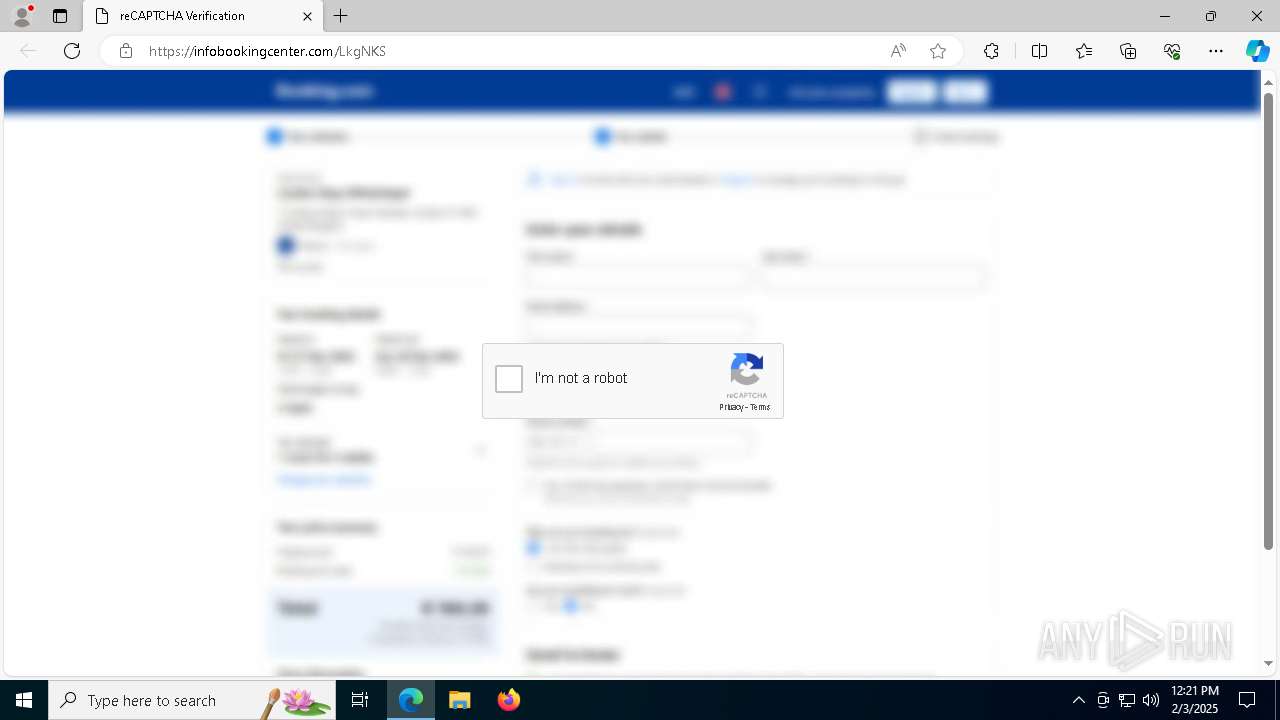
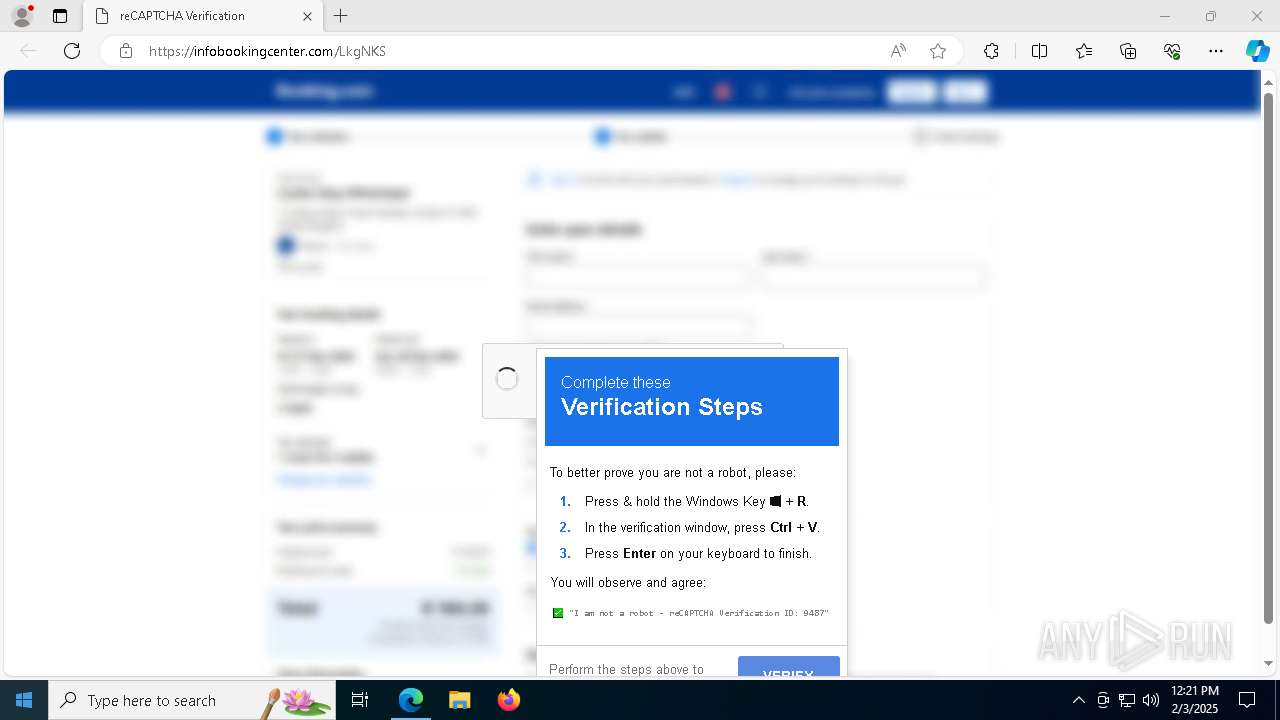
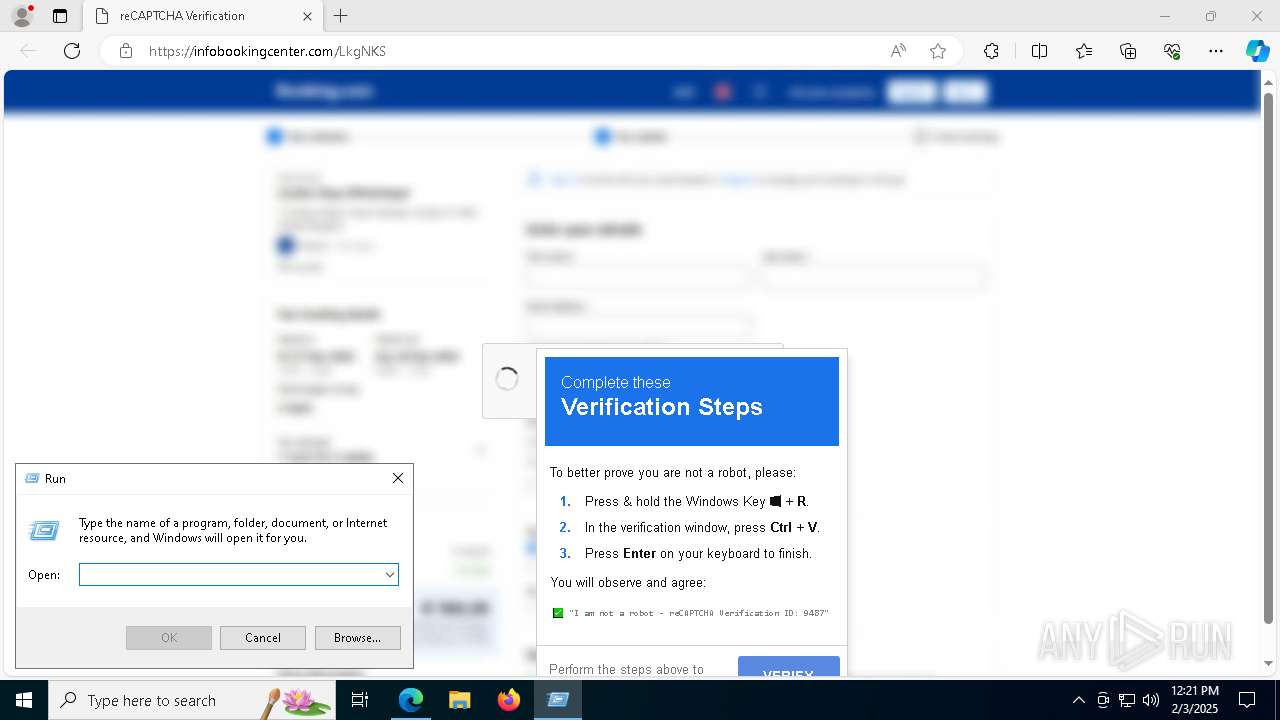
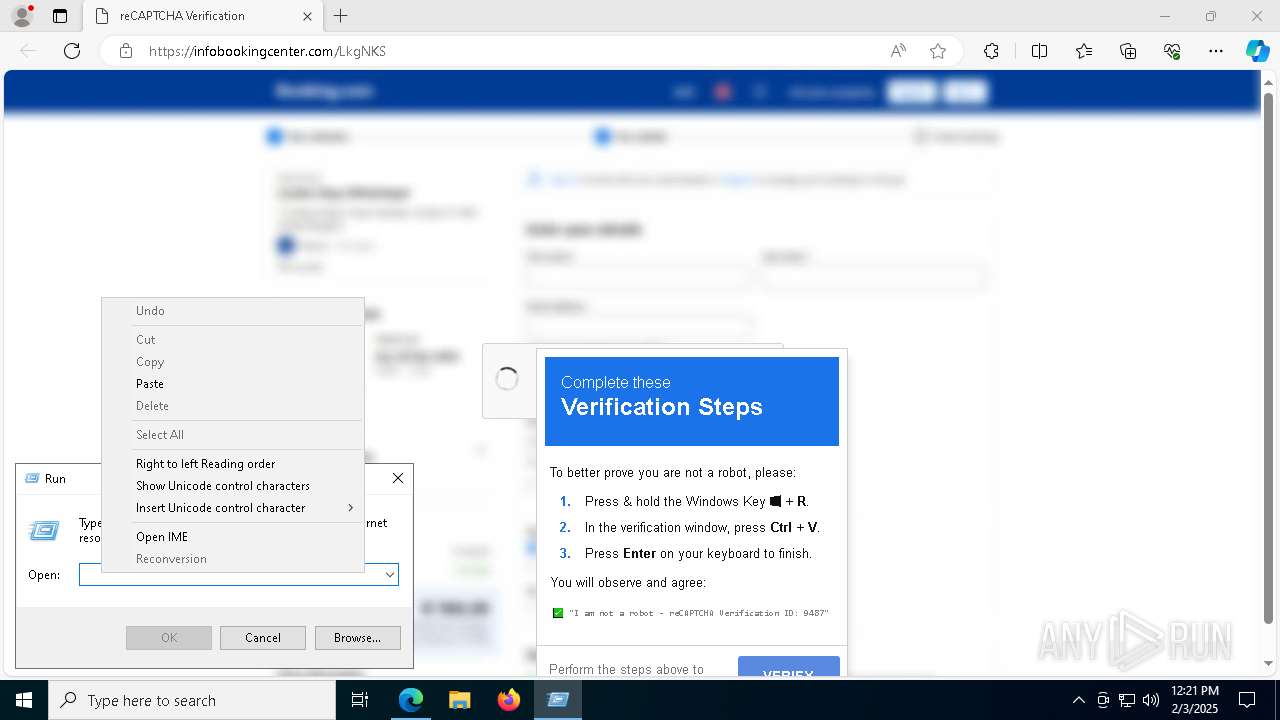
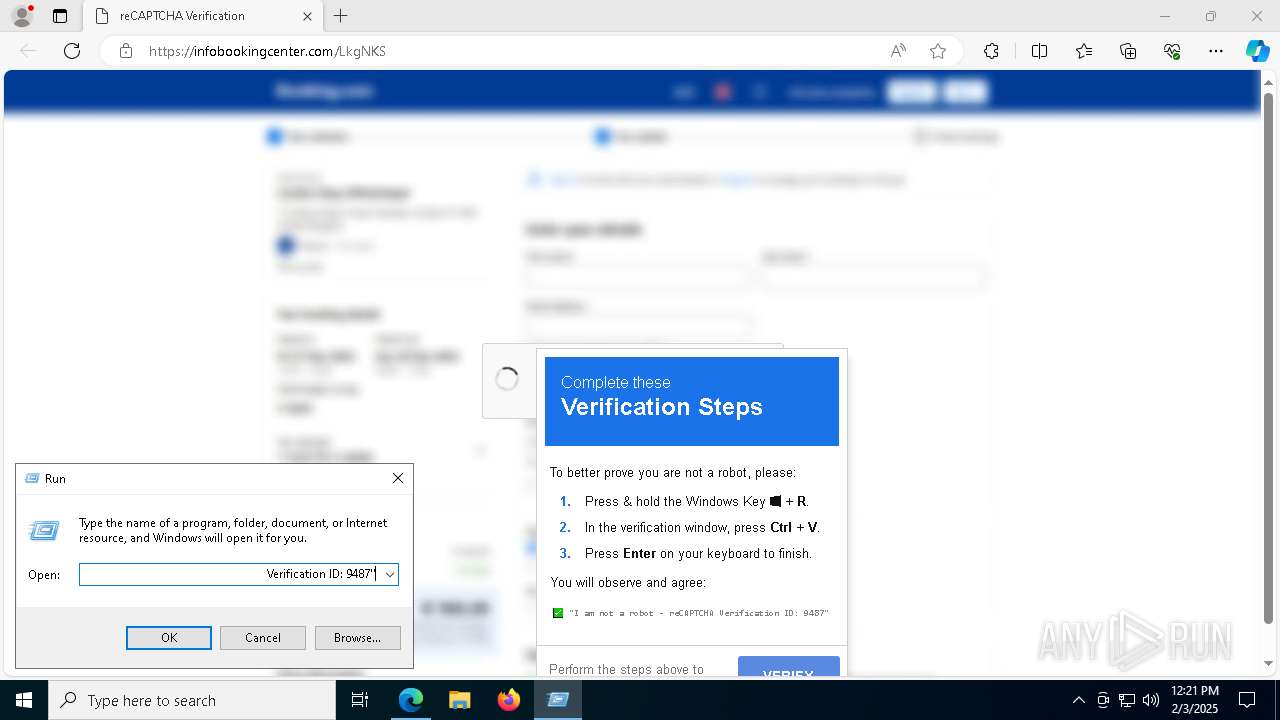
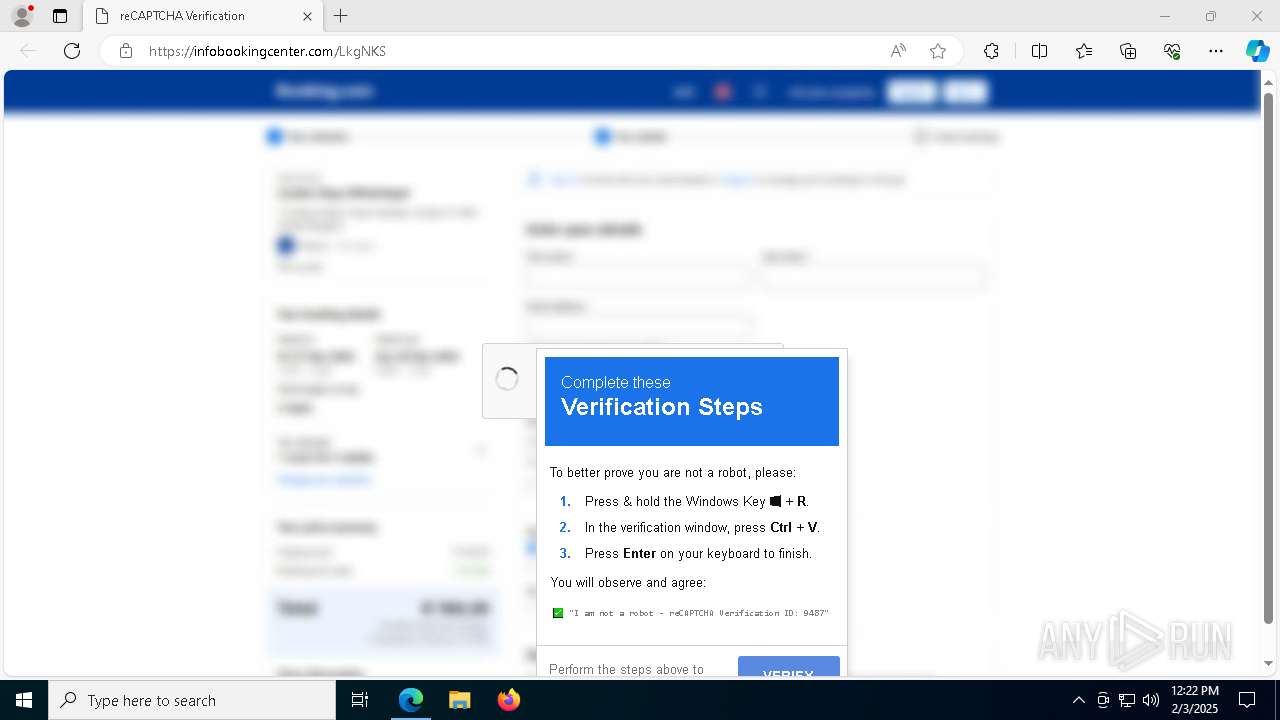
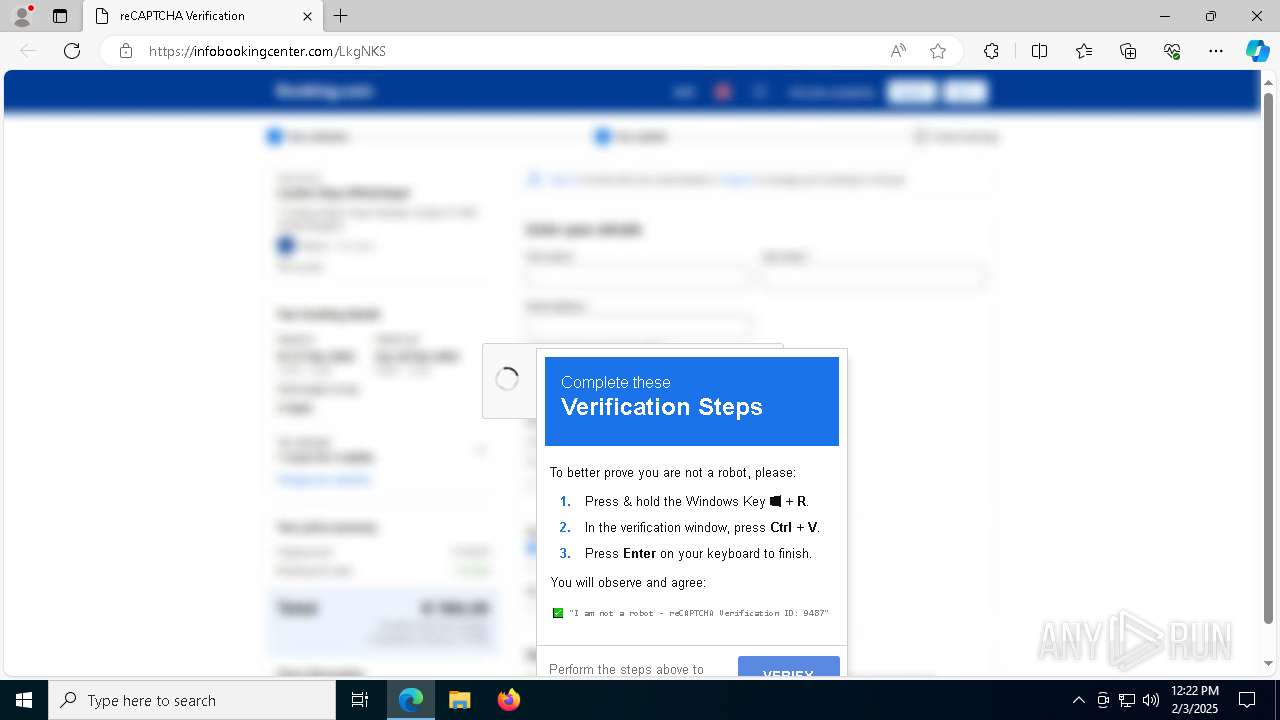
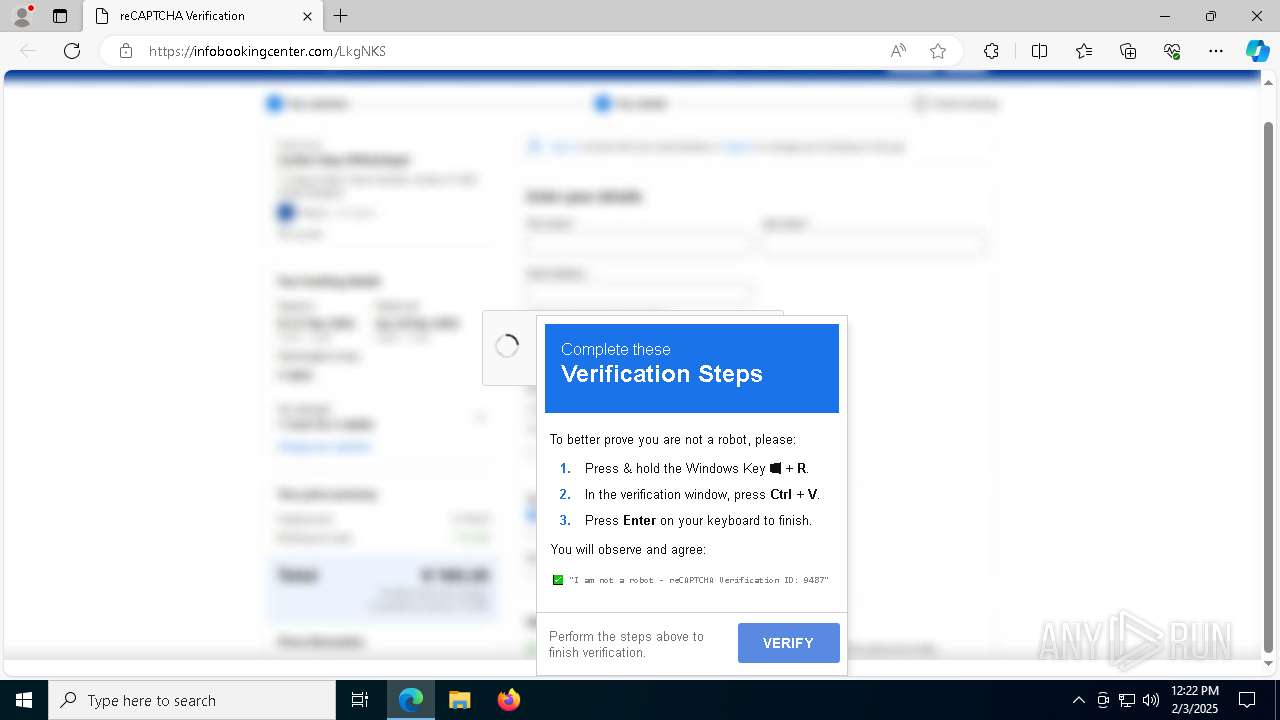
| URL: | https://infobookingcenter.com/LkgNKS |
| Full analysis: | https://app.any.run/tasks/f77a3fb6-d00d-4beb-86d6-bee0b95fd62c |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 03, 2025, 12:21:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A66A3FA5B665529ECD7B01EC61365C37 |
| SHA1: | FDC36AA251C541C7094D9C343A8C48C1F7CC6245 |
| SHA256: | 5697D5F20B9AD78F6D8DC4404A0A986BB02FBB8A4634691C1340643F7E70ACC4 |
| SSDEEP: | 3:N8e74LGKZZu2n:2eKo2n |
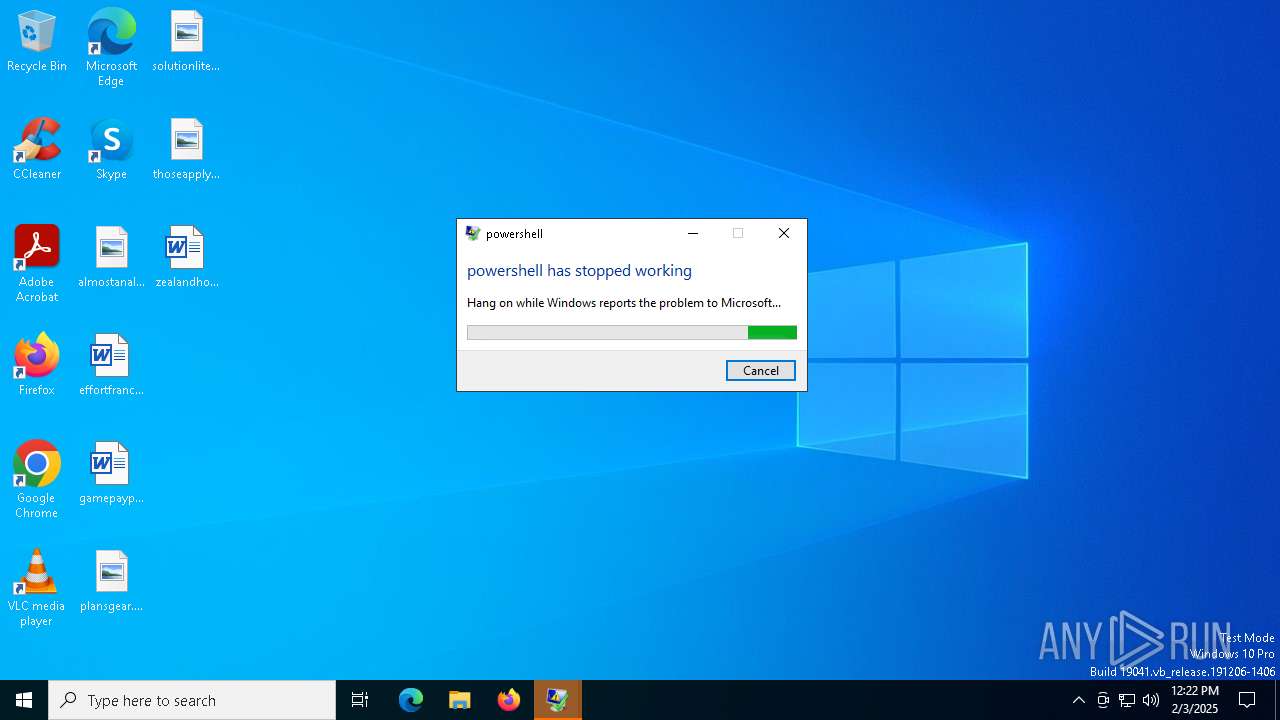
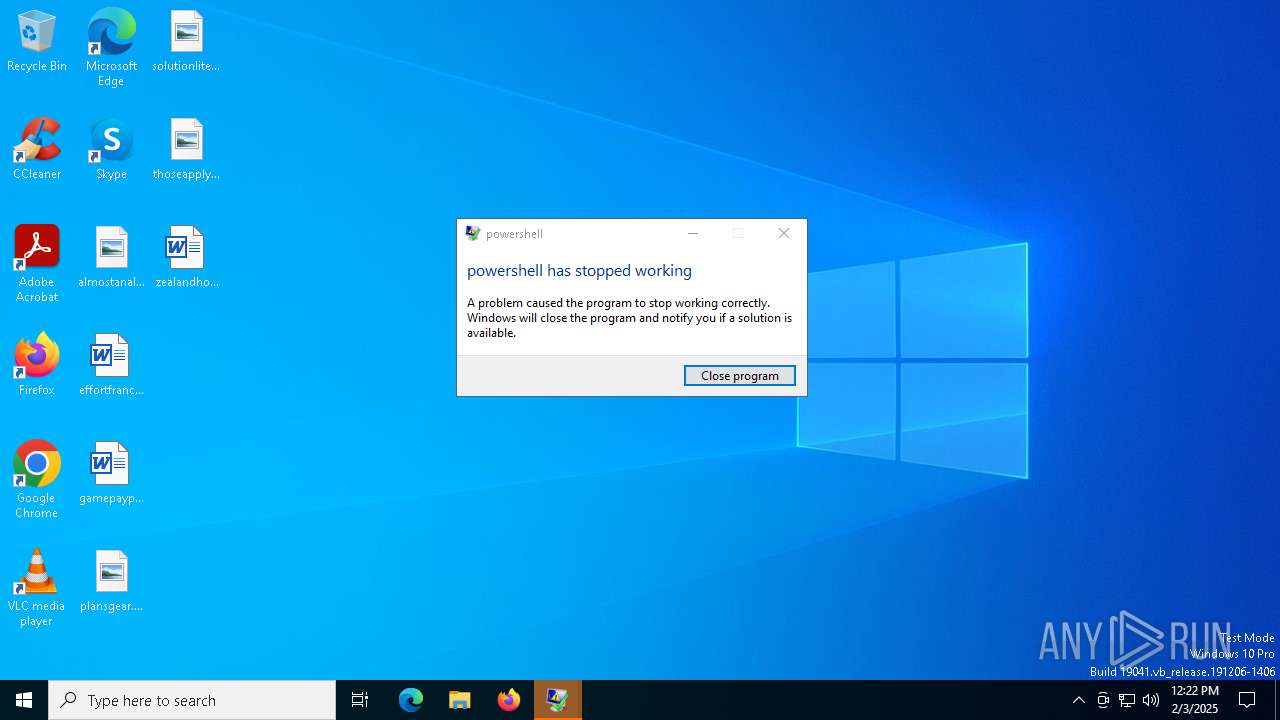
MALICIOUS
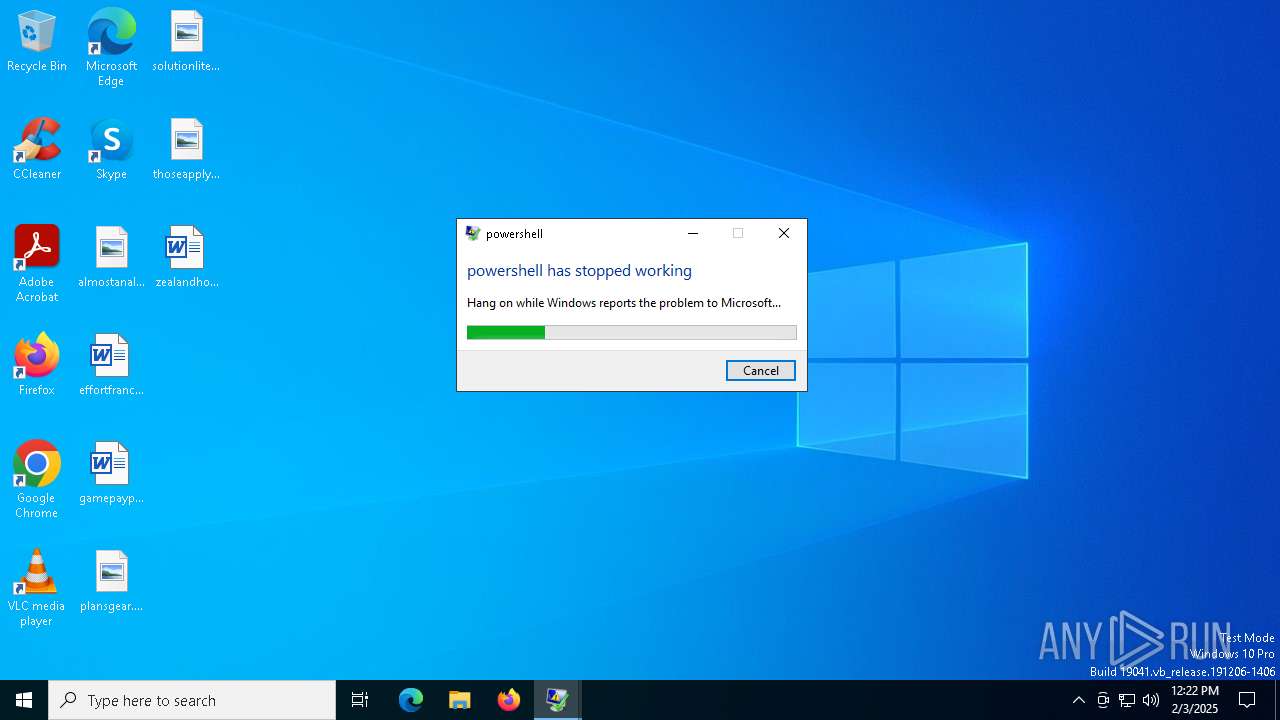
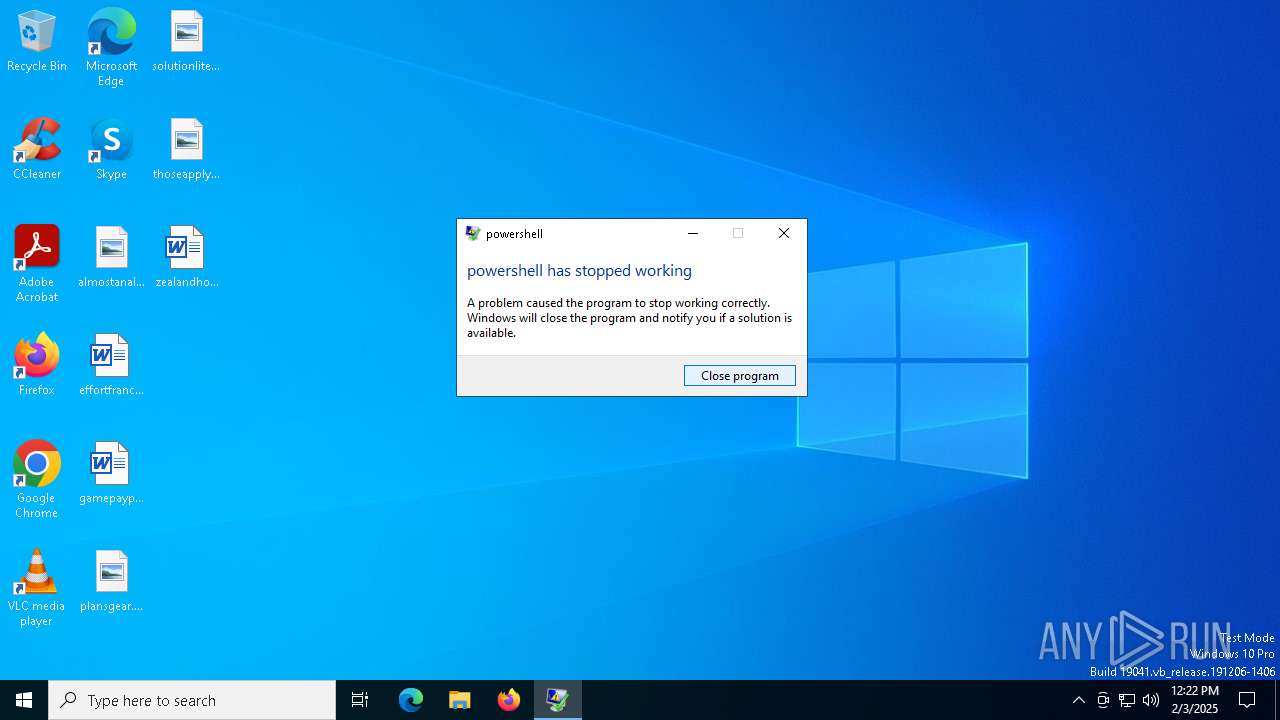
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 3568)
- powershell.exe (PID: 3288)
- powershell.exe (PID: 5736)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 3288)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 5736)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 3288)
Changes the autorun value in the registry
- RegSvcs.exe (PID: 7456)
LUMMA mutex has been found
- RegSvcs.exe (PID: 7624)
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 7624)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 7624)
XWORM has been detected (SURICATA)
- RegSvcs.exe (PID: 7484)
XWORM has been detected (YARA)
- RegSvcs.exe (PID: 7484)
SUSPICIOUS
Obfuscated call of IEX
- powershell.exe (PID: 3568)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 3288)
Found IP address in command line
- powershell.exe (PID: 3568)
- powershell.exe (PID: 3288)
- powershell.exe (PID: 5736)
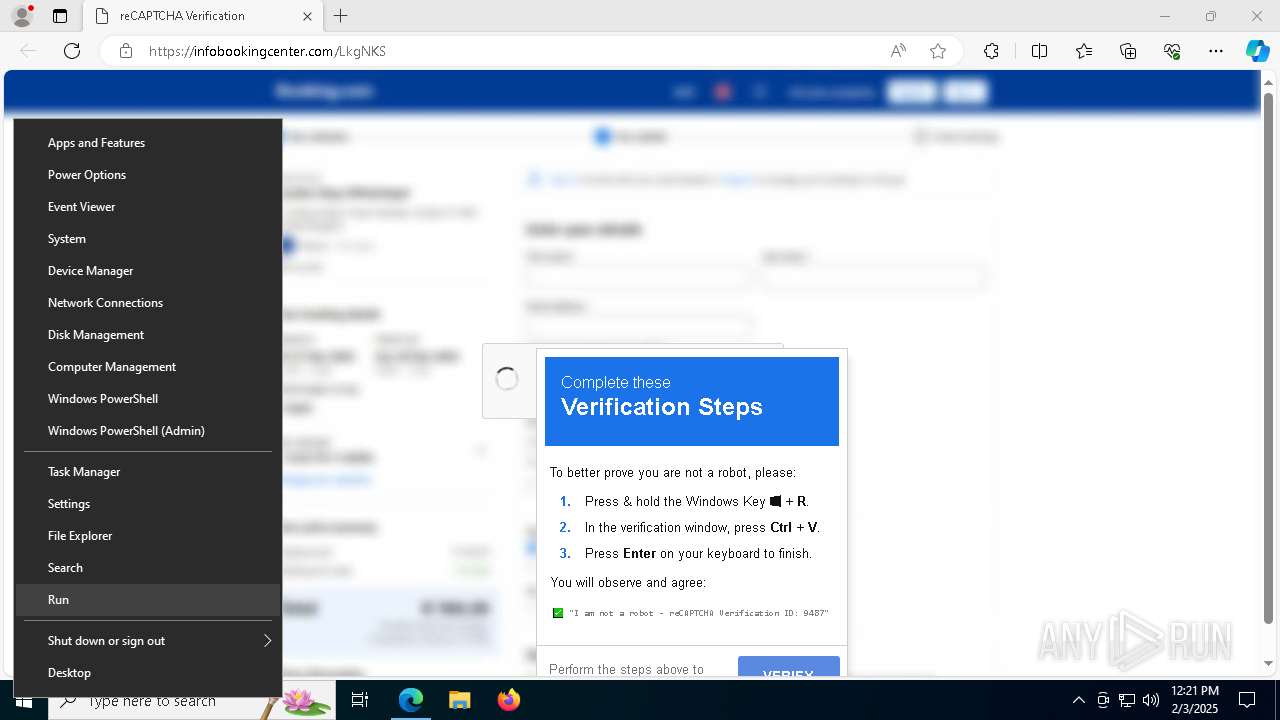
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 6012)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 6012)
Connects to the server without a host name
- powershell.exe (PID: 3568)
- powershell.exe (PID: 3288)
- powershell.exe (PID: 5736)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 3288)
The process creates files with name similar to system file names
- wermgr.exe (PID: 7576)
- wermgr.exe (PID: 7568)
- wermgr.exe (PID: 7652)
Searches for installed software
- RegSvcs.exe (PID: 7624)
Connects to unusual port
- RegSvcs.exe (PID: 7484)
Contacting a server suspected of hosting an CnC
- RegSvcs.exe (PID: 7484)
INFO
Checks supported languages
- identity_helper.exe (PID: 5652)
- RegSvcs.exe (PID: 7456)
- RegSvcs.exe (PID: 7624)
- RegSvcs.exe (PID: 7484)
- identity_helper.exe (PID: 6664)
Reads Environment values
- identity_helper.exe (PID: 5652)
- identity_helper.exe (PID: 6664)
Reads the computer name
- identity_helper.exe (PID: 5652)
- RegSvcs.exe (PID: 7484)
- RegSvcs.exe (PID: 7624)
- RegSvcs.exe (PID: 7456)
- identity_helper.exe (PID: 6664)
Manual execution by a user
- mshta.exe (PID: 6012)
Application launched itself
- msedge.exe (PID: 3732)
- msedge.exe (PID: 7884)
Reads Internet Explorer settings
- mshta.exe (PID: 6012)
Checks proxy server information
- mshta.exe (PID: 6012)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 3288)
- wermgr.exe (PID: 7576)
- wermgr.exe (PID: 7568)
- wermgr.exe (PID: 7652)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 3288)
- powershell.exe (PID: 5736)
Disables trace logs
- powershell.exe (PID: 3288)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 3568)
Creates files in the program directory
- powershell.exe (PID: 3288)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 5736)
Reads the software policy settings
- RegSvcs.exe (PID: 7624)
- wermgr.exe (PID: 7576)
- wermgr.exe (PID: 7568)
- wermgr.exe (PID: 7652)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 7624)
- RegSvcs.exe (PID: 7484)
Detects Fody packer (YARA)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 3288)
Executable content was dropped or overwritten
- msedge.exe (PID: 6916)
The sample compiled with english language support
- msedge.exe (PID: 6916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(7484) RegSvcs.exe
C2176.113.115.225:4444
Keys
AESP0WER
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm
MutexpWbxsRP5Z5tLW4V1
Total processes
225
Monitored processes
82
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6164 --field-trial-handle=2276,i,15581659043512282817,4559880208366846746,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1400 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3076 --field-trial-handle=2324,i,16962540182722365730,4048401529104293461,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5508 --field-trial-handle=2324,i,16962540182722365730,4048401529104293461,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4500 --field-trial-handle=2324,i,16962540182722365730,4048401529104293461,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2152 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6124 --field-trial-handle=2324,i,16962540182722365730,4048401529104293461,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5856 --field-trial-handle=2324,i,16962540182722365730,4048401529104293461,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6828 --field-trial-handle=2276,i,15581659043512282817,4559880208366846746,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2612 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6884 --field-trial-handle=2276,i,15581659043512282817,4559880208366846746,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
50 477
Read events
50 448
Write events
29
Delete events
0
Modification events
| (PID) Process: | (3732) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3732) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3732) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3732) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3732) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5C930938D28B2F00 | |||
| (PID) Process: | (3732) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393904 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FC640BE7-5817-4036-BAB8-B004BBB21296} | |||
| (PID) Process: | (3732) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393904 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6951F5B3-4AA4-4A0C-93F5-FEAF8FC837AA} | |||
| (PID) Process: | (3732) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C0928338D28B2F00 | |||
| (PID) Process: | (3732) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 706B1C38D28B2F00 | |||
| (PID) Process: | (3732) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393904 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4AAA1E1C-48F4-4FB9-A4EC-5B27925E8827} | |||
Executable files
19
Suspicious files
419
Text files
123
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13642c.TMP | — | |
MD5:— | SHA256:— | |||
| 3732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13642c.TMP | — | |
MD5:— | SHA256:— | |||
| 3732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13643b.TMP | — | |
MD5:— | SHA256:— | |||
| 3732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF13643b.TMP | — | |
MD5:— | SHA256:— | |||
| 3732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136489.TMP | — | |
MD5:— | SHA256:— | |||
| 3732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
163
TCP/UDP connections
133
DNS requests
84
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 13.107.253.45:443 | https://edge-mobile-static.azureedge.net/eccp/get?settenant=edge-config&setplatform=win&setmkt=en-US&setchannel=stable | unknown | — | — | unknown |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/api/v1/user/token/microsoftgraph?&clienttype=edge-omnibox | unknown | — | — | unknown |
— | — | OPTIONS | 504 | 23.48.23.152:443 | https://bzib.nelreports.net/api/report?cat=bingbusiness | unknown | — | — | unknown |
— | — | GET | 200 | 142.250.186.100:443 | https://www.google.com/recaptcha/about/images/reCAPTCHA-logo@2x.png | unknown | image | 17.7 Kb | whitelisted |
— | — | GET | 200 | 172.67.142.245:443 | https://use.fontawesome.com/releases/v5.0.0/css/all.css | unknown | text | 32.6 Kb | whitelisted |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/work/api/v2/tenant/my/settingswithflights?&clienttype=edge-omnibox | unknown | binary | 591 b | whitelisted |
— | — | GET | 200 | 13.107.21.239:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=122.0.2365.59&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | binary | 748 b | whitelisted |
— | — | GET | 200 | 204.79.197.239:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=arbitration_priority_list&version=9.*.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | unknown | text | 271 b | whitelisted |
— | — | GET | 200 | 13.107.21.239:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=edge_hub_apps_manifest_gz&version=4.10.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | unknown | text | 266 b | whitelisted |
— | — | GET | 200 | 13.107.253.45:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v2/GetEligibleSites?version=0&type=topSite&IsStable=false | unknown | binary | 497 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6296 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6296 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6296 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3732 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6296 | msedge.exe | 104.21.32.1:443 | infobookingcenter.com | CLOUDFLARENET | — | unknown |
6296 | msedge.exe | 104.21.27.152:443 | use.fontawesome.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
infobookingcenter.com |
| unknown |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
use.fontawesome.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6296 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
7484 | RegSvcs.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm Network Packet |