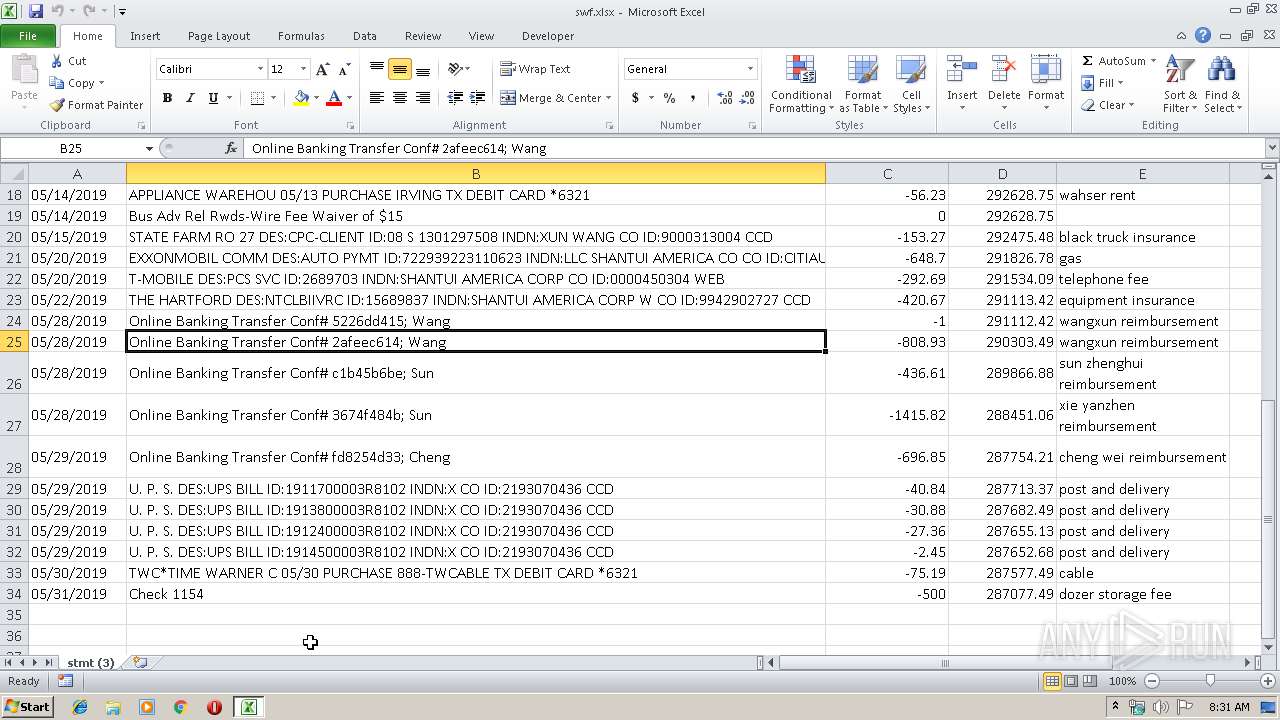
| File name: | swf.xlsx |
| Full analysis: | https://app.any.run/tasks/243eaa3e-12ed-4e6b-b4f6-d9181895b689 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | October 14, 2019, 07:30:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | Microsoft OOXML |
| MD5: | EFA6B94FAA282326C7FF7F82A6B9647C |
| SHA1: | 02F78C866203F3DDBC3A325890E55BBD0DE8BC6E |
| SHA256: | 532BEA8CBBE360B09DC64ED7299DF2242CBB349FED6D153B00CD59D88107FFE6 |
| SSDEEP: | 24576:p0bcdCmfypoX1IOoUYb1t8FQ5IYtDDfnzrDqCQMEDusL4fmHEXxVlcHaaaxb:WQdCm6qKpHQ8I23fzHK1DusL+W6aaJ |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2456)
Application was dropped or rewritten from another process
- avast.exe (PID: 4040)
- winzzehntbp.exe (PID: 3336)
FORMBOOK was detected
- explorer.exe (PID: 352)
- chkdsk.exe (PID: 2812)
- Firefox.exe (PID: 3232)
Changes the autorun value in the registry
- chkdsk.exe (PID: 2812)
Actions looks like stealing of personal data
- chkdsk.exe (PID: 2812)
Connects to CnC server
- explorer.exe (PID: 352)
Stealing of credential data
- chkdsk.exe (PID: 2812)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 2456)
- DllHost.exe (PID: 1972)
Creates files in the user directory
- EQNEDT32.EXE (PID: 2456)
- chkdsk.exe (PID: 2812)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 2456)
- explorer.exe (PID: 352)
- DllHost.exe (PID: 1972)
Starts CMD.EXE for commands execution
- chkdsk.exe (PID: 2812)
Loads DLL from Mozilla Firefox
- chkdsk.exe (PID: 2812)
Creates files in the program directory
- DllHost.exe (PID: 1972)
Uses NETSH.EXE for network configuration
- explorer.exe (PID: 352)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 352)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2148)
Manual execution by user
- chkdsk.exe (PID: 2812)
Reads the hosts file
- chkdsk.exe (PID: 2812)
Creates files in the user directory
- Firefox.exe (PID: 3232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:13 16:11:04 |
| ZipCRC: | 0xea720091 |
| ZipCompressedSize: | 396 |
| ZipUncompressedSize: | 1630 |
| ZipFileName: | [Content_Types].xml |
XML
| Application: | WPS 表格 |
|---|---|
| HeadingPairs: |
|
| TitlesOfParts: | stmt (3) |
| CreateDate: | 2019:06:02 21:01:48Z |
| ModifyDate: | 2019:06:02 21:04:29Z |
| KSOProductBuildVer: | 2052-1.1.0.1454 |
Total processes
46
Monitored processes
10
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1972 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2812 | "C:\Windows\System32\chkdsk.exe" | C:\Windows\System32\chkdsk.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Check Disk Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2872 | /c del "C:\Users\admin\AppData\Roaming\avast.exe" | C:\Windows\System32\cmd.exe | — | chkdsk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3232 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | chkdsk.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3336 | "C:\Program Files\Rndfxwnq8\winzzehntbp.exe" | C:\Program Files\Rndfxwnq8\winzzehntbp.exe | — | explorer.exe | |||||||||||
User: admin Company: IDM Computer Solutions, Inc. Integrity Level: MEDIUM Description: Msnews Dialup Scheduler Extra Usman Horizontal Exit code: 0 Version: 3.7.1.7 Modules
| |||||||||||||||
| 3472 | "C:\Windows\System32\netsh.exe" | C:\Windows\System32\netsh.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4040 | C:\Users\admin\AppData\Roaming\avast.exe | C:\Users\admin\AppData\Roaming\avast.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: IDM Computer Solutions, Inc. Integrity Level: MEDIUM Description: Msnews Dialup Scheduler Extra Usman Horizontal Exit code: 0 Version: 3.7.1.7 Modules
| |||||||||||||||
Total events
727
Read events
634
Write events
82
Delete events
11
Modification events
| (PID) Process: | (2148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | +%b |
Value: 2B25620064080000010000000000000000000000 | |||
| (PID) Process: | (2148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2148) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1330511897 | |||
Executable files
4
Suspicious files
78
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2148 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRA92B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2456 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\papx5[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2812 | chkdsk.exe | C:\Users\admin\AppData\Roaming\4L8P-DA7\4L8logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 4040 | avast.exe | C:\Users\admin\AppData\Local\Temp\D22F.tmp | binary | |
MD5:— | SHA256:— | |||
| 2456 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\avast.exe | executable | |
MD5:— | SHA256:— | |||
| 2812 | chkdsk.exe | C:\Users\admin\AppData\Roaming\4L8P-DA7\4L8logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 3336 | winzzehntbp.exe | C:\Users\admin\AppData\Local\Temp\116C.tmp | binary | |
MD5:— | SHA256:— | |||
| 1972 | DllHost.exe | C:\Program Files\Rndfxwnq8\winzzehntbp.exe | executable | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Rndfxwnq8\winzzehntbp.exe | executable | |
MD5:— | SHA256:— | |||
| 2812 | chkdsk.exe | C:\Users\admin\AppData\Roaming\4L8P-DA7\4L8logrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
18
DNS requests
14
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | explorer.exe | GET | — | 185.53.178.6:80 | http://www.drpayceter.com/zu3/?Bv1=/sj9YTBQupoVb2kQDEH6T8mqOC7vYjKDlSdQ2s+OzrrT69IBEBWaBYXomafxmCLKeYlPEA==&elN=xP3DUfwPwr | DE | — | — | malicious |
352 | explorer.exe | GET | 404 | 217.160.0.39:80 | http://www.ensemblelecenacle.com/zu3/?Bv1=4OtVXqshCSakqtNeErksus2BoZOOYCvedP2t+fSXL4maT/0zpHLv9adH1exkWMLZbKrqZw==&elN=xP3DUfwPwr | DE | html | 823 b | malicious |
352 | explorer.exe | GET | 404 | 80.237.133.145:80 | http://www.undercover-trainer.com/zu3/?Bv1=SLQyPbHhUjAxryS/t+yAH+VSXSvKgg521Y5cP6AUipcy+oMO148WKXxvw0hQogWiC7Xb1g==&elN=xP3DUfwPwr | DE | xml | 1000 b | malicious |
352 | explorer.exe | POST | 404 | 199.192.30.91:80 | http://www.kerxbin.com/zu3/ | US | html | 292 b | malicious |
352 | explorer.exe | POST | 404 | 199.192.30.91:80 | http://www.kerxbin.com/zu3/ | US | html | 292 b | malicious |
352 | explorer.exe | GET | 404 | 199.192.30.91:80 | http://www.kerxbin.com/zu3/?Bv1=ClTFAbWZtVgtkLaI9UyACQOFnw6u7mzeywWqevp5q9XC1tjZcoir/i38SalmHejiJ9m3nA==&elN=xP3DUfwPwr | US | html | 327 b | malicious |
352 | explorer.exe | POST | — | 217.160.0.39:80 | http://www.ensemblelecenacle.com/zu3/ | DE | — | — | malicious |
352 | explorer.exe | POST | — | 217.160.0.39:80 | http://www.ensemblelecenacle.com/zu3/ | DE | — | — | malicious |
352 | explorer.exe | POST | — | 217.160.0.39:80 | http://www.ensemblelecenacle.com/zu3/ | DE | — | — | malicious |
352 | explorer.exe | POST | — | 185.53.178.6:80 | http://www.drpayceter.com/zu3/ | DE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2456 | EQNEDT32.EXE | 5.101.174.39:443 | turacoenterprises.com | UK Dedicated Servers Limited | GB | malicious |
352 | explorer.exe | 80.237.133.145:80 | www.undercover-trainer.com | Host Europe GmbH | DE | malicious |
352 | explorer.exe | 109.241.247.86:80 | www.wlosniewska.com | Vectra S.A. | PL | malicious |
352 | explorer.exe | 199.192.30.91:80 | www.kerxbin.com | — | US | malicious |
352 | explorer.exe | 217.160.0.39:80 | www.ensemblelecenacle.com | 1&1 Internet SE | DE | malicious |
352 | explorer.exe | 185.53.178.6:80 | www.drpayceter.com | Team Internet AG | DE | malicious |
— | — | 109.241.247.86:80 | www.wlosniewska.com | Vectra S.A. | PL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
turacoenterprises.com |
| unknown |
www.arenaporn.win |
| unknown |
www.xp5q49.download |
| unknown |
www.qtcqh4.link |
| unknown |
www.zwktb.com |
| unknown |
www.gegaomeizy7.com |
| unknown |
www.keralasslcresults2018.com |
| unknown |
www.undercover-trainer.com |
| malicious |
www.kerxbin.com |
| malicious |
www.zhyft.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
13 ETPRO signatures available at the full report