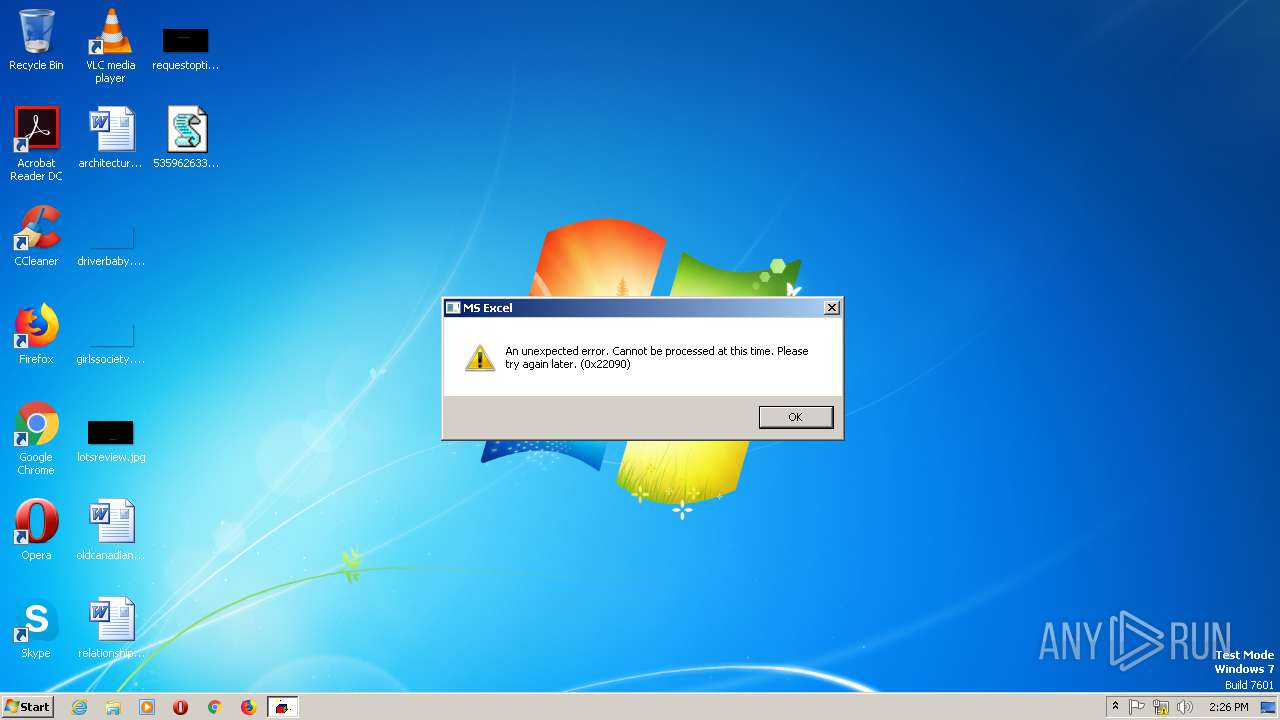
| File name: | 5359626331231626.vbs |
| Full analysis: | https://app.any.run/tasks/850726cb-6dcc-43b7-b8bf-169e8f73b60a |
| Verdict: | Malicious activity |
| Threats: | Hancitor was created in 2014 to drop other malware on infected machines. It is also known as Tordal and Chanitor. This malware is available as a service which makes it accessible tools to criminals and contributes to the popularity of this virus. |
| Analysis date: | December 06, 2019, 14:25:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | E9381F83BAB68A1B29472BF001A13841 |
| SHA1: | 9319E2E6DB57527925FE26184B8AD0BD94191115 |
| SHA256: | 5785FD9336906685B51D4DDCE328168AB737CB997565E2E9FA12046D0D8DC2BF |
| SSDEEP: | 6144:OylyTh0yw/CpCu3/oCBztLti8+TrHoLldA2lKbqAQVpZD5zTDit45JIzBMTYVFR4:vlA+j/CpfHLHy0L8P+PDt7TKRMKhu |
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- regsvr32.exe (PID: 308)
Connects to CnC server
- svchost.exe (PID: 956)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 308)
HANCITOR was detected
- svchost.exe (PID: 956)
SUSPICIOUS
Reads the machine GUID from the registry
- WScript.exe (PID: 992)
Executed via WMI
- regsvr32.exe (PID: 2288)
Executable content was dropped or overwritten
- WScript.exe (PID: 992)
Checks for external IP
- svchost.exe (PID: 956)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
256
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | -s C:\Users\admin\AppData\Local\Temp\ieZbASxlSVMCP.txt | C:\Windows\SysWOW64\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | C:\Windows\System32\svchost.exe | C:\Windows\SysWOW64\svchost.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\5359626331231626.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2288 | regsvr32.exe -s C:\Users\admin\AppData\Local\Temp\ieZbASxlSVMCP.txt | C:\Windows\system32\regsvr32.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
521
Read events
505
Write events
16
Delete events
0
Modification events
| (PID) Process: | (992) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (992) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (992) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (992) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (992) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories64\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E3070C00050006000E001A0018007C00010000001E768127E028094199FEB9D127C57AFE | |||
| (PID) Process: | (992) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000093723B2341ACD501 | |||
| (PID) Process: | (956) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (956) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000007D000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (956) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (956) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 992 | WScript.exe | C:\Users\admin\AppData\Local\Temp\dQfIOtgF.txt | — | |
MD5:— | SHA256:— | |||
| 992 | WScript.exe | C:\Users\admin\AppData\Local\Temp\dQfIOtgF.txt.zip | compressed | |
MD5:— | SHA256:— | |||
| 992 | WScript.exe | C:\Users\admin\AppData\Local\Temp\ieZbASxlSVMCP.txt | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
4
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
956 | svchost.exe | POST | 200 | 178.170.248.82:80 | http://furnandol.com/4/forum.php | RU | text | 12 b | malicious |
2004 | mscorsvw.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
2004 | mscorsvw.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 555 b | whitelisted |
2808 | mscorsvw.exe | GET | 200 | 67.27.234.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e8f6856a441fb10b | US | compressed | 6.73 Kb | whitelisted |
956 | svchost.exe | POST | 200 | 178.170.248.82:80 | http://furnandol.com/4/forum.php | RU | text | 12 b | malicious |
956 | svchost.exe | POST | 200 | 178.170.248.82:80 | http://furnandol.com/4/forum.php | RU | text | 12 b | malicious |
956 | svchost.exe | POST | 200 | 178.170.248.82:80 | http://furnandol.com/4/forum.php | RU | text | 12 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2004 | mscorsvw.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
956 | svchost.exe | 23.23.229.94:80 | api.ipify.org | Amazon.com, Inc. | US | malicious |
956 | svchost.exe | 178.170.248.82:80 | furnandol.com | Electrics Ltd | RU | malicious |
2808 | mscorsvw.exe | 67.27.234.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
furnandol.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
956 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
956 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
956 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
956 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
956 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
4 ETPRO signatures available at the full report