| File name: | 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792 |
| Full analysis: | https://app.any.run/tasks/f9c08a31-3bb8-4c57-b656-cff7faa61679 |
| Verdict: | Malicious activity |
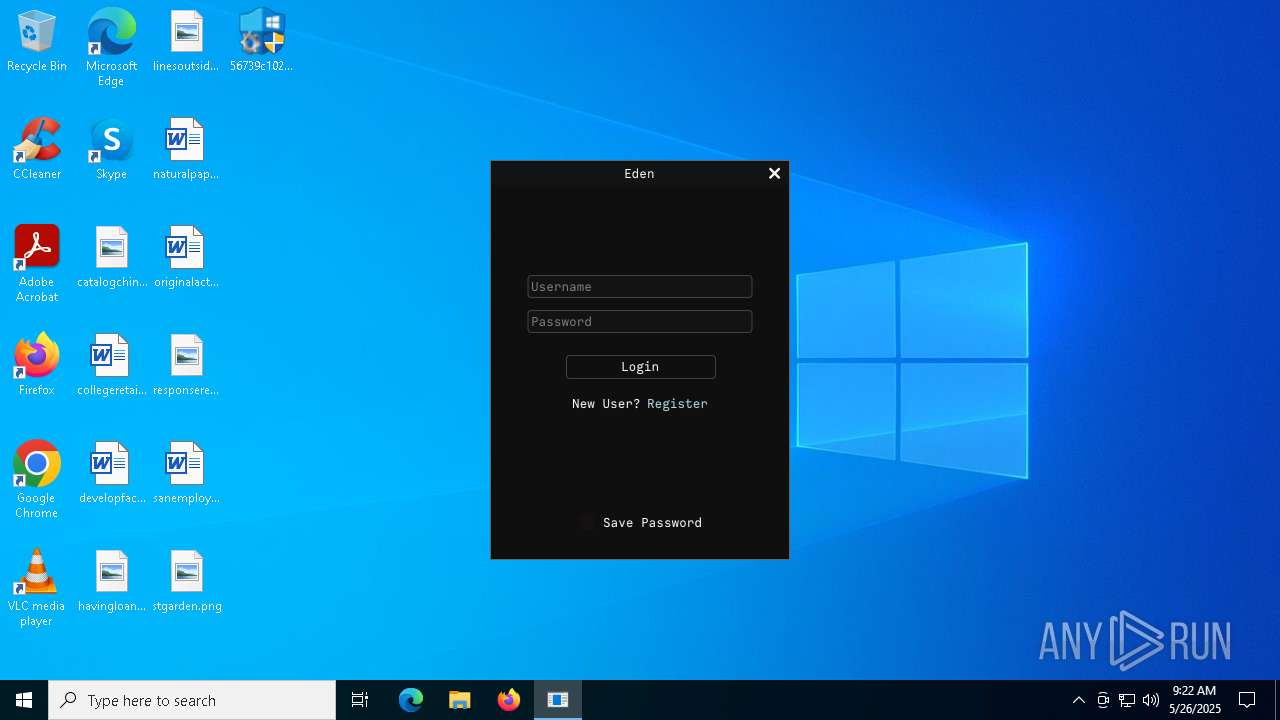
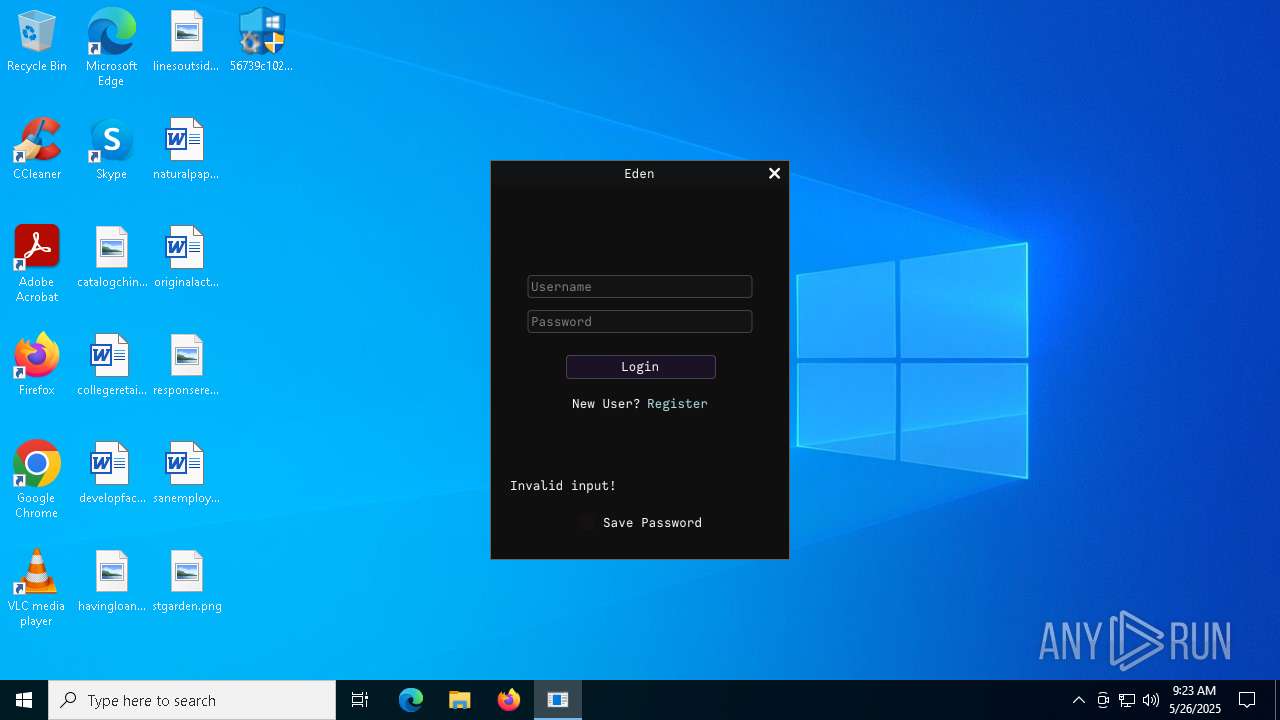
| Threats: | Gh0st RAT is a malware with advanced trojan functionality that enables attackers to establish full control over the victim’s system. The spying capabilities of Gh0st RAT made it a go-to tool for numerous criminal groups in high-profile attacks against government and corporate organizations. The most common vector of attack involving this malware begins with spam and phishing emails. |
| Analysis date: | May 26, 2025, 09:22:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | C3F3CA32D0F41A2895FDF8D30186A4CD |
| SHA1: | 41678CFC4E796F81C854C87B8E24CB3E615FE79D |
| SHA256: | 56739C102BBDB3669873CC452A77A2B7168ED584B2CFBECE4E89887003E87792 |
| SSDEEP: | 98304:UQf3S4KBxR1SVSg5p5aZzrSNe6WZderS9mIOcmVOV5c4s2g84G09z86HbjpcZETS:FXbjZDKWI |
MALICIOUS
GH0ST mutex has been found
- look2.exe (PID: 7744)
- svchcst.exe (PID: 8024)
Creates or modifies Windows services
- look2.exe (PID: 7744)
SUSPICIOUS
Executable content was dropped or overwritten
- look2.exe (PID: 7744)
- 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe (PID: 7720)
Suspicious files were dropped or overwritten
- look2.exe (PID: 7744)
Payload loading activity detected
- HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe (PID: 7812)
Connects to the server without a host name
- HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe (PID: 7812)
There is functionality for taking screenshot (YARA)
- HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe (PID: 7812)
- 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe (PID: 7720)
INFO
Checks supported languages
- 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe (PID: 7720)
- look2.exe (PID: 7744)
- HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe (PID: 7812)
The sample compiled with chinese language support
- 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe (PID: 7720)
- look2.exe (PID: 7744)
Create files in a temporary directory
- 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe (PID: 7720)
Reads the computer name
- look2.exe (PID: 7744)
- HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe (PID: 7812)
Checks proxy server information
- slui.exe (PID: 5024)
Reads the software policy settings
- slui.exe (PID: 5024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:17 03:22:40+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 520192 |
| InitializedDataSize: | 675840 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x60d55 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.9.0.9 |
| ProductVersionNumber: | 2.9.0.9 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 2.9.0.9 |
| FileDescription: | 应用程序 |
| ProductName: | PopWndL0g |
| ProductVersion: | 2.9.0.9 |
| CompanyName: | RuntimeBroker |
| LegalCopyright: | RuntimeBroker |
| Comments: | PopWndL0g |
Total processes
135
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5024 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7640 | "C:\Users\admin\Desktop\56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe" | C:\Users\admin\Desktop\56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | — | explorer.exe | |||||||||||
User: admin Company: RuntimeBroker Integrity Level: MEDIUM Description: 应用程序 Exit code: 3221226540 Version: 2.9.0.9 Modules
| |||||||||||||||
| 7720 | "C:\Users\admin\Desktop\56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe" | C:\Users\admin\Desktop\56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | explorer.exe | ||||||||||||
User: admin Company: RuntimeBroker Integrity Level: HIGH Description: 应用程序 Exit code: 0 Version: 2.9.0.9 Modules
| |||||||||||||||
| 7744 | C:\Users\admin\AppData\Local\Temp\\look2.exe | C:\Users\admin\AppData\Local\Temp\look2.exe | 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: GradualChange Microsoft 基础类应用程序 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 7812 | C:\Users\admin\Desktop\HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | C:\Users\admin\Desktop\HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 8024 | C:\WINDOWS\system32\svchcst.exe "c:\windows\system32\1098625.bat",MainThread | C:\Windows\SysWOW64\svchcst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 221
Read events
4 218
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7744) look2.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\svchcst |
| Operation: | write | Name: | Description |
Value: ¹ÜÀí»ùÓÚ×é¼þ¶ÔÏóÄ£Ð͵ĺËÐÄ·þÎñ,Èç¹û·þÎñ±»½ûÓ㬼ÆËã»ú½«ÎÞ·¨Õý³£ÔËÐС£ | |||
| (PID) Process: | (7744) look2.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\svchcst\Parameters |
| Operation: | write | Name: | ServiceDll |
Value: C:\WINDOWS\system32\1098625.bat | |||
| (PID) Process: | (7744) look2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\Svchost |
| Operation: | write | Name: | svchcst |
Value: svchcst | |||
Executable files
4
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7720 | 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | C:\Users\admin\AppData\Local\Temp\look2.exe | executable | |
MD5:2F3B6F16E33E28AD75F3FDAEF2567807 | SHA256:86492EBF2D6F471A5EE92977318D099B3EA86175B5B7AE522237AE01D07A4857 | |||
| 7744 | look2.exe | C:\Windows\SysWOW64\1098625.bat | executable | |
MD5:881EA84FACB4D8449111F23AD2AB6CCA | SHA256:05BF6484D93B87C375033E88DA4F88705A4EBD5AE14317D24034DC4C42C1EDCE | |||
| 7720 | 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | C:\Users\admin\Desktop\HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | executable | |
MD5:FF7B9E1F7106C2DC03416EFC70ACEFD3 | SHA256:96A11C22736F6F5DA7A1C360618A87B5D18635A1830D6B960908C2F6E9CE16AE | |||
| 7744 | look2.exe | C:\Windows\SysWOW64\ini.ini | text | |
MD5:EF6A0C3383A52C3F5A1736717A30B7FD | SHA256:70DDF47FF507B80ABABF5ADFEC9BD1A707C691D399FA46F30C25BB158C8D9307 | |||
| 7720 | 56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | C:\Users\admin\AppData\Local\Temp\HD_X.dat | executable | |
MD5:7E3280E5BF358966E6E558D2BCAE8961 | SHA256:8ABF3CBAA53B4F175634A96FB35A416EE2B66DBE0C6C2EA2132F8A37AA40CC78 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
32
DNS requests
36
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2656 | RUXIMICS.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7812 | HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | GET | 200 | 138.199.46.68:80 | http://eden1337.b-cdn.net/latest.db | unknown | — | — | whitelisted |
7812 | HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | POST | 200 | 216.146.26.9:80 | http://216.146.26.9/Ping.php | unknown | — | — | unknown |
2656 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7812 | HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | POST | 200 | 216.146.26.114:80 | http://216.146.26.114/Ping.php | unknown | — | — | unknown |
7812 | HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | POST | 200 | 159.223.35.214:80 | http://159.223.35.214/Ping.php | unknown | — | — | unknown |
7812 | HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | POST | 200 | 216.146.26.116:80 | http://216.146.26.116/Ping.php | unknown | — | — | unknown |
7812 | HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | POST | 200 | 216.146.26.68:80 | http://216.146.26.68/Ping.php | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7812 | HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | 138.199.46.68:80 | eden1337.b-cdn.net | Datacamp Limited | SG | whitelisted |
2104 | svchost.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
2656 | RUXIMICS.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2656 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
eden1337.b-cdn.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
kinh.xmcxmr.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7812 | HD_56739c102bbdb3669873cc452a77a2b7168ed584b2cfbece4e89887003e87792.exe | Potentially Bad Traffic | PAYLOAD [ANY.RUN] XORed (14-bytes) Windows executable has been loaded |