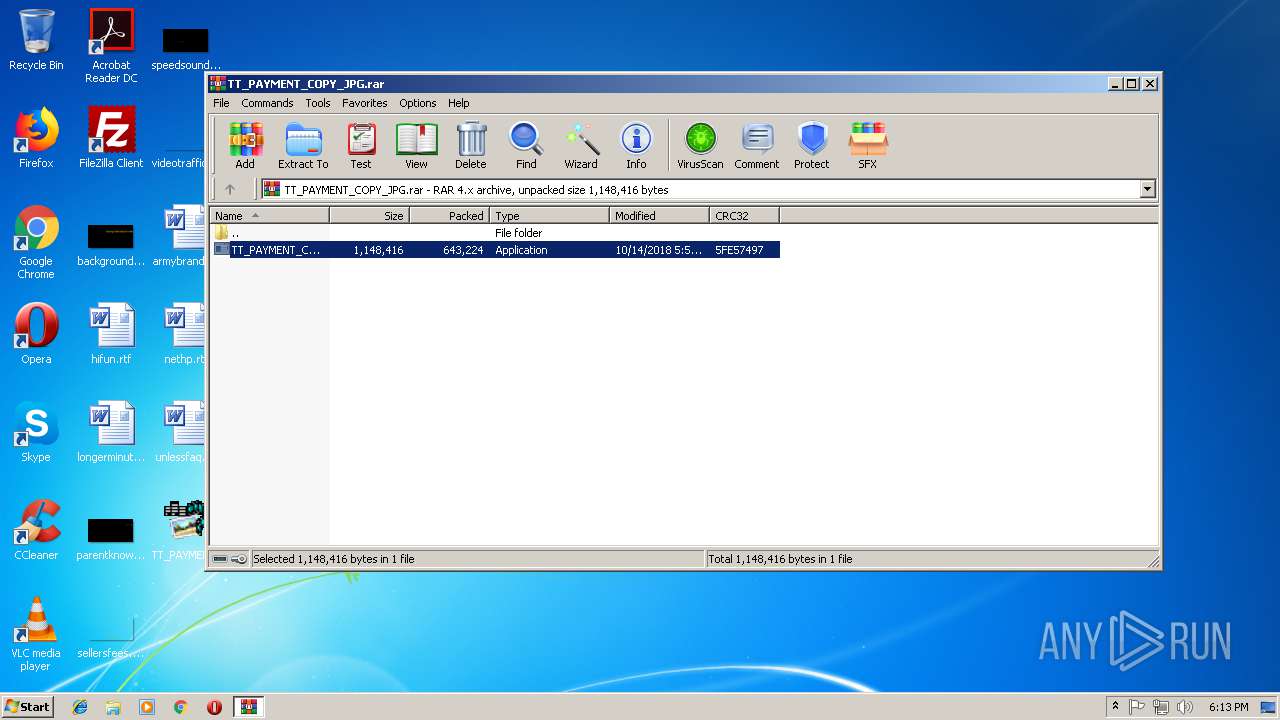
| download: | TT_PAYMENT_COPY_JPG.rar |
| Full analysis: | https://app.any.run/tasks/3d4813a3-810d-44df-a789-c5e52e665b59 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | November 15, 2018, 18:12:31 |
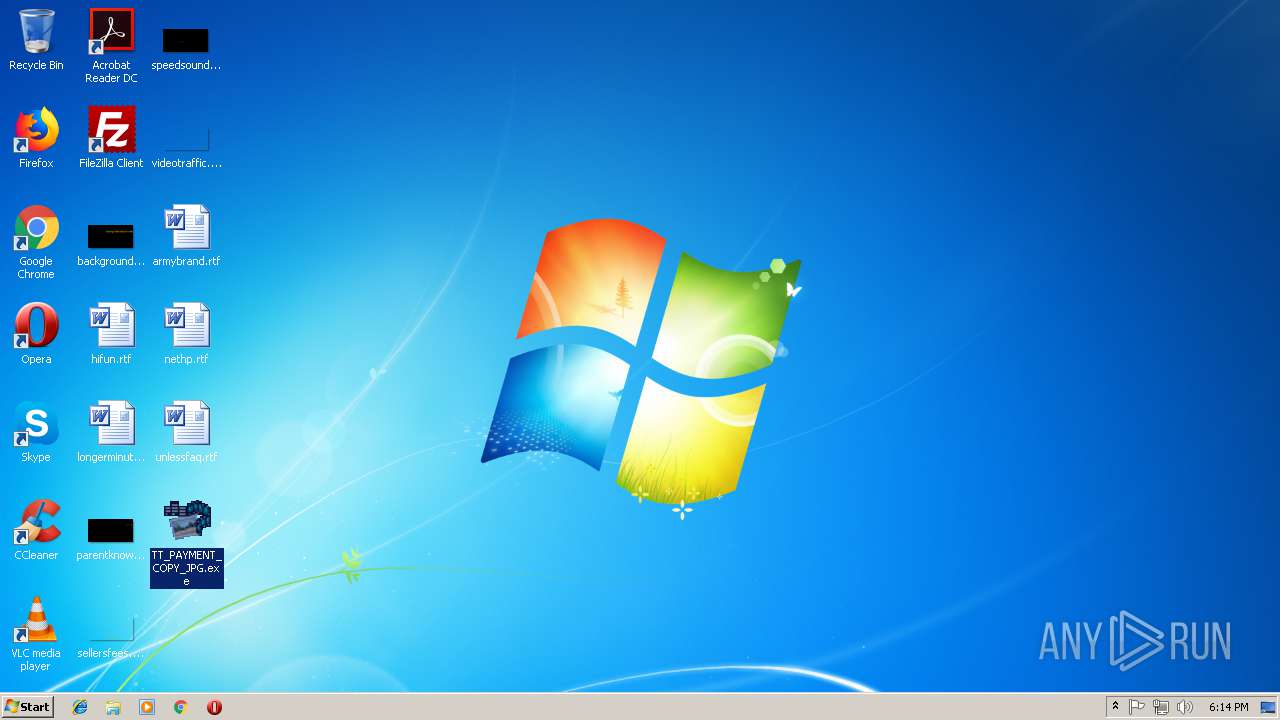
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
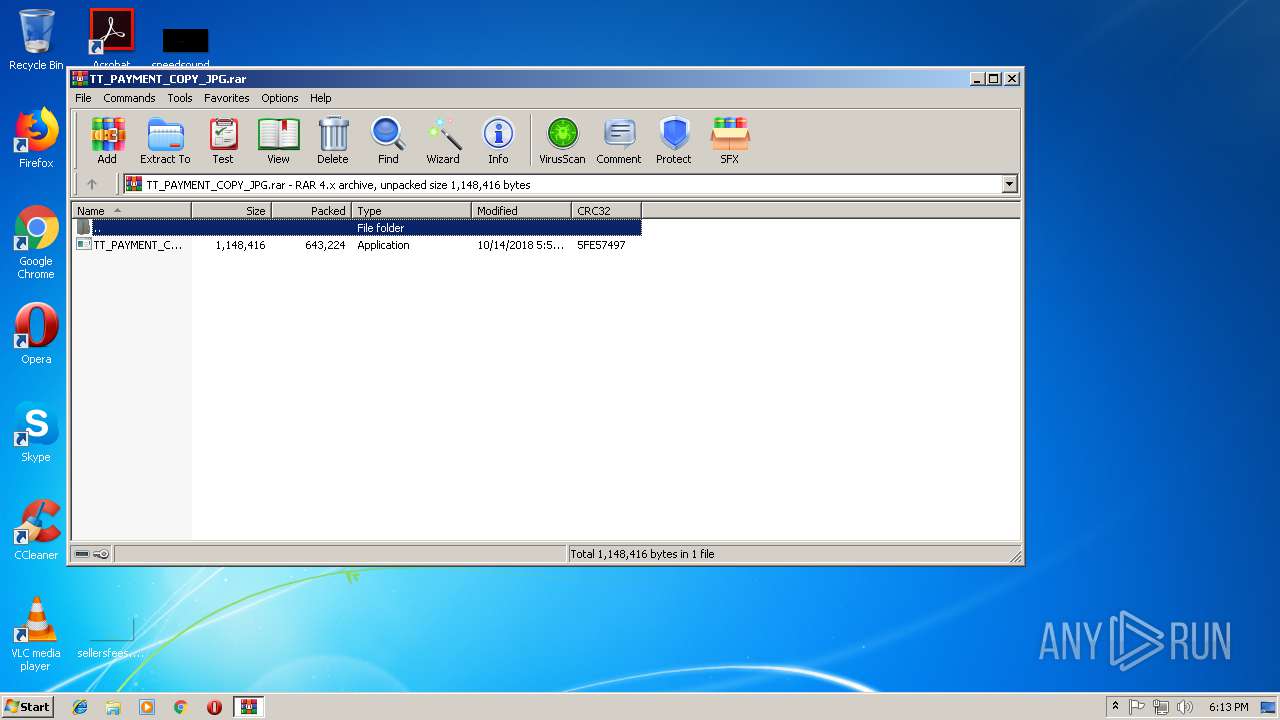
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 99031C1136BFECE8D19A8D96EBE8FAF1 |
| SHA1: | 040BEE40675AC261FE52EB50373027919AC1A5F6 |
| SHA256: | 57C1A0F78ECFB59DAAC9F7369657684845E32C4BC79DDEAF3CB470AB1E051A7E |
| SSDEEP: | 12288:tnzHIxIBNCtN5viYdxBze+T85SxigCG0qmXNTdyNoLknnDyxNfxEI:tHwUEtBM+wEA00vXNTd/knnk |
MALICIOUS
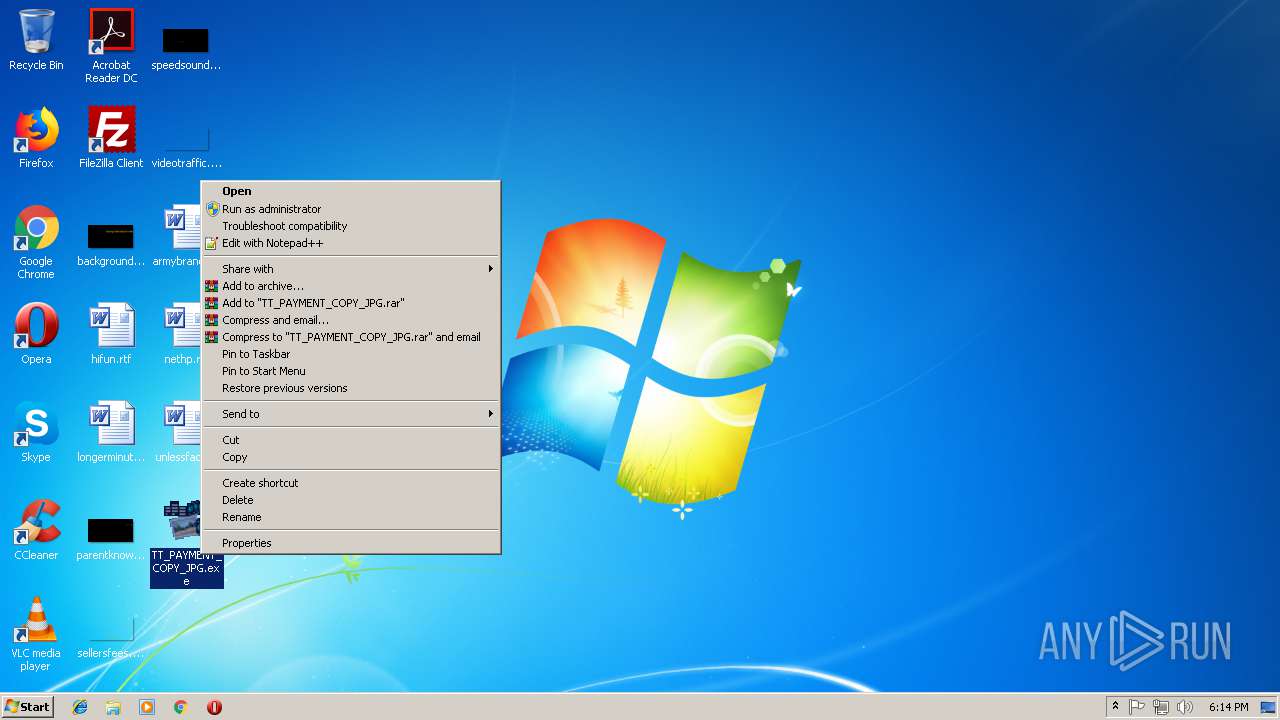
Application was dropped or rewritten from another process
- TT_PAYMENT_COPY_JPG.exe (PID: 3984)
- TT_PAYMENT_COPY_JPG.exe (PID: 2956)
- TT_PAYMENT_COPY_JPG.exe (PID: 2692)
- TT_PAYMENT_COPY_JPG.exe (PID: 564)
- TT_PAYMENT_COPY_JPG.exe (PID: 3604)
- TT_PAYMENT_COPY_JPG.exe (PID: 1904)
Actions looks like stealing of personal data
- vbc.exe (PID: 3260)
- vbc.exe (PID: 3552)
- vbc.exe (PID: 3140)
- vbc.exe (PID: 3412)
Detected Hawkeye Keylogger
- TT_PAYMENT_COPY_JPG.exe (PID: 564)
- TT_PAYMENT_COPY_JPG.exe (PID: 3604)
Stealing of credential data
- vbc.exe (PID: 3260)
- vbc.exe (PID: 3552)
- vbc.exe (PID: 3412)
- vbc.exe (PID: 3140)
SUSPICIOUS
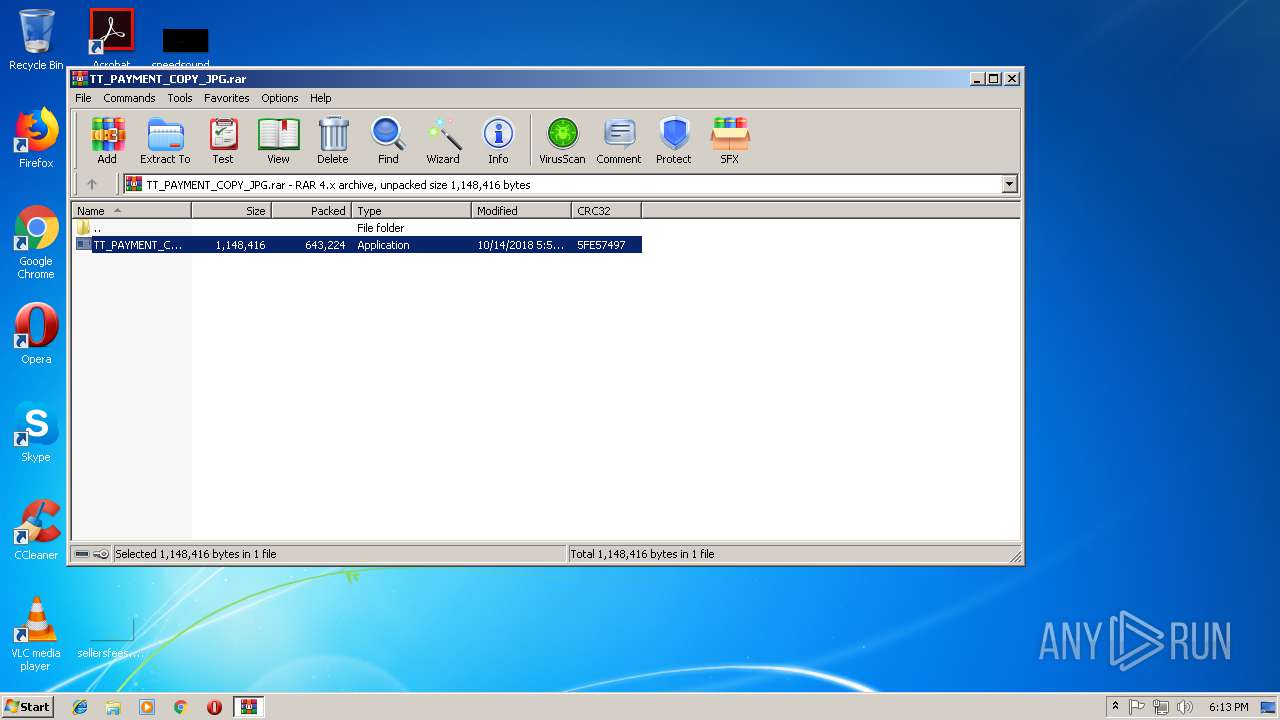
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2788)
Application launched itself
- TT_PAYMENT_COPY_JPG.exe (PID: 3984)
- TT_PAYMENT_COPY_JPG.exe (PID: 2956)
Executes scripts
- TT_PAYMENT_COPY_JPG.exe (PID: 564)
- TT_PAYMENT_COPY_JPG.exe (PID: 3604)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3260)
- vbc.exe (PID: 3412)
Connects to SMTP port
- TT_PAYMENT_COPY_JPG.exe (PID: 564)
- TT_PAYMENT_COPY_JPG.exe (PID: 3604)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 643273 |
|---|---|
| UncompressedSize: | 1148416 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2018:10:14 17:59:22 |
| PackingMethod: | Normal |
| ArchivedFileName: | TT_PAYMENT_COPY_JPG.exe |
Total processes
46
Monitored processes
11
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe" | C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe | TT_PAYMENT_COPY_JPG.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1904 | "C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe" 2 3604 6328671 | C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe | — | TT_PAYMENT_COPY_JPG.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2692 | "C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe" 2 564 6252281 | C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe | — | TT_PAYMENT_COPY_JPG.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
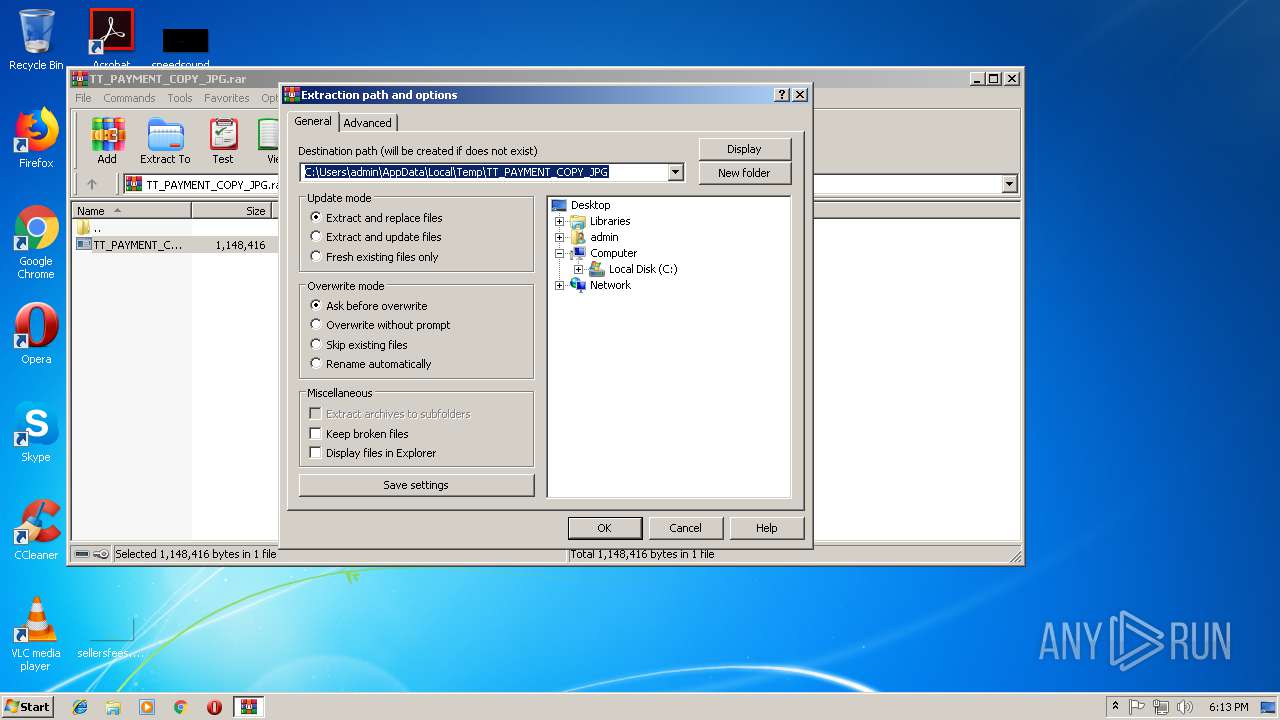
| 2788 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\TT_PAYMENT_COPY_JPG.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe" | C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3140 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpBFF2.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | TT_PAYMENT_COPY_JPG.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3260 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp9210.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | TT_PAYMENT_COPY_JPG.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3412 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpBBFA.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | TT_PAYMENT_COPY_JPG.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3552 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpA81A.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | TT_PAYMENT_COPY_JPG.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3604 | "C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe" | C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe | TT_PAYMENT_COPY_JPG.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
563
Read events
522
Write events
41
Delete events
0
Modification events
| (PID) Process: | (2788) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2788) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2788) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2788) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\TT_PAYMENT_COPY_JPG.rar | |||
| (PID) Process: | (2788) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2788) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2788) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2788) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2788) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2788) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFABFFFFFF1E0200006B03000013040000 | |||
Executable files
1
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 564 | TT_PAYMENT_COPY_JPG.exe | C:\Users\admin\AppData\Local\Temp\5c3f14c3-35ed-56cf-c498-6edeaf57da4d | text | |
MD5:— | SHA256:— | |||
| 2788 | WinRAR.exe | C:\Users\admin\Desktop\TT_PAYMENT_COPY_JPG.exe | executable | |
MD5:— | SHA256:— | |||
| 3260 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmp9210.tmp | text | |
MD5:— | SHA256:— | |||
| 564 | TT_PAYMENT_COPY_JPG.exe | C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\E02357FC7708441D4B0BE5F371F4B28961870F70 | binary | |
MD5:— | SHA256:— | |||
| 3412 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmpBBFA.tmp | text | |
MD5:— | SHA256:— | |||
| 3552 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmpA81A.tmp | text | |
MD5:7FB9A9AD0FD9B1E0108ED71FBB276048 | SHA256:7D63C301317E144B0133A72250AE2D8E09AF65A92E6A807EC58A71939FE530A9 | |||
| 3140 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmpBFF2.tmp | text | |
MD5:7FB9A9AD0FD9B1E0108ED71FBB276048 | SHA256:7D63C301317E144B0133A72250AE2D8E09AF65A92E6A807EC58A71939FE530A9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
564 | TT_PAYMENT_COPY_JPG.exe | 66.23.237.186:587 | mail.britesurgical.com | NEW JERSEY INTERNATIONAL INTERNET EXCHANGE LLC | US | suspicious |
3604 | TT_PAYMENT_COPY_JPG.exe | 66.23.237.186:587 | mail.britesurgical.com | NEW JERSEY INTERNATIONAL INTERNET EXCHANGE LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mail.britesurgical.com |
| unknown |