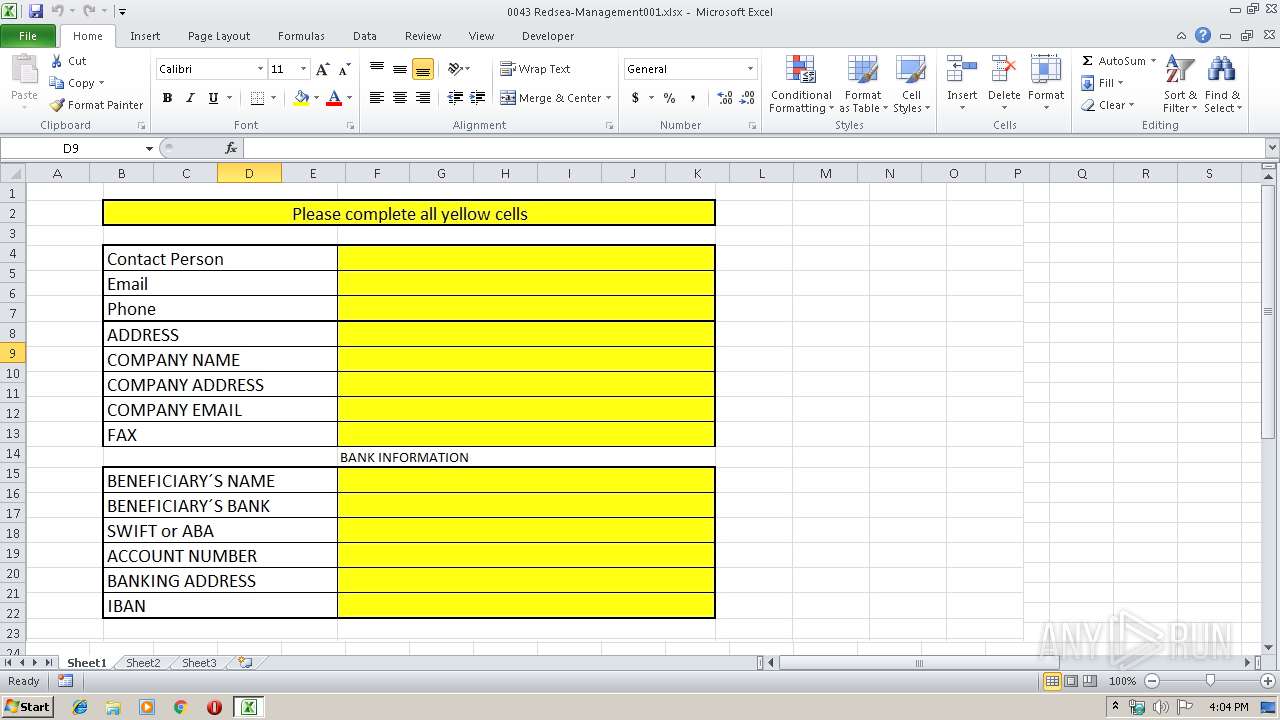
| File name: | 0043 Redsea-Management001.xlsx |
| Full analysis: | https://app.any.run/tasks/7d4fbad4-d997-4f2c-8900-ed3e0d07ac2c |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
| Analysis date: | September 18, 2019, 15:03:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | ED2140B0F5D41B0ECE518B62B7F25EA7 |
| SHA1: | 0ACA7E3A25494701511FE7862D59B05B26DC5865 |
| SHA256: | 5395FD196E20FF8A7C49CD83249275BB068AB02E224078B792383C11CD4F9329 |
| SSDEEP: | 24576:icR+meeWGT4EyCnvVcIuloCo8hlQlMvLKIUz1RVwOETJtRk1A:ixme4sFCnNYl+VlMjEz1YOMJtcA |
MALICIOUS
Detected Pony/Fareit Trojan
- RegAsm.exe (PID: 3056)
Application was dropped or rewritten from another process
- vbc.exe (PID: 3268)
Writes to a start menu file
- vbc.exe (PID: 3268)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3452)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 3452)
Connects to CnC server
- RegAsm.exe (PID: 3056)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 3056)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 3452)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3452)
- vbc.exe (PID: 3268)
Creates files in the user directory
- vbc.exe (PID: 3268)
Starts CMD.EXE for commands execution
- RegAsm.exe (PID: 3056)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2700 | cmd /c ""C:\Users\admin\AppData\Local\Temp\1494953.bat" "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" " | C:\Windows\system32\cmd.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3056 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | vbc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3268 | "C:\Users\Public\vbc.exe" | C:\Users\Public\vbc.exe | EQNEDT32.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3452 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3568 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 002
Read events
952
Write events
43
Delete events
7
Modification events
| (PID) Process: | (3568) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | <1$ |
Value: 3C312400F00D0000010000000000000000000000 | |||
| (PID) Process: | (3568) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3568) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3568) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: F00D00002ACA5656326ED50100000000 | |||
| (PID) Process: | (3568) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | <1$ |
Value: 3C312400F00D0000010000000000000000000000 | |||
| (PID) Process: | (3568) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3568) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3452) EQNEDT32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109E60090400000000000F01FEC\Usage |
| Operation: | write | Name: | EquationEditorFilesIntl_1033 |
Value: 1328676867 | |||
| (PID) Process: | (3568) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3568) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9D9C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3452 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\wop[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3268 | vbc.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\HJdyTuap.exe | executable | |
MD5:— | SHA256:— | |||
| 3452 | EQNEDT32.EXE | C:\Users\Public\vbc.exe | executable | |
MD5:— | SHA256:— | |||
| 3056 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\1494953.bat | text | |
MD5:3880EEB1C736D853EB13B44898B718AB | SHA256:936D9411D5226B7C5A150ECAF422987590A8870C8E095E1CAA072273041A86E7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3452 | EQNEDT32.EXE | GET | 200 | 207.55.244.103:80 | http://acmestoolsmfg.com/wop.exe | US | executable | 572 Kb | malicious |
3056 | RegAsm.exe | POST | — | 198.23.213.114:80 | http://hushpan.icu/jo/gate.php | US | — | — | malicious |
3056 | RegAsm.exe | GET | 404 | 198.23.213.114:80 | http://hushpan.icu/jo/jo.exe | US | html | 315 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3056 | RegAsm.exe | 198.23.213.114:80 | hushpan.icu | ColoCrossing | US | malicious |
3452 | EQNEDT32.EXE | 207.55.244.103:80 | acmestoolsmfg.com | CONTINENTAL BROADBAND PENNSYLVANIA, INC. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
acmestoolsmfg.com |
| malicious |
hushpan.icu |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3452 | EQNEDT32.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3452 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
3056 | RegAsm.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
3056 | RegAsm.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
3056 | RegAsm.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Internet Explorer Version MSIE 5. |
3056 | RegAsm.exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no referer |
3056 | RegAsm.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.icu domain |
3056 | RegAsm.exe | A Network Trojan was detected | ET TROJAN Pony Downloader HTTP Library MSIE 5 Win98 |
3056 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony Downloader Checkin |
1 ETPRO signatures available at the full report