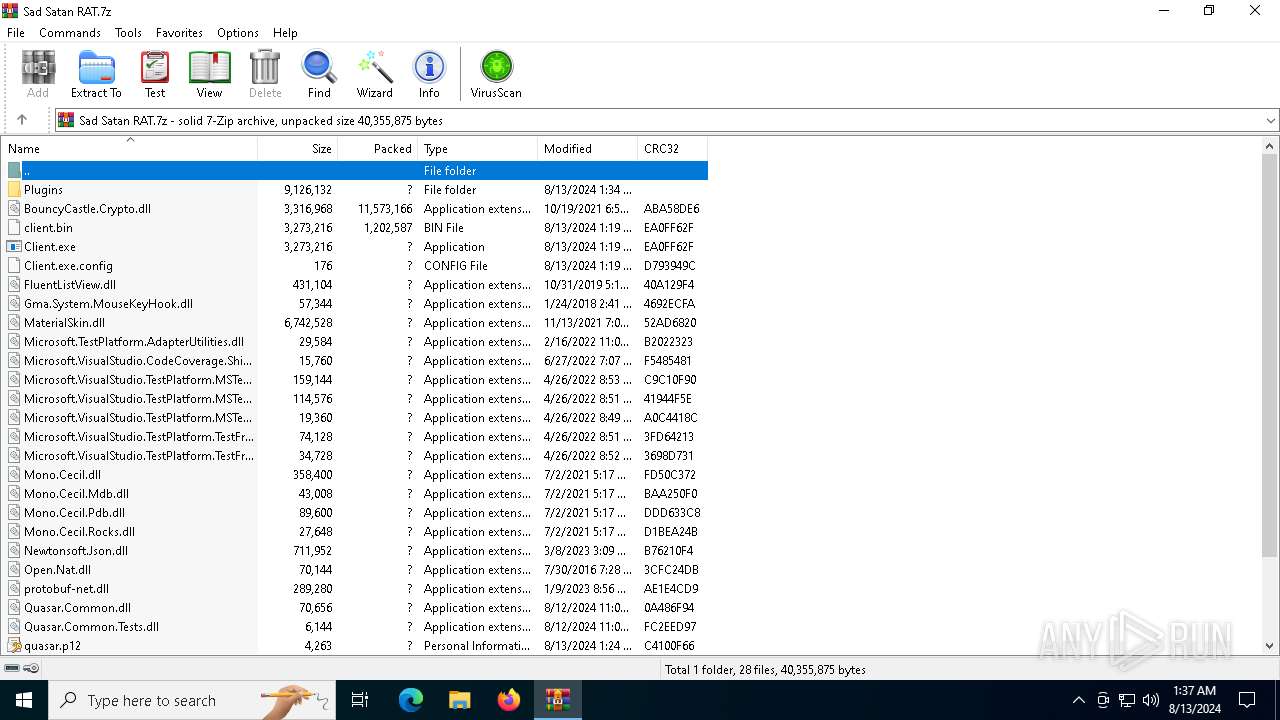
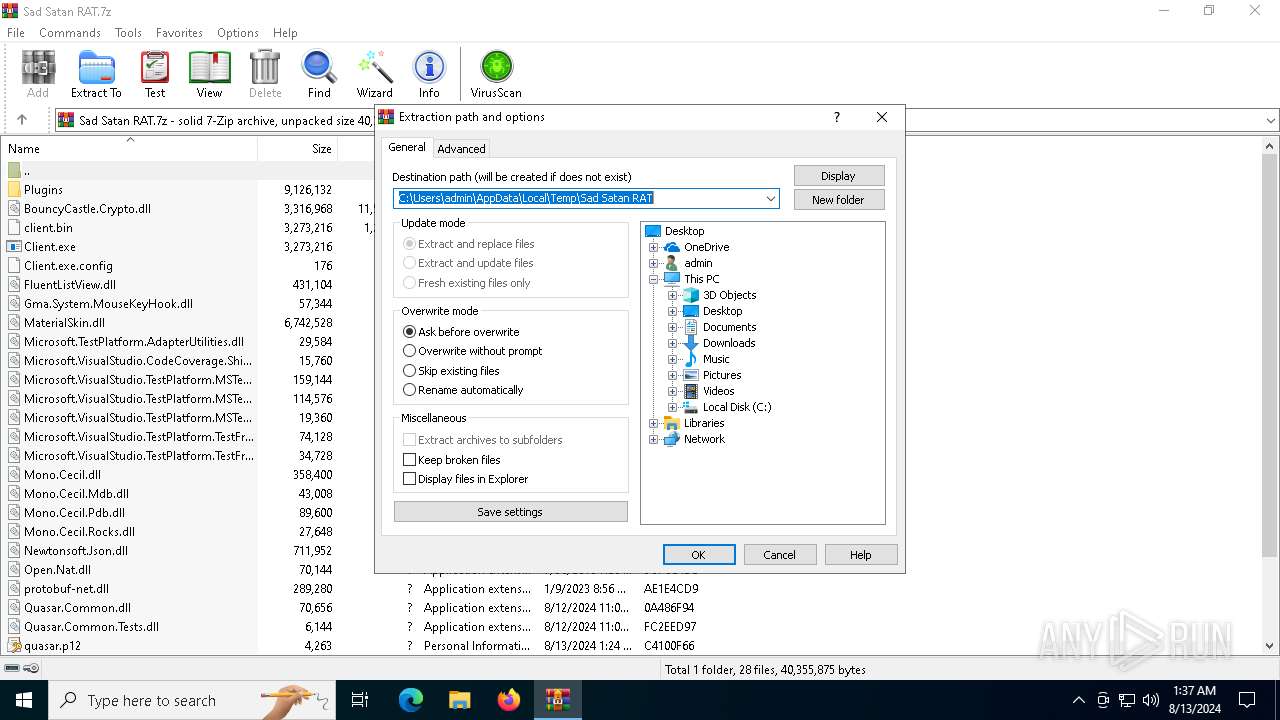
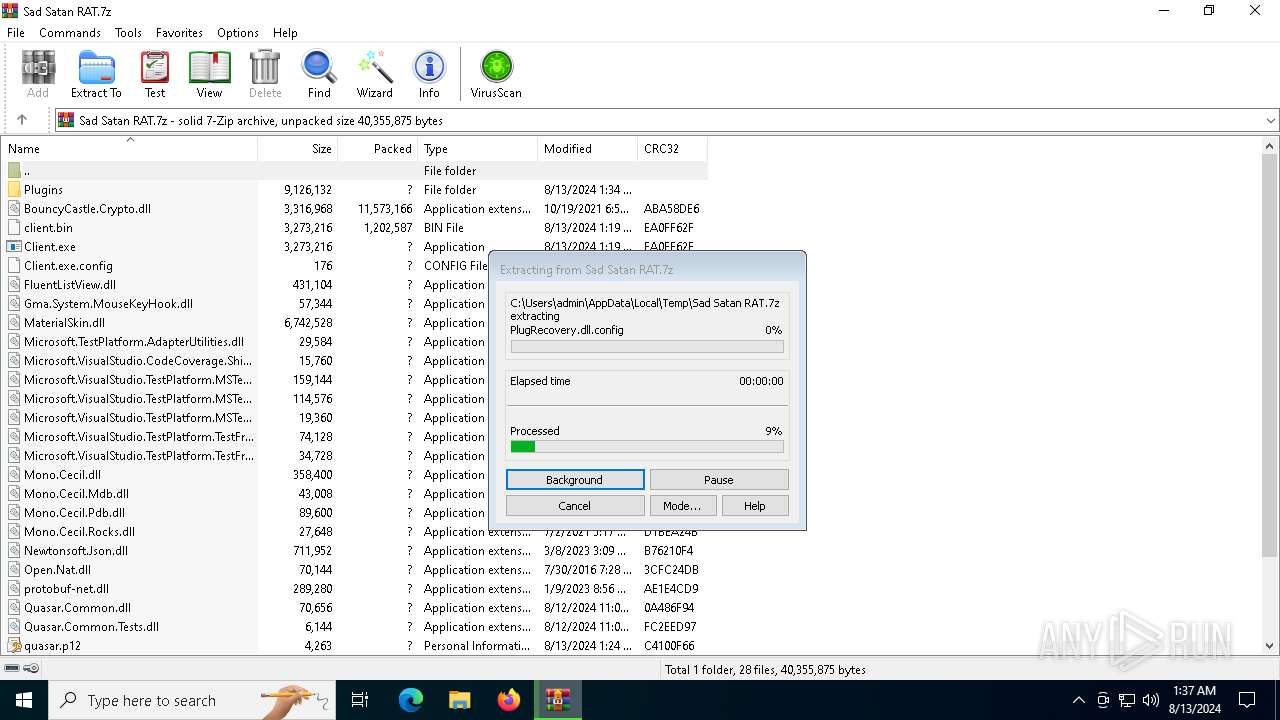
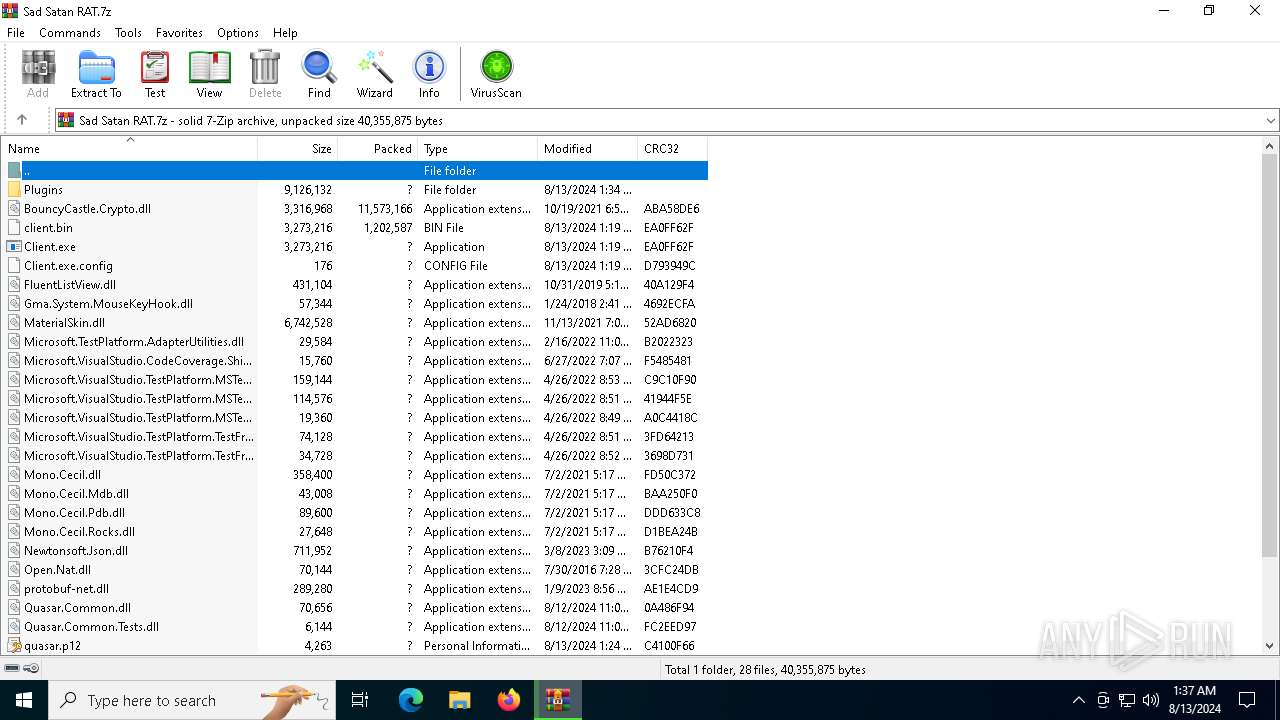
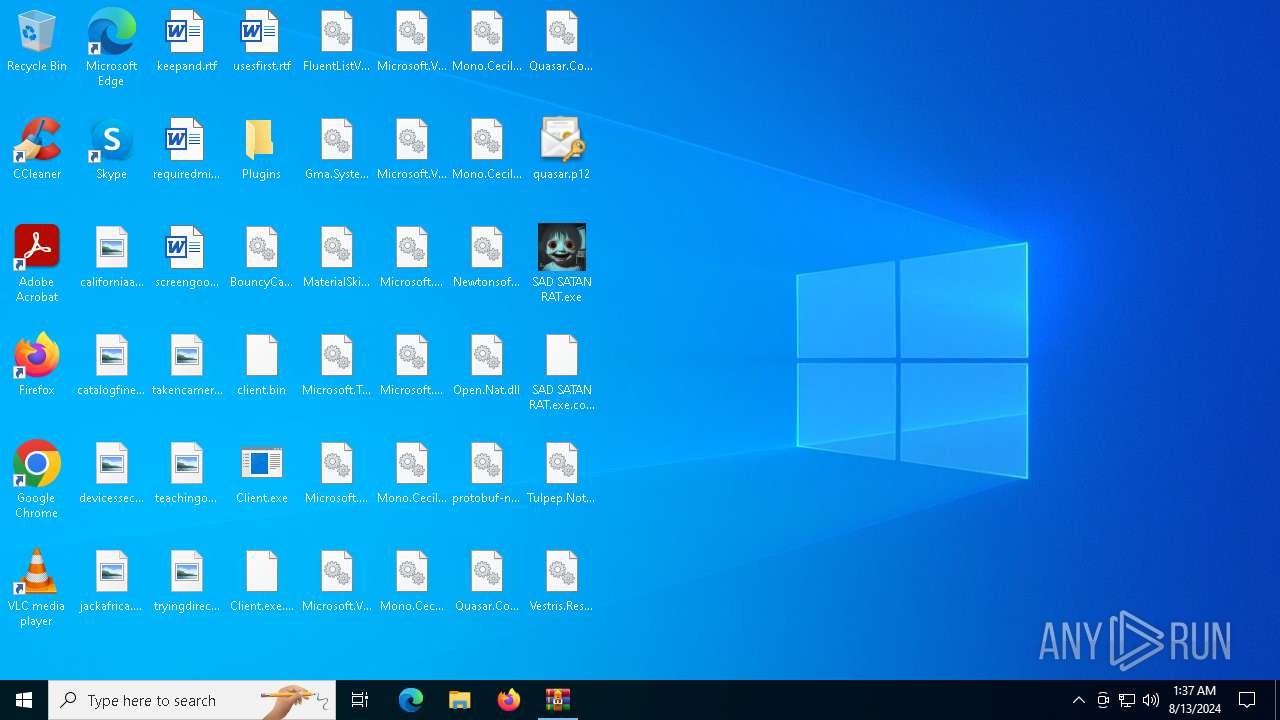
| File name: | Sad Satan RAT.7z |
| Full analysis: | https://app.any.run/tasks/3acb6031-38c5-4d48-897f-c10af74cc7bc |
| Verdict: | Malicious activity |
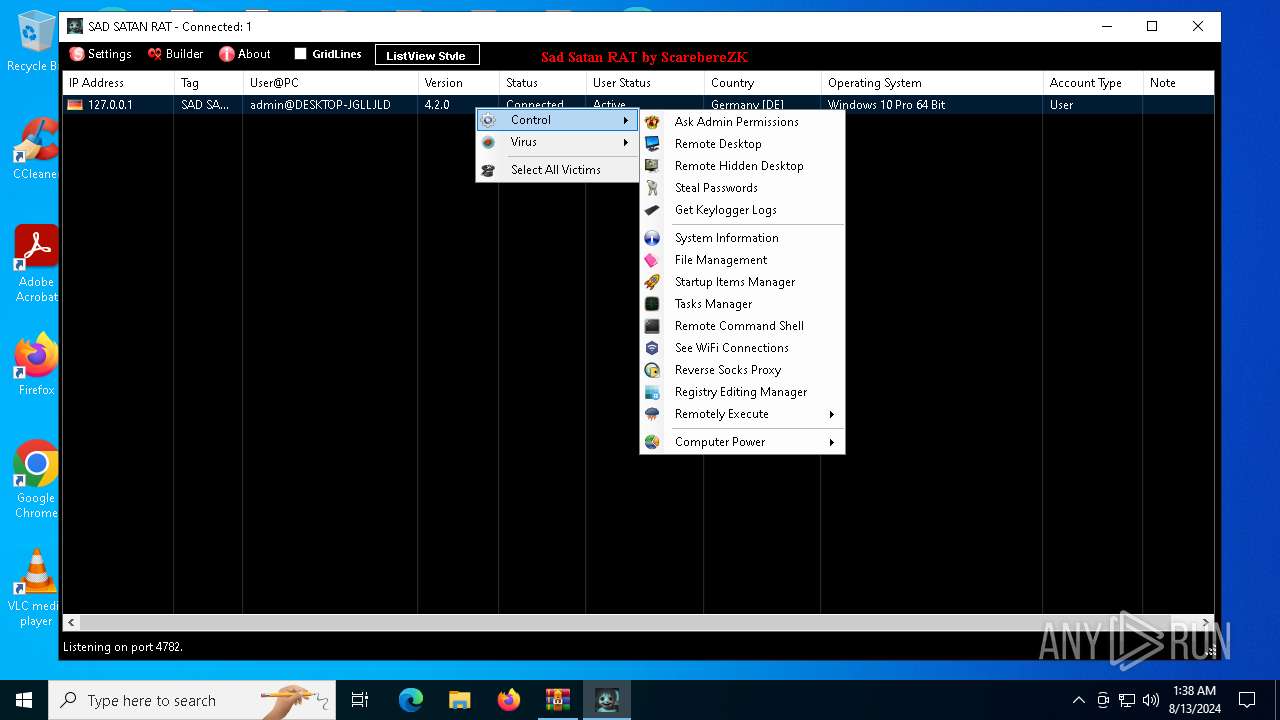
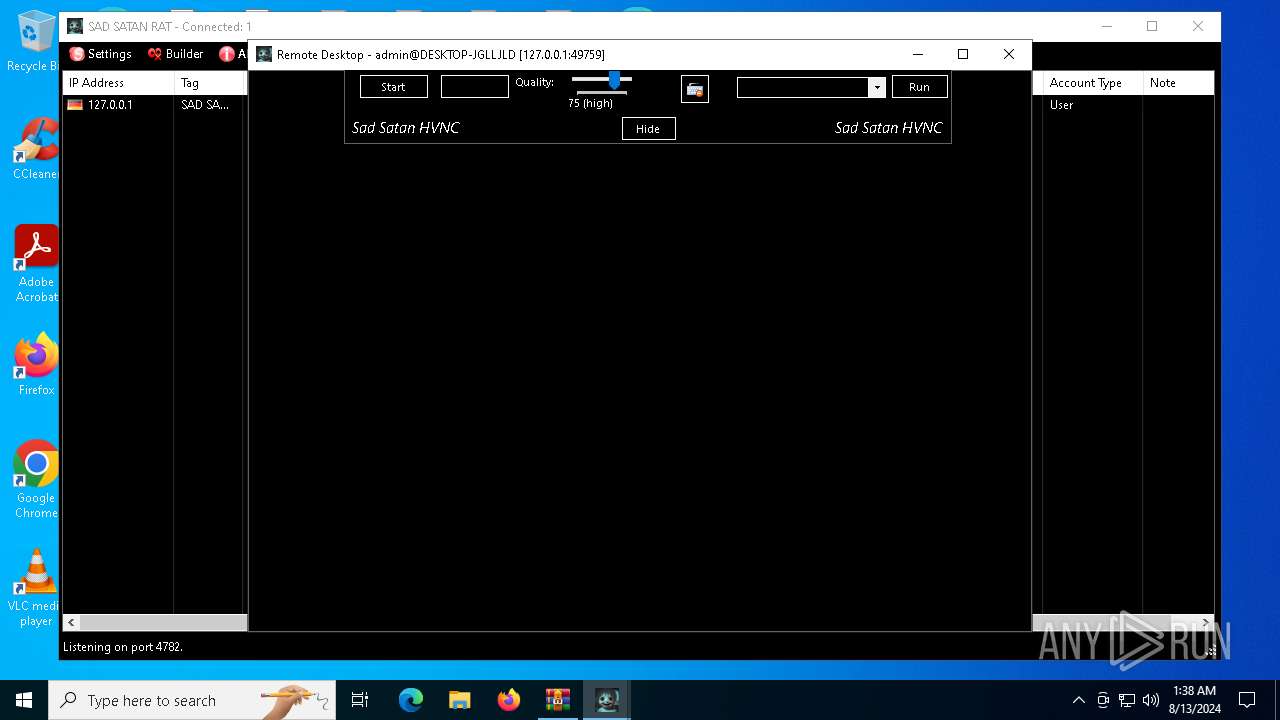
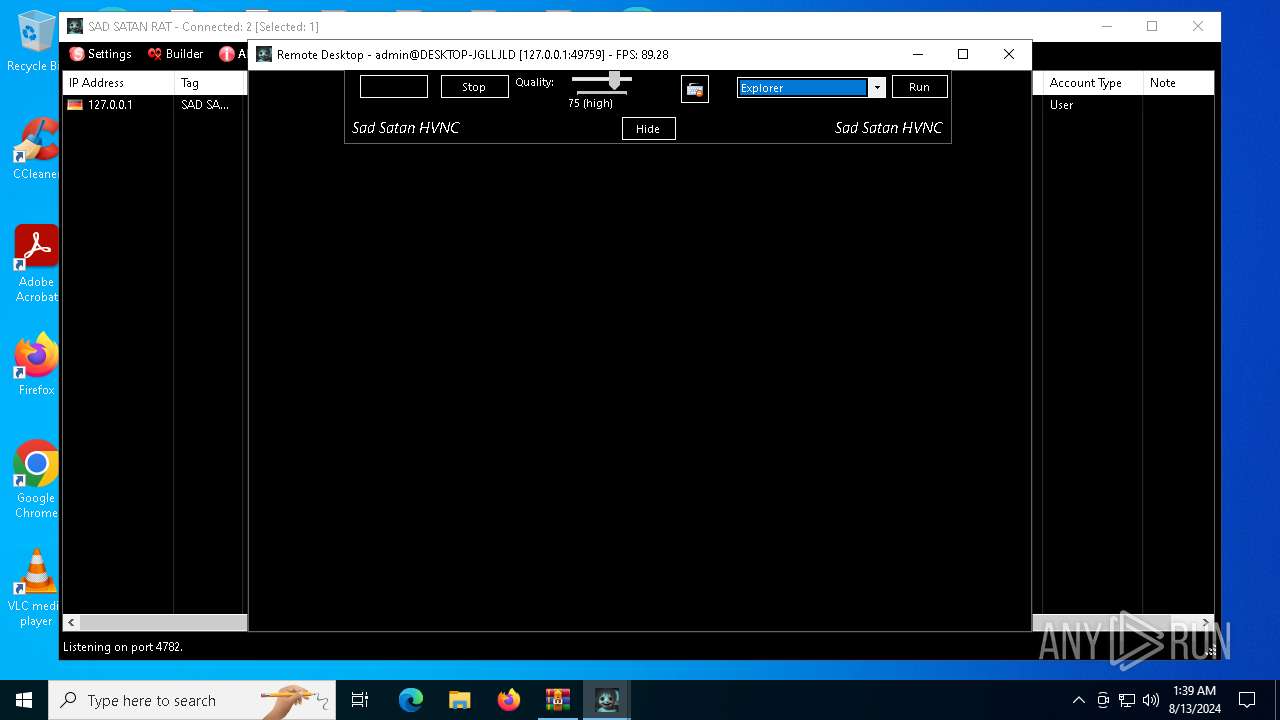
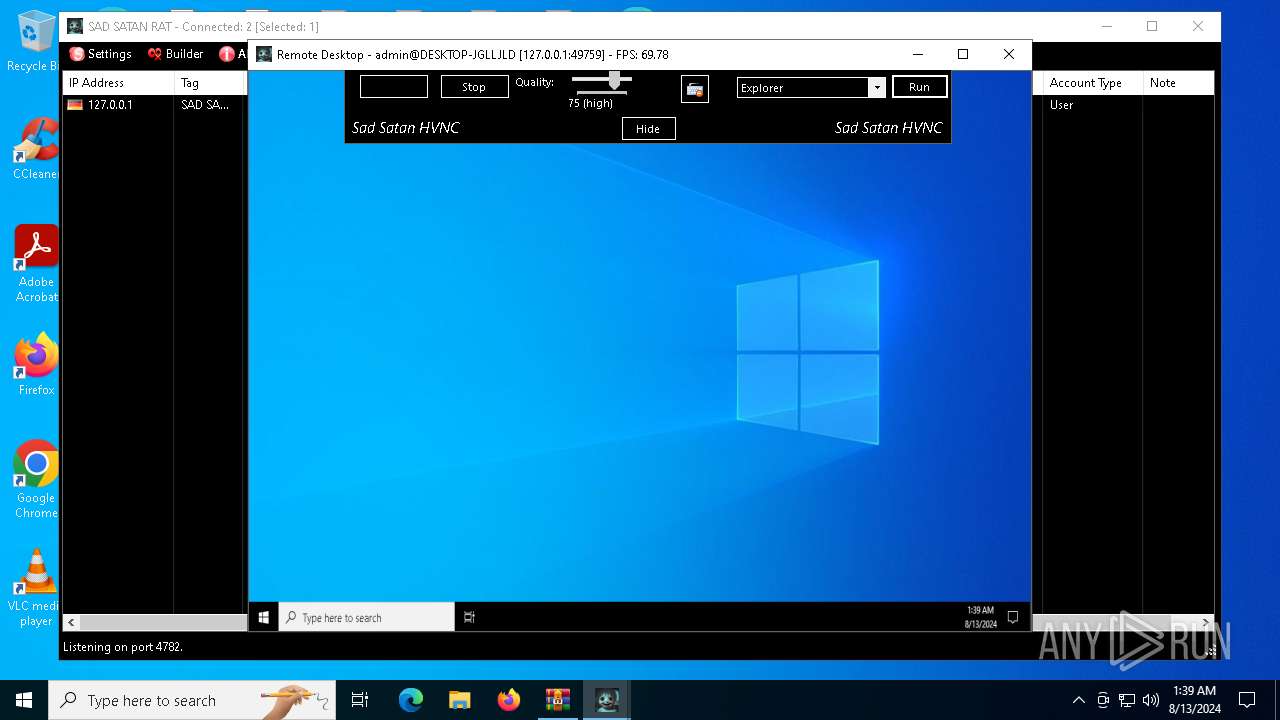
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | August 13, 2024, 01:36:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 1A50666803648F088807749A5223BA4C |
| SHA1: | 1FDD07D6EBFA32CC4CA45FE9B05E40144C53F898 |
| SHA256: | 53666C8B8F134B64CE161CCAE30B801BD7AB16A105C5F8402D189613EBF88F12 |
| SSDEEP: | 98304:0LexVVzxs4brrXnZdIjT+i/o2VvyWjIpa1fUQH82v8o2+EymMyWb4CwVYx2rJi31:brYA0JYmWXonHiw/wbPMH |
MALICIOUS
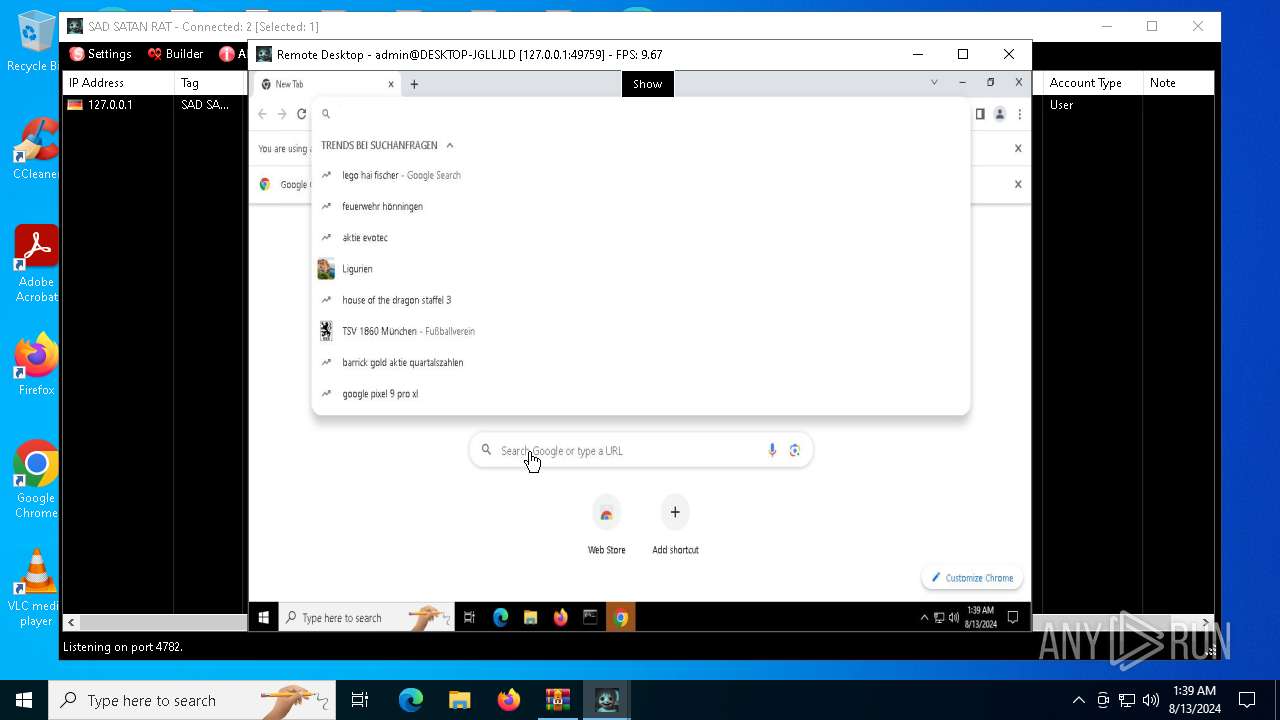
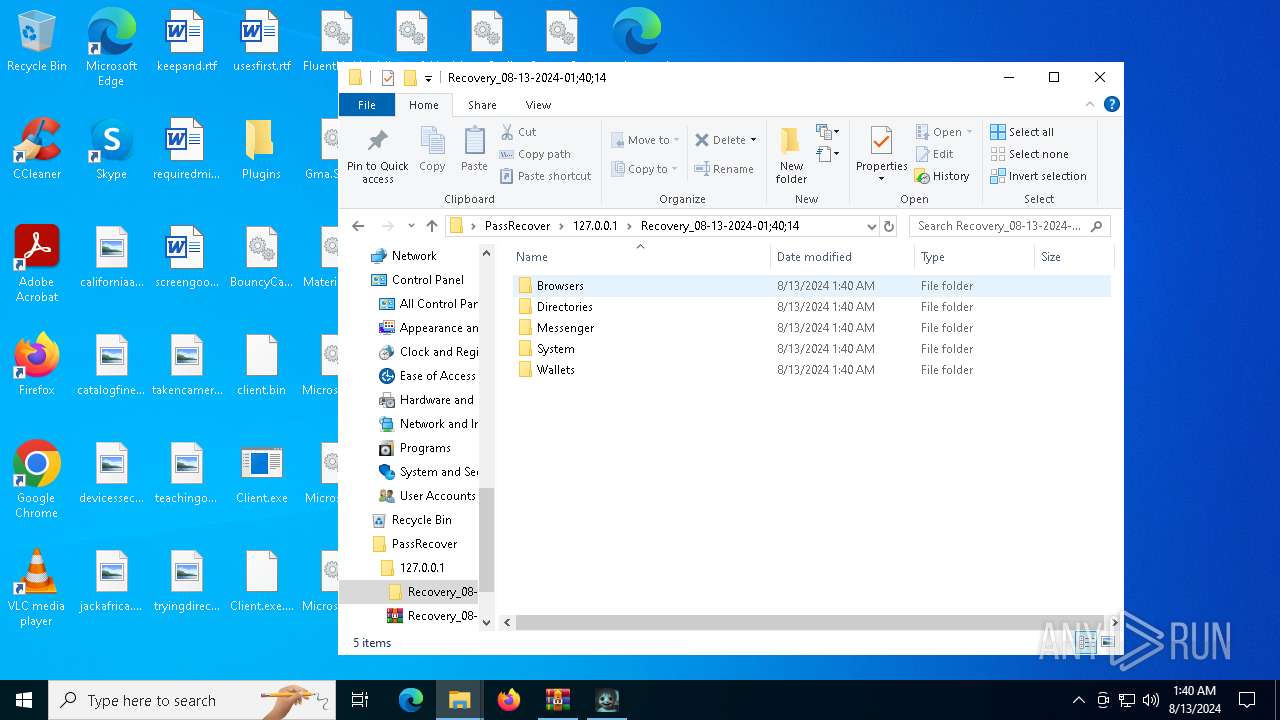
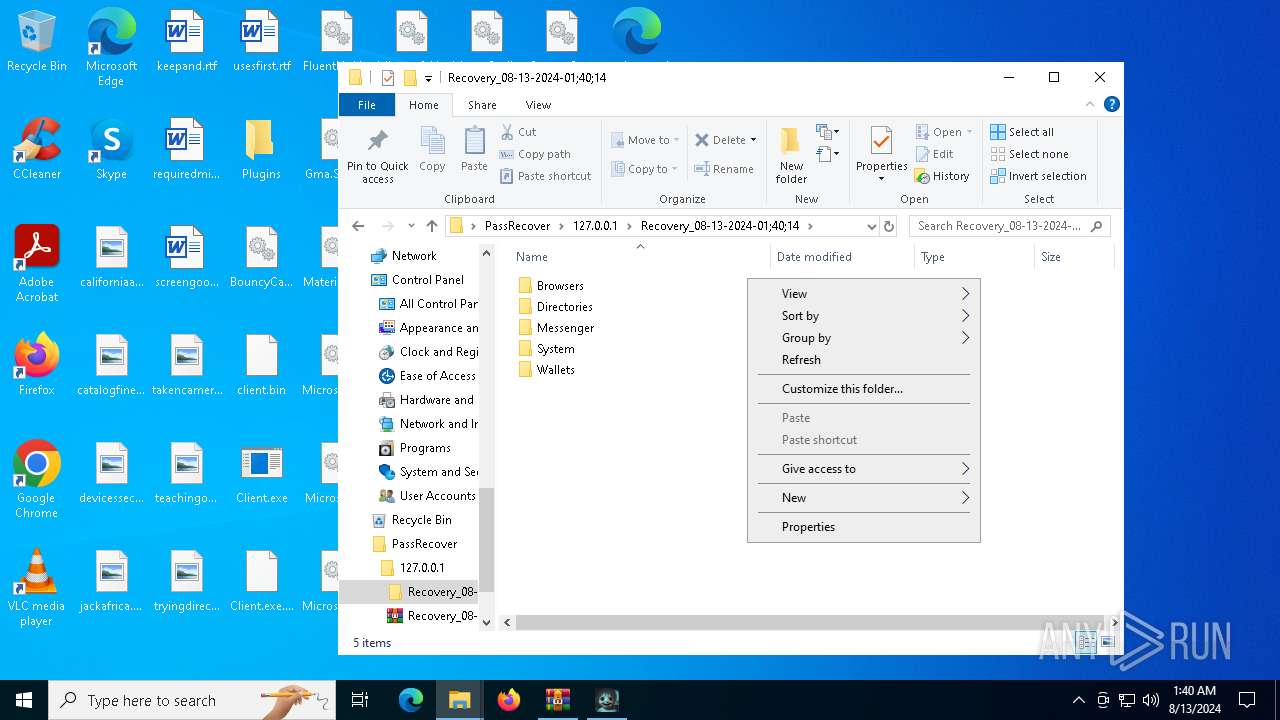
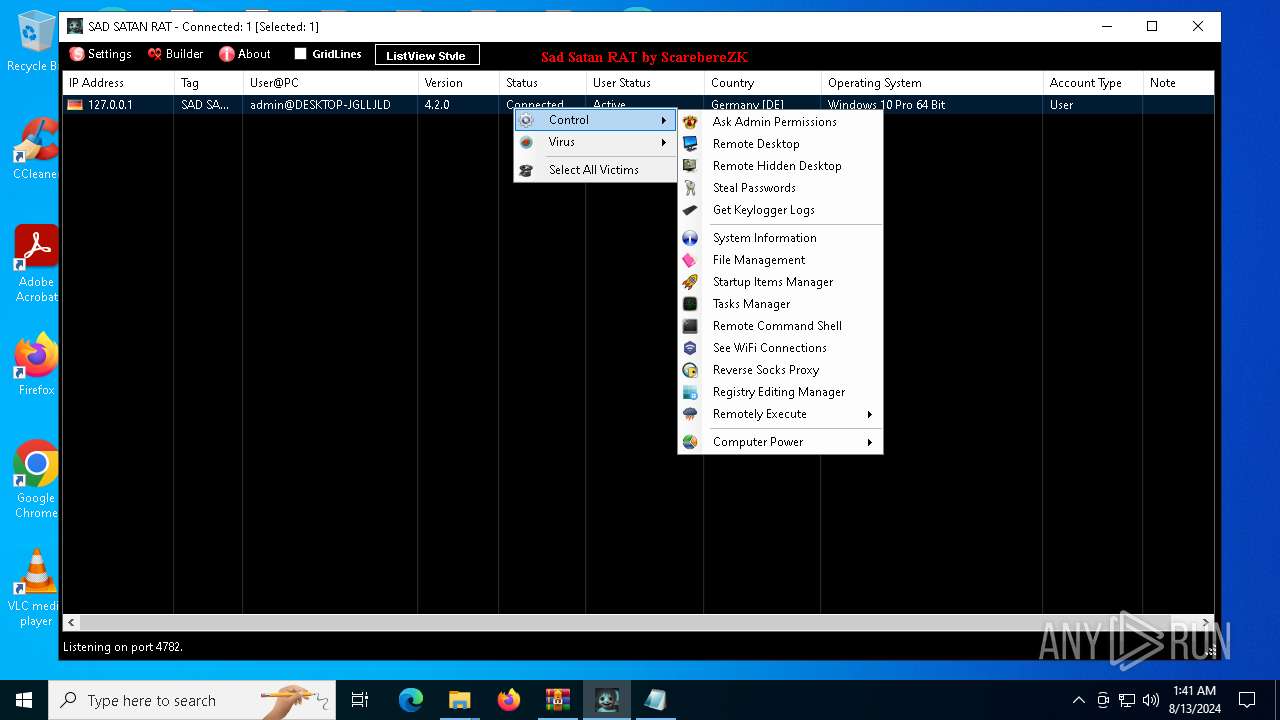
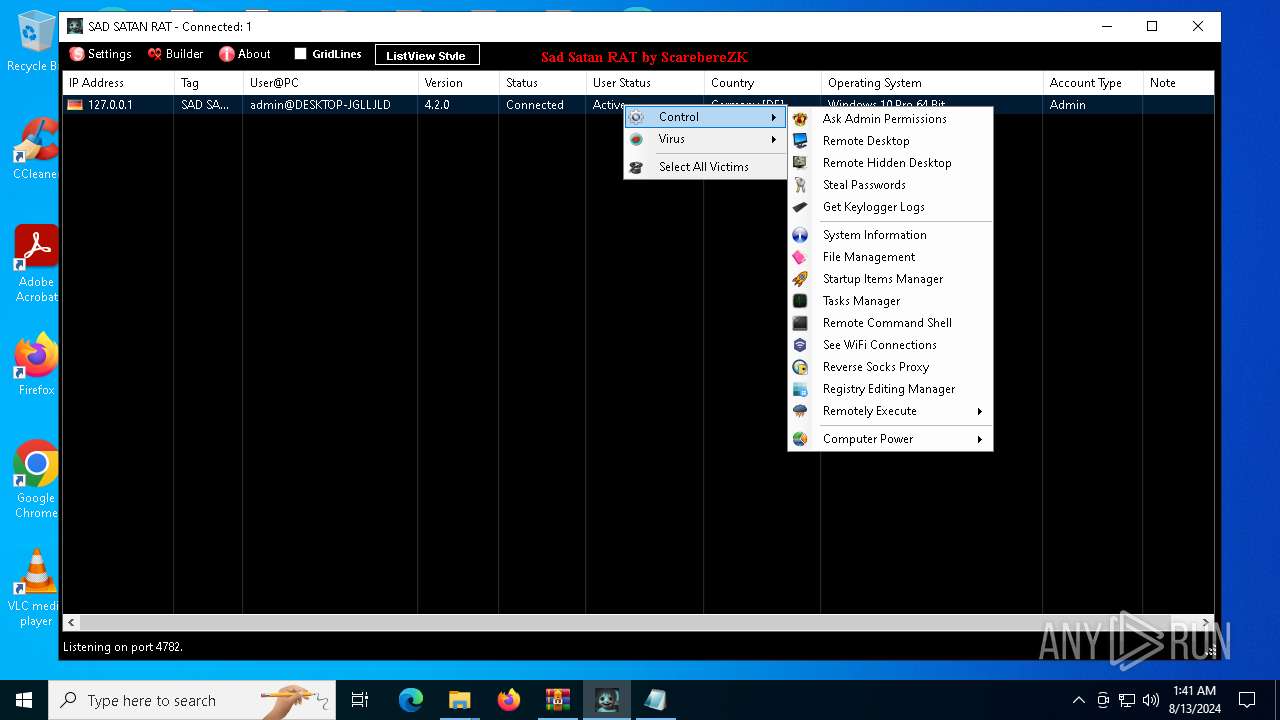
Actions looks like stealing of personal data
- SAD-SATAN-CLIENT.exe (PID: 6580)
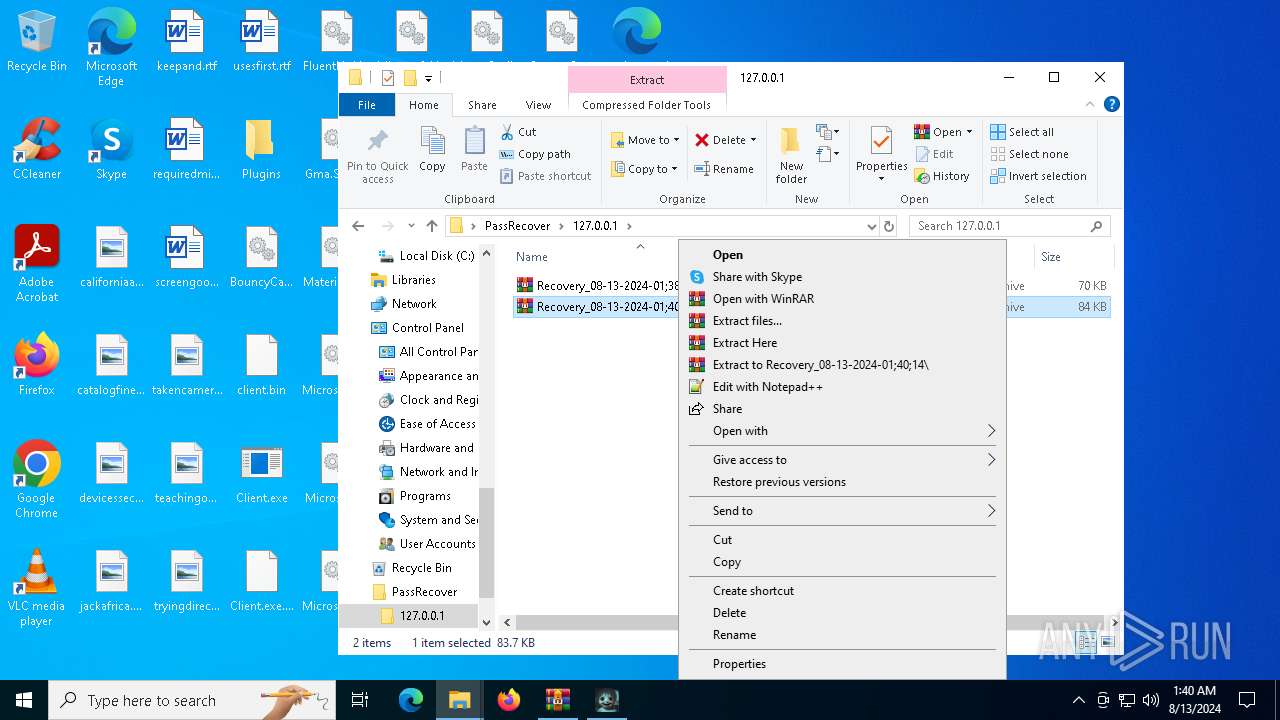
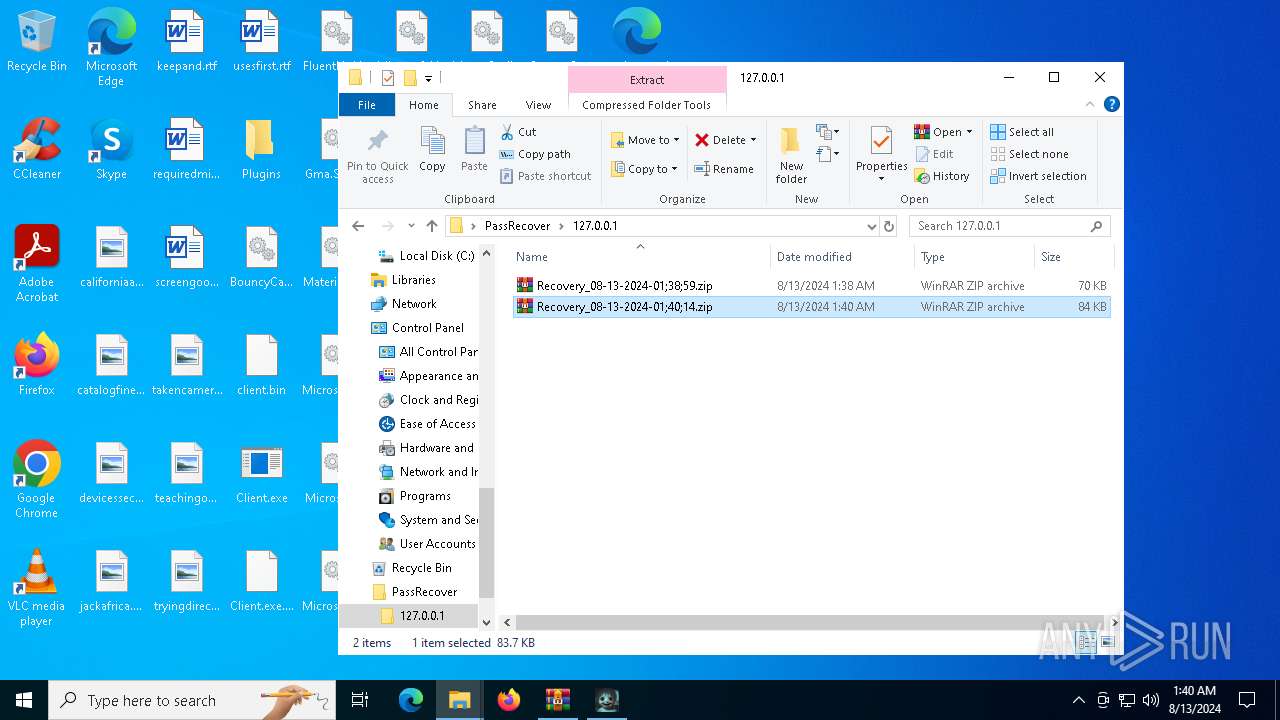
- WinRAR.exe (PID: 7364)
- SAD-SATAN-CLIENT.exe (PID: 3324)
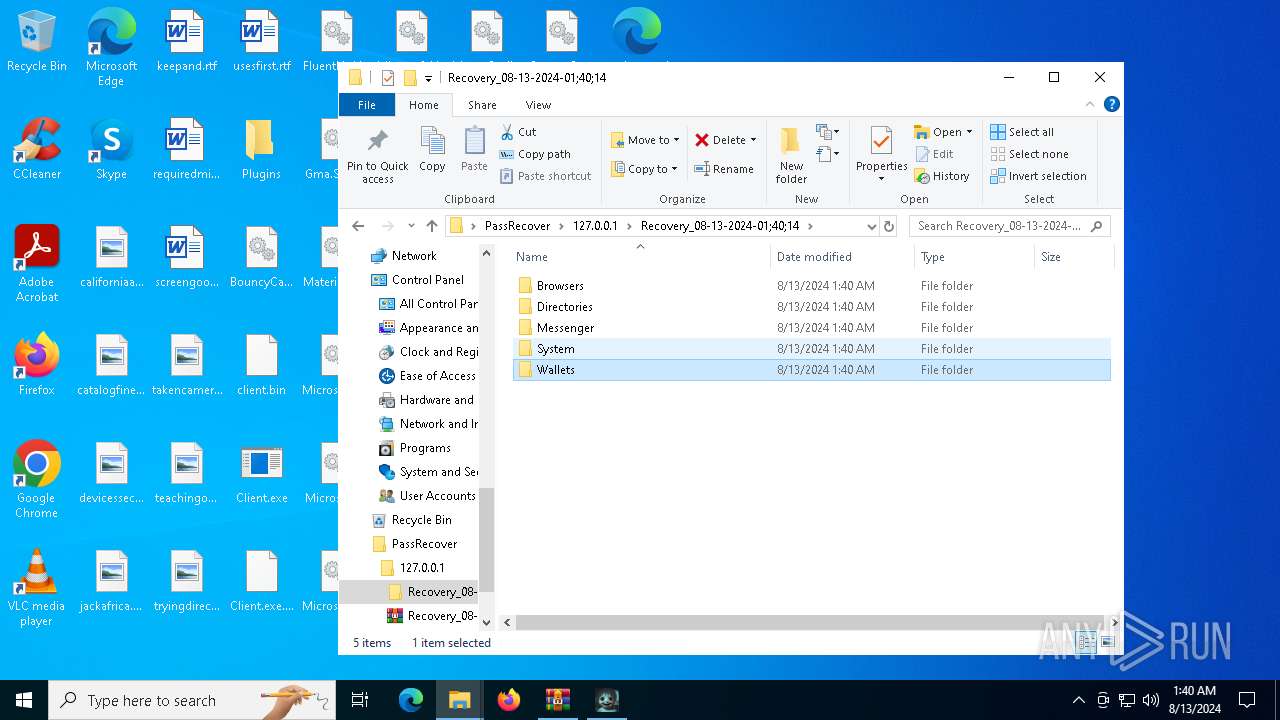
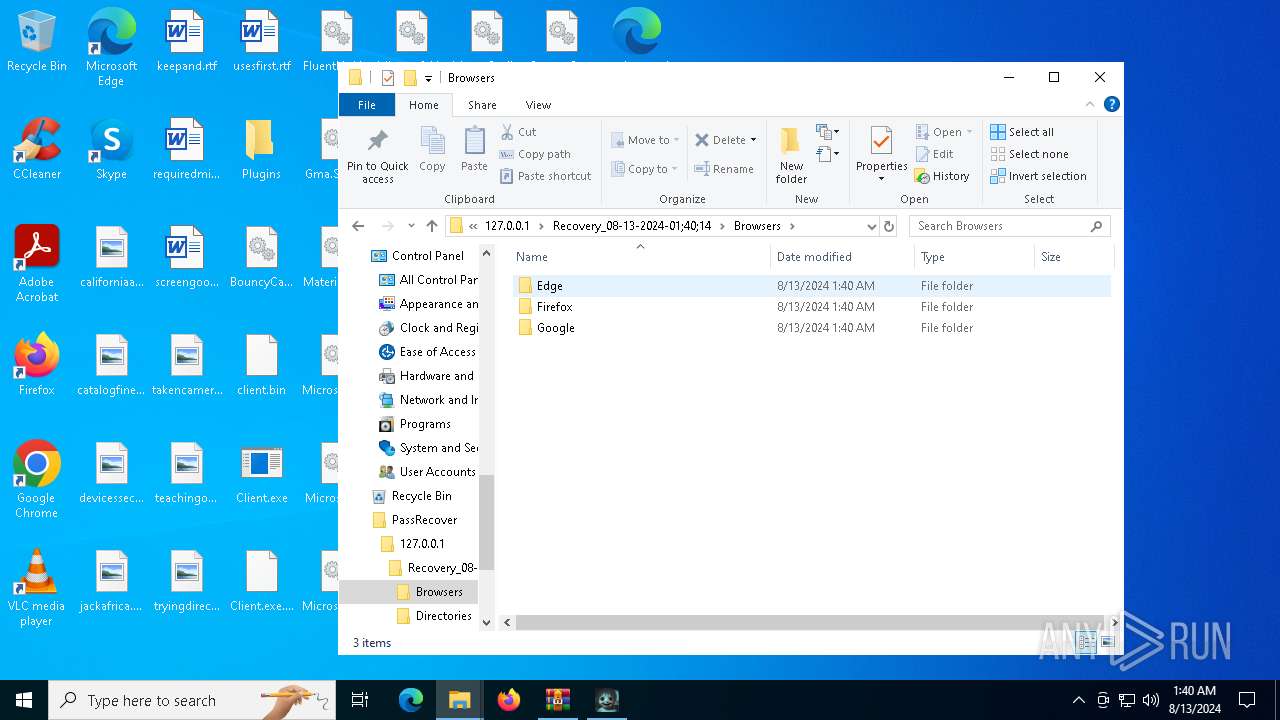
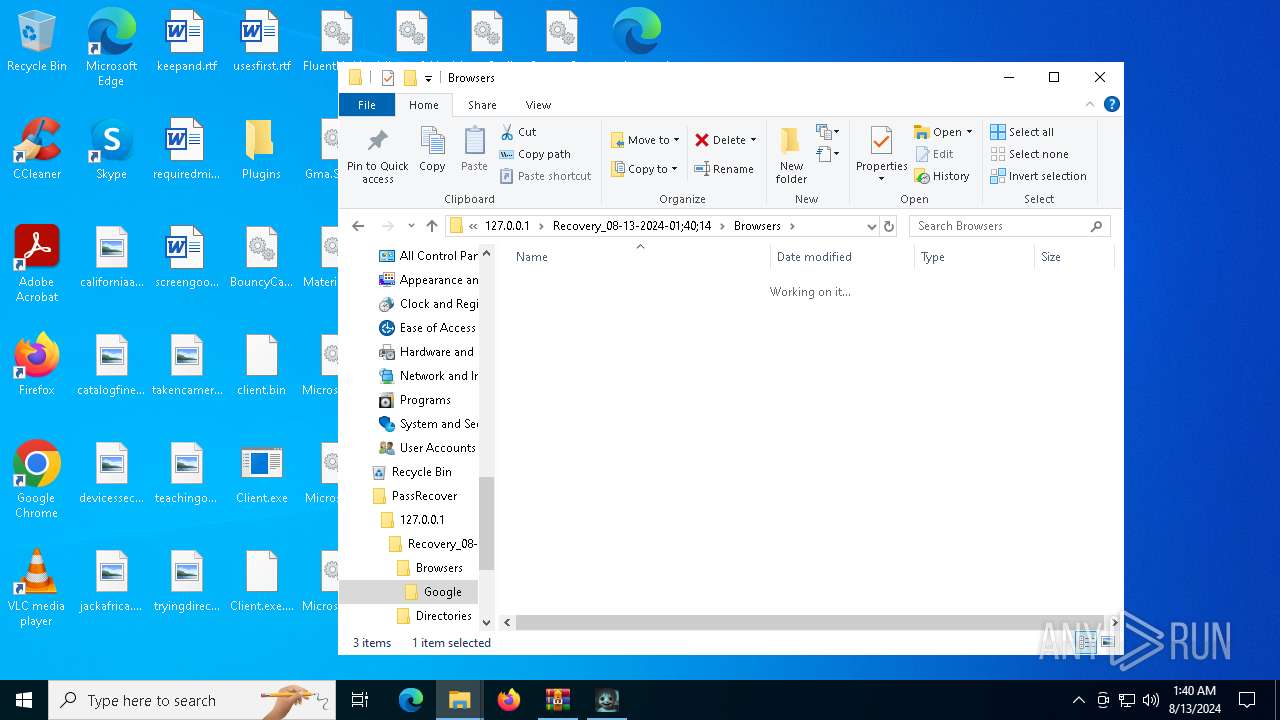
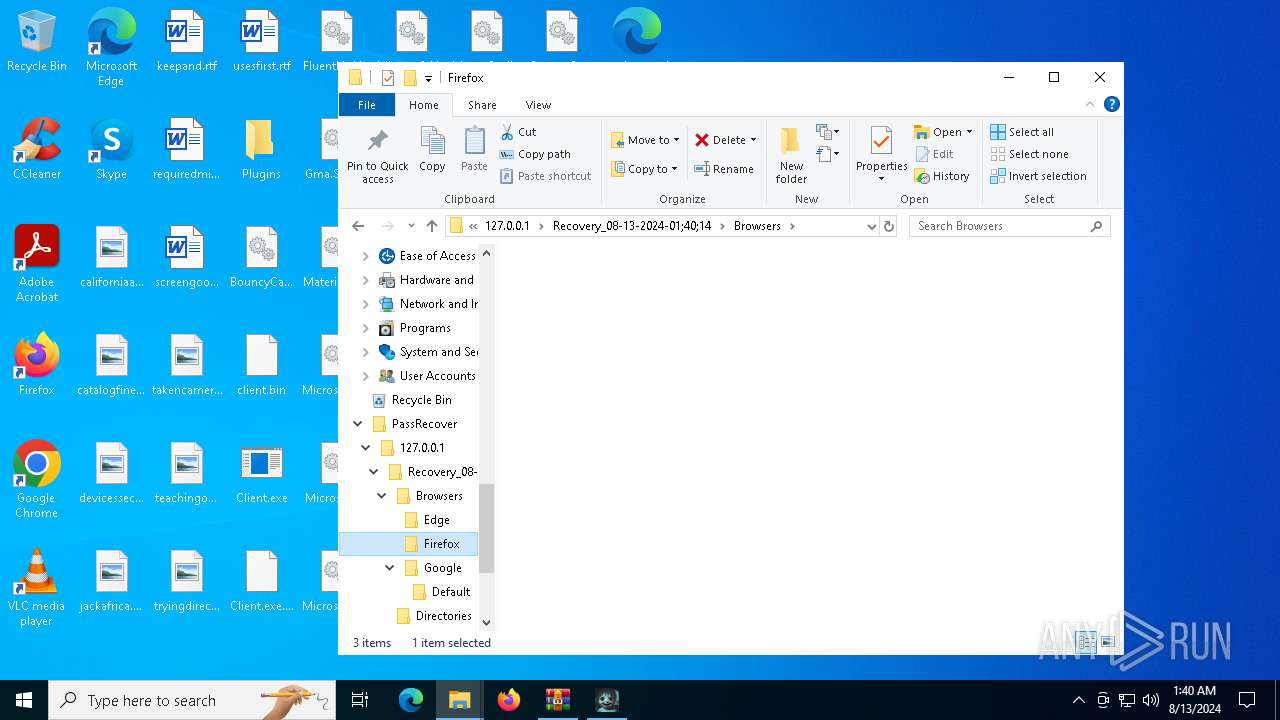
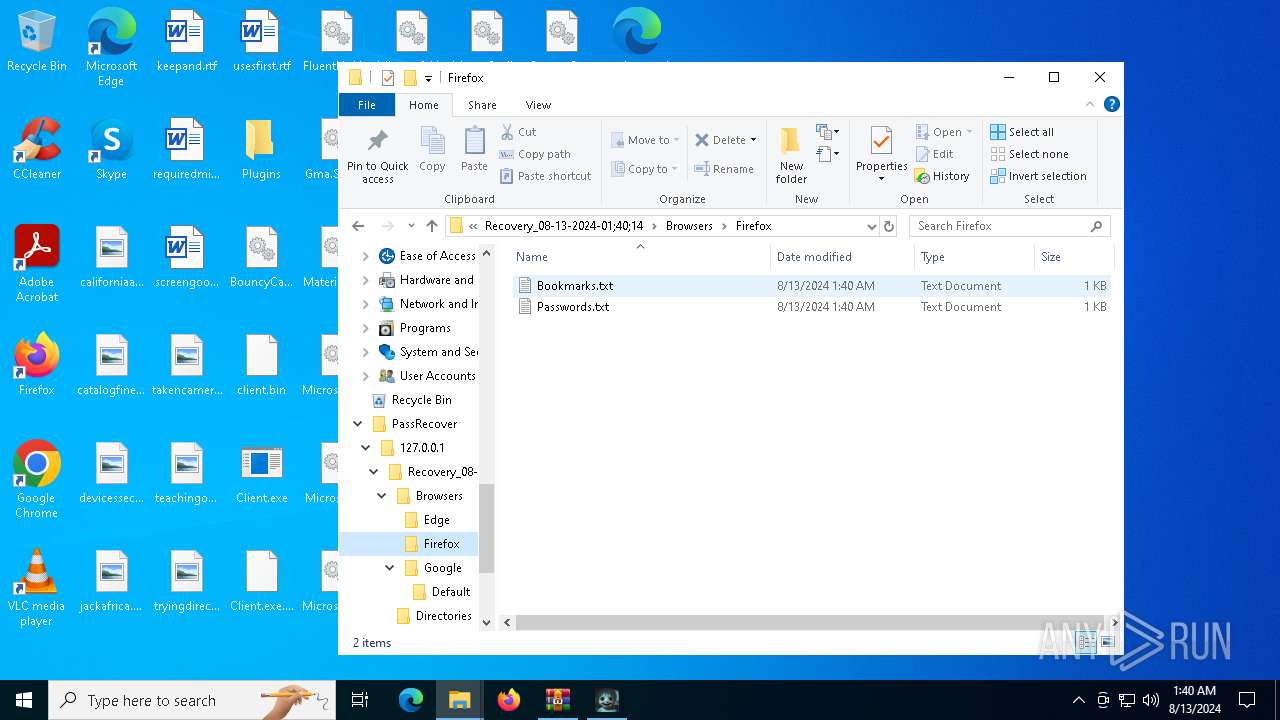
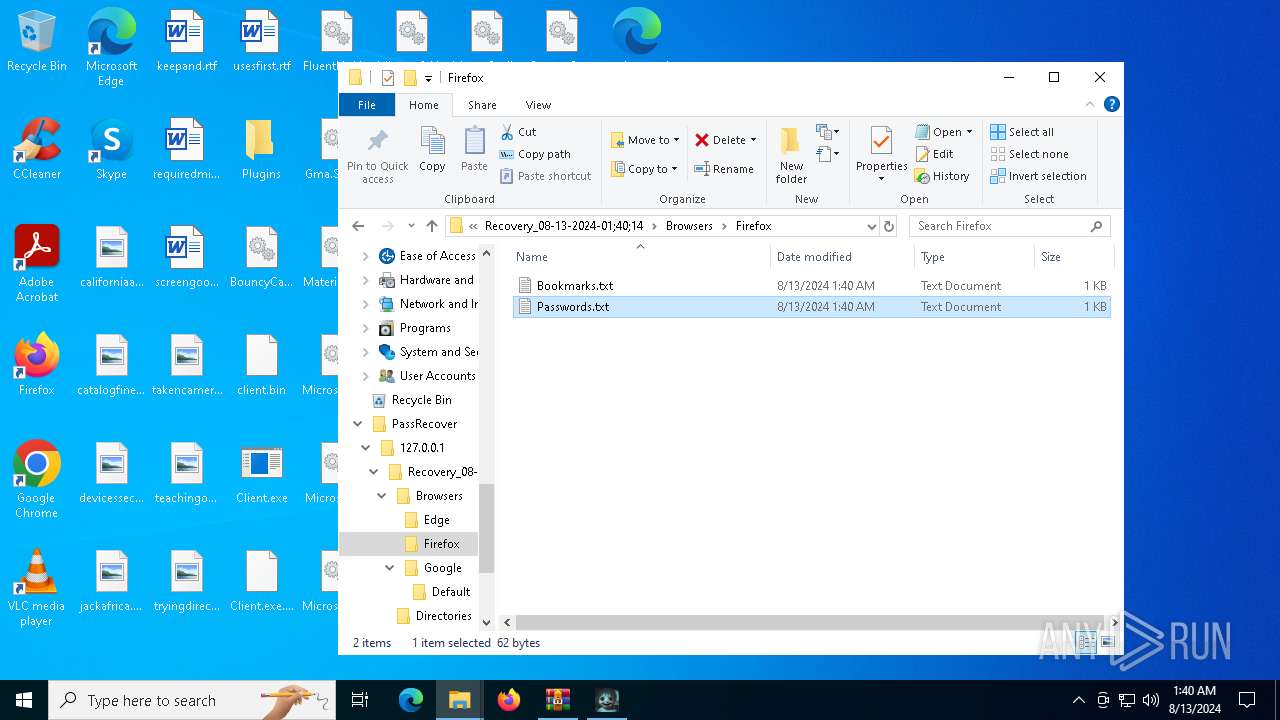
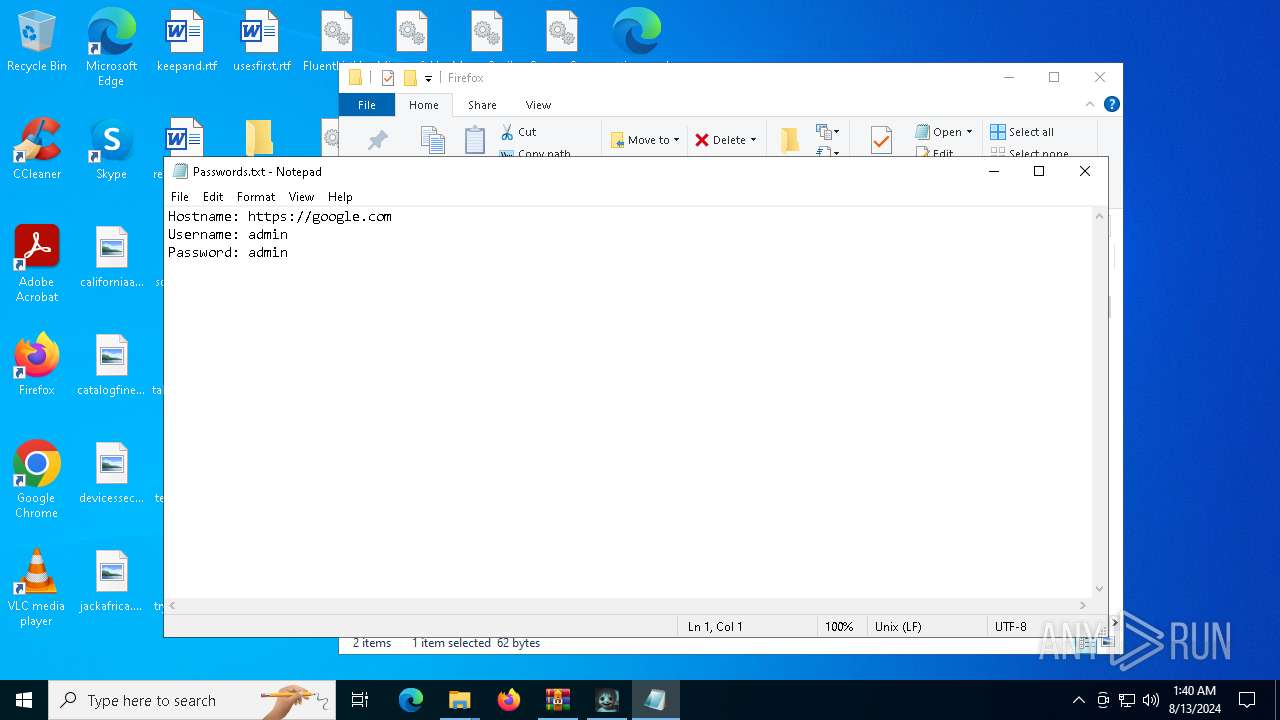
Steals credentials from Web Browsers
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SAD-SATAN-CLIENT.exe (PID: 3324)
STEALERIUM has been detected (YARA)
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SAD-SATAN-CLIENT.exe (PID: 3324)
QUASAR has been detected (YARA)
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SAD-SATAN-CLIENT.exe (PID: 3324)
Scans artifacts that could help determine the target
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SAD-SATAN-CLIENT.exe (PID: 3324)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 7084)
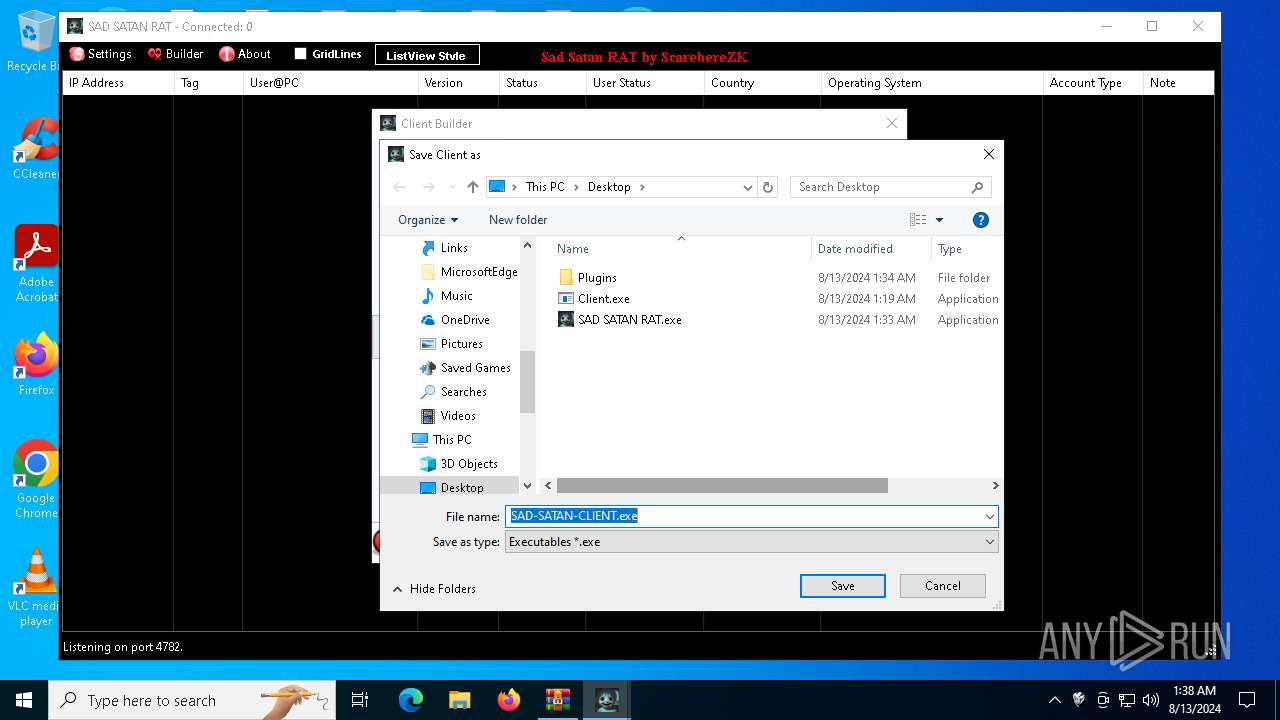
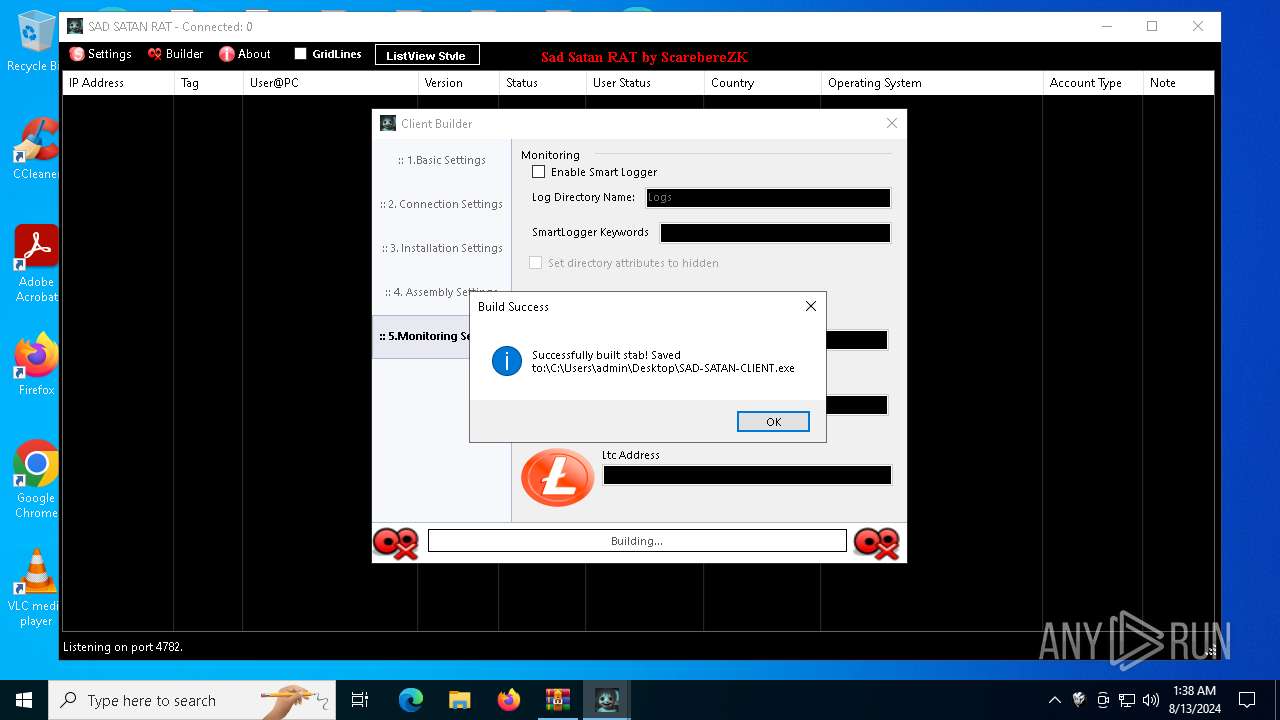
Drops the executable file immediately after the start
- WinRAR.exe (PID: 7084)
- SAD SATAN RAT.exe (PID: 5400)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 7084)
Reads security settings of Internet Explorer
- SAD SATAN RAT.exe (PID: 5400)
- StartMenuExperienceHost.exe (PID: 5760)
- SAD-SATAN-CLIENT.exe (PID: 6580)
Executable content was dropped or overwritten
- SAD SATAN RAT.exe (PID: 5400)
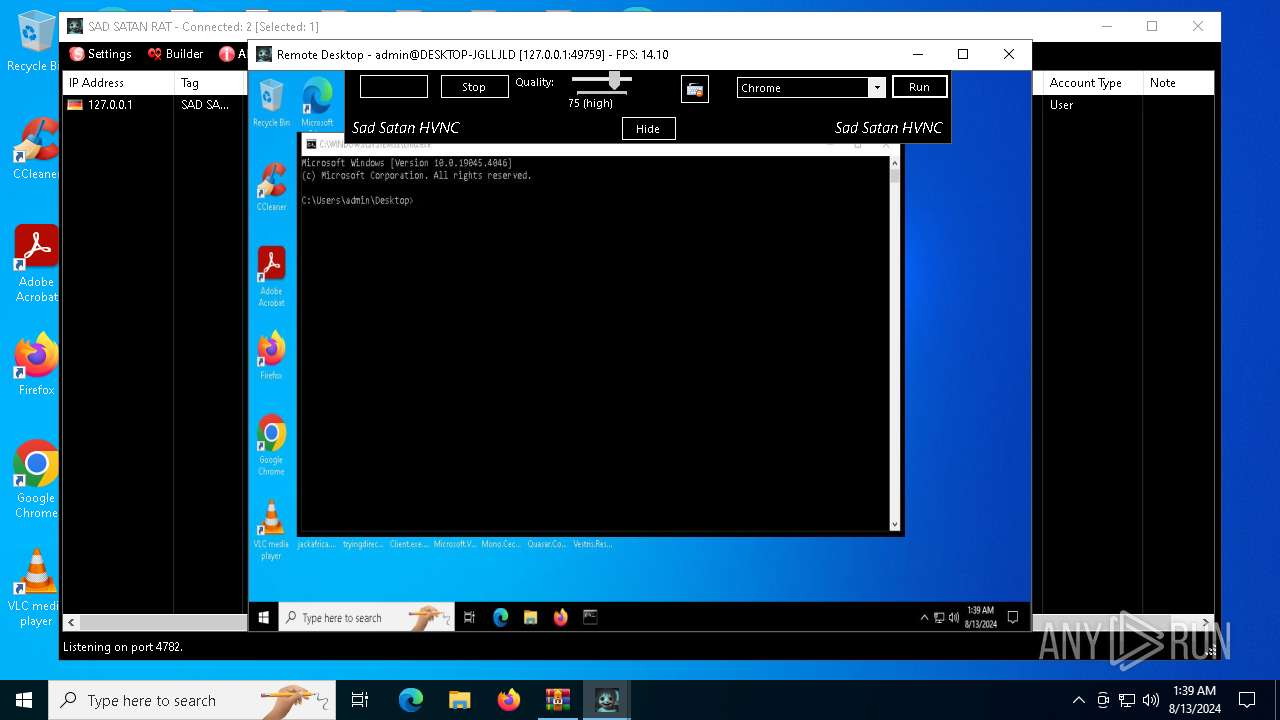
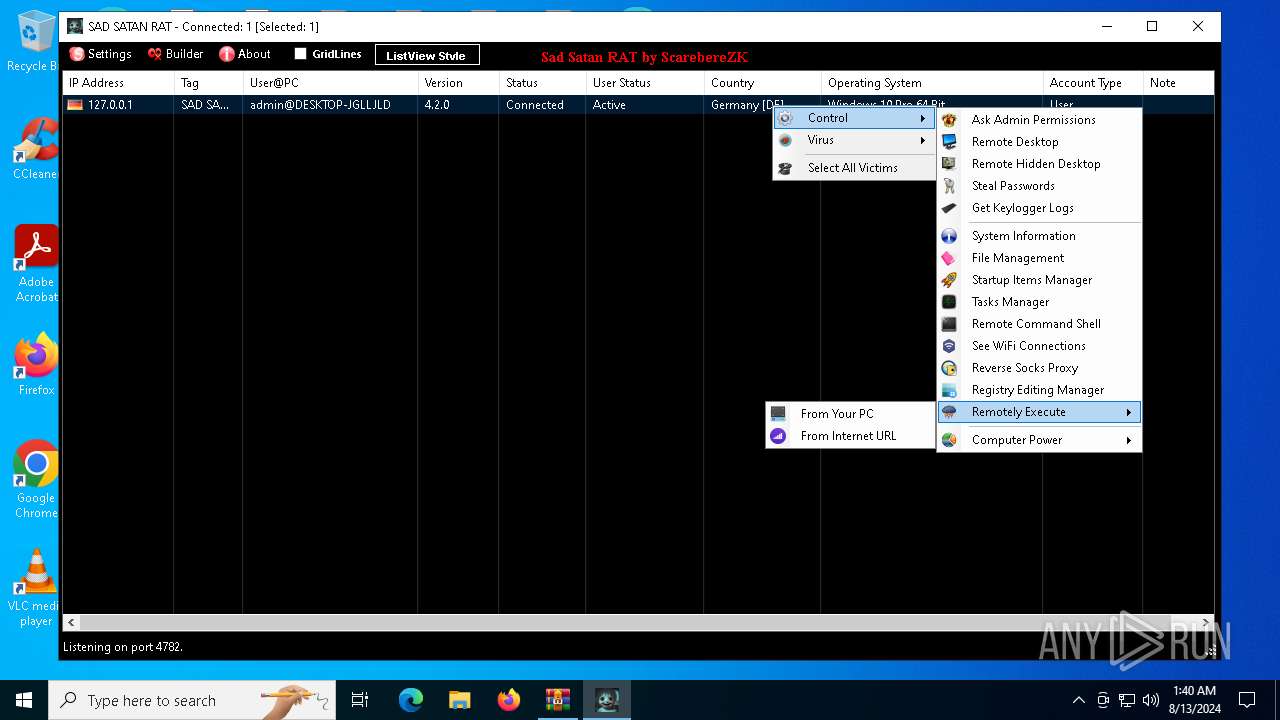
Starts application with an unusual extension
- cmd.exe (PID: 3140)
- cmd.exe (PID: 6696)
- cmd.exe (PID: 2900)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 6740)
Loads DLL from Mozilla Firefox
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SAD-SATAN-CLIENT.exe (PID: 3324)
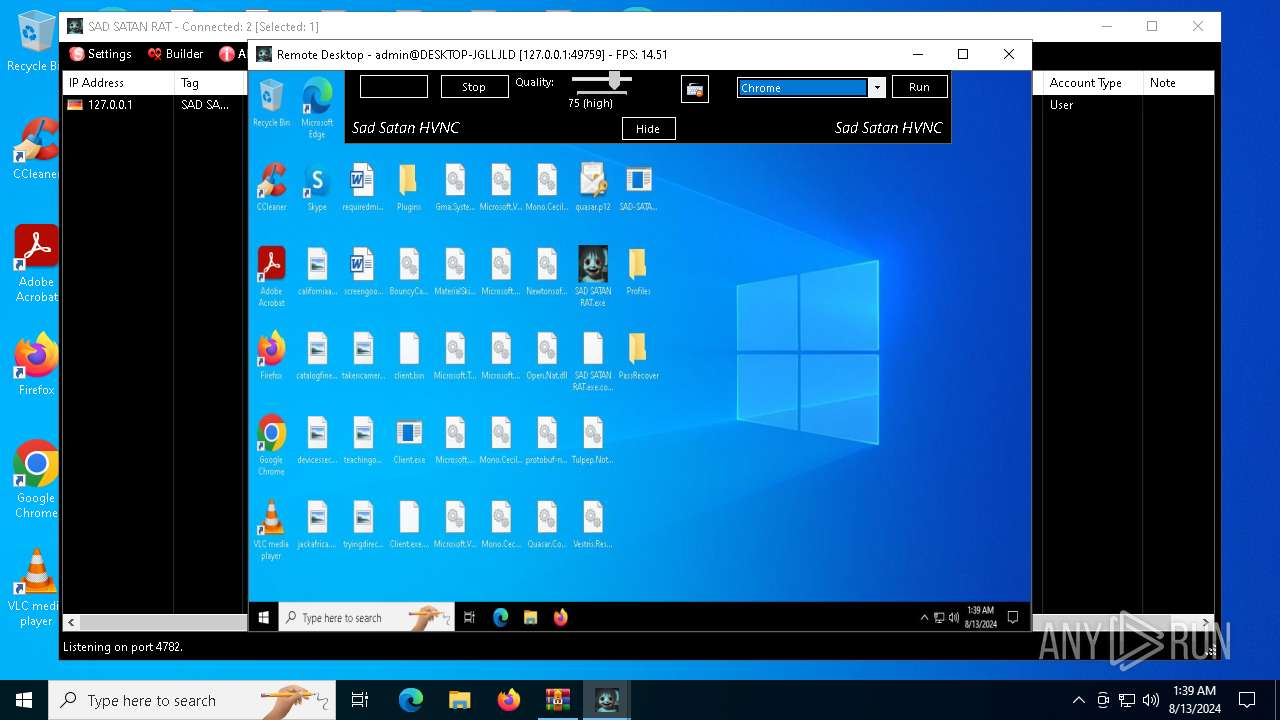
Starts CMD.EXE for commands execution
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SAD-SATAN-CLIENT.exe (PID: 3324)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 6696)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 2900)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 6740)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6696)
- cmd.exe (PID: 2900)
- cmd.exe (PID: 5292)
Checks for external IP
- svchost.exe (PID: 2256)
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SAD-SATAN-CLIENT.exe (PID: 3324)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 5760)
- SearchApp.exe (PID: 6028)
- SAD-SATAN-CLIENT.exe (PID: 6580)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7084)
Reads the computer name
- SAD SATAN RAT.exe (PID: 5400)
- SAD-SATAN-CLIENT.exe (PID: 6580)
- StartMenuExperienceHost.exe (PID: 5760)
- msiexec.exe (PID: 4560)
- SearchApp.exe (PID: 6028)
- SAD-SATAN-CLIENT.exe (PID: 3324)
Reads Environment values
- SAD SATAN RAT.exe (PID: 5400)
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SearchApp.exe (PID: 6028)
- SAD-SATAN-CLIENT.exe (PID: 3324)
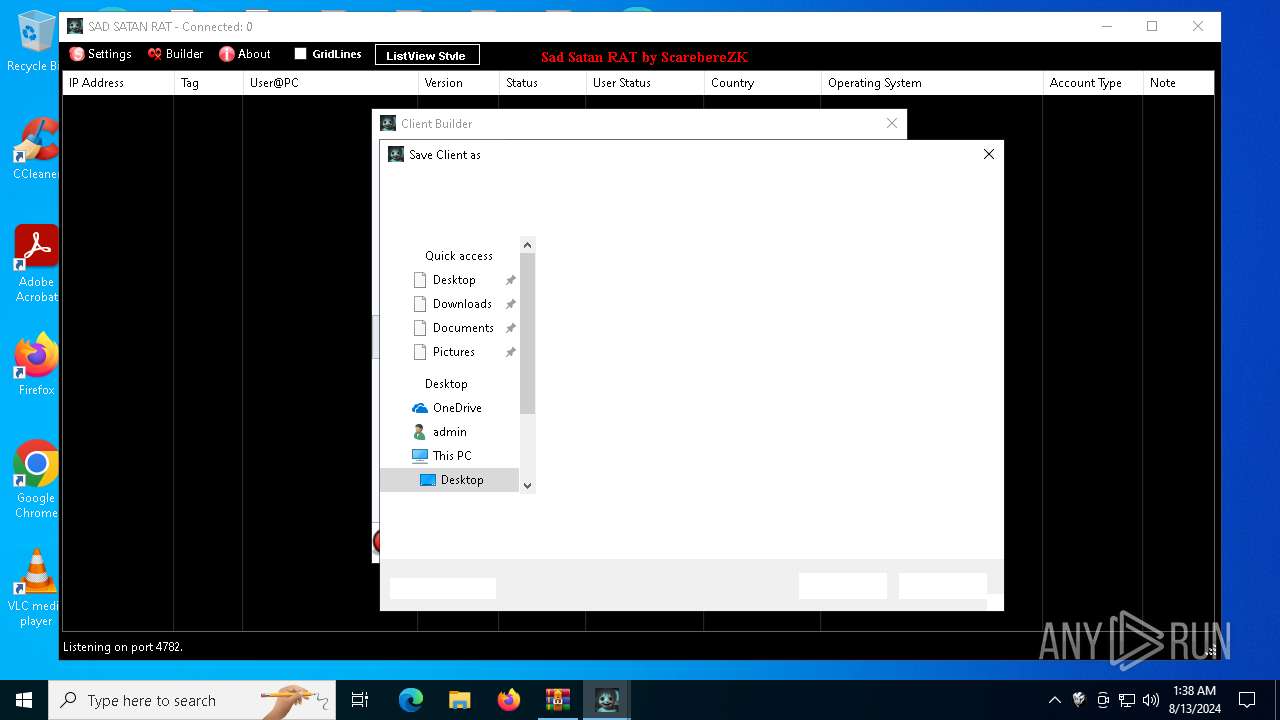
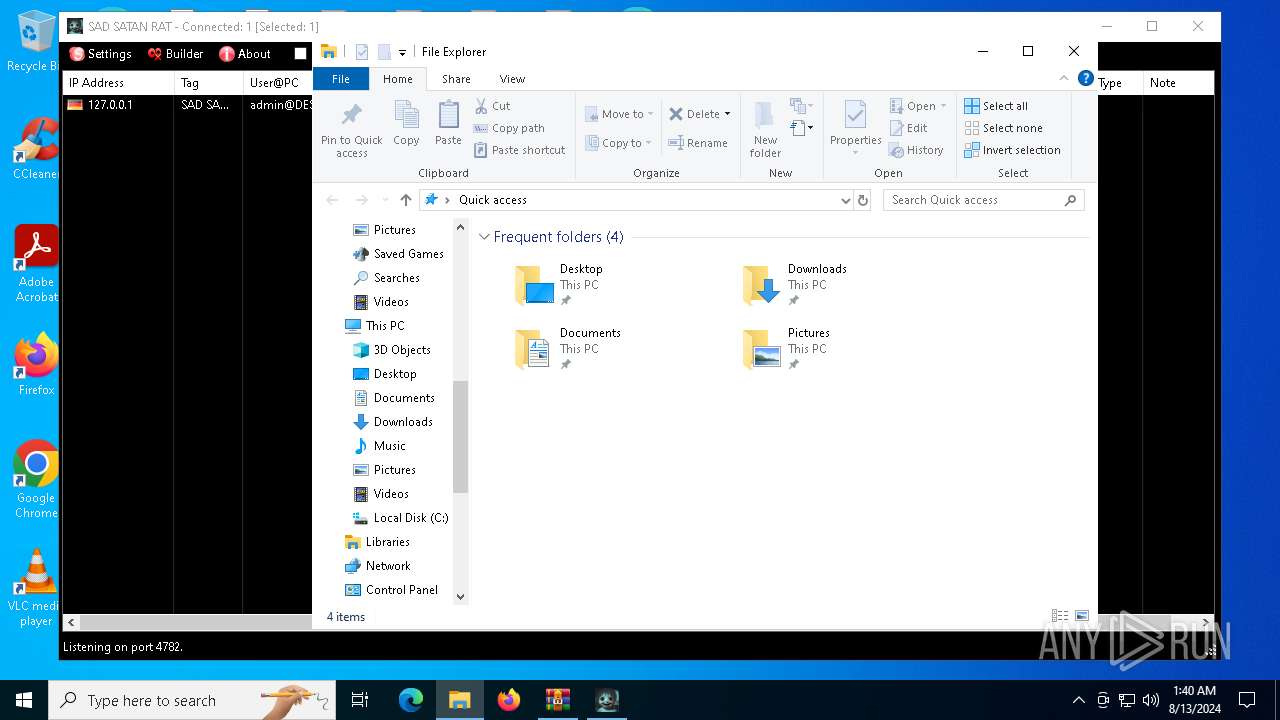
Creates files or folders in the user directory
- SAD SATAN RAT.exe (PID: 5400)
- SAD-SATAN-CLIENT.exe (PID: 6580)
- explorer.exe (PID: 3660)
- SAD-SATAN-CLIENT.exe (PID: 3324)
Checks supported languages
- SAD SATAN RAT.exe (PID: 5400)
- SAD-SATAN-CLIENT.exe (PID: 6580)
- chcp.com (PID: 4160)
- chcp.com (PID: 6256)
- msiexec.exe (PID: 4560)
- StartMenuExperienceHost.exe (PID: 5760)
- SearchApp.exe (PID: 6028)
- chcp.com (PID: 7756)
- chcp.com (PID: 7936)
- SAD-SATAN-CLIENT.exe (PID: 3324)
- chcp.com (PID: 1568)
- chcp.com (PID: 7892)
Reads the machine GUID from the registry
- SAD SATAN RAT.exe (PID: 5400)
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SearchApp.exe (PID: 6028)
- SAD-SATAN-CLIENT.exe (PID: 3324)
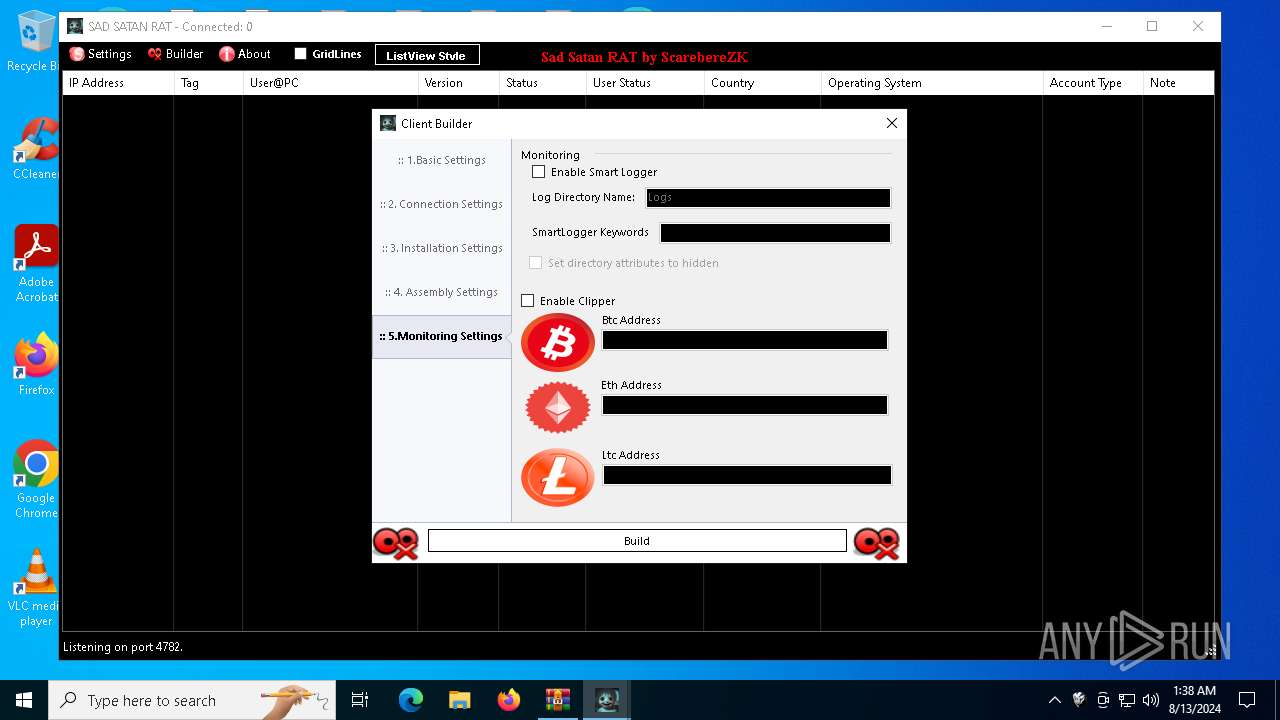
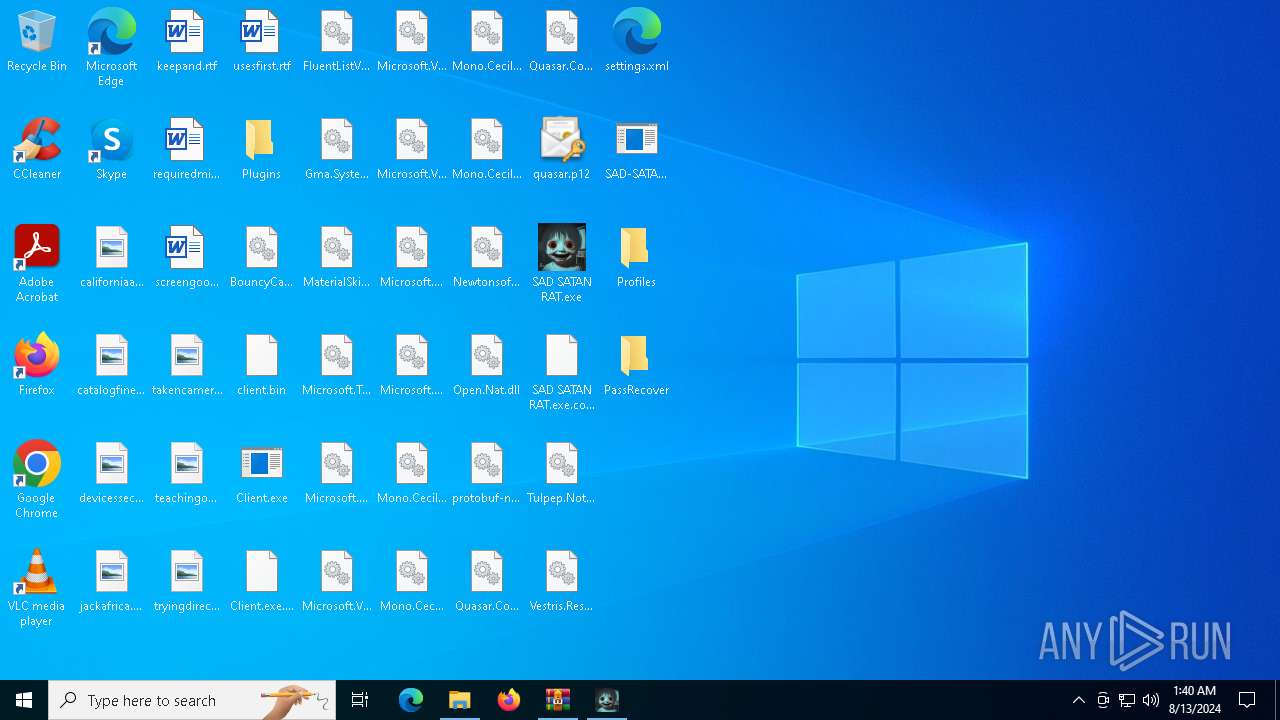
Manual execution by a user
- SAD SATAN RAT.exe (PID: 5400)
- SAD-SATAN-CLIENT.exe (PID: 6580)
- WinRAR.exe (PID: 7364)
- notepad.exe (PID: 8076)
Disables trace logs
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SAD-SATAN-CLIENT.exe (PID: 3324)
Reads the software policy settings
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SearchApp.exe (PID: 6028)
- SAD-SATAN-CLIENT.exe (PID: 3324)
Checks proxy server information
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SearchApp.exe (PID: 6028)
- explorer.exe (PID: 3660)
- SAD-SATAN-CLIENT.exe (PID: 3324)
Create files in a temporary directory
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SAD-SATAN-CLIENT.exe (PID: 3324)
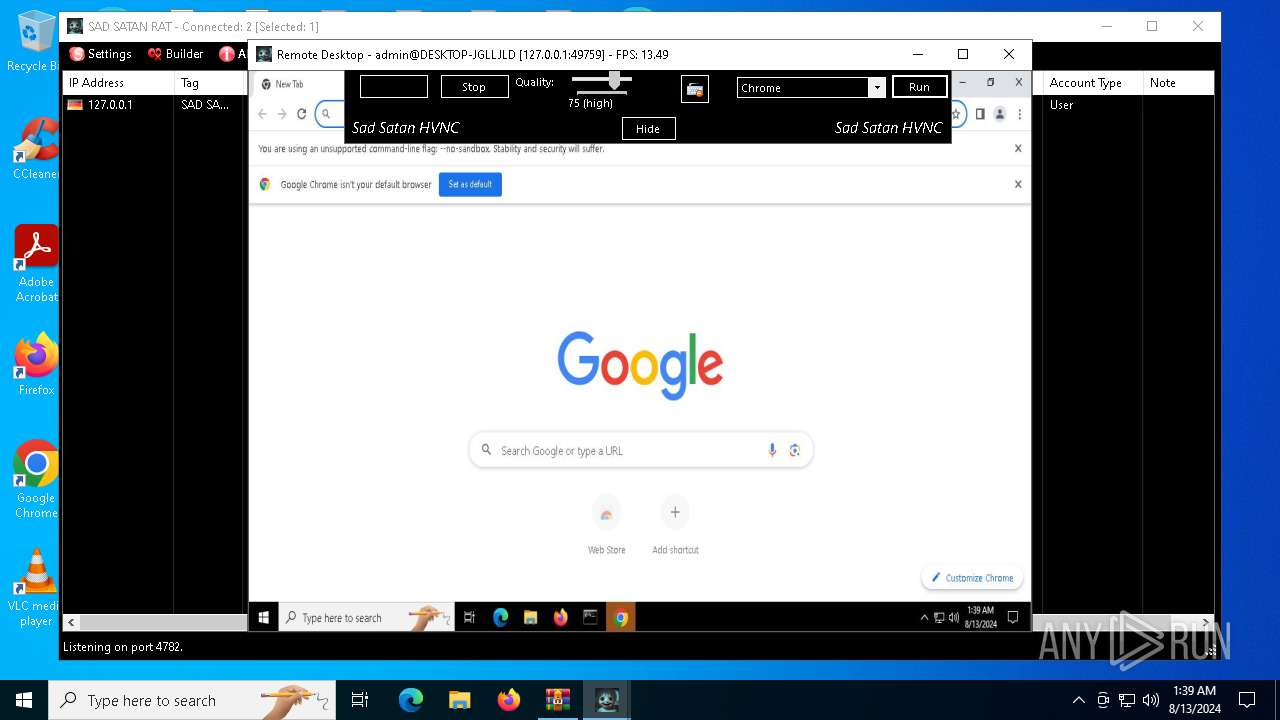
Reads Microsoft Office registry keys
- SAD-SATAN-CLIENT.exe (PID: 6580)
- explorer.exe (PID: 3660)
- chrome.exe (PID: 5004)
- SAD-SATAN-CLIENT.exe (PID: 3324)
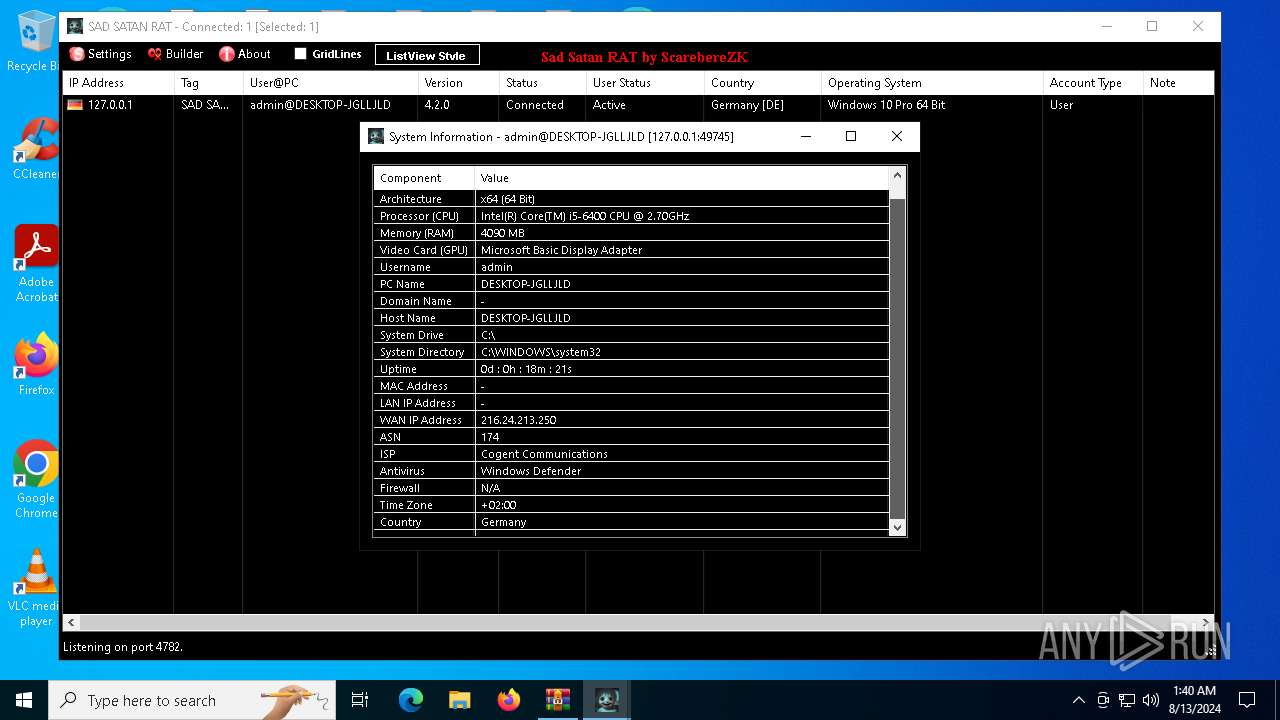
Reads CPU info
- SAD-SATAN-CLIENT.exe (PID: 6580)
- SAD-SATAN-CLIENT.exe (PID: 3324)
Changes the display of characters in the console
- chcp.com (PID: 6256)
- chcp.com (PID: 4160)
- chcp.com (PID: 7756)
- chcp.com (PID: 7936)
- chcp.com (PID: 1568)
- chcp.com (PID: 7892)
Reads security settings of Internet Explorer
- explorer.exe (PID: 3660)
- notepad.exe (PID: 8076)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 5760)
- SearchApp.exe (PID: 6028)
- SAD-SATAN-CLIENT.exe (PID: 6580)
Process checks Internet Explorer phishing filters
- SearchApp.exe (PID: 6028)
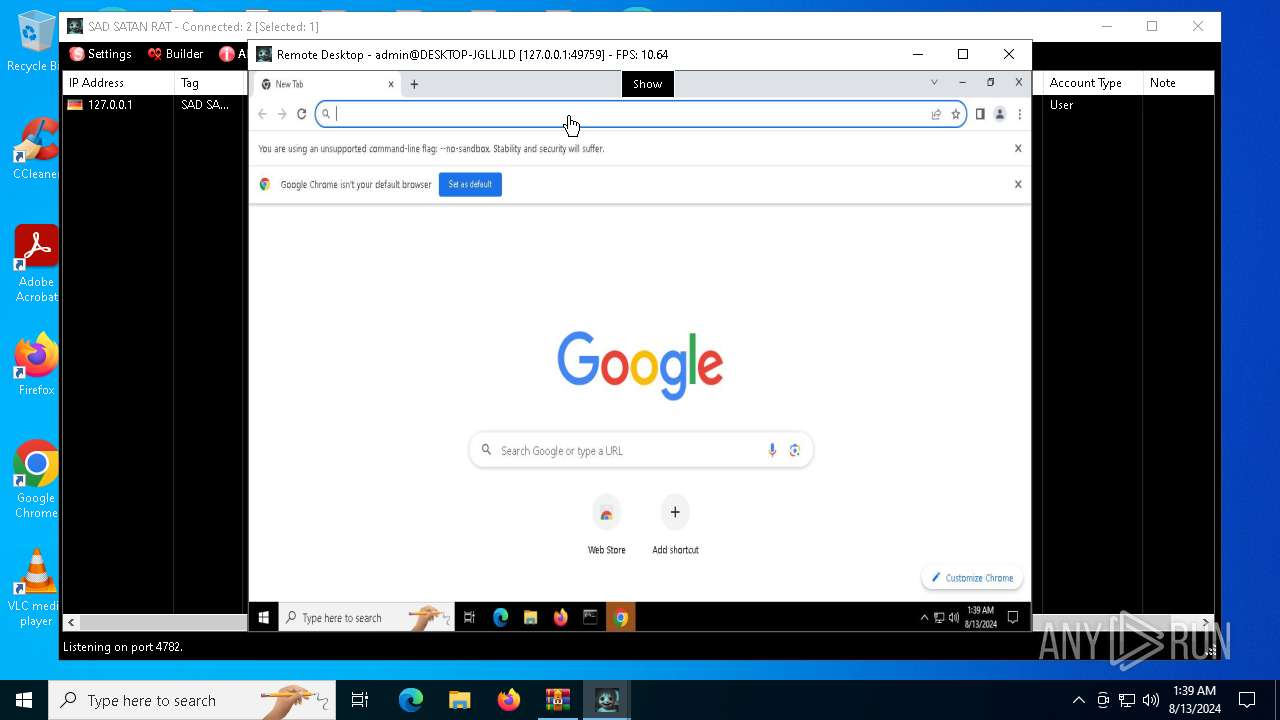
The process uses the downloaded file
- chrome.exe (PID: 7752)
- chrome.exe (PID: 7796)
- chrome.exe (PID: 7716)
- chrome.exe (PID: 692)
- chrome.exe (PID: 7932)
- chrome.exe (PID: 7984)
- chrome.exe (PID: 8104)
- chrome.exe (PID: 7848)
Application launched itself
- chrome.exe (PID: 5004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
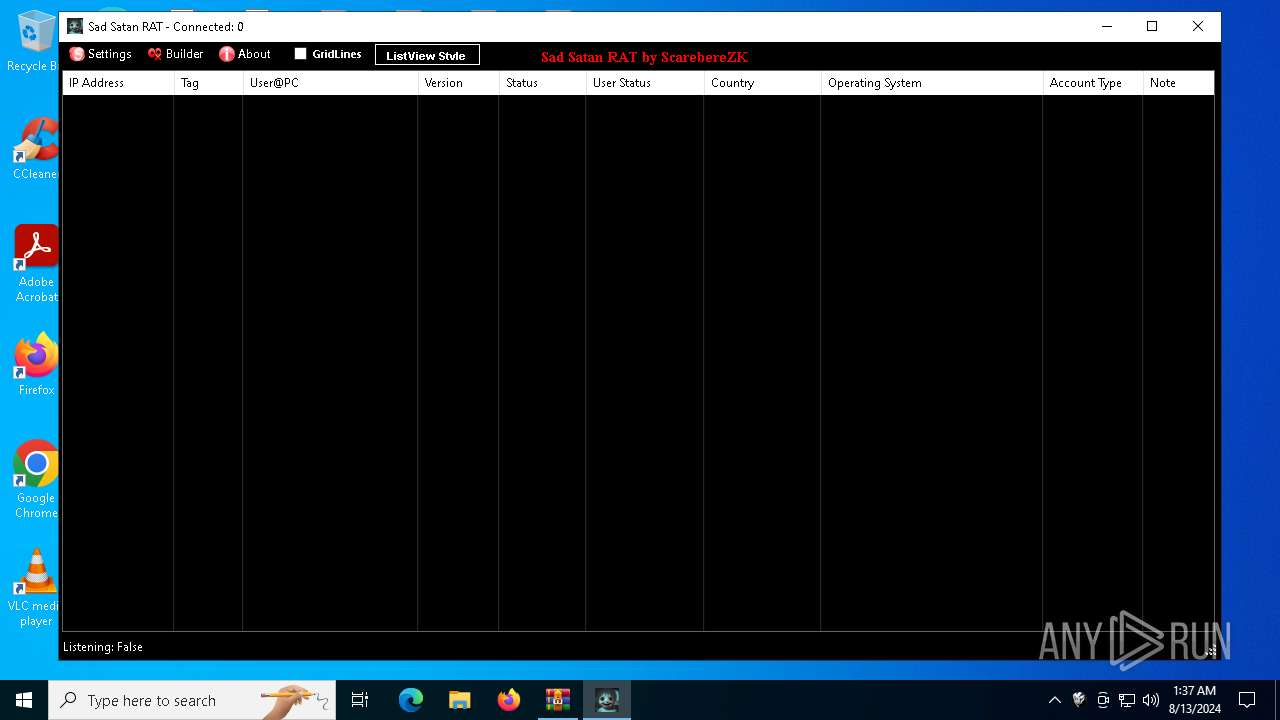
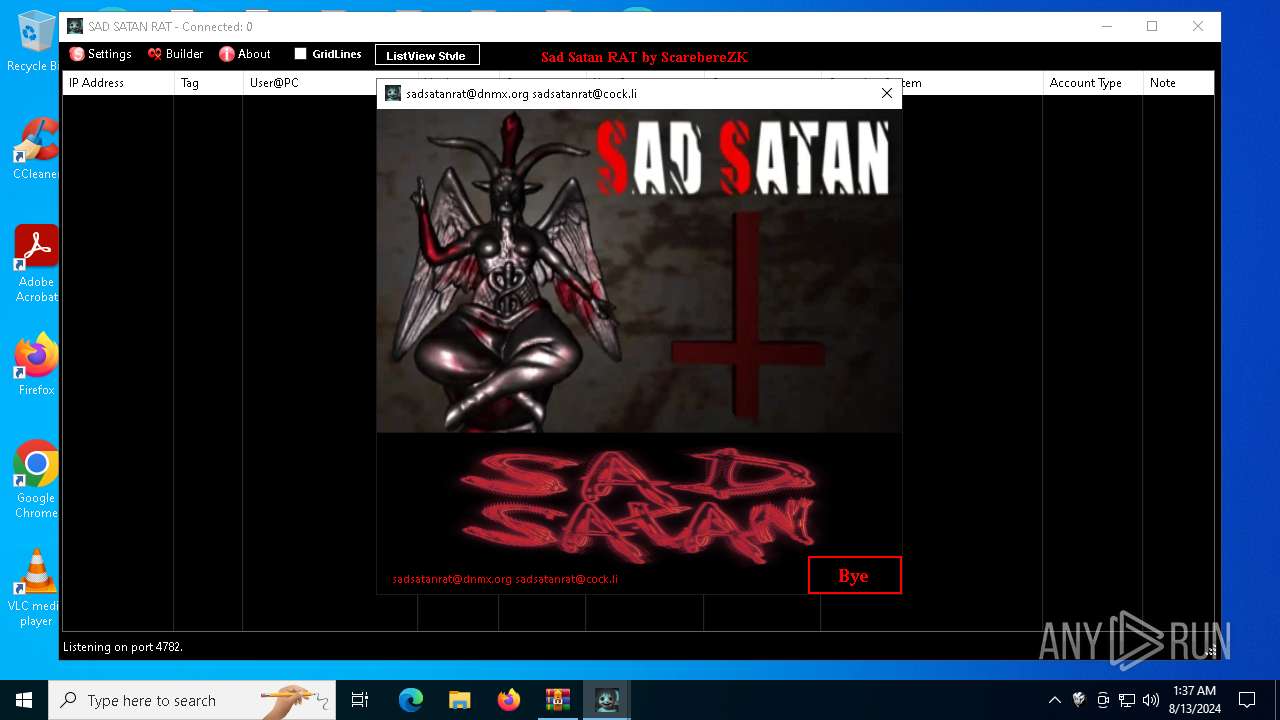
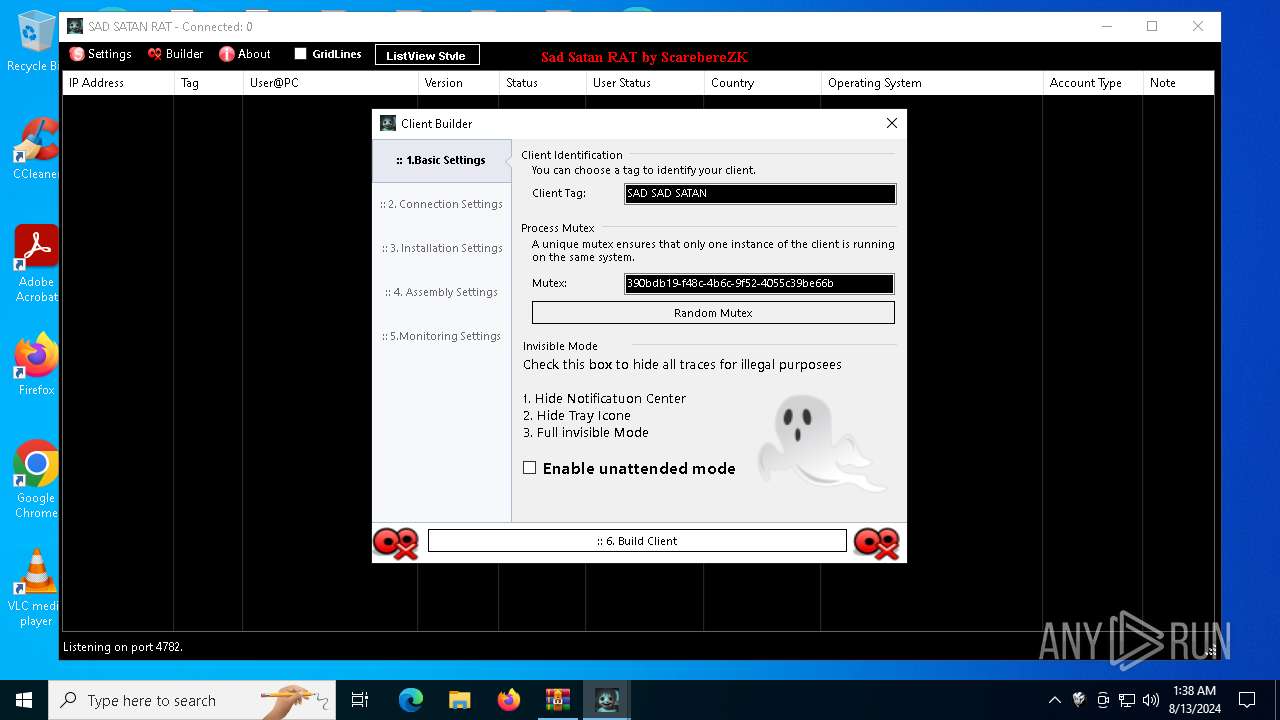
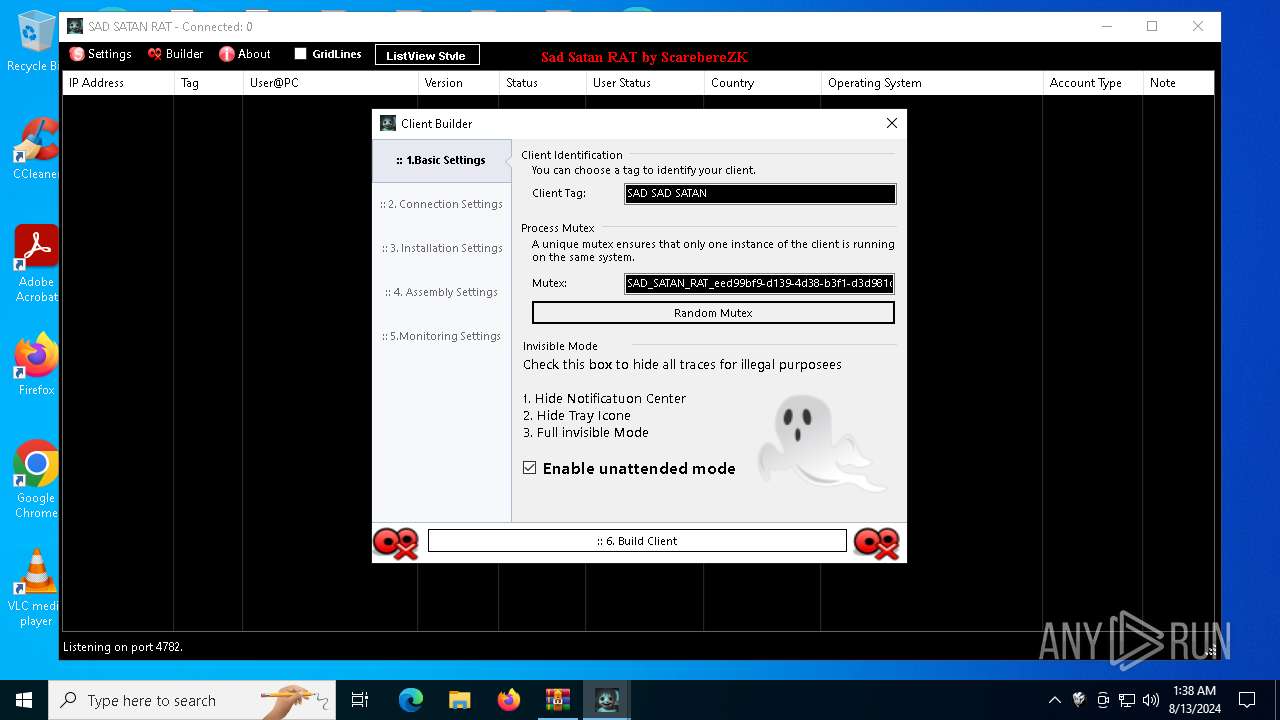
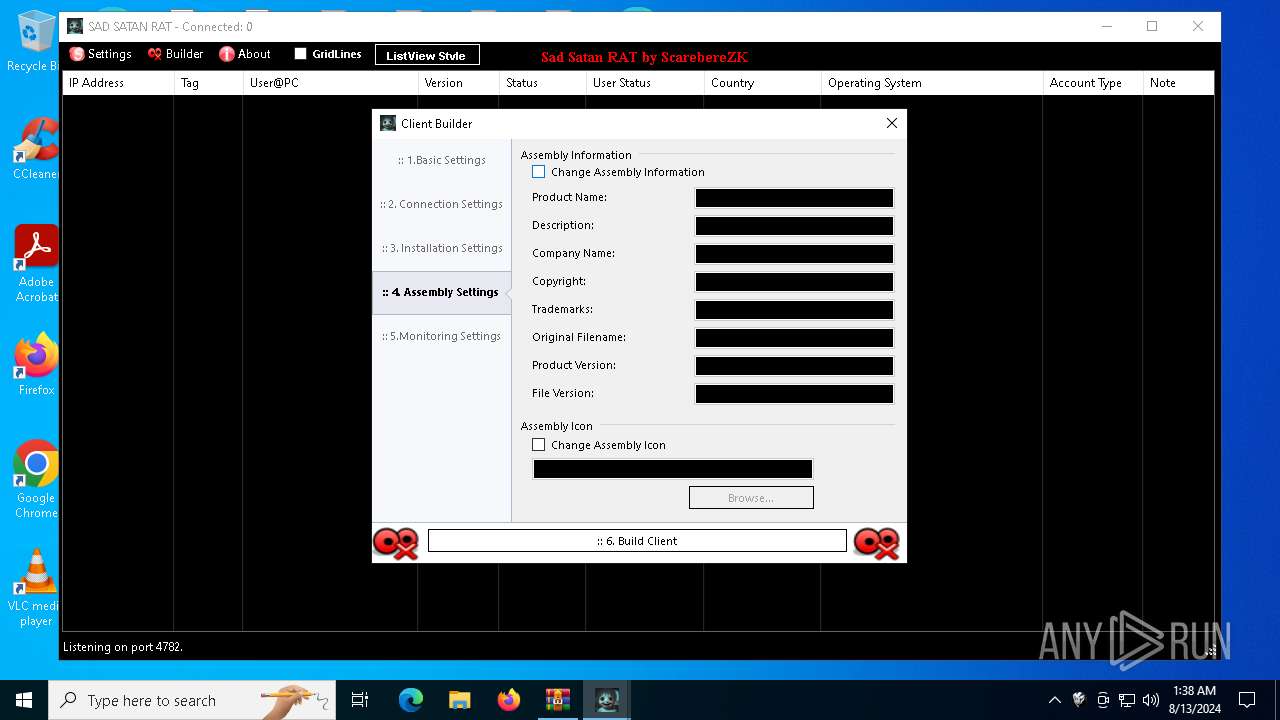
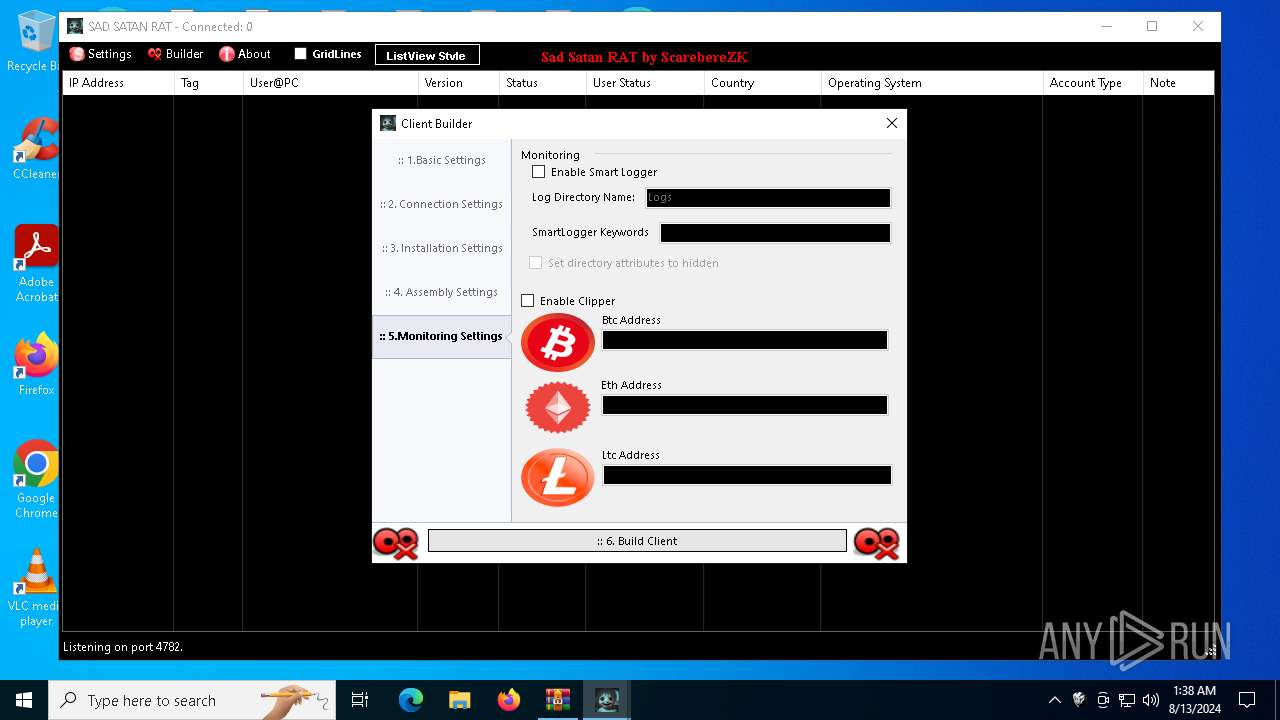
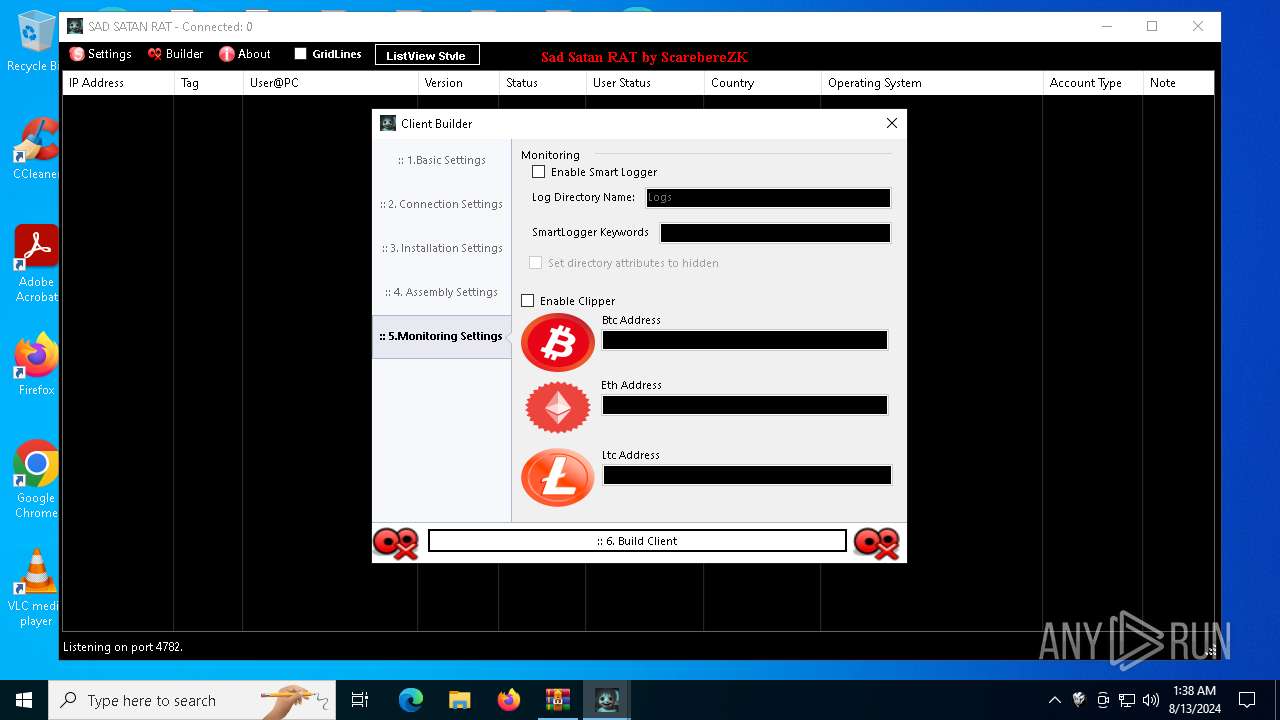
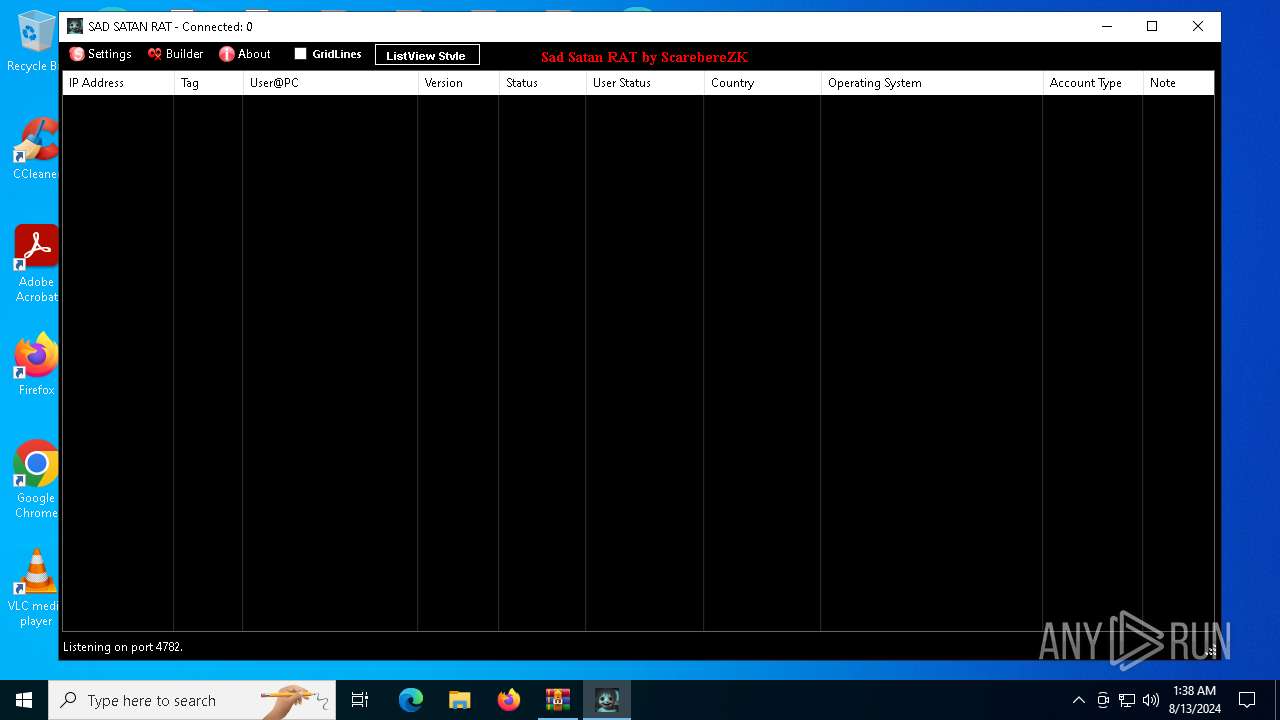
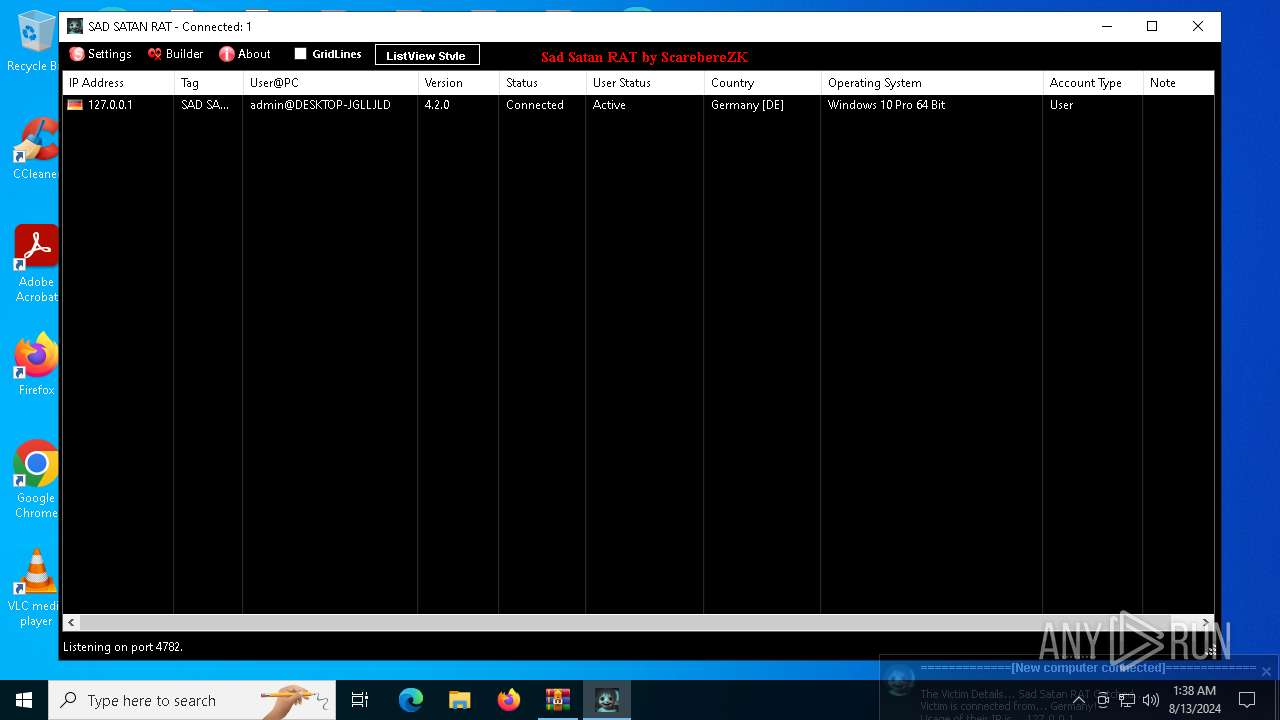
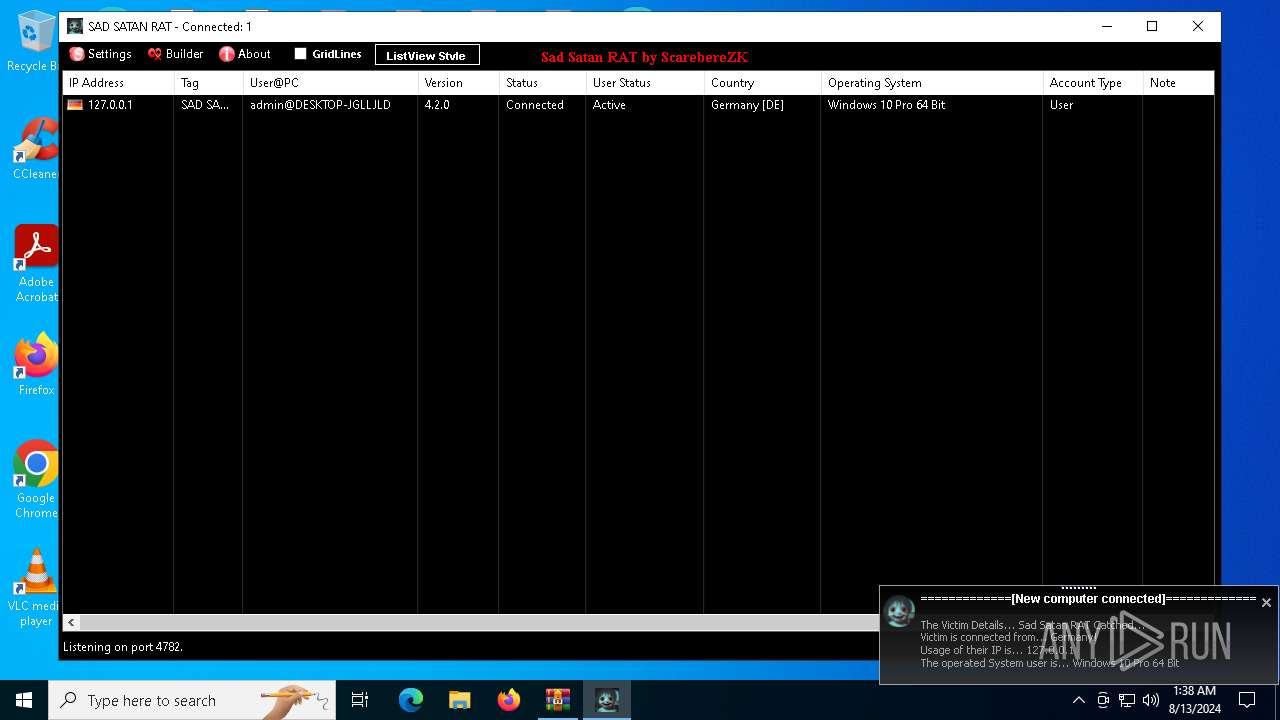
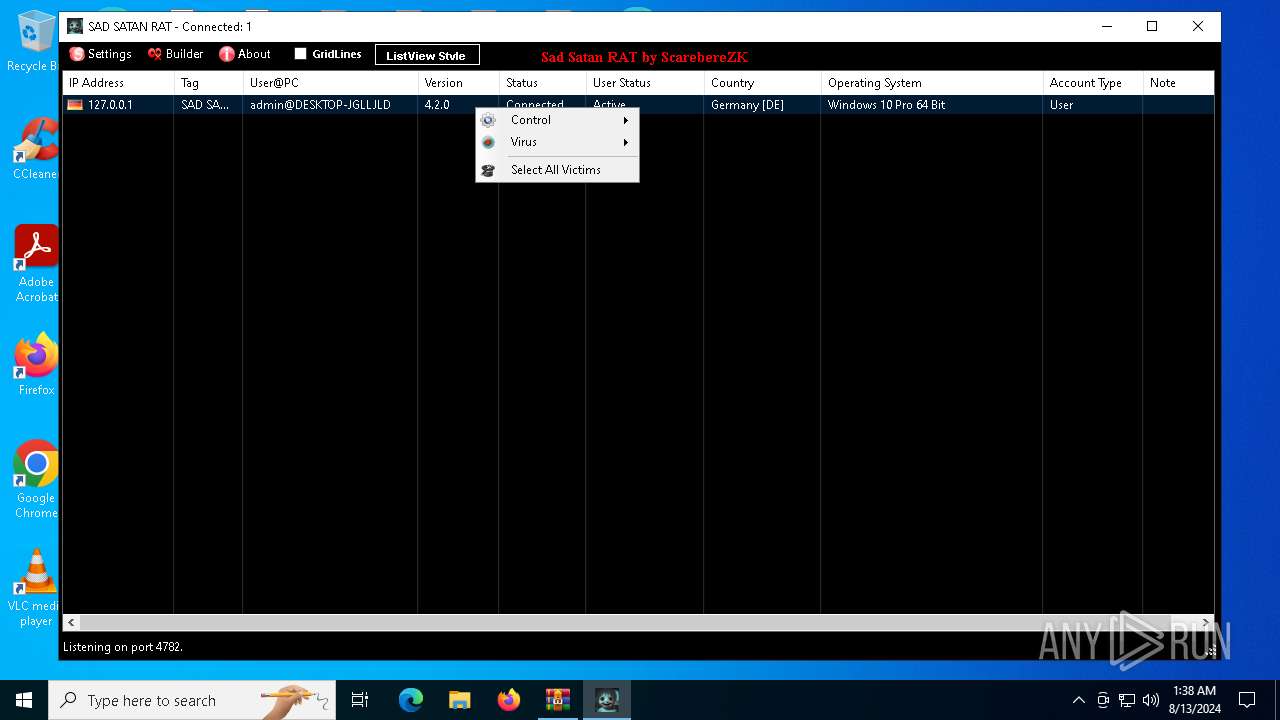
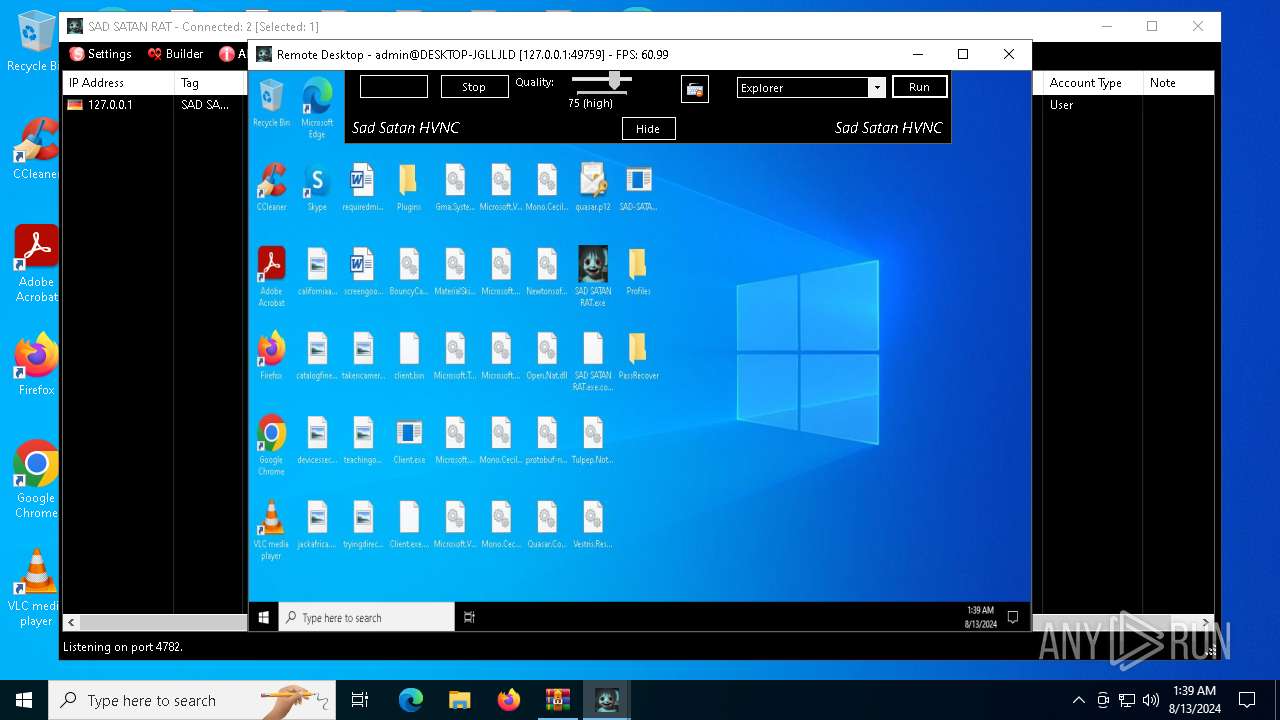
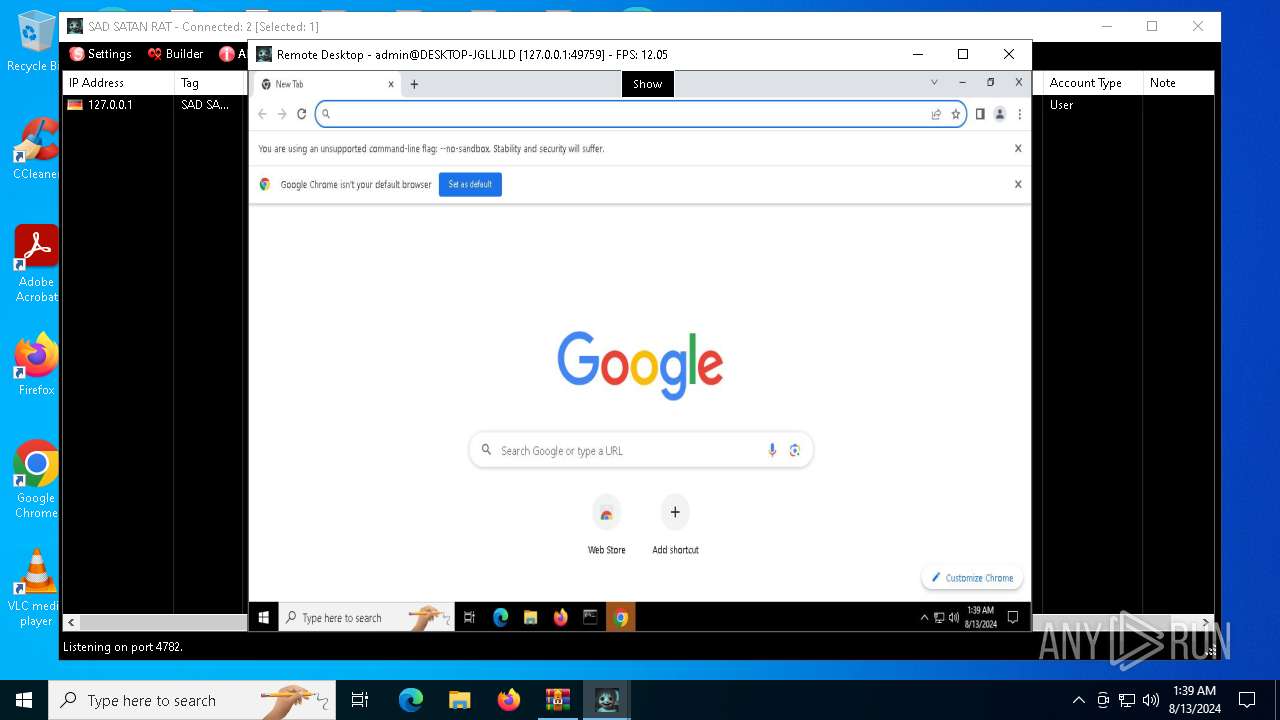
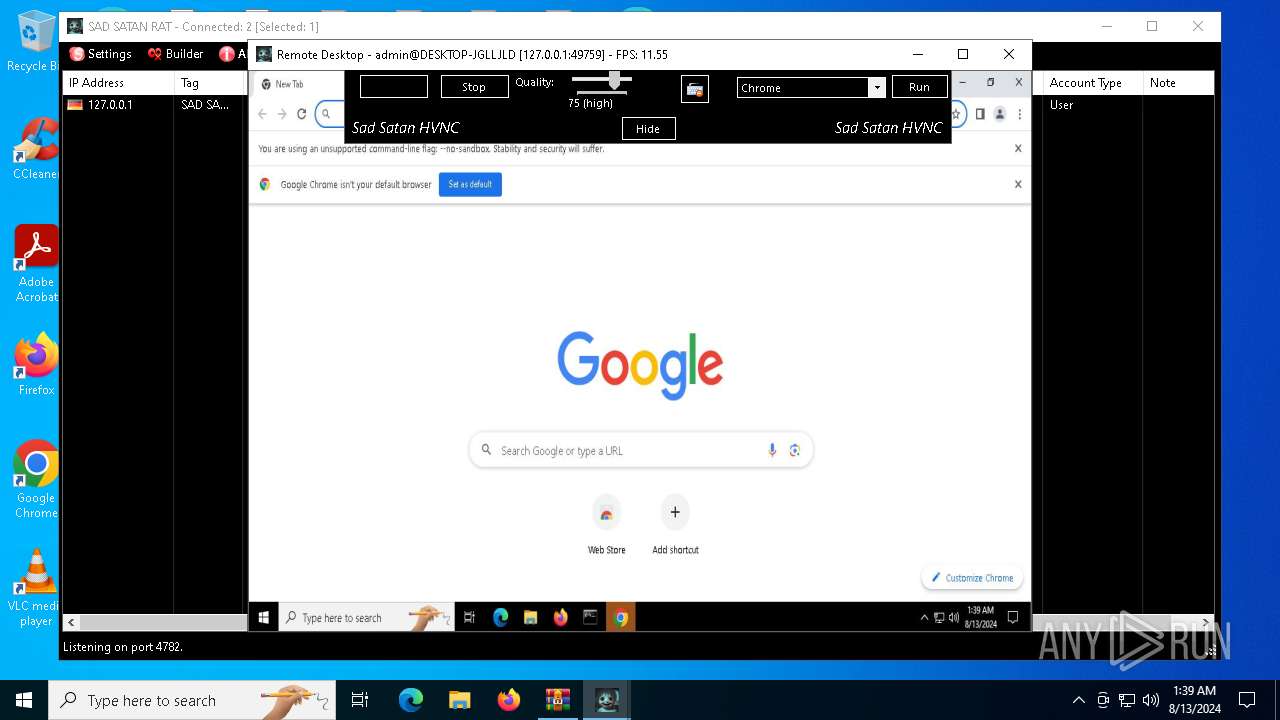
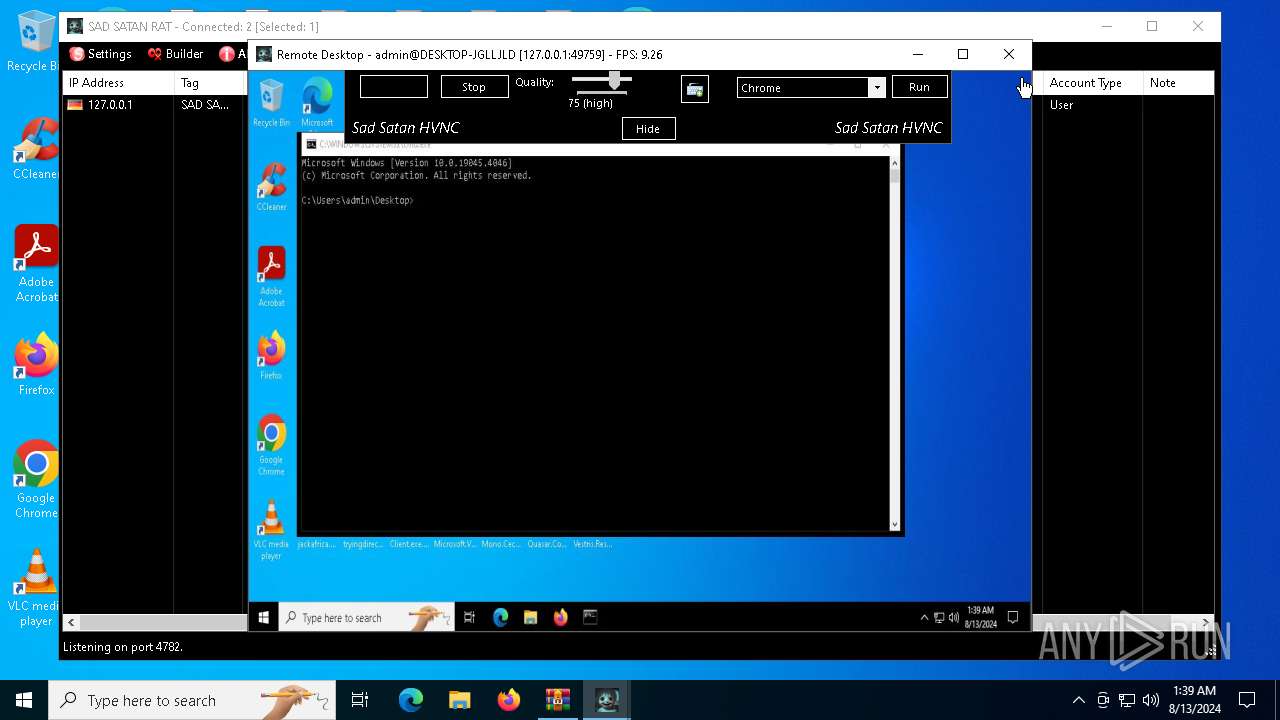
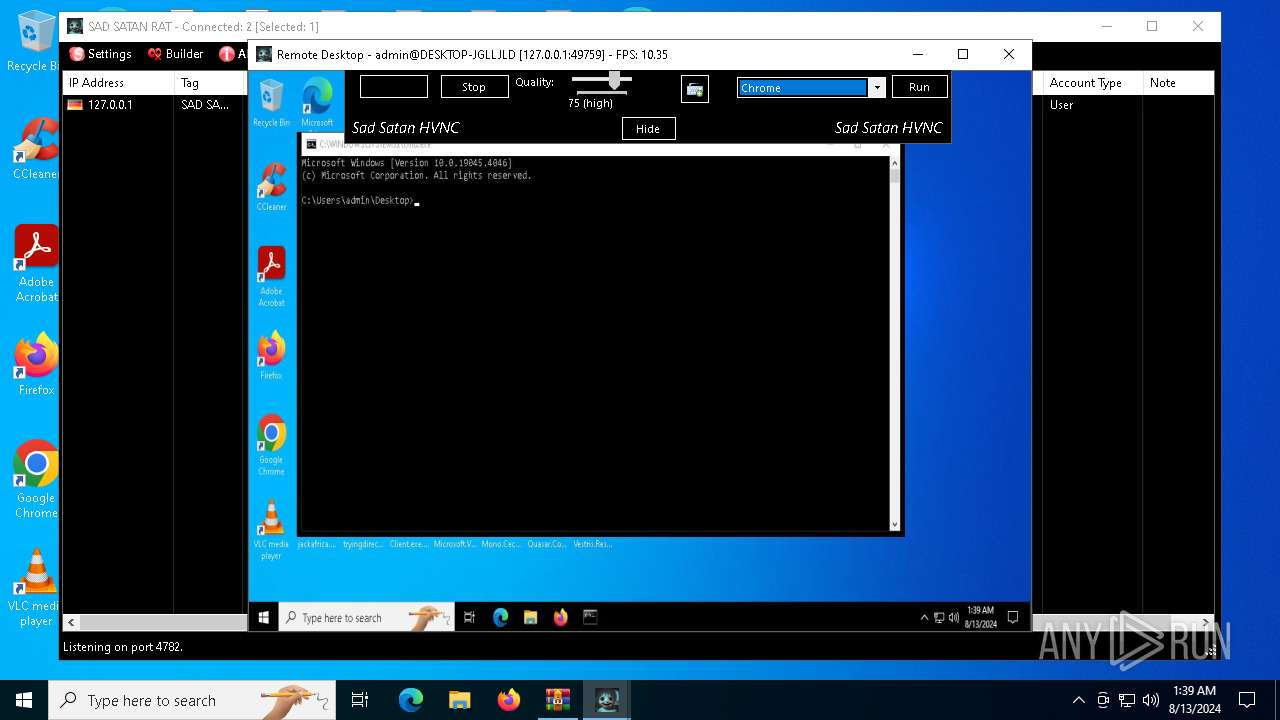
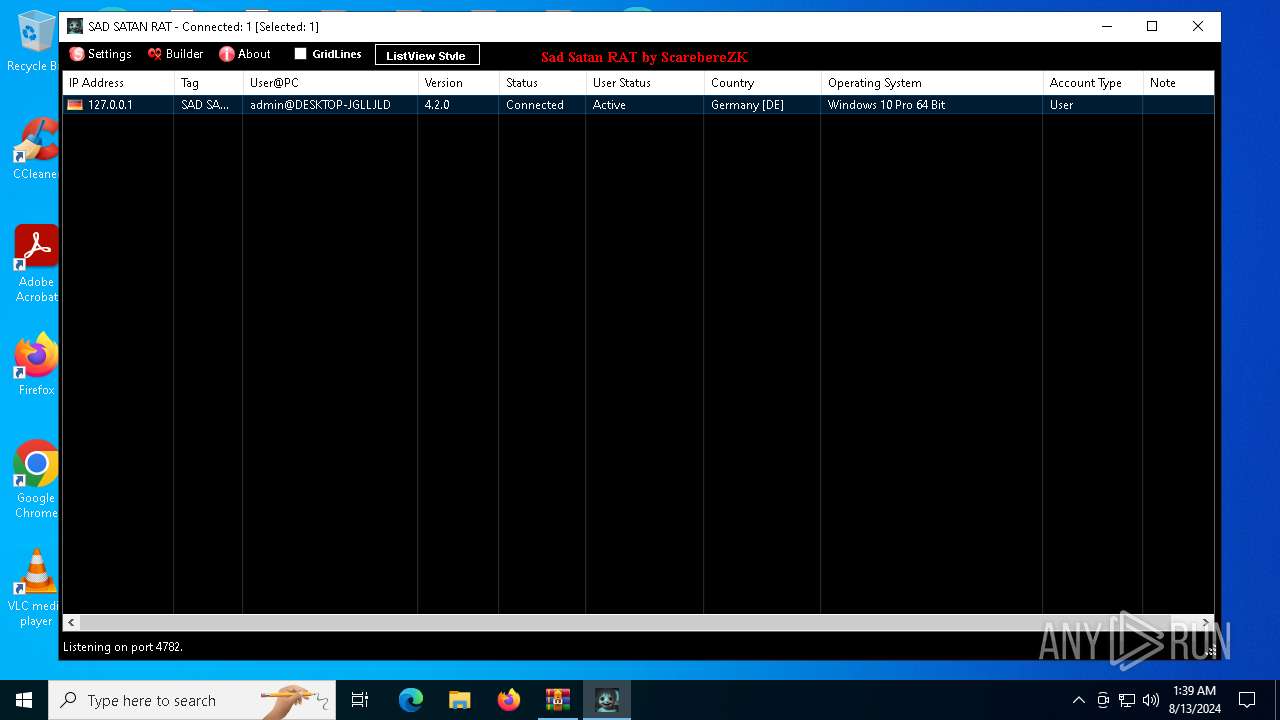
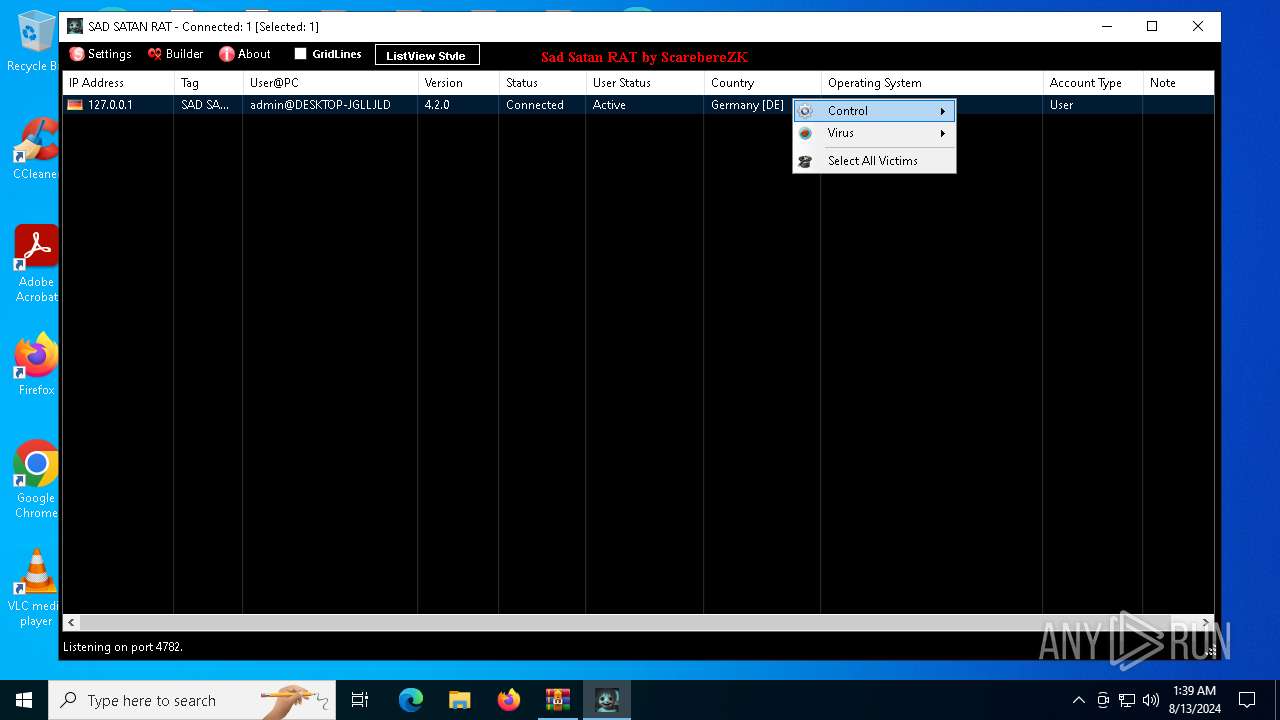
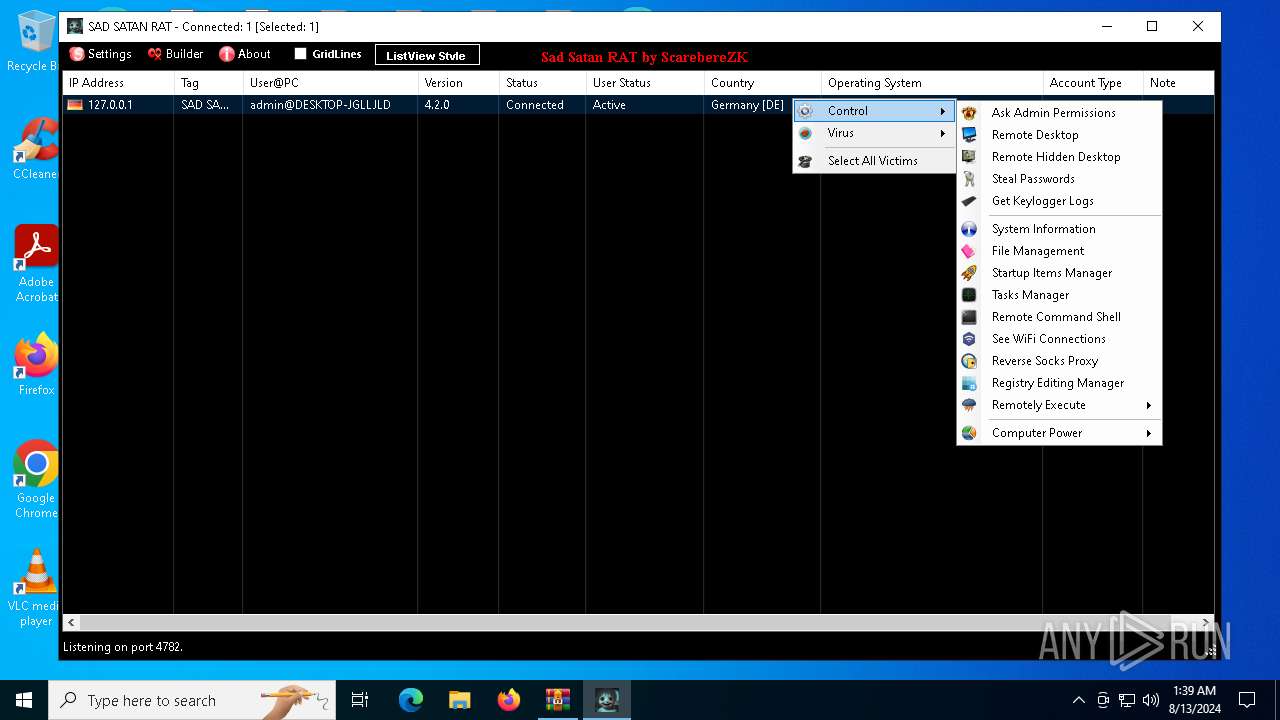
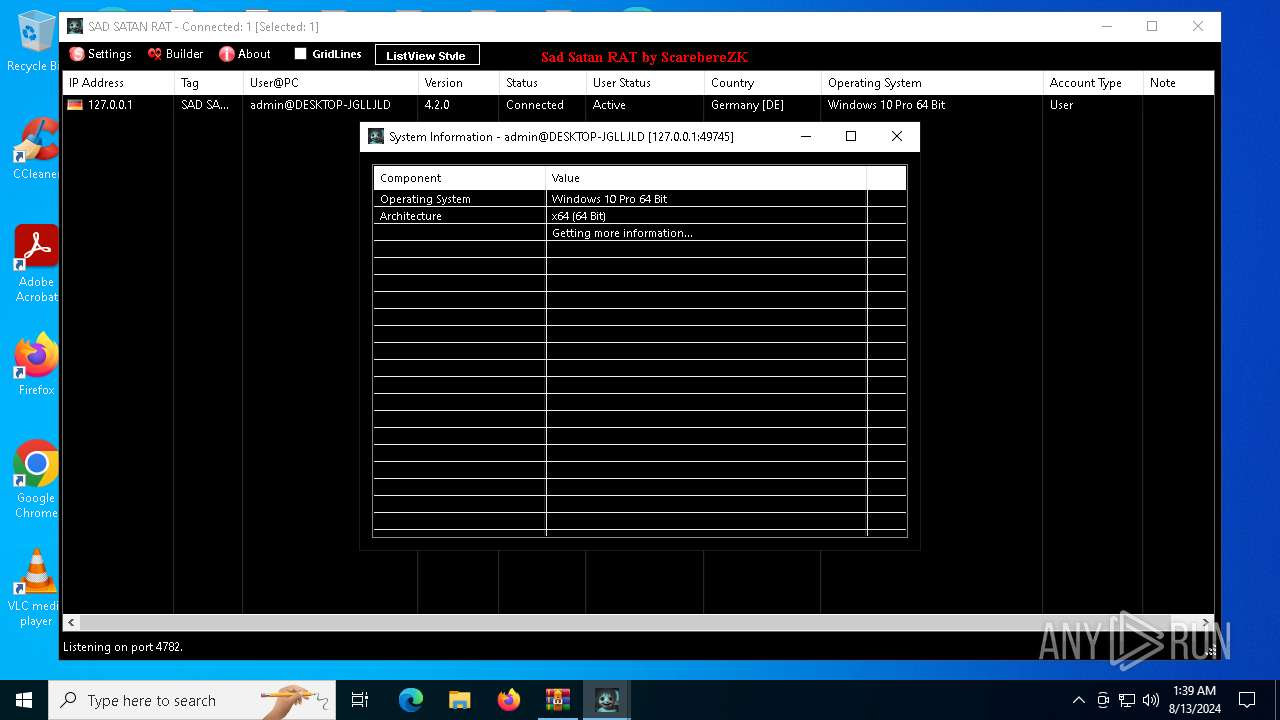
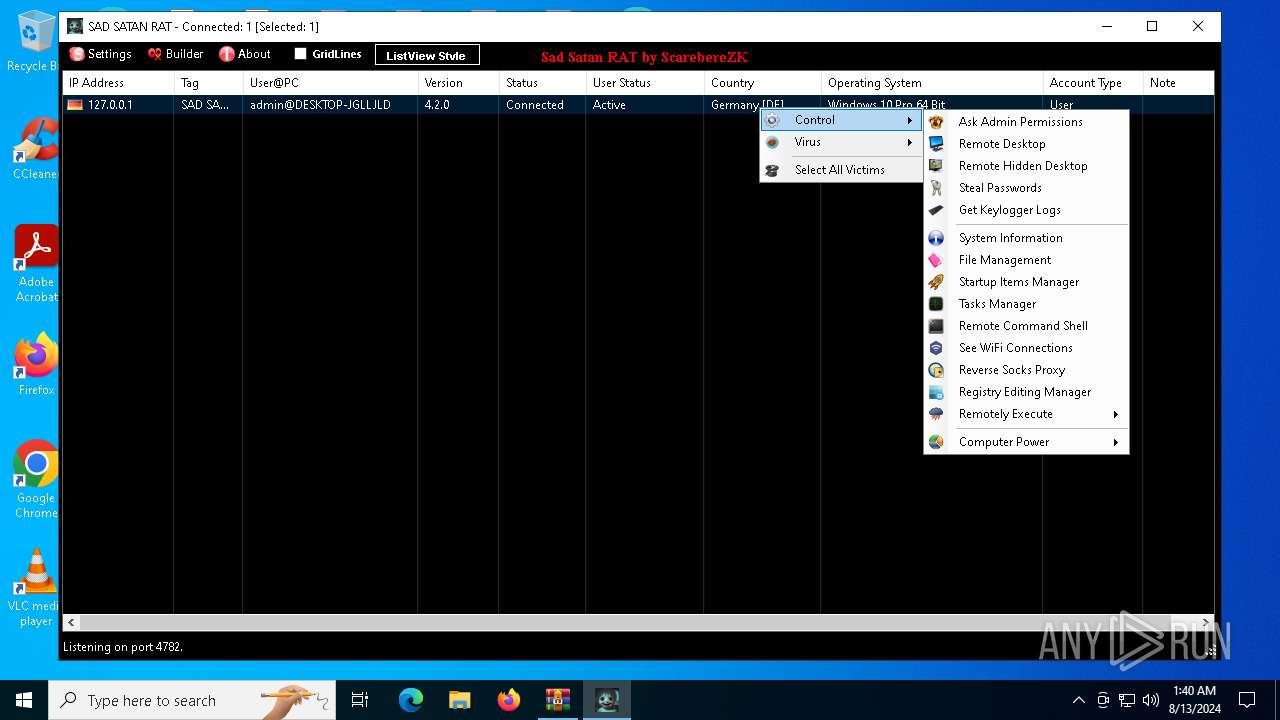
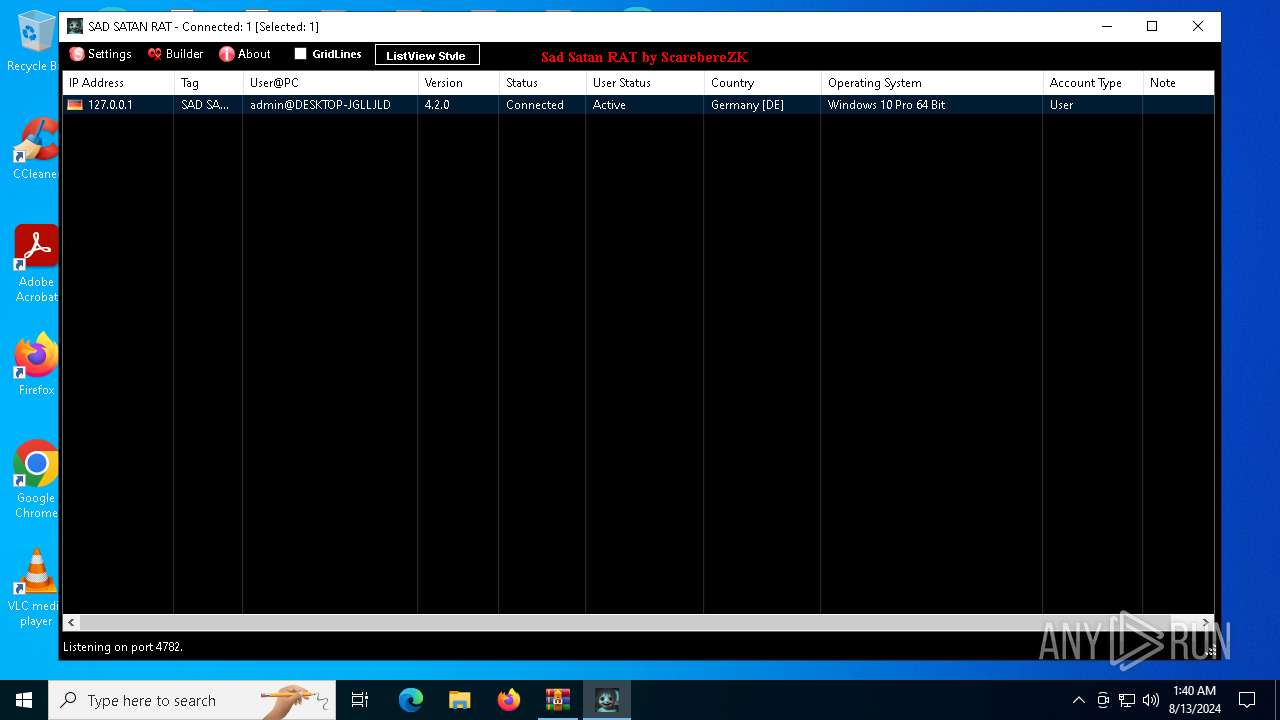
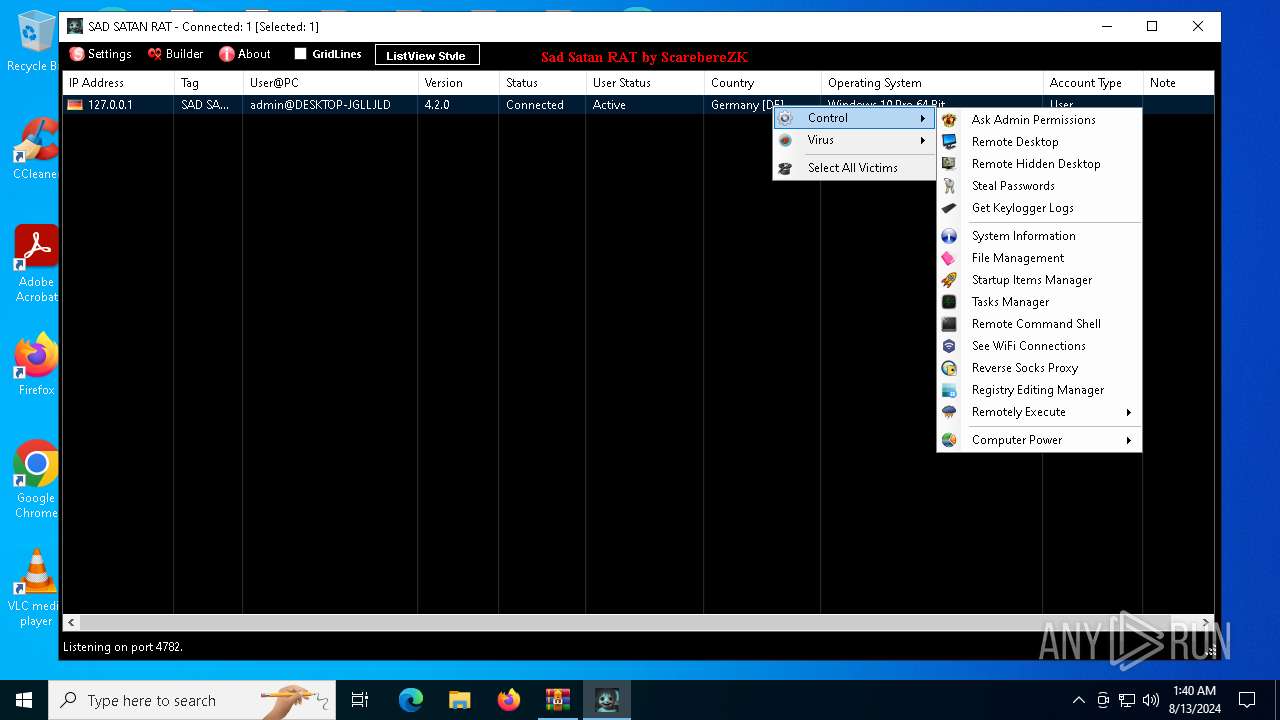
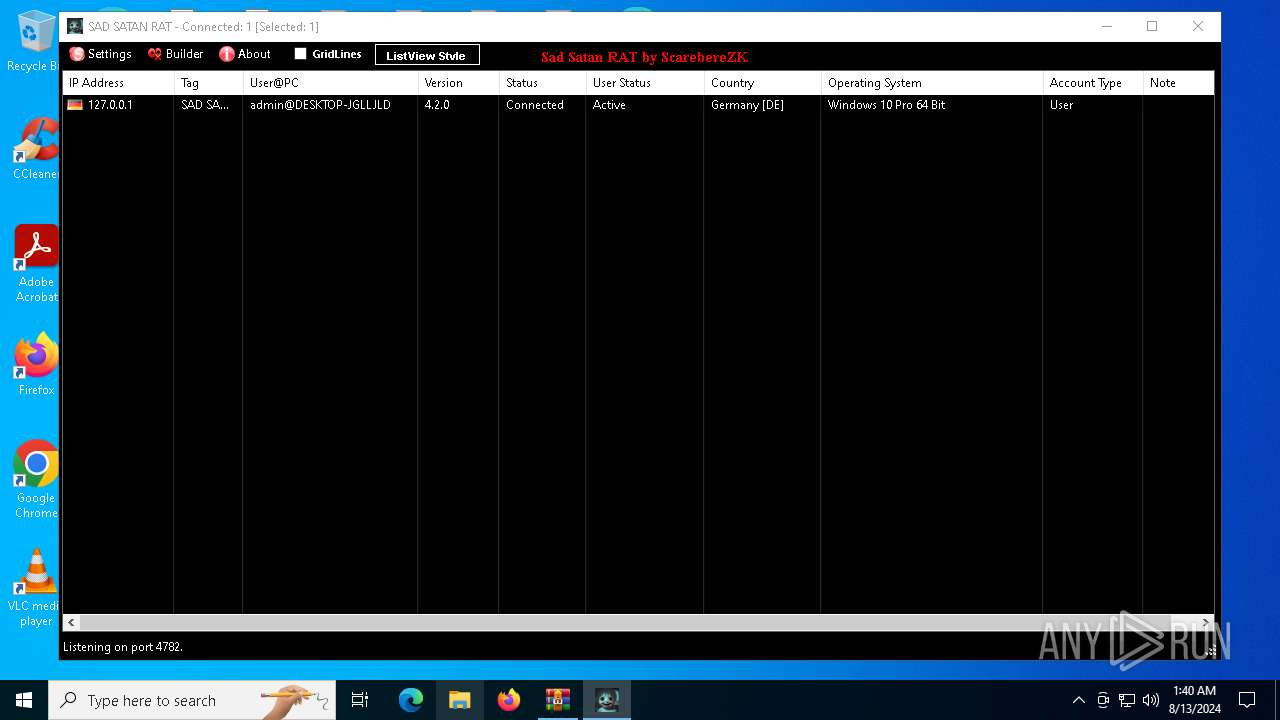
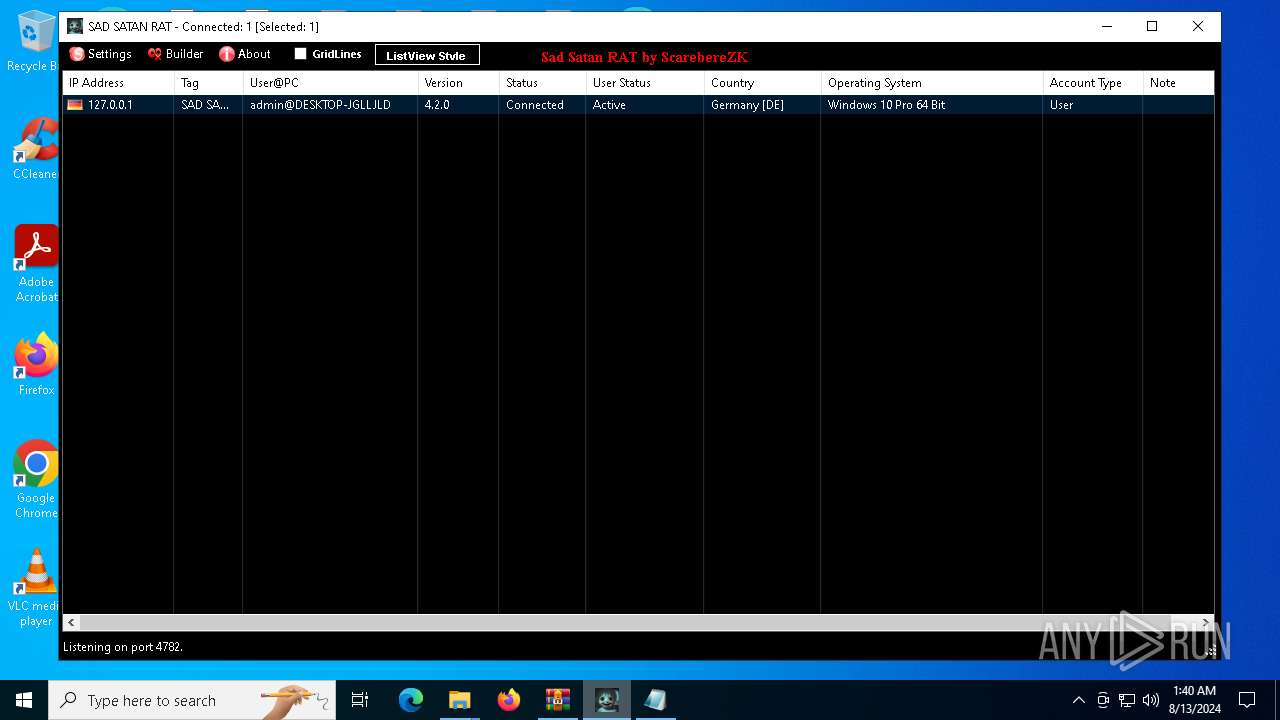
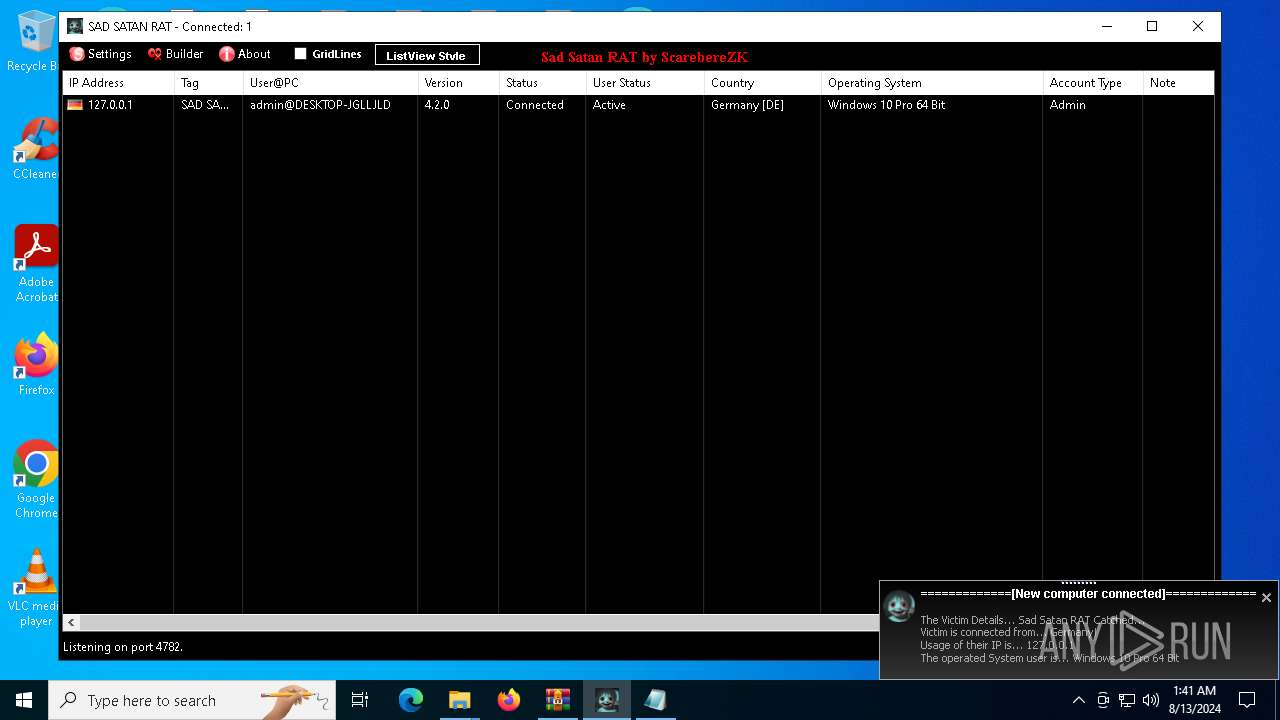
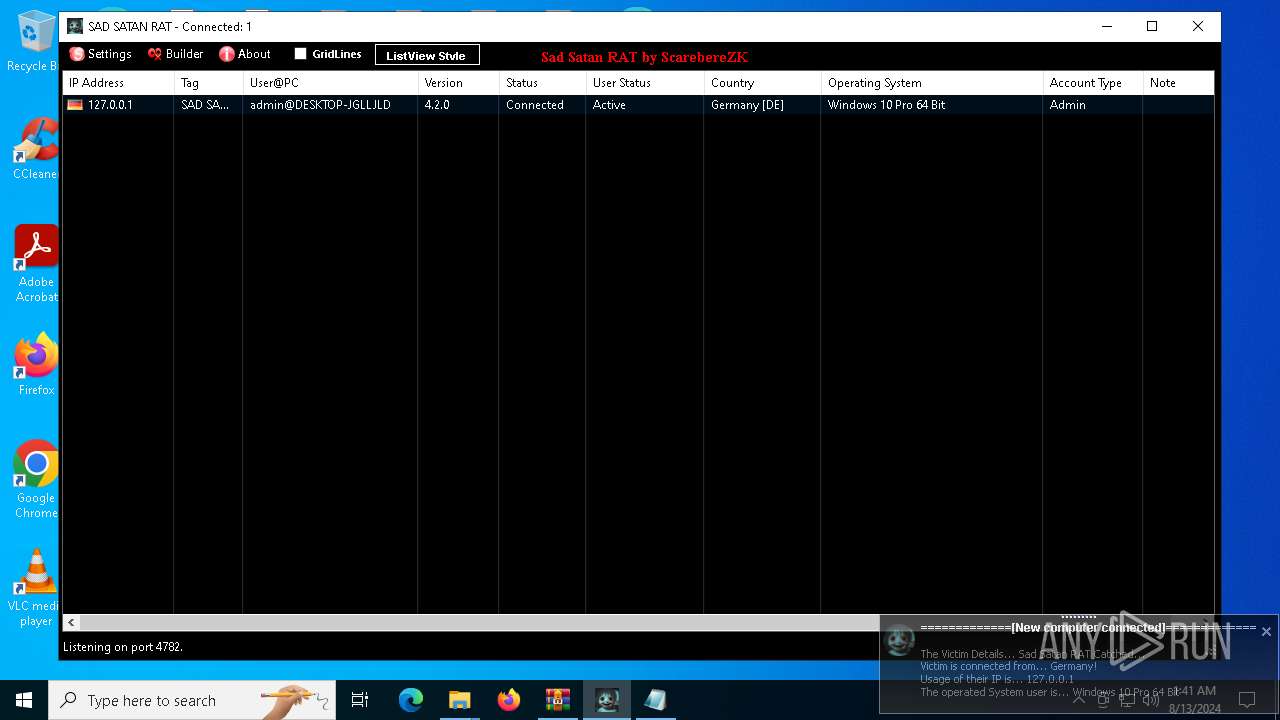
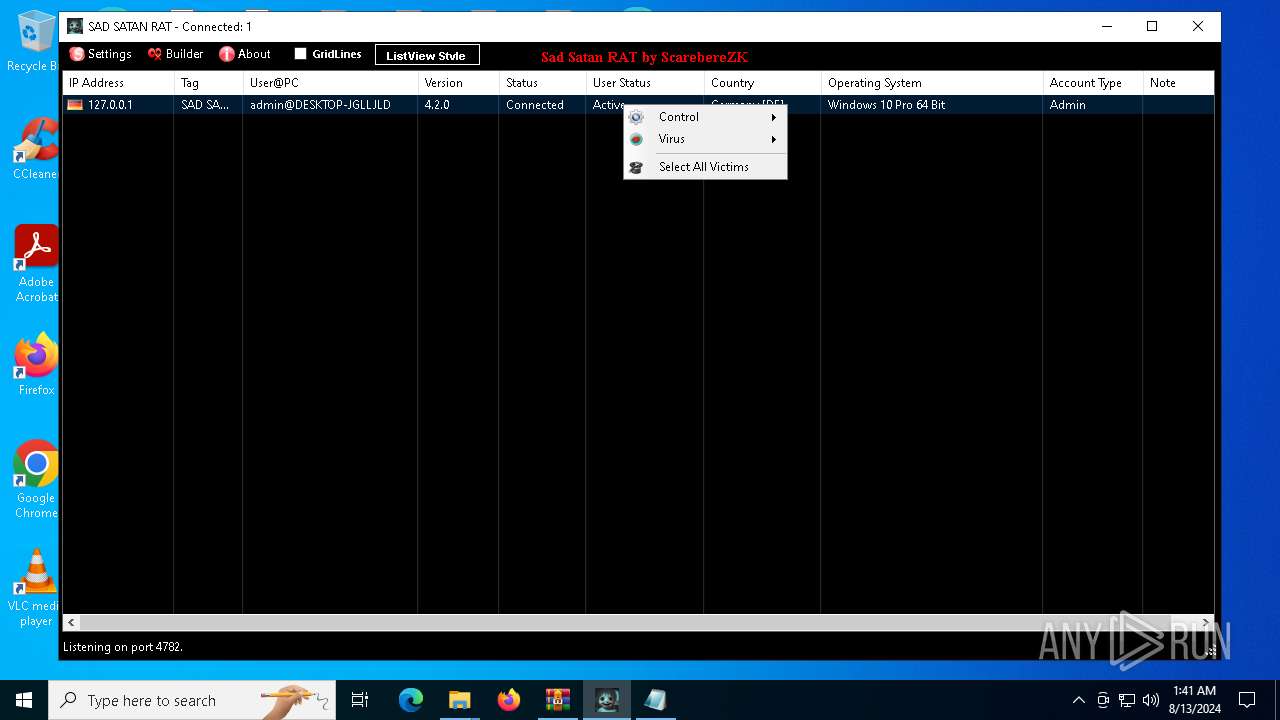
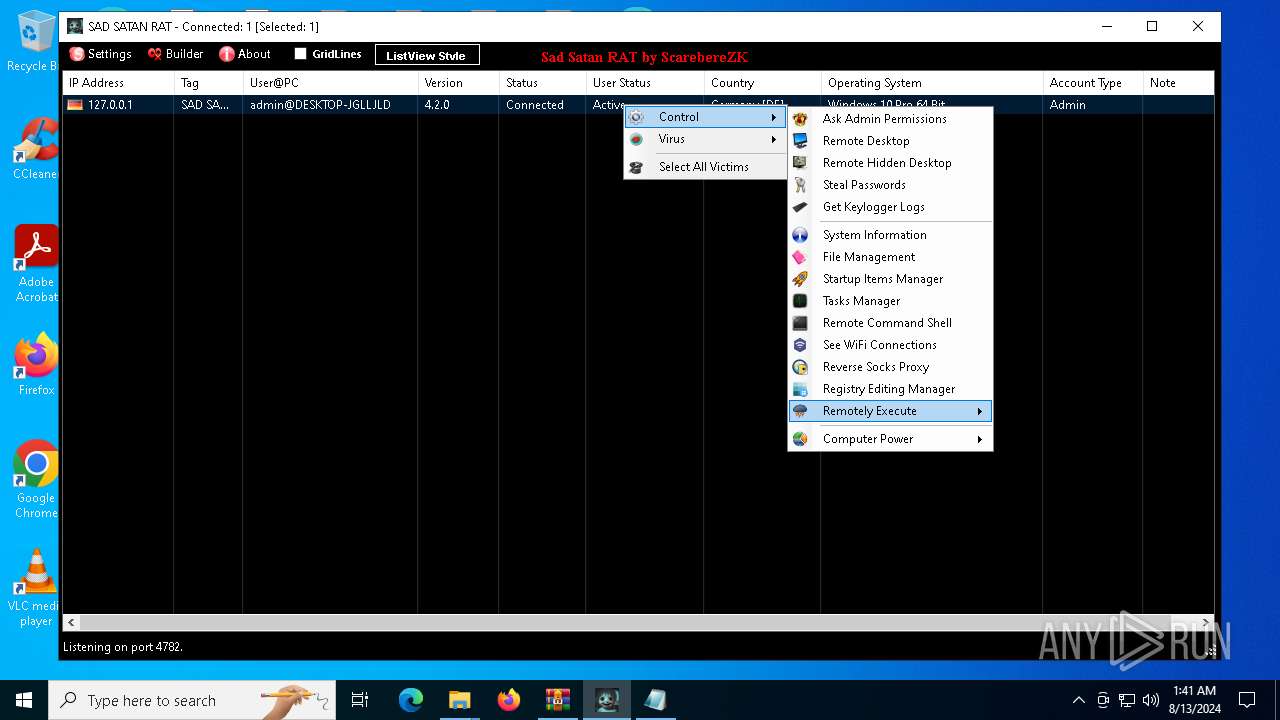
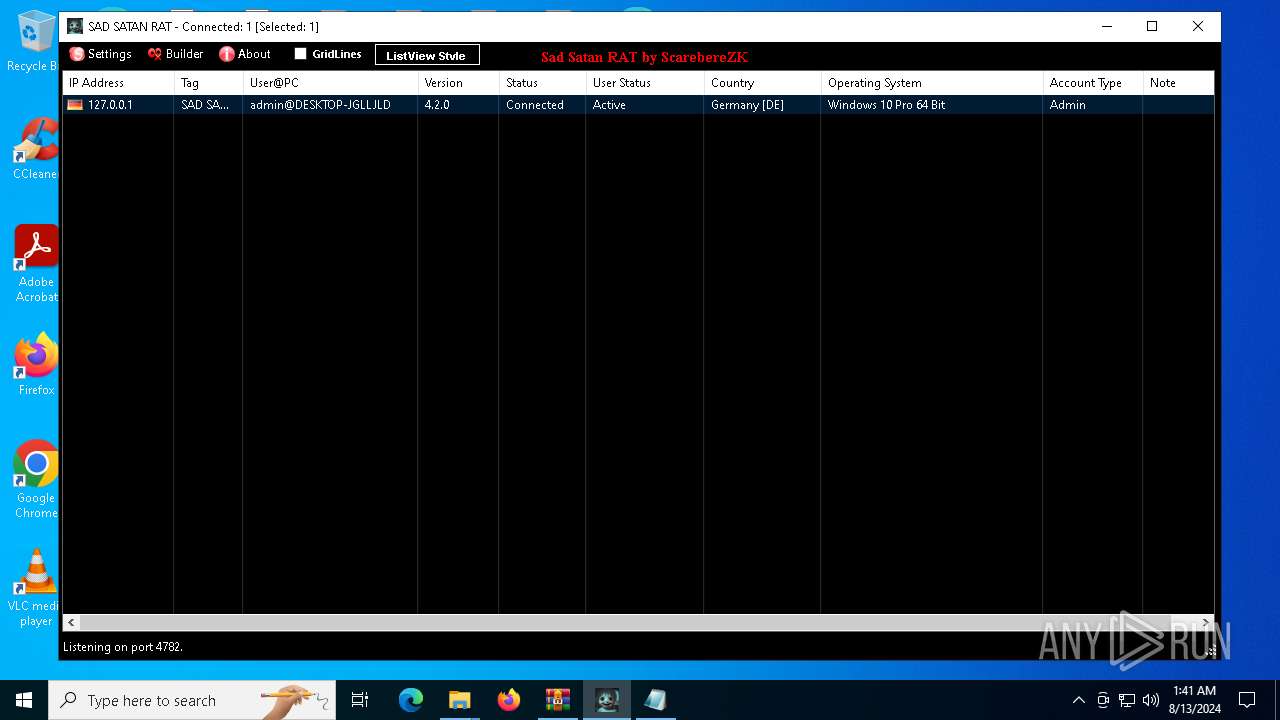
Quasar
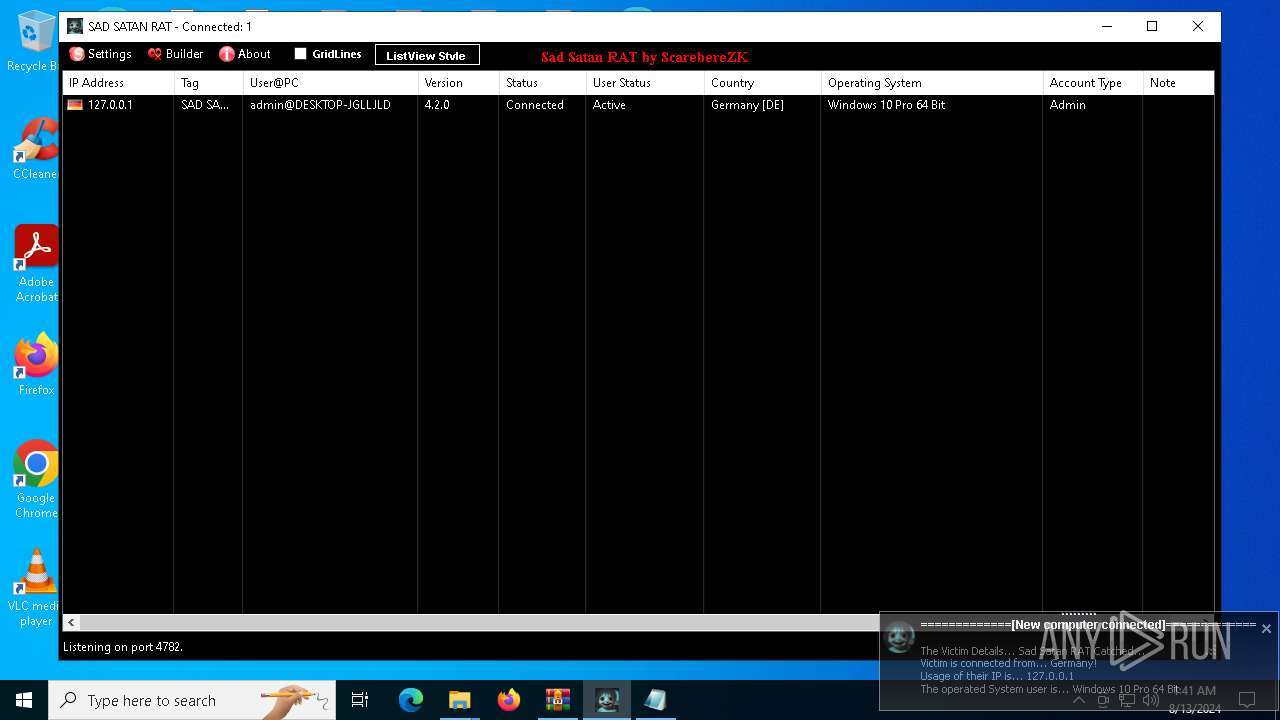
(PID) Process(6580) SAD-SATAN-CLIENT.exe
Version4.2.0
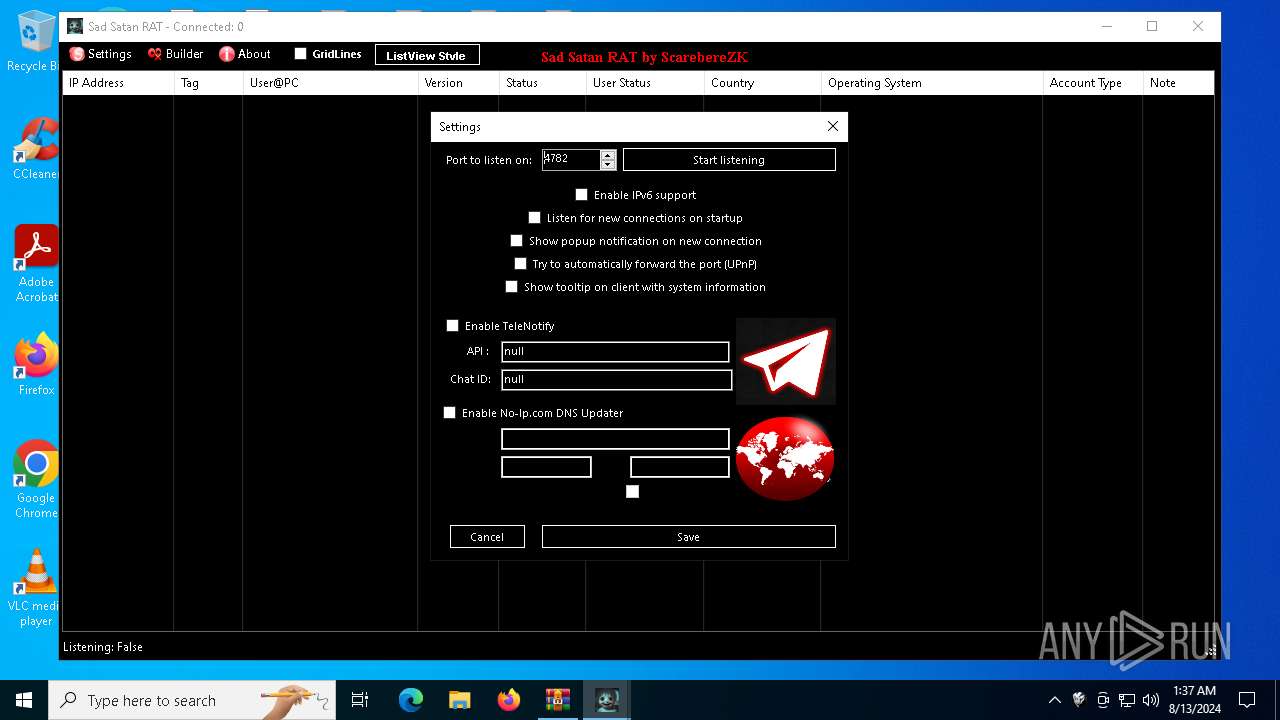
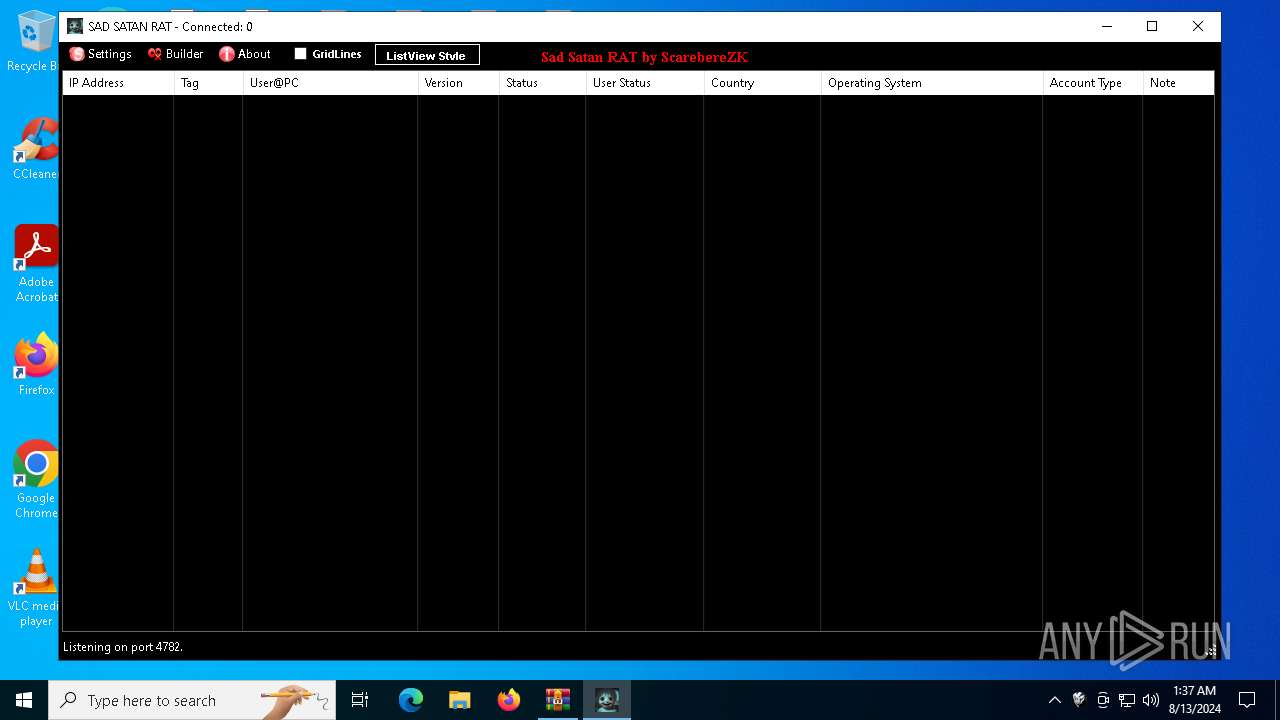
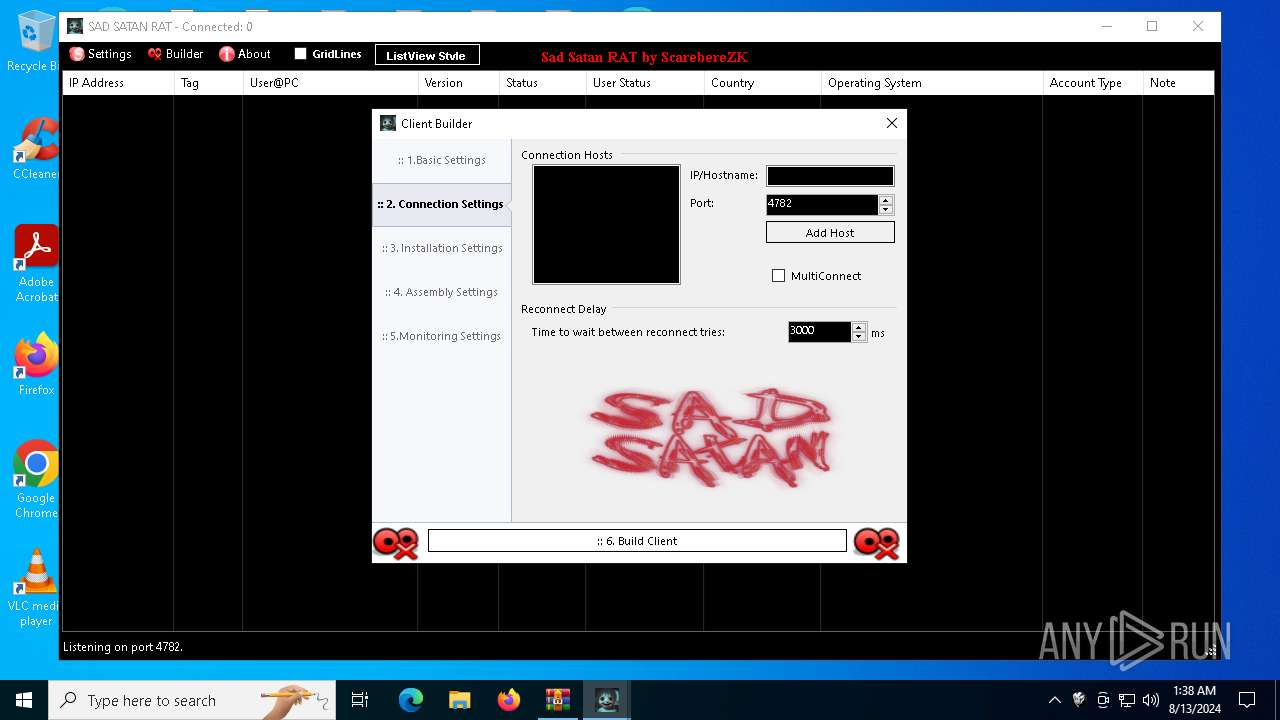
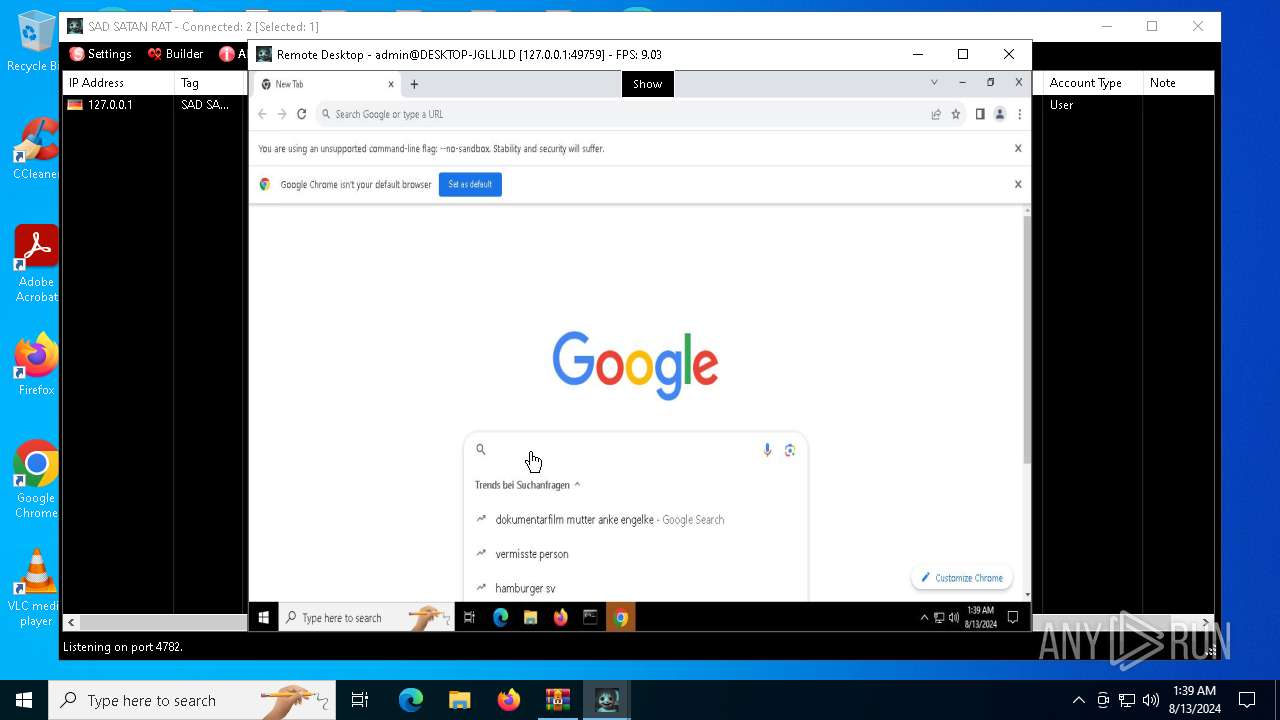
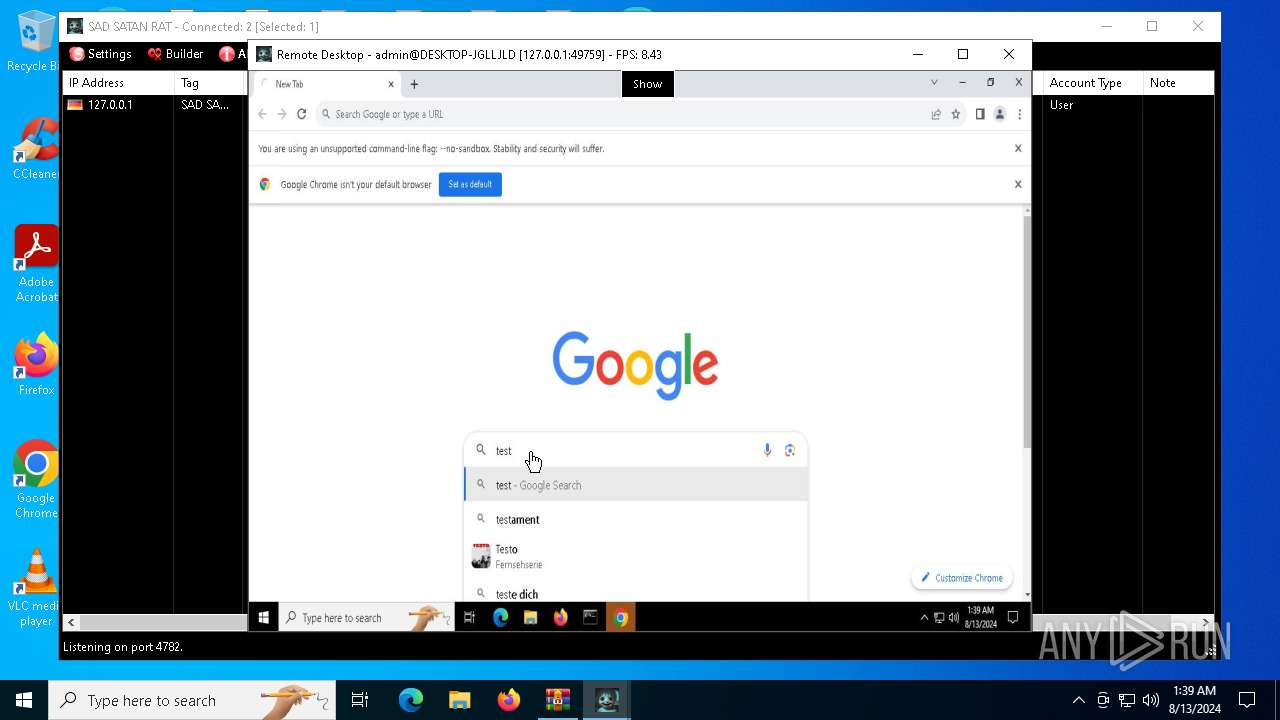
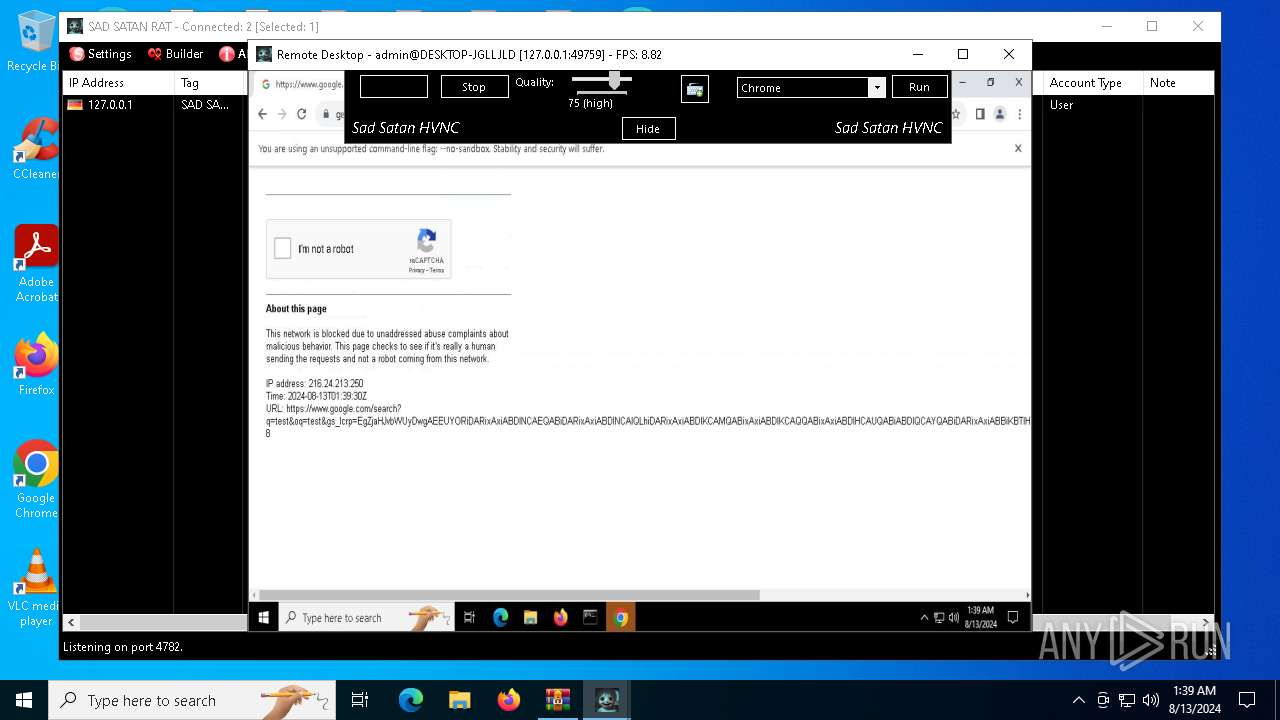
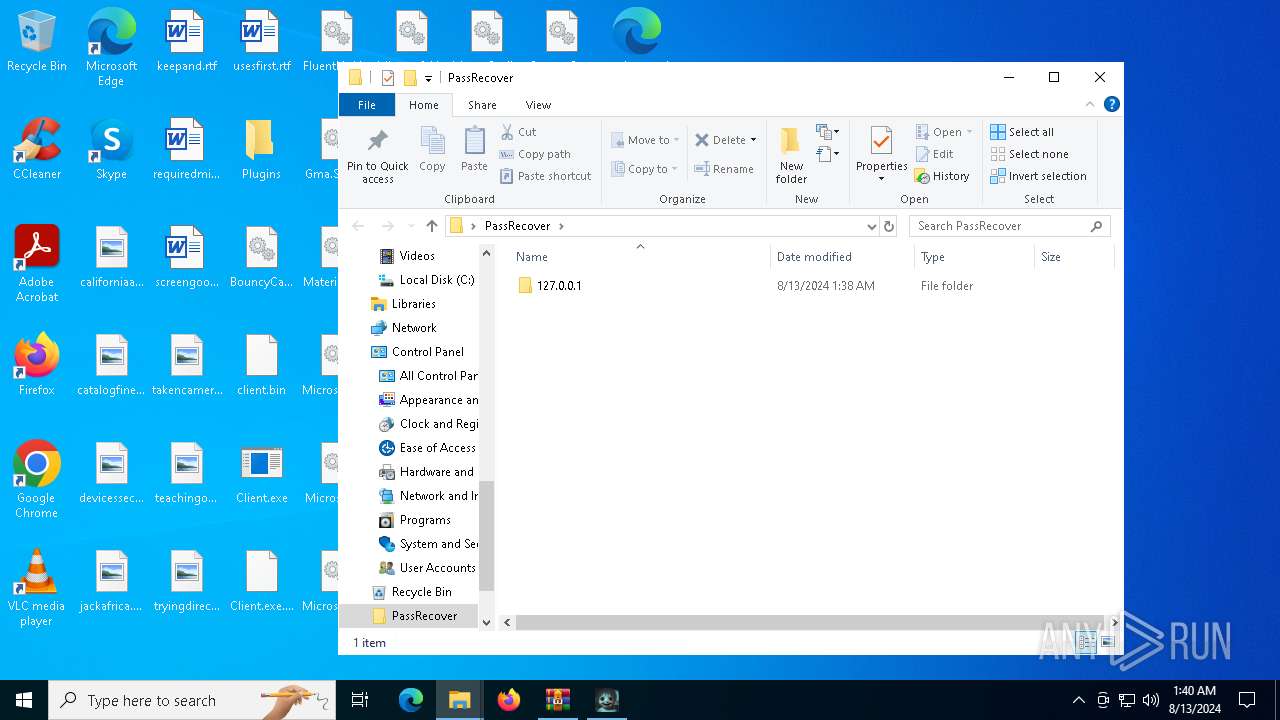
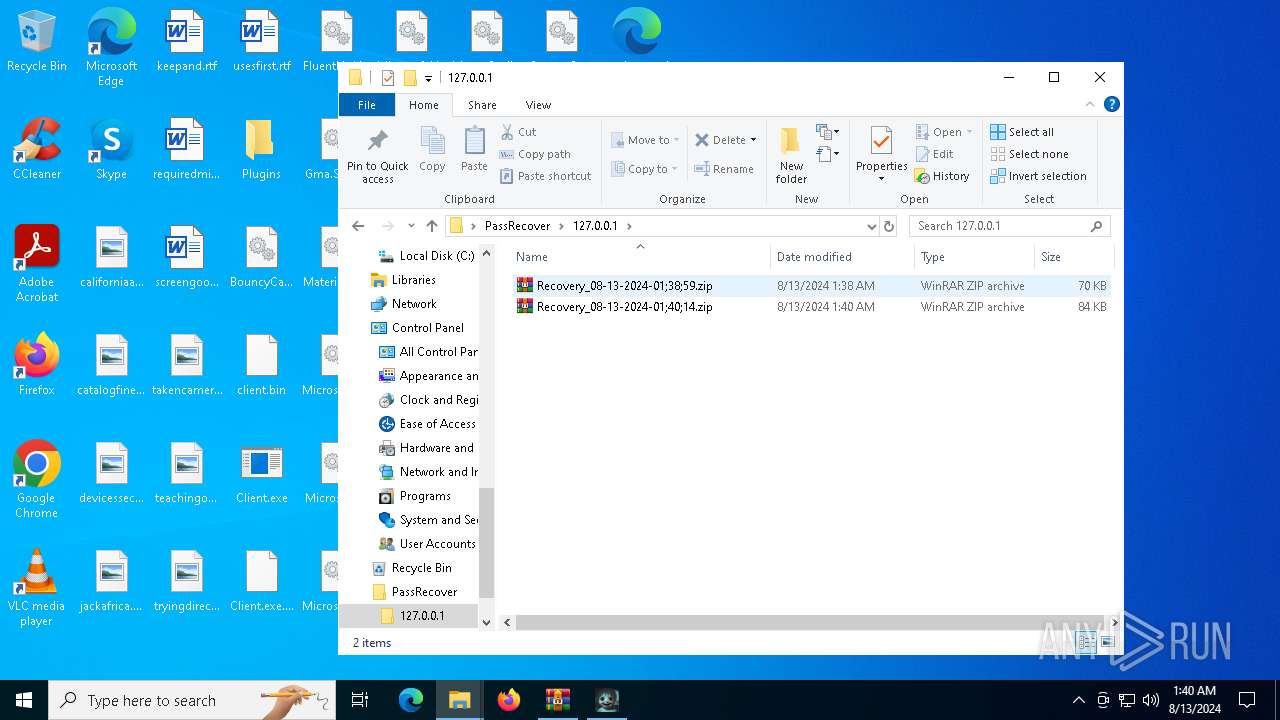
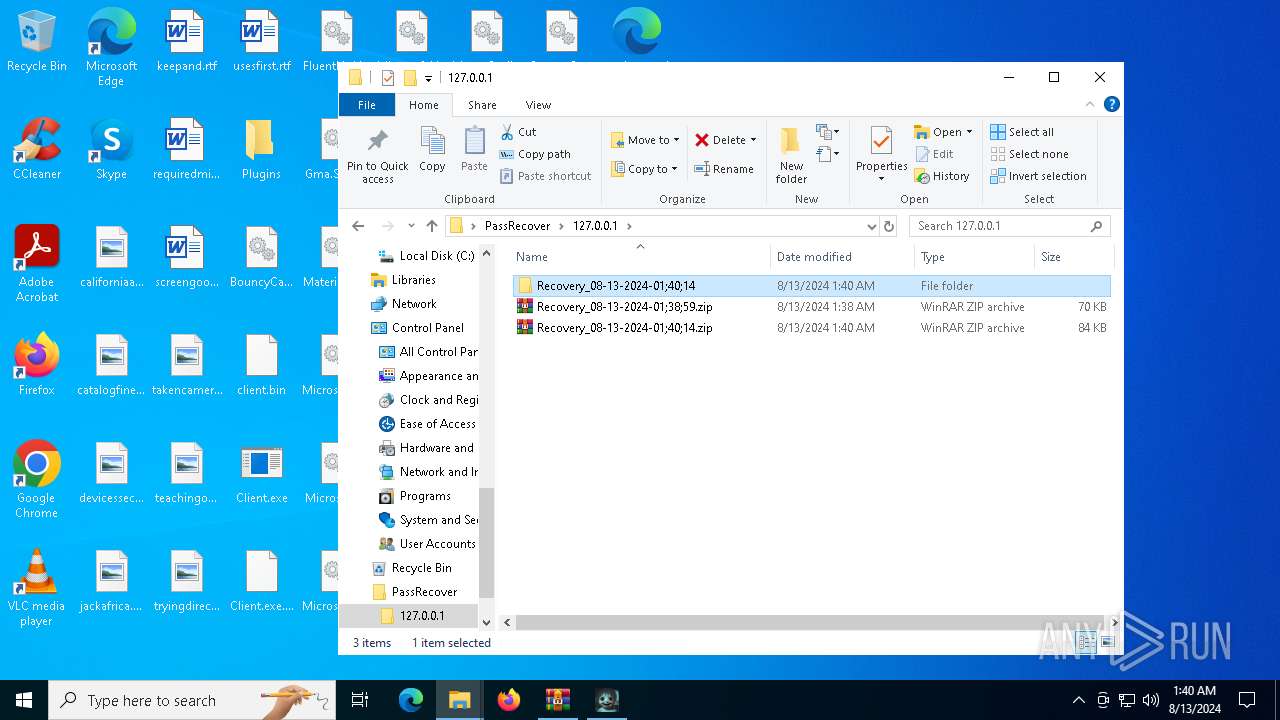
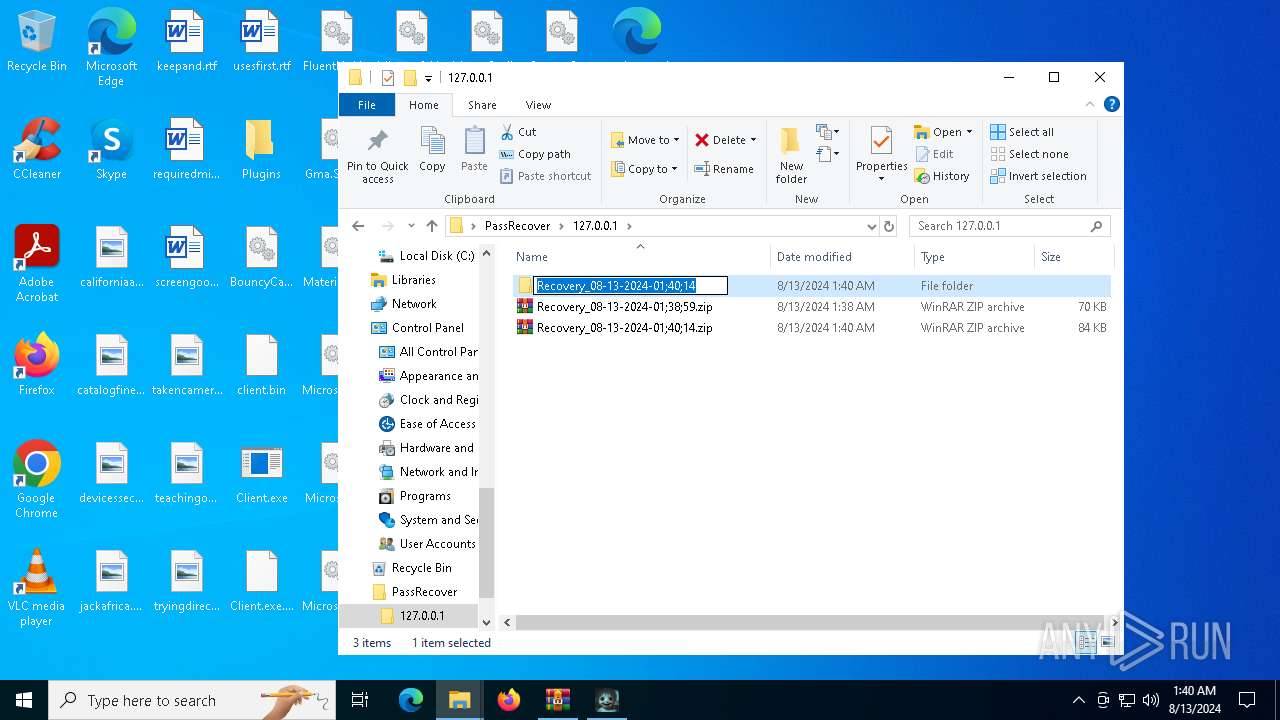
C2 (2)127.0.0.1:4782
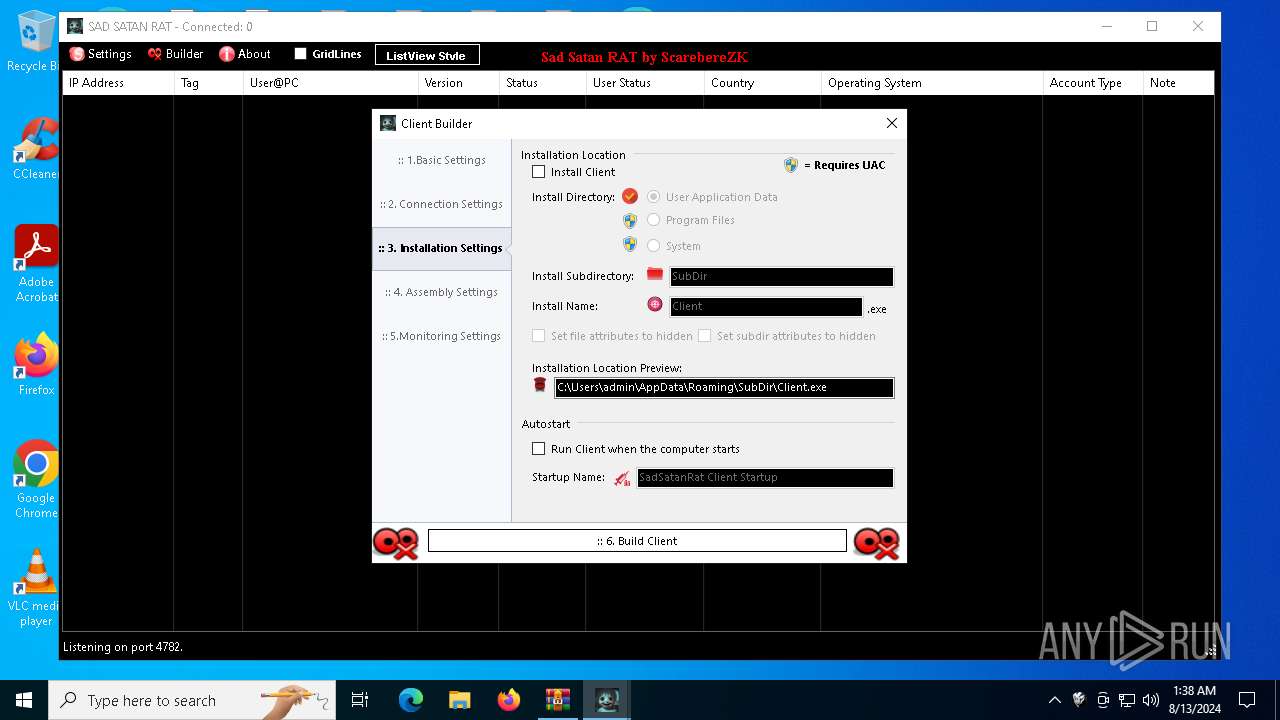
Sub_DirSubDir
Install_NameClient.exe
MutexSAD_SATAN_RAT_eed99bf9-d139-4d38-b3f1-d3d981c2821e
StartupSadSatanRat Client Startup
TagSAD SAD SATAN
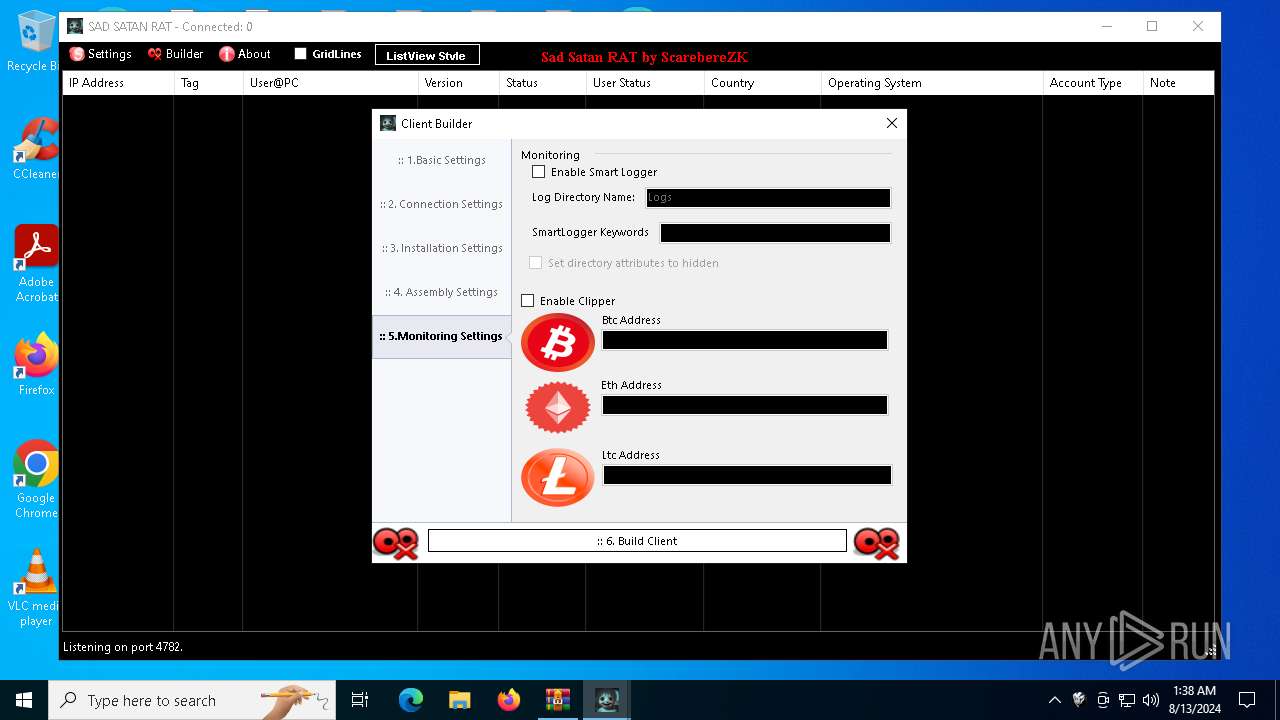
LogDirLogs
Signature
Certificate
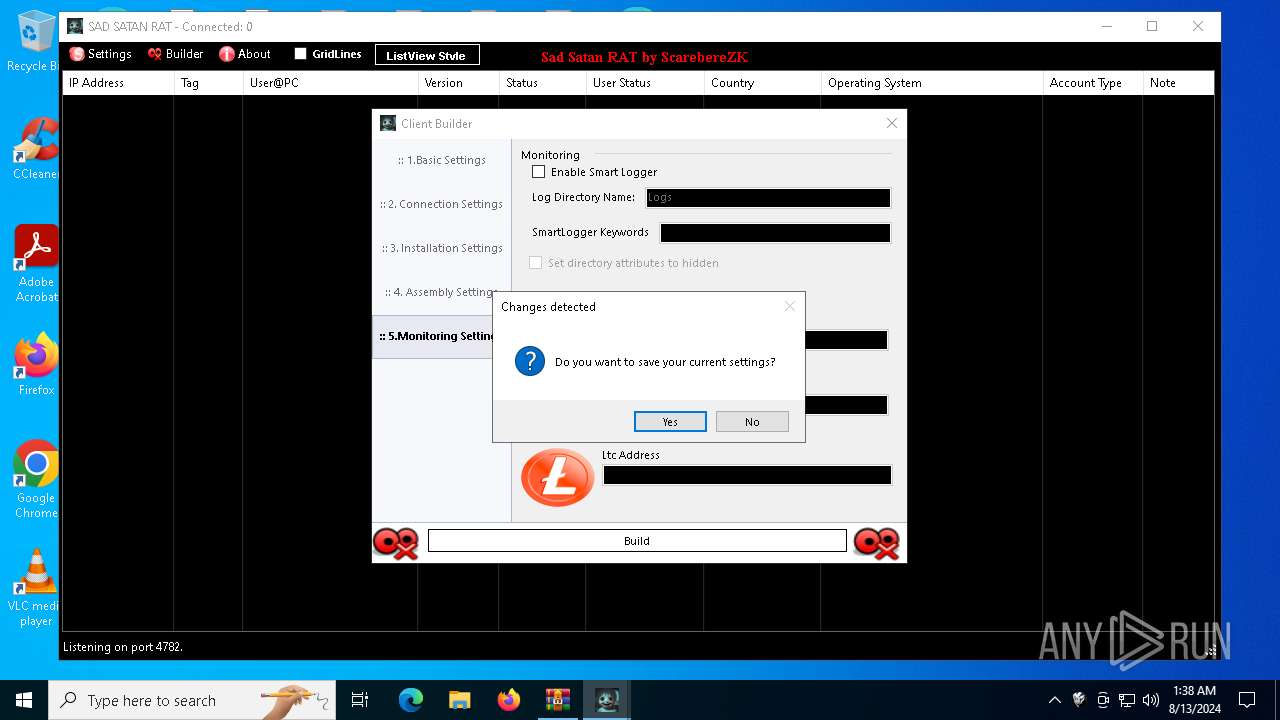
(PID) Process(3324) SAD-SATAN-CLIENT.exe
Version4.2.0
C2 (2)127.0.0.1:4782
Sub_DirSubDir
Install_NameClient.exe
MutexSAD_SATAN_RAT_eed99bf9-d139-4d38-b3f1-d3d981c2821e
StartupSadSatanRat Client Startup
TagSAD SAD SATAN
LogDirLogs
Signature
Certificate
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
215
Monitored processes
75
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | findstr All | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-sandbox --disable-quic --user-data-dir="C:\Users\admin\AppData\Local\Google\Chrome\SecureFolder" --no-appcompat-clear --mojo-platform-channel-handle=5000 --field-trial-handle=1932,i,11559648011221117440,8978591801235361436,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1568 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2728 | netsh wlan show profile | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2768 | cmd.exe taskkill /IM chrome.exe /F | C:\Windows\System32\cmd.exe | — | SAD-SATAN-CLIENT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2900 | "cmd.exe" /C chcp 65001 && netsh wlan show profile | findstr All | C:\Windows\System32\cmd.exe | — | SAD-SATAN-CLIENT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-sandbox --disable-quic --user-data-dir="C:\Users\admin\AppData\Local\Google\Chrome\SecureFolder" --no-appcompat-clear --mojo-platform-channel-handle=2028 --field-trial-handle=1932,i,11559648011221117440,8978591801235361436,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3140 | "cmd.exe" /C chcp 65001 && netsh wlan show networks mode=bssid | C:\Windows\System32\cmd.exe | — | SAD-SATAN-CLIENT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3256 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
94 838
Read events
94 397
Write events
409
Delete events
32
Modification events
| (PID) Process: | (7084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (7084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Sad Satan RAT.7z | |||
| (PID) Process: | (7084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7084) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @cryptext.dll,-6148 |
Value: Personal Information Exchange | |||
| (PID) Process: | (7084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
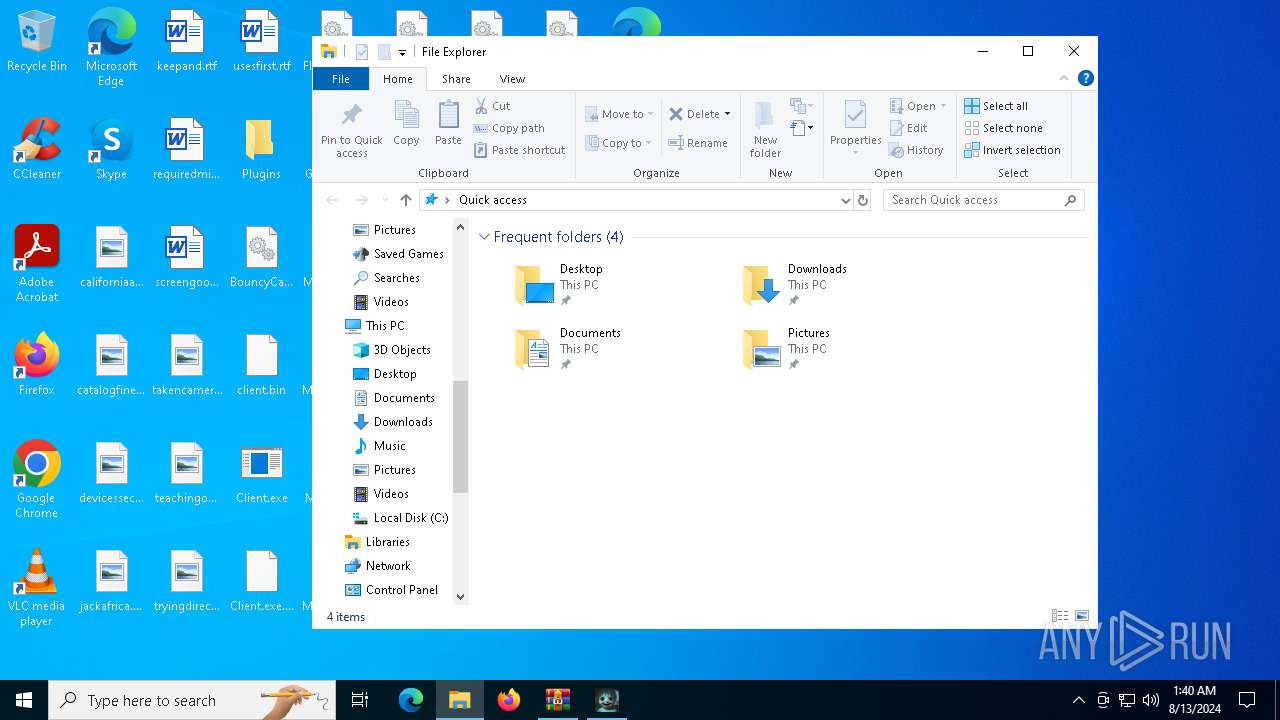
Executable files
32
Suspicious files
292
Text files
370
Unknown types
79
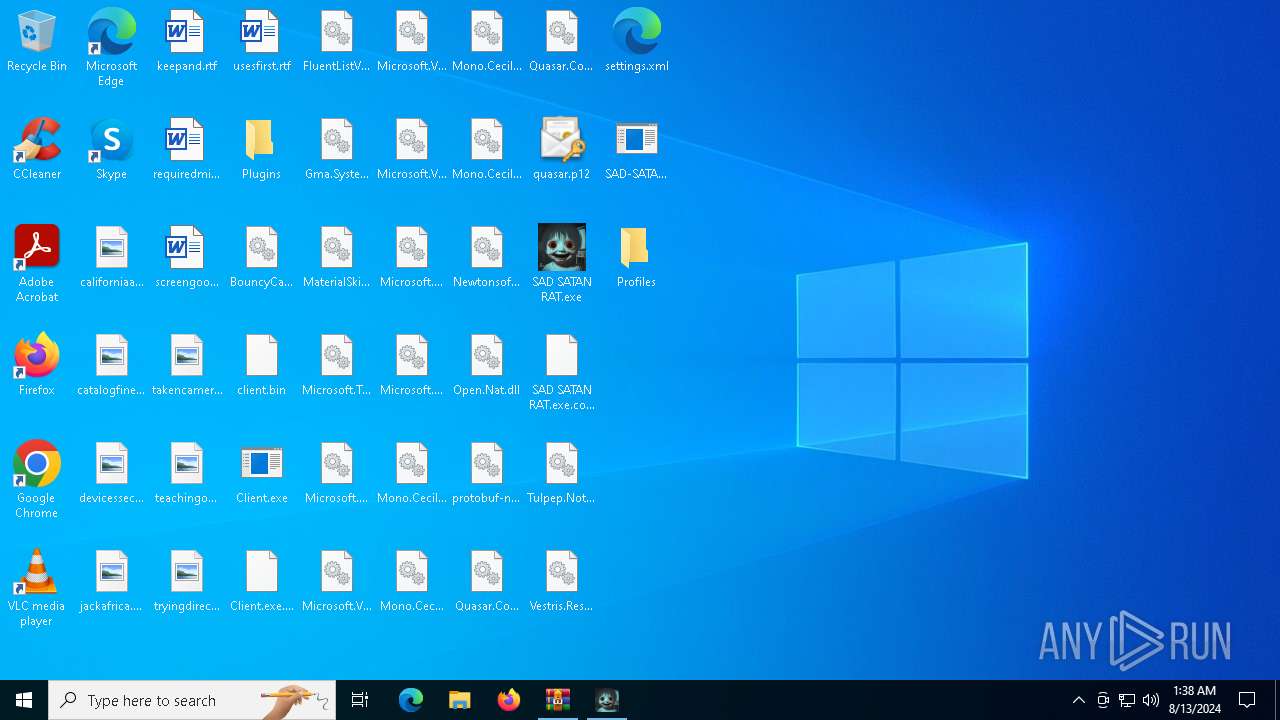
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7084 | WinRAR.exe | C:\Users\admin\Desktop\Plugins\EntityFramework.SqlServer.xml | xml | |
MD5:2D1549C365902D6CBEE20E02A985B68B | SHA256:902F57044BAF104DD9A491DADCBA4C787B6F64531880DC3B11345D5758D7BD81 | |||
| 7084 | WinRAR.exe | C:\Users\admin\Desktop\Client.exe.config | xml | |
MD5:DC77BDB7FBF40A24BAAE4FDC78B72F44 | SHA256:40FA7D2CF05768C2C660556ED04AE1A2615B02516EC1B059778E065B0B259043 | |||
| 7084 | WinRAR.exe | C:\Users\admin\Desktop\FluentListView.dll | executable | |
MD5:7FF94290453212CFBA0DF79CE8A01A44 | SHA256:85AD16ABE11603047479ACDF452D0CE9B3DD05702FC87DA4D338AFF47D7F4CC8 | |||
| 7084 | WinRAR.exe | C:\Users\admin\Desktop\BouncyCastle.Crypto.dll | executable | |
MD5:0CF454B6ED4D9E46BC40306421E4B800 | SHA256:E51721DC0647F4838B1ABC592BD95FD8CB924716E8A64F83D4B947821FA1FA42 | |||
| 7084 | WinRAR.exe | C:\Users\admin\Desktop\Plugins\PluginHVNC.pdb | binary | |
MD5:9CD86E303945AAB646ADB15634F16A07 | SHA256:7B363877C4107FD0B5FA540F633BB3DB9628C2FADEBD48251EC4A41244A17EB1 | |||
| 7084 | WinRAR.exe | C:\Users\admin\Desktop\Plugins\Newtonsoft.Json.xml | xml | |
MD5:D398FFE9FDAC6A53A8D8BB26F29BBB3C | SHA256:79EE87D4EDE8783461DE05B93379D576F6E8575D4AB49359F15897A854B643C4 | |||
| 7084 | WinRAR.exe | C:\Users\admin\Desktop\SAD SATAN RAT.exe.config | xml | |
MD5:C8CD50E8472B71736E6543F5176A0C12 | SHA256:B44739EEFF82DB2B575A45B668893E2FE8FDD24A709CBF0554732FD3520B2190 | |||
| 7084 | WinRAR.exe | C:\Users\admin\Desktop\MaterialSkin.dll | executable | |
MD5:022F385E55D9D3D42A33B4CA999BF22A | SHA256:3B0E1B3AF6D2B8B3D02B6CD52849277C9C8066C2AE565E68253D4551C37492D3 | |||
| 7084 | WinRAR.exe | C:\Users\admin\Desktop\Microsoft.VisualStudio.TestPlatform.MSTest.TestAdapter.dll | executable | |
MD5:2DDC54871FF84B3692AD11BA4A5FF771 | SHA256:CB1D59FD79A412B1B05A27B32C342CBC85F018A9F1E1D67B43EBE87E43FEC0D1 | |||
| 7084 | WinRAR.exe | C:\Users\admin\Desktop\Gma.System.MouseKeyHook.dll | executable | |
MD5:BFB3BD1CB571360435100BFA6ED2B997 | SHA256:A67A424013544C8270C12633E2E1E287CD5CF0B3F2E81E8D8204B37A03DA59EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
78
DNS requests
44
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1344 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1344 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6580 | SAD-SATAN-CLIENT.exe | GET | 200 | 104.16.185.241:80 | http://icanhazip.com/ | unknown | — | — | shared |
6344 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6396 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6580 | SAD-SATAN-CLIENT.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
6580 | SAD-SATAN-CLIENT.exe | GET | 200 | 104.16.185.241:80 | http://icanhazip.com/ | unknown | — | — | shared |
5984 | WmiPrvSE.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5984 | WmiPrvSE.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5240 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 184.86.251.19:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1344 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
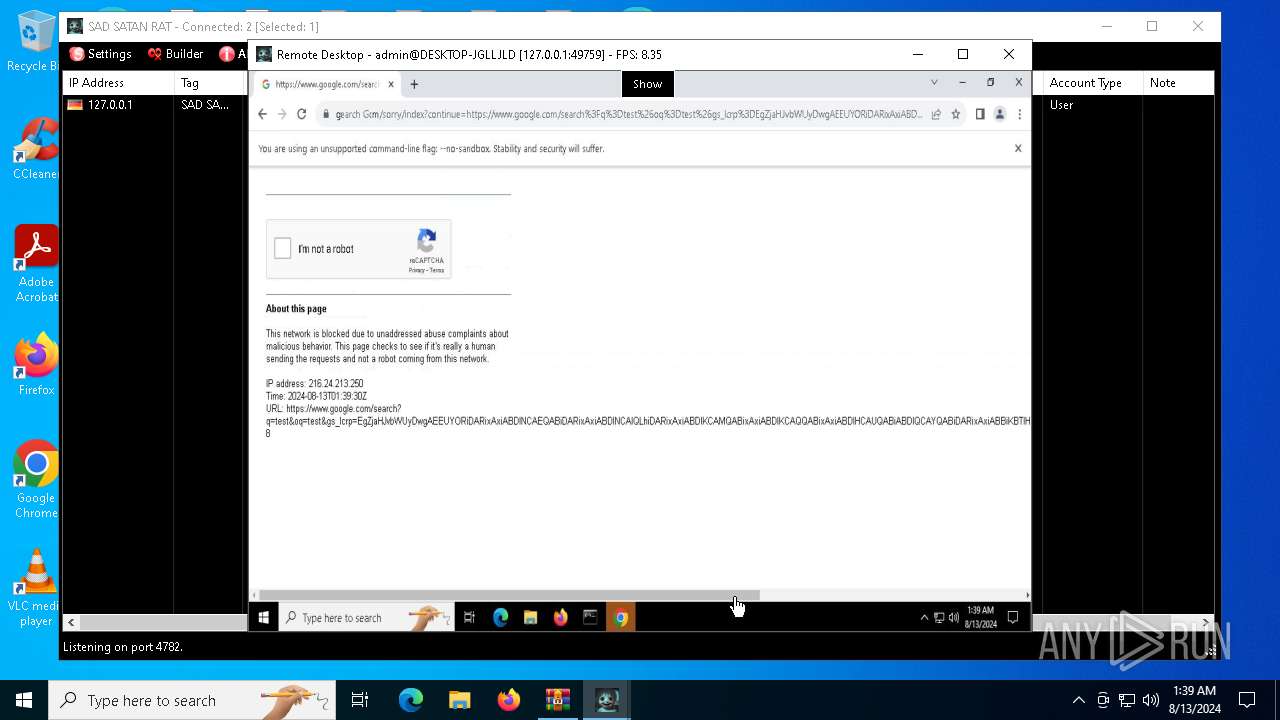
2256 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
6580 | SAD-SATAN-CLIENT.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
6580 | SAD-SATAN-CLIENT.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
6580 | SAD-SATAN-CLIENT.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6580 | SAD-SATAN-CLIENT.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6580 | SAD-SATAN-CLIENT.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
6580 | SAD-SATAN-CLIENT.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
Process | Message |
|---|---|
SAD-SATAN-CLIENT.exe | sad satan ratt!
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Google\Chrome\SecureFolder directory exists )
|
SAD-SATAN-CLIENT.exe | sad satan ratt!
|