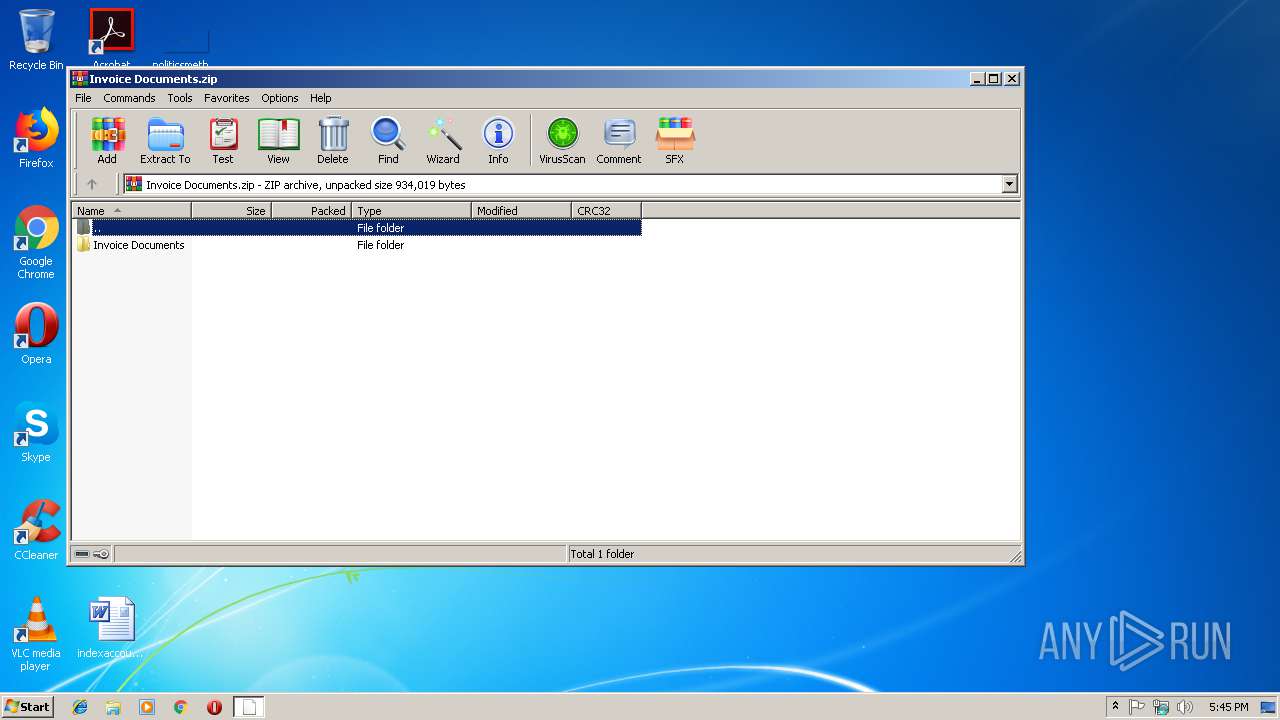
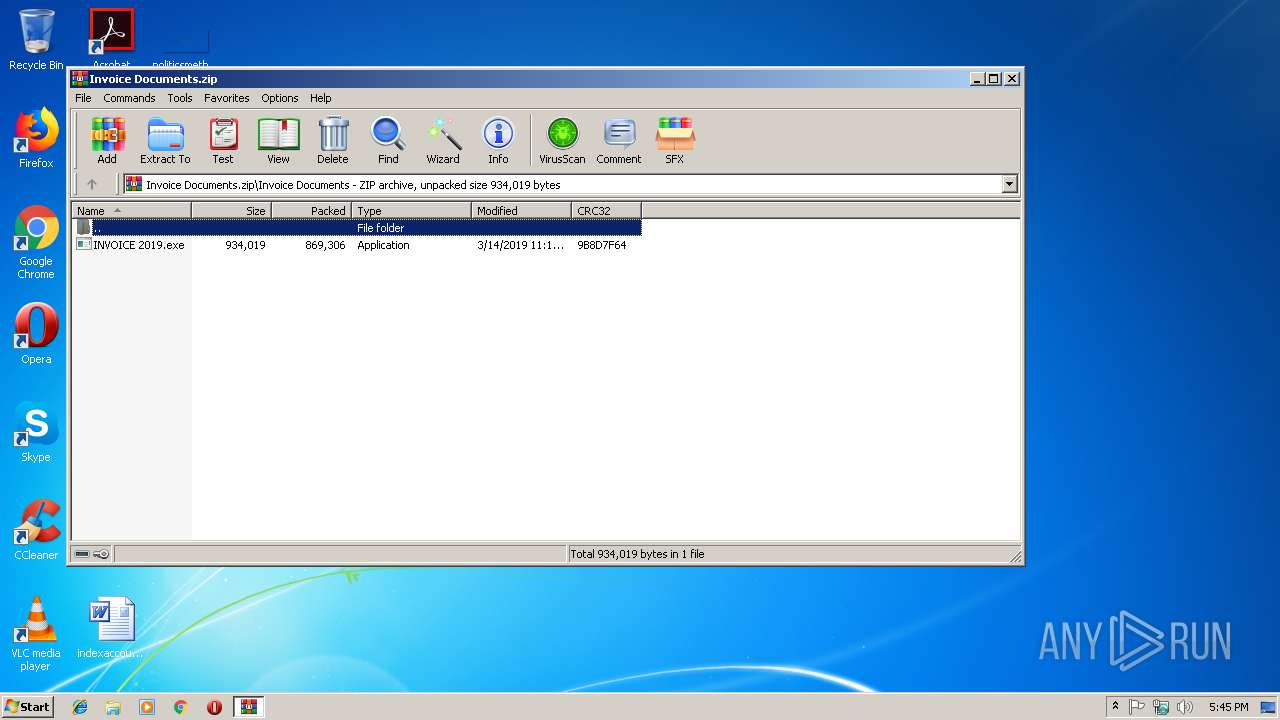
| File name: | Invoice Documents.zip |
| Full analysis: | https://app.any.run/tasks/41bc1870-0dde-4051-b8b6-58e451b7cf54 |
| Verdict: | Malicious activity |
| Threats: | NanoCore is a Remote Access Trojan or RAT. This malware is highly customizable with plugins which allow attackers to tailor its functionality to their needs. Nanocore is created with the .NET framework and it’s available for purchase for just $25 from its “official” website. |
| Analysis date: | March 14, 2019, 17:45:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 11435D732A81575AAC4C31AE11EF0FAF |
| SHA1: | A29D5C0F86CAC1A9BFE3386132B40F0C82E30D75 |
| SHA256: | 534294EC46C7E528A7E6AD708A2950E5EFC76C4B0CD69A7D93CE1C5074ABD378 |
| SSDEEP: | 24576:D+d+6KMSywevNdTvO7XIbv0YzhIPl3XUq49GIos:DAuMIMN1q4bv0Yzm93oV |
MALICIOUS
Application was dropped or rewritten from another process
- wgs.exe (PID: 2720)
- INVOICE 2019.exe (PID: 3180)
- wgs.exe (PID: 2600)
Changes the autorun value in the registry
- wgs.exe (PID: 2600)
- RegSvcs.exe (PID: 3736)
NanoCore was detected
- RegSvcs.exe (PID: 3736)
Connects to CnC server
- RegSvcs.exe (PID: 3736)
Actions looks like stealing of personal data
- vbc.exe (PID: 2884)
- vbc.exe (PID: 4064)
Stealing of credential data
- vbc.exe (PID: 2884)
SUSPICIOUS
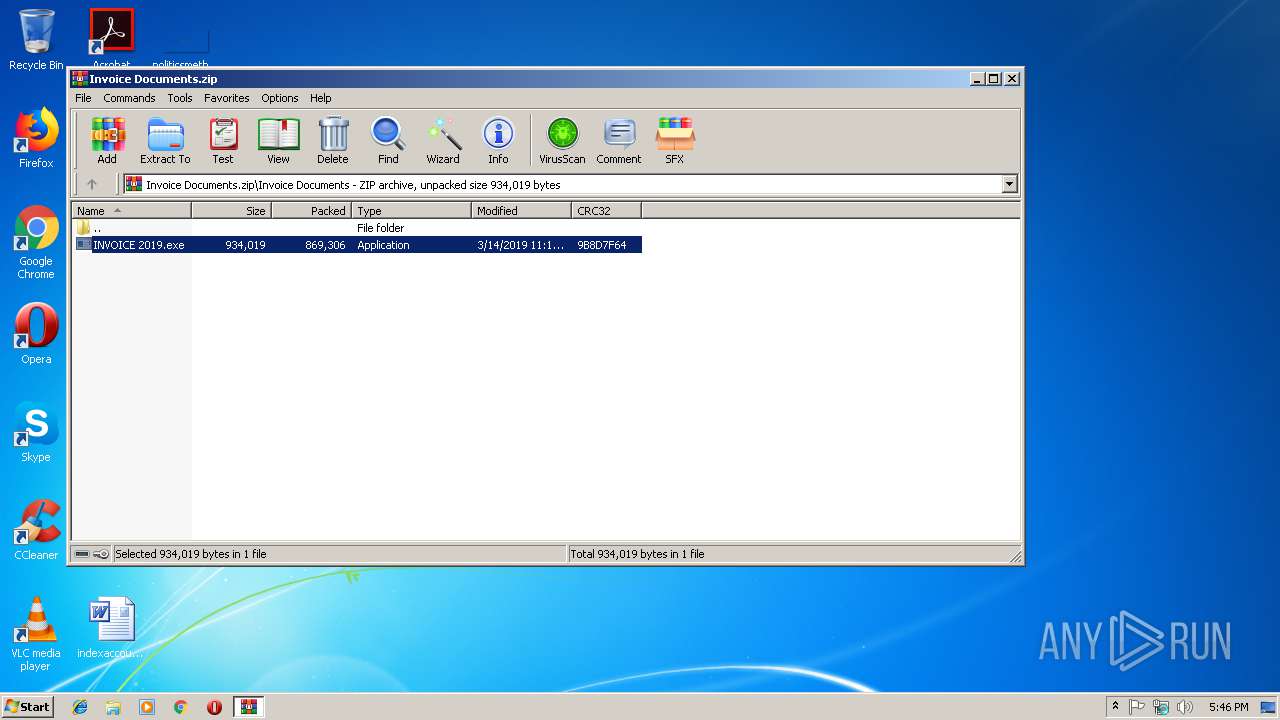
Executable content was dropped or overwritten
- INVOICE 2019.exe (PID: 3180)
- WinRAR.exe (PID: 3500)
Drop AutoIt3 executable file
- INVOICE 2019.exe (PID: 3180)
Application launched itself
- wgs.exe (PID: 2720)
Connects to unusual port
- RegSvcs.exe (PID: 3736)
Creates files in the user directory
- RegSvcs.exe (PID: 3736)
Executes scripts
- RegSvcs.exe (PID: 3736)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 2712)
INFO
Dropped object may contain Bitcoin addresses
- INVOICE 2019.exe (PID: 3180)
- wgs.exe (PID: 2720)
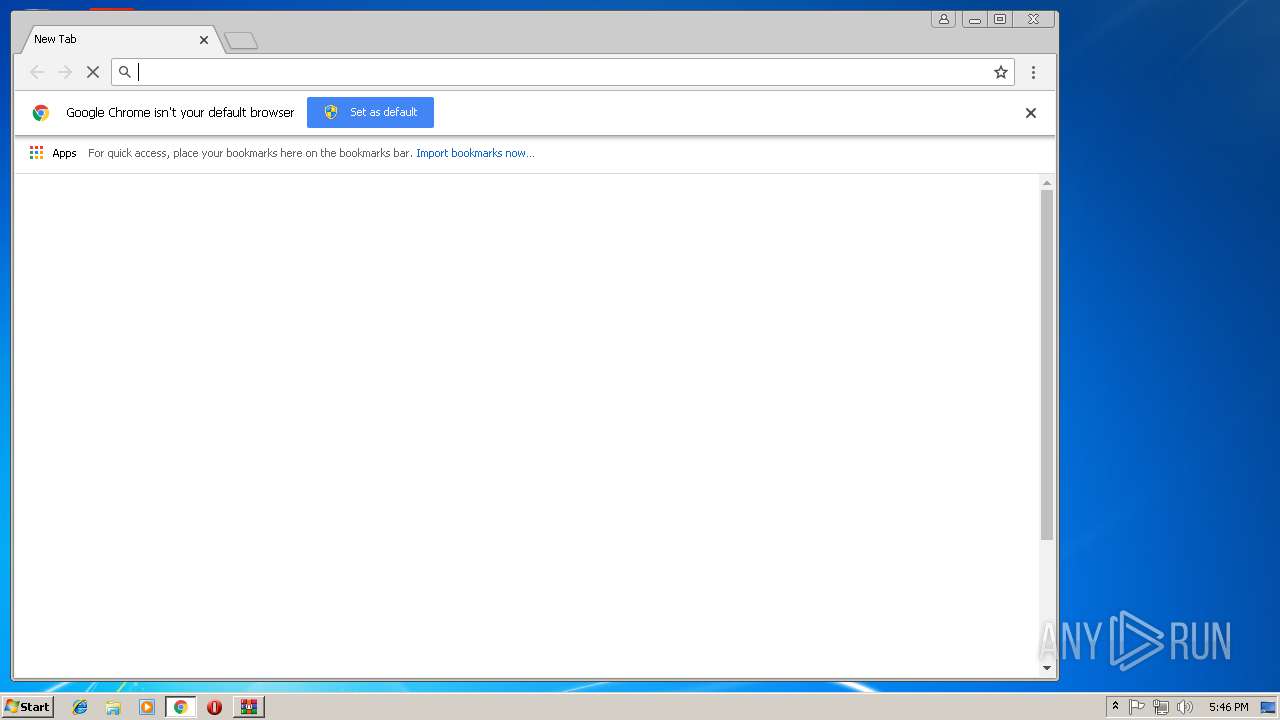
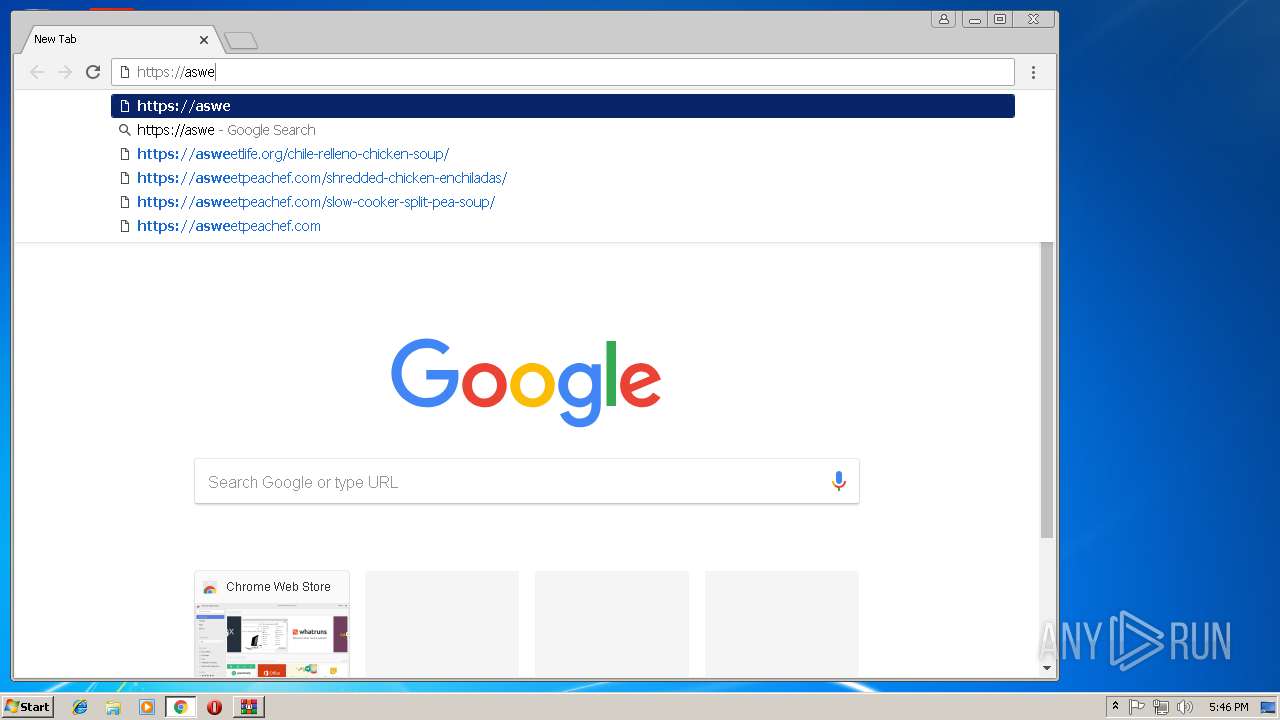
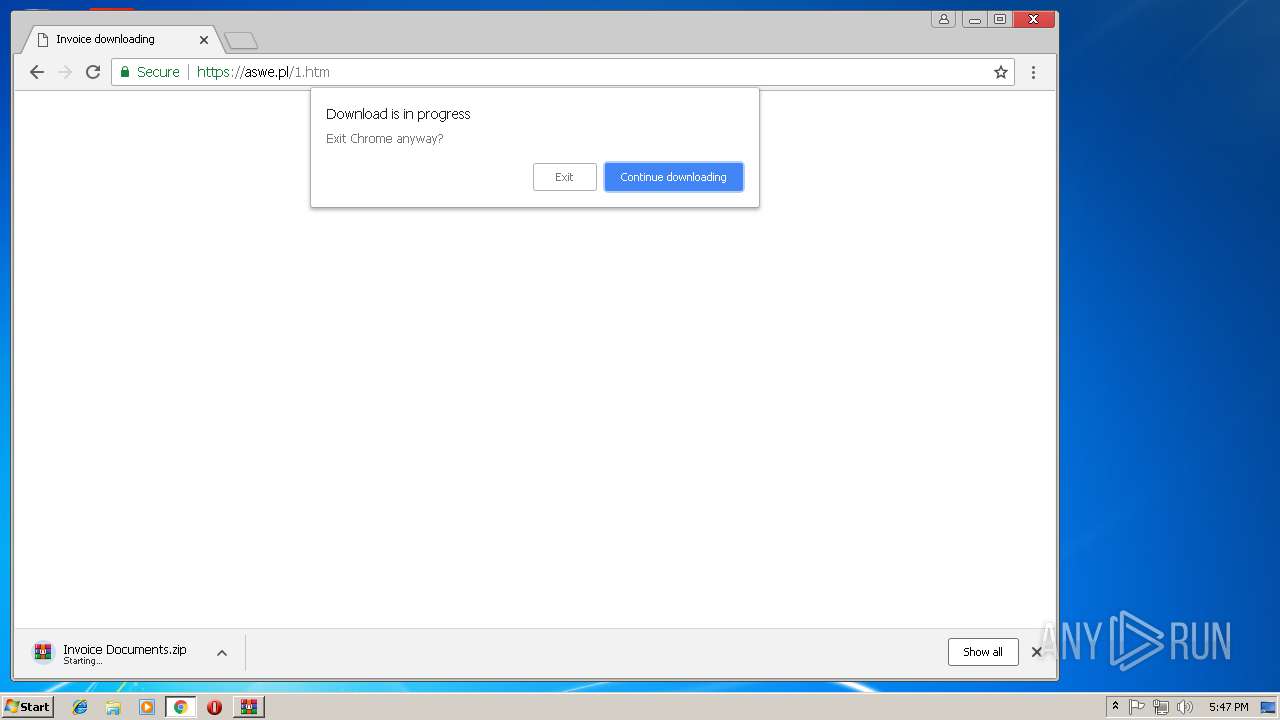
Application launched itself
- chrome.exe (PID: 2848)
Reads settings of System Certificates
- chrome.exe (PID: 2848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:14 11:15:19 |
| ZipCRC: | 0x9b8d7f64 |
| ZipCompressedSize: | 869306 |
| ZipUncompressedSize: | 934019 |
| ZipFileName: | Invoice Documents/INVOICE 2019.exe |
Total processes
60
Monitored processes
29
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1980 | "c:\windows\microsoft.net\framework\v4.0.30319\vbc.exe" /shtml "C:\Users\admin\AppData\Local\Temp\jehr3q5a.vdq" | c:\windows\microsoft.net\framework\v4.0.30319\vbc.exe | — | RegSvcs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 14.0.1055.0 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,2237042951565875675,12269565573791572058,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=CFB2E49423CA261CFBC49268937170AC --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,2237042951565875675,12269565573791572058,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7A18ACFB50D8658F6A0C285EEDF9F45E --mojo-platform-channel-handle=612 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,2237042951565875675,12269565573791572058,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=C090082786744B1D7F8CFAB169C491DE --mojo-platform-channel-handle=3956 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,2237042951565875675,12269565573791572058,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=B8F20C228C3C0C8E2704B9F5FE5E7544 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B8F20C228C3C0C8E2704B9F5FE5E7544 --renderer-client-id=10 --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2600 | C:\Users\admin\AppData\Local\Temp\23633053\wgs.exe C:\Users\admin\AppData\Local\Temp\23633053\NCOBY | C:\Users\admin\AppData\Local\Temp\23633053\wgs.exe | wgs.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 2620 | "c:\windows\microsoft.net\framework\v4.0.30319\vbc.exe" /shtml "C:\Users\admin\AppData\Local\Temp\jehr3q5a.vdq" | c:\windows\microsoft.net\framework\v4.0.30319\vbc.exe | — | RegSvcs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 14.0.1055.0 Modules
| |||||||||||||||
| 2712 | "c:\windows\microsoft.net\framework\v4.0.30319\vbc.exe" /shtml "C:\Users\admin\AppData\Local\Temp\iwn0ee3r.tc1" | c:\windows\microsoft.net\framework\v4.0.30319\vbc.exe | — | RegSvcs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.0.1055.0 Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Temp\23633053\wgs.exe" buw=lpj | C:\Users\admin\AppData\Local\Temp\23633053\wgs.exe | — | INVOICE 2019.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 370
Read events
1 282
Write events
84
Delete events
4
Modification events
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Invoice Documents.zip | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
69
Text files
122
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | INVOICE 2019.exe | C:\Users\admin\AppData\Local\Temp\23633053\kin.pdf | text | |
MD5:— | SHA256:— | |||
| 3180 | INVOICE 2019.exe | C:\Users\admin\AppData\Local\Temp\23633053\ven.jpg | text | |
MD5:— | SHA256:— | |||
| 3180 | INVOICE 2019.exe | C:\Users\admin\AppData\Local\Temp\23633053\cfs.ppt | text | |
MD5:— | SHA256:— | |||
| 3180 | INVOICE 2019.exe | C:\Users\admin\AppData\Local\Temp\23633053\xcq.dat | text | |
MD5:— | SHA256:— | |||
| 3180 | INVOICE 2019.exe | C:\Users\admin\AppData\Local\Temp\23633053\jwj.pdf | text | |
MD5:— | SHA256:— | |||
| 3180 | INVOICE 2019.exe | C:\Users\admin\AppData\Local\Temp\23633053\hme.mp4 | text | |
MD5:— | SHA256:— | |||
| 3180 | INVOICE 2019.exe | C:\Users\admin\AppData\Local\Temp\23633053\dcl.ico | text | |
MD5:— | SHA256:— | |||
| 3180 | INVOICE 2019.exe | C:\Users\admin\AppData\Local\Temp\23633053\pjh.txt | text | |
MD5:— | SHA256:— | |||
| 3180 | INVOICE 2019.exe | C:\Users\admin\AppData\Local\Temp\23633053\gfw.jpg | text | |
MD5:— | SHA256:— | |||
| 3180 | INVOICE 2019.exe | C:\Users\admin\AppData\Local\Temp\23633053\kuf.icm | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
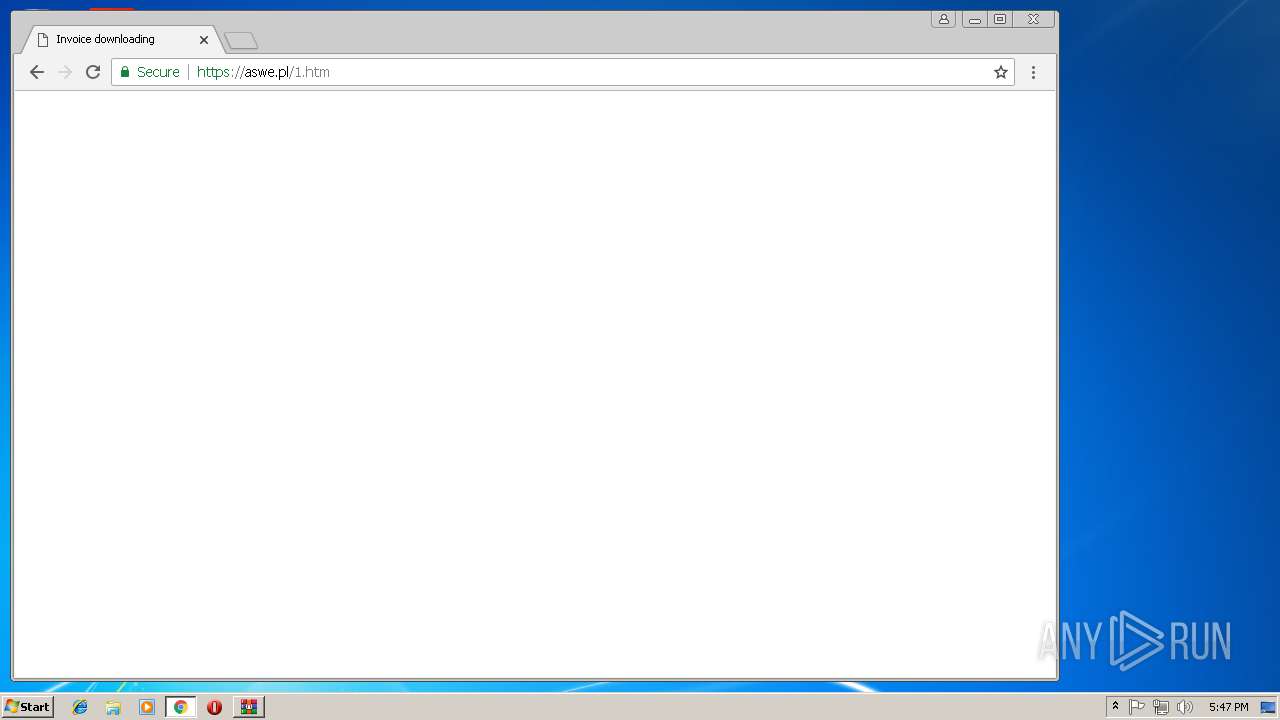
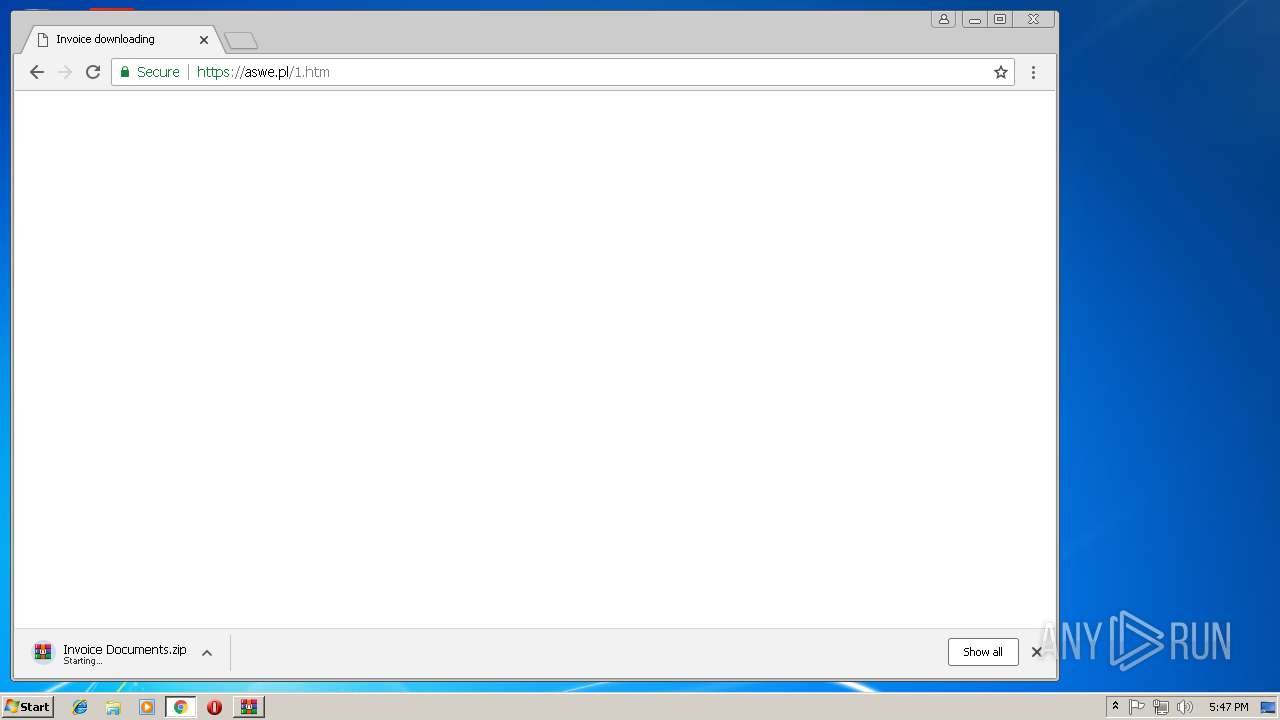
HTTP(S) requests
1
TCP/UDP connections
27
DNS requests
19
Threats
87
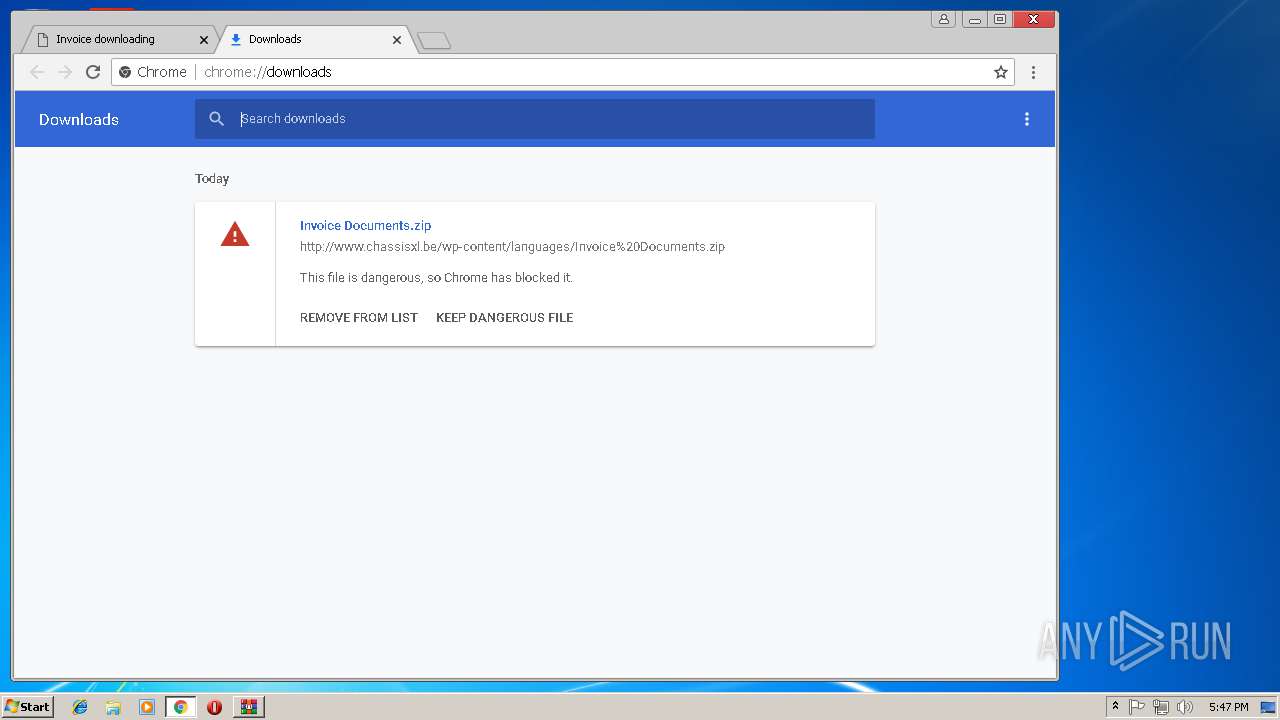
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2848 | chrome.exe | GET | 200 | 91.204.116.75:80 | http://www.chassisxl.be/wp-content/languages/Invoice%20Documents.zip | FR | compressed | 849 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3736 | RegSvcs.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
3736 | RegSvcs.exe | 5.2.79.228:5456 | likotrading.hopto.org | Liteserver VOF | NL | malicious |
2848 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.58.207.67:443 | www.google.de | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.58.207.46:443 | apis.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.22.35:443 | www.google.lv | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
likotrading.hopto.org |
| malicious |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.lv |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3736 | RegSvcs.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 60B |
3736 | RegSvcs.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
3736 | RegSvcs.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
3736 | RegSvcs.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
3736 | RegSvcs.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
3736 | RegSvcs.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
3736 | RegSvcs.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
3736 | RegSvcs.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
3736 | RegSvcs.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
3736 | RegSvcs.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
69 ETPRO signatures available at the full report