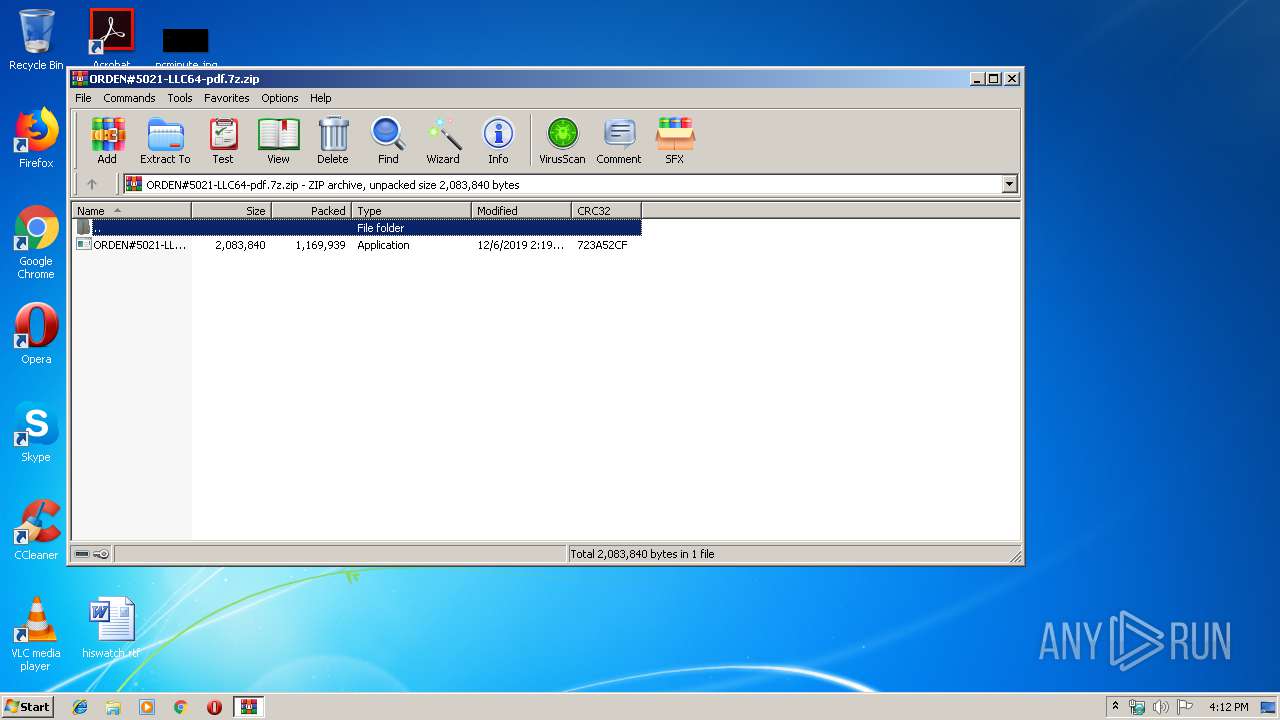
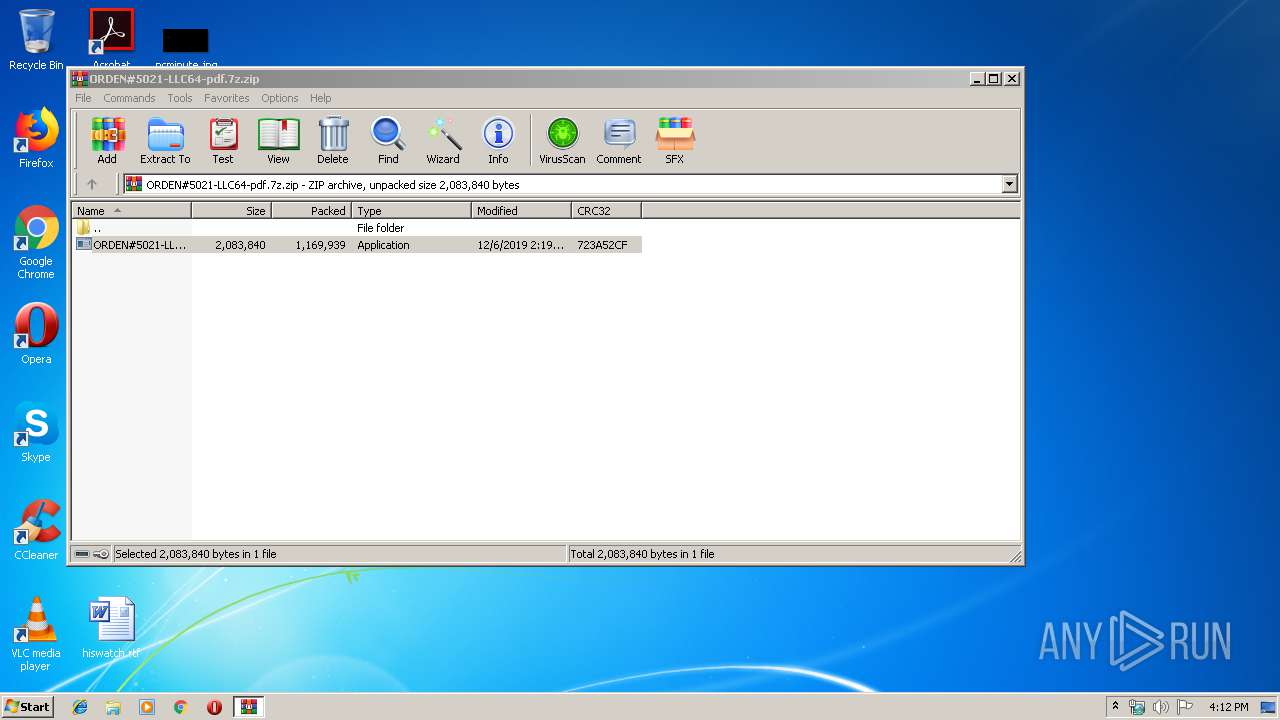
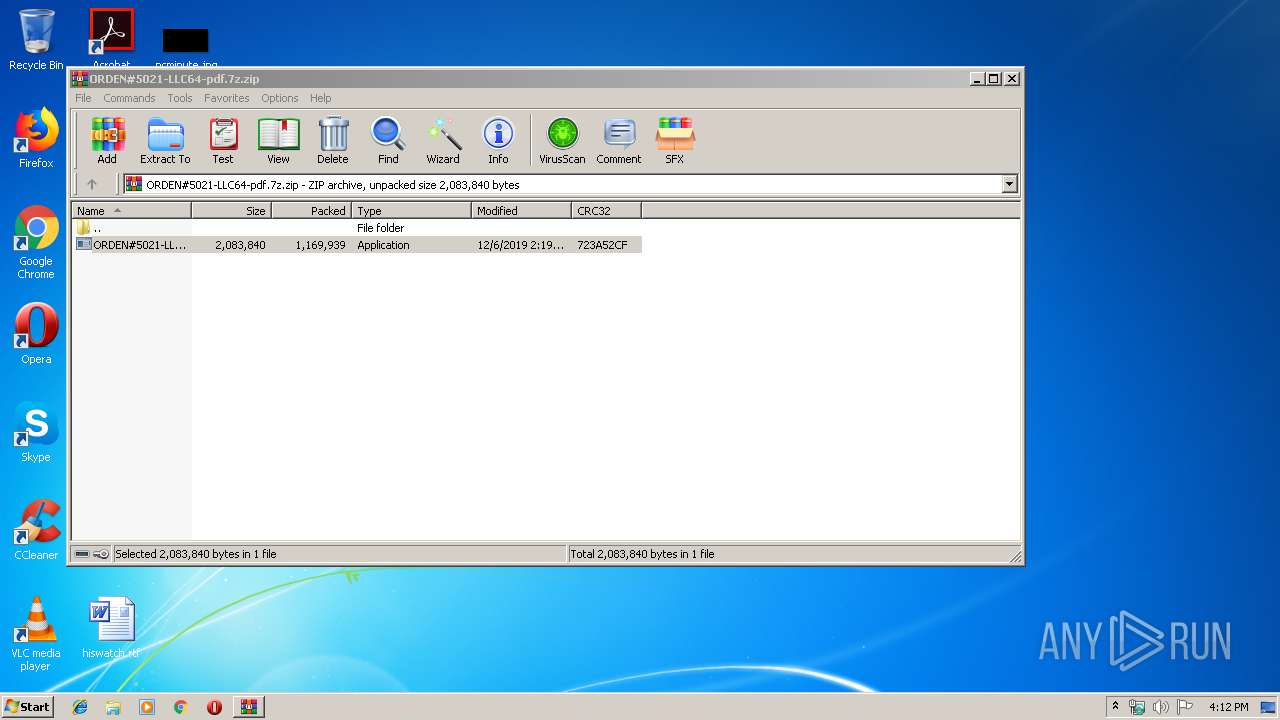
| File name: | ORDEN#5021-LLC64-pdf.7z |
| Full analysis: | https://app.any.run/tasks/4bdaea44-9d63-4857-aaec-2a662493a0fb |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | December 06, 2019, 16:12:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F46FBADE40EF11D52B7029A1B21F9FED |
| SHA1: | 5F922683C644746184BFBC05C24DAFB09E12FA2F |
| SHA256: | 5235C0EF89E731EB7A17C2BDB2CB15A8905545FD472C289622D19A11674F6B34 |
| SSDEEP: | 24576:TC0pFnQKwxlzkBbJoMSTTCfr9U1DARE0i6aeRDdo98dTA6g:Oun2lzkBbJo3H09USO0i6po9oTA6g |
MALICIOUS
Application was dropped or rewritten from another process
- ORDEN#5021-LLC64-pdf.exe (PID: 3880)
Detected Hawkeye Keylogger
- RegAsm.exe (PID: 1648)
Uses NirSoft utilities to collect credentials
- vbc.exe (PID: 3068)
Actions looks like stealing of personal data
- vbc.exe (PID: 492)
- vbc.exe (PID: 3068)
Stealing of credential data
- vbc.exe (PID: 3068)
SUSPICIOUS
Executes scripts
- RegAsm.exe (PID: 1648)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2932)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 492)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:06 15:19:13 |
| ZipCRC: | 0x723a52cf |
| ZipCompressedSize: | 1169939 |
| ZipUncompressedSize: | 2083840 |
| ZipFileName: | ORDEN#5021-LLC64-pdf.exe |
Total processes
39
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp3BFA.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 1648 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v2.0.50727\\\\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | ORDEN#5021-LLC64-pdf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2932 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\ORDEN#5021-LLC64-pdf.7z.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3068 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp539A.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3880 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2932.25947\ORDEN#5021-LLC64-pdf.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2932.25947\ORDEN#5021-LLC64-pdf.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
497
Read events
472
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ORDEN#5021-LLC64-pdf.7z.zip | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 492 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmp3BFA.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2932.25947\ORDEN#5021-LLC64-pdf.exe | executable | |
MD5:— | SHA256:— | |||
| 1648 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\25291068-43af-3e16-50f6-5889d9ce7904 | text | |
MD5:454353131947D1483FF5470107478978 | SHA256:2DF94DC1C58E952A1EBD1AE1185A291A8A573982CA90EC1BBB87B81126002668 | |||
| 3068 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmp539A.tmp | text | |
MD5:7FB9A9AD0FD9B1E0108ED71FBB276048 | SHA256:7D63C301317E144B0133A72250AE2D8E09AF65A92E6A807EC58A71939FE530A9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1648 | RegAsm.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
1648 | RegAsm.exe | 185.240.248.22:21 | ftp.oficina-ci.pt | — | — | malicious |
1648 | RegAsm.exe | 185.240.248.22:59793 | ftp.oficina-ci.pt | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bot.whatismyipaddress.com |
| shared |
ftp.oficina-ci.pt |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1648 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spy.HawkEye IP Check |
1648 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1648 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spyware.HawkEyeKeyLogger Exfiltration over FTP |
2 ETPRO signatures available at the full report