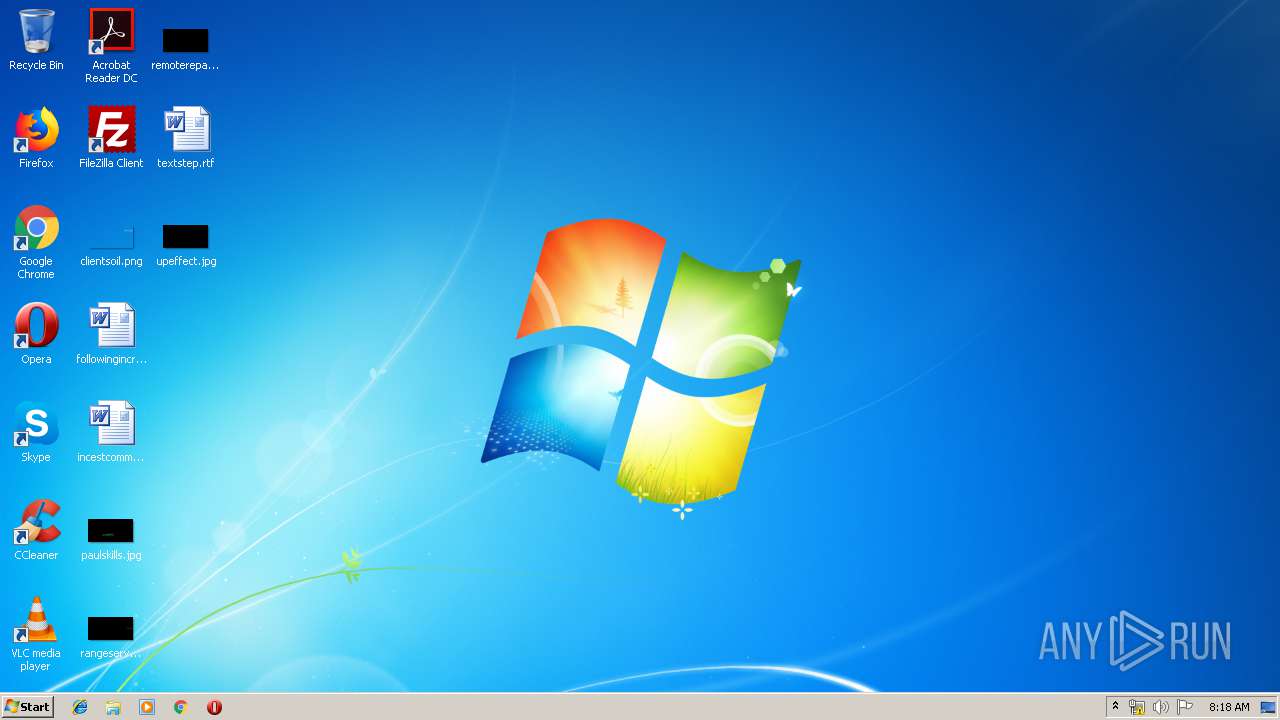
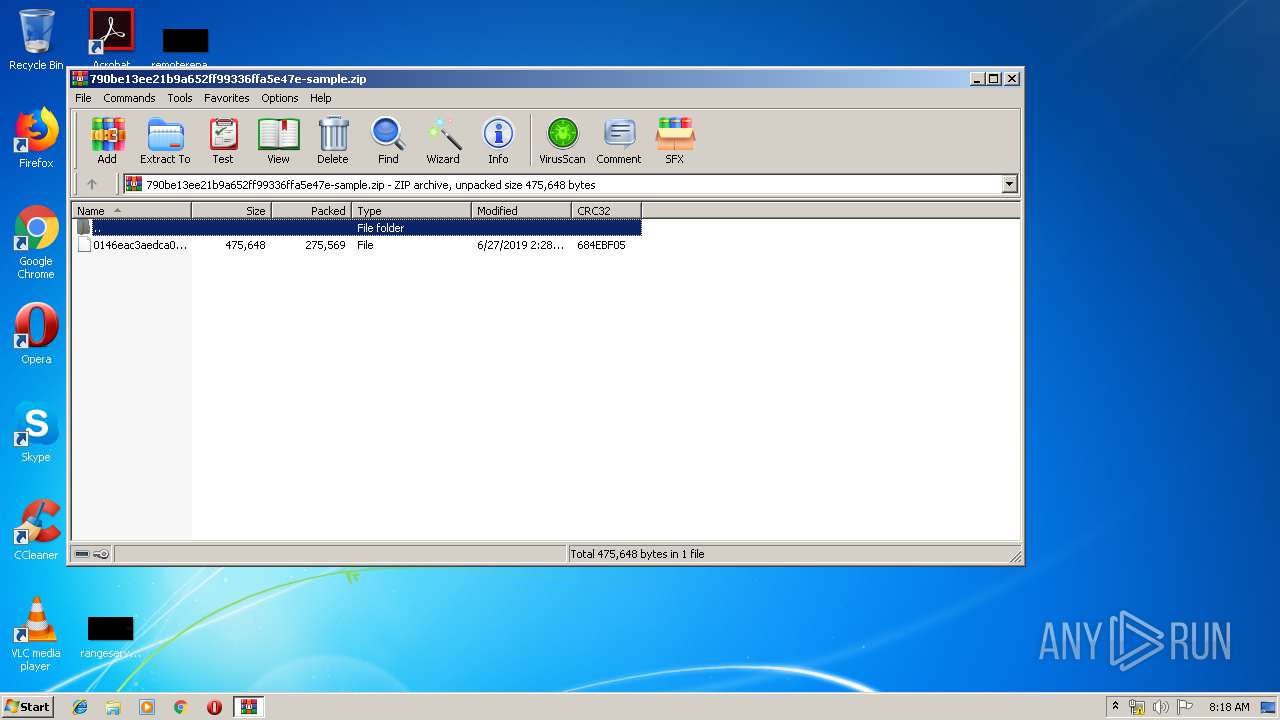
| File name: | 790be13ee21b9a652ff99336ffa5e47e-sample.zip |
| Full analysis: | https://app.any.run/tasks/c5896f5c-d10e-4028-bd07-1f28d5b724f1 |
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | July 18, 2019, 07:17:53 |
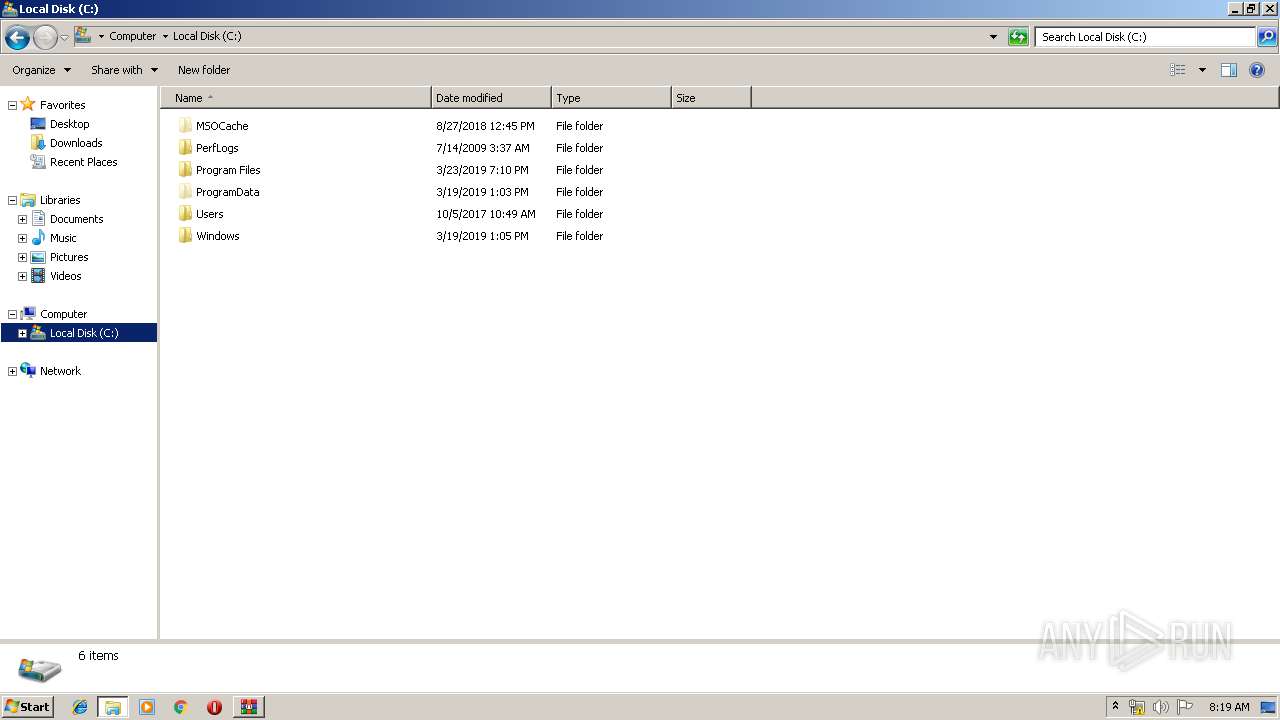
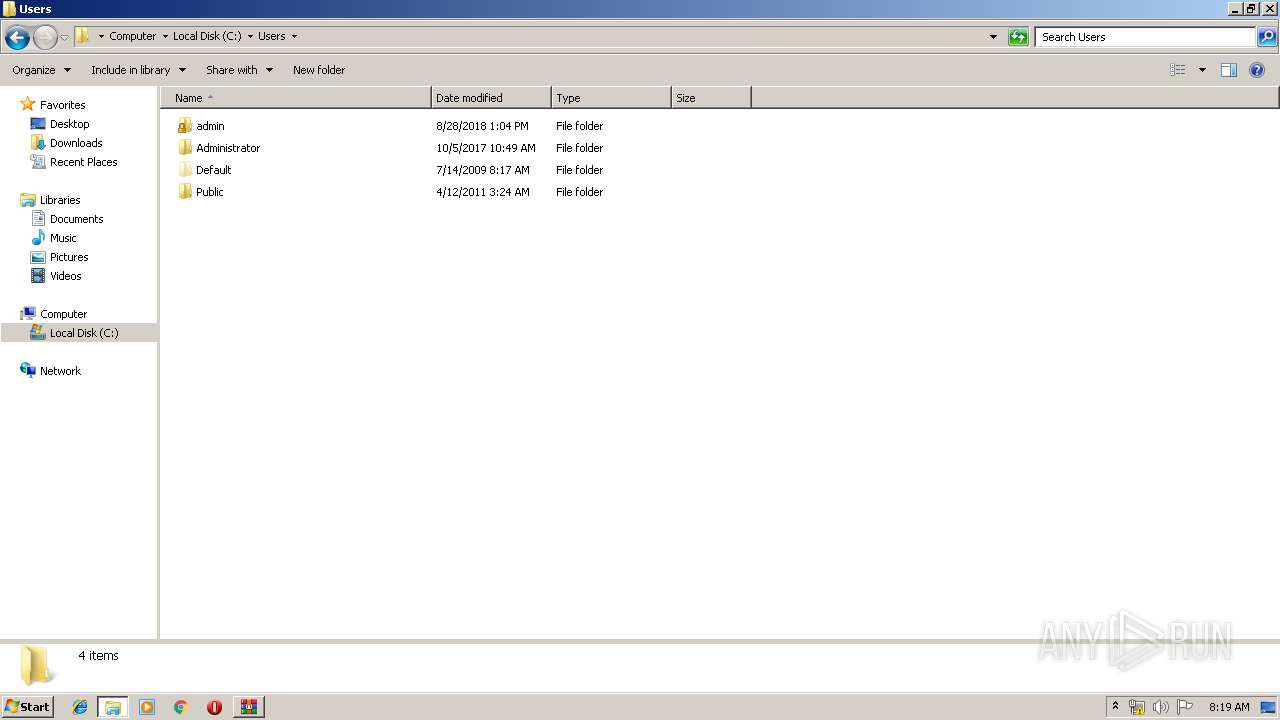
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 75617A0BD7D6F45CC377EA589F17A44D |
| SHA1: | 8AE1DAF3CD18C6642AF0D53A9FB51F0AB09F265C |
| SHA256: | 55546232C0AB0365F1657DA4A3B75422A36B859724D8434C49791072AFBE64C7 |
| SSDEEP: | 6144:PD4Ic41bI0pCMxY294gd447Wu1HsWGV4A1cXoBCe78+gM:PBcQCv2m47K1cXosU3h |
MALICIOUS
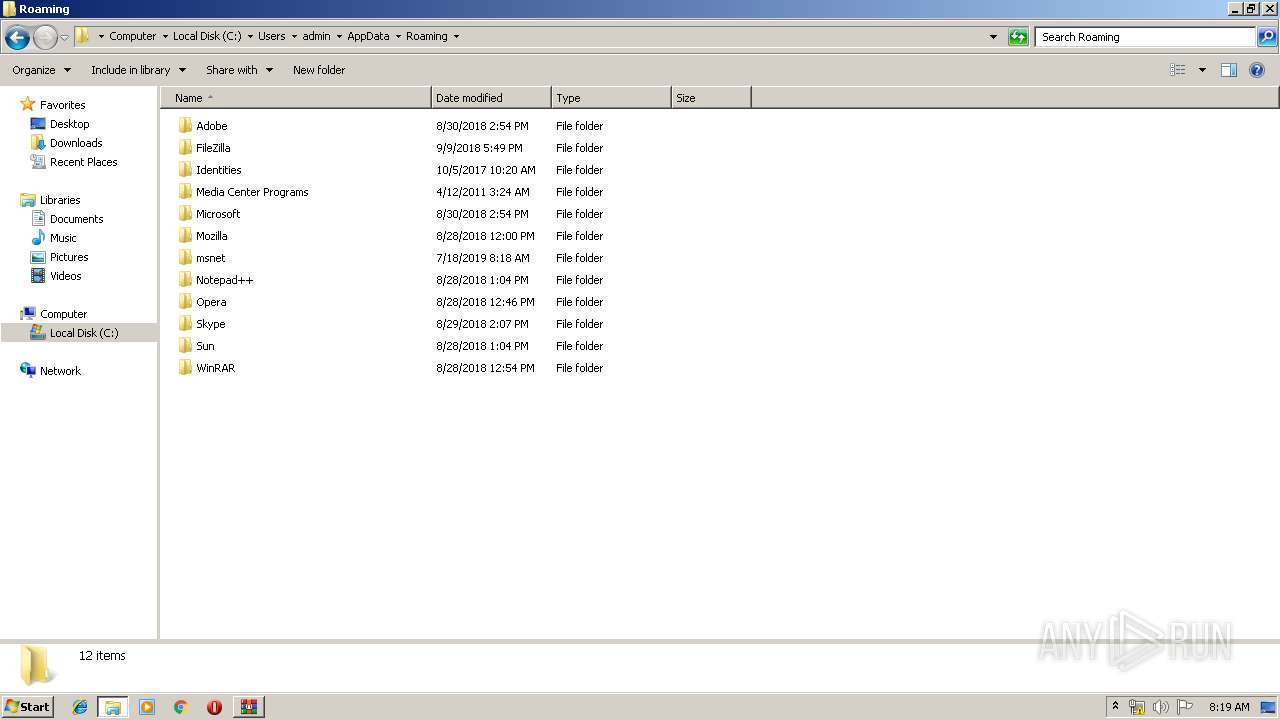
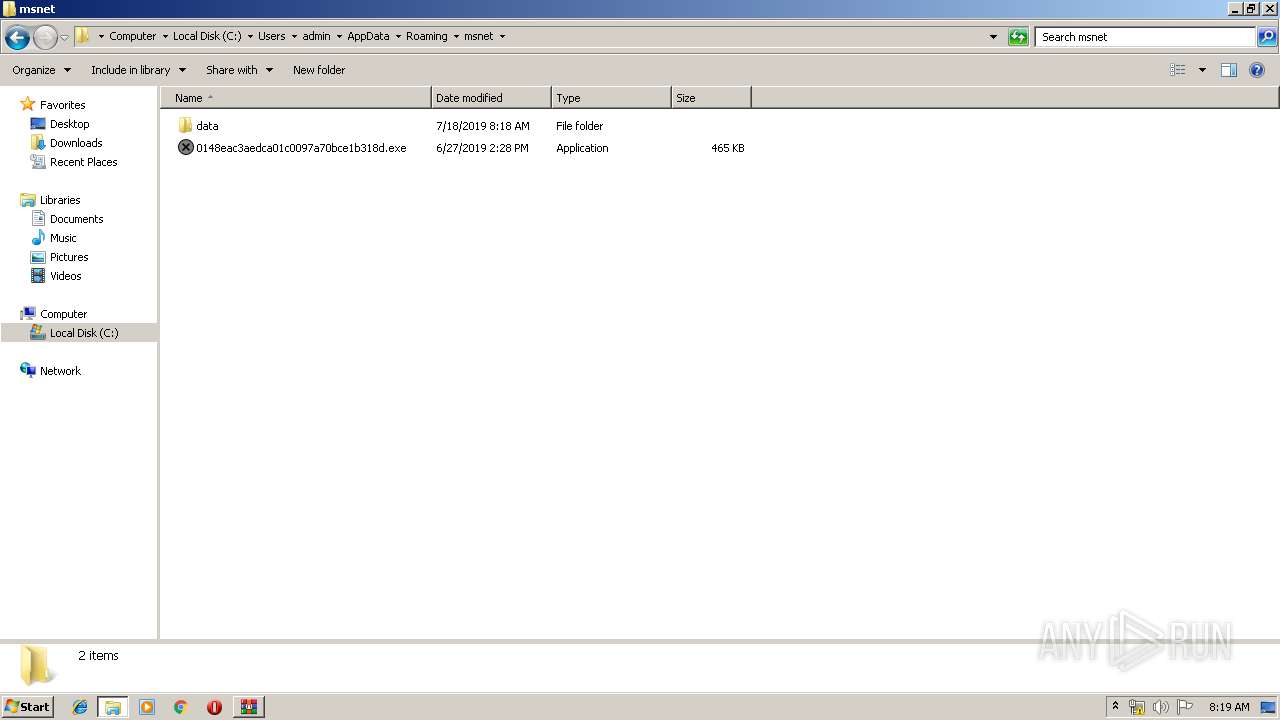
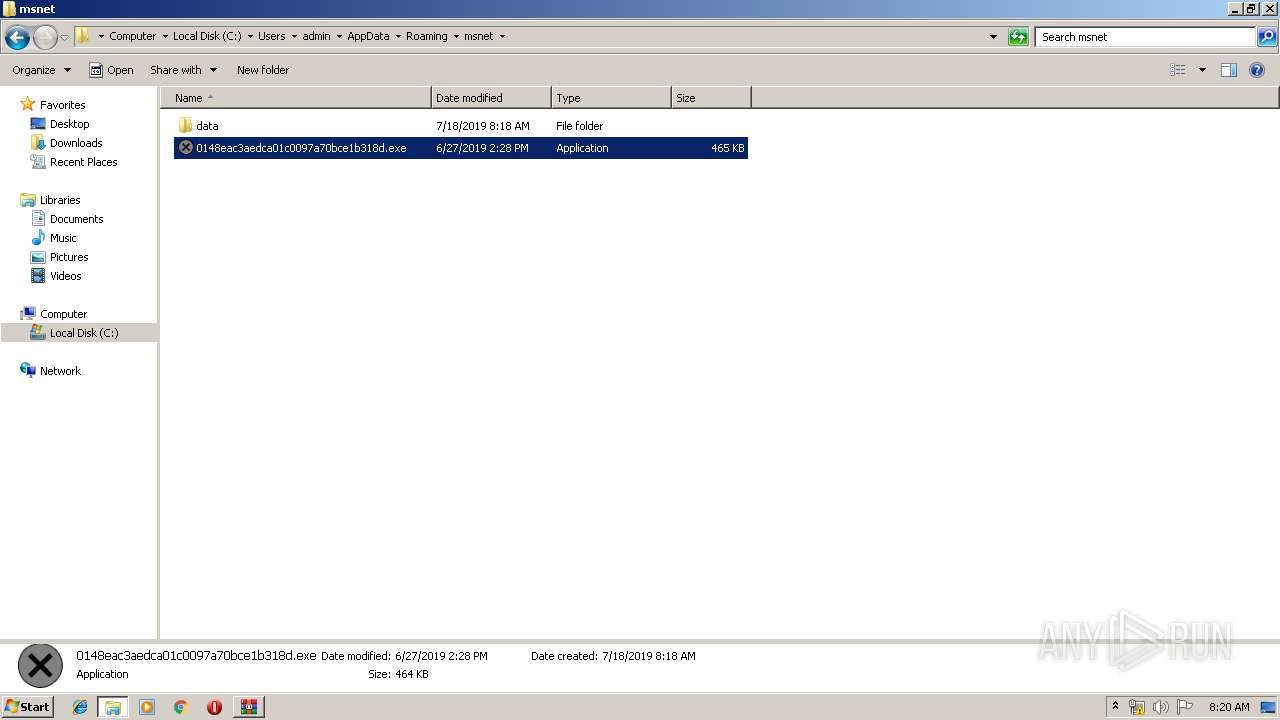
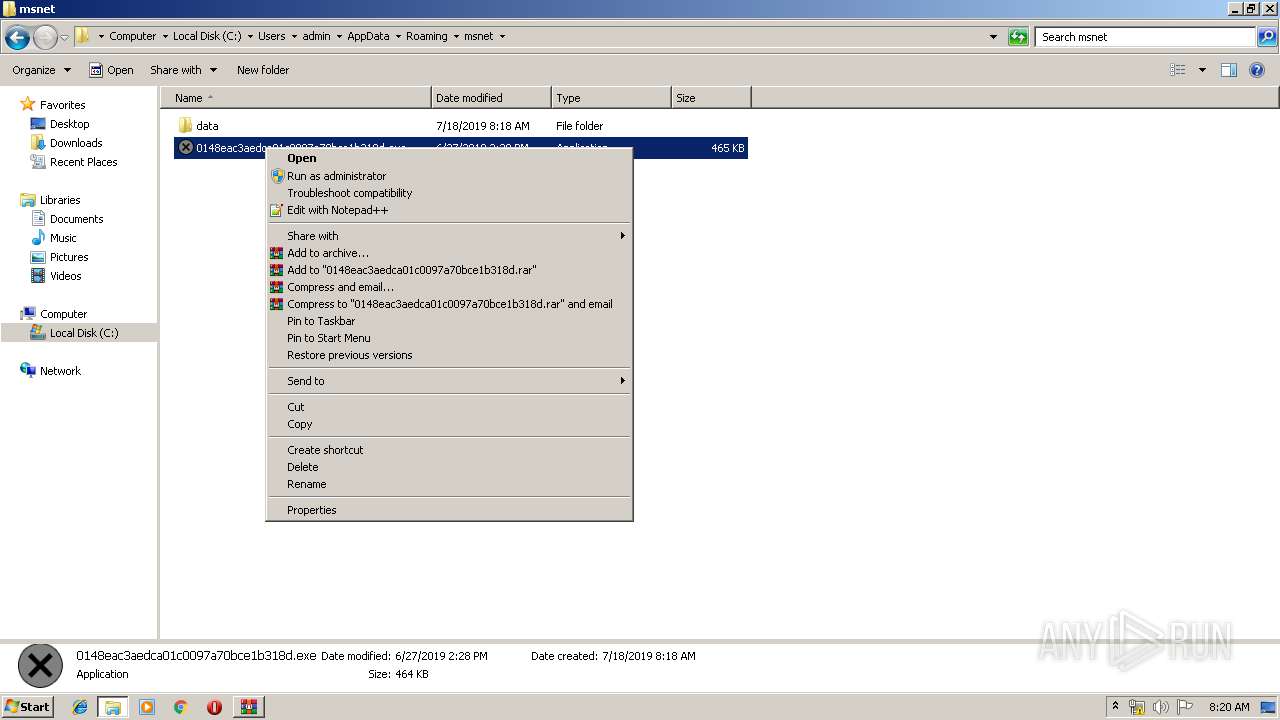
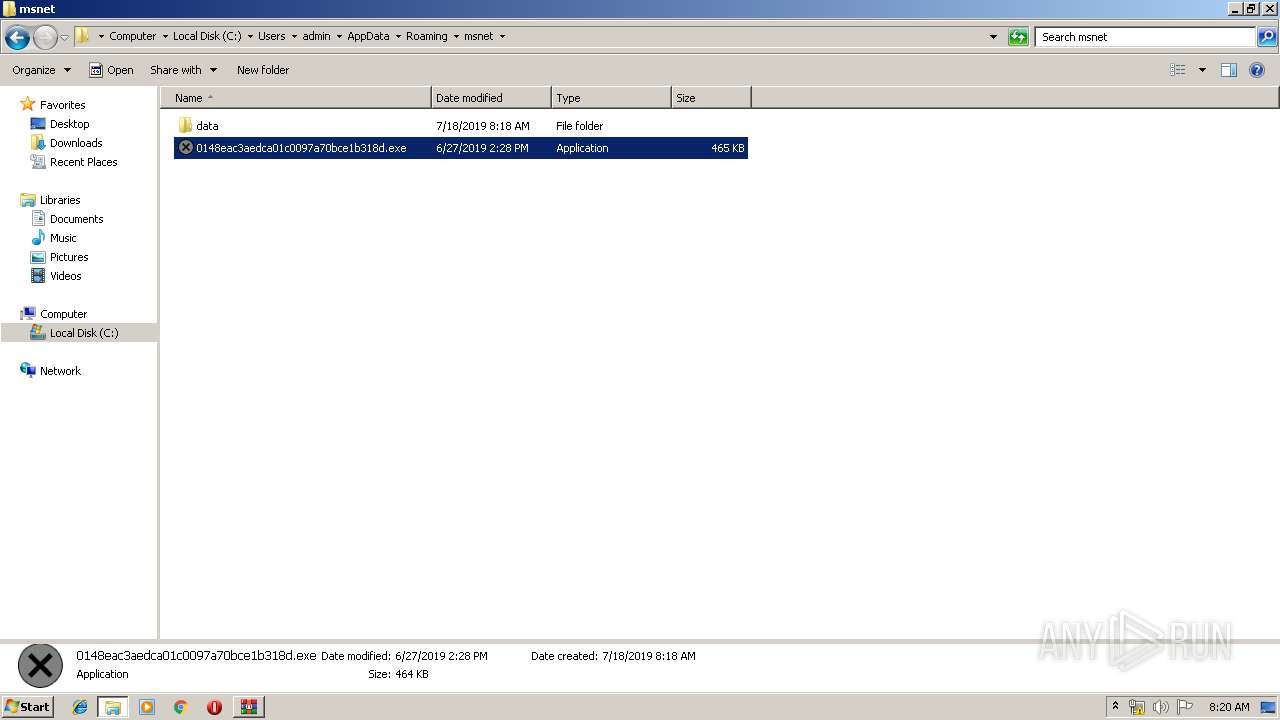
Application was dropped or rewritten from another process
- 0146eac3aedca01c0095a50bce1b316d.exe (PID: 3076)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 4084)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 2296)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 4068)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 1428)
Disables Windows Defender
- 0146eac3aedca01c0095a50bce1b316d.exe (PID: 3076)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 4084)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 2296)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 4068)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 1428)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 2804)
- cmd.exe (PID: 3464)
- cmd.exe (PID: 1696)
- cmd.exe (PID: 1468)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 3232)
- cmd.exe (PID: 2184)
- cmd.exe (PID: 1456)
- cmd.exe (PID: 3424)
- cmd.exe (PID: 3552)
Trickbot detected
- 0146eac3aedca01c0095a50bce1b316d.exe (PID: 3076)
Loads the Task Scheduler COM API
- 0146eac3aedca01c0095a50bce1b316d.exe (PID: 3076)
Executes PowerShell scripts
- cmd.exe (PID: 2152)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 0146eac3aedca01c0095a50bce1b316d.exe (PID: 3076)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 4084)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 2296)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 4068)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 1428)
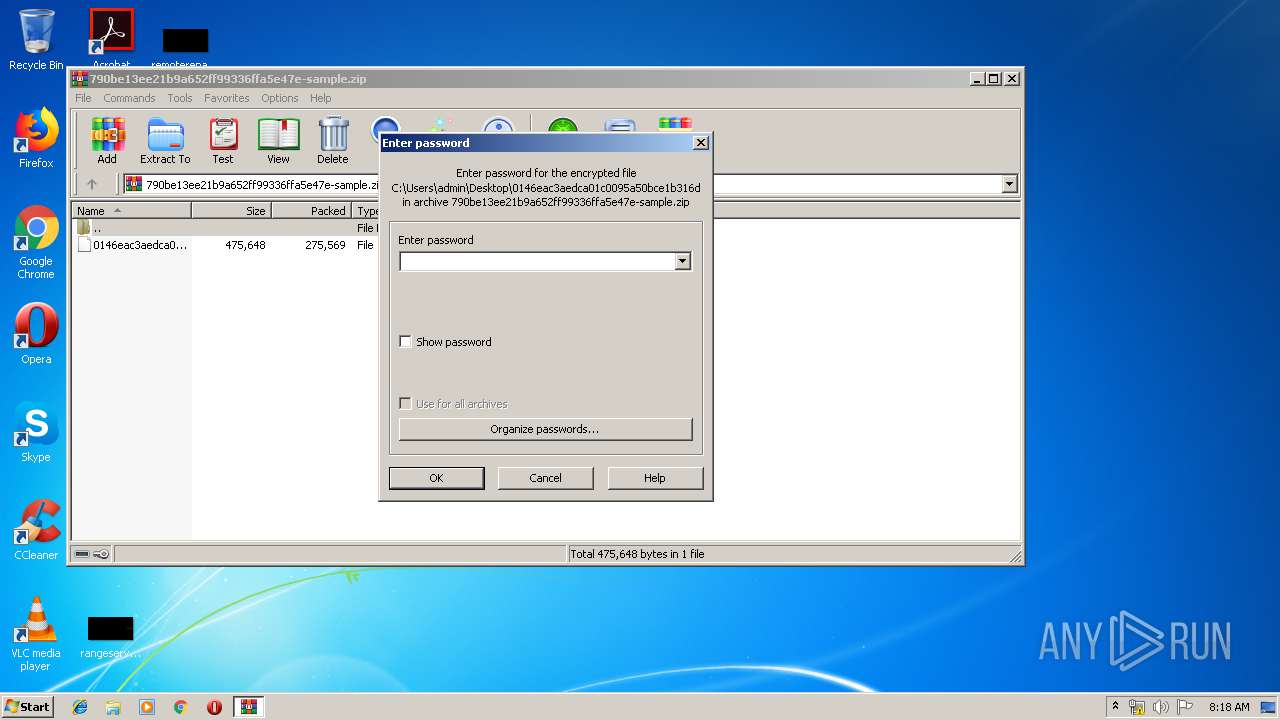
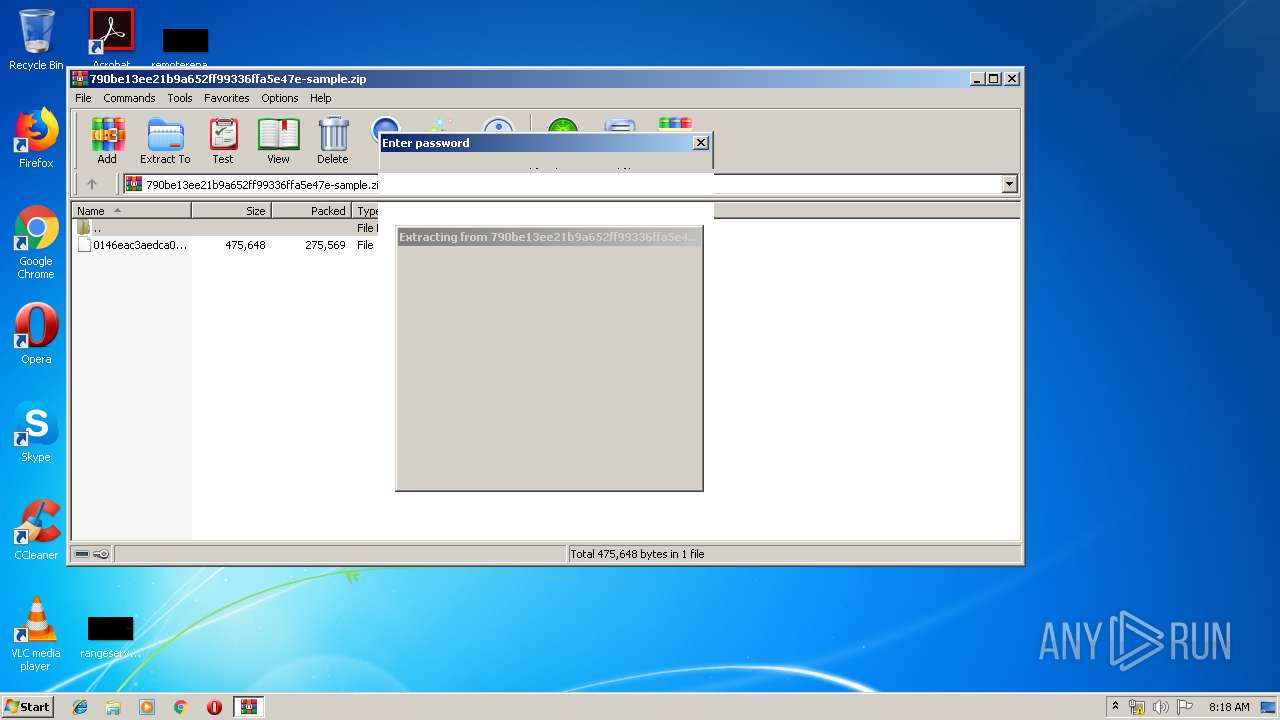
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3728)
- 0146eac3aedca01c0095a50bce1b316d.exe (PID: 3076)
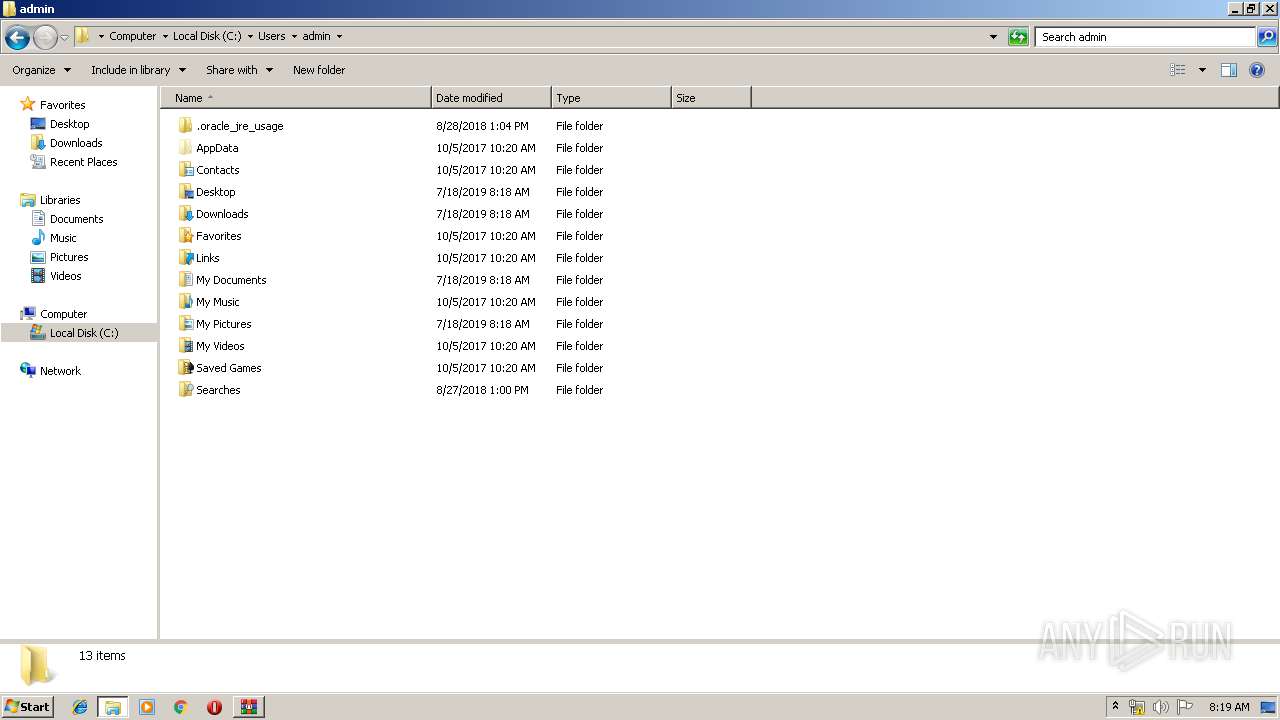
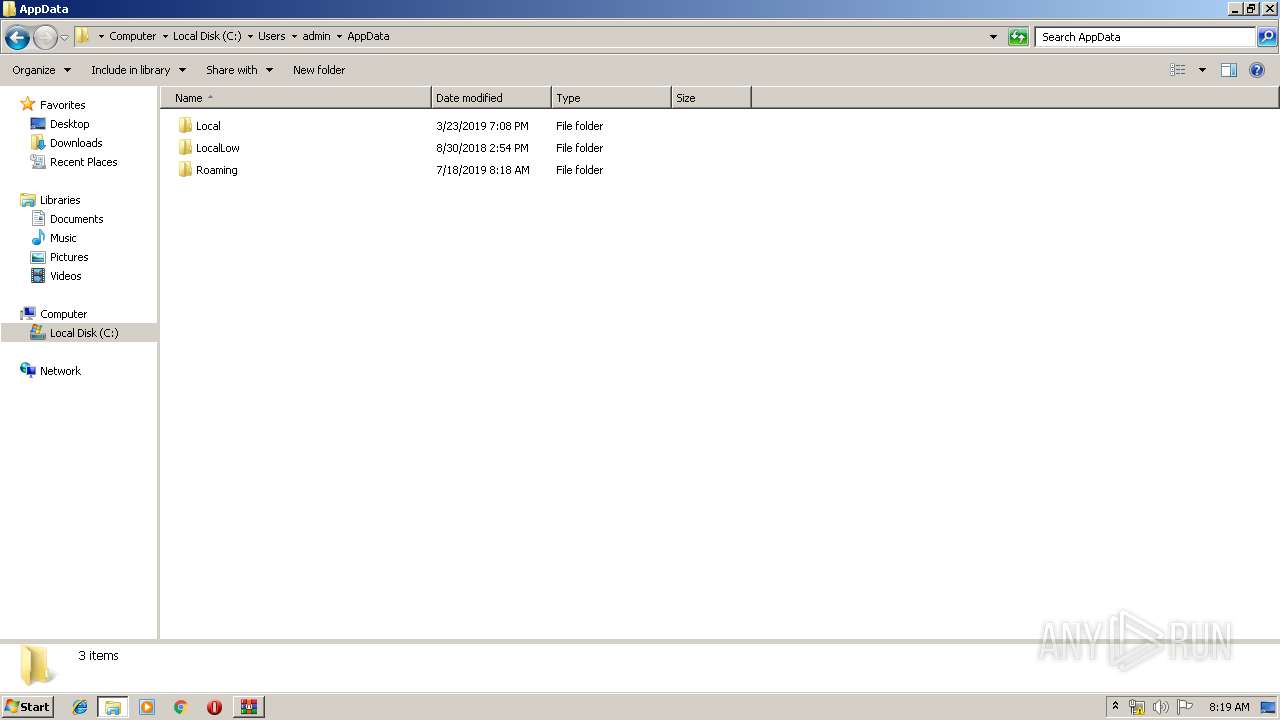
Creates files in the user directory
- powershell.exe (PID: 2932)
- 0146eac3aedca01c0095a50bce1b316d.exe (PID: 3076)
- powershell.exe (PID: 2628)
- powershell.exe (PID: 2748)
- powershell.exe (PID: 3804)
- powershell.exe (PID: 3228)
- powershell.exe (PID: 3536)
Executes PowerShell scripts
- cmd.exe (PID: 1816)
- cmd.exe (PID: 3684)
- cmd.exe (PID: 3832)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 1656)
Executed via Task Scheduler
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 2296)
INFO
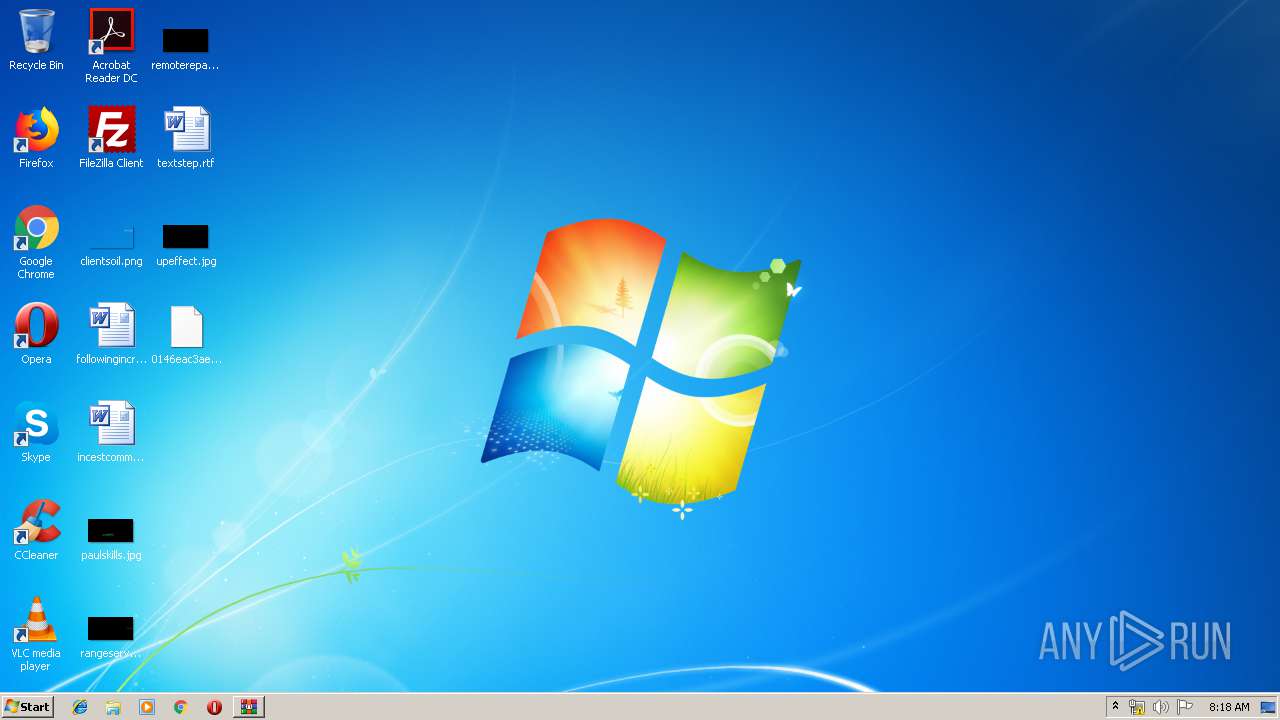
Manual execution by user
- 0146eac3aedca01c0095a50bce1b316d.exe (PID: 3076)
- explorer.exe (PID: 3160)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 4084)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 4068)
- 0148eac3aedca01c0097a70bce1b318d.exe (PID: 1428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
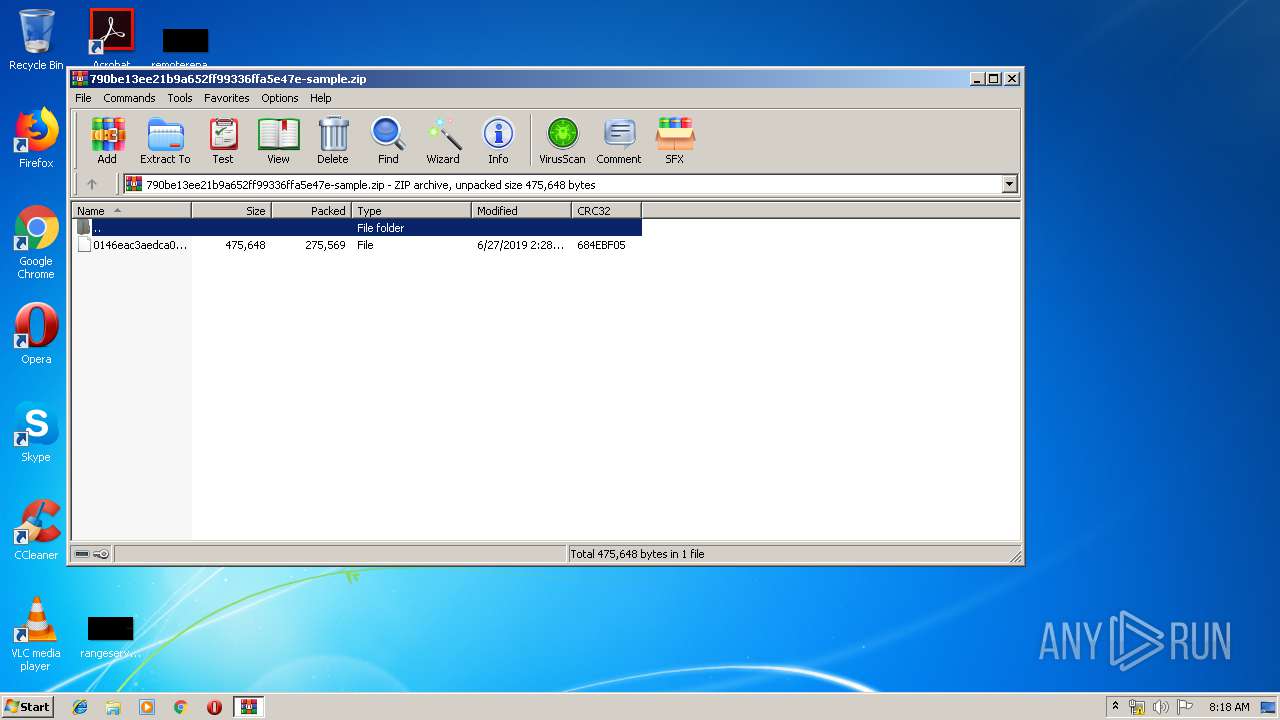
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:06:27 14:28:06 |
| ZipCRC: | 0x684ebf05 |
| ZipCompressedSize: | 275569 |
| ZipUncompressedSize: | 475648 |
| ZipFileName: | 0146eac3aedca01c0095a50bce1b316d |
Total processes
102
Monitored processes
43
Malicious processes
6
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | sc stop WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1062 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 836 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1428 | "C:\Users\admin\AppData\Roaming\msnet\0148eac3aedca01c0097a70bce1b318d.exe" | C:\Users\admin\AppData\Roaming\msnet\0148eac3aedca01c0097a70bce1b318d.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Macedonian (FYROM) - Standard Keyboard Layout Exit code: 0 Version: 10.0.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1456 | "C:\Windows\System32\cmd.exe" /c sc stop WinDefend | C:\Windows\System32\cmd.exe | — | 0148eac3aedca01c0097a70bce1b318d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1062 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1468 | /c sc delete WinDefend | C:\Windows\system32\cmd.exe | — | 0148eac3aedca01c0097a70bce1b318d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1532 | /c sc stop WinDefend | C:\Windows\system32\cmd.exe | — | 0148eac3aedca01c0097a70bce1b318d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1656 | /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\system32\cmd.exe | — | 0148eac3aedca01c0097a70bce1b318d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1696 | /c sc stop WinDefend | C:\Windows\system32\cmd.exe | — | 0148eac3aedca01c0097a70bce1b318d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1816 | /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\system32\cmd.exe | — | 0146eac3aedca01c0095a50bce1b316d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 860
Read events
1 505
Write events
355
Delete events
0
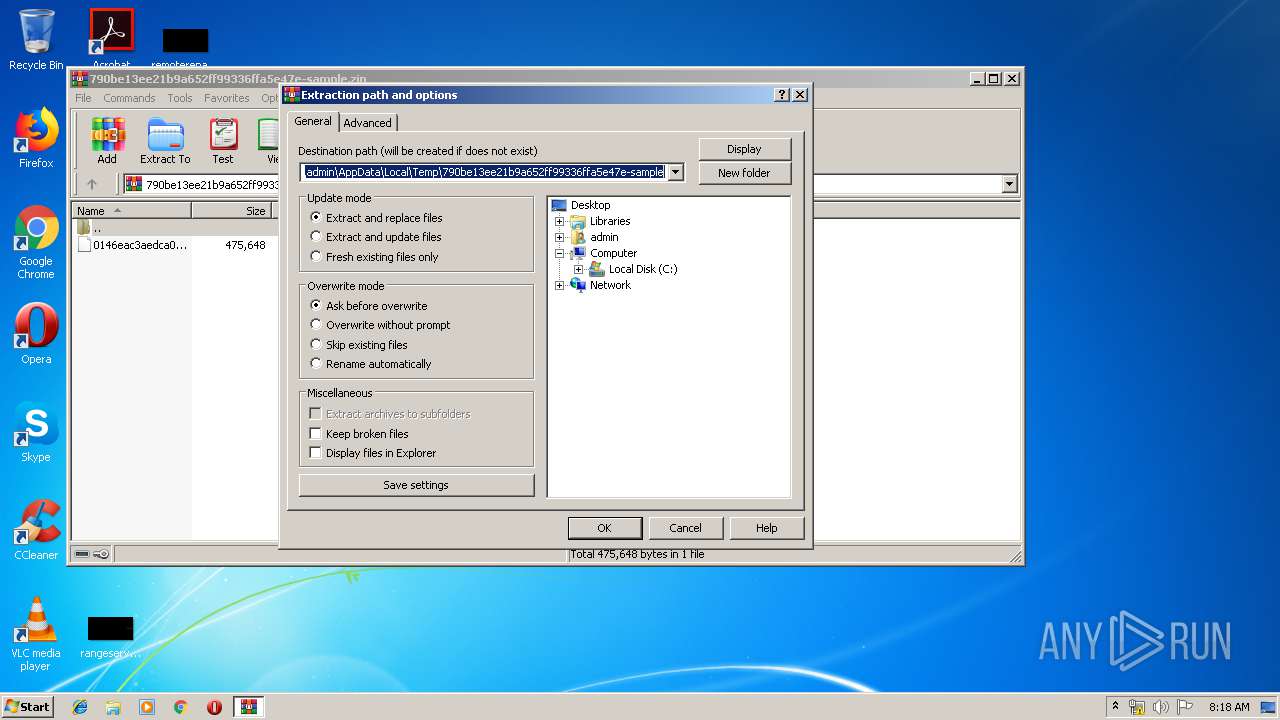
Modification events
| (PID) Process: | (3728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3728) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\790be13ee21b9a652ff99336ffa5e47e-sample.zip | |||
| (PID) Process: | (3728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (3728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
17
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\C3LIOPS6REFEY1VVOTTH.temp | — | |
MD5:— | SHA256:— | |||
| 2628 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2CSTWPY1OUQYVJN6GIRU.temp | — | |
MD5:— | SHA256:— | |||
| 2748 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\50N84JSE4UBUDSWLXUJ2.temp | — | |
MD5:— | SHA256:— | |||
| 3536 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\U3CRWX9WLJ4QYXF4T4E6.temp | — | |
MD5:— | SHA256:— | |||
| 3804 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HKGBCS11BYL4BIUCIS88.temp | — | |
MD5:— | SHA256:— | |||
| 3228 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\M68KB09I47QX2WN931IO.temp | — | |
MD5:— | SHA256:— | |||
| 3076 | 0146eac3aedca01c0095a50bce1b316d.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 3728 | WinRAR.exe | C:\Users\admin\Desktop\0146eac3aedca01c0095a50bce1b316d | executable | |
MD5:— | SHA256:— | |||
| 4084 | 0148eac3aedca01c0097a70bce1b318d.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 2628 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report