| File name: | phish_alert_sp2_2.0.0.0 (29).eml |
| Full analysis: | https://app.any.run/tasks/0ff5835a-608d-4aa7-b2c5-0cc6564da367 |
| Verdict: | Malicious activity |
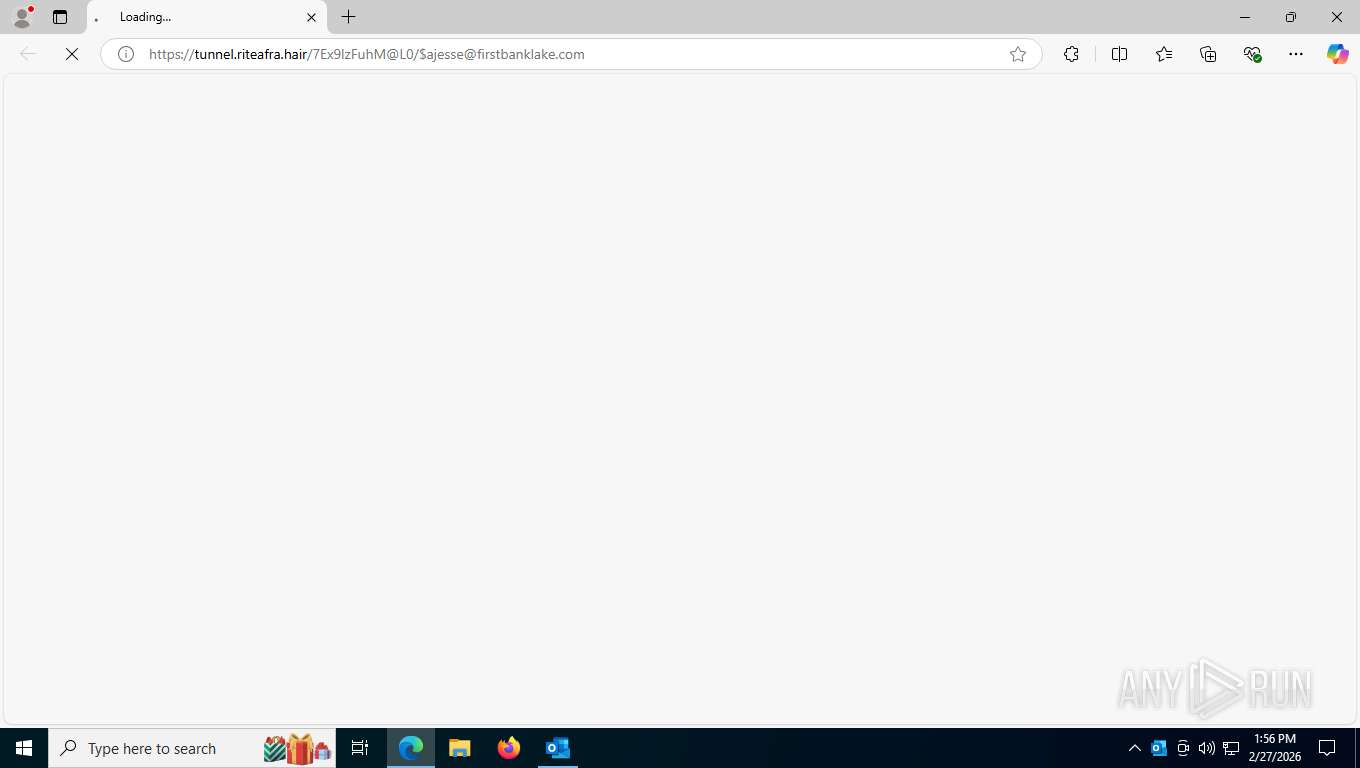
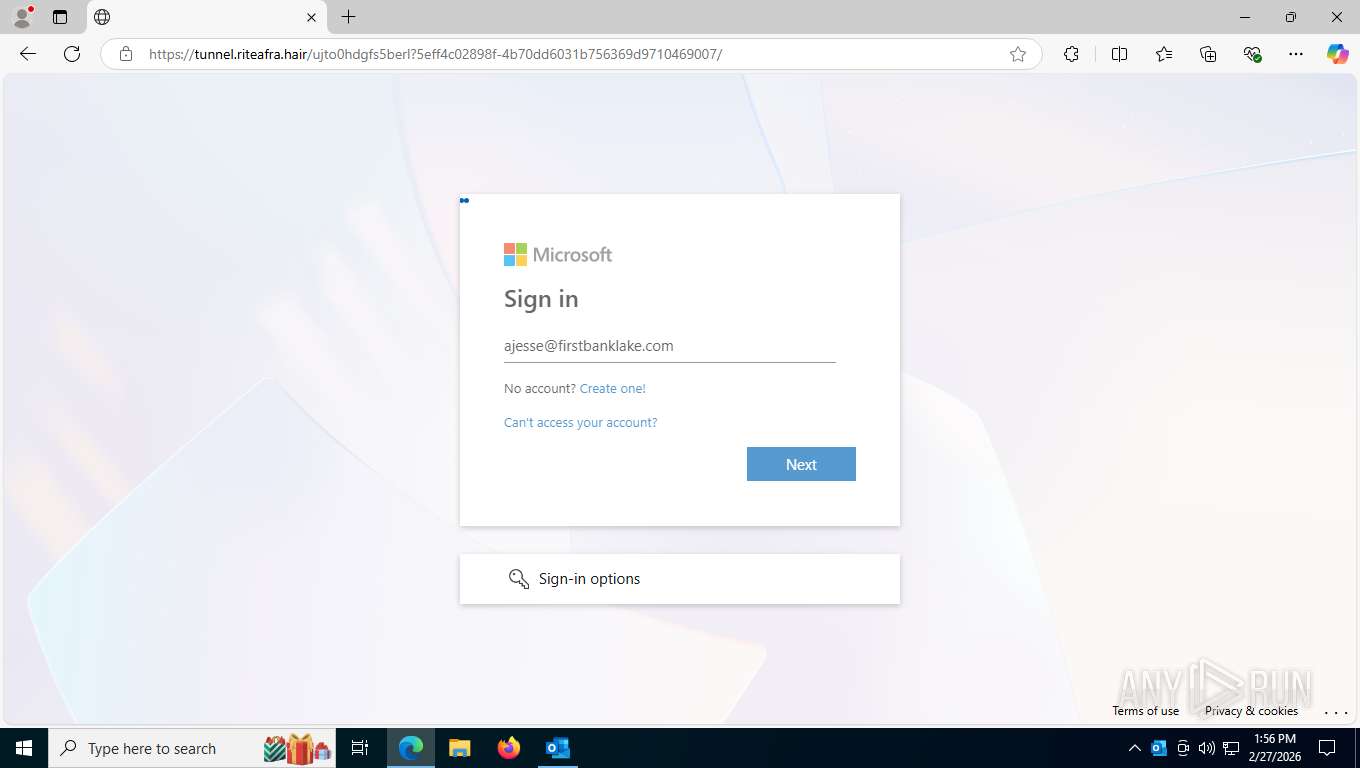
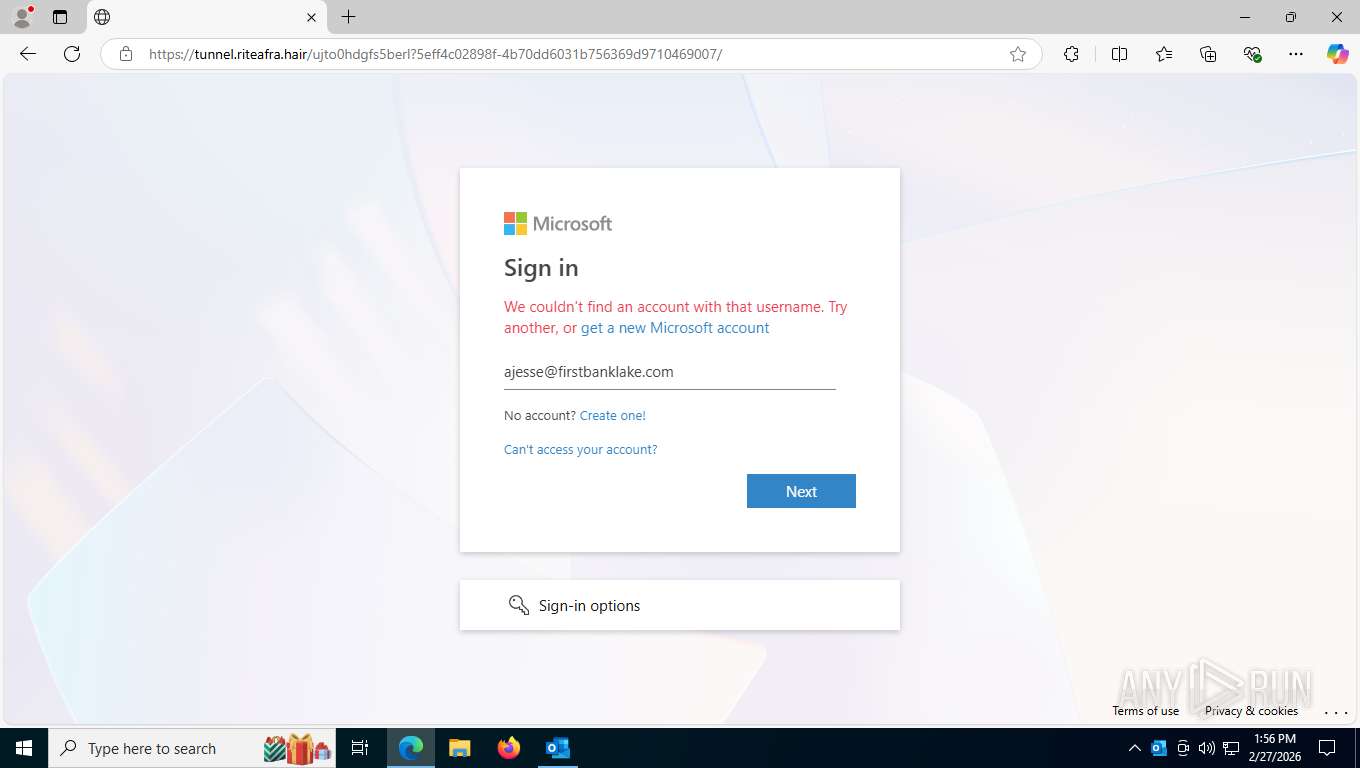
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | February 27, 2026, 18:56:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines (718), with CRLF line terminators |
| MD5: | 163D84D915FD06962FCD0EFF7FA028BC |
| SHA1: | 710959945167426261483E70CAFCF1AB9A1915B4 |
| SHA256: | 51A4AF7ACB58F8D12EB52CF0F8789C06D70EC3DE54A8E1130E37D88F087A2DA0 |
| SSDEEP: | 3072:pXOGcSnt1pB3dDVBZs1qV0+l4XAJvY2lZgbmS/HdWglJ/U0GiwFRKqDRyYdIsJon:9OxQt1Lbu+Sw+nx/n/U5FxbWvYdb8T |
MALICIOUS
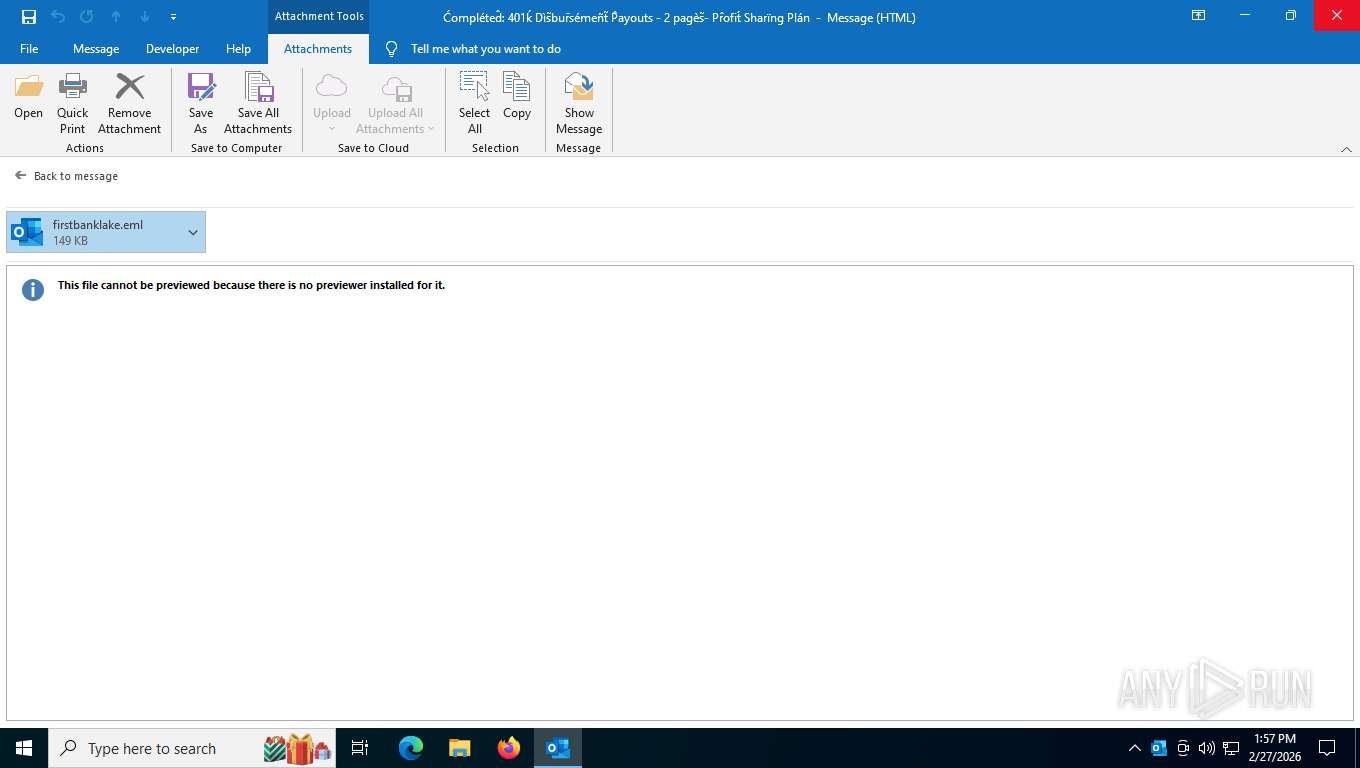
PHISHING has been detected (ML)
- msedge.exe (PID: 3188)
QR code contains URL with email
- OUTLOOK.EXE (PID: 7704)
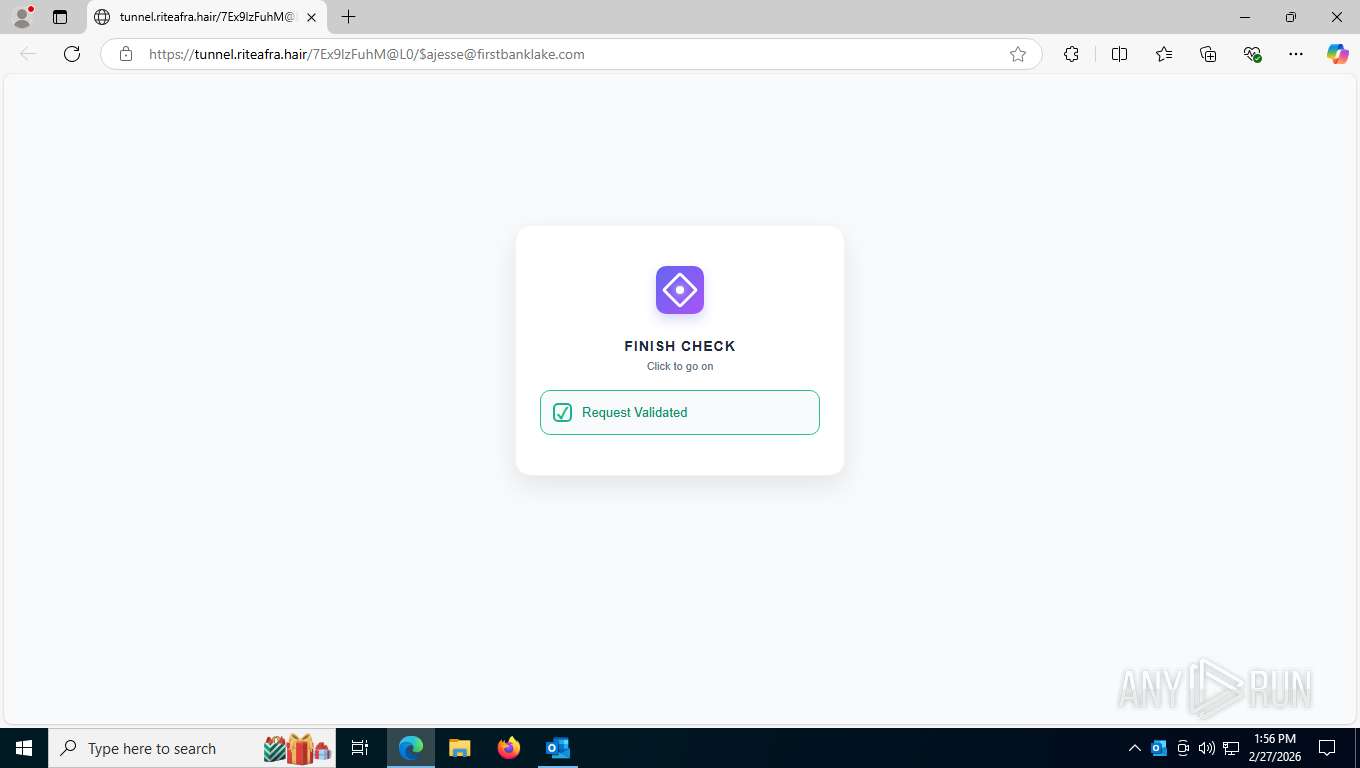
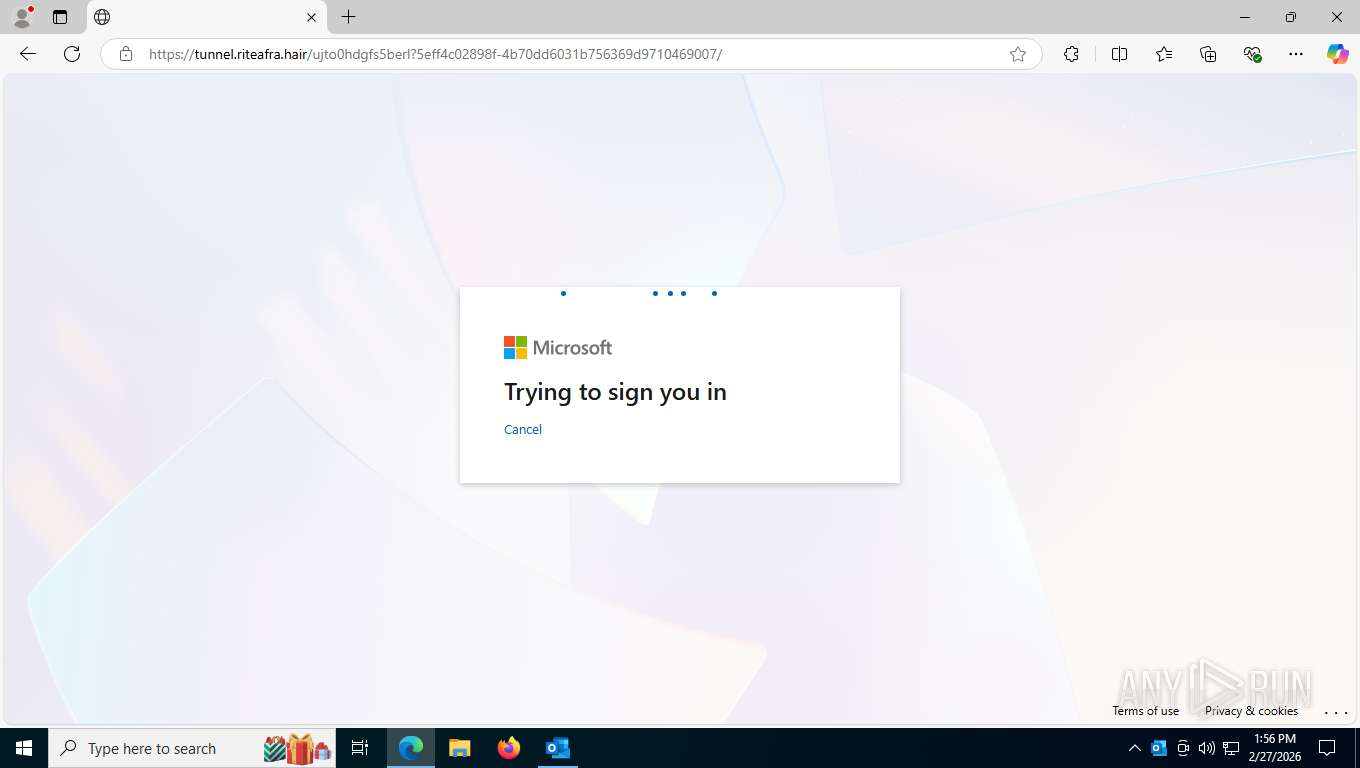
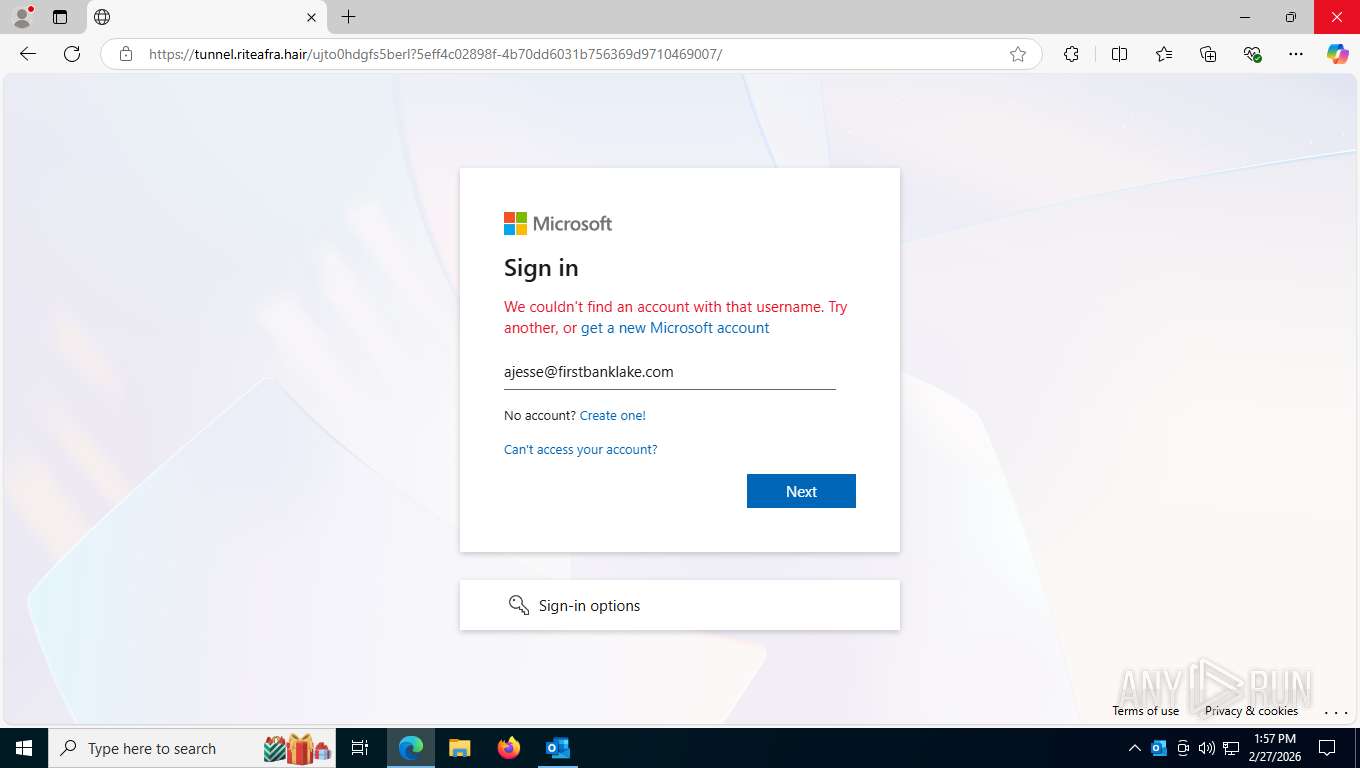
Tycoon 2FA phishing kit has been detected
- msedge.exe (PID: 3188)
Fake Microsoft Authentication Page has been detected
- msedge.exe (PID: 3188)
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 6392)
SUSPICIOUS
Page with zero-length space title
- msedge.exe (PID: 3188)
INFO
Manual execution by a user
- msedge.exe (PID: 3188)
Drops script file
- msedge.exe (PID: 3188)
- msedge.exe (PID: 8028)
Application launched itself
- msedge.exe (PID: 3188)
Reads the computer name
- identity_helper.exe (PID: 7104)
Checks supported languages
- identity_helper.exe (PID: 7104)
Reads Environment values
- identity_helper.exe (PID: 7104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
171
Monitored processes
22
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4244,i,689827236793920515,17272742473642931076,262144 --variations-seed-version --mojo-platform-channel-handle=4264 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3632,i,689827236793920515,17272742473642931076,262144 --variations-seed-version --mojo-platform-channel-handle=3680 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
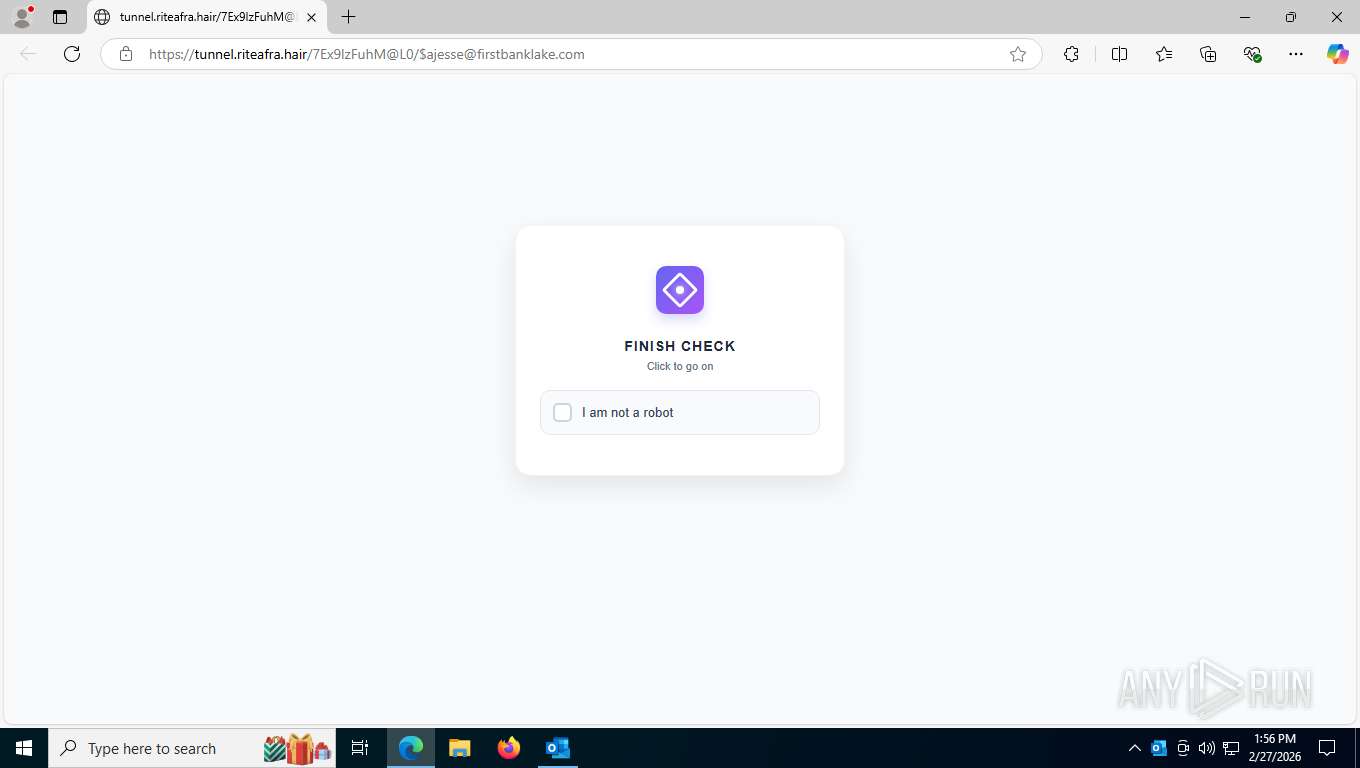
| 3188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" https://tunnel.riteafra.hair/7Ex9lzFuhM@L0/$ajesse@firstbanklake.com | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6208,i,689827236793920515,17272742473642931076,262144 --variations-seed-version --mojo-platform-channel-handle=6212 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2272,i,689827236793920515,17272742473642931076,262144 --variations-seed-version --mojo-platform-channel-handle=2268 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5400,i,689827236793920515,17272742473642931076,262144 --variations-seed-version --mojo-platform-channel-handle=5512 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5528 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1480,i,689827236793920515,17272742473642931076,262144 --variations-seed-version --mojo-platform-channel-handle=6840 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6392 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2300,i,689827236793920515,17272742473642931076,262144 --variations-seed-version --mojo-platform-channel-handle=2232 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 7104 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5840,i,689827236793920515,17272742473642931076,262144 --variations-seed-version --mojo-platform-channel-handle=5896 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 7324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5140,i,689827236793920515,17272742473642931076,262144 --variations-seed-version --mojo-platform-channel-handle=5268 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
11 892
Read events
10 765
Write events
1 006
Delete events
121
Modification events
| (PID) Process: | (7704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (7704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsData |
| Operation: | write | Name: | SessionId |
Value: 7CD02D2C-917D-4762-8007-79F23CF2B568 | |||
| (PID) Process: | (7704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (7704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | FilePath |
Value: officeclient.microsoft.com\F6133A31-CFB2-4D18-92AA-C5CCE55F91C6 | |||
| (PID) Process: | (7704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | StartDate |
Value: 50CD7DC31AA8DC01 | |||
| (PID) Process: | (7704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | EndDate |
Value: 508DE7EDE3A8DC01 | |||
| (PID) Process: | (7704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ClientTelemetry\RulesMetadata\outlook.exe\ETWMonitor\{02CAC15F-D4BE-400E-9127-D54982AA4AE9} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ClientTelemetry\RulesMetadata\outlook.exe\ETWMonitor\{11ADBD74-7DF2-4E8E-802B-B3BCBFD04A78} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ClientTelemetry\RulesMetadata\outlook.exe\ETWMonitor\{287BF315-5A11-4B2F-B069-B761ADE25A49} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ClientTelemetry\RulesMetadata\outlook.exe\ETWMonitor\{691E1C12-2693-4D4A-852C-7478657BBE6E} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
80
Text files
251
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7704 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 7704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\olk5B0E.tmp | text | |
MD5:AC8208F808E6A4B7A6F97D1BC47847AB | SHA256:93C77E3A70867EC38C6A9765F6DAB60BA98CA79459C7B9743F4B5C4239941ACD | |||
| 7704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 7704 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B76BE66D46C355931939D8CF818D03FD_30070D1E013A39CA7A94F919F7922FDF | binary | |
MD5:CAEB49ED19657D2A433342C64736EA5B | SHA256:A23D9B0ED02EDAECBB348D4426BA412D2908E3DE100087AEBF47E2D3982FDBEE | |||
| 7704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_DBE94A85F8649B4FBBEA7ED958BFE171.dat | xml | |
MD5:9CA1DA1D62A9FF574E63B8946B541C96 | SHA256:B6B10A07FAA634027F3780E77FC3B165DCF7D37E800195BFF5E147CCC492B828 | |||
| 7704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:33BA52889E1B966F7E4BAF5DBCB7A029 | SHA256:F6B8ADD8B3CA3D18C69392B6D6B8FD41A3D1CD397F93403266A9DF54114FDA42 | |||
| 7704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\F6133A31-CFB2-4D18-92AA-C5CCE55F91C6 | xml | |
MD5:9B4EC24B323252125544E6B94787AE5F | SHA256:51E994E0A5BBE544837C5858AA447E9B1C8E9B2D58D0EB0A9ED88F645D37CA01 | |||
| 7704 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_EAF5D55D93603A879FA973006301F24F | binary | |
MD5:79F30DA0EDB8D9D6701584F9CE5A995F | SHA256:865DF5D655A99D05EAA692335F664FF264D8F45EF076D0611F437432635E80CA | |||
| 7704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\5475cb191e478c39370a215b2da98a37e9dc813d.tbres | binary | |
MD5:142651C4E9A131B42823EF071CBBFE0D | SHA256:8C4D0A1FFB1188065DA3F675F5C0EC0ACA4509DE8C1F6B9DA97D5C2BA0F8D5DB | |||
| 7704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:FEF631787076BD74E7D74D7C9EC7E104 | SHA256:E7B7C311672B006515616F08D1881B5B81DF83A7C6A455633182D6EA1164F654 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
101
TCP/UDP connections
74
DNS requests
67
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
7704 | OUTLOOK.EXE | GET | 200 | 52.110.17.63:443 | https://officeclient.microsoft.com/config16/?lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3 | unknown | xml | 187 Kb | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
7704 | OUTLOOK.EXE | GET | 200 | 52.123.129.14:443 | https://ecs.office.com/config/v2/Office/outlook/16.0.16026.20146/Production/CC?&Clientid=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&Application=outlook&Platform=win32&Version=16.0.16026.20146&MsoVersion=16.0.16026.20002&SDX=fa000000002.2.0.1907.31003&SDX=fa000000005.1.0.1909.30011&SDX=fa000000006.1.0.1909.13002&SDX=fa000000008.1.0.1908.16006&SDX=fa000000009.1.0.1908.6002&SDX=fa000000016.1.0.1810.13001&SDX=fa000000029.1.0.1906.25001&SDX=fa000000033.1.0.1908.24001&SDX=wa104381125.1.0.1810.9001&ProcessName=outlook.exe&Audience=Production&Build=ship&Architecture=x64&Language=en-US&SubscriptionLicense=false&PerpetualLicense=2019&LicenseCategory=6&LicenseSKU=Professional2019Retail&OsVersion=10.0&OsBuild=19045&Channel=CC&InstallType=C2R&SessionId=%7b7CD02D2C-917D-4762-8007-79F23CF2B568%7d&LabMachine=false | unknown | text | 346 Kb | unknown |
7704 | OUTLOOK.EXE | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAsMayxGaRewR3PGR9SvwMg%3D | unknown | — | — | whitelisted |
7704 | OUTLOOK.EXE | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBR0TBEVYklX7A9yLoLD9hqmCWDxFgQU3pGGSLehMVkx8UtfB6nciHnaqHYCEzMAAAAPMyBlN%2B5Crk8AAAAAAA8%3D | unknown | — | — | whitelisted |
7704 | OUTLOOK.EXE | POST | 200 | 52.110.17.26:443 | https://roaming.svc.cloud.microsoft/rs/RoamingSoapService.svc | unknown | — | 654 b | unknown |
7704 | OUTLOOK.EXE | GET | 200 | 95.101.27.171:443 | https://omex.cdn.office.net/addinclassifier/officesharedentities | unknown | text | 314 Kb | whitelisted |
7704 | OUTLOOK.EXE | GET | 200 | 52.111.243.12:443 | https://messaging.lifecycle.office.com/getcustommessage16?app=6&ui=en-US&src=BizBar&messagetype=BizBar&hwid=04111-083-043729&ver=16.0.16026&lc=en-US&platform=10%3A0%3A19045%3A2%3A0%3A0%3A256%3A1%3A&productid=%7B1717C1E0-47D3-4899-A6D3-1022DB7415E0%7D%3A00411-10830-43729-AA720%3AOffice%2019%2C%20Office19Professional2019R_Retail%20edition&clientsessionid=%7B7CD02D2C-917D-4762-8007-79F23CF2B568%7D&datapropertybag=%7B%22Audience%22%3A%22Production%22%2C%22AudienceGroup%22%3A%22Production%22%2C%22AudienceChannel%22%3A%22CC%22%2C%22Flight%22%3A%22ofsh6c2b1tla1a31%2Cofcrui4yvdulbf31%2Cofhpex3jznepoo31%2Cofpioygfqmufst31%22%7D | unknown | text | 542 b | unknown |
7704 | OUTLOOK.EXE | POST | 200 | 135.225.150.15:443 | https://editor.svc.cloud.microsoft/NlEditor/CloudSuggest/V1 | unknown | text | 155 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7228 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.138:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.16.204.137:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.svc.cloud.microsoft |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1324 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
6392 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Tycoon2FA related URL pattern observed (tilda-variant) |
6392 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6392 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6392 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspicious sending of an email address as an unencrypted POST request |
6392 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Tycoon related URL chain observed |
6392 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6392 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6392 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6392 | msedge.exe | Misc activity | INFO [ANY.RUN] External IP Lookup Service DNS query (ipbase .com) |