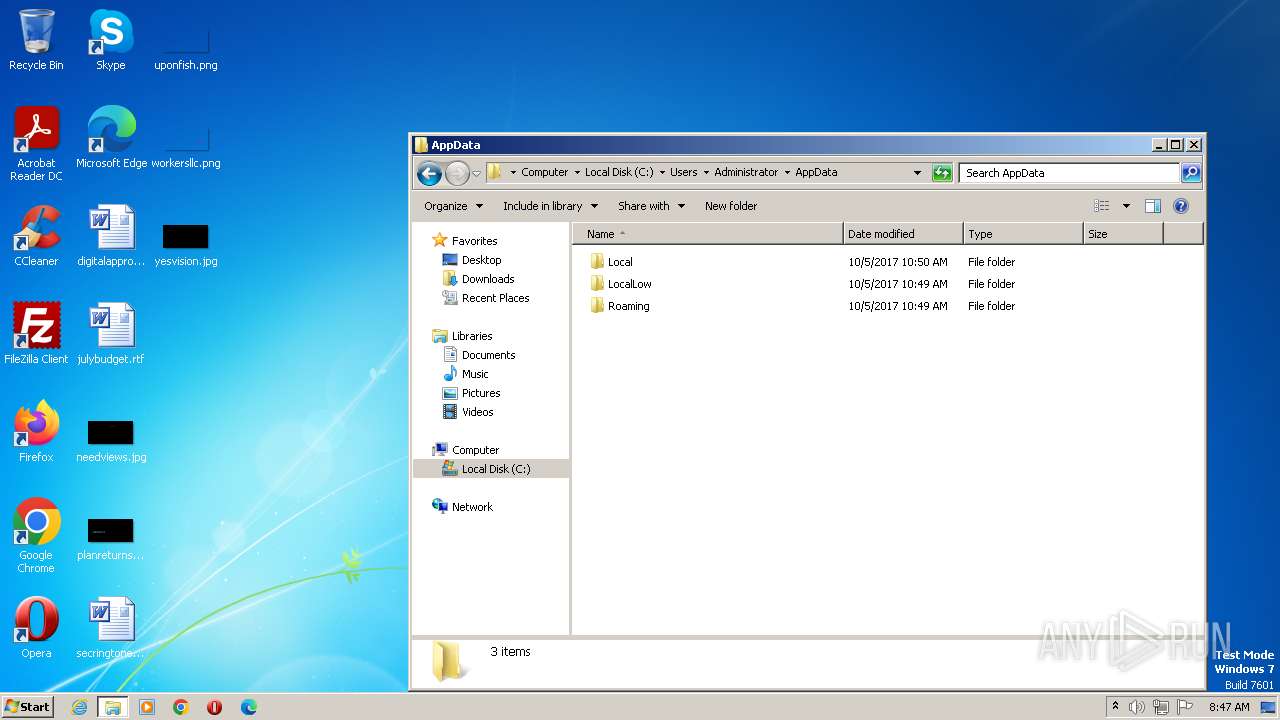
DataFolderBuilderProperty
Path%appdata%\Java
DefaultPrivilegesBuilderProperty
RequireAdministratorRightstrue
DisableInstallationPromptBuilderProperty
IsDisabledtrue
FrameworkVersionBuilderProperty
FrameworkVersionNET35
HideFileBuilderProperty
HideFiletrue
InstallationLocationBuilderProperty
Path%appdata%\Java\javaUpdate.exe
InstallBuilderProperty
Installtrue
KeyloggerBuilderProperty
IsEnabledtrue
MutexBuilderProperty
Mutex8f9ad032680b48e4921e3dead6b0b2ce
ProxyBuilderProperty
ProxyOptionAutomaticDetection
ProxyAddressnull
ProxyPort1080
ProxyType2
ReconnectDelayProperty
Delay10000
RequireAdministratorPrivilegesInstallerBuilderProperty
RequireAdministratorPrivilegesfalse
RespawnTaskBuilderProperty
IsEnabledtrue
TaskNameRespawn
ServiceBuilderProperty
Installtrue
SetRunProgramAsAdminFlagBuilderProperty
SetFlagfalse
WatchdogBuilderProperty
IsEnabledfalse
NameOrcusWatchdog.exe
WatchdogLocationAppData
PreventFileDeletionfalse
Plugins
PluginNameBSoD Protection
PluginVersion2.0
ResourceNamef1e33d31c0594a829d706111b9d8b529
ResourceTypeClientPlugin
Guiddccbc1db-f7d1-413d-bba4-72611d485d3a
PluginNameDisable Webcam Lights
PluginVersion1.0
ResourceNamee4be54ec860349e2ad34f2c25c5897dc
ResourceTypeClientPlugin
Guide6ee5674-bb94-46c7-8bbc-5729af6e2c28
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | - |
| OriginalFileName: | Orcus.exe |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | Java Update |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Java Up to date |
| CompanyName: | Java |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xe67de |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2560 |
| CodeSize: | 935936 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:08:05 07:45:58+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Aug-2023 07:45:58 |
| Comments: | - |
| CompanyName: | Java |
| FileDescription: | Java Up to date |
| FileVersion: | 1.0.0.0 |
| InternalName: | Java Update |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | Orcus.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 05-Aug-2023 07:45:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000E47E4 | 0x000E4800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.16625 |
.rsrc | 0x000E8000 | 0x000006C8 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00648 |
.reloc | 0x000EA000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28751 | 831 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
54
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1108 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\kohbjyxx.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | hah.exe | ||||||||||||
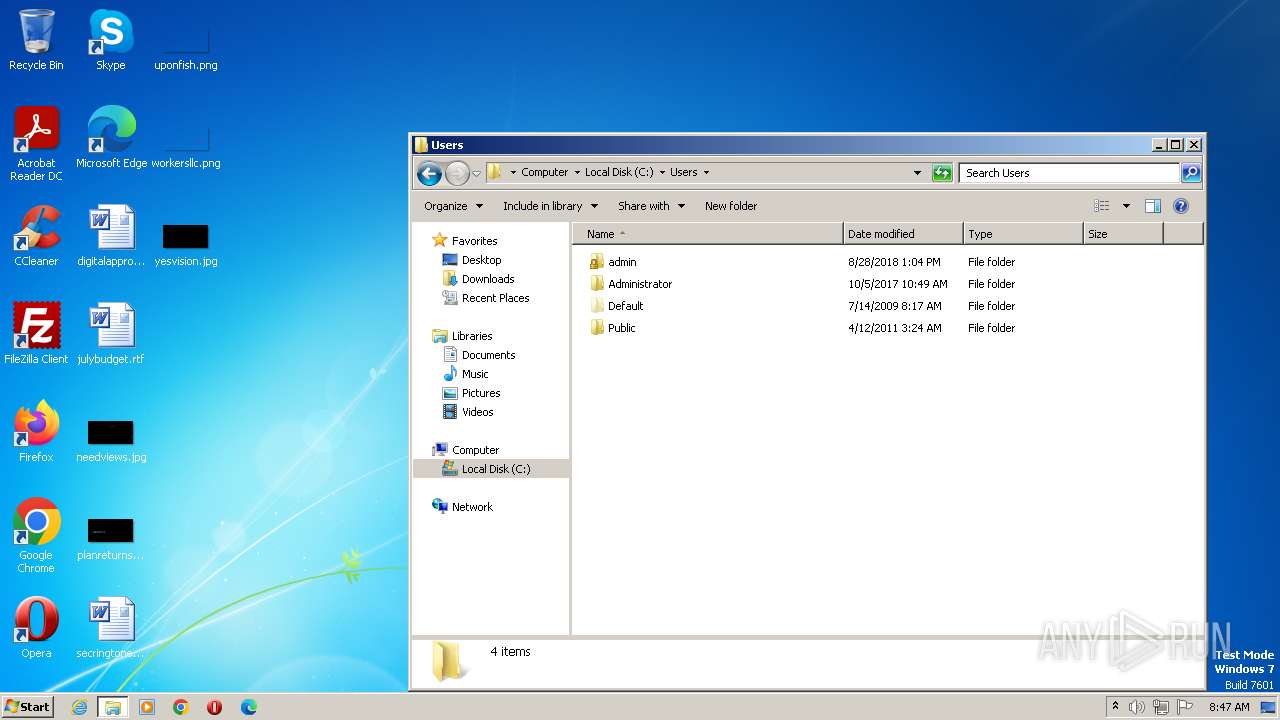
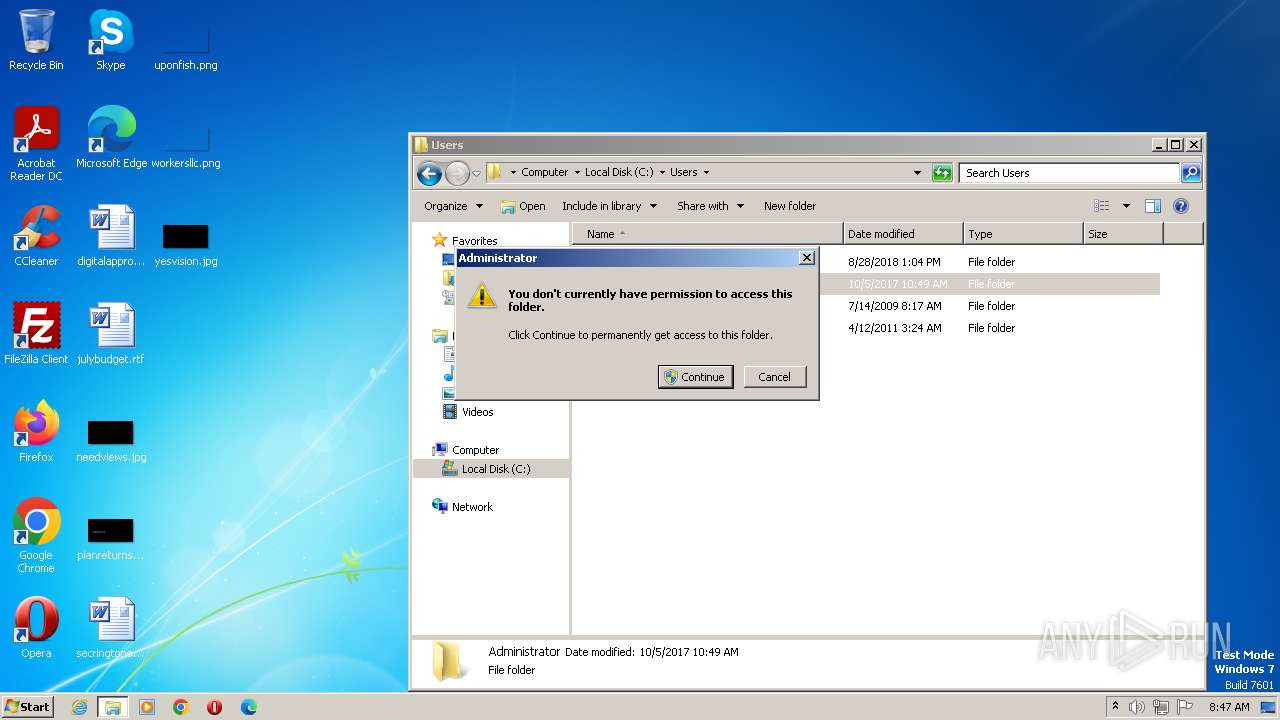
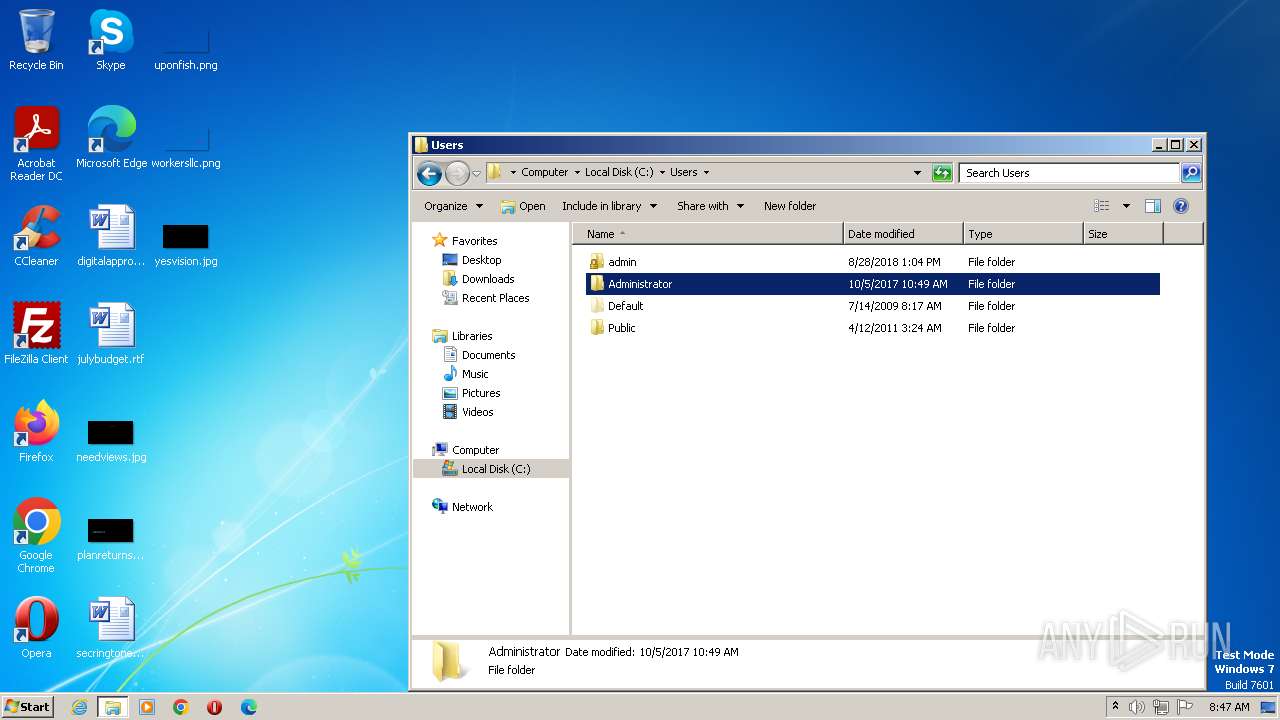
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2164 | "C:\Windows\system32\WindowsInput.exe" --install | C:\Windows\System32\WindowsInput.exe | — | hah.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Windows Input Exit code: 0 Version: 0.1.0 Modules
| |||||||||||||||
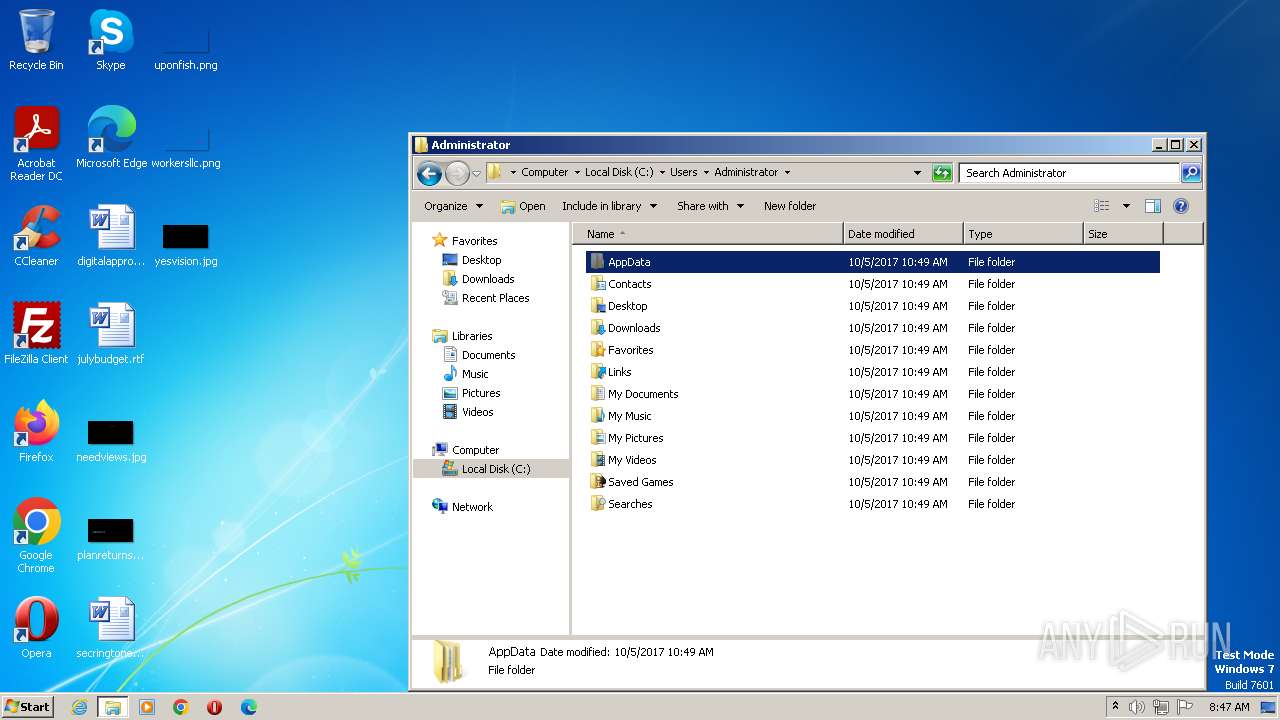
| 2804 | "C:\Users\admin\AppData\Roaming\Java\javaUpdate.exe" | C:\Users\admin\AppData\Roaming\Java\javaUpdate.exe | hah.exe | ||||||||||||
User: admin Company: Java Integrity Level: HIGH Description: Java Up to date Exit code: 0 Version: 1.0.0.0 Modules
Orcus(PID) Process(2804) javaUpdate.exe C2 (1)s7vety-64001.portmap.io:64001 Keys AES9be6604a9d1844c20eb2e39f8ed3d10cb26e46b1697b0151bb7446c13a4fd377 Salt Options AutostartBuilderProperty AutostartMethodTaskScheduler TaskSchedulerTaskNameJavaUpate TaskHighestPrivilegestrue RegistryHiddenStarttrue RegistryKeyNameJavaUpate TryAllAutostartMethodsOnFailtrue ChangeAssemblyInformationBuilderProperty ChangeAssemblyInformationtrue AssemblyTitleJava Update AssemblyDescriptionJava Up to date AssemblyCompanyNameJava AssemblyProductNamenull AssemblyCopyrightnull AssemblyTrademarksnull AssemblyProductVersion1.0.0.0 AssemblyFileVersion1.0.0.0 ChangeCreationDateBuilderProperty IsEnabledfalse NewCreationDate2020-07-31T06:20:28 ChangeIconBuilderProperty ChangeIconfalse IconPathnull ClientTagBuilderProperty ClientTagnull DataFolderBuilderProperty Path%appdata%\Java DefaultPrivilegesBuilderProperty RequireAdministratorRightstrue DisableInstallationPromptBuilderProperty IsDisabledtrue FrameworkVersionBuilderProperty FrameworkVersionNET35 HideFileBuilderProperty HideFiletrue InstallationLocationBuilderProperty Path%appdata%\Java\javaUpdate.exe InstallBuilderProperty Installtrue KeyloggerBuilderProperty IsEnabledtrue MutexBuilderProperty Mutex8f9ad032680b48e4921e3dead6b0b2ce ProxyBuilderProperty ProxyOptionAutomaticDetection ProxyAddressnull ProxyPort1080 ProxyType2 ReconnectDelayProperty Delay10000 RequireAdministratorPrivilegesInstallerBuilderProperty RequireAdministratorPrivilegesfalse RespawnTaskBuilderProperty IsEnabledtrue TaskNameRespawn ServiceBuilderProperty Installtrue SetRunProgramAsAdminFlagBuilderProperty SetFlagfalse WatchdogBuilderProperty IsEnabledfalse NameOrcusWatchdog.exe WatchdogLocationAppData PreventFileDeletionfalse Plugins PluginNameBSoD Protection PluginVersion2.0 ResourceNamef1e33d31c0594a829d706111b9d8b529 ResourceTypeClientPlugin Guiddccbc1db-f7d1-413d-bba4-72611d485d3a PluginNameDisable Webcam Lights PluginVersion1.0 ResourceNamee4be54ec860349e2ad34f2c25c5897dc ResourceTypeClientPlugin Guide6ee5674-bb94-46c7-8bbc-5729af6e2c28 | |||||||||||||||
| 2880 | "C:\Users\admin\AppData\Local\Temp\hah.exe" | C:\Users\admin\AppData\Local\Temp\hah.exe | — | explorer.exe | |||||||||||
User: admin Company: Java Integrity Level: MEDIUM Description: Java Up to date Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3024 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES71C1.tmp" "c:\Users\admin\AppData\Local\Temp\CSC71C0.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 3216 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3360 | C:\Users\admin\AppData\Roaming\Java\javaUpdate.exe | C:\Users\admin\AppData\Roaming\Java\javaUpdate.exe | taskeng.exe | ||||||||||||
User: admin Company: Java Integrity Level: HIGH Description: Java Up to date Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3568 | "C:\Users\admin\AppData\Local\Temp\hah.exe" | C:\Users\admin\AppData\Local\Temp\hah.exe | explorer.exe | ||||||||||||
User: admin Company: Java Integrity Level: HIGH Description: Java Up to date Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3908 | "C:\Windows\system32\WindowsInput.exe" | C:\Windows\System32\WindowsInput.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Integrity Level: SYSTEM Description: Windows Input Exit code: 0 Version: 0.1.0 Modules
| |||||||||||||||
Total events
1 627
Read events
1 611
Write events
16
Delete events
0
Modification events
| (PID) Process: | (3568) hah.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3568) hah.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3568) hah.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3568) hah.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2164) WindowsInput.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2164) WindowsInput.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2164) WindowsInput.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2164) WindowsInput.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
2
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | hah.exe | C:\Windows\system32\WindowsInput.exe | executable | |
MD5:E6FCF516D8ED8D0D4427F86E08D0D435 | SHA256:8DBE814359391ED6B0B5B182039008CF1D00964DA9FBC4747F46242A95C24337 | |||
| 3568 | hah.exe | C:\Users\admin\AppData\Local\Temp\kohbjyxx.0.cs | text | |
MD5:C2BD47F2E16E10B0D6B3CBD8228700D4 | SHA256:86A1DCE2B462C118B3D8BF841130B6C3482DB7A8851CF90BEE1F068C80943B7A | |||
| 3024 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES71C1.tmp | binary | |
MD5:98996FC1AB70EA22B6948A1BAD04A277 | SHA256:E9D8031701B7190030445A54184093BE10FC1CF36D92999169626FB78B4434E6 | |||
| 3568 | hah.exe | C:\Users\admin\AppData\Roaming\Java\javaUpdate.exe | executable | |
MD5:51A72CBA85E56E68571F1737A3867248 | SHA256:57EA66A57F97ECEE958CCA1C7379025750C23BA98EA6DCFAAE17FC5F64C9D1C5 | |||
| 1108 | csc.exe | C:\Users\admin\AppData\Local\Temp\kohbjyxx.out | text | |
MD5:C3FAC71121FFE0B8A8B80D186D4BA616 | SHA256:1DD694DDBF10F67D7F008ABAE519E6327547425BC88E5805CD0AA0FAE3CB912D | |||
| 2164 | WindowsInput.exe | C:\Windows\system32\WindowsInput.InstallState | xml | |
MD5:FFB29BD88BD23C639985F1D369DBD1CA | SHA256:1ADB4F9D1D152E018246A0A2762B473D910906340207F57D3F8CE1097E1DE09F | |||
| 3568 | hah.exe | C:\Users\admin\AppData\Roaming\Java\javaUpdate.exe.config | xml | |
MD5:A2B76CEA3A59FA9AF5EA21FF68139C98 | SHA256:F99EF5BF79A7C43701877F0BB0B890591885BB0A3D605762647CC8FFBF10C839 | |||
| 3568 | hah.exe | C:\Users\admin\AppData\Local\Temp\kohbjyxx.cmdline | text | |
MD5:EDFF6F0B77D1615BDD814D9E45160196 | SHA256:A0AB641C62DE960295C159067CC309233DCF6021F21058A9E5BAA75C15A1B0D7 | |||
| 1108 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC71C0.tmp | binary | |
MD5:97AEBCDFA3955A3FB5AB0C685E450786 | SHA256:456B1A2610D5E275E2E8F857EF2E7AAE53A775894B22DA5B37C2E6FDAD67B72A | |||
| 3568 | hah.exe | C:\Windows\system32\WindowsInput.exe.config | xml | |
MD5:A2B76CEA3A59FA9AF5EA21FF68139C98 | SHA256:F99EF5BF79A7C43701877F0BB0B890591885BB0A3D605762647CC8FFBF10C839 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
16
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2804 | javaUpdate.exe | 193.161.193.99:64001 | s7vety-64001.portmap.io | OOO Bitree Networks | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s7vety-64001.portmap.io |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a Reverse Proxy Service Observed |