| File name: | 20969e312596ebe708c3729f09d38945.rar |
| Full analysis: | https://app.any.run/tasks/640a97a8-5c0e-4ff9-89d4-6a370e6b224e |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | June 12, 2019, 04:37:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 20969E312596EBE708C3729F09D38945 |
| SHA1: | B446808530CCD9D006247C785B95E5ECA27C718D |
| SHA256: | 5272C571C9FDA901FEAC83808C572318718D02008DD7BD905411F81DEEC612F1 |
| SSDEEP: | 12288:1hG8oFcK0ioI8Ks4gryzWJbaAi5Ym7bGHBndAyg1lyNTMNt3IQmb:vG8oqpivA4waVYm7bGhCvdJLy |
MALICIOUS
Application was dropped or rewritten from another process
- INV-2003493202-201906.exe (PID: 3008)
Detected Hawkeye Keylogger
- RegAsm.exe (PID: 3032)
Actions looks like stealing of personal data
- vbc.exe (PID: 3816)
- vbc.exe (PID: 3596)
Stealing of credential data
- vbc.exe (PID: 3816)
- vbc.exe (PID: 3596)
SUSPICIOUS
Starts CMD.EXE for commands execution
- INV-2003493202-201906.exe (PID: 3008)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2940)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 2356)
Executes scripts
- RegAsm.exe (PID: 3032)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3816)
INFO
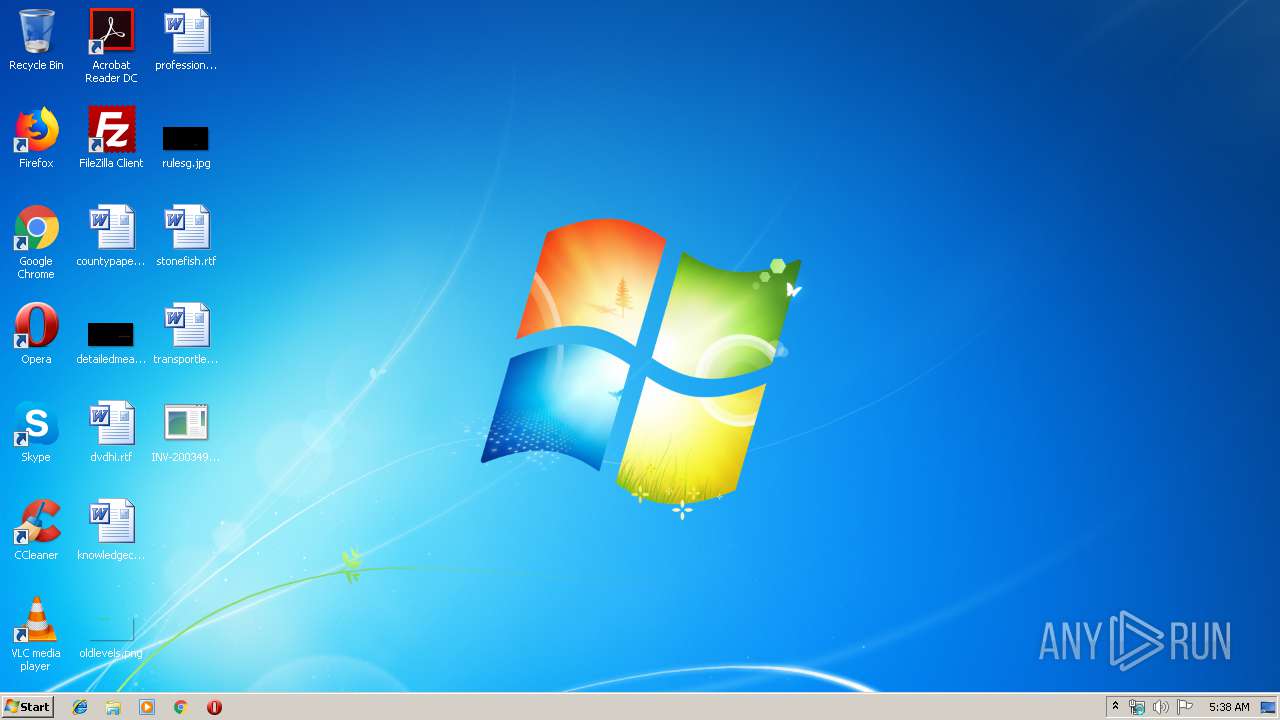
Manual execution by user
- INV-2003493202-201906.exe (PID: 3008)
- WINWORD.EXE (PID: 3180)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3180)
Creates files in the user directory
- WINWORD.EXE (PID: 3180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
43
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2356 | "C:\Windows\System32\cmd.exe" /C choice /C Y /N /D Y /T 3 & Del "C:\Users\admin\Desktop\INV-2003493202-201906.exe" | C:\Windows\System32\cmd.exe | — | INV-2003493202-201906.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
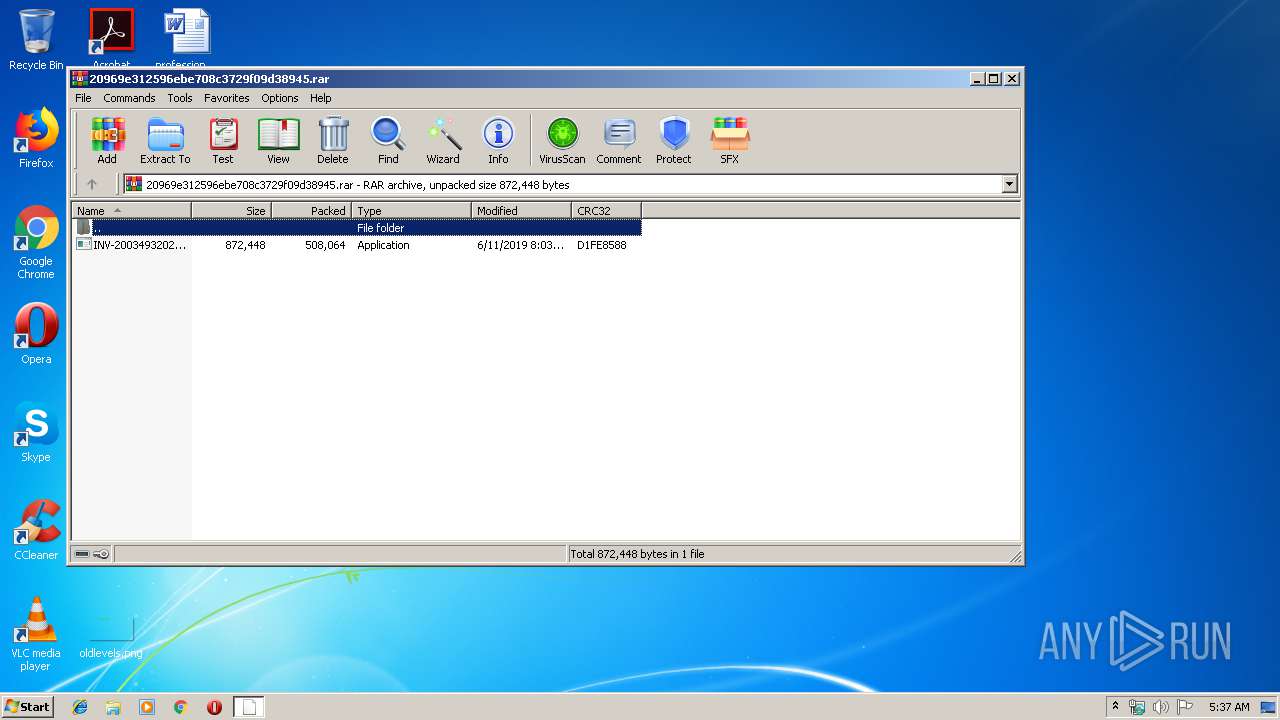
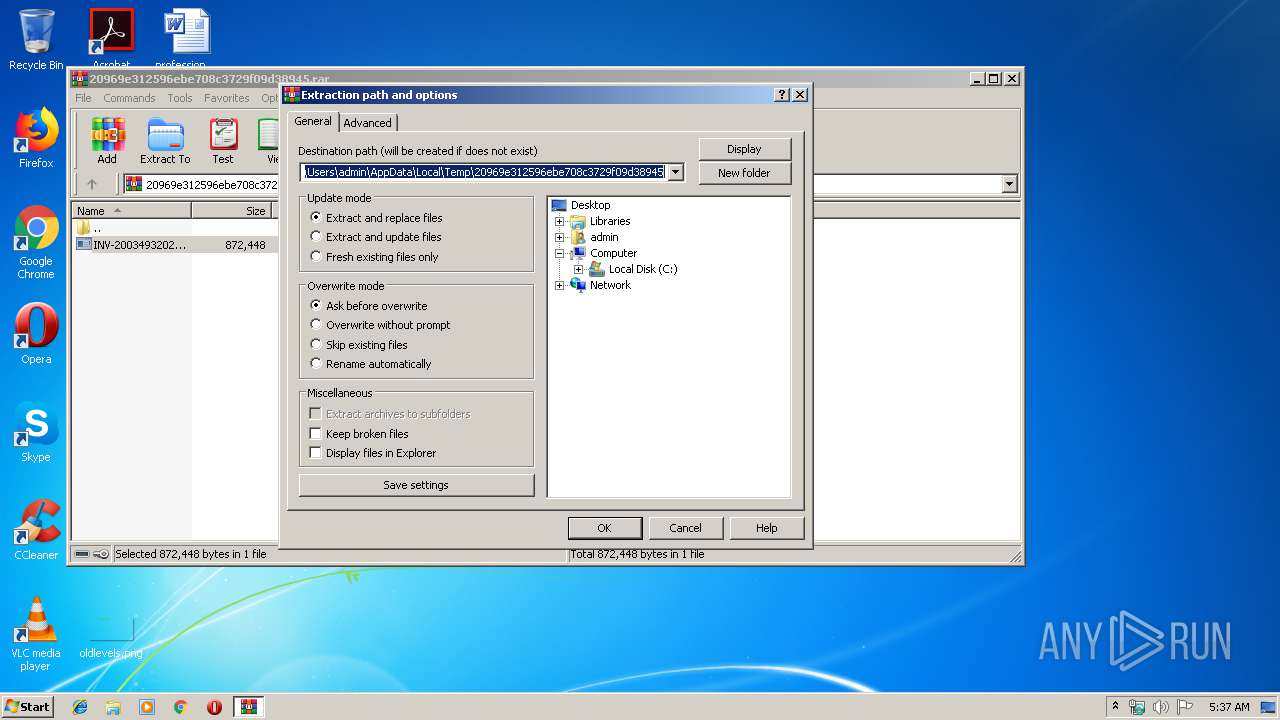
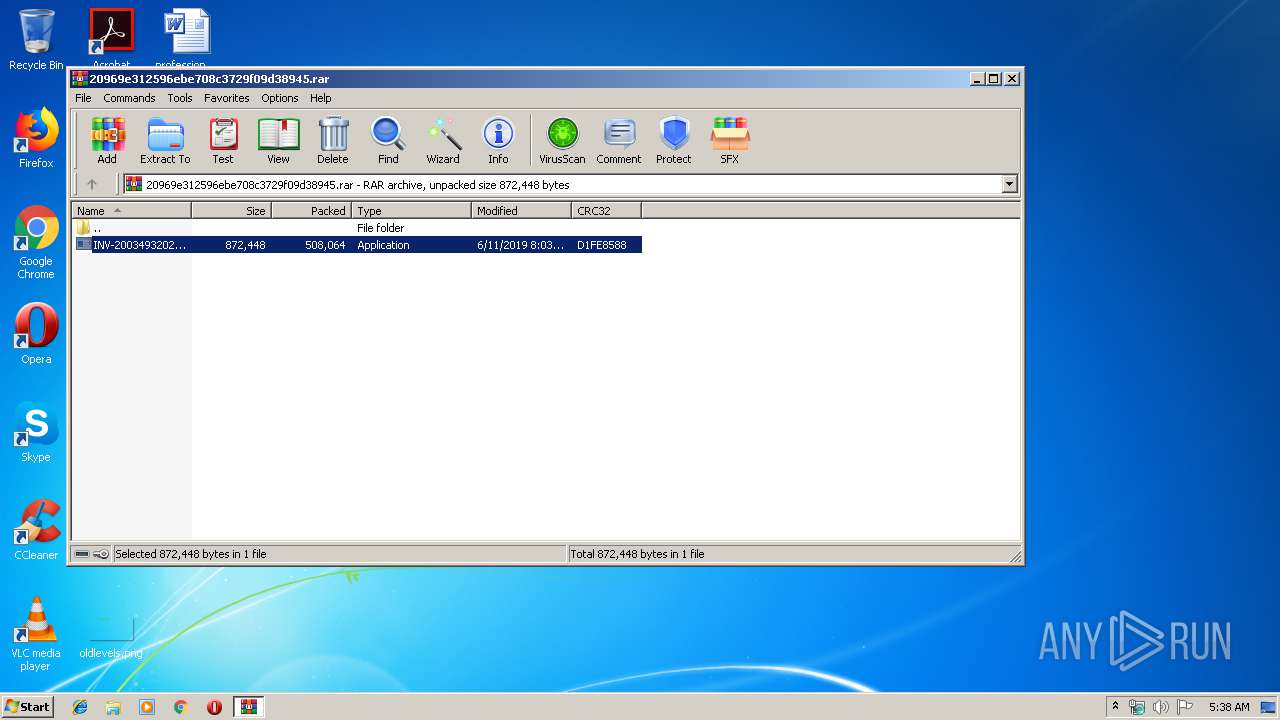
| 2940 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\20969e312596ebe708c3729f09d38945.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2992 | choice /C Y /N /D Y /T 3 | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3008 | "C:\Users\admin\Desktop\INV-2003493202-201906.exe" | C:\Users\admin\Desktop\INV-2003493202-201906.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3032 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | INV-2003493202-201906.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3180 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\stonefish.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3596 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpC4E1.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3816 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp9813.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
Total events
1 138
Read events
1 057
Write events
75
Delete events
6
Modification events
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\20969e312596ebe708c3729f09d38945.rar | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
1
Suspicious files
0
Text files
5
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAAB1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3180 | WINWORD.EXE | C:\Users\admin\Desktop\~$onefish.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\INV-2003493202-201906.exe | executable | |
MD5:— | SHA256:— | |||
| 3180 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\stonefish.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3180 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3180 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3032 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\25291068-43af-3e16-50f6-5889d9ce7904 | text | |
MD5:454353131947D1483FF5470107478978 | SHA256:2DF94DC1C58E952A1EBD1AE1185A291A8A573982CA90EC1BBB87B81126002668 | |||
| 3596 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmpC4E1.tmp | text | |
MD5:7FB9A9AD0FD9B1E0108ED71FBB276048 | SHA256:7D63C301317E144B0133A72250AE2D8E09AF65A92E6A807EC58A71939FE530A9 | |||
| 3816 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmp9813.tmp | text | |
MD5:3E1E093DCCE32C716267A28292E0EE27 | SHA256:56285445424AD06DC043154819B5BDABAA7C26F5779CA3E37E08424ED9926CB8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3032 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 14 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3032 | RegAsm.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
3032 | RegAsm.exe | 202.143.99.153:587 | mail.gattibufood.com | CtrlS Datacenters Ltd. | IN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bot.whatismyipaddress.com |
| shared |
mail.gattibufood.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3032 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spy.HawkEye IP Check |
2 ETPRO signatures available at the full report