| File name: | wextract.exe |
| Full analysis: | https://app.any.run/tasks/67ab52c6-4459-4ebe-b752-fca8f5a603de |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | October 27, 2023, 11:00:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 751B48D719E1FCA2BDA5F16480E8BC85 |
| SHA1: | 35FA46A82EDBA147FDD4A2751F7F1A7EA203A4D9 |
| SHA256: | 5304B4F24C9283FAB4E768233A26E2CB6A40CEDABBCDB711588FEEE0361692BF |
| SSDEEP: | 49152:tLnemIreQ6FvAUH5TemprSKoulT3lxc8iGDJHR+hz+MNorA4/8Z8bPlVBtUTNEcq:Jn2S5H5TeG2KoiTXc9GD9UHSrRe8Jrtl |
MALICIOUS
Drops the executable file immediately after the start
- UR4jf4pv.exe (PID: 2224)
- wextract.exe (PID: 1612)
- Cm6LD8uU.exe (PID: 2764)
- GU4bi5we.exe (PID: 3020)
Application was dropped or rewritten from another process
- UR4jf4pv.exe (PID: 2224)
- Cm6LD8uU.exe (PID: 2764)
- 2xV122Gv.exe (PID: 1256)
- GU4bi5we.exe (PID: 3020)
- 1ep95yZ9.exe (PID: 1136)
- 3Bz6tq00.exe (PID: 2864)
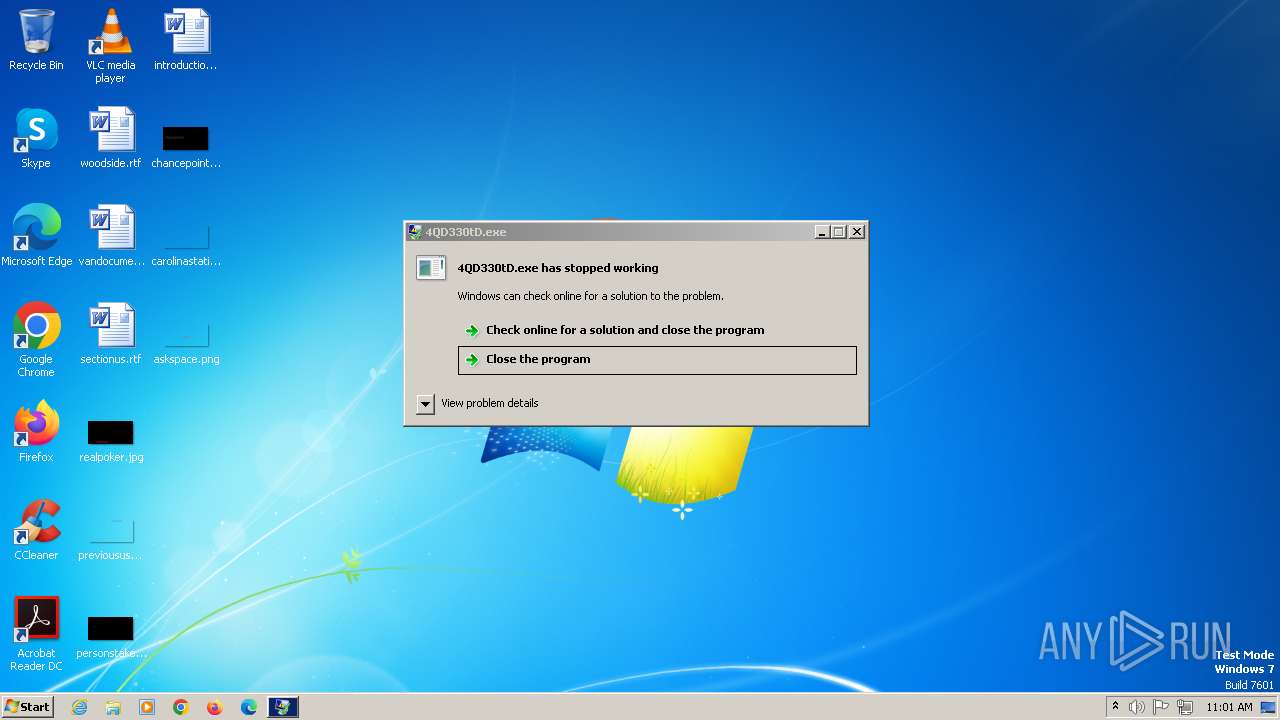
- 4QD330tD.exe (PID: 2464)
REDLINE has been detected (SURICATA)
- 2xV122Gv.exe (PID: 1256)
Connects to the CnC server
- 2xV122Gv.exe (PID: 1256)
- AppLaunch.exe (PID: 3012)
STEALC has been detected (SURICATA)
- AppLaunch.exe (PID: 3012)
Steals credentials from Web Browsers
- 2xV122Gv.exe (PID: 1256)
Actions looks like stealing of personal data
- 2xV122Gv.exe (PID: 1256)
SUSPICIOUS
Process drops legitimate windows executable
- wextract.exe (PID: 1612)
- UR4jf4pv.exe (PID: 2224)
- Cm6LD8uU.exe (PID: 2764)
Reads the Internet Settings
- AppLaunch.exe (PID: 3012)
Connects to unusual port
- 2xV122Gv.exe (PID: 1256)
Reads browser cookies
- 2xV122Gv.exe (PID: 1256)
Searches for installed software
- 2xV122Gv.exe (PID: 1256)
Connects to the server without a host name
- AppLaunch.exe (PID: 3012)
INFO
Create files in a temporary directory
- wextract.exe (PID: 1612)
- UR4jf4pv.exe (PID: 2224)
- Cm6LD8uU.exe (PID: 2764)
- GU4bi5we.exe (PID: 3020)
Checks supported languages
- wextract.exe (PID: 1612)
- UR4jf4pv.exe (PID: 2224)
- Cm6LD8uU.exe (PID: 2764)
- GU4bi5we.exe (PID: 3020)
- 1ep95yZ9.exe (PID: 1136)
- AppLaunch.exe (PID: 3012)
- 2xV122Gv.exe (PID: 1256)
- 3Bz6tq00.exe (PID: 2864)
- 4QD330tD.exe (PID: 2464)
Checks proxy server information
- AppLaunch.exe (PID: 3012)
Reads the computer name
- AppLaunch.exe (PID: 3012)
- 2xV122Gv.exe (PID: 1256)
Reads the machine GUID from the registry
- 2xV122Gv.exe (PID: 1256)
- AppLaunch.exe (PID: 3012)
Reads Environment values
- 2xV122Gv.exe (PID: 1256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:05:25 00:49:06+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 25600 |
| InitializedDataSize: | 1363456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a60 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.17763.1 |
| ProductVersionNumber: | 11.0.17763.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.17763.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.17763.1 |
Total processes
41
Monitored processes
9
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1136 | C:\Users\admin\AppData\Local\Temp\IXP003.TMP\1ep95yZ9.exe | C:\Users\admin\AppData\Local\Temp\IXP003.TMP\1ep95yZ9.exe | — | GU4bi5we.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1256 | C:\Users\admin\AppData\Local\Temp\IXP003.TMP\2xV122Gv.exe | C:\Users\admin\AppData\Local\Temp\IXP003.TMP\2xV122Gv.exe | GU4bi5we.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Fps boost Exit code: 0 Version: 15.9.1.22 Modules
| |||||||||||||||
| 1612 | "C:\Users\admin\AppData\Local\Temp\wextract.exe" | C:\Users\admin\AppData\Local\Temp\wextract.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2224 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\UR4jf4pv.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\UR4jf4pv.exe | — | wextract.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2464 | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\4QD330tD.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\4QD330tD.exe | UR4jf4pv.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2764 | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\Cm6LD8uU.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\Cm6LD8uU.exe | — | UR4jf4pv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2864 | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\3Bz6tq00.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\3Bz6tq00.exe | — | Cm6LD8uU.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3012 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe | 1ep95yZ9.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET ClickOnce Launch Utility Exit code: 1 Version: 4.7.2558.0 built by: NET471REL1 Modules
| |||||||||||||||
| 3020 | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\GU4bi5we.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\GU4bi5we.exe | — | Cm6LD8uU.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
797
Read events
793
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3012) AppLaunch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3012) AppLaunch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3012) AppLaunch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3012) AppLaunch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000C1000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
8
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1612 | wextract.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\UR4jf4pv.exe | executable | |
MD5:0679464F3E08D4566F8139CEE4D39D3E | SHA256:69AF53170DD9D057961C7B6C2651925EA1E141BD137DC353F827D154D4FDEF6E | |||
| 2224 | UR4jf4pv.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\4QD330tD.exe | executable | |
MD5:331AC8C8594C4C00AE89548CB001787A | SHA256:7D88595FCFDDA1BC273A4159EF62F6624C1AA410E078607258AF33CFDD928425 | |||
| 3020 | GU4bi5we.exe | C:\Users\admin\AppData\Local\Temp\IXP003.TMP\1ep95yZ9.exe | executable | |
MD5:1C4D409E35DD87E1BD3B8A77B8C3000D | SHA256:F901B9504F6098DB96DCEFE5D83298F85CDEDD326D1C3E30AECACD9A968D8079 | |||
| 1612 | wextract.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\5Tl19rh.exe | executable | |
MD5:BC86CA064DD470669C0DD1B020E4C67E | SHA256:6C6F3A37EECB15C7558FAF5D6DB535E46ECC1C9DFB26C00FE3CDE00211545620 | |||
| 2764 | Cm6LD8uU.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\GU4bi5we.exe | executable | |
MD5:7288969905779598014E022E75AF89E8 | SHA256:19EDBA3D4C9B60F59471DCACEAC19C323B0998BD7389E5AD5A9C344955C63DF3 | |||
| 2764 | Cm6LD8uU.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\3Bz6tq00.exe | executable | |
MD5:57B875DD6C1ACFB1F4F03DB1FF643AB4 | SHA256:B937C1568455D6195210871F74CAF02756280CEF1E4B71724C57FDA76081BAEE | |||
| 3020 | GU4bi5we.exe | C:\Users\admin\AppData\Local\Temp\IXP003.TMP\2xV122Gv.exe | executable | |
MD5:1408C7DD4A3A4F8CE30ABC66A3E6A199 | SHA256:88FDFE1871031C0B99C274A6ECD25DB501A4E8DDCD80EB52199C8FA8572C32A0 | |||
| 2224 | UR4jf4pv.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\Cm6LD8uU.exe | executable | |
MD5:AA009FE6F2AE327053E304109922920E | SHA256:290D55852C6A2BBA5D293A35593DBE449E4B5A7291C75FD13FE80F08017DDD4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
0
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3012 | AppLaunch.exe | POST | 200 | 193.233.255.73:80 | http://193.233.255.73/loghub/master | unknown | text | 8 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3012 | AppLaunch.exe | 193.233.255.73:80 | — | LLC Baxet | RU | malicious |
1256 | 2xV122Gv.exe | 77.91.124.86:19084 | — | Foton Telecom CJSC | RU | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
1256 | 2xV122Gv.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
1256 | 2xV122Gv.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1256 | 2xV122Gv.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer Related (MC-NMF Authorization) |
1256 | 2xV122Gv.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC - Id1Response |
1256 | 2xV122Gv.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1256 | 2xV122Gv.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1256 | 2xV122Gv.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1256 | 2xV122Gv.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1256 | 2xV122Gv.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1256 | 2xV122Gv.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |