| File name: | 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe |
| Full analysis: | https://app.any.run/tasks/7c13d3eb-705a-4c0a-a45f-e9f6e1db4bd4 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | January 07, 2026, 15:17:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 95D134CCB4AF94E86563DF75932B3B41 |
| SHA1: | 2924FBE5AF2D87553AC198FEDB3EF26B96BAD944 |
| SHA256: | 552476CFCDCB965FBE7CC8A7689B3A2DFDDE5DCC1548895A22CCAEF19D2B254B |
| SSDEEP: | 49152:3sj8LlaqK/2z8LhfzLO88ST2aJ/G91LOEujqYjaeCgHEfH2BHQZE7FlzRH2Zi0JC:cj8LlMLYlhYjajyedydFZ5A6 |
MALICIOUS
Changes the autorun value in the registry
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
- winmgr21.exe (PID: 8040)
- RegAsm.exe (PID: 1092)
Uses Task Scheduler to run other applications
- winmgr21.exe (PID: 8040)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 1960)
- RegAsm.exe (PID: 5436)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 5436)
- RegAsm.exe (PID: 1092)
HAWKEYE has been detected (YARA)
- RegAsm.exe (PID: 1092)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
- winmgr21.exe (PID: 7996)
- winmgr21.exe (PID: 8040)
Starts itself from another location
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
Executable content was dropped or overwritten
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
- RegAsm.exe (PID: 1092)
Application launched itself
- RegAsm.exe (PID: 1092)
Possible stealing of email data
- RegAsm.exe (PID: 1960)
Process drops legitimate windows executable
- RegAsm.exe (PID: 1092)
Possible stealing of FTP data
- RegAsm.exe (PID: 1092)
Possible stealing from browsers
- RegAsm.exe (PID: 5436)
The process executes via Task Scheduler
- winmgr21.exe (PID: 7860)
- winmgr21.exe (PID: 5752)
INFO
The sample compiled with chinese language support
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
The process uses AutoIt
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
- winmgr21.exe (PID: 7996)
- winmgr21.exe (PID: 8040)
Reads mouse settings
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
- winmgr21.exe (PID: 7996)
- winmgr21.exe (PID: 8040)
- winmgr21.exe (PID: 7860)
- winmgr21.exe (PID: 5752)
Reads the computer name
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
- winmgr21.exe (PID: 7996)
- winmgr21.exe (PID: 8040)
- RegAsm.exe (PID: 1092)
- RegAsm.exe (PID: 1960)
- RegAsm.exe (PID: 5436)
- winmgr21.exe (PID: 5752)
- winmgr21.exe (PID: 7860)
Checks supported languages
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
- winmgr21.exe (PID: 7996)
- winmgr21.exe (PID: 8040)
- RegAsm.exe (PID: 1092)
- RegAsm.exe (PID: 1960)
- RegAsm.exe (PID: 5436)
- Important.exe (PID: 356)
- winmgr21.exe (PID: 7860)
- winmgr21.exe (PID: 5752)
Creates files in the program directory
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
- RegAsm.exe (PID: 1960)
- winmgr21.exe (PID: 8040)
- RegAsm.exe (PID: 1092)
- RegAsm.exe (PID: 5436)
Launching a file from a Registry key
- 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe (PID: 7484)
- winmgr21.exe (PID: 8040)
- RegAsm.exe (PID: 1092)
Manual execution by a user
- winmgr21.exe (PID: 8040)
- Important.exe (PID: 356)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 1092)
- RegAsm.exe (PID: 5436)
- winmgr21.exe (PID: 8040)
Create files in a temporary directory
- RegAsm.exe (PID: 5436)
The sample compiled with english language support
- RegAsm.exe (PID: 1092)
Disables trace logs
- RegAsm.exe (PID: 1092)
Checks proxy server information
- RegAsm.exe (PID: 1092)
- slui.exe (PID: 7592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:01:15 16:09:54+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 529920 |
| InitializedDataSize: | 1667584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x17850 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.0.0 |
| ProductVersionNumber: | 9.0.0.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | CHENGDU YIWO Tech Development Co., Ltd |
| FileDescription: | EaseUS Data Recovery Wizard |
| FileVersion: | 9.0.0 |
| InternalName: | Data Recovery Wizard |
| LegalCopyright: | Copyright (c) 2004-2015 EaseUS.ALL RIGHTS RESERVED. |
| OriginalFileName: | EaseUS Data Recovery Wizard |
| ProductName: | EaseUS Data Recovery Wizard |
| ProductVersion: | 9.0.0 |
Total processes
202
Monitored processes
61
Malicious processes
6
Suspicious processes
0
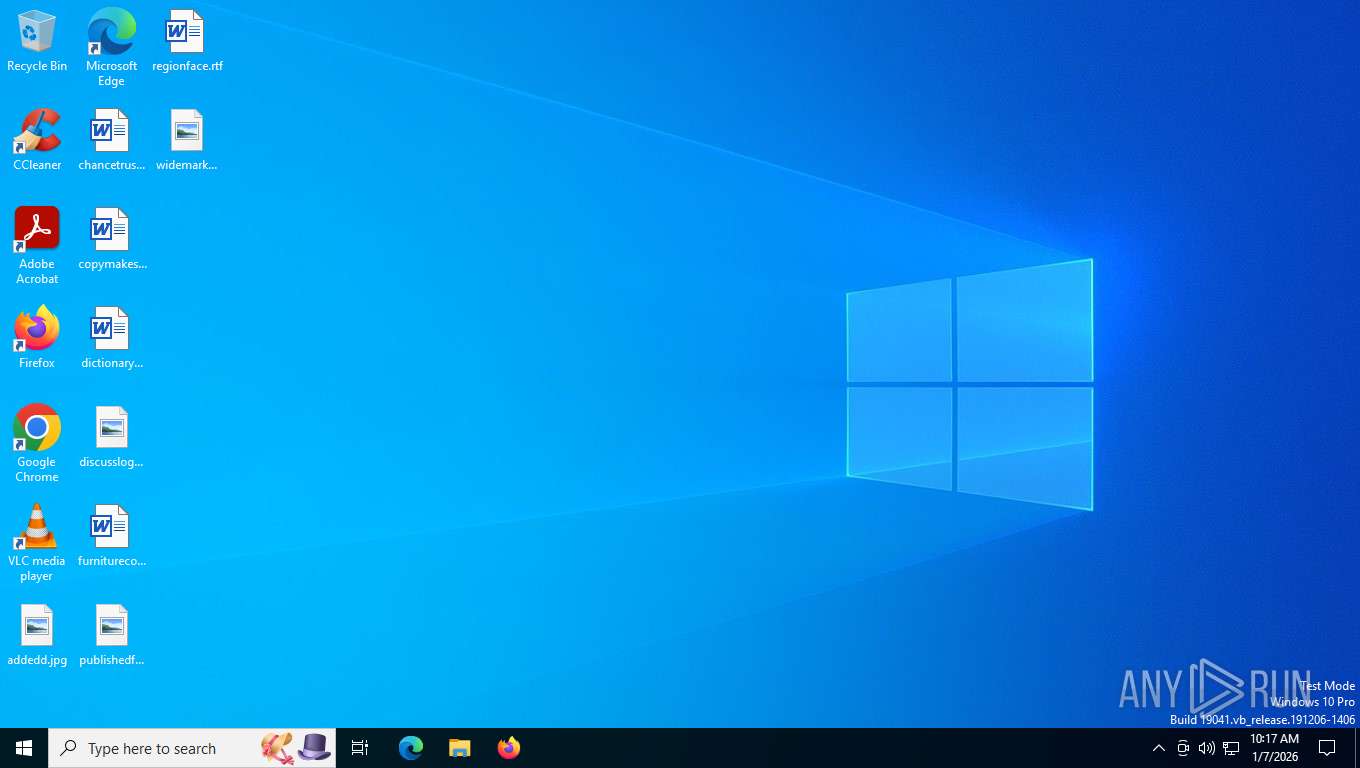
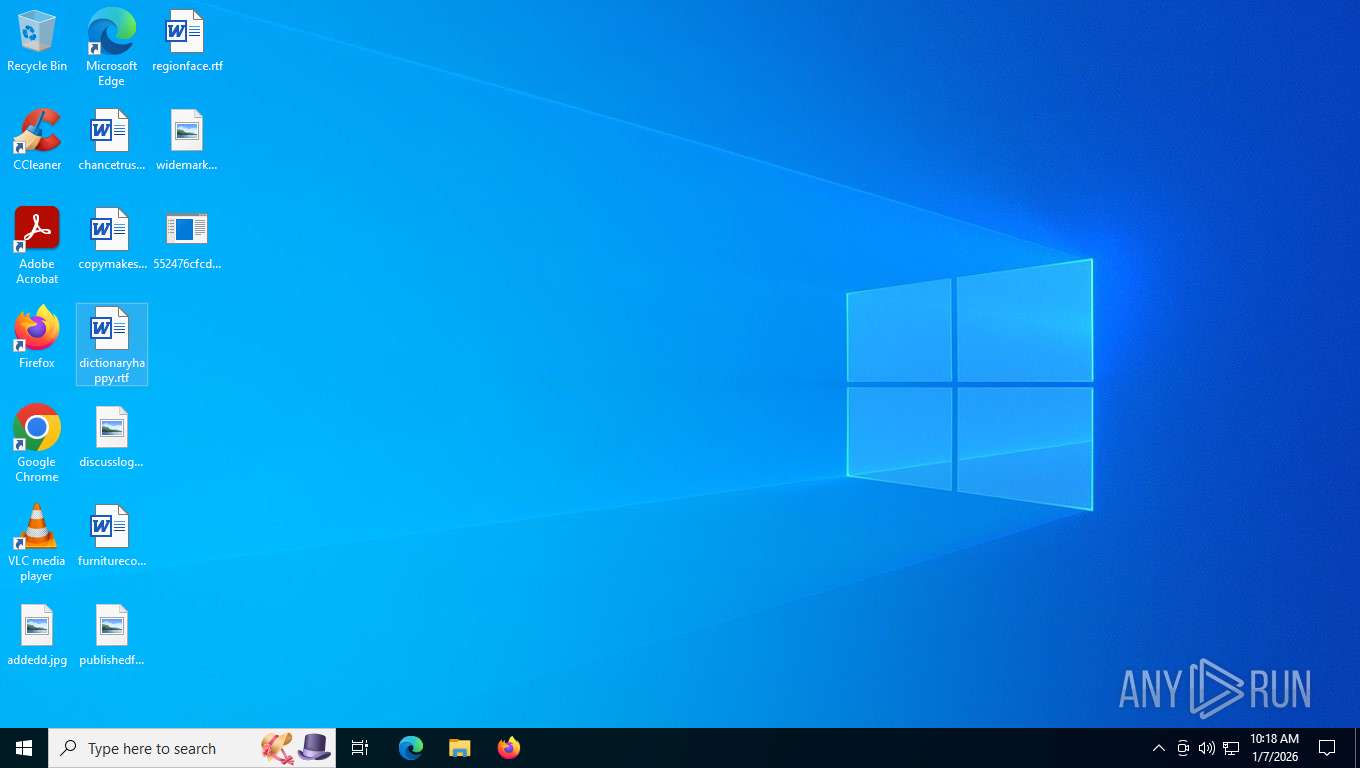
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | C:\ProgramData\Important.exe | C:\ProgramData\Important.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.9149 (WinRelRS6.050727-9100) Modules
| |||||||||||||||
| 468 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 816 | C:\WINDOWS\SysWOW64\schtasks.exe /create /sc minute /mo 1 /tn "winmgr21.exe" /tr "C:\ProgramData\winmgr21.exe" /f | C:\Windows\SysWOW64\schtasks.exe | — | winmgr21.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1092 | 0 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | winmgr21.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Version: 2.0.50727.9149 (WinRelRS6.050727-9100) Modules
| |||||||||||||||
| 1348 | C:\WINDOWS\SysWOW64\schtasks.exe /create /sc minute /mo 1 /tn "winmgr21.exe" /tr "C:\ProgramData\winmgr21.exe" /f | C:\Windows\SysWOW64\schtasks.exe | — | winmgr21.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1960 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" /stext C:\ProgramData\Mails.txt | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.9149 (WinRelRS6.050727-9100) Modules
| |||||||||||||||
| 1976 | C:\WINDOWS\SysWOW64\schtasks.exe /create /sc minute /mo 1 /tn "winmgr21.exe" /tr "C:\ProgramData\winmgr21.exe" /f | C:\Windows\SysWOW64\schtasks.exe | — | winmgr21.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 611
Read events
5 594
Write events
17
Delete events
0
Modification events
| (PID) Process: | (7484) 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 2 |
Value: C:\ProgramData\winmgr21.exe | |||
| (PID) Process: | (8040) winmgr21.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 2 |
Value: C:\ProgramData\winmgr21.exe | |||
| (PID) Process: | (1092) RegAsm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | e58494ba81888876514df0d106b49971 |
Value: C:\ProgramData\Important.exe | |||
| (PID) Process: | (1092) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1092) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1092) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1092) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1092) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1092) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1092) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
3
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5436 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\bhv593D.tmp | — | |
MD5:— | SHA256:— | |||
| 7484 | 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe | C:\Users\admin\Desktop\552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe:Zone.Identifier | text | |
MD5:6C72A5FCDB3C81DCC440E3616F704C5D | SHA256:CCC0133D8F43D3021EB667F86AE939F7F8EC83E727B8334F9E0FACCCD6D01063 | |||
| 8040 | winmgr21.exe | C:\ProgramData\winmgr21.exe:Zone.Identifier | text | |
MD5:6C72A5FCDB3C81DCC440E3616F704C5D | SHA256:CCC0133D8F43D3021EB667F86AE939F7F8EC83E727B8334F9E0FACCCD6D01063 | |||
| 1092 | RegAsm.exe | C:\ProgramData\Important.exe | executable | |
MD5:A64DACA3CFBCD039DF3EC29D3EDDD001 | SHA256:403752009F29381D5E4036B8BE94589C89188F9CE8EF5F86959EAAADA019ED36 | |||
| 7484 | 552476cfcdcb965fbe7cc8a7689b3a2dfdde5dcc1548895a22ccaef19d2b254b.exe | C:\ProgramData\winmgr21.exe | executable | |
MD5:801C6059D58883D17EC6BD4BC9BEF706 | SHA256:2072521ECC59C5B9076960A0C3421B9E7F37AA3B51B397260A83766367C8500C | |||
| 1092 | RegAsm.exe | C:\ProgramData\DESKTOP-JGLLJLD_1_7_10_18_1.jpg | image | |
MD5:9D65D17439AE402DD633F54C3A9BFB31 | SHA256:87656D5A7D1932FB02BA05F9B81AA63274F1CC499869DDBA29D4435E7228AC9A | |||
| 5436 | RegAsm.exe | C:\ProgramData\Browsers.txt | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
44
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=562&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
5180 | RUXIMICS.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/RUXIM?os=Windows&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3623&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&FlightRing=Retail&AttrDataVer=186&App=RUXIM&AppVer=&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
4404 | svchost.exe | GET | 200 | 2.16.164.104:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.104:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5180 | RUXIMICS.exe | GET | 200 | 2.16.164.104:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4404 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4404 | svchost.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaasMedic?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&appVer=10.0.19041.3758&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4 | unknown | text | 3.41 Kb | whitelisted |
4684 | svchost.exe | POST | 200 | 40.126.31.129:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.74:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
4684 | svchost.exe | POST | 200 | 40.126.31.129:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4404 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5180 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4404 | svchost.exe | 2.16.164.104:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.104:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5180 | RUXIMICS.exe | 2.16.164.104:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
4404 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
vaibaht.com |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |