| File name: | OrderV548780.exe |
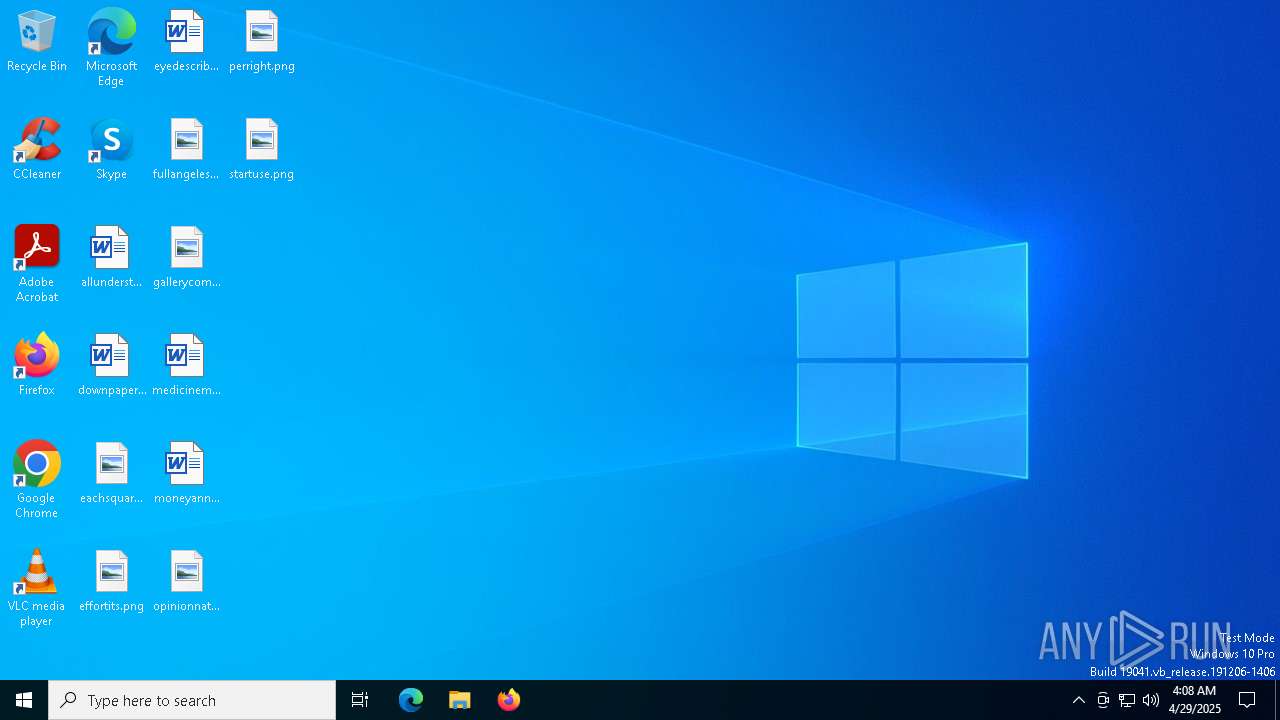
| Full analysis: | https://app.any.run/tasks/7a6c1f57-a09f-4a5a-aa8f-8349ec7542ba |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 29, 2025, 04:08:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 912C123891A7D463E1EA75B86E54F947 |
| SHA1: | E937E1707808EB4AAB8989F62E5EE2D528837B76 |
| SHA256: | 51EB3B1C63AEC8D2DFD4A8D3B1032567D81FF493B2DFE5166C35A50E05EBCB06 |
| SSDEEP: | 49152:6Al9/mvE3gA2yMZ1ZeshRWKK1pahEpHy/KTkuqIr5ozTr72vmOo5OhzGuSR+LFJf:6OUvE3AyMPfRWKGpackuqKS+o52/++r+ |
MALICIOUS
PURECRYPTER has been detected (YARA)
- OrderV548780.exe (PID: 720)
Create files in the Startup directory
- OrderV548780.exe (PID: 720)
AGENTTESLA has been detected (YARA)
- InstallUtil.exe (PID: 5244)
- InstallUtil.exe (PID: 840)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 840)
- InstallUtil.exe (PID: 5244)
SUSPICIOUS
Reads security settings of Internet Explorer
- OrderV548780.exe (PID: 720)
- main.exe (PID: 6660)
Starts CMD.EXE for commands execution
- OrderV548780.exe (PID: 720)
- main.exe (PID: 6660)
BASE64 encoded PowerShell command has been detected
- OrderV548780.exe (PID: 720)
Base64-obfuscated command line is found
- OrderV548780.exe (PID: 720)
Starts POWERSHELL.EXE for commands execution
- OrderV548780.exe (PID: 720)
Executable content was dropped or overwritten
- OrderV548780.exe (PID: 720)
Process uses IPCONFIG to renew DHCP configuration
- cmd.exe (PID: 5084)
- cmd.exe (PID: 1096)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1512)
Process uses IPCONFIG to discard the IP address configuration
- cmd.exe (PID: 4040)
Checks for external IP
- svchost.exe (PID: 2196)
- InstallUtil.exe (PID: 5244)
- InstallUtil.exe (PID: 840)
Potential Corporate Privacy Violation
- InstallUtil.exe (PID: 5244)
- InstallUtil.exe (PID: 840)
Connects to SMTP port
- InstallUtil.exe (PID: 840)
- InstallUtil.exe (PID: 5244)
INFO
Reads the computer name
- OrderV548780.exe (PID: 720)
- InstallUtil.exe (PID: 5244)
- main.exe (PID: 6660)
- InstallUtil.exe (PID: 840)
Process checks computer location settings
- OrderV548780.exe (PID: 720)
- main.exe (PID: 6660)
Reads the machine GUID from the registry
- OrderV548780.exe (PID: 720)
- main.exe (PID: 6660)
- InstallUtil.exe (PID: 5244)
- InstallUtil.exe (PID: 840)
Checks supported languages
- OrderV548780.exe (PID: 720)
- InstallUtil.exe (PID: 5244)
- main.exe (PID: 6660)
- InstallUtil.exe (PID: 840)
.NET Reactor protector has been detected
- OrderV548780.exe (PID: 720)
- main.exe (PID: 6660)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 632)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 632)
Auto-launch of the file from Startup directory
- OrderV548780.exe (PID: 720)
Creates files or folders in the user directory
- OrderV548780.exe (PID: 720)
Manual execution by a user
- InstallUtil.exe (PID: 5244)
- wscript.exe (PID: 1512)
- InstallUtil.exe (PID: 840)
Checks proxy server information
- InstallUtil.exe (PID: 5244)
- InstallUtil.exe (PID: 840)
- slui.exe (PID: 960)
Disables trace logs
- InstallUtil.exe (PID: 5244)
- InstallUtil.exe (PID: 840)
Reads the software policy settings
- InstallUtil.exe (PID: 5244)
- InstallUtil.exe (PID: 840)
- slui.exe (PID: 960)
ULTRAVNC has been detected
- InstallUtil.exe (PID: 840)
- InstallUtil.exe (PID: 5244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(5244) InstallUtil.exe
Protocolsmtp
Hostmail.iaa-airferight.com
Port25
Usernamemail@iaa-airferight.com
PasswordAsaprocky11
(PID) Process(840) InstallUtil.exe
Protocolsmtp
Hostmail.iaa-airferight.com
Port25
Usernamemail@iaa-airferight.com
PasswordAsaprocky11
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:29 00:23:26+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1253376 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x133dfe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.2191.3444 |
| ProductVersionNumber: | 1.0.2191.3444 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Zyesucax |
| FileVersion: | 1.0.2191.3444 |
| InternalName: | Zyesucax.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | Zyesucax.exe |
| ProductName: | Zyesucax |
| ProductVersion: | 1.0.2191.3444 |
| AssemblyVersion: | 1.0.3019.18453 |
Total processes
143
Monitored processes
19
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -enc QQBkAGQALQBNAHAAUAByAGUAZgBlAHIAZQBuAGMAZQAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEMAOgBcAFUAcwBlAHIAcwBcAGEAZABtAGkAbgBcAEQAZQBzAGsAdABvAHAAXABPAHIAZABlAHIAVgA1ADQAOAA3ADgAMAAuAGUAeABlADsAIABBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAALQBFAHgAYwBsAHUAcwBpAG8AbgBQAHIAbwBjAGUAcwBzACAAQwA6AFwAVQBzAGUAcgBzAFwAYQBkAG0AaQBuAFwARABlAHMAawB0AG8AcABcAE8AcgBkAGUAcgBWADUANAA4ADcAOAAwAC4AZQB4AGUAOwBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAALQBFAHgAYwBsAHUAcwBpAG8AbgBQAGEAdABoACAAQwA6AFwAVQBzAGUAcgBzAFwAYQBkAG0AaQBuAFwAQQBwAHAARABhAHQAYQBcAFIAbwBhAG0AaQBuAGcAXABtAGEAaQBuAC4AZQB4AGUAOwAgAEEAZABkAC0ATQBwAFAAcgBlAGYAZQByAGUAbgBjAGUAIAAtAEUAeABjAGwAdQBzAGkAbwBuAFAAcgBvAGMAZQBzAHMAIABDADoAXABVAHMAZQByAHMAXABhAGQAbQBpAG4AXABBAHAAcABEAGEAdABhAFwAUgBvAGEAbQBpAG4AZwBcAG0AYQBpAG4ALgBlAHgAZQA= | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | OrderV548780.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\Users\admin\Desktop\OrderV548780.exe" | C:\Users\admin\Desktop\OrderV548780.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Zyesucax Exit code: 4294967295 Version: 1.0.2191.3444 Modules
| |||||||||||||||
| 840 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
AgentTesla(PID) Process(840) InstallUtil.exe Protocolsmtp Hostmail.iaa-airferight.com Port25 Usernamemail@iaa-airferight.com PasswordAsaprocky11 | |||||||||||||||
| 960 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Windows\System32\cmd.exe" /c ipconfig /renew | C:\Windows\SysWOW64\cmd.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | wscript "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\main.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1804 | ipconfig /release | C:\Windows\SysWOW64\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 605
Read events
18 591
Write events
14
Delete events
0
Modification events
| (PID) Process: | (5244) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5244) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5244) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5244) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5244) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5244) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5244) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5244) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5244) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5244) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4ifx0pqw.fzn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eio0drvg.a02.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zl3io225.tuc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1ffwb3y1.oyg.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 720 | OrderV548780.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\main.vbs | text | |
MD5:712510D093BA2A822DE52C8020555089 | SHA256:51B8A04FC1C9B67BEFEA5C840EE8956EC411F9E8945505C75D18B32585955E49 | |||
| 632 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:AEB77ECA160340235AB7113B266336C8 | SHA256:EF3086E61DBC17F8F959A338F2671171AB5AB7618F3674A9519E245CF3A062DE | |||
| 720 | OrderV548780.exe | C:\Users\admin\AppData\Roaming\main.exe | executable | |
MD5:912C123891A7D463E1EA75B86E54F947 | SHA256:51EB3B1C63AEC8D2DFD4A8D3B1032567D81FF493B2DFE5166C35A50E05EBCB06 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
54
DNS requests
19
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
5200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5200 | SIHClient.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5200 | SIHClient.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
5200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
api.ipify.org |
| shared |
mail.iaa-airferight.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5244 | InstallUtil.exe | Potential Corporate Privacy Violation | ET INFO Possible IP Check api.ipify.org |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
5244 | InstallUtil.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
— | — | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
840 | InstallUtil.exe | Potential Corporate Privacy Violation | ET INFO Possible IP Check api.ipify.org |
840 | InstallUtil.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
— | — | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |