| File name: | Lynx Ransomware |
| Full analysis: | https://app.any.run/tasks/c0f2aff1-b6f4-4e32-b97e-63d375393593 |
| Verdict: | Malicious activity |
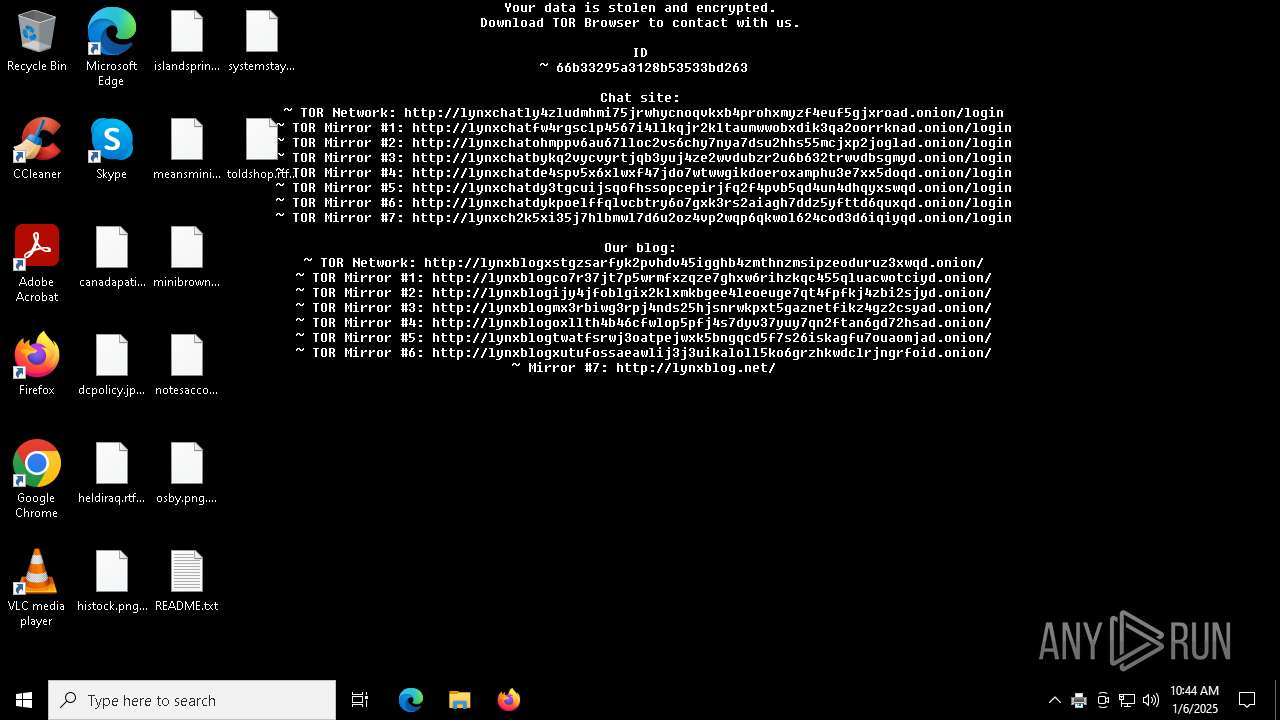
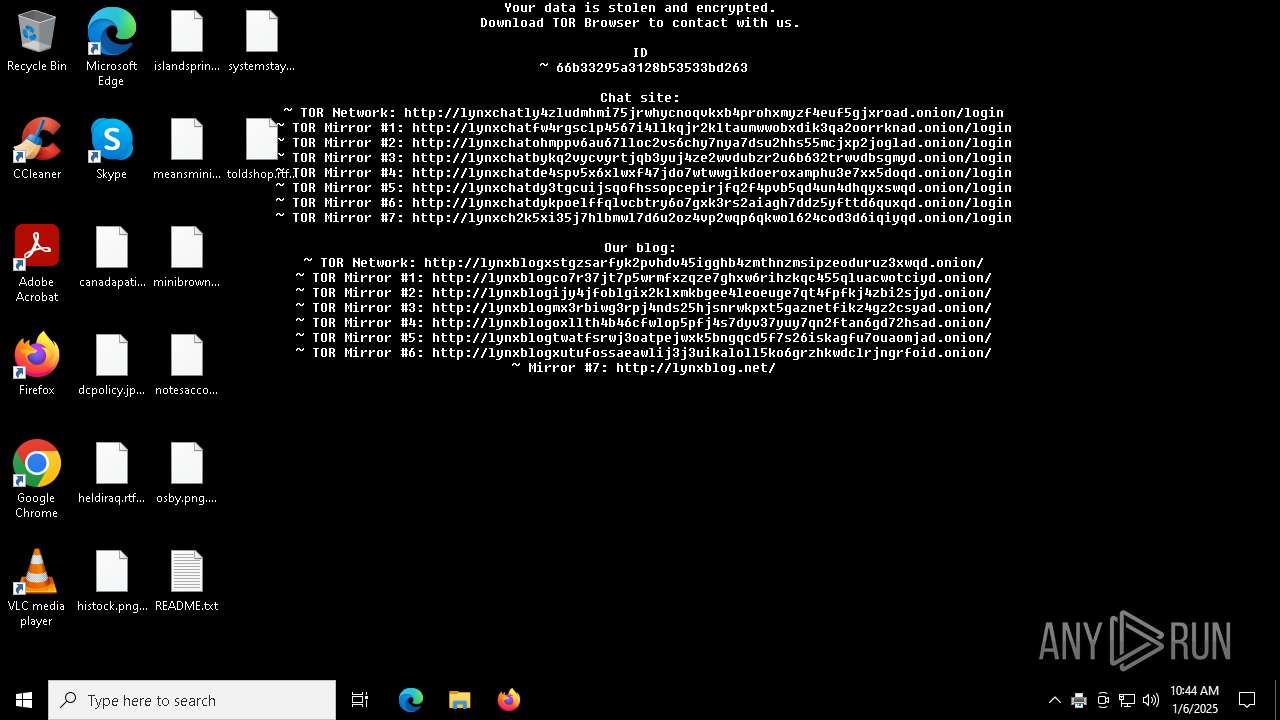
| Threats: | Lynx is a double extortion ransomware: attackers encrypt important and sensitive data and demand a ransom for decryption simultaneously threatening to publish or sell the data. Active since mid-2024. Among techniques are terminating processes and services, privilege escalation, deleting shadow copies. Distribution by phishing, malvertising, exploiting vulnerabilities. |
| Analysis date: | January 06, 2025, 10:44:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | D972BBBB3EDB0E5AB5751B911F3DDA17 |
| SHA1: | C632223F5F7A8A469BBF07EB017863BB83564B84 |
| SHA256: | 571F5DE9DD0D509ED7E5242B9B7473C2B2CBB36BA64D38B32122A0A337D6CF8B |
| SSDEEP: | 3072:U4BBDFFFb1jQRbLuZJ3hbUXe1FXkutxL4HBc6XwYUbgxFwxtMMeX4/PHhdse:UG1jYePWXAPxL4Hm6XwYUsAnBdse |
MALICIOUS
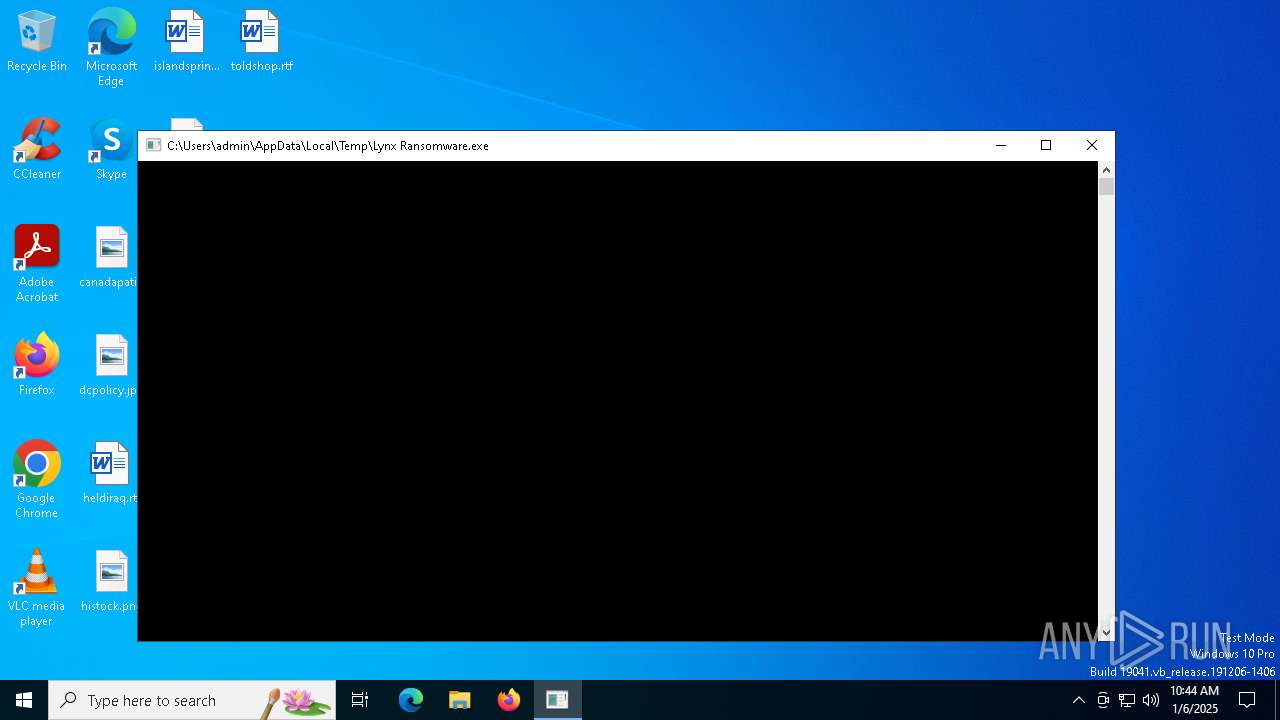
LYNX has been detected
- Lynx Ransomware.exe (PID: 5712)
Renames files like ransomware
- Lynx Ransomware.exe (PID: 5712)
Scans artifacts that could help determine the target
- ONENOTE.EXE (PID: 6244)
SUSPICIOUS
Executes as Windows Service
- FXSSVC.exe (PID: 6176)
Reads security settings of Internet Explorer
- ONENOTE.EXE (PID: 6244)
INFO
Creates files in the program directory
- Lynx Ransomware.exe (PID: 5712)
- FXSSVC.exe (PID: 6176)
Checks supported languages
- Lynx Ransomware.exe (PID: 5712)
- ONENOTE.EXE (PID: 6244)
Reads the machine GUID from the registry
- Lynx Ransomware.exe (PID: 5712)
Reads the computer name
- ONENOTE.EXE (PID: 6244)
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 6244)
Reads product name
- ONENOTE.EXE (PID: 6244)
Checks proxy server information
- ONENOTE.EXE (PID: 6244)
Reads the software policy settings
- ONENOTE.EXE (PID: 6244)
Creates files or folders in the user directory
- ONENOTE.EXE (PID: 6244)
Reads Environment values
- ONENOTE.EXE (PID: 6244)
Sends debugging messages
- ONENOTE.EXE (PID: 6244)
Reads CPU info
- ONENOTE.EXE (PID: 6244)
Process checks computer location settings
- ONENOTE.EXE (PID: 6244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:08:04 06:49:12+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 119808 |
| InitializedDataSize: | 49664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9de7 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
136
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Lynx Ransomware.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5712 | "C:\Users\admin\AppData\Local\Temp\Lynx Ransomware.exe" | C:\Users\admin\AppData\Local\Temp\Lynx Ransomware.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6176 | C:\WINDOWS\system32\fxssvc.exe | C:\Windows\System32\FXSSVC.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Fax Service Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6244 | /insertdoc "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\{E4166D67-A994-4958-8F82-B0076C75DF00}.xps" 133806338755930000 | C:\Program Files\Microsoft Office\root\Office16\ONENOTE.EXE | printfilterpipelinesvc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 9532 | C:\WINDOWS\system32\printfilterpipelinesvc.exe -Embedding | C:\Windows\System32\printfilterpipelinesvc.exe | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Print Filter Pipeline Host Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 760
Read events
7 504
Write events
232
Delete events
24
Modification events
| (PID) Process: | (5712) Lynx Ransomware.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp\\background-image.jpg | |||
| (PID) Process: | (6176) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax |
| Operation: | write | Name: | RedirectionGuard |
Value: 1 | |||
| (PID) Process: | (6176) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Receipts |
| Operation: | write | Name: | Password |
Value: 00 | |||
| (PID) Process: | (6176) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Receipts |
| Operation: | delete value | Name: | Password |
Value: | |||
| (PID) Process: | (6176) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Receipts |
| Operation: | write | Name: | Server |
Value: | |||
| (PID) Process: | (6176) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Receipts |
| Operation: | write | Name: | From |
Value: | |||
| (PID) Process: | (6176) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Receipts |
| Operation: | write | Name: | User |
Value: | |||
| (PID) Process: | (6176) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Security |
| Operation: | write | Name: | Descriptor |
Value: 010004805C000000680000000000000014000000020048000300000000001800E7020E000102000000000005200000002002000000001400030002000101000000000001000000000000140027020200010100000000000504000000010100000000000514000000010100000000000514000000 | |||
| (PID) Process: | (6176) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Outbound Routing\Groups\<All devices> |
| Operation: | write | Name: | Devices |
Value: | |||
| (PID) Process: | (6176) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Outbound Routing\Rules\0:0 |
| Operation: | write | Name: | CountryCode |
Value: 0 | |||
Executable files
0
Suspicious files
195
Text files
120
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5712 | Lynx Ransomware.exe | C:\ProgramData\Adobe\ARM\Acrobat_23.001.20093\AcroRdrDCx64Upd2300820470_MUI.msp | — | |
MD5:— | SHA256:— | |||
| 5712 | Lynx Ransomware.exe | C:\ProgramData\Adobe\ARM\Acrobat_23.001.20093\AcroRdrDCx64Upd2300820470_MUI.msp.LYNX | — | |
MD5:— | SHA256:— | |||
| 5712 | Lynx Ransomware.exe | C:\ProgramData\Microsoft\User Account Pictures\admin.dat | — | |
MD5:— | SHA256:— | |||
| 5712 | Lynx Ransomware.exe | C:\ProgramData\Microsoft OneDrive\setup\refcount.ini | — | |
MD5:— | SHA256:— | |||
| 5712 | Lynx Ransomware.exe | C:\ProgramData\Adobe\ARM\S\README.txt | text | |
MD5:4B051374CF41085B6A50968EB0C37423 | SHA256:9BF2BA205A39030FB75C270FF117B3A2496CB40CBFEC44C2906D86B6E668E31B | |||
| 5712 | Lynx Ransomware.exe | C:\ProgramData\Microsoft\NetFramework\BreadcrumbStore\README.txt | text | |
MD5:4B051374CF41085B6A50968EB0C37423 | SHA256:9BF2BA205A39030FB75C270FF117B3A2496CB40CBFEC44C2906D86B6E668E31B | |||
| 5712 | Lynx Ransomware.exe | C:\ProgramData\Mozilla-1de4eec8-1241-4177-a864-e594e8d1fb38\UpdateLock-308046B0AF4A39CB | — | |
MD5:— | SHA256:— | |||
| 5712 | Lynx Ransomware.exe | C:\ProgramData\Microsoft\DataMart\PaidWiFi\README.txt | text | |
MD5:4B051374CF41085B6A50968EB0C37423 | SHA256:9BF2BA205A39030FB75C270FF117B3A2496CB40CBFEC44C2906D86B6E668E31B | |||
| 5712 | Lynx Ransomware.exe | C:\ProgramData\Adobe\ARM\Acrobat_23.001.20093\README.txt | text | |
MD5:4B051374CF41085B6A50968EB0C37423 | SHA256:9BF2BA205A39030FB75C270FF117B3A2496CB40CBFEC44C2906D86B6E668E31B | |||
| 5712 | Lynx Ransomware.exe | C:\ProgramData\Adobe\ARM\README.txt | text | |
MD5:4B051374CF41085B6A50968EB0C37423 | SHA256:9BF2BA205A39030FB75C270FF117B3A2496CB40CBFEC44C2906D86B6E668E31B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
40
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6244 | ONENOTE.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6848 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.154:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
Threats
Process | Message |
|---|---|
ONENOTE.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ONENOTE.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ONENOTE.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|