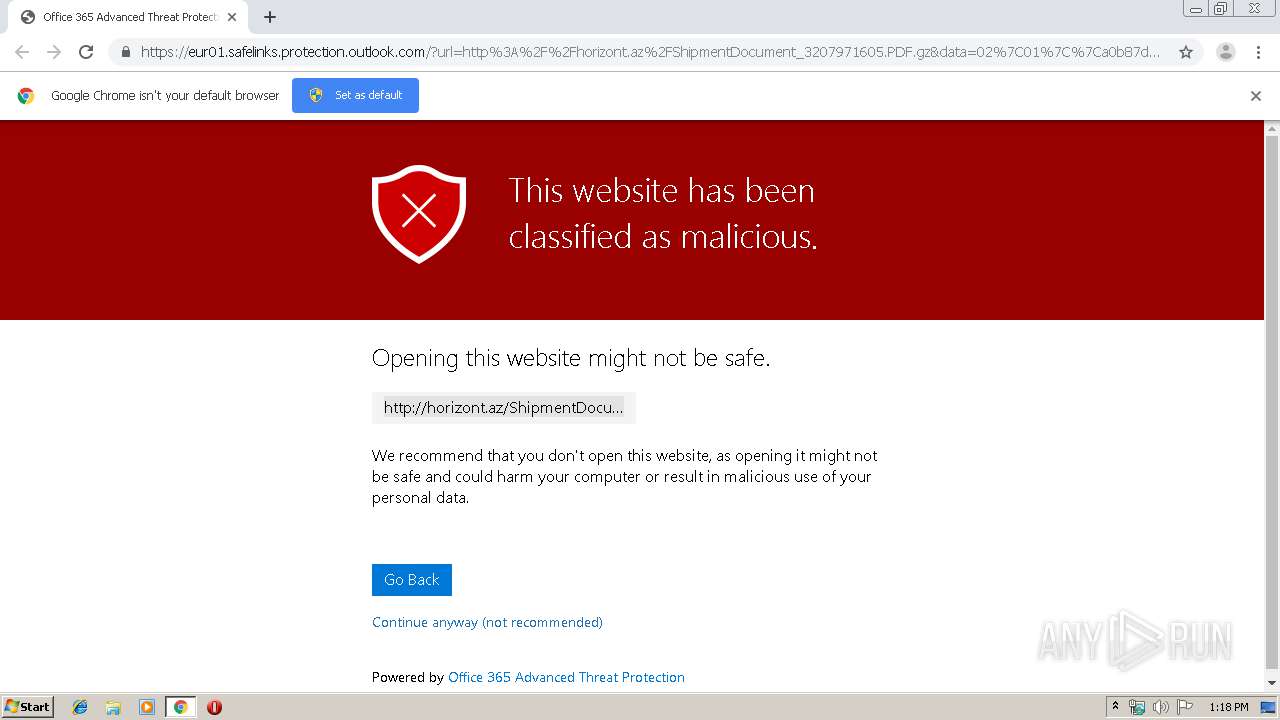
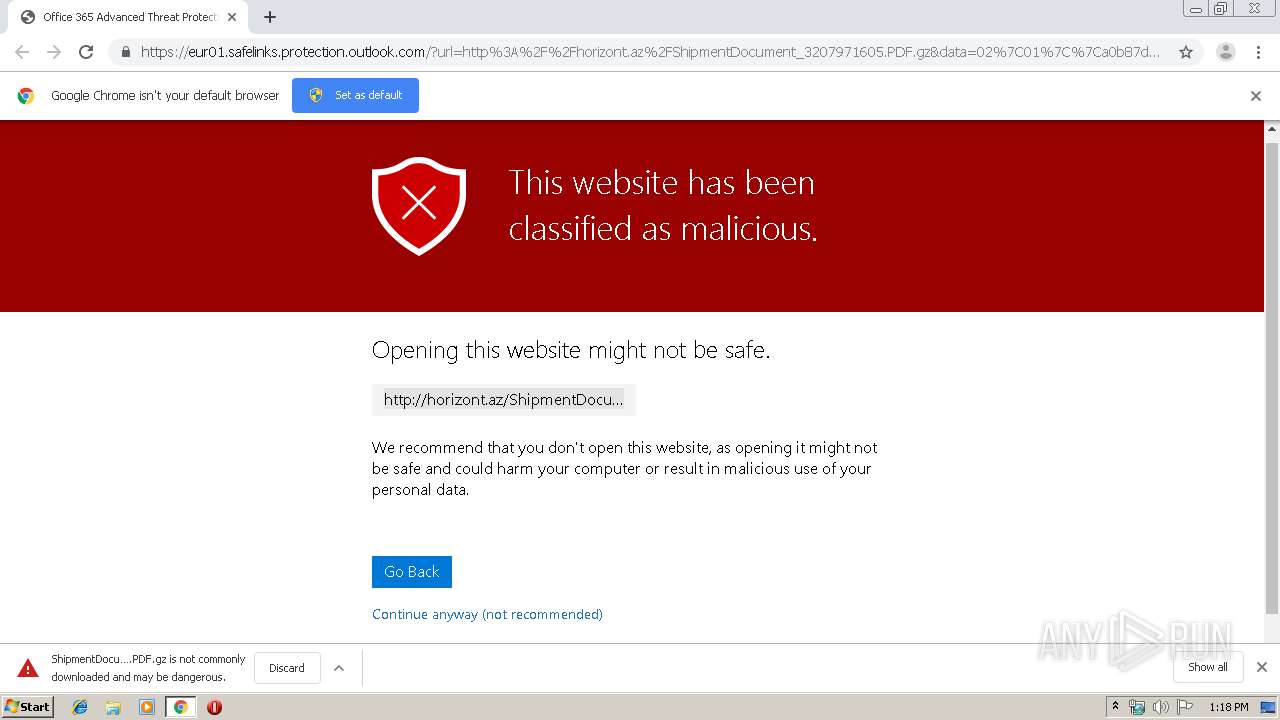
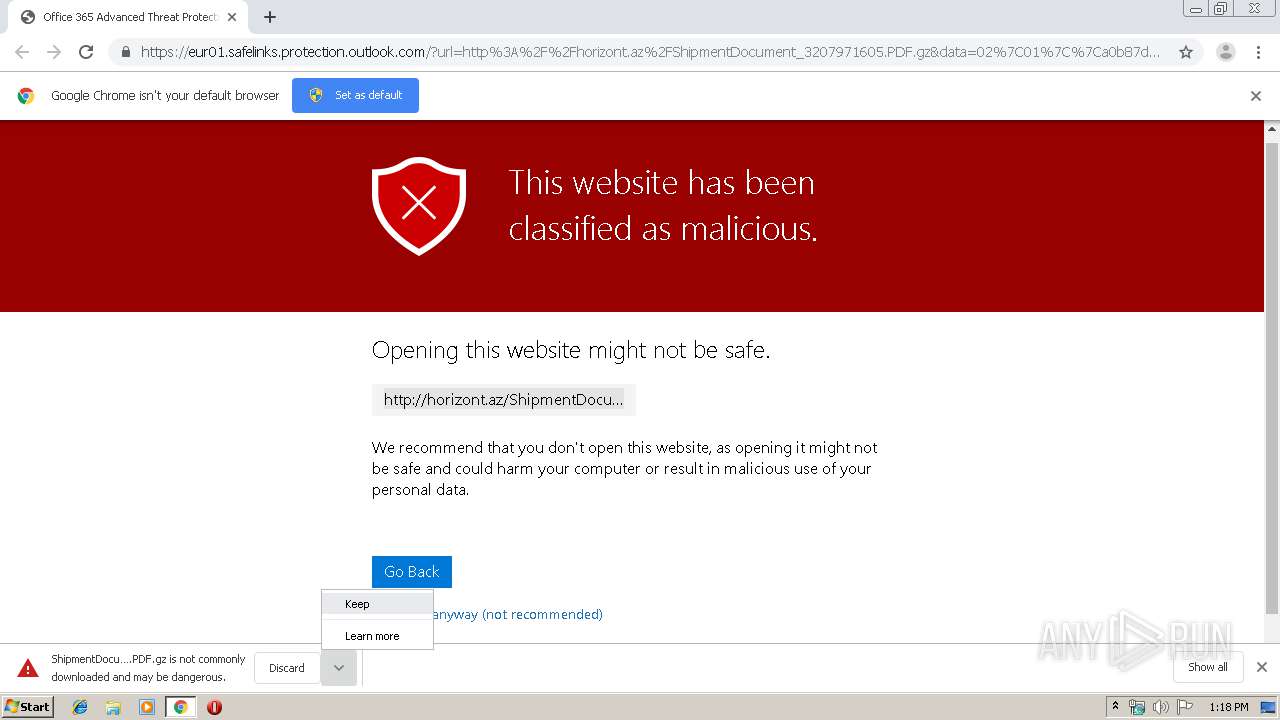
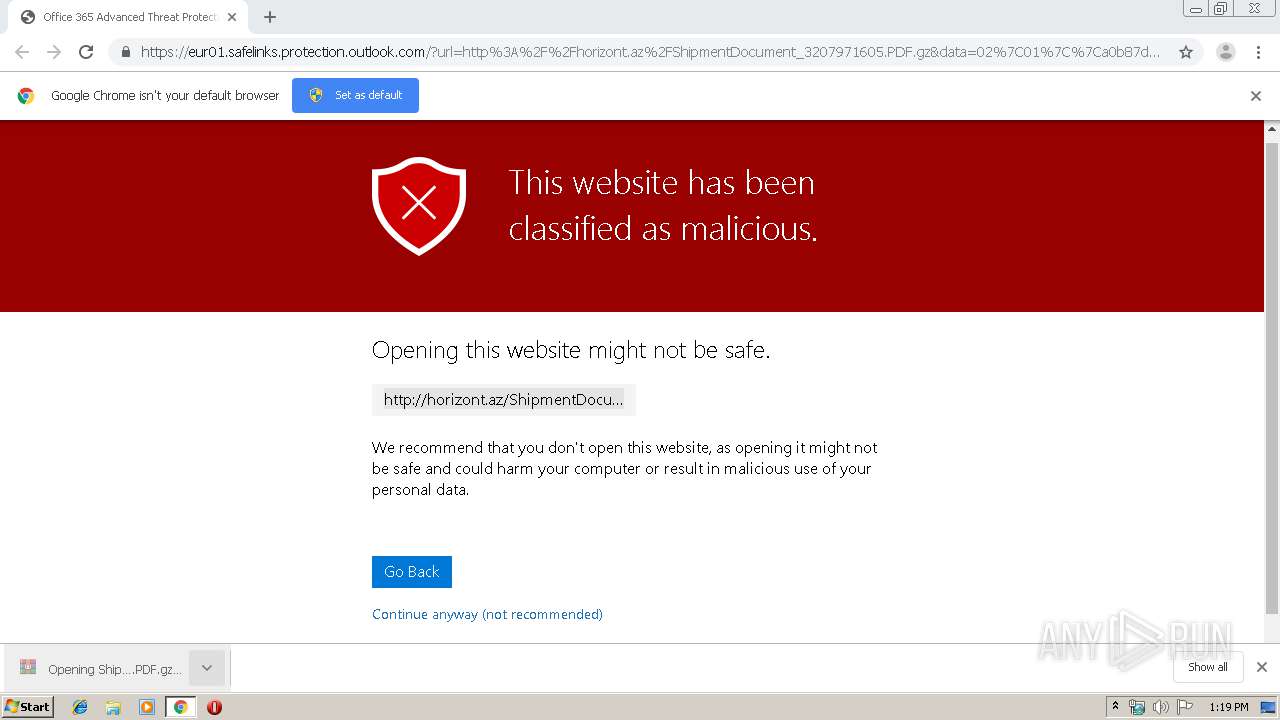
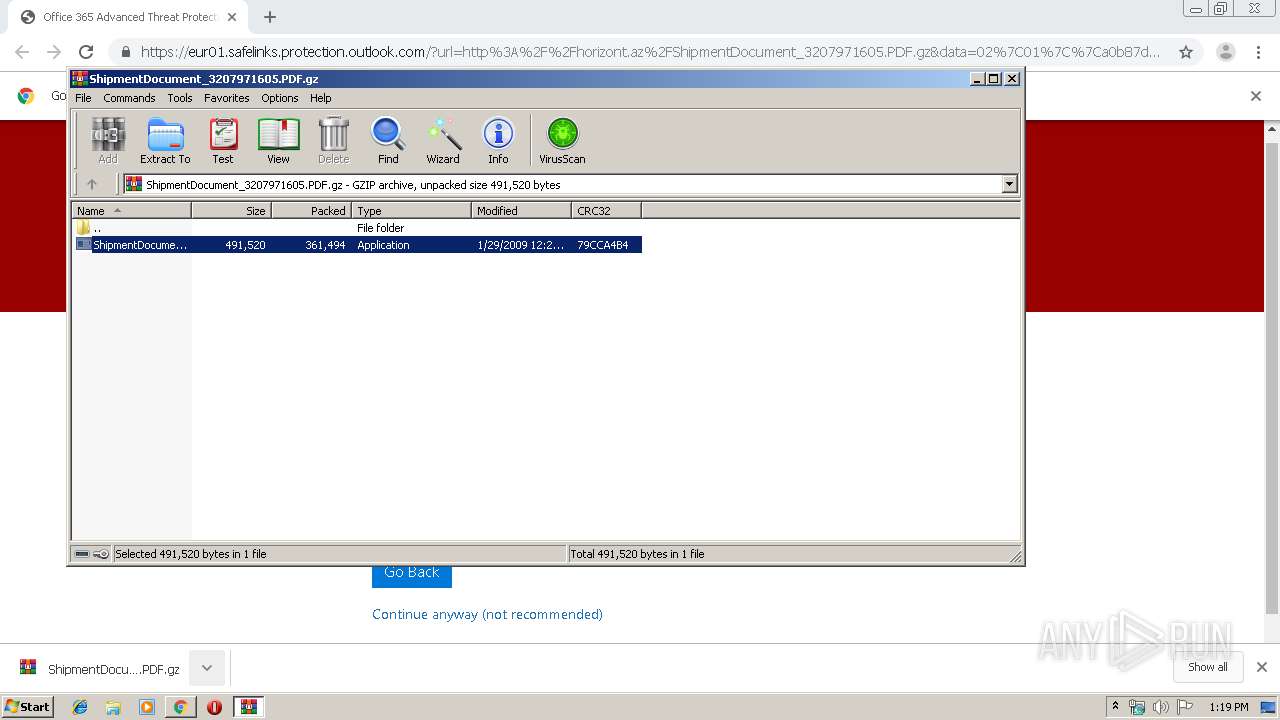
| URL: | https://eur01.safelinks.protection.outlook.com/?url=http%3A%2F%2Fhorizont.az%2FShipmentDocument_3207971605.PDF.gz&data=02%7C01%7C%7Ca0b87db1eeb24d27d67908d736afd8b0%7C28042244bb514cd680347776fa3703e8%7C1%7C0%7C637038001201230457&sdata=mprqNP2mH78zC%2FL1k950iqYbcgw4EYwkxpOVmH1UtOg%3D&reserved=0 |
| Full analysis: | https://app.any.run/tasks/cd8c5f5c-70ed-4e60-9beb-408548ec911d |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
| Analysis date: | September 11, 2019, 12:18:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D16BD2FC461E1E91A7B0B5A282F1C43 |
| SHA1: | 923451C0C6387E3ADC334B95BDDCEE4DFDFD87BE |
| SHA256: | 5546C0CE9C623A50BD035B5D3AF084BC1E5A9840E9DE93D366664E7BD15E47AD |
| SSDEEP: | 6:2U9V9iRXPNHszB89CxPuBh3CVW13YE76YTXQILgWES/sc62YgrM4RH0:2U9qVsFTPunSW13376KLZjsYYgjU |
MALICIOUS
Application was dropped or rewritten from another process
- ShipmentDocument_3207971605-PDF.exe (PID: 3144)
- ShipmentDocument_3207971605-PDF.exe (PID: 3920)
Detected Pony/Fareit Trojan
- ShipmentDocument_3207971605-PDF.exe (PID: 3920)
Connects to CnC server
- ShipmentDocument_3207971605-PDF.exe (PID: 3920)
Actions looks like stealing of personal data
- ShipmentDocument_3207971605-PDF.exe (PID: 3920)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2800)
Executable content was dropped or overwritten
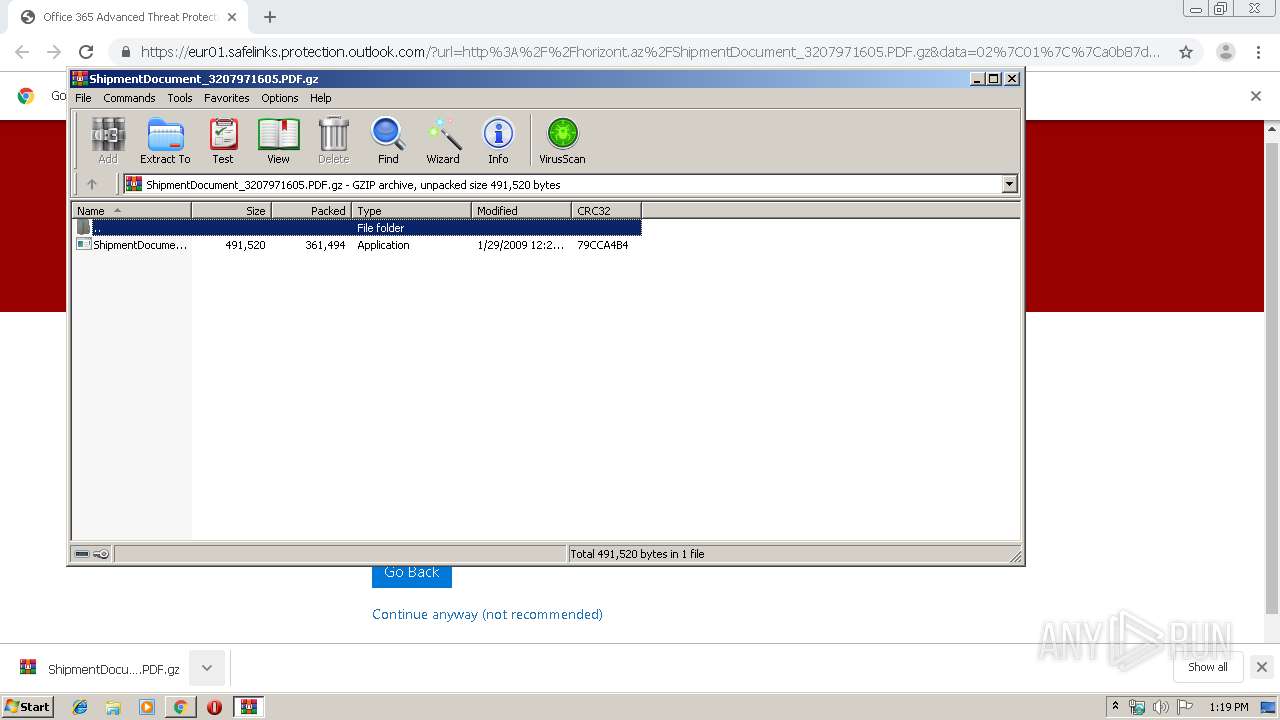
- WinRAR.exe (PID: 848)
Reads Internet Cache Settings
- ShipmentDocument_3207971605-PDF.exe (PID: 3920)
Application launched itself
- ShipmentDocument_3207971605-PDF.exe (PID: 3144)
Starts CMD.EXE for commands execution
- ShipmentDocument_3207971605-PDF.exe (PID: 3920)
INFO
Reads the hosts file
- chrome.exe (PID: 2544)
- chrome.exe (PID: 2800)
Reads Internet Cache Settings
- chrome.exe (PID: 2800)
Creates files in the user directory
- chrome.exe (PID: 2800)
Application launched itself
- chrome.exe (PID: 2800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
25
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ShipmentDocument_3207971605.PDF.gz" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,7337260193840206380,8171722316359502993,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6970588977468122084 --mojo-platform-channel-handle=3544 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | cmd /c ""C:\Users\admin\AppData\Local\Temp\1573109.bat" "C:\Users\admin\AppData\Local\Temp\Rar$EXa848.35138\ShipmentDocument_3207971605-PDF.exe" " | C:\Windows\system32\cmd.exe | — | ShipmentDocument_3207971605-PDF.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,7337260193840206380,8171722316359502993,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11871630675352180761 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,7337260193840206380,8171722316359502993,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2570617874941417659 --mojo-platform-channel-handle=3948 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,7337260193840206380,8171722316359502993,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=757714658008907026 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,7337260193840206380,8171722316359502993,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1461989144900494963 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,7337260193840206380,8171722316359502993,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11311284795992947924 --mojo-platform-channel-handle=3476 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,7337260193840206380,8171722316359502993,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3782705801910117764 --mojo-platform-channel-handle=1608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://eur01.safelinks.protection.outlook.com/?url=http%3A%2F%2Fhorizont.az%2FShipmentDocument_3207971605.PDF.gz&data=02%7C01%7C%7Ca0b87db1eeb24d27d67908d736afd8b0%7C28042244bb514cd680347776fa3703e8%7C1%7C0%7C637038001201230457&sdata=mprqNP2mH78zC%2FL1k950iqYbcgw4EYwkxpOVmH1UtOg%3D&reserved=0" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 806
Read events
1 692
Write events
109
Delete events
5
Modification events
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2800-13212677912339750 |
Value: 259 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
15
Text files
147
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169d5e.TMP | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a88ee27c-fbf7-4891-87eb-c9f0dc8e042e.tmp | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169d3e.TMP | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169dcb.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
29
DNS requests
16
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3920 | ShipmentDocument_3207971605-PDF.exe | GET | — | 194.209.228.145:443 | http://massaggiati.ch:443/www/enter/shit.exe | CH | — | — | malicious |
3920 | ShipmentDocument_3207971605-PDF.exe | POST | — | 128.140.230.207:80 | http://marinebuilding.ro/lib/enter/gate.php | RO | — | — | malicious |
3920 | ShipmentDocument_3207971605-PDF.exe | GET | 301 | 194.209.228.145:80 | http://massaggiati.ch/www/enter/shit.exe | CH | html | 249 b | malicious |
2544 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2544 | chrome.exe | GET | 200 | 23.254.164.59:80 | http://horizont.az/ShipmentDocument_3207971605.PDF.gz | US | compressed | 353 Kb | unknown |
2544 | chrome.exe | GET | 200 | 173.194.150.135:80 | http://r1---sn-f5f7ln7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.222.142&mm=28&mn=sn-f5f7ln7s&ms=nvh&mt=1568203911&mv=u&mvi=0&pl=23&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2544 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2544 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2544 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2544 | chrome.exe | 216.58.208.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2544 | chrome.exe | 172.217.22.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2544 | chrome.exe | 173.194.150.135:80 | r1---sn-f5f7ln7s.gvt1.com | Google Inc. | US | whitelisted |
2544 | chrome.exe | 172.217.18.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2544 | chrome.exe | 23.254.164.59:80 | horizont.az | Hostwinds LLC. | US | unknown |
2544 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
eur01.safelinks.protection.outlook.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-f5f7ln7s.gvt1.com |
| whitelisted |
horizont.az |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3920 | ShipmentDocument_3207971605-PDF.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
3920 | ShipmentDocument_3207971605-PDF.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
3920 | ShipmentDocument_3207971605-PDF.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Internet Explorer Version MSIE 5. |
3920 | ShipmentDocument_3207971605-PDF.exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no referer |
3920 | ShipmentDocument_3207971605-PDF.exe | A Network Trojan was detected | ET TROJAN Pony Downloader HTTP Library MSIE 5 Win98 |
3920 | ShipmentDocument_3207971605-PDF.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony Downloader Checkin |
3920 | ShipmentDocument_3207971605-PDF.exe | Potentially Bad Traffic | ET TROJAN Generic -POST To gate.php w/Extended ASCII Characters (Likely Zeus Derivative) |
3920 | ShipmentDocument_3207971605-PDF.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 3 |
3920 | ShipmentDocument_3207971605-PDF.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
3920 | ShipmentDocument_3207971605-PDF.exe | A Network Trojan was detected | ET TROJAN Pony Downloader HTTP Library MSIE 5 Win98 |