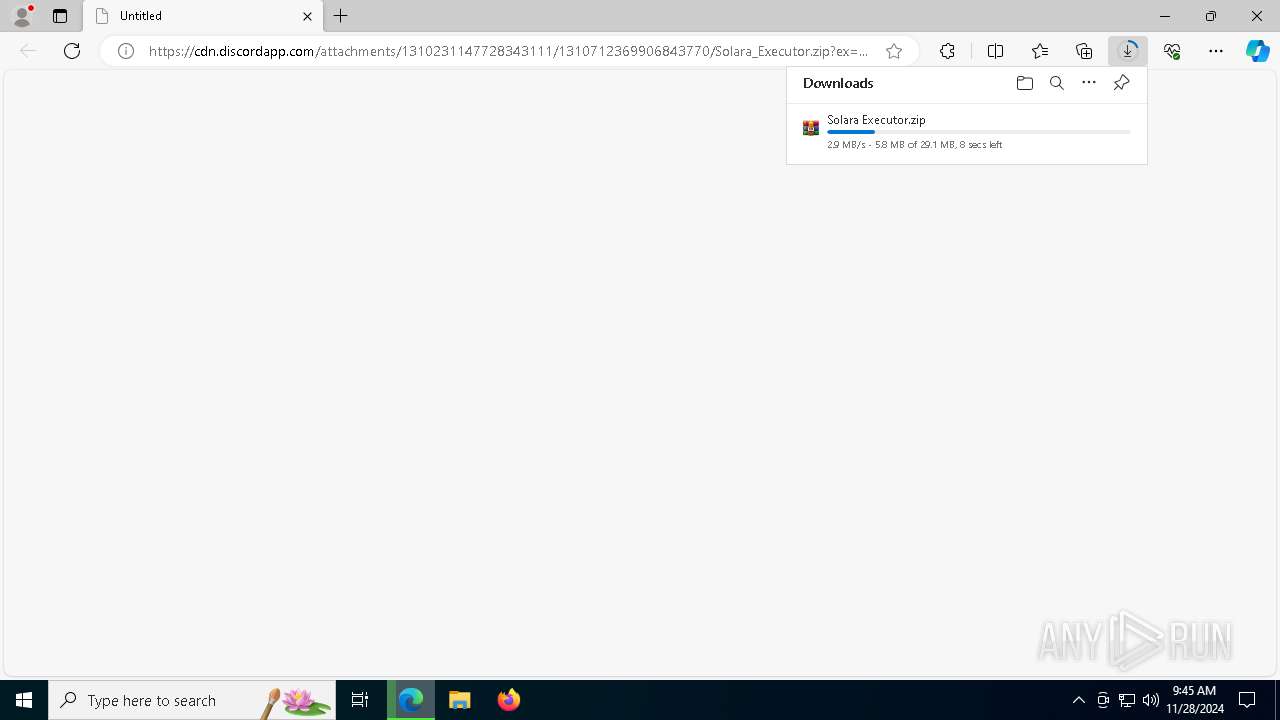
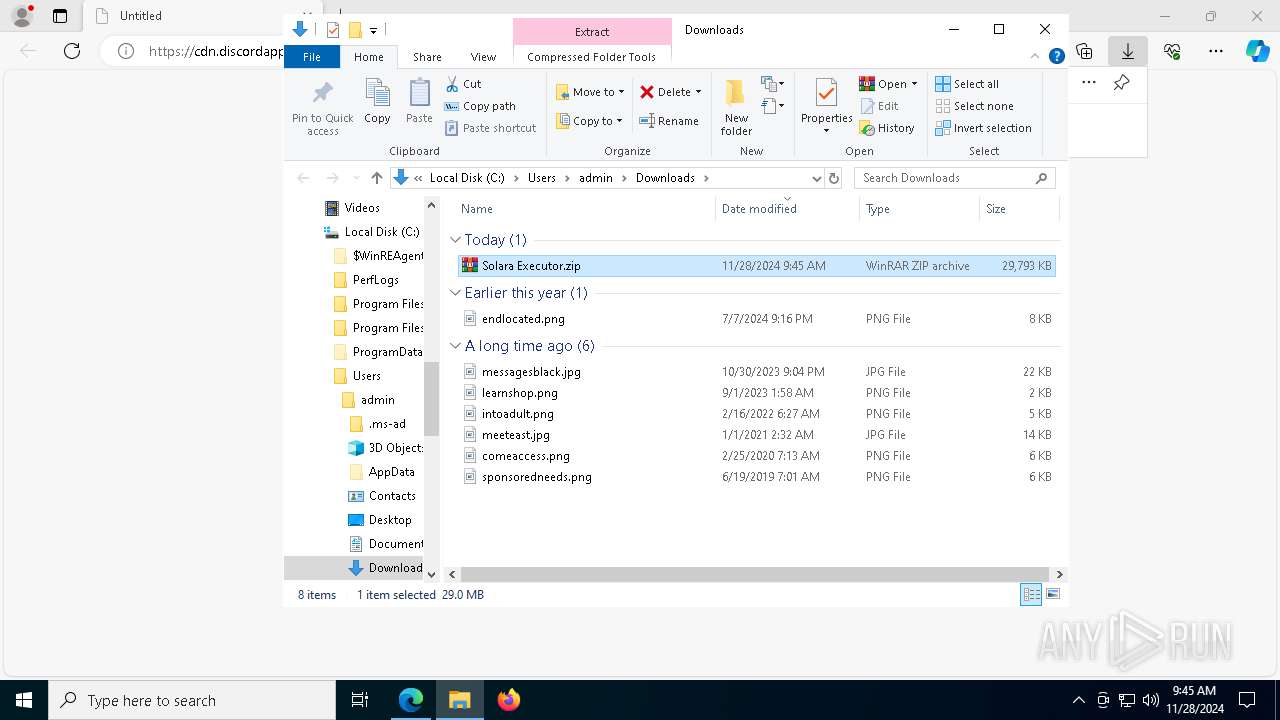
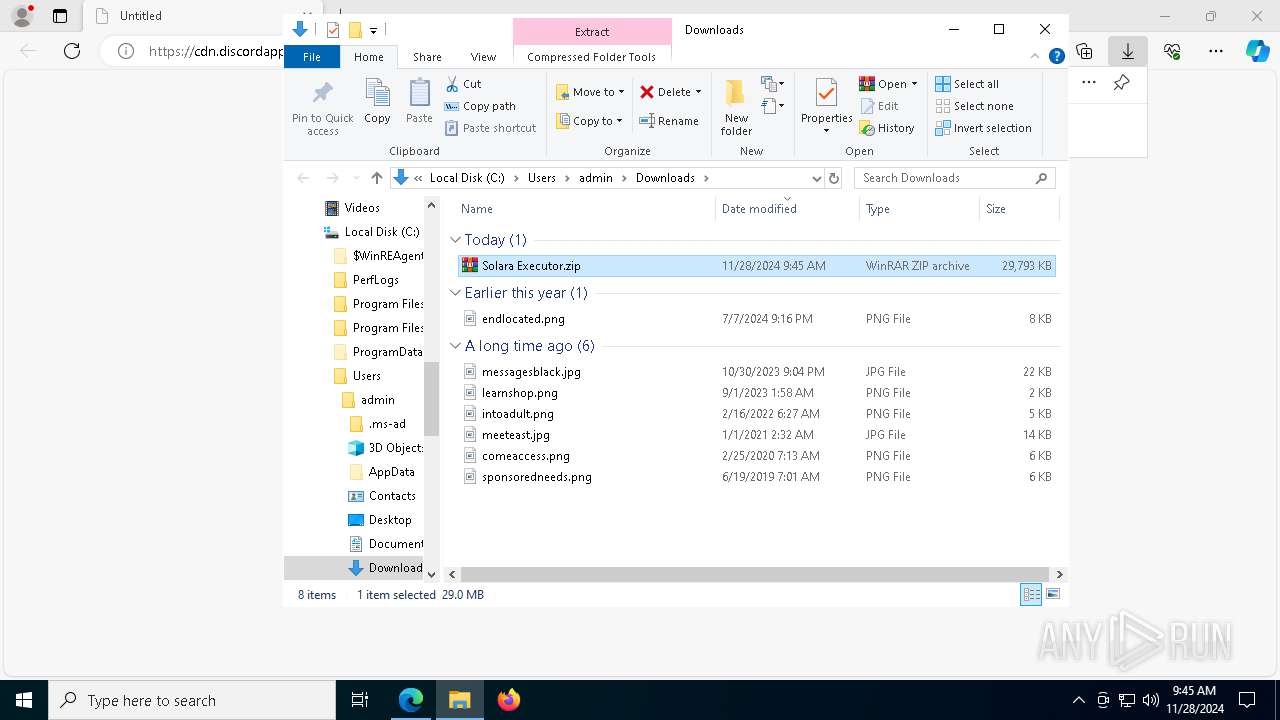
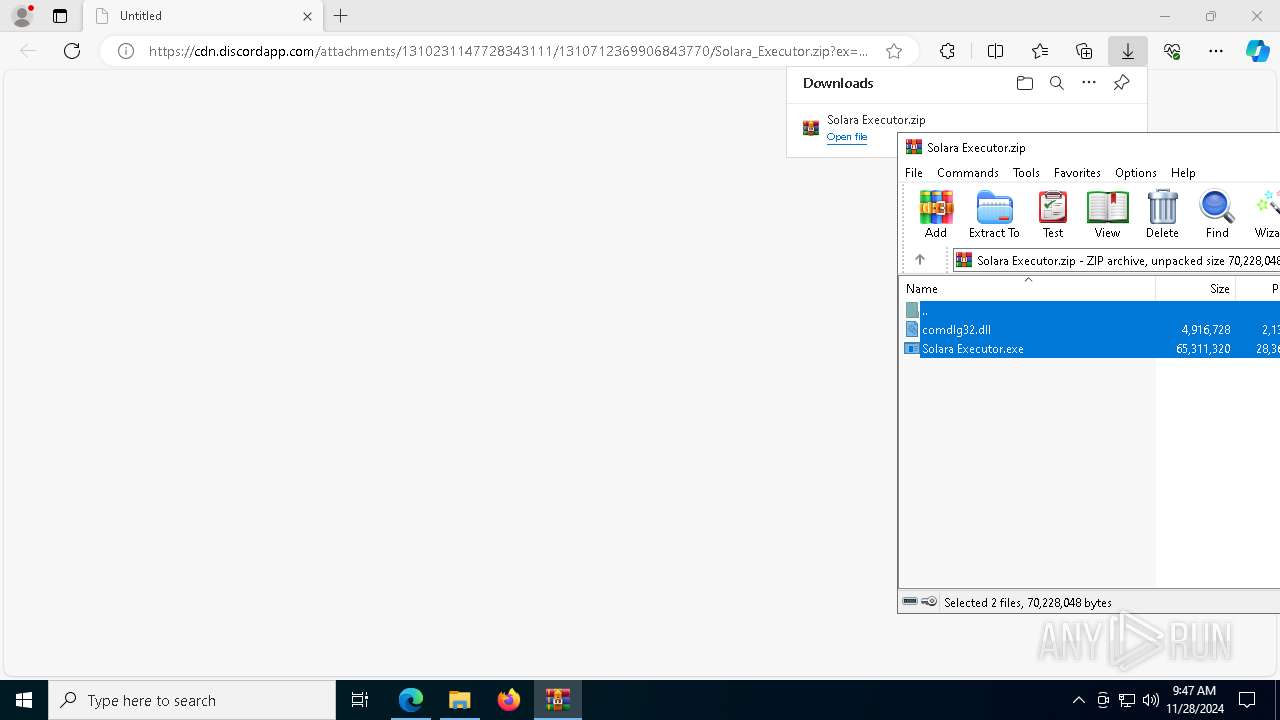
| URL: | https://cdn.discordapp.com/attachments/1310231147728343111/1310712369906843770/Solara_Executor.zip?ex=67498344&is=674831c4&hm=42f768d198c1e24fcb0c79e0e2ba4508290420d503c7b425e918474458052feb& |
| Full analysis: | https://app.any.run/tasks/8ad8fc78-5345-446b-88bc-de98d5ef9e37 |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | November 28, 2024, 09:45:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
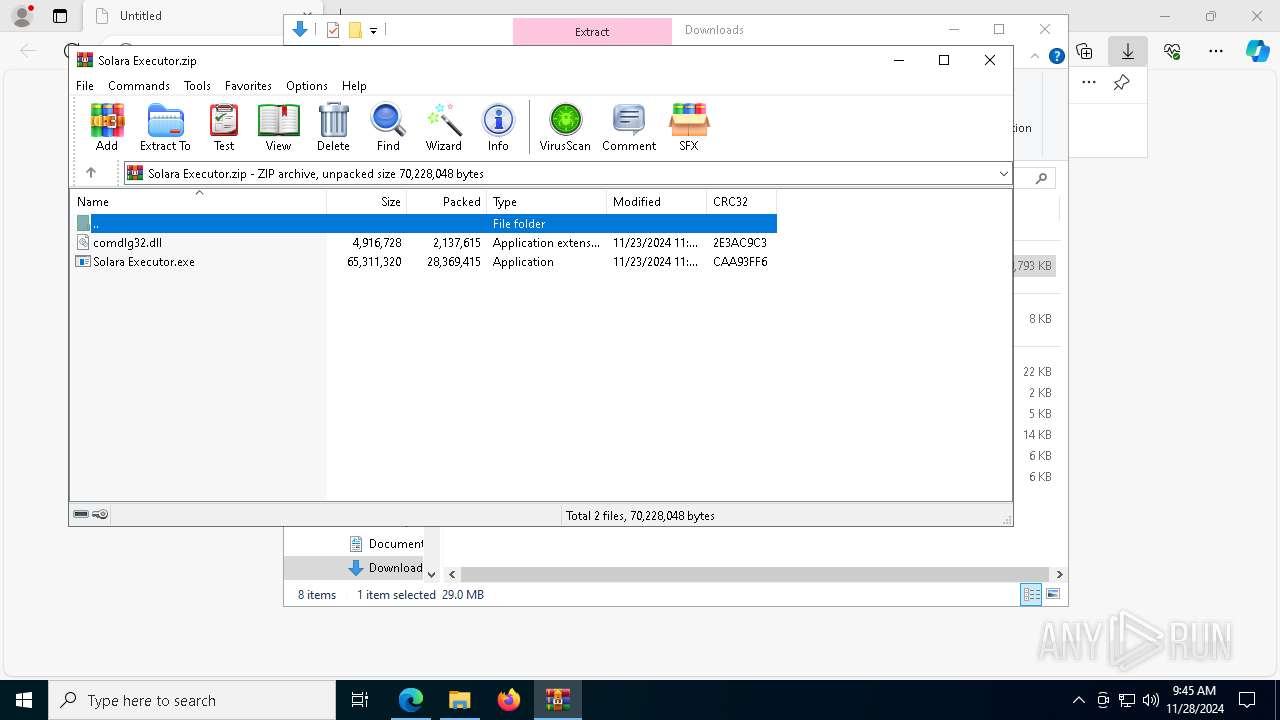
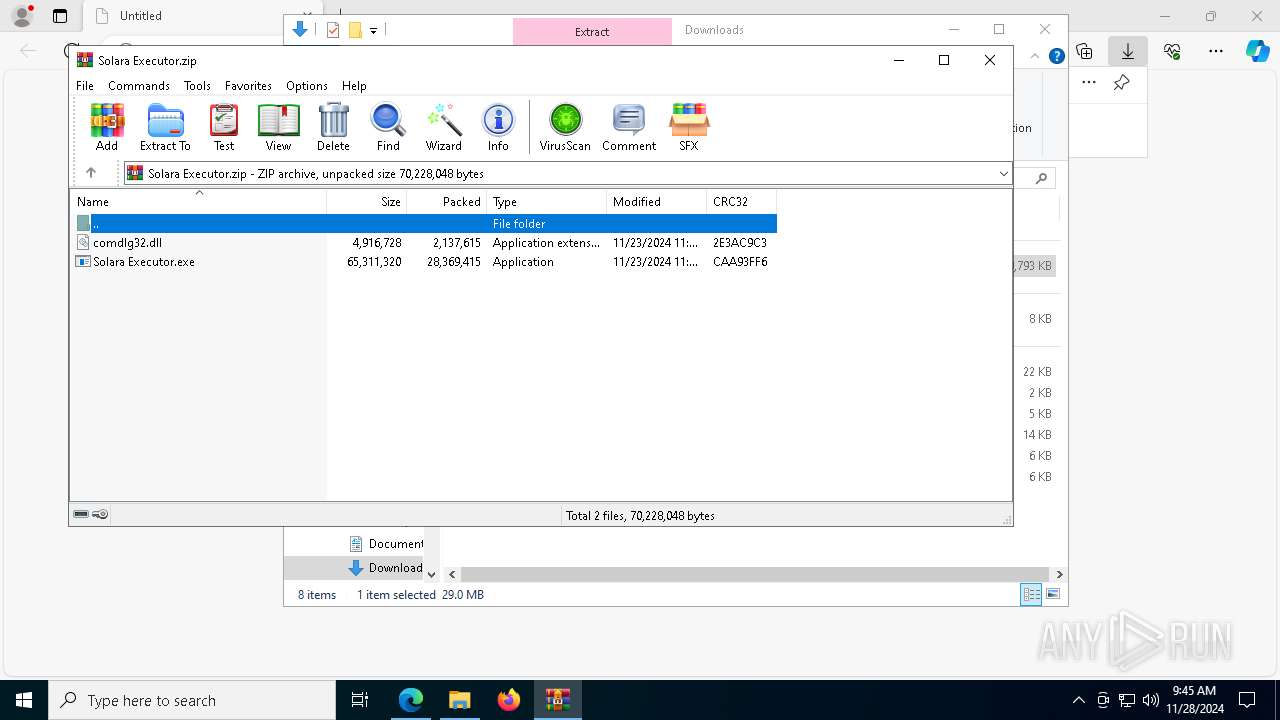
| MD5: | 716782C9673FF98B91FF819091D3E716 |
| SHA1: | 991C8CE8035ED4A7363EEA0992EBB347E3403187 |
| SHA256: | 57321DEEEB77DF8CC6012406D165153E50414F33510810A5DB190762147E56B5 |
| SSDEEP: | 3:N8cCWdy6//PUmhEwGKUsNTT4Vt3XRxKHAZcIlIyWdaUY/ZHwFERQVdUNLx:2cry6XPU0rpy7iAZcI/WdpWqFERPl |
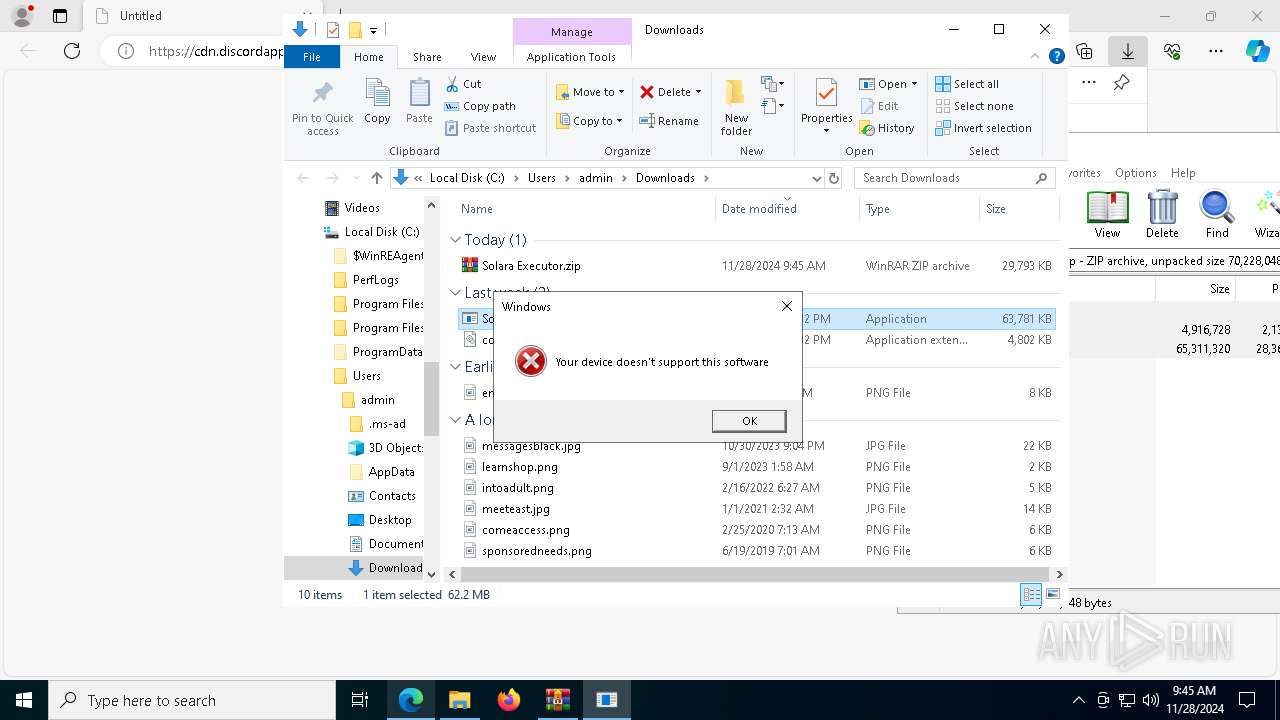
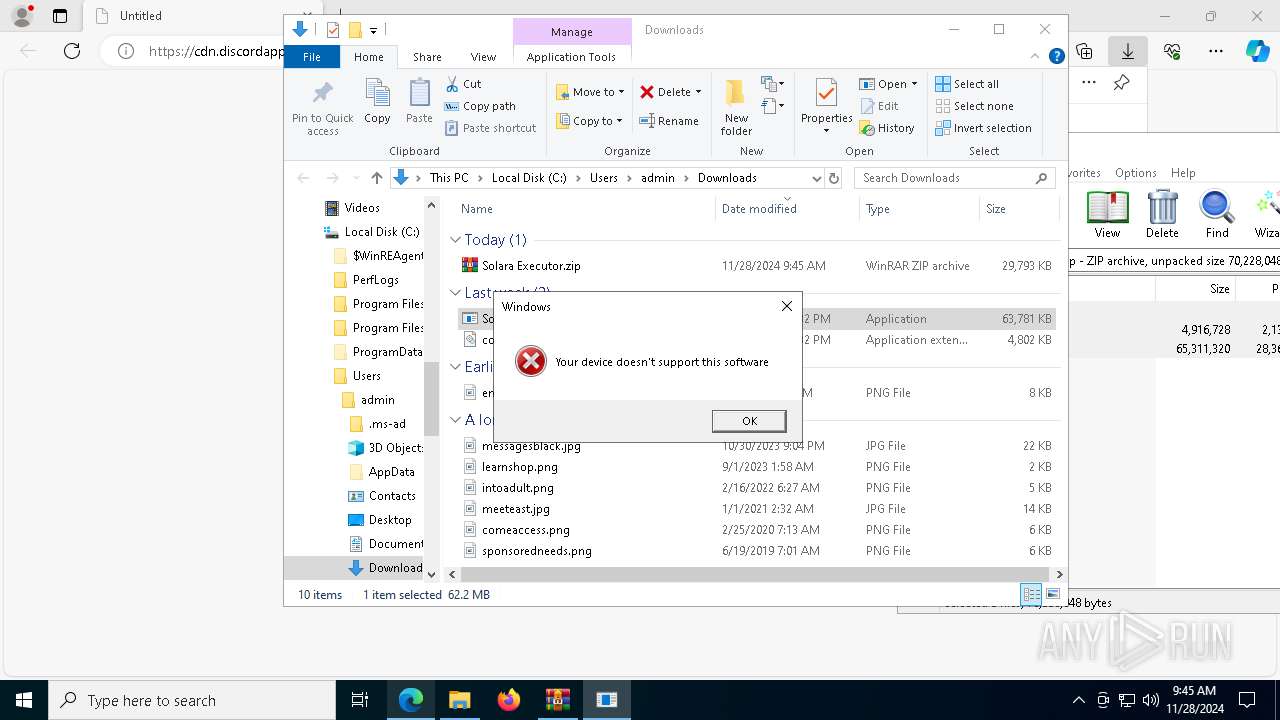
MALICIOUS
Executing a file with an untrusted certificate
- Solara Executor.exe (PID: 5472)
- Solara Executor.exe (PID: 5316)
Adds path to the Windows Defender exclusion list
- Solara Executor.exe (PID: 5316)
- powershell.exe (PID: 8104)
Uses Task Scheduler to run other applications
- Solara Executor.exe (PID: 5316)
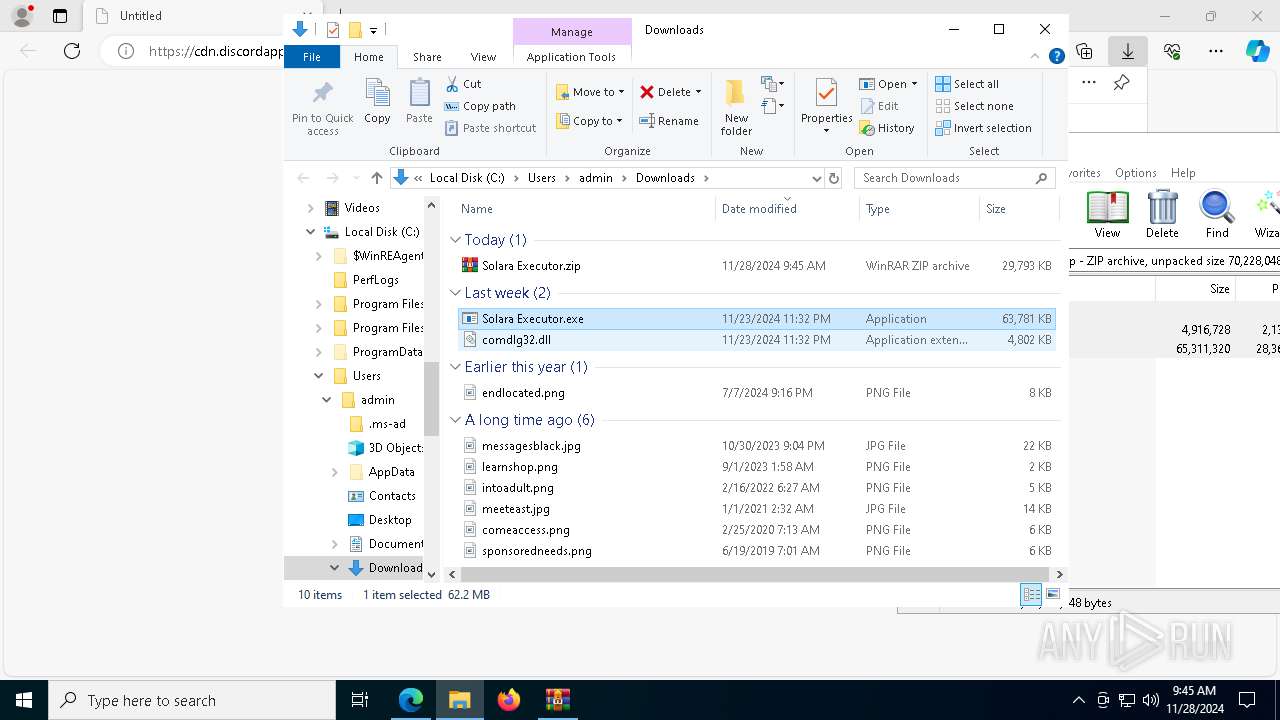
RHADAMANTHYS has been detected (SURICATA)
- svchost.exe (PID: 4932)
- svchost.exe (PID: 7076)
- dllhost.exe (PID: 7672)
RHADAMANTHYS has been detected (YARA)
- svchost.exe (PID: 7076)
Stealers network behavior
- svchost.exe (PID: 7076)
SUSPICIOUS
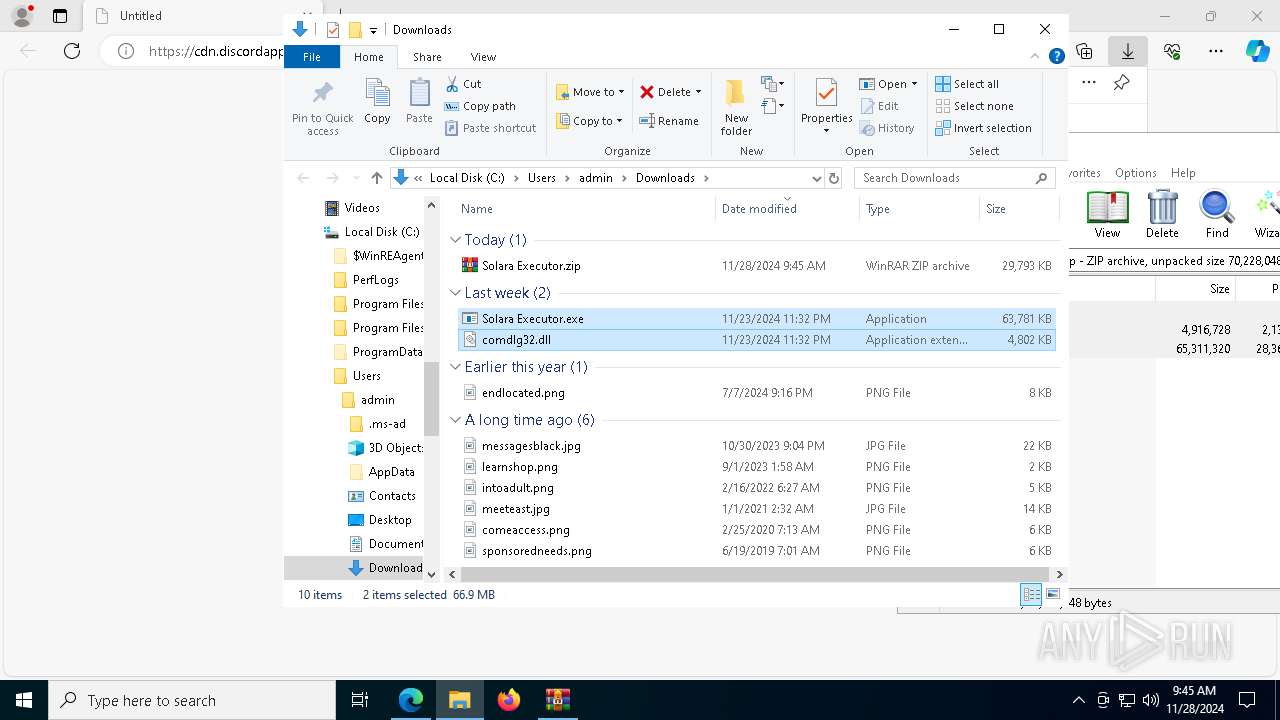
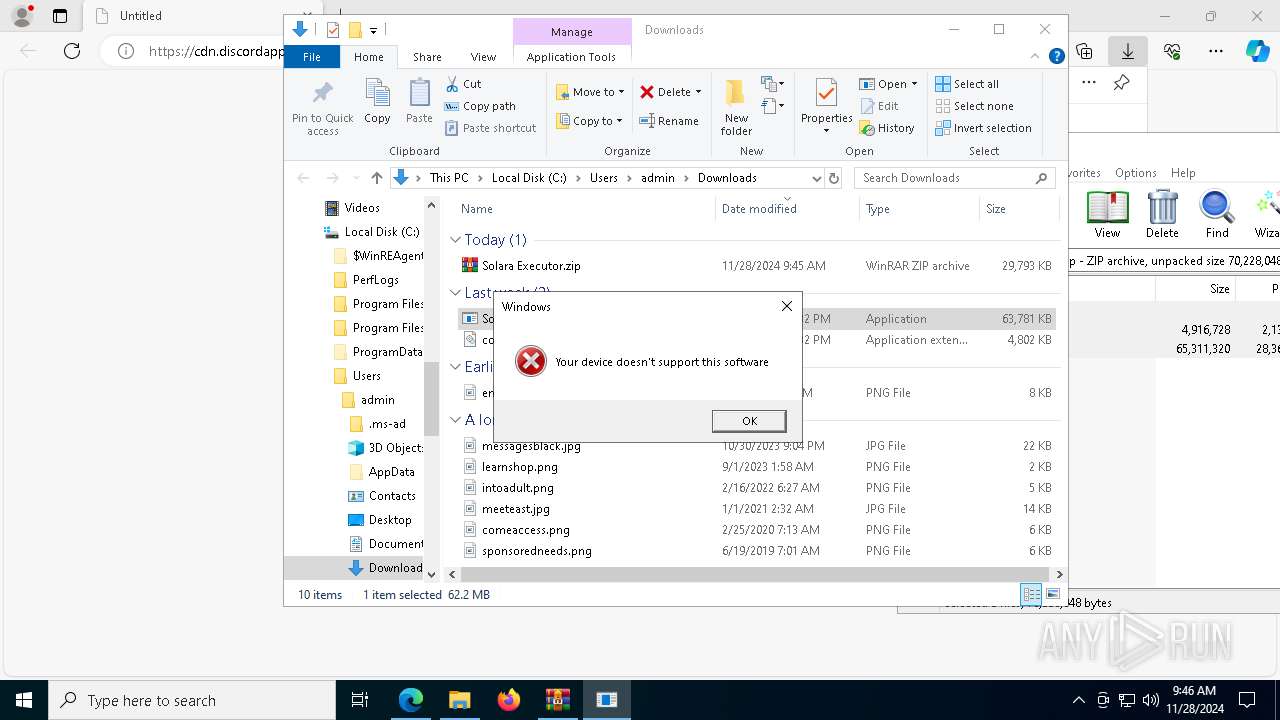
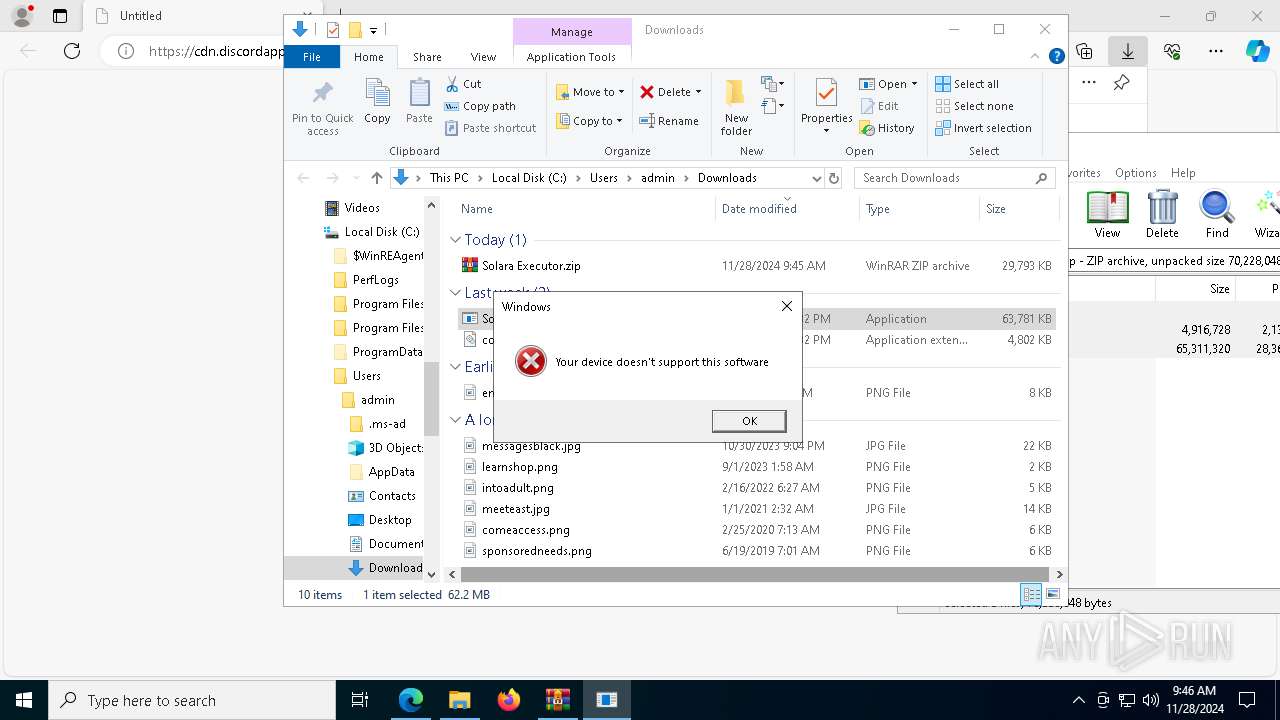
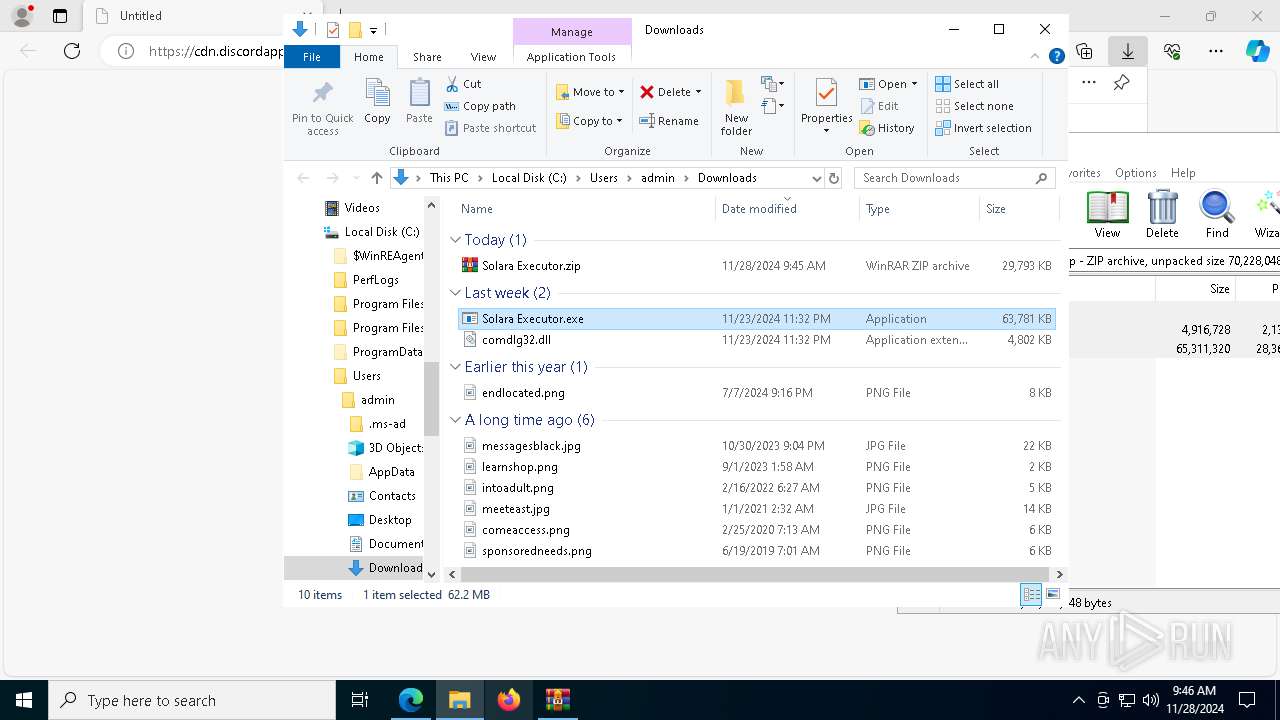
Process drops legitimate windows executable
- WinRAR.exe (PID: 396)
- msedge.exe (PID: 6580)
- msedge.exe (PID: 6236)
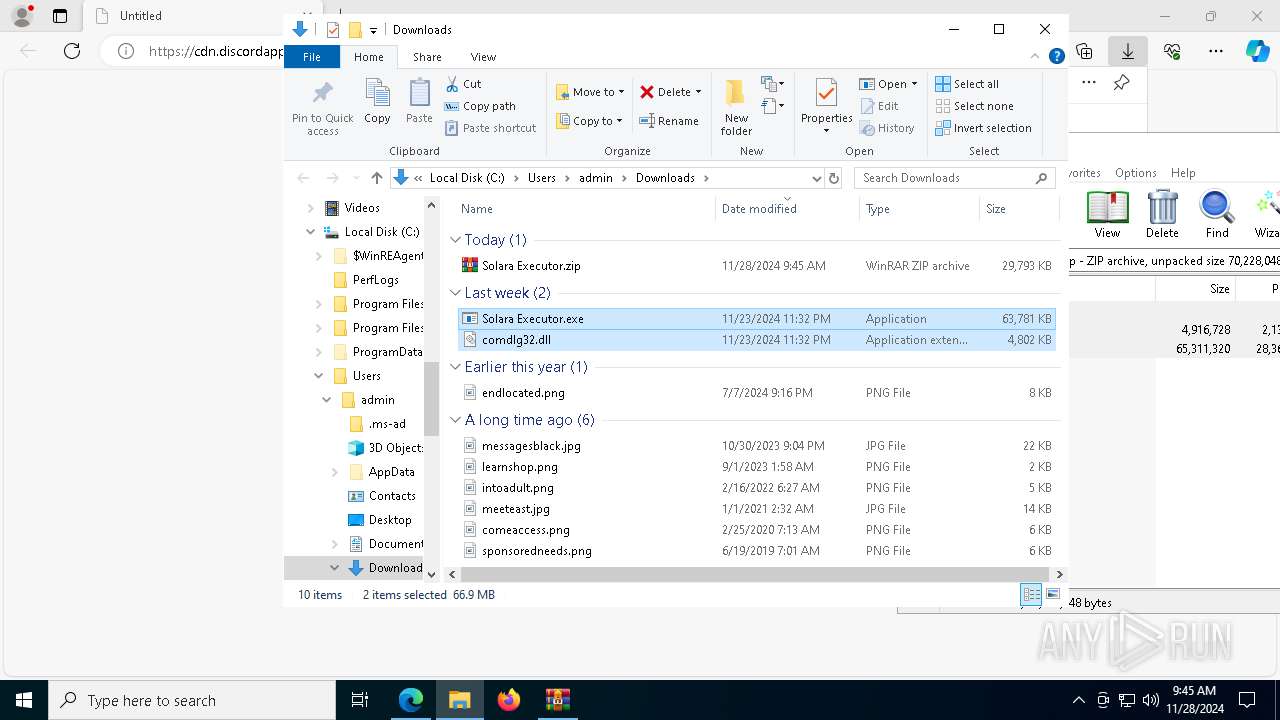
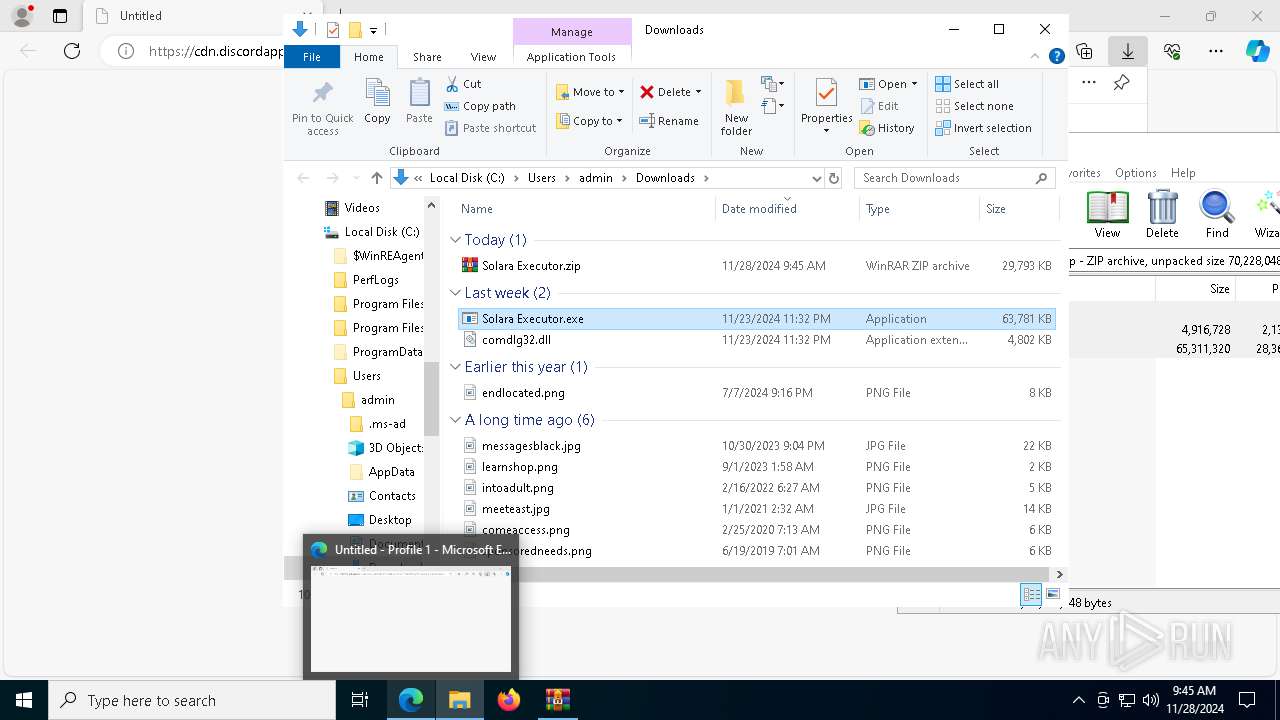
Application launched itself
- Solara Executor.exe (PID: 5472)
- powershell.exe (PID: 8104)
- msedge.exe (PID: 2996)
- chrome.exe (PID: 7340)
Discord domain found in command line (probably downloading payload)
- msedge.exe (PID: 6236)
Starts POWERSHELL.EXE for commands execution
- Solara Executor.exe (PID: 5316)
- powershell.exe (PID: 8104)
Script adds exclusion path to Windows Defender
- Solara Executor.exe (PID: 5316)
- powershell.exe (PID: 8104)
Uses WMIC.EXE to obtain Windows Installer data
- Solara Executor.exe (PID: 5316)
Connects to unusual port
- Solara Executor.exe (PID: 5316)
- svchost.exe (PID: 4932)
- svchost.exe (PID: 7076)
Executes application which crashes
- driver1.exe (PID: 1620)
Executable content was dropped or overwritten
- Solara Executor.exe (PID: 5316)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 4932)
- svchost.exe (PID: 7076)
- dllhost.exe (PID: 7672)
INFO
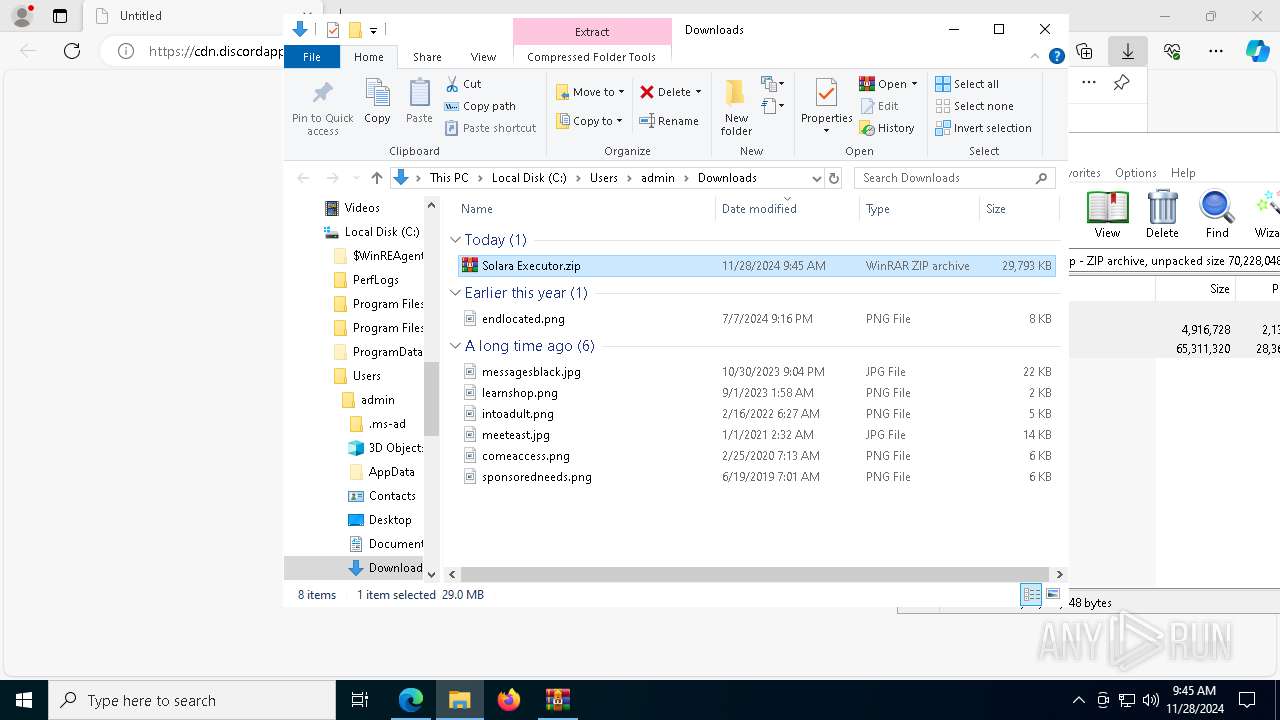
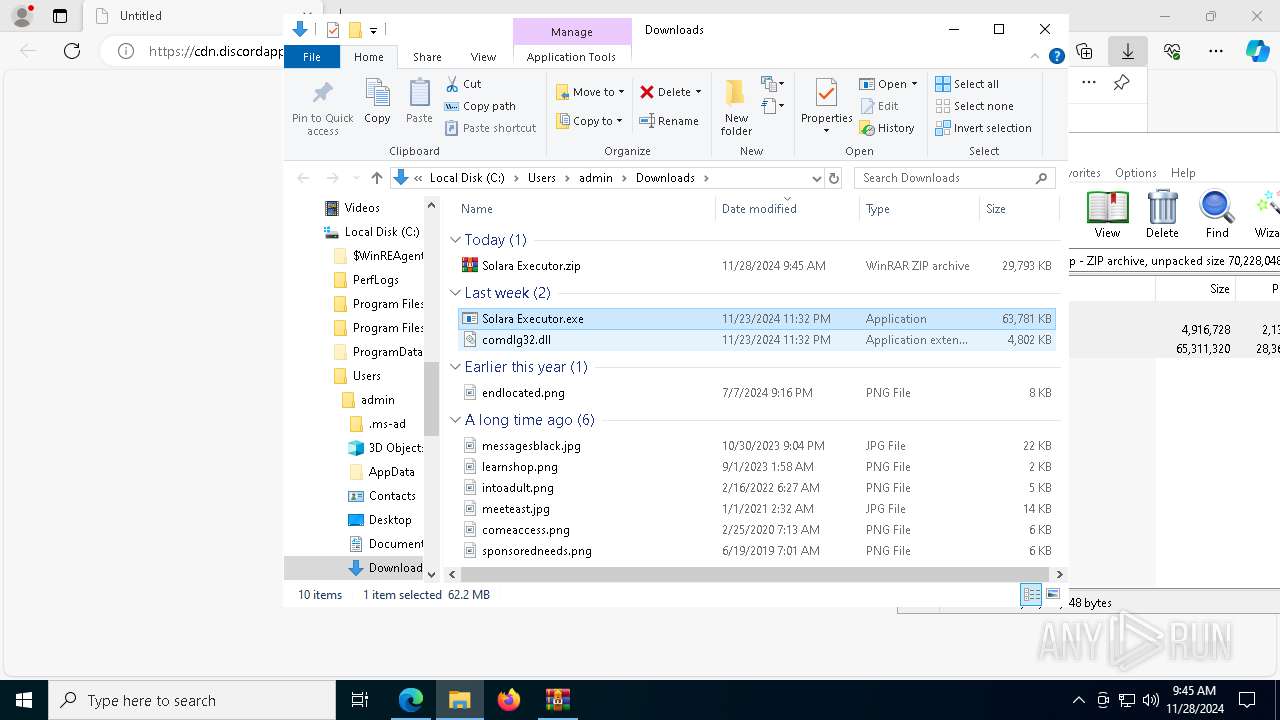
Manual execution by a user
- WinRAR.exe (PID: 396)
- Solara Executor.exe (PID: 5472)
- msedge.exe (PID: 3984)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 396)
- msedge.exe (PID: 7156)
Attempting to use instant messaging service
- msedge.exe (PID: 6580)
Application based on Golang
- Solara Executor.exe (PID: 5316)
Application launched itself
- msedge.exe (PID: 6236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
222
Monitored processes
83
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Solara Executor.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7280 --field-trial-handle=2336,i,2424695500059040611,17407969970968049678,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5468 --field-trial-handle=2336,i,2424695500059040611,17407969970968049678,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6044 --field-trial-handle=2336,i,2424695500059040611,17407969970968049678,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2228 --field-trial-handle=1912,i,3349087378271556125,2867023086890304052,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2180 --field-trial-handle=1912,i,3349087378271556125,2867023086890304052,262144 --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5524 --field-trial-handle=2336,i,2424695500059040611,17407969970968049678,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1620 | C:\ProgramData\driver1.exe | C:\ProgramData\driver1.exe | Solara Executor.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 2160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2332 --field-trial-handle=2324,i,10545636483106127403,8637337241922277327,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7524 --field-trial-handle=2336,i,2424695500059040611,17407969970968049678,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
32 455
Read events
32 410
Write events
40
Delete events
5
Modification events
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6E499D388C862F00 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 15F4A6388C862F00 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328536 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {68A21920-8739-4AA8-ACA0-5AB35BEC8067} | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BD92C6388C862F00 | |||
| (PID) Process: | (7852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000012CB203B7A41DB01 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
4
Suspicious files
438
Text files
129
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135382.TMP | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135382.TMP | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135382.TMP | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135392.TMP | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135382.TMP | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
89
DNS requests
78
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
188 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733056861&P2=404&P3=2&P4=Tk1Cf6RwNsFtHexdd8GwqWEvugk2DShuBvsxmdvXDinOHrJpKLzy9qh0RPEY9cPVr90EtQiCErRA40fNMRRa3g%3d%3d | unknown | — | — | whitelisted |
188 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733056861&P2=404&P3=2&P4=Tk1Cf6RwNsFtHexdd8GwqWEvugk2DShuBvsxmdvXDinOHrJpKLzy9qh0RPEY9cPVr90EtQiCErRA40fNMRRa3g%3d%3d | unknown | — | — | whitelisted |
5316 | Solara Executor.exe | GET | 301 | 157.240.251.35:80 | http://facebook.com/ | unknown | — | — | whitelisted |
5472 | Solara Executor.exe | GET | 301 | 157.240.251.35:80 | http://facebook.com/ | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5316 | Solara Executor.exe | GET | 301 | 157.240.251.174:80 | http://instagram.com/ | unknown | — | — | whitelisted |
7876 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
524 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7876 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5316 | Solara Executor.exe | GET | 200 | 147.45.47.37:1488 | http://147.45.47.37:1488/moa/Tricky.rar | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3220 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.160:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
524 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
524 | RUXIMICS.exe | 23.32.238.152:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6580 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6580 | msedge.exe | 162.159.130.233:443 | cdn.discordapp.com | — | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
cdn.discordapp.com |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6580 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6580 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
5472 | Solara Executor.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
5472 | Solara Executor.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
5316 | Solara Executor.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
5316 | Solara Executor.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
5316 | Solara Executor.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
5316 | Solara Executor.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host RAR Request |
5316 | Solara Executor.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
4932 | svchost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 25 |
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr2970.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr39DC.tmp directory exists )
|
dllhost.exe | ba 61 fe af b5 22 de 41
|
dllhost.exe | [service_reconnect_interval] set timer
|
dllhost.exe | [backend_tunnel_on_connect] set timer
|