| URL: | http://cmokc.com/wp-content/themes/gaukingo/9qph4uxbvqdfzv/wrqqfxwr.php |
| Full analysis: | https://app.any.run/tasks/b19045b8-76c3-4bb0-b144-bef23641de9a |
| Verdict: | Malicious activity |
| Threats: | Maze is ransomware — a malware type that encrypts the victim’s files and restores the data in exchange for a ransom payment. One of the most distinguishable features of Maze is that it is one of the first malware of the kind to publicly release stolen data. |
| Analysis date: | November 08, 2019, 15:30:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 00687731AC25ED56C3E5FD86BDBE82C9 |
| SHA1: | 64352667125CAAEC965123137C3676C35034E2F2 |
| SHA256: | 5510D6366146E1825FF07378FECD56E9DC4BAD8977DEE7F203CA054E51380DA3 |
| SSDEEP: | 3:N1KdIqGvOlAQrF6FPsTGJ9MV:CKqGvOlAkFmaEU |
MALICIOUS
Application was dropped or rewritten from another process
- 963451.dat (PID: 3544)
Actions looks like stealing of personal data
- 963451.dat (PID: 3544)
Writes to a start menu file
- 963451.dat (PID: 3544)
Deletes shadow copies
- 963451.dat (PID: 3544)
Writes file to Word startup folder
- 963451.dat (PID: 3544)
Downloads executable files from the Internet
- WScript.exe (PID: 1944)
MAZE was detected
- 963451.dat (PID: 3544)
Renames files like Ransomware
- 963451.dat (PID: 3544)
SUSPICIOUS
Executable content was dropped or overwritten
- WScript.exe (PID: 1944)
Starts application with an unusual extension
- WScript.exe (PID: 1944)
Creates files in the program directory
- 963451.dat (PID: 3544)
Reads the cookies of Mozilla Firefox
- 963451.dat (PID: 3544)
Creates files like Ransomware instruction
- 963451.dat (PID: 3544)
Connects to server without host name
- 963451.dat (PID: 3544)
Executes scripts
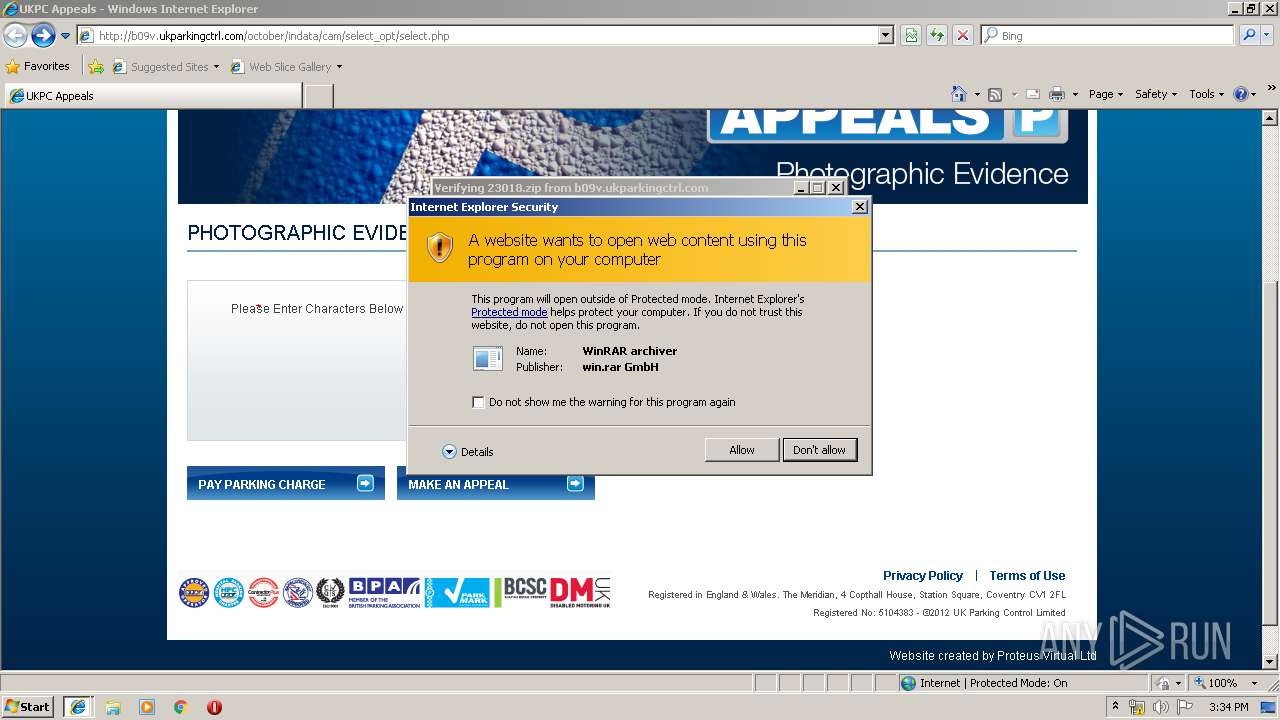
- WinRAR.exe (PID: 2820)
Creates files in the user directory
- WScript.exe (PID: 1944)
- 963451.dat (PID: 3544)
INFO
Application launched itself
- iexplore.exe (PID: 2128)
Creates files in the user directory
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 2128)
Reads settings of System Certificates
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 3380)
Reads internet explorer settings
- iexplore.exe (PID: 3380)
Reads Internet Cache Settings
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 2128)
Changes internet zones settings
- iexplore.exe (PID: 2128)
Dropped object may contain TOR URL's
- 963451.dat (PID: 3544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 792 | "C:\jr\..\Windows\d\..\system32\cca\pcce\..\..\wbem\woply\iruhn\..\..\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | 963451.dat | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | "C:\bs\..\Windows\uakxr\ec\qbyvd\..\..\..\system32\msij\xilox\o\..\..\..\wbem\r\usru\..\..\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | 963451.dat | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
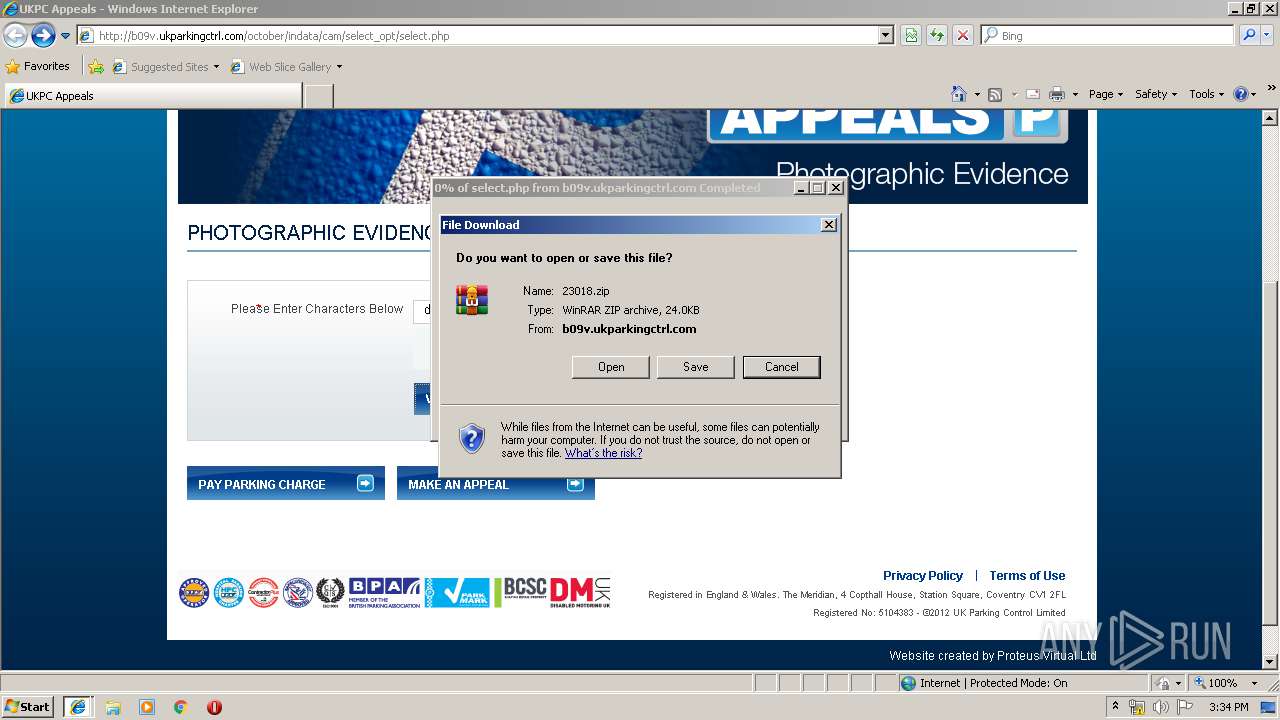
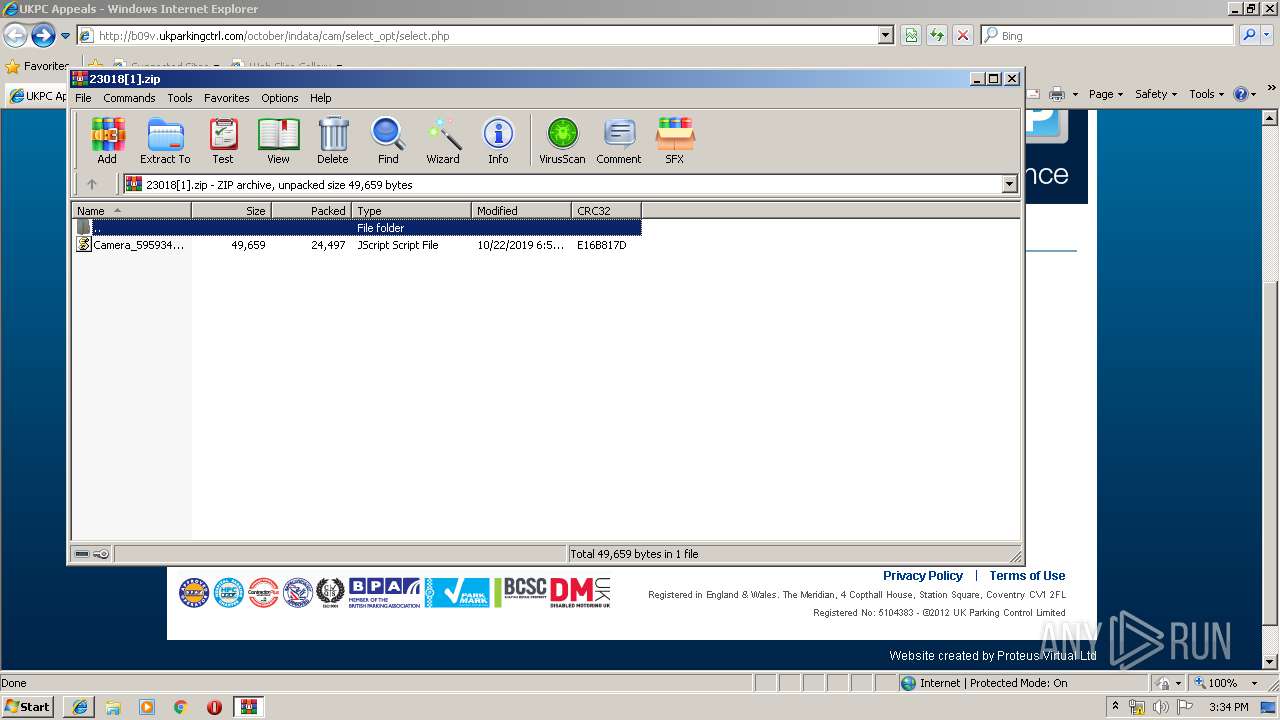
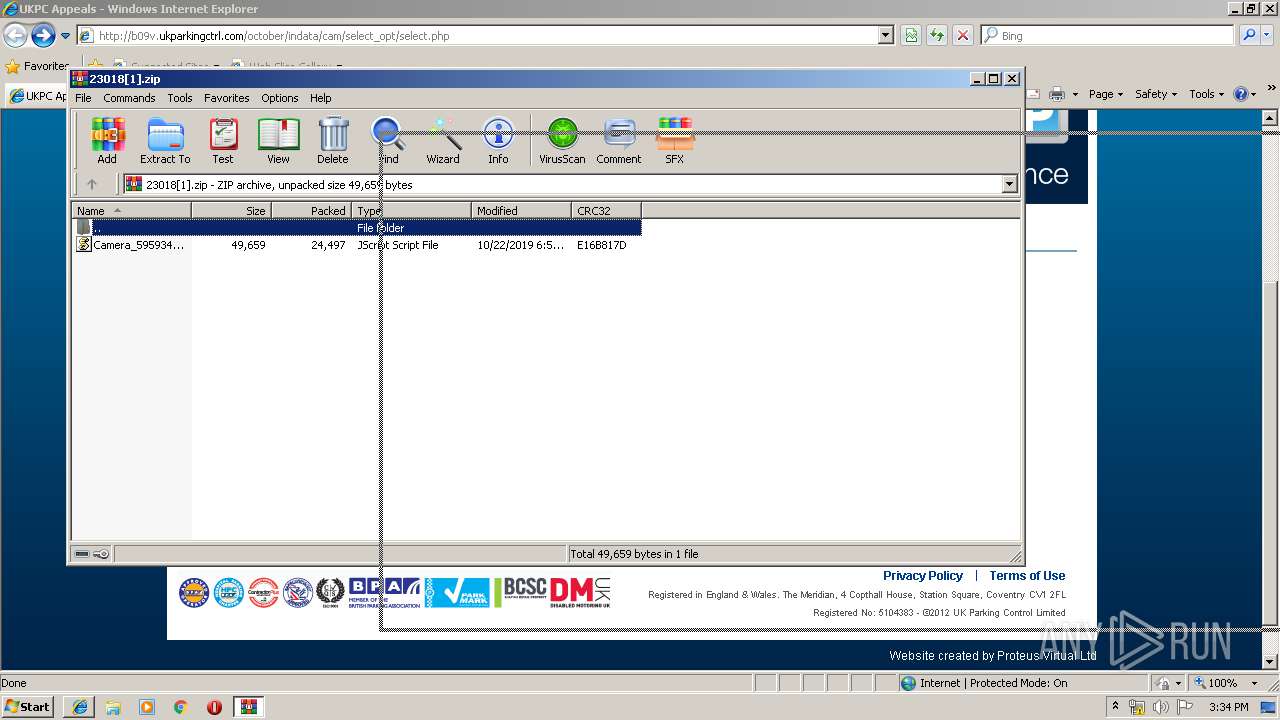
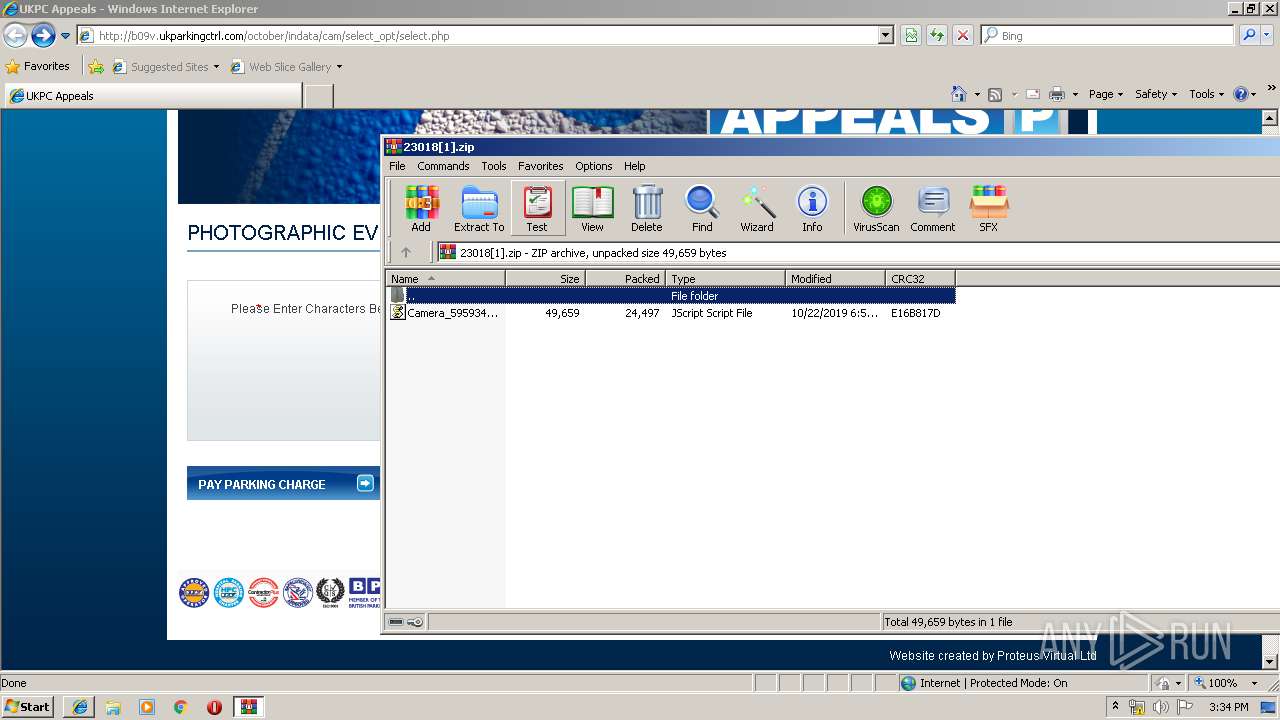
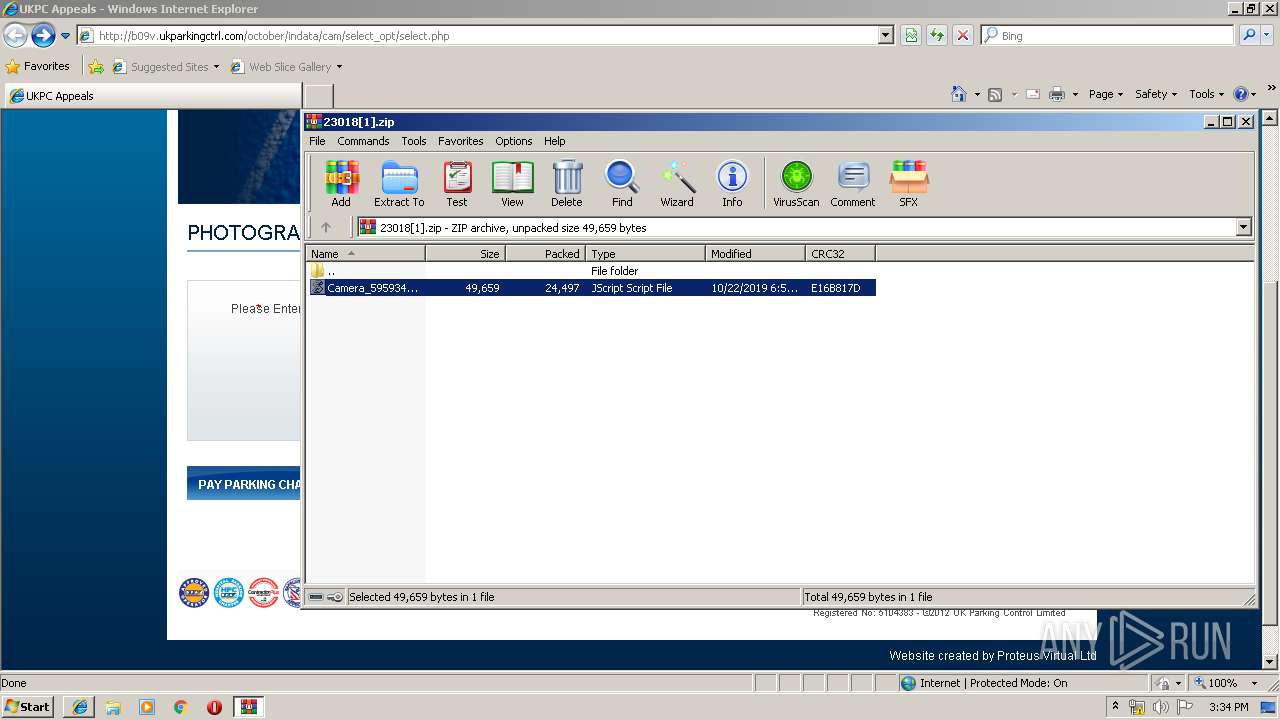
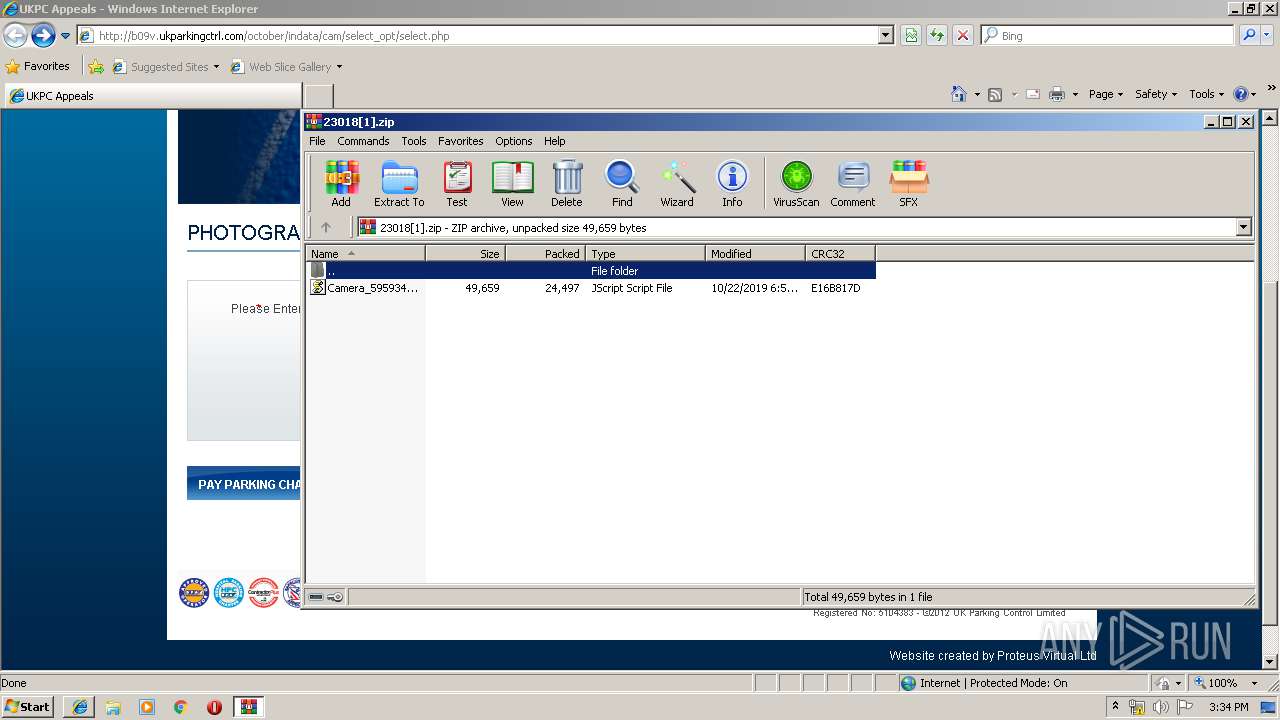
| 1944 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2820.27434\Camera_595934025.js" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
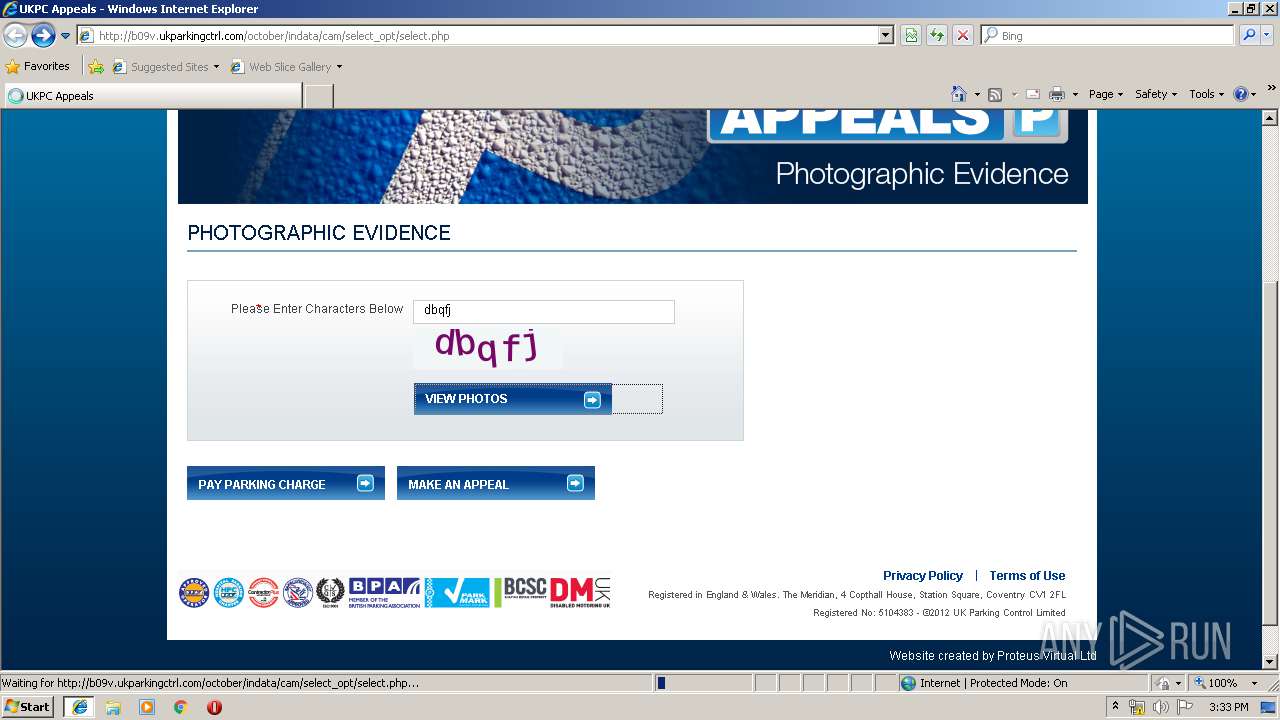
| 2128 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://cmokc.com/wp-content/themes/gaukingo/9qph4uxbvqdfzv/wrqqfxwr.php" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
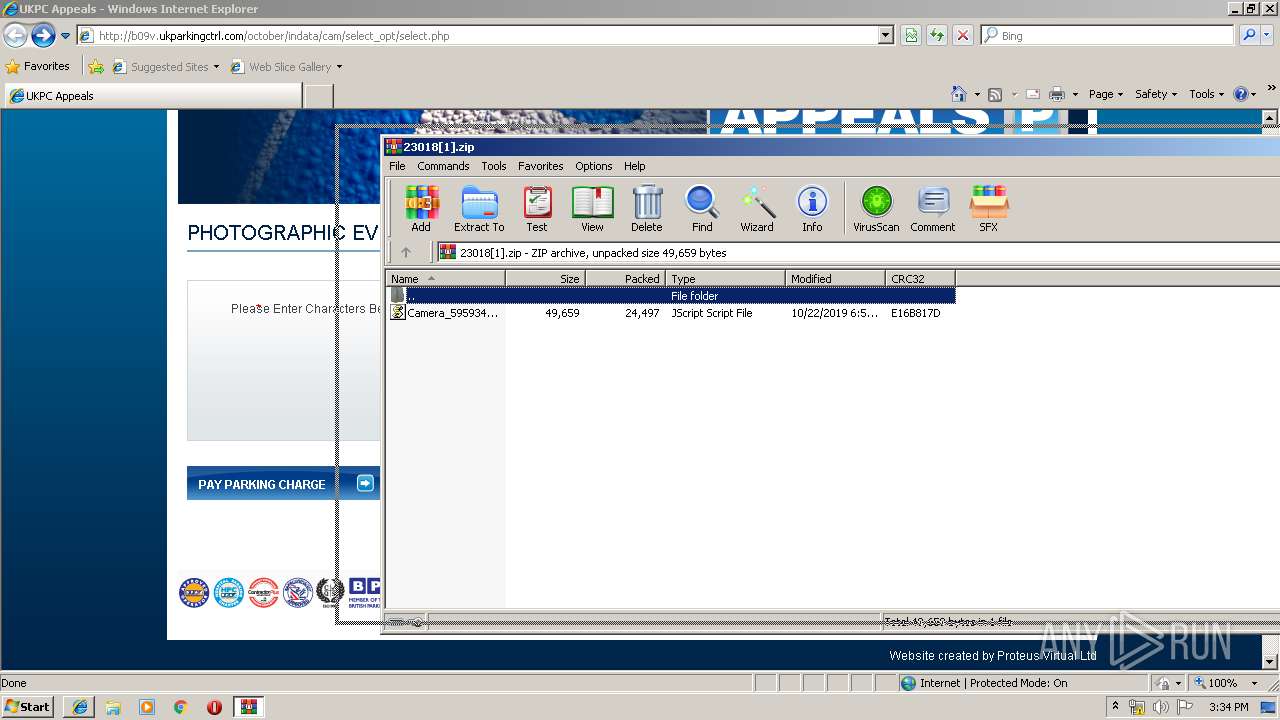
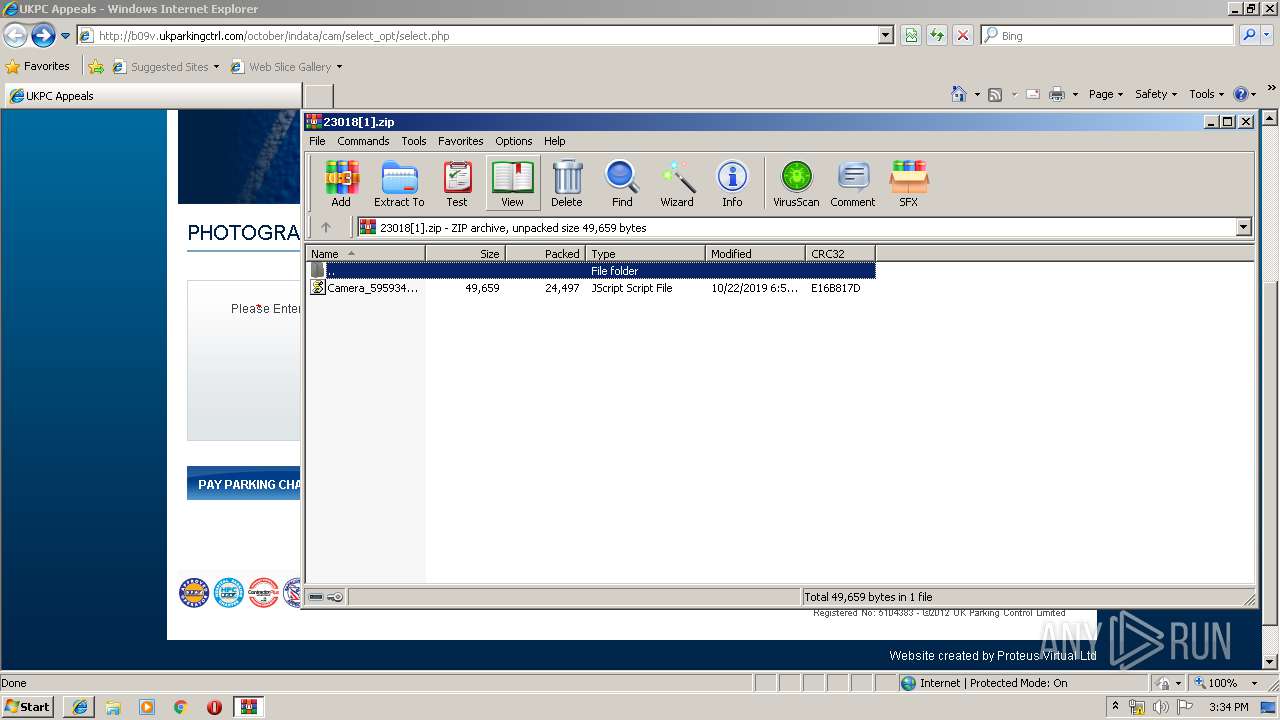
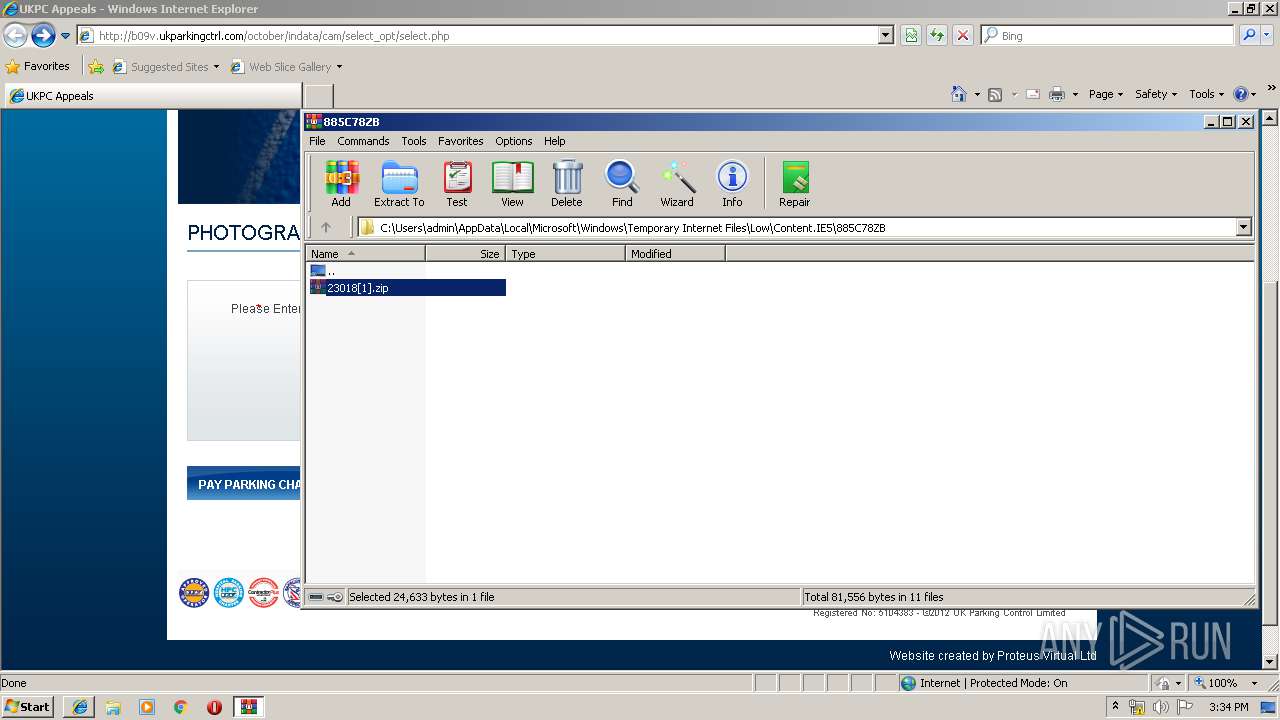
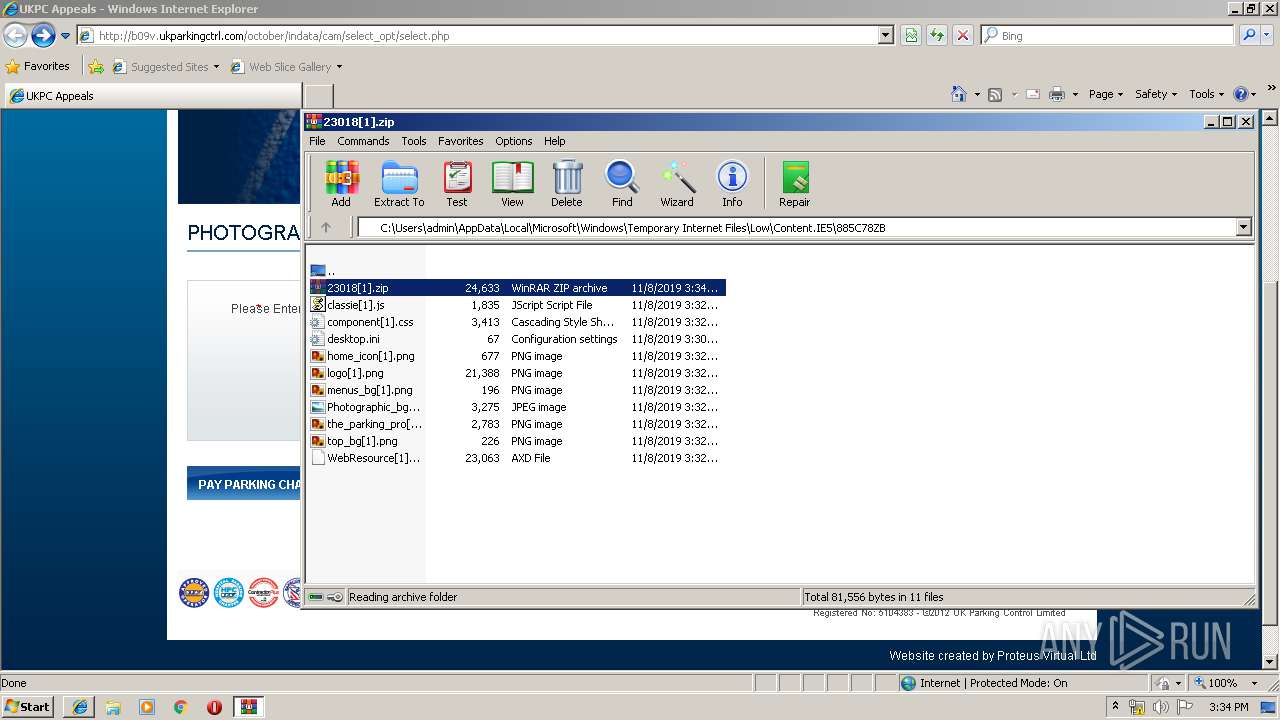
| 2820 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\885C78ZB\23018[1].zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3380 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2128 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3544 | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\963451.dat | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\963451.dat | WScript.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 581
Read events
1 376
Write events
200
Delete events
5
Modification events
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {BB70E8B9-023C-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070B00050008000F001E002E00C202 | |||
Executable files
2
Suspicious files
333
Text files
279
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
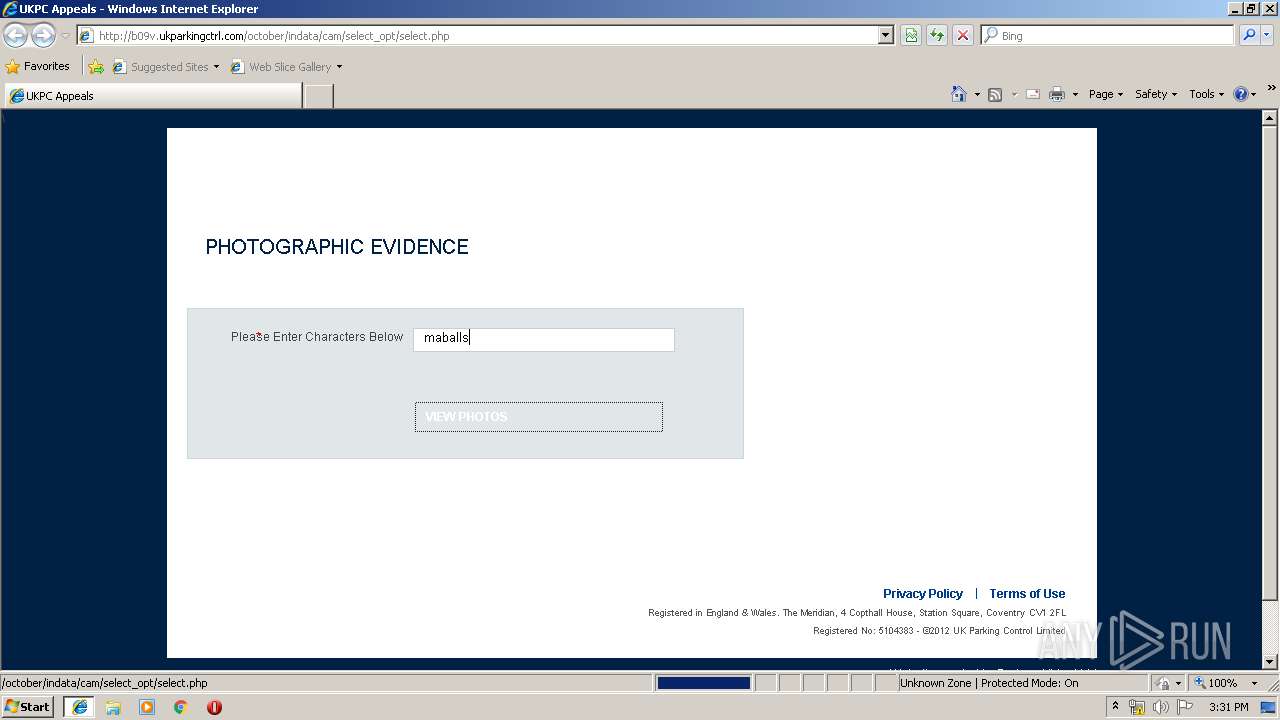
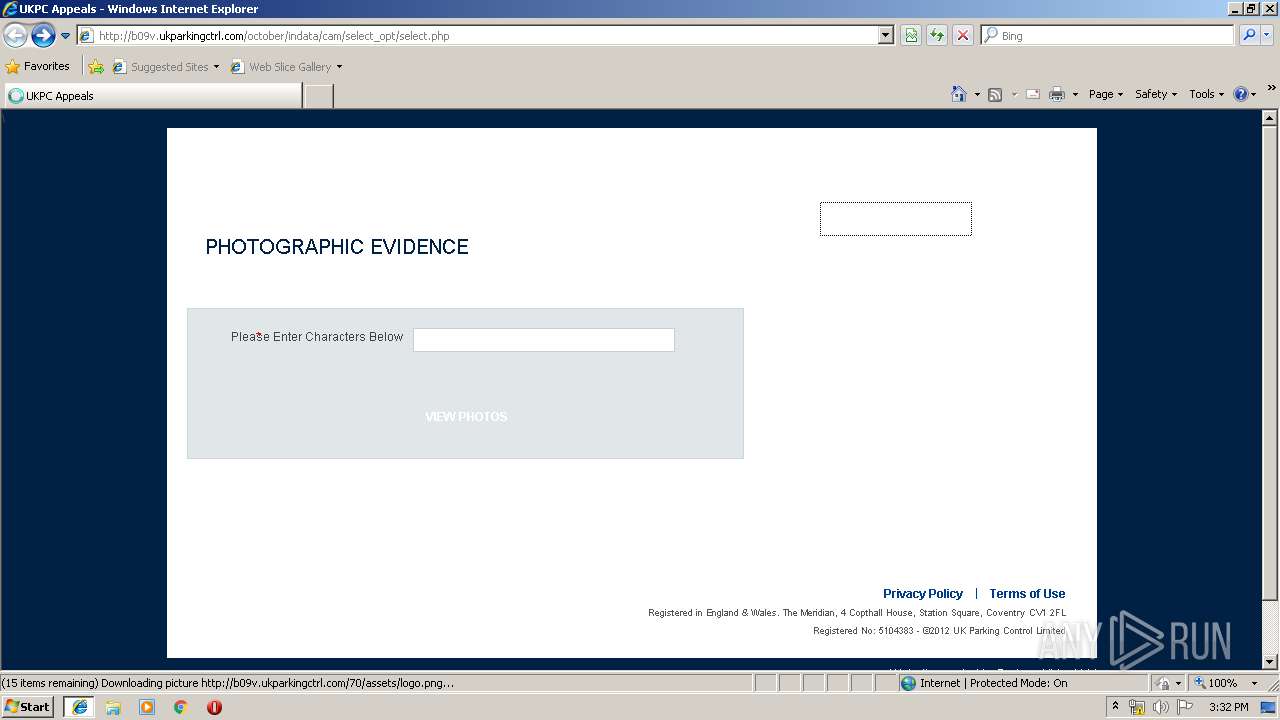
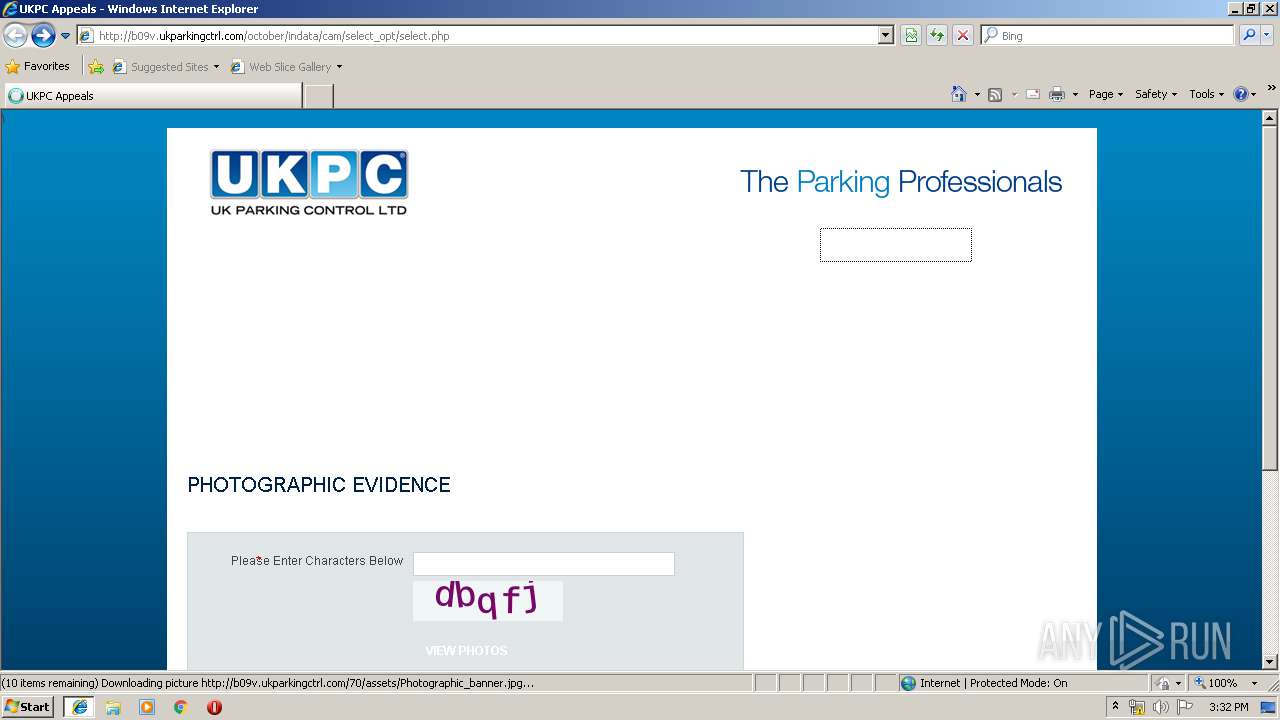
| 3380 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\3ED3LN8I\select[1].php | — | |
MD5:— | SHA256:— | |||
| 3380 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\QZJR0YN6\Default[1].txt | — | |
MD5:— | SHA256:— | |||
| 3380 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3380 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\3ED3LN8I\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3380 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3380 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\3ED3LN8I\select[1].htm | html | |
MD5:— | SHA256:— | |||
| 3380 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\QZJR0YN6\fontawesome[1].eot | eot | |
MD5:— | SHA256:— | |||
| 3380 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\885C78ZB\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
57
DNS requests
6
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
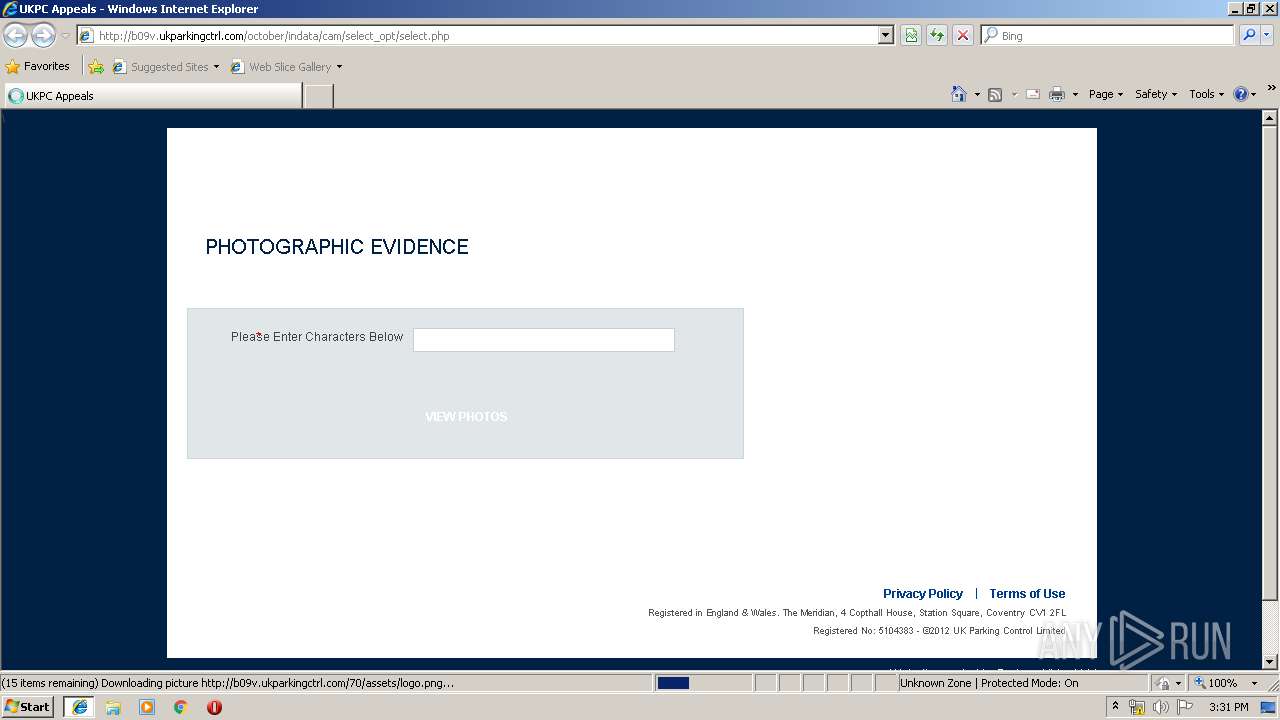
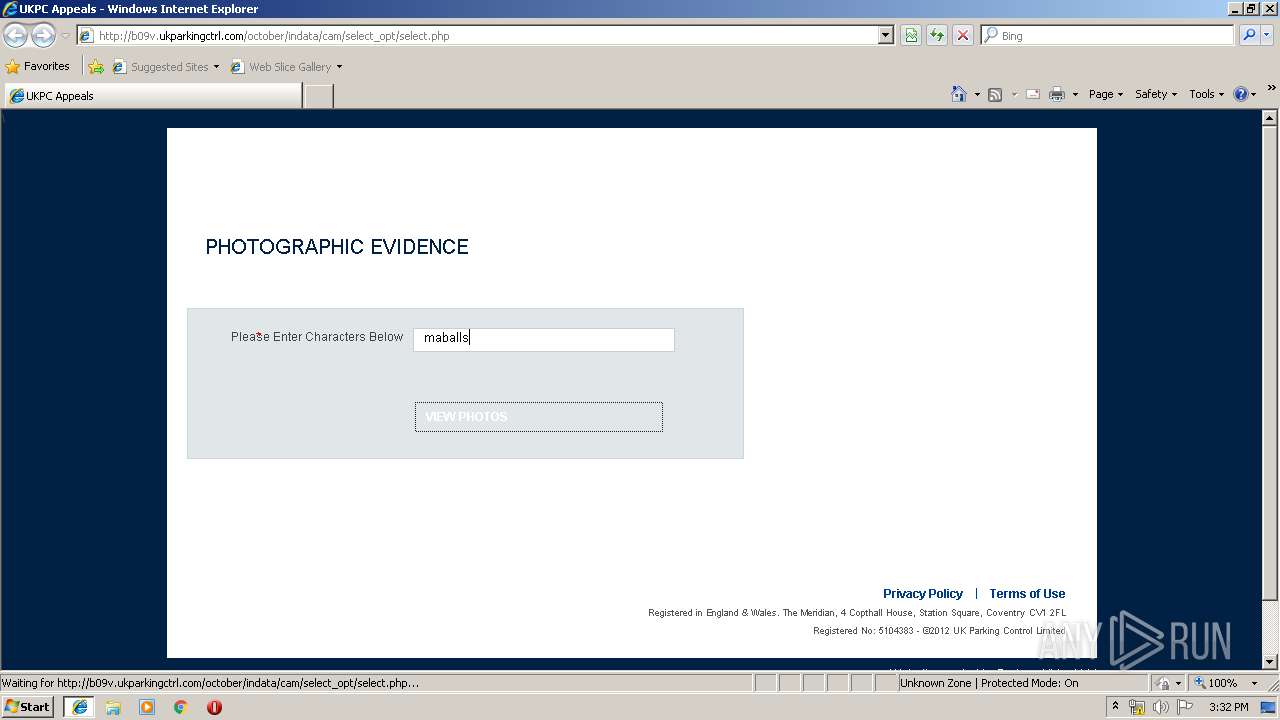
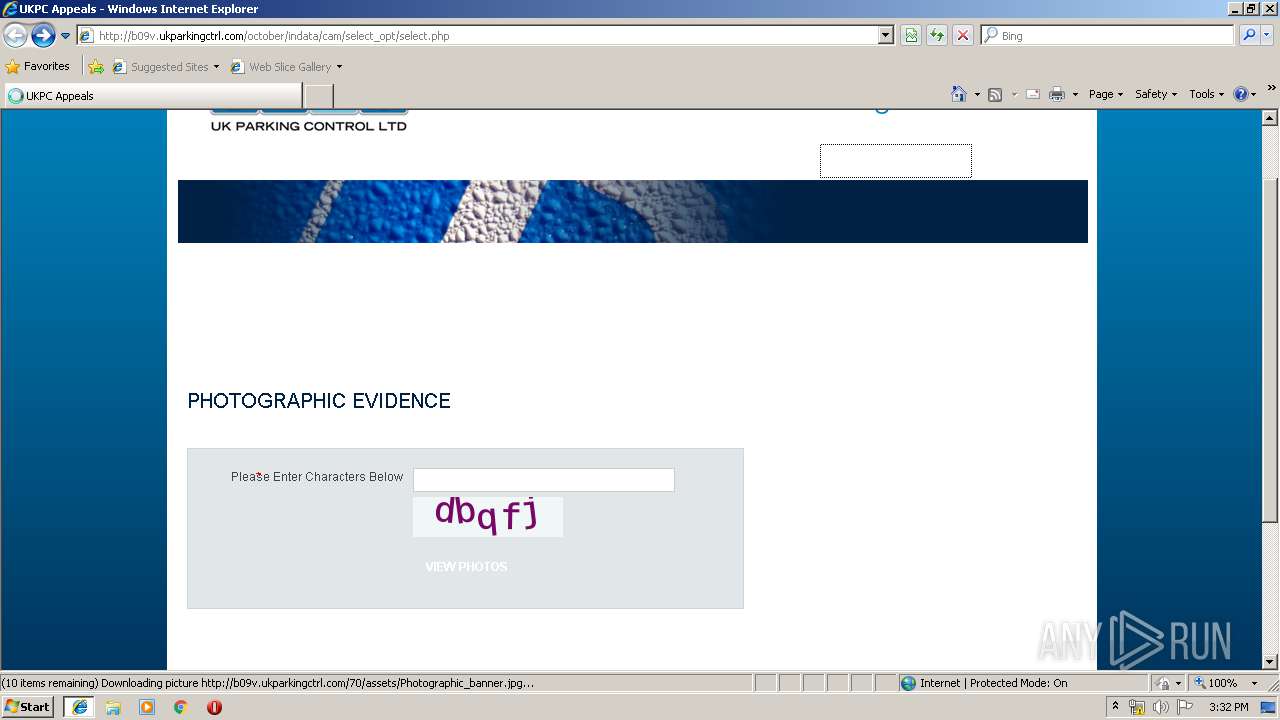
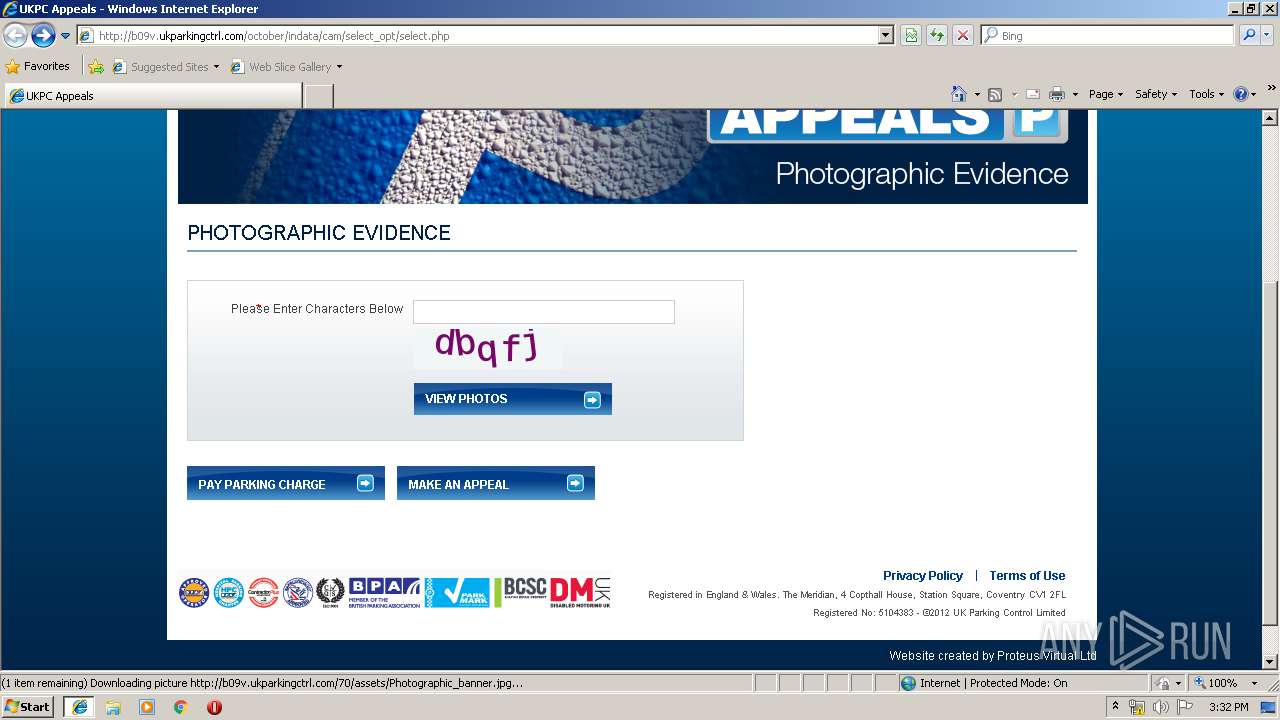
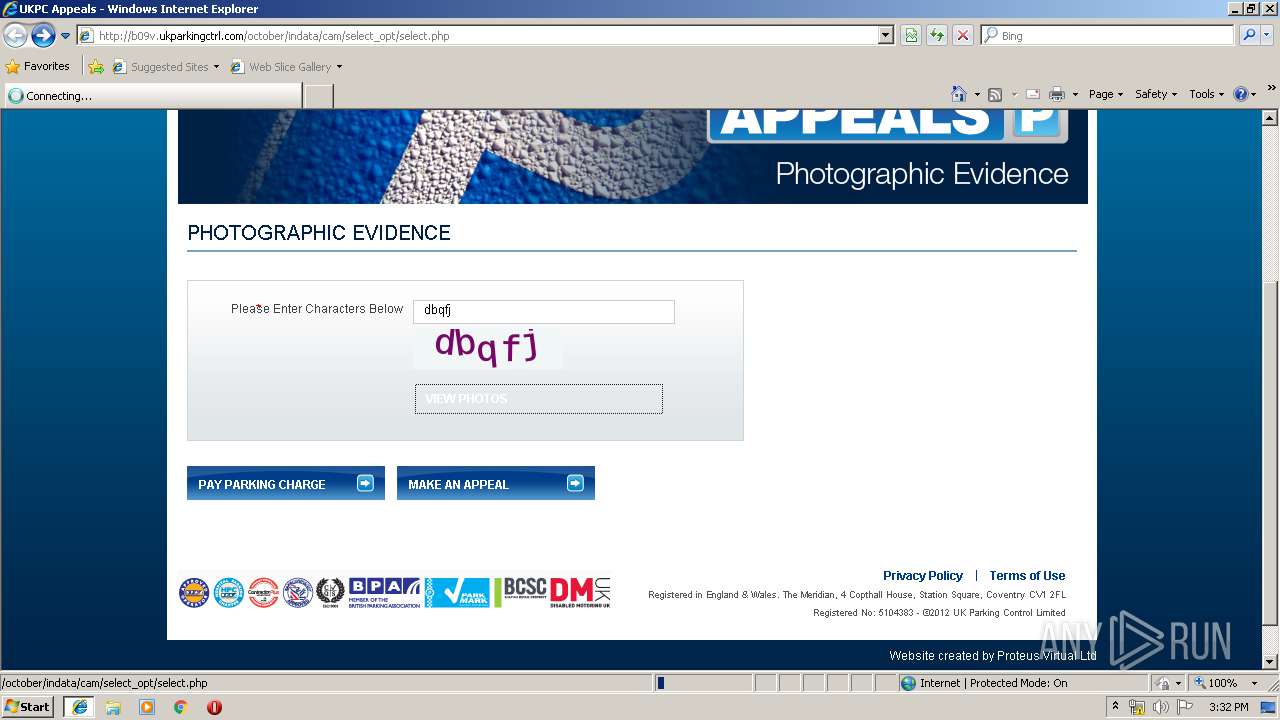
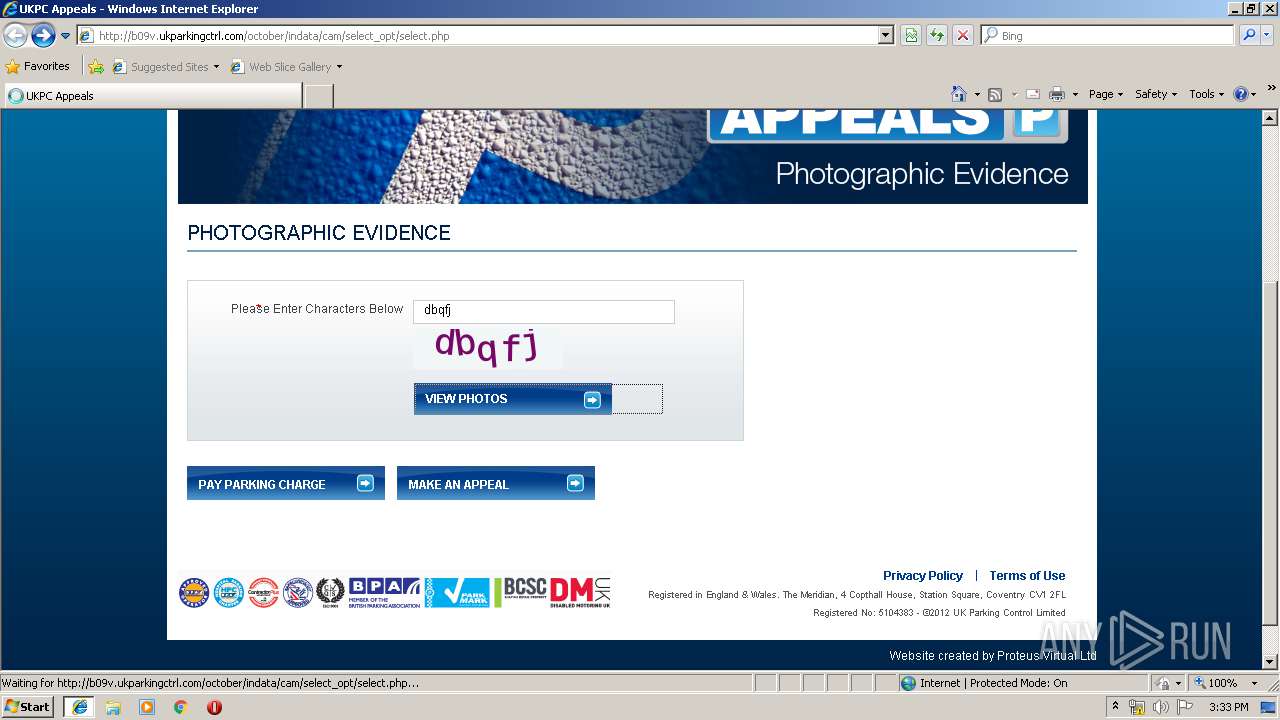
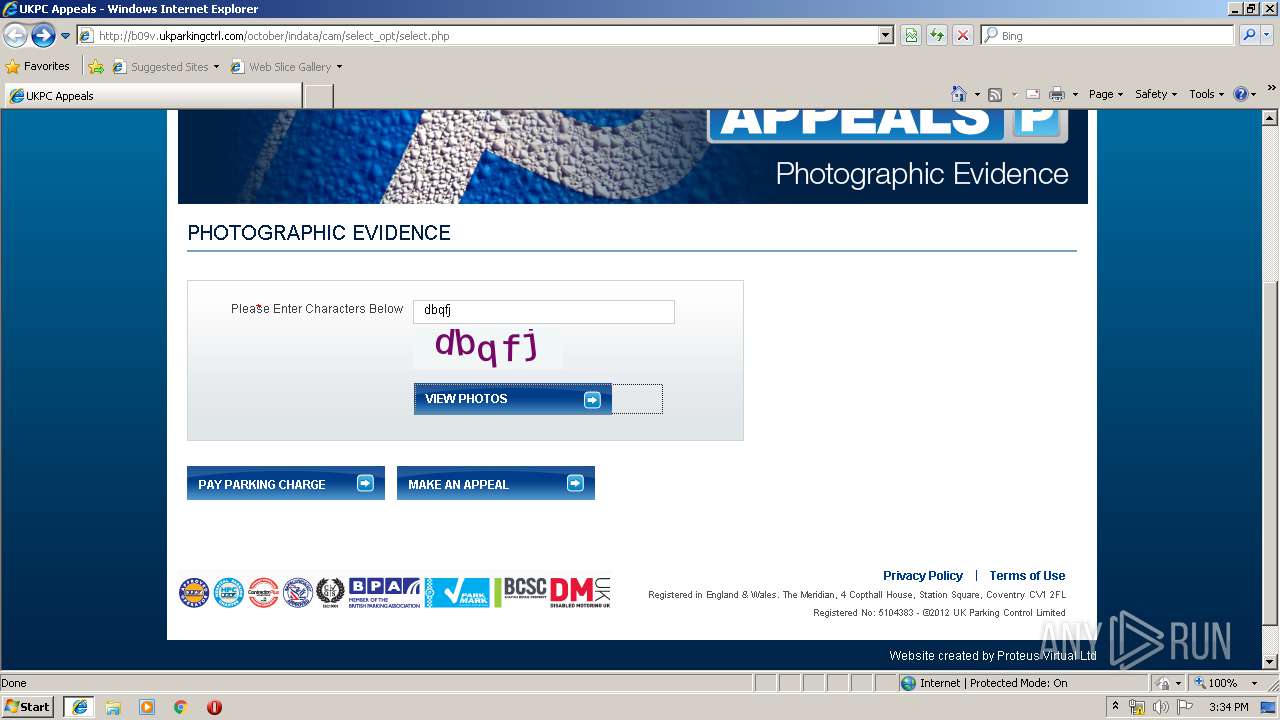
3380 | iexplore.exe | GET | — | 147.139.137.244:80 | http://b09v.ukparkingctrl.com/70/assets/the_parking_pro.png | US | — | — | malicious |
3380 | iexplore.exe | GET | — | 147.139.137.244:80 | http://b09v.ukparkingctrl.com/70/assets/Photographic_banner.jpg | US | — | — | malicious |
3380 | iexplore.exe | GET | 302 | 52.116.231.90:80 | http://cmokc.com/wp-content/themes/gaukingo/9qph4uxbvqdfzv/wrqqfxwr.php | US | — | — | unknown |
3380 | iexplore.exe | GET | — | 147.139.137.244:80 | http://b09v.ukparkingctrl.com/70/assets/top_bg.png | US | — | — | malicious |
3380 | iexplore.exe | GET | — | 147.139.137.244:80 | http://b09v.ukparkingctrl.com/october/indata/cam/select_opt/select.php?module=captcha | US | — | — | malicious |
3380 | iexplore.exe | GET | — | 147.139.137.244:80 | http://b09v.ukparkingctrl.com/70/assets/bg.png | US | — | — | malicious |
3380 | iexplore.exe | GET | — | 147.139.137.244:80 | http://b09v.ukparkingctrl.com/october/indata/cam/select_opt/select.php?module=captcha | US | — | — | malicious |
3380 | iexplore.exe | GET | — | 147.139.137.244:80 | http://b09v.ukparkingctrl.com/70/assets/logo.png | US | — | — | malicious |
3380 | iexplore.exe | GET | — | 147.139.137.244:80 | http://b09v.ukparkingctrl.com/70/assets/footer_logos.png | US | — | — | malicious |
3380 | iexplore.exe | GET | 200 | 147.139.137.244:80 | http://b09v.ukparkingctrl.com/70/assets/the_parking_pro.png | US | image | 2.72 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3380 | iexplore.exe | 52.116.231.90:80 | cmokc.com | — | US | unknown |
3380 | iexplore.exe | 152.199.19.160:443 | ajax.aspnetcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
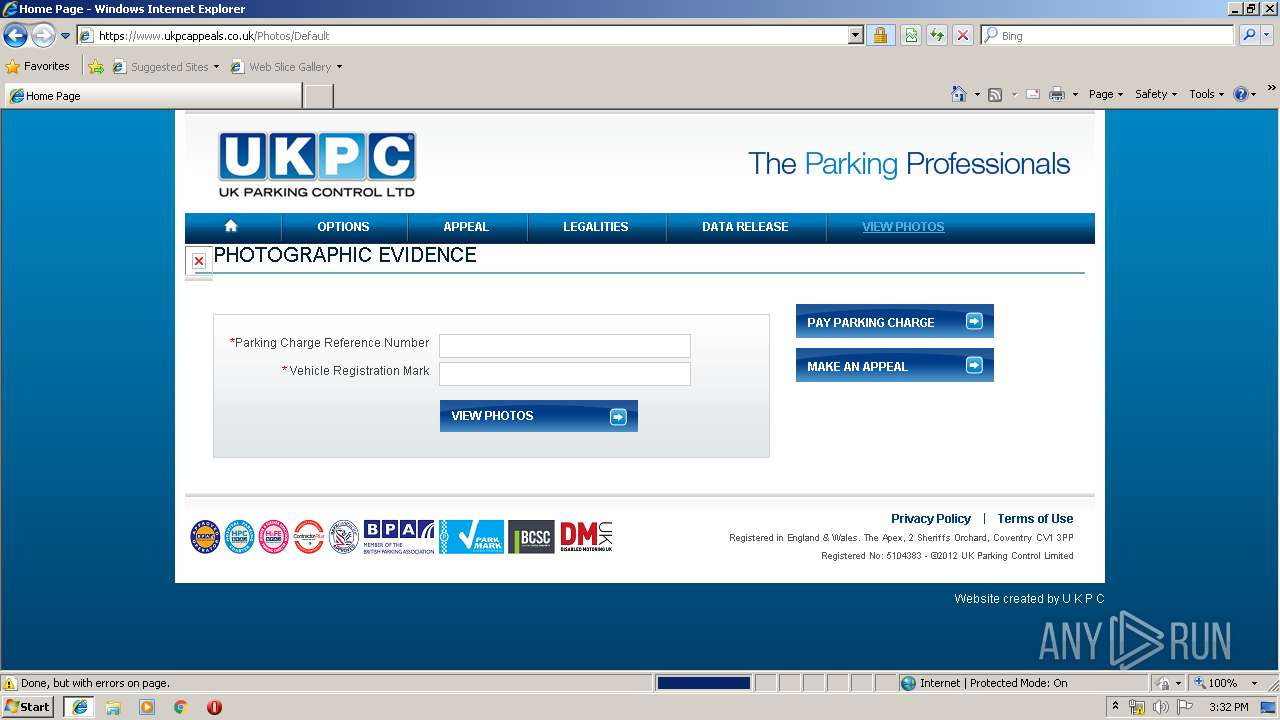
3380 | iexplore.exe | 51.145.119.85:443 | www.ukpcappeals.co.uk | Microsoft Corporation | GB | unknown |
2128 | iexplore.exe | 147.139.137.244:80 | b09v.ukparkingctrl.com | — | US | malicious |
2128 | iexplore.exe | 51.145.119.85:443 | www.ukpcappeals.co.uk | Microsoft Corporation | GB | unknown |
— | — | 51.145.119.85:443 | www.ukpcappeals.co.uk | Microsoft Corporation | GB | unknown |
3544 | 963451.dat | 91.218.114.11:80 | — | Mir Telematiki Ltd | RU | malicious |
3544 | 963451.dat | 91.218.114.26:80 | — | Mir Telematiki Ltd | RU | malicious |
3544 | 963451.dat | 91.218.114.4:80 | — | Mir Telematiki Ltd | RU | malicious |
2128 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cmokc.com |
| unknown |
www.bing.com |
| whitelisted |
b09v.ukparkingctrl.com |
| malicious |
www.ukpcappeals.co.uk |
| unknown |
ajax.aspnetcdn.com |
| whitelisted |
www.highlevelsuccess.monster |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3380 | iexplore.exe | Misc activity | ET INFO SUSPICIOUS Single JS file inside of ZIP Download (Observed as lure in malspam campaigns) |
1944 | WScript.exe | A Network Trojan was detected | ET TROJAN Possible Malicious Macro DL EXE Feb 2016 |
1944 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1944 | WScript.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
3544 | 963451.dat | A Network Trojan was detected | MALWARE [PTsecurity] Maze Ransomware |
3544 | 963451.dat | A Network Trojan was detected | MALWARE [PTsecurity] Maze Ransomware |
3544 | 963451.dat | A Network Trojan was detected | MALWARE [PTsecurity] Maze Ransomware |
3544 | 963451.dat | A Network Trojan was detected | MALWARE [PTsecurity] Maze Ransomware |
3544 | 963451.dat | A Network Trojan was detected | MALWARE [PTsecurity] Maze Ransomware |
3 ETPRO signatures available at the full report