| File name: | client.jar |
| Full analysis: | https://app.any.run/tasks/063c777b-f72c-48c2-9c2e-29dab1ae0dc0 |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | November 29, 2024, 22:02:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D091E0C194AA72DA2A697D269F67EBA1 |
| SHA1: | 615843C2DF96A019CC2C495DD219A050CC4BFA06 |
| SHA256: | 53A690981032AF4FC1BA3162EBBAC61EB03FBD14392A5BC9FD7781ECA1F8DE9B |
| SSDEEP: | 24576:/YjCH4q8AVpNhdqFlH5KEOpoMe/vCMyvKSwHKx3CjEewl7+2RlU:/YjCH4q8AVpNhdaH5KBpoMSvCMyvKSwB |
MALICIOUS
ADWIND has been detected
- javaw.exe (PID: 4320)
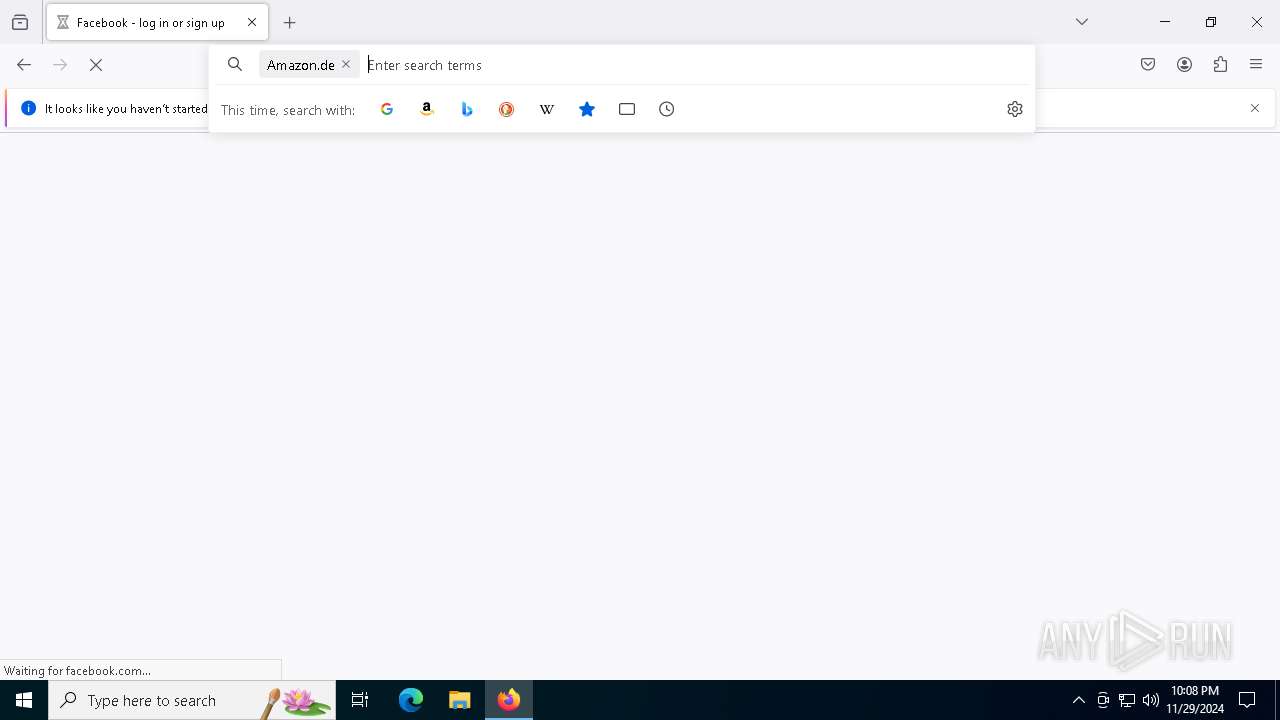
Steals credentials from Web Browsers
- javaw.exe (PID: 4320)
Actions looks like stealing of personal data
- javaw.exe (PID: 4320)
Starts CMD.EXE for self-deleting
- javaw.exe (PID: 4320)
ADWIND has been detected (SURICATA)
- javaw.exe (PID: 4320)
SUSPICIOUS
Uses WMIC.EXE to obtain Windows Installer data
- javaw.exe (PID: 4320)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 4388)
Connects to unusual port
- javaw.exe (PID: 4320)
Executable content was dropped or overwritten
- javaw.exe (PID: 4320)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 4320)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3544)
Hides command output
- cmd.exe (PID: 4864)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 4864)
INFO
Creates files in the program directory
- javaw.exe (PID: 4320)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 4388)
Application based on Java
- javaw.exe (PID: 4320)
Creates files or folders in the user directory
- javaw.exe (PID: 4320)
Reads the computer name
- javaw.exe (PID: 4320)
Checks supported languages
- javaw.exe (PID: 4320)
Reads the machine GUID from the registry
- javaw.exe (PID: 4320)
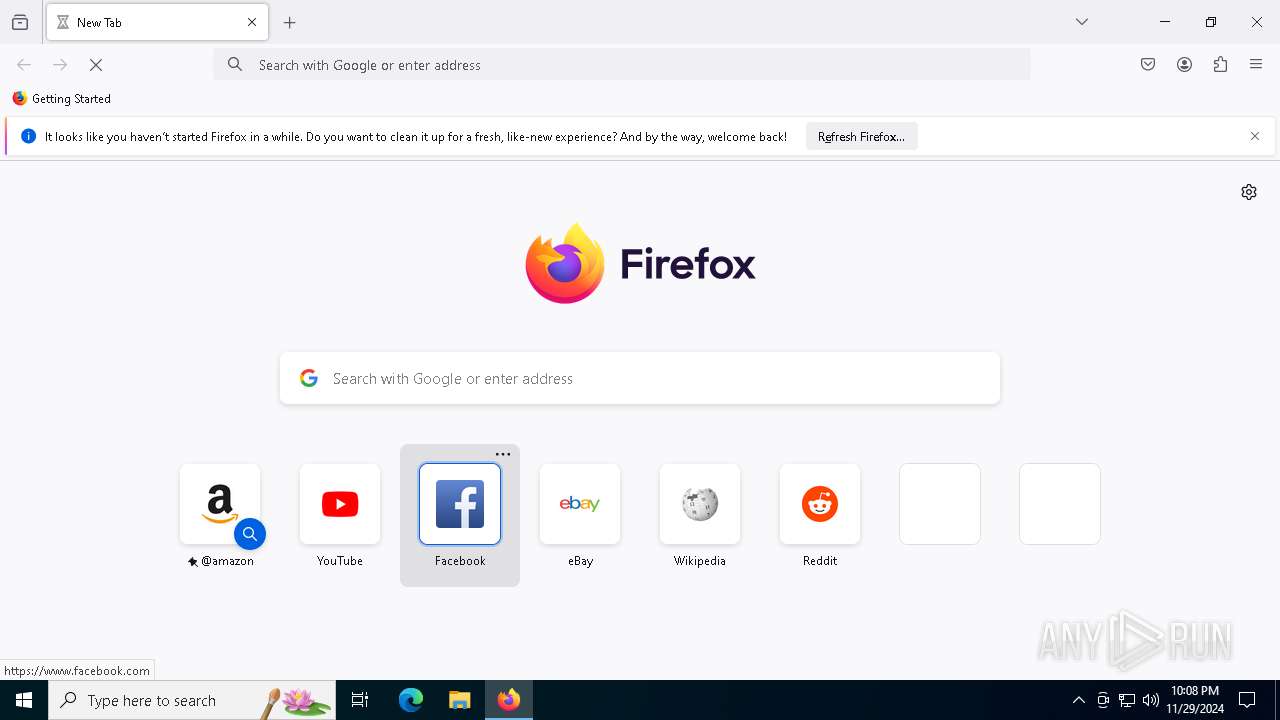
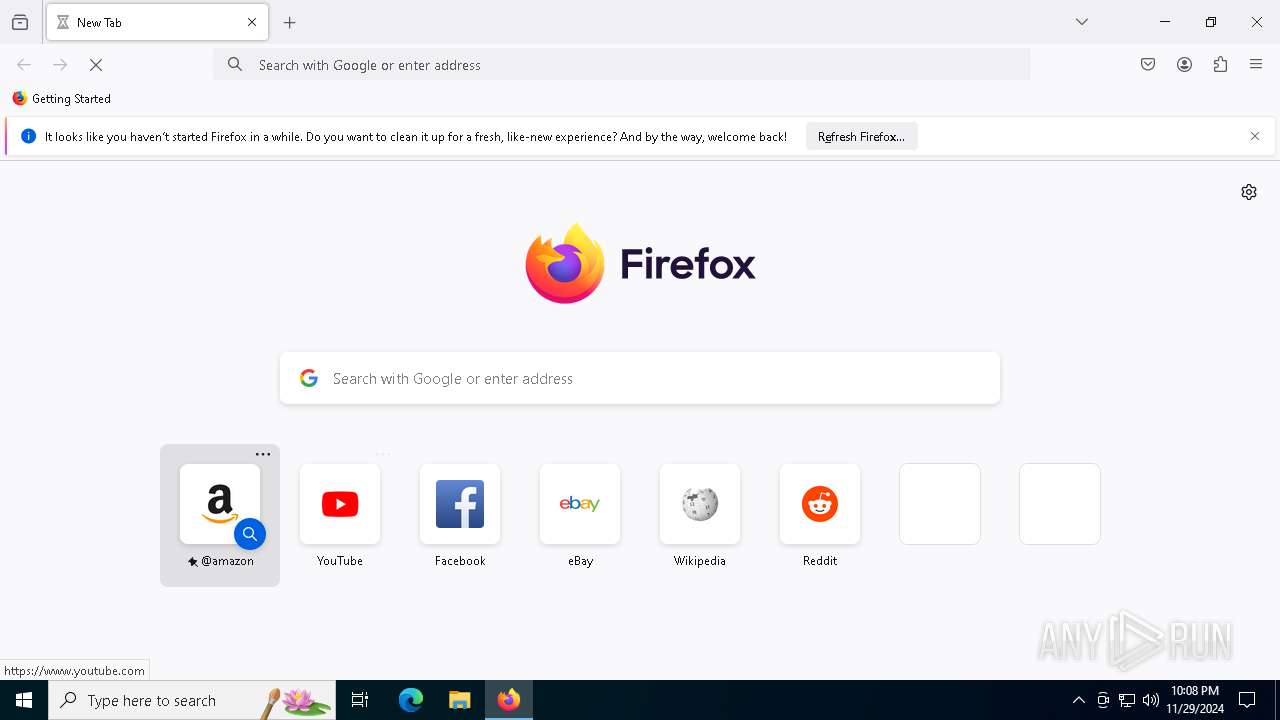
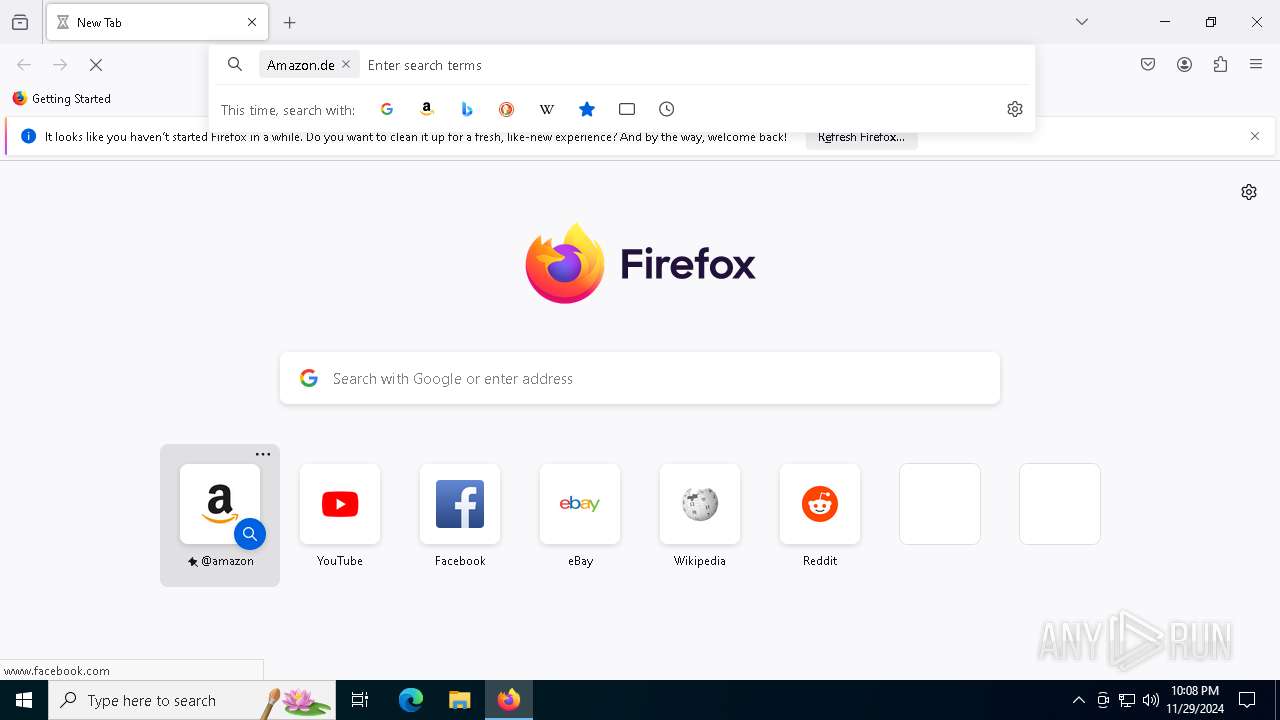
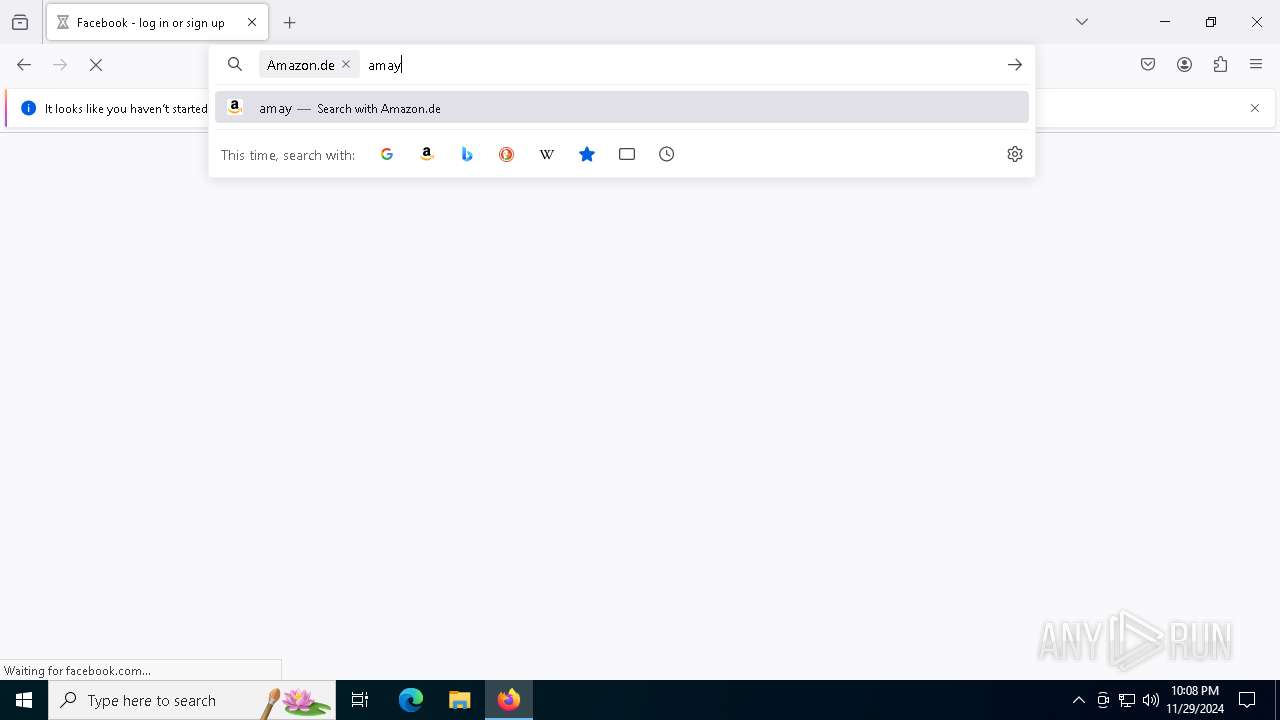
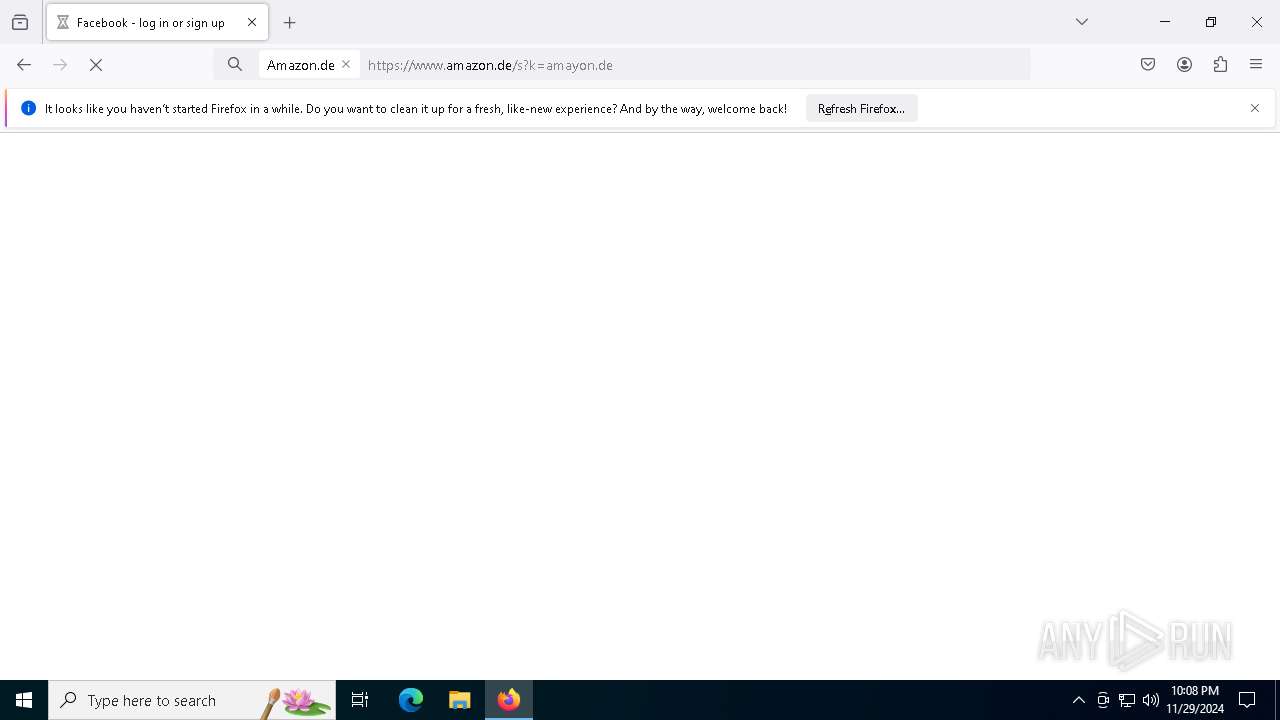
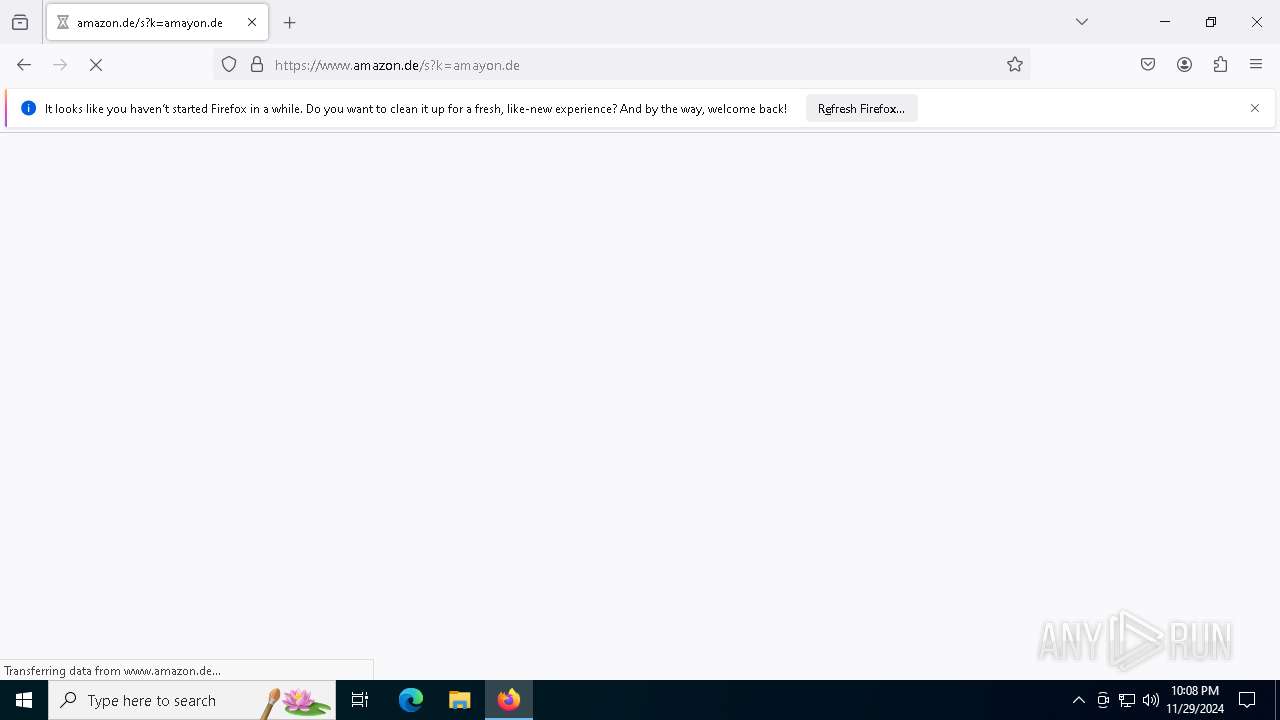
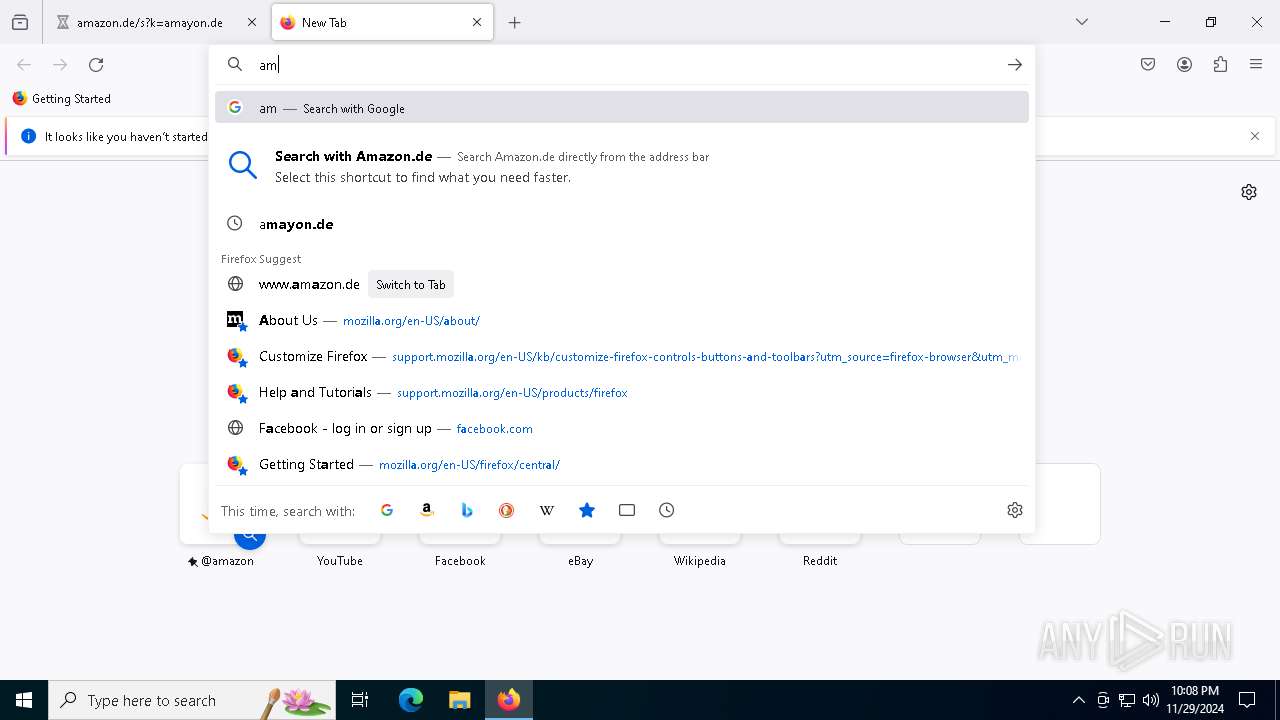
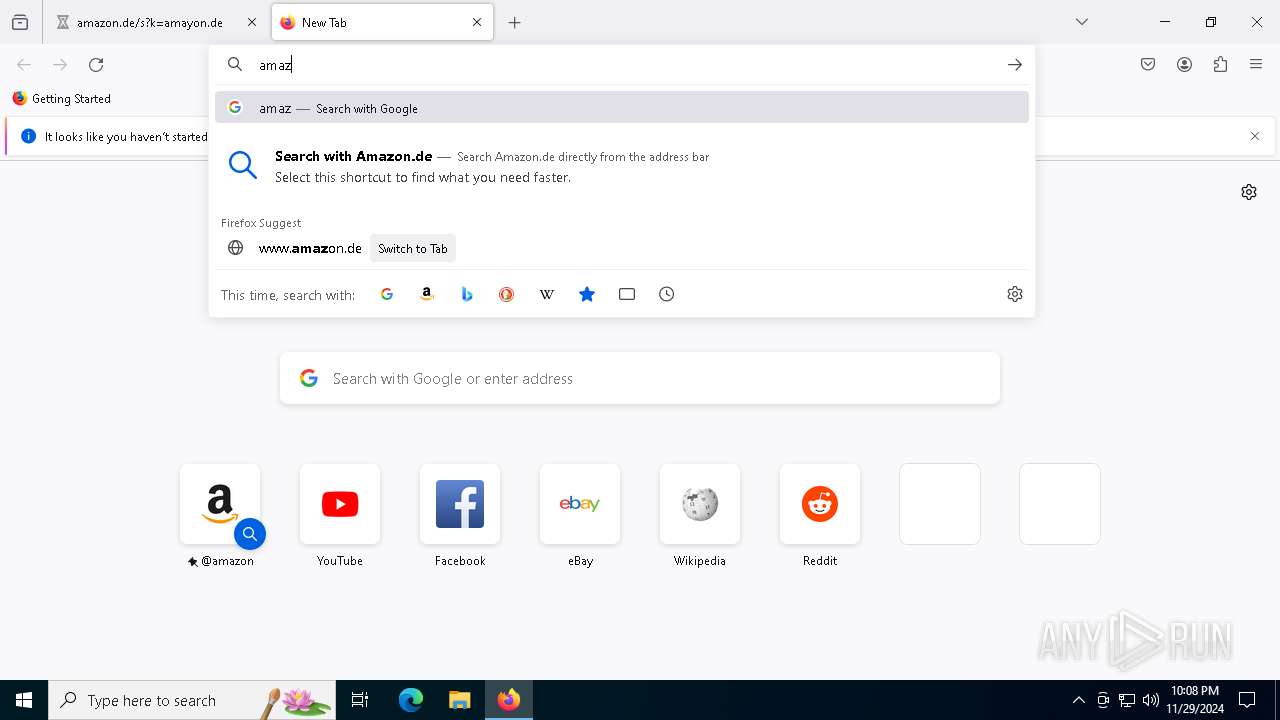
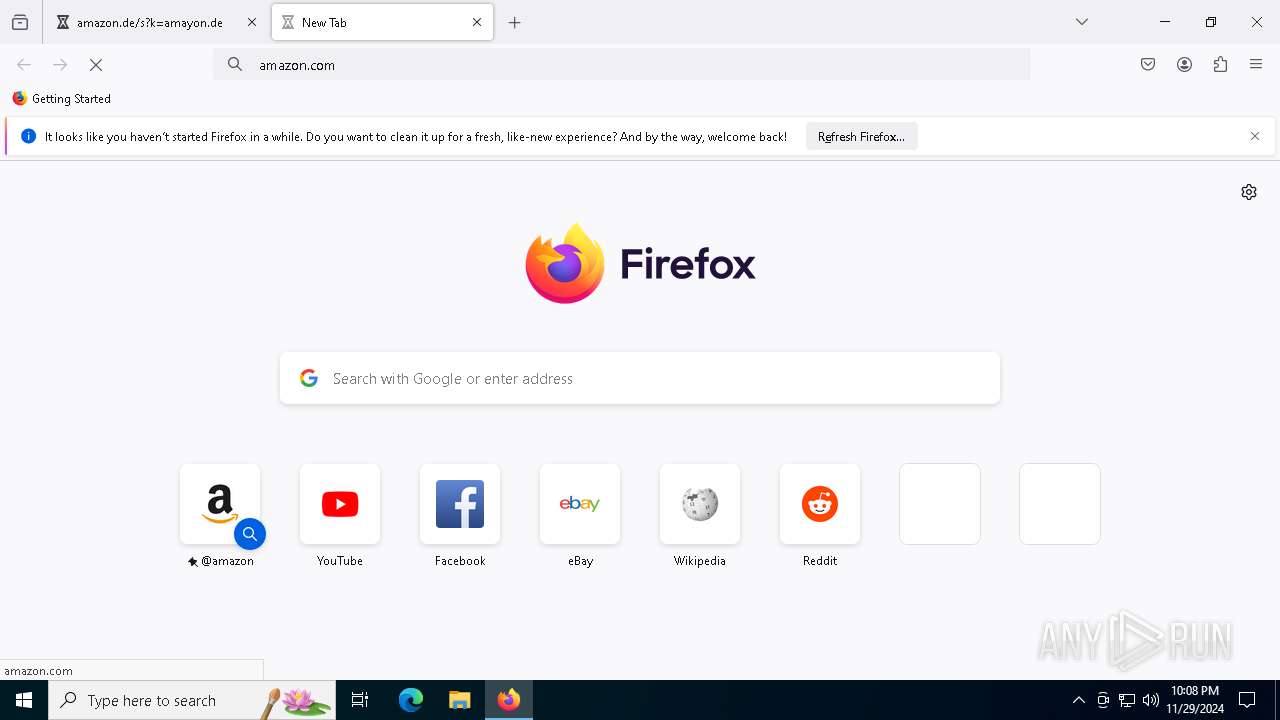
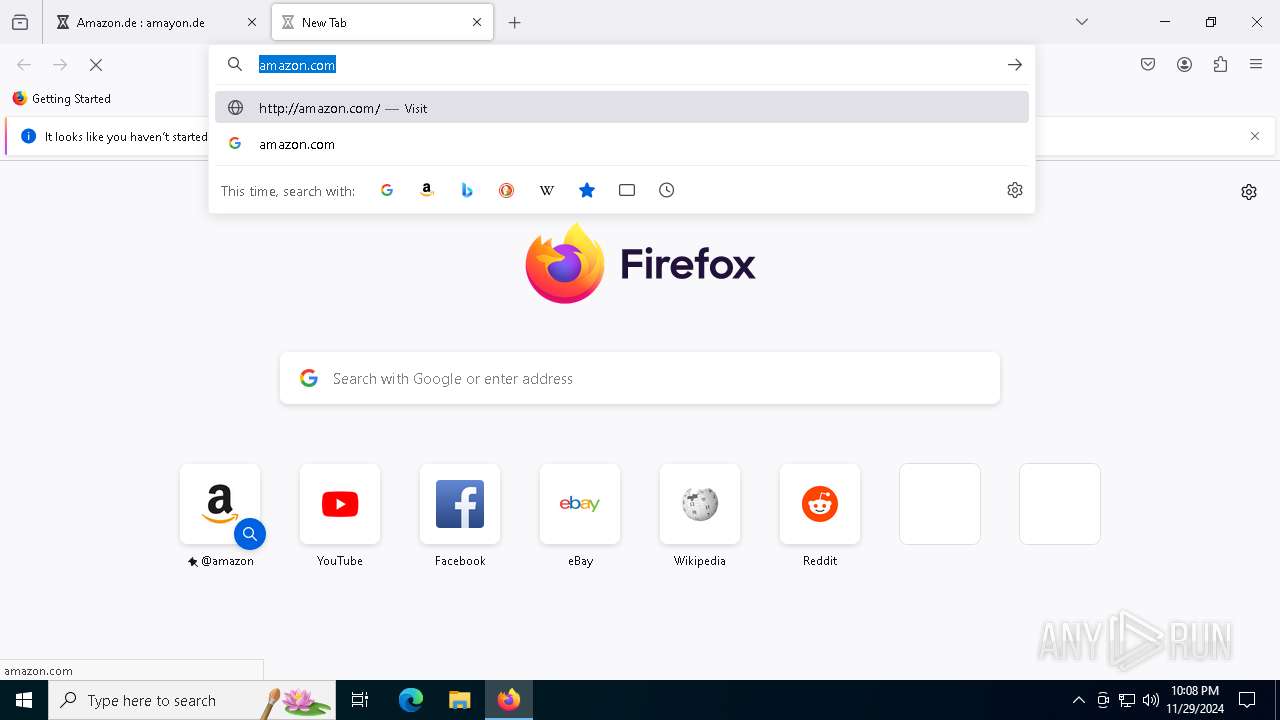
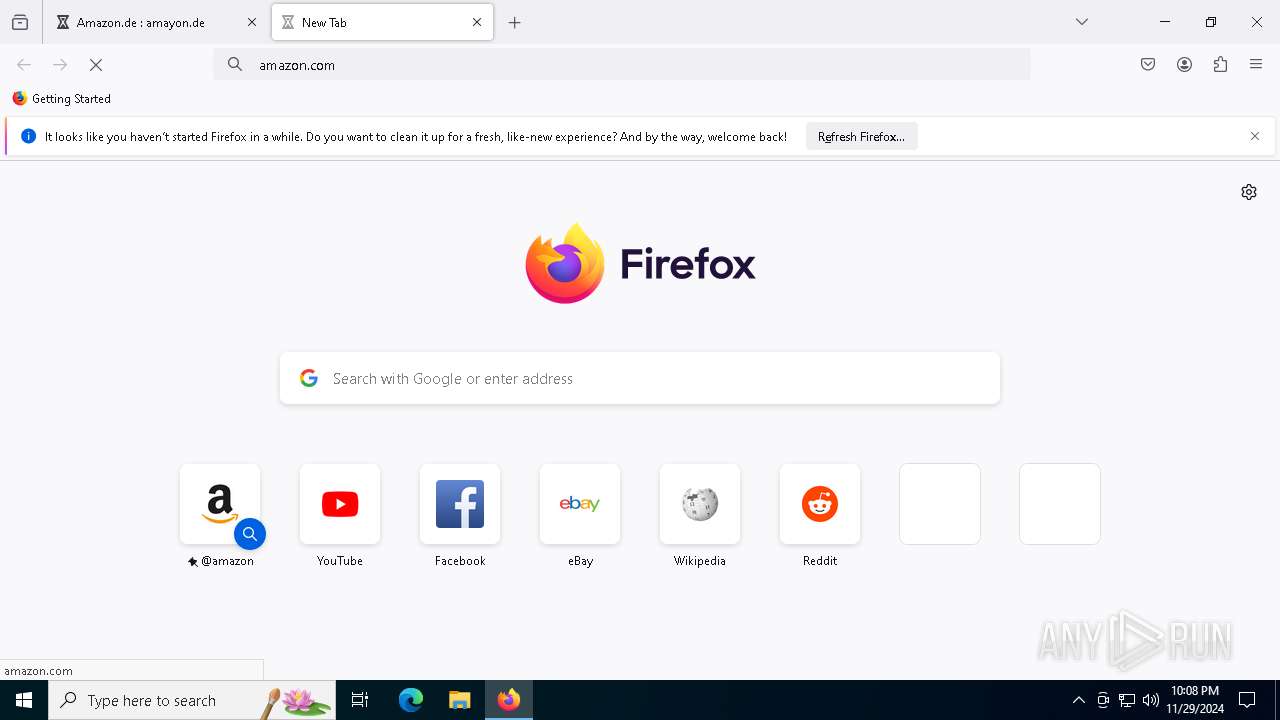
Manual execution by a user
- firefox.exe (PID: 5848)
Create files in a temporary directory
- javaw.exe (PID: 4320)
Application launched itself
- firefox.exe (PID: 5848)
- firefox.exe (PID: 2212)
Executable content was dropped or overwritten
- firefox.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:11:29 22:49:42 |
| ZipCRC: | 0x5a7c0dba |
| ZipCompressedSize: | 1751 |
| ZipUncompressedSize: | 4422 |
| ZipFileName: | IIllIlIlI/lIlIIIlIl/IIllII/IlllIIlI/llIllIlllllllIIIIlI.class |
Total processes
154
Monitored processes
27
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1304 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2672 -childID 1 -isForBrowser -prefsHandle 2864 -prefMapHandle 2860 -prefsLen 31447 -prefMapSize 244583 -jsInitHandle 1472 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {67a523db-ad8e-4572-a71c-b98f6eee45a8} 2212 "\\.\pipe\gecko-crash-server-pipe.2212" 23b2af9dd90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2144 -parentBuildID 20240213221259 -prefsHandle 2136 -prefMapHandle 2124 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {526d0db3-a6b8-4ab7-b66a-955da4d920f4} 2212 "\\.\pipe\gecko-crash-server-pipe.2212" 23b19281510 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2332 | REG DELETE HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v Home /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3544 | cmd.exe /c "REG DELETE HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v Home /f" | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | C:\WINDOWS\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3632 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1912 -parentBuildID 20240213221259 -prefsHandle 1852 -prefMapHandle 1840 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {183fa7b0-921a-4c85-af58-8d15dee6b21a} 2212 "\\.\pipe\gecko-crash-server-pipe.2212" 23b25ff0c10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4036 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4240 -childID 2 -isForBrowser -prefsHandle 4232 -prefMapHandle 4228 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1472 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {ab80339e-a23d-4342-9fc5-4d7cb7ea6194} 2212 "\\.\pipe\gecko-crash-server-pipe.2212" 23b2d1b7a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
21 104
Read events
21 102
Write events
1
Delete events
1
Modification events
| (PID) Process: | (2212) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (2332) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Home |
Value: | |||
Executable files
4
Suspicious files
163
Text files
79
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2212 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4320 | javaw.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Login Data For Account.db | sqlite | |
MD5:A45465CDCDC6CB30C8906F3DA4EC114C | SHA256:4412319EF944EBCCA9581CBACB1D4E1DC614C348D1DFC5D2FAAAAD863D300209 | |||
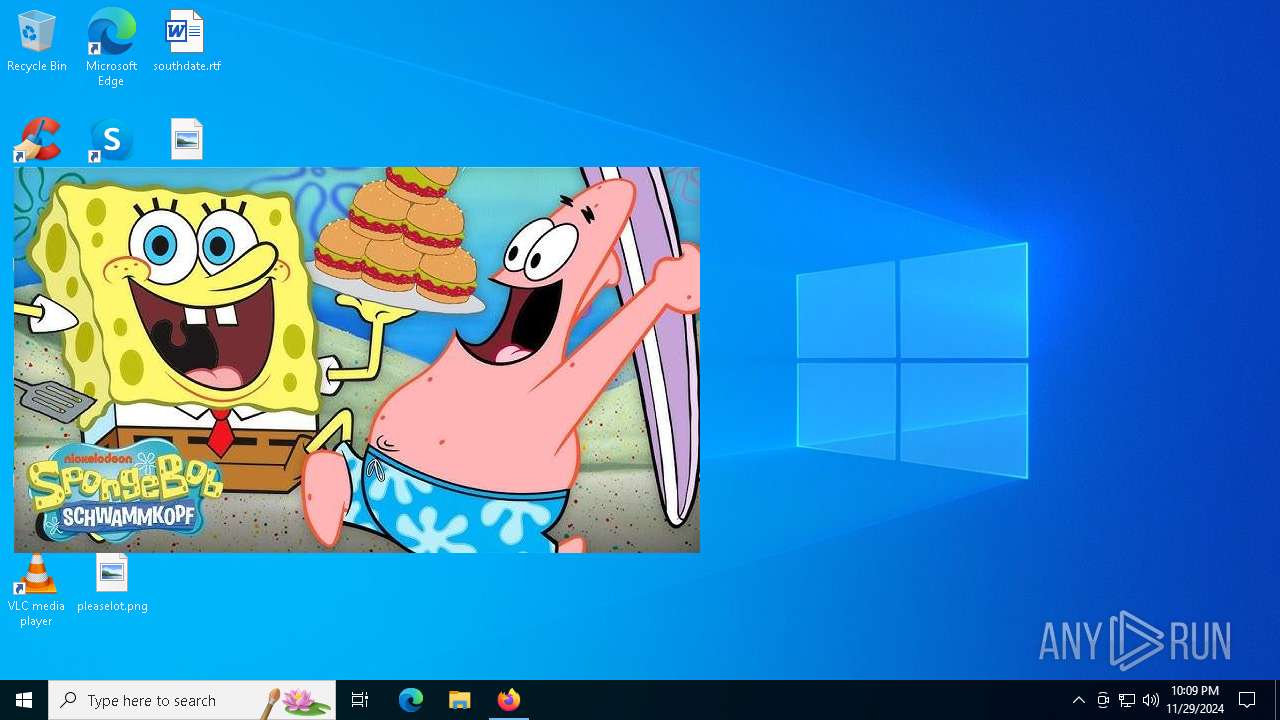
| 4320 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio8656205670201255848.tmp | image | |
MD5:060F557100559AC8251D9A4430C53031 | SHA256:6F3608CE89DF7DF417A805E289E69E7D4026A0FA247387D3753E7858BDD99E76 | |||
| 4320 | javaw.exe | C:\Users\admin\.plugins\.libraries\jna70 | compressed | |
MD5:B22EF746FD14C702E5BD29B466C6312B | SHA256:121F7A1D3AA9F538FD4710FD3A2175A7F062E1260D3E2DF83752512A28F290D6 | |||
| 4320 | javaw.exe | C:\Users\admin\AppData\Local\Temp\tmpus7439296857933654159upl | compressed | |
MD5:B22EF746FD14C702E5BD29B466C6312B | SHA256:121F7A1D3AA9F538FD4710FD3A2175A7F062E1260D3E2DF83752512A28F290D6 | |||
| 4320 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\83aa4cc77f591dfc2374580bbd95f6ba_bb926e54-e3ca-40fd-ae90-2764341e7792 | binary | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 4320 | javaw.exe | C:\Users\admin\AppData\Local\Temp\sqlite-unknown-cb8b0d06-bb84-40cf-8c8c-e7abdb242193-sqlitejdbc.dll | executable | |
MD5:98EAC6AD76D39E73967252542F6F40E4 | SHA256:51CC105F172859E6866F3CAD5C99188663BE503CD4BB618C946B0C83FAABF0B8 | |||
| 4320 | javaw.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Login Data.db | binary | |
MD5:A45465CDCDC6CB30C8906F3DA4EC114C | SHA256:4412319EF944EBCCA9581CBACB1D4E1DC614C348D1DFC5D2FAAAAD863D300209 | |||
| 4320 | javaw.exe | C:\Users\admin\AppData\Local\Temp\tmpus1336807705342512050upl | compressed | |
MD5:137A448313D5B6D19279833D841B3590 | SHA256:DE349716E627E245E4B17FD487DBA4033DBC92E5E22FB950C25514700334F97E | |||
| 2212 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
83
TCP/UDP connections
387
DNS requests
419
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
524 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
524 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4264 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1576 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4264 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2212 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2212 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
2212 | firefox.exe | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/s/wr3/yvU | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
524 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1576 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
524 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
524 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1576 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
only-decreased.gl.at.ply.gg |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2192 | svchost.exe | Misc activity | ET INFO Tunneling Service in DNS Lookup (* .ply .gg) |
4320 | javaw.exe | A Network Trojan was detected | BACKDOOR [ANY.RUN] Adwind TCP Initial Pcaket |