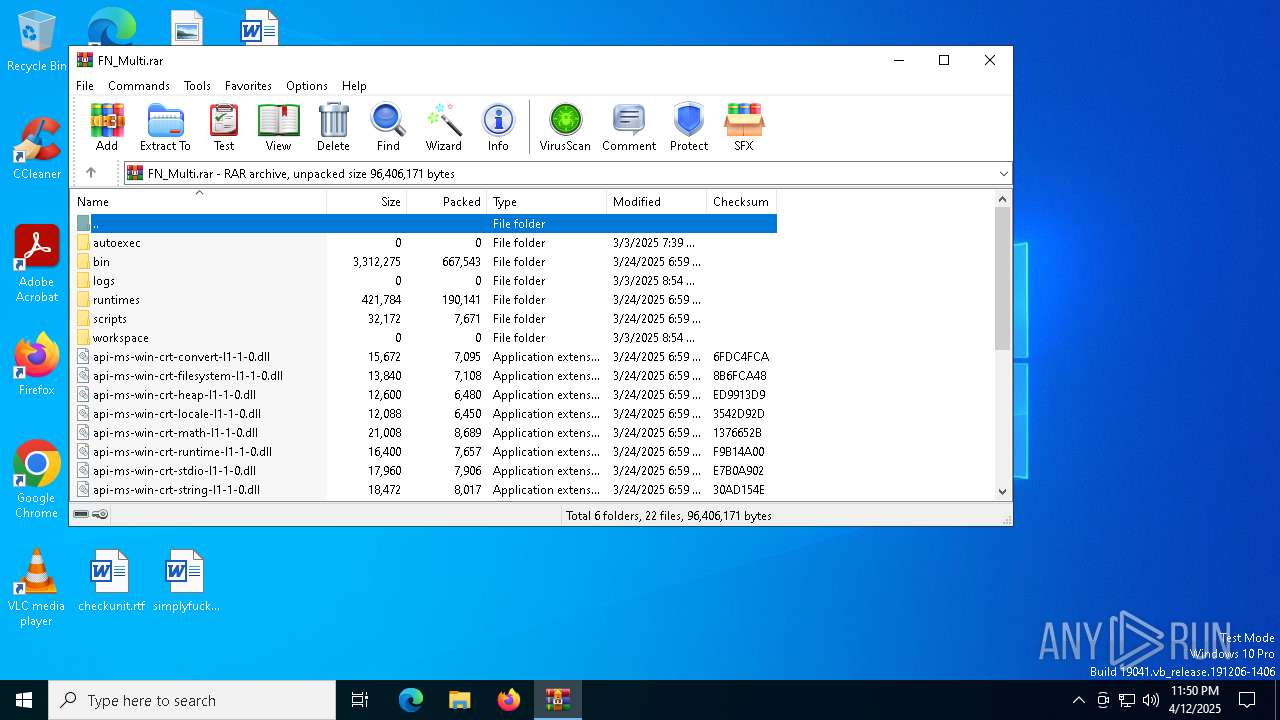
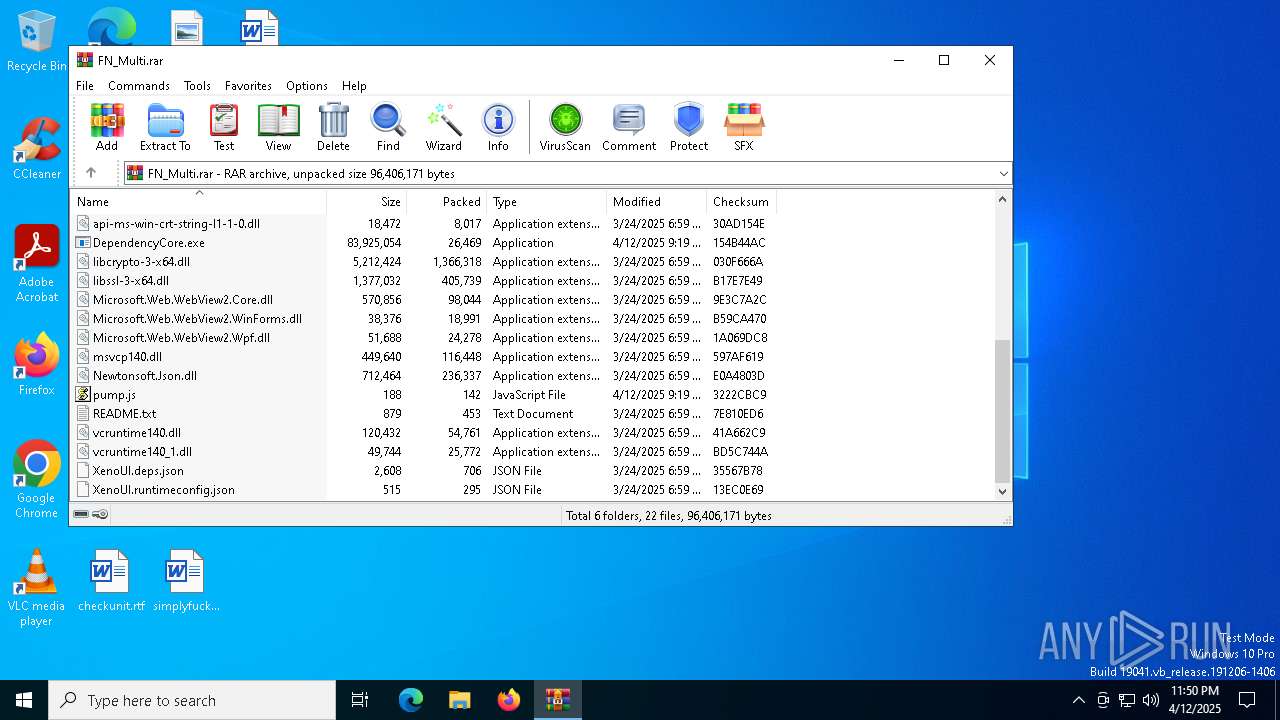
| File name: | FN_Multi.rar |
| Full analysis: | https://app.any.run/tasks/57b8a7a9-56c7-4e9f-a945-cae3d314e8be |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 12, 2025, 23:50:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 397A0E7D4342529E0F29336D0EE5023D |
| SHA1: | 0E020B10C816125B253F52F8BF2440F5D233B8D3 |
| SHA256: | 551F2E1DA2F7C2F60F13CB948C65786EBD62E4E0DC98190882D0BC933745720A |
| SSDEEP: | 98304:ecsWeTdY/dUAwrq7Hy8gZrZLLxfgDE3OuT5vsJzKWcBaEZJtoKxr6Aqu51qJh6bH:WNK4IyIy |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 6724)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- AddInProcess32.exe (PID: 7568)
LUMMA mutex has been found
- AddInProcess32.exe (PID: 7568)
- AddInProcess32.exe (PID: 6644)
Actions looks like stealing of personal data
- AddInProcess32.exe (PID: 7568)
- AddInProcess32.exe (PID: 6644)
Steals credentials from Web Browsers
- AddInProcess32.exe (PID: 7568)
- AddInProcess32.exe (PID: 6644)
SUSPICIOUS
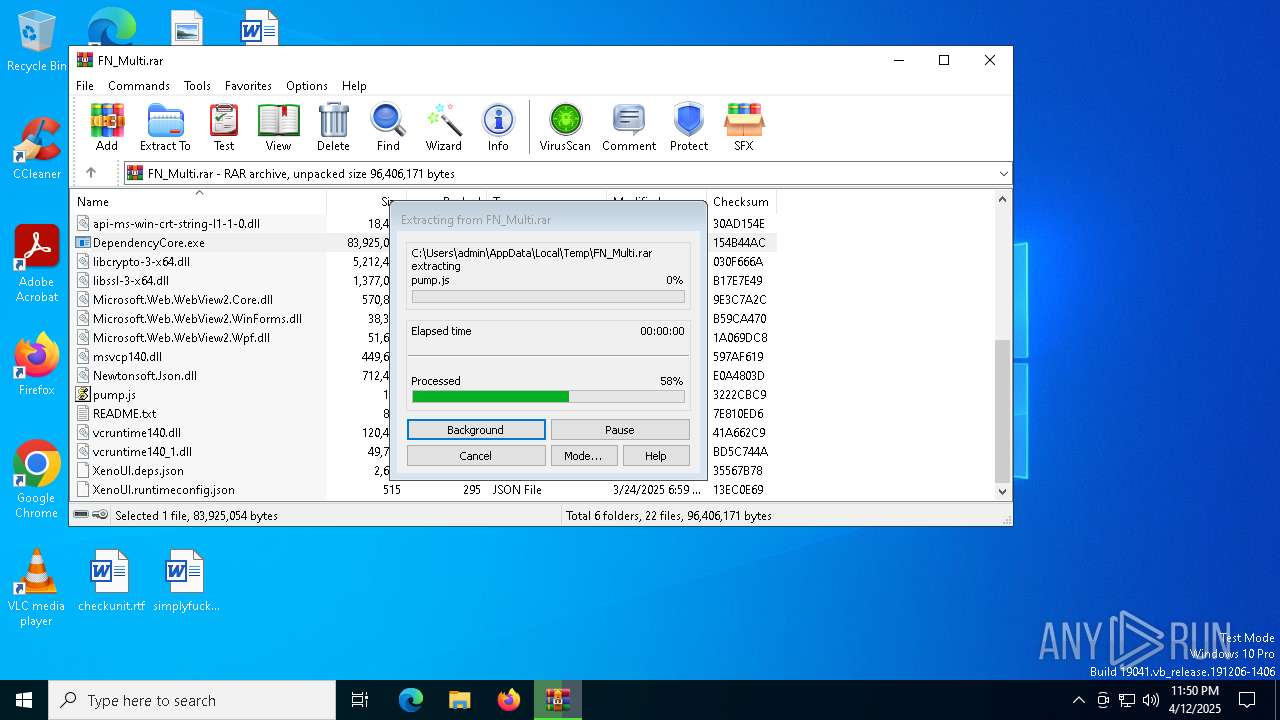
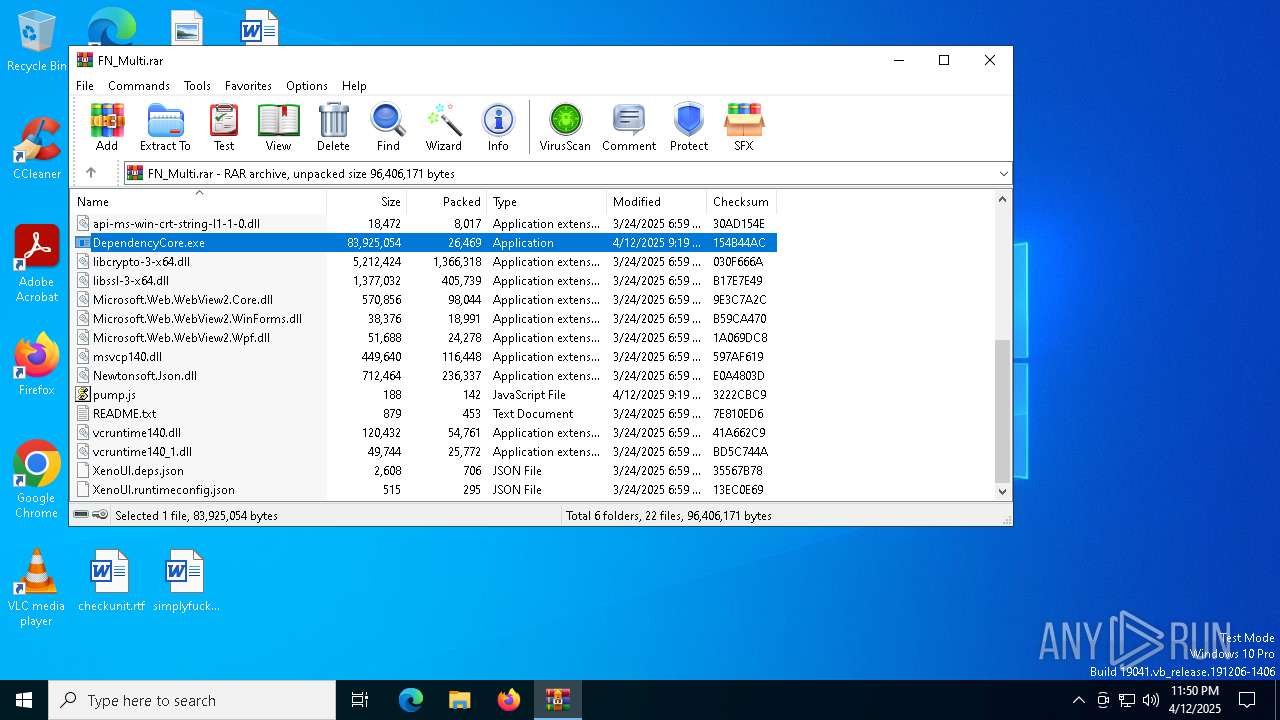
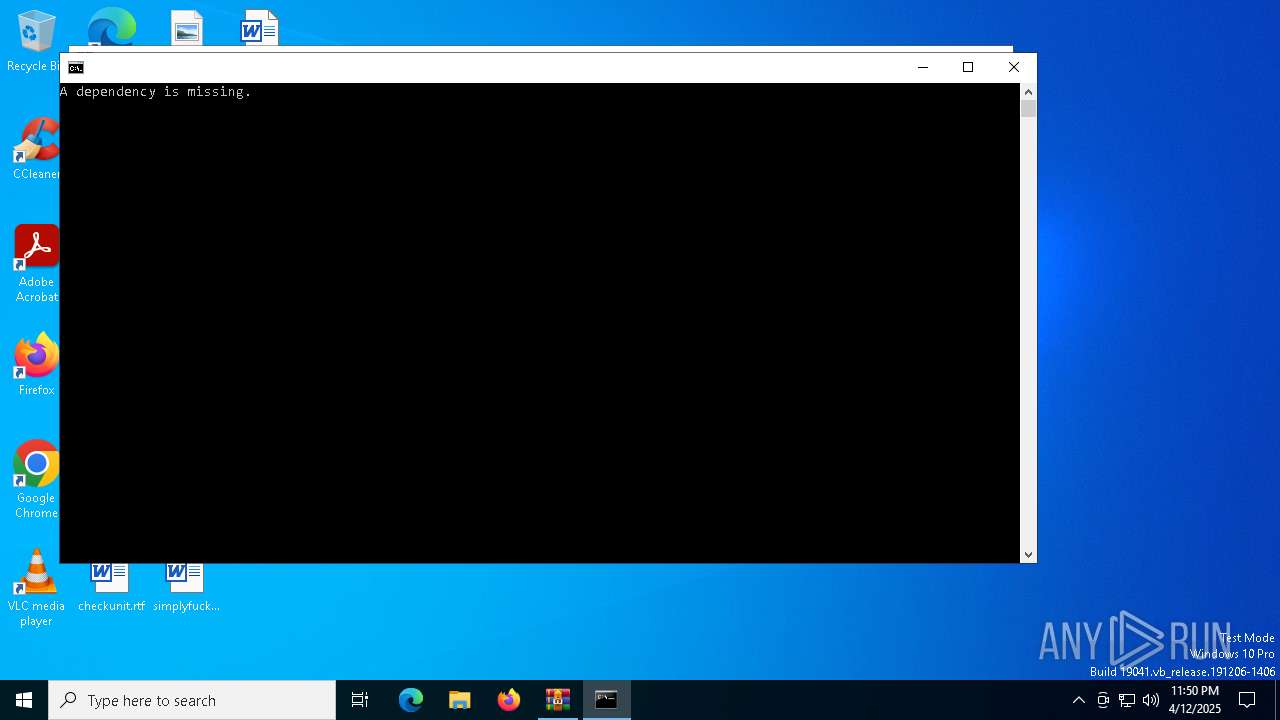
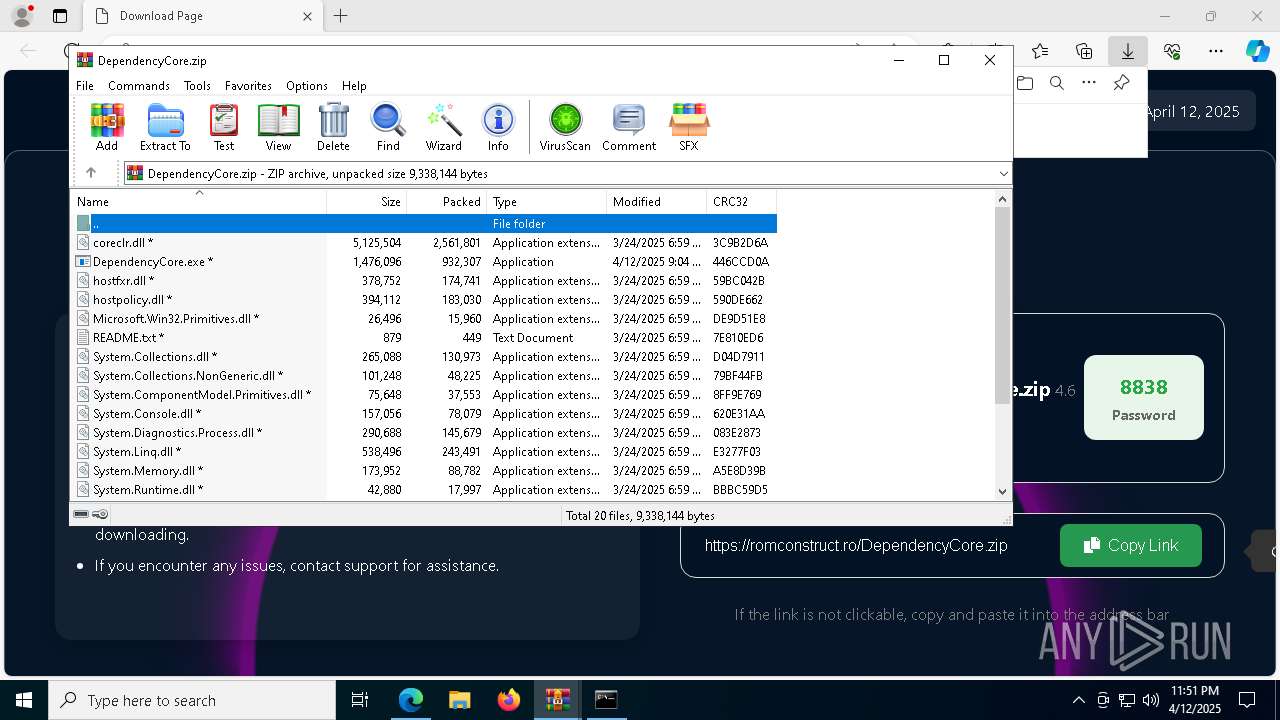
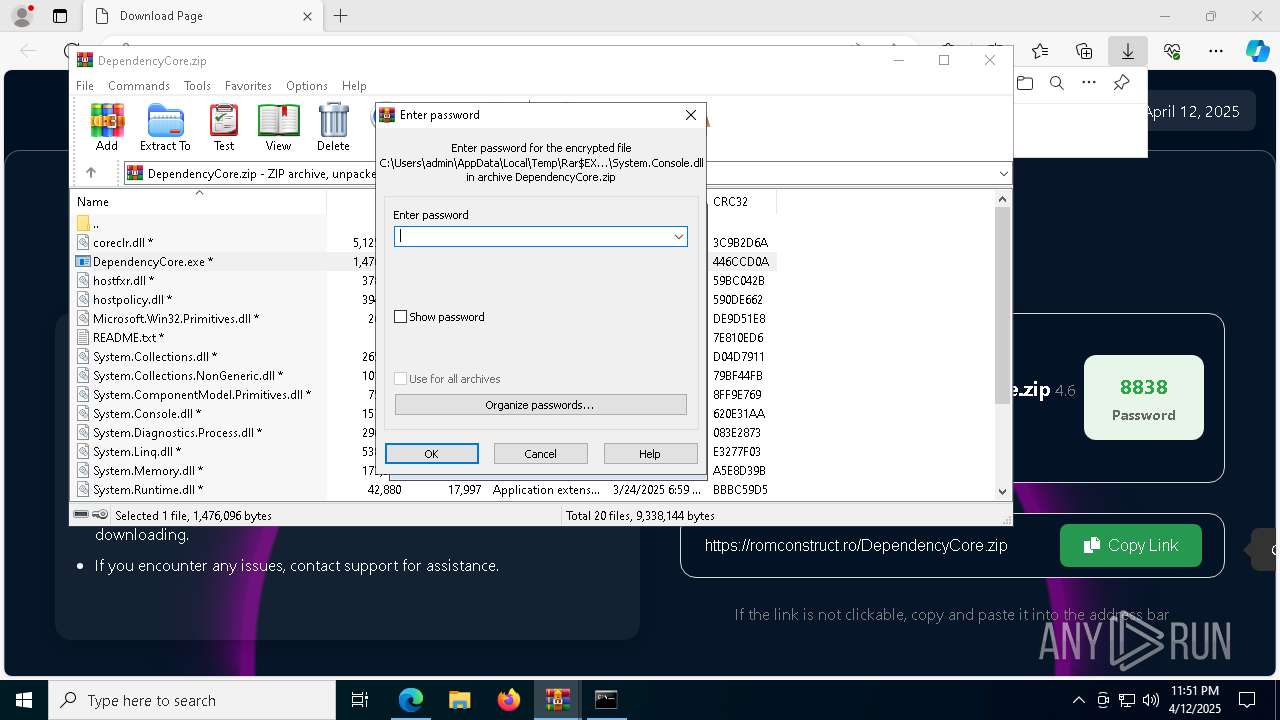
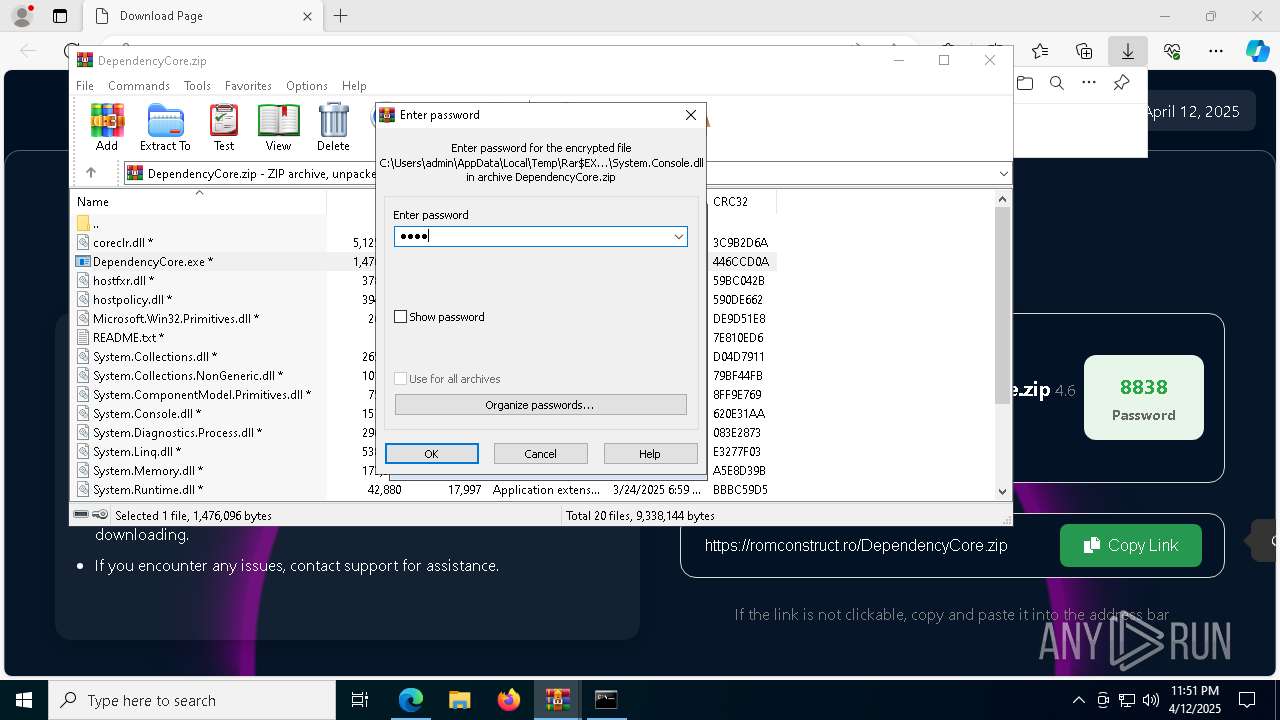
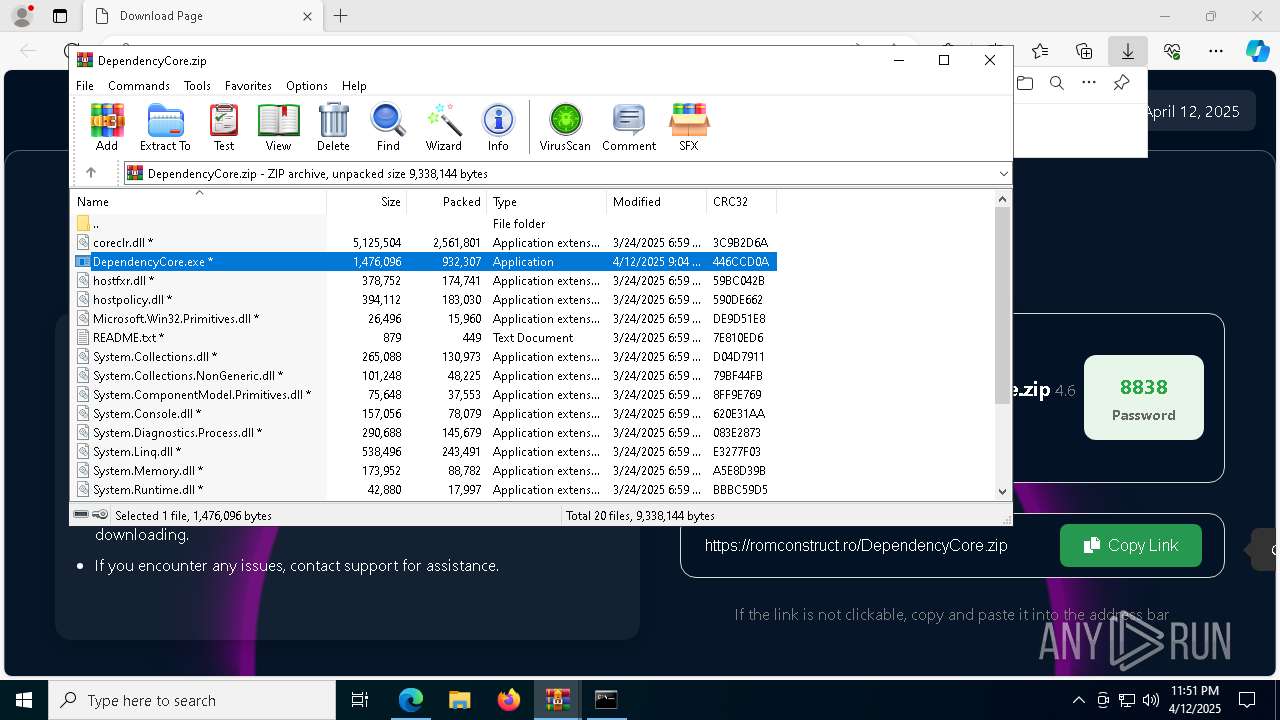
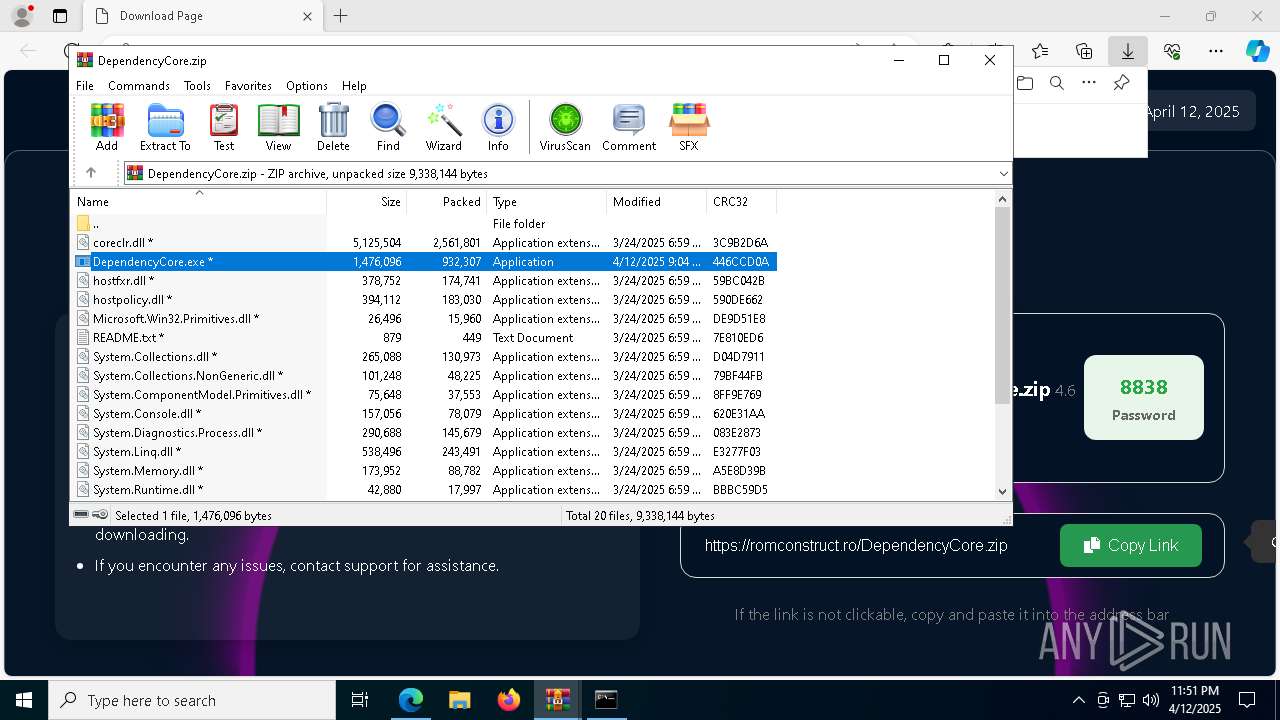
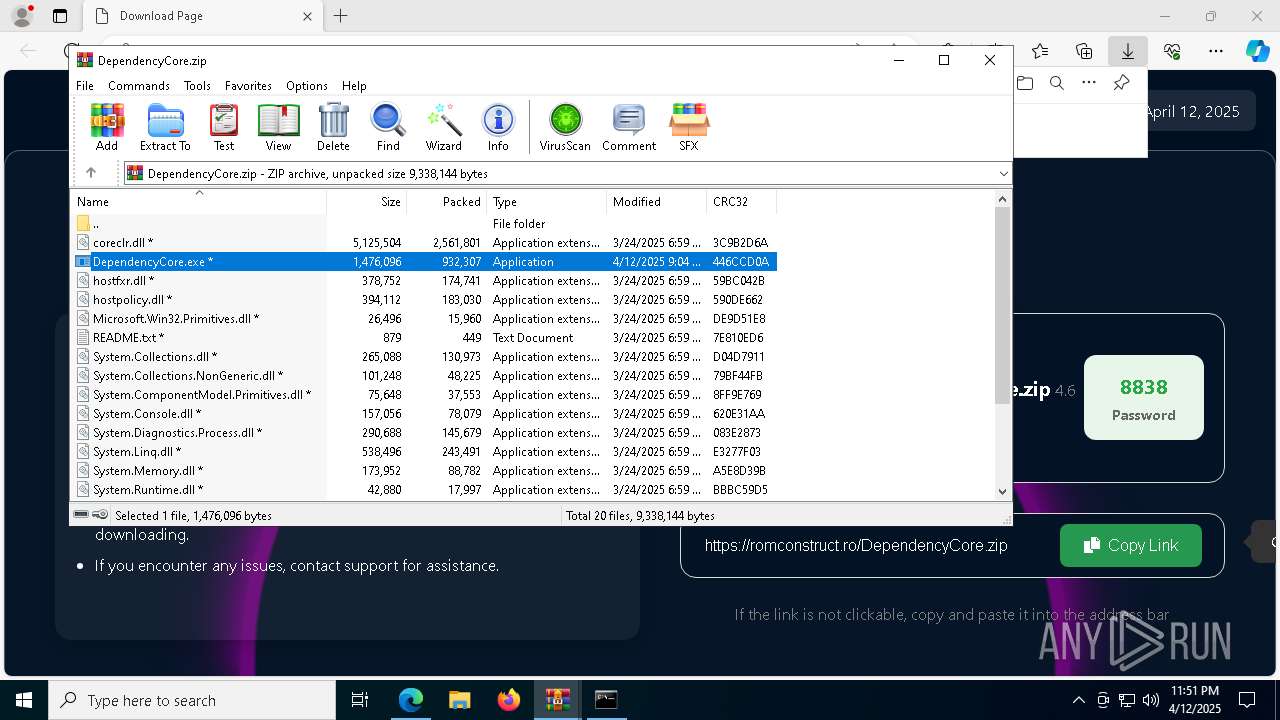
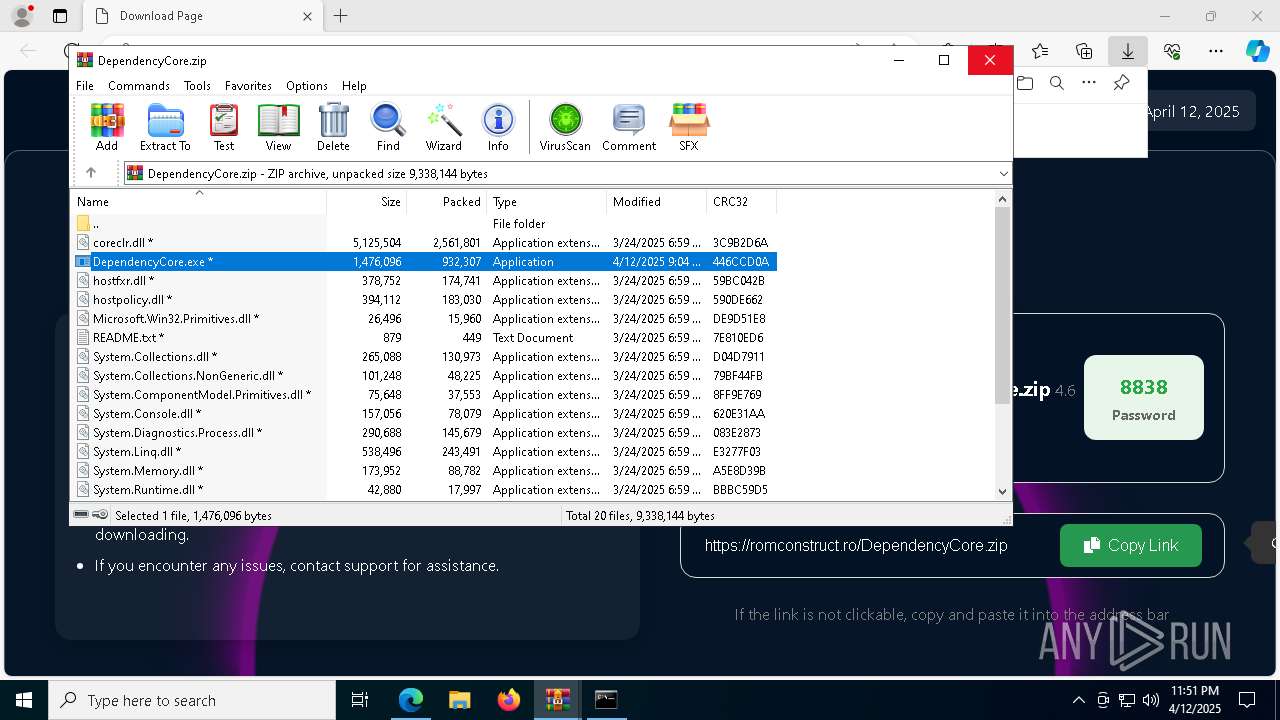
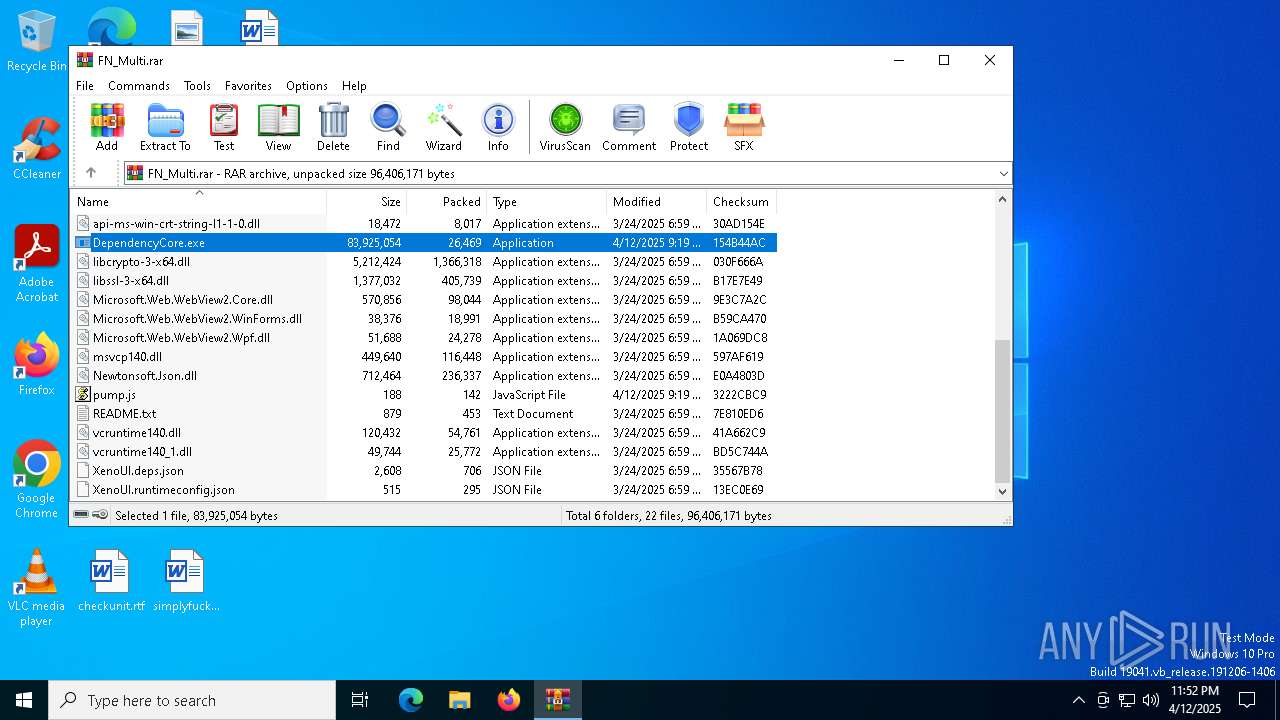
Process drops legitimate windows executable
- WinRAR.exe (PID: 7316)
- WinRAR.exe (PID: 3008)
Reads security settings of Internet Explorer
- DependencyCore.exe (PID: 7920)
- WinRAR.exe (PID: 7316)
- WinRAR.exe (PID: 3008)
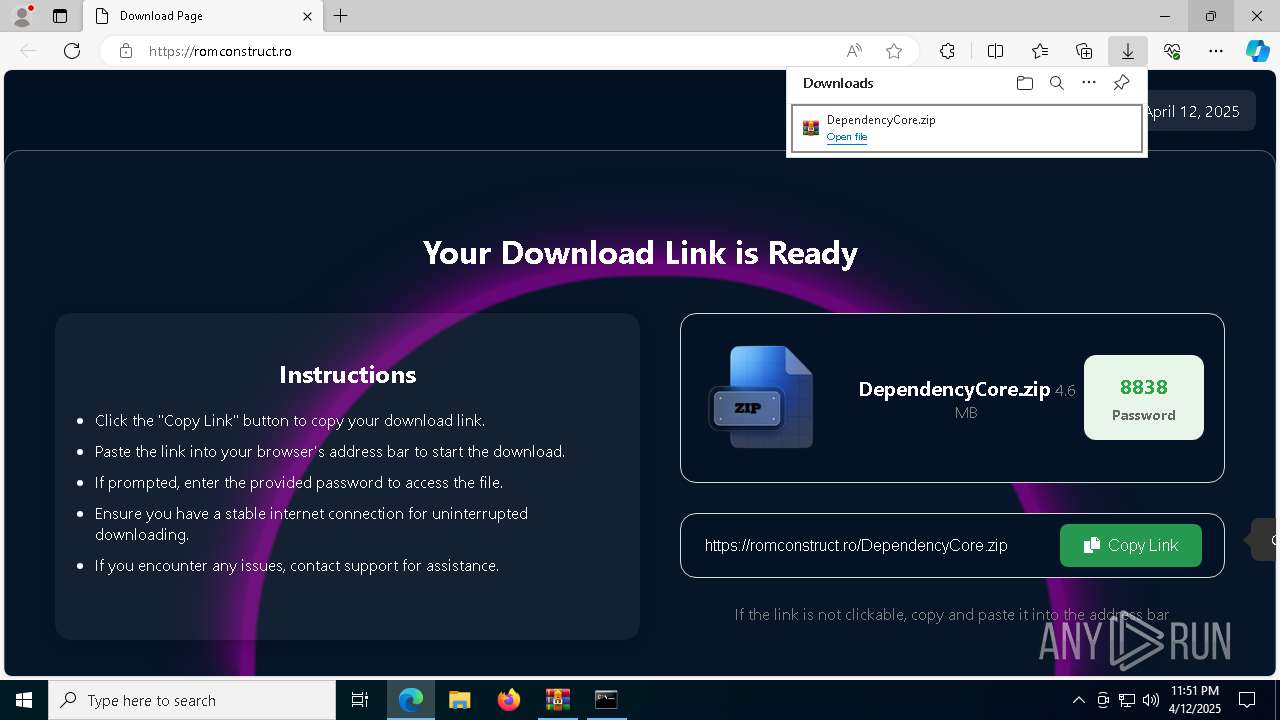
Starts CMD.EXE for commands execution
- DependencyCore.exe (PID: 7920)
- DependencyCore.exe (PID: 4784)
Hides command output
- cmd.exe (PID: 7960)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 132)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7960)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 132)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 3008)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7648)
Executable content was dropped or overwritten
- cmd.exe (PID: 132)
Application launched itself
- AddInProcess32.exe (PID: 7732)
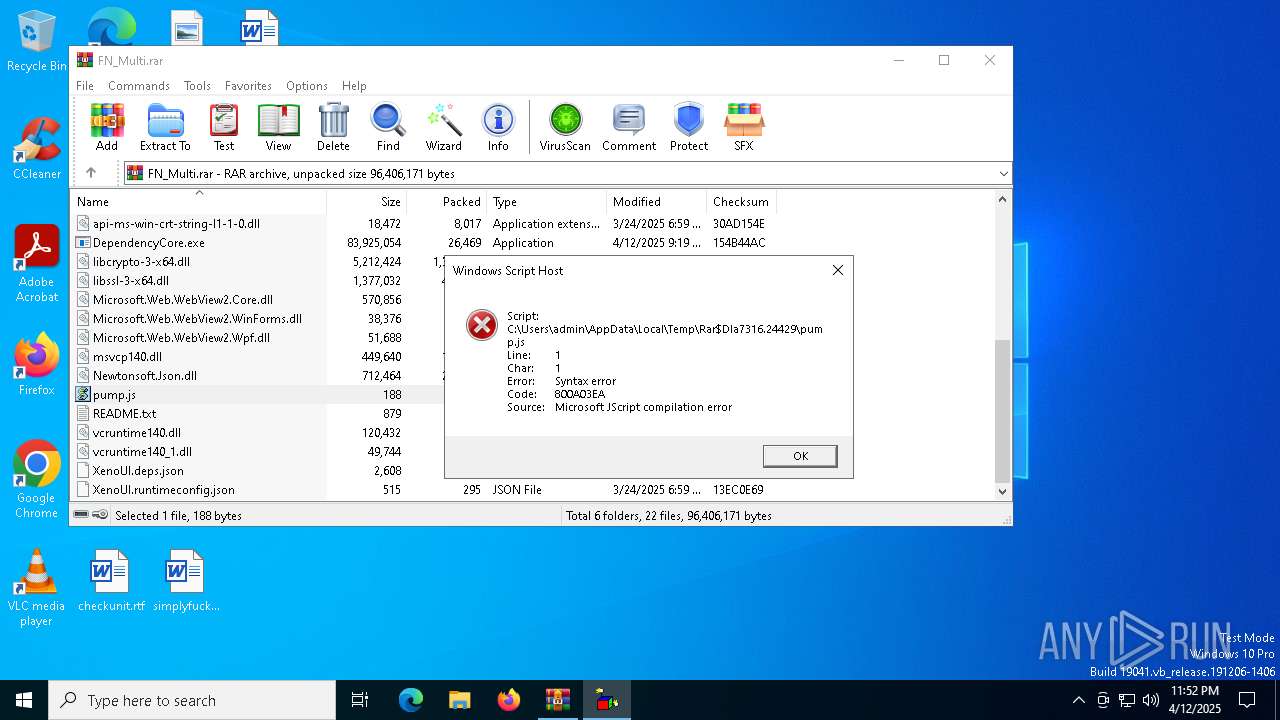
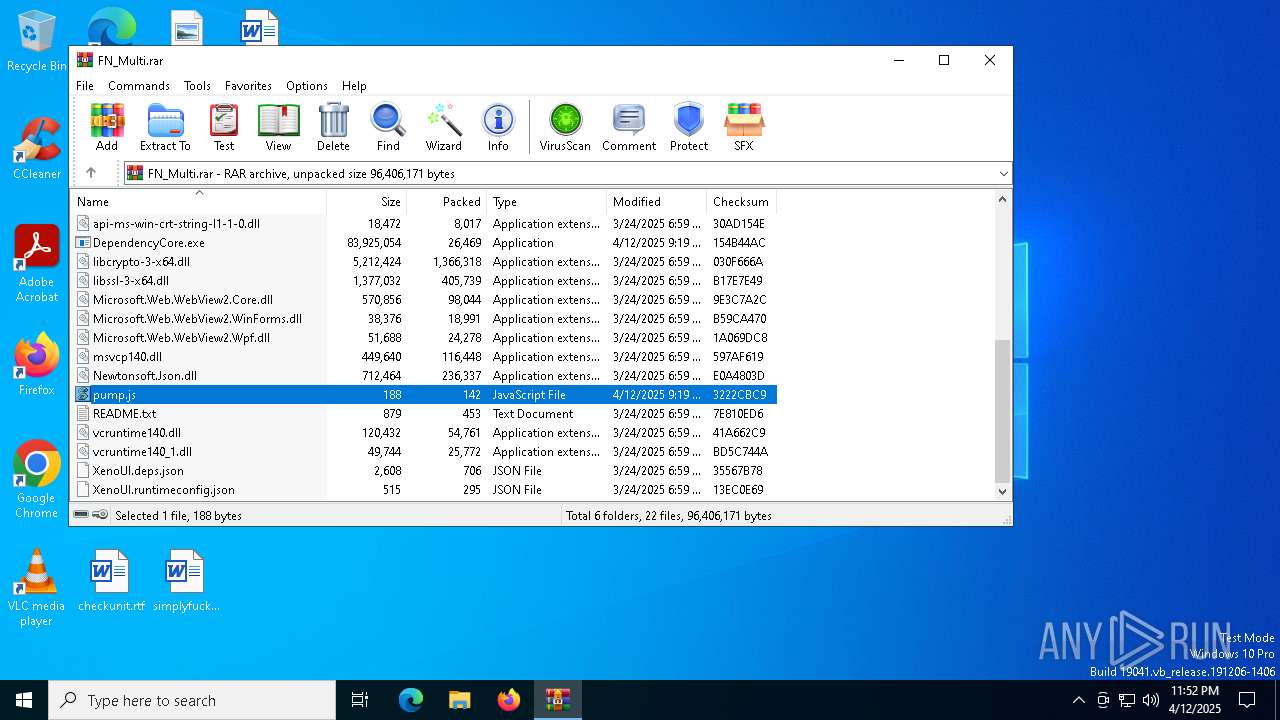
The process executes JS scripts
- WinRAR.exe (PID: 7316)
The executable file from the user directory is run by the CMD process
- local.exe (PID: 6564)
Contacting a server suspected of hosting an CnC
- AddInProcess32.exe (PID: 7568)
- svchost.exe (PID: 2196)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- AddInProcess32.exe (PID: 6644)
Searches for installed software
- AddInProcess32.exe (PID: 7568)
- AddInProcess32.exe (PID: 6644)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7316)
- WinRAR.exe (PID: 3008)
- cmd.exe (PID: 132)
Checks supported languages
- DependencyCore.exe (PID: 7920)
- identity_helper.exe (PID: 7552)
- DependencyCore.exe (PID: 4784)
- identity_helper.exe (PID: 4212)
- AddInProcess32.exe (PID: 7732)
- local.exe (PID: 6564)
- AddInProcess32.exe (PID: 7568)
- AddInProcess32.exe (PID: 6644)
Process checks computer location settings
- DependencyCore.exe (PID: 7920)
Reads the computer name
- DependencyCore.exe (PID: 7920)
- identity_helper.exe (PID: 7552)
- DependencyCore.exe (PID: 4784)
- identity_helper.exe (PID: 4212)
- AddInProcess32.exe (PID: 7568)
- local.exe (PID: 6564)
- AddInProcess32.exe (PID: 7732)
- AddInProcess32.exe (PID: 6644)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7316)
- WinRAR.exe (PID: 3008)
Application launched itself
- msedge.exe (PID: 2564)
- msedge.exe (PID: 7940)
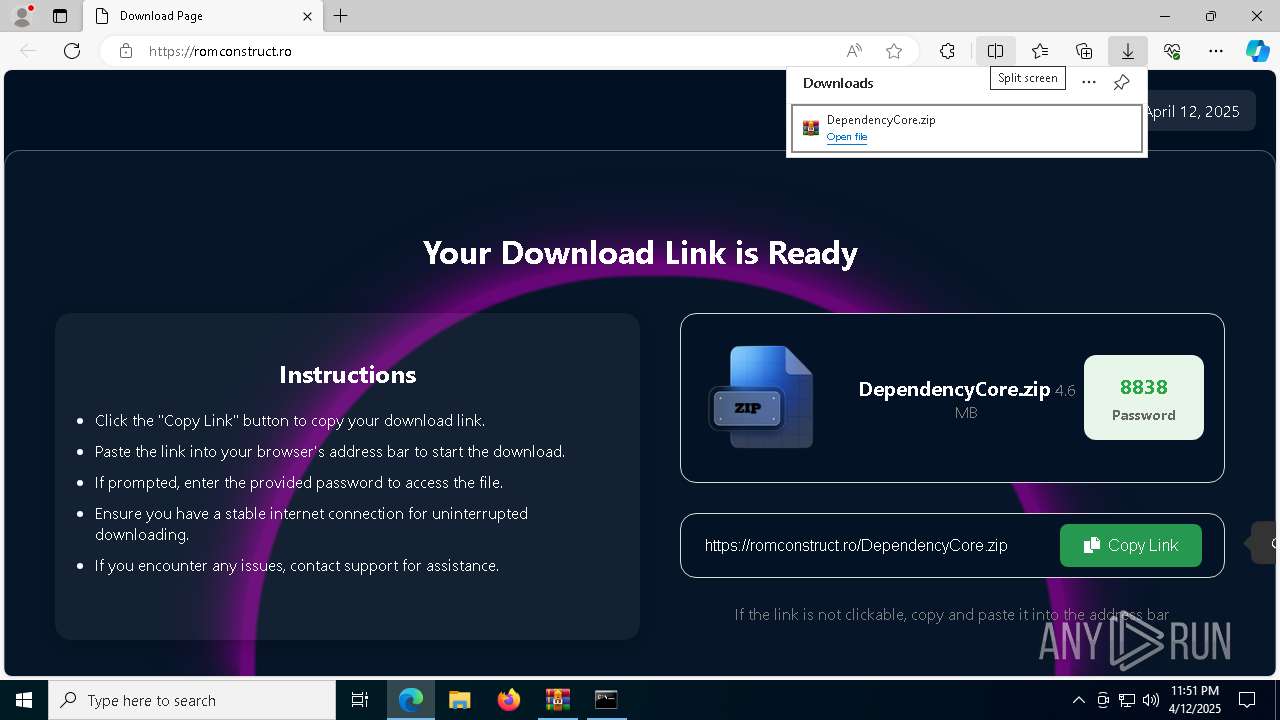
Autorun file from Downloads
- msedge.exe (PID: 2564)
- msedge.exe (PID: 2240)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2564)
- WinRAR.exe (PID: 7316)
Reads Environment values
- identity_helper.exe (PID: 4212)
- identity_helper.exe (PID: 7552)
Reads the machine GUID from the registry
- DependencyCore.exe (PID: 4784)
- AddInProcess32.exe (PID: 7732)
- local.exe (PID: 6564)
Reads the software policy settings
- slui.exe (PID: 7484)
- slui.exe (PID: 3884)
- AddInProcess32.exe (PID: 7568)
- AddInProcess32.exe (PID: 6644)
Checks proxy server information
- slui.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 7108 |
| UncompressedSize: | 13840 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | api-ms-win-crt-filesystem-l1-1-0.dll |
Total processes
214
Monitored processes
82
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "cmd" /c ping 127.0.0.1 -n 8 > nul && copy "C:\Users\admin\AppData\Local\Temp\Rar$EXb3008.18841\DependencyCore.exe" "C:\Users\admin\AppData\Local\local.exe" && ping 127.0.0.1 -n 8 > nul && "C:\Users\admin\AppData\Local\local.exe" | C:\Windows\SysWOW64\cmd.exe | DependencyCore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=5140 --field-trial-handle=2420,i,15940989664735163780,16669487115248735593,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5064 --field-trial-handle=2376,i,10314101868943894059,97744347139972890,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa7316.24429\pump.js" | C:\Windows\System32\wscript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1280 | ping 127.0.0.1 -n 8 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5344 --field-trial-handle=2420,i,15940989664735163780,16669487115248735593,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6948 --field-trial-handle=2420,i,15940989664735163780,16669487115248735593,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
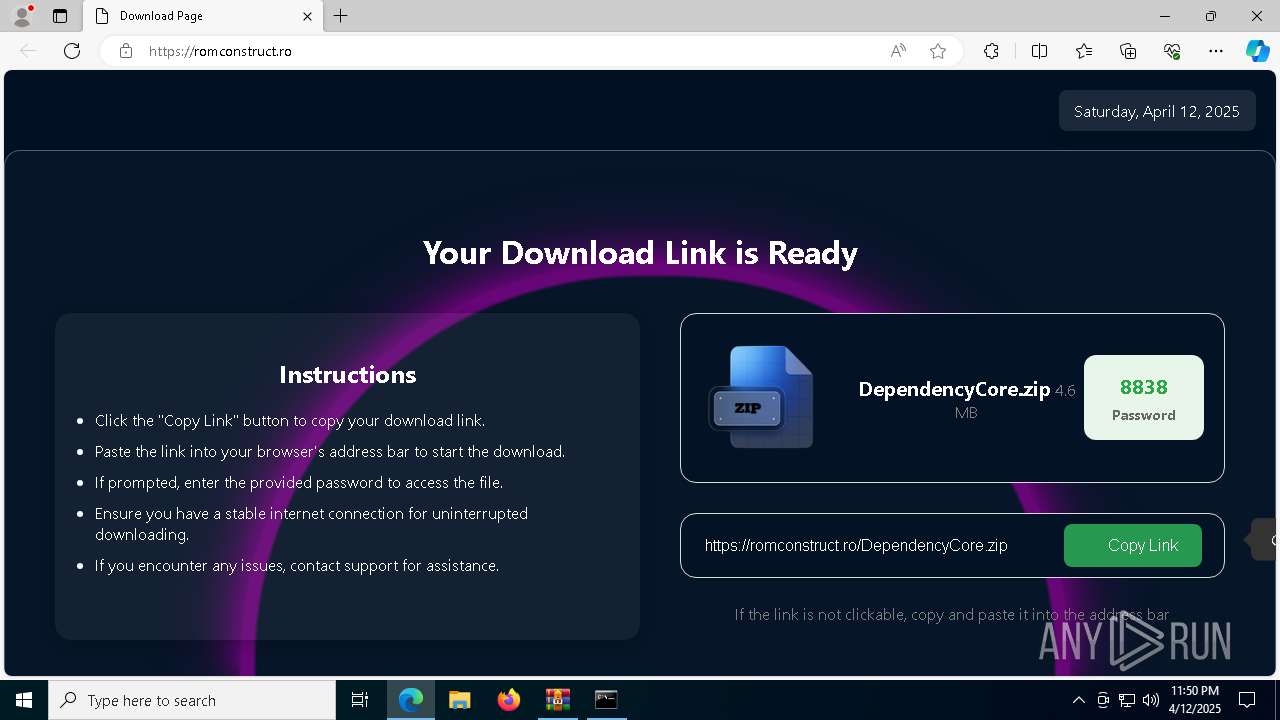
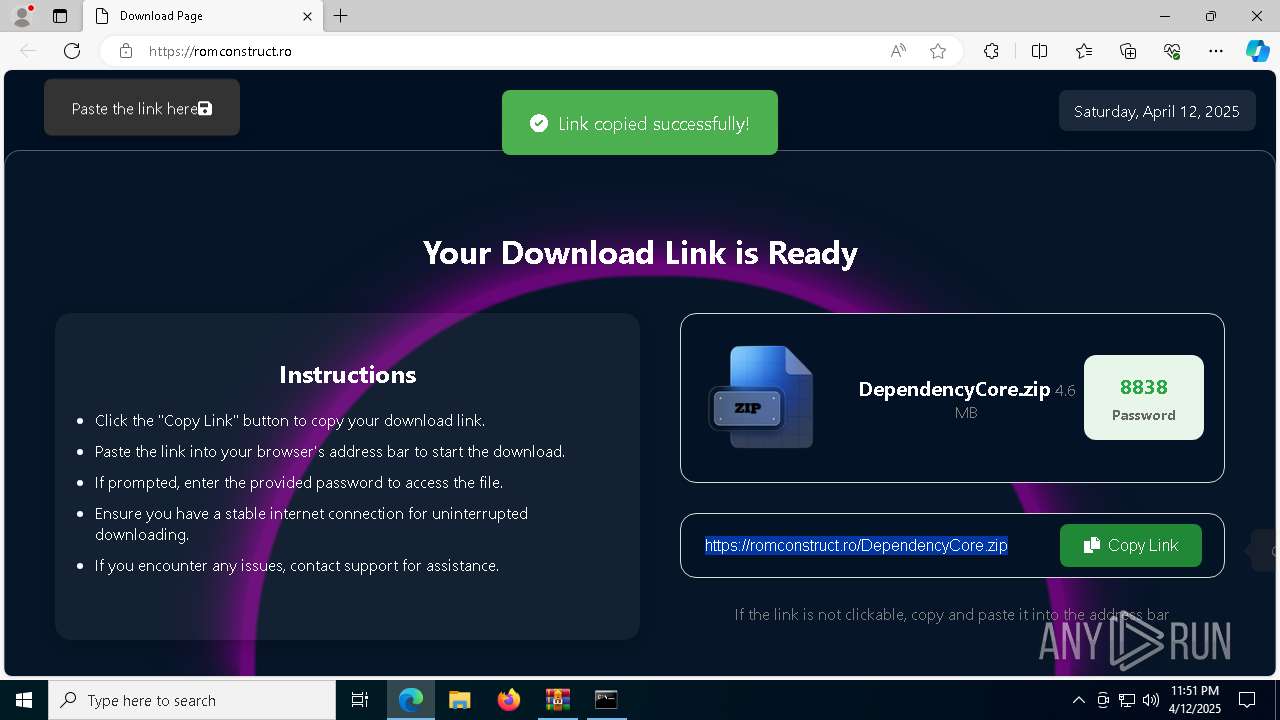
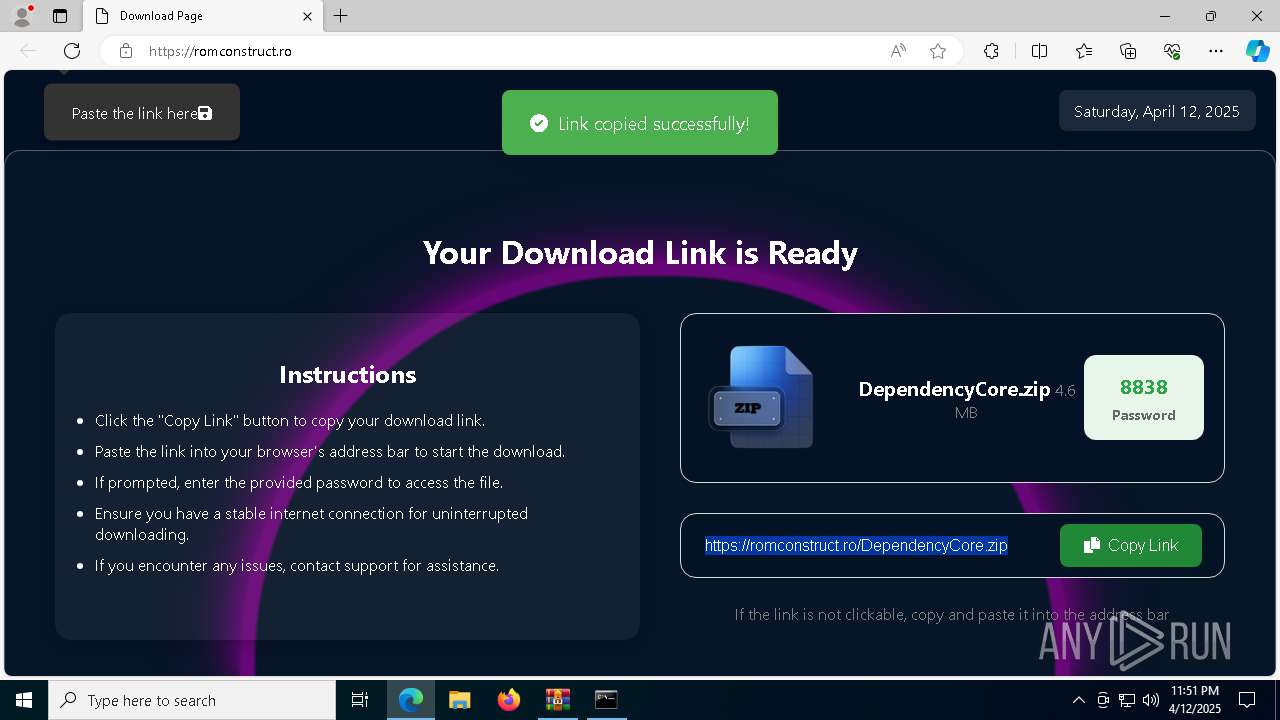
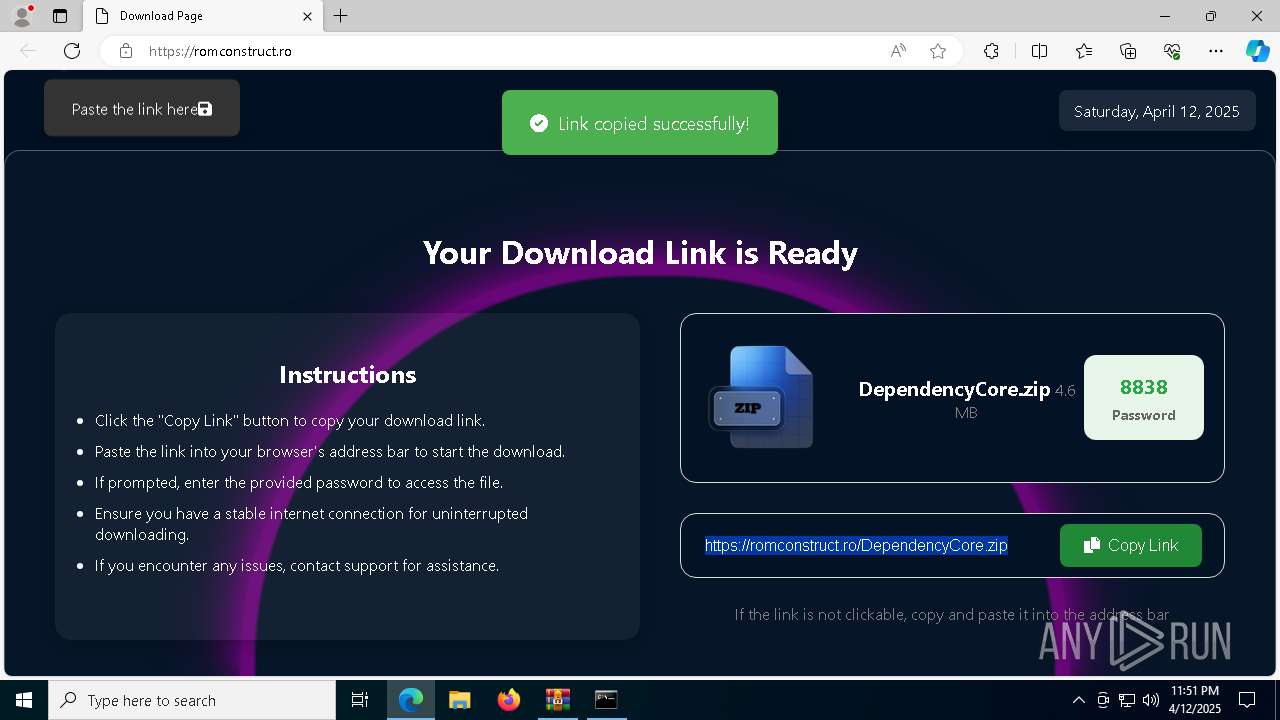
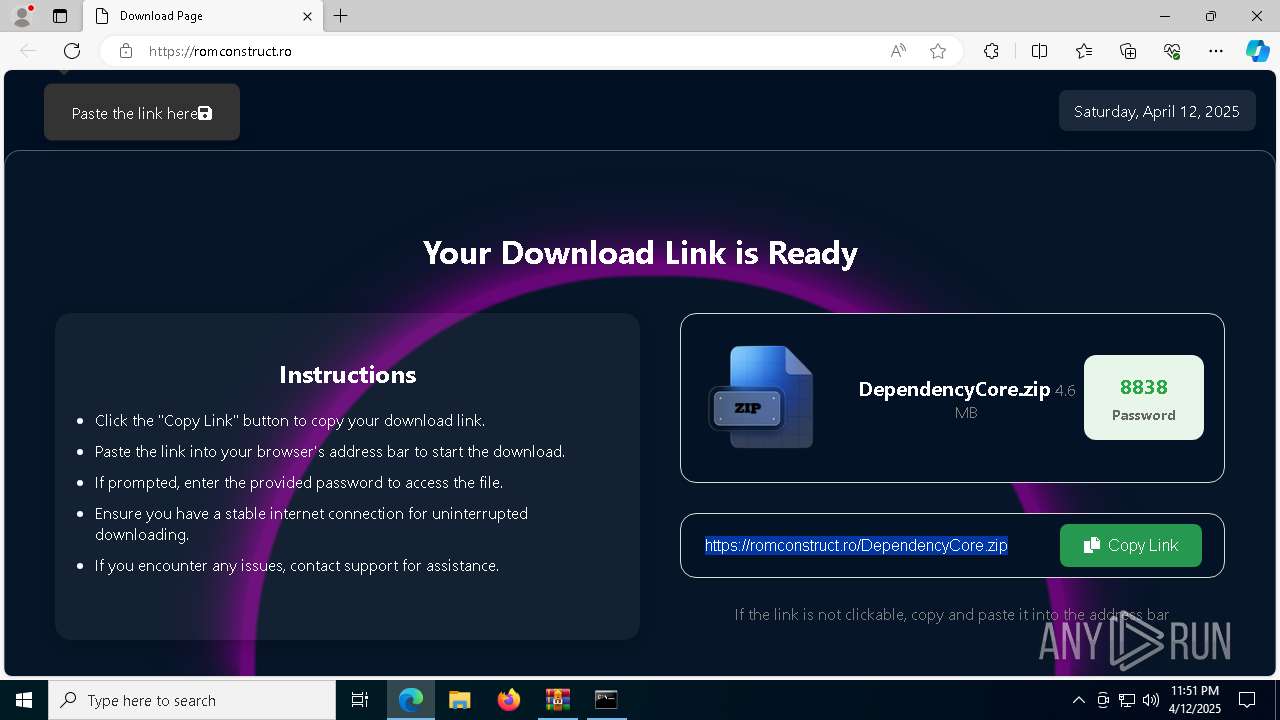
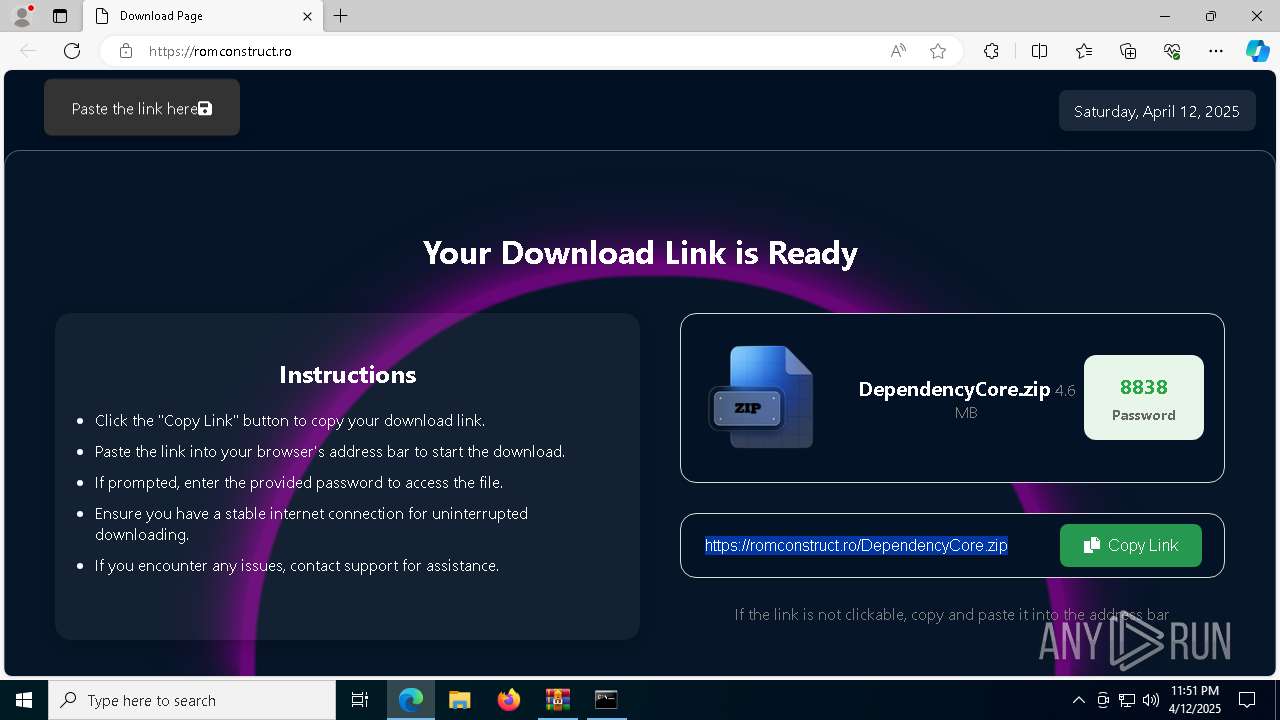
| 2564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://romconstruct.ro/ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
17 847
Read events
17 777
Write events
70
Delete events
0
Modification events
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\FN_Multi.rar | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7960) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (7960) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
50
Suspicious files
282
Text files
95
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
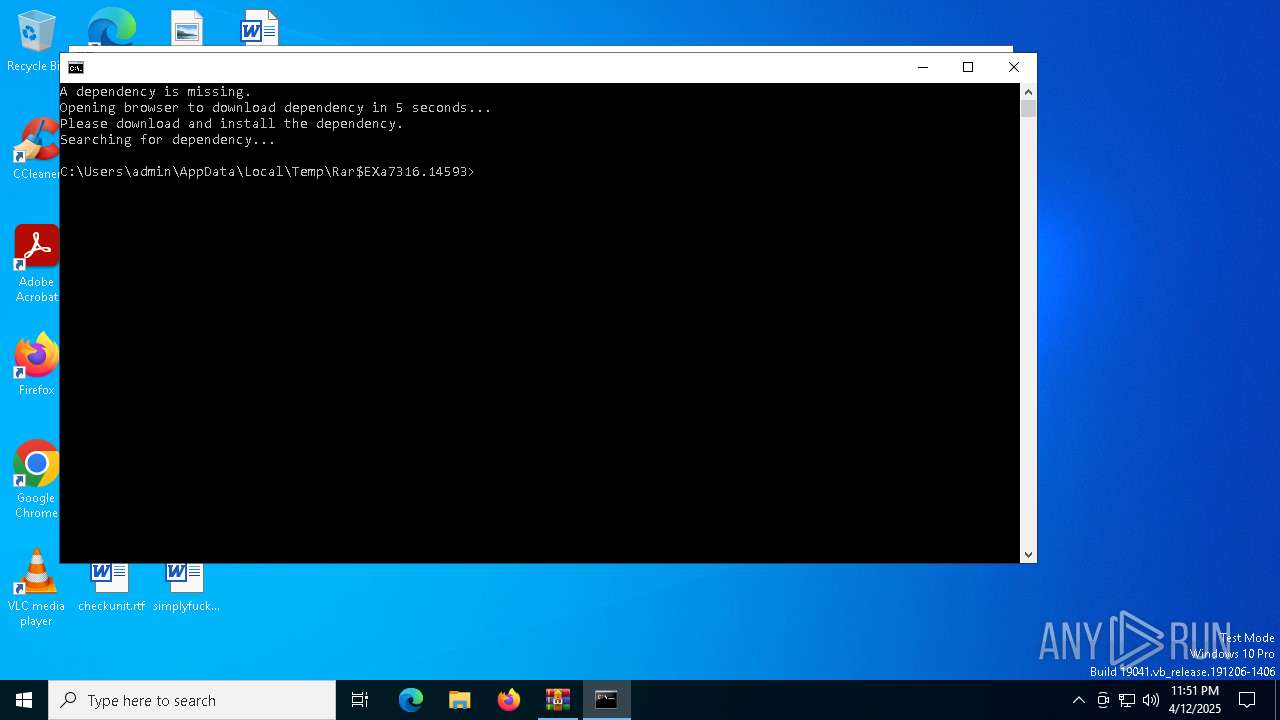
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7316.14593\DependencyCore.exe | — | |
MD5:— | SHA256:— | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7316.14593\api-ms-win-crt-locale-l1-1-0.dll | executable | |
MD5:FF48B107B2449A647C64BAABD49408A1 | SHA256:7BB8644E565AD4BCFD890F9044BCCB4D99953A740E9A500B1F820B2FDC3FC240 | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7316.14593\api-ms-win-crt-math-l1-1-0.dll | executable | |
MD5:E10E077BB06209AEDD0D0D378C758F73 | SHA256:8A7BFF1C918539A75C25568DB25933D653C003E016FD7791A37186B42BBB7C20 | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7316.14593\api-ms-win-crt-stdio-l1-1-0.dll | executable | |
MD5:429C26ED27A026442F89C95FF16CE8C2 | SHA256:2A466648AFFD3D51B944F563BB65046A3DA91006A0D90FB2C0B123487A1FC1B3 | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7316.14593\api-ms-win-crt-string-l1-1-0.dll | executable | |
MD5:0F593E50BE4715AA8E1F6EB39434EDD5 | SHA256:BF4EA10BE1B64C442AC0CCF4BDF69F6703467176A27E9E14A488D26448A6E179 | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7316.14593\api-ms-win-crt-heap-l1-1-0.dll | executable | |
MD5:98DA186FD7D7873C164A51C5D7B77F1A | SHA256:80139E4CAA379D87B1D1DAFC23ACE71D2B330368115F6314140D4AE59C2A78E8 | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7316.14593\api-ms-win-crt-runtime-l1-1-0.dll | executable | |
MD5:F91E1FF896B5616919AC97C7095C513E | SHA256:07382C0D91DAD2BB6BA8BD06EA02F12C57ABF7C4E5A70672E9F2954D09A4FFD4 | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7316.14593\Microsoft.Web.WebView2.Core.dll | executable | |
MD5:B037CA44FD19B8EEDB6D5B9DE3E48469 | SHA256:11E88B2CA921E5C88F64567F11BD83CBC396C10365D40972F3359FCC7965D197 | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7316.14593\api-ms-win-crt-filesystem-l1-1-0.dll | executable | |
MD5:42A2A95F1BB940D01F55EB1674A81FE2 | SHA256:51541EC6684B43157A85EA46A42EBED4555BE06BED0D0D07FF3EA6377301318D | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7316.14593\vcruntime140.dll | executable | |
MD5:943FC74C2E39FE803D828CCFA7E62409 | SHA256:DA72E6677BD1BCD01C453C1998AAA19AEAF6659F4774CF6848409DA8232A95B2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
73
DNS requests
65
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5984 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744952119&P2=404&P3=2&P4=CV6AQ7gnKGvLWbuDh4hnrA8NXziQPTDSGDmMx630u4b4hY8P4fXTQJa0pZzvxUESHn9uje1MuoPsARafVrnEfA%3d%3d | unknown | — | — | whitelisted |
6344 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6344 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5984 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744952119&P2=404&P3=2&P4=CV6AQ7gnKGvLWbuDh4hnrA8NXziQPTDSGDmMx630u4b4hY8P4fXTQJa0pZzvxUESHn9uje1MuoPsARafVrnEfA%3d%3d | unknown | — | — | whitelisted |
5984 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744952119&P2=404&P3=2&P4=CV6AQ7gnKGvLWbuDh4hnrA8NXziQPTDSGDmMx630u4b4hY8P4fXTQJa0pZzvxUESHn9uje1MuoPsARafVrnEfA%3d%3d | unknown | — | — | whitelisted |
5984 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744952119&P2=404&P3=2&P4=CV6AQ7gnKGvLWbuDh4hnrA8NXziQPTDSGDmMx630u4b4hY8P4fXTQJa0pZzvxUESHn9uje1MuoPsARafVrnEfA%3d%3d | unknown | — | — | whitelisted |
5984 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744952119&P2=404&P3=2&P4=CV6AQ7gnKGvLWbuDh4hnrA8NXziQPTDSGDmMx630u4b4hY8P4fXTQJa0pZzvxUESHn9uje1MuoPsARafVrnEfA%3d%3d | unknown | — | — | whitelisted |
5984 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744952119&P2=404&P3=2&P4=CV6AQ7gnKGvLWbuDh4hnrA8NXziQPTDSGDmMx630u4b4hY8P4fXTQJa0pZzvxUESHn9uje1MuoPsARafVrnEfA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5800 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5800 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5800 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
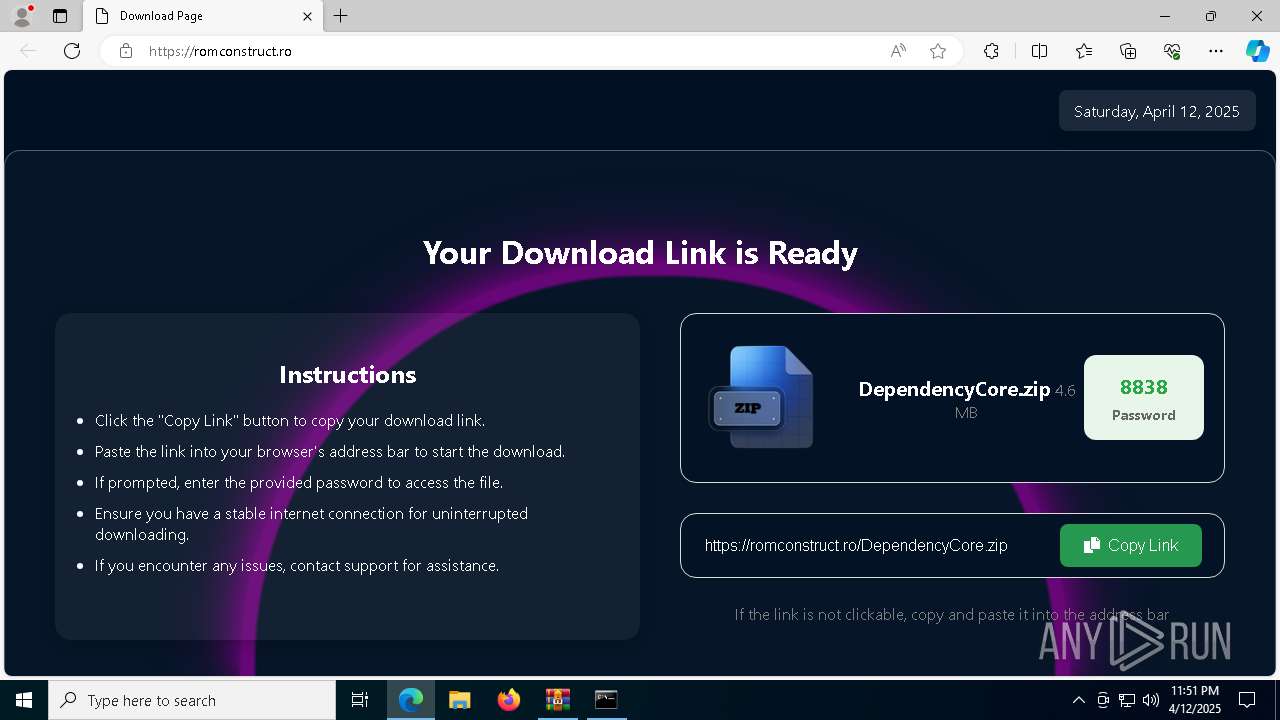
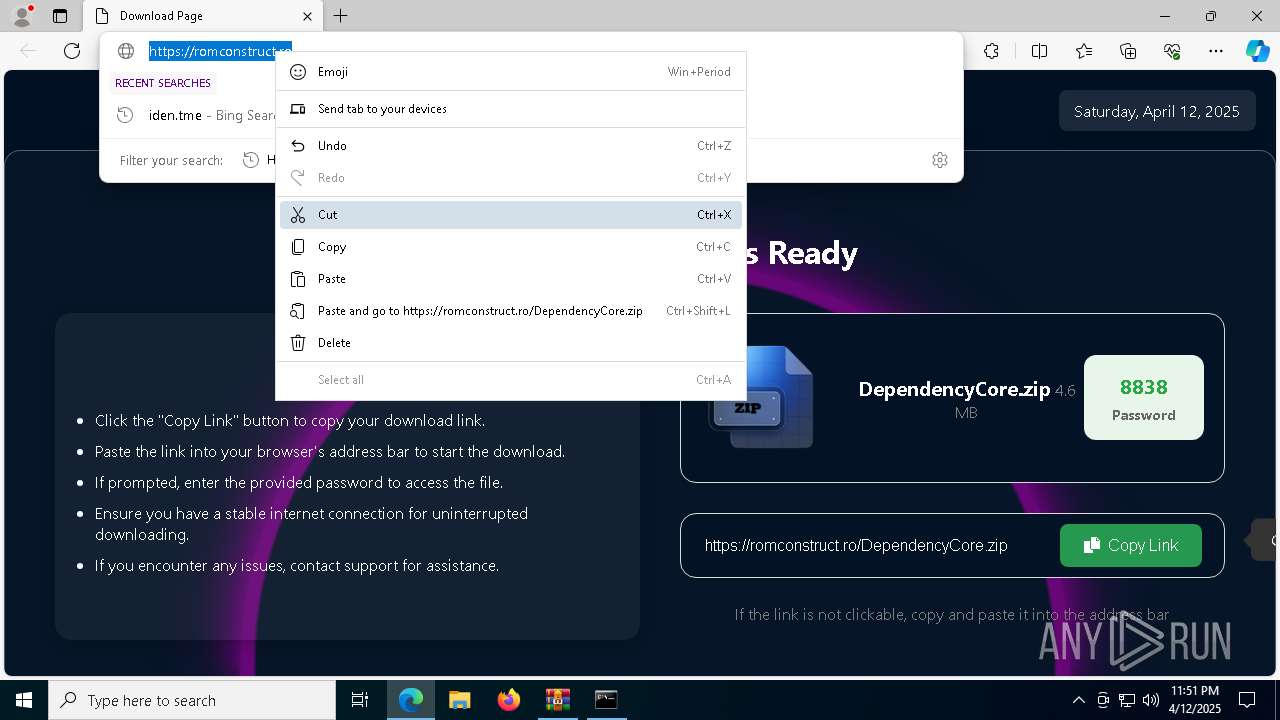
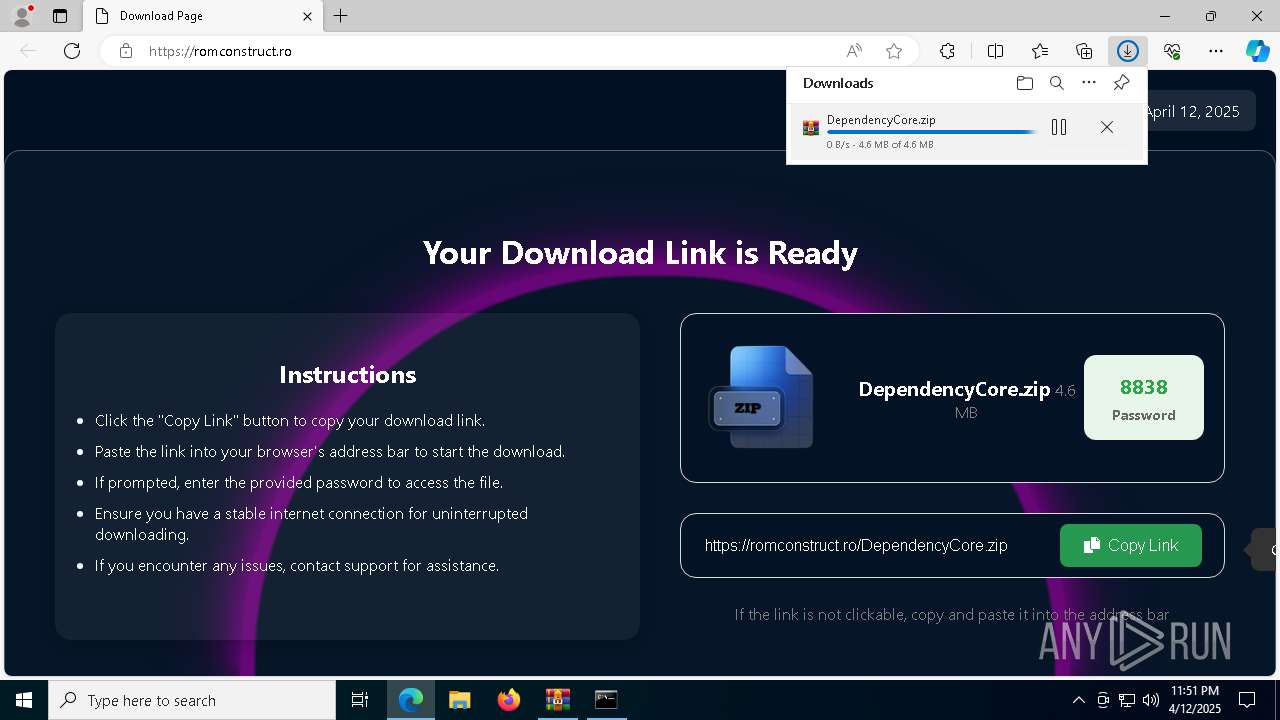
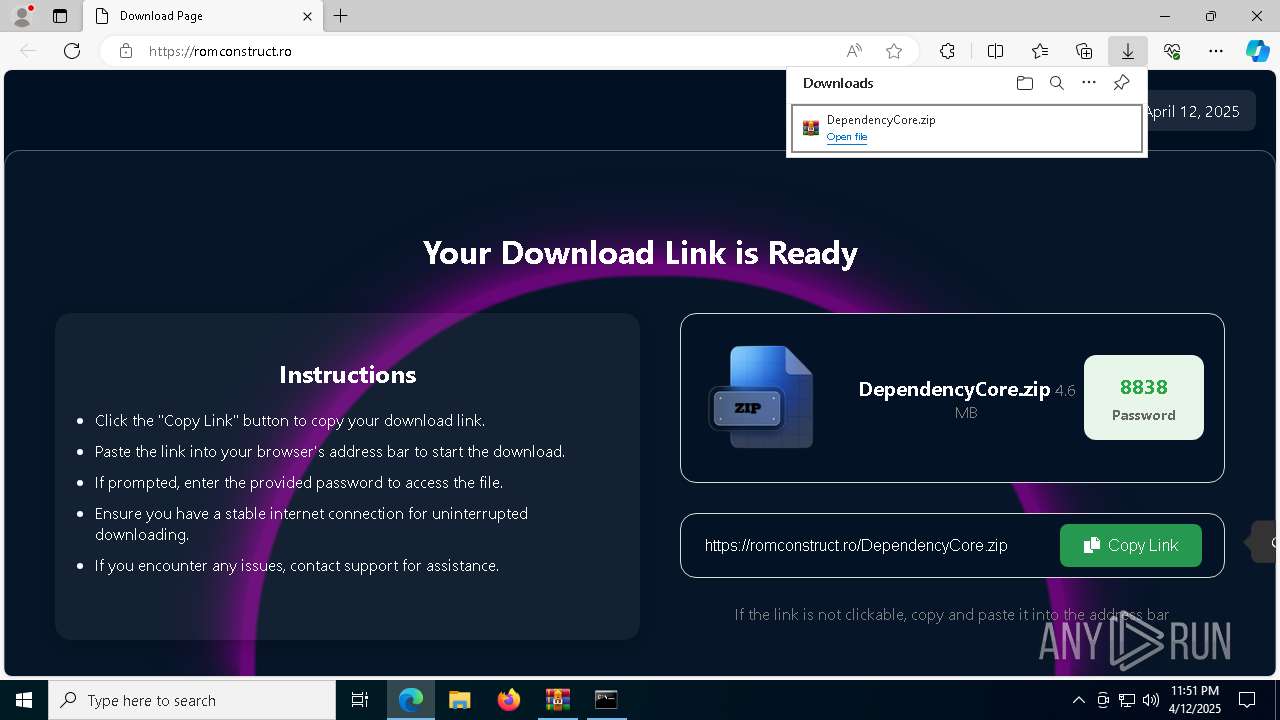
romconstruct.ro |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5800 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5800 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (clarmodq .top) |
7568 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
7568 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
7568 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
7568 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
7568 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
7568 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |