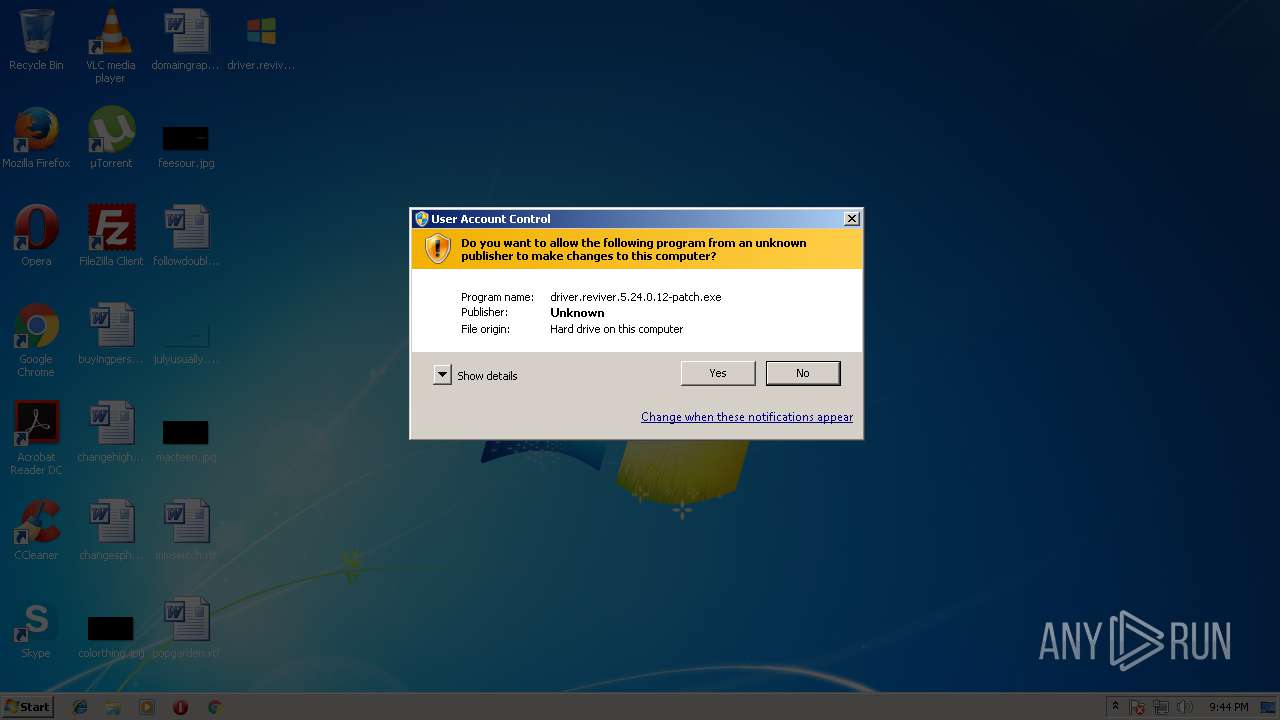
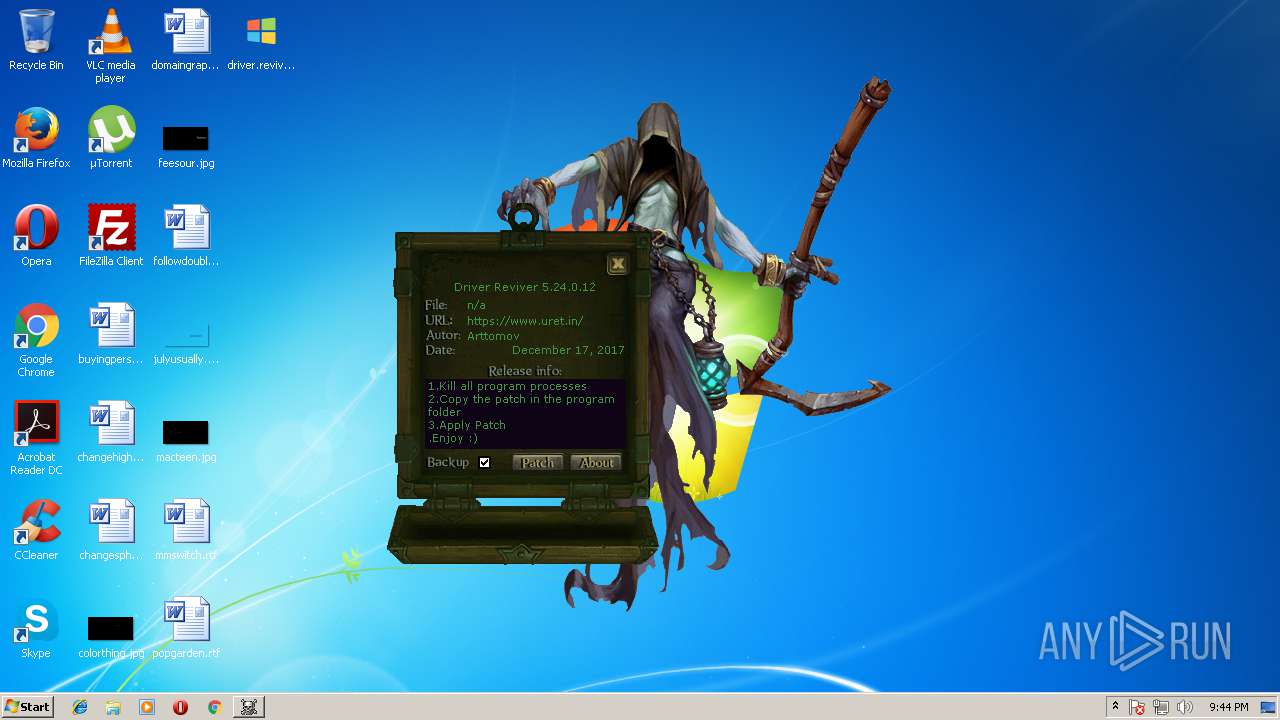
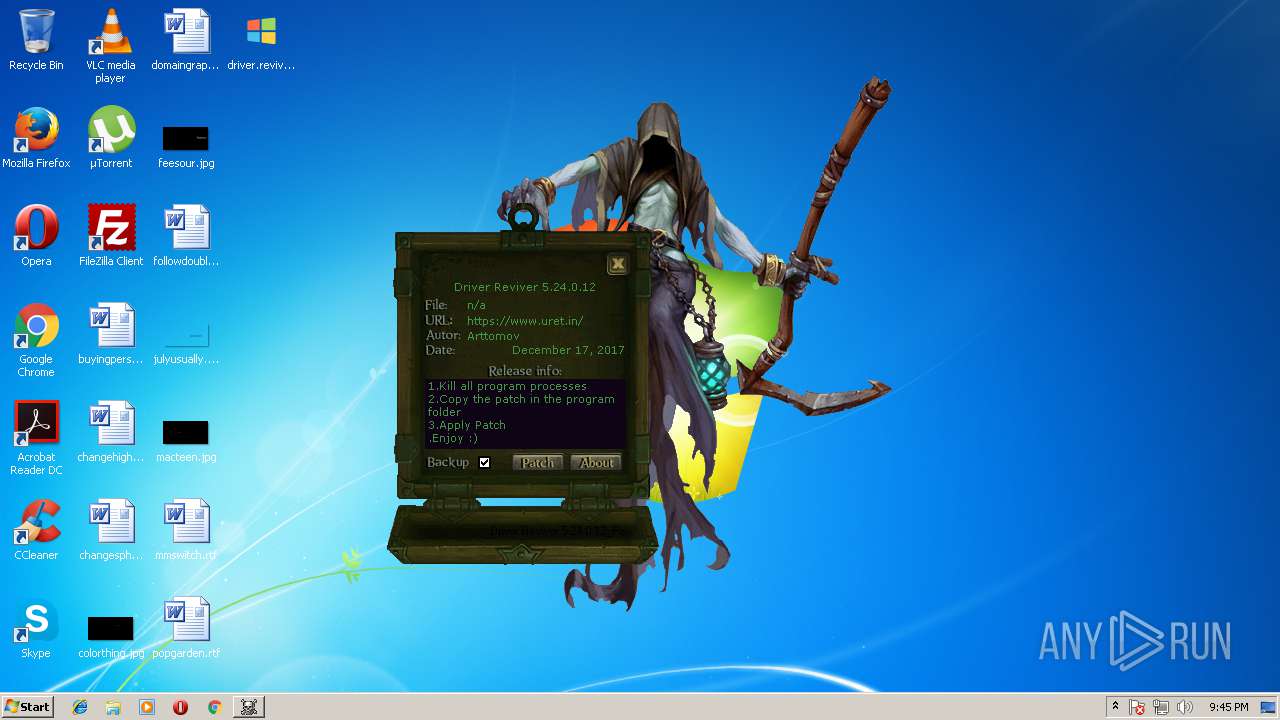
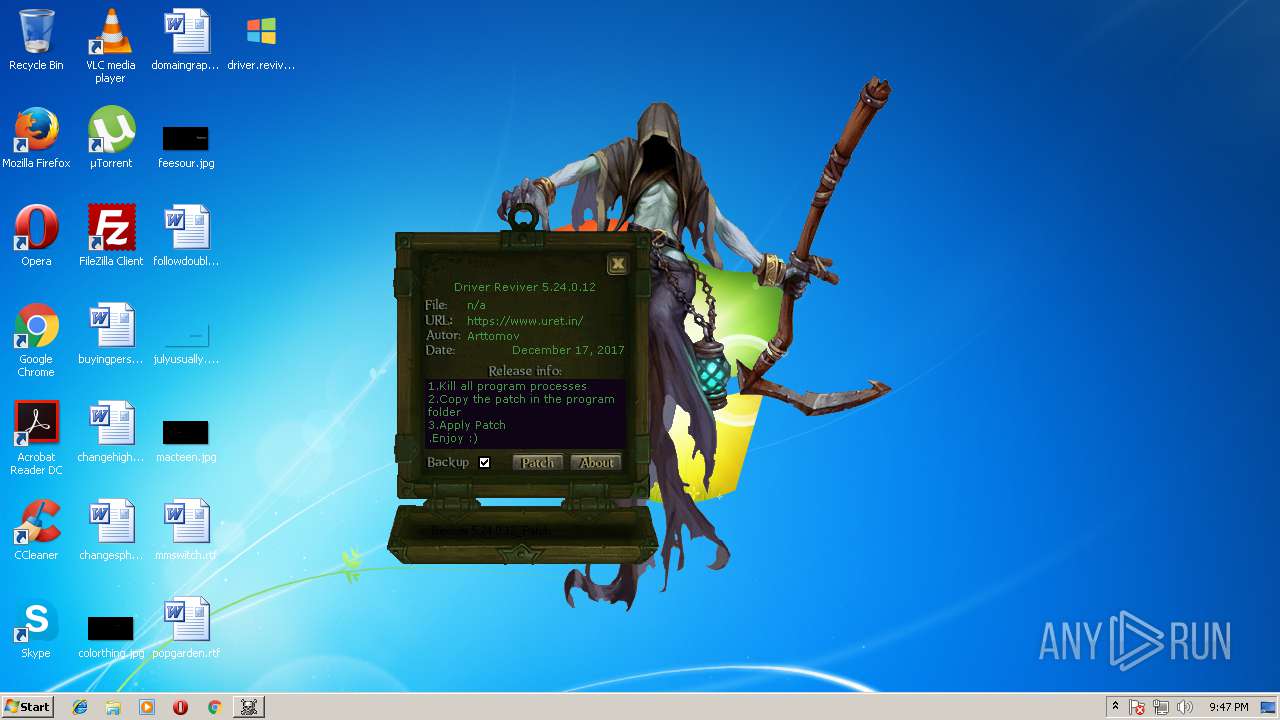
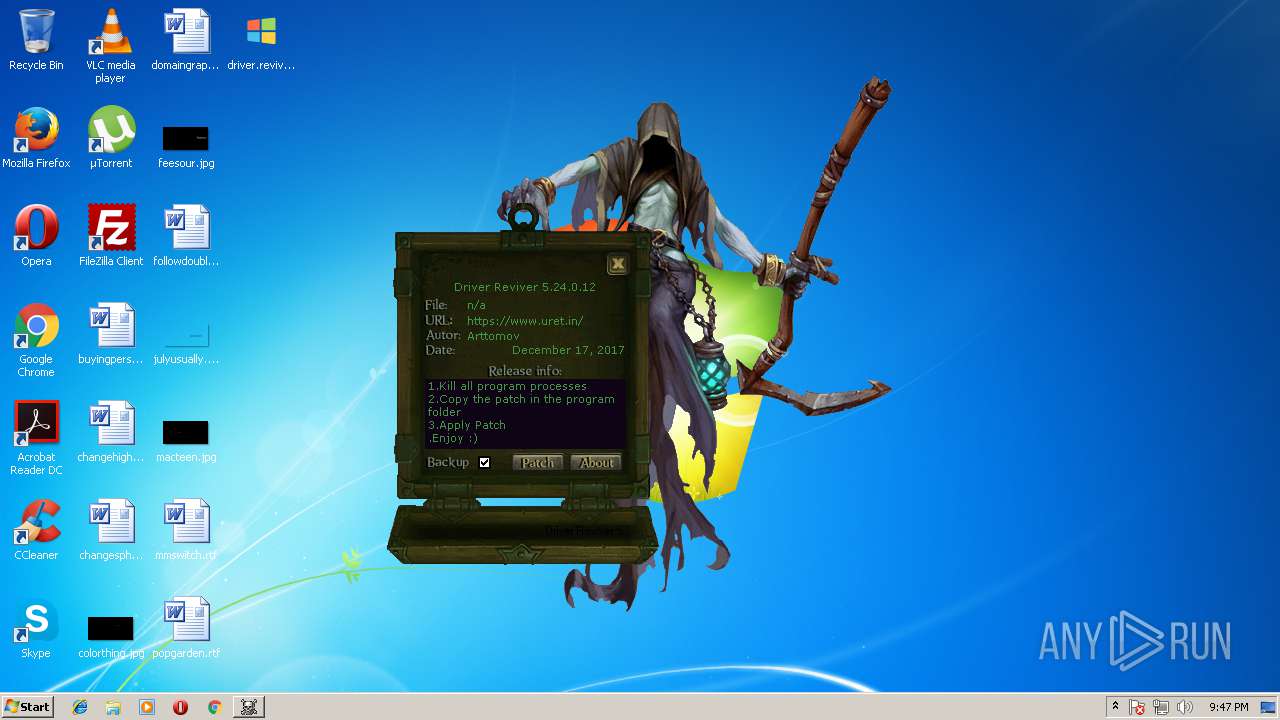
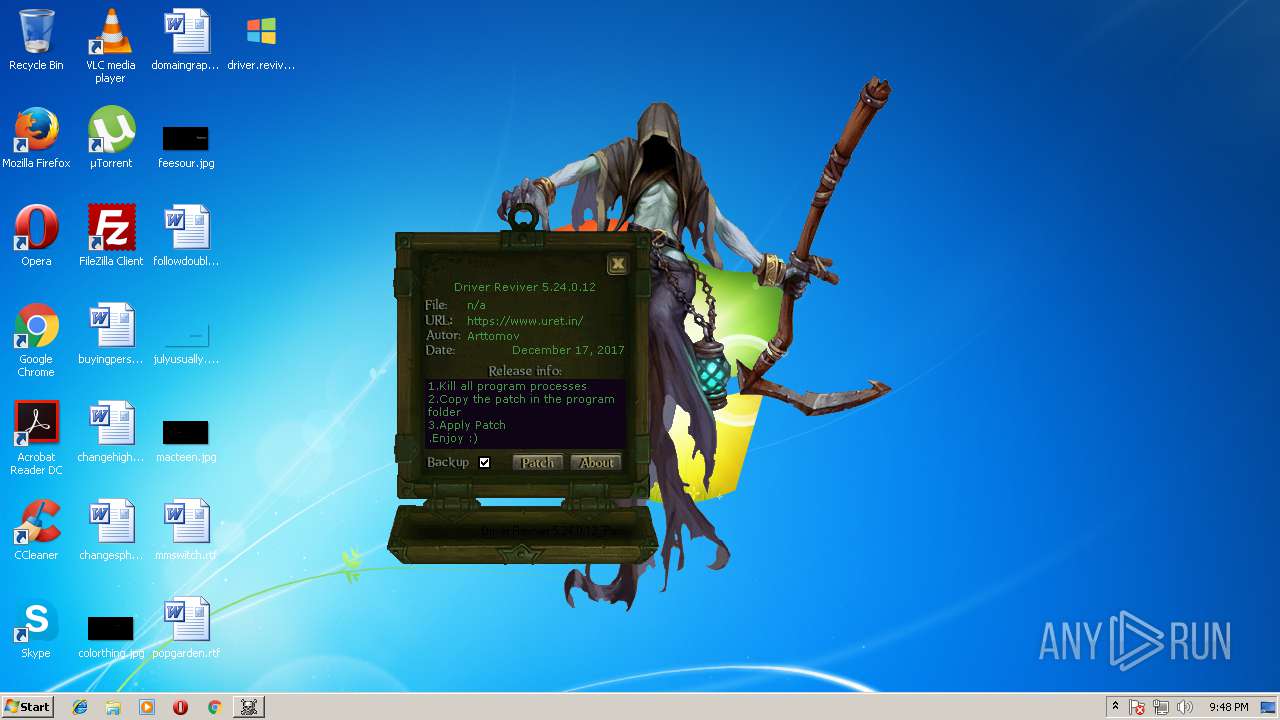
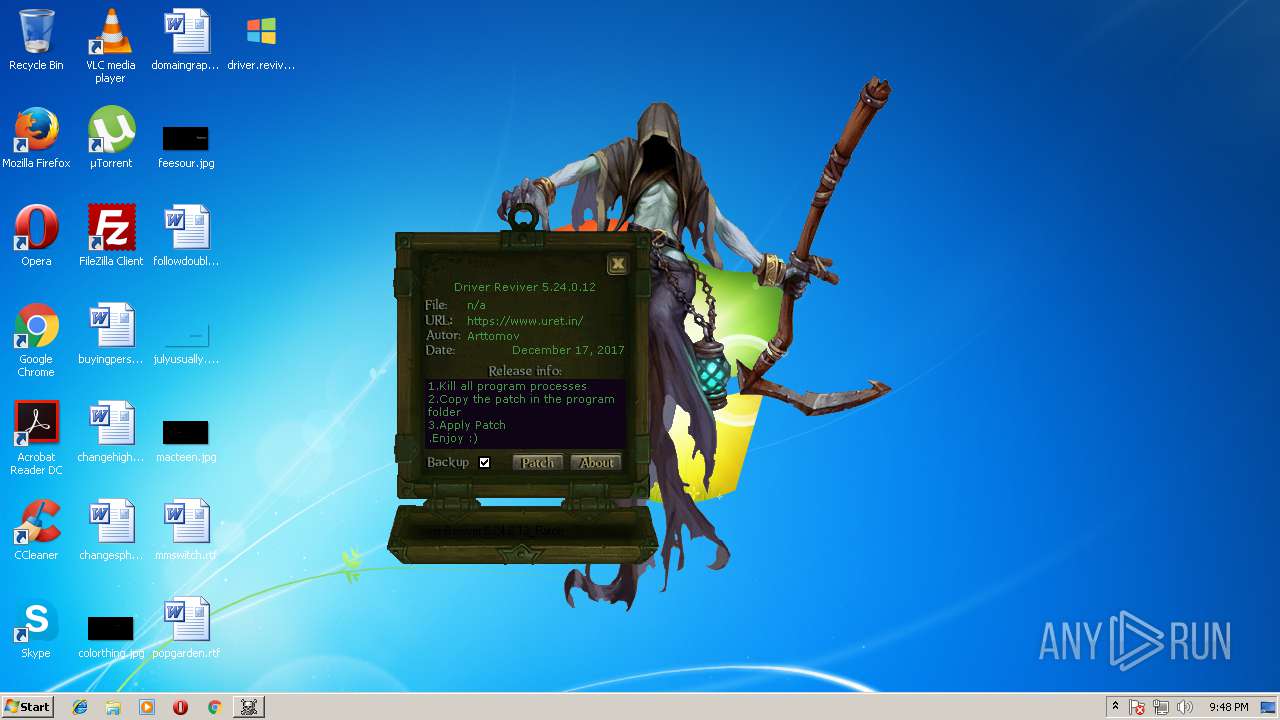
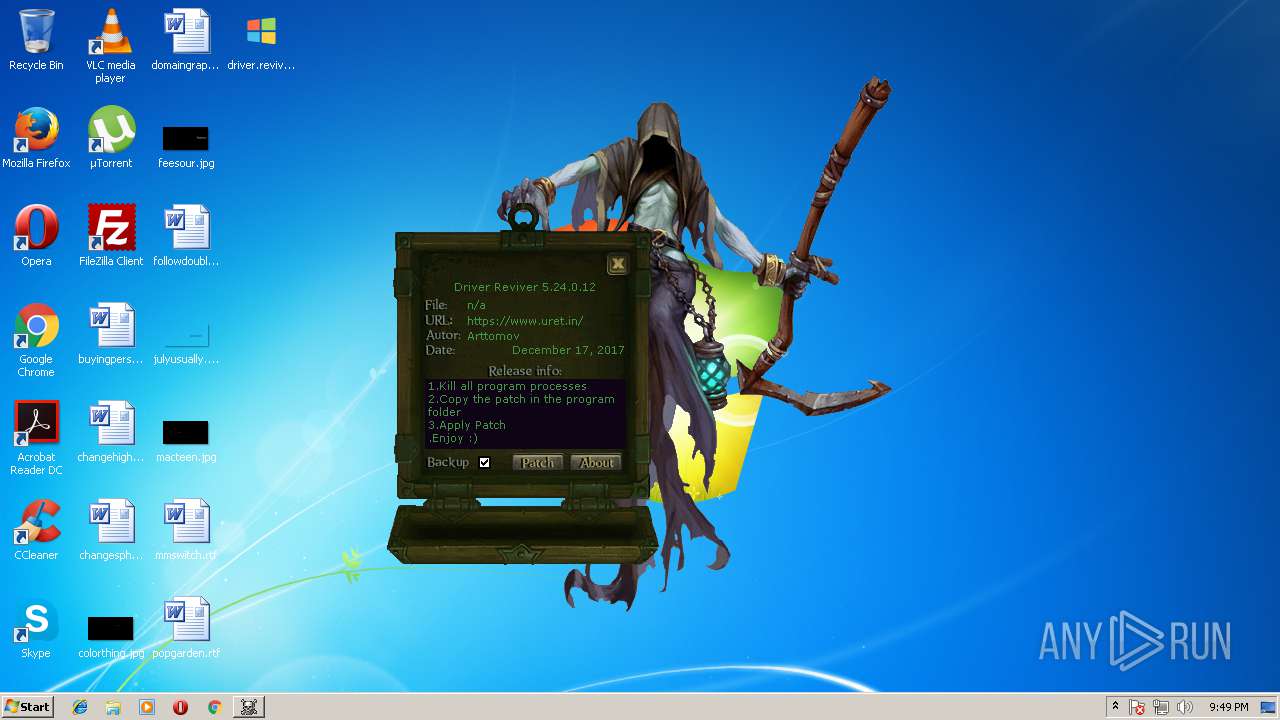
| File name: | driver.reviver.5.24.0.12-patch.exe |
| Full analysis: | https://app.any.run/tasks/10117f3f-9da7-48d3-bd6d-e824b2fb2ab3 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | June 22, 2018, 20:44:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | F2D7E52B6F02DA7E308E27681BA27B39 |
| SHA1: | B96ABA9B3E867C22E29C72E083B14F1865A1C7FF |
| SHA256: | 523FC53A3AFA854CA34ABB66F224281F57467BEE9CC0EB10BEEA5FD14EBF60A9 |
| SSDEEP: | 24576:YA3vHfd8y8jgZDjAYYUJIPe3X9uuBWqsDu8UukFzYxz2k2D5LJSYxi:5v/d83gZAJPruBWqyuFuYzu6x5bi |
MALICIOUS
Loads dropped or rewritten executable
- driver.reviver.5.24.0.12-patch.exe (PID: 1896)
- googleup.exe (PID: 1272)
- driver.reviver.5.24.0.12-patch.exe (PID: 1816)
- driver.reviver.5.24.0.12-patch.exe (PID: 2648)
- googleup.exe (PID: 1980)
- driver.reviver.5.24.0.12-patch.exe (PID: 3732)
- 157km3o99gmy_1.exe (PID: 2112)
Application was dropped or rewritten from another process
- driver.reviver.5.24.0.12-patch.exe (PID: 3732)
- googleup.exe (PID: 1980)
- driver.reviver.5.24.0.12-patch.exe (PID: 1420)
- googleup.exe (PID: 3584)
- 157km3o99gmy_1.exe (PID: 2112)
- googleup.exe (PID: 1272)
Known privilege escalation attack
- DllHost.exe (PID: 2984)
Changes the autorun value in the registry
- driver.reviver.5.24.0.12-patch.exe (PID: 2648)
- explorer.exe (PID: 3412)
- driver.reviver.5.24.0.12-patch.exe (PID: 3732)
- driver.reviver.5.24.0.12-patch.exe (PID: 1896)
- driver.reviver.5.24.0.12-patch.exe (PID: 1816)
Runs injected code in another process
- charmap.exe (PID: 1736)
Application was injected by another process
- explorer.exe (PID: 1676)
Changes internet zones settings
- explorer.exe (PID: 3412)
Changes Image File Execution Options
- explorer.exe (PID: 3412)
Connects to CnC server
- wuapp.exe (PID: 2832)
- explorer.exe (PID: 3412)
- wuapp.exe (PID: 1504)
Changes firewall settings
- explorer.exe (PID: 3412)
SUSPICIOUS
Creates files in the user directory
- driver.reviver.5.24.0.12-patch.exe (PID: 1896)
Application launched itself
- driver.reviver.5.24.0.12-patch.exe (PID: 1896)
- googleup.exe (PID: 1980)
Executable content was dropped or overwritten
- driver.reviver.5.24.0.12-patch.exe (PID: 3732)
- driver.reviver.5.24.0.12-patch.exe (PID: 1816)
- googleup.exe (PID: 1272)
- googleup.exe (PID: 1980)
- googleup.exe (PID: 3584)
- driver.reviver.5.24.0.12-patch.exe (PID: 2648)
- 157km3o99gmy_1.exe (PID: 2112)
- explorer.exe (PID: 3412)
- driver.reviver.5.24.0.12-patch.exe (PID: 1896)
Creates files in the program directory
- googleup.exe (PID: 3584)
- charmap.exe (PID: 1736)
Disables SEHOP
- googleup.exe (PID: 3584)
Creates or modifies windows services
- explorer.exe (PID: 3412)
Connects to unusual port
- wuapp.exe (PID: 2832)
- wuapp.exe (PID: 1504)
INFO
Dropped object may contain URL's
- googleup.exe (PID: 3584)
- explorer.exe (PID: 3412)
- driver.reviver.5.24.0.12-patch.exe (PID: 1896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:05:11 22:03:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x337c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-May-2014 20:03:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-May-2014 20:03:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000061D6 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50718 |
.rdata | 0x00008000 | 0x00001460 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94548 |
.data | 0x0000A000 | 0x0002AFB8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.88909 |
.ndata | 0x00035000 | 0x00021000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00056000 | 0x0005BA80 | 0x0005BC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.82142 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26917 | 1002 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.74891 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 1.93202 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 2.17802 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 2.29538 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 2.79063 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.72161 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70992 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
58
Monitored processes
21
Malicious processes
9
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1272 | "C:\Users\admin\AppData\Roaming\googleup.exe" | C:\Users\admin\AppData\Roaming\googleup.exe | driver.reviver.5.24.0.12-patch.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1420 | "C:\Users\admin\AppData\Roaming\driver.reviver.5.24.0.12-patch.exe" | C:\Users\admin\AppData\Roaming\driver.reviver.5.24.0.12-patch.exe | — | driver.reviver.5.24.0.12-patch.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1504 | "C:\Windows\System32\wuapp.exe" -c "C:\ProgramData\muFkUXeNTJ\cfgi" | C:\Windows\System32\wuapp.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Application Launcher Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1676 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1736 | C:\Windows\system32\charmap.exe | C:\Windows\system32\charmap.exe | — | driver.reviver.5.24.0.12-patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Character Map Exit code: 0 Version: 5.2.3668.0 Modules
| |||||||||||||||
| 1816 | C:\Users\admin\Desktop\driver.reviver.5.24.0.12-patch.exe | C:\Users\admin\Desktop\driver.reviver.5.24.0.12-patch.exe | driver.reviver.5.24.0.12-patch.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1828 | C:\Windows\system32\msiexec.exe | C:\Windows\system32\msiexec.exe | — | 157km3o99gmy_1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1896 | "C:\Users\admin\Desktop\driver.reviver.5.24.0.12-patch.exe" | C:\Users\admin\Desktop\driver.reviver.5.24.0.12-patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 1980 | "C:\Users\admin\AppData\Roaming\googleup.exe" | C:\Users\admin\AppData\Roaming\googleup.exe | DllHost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2112 | /suac | C:\Users\admin\AppData\Local\Temp\157km3o99gmy_1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
3 355
Read events
3 009
Write events
346
Delete events
0
Modification events
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000001800000084F73805 | |||
| (PID) Process: | (1896) driver.reviver.5.24.0.12-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | mahonia |
Value: C:\Users\admin\AppData\Roaming\mahonia.exe | |||
| (PID) Process: | (1896) driver.reviver.5.24.0.12-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1896) driver.reviver.5.24.0.12-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1816) driver.reviver.5.24.0.12-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | mahonia |
Value: C:\Users\admin\AppData\Roaming\mahonia.exe | |||
| (PID) Process: | (2648) driver.reviver.5.24.0.12-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | mahonia |
Value: C:\Users\admin\AppData\Roaming\mahonia.exe | |||
| (PID) Process: | (2984) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2984) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3584) googleup.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Google Updater |
| Operation: | write | Name: | LastUpdate |
Value: 5A2DD7343B28867A8E893A69407AC558 | |||
| (PID) Process: | (3584) googleup.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\{4631CB28-2734-9A66-9295-26755C66D944}\15721F09\20acdebdb03c19f95 |
| Operation: | write | Name: | 3bca87e47b |
Value: 05EE0000 | |||
Executable files
21
Suspicious files
6
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1896 | driver.reviver.5.24.0.12-patch.exe | C:\Users\admin\AppData\Local\Temp\nsx8DAC.tmp | — | |
MD5:— | SHA256:— | |||
| 1272 | googleup.exe | C:\Users\admin\AppData\Local\Temp\nsiAA0D.tmp | — | |
MD5:— | SHA256:— | |||
| 1816 | driver.reviver.5.24.0.12-patch.exe | C:\Users\admin\AppData\Local\Temp\nsyAA1D.tmp | — | |
MD5:— | SHA256:— | |||
| 1896 | driver.reviver.5.24.0.12-patch.exe | C:\Users\admin\AppData\Roaming\mahonia.exe | executable | |
MD5:— | SHA256:— | |||
| 1980 | googleup.exe | C: | — | |
MD5:— | SHA256:— | |||
| 1896 | driver.reviver.5.24.0.12-patch.exe | C:\Users\admin\AppData\Roaming\driver.reviver.5.24.0.12-patch.exe | executable | |
MD5:— | SHA256:— | |||
| 1896 | driver.reviver.5.24.0.12-patch.exe | C:\Users\admin\AppData\Roaming\rniamxsej.txt | text | |
MD5:— | SHA256:— | |||
| 2648 | driver.reviver.5.24.0.12-patch.exe | C: | — | |
MD5:— | SHA256:— | |||
| 1980 | googleup.exe | C:\Users\admin\AppData\Local\Temp\nslE254.tmp | — | |
MD5:— | SHA256:— | |||
| 3732 | driver.reviver.5.24.0.12-patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
3
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3412 | explorer.exe | POST | 200 | 47.74.218.175:80 | http://microsup.ru/panels_encoded/logout.php | US | binary | 109 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2832 | wuapp.exe | 69.195.135.90:3333 | — | Joe's Datacenter, LLC | US | suspicious |
3412 | explorer.exe | 172.217.18.206:80 | google.com | Google Inc. | US | whitelisted |
3412 | explorer.exe | 47.74.218.175:80 | microsup.ru | Alibaba (China) Technology Co., Ltd. | US | malicious |
1504 | wuapp.exe | 69.195.135.90:3333 | — | Joe's Datacenter, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
microsup.ru |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2832 | wuapp.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
3412 | explorer.exe | A Network Trojan was detected | ET TROJAN Win32/Neurevt.A/Betabot Check-in 4 |
2832 | wuapp.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
1504 | wuapp.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
1504 | wuapp.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |