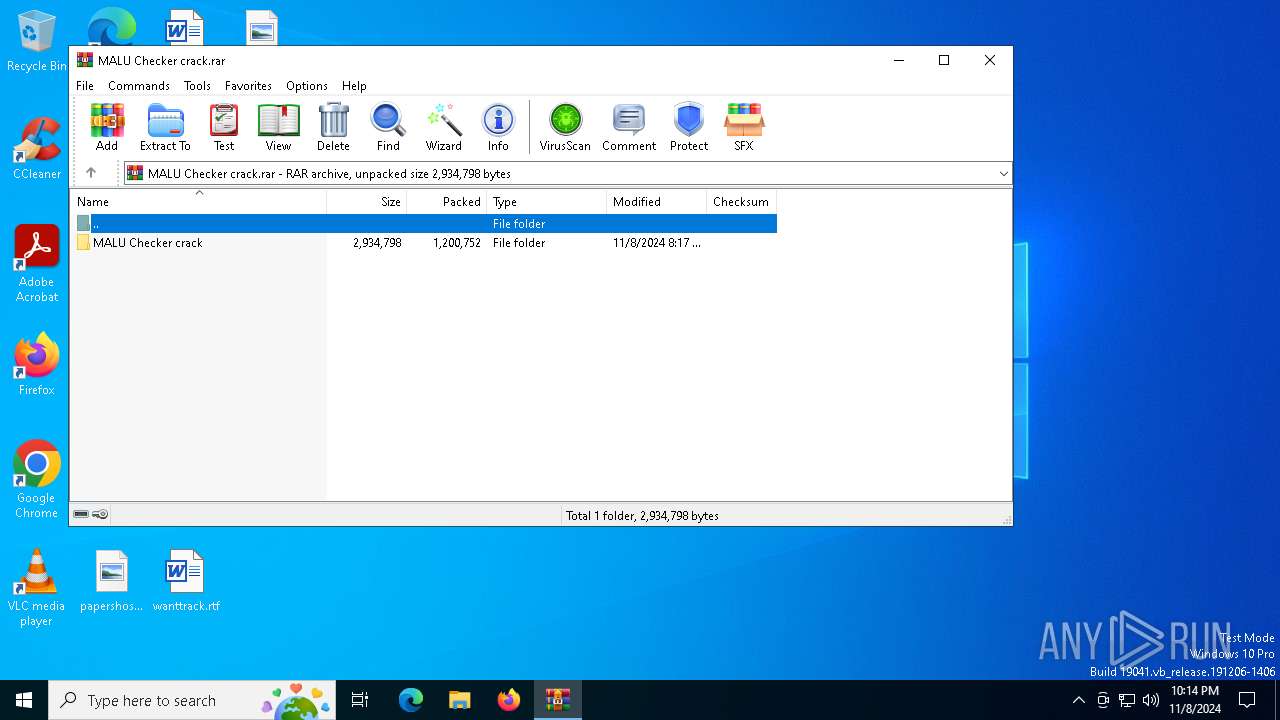
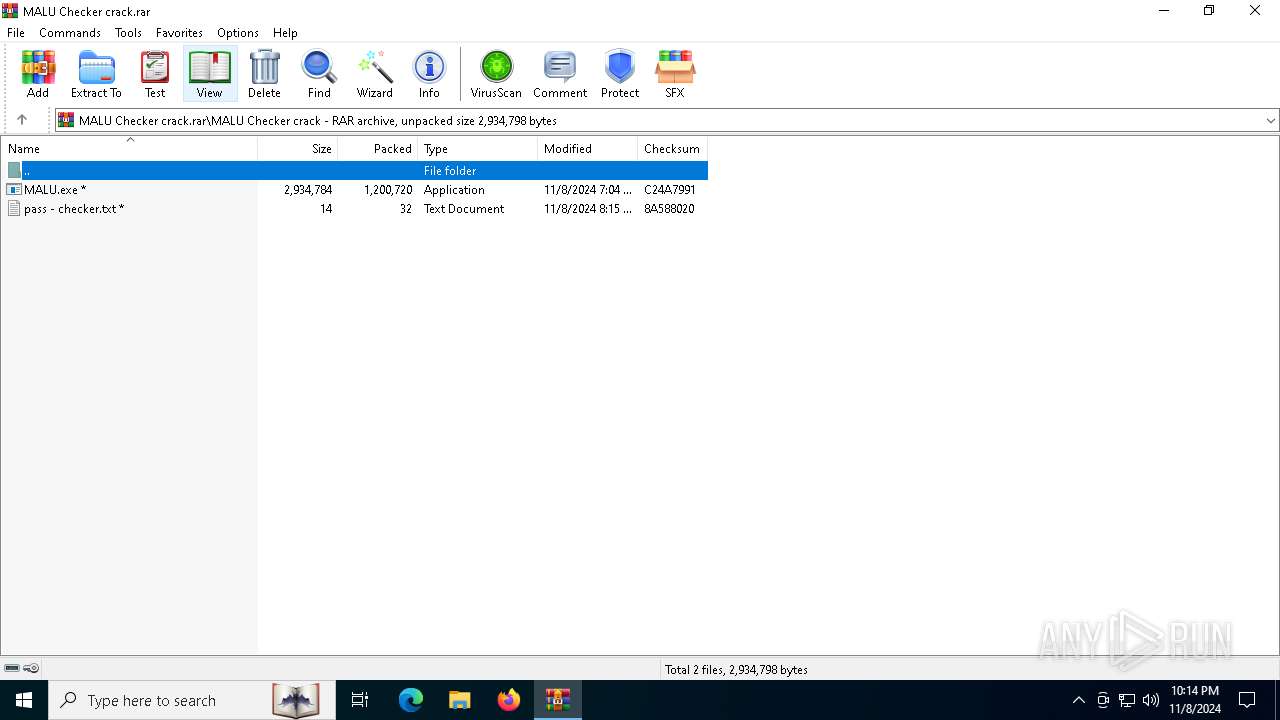
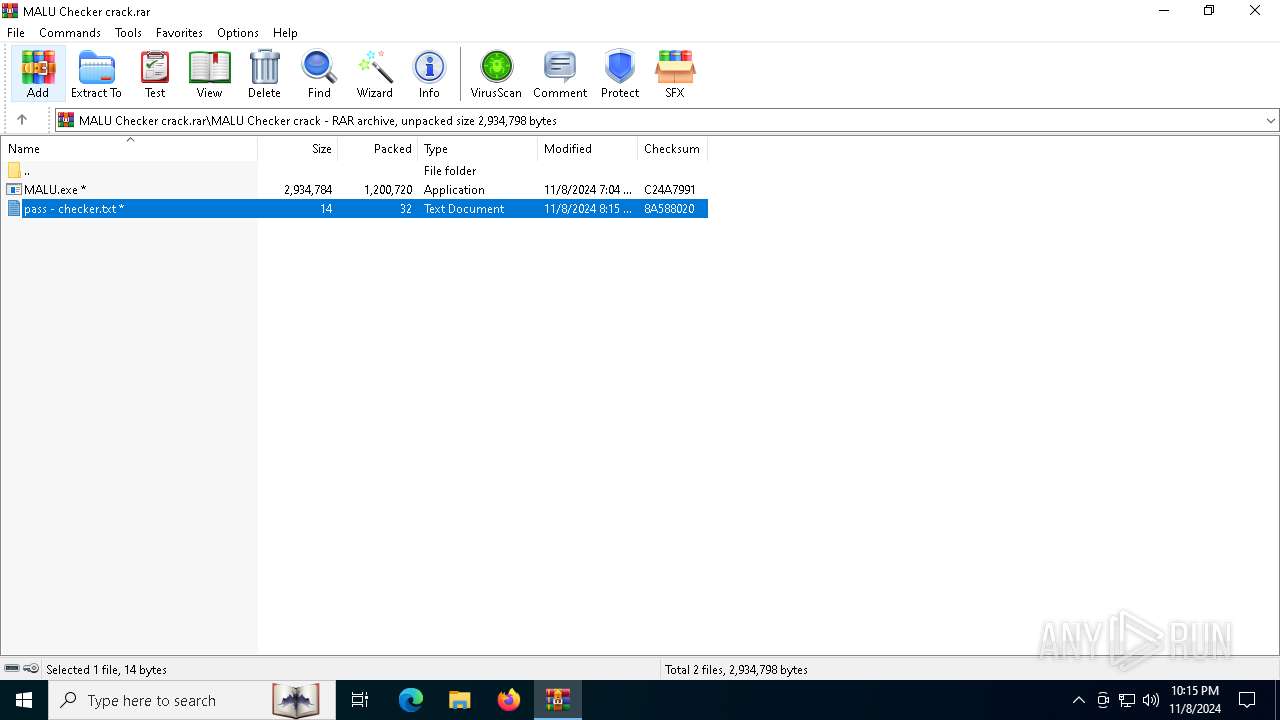
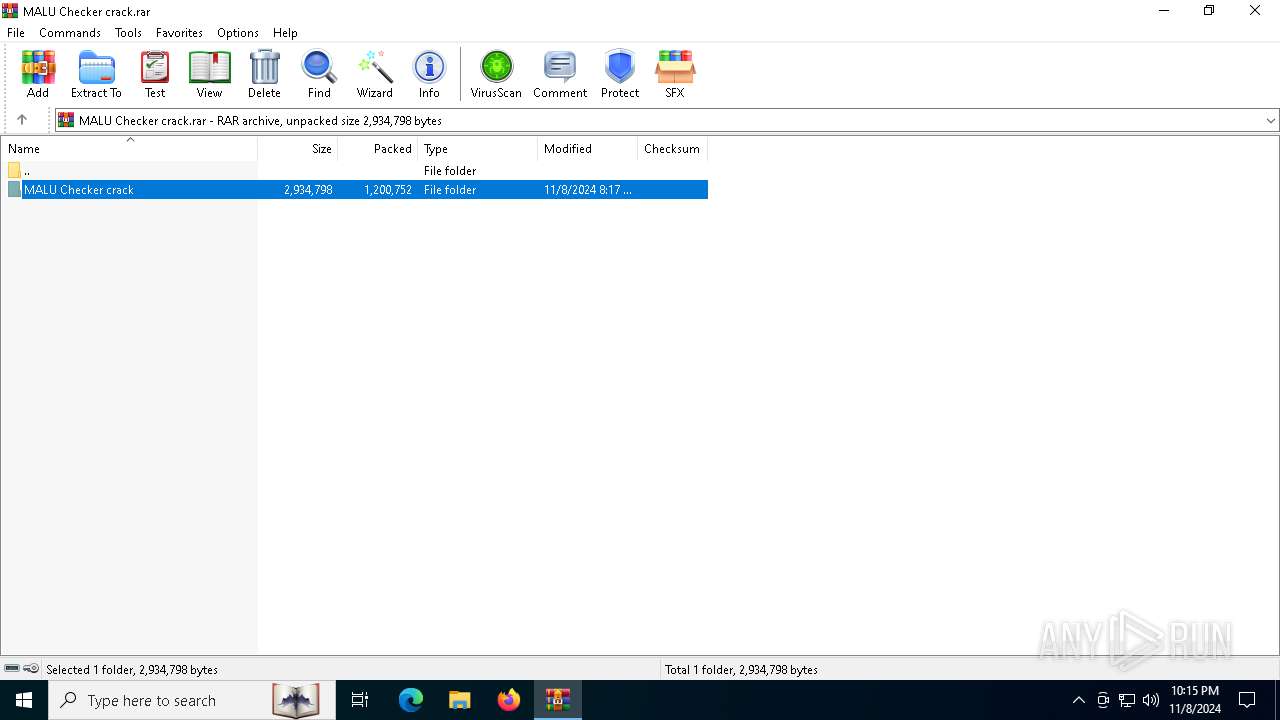
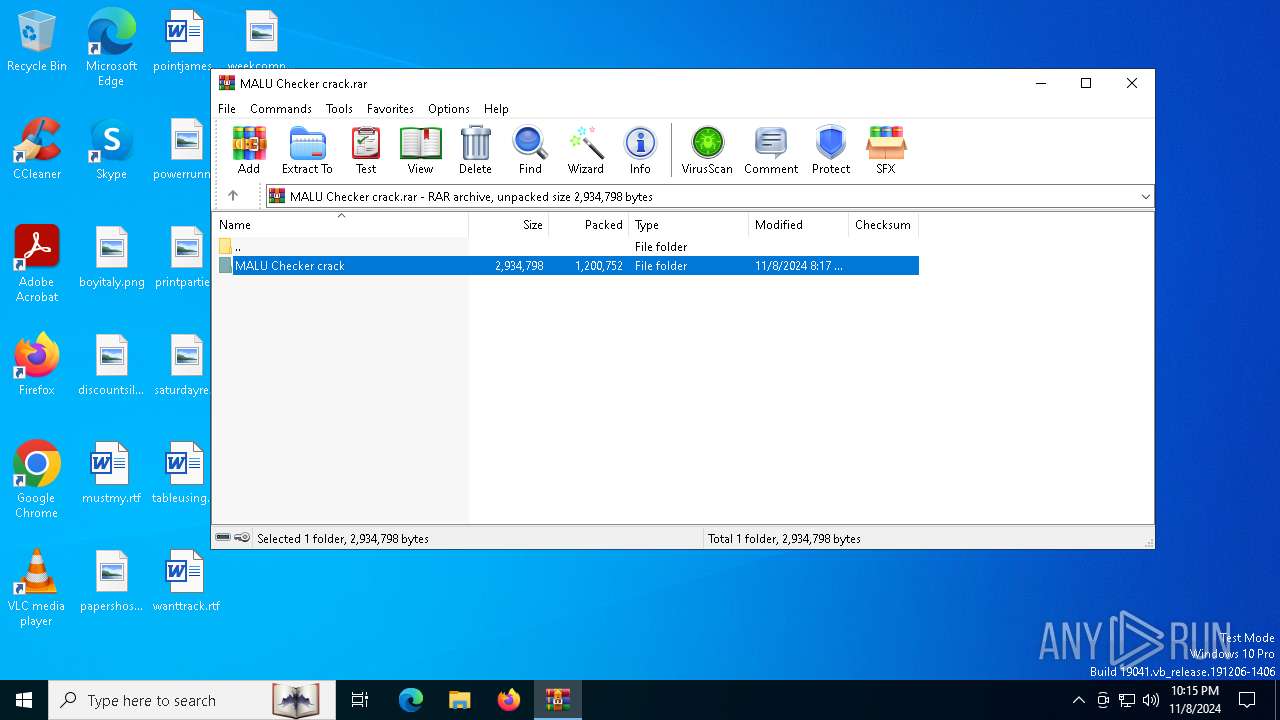
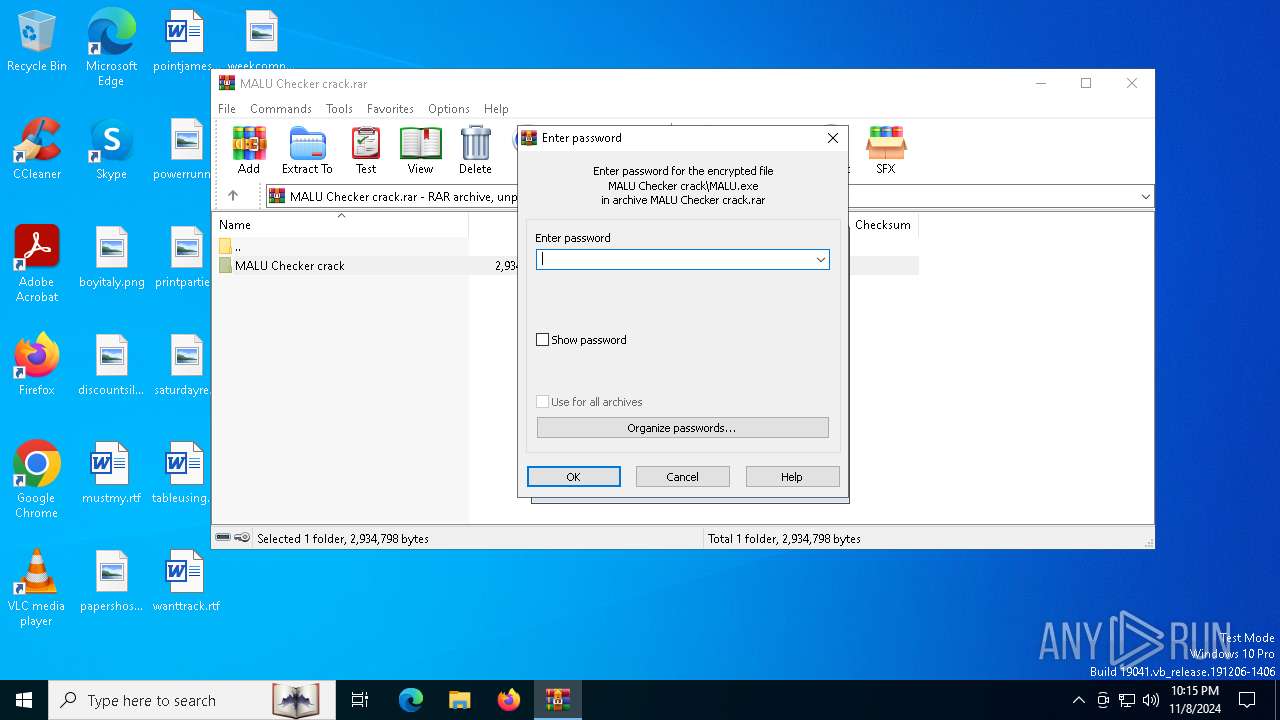
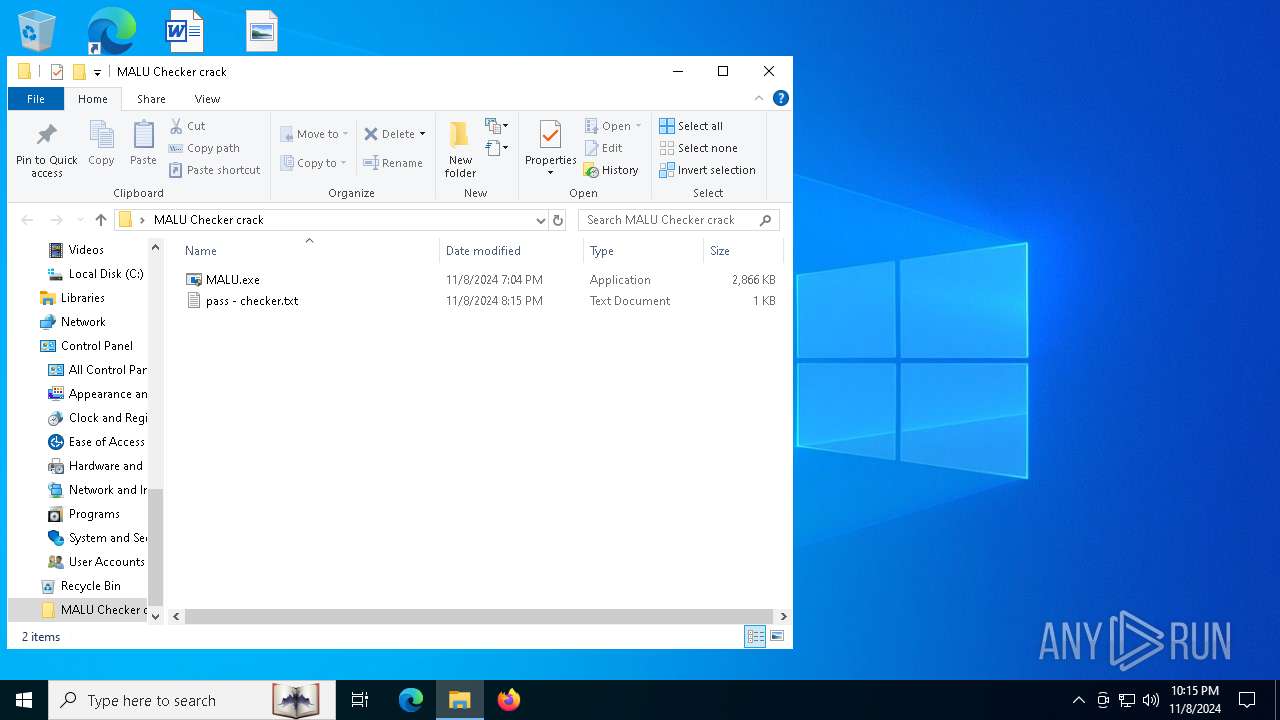
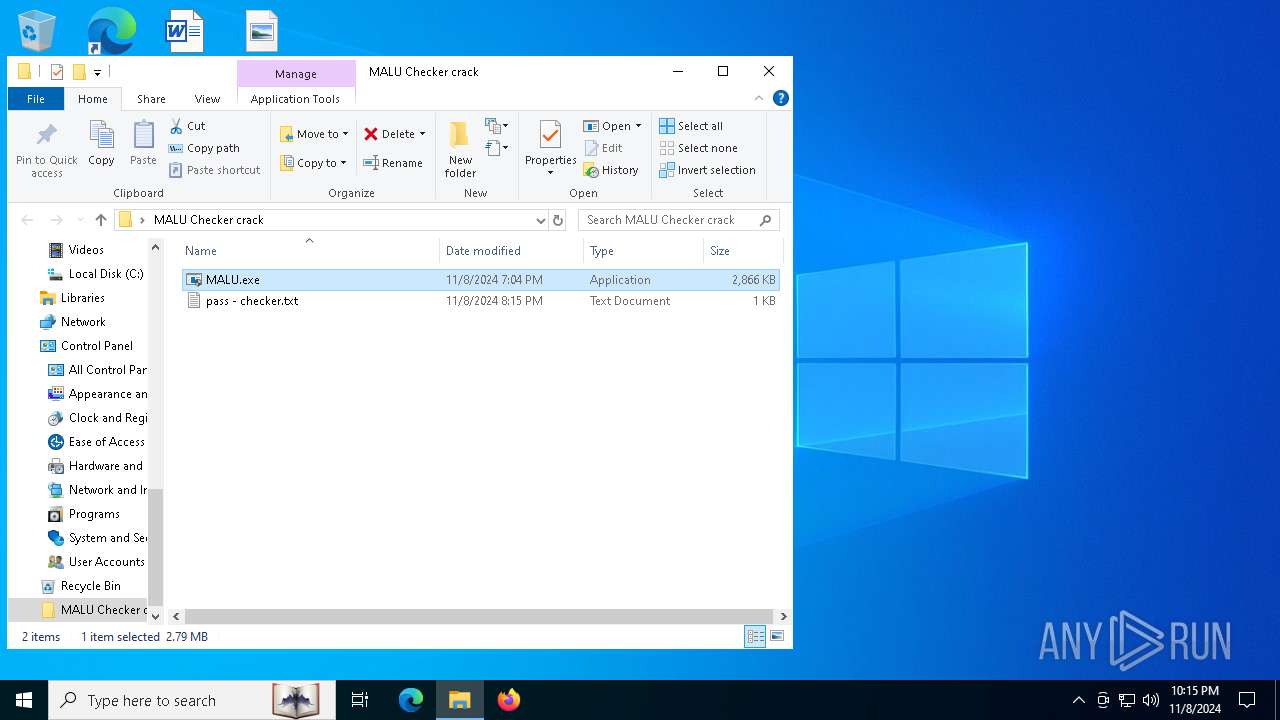
| File name: | MALU Checker crack.rar |
| Full analysis: | https://app.any.run/tasks/76887c4d-a925-4dea-999b-b8cb2c82b2ae |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | November 08, 2024, 22:14:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
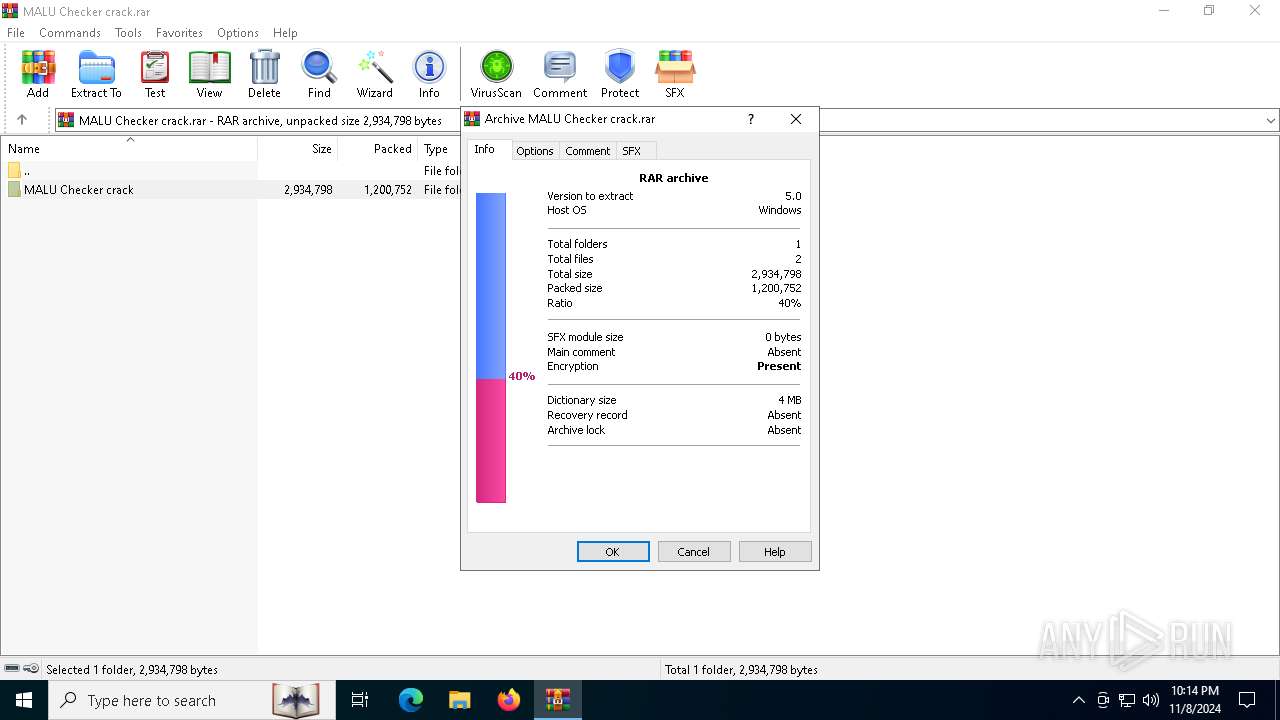
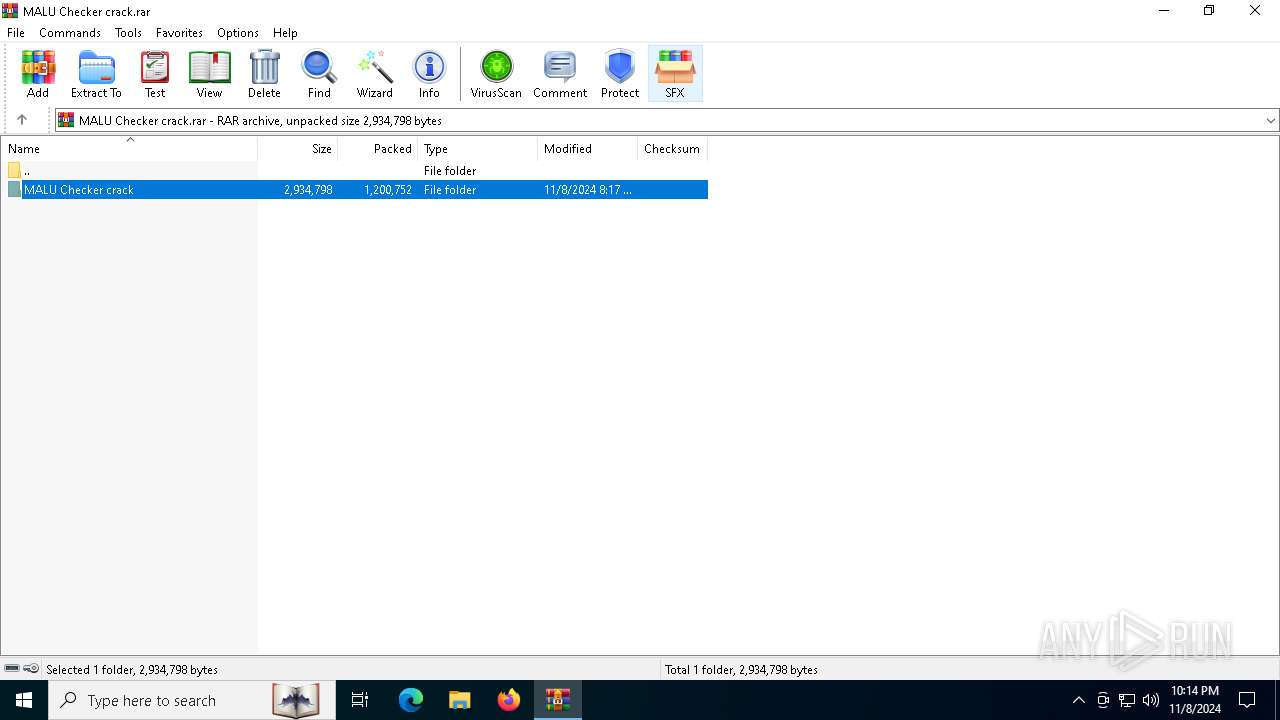
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 7986E643EADC9696824E5BF83CCEBCC3 |
| SHA1: | B226A5180C9D9790A1F2E83E006FB39E9A6F00C3 |
| SHA256: | 51D3F483704C68DE955242DF3B2B16AA8DB9210AAC4476515FFE4650D4C37908 |
| SSDEEP: | 49152:DhOnzFBoJD5LvkyP5is6wh90M47mbhtWAQuPoLPSCfJFjOuylanhx0MuDMXbwP42:DO3qlvD+wfdtDQYoGChJOXlSx7uDMXYF |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6124)
- powershell.exe (PID: 6028)
Adds path to the Windows Defender exclusion list
- MALU.exe (PID: 6636)
- MALU.exe (PID: 3008)
REDLINE has been detected (YARA)
- payload.exe (PID: 6280)
SUSPICIOUS
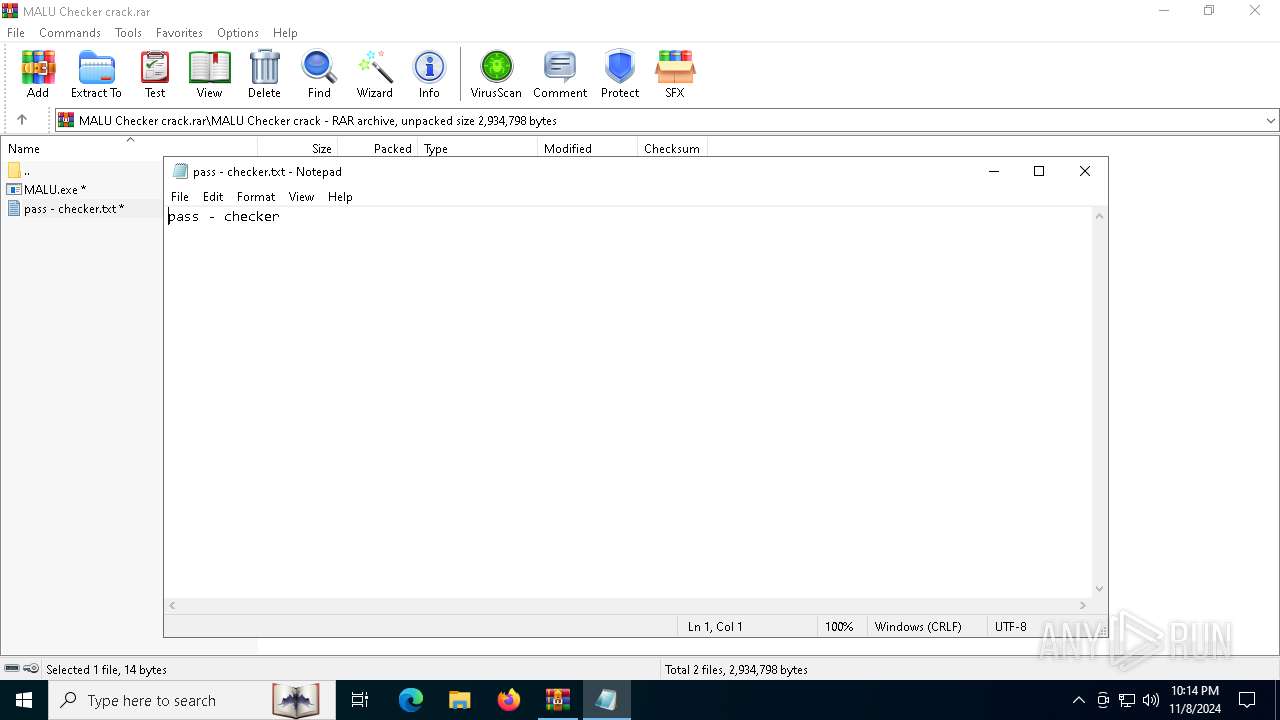
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 6256)
Starts POWERSHELL.EXE for commands execution
- MALU.exe (PID: 6636)
- MALU.exe (PID: 3008)
Script adds exclusion path to Windows Defender
- MALU.exe (PID: 6636)
- MALU.exe (PID: 3008)
Executable content was dropped or overwritten
- MALU.exe (PID: 6636)
- MALU.exe (PID: 3008)
Connects to unusual port
- payload.exe (PID: 6280)
- payload.exe (PID: 3696)
INFO
Executable content was dropped or overwritten
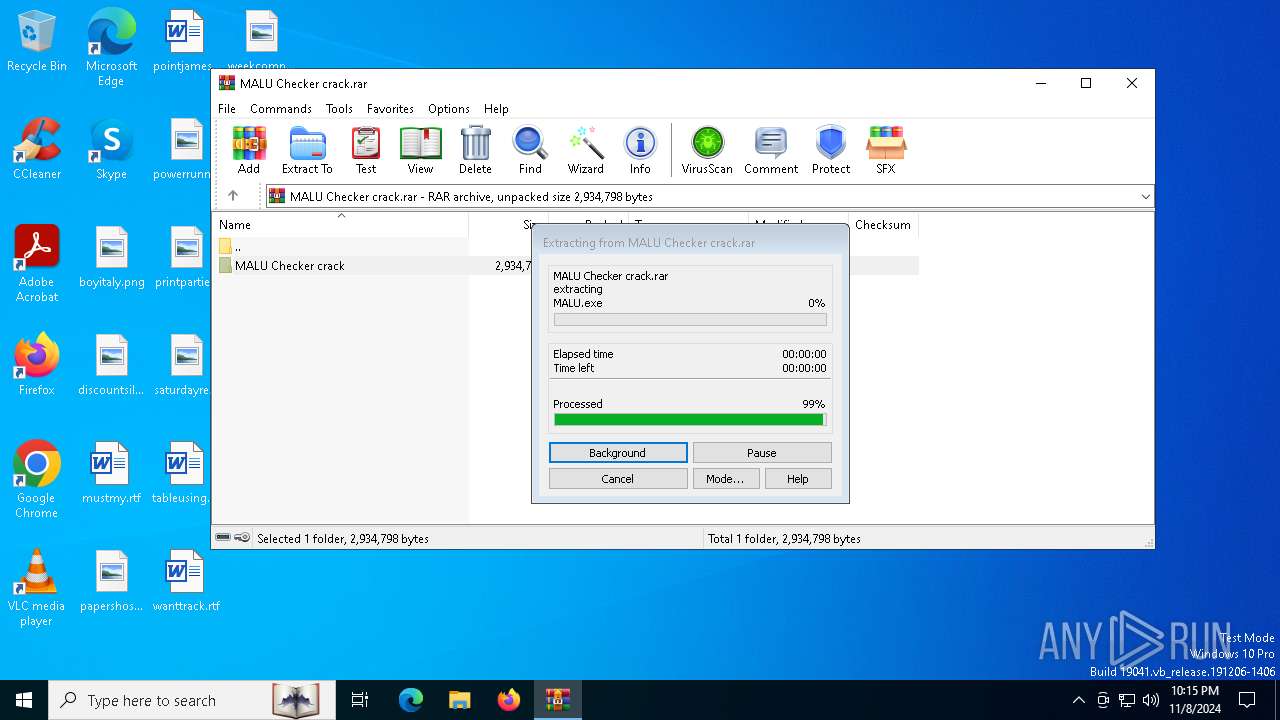
- WinRAR.exe (PID: 6256)
Manual execution by a user
- MALU.exe (PID: 6636)
- MALU.exe (PID: 540)
- MALU.exe (PID: 6352)
- MALU.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(6280) payload.exe
C2 (1)147.45.44.221:1912
BotnetVOVCHIK
Options
ErrorMessage
Keys
XorSADJisjigfjifgjid
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
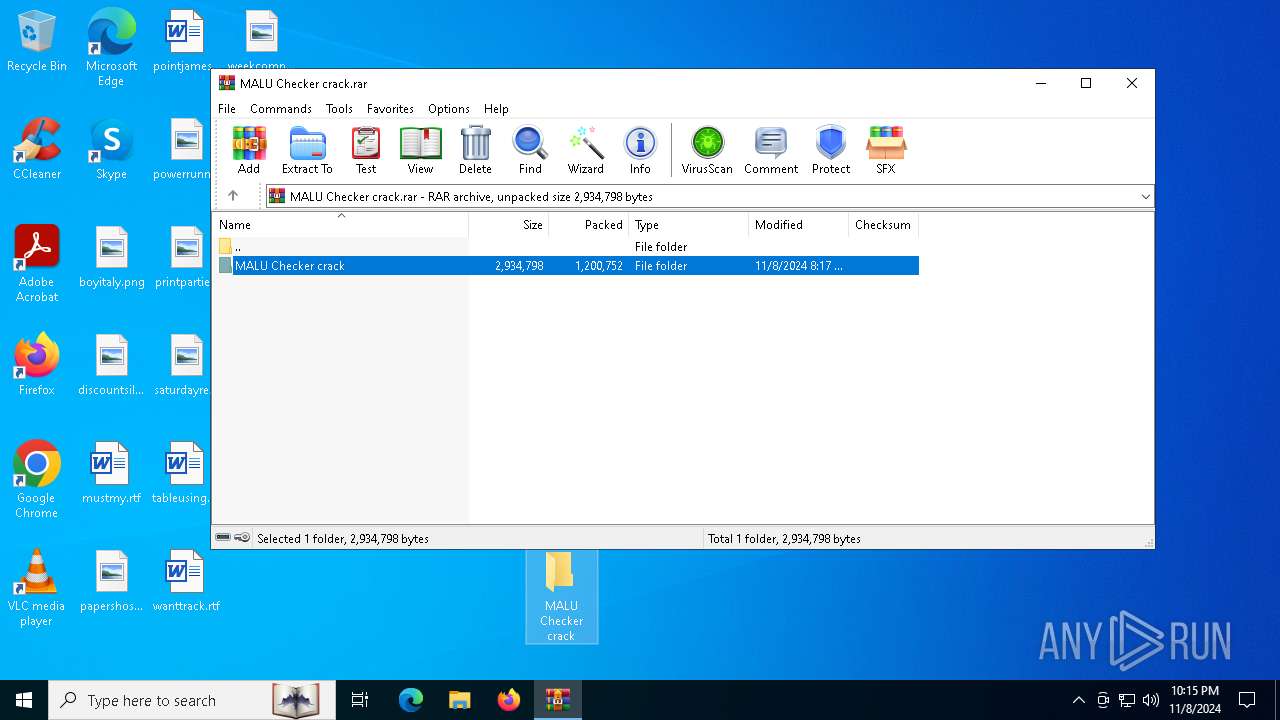
| CompressedSize: | 1200720 |
| UncompressedSize: | 2934784 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | MALU Checker crack/MALU.exe |
Total processes
145
Monitored processes
13
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
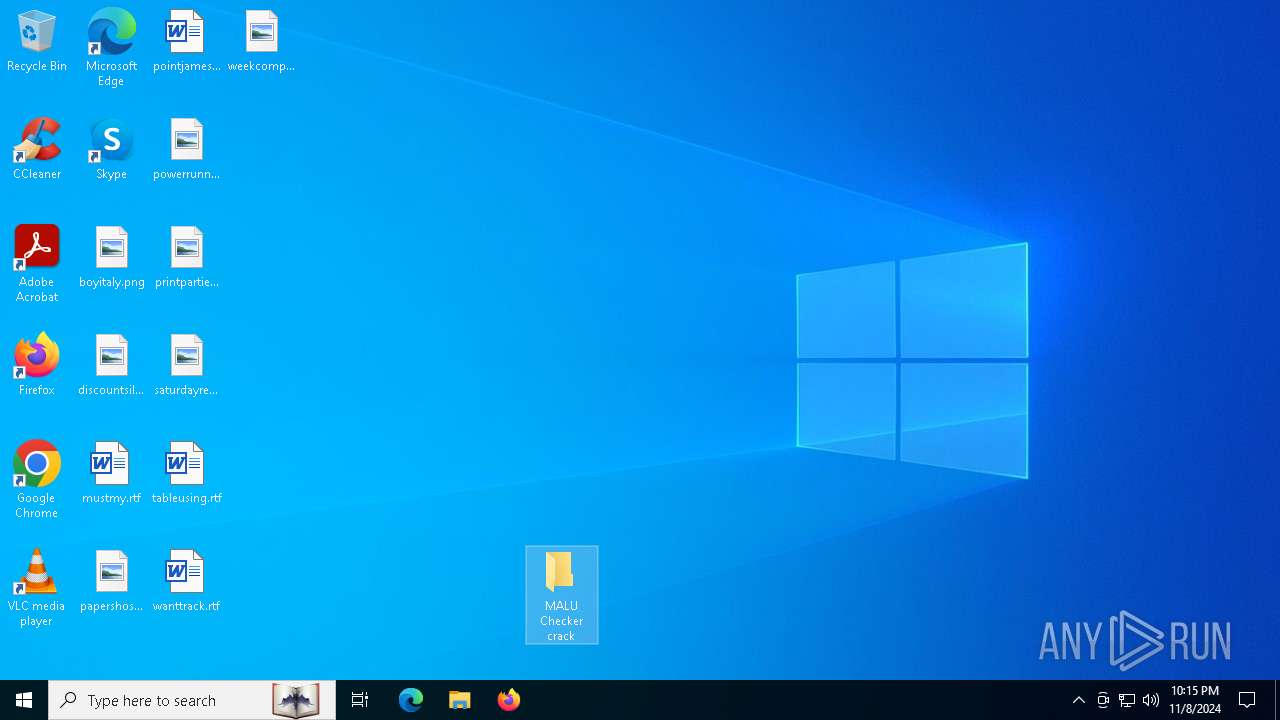
| 540 | "C:\Users\admin\Desktop\MALU Checker crack\MALU.exe" | C:\Users\admin\Desktop\MALU Checker crack\MALU.exe | — | explorer.exe | |||||||||||
User: admin Company: ConsoleApp1 Integrity Level: MEDIUM Description: ConsoleApp1 Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1168 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3008 | "C:\Users\admin\Desktop\MALU Checker crack\MALU.exe" | C:\Users\admin\Desktop\MALU Checker crack\MALU.exe | explorer.exe | ||||||||||||
User: admin Company: ConsoleApp1 Integrity Level: HIGH Description: ConsoleApp1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3696 | "C:\Users\admin\AppData\Roaming\l43423ab.pw4\payload.exe" | C:\Users\admin\AppData\Roaming\l43423ab.pw4\payload.exe | MALU.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: XHP Version: 12.9.1.22 Modules
| |||||||||||||||
| 6028 | "powershell.exe" -WindowStyle Hidden -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Roaming\l43423ab.pw4'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | MALU.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6124 | "powershell.exe" -WindowStyle Hidden -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Roaming\eqgf1fra.1mm'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | MALU.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6152 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6256 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MALU Checker crack.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6280 | "C:\Users\admin\AppData\Roaming\eqgf1fra.1mm\payload.exe" | C:\Users\admin\AppData\Roaming\eqgf1fra.1mm\payload.exe | MALU.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: XHP Version: 12.9.1.22 Modules
RedLine(PID) Process(6280) payload.exe C2 (1)147.45.44.221:1912 BotnetVOVCHIK Options ErrorMessage Keys XorSADJisjigfjifgjid | |||||||||||||||
| 6352 | "C:\Users\admin\Desktop\MALU Checker crack\MALU.exe" | C:\Users\admin\Desktop\MALU Checker crack\MALU.exe | — | explorer.exe | |||||||||||
User: admin Company: ConsoleApp1 Integrity Level: MEDIUM Description: ConsoleApp1 Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
16 638
Read events
16 619
Write events
19
Delete events
0
Modification events
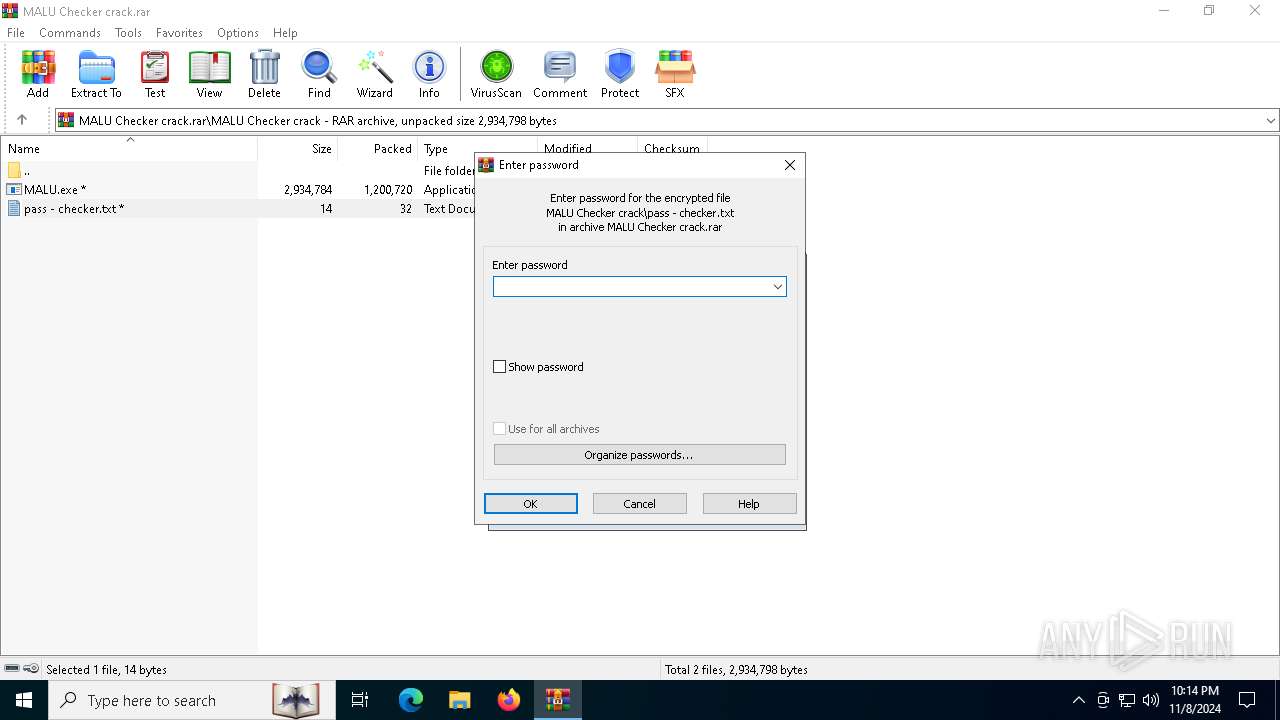
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MALU Checker crack.rar | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFCB000000440000008B0400002D020000 | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
3
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6256.42005\MALU Checker crack\MALU.exe | executable | |
MD5:F0638EBC6BF1CAC01FE84C0FD767C4A8 | SHA256:AA388C640AFCC43E28456575970367EAA784149600089377E95F078FAB355ED3 | |||
| 6124 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iygnpj1y.sfr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6256.42005\MALU Checker crack\pass - checker.txt | text | |
MD5:5BF5AE94A4954534ECD626A94A9FF459 | SHA256:69E9393AFE9083FA41D16478123FF627195596767DC489FC68246E32B9594478 | |||
| 6124 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:E95CB7FB49CE725F908F968B54586CF5 | SHA256:50EEBB11567C721DA3FF94A97C9FBDB11F188ACA137DBD55AF2A35B16FDA72A3 | |||
| 6256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb6256.40087\pass - checker.txt | text | |
MD5:5BF5AE94A4954534ECD626A94A9FF459 | SHA256:69E9393AFE9083FA41D16478123FF627195596767DC489FC68246E32B9594478 | |||
| 6028 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jgh31lhw.lup.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6636 | MALU.exe | C:\Users\admin\AppData\Roaming\eqgf1fra.1mm\payload.exe | executable | |
MD5:BCA9AEA1FC37E8A452EAB189D35F1F75 | SHA256:07B33F214887B7DBCB36ECE8A6656A9929B7BC002EDB8838F54516917FE6E580 | |||
| 6028 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_koa0sb3l.vw3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3008 | MALU.exe | C:\Users\admin\AppData\Roaming\l43423ab.pw4\payload.exe | executable | |
MD5:BCA9AEA1FC37E8A452EAB189D35F1F75 | SHA256:07B33F214887B7DBCB36ECE8A6656A9929B7BC002EDB8838F54516917FE6E580 | |||
| 6124 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_r4cfjglb.xyq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
44
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6208 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6044 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6044 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.129:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4376 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |