| File name: | mampato.exe |
| Full analysis: | https://app.any.run/tasks/599e3efc-093c-49a9-aaf2-87e9fd080f95 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | December 27, 2024, 18:14:34 |
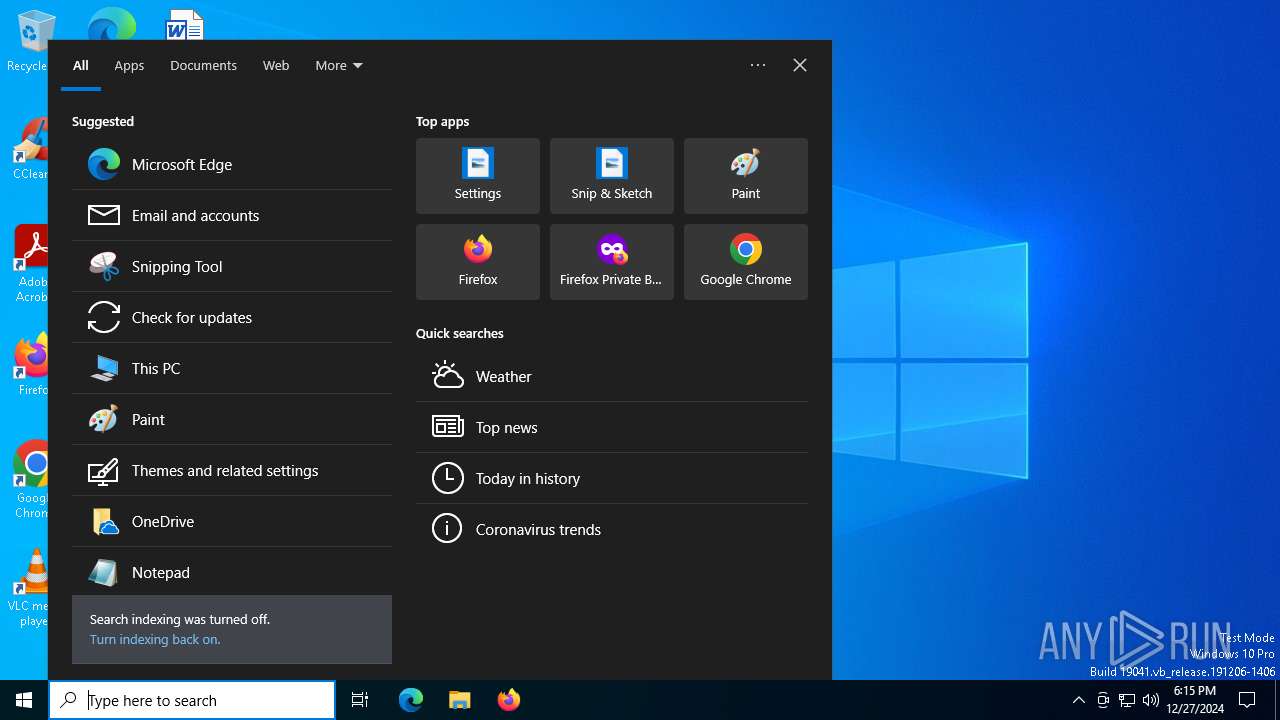
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | D49C0406105741EF94941ED7C37F0428 |
| SHA1: | F1BF31B6A744348234ECB09219F0960D4A70C64F |
| SHA256: | 55E43FAED33C4F84C08BA1EB331E0BF5F96A22F34D6144783C89ADF0EB69FC7F |
| SSDEEP: | 98304:X2NkKCmRf7uY1+DVlYZ+hHaIDgQCpeZykoe:lXgP |
MALICIOUS
QUASAR has been detected (YARA)
- mampato.exe (PID: 6412)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- mampato.exe (PID: 6412)
Reads the machine GUID from the registry
- mampato.exe (PID: 6412)
Reads Environment values
- mampato.exe (PID: 6412)
The process uses the downloaded file
- mampato.exe (PID: 6412)
Reads the computer name
- mampato.exe (PID: 6412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(6412) mampato.exe
Version1.4.1
C2 (3)192.168.0.7:8888
181.73.20.67:8888
Sub_DirMicrosoftCorp
Install_Namemsedit.exe
Mutexf716083e-7daa-4ff1-b809-07fd60392f7f
Startupmsaudiobg
TagInfected
LogDirLogs
SignatureLOpVC9Lgce5P+tB6zaF4khYkmKSy/Fkdp6JQeoTxykBIeM4o5h+S5xv2u9MiArxzNV1hrybu7Pv9nuJKLCmGt+kiLoZNo/dXWITroHm92XfKaS9IEgNdQqgEyi8xICj+5LyjnBLDSTh1xmTx2zPvWnpuOpz9Ok0IgPxGQzkFuoXKJTw5/G5XXz6U1JT2pq3o0kZebQ4YygrWOnhXs6dXymYaQTjz18II+5b1AOAjpaLLI5E2j/bWP37z87Z2cC6XMlIVE+PCns4sze2kuN7sIi3gpKAu9zBFTVHBLyKcne8+...
CertificateMIIE9DCCAtygAwIBAgIQAIlGNwQwhlTNAUd9CfUnHTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MTIyNTE2NDI1MFoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAvfa7mIrii2mPSw9t4Ap2hyBv25Jqv6cCgVbH8bq27WDXQUTwg//xk2KNRnqImvCadYNM+4vu...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:12 16:16:39+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3261952 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e41e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.1.0 |
| ProductVersionNumber: | 1.4.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Quasar Client |
| FileVersion: | 1.4.1 |
| InternalName: | Client.exe |
| LegalCopyright: | Copyright © MaxXor 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Client.exe |
| ProductName: | Quasar |
| ProductVersion: | 1.4.1 |
| AssemblyVersion: | 1.4.1.0 |
Total processes
125
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6412 | "C:\Users\admin\AppData\Local\Temp\mampato.exe" | C:\Users\admin\AppData\Local\Temp\mampato.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Version: 1.4.1 Modules
Quasar(PID) Process(6412) mampato.exe Version1.4.1 C2 (3)192.168.0.7:8888 181.73.20.67:8888 Sub_DirMicrosoftCorp Install_Namemsedit.exe Mutexf716083e-7daa-4ff1-b809-07fd60392f7f Startupmsaudiobg TagInfected LogDirLogs SignatureLOpVC9Lgce5P+tB6zaF4khYkmKSy/Fkdp6JQeoTxykBIeM4o5h+S5xv2u9MiArxzNV1hrybu7Pv9nuJKLCmGt+kiLoZNo/dXWITroHm92XfKaS9IEgNdQqgEyi8xICj+5LyjnBLDSTh1xmTx2zPvWnpuOpz9Ok0IgPxGQzkFuoXKJTw5/G5XXz6U1JT2pq3o0kZebQ4YygrWOnhXs6dXymYaQTjz18II+5b1AOAjpaLLI5E2j/bWP37z87Z2cC6XMlIVE+PCns4sze2kuN7sIi3gpKAu9zBFTVHBLyKcne8+... CertificateMIIE9DCCAtygAwIBAgIQAIlGNwQwhlTNAUd9CfUnHTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MTIyNTE2NDI1MFoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAvfa7mIrii2mPSw9t4Ap2hyBv25Jqv6cCgVbH8bq27WDXQUTwg//xk2KNRnqImvCadYNM+4vu... | |||||||||||||||
Total events
181
Read events
181
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
45
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4328 | svchost.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4328 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6876 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
6876 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4328 | svchost.exe | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4328 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.161:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |