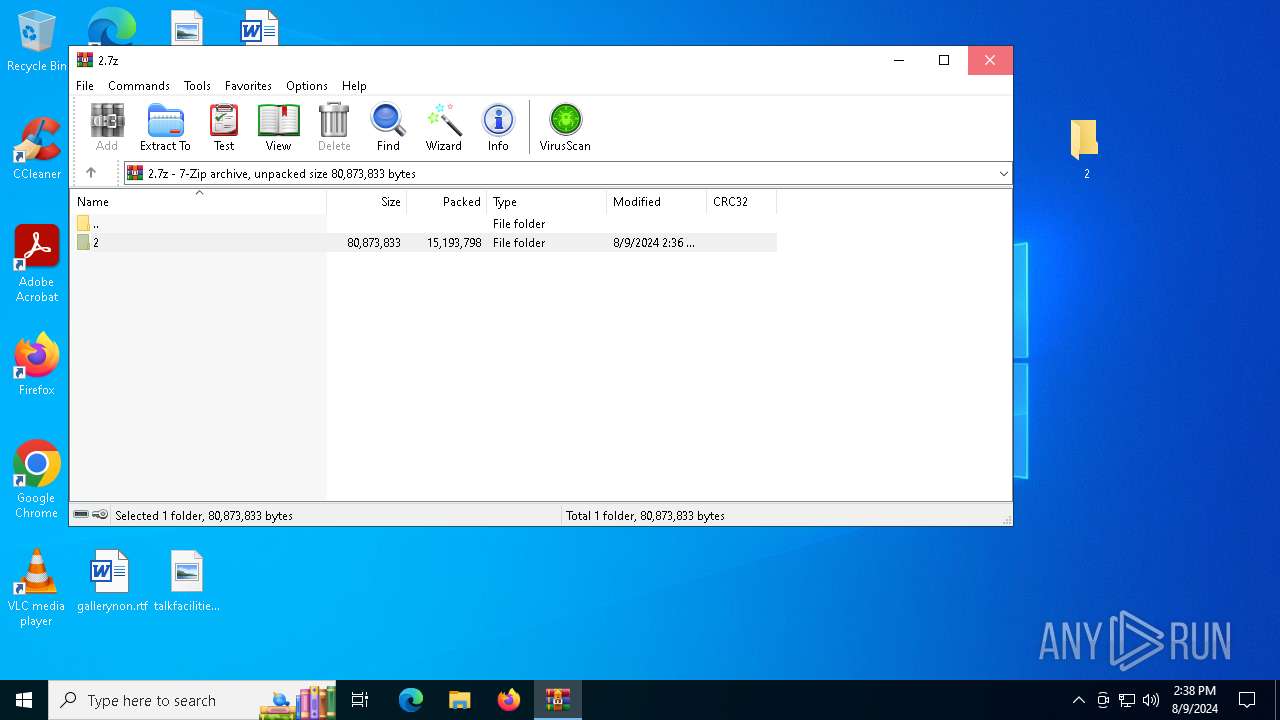
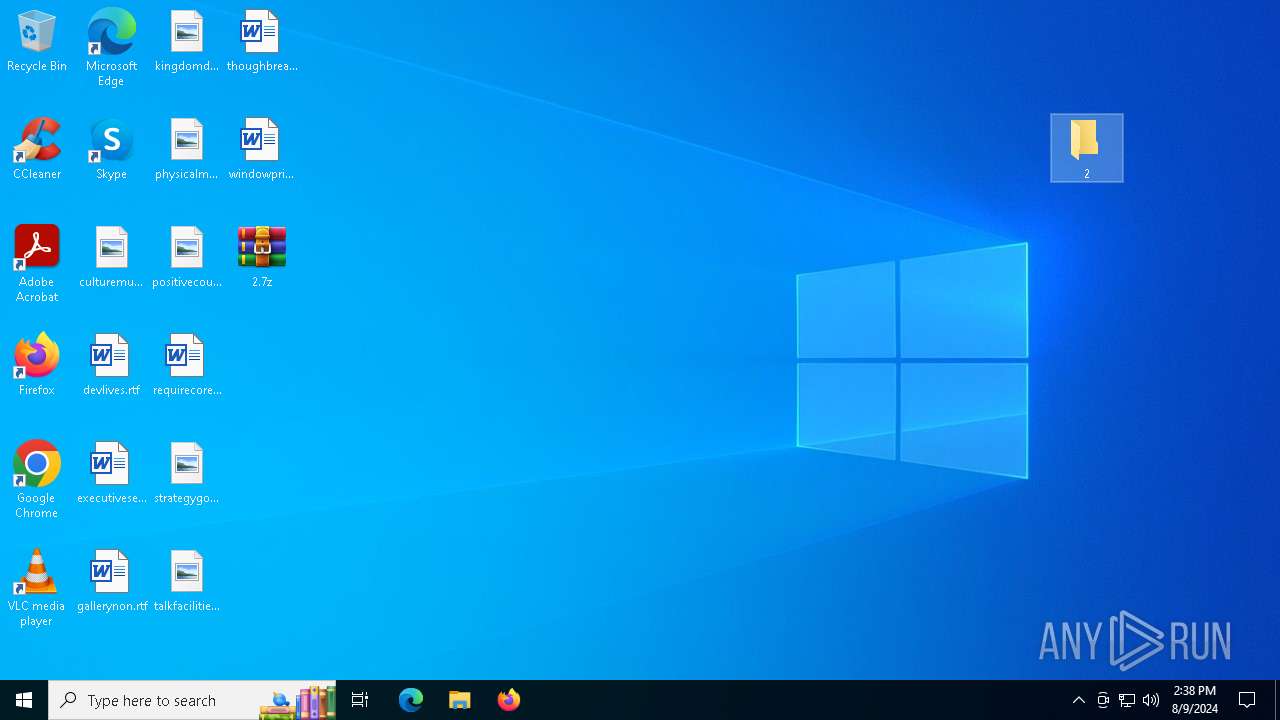
| File name: | 2.7z |
| Full analysis: | https://app.any.run/tasks/bd22db50-4ccf-463d-8676-fc7e727c2c03 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | August 09, 2024, 14:38:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 92744EA32EE8C48D927106AF0336F1DE |
| SHA1: | D6B170D0CC0BDFEF84BB6E2A893F4729810692DC |
| SHA256: | 5585C9C1F432C9C4BB510FD9FDC42A06B5E38A29FAF19115A5991A154797DEF1 |
| SSDEEP: | 98304:fyZPFAhYoDyyFn6JnRtokbYAgdUlb2W5hvfn89uiMsFokOjB9FW8y7kDFDT4Q0se:OB2NP6z5V4+JRKVoirudfEgI1P |
MALICIOUS
COBALTSTRIKE has been detected (YARA)
- osd.com (PID: 1432)
SUSPICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6536)
Reads security settings of Internet Explorer
- osd.com (PID: 1432)
There is functionality for VM detection (antiVM strings)
- osd.com (PID: 1432)
Checks Windows Trust Settings
- osd.com (PID: 1432)
INFO
Manual execution by a user
- osd.com (PID: 1432)
Checks proxy server information
- osd.com (PID: 1432)
Checks supported languages
- osd.com (PID: 1432)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6536)
Reads the computer name
- osd.com (PID: 1432)
Reads the machine GUID from the registry
- osd.com (PID: 1432)
Reads the software policy settings
- osd.com (PID: 1432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
CobalStrike
(PID) Process(1432) osd.com
C2 (4)vangogh.bytedance.com/v4/static/v1.7.9/gcaptcha4.js
passport.bytedance.com/v4/static/v1.7.9/gcaptcha4.js
learning.bytedance.com/v4/static/v1.7.9/gcaptcha4.js
news.163.com/v4/static/v1.7.9/gcaptcha4.js
BeaconTypeHTTPS
Port443
SleepTime5000
MaxGetSize1412336
Jitter37
PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDhZrDpo62NHZnfVYr1IlwYsino
KL1sKjhut0EBkybUBfs58IhqI916OZ2/9a6JSzjcYNEZ/mdiqa6dUm6aP5uJkDuj
nBHrGrnDCWy5kwGJMZAwh0rkwoLzrLin4+LPnncnNF7syySVYBkEHkEgb77fOJ00
gcIIh1fcTdkYq7Ec8wIDAQAB
-----END PUBLIC KEY-----
DNS_strategyround-robin
DNS_strategy_rotate_seconds-1
DNS_strategy_fail_x-1
DNS_strategy_fail_seconds-1
SpawnTo00000000000000000000000000000000
Spawnto_x86%windir%\syswow64\runonce.exe
Spawnto_x64%windir%\sysnative\runonce.exe
CryptoScheme0
HttpGet_VerbGET
HttpPost_VerbPOST
HttpPostChunk0
Watermark666666666
bStageCleanupTrue
bCFGCautionTrue
UserAgentMozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.35 (KHTML, like Gecko) Chrome/127.0.0.0 Safari/537.35
HttpPostUri/v4/static/v1.7.9/script.js
Malleable_C2_InstructionsRemove 14234 bytes from the beginning, Base64 URL-safe decode
HttpGet_Metadata
ConstHeaders (4)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Host: static.microsoft.com
Referer: https://static.microsoft.com/
Accept-Encoding: gzip, deflate
SessionId (3)base64url
prepend: __ms-cv=
header: Cookie
HttpPost_Metadata
ConstHeaders (4)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Host: cdn.bootcss.com
Referer: http://cdn.bootcss.com/
Accept-Encoding: gzip, deflate
SessionId (2)base64url
parameter: __ms-cv
Output (2)base64url
print
SSH_BannerHost: staos.microsoft.com
bUsesCookies0001
Proxy_BehaviorUse IE settings
tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
smbFrameHeader0005800000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
KillDate0-0-0
bProcInject_StartRWXFalse
bProcInject_UseRWXFalse
bProcInject_MinAllocSize18700
ProcInject_PrependAppend_x8690909090..90909090
ProcInject_PrependAppend_x6490909090..90909090
ProcInject_Stub40ed048138df0b3e23a0ef24dc5efa1a
ProcInject_AllocationMethodVirtualAllocEx
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
124
Monitored processes
3
Malicious processes
1
Suspicious processes
0
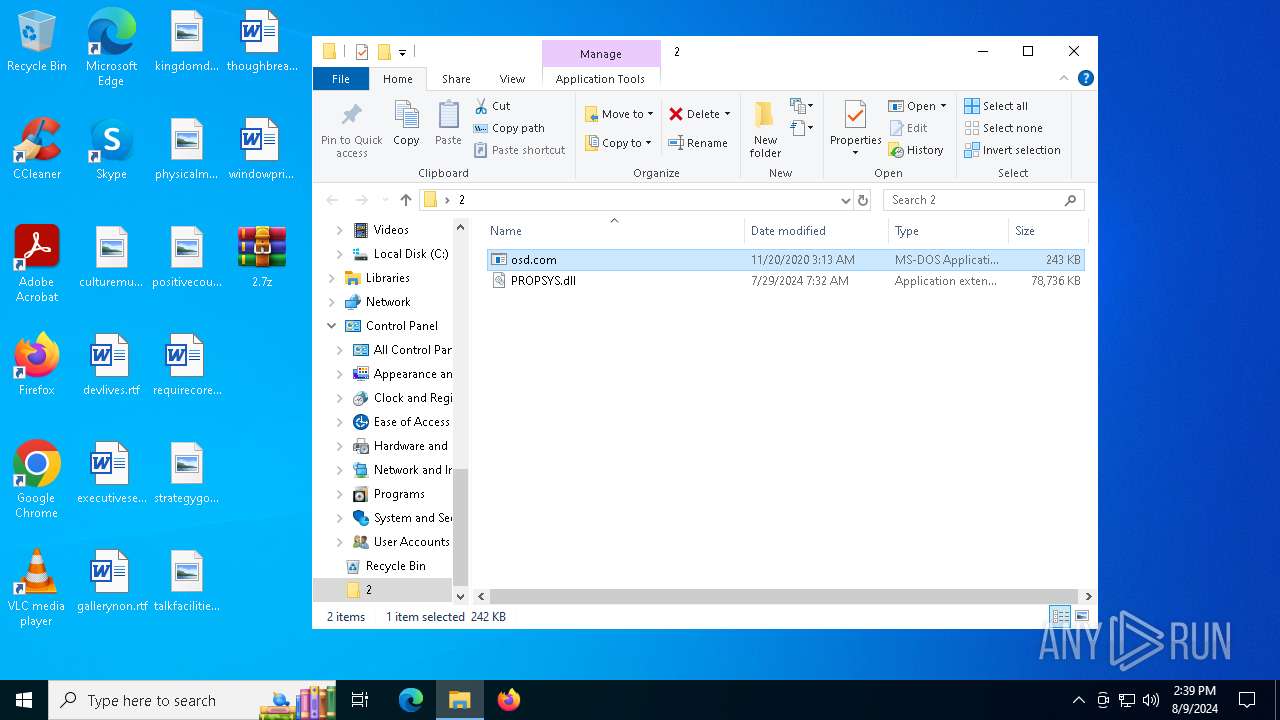
Behavior graph
Click at the process to see the details
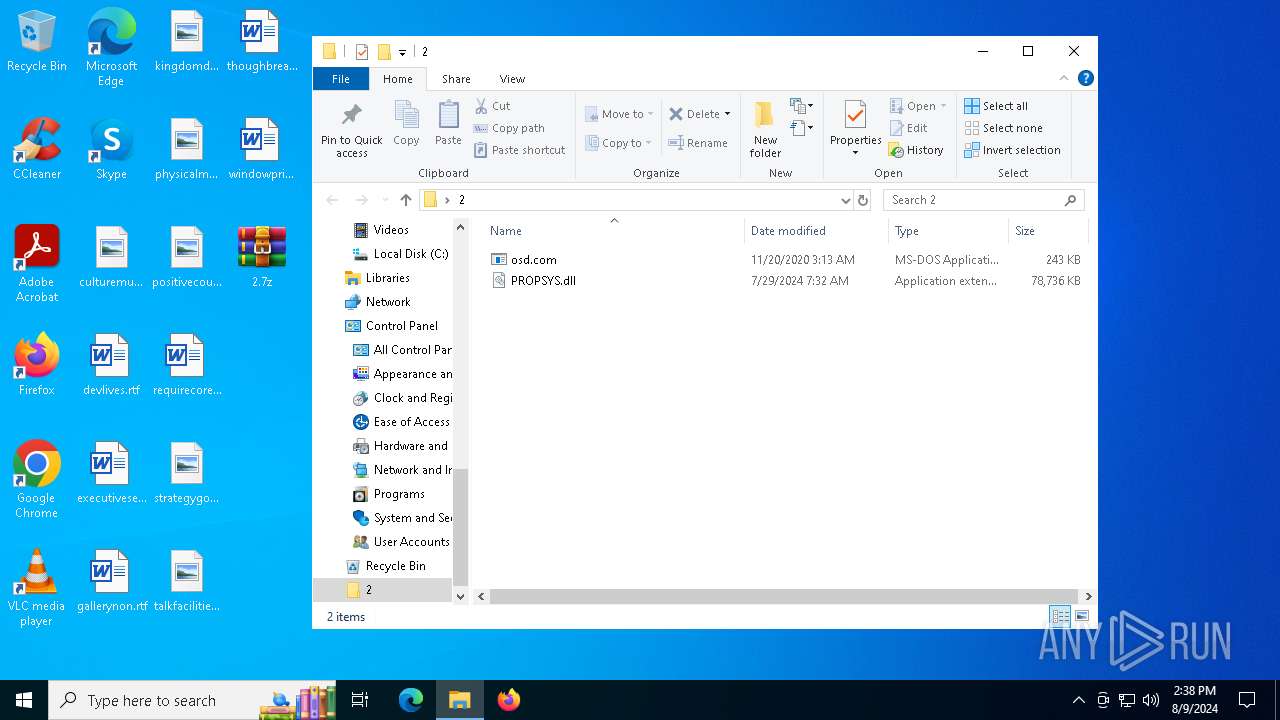
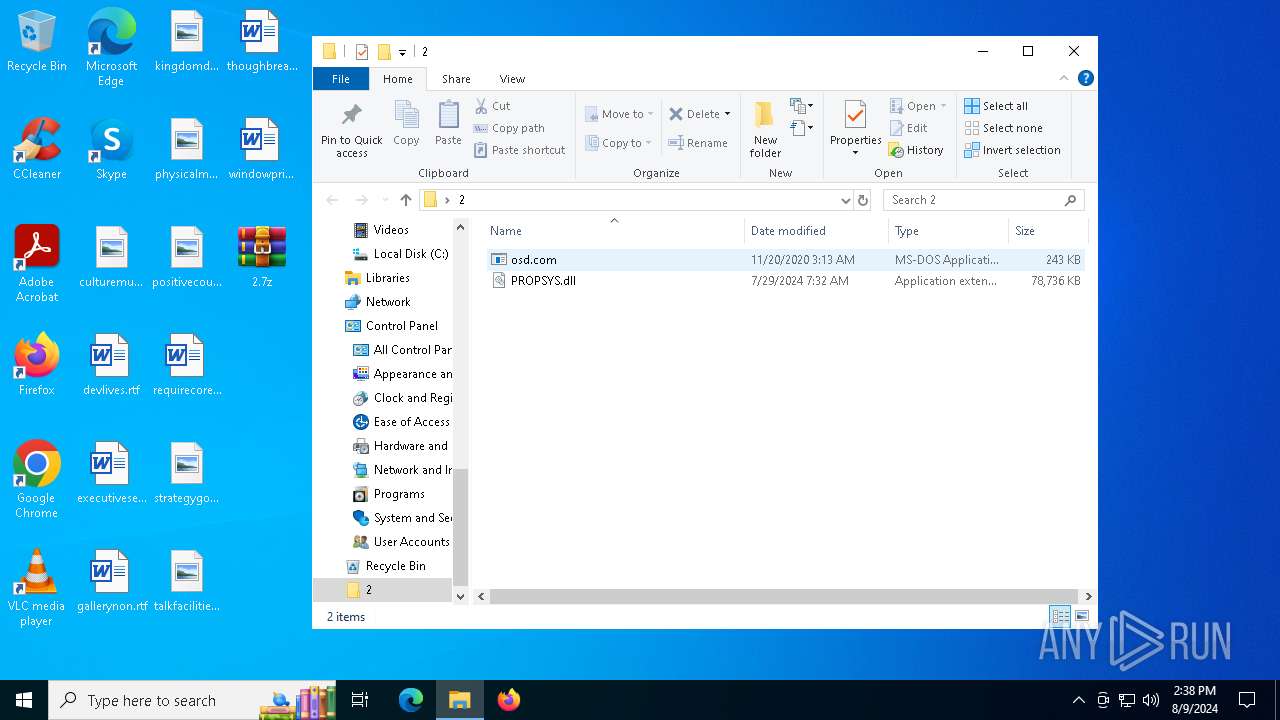
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1432 | "C:\Users\admin\Desktop\2\osd.com" | C:\Users\admin\Desktop\2\osd.com | explorer.exe | ||||||||||||
User: admin Company: Xiaomi Inc. Integrity Level: MEDIUM Description: Mi Notebook core components Version: 1.0.0.152 Modules
CobalStrike(PID) Process(1432) osd.com C2 (4)vangogh.bytedance.com/v4/static/v1.7.9/gcaptcha4.js passport.bytedance.com/v4/static/v1.7.9/gcaptcha4.js learning.bytedance.com/v4/static/v1.7.9/gcaptcha4.js news.163.com/v4/static/v1.7.9/gcaptcha4.js BeaconTypeHTTPS Port443 SleepTime5000 MaxGetSize1412336 Jitter37 PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDhZrDpo62NHZnfVYr1IlwYsino
KL1sKjhut0EBkybUBfs58IhqI916OZ2/9a6JSzjcYNEZ/mdiqa6dUm6aP5uJkDuj
nBHrGrnDCWy5kwGJMZAwh0rkwoLzrLin4+LPnncnNF7syySVYBkEHkEgb77fOJ00
gcIIh1fcTdkYq7Ec8wIDAQAB
-----END PUBLIC KEY----- DNS_strategyround-robin DNS_strategy_rotate_seconds-1 DNS_strategy_fail_x-1 DNS_strategy_fail_seconds-1 SpawnTo00000000000000000000000000000000 Spawnto_x86%windir%\syswow64\runonce.exe Spawnto_x64%windir%\sysnative\runonce.exe CryptoScheme0 HttpGet_VerbGET HttpPost_VerbPOST HttpPostChunk0 Watermark666666666 bStageCleanupTrue bCFGCautionTrue UserAgentMozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.35 (KHTML, like Gecko) Chrome/127.0.0.0 Safari/537.35 HttpPostUri/v4/static/v1.7.9/script.js Malleable_C2_InstructionsRemove 14234 bytes from the beginning, Base64 URL-safe decode HttpGet_Metadata ConstHeaders (4)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Host: static.microsoft.com Referer: https://static.microsoft.com/ Accept-Encoding: gzip, deflate SessionId (3)base64url prepend: __ms-cv= header: Cookie HttpPost_Metadata ConstHeaders (4)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Host: cdn.bootcss.com Referer: http://cdn.bootcss.com/ Accept-Encoding: gzip, deflate SessionId (2)base64url parameter: __ms-cv Output (2)base64url print SSH_BannerHost: staos.microsoft.com bUsesCookies0001 Proxy_BehaviorUse IE settings tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 smbFrameHeader0005800000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 KillDate0-0-0 bProcInject_StartRWXFalse bProcInject_UseRWXFalse bProcInject_MinAllocSize18700 ProcInject_PrependAppend_x8690909090..90909090 ProcInject_PrependAppend_x6490909090..90909090 ProcInject_Stub40ed048138df0b3e23a0ef24dc5efa1a ProcInject_AllocationMethodVirtualAllocEx | |||||||||||||||
| 3540 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6536 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\2.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
4 460
Read events
4 433
Write events
27
Delete events
0
Modification events
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\2.7z | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.13919\2\PROPSYS.dll | — | |
MD5:— | SHA256:— | |||
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.13919\2\osd.com | executable | |
MD5:D239ED3700F590720B4639CD88478C00 | SHA256:EC8E4A4A211D934595A9AD4AA8112D9DECF682F74B08BF45D5AA38AB8FD172F5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
56
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6632 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4772 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4772 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2804 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.19:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4772 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6608 | backgroundTaskHost.exe | 92.123.104.19:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
th.bing.com |
| whitelisted |
vangogh.bytedance.com |
| whitelisted |