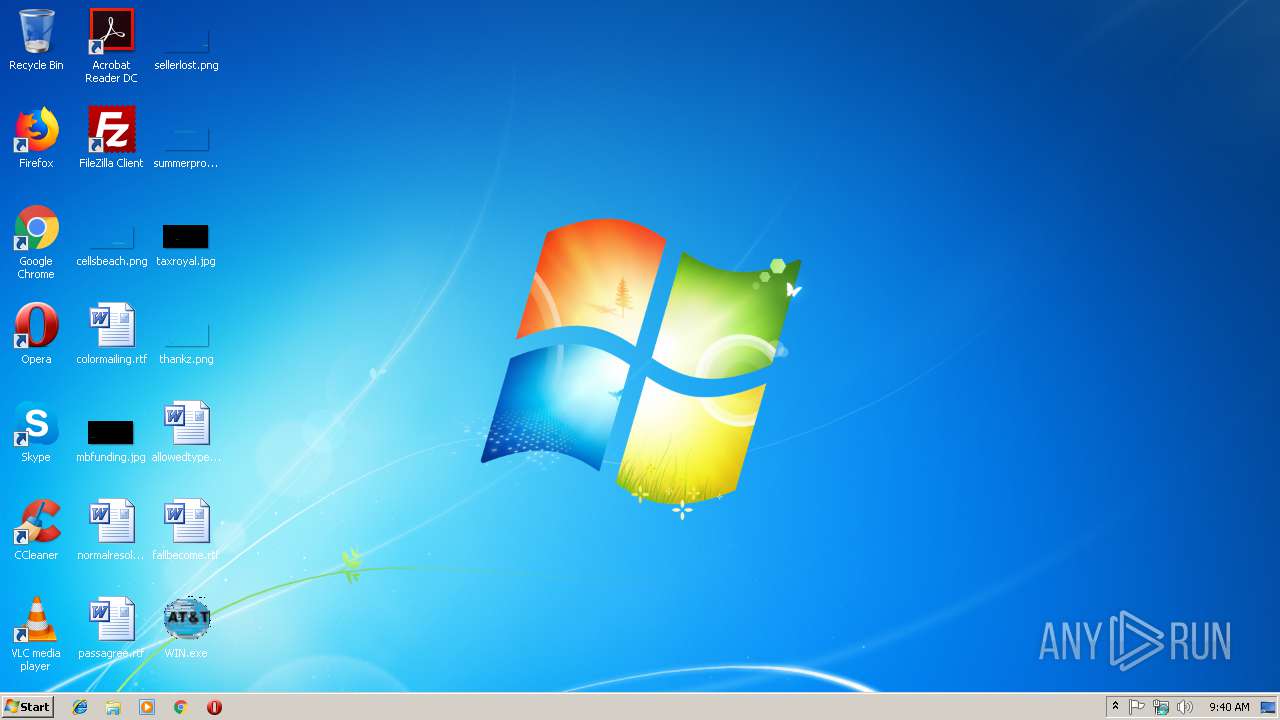
| File name: | WIN.exe |
| Full analysis: | https://app.any.run/tasks/3dd2da19-a899-40af-af84-f96edba346fd |
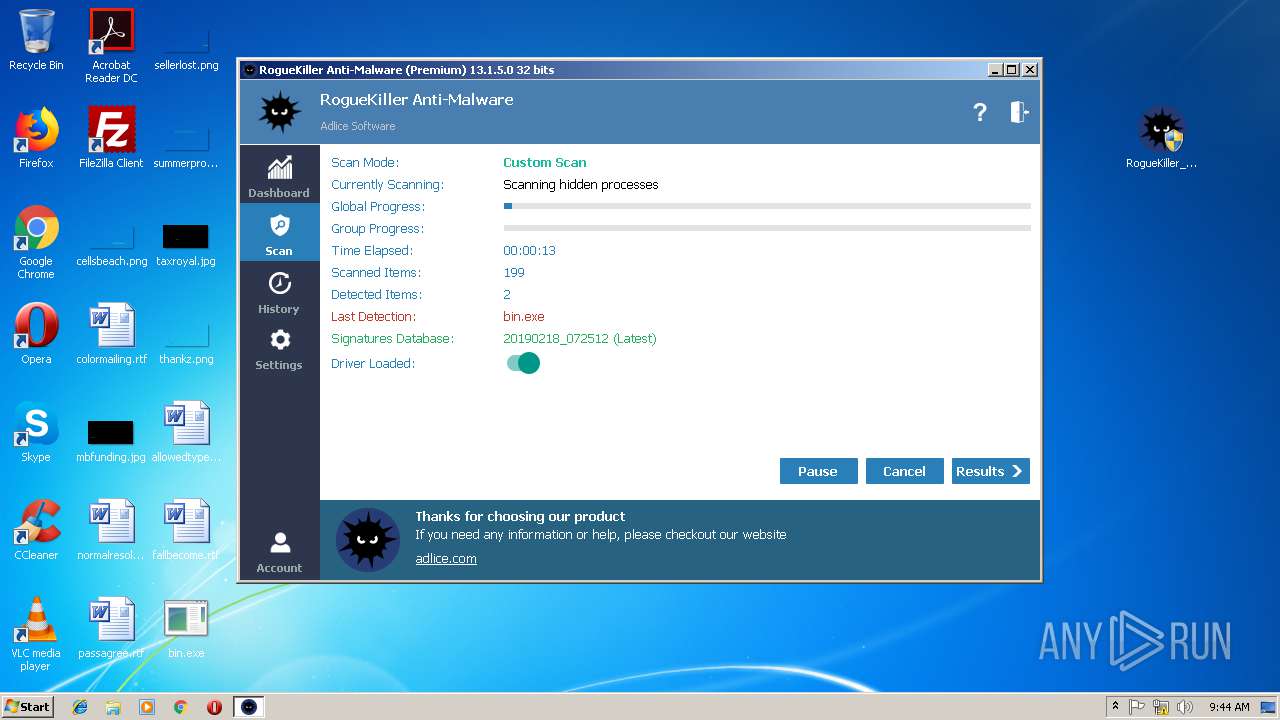
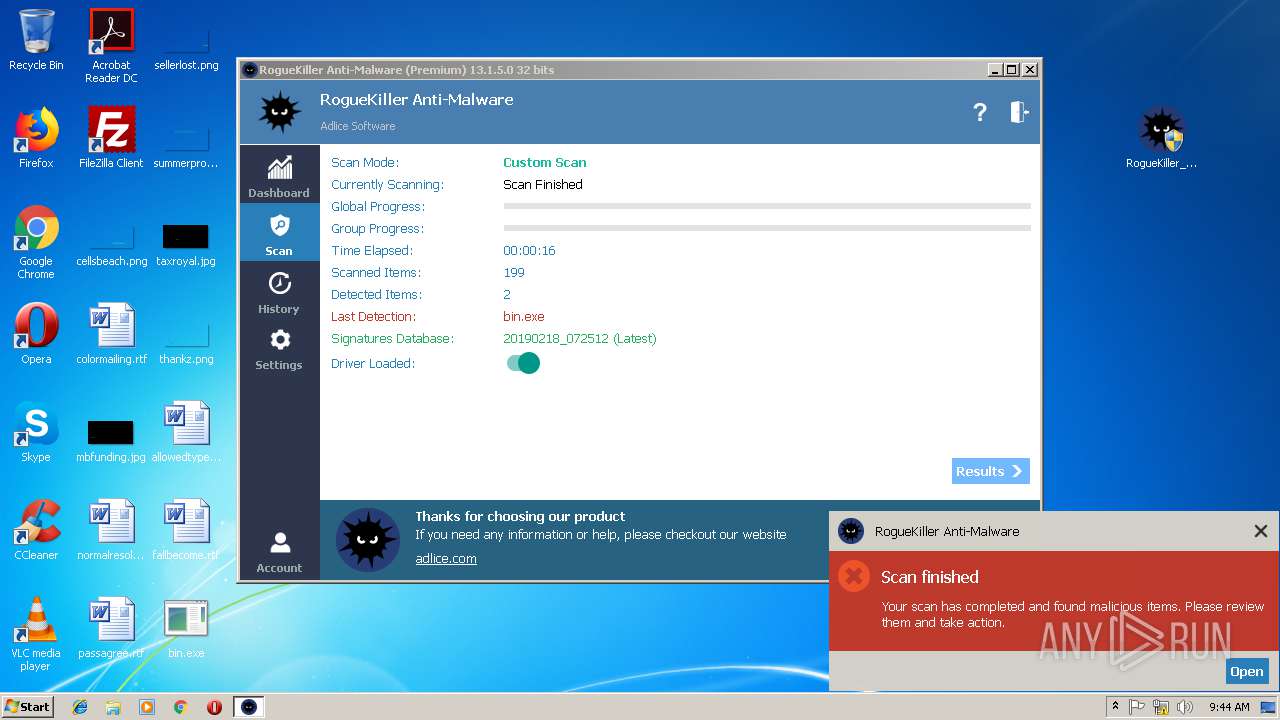
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | February 18, 2019, 09:39:45 |
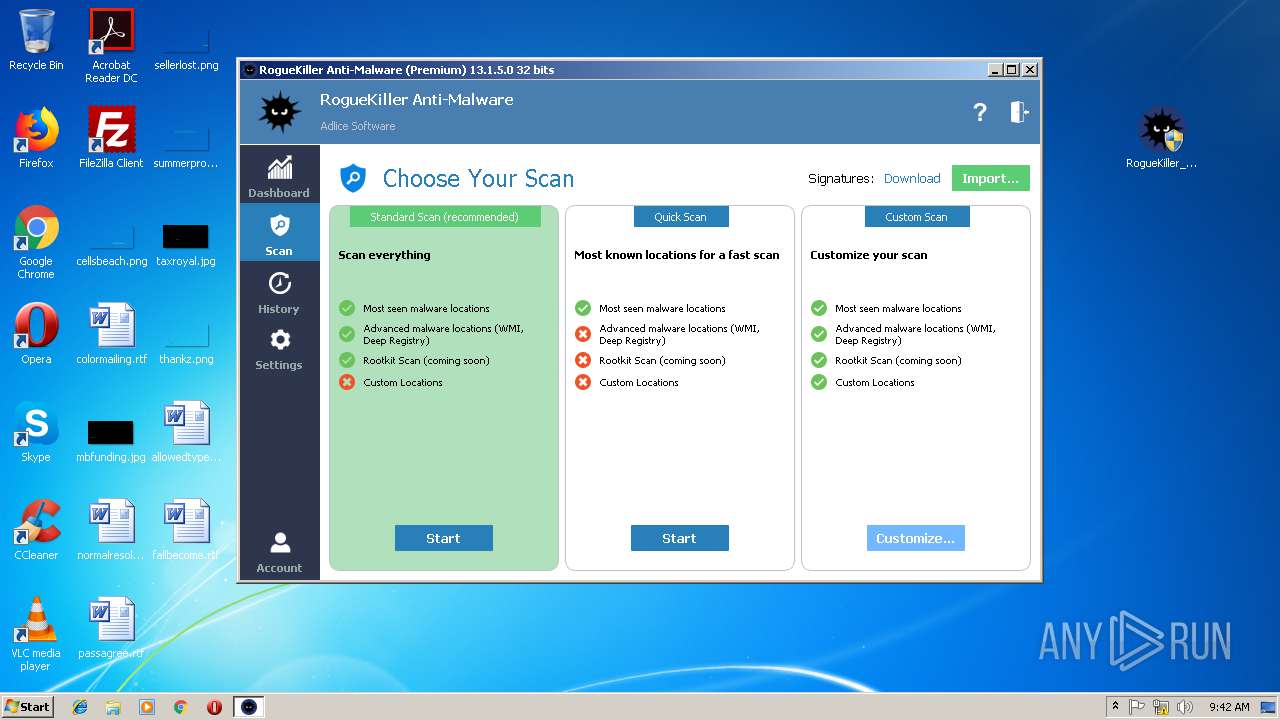
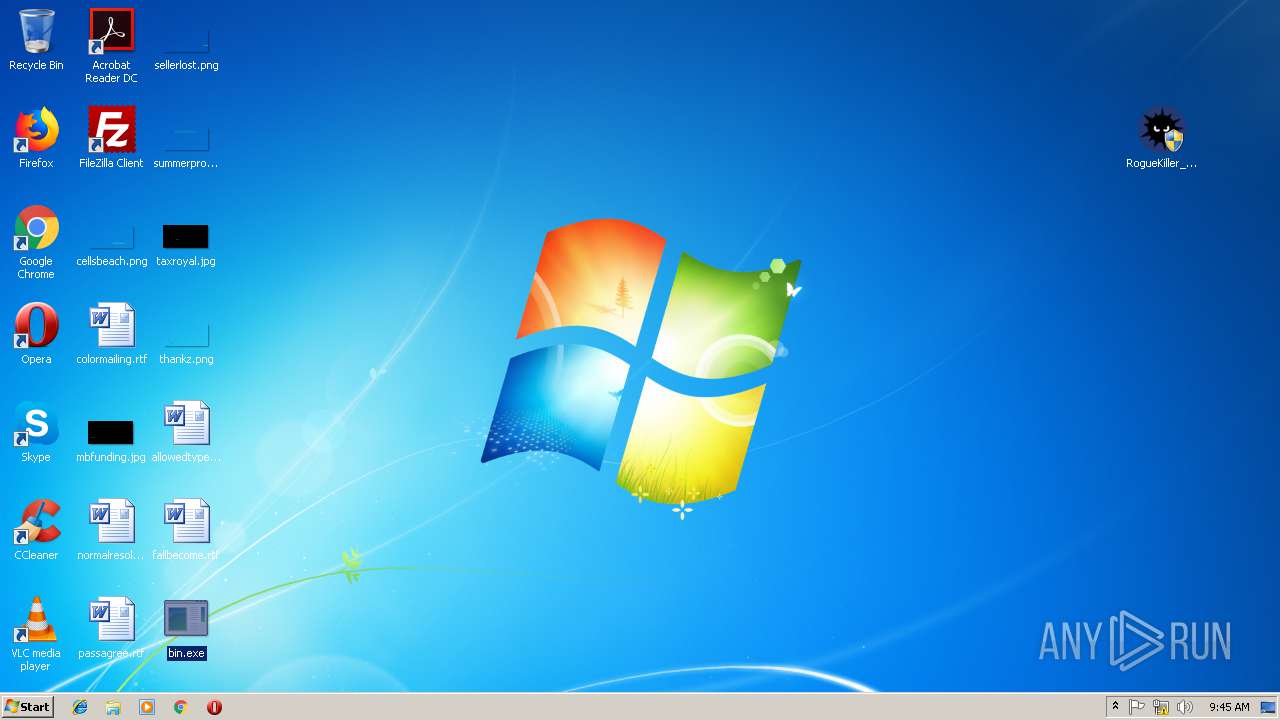
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2B1911E865BAC0D002A7A4DA7D1ADB4B |
| SHA1: | 9C123851550DC0925068D162EE9D7B711CD434CD |
| SHA256: | 554E948B18C0B447C8A685F03F301D67BD3B8CD6B63C1293774B8DD7E1457E2E |
| SSDEEP: | 6144:HaWHTjwCE3oPavN9H/syPMT6lEL3RnUGEEFSpytE1ml0jS6KA2rG617w7X0DMaO5:6IjHELKD8wJJq |
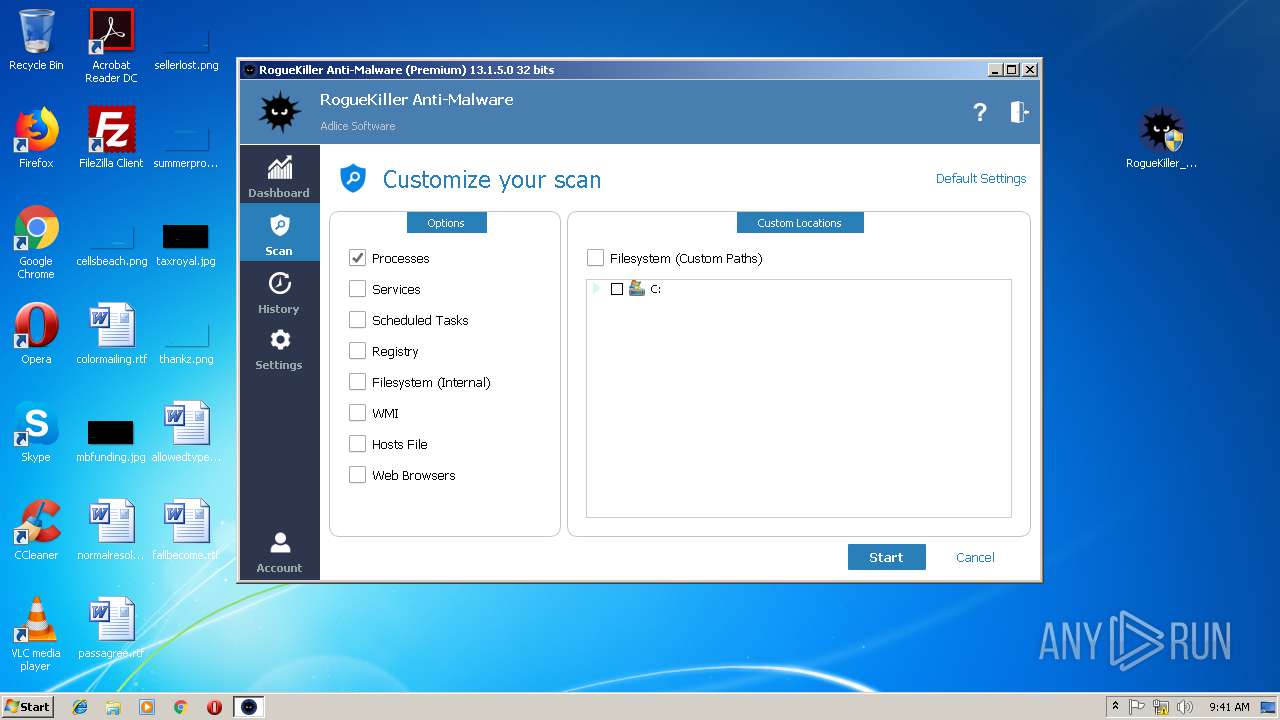
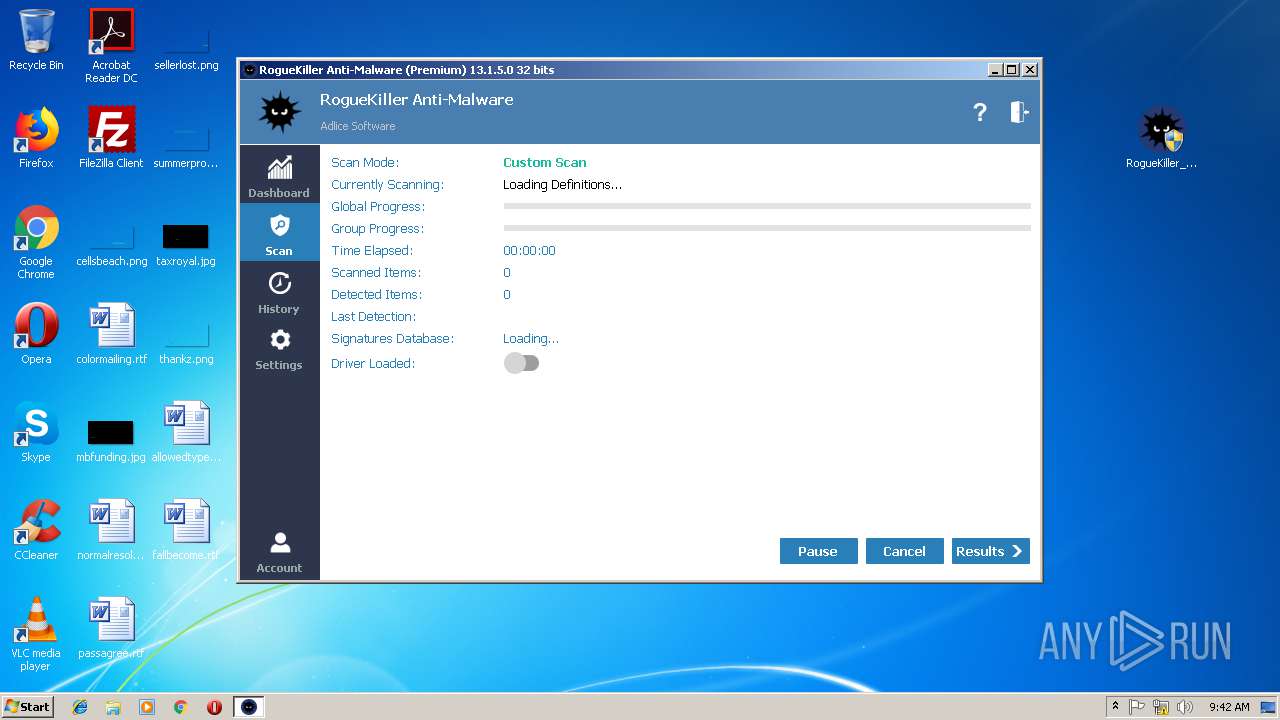
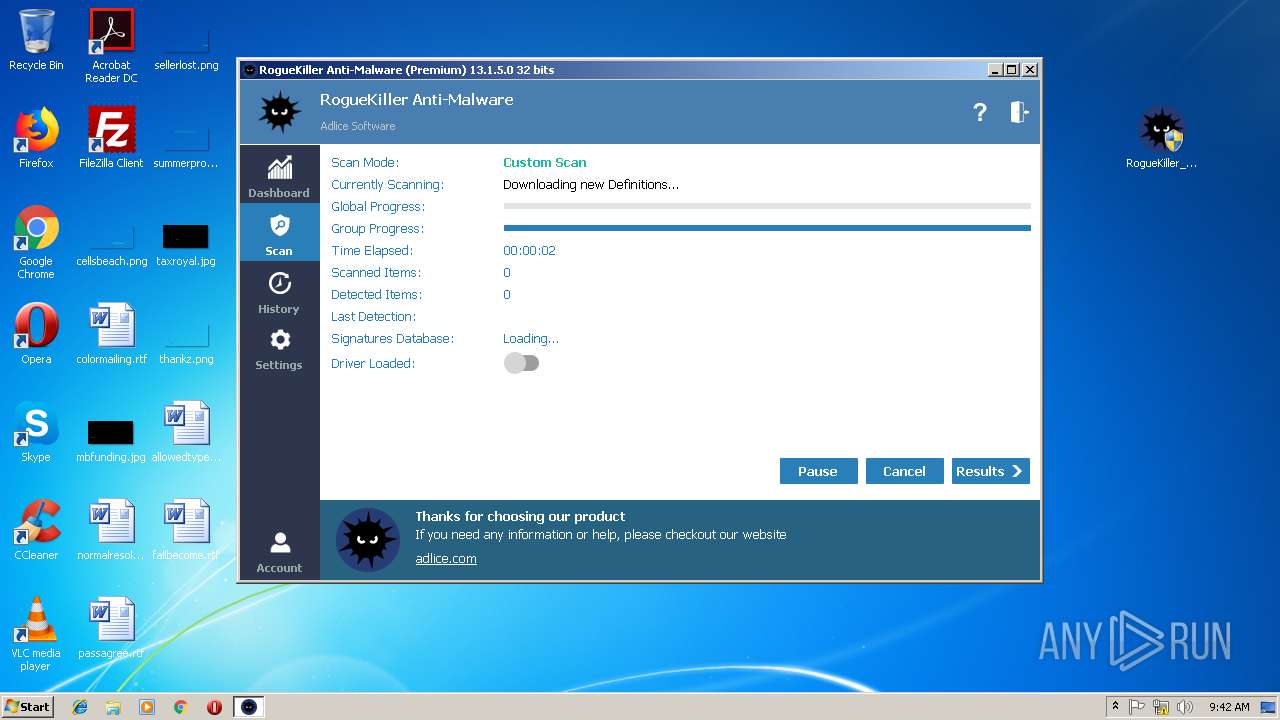
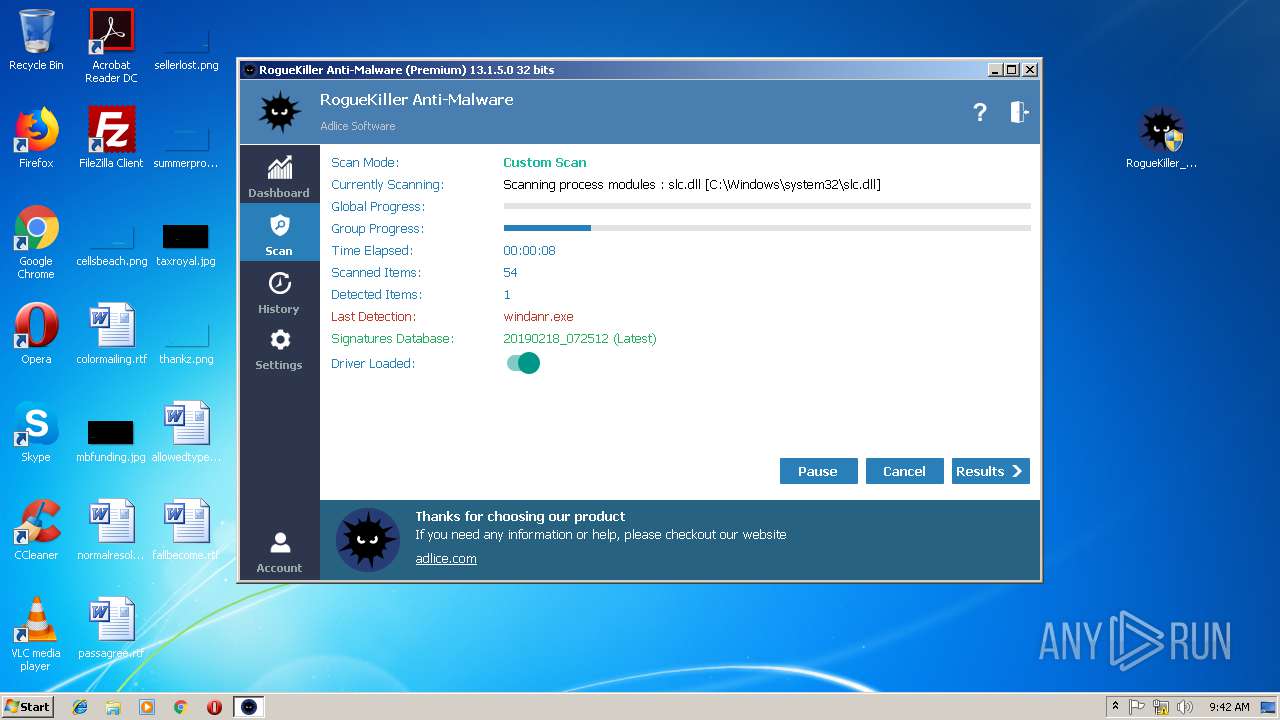
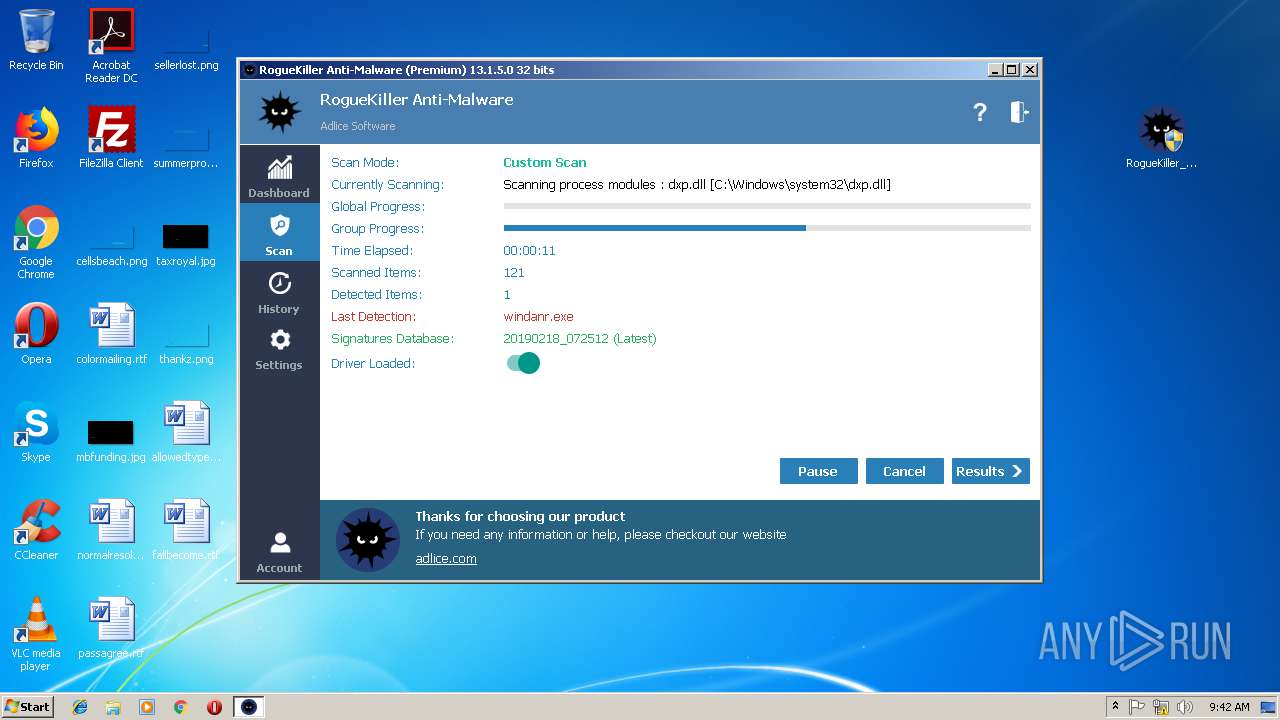
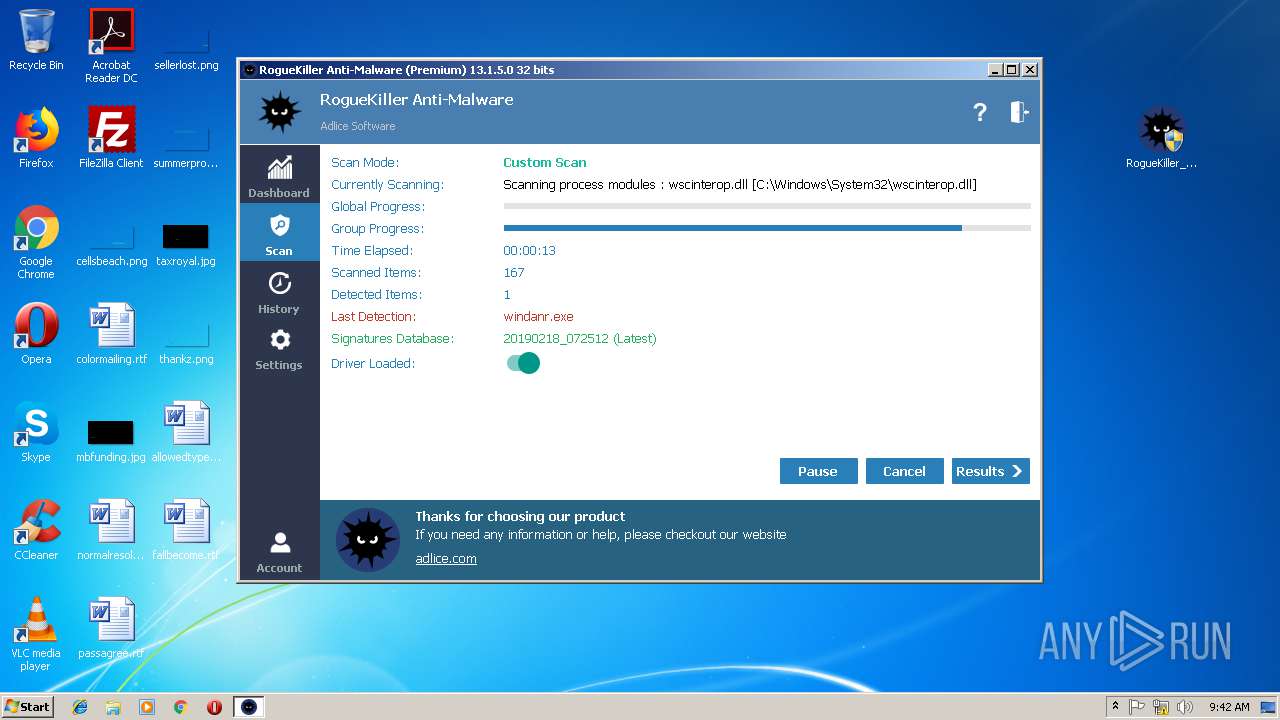
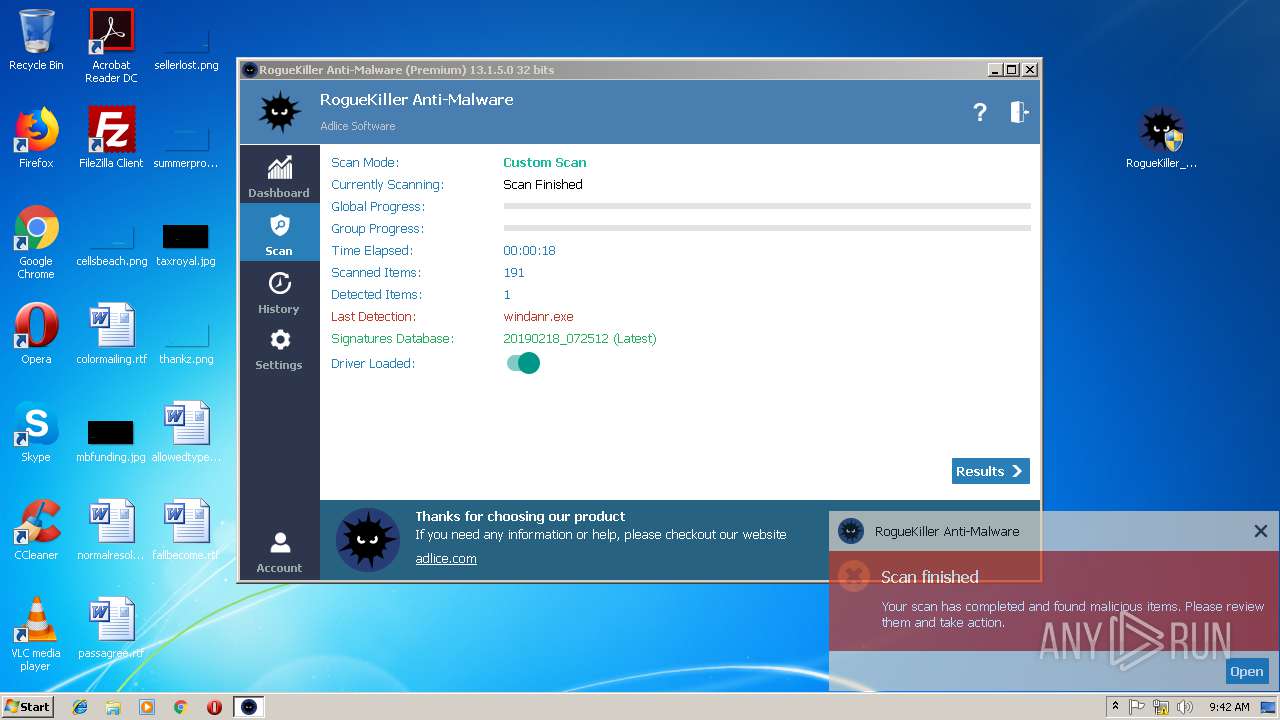
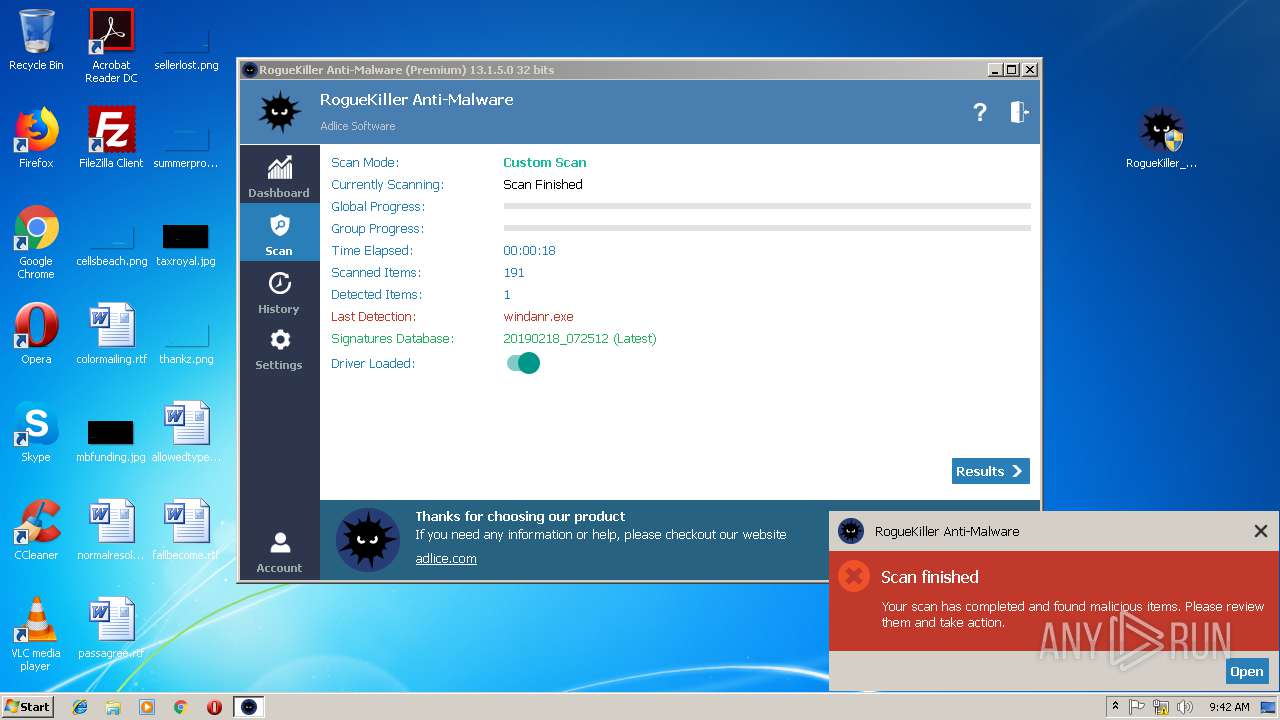
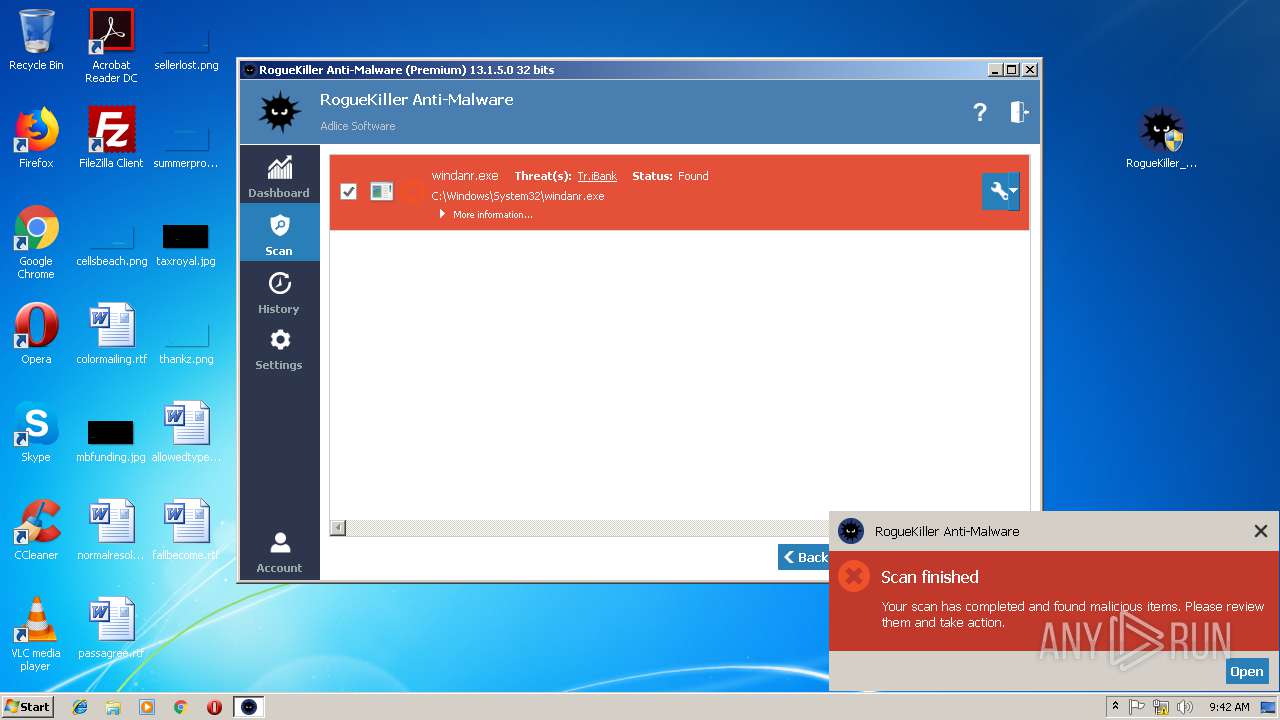
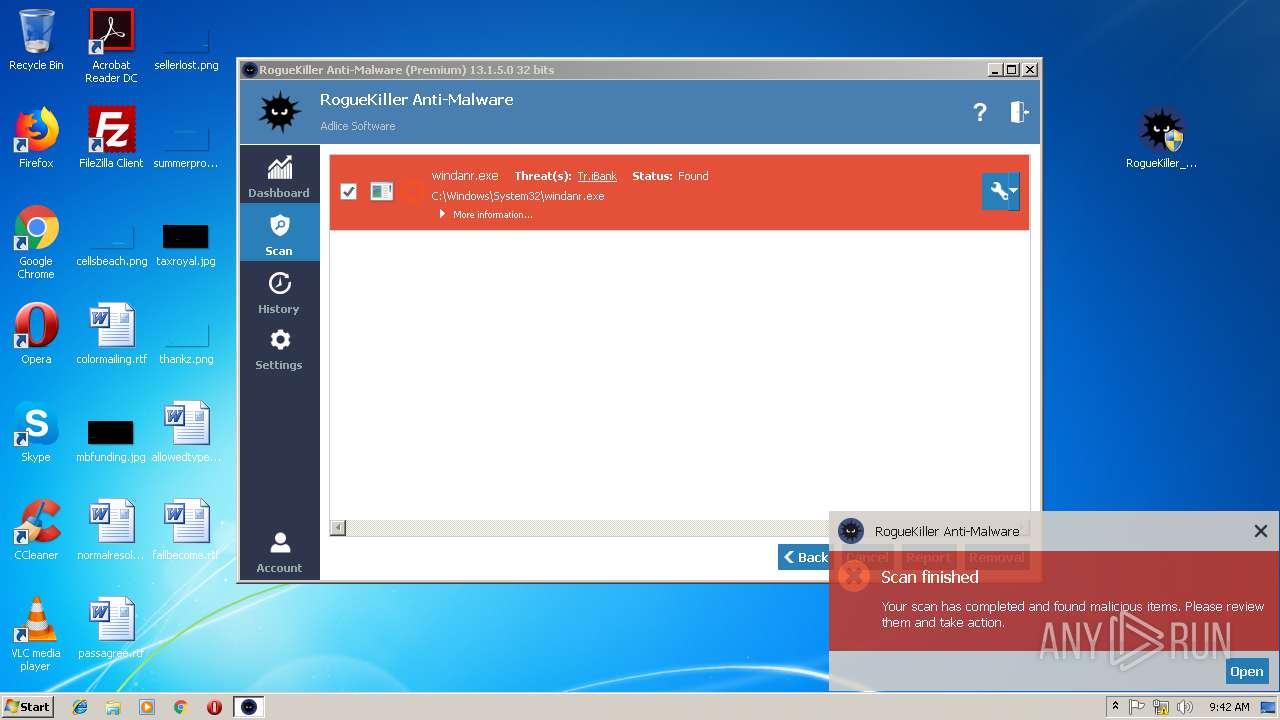
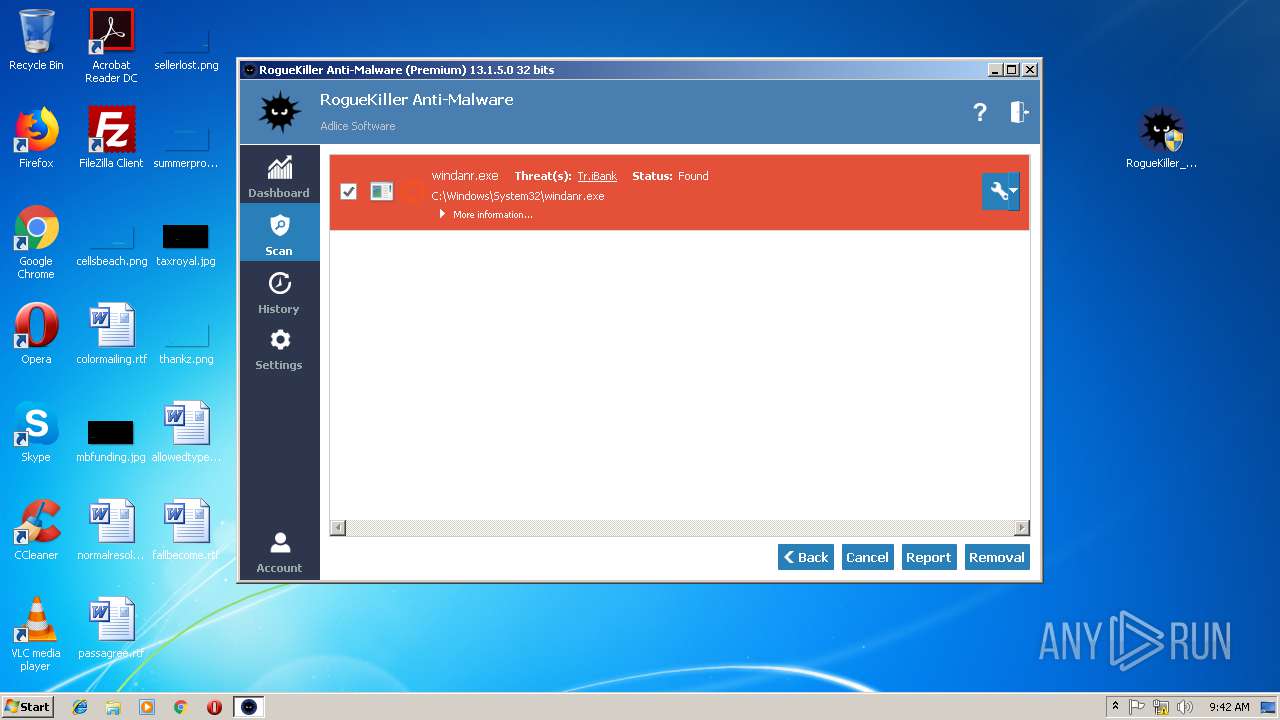
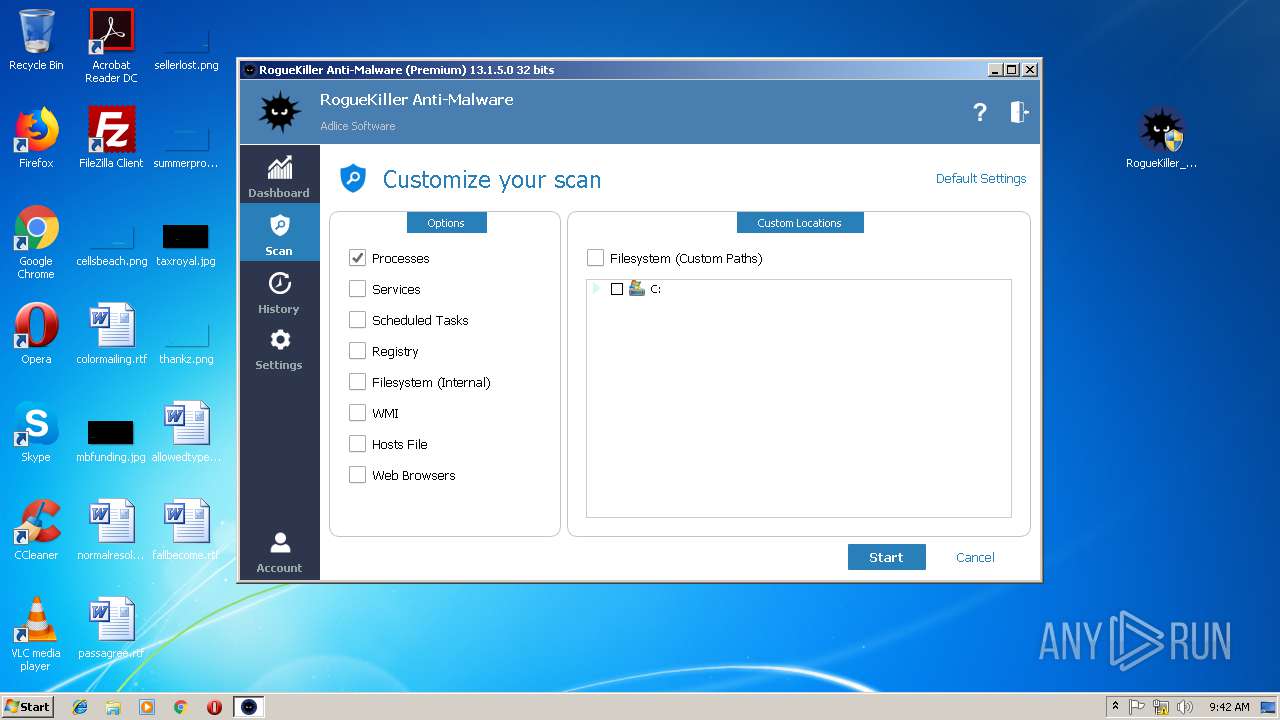
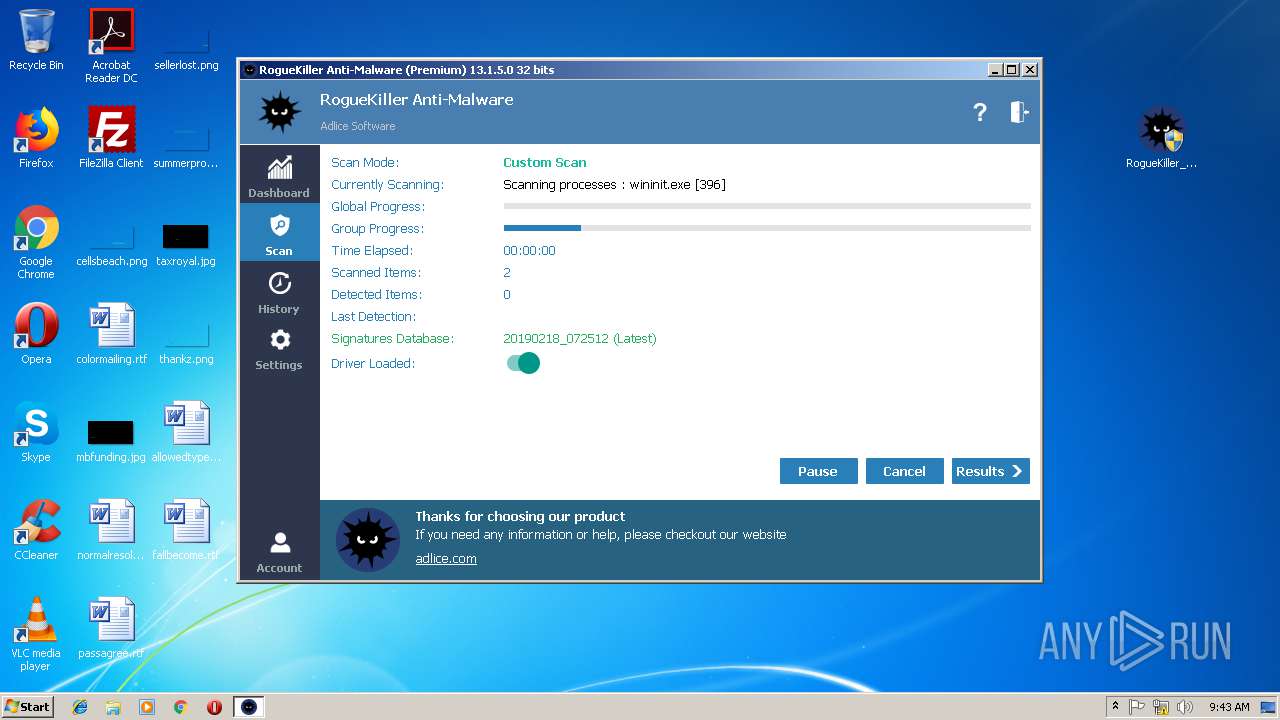
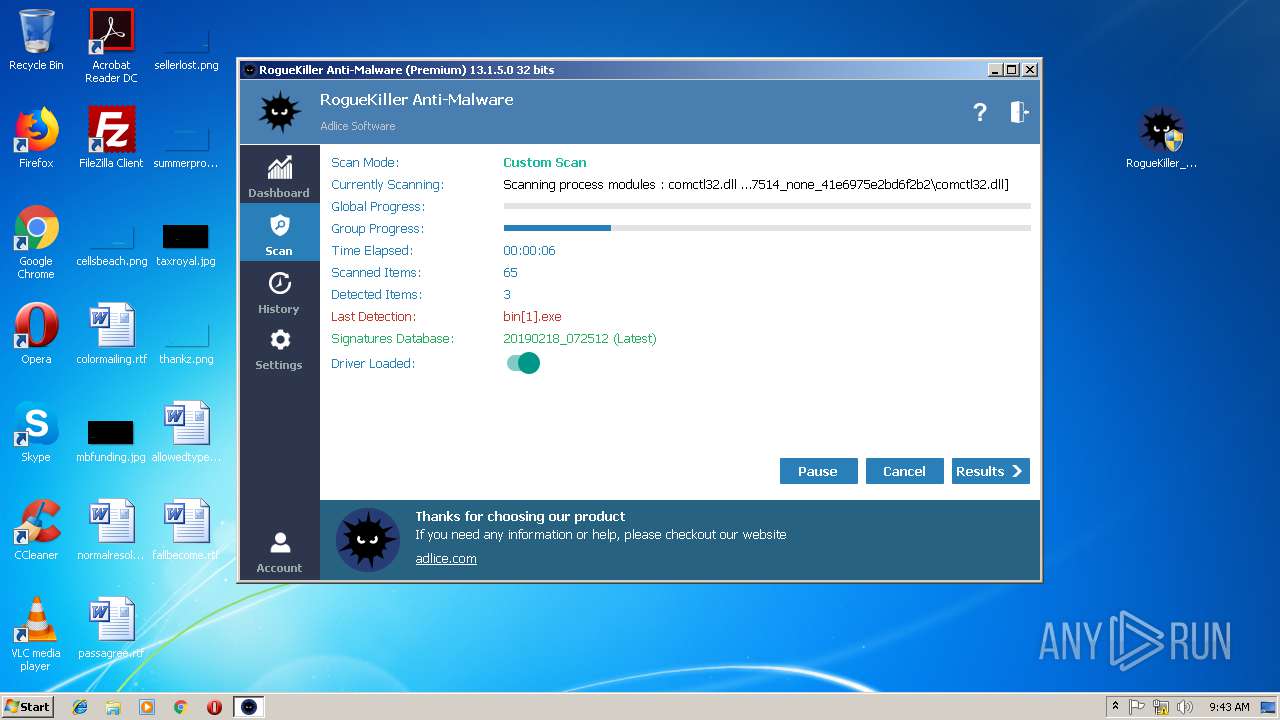
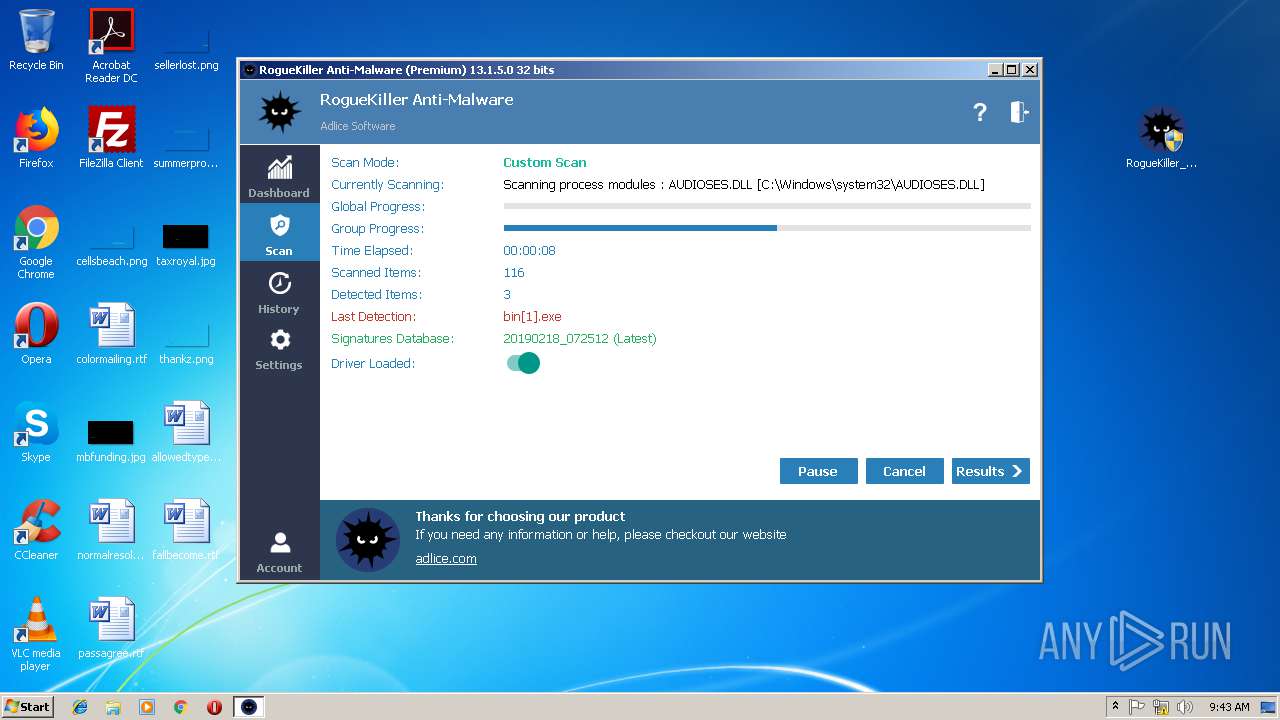
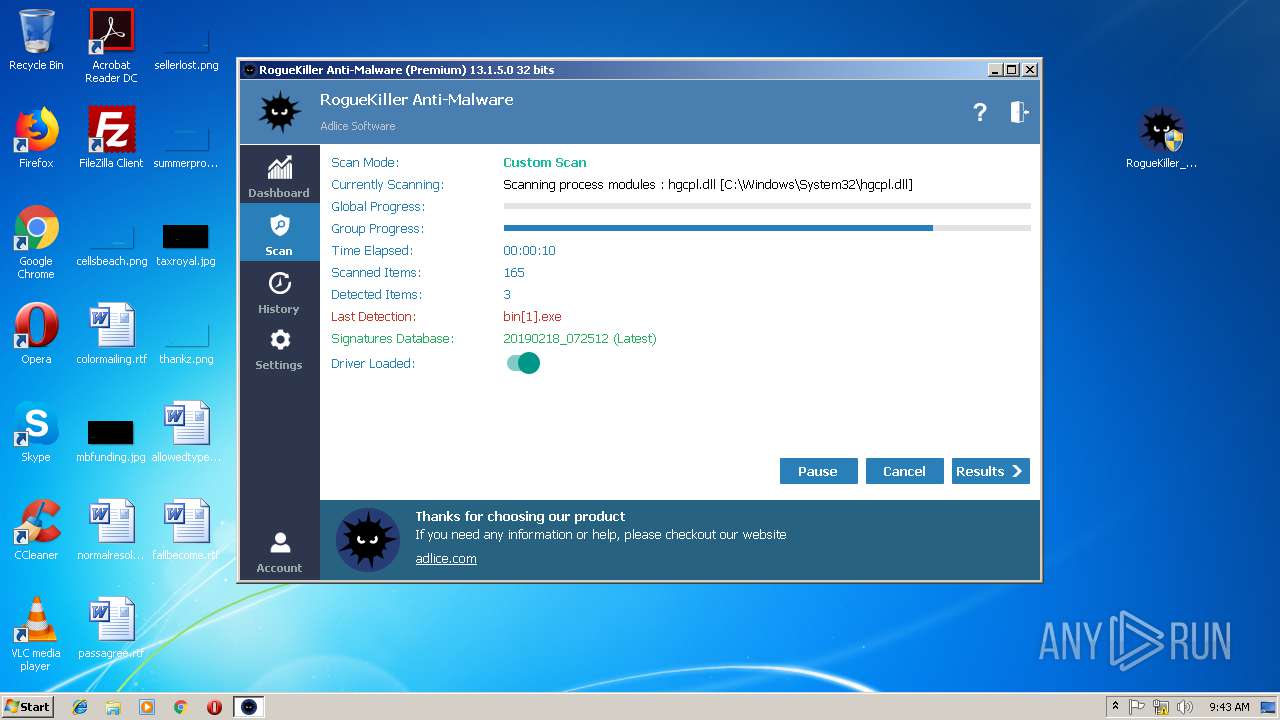
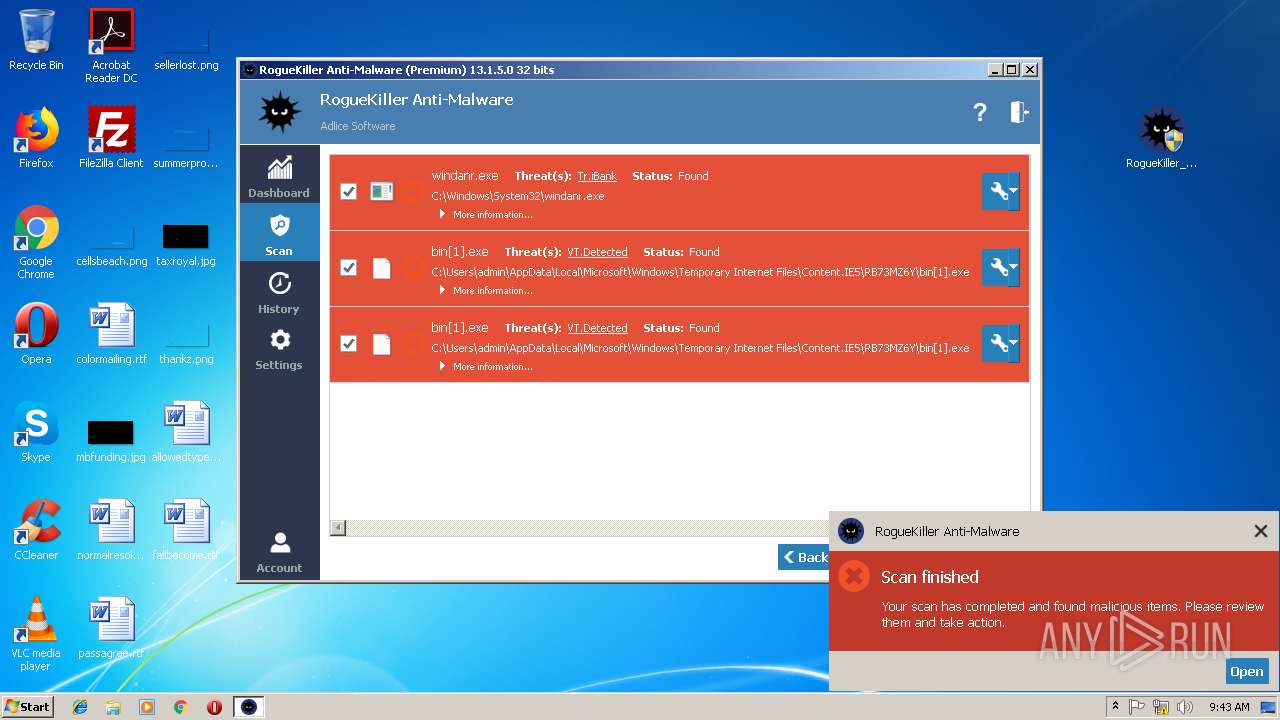
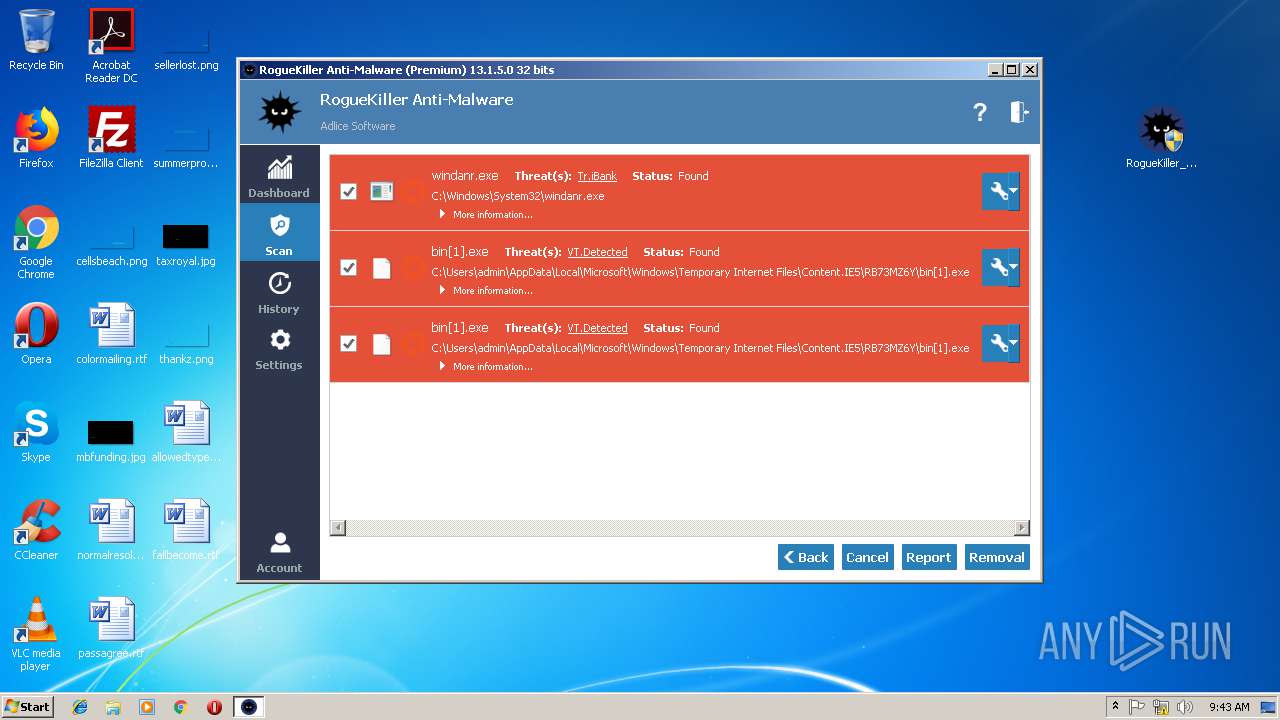
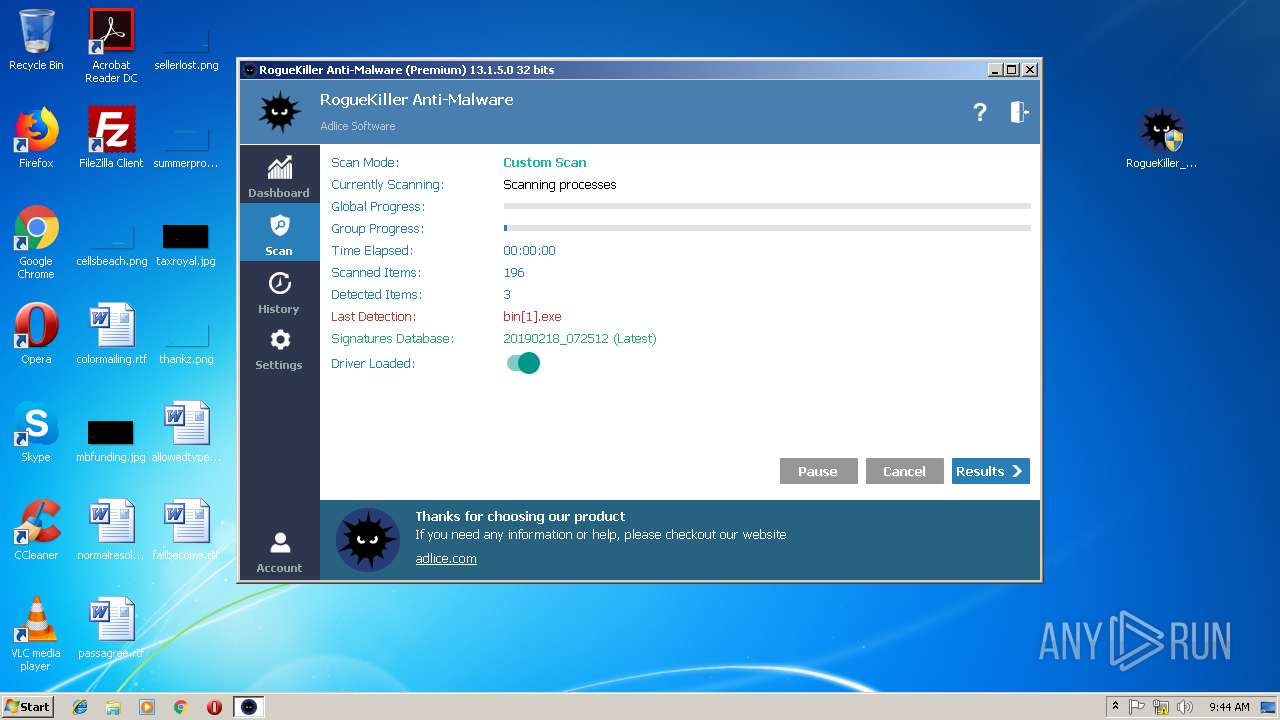
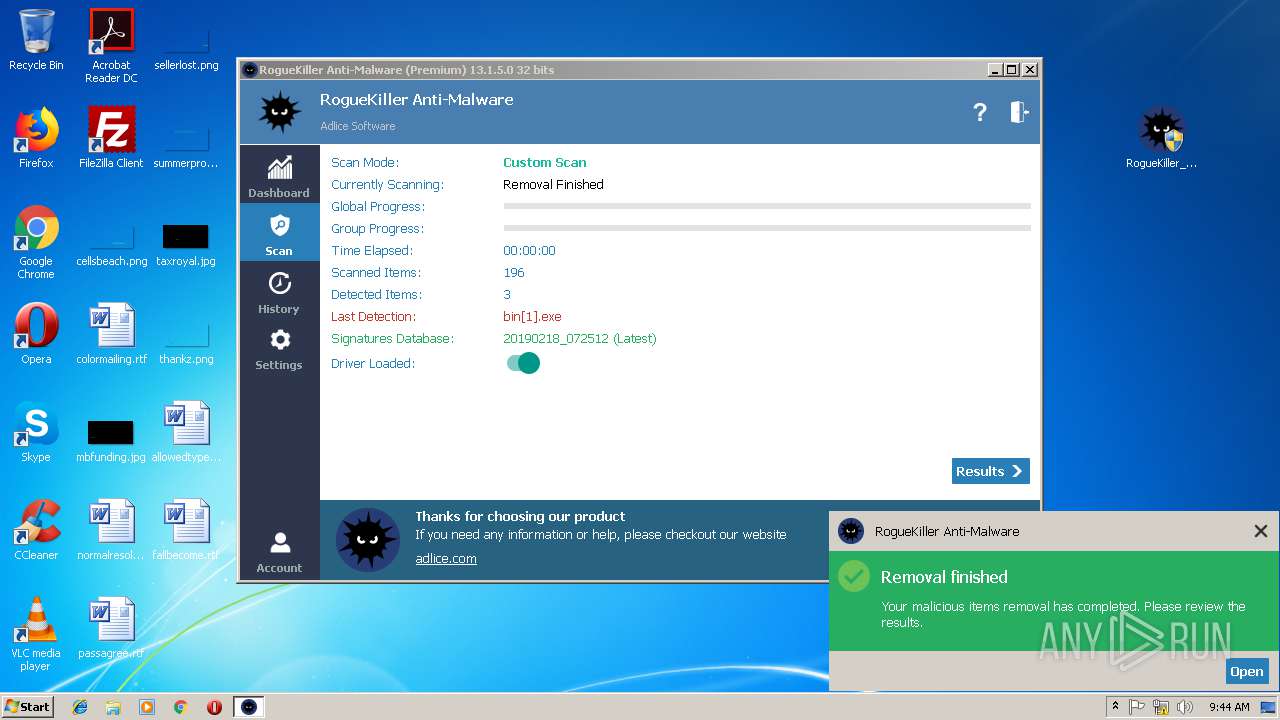
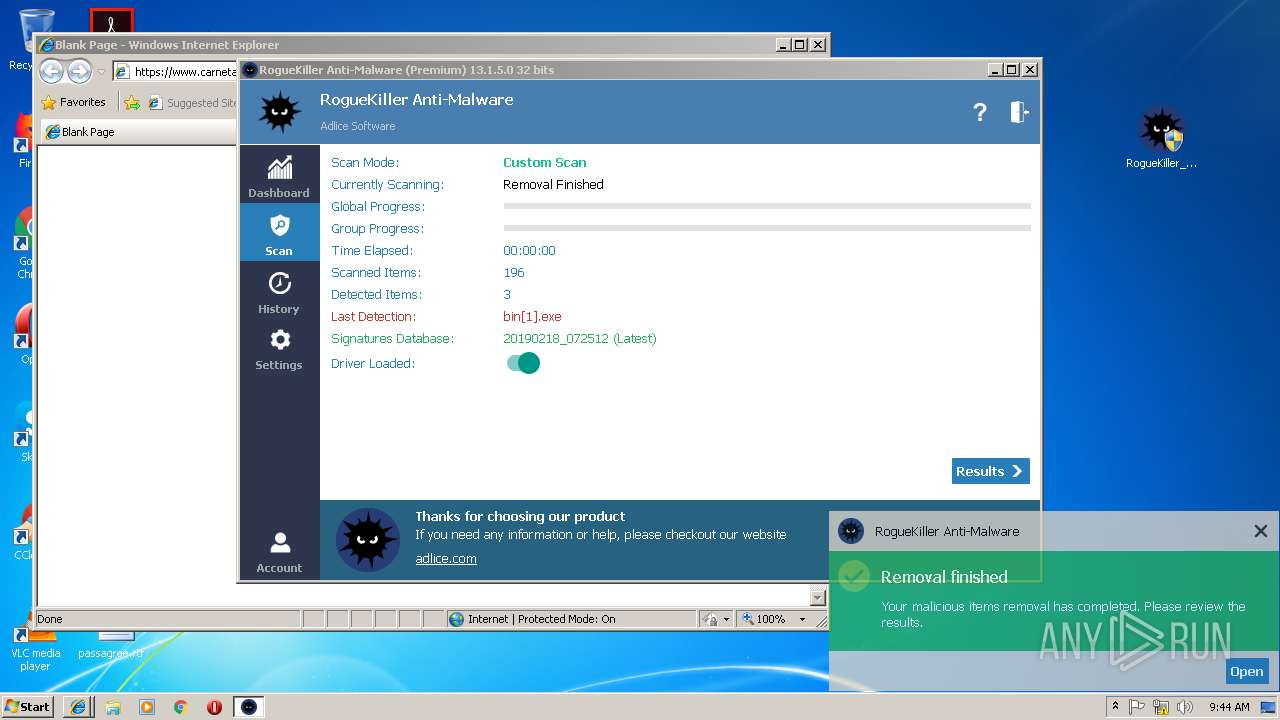
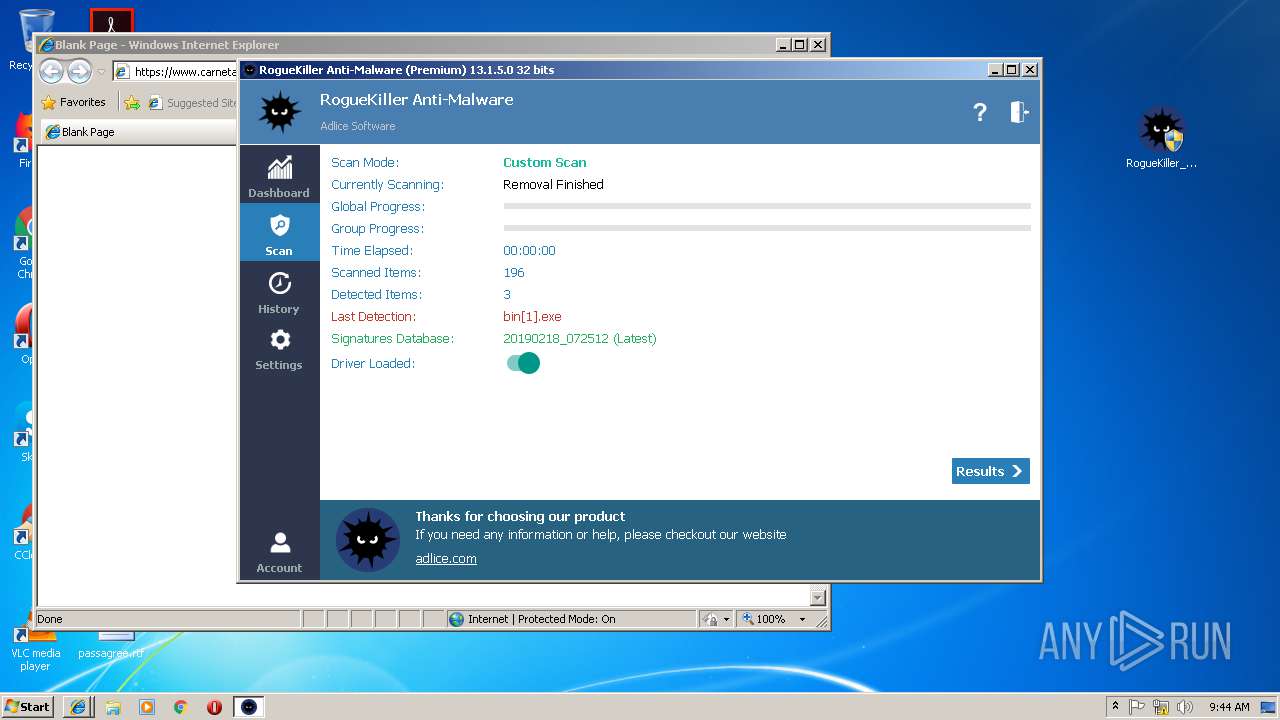
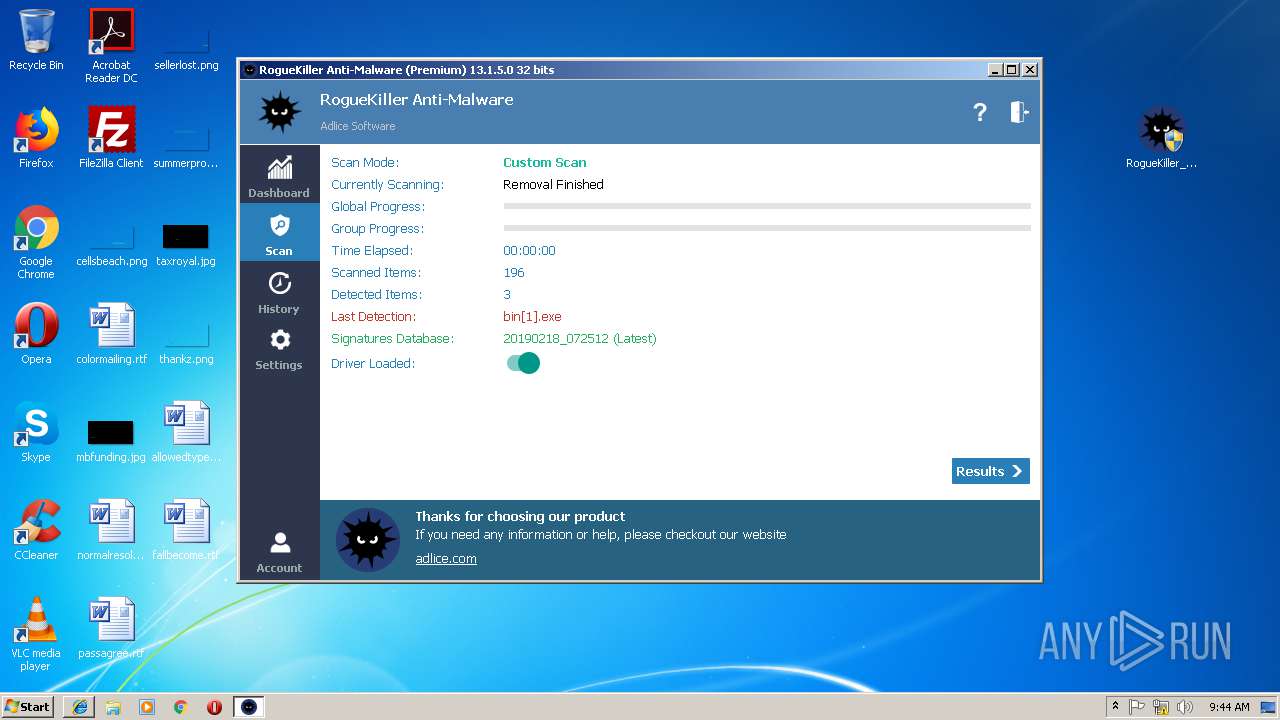
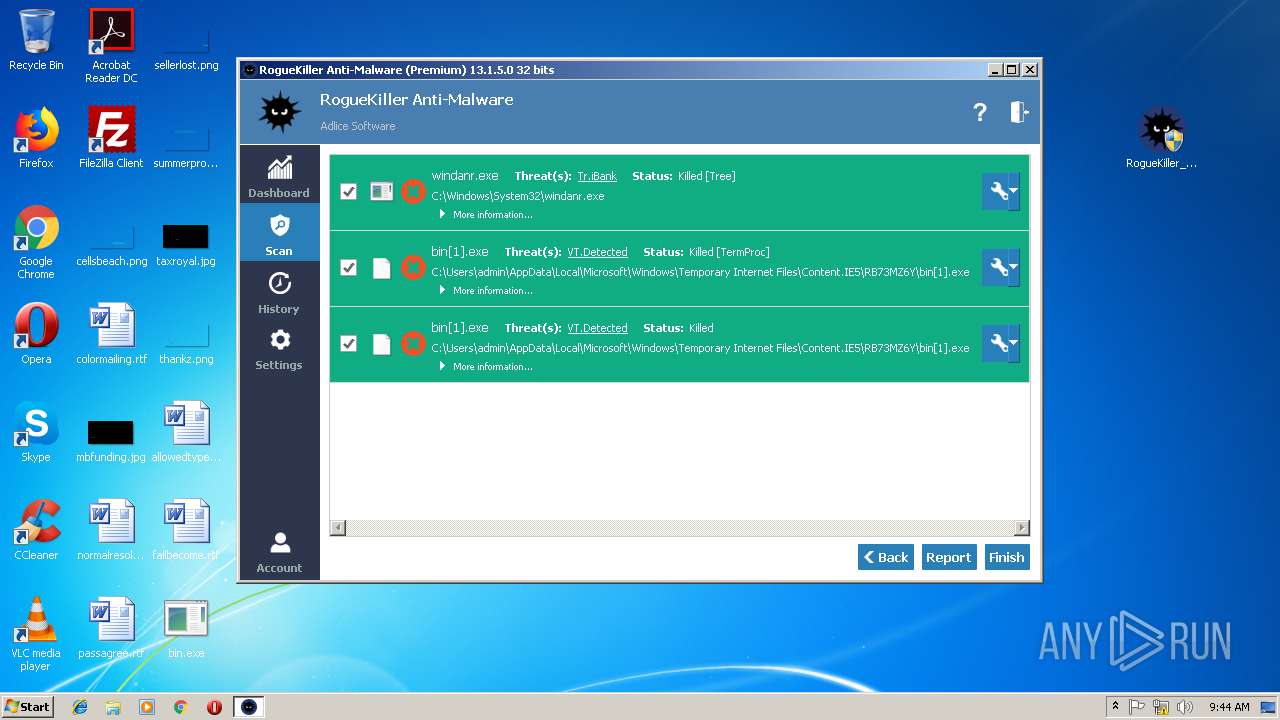
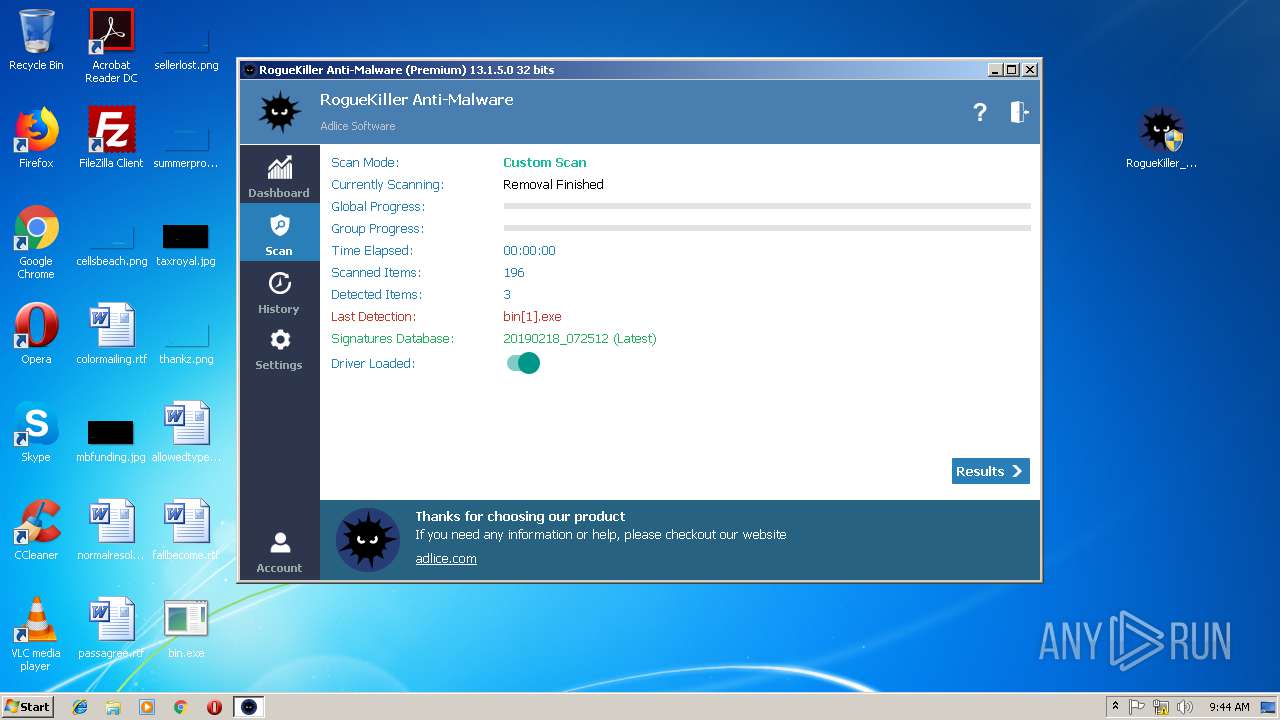
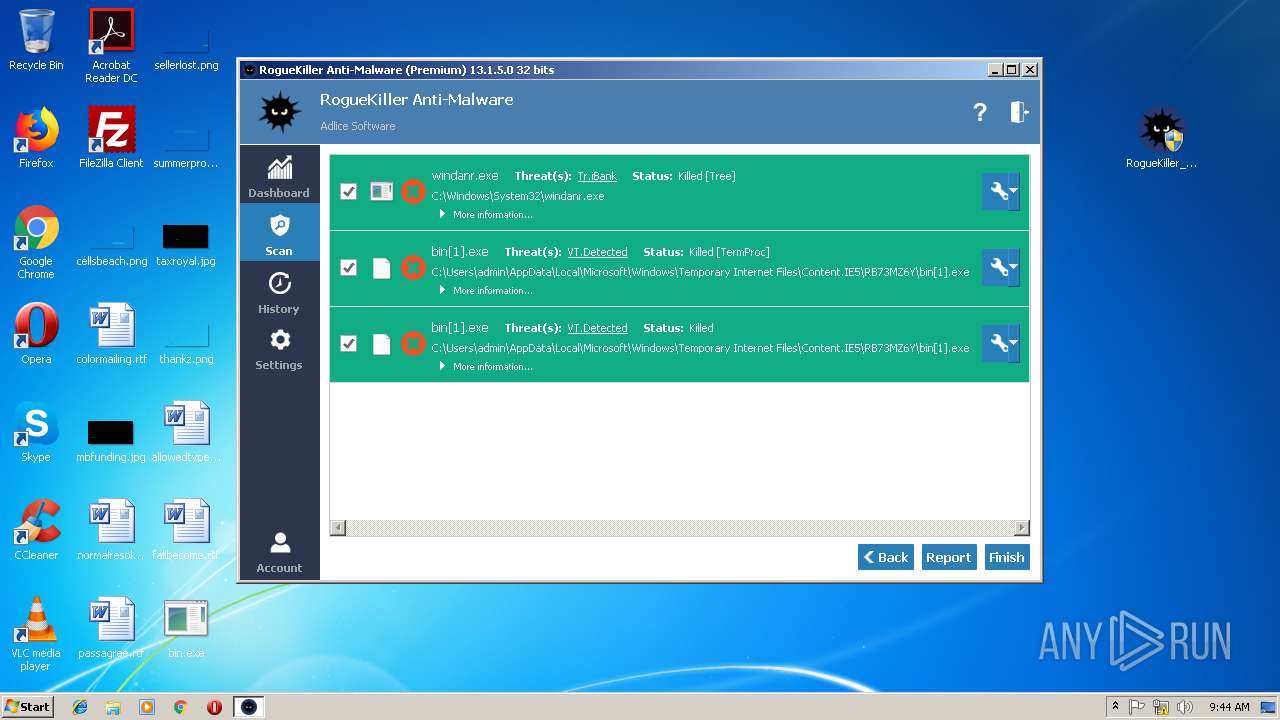
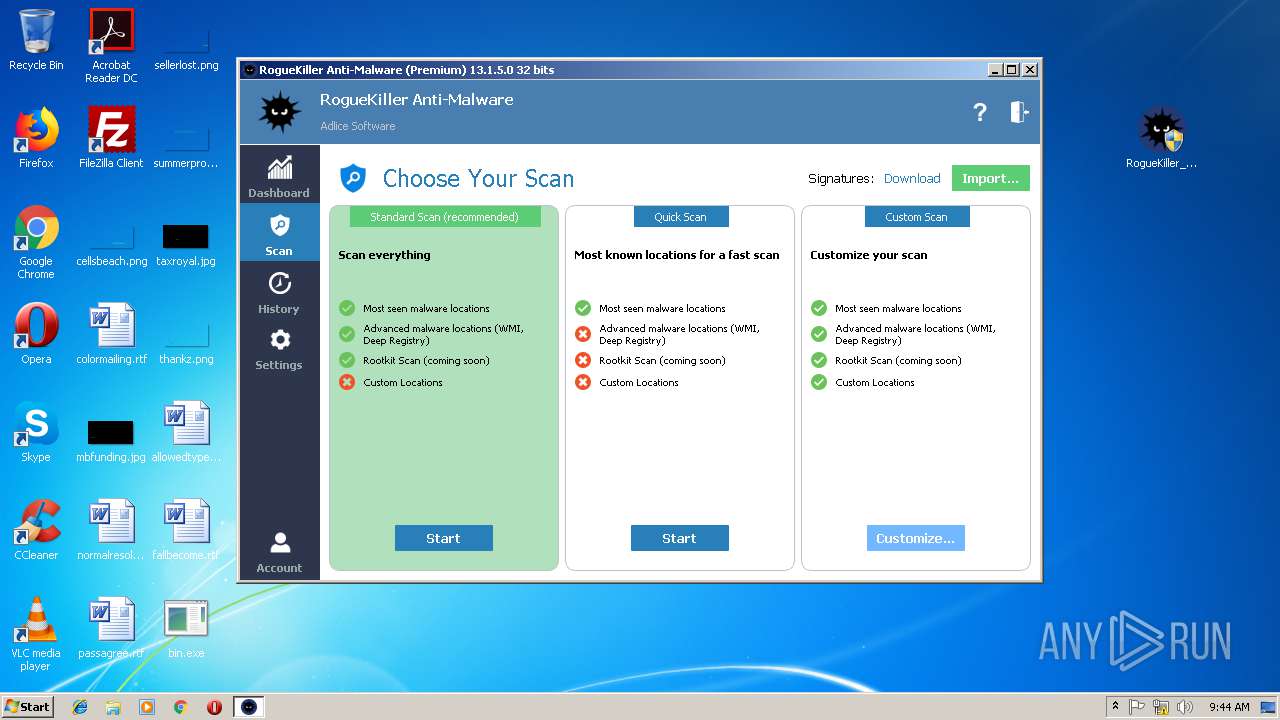
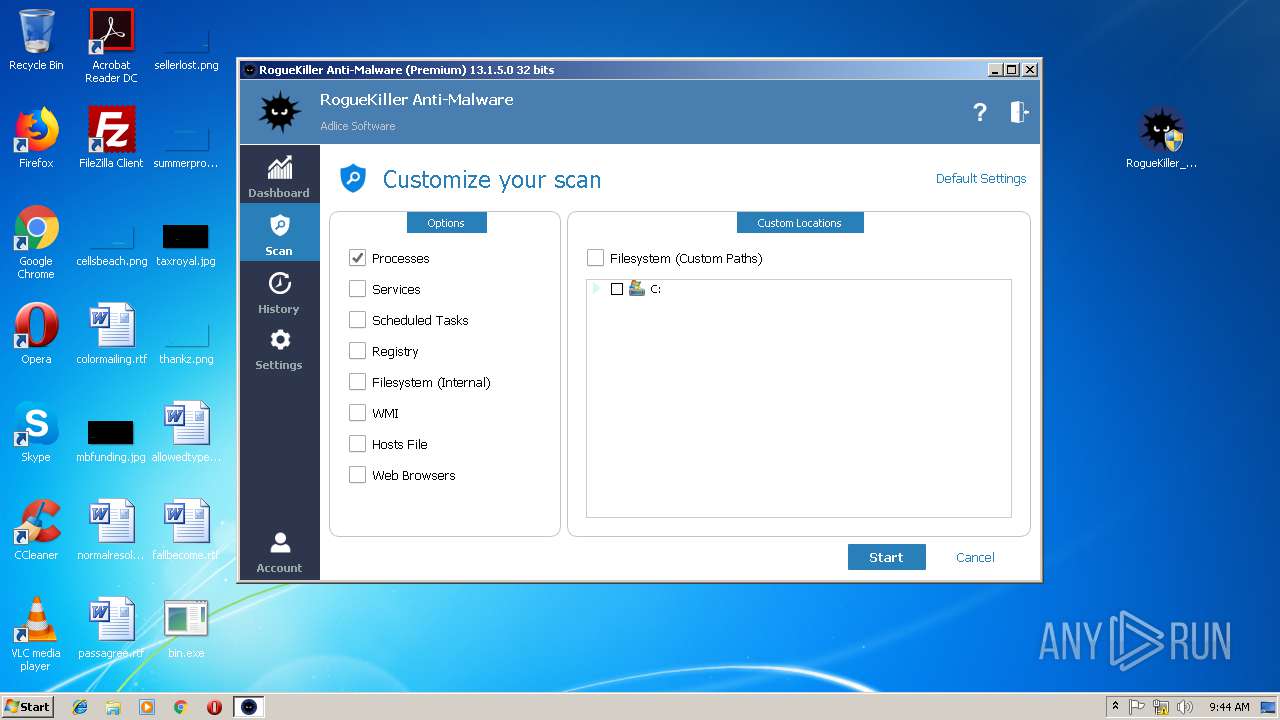
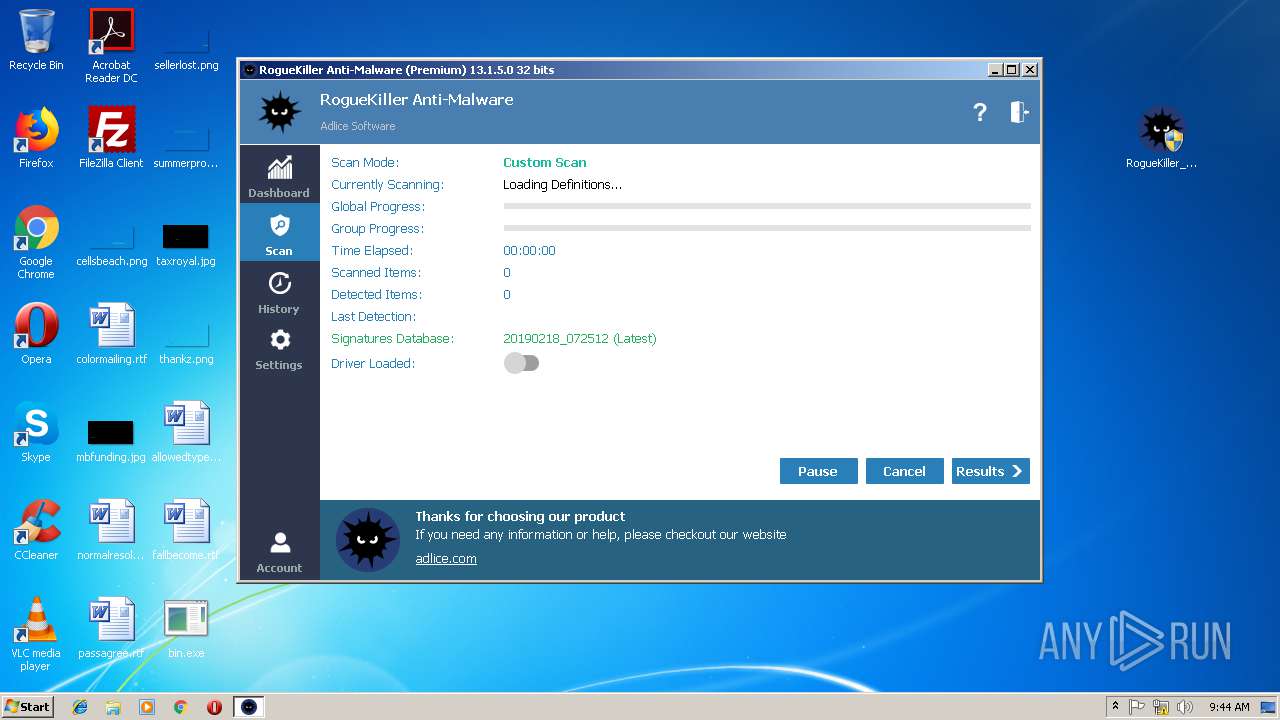
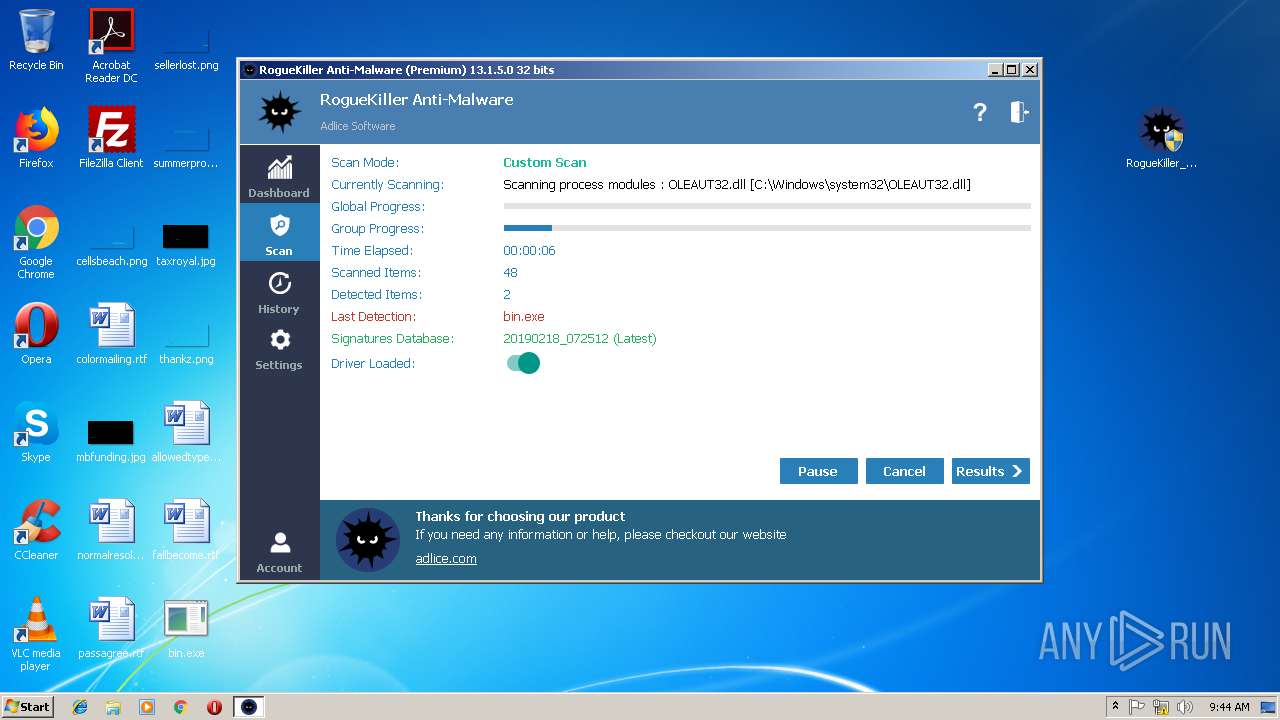
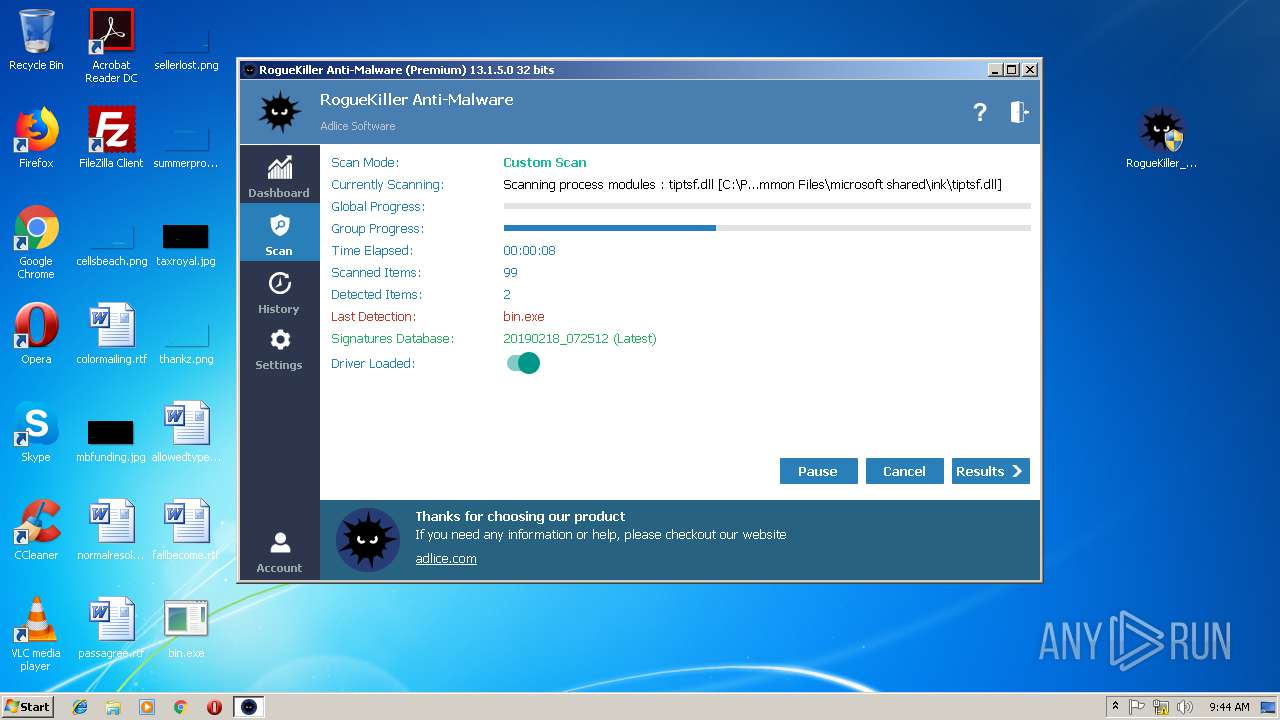
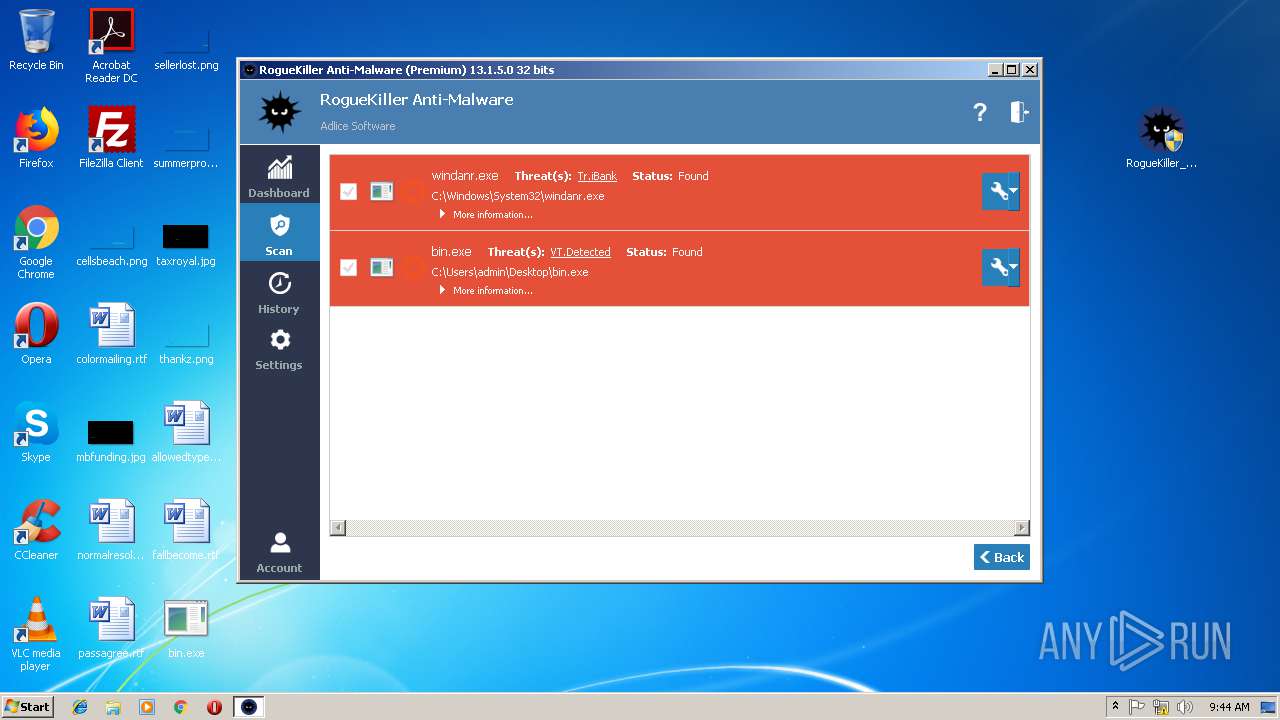
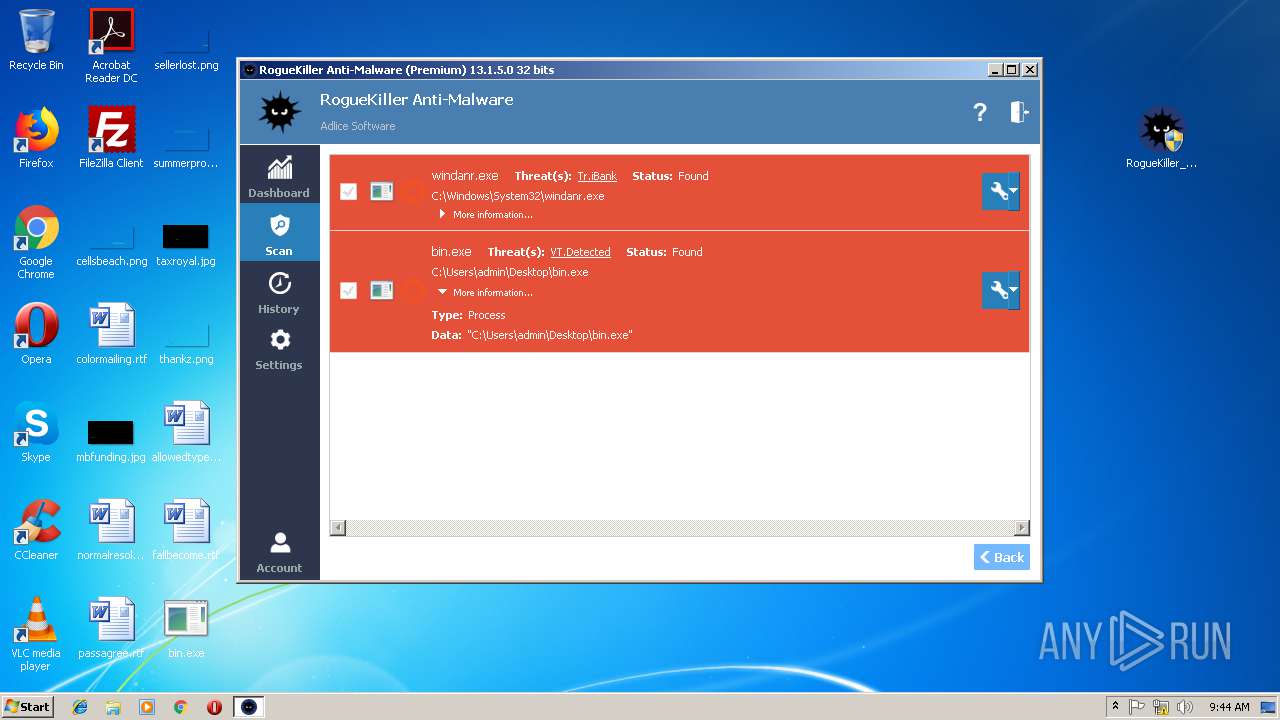
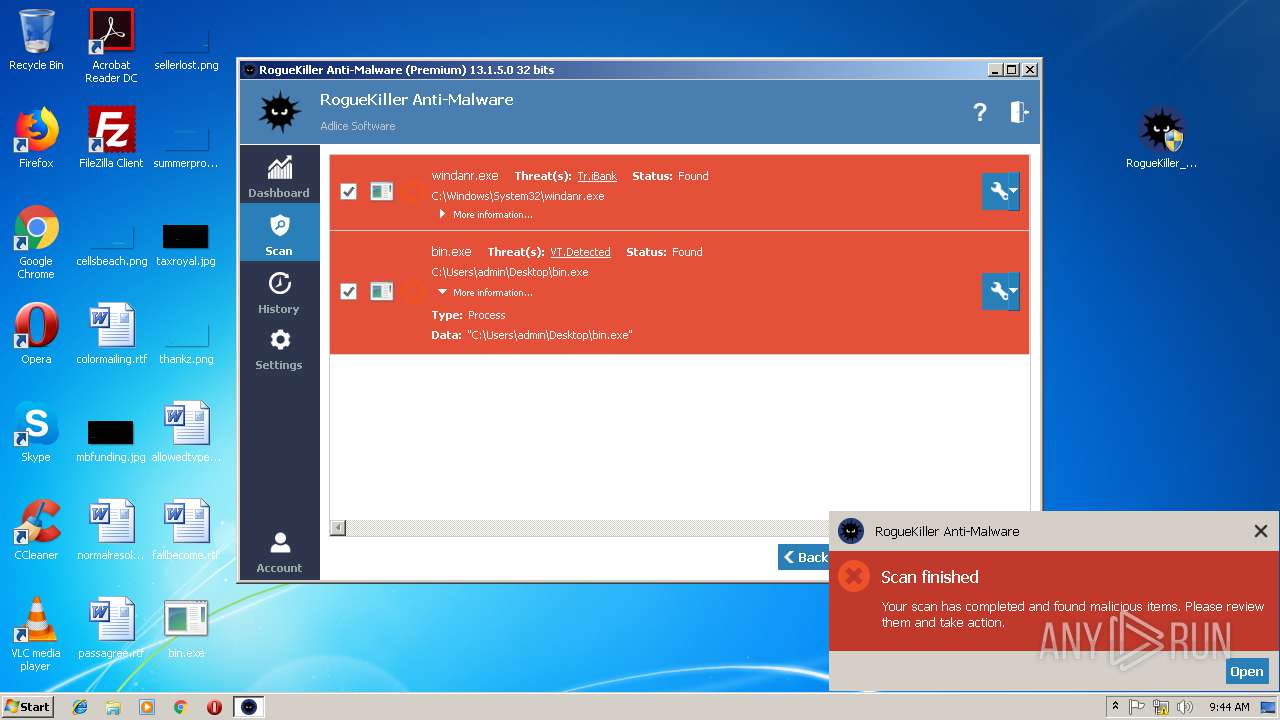
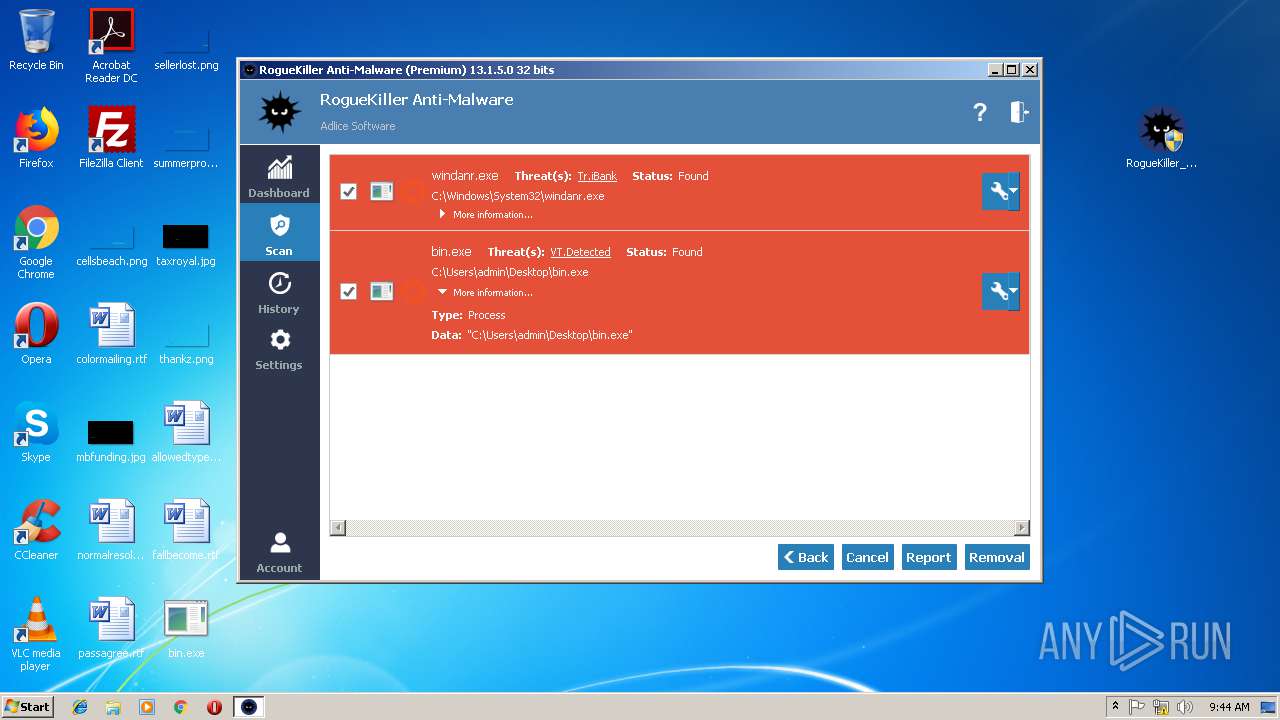
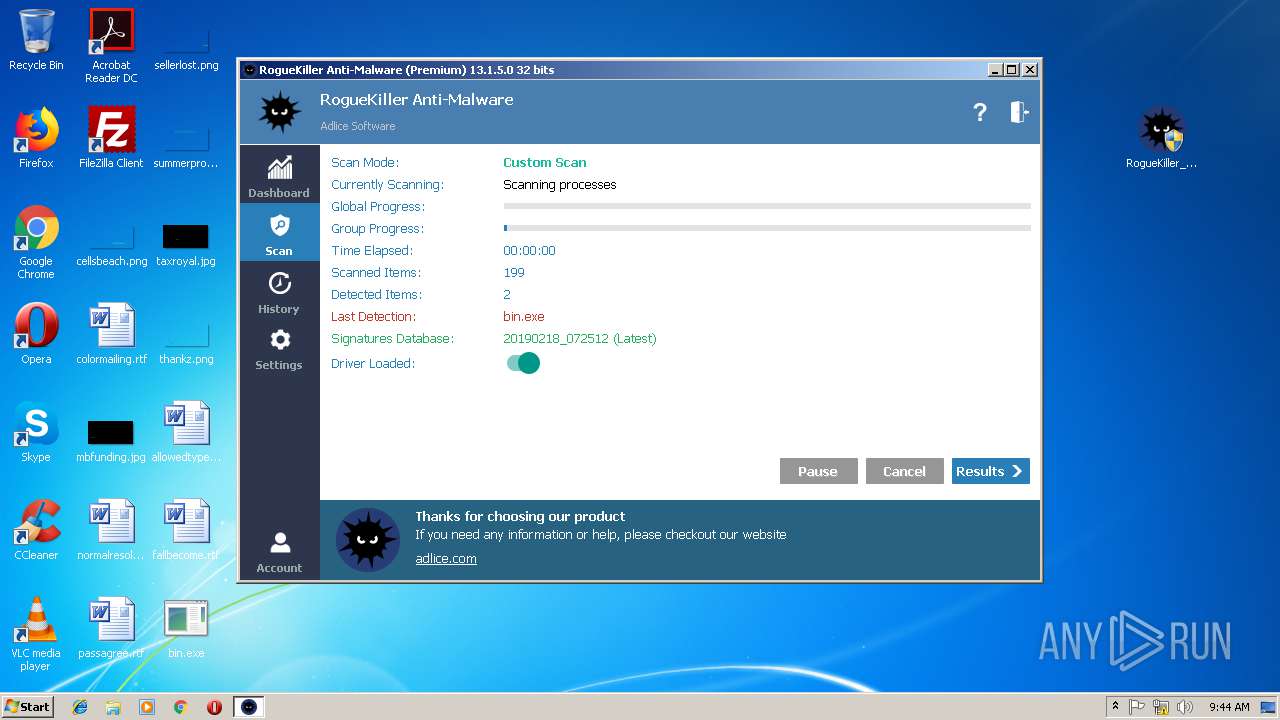
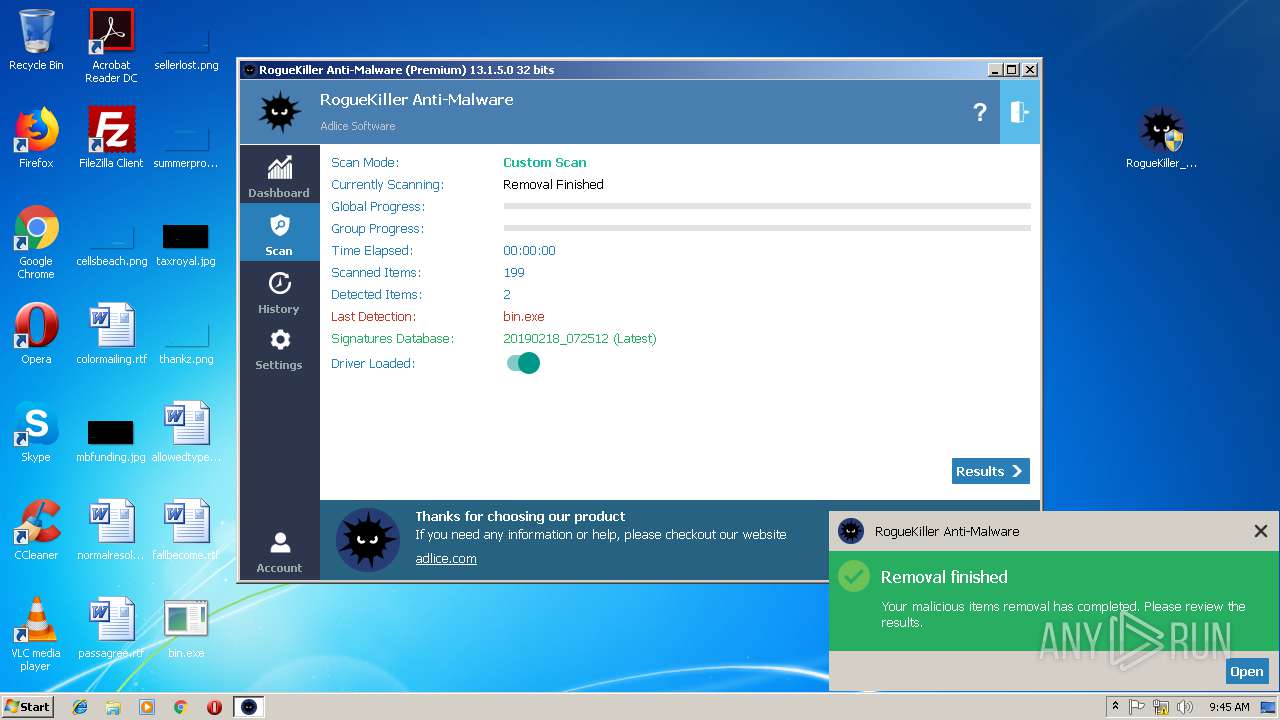
MALICIOUS
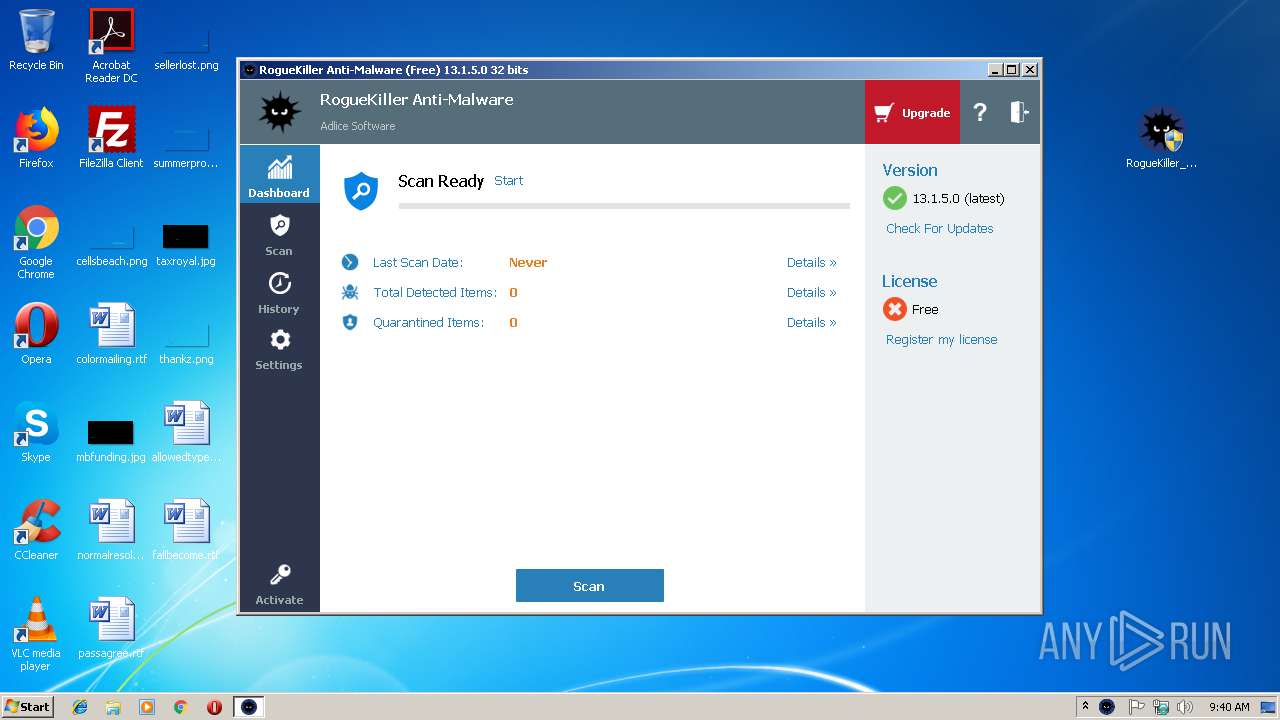
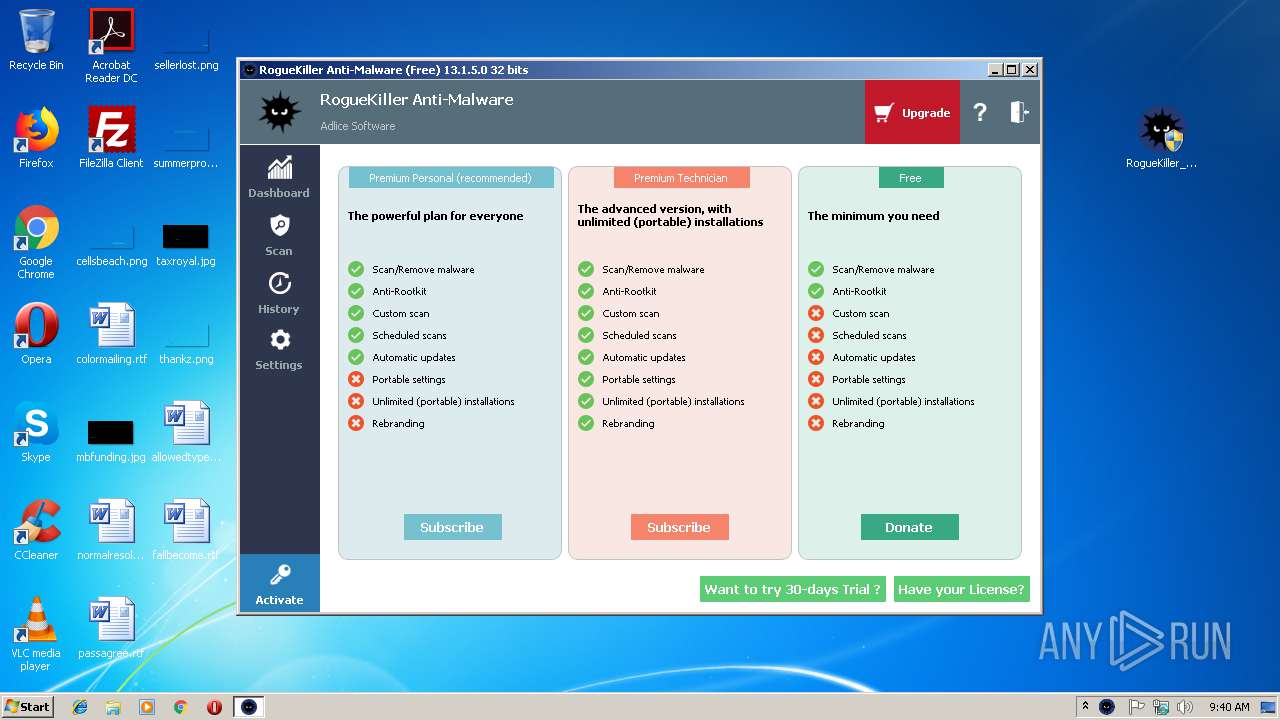
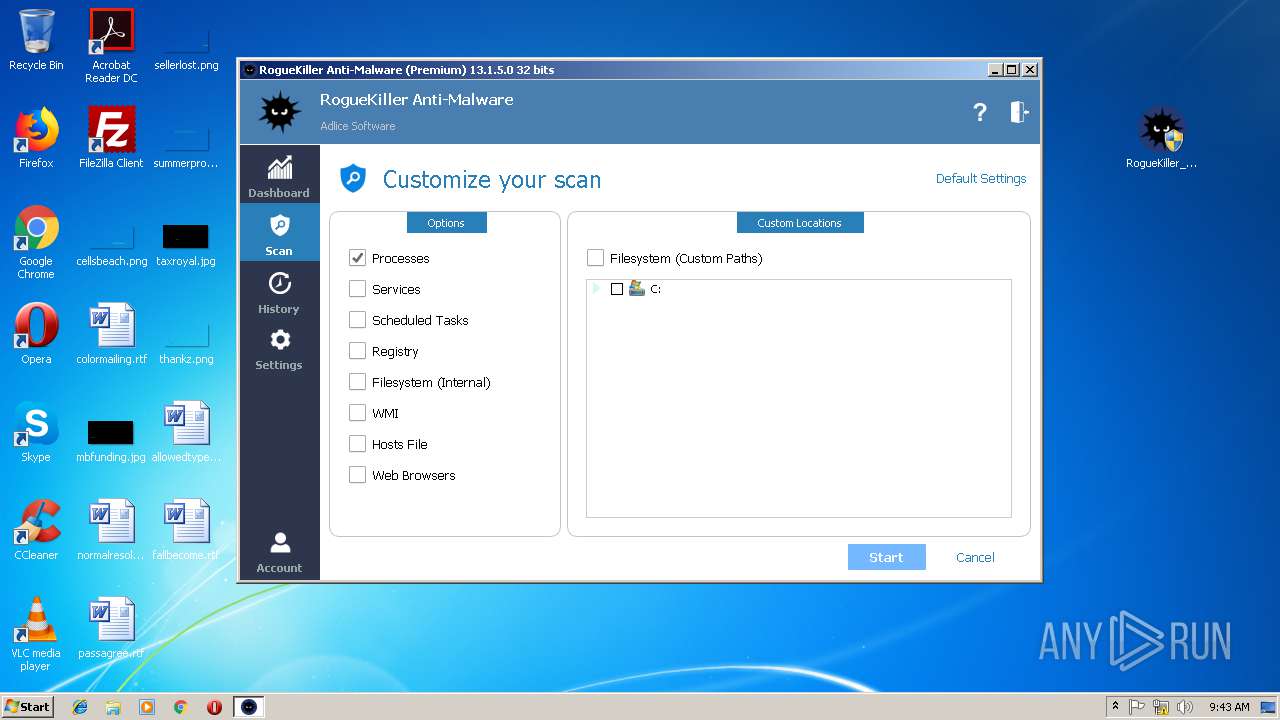
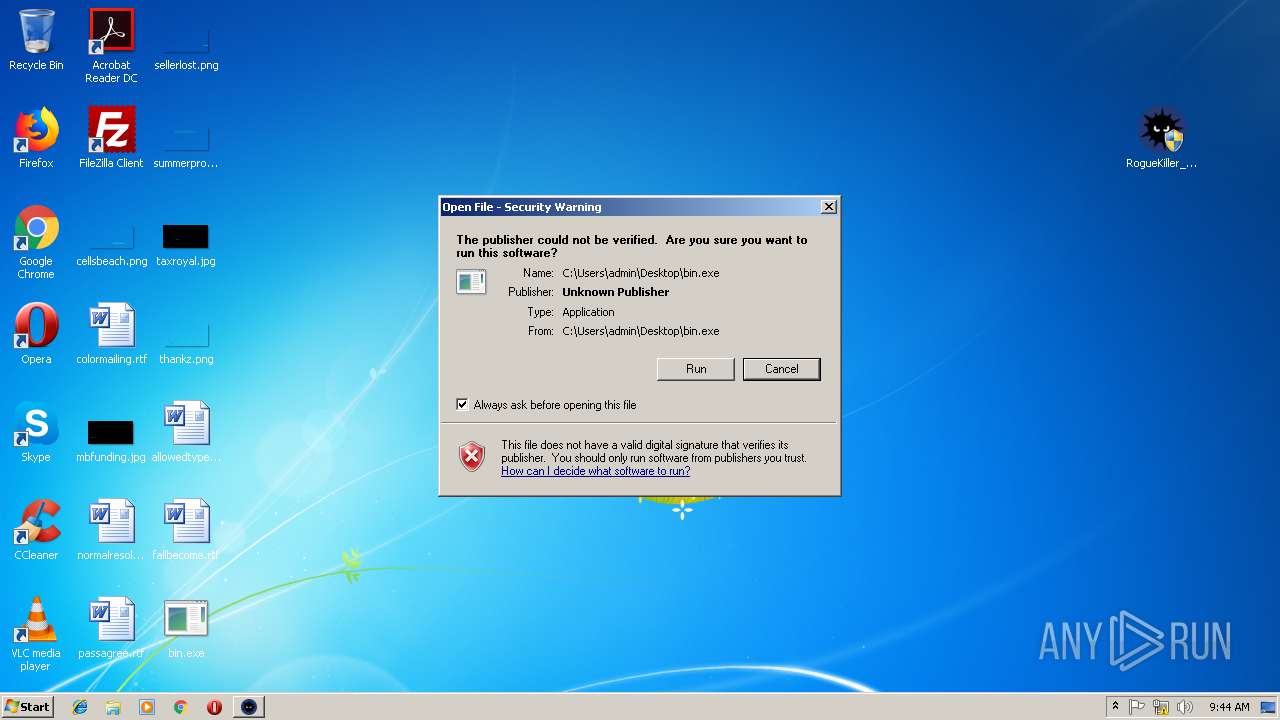
Application was dropped or rewritten from another process
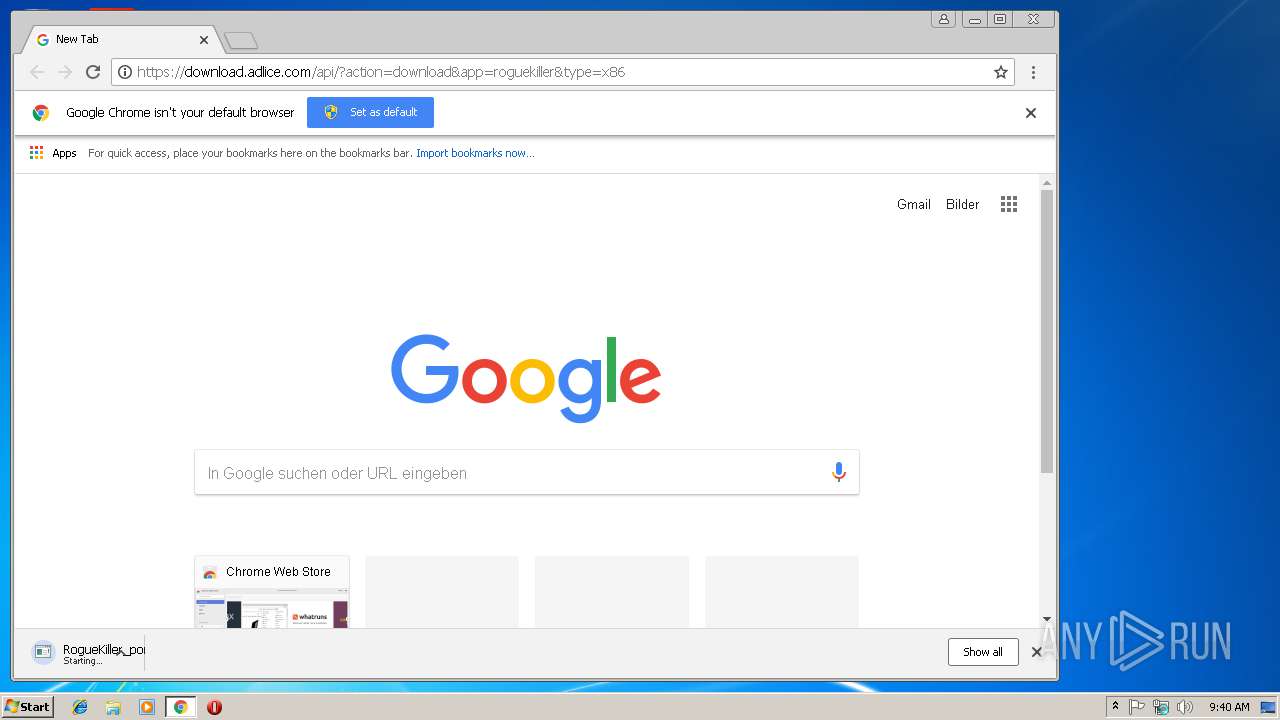
- RogueKiller_portable32.exe (PID: 2892)
- RogueKiller_portable32.exe (PID: 2172)
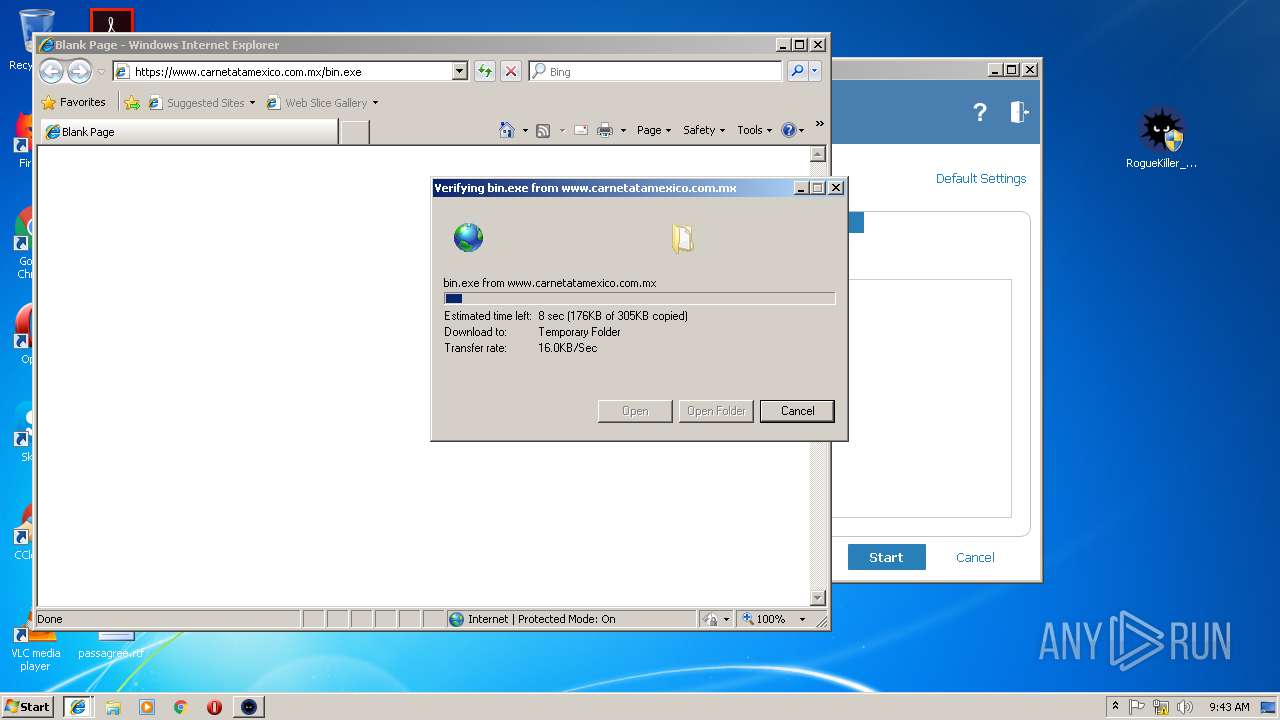
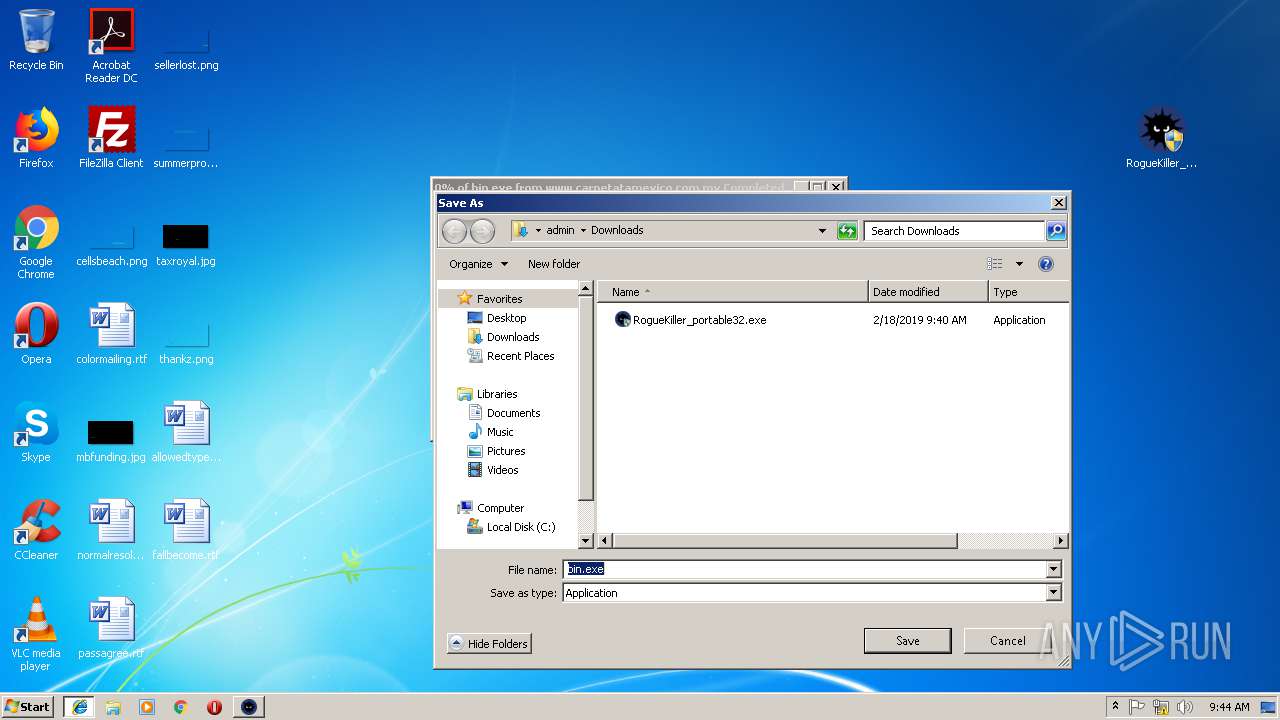
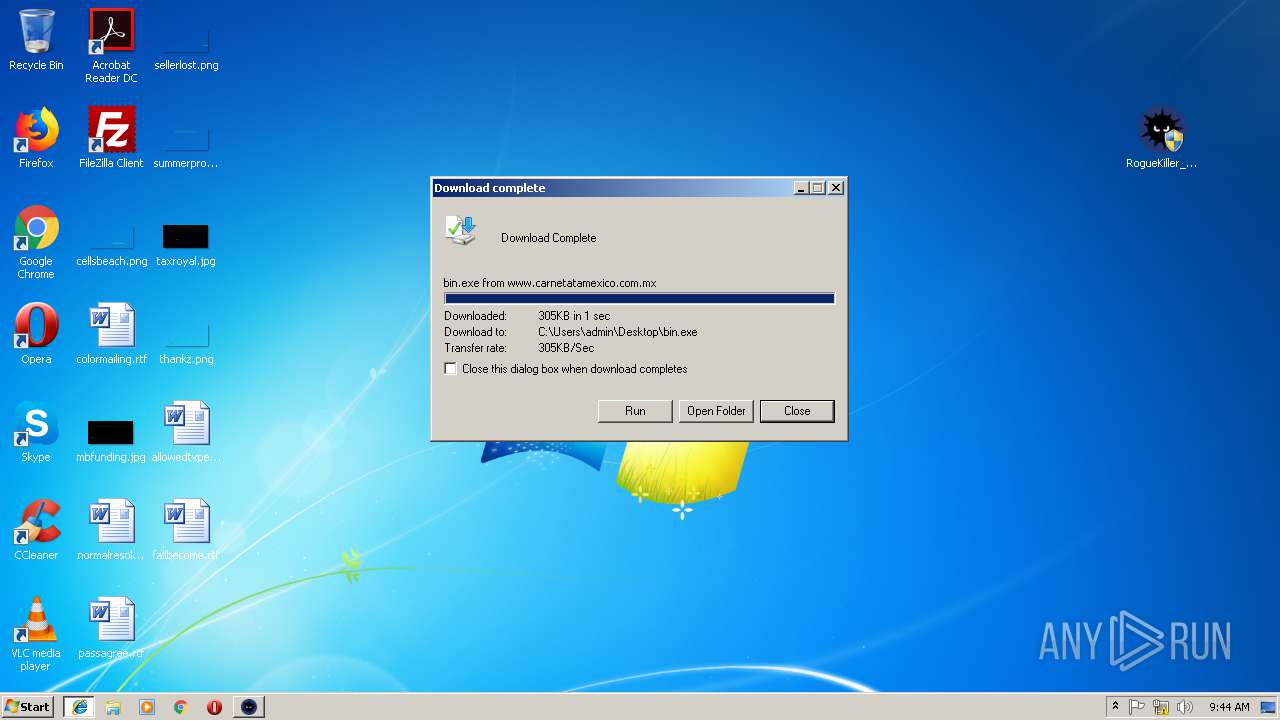
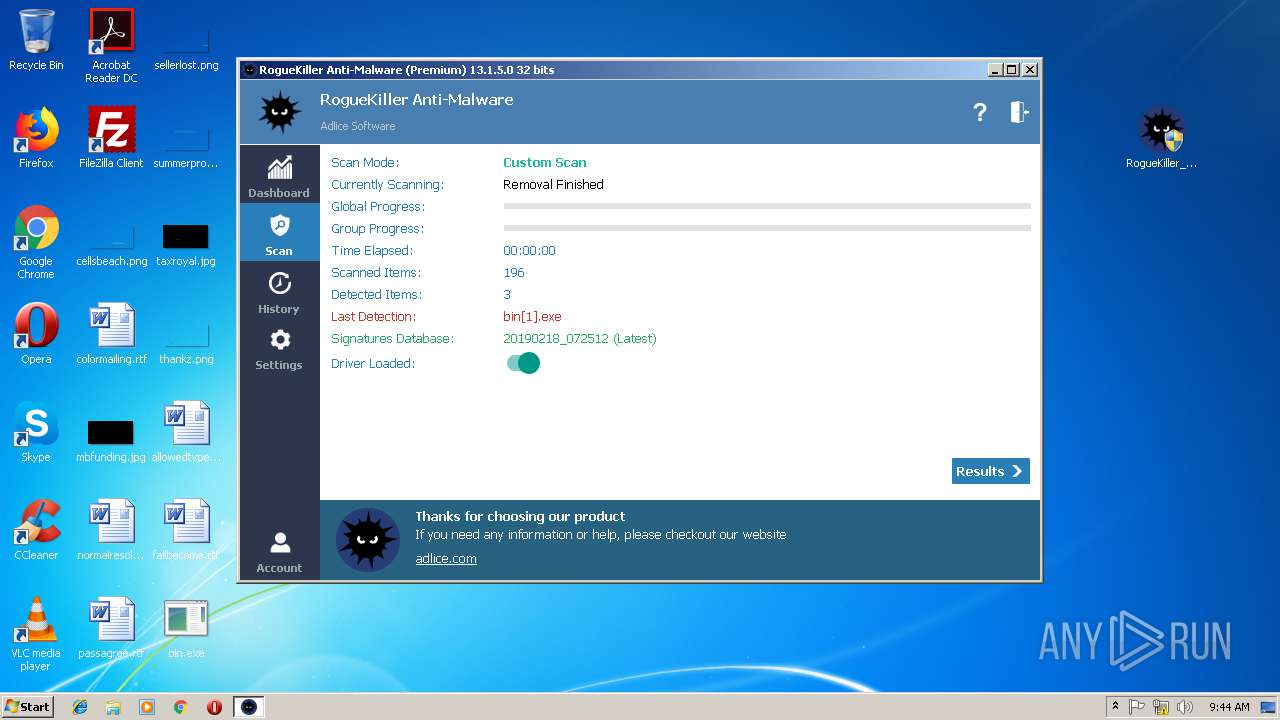
- bin[1].exe (PID: 4056)
- bin[1].exe (PID: 1404)
- bin.exe (PID: 1336)
- bin.exe (PID: 3092)
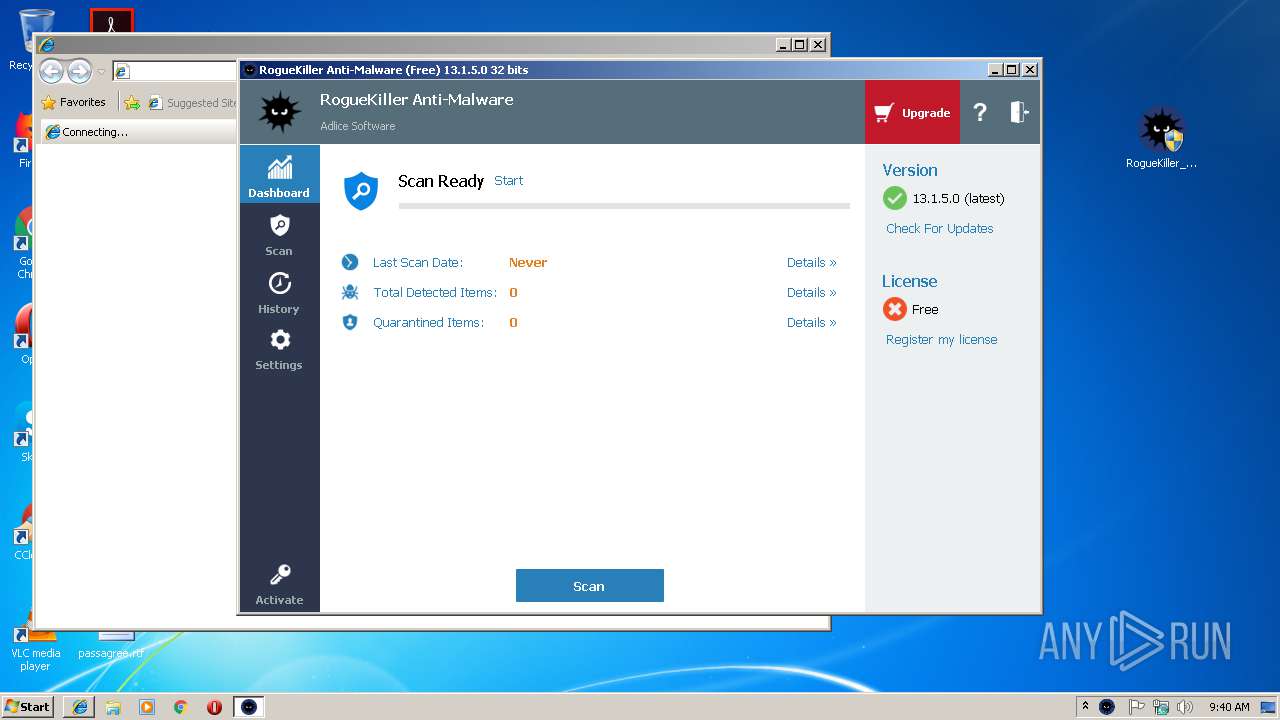
Loads the Task Scheduler COM API
- RogueKiller_portable32.exe (PID: 2892)
Detected artifacts of LokiBot
- WIN.exe (PID: 3200)
Loads the Task Scheduler DLL interface
- RogueKiller_portable32.exe (PID: 2892)
Actions looks like stealing of personal data
- WIN.exe (PID: 3200)
Changes the login/logoff helper path in the registry
- bin[1].exe (PID: 4056)
- bin.exe (PID: 1336)
SUSPICIOUS
Creates files in the user directory
- WIN.exe (PID: 3200)
- bin[1].exe (PID: 4056)
- bin.exe (PID: 1336)
Loads DLL from Mozilla Firefox
- WIN.exe (PID: 3200)
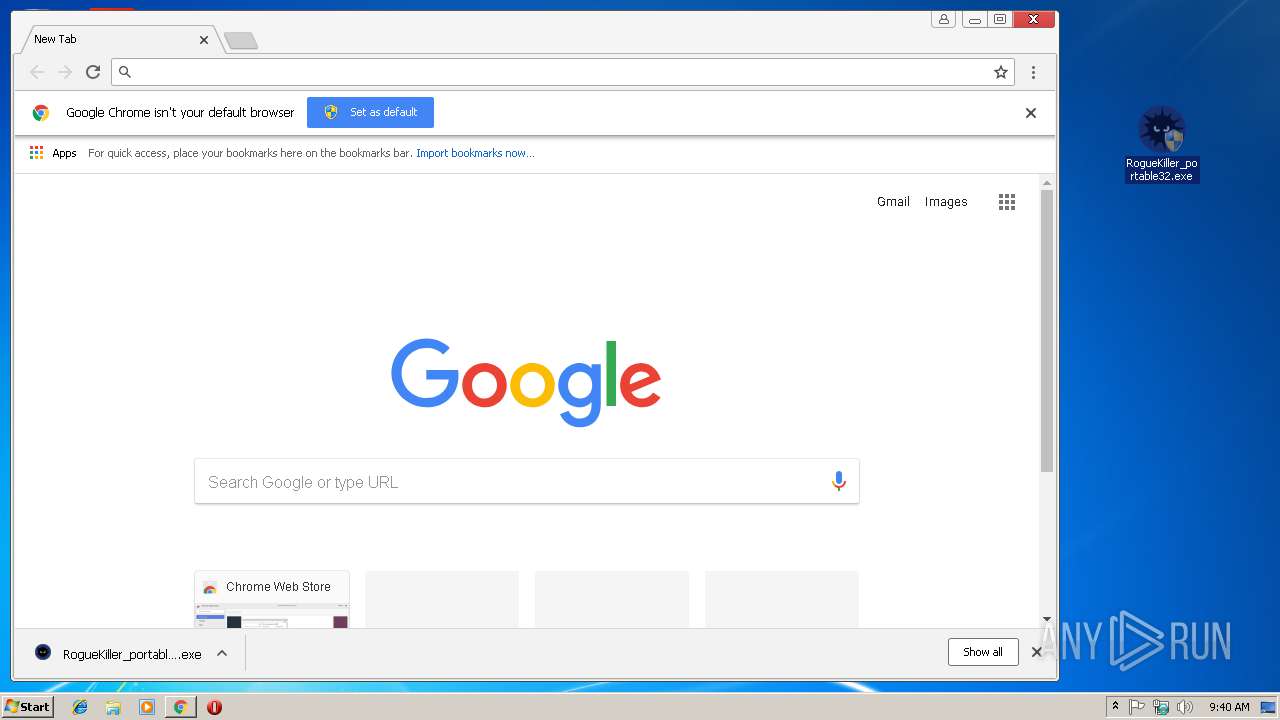
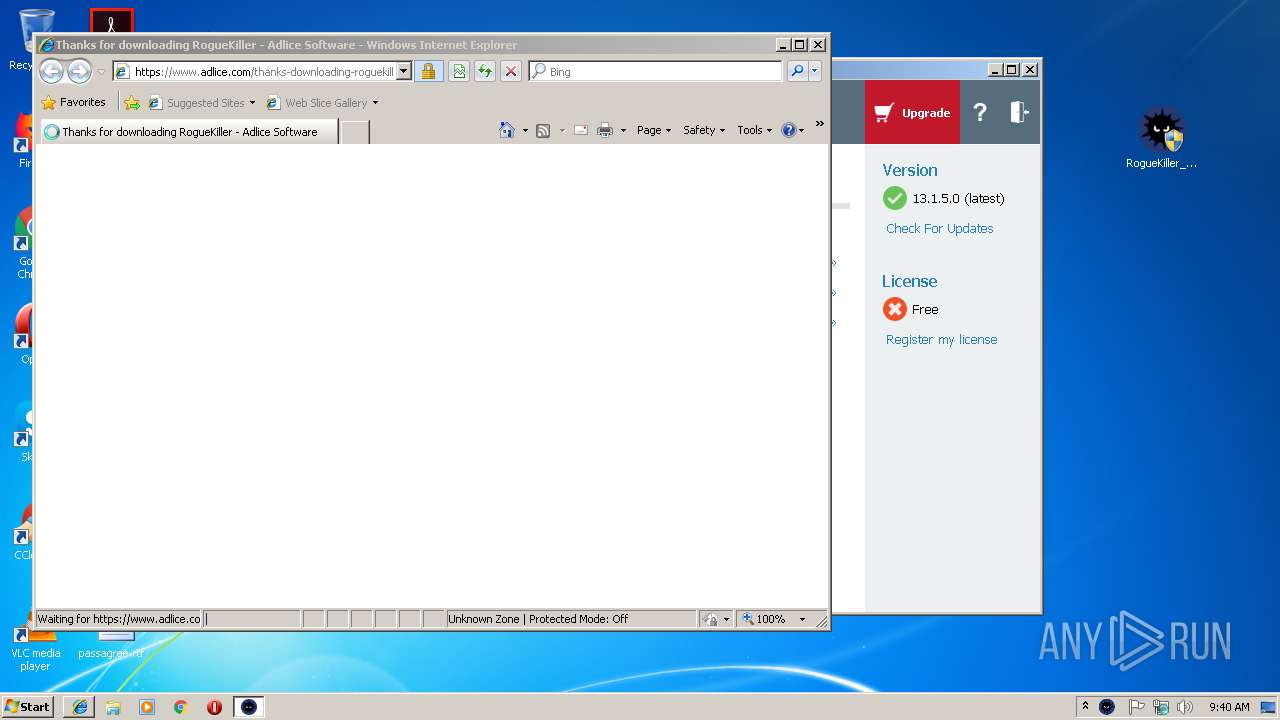
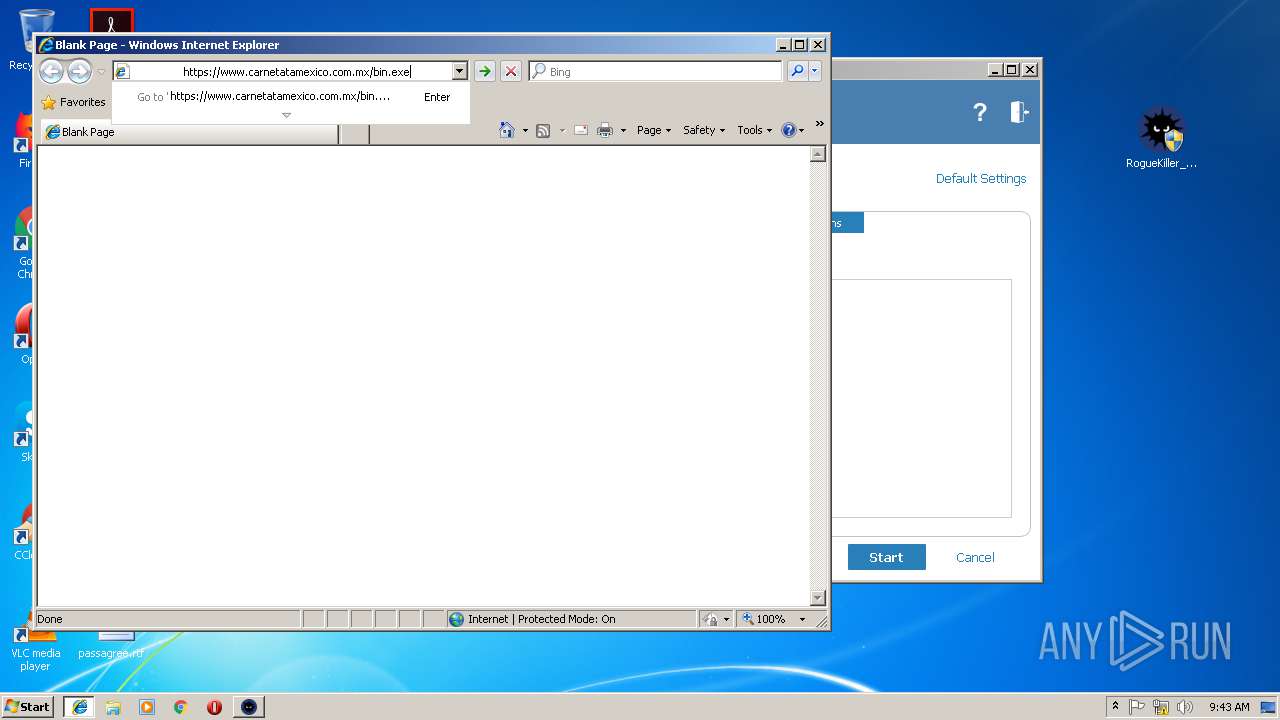
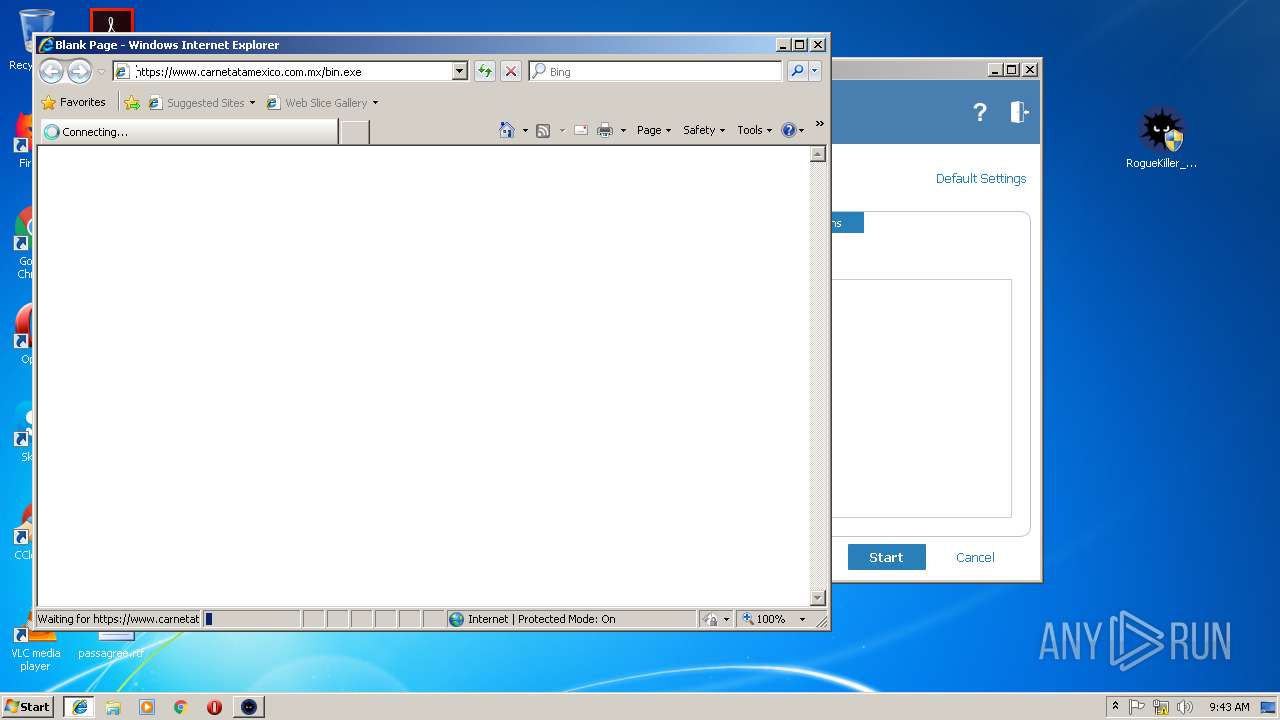
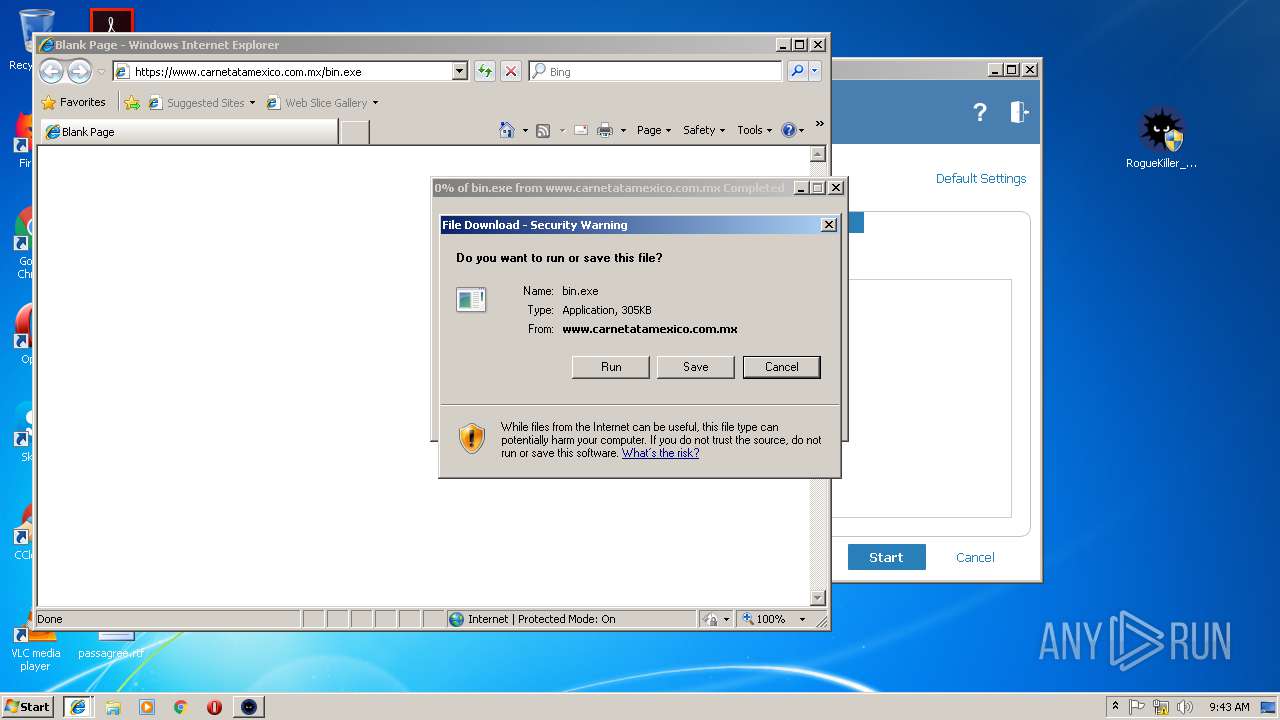
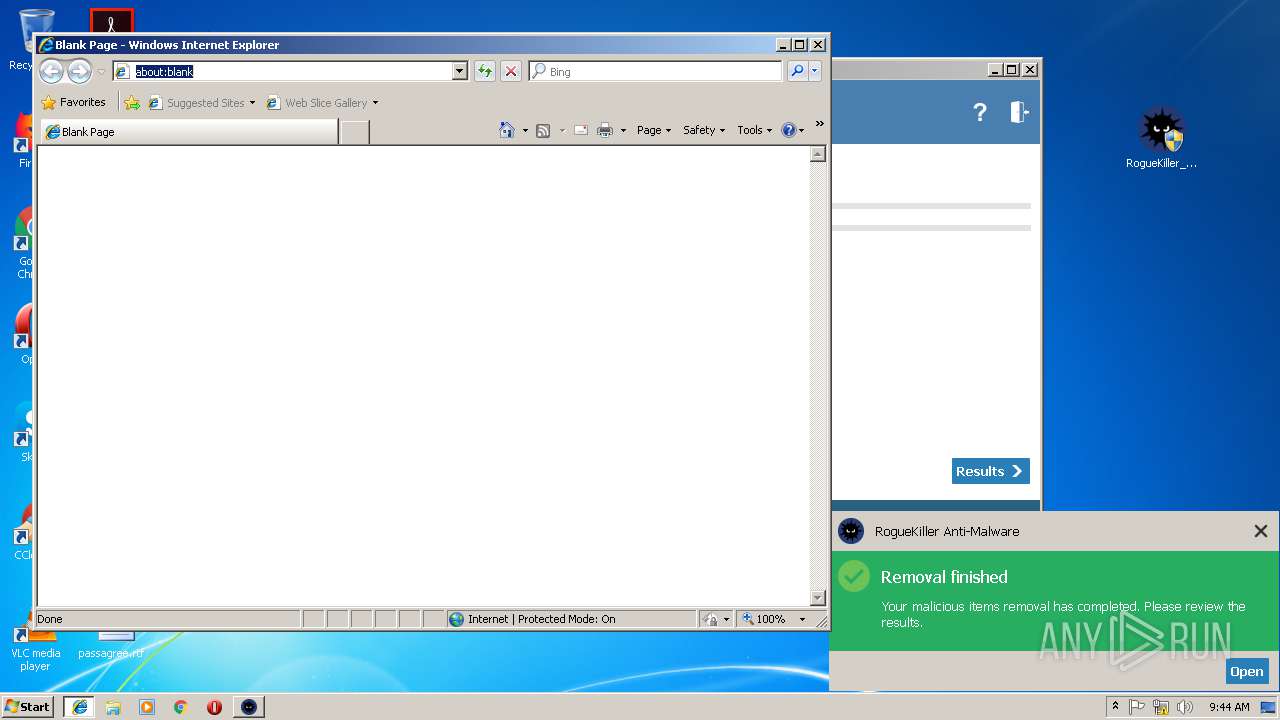
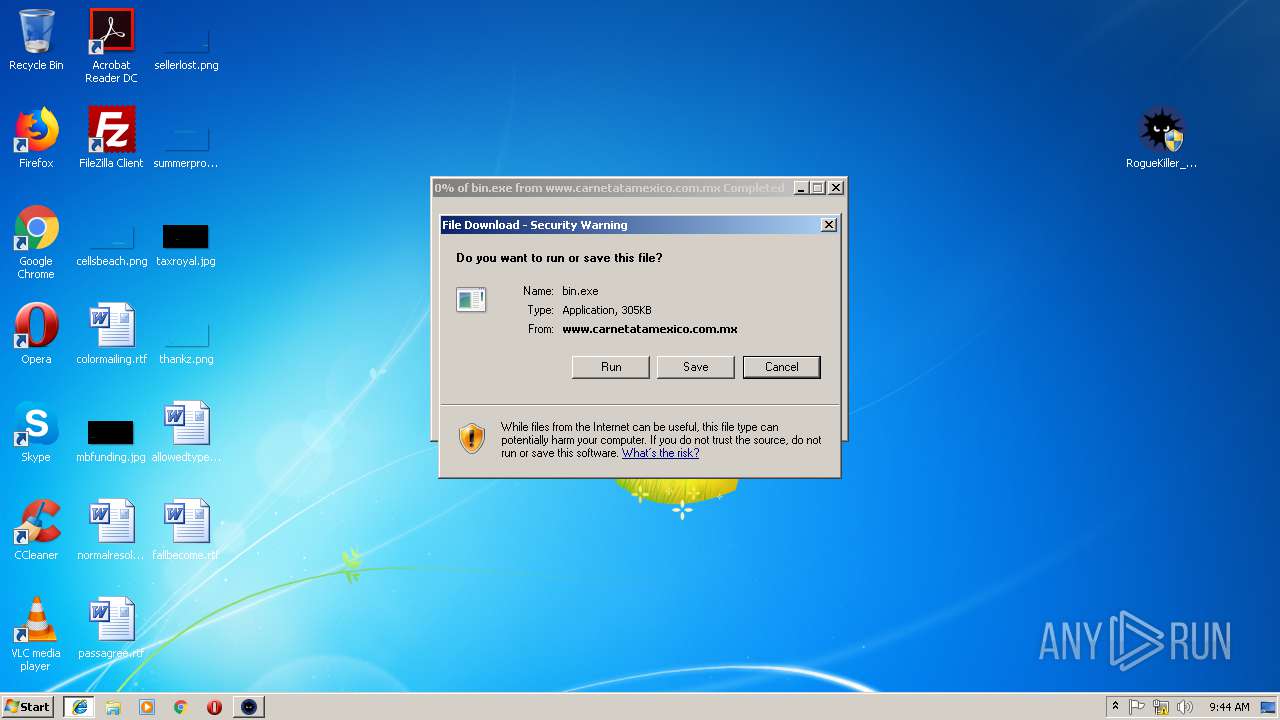
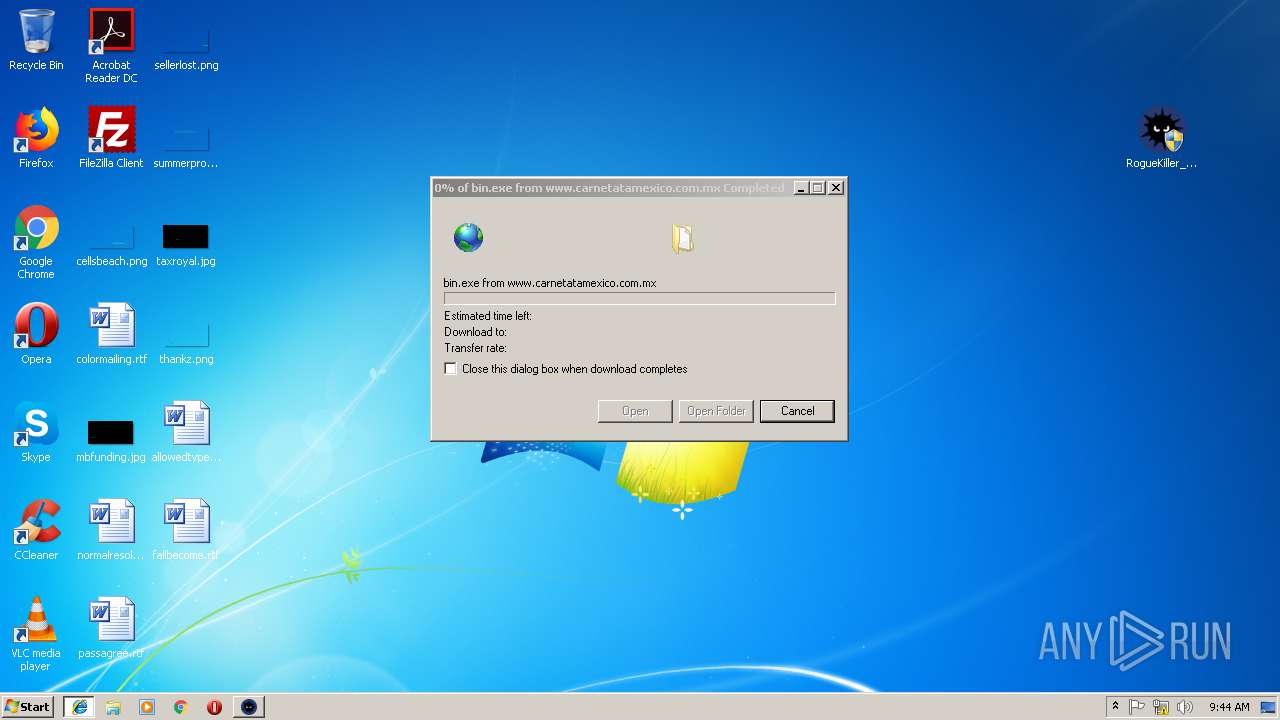
Starts Internet Explorer
- RogueKiller_portable32.exe (PID: 2892)
Application launched itself
- WIN.exe (PID: 3128)
- bin[1].exe (PID: 4056)
- bin.exe (PID: 1336)
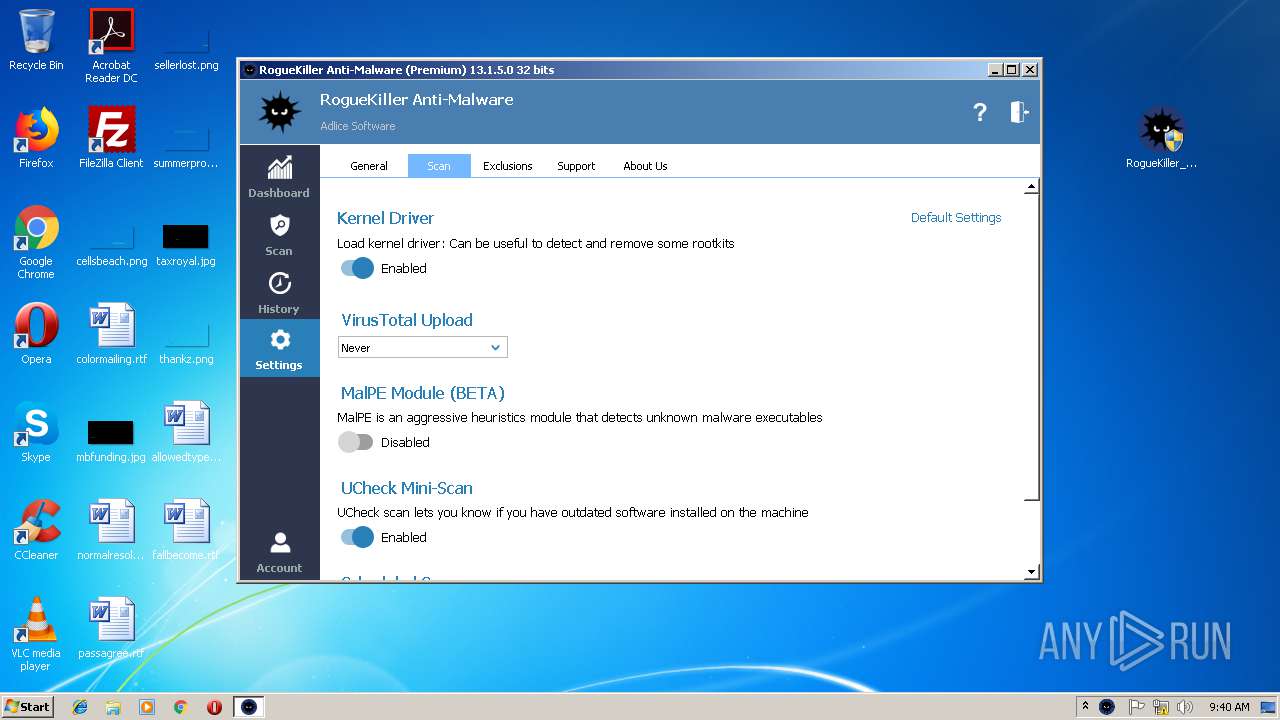
Low-level read access rights to disk partition
- RogueKiller_portable32.exe (PID: 2892)
Executable content was dropped or overwritten
- chrome.exe (PID: 3748)
- WIN.exe (PID: 3200)
- RogueKiller_portable32.exe (PID: 2892)
- iexplore.exe (PID: 2992)
- iexplore.exe (PID: 3116)
- bin[1].exe (PID: 4056)
- iexplore.exe (PID: 1332)
- iexplore.exe (PID: 2568)
- bin.exe (PID: 1336)
Creates files in the program directory
- RogueKiller_portable32.exe (PID: 2892)
Creates files in the Windows directory
- RogueKiller_portable32.exe (PID: 2892)
Creates or modifies windows services
- RogueKiller_portable32.exe (PID: 2892)
Creates files in the driver directory
- RogueKiller_portable32.exe (PID: 2892)
Cleans NTFS data-stream (Zone Identifier)
- bin[1].exe (PID: 4056)
Removes files from Windows directory
- RogueKiller_portable32.exe (PID: 2892)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3748)
- RogueKiller_portable32.exe (PID: 2892)
Application launched itself
- chrome.exe (PID: 3748)
- iexplore.exe (PID: 3116)
- iexplore.exe (PID: 2568)
Reads Internet Cache Settings
- chrome.exe (PID: 3748)
- iexplore.exe (PID: 2992)
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 1332)
Reads internet explorer settings
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 2992)
- iexplore.exe (PID: 1332)
Creates files in the user directory
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 3116)
- iexplore.exe (PID: 2992)
Changes internet zones settings
- iexplore.exe (PID: 3968)
- iexplore.exe (PID: 3116)
- iexplore.exe (PID: 2568)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2428)
Changes settings of System certificates
- iexplore.exe (PID: 2428)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 2992)
- iexplore.exe (PID: 3116)
- iexplore.exe (PID: 1332)
- bin[1].exe (PID: 4056)
- bin.exe (PID: 1336)
- iexplore.exe (PID: 2568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (90.6) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:06:17 12:49:53+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 823296 |
| InitializedDataSize: | 32768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1338 |
| OSVersion: | 4 |
| ImageVersion: | 6.3 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.3.0.3 |
| ProductVersionNumber: | 6.3.0.3 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | WELLTREATED |
| ProductName: | OZONED3 |
| FileVersion: | 6.03.0003 |
| ProductVersion: | 6.03.0003 |
| InternalName: | multiplexers |
| OriginalFileName: | multiplexers.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jun-2005 10:49:53 |
| Detected languages: |
|
| CompanyName: | WELLTREATED |
| ProductName: | OZONED3 |
| FileVersion: | 6.03.0003 |
| ProductVersion: | 6.03.0003 |
| InternalName: | multiplexers |
| OriginalFilename: | multiplexers.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 17-Jun-2005 10:49:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000C879C | 0x000C9000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.89325 |
.data | 0x000CA000 | 0x00000A38 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000CB000 | 0x000064C4 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17364 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.31658 | 568 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
2 | 2.55987 | 744 | Unicode (UTF 16LE) | English - United States | RT_ICON |
3 | 2.08999 | 744 | Unicode (UTF 16LE) | English - United States | RT_ICON |
101 | 2.26096 | 20 | Unicode (UTF 16LE) | English - United States | RT_GROUP_ICON |
102 | 2.32322 | 20 | Unicode (UTF 16LE) | English - United States | RT_GROUP_ICON |
103 | 2.42322 | 20 | Unicode (UTF 16LE) | English - United States | RT_GROUP_ICON |
30001 | 5.25052 | 5672 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 5.71794 | 3752 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 5.80371 | 12840 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
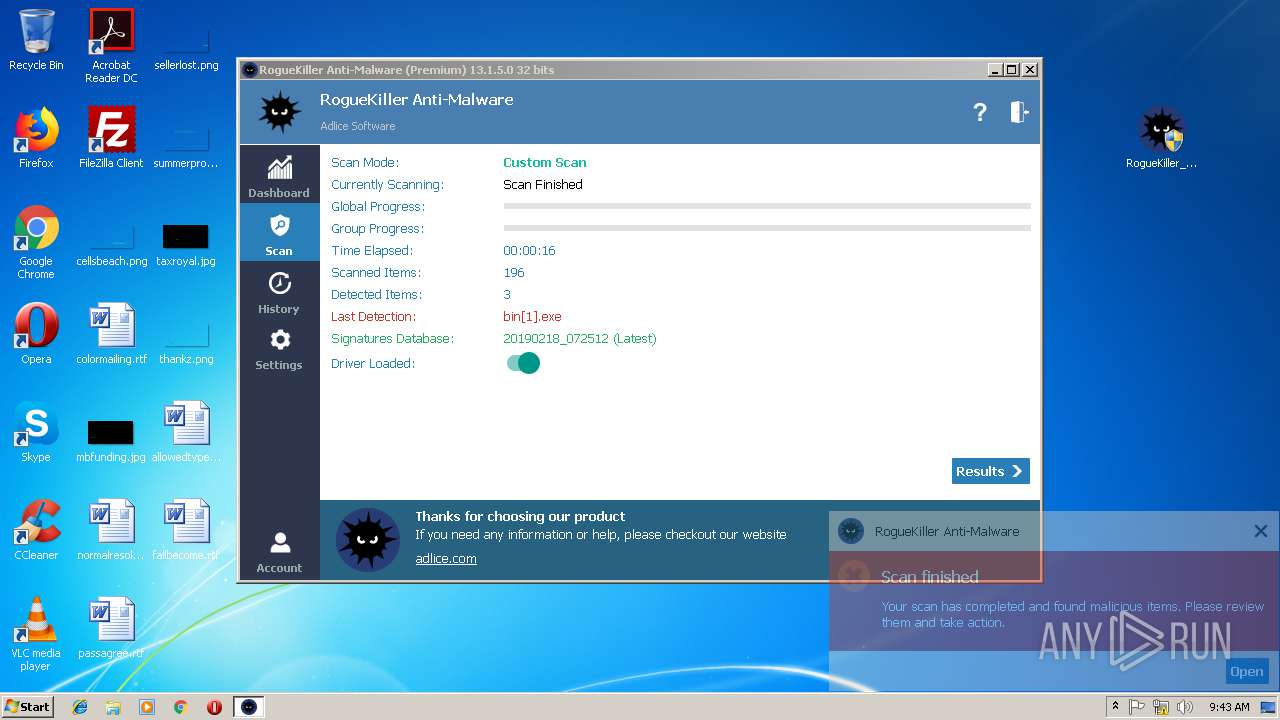
Total processes
67
Monitored processes
24
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1332 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2568 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1336 | "C:\Users\admin\Desktop\bin.exe" | C:\Users\admin\Desktop\bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DbMux Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1404 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\bin[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\bin[1].exe | — | bin[1].exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DbMux Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
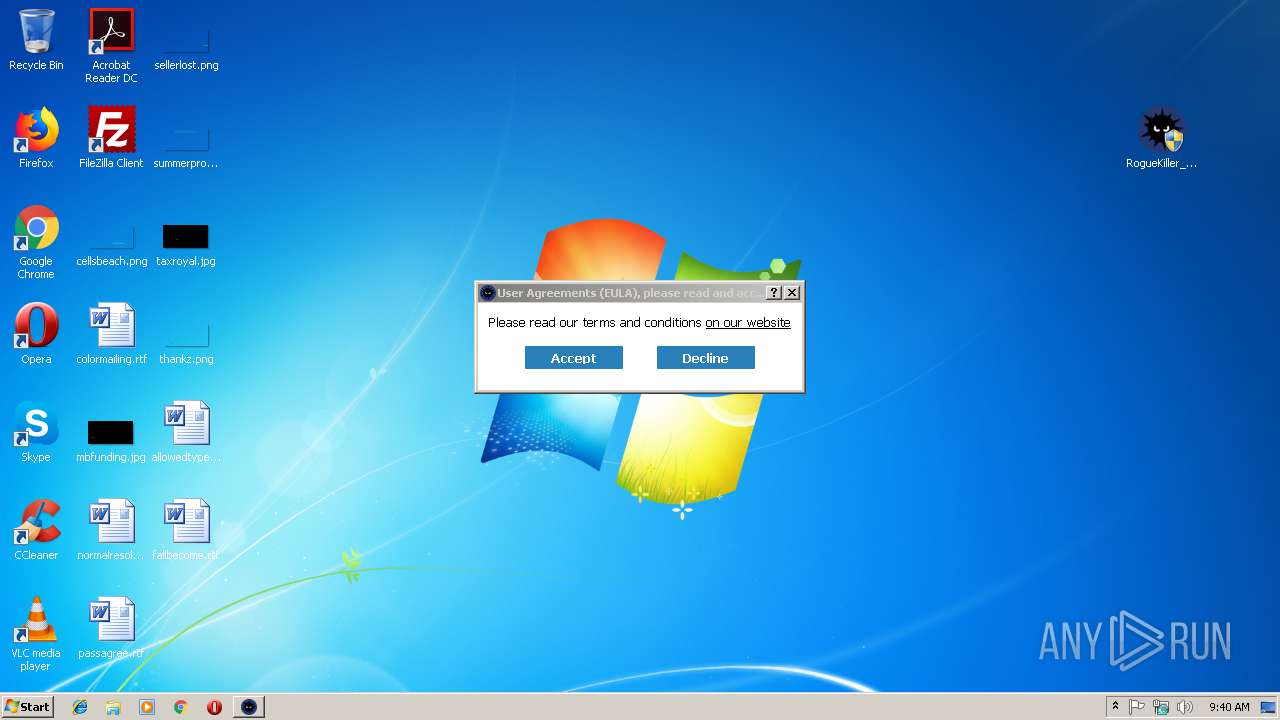
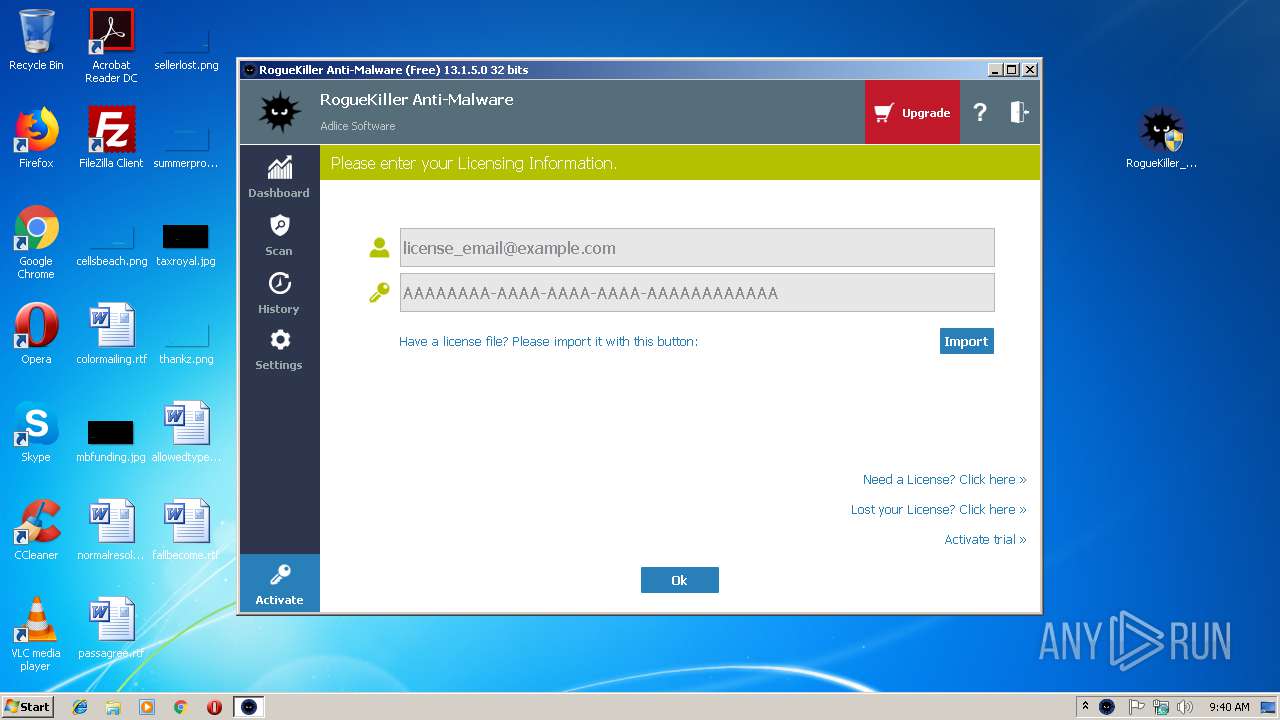
| 2172 | "C:\Users\admin\Desktop\RogueKiller_portable32.exe" | C:\Users\admin\Desktop\RogueKiller_portable32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,9101526334213683802,3342244265961184017,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2A2B2A30CA42B799F1B6804998A059DF --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2A2B2A30CA42B799F1B6804998A059DF --renderer-client-id=6 --mojo-platform-channel-handle=3052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,9101526334213683802,3342244265961184017,131072 --enable-features=PasswordImport --service-pipe-token=DF64F28B488534F326022E1B4A4657CA --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=DF64F28B488534F326022E1B4A4657CA --renderer-client-id=3 --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3968 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f3700b0,0x6f3700c0,0x6f3700cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
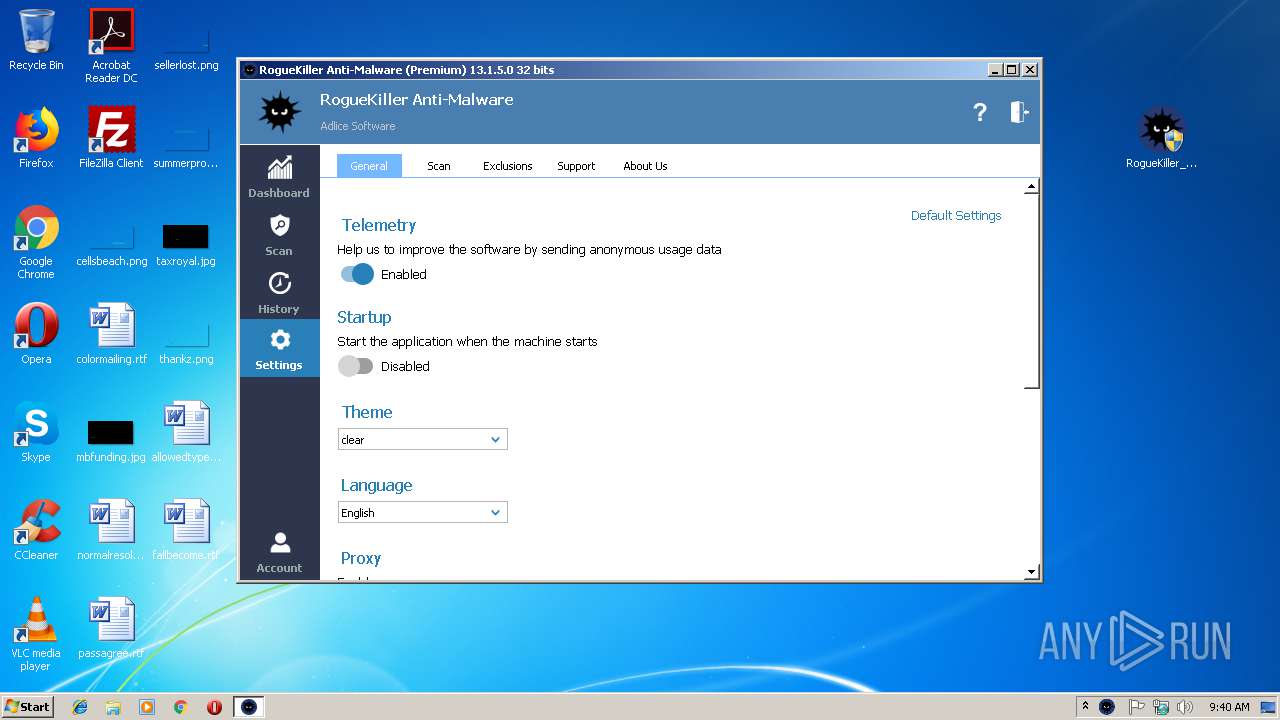
| 2892 | "C:\Users\admin\Desktop\RogueKiller_portable32.exe" | C:\Users\admin\Desktop\RogueKiller_portable32.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 821
Read events
2 421
Write events
386
Delete events
14
Modification events
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3748-13194956423289250 |
Value: 259 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
11
Suspicious files
86
Text files
155
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bba02d18-682d-479a-88c7-c4fa4c527df0.tmp | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\63bf9ff5-3916-4ca0-957b-647d4de0f62a.tmp | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF24bf3a.TMP | text | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF24bf59.TMP | text | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 3128 | WIN.exe | C:\Users\admin\AppData\Local\Temp\~DFC77E23AF6E09AB45.TMP | binary | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
60
DNS requests
36
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3116 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3968 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2568 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3748 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
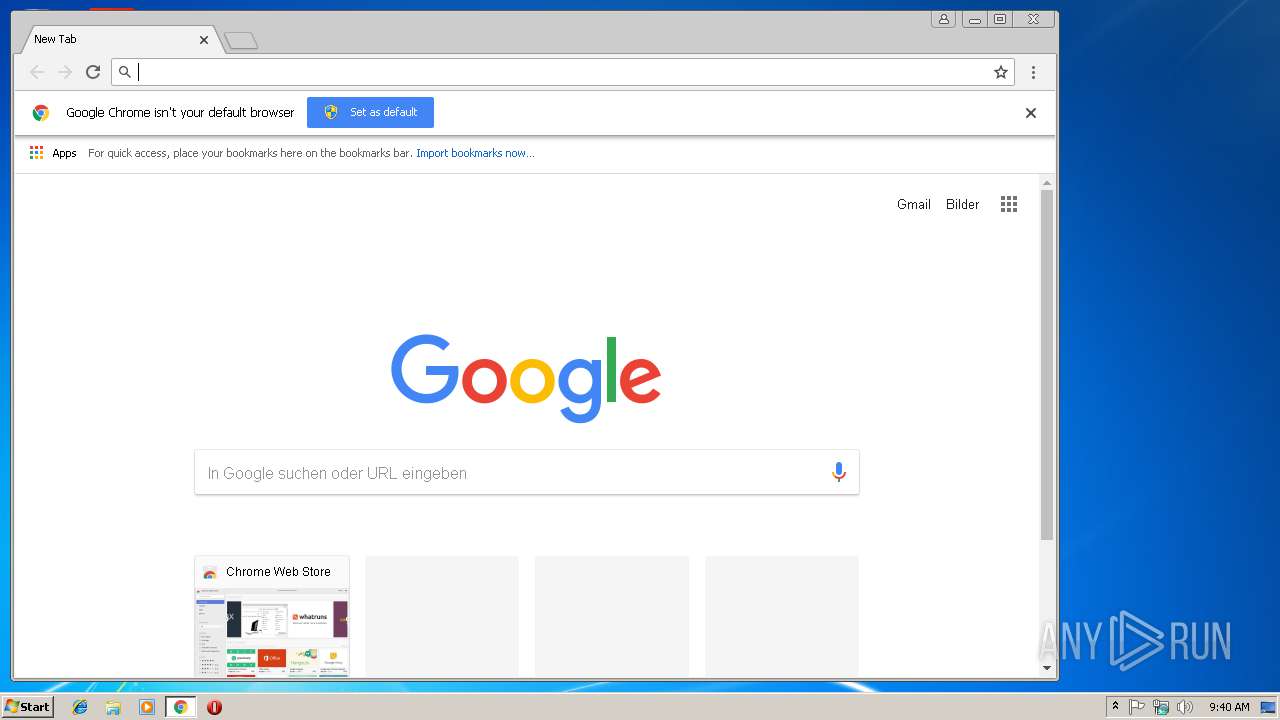
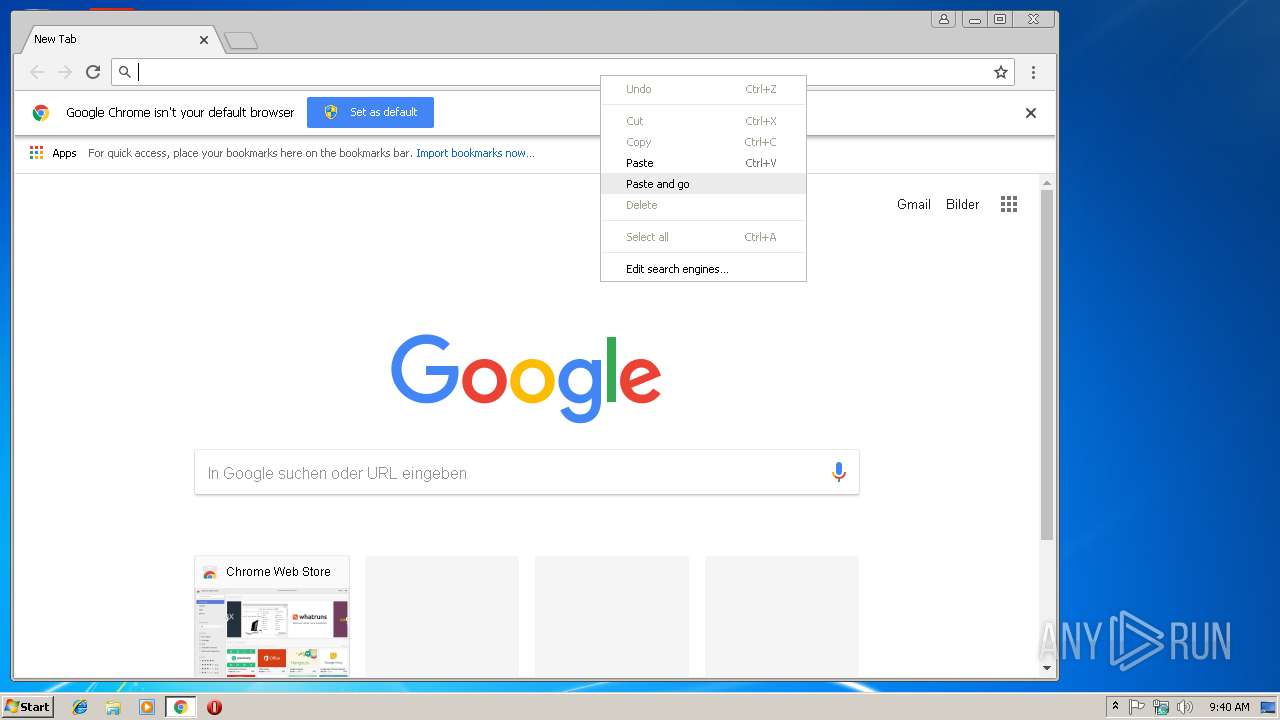
3748 | chrome.exe | 178.33.106.117:443 | download.adlice.com | OVH SAS | FR | suspicious |
3748 | chrome.exe | 216.58.207.67:443 | www.google.at | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.16.131:443 | www.google.de | Google Inc. | US | whitelisted |
3748 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.23.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
martfire.gq |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
download.adlice.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
Process | Message |
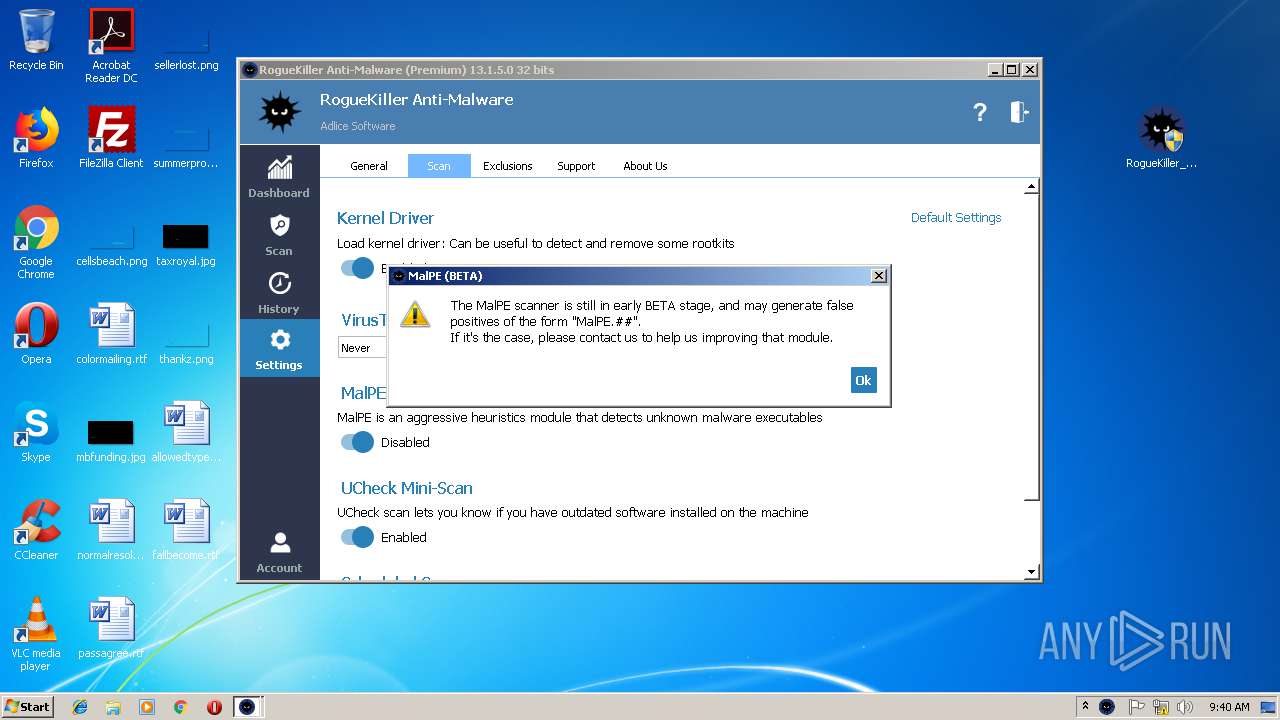
|---|---|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|