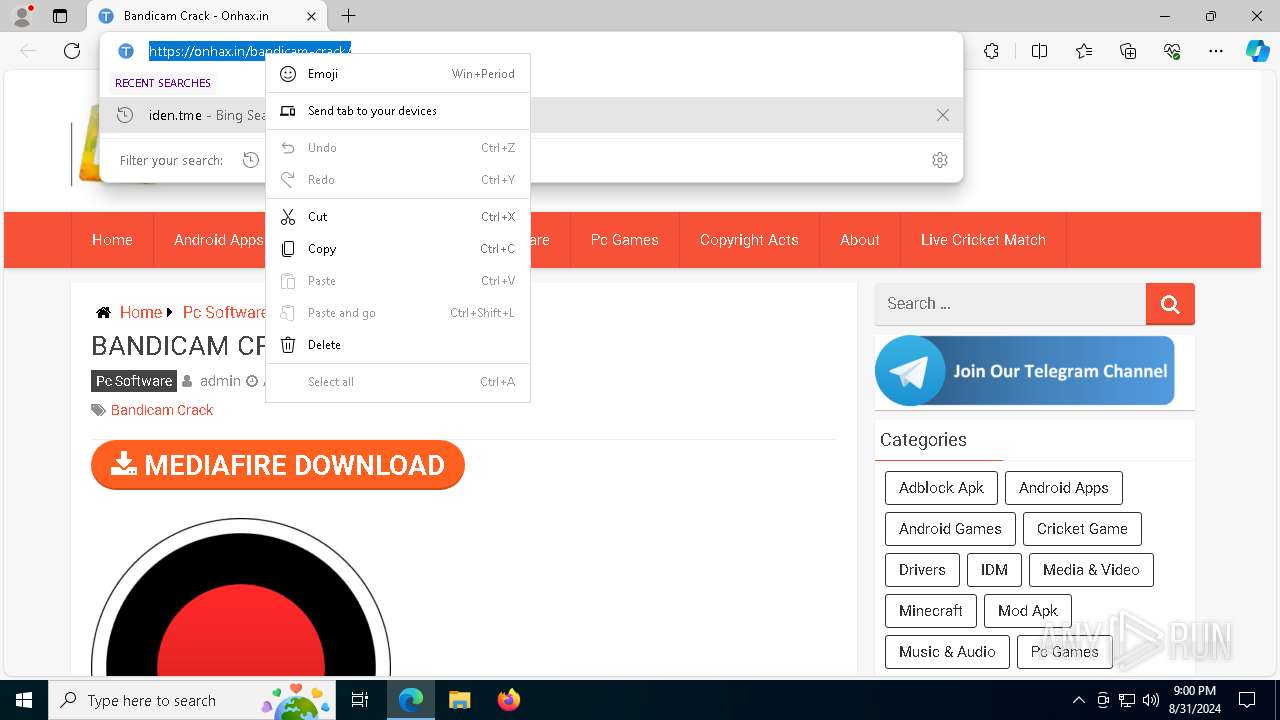
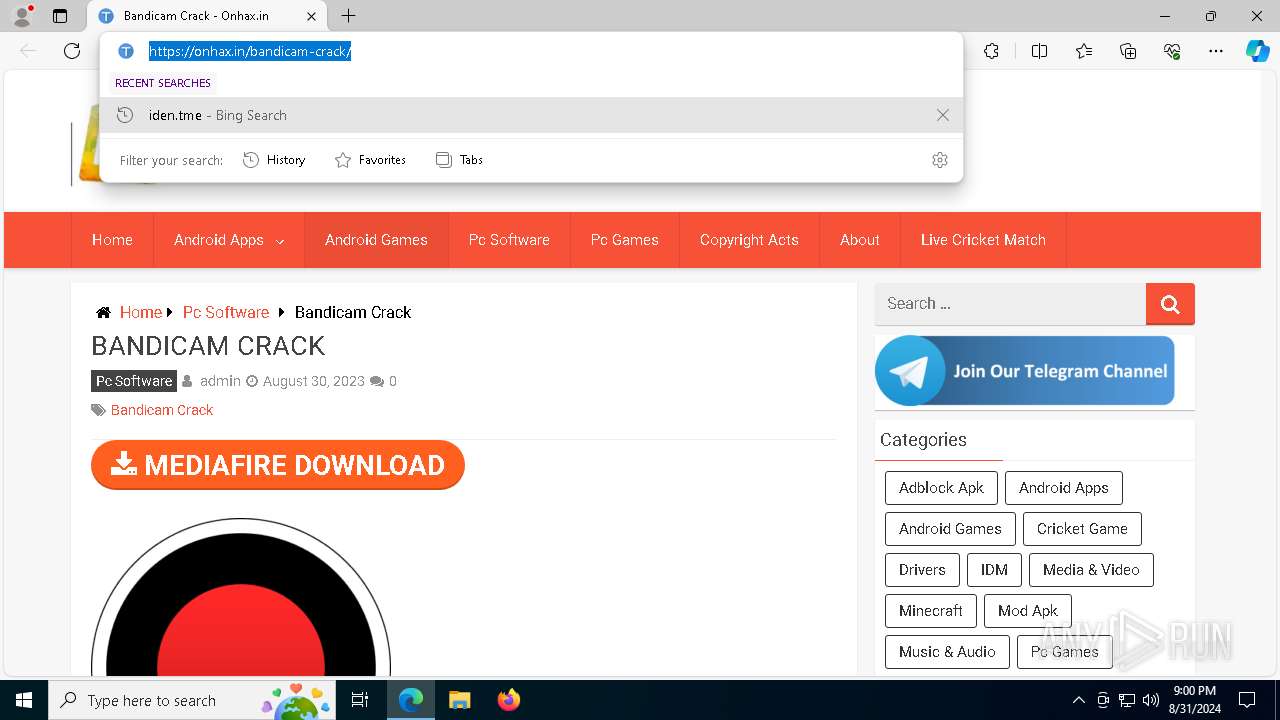
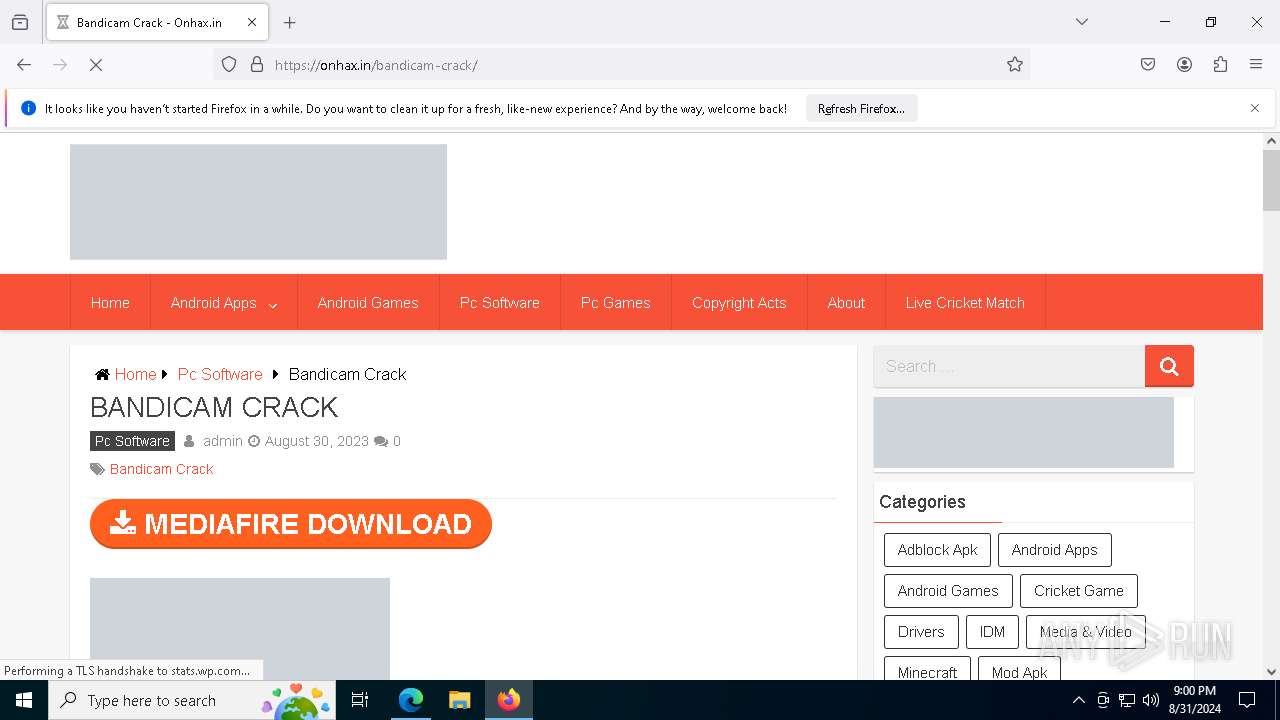
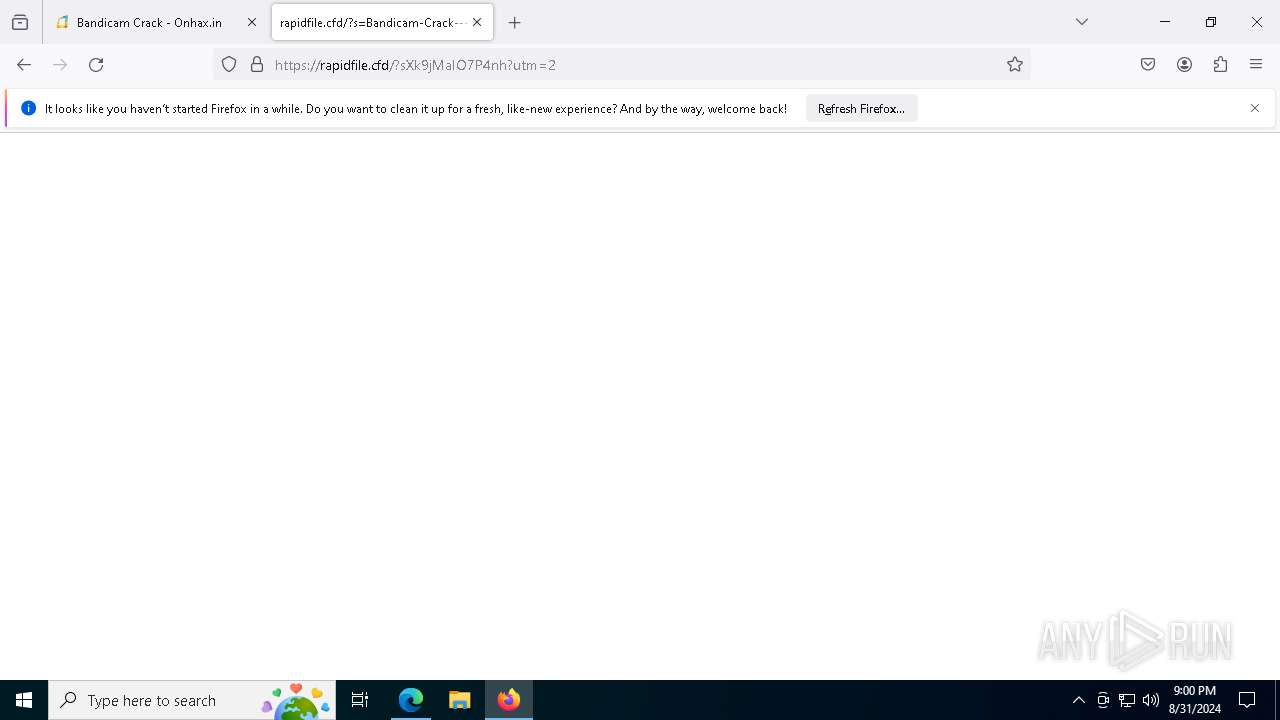
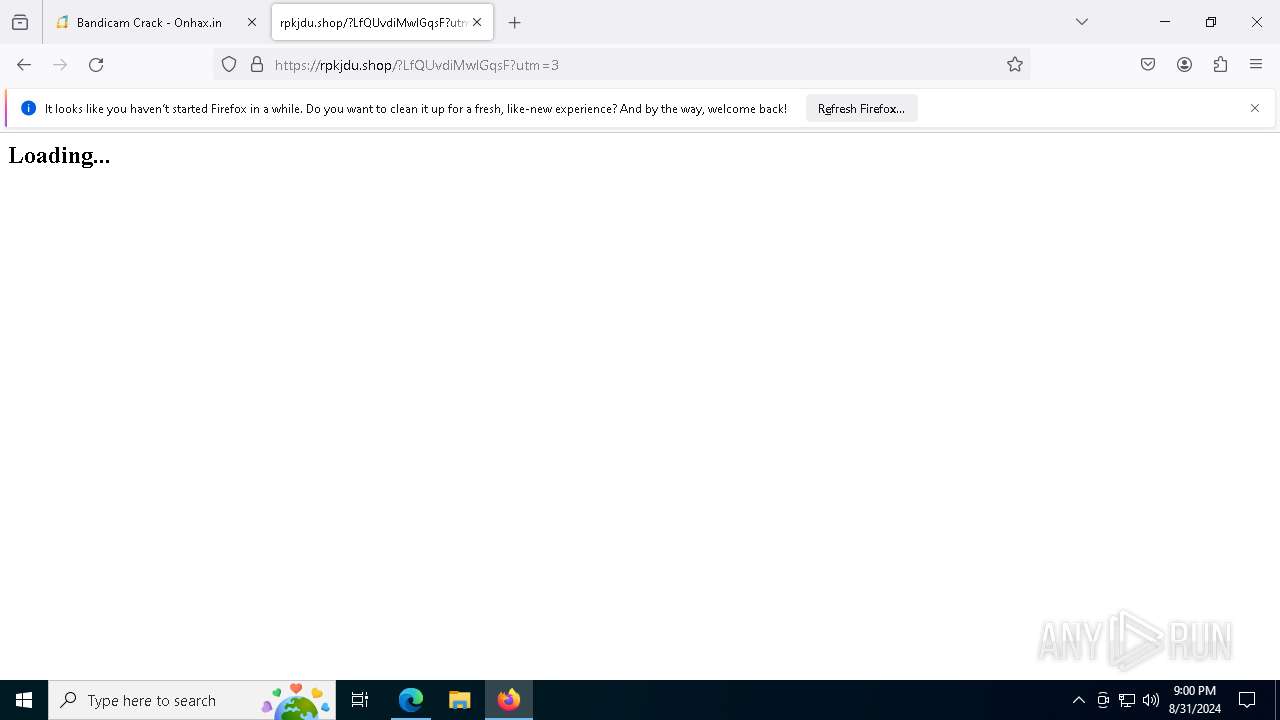
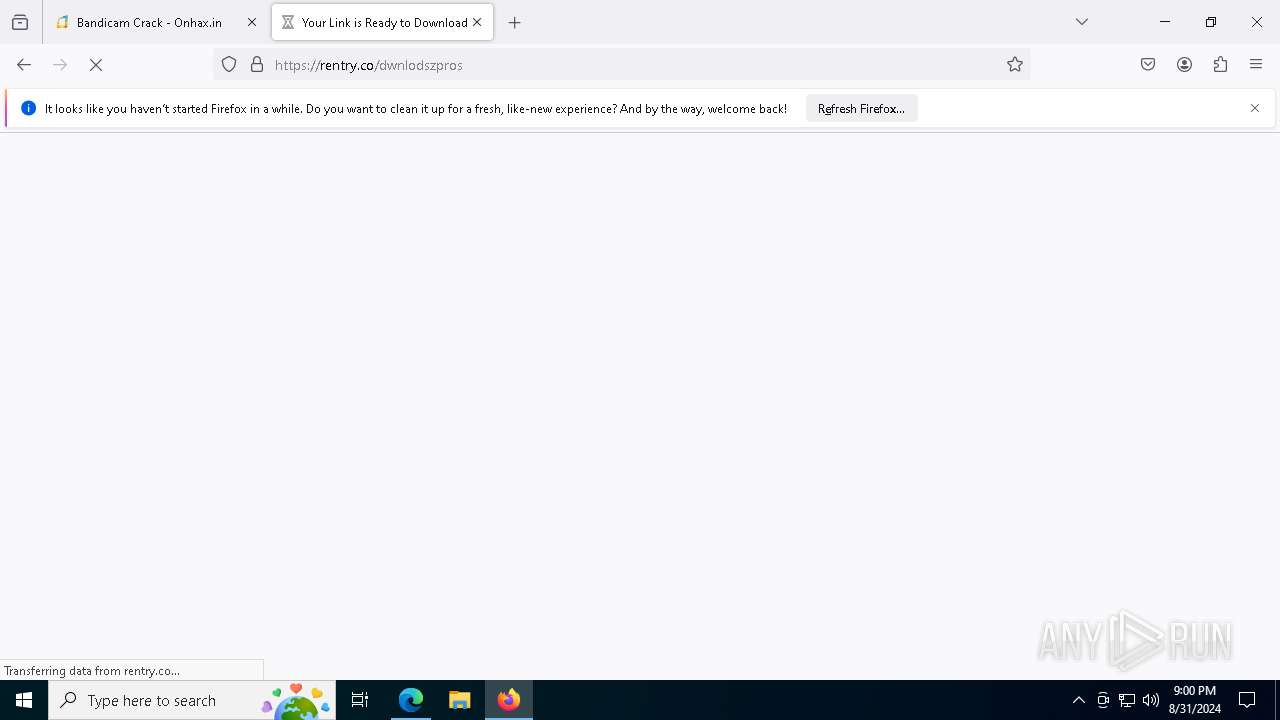
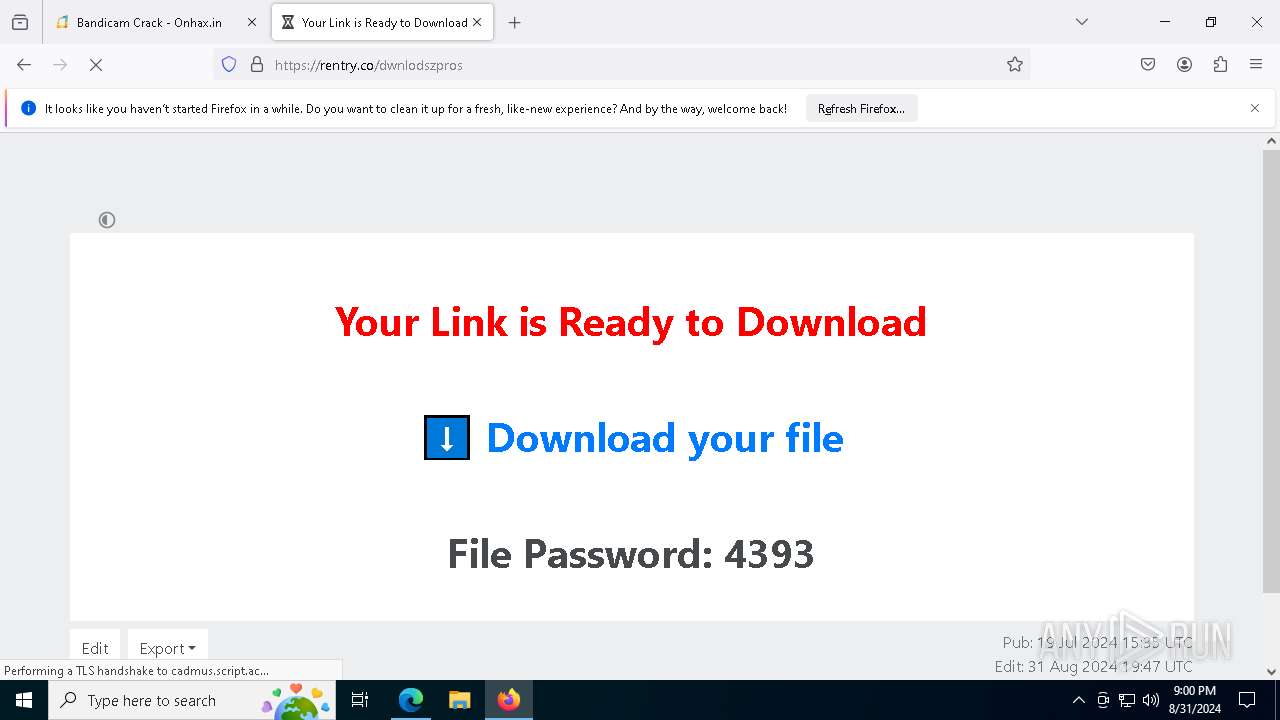
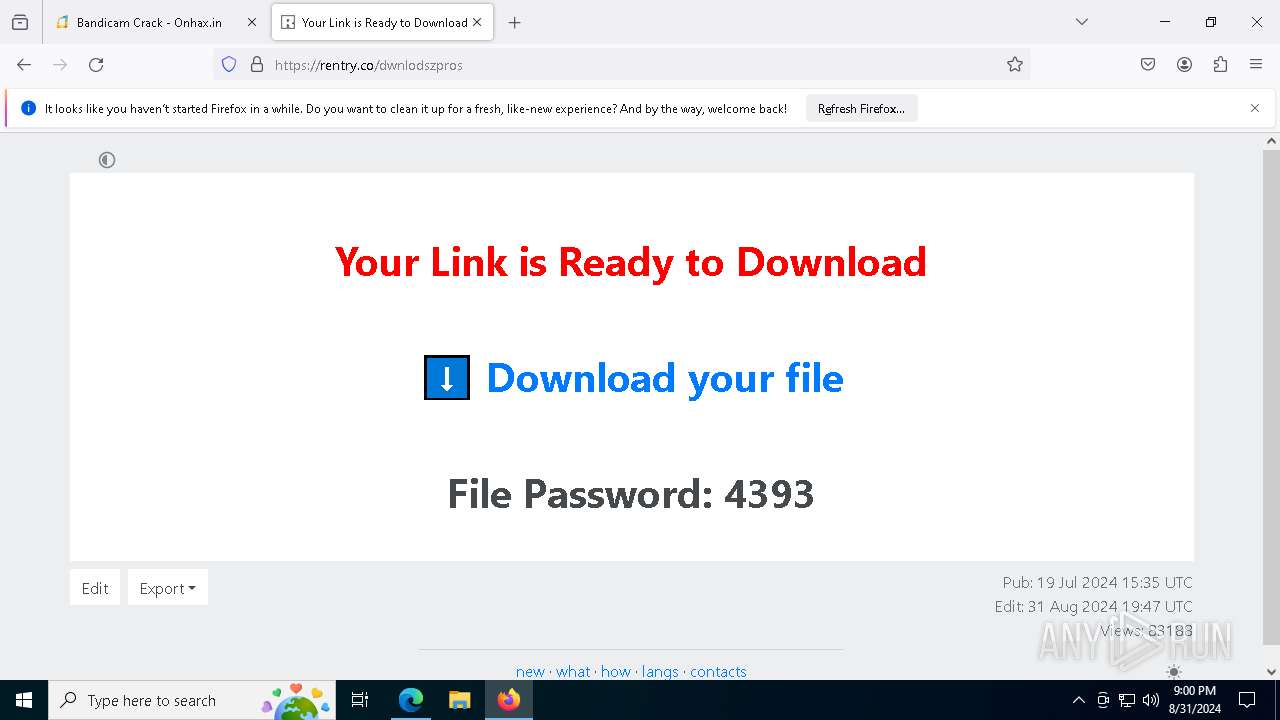
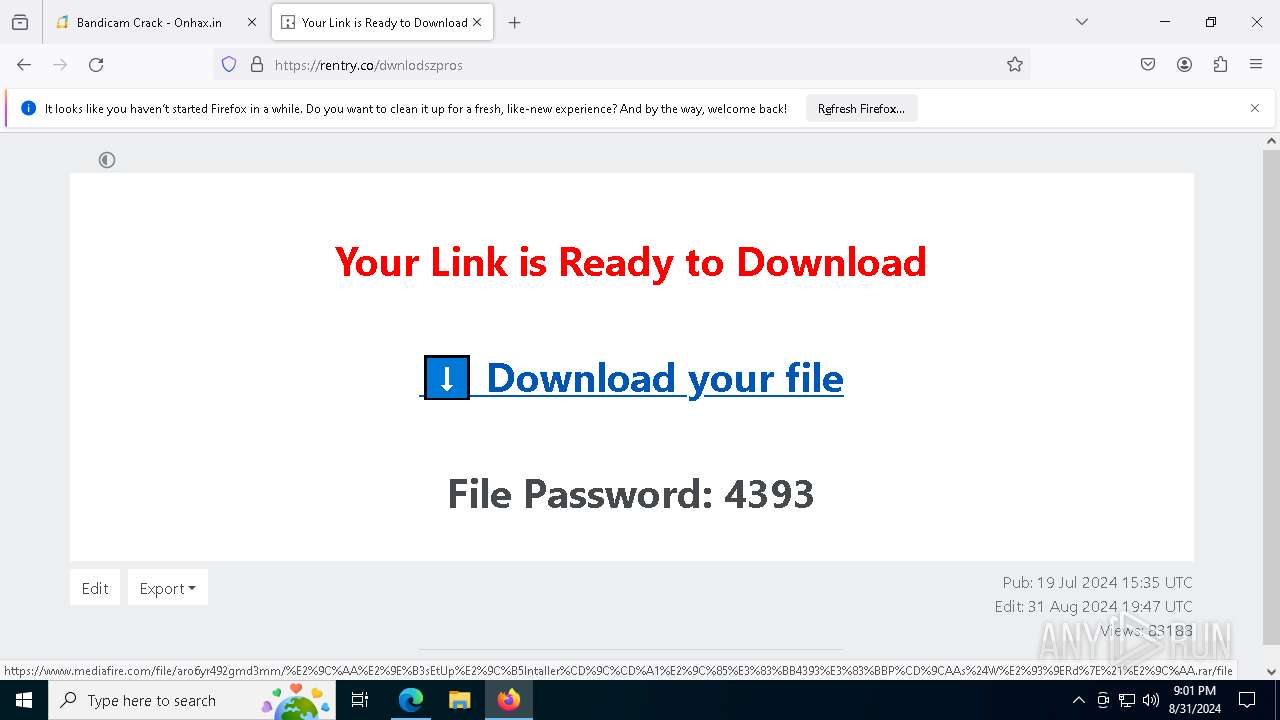
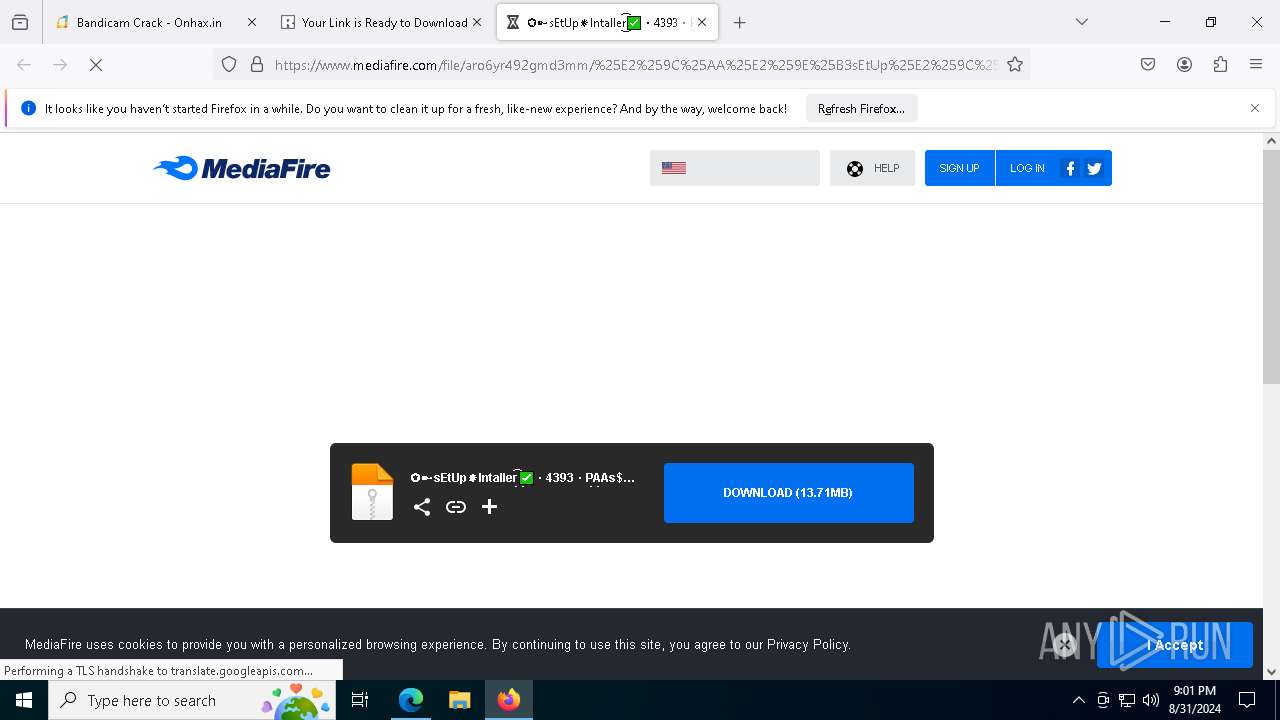
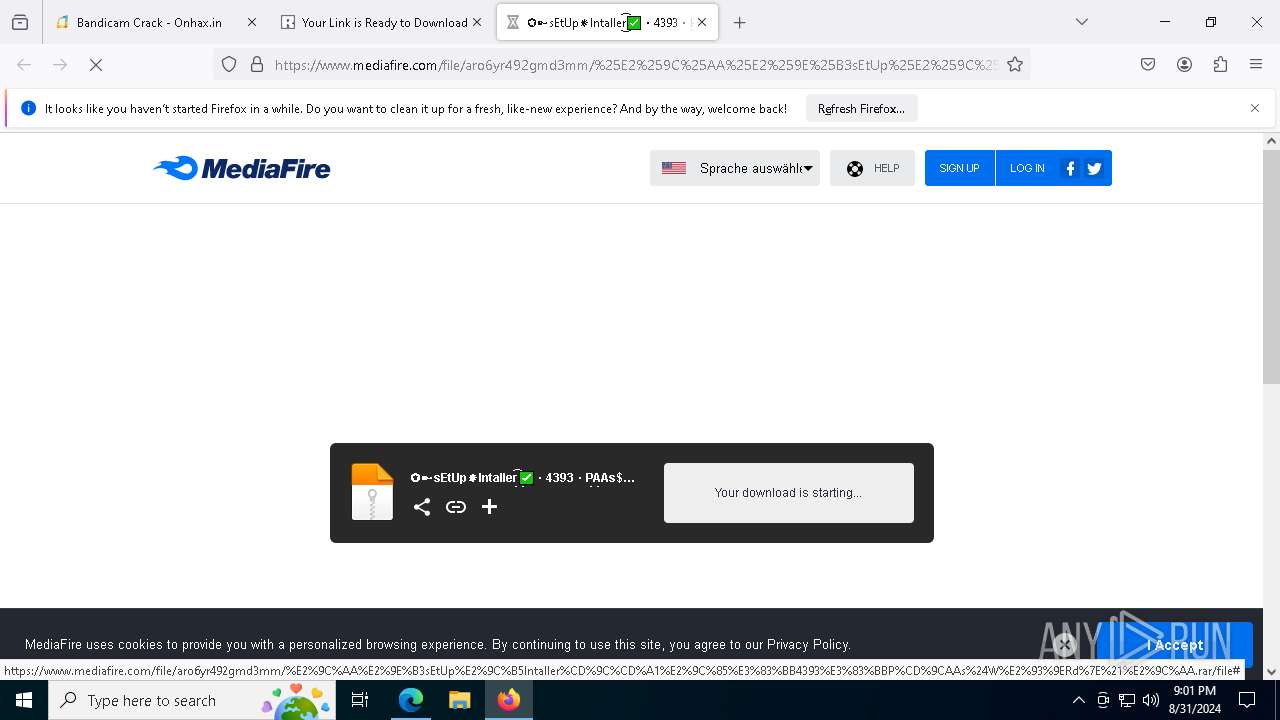
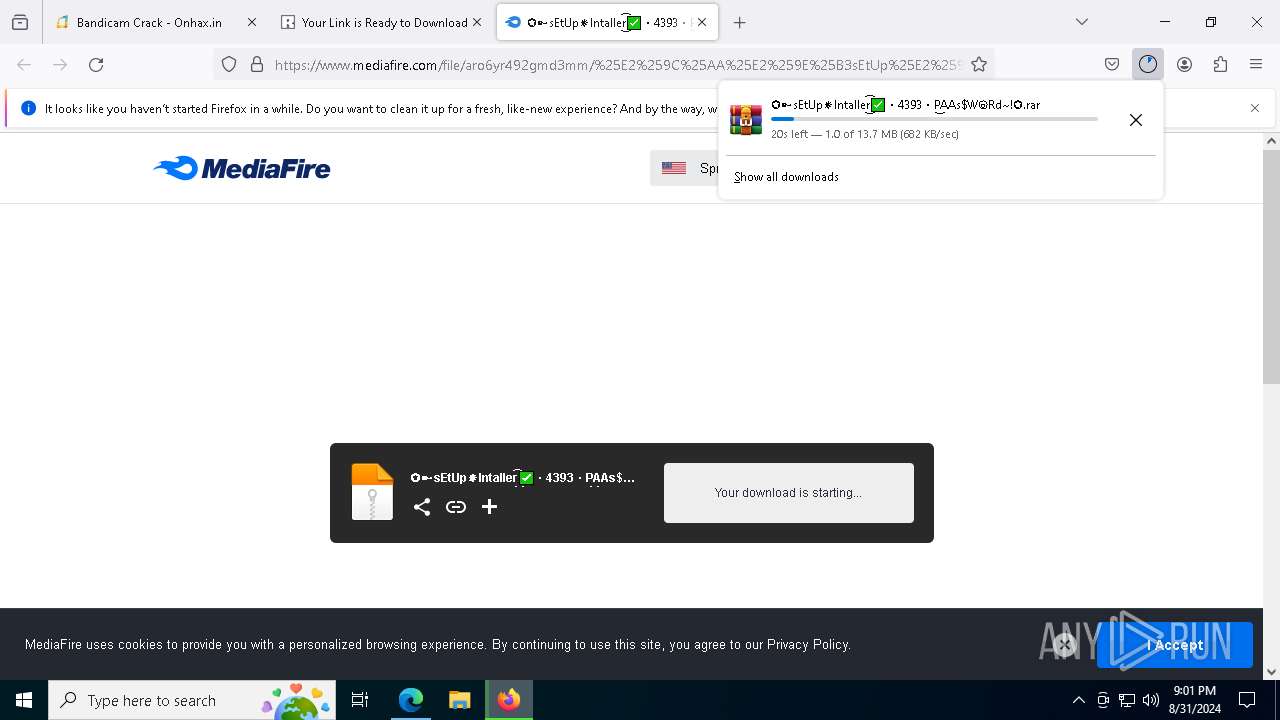
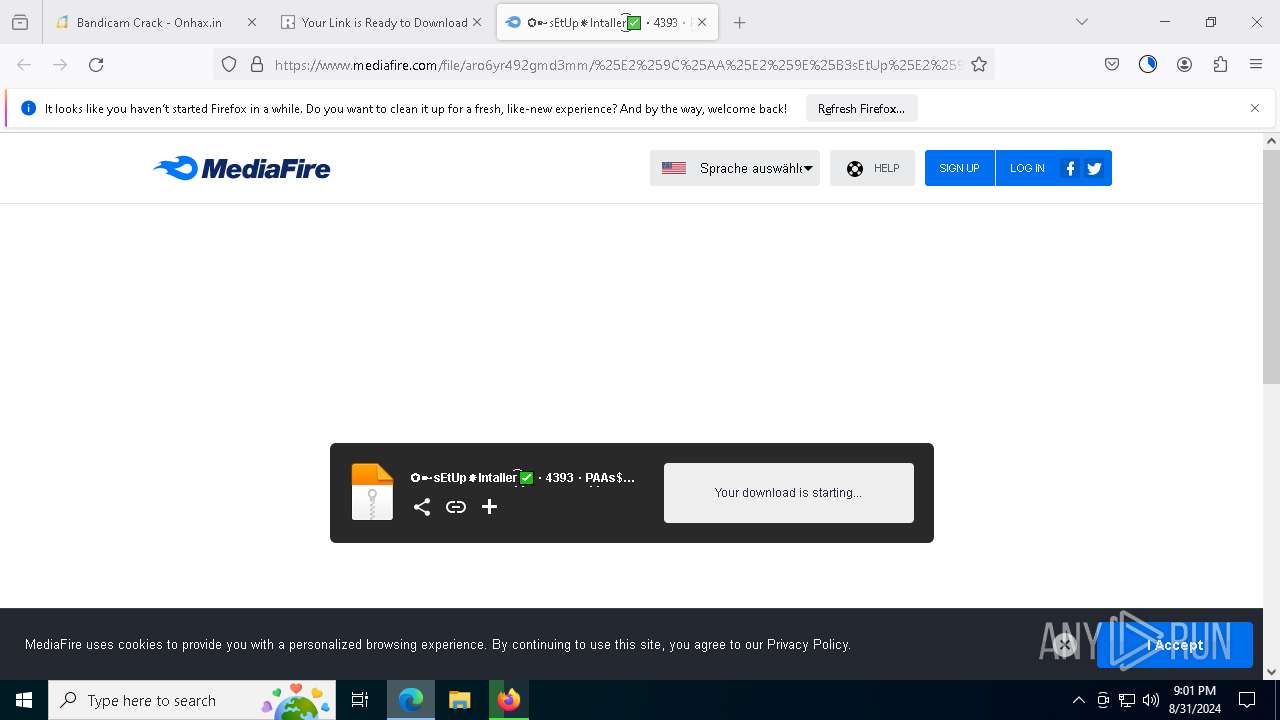
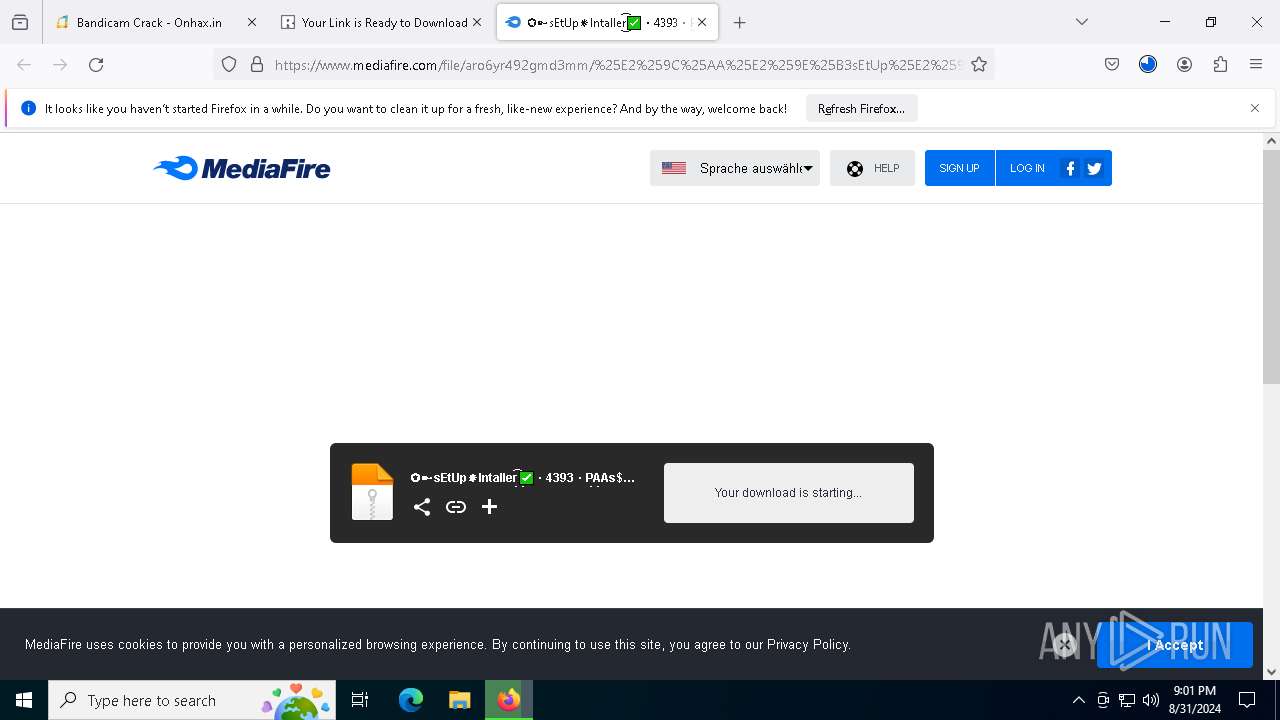
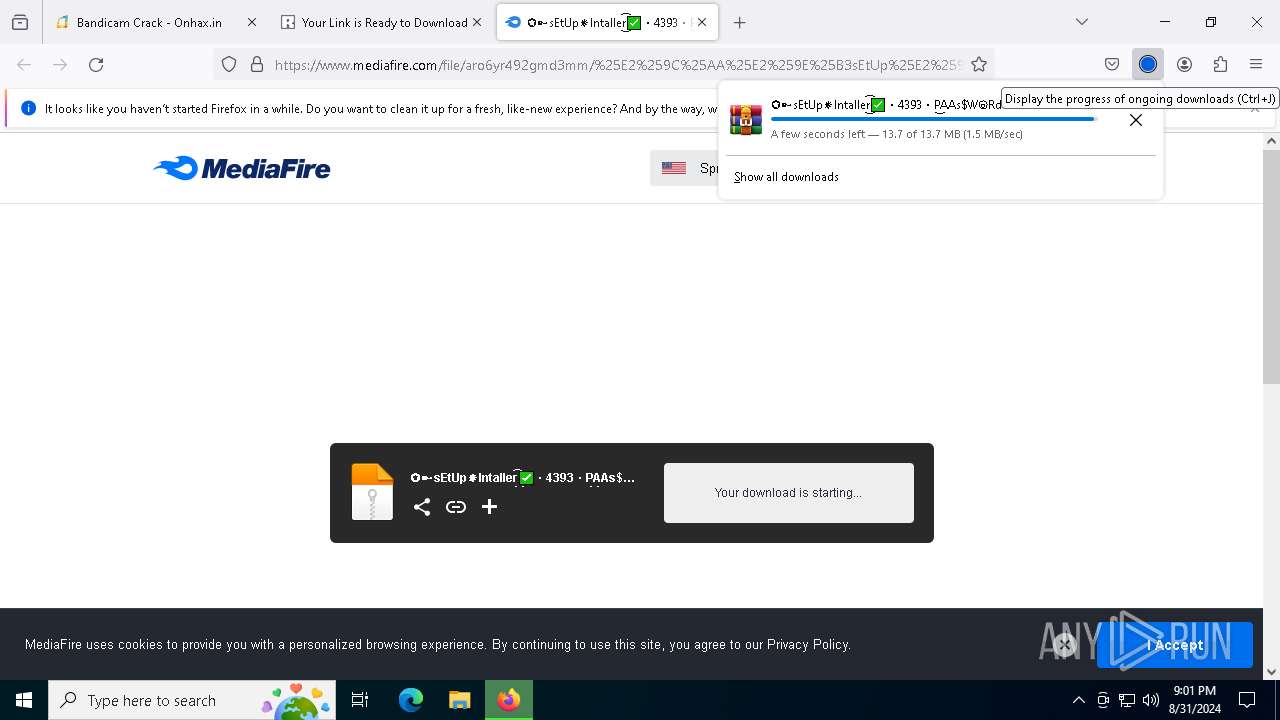
| URL: | https://onhax.in/bandicam-crack/ |
| Full analysis: | https://app.any.run/tasks/b51f414d-d35d-4195-bab2-86540ff4cf86 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 31, 2024, 20:59:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 19D05991F76826787008B61C0FDFA6E1 |
| SHA1: | 0E8988A74F2C33D34225F2B88504954D70097B1F |
| SHA256: | 563B6B748F4CAE7BDABC5EBF95FB9BC85D267343E4CA339A73CCB77F296B8384 |
| SSDEEP: | 3:N8CAKKC6TM9:2CAKB6Tw |
MALICIOUS
Actions looks like stealing of personal data
- DeploredBonded.a3x (PID: 1480)
Stealers network behavior
- DeploredBonded.a3x (PID: 1480)
LUMMA has been detected (SURICATA)
- DeploredBonded.a3x (PID: 1480)
Bypass execution policy to execute commands
- powershell.exe (PID: 8800)
Changes powershell execution policy (Bypass)
- DeploredBonded.a3x (PID: 1480)
Probably downloads file via BitsAdmin (POWERSHELL)
- powershell.exe (PID: 8800)
SUSPICIOUS
Potential Corporate Privacy Violation
- msedge.exe (PID: 1616)
- firefox.exe (PID: 7064)
- svchost.exe (PID: 2256)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 9992)
- WinRAR.exe (PID: 4284)
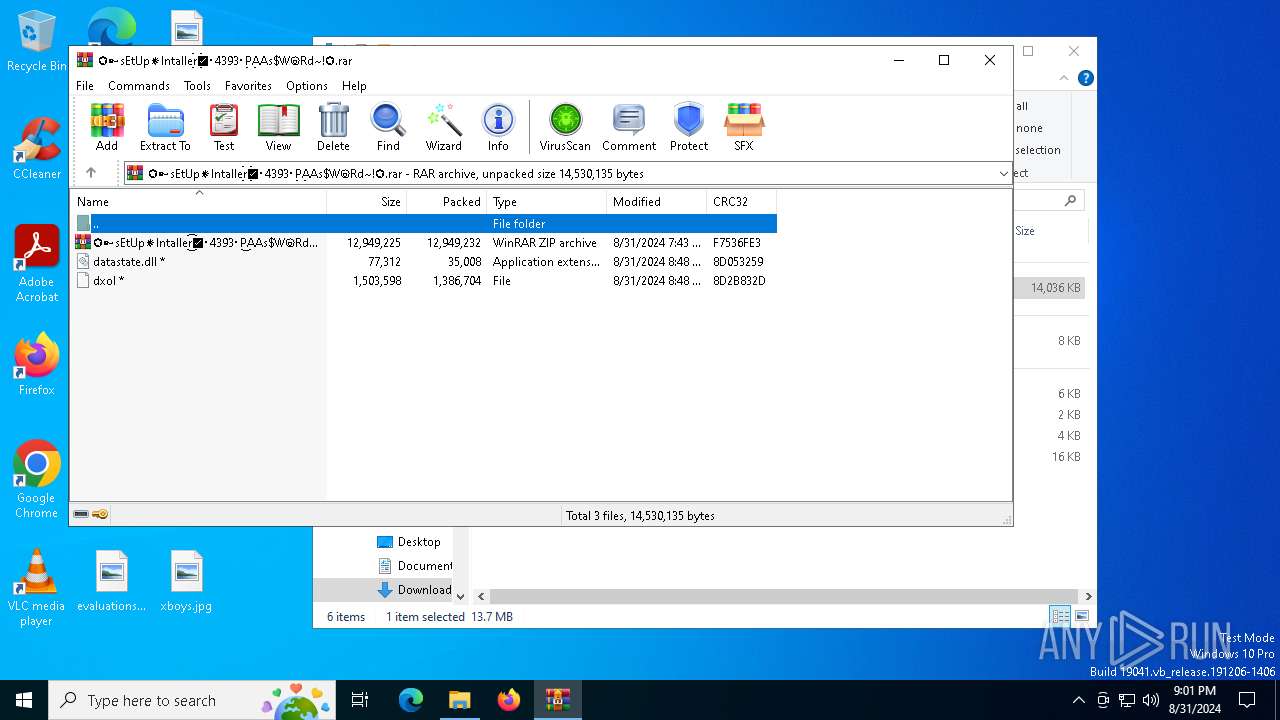
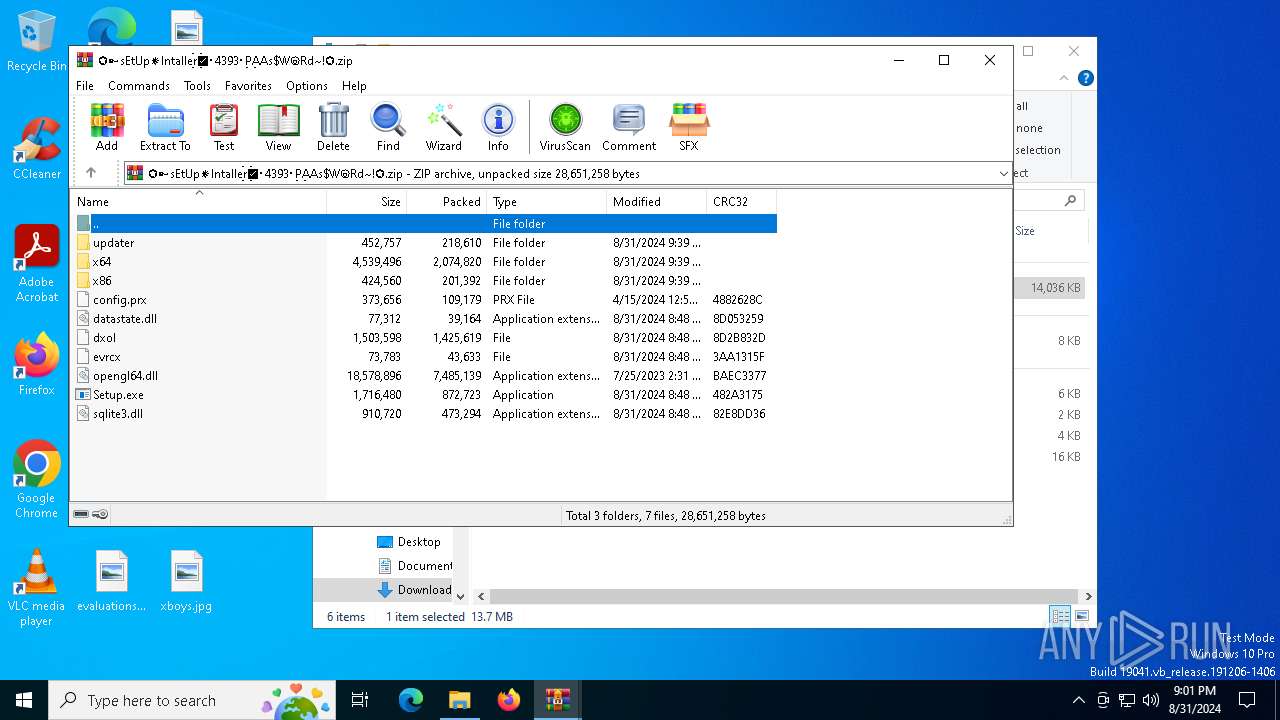
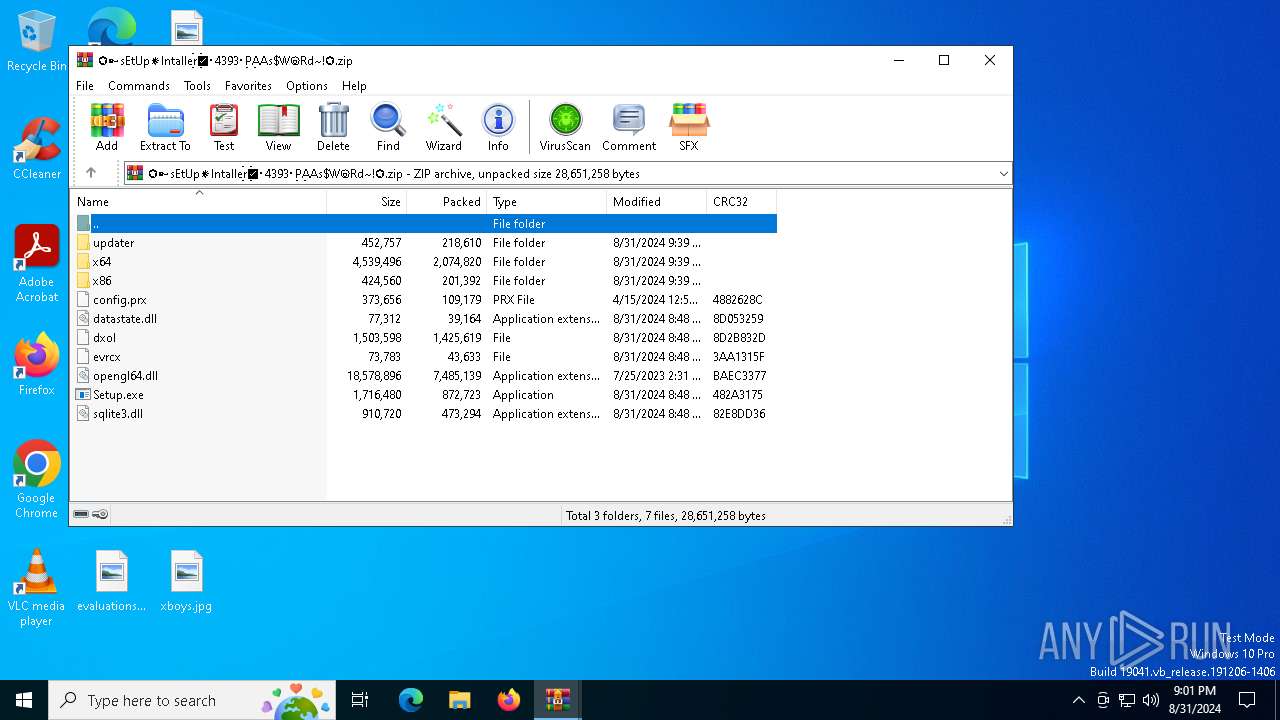
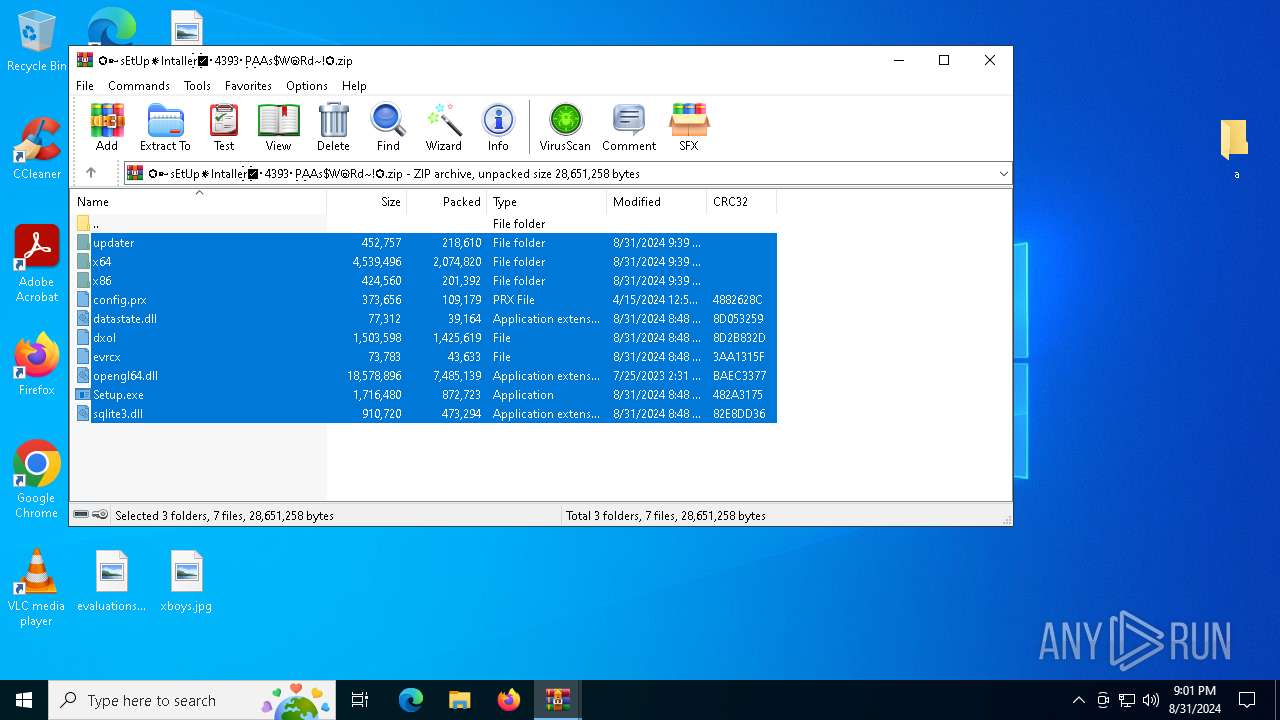
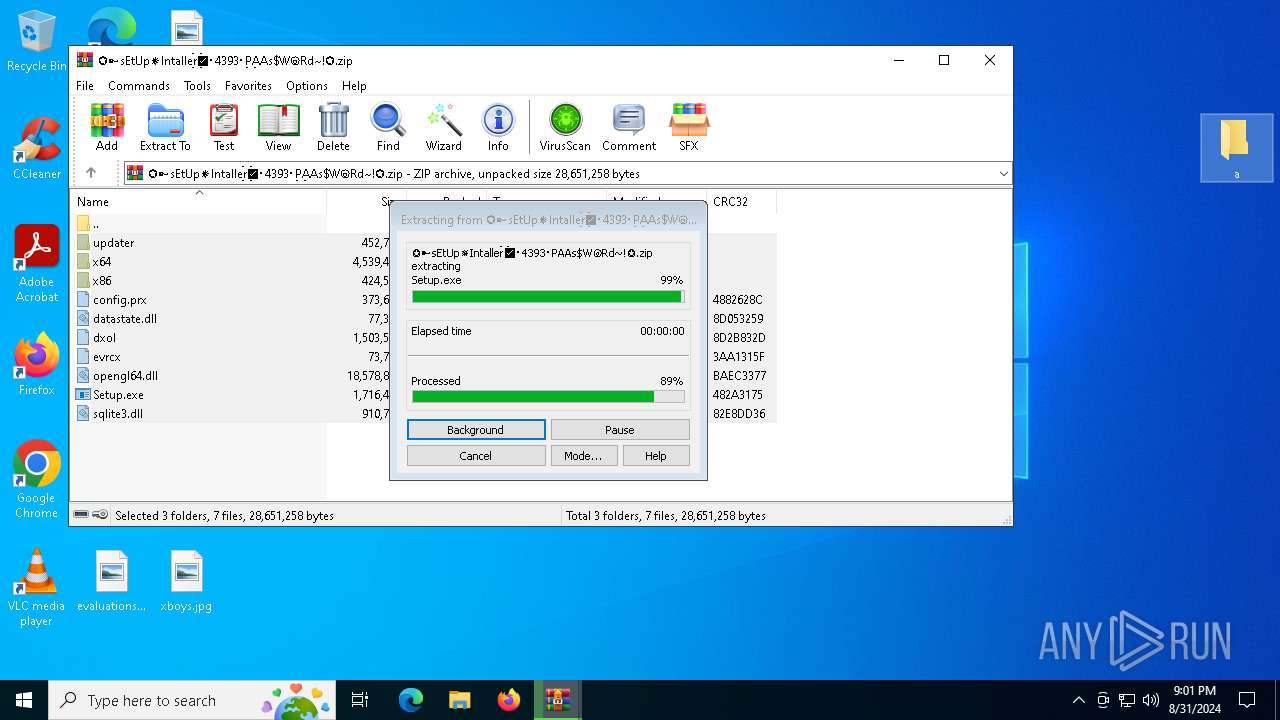
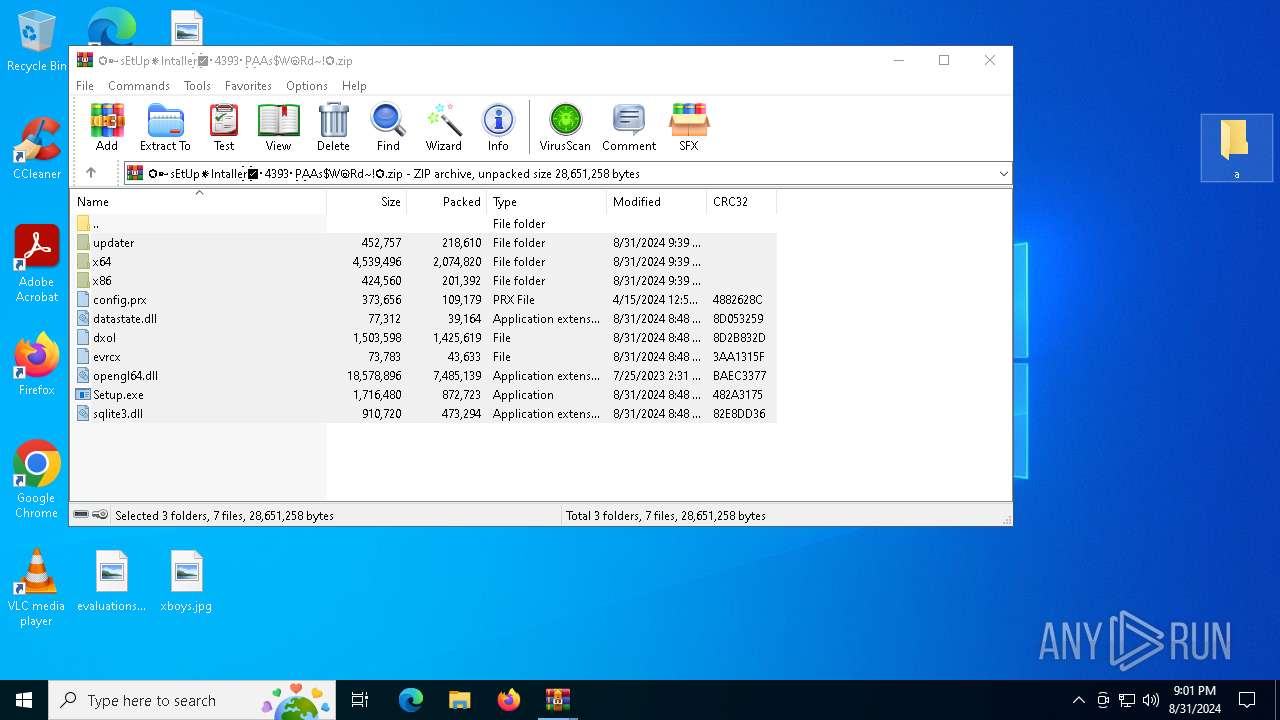
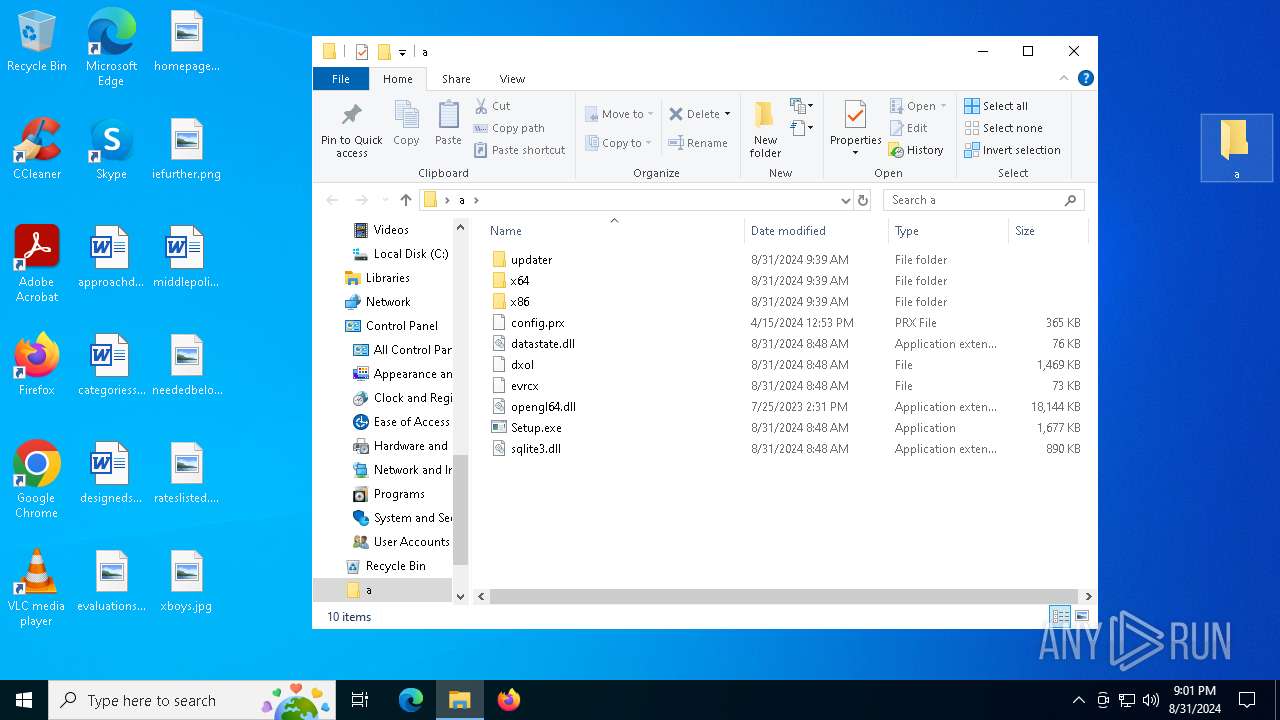
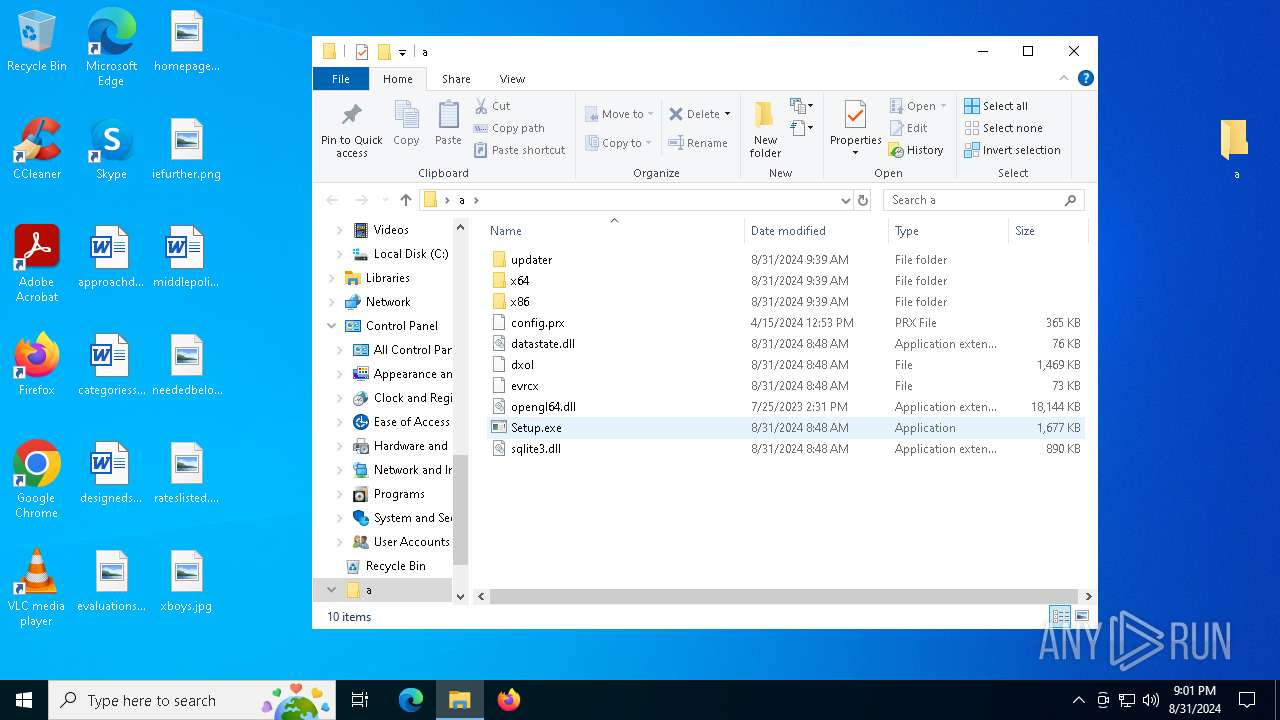
Process drops legitimate windows executable
- WinRAR.exe (PID: 4284)
- WinRAR.exe (PID: 2640)
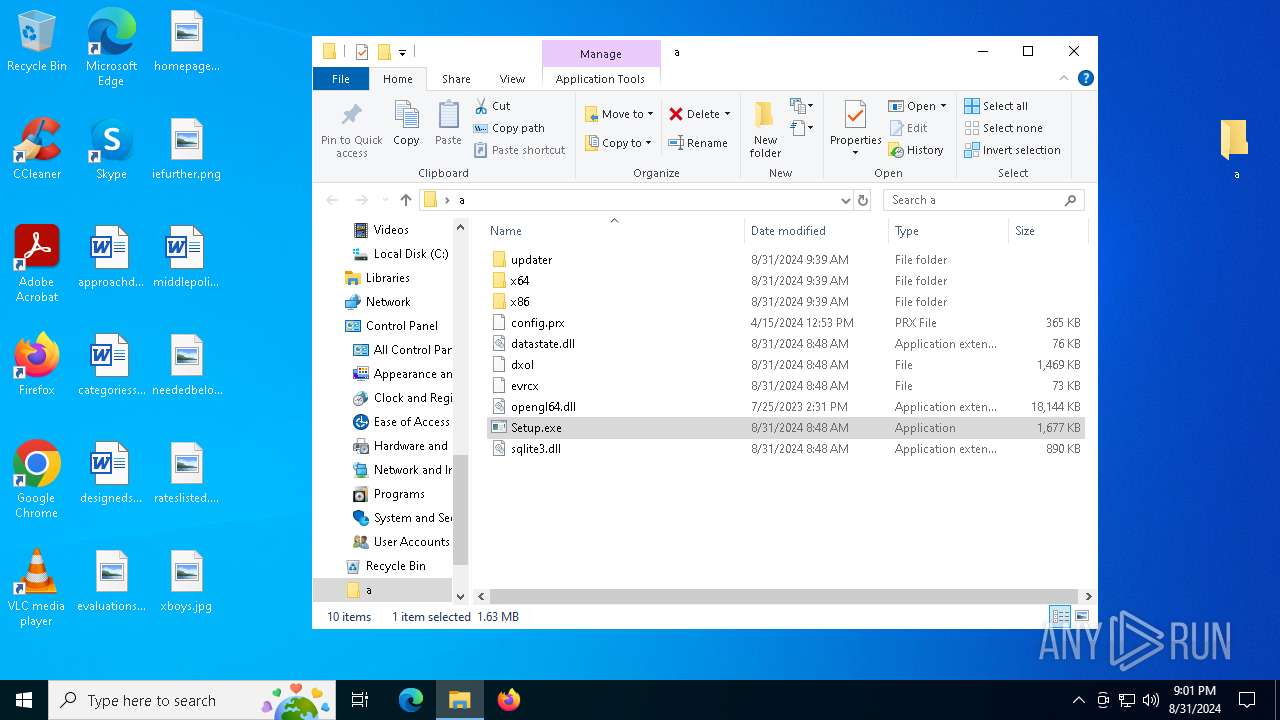
Process drops SQLite DLL files
- WinRAR.exe (PID: 4284)
- WinRAR.exe (PID: 2640)
- Setup.exe (PID: 6812)
Application launched itself
- WinRAR.exe (PID: 4284)
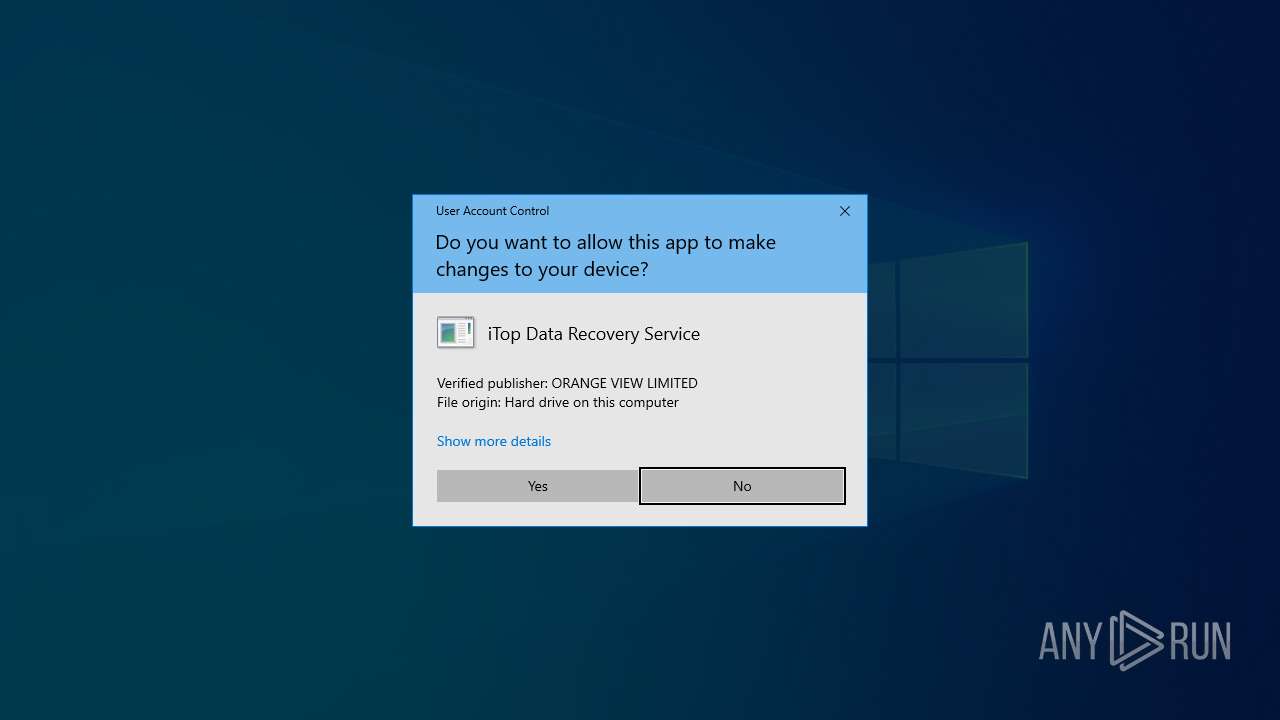
Executable content was dropped or overwritten
- Setup.exe (PID: 6812)
- more.com (PID: 8040)
Drops the executable file immediately after the start
- Setup.exe (PID: 6812)
- more.com (PID: 8040)
Starts application with an unusual extension
- Setup.exe (PID: 6812)
- more.com (PID: 8040)
Searches for installed software
- DeploredBonded.a3x (PID: 1480)
Starts POWERSHELL.EXE for commands execution
- DeploredBonded.a3x (PID: 1480)
The process executes Powershell scripts
- DeploredBonded.a3x (PID: 1480)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 8800)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 8800)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 3964)
- firefox.exe (PID: 7064)
- msedge.exe (PID: 7176)
Reads Environment values
- identity_helper.exe (PID: 2476)
- identity_helper.exe (PID: 6016)
Reads the computer name
- identity_helper.exe (PID: 2476)
- ShellExperienceHost.exe (PID: 9992)
- Setup.exe (PID: 6812)
- StrCmp.exe (PID: 7876)
- more.com (PID: 8040)
- DeploredBonded.a3x (PID: 1480)
- identity_helper.exe (PID: 6016)
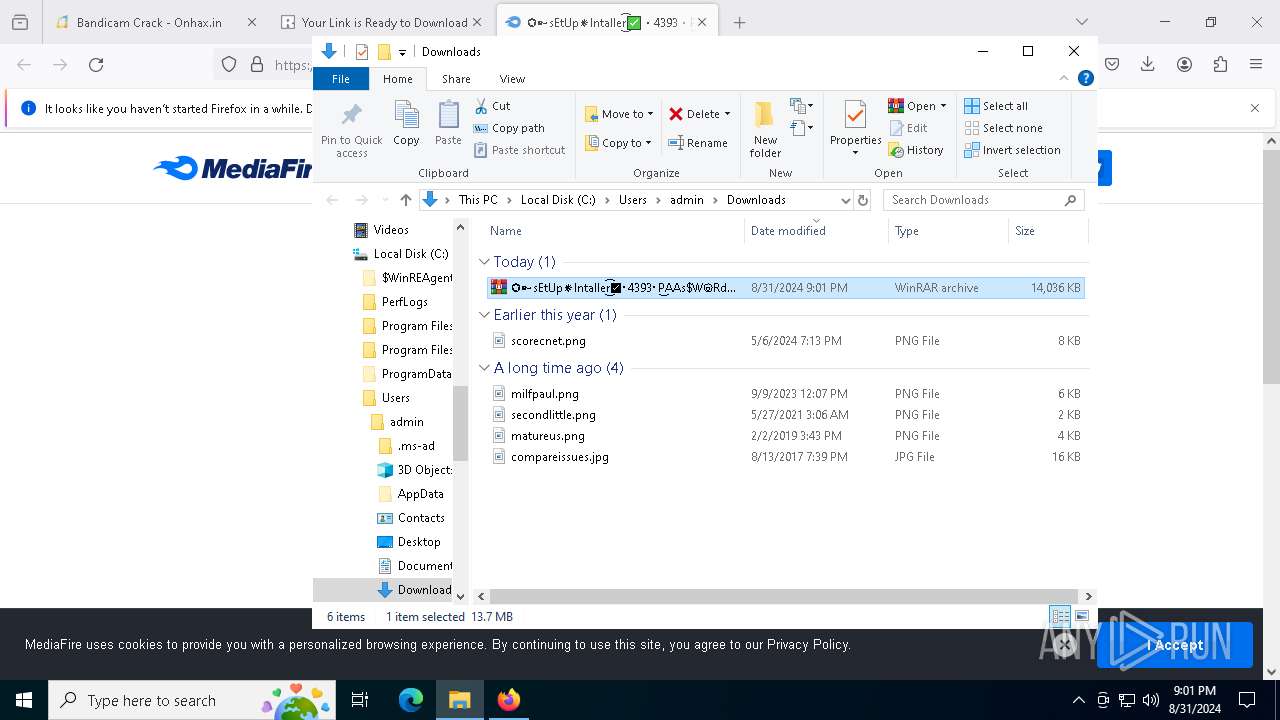
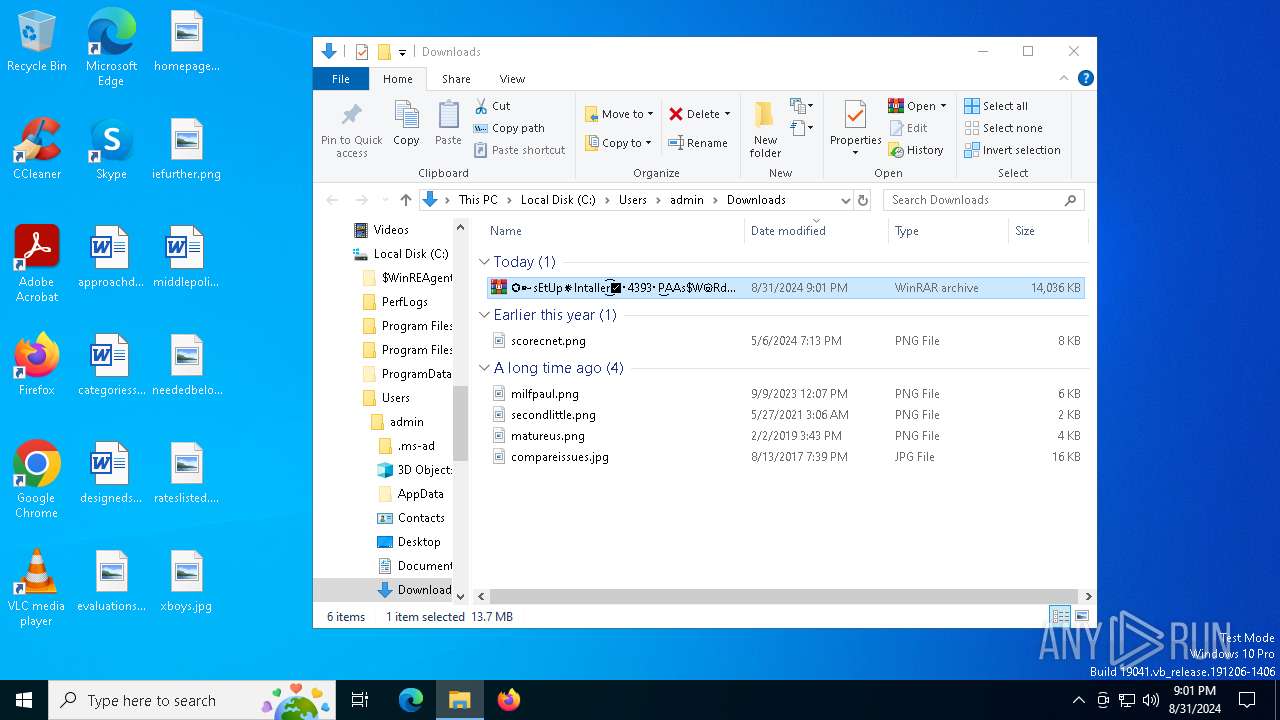
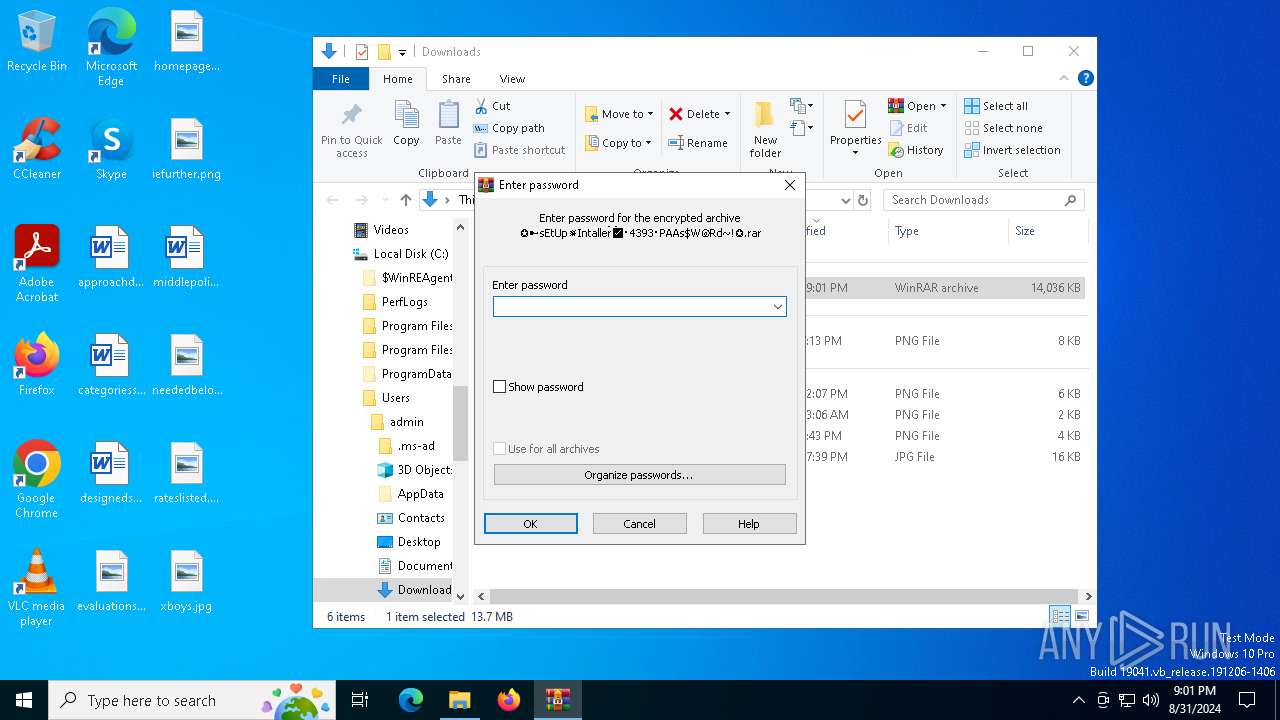
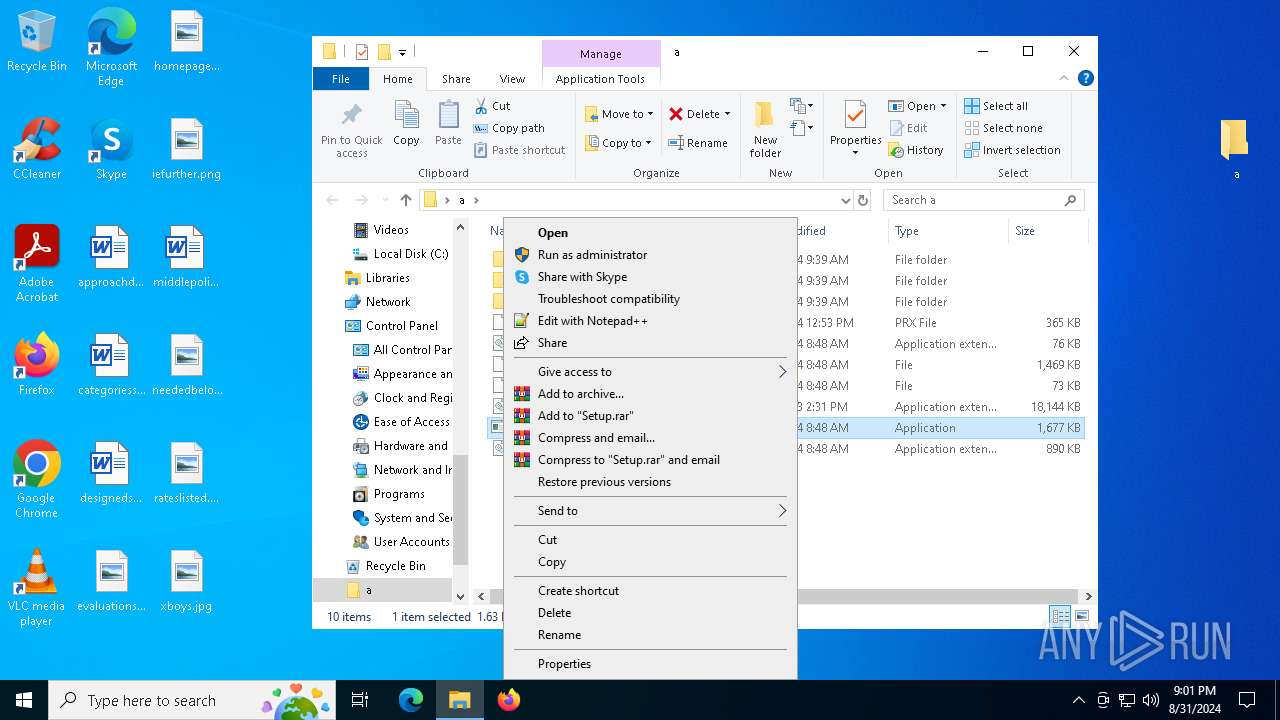
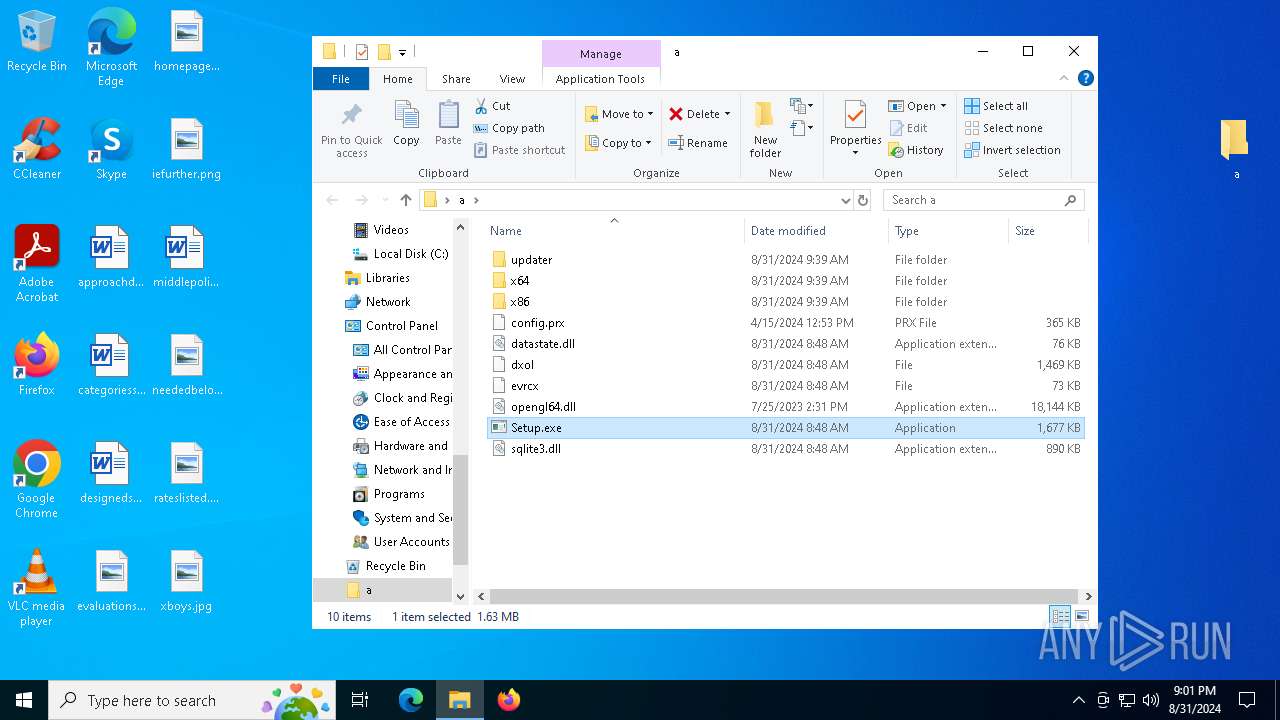
Manual execution by a user
- firefox.exe (PID: 5124)
- WinRAR.exe (PID: 4284)
- Setup.exe (PID: 6812)
Application launched itself
- msedge.exe (PID: 3964)
- firefox.exe (PID: 5124)
- firefox.exe (PID: 7064)
- msedge.exe (PID: 7176)
Checks supported languages
- identity_helper.exe (PID: 2476)
- ShellExperienceHost.exe (PID: 9992)
- identity_helper.exe (PID: 6016)
- Setup.exe (PID: 6812)
- StrCmp.exe (PID: 7876)
- more.com (PID: 8040)
- DeploredBonded.a3x (PID: 1480)
Reads the software policy settings
- slui.exe (PID: 6012)
- slui.exe (PID: 7720)
- DeploredBonded.a3x (PID: 1480)
The process uses the downloaded file
- firefox.exe (PID: 7064)
- WinRAR.exe (PID: 4284)
- WinRAR.exe (PID: 2640)
- powershell.exe (PID: 8800)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2640)
Checks proxy server information
- slui.exe (PID: 7720)
Creates files or folders in the user directory
- Setup.exe (PID: 6812)
Create files in a temporary directory
- more.com (PID: 8040)
- Setup.exe (PID: 6812)
- DeploredBonded.a3x (PID: 1480)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8800)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
292
Monitored processes
161
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3668 --field-trial-handle=2292,i,1500504553509320810,14060329751570330821,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7180 -parentBuildID 20240213221259 -sandboxingKind 1 -prefsHandle 7172 -prefMapHandle 6972 -prefsLen 34713 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {67860319-c4c9-48d9-b03a-55ddf5bad09d} 7064 "\\.\pipe\gecko-crash-server-pipe.7064" 2de3772e310 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x25c,0x250,0x254,0x218,0x310,0x7fffd2885fd8,0x7fffd2885fe4,0x7fffd2885ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 608 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2672 --field-trial-handle=2292,i,1500504553509320810,14060329751570330821,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 752 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4908 --field-trial-handle=2292,i,1500504553509320810,14060329751570330821,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5584 --field-trial-handle=2308,i,134955650957113860,9116571731121723410,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1360 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4896 --field-trial-handle=2292,i,1500504553509320810,14060329751570330821,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1404 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=51 --mojo-platform-channel-handle=5768 --field-trial-handle=2308,i,134955650957113860,9116571731121723410,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4548 --field-trial-handle=2308,i,134955650957113860,9116571731121723410,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1480 | C:\Users\admin\AppData\Local\Temp\DeploredBonded.a3x | C:\Users\admin\AppData\Local\Temp\DeploredBonded.a3x | more.com | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: HIGH Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 1 Modules
| |||||||||||||||
Total events
87 154
Read events
86 767
Write events
381
Delete events
6
Modification events
| (PID) Process: | (3964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (3964) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3964) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
36
Suspicious files
588
Text files
200
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129f55.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129f55.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129f65.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129f55.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF129f94.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
161
TCP/UDP connections
496
DNS requests
718
Threats
63
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1128 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1752 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1452 | svchost.exe | HEAD | 200 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725594966&P2=404&P3=2&P4=efepzQlGQeno16B%2fuiekD9wRR21nHhswHu7pRdn03tHrSgoDkyWwwkRk4S3hNd9WkjmLnlIbrDO7N221%2fQcGNg%3d%3d | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1452 | svchost.exe | GET | 206 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725594966&P2=404&P3=2&P4=efepzQlGQeno16B%2fuiekD9wRR21nHhswHu7pRdn03tHrSgoDkyWwwkRk4S3hNd9WkjmLnlIbrDO7N221%2fQcGNg%3d%3d | unknown | — | — | whitelisted |
1452 | svchost.exe | GET | 206 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725594966&P2=404&P3=2&P4=efepzQlGQeno16B%2fuiekD9wRR21nHhswHu7pRdn03tHrSgoDkyWwwkRk4S3hNd9WkjmLnlIbrDO7N221%2fQcGNg%3d%3d | unknown | — | — | whitelisted |
1452 | svchost.exe | GET | 206 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725594966&P2=404&P3=2&P4=efepzQlGQeno16B%2fuiekD9wRR21nHhswHu7pRdn03tHrSgoDkyWwwkRk4S3hNd9WkjmLnlIbrDO7N221%2fQcGNg%3d%3d | unknown | — | — | whitelisted |
1452 | svchost.exe | GET | 206 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725594966&P2=404&P3=2&P4=efepzQlGQeno16B%2fuiekD9wRR21nHhswHu7pRdn03tHrSgoDkyWwwkRk4S3hNd9WkjmLnlIbrDO7N221%2fQcGNg%3d%3d | unknown | — | — | whitelisted |
1452 | svchost.exe | GET | 206 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725594966&P2=404&P3=2&P4=efepzQlGQeno16B%2fuiekD9wRR21nHhswHu7pRdn03tHrSgoDkyWwwkRk4S3hNd9WkjmLnlIbrDO7N221%2fQcGNg%3d%3d | unknown | — | — | whitelisted |
1452 | svchost.exe | GET | 206 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725594966&P2=404&P3=2&P4=efepzQlGQeno16B%2fuiekD9wRR21nHhswHu7pRdn03tHrSgoDkyWwwkRk4S3hNd9WkjmLnlIbrDO7N221%2fQcGNg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4132 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1616 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1616 | msedge.exe | 188.114.96.3:443 | onhax.in | — | — | unknown |
1616 | msedge.exe | 172.67.216.196:443 | jazzyzest.cfd | — | — | unknown |
3964 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1616 | msedge.exe | 13.107.246.67:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1616 | msedge.exe | 142.250.185.74:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
onhax.in |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
stats.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
1616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
1616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
1616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
1616 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Browser Automation Toolkit in DNS Lookup (bablosoft .com) |
1616 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Browser Automation Toolkit in DNS Lookup (bablosoft .com) |
1616 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Fingerprinting Service in DNS Lookup (customfingerprints .bablosoft .com) |
1616 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Fingerprinting Service in DNS Lookup (customfingerprints .bablosoft .com) |
1616 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Browser Automation Toolkit in TLS SNI (bablosoft .com) |
1616 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Fingerprinting Service in TLS SNI (customfingerprints .bablosoft .com) |
Process | Message |
|---|---|
msedge.exe | [0831/205940.856:WARNING:device_ticket.cc(151)] Timed out waiting for device ticket. Canceling async operation.
|
msedge.exe | [0831/205941.458:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ff6278d0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0831/205941.460:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe
|
msedge.exe | [0831/205941.460:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff85f0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0831/205941.460:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\SYSTEM32\ntdll.dll
|
msedge.exe | [0831/205941.460:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff6f10000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0831/205941.460:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\System32\KERNEL32.DLL
|
msedge.exe | [0831/205941.460:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff5da0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0831/205941.460:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\System32\KERNELBASE.dll
|
msedge.exe | [0831/205941.460:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7fffd24a0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|