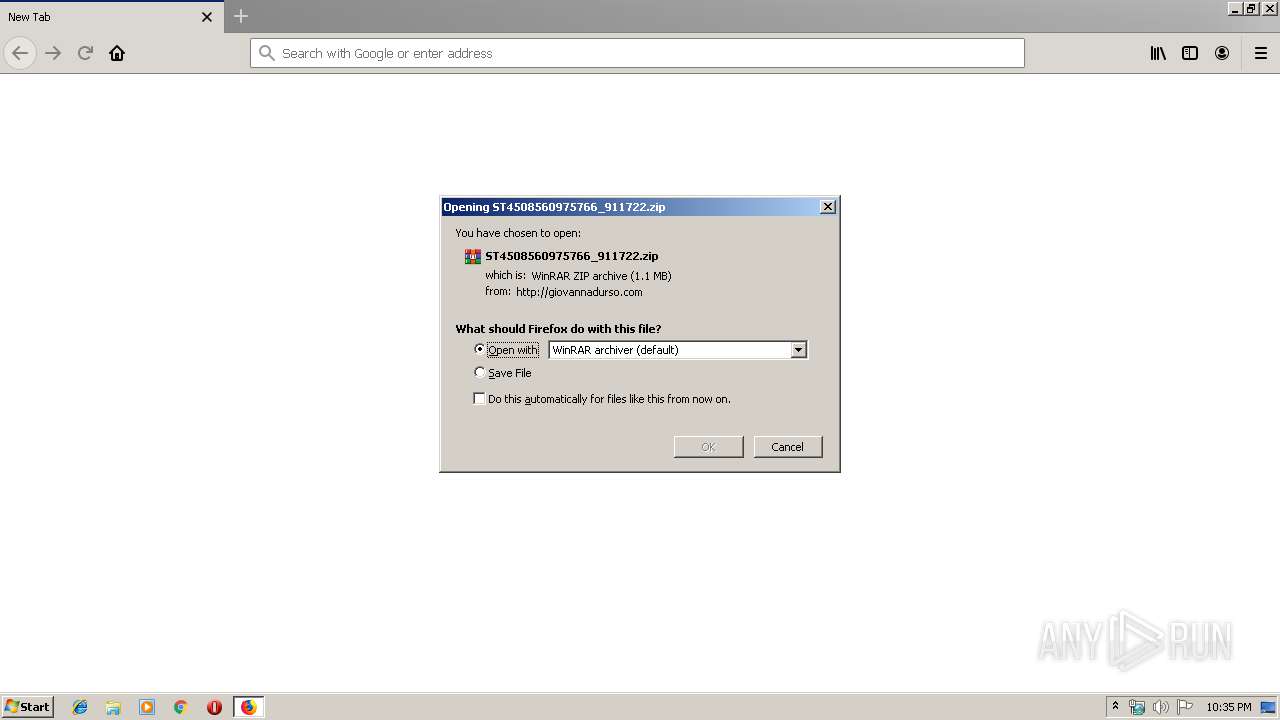
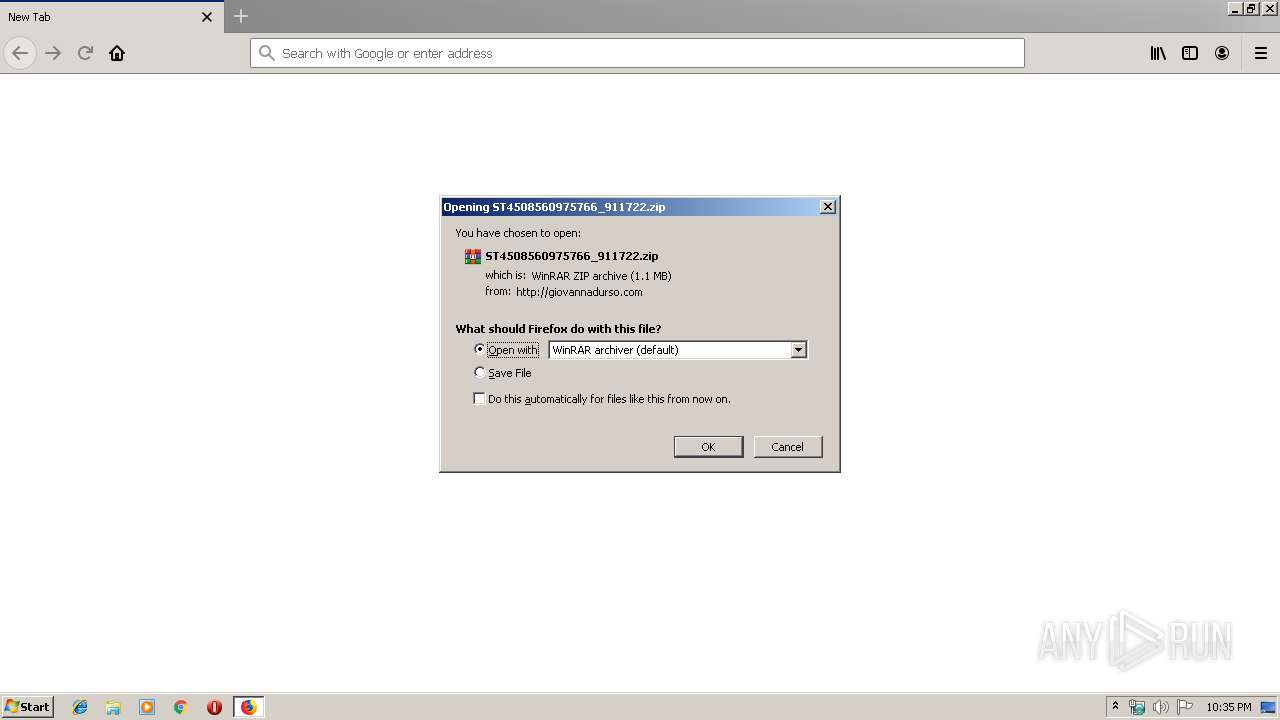
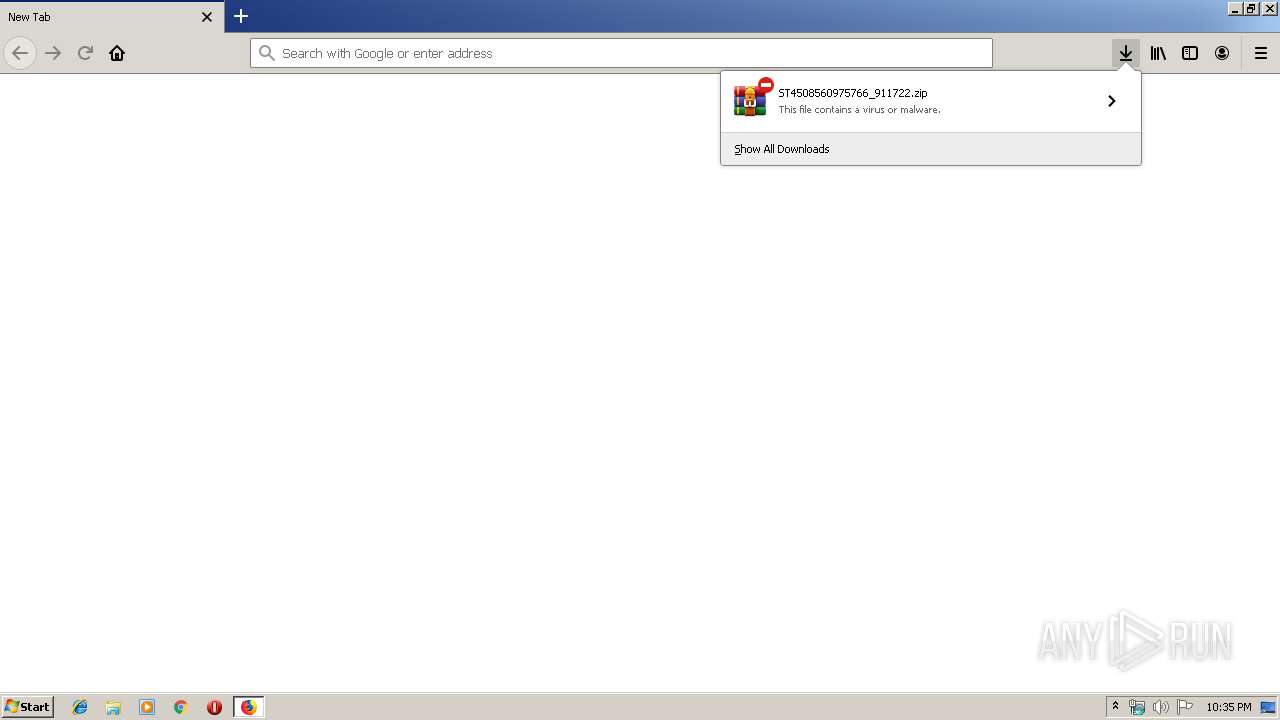
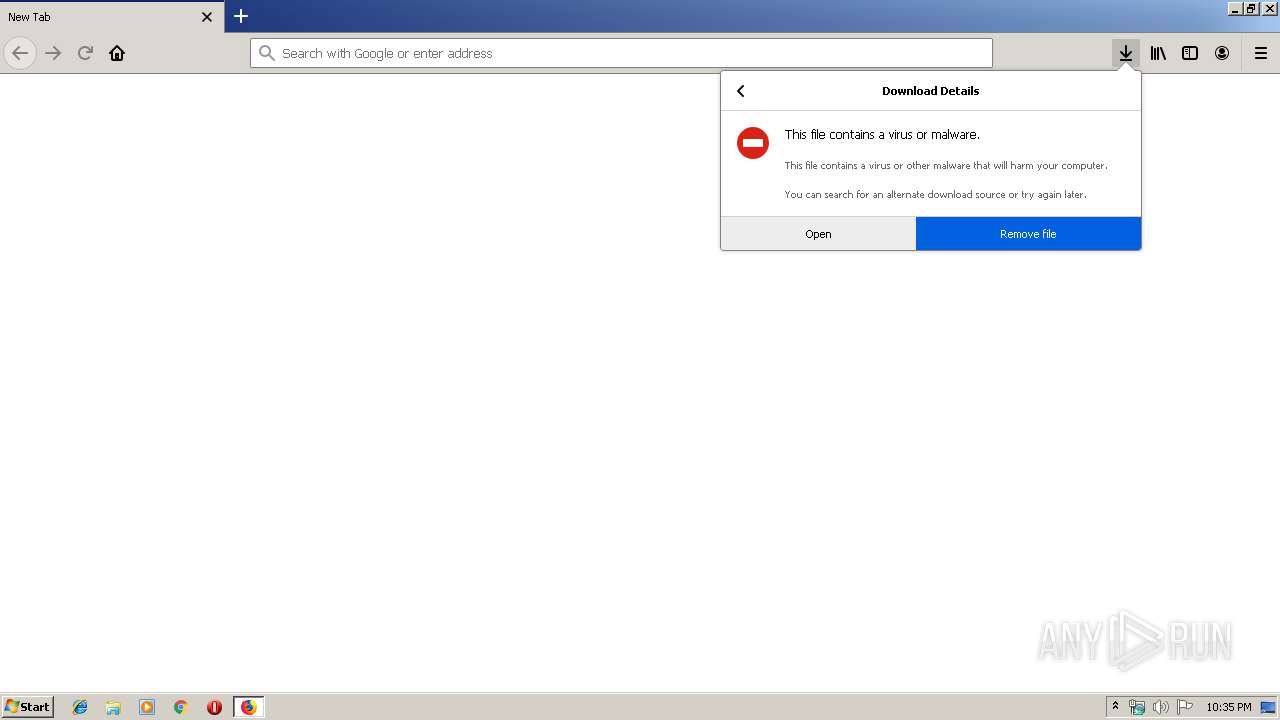
| URL: | http://giovannadurso.com/media/editors/tinymce/jscripts/tiny_mce/plugins/inlinepopups/skins/clearlooks2/img/ST4508560975766_911722.zip |
| Full analysis: | https://app.any.run/tasks/9ee8af0d-e835-41f5-9eaa-62f9f1358839 |
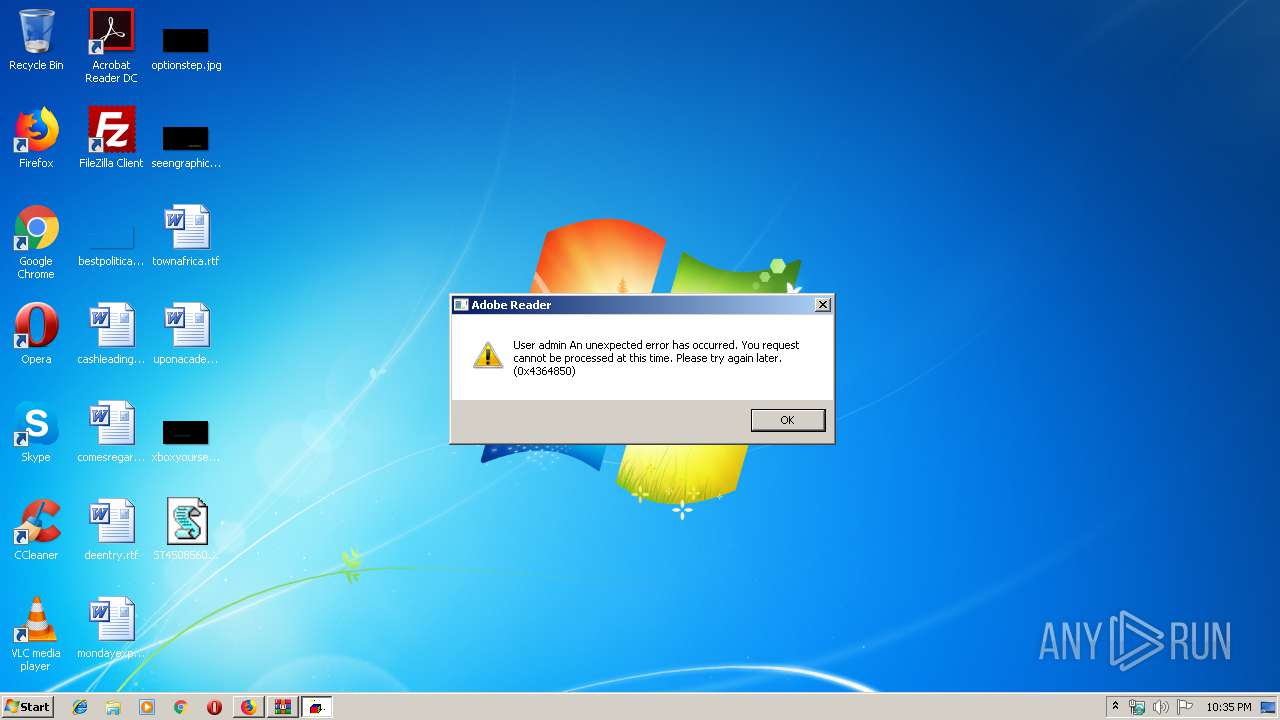
| Verdict: | Malicious activity |
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
| Analysis date: | September 18, 2019, 21:34:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 055B4038C7E44C88173E266F019E2DA5 |
| SHA1: | 03E9AE853BCC434C012EAE72A76D6A51DBC50183 |
| SHA256: | 545989ABD5953987C900BA84BD89005B242713E120AE0521CB430D651BE5BB47 |
| SSDEEP: | 3:N1KZMKIMcSjrHh+L7b6UJbPd/LXvK2x2Vg2SzTQrc:CyKIMcSjrHMJBziW2W+Y |
MALICIOUS
Application was dropped or rewritten from another process
- DUZGZkDG.exe (PID: 3372)
- DUZGZkDG.exe (PID: 3440)
- ytfovlym.exe (PID: 2404)
- ytfovlym.exe (PID: 2320)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2488)
QBOT was detected
- DUZGZkDG.exe (PID: 3372)
Changes the autorun value in the registry
- explorer.exe (PID: 2256)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2428)
Executable content was dropped or overwritten
- WScript.exe (PID: 3412)
- DUZGZkDG.exe (PID: 3372)
- cmd.exe (PID: 2488)
Executed via WMI
- DUZGZkDG.exe (PID: 3372)
Application launched itself
- DUZGZkDG.exe (PID: 3372)
- ytfovlym.exe (PID: 2404)
Creates files in the user directory
- DUZGZkDG.exe (PID: 3372)
Starts CMD.EXE for commands execution
- DUZGZkDG.exe (PID: 3372)
Starts itself from another location
- DUZGZkDG.exe (PID: 3372)
INFO
Reads CPU info
- firefox.exe (PID: 2428)
Application launched itself
- firefox.exe (PID: 2428)
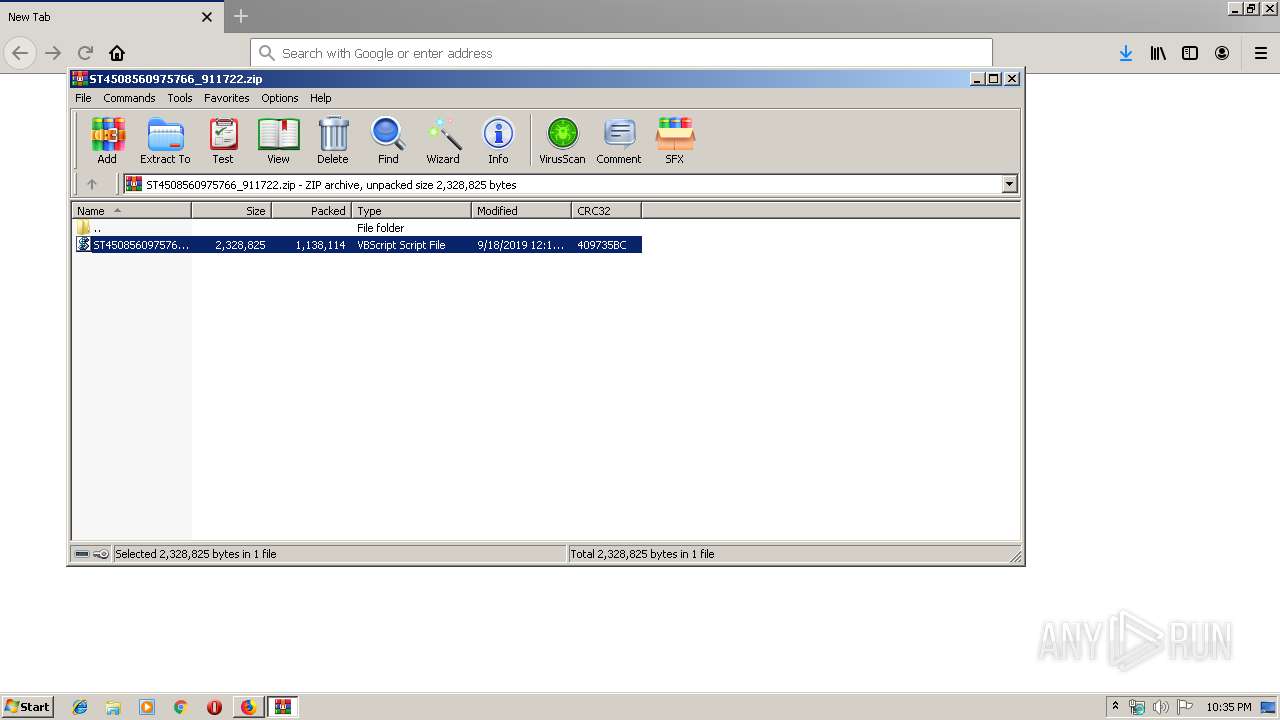
Manual execution by user
- WScript.exe (PID: 3412)
Creates files in the user directory
- firefox.exe (PID: 2428)
Dropped object may contain Bitcoin addresses
- cmd.exe (PID: 2488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
15
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2256 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | ytfovlym.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2428.3.1631032610\700455295" -childID 1 -isForBrowser -prefsHandle 1648 -prefMapHandle 1632 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2428 "\\.\pipe\gecko-crash-server-pipe.2428" 1304 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
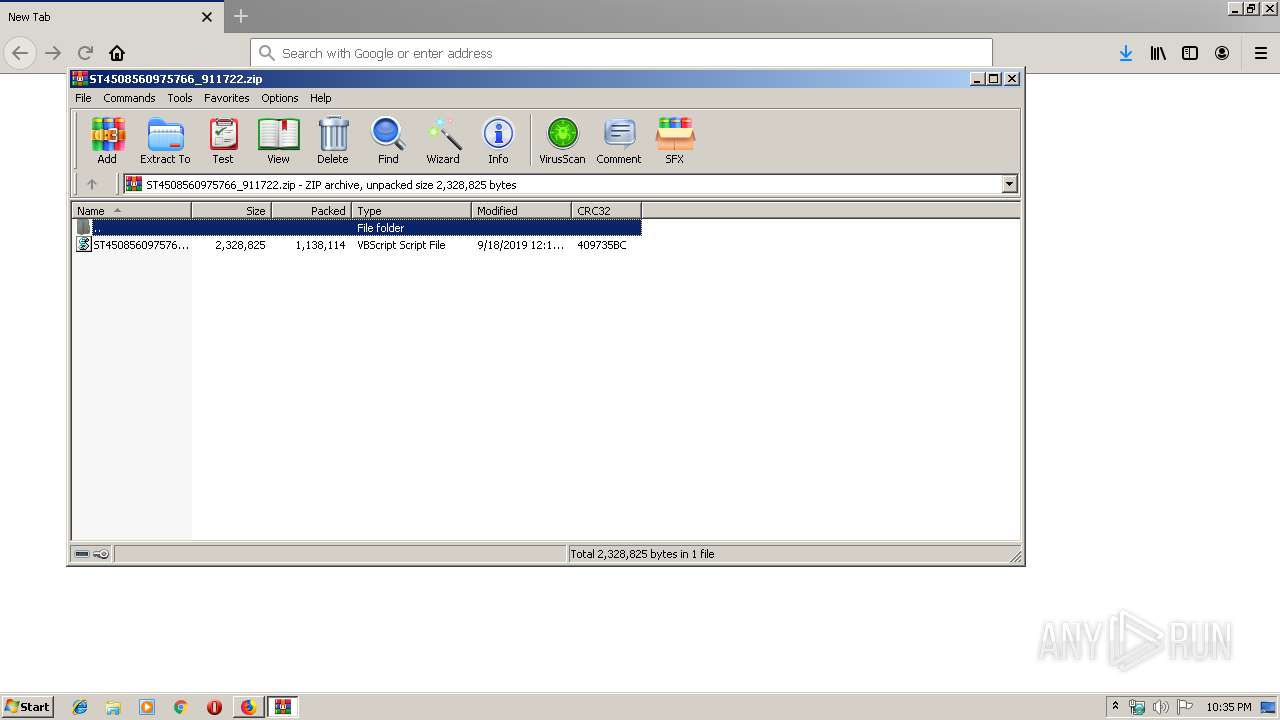
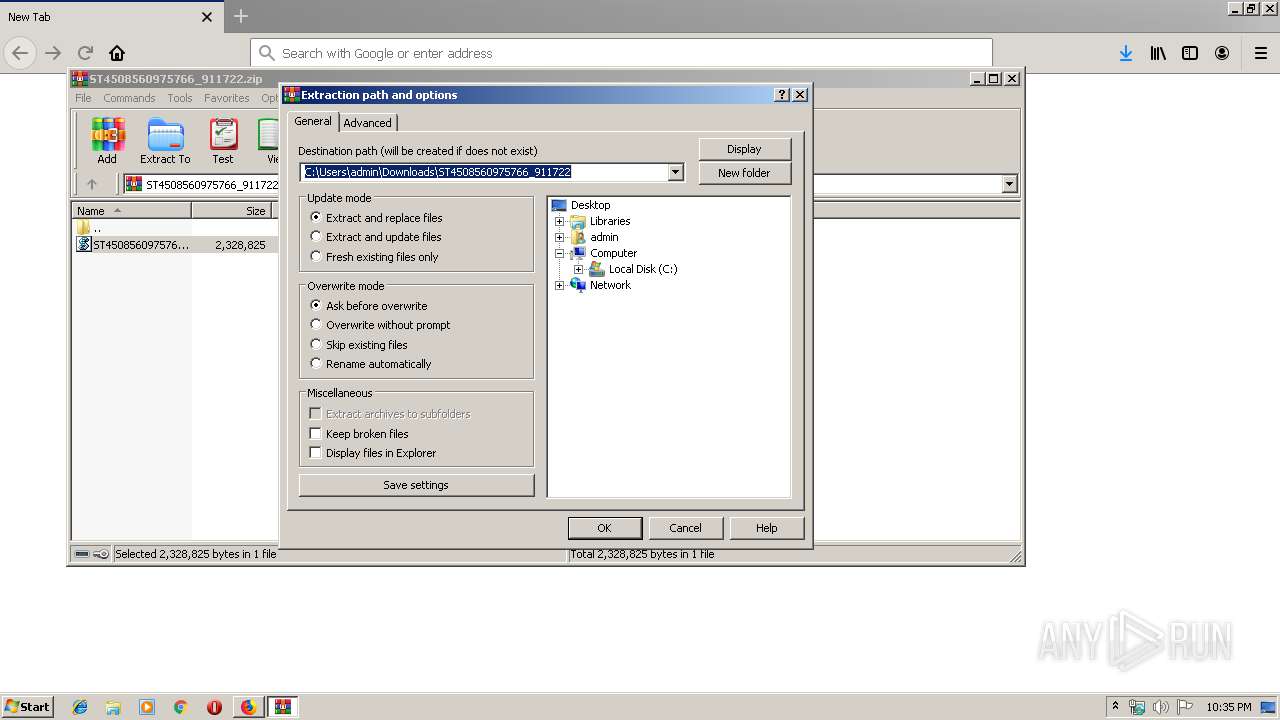
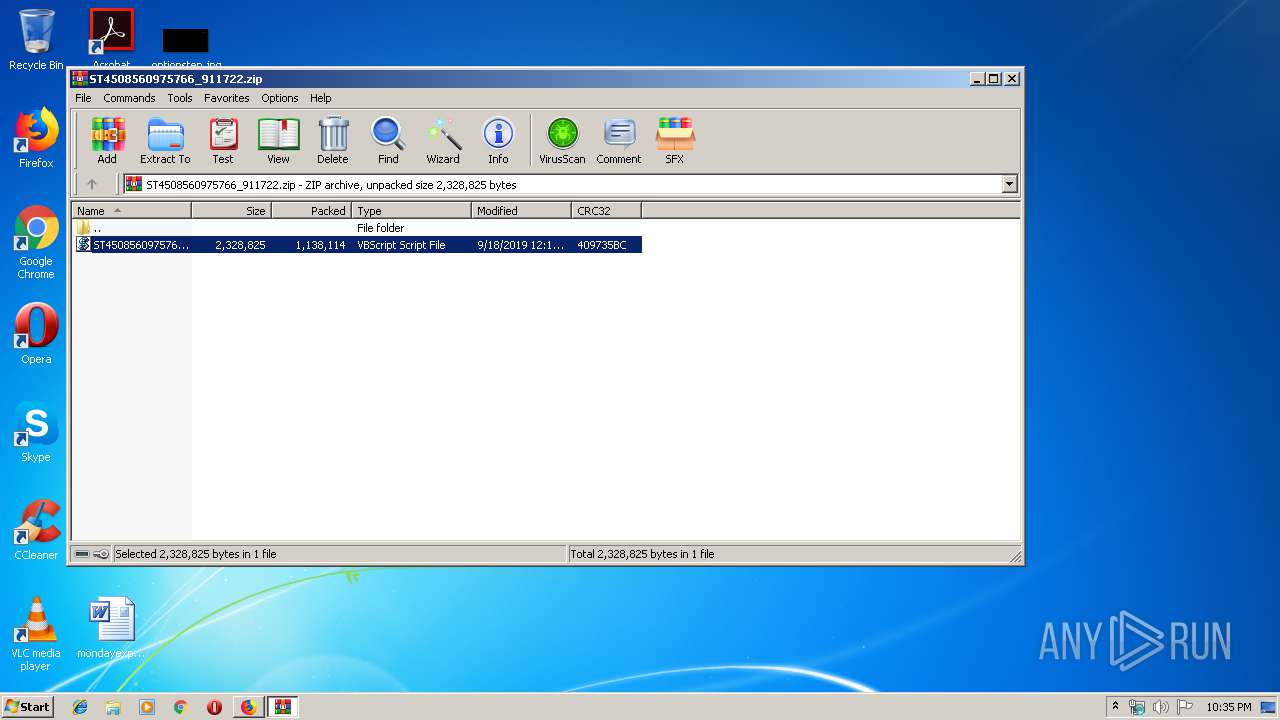
| 2268 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ST4508560975766_911722.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | firefox.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2320 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe /C | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | ytfovlym.exe | |||||||||||
User: admin Company: Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Java(TM) Plug-in for Internet Explorer Exit code: 0 Version: 5.0.60.5 Modules
| |||||||||||||||
| 2404 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | DUZGZkDG.exe | |||||||||||
User: admin Company: Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Java(TM) Plug-in for Internet Explorer Exit code: 0 Version: 5.0.60.5 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://giovannadurso.com/media/editors/tinymce/jscripts/tiny_mce/plugins/inlinepopups/skins/clearlooks2/img/ST4508560975766_911722.zip | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2488 | "C:\Windows\System32\cmd.exe" /c ping.exe -n 6 127.0.0.1 & type "C:\Windows\System32\calc.exe" > "C:\Users\admin\AppData\Local\Temp\DUZGZkDG.exe" | C:\Windows\System32\cmd.exe | DUZGZkDG.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2996 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2428.13.1110991345\671911562" -childID 2 -isForBrowser -prefsHandle 2820 -prefMapHandle 2824 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2428 "\\.\pipe\gecko-crash-server-pipe.2428" 2836 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2428.0.1209772159\1450506228" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2428 "\\.\pipe\gecko-crash-server-pipe.2428" 1136 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3372 | C:\Users\admin\AppData\Local\Temp\DUZGZkDG.exe | C:\Users\admin\AppData\Local\Temp\DUZGZkDG.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Java(TM) Plug-in for Internet Explorer Exit code: 0 Version: 5.0.60.5 Modules
| |||||||||||||||
Total events
1 408
Read events
1 375
Write events
33
Delete events
0
Modification events
| (PID) Process: | (2428) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 25BE403601000000 | |||
| (PID) Process: | (3536) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: B6103D3601000000 | |||
| (PID) Process: | (2428) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2428) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2428) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2428) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2428) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2428) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
Executable files
3
Suspicious files
77
Text files
37
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2428 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2428 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2428 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2428 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2428 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2428 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2428 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 2428 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2428 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
| 2428 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\doomed\29978 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
35
DNS requests
82
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2428 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2428 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2428 | firefox.exe | GET | 200 | 104.18.54.201:80 | http://giovannadurso.com/.well-known/http-opportunistic | US | text | 98 b | shared |
2428 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2428 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2428 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2428 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2428 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2428 | firefox.exe | GET | 200 | 104.18.54.201:80 | http://giovannadurso.com/media/editors/tinymce/jscripts/tiny_mce/plugins/inlinepopups/skins/clearlooks2/img/ST4508560975766_911722.zip | US | compressed | 1.09 Mb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2428 | firefox.exe | 34.208.5.128:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
2428 | firefox.exe | 35.166.89.106:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2428 | firefox.exe | 52.222.251.168:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2428 | firefox.exe | 104.18.54.201:80 | giovannadurso.com | Cloudflare Inc | US | shared |
2428 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2428 | firefox.exe | 104.18.54.201:443 | giovannadurso.com | Cloudflare Inc | US | shared |
2428 | firefox.exe | 52.36.193.139:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2428 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2428 | firefox.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2428 | firefox.exe | 172.217.21.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
giovannadurso.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |