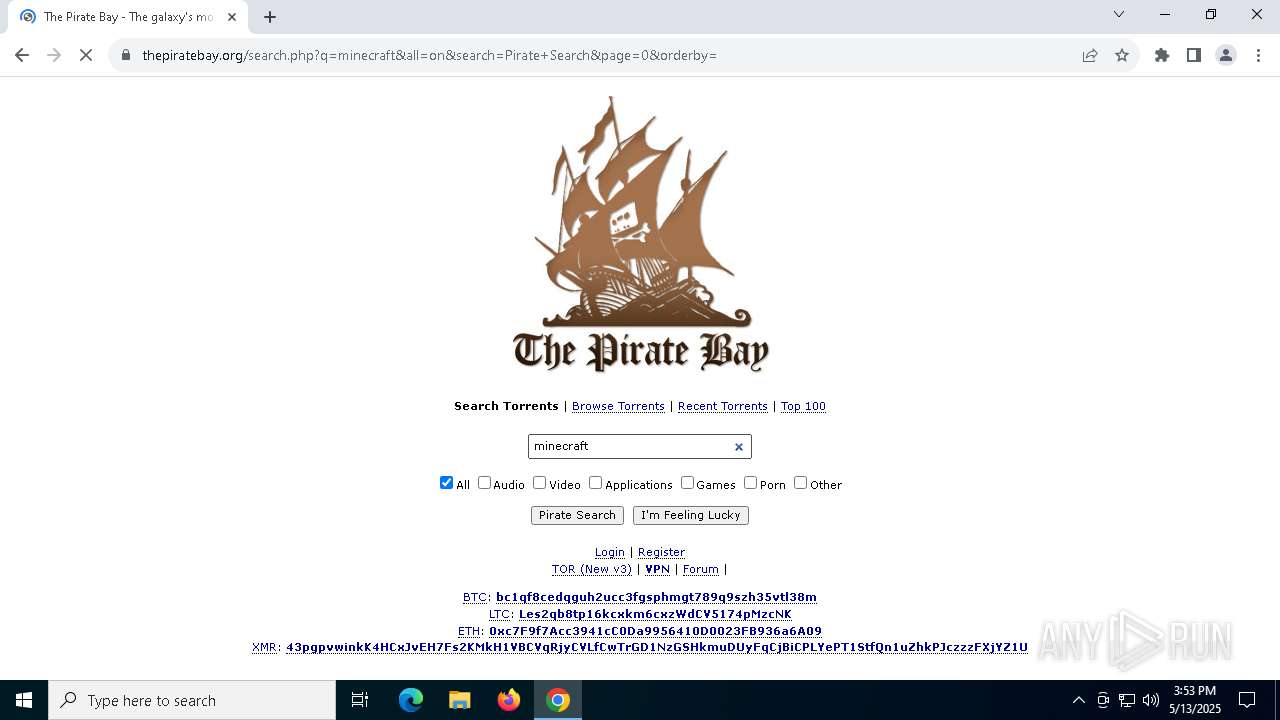
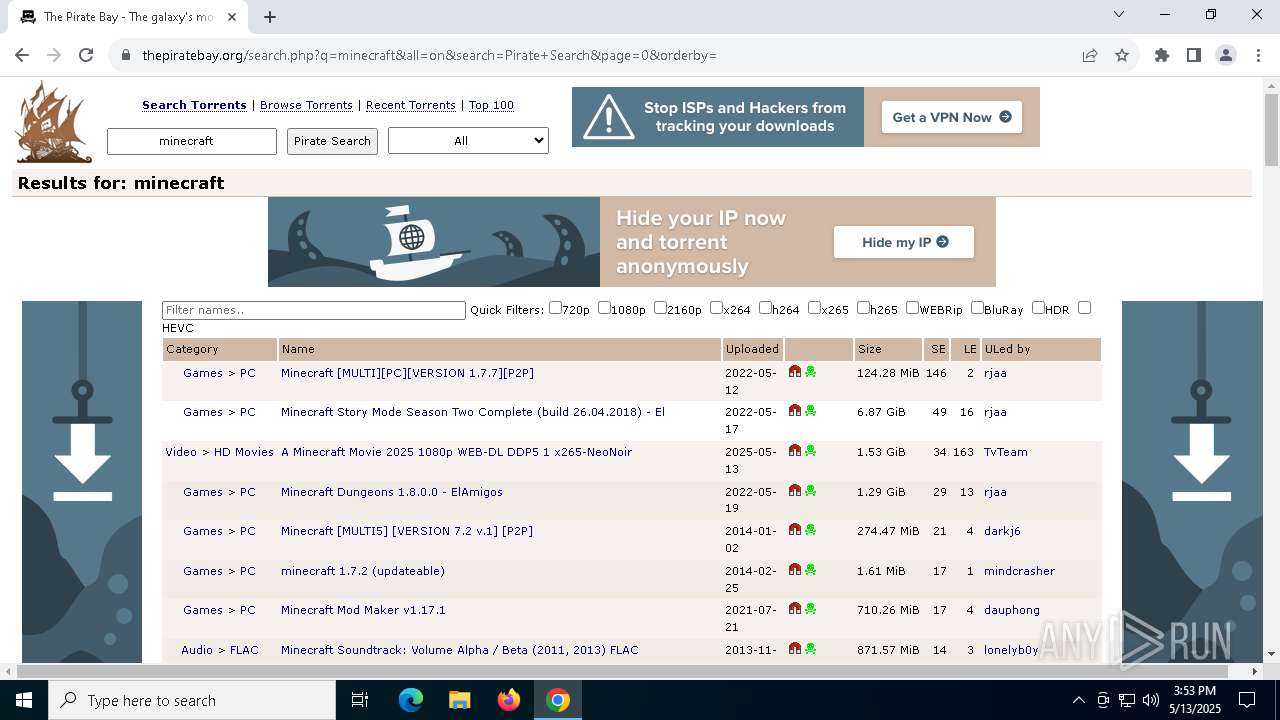
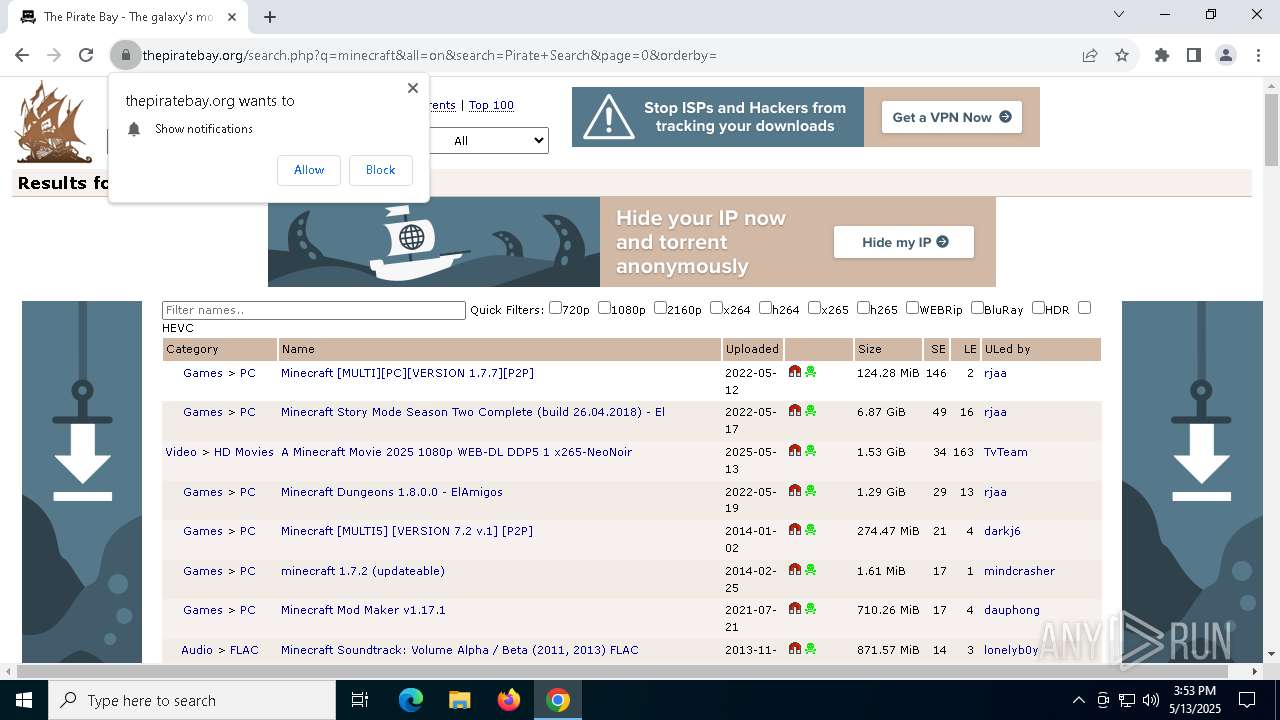
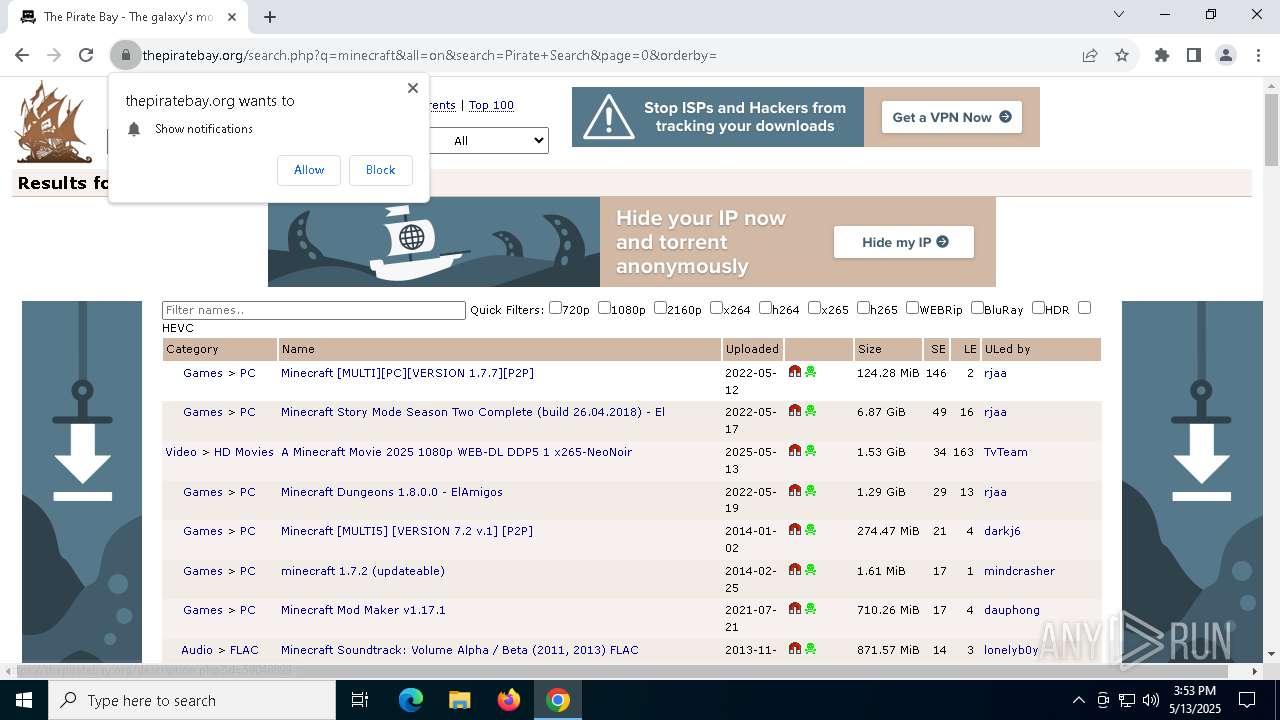
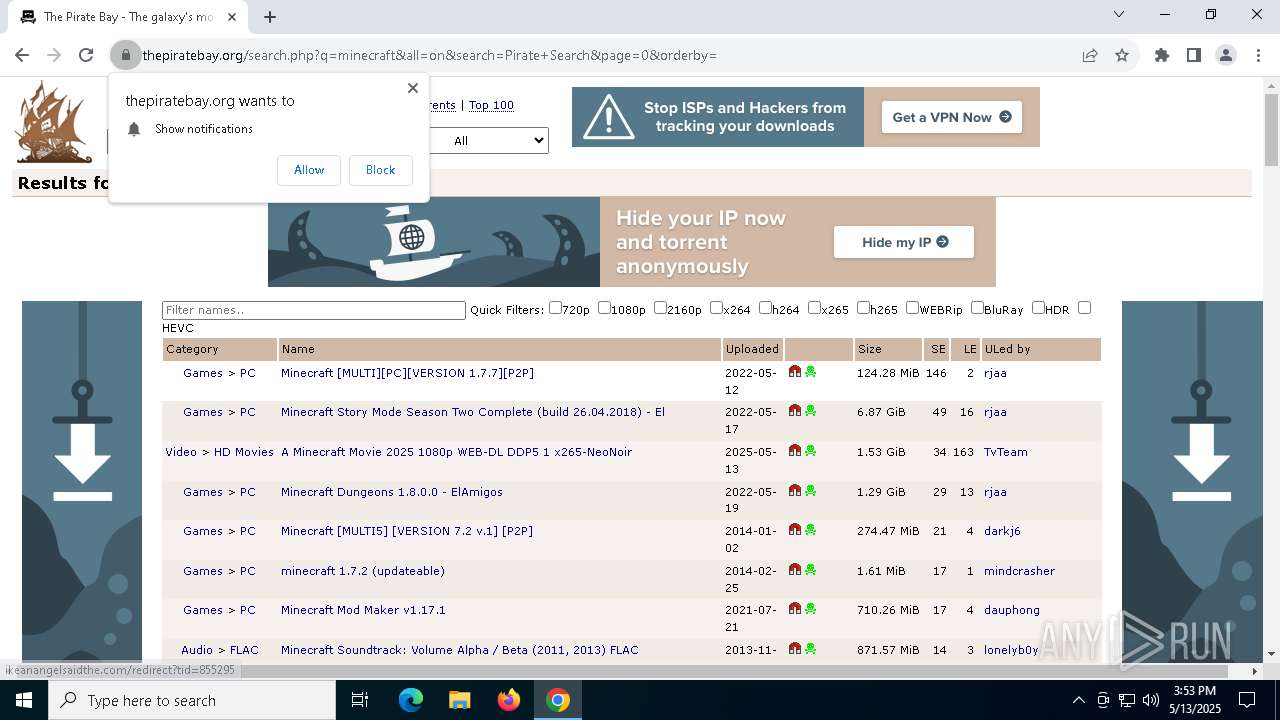
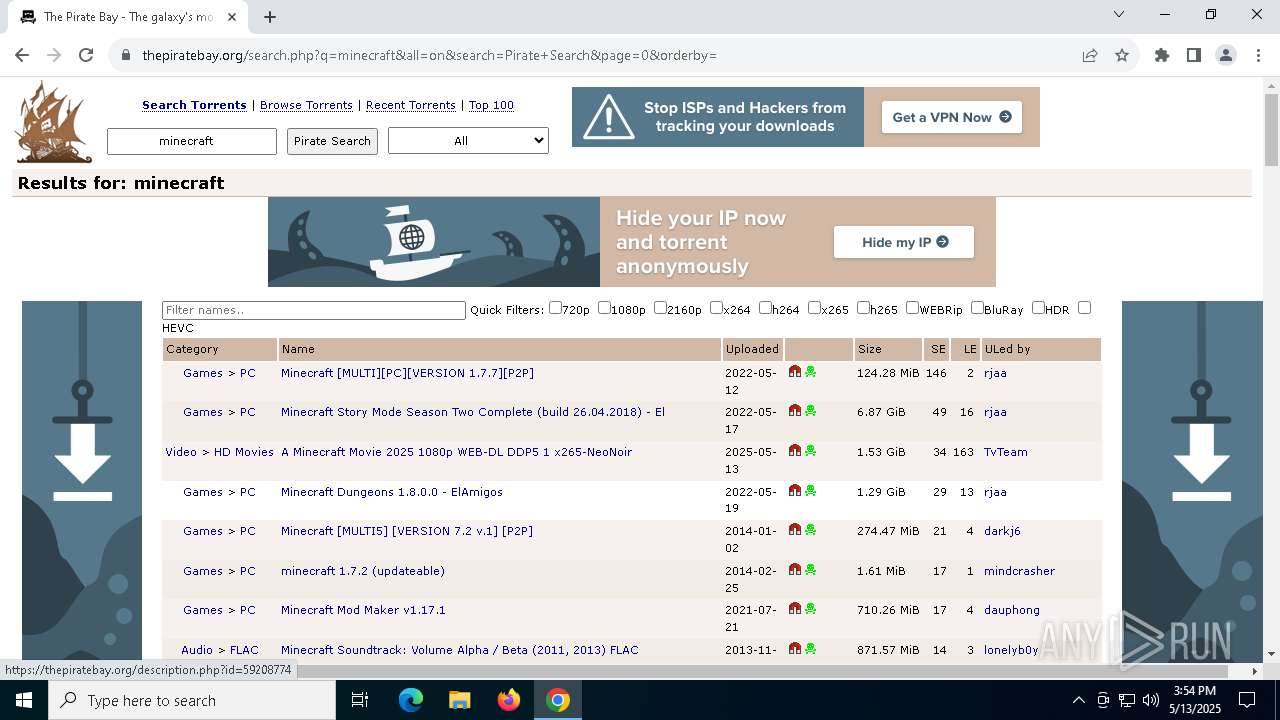
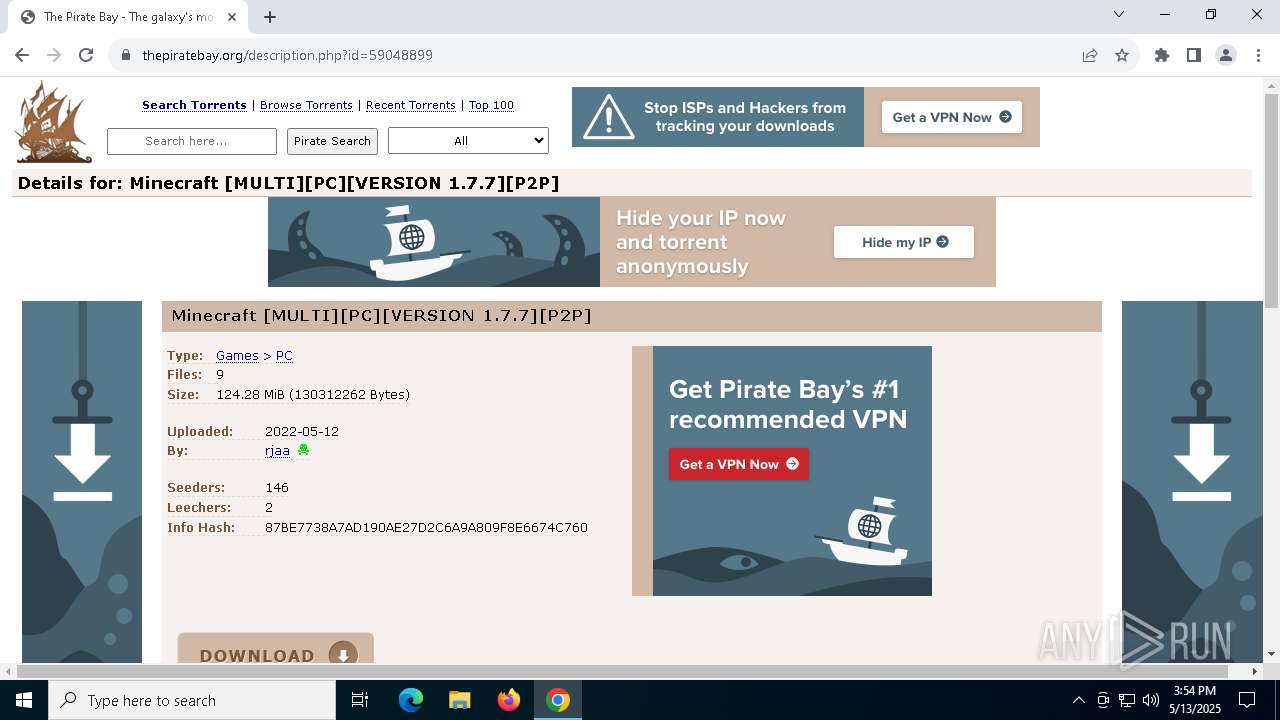
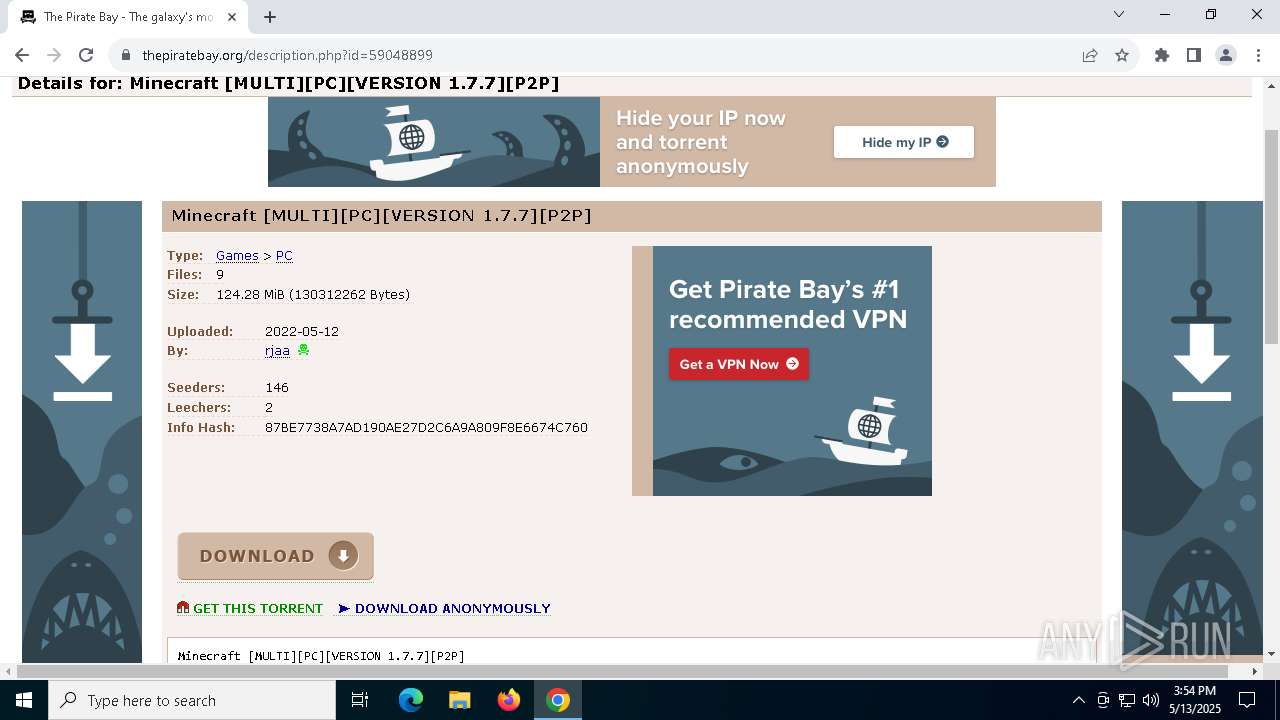
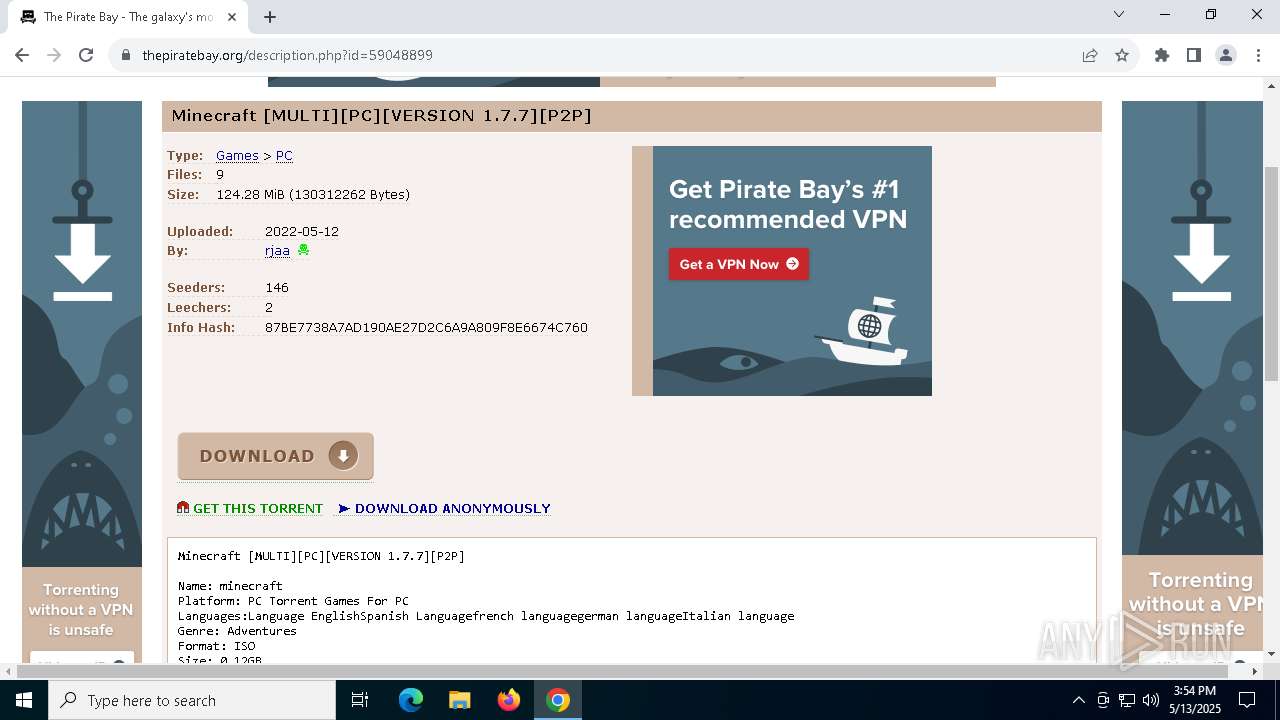
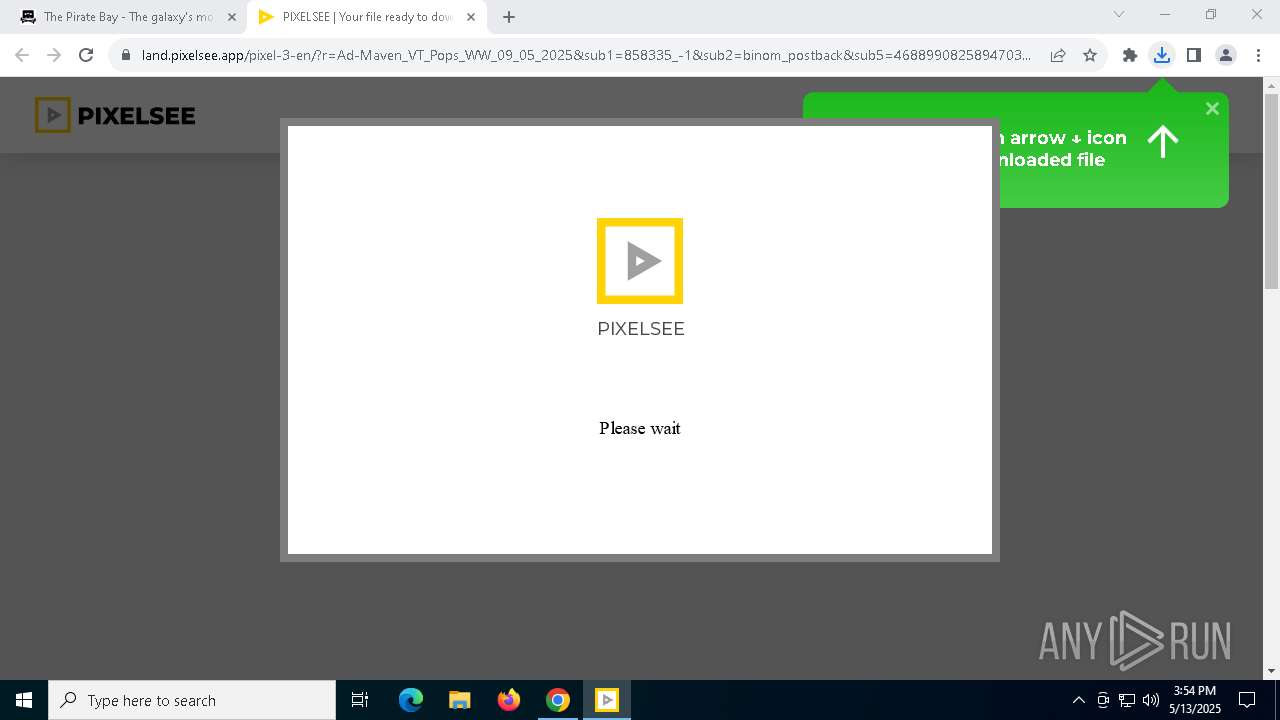
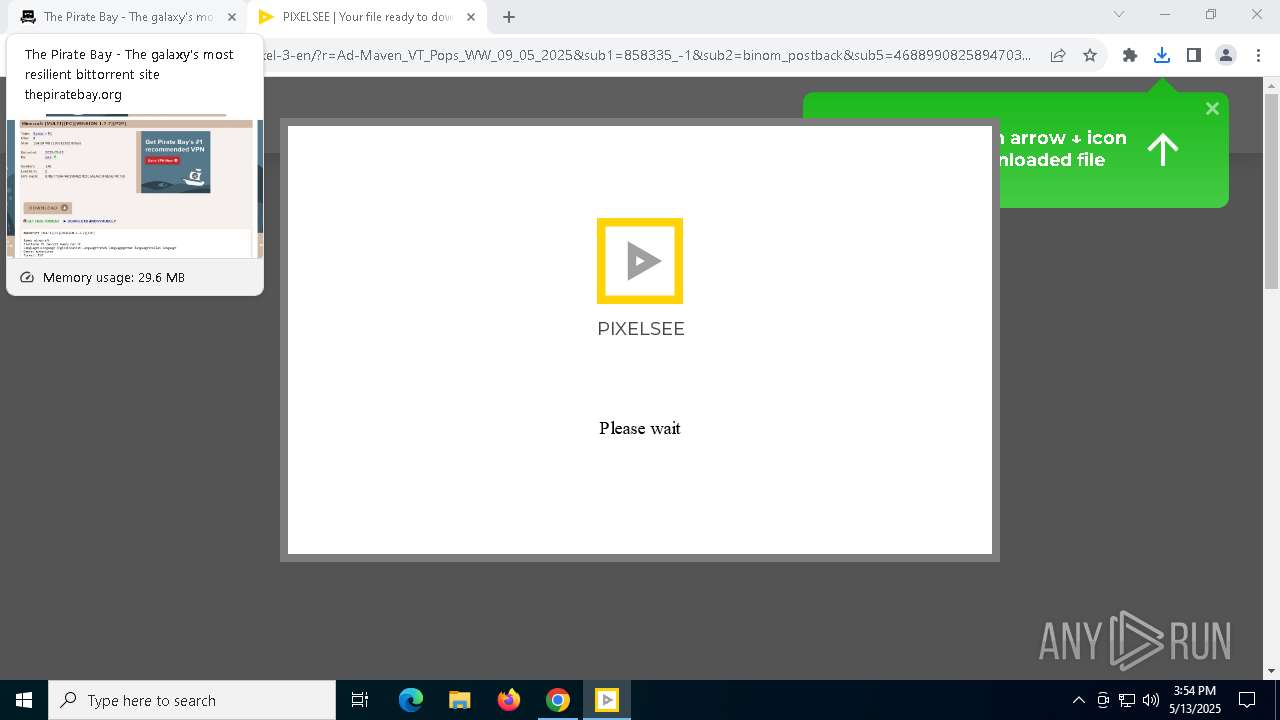
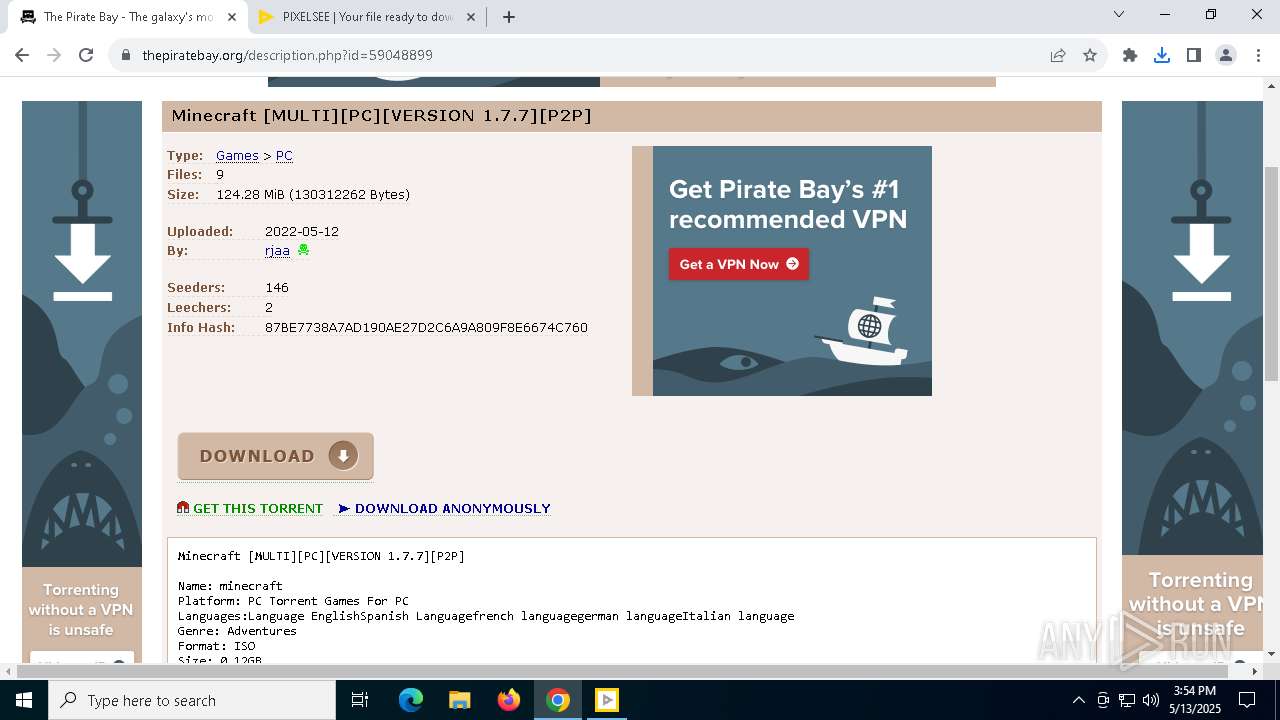
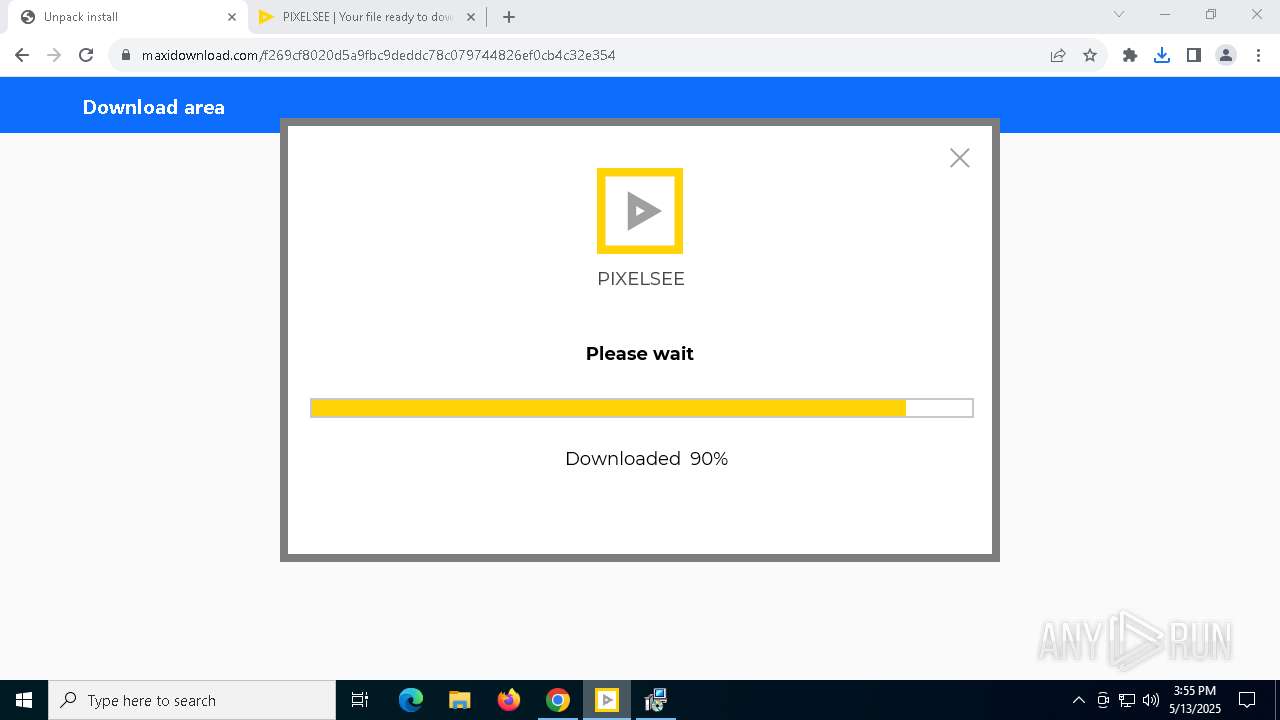
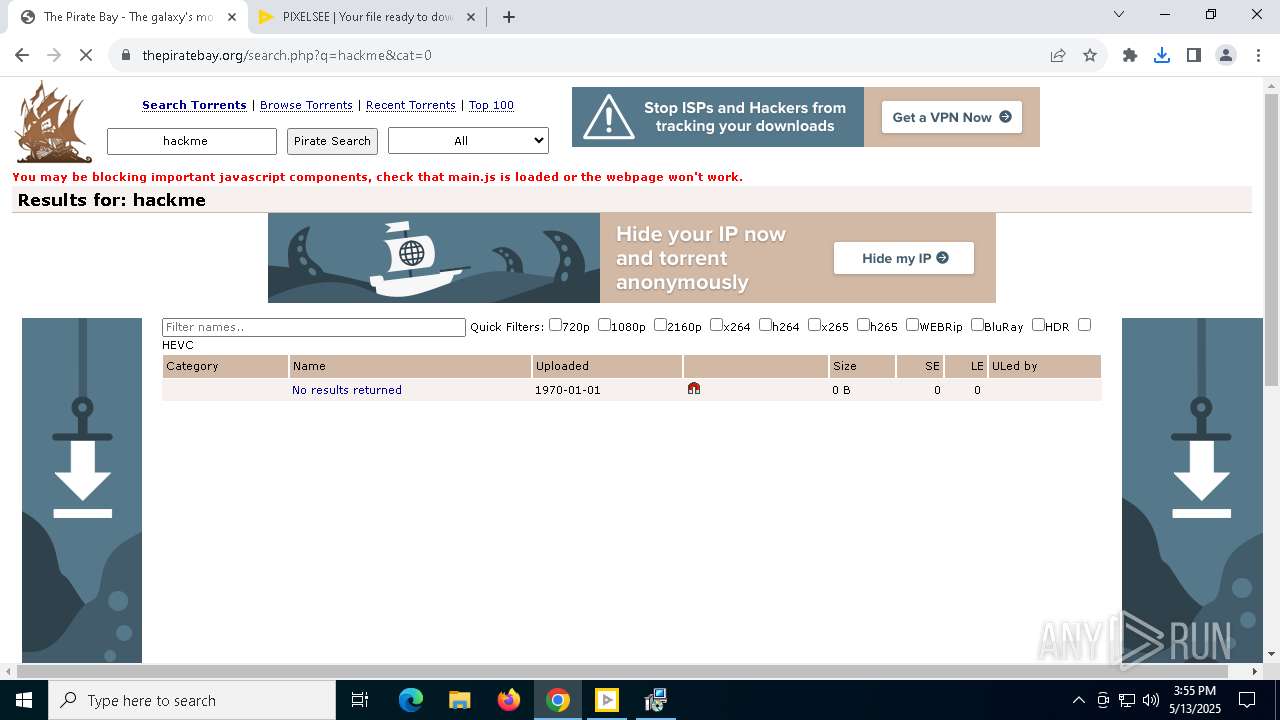
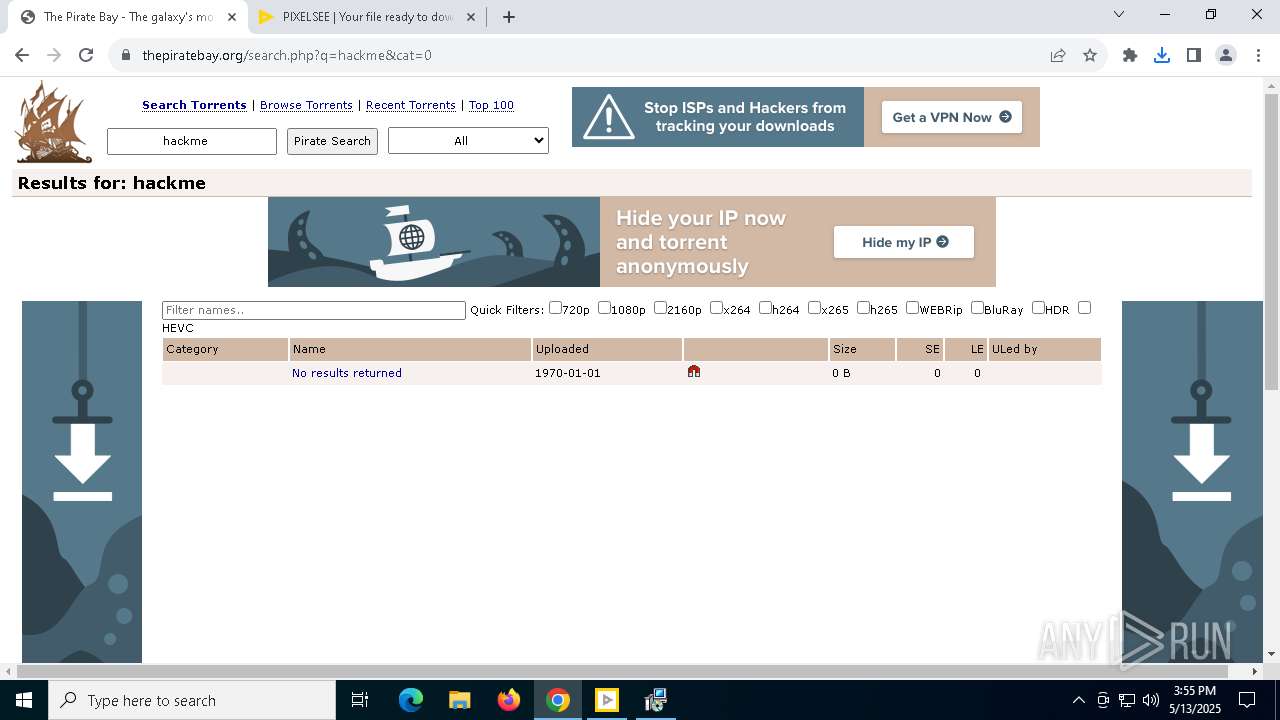
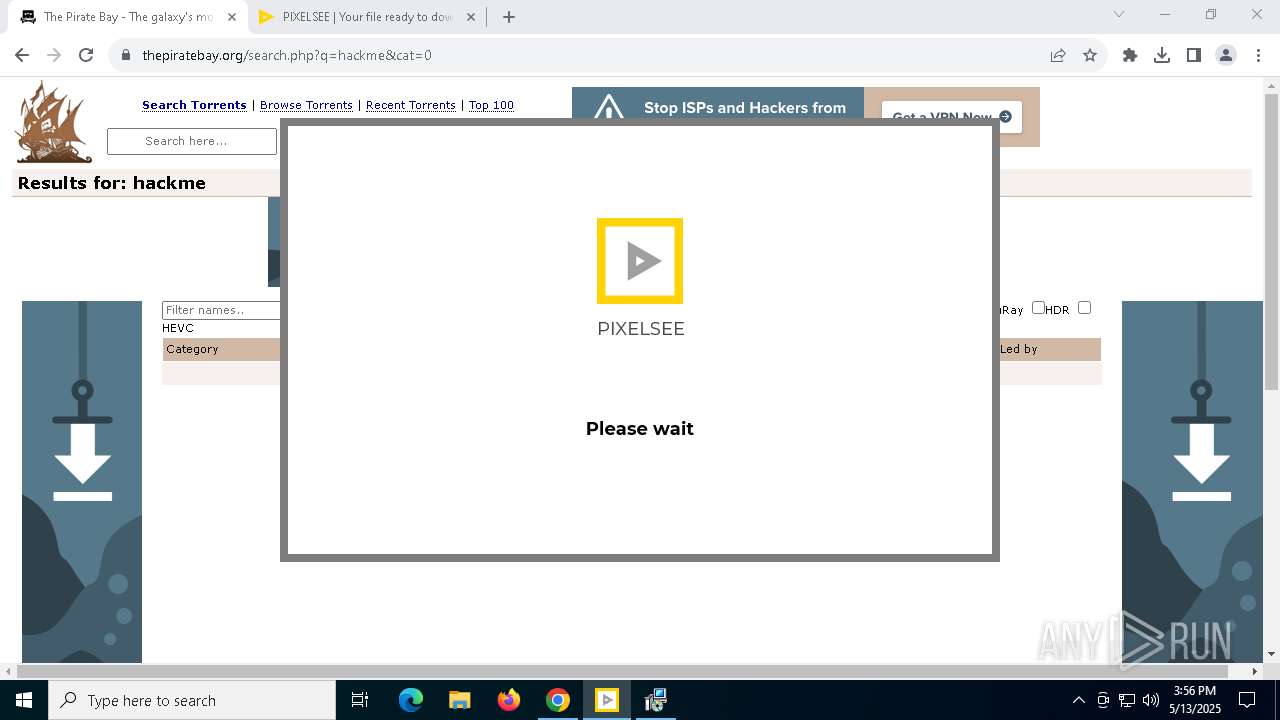
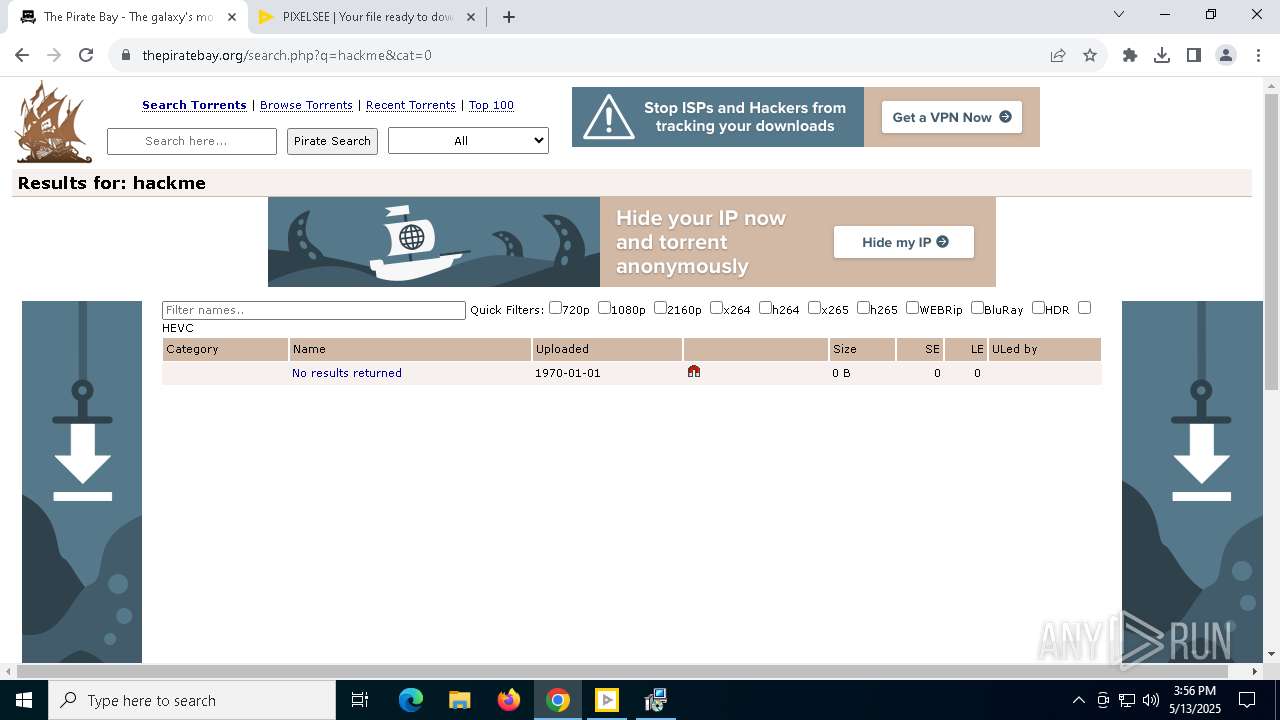
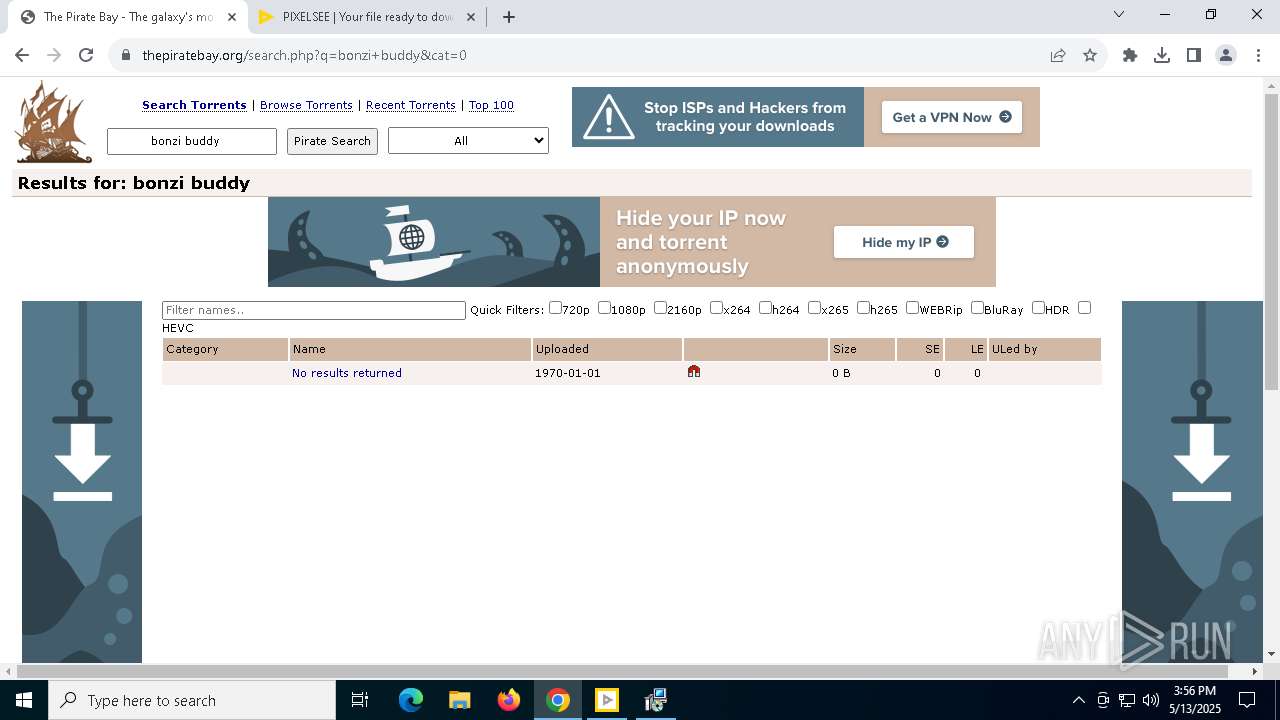
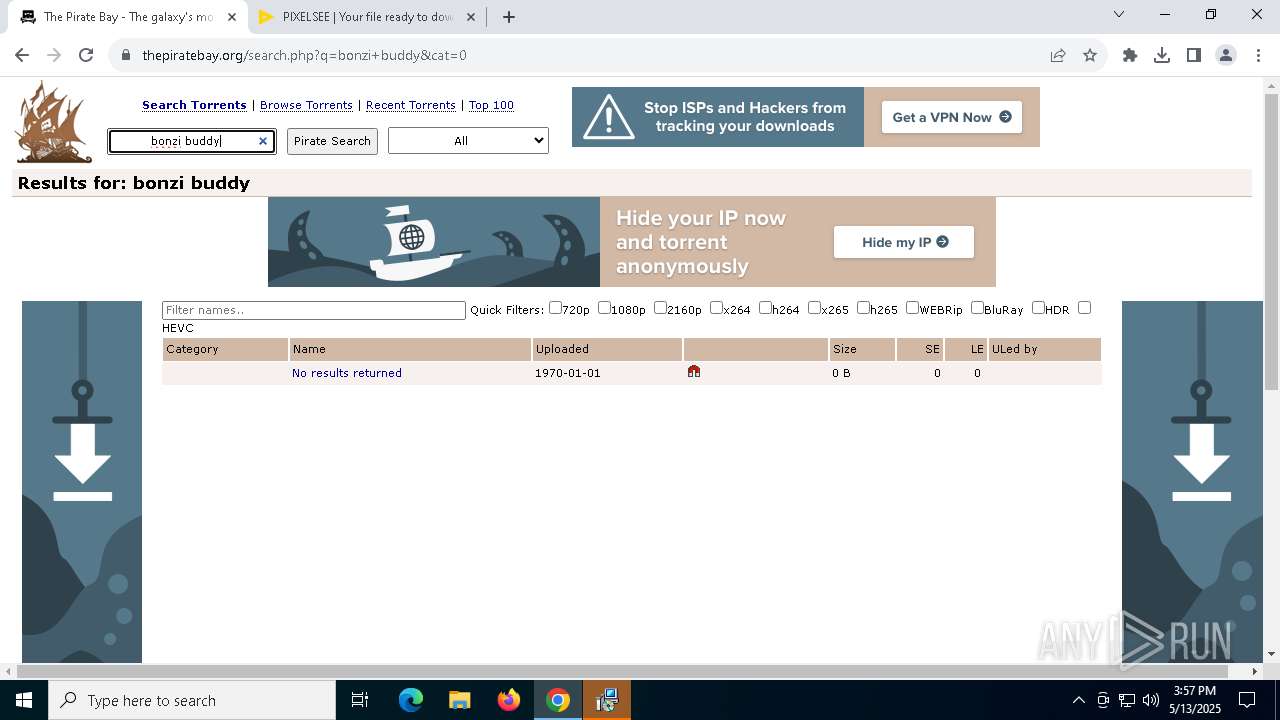
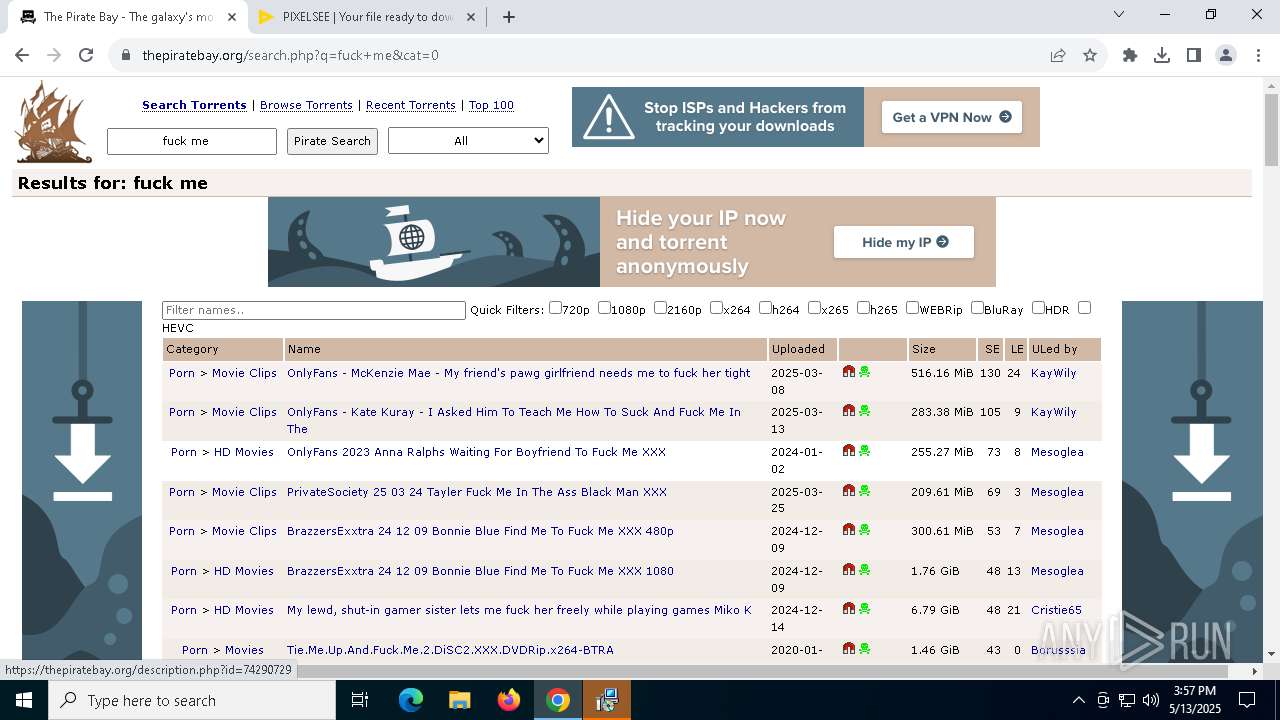
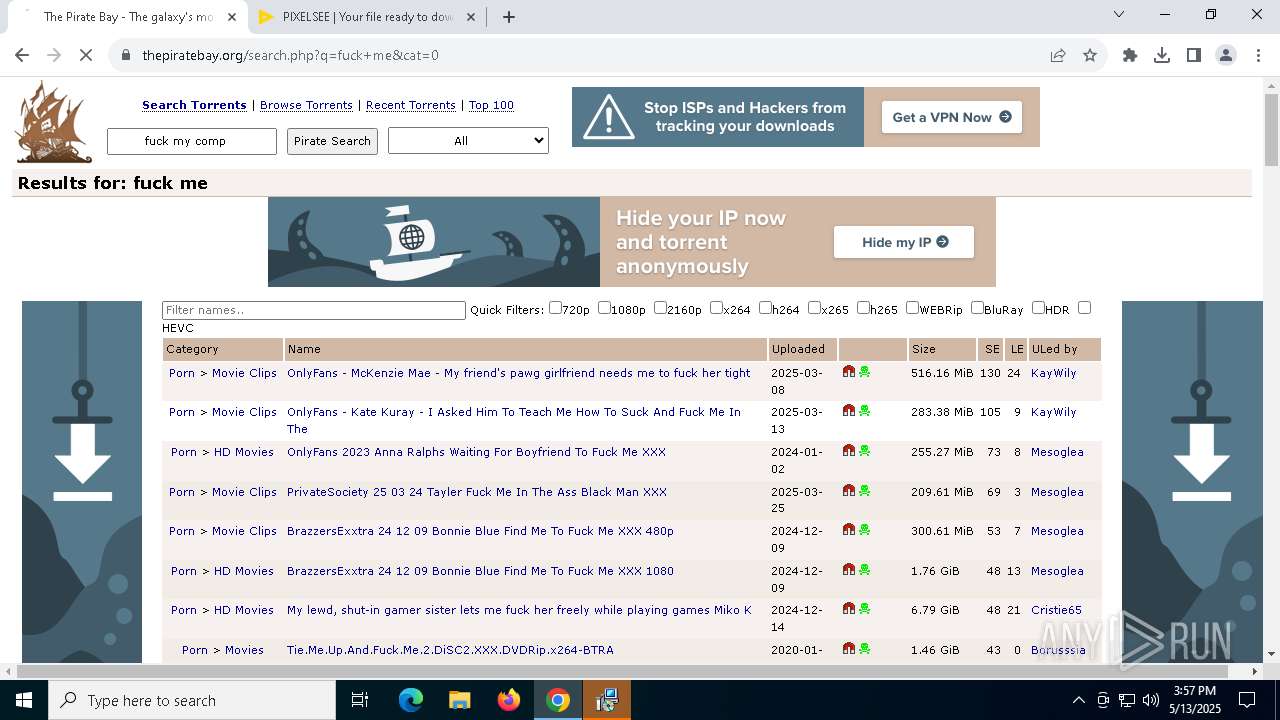
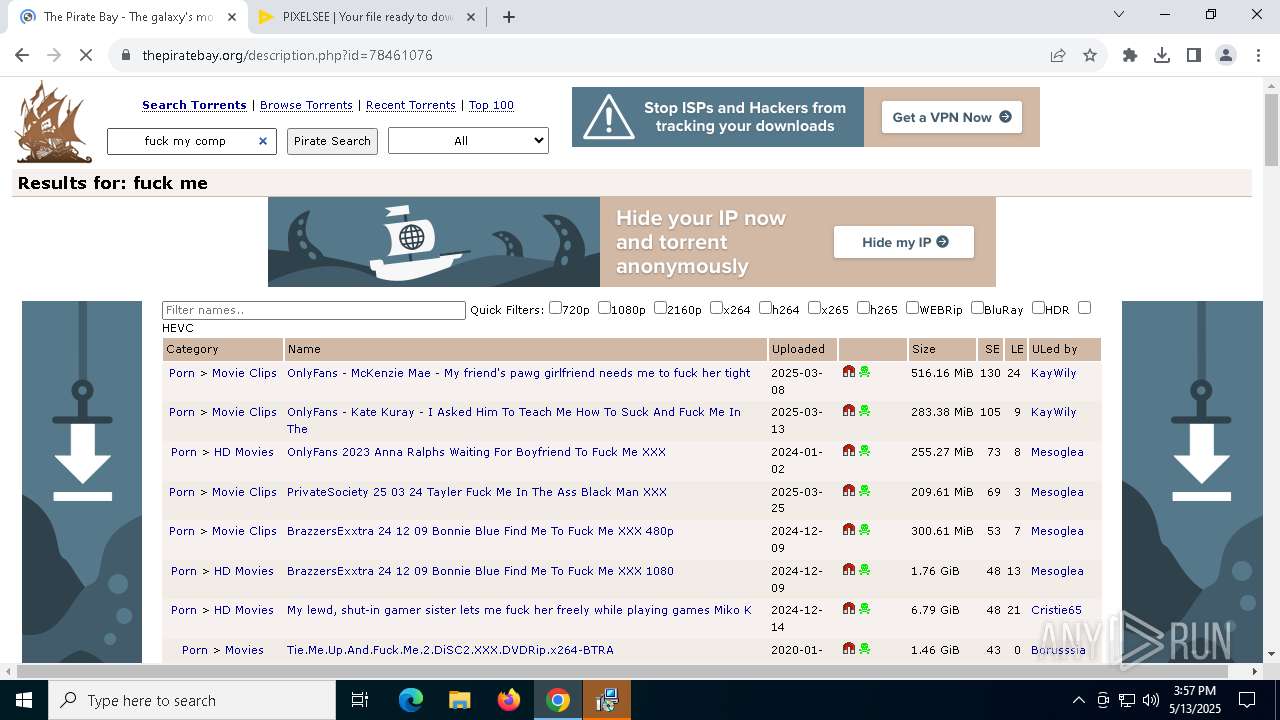
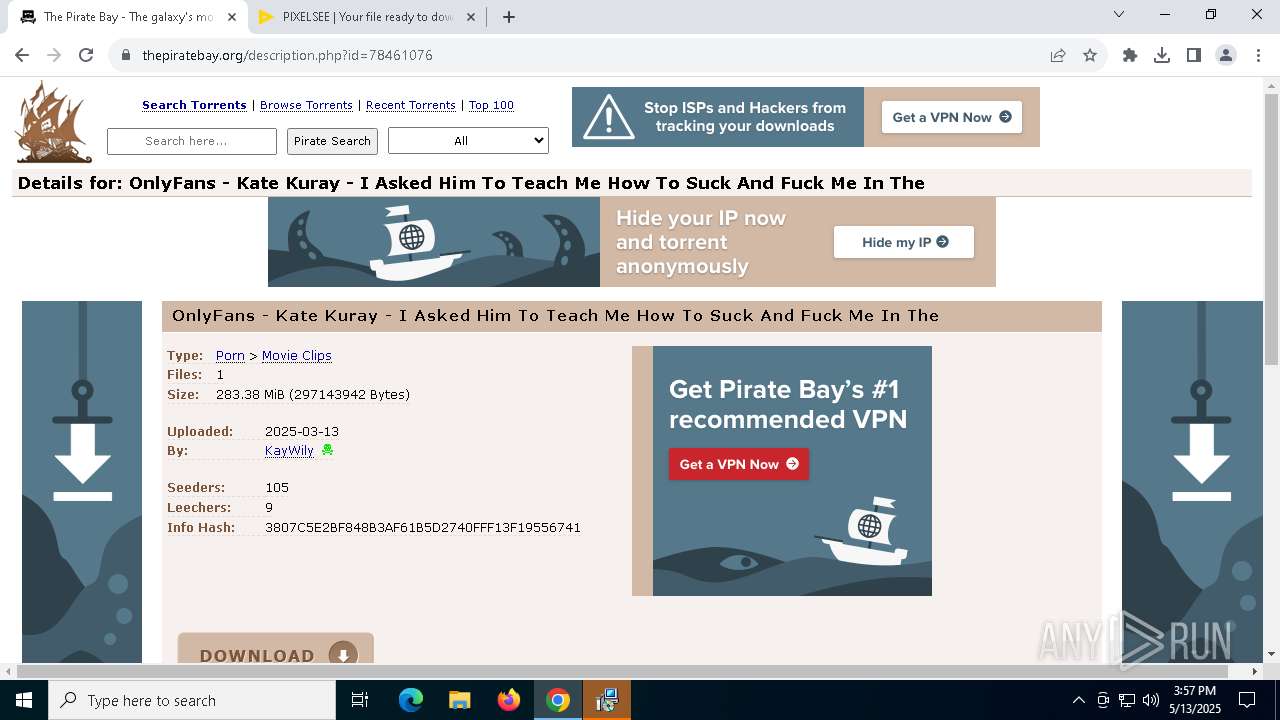
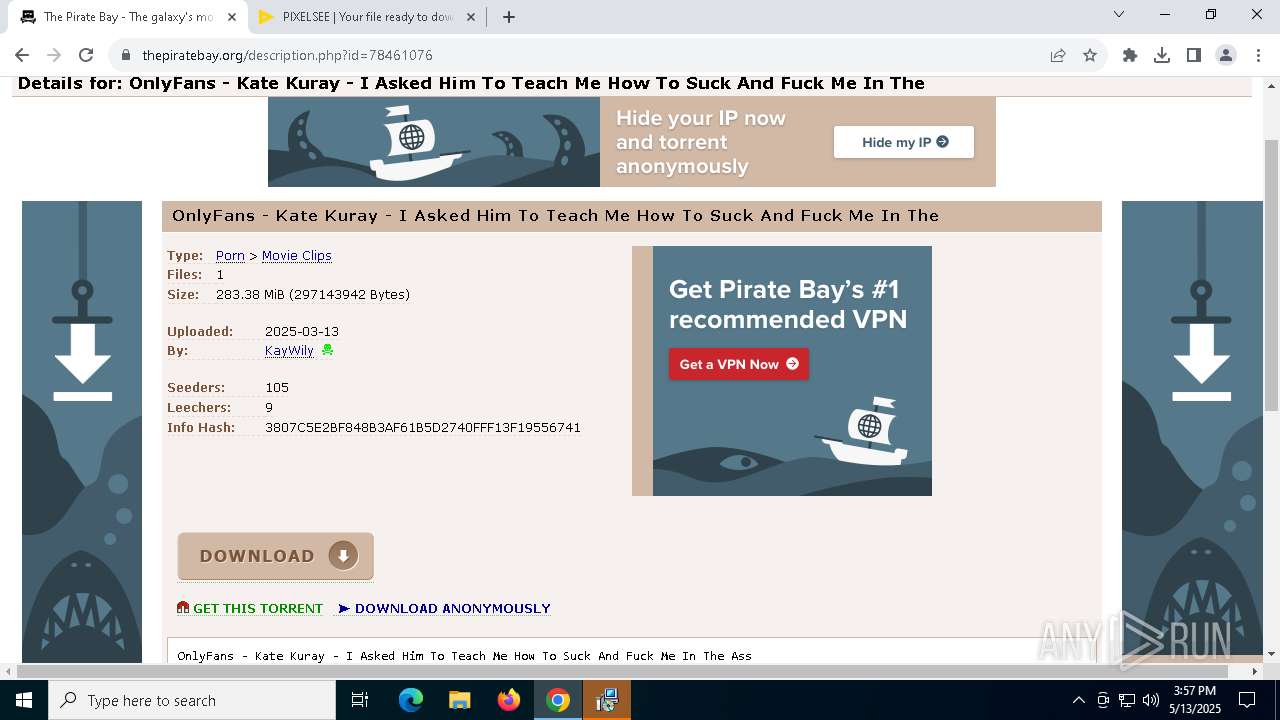
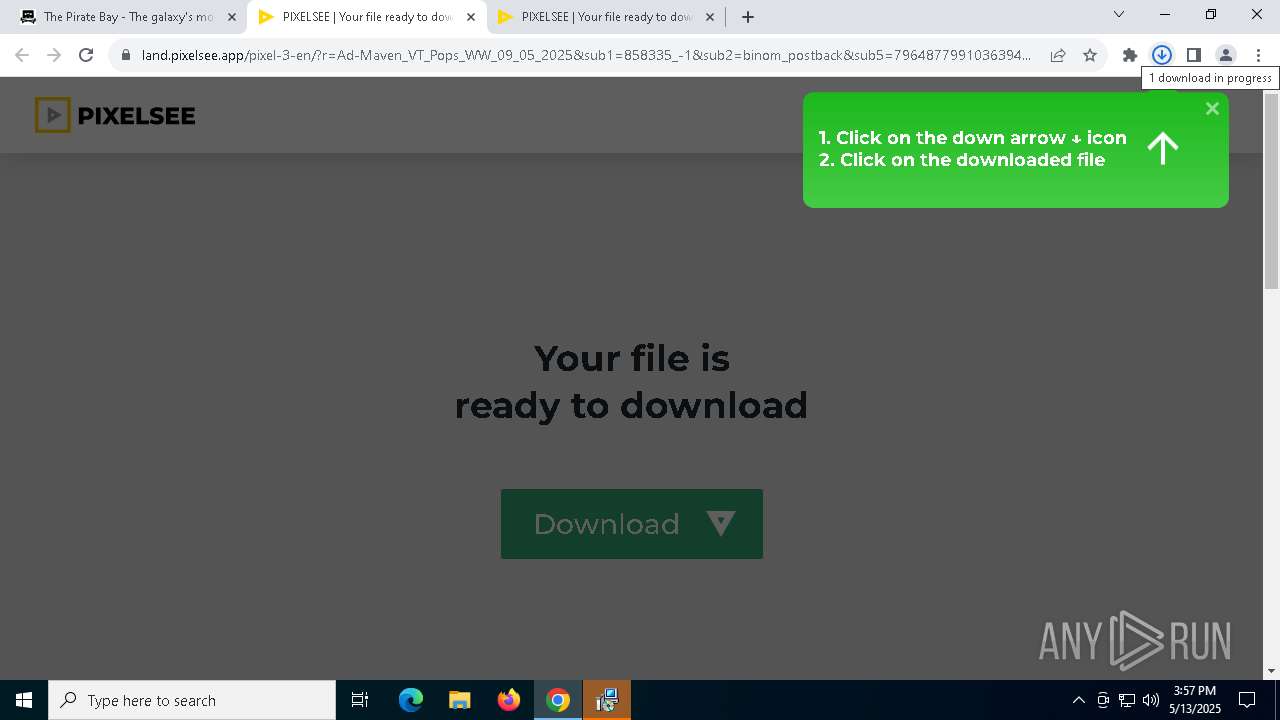
| URL: | https://thepiratebay.org/ |
| Full analysis: | https://app.any.run/tasks/8e329123-18c3-4e36-83f4-83239cf2803e |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 13, 2025, 15:53:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
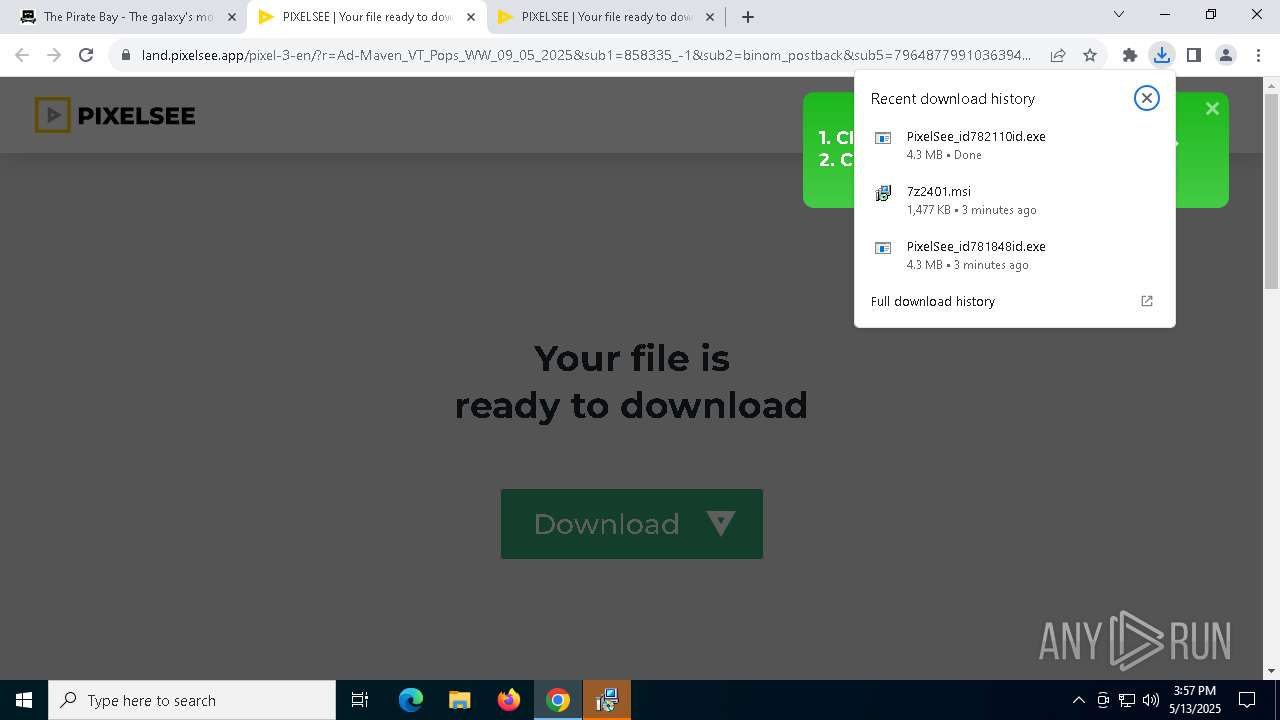
| MD5: | A0995E927E0013AEF96792F170D82E89 |
| SHA1: | 3D4FB249C5BDC1CD42C628B9C14EB88328C77065 |
| SHA256: | 517FBCAA033952F98E173E27E58ED4832C4AA72B8F270D018B8818965F76E0CC |
| SSDEEP: | 3:N8FAV0MJ:27W |
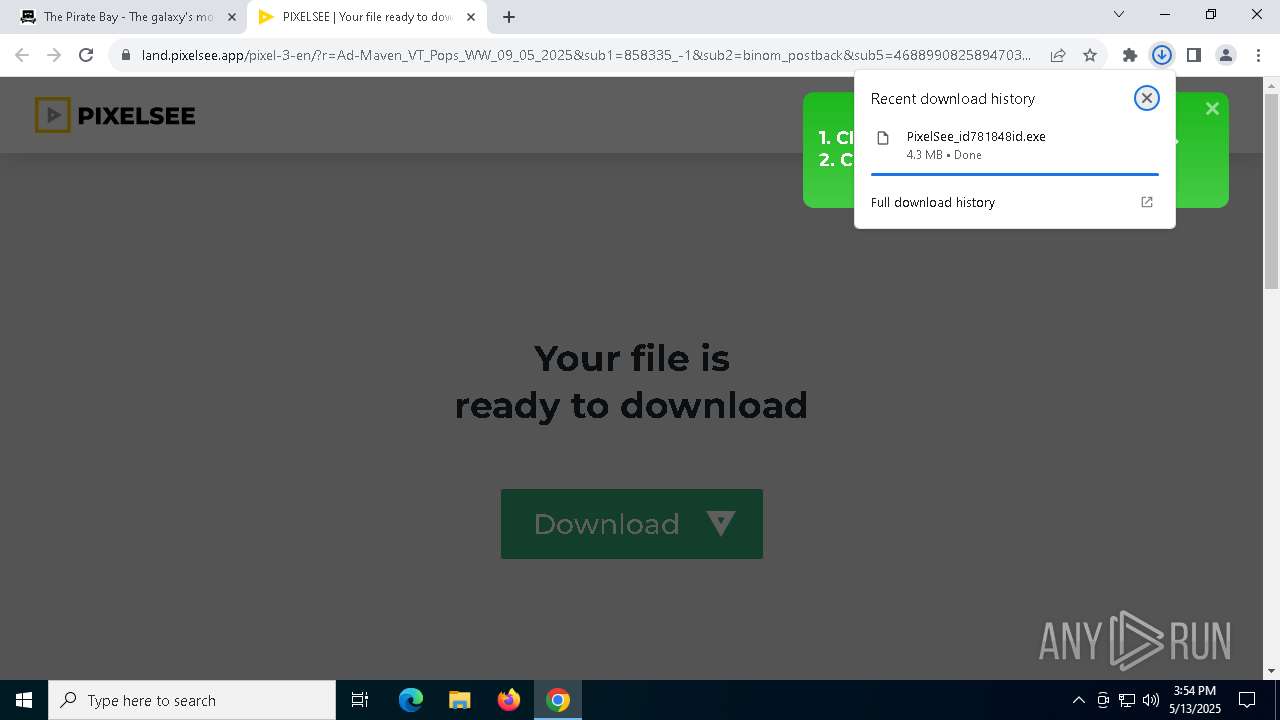
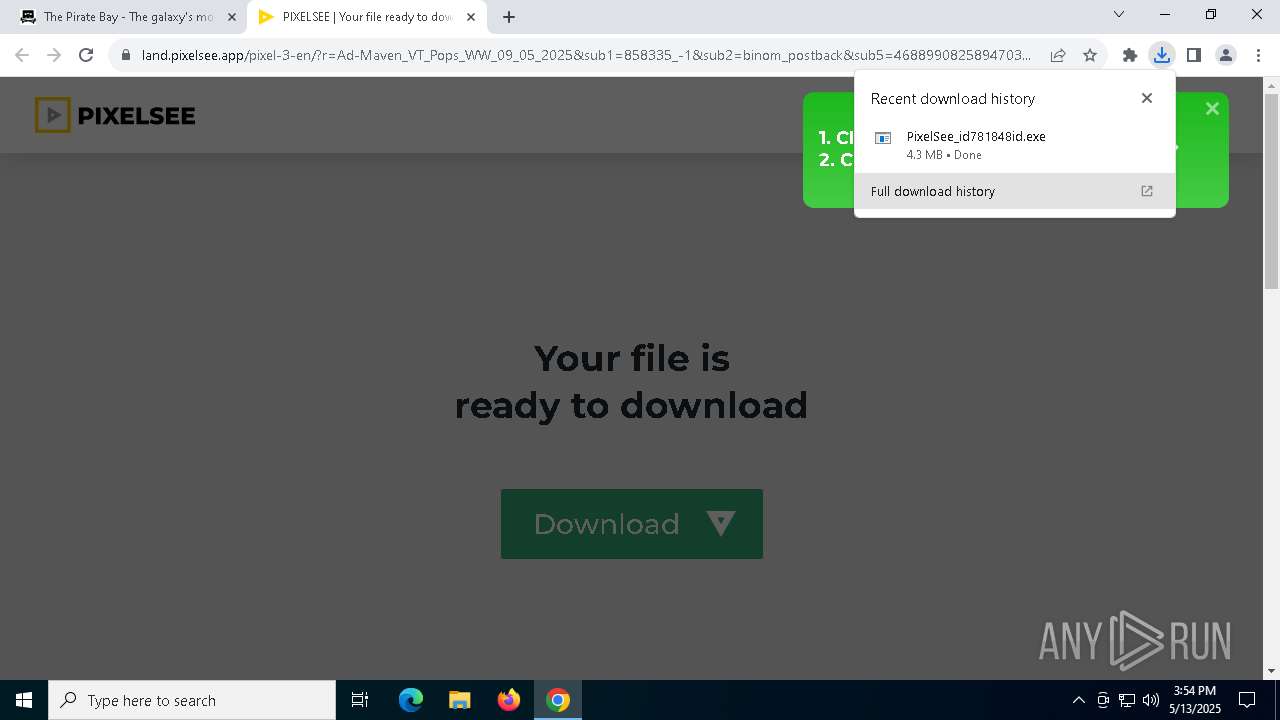
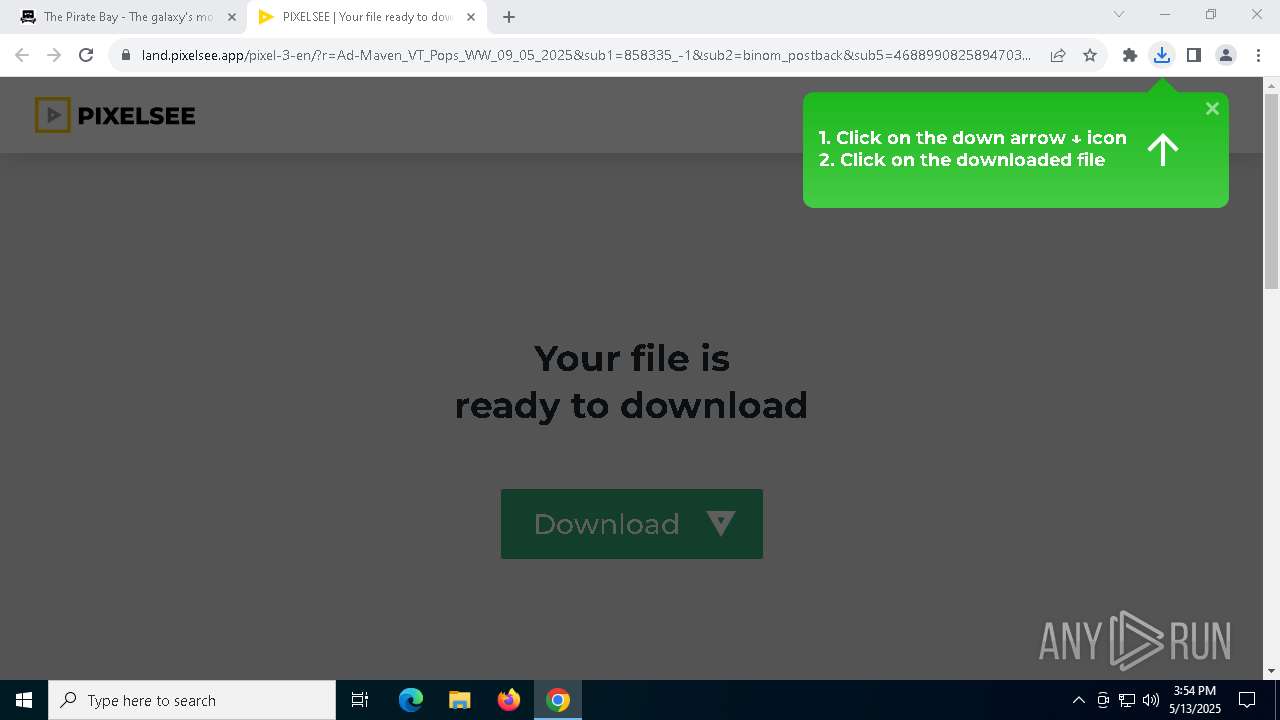
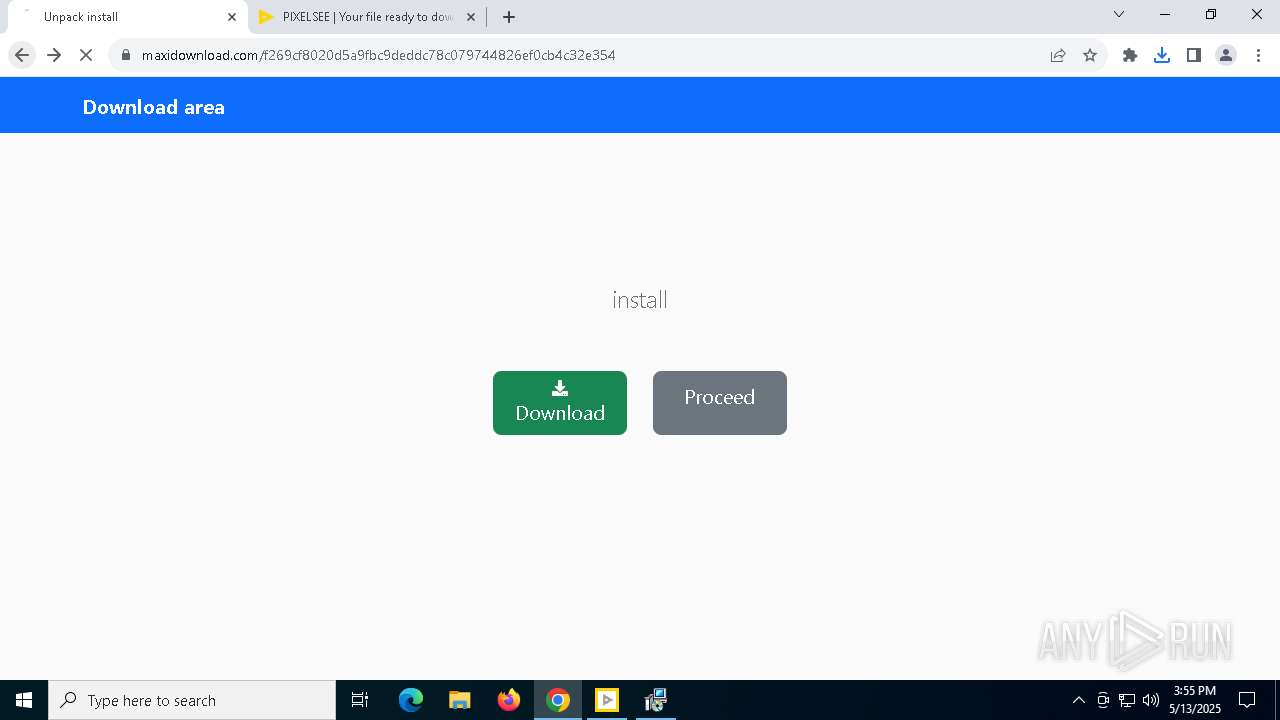
MALICIOUS
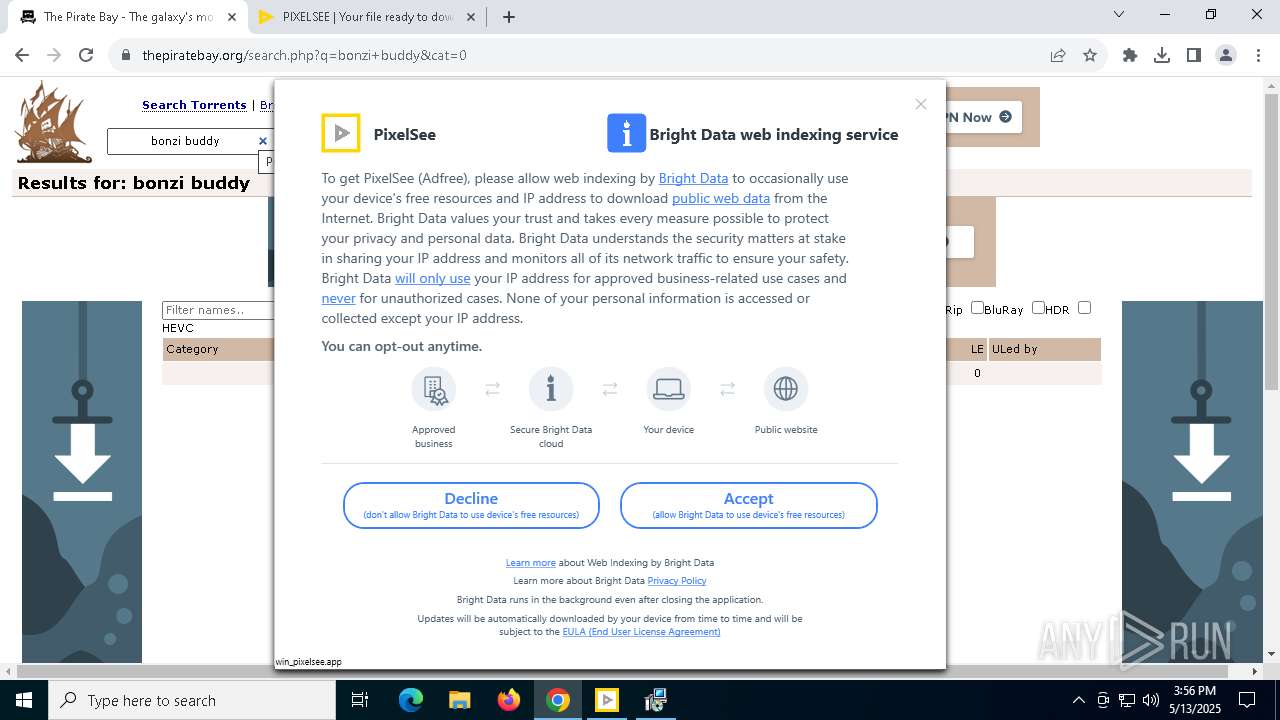
AMADEY has been found (auto)
- chrome.exe (PID: 7672)
Actions looks like stealing of personal data
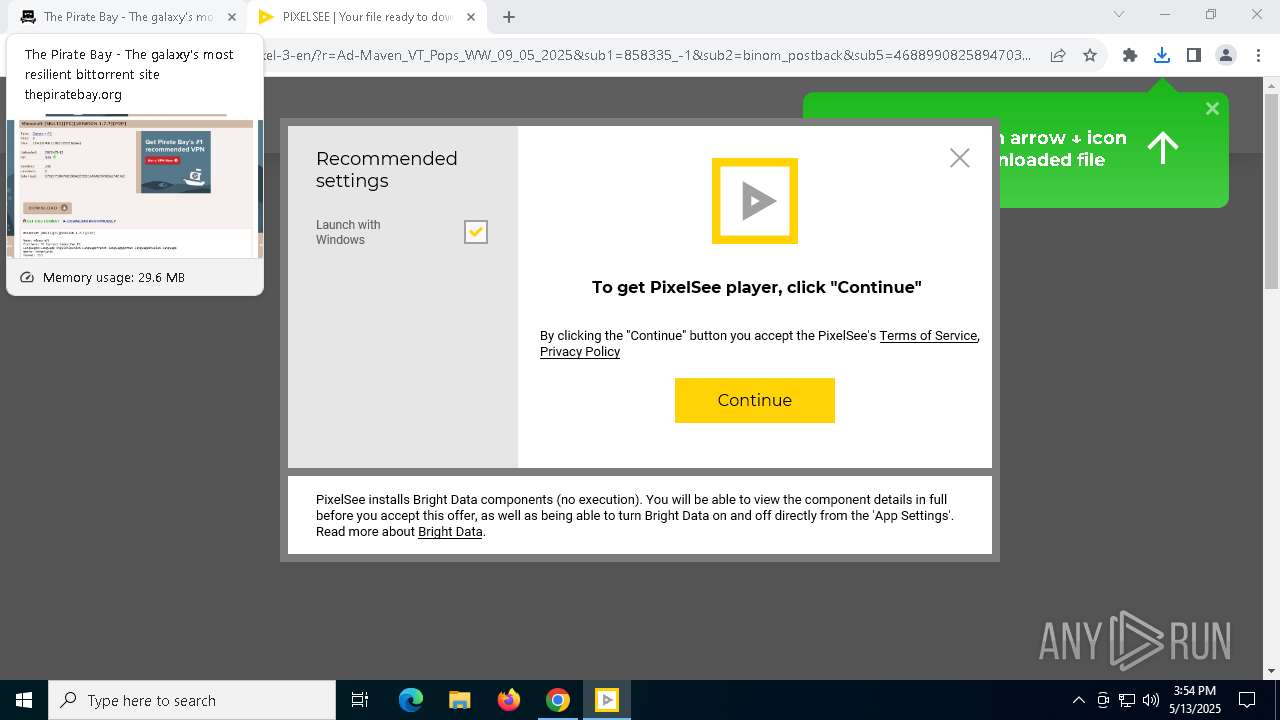
- PixelSee_id781848id.exe (PID: 4608)
SUSPICIOUS
Reads security settings of Internet Explorer
- PixelSee_id781848id.exe (PID: 4608)
Reads Microsoft Outlook installation path
- PixelSee_id781848id.exe (PID: 4608)
Reads Internet Explorer settings
- PixelSee_id781848id.exe (PID: 4608)
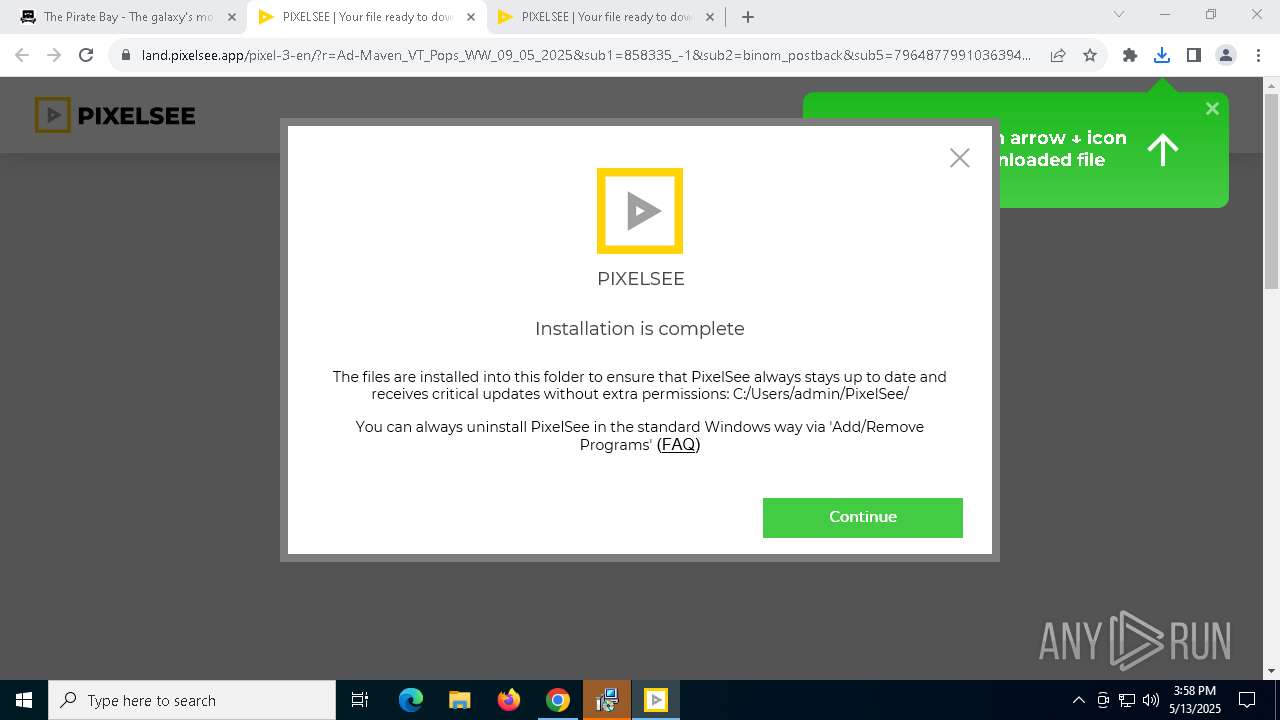
Executable content was dropped or overwritten
- PixelSee_id781848id.exe (PID: 4608)
- net_updater32.exe (PID: 5740)
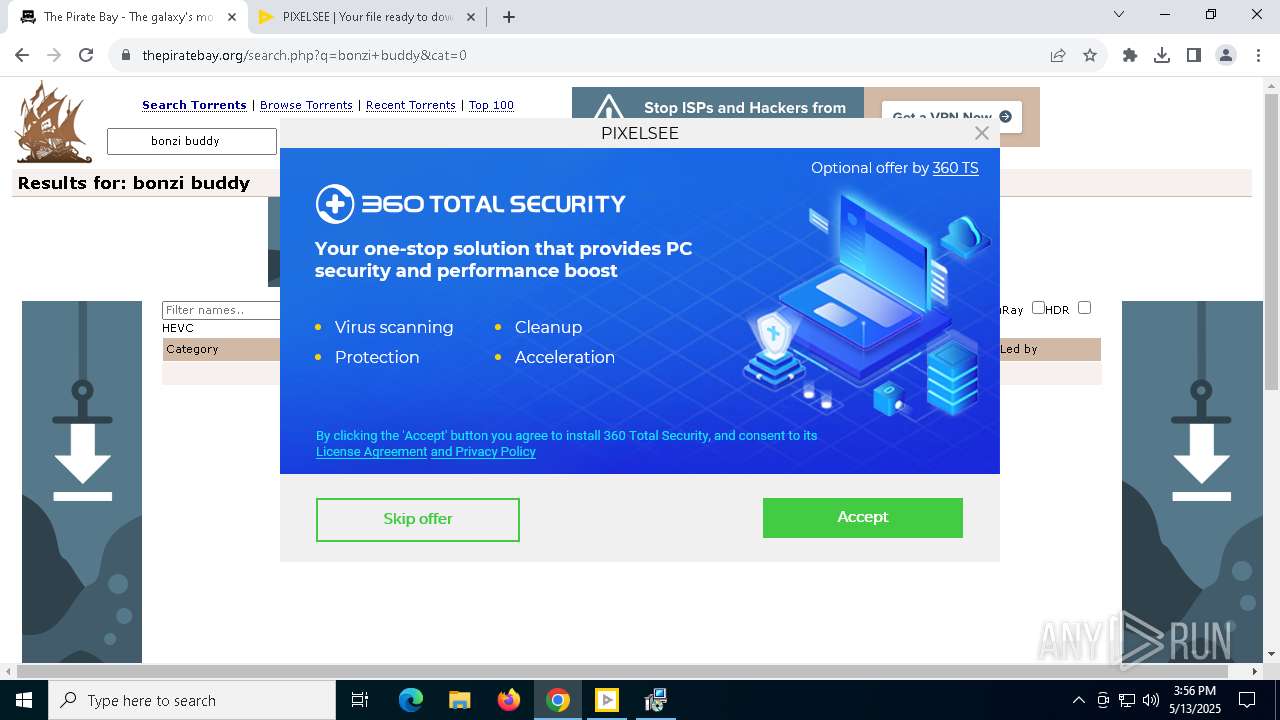
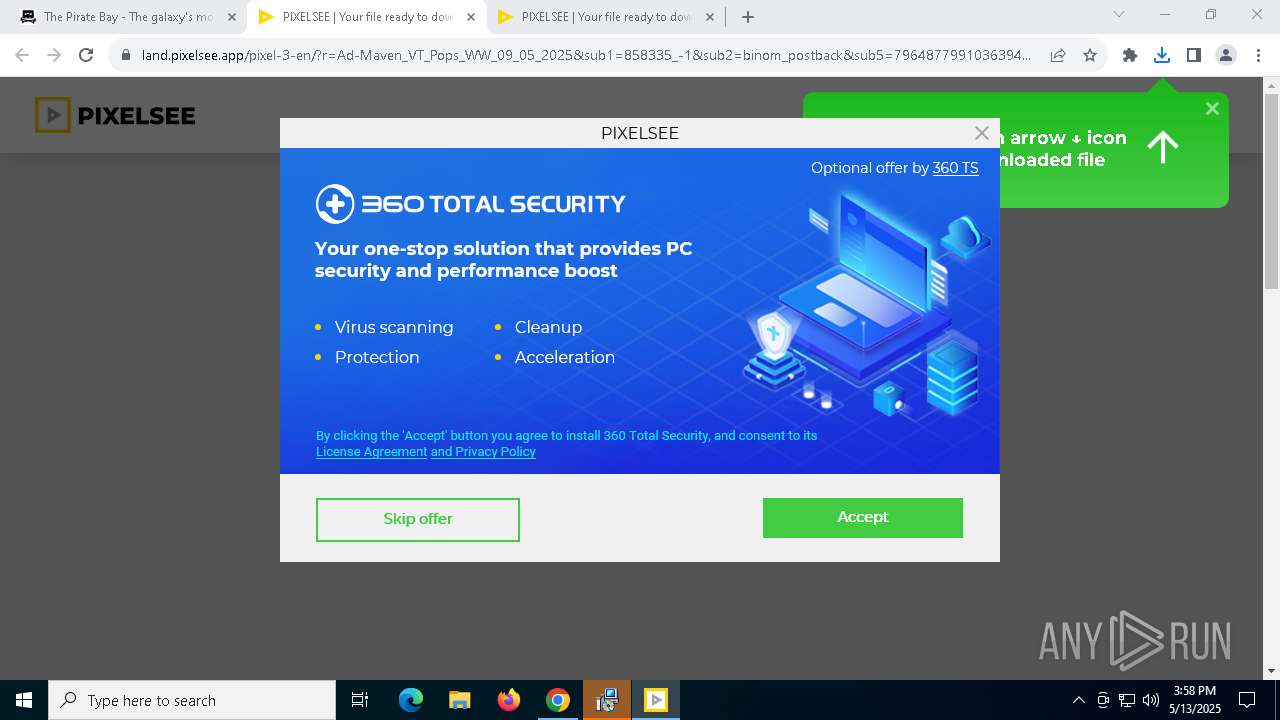
- antivirus360.exe (PID: 6572)
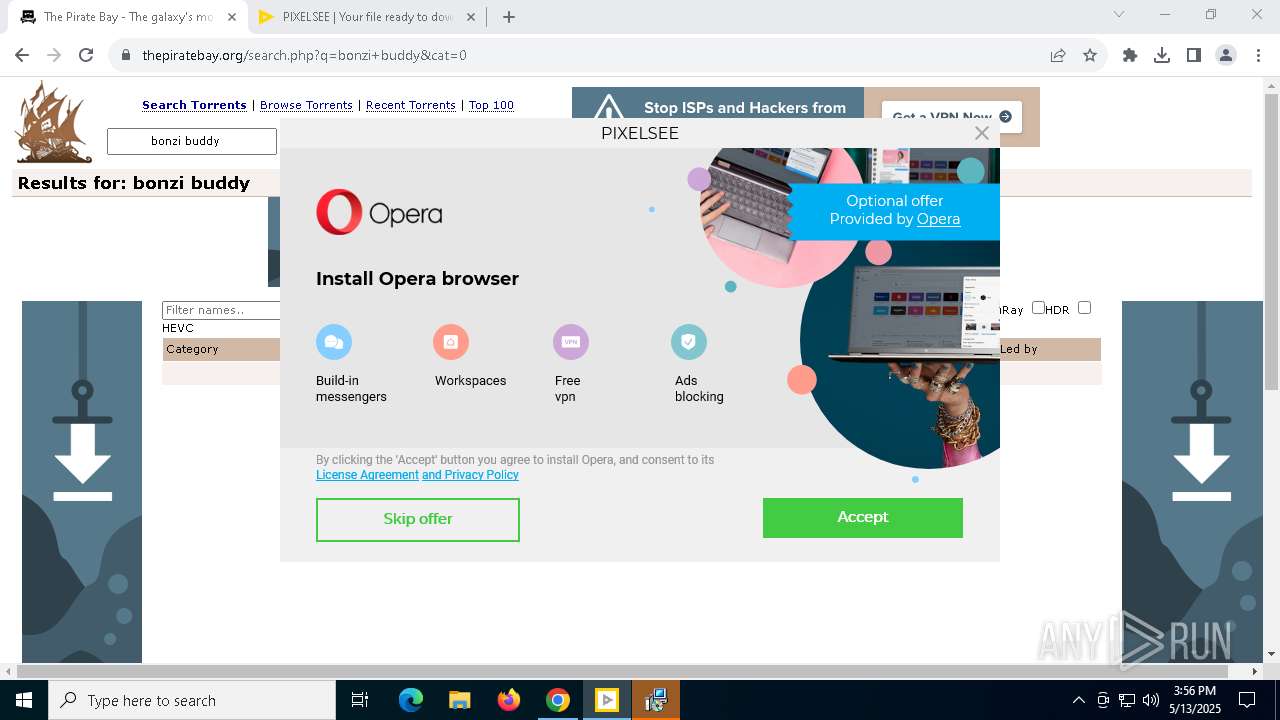
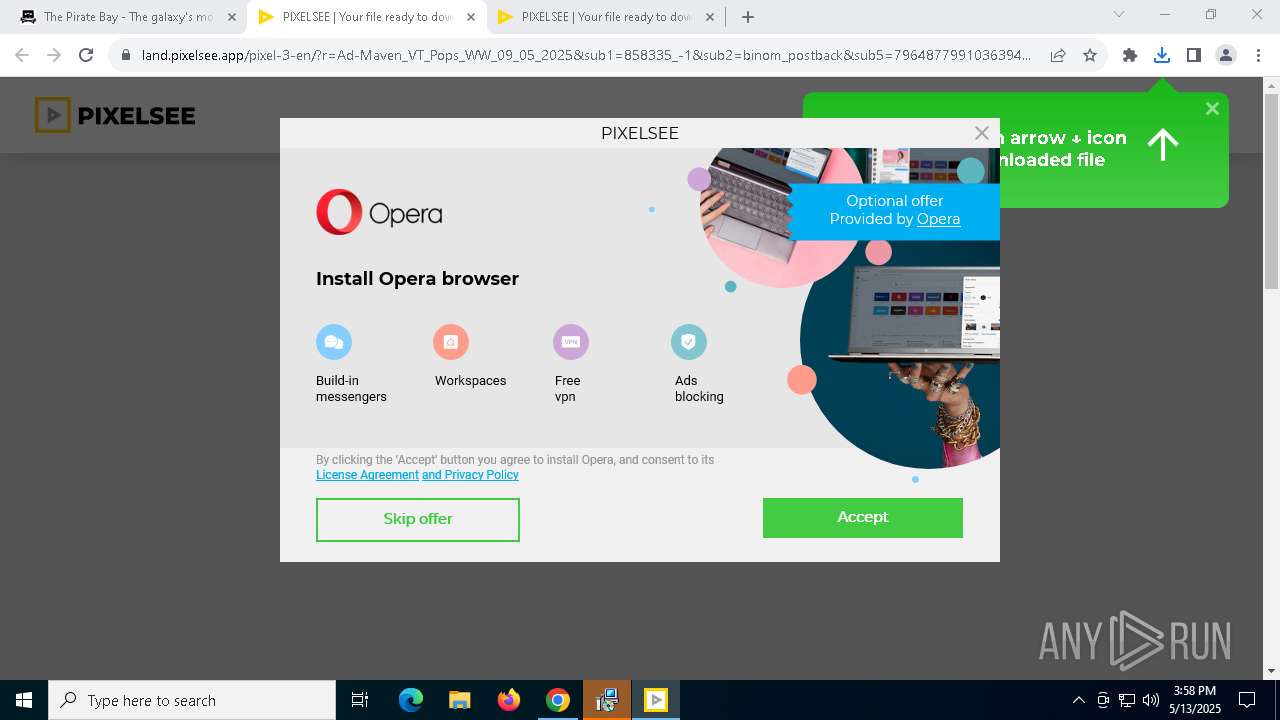
- opera_binst.exe (PID: 6252)
- lum_inst.tmp (PID: 7796)
- lum_inst.exe (PID: 7012)
- luminati-m-controller.exe (PID: 8184)
- setup.exe (PID: 728)
- setup.exe (PID: 6820)
- setup.exe (PID: 8212)
- setup.exe (PID: 7628)
- setup.exe (PID: 8256)
- luminati-m-controller.exe (PID: 8432)
- 360TS_Setup.exe (PID: 9124)
- 360TS_Setup.exe (PID: 8468)
- PixelSee_id782110id.exe (PID: 4008)
- Assistant_118.0.5461.41_Setup.exe_sfx.exe (PID: 8380)
- antivirus360.exe (PID: 540)
- 360TS_Setup.exe (PID: 3708)
Process drops legitimate windows executable
- PixelSee_id781848id.exe (PID: 4608)
- luminati-m-controller.exe (PID: 8184)
- Assistant_118.0.5461.41_Setup.exe_sfx.exe (PID: 8380)
Executes as Windows Service
- VSSVC.exe (PID: 5744)
- net_updater32.exe (PID: 5740)
- WmiApSrv.exe (PID: 5044)
The process drops C-runtime libraries
- PixelSee_id781848id.exe (PID: 4608)
- luminati-m-controller.exe (PID: 8184)
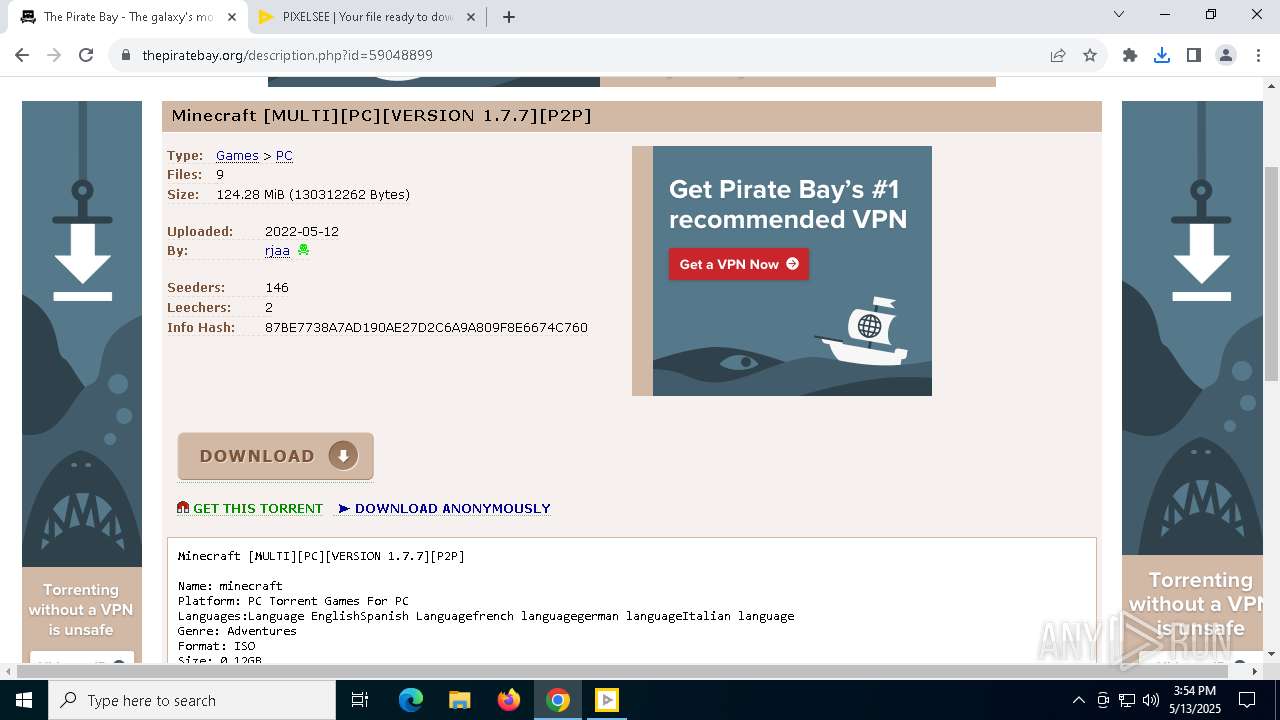
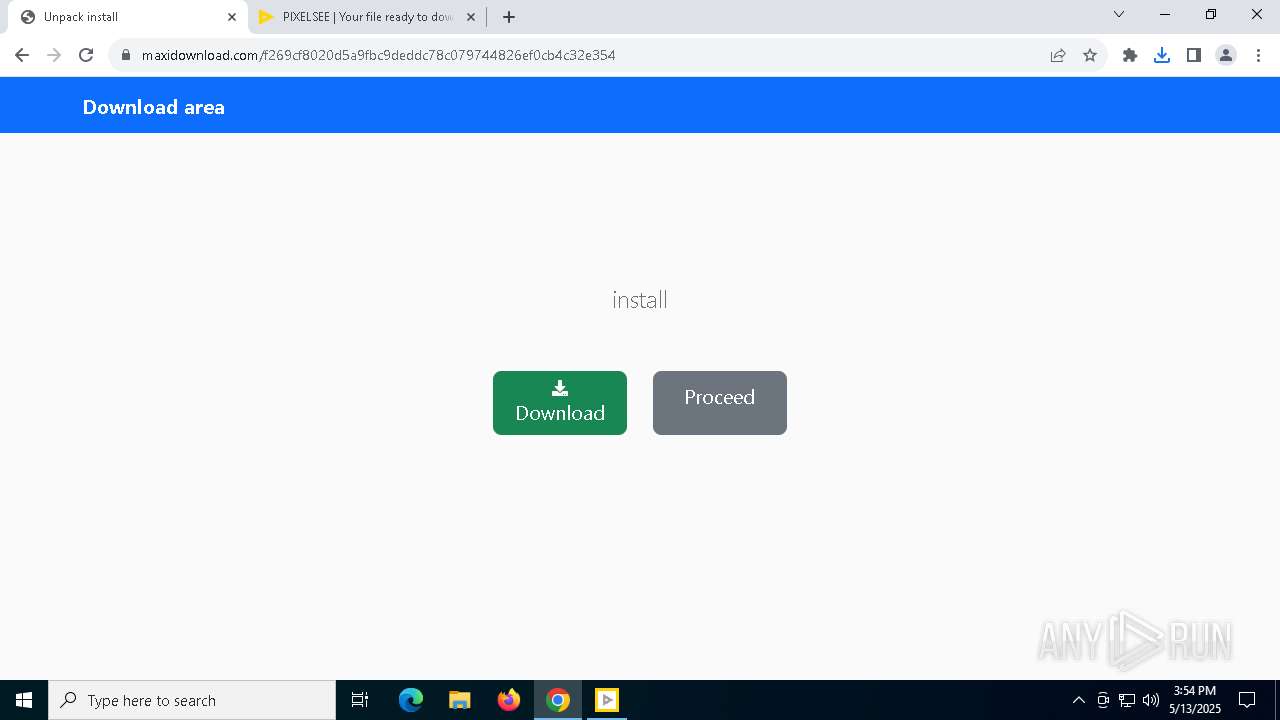
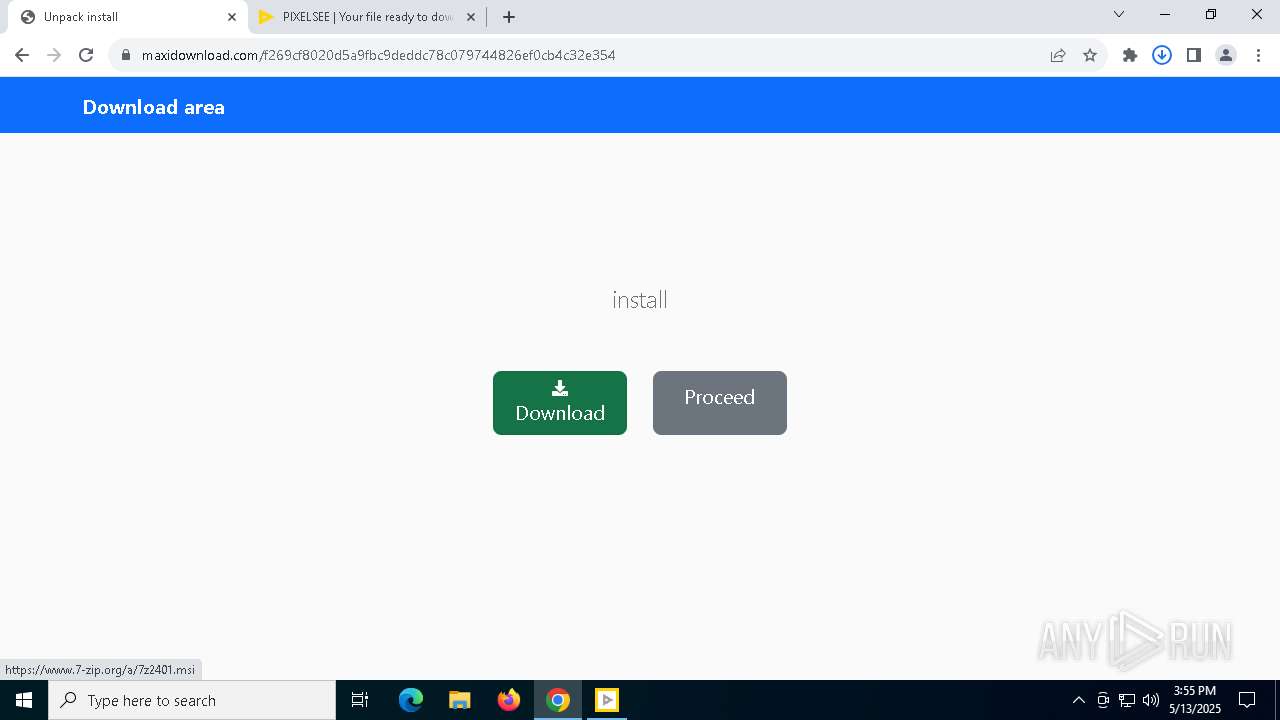
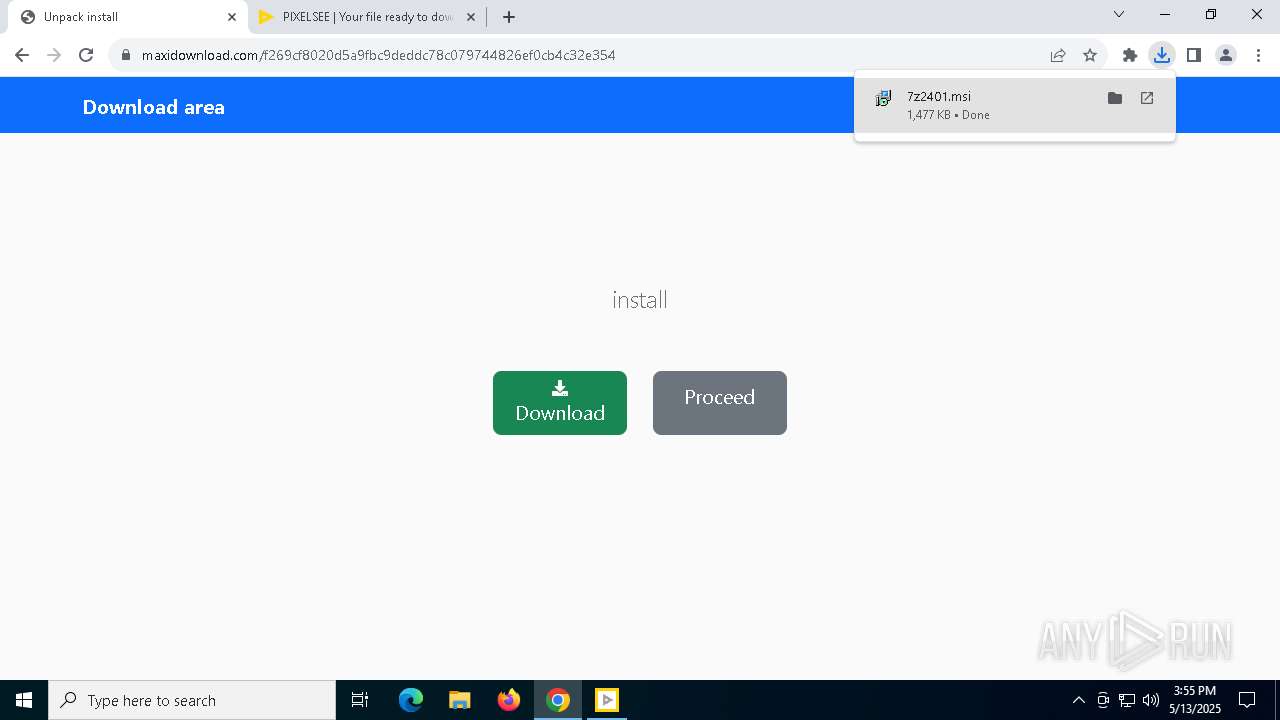
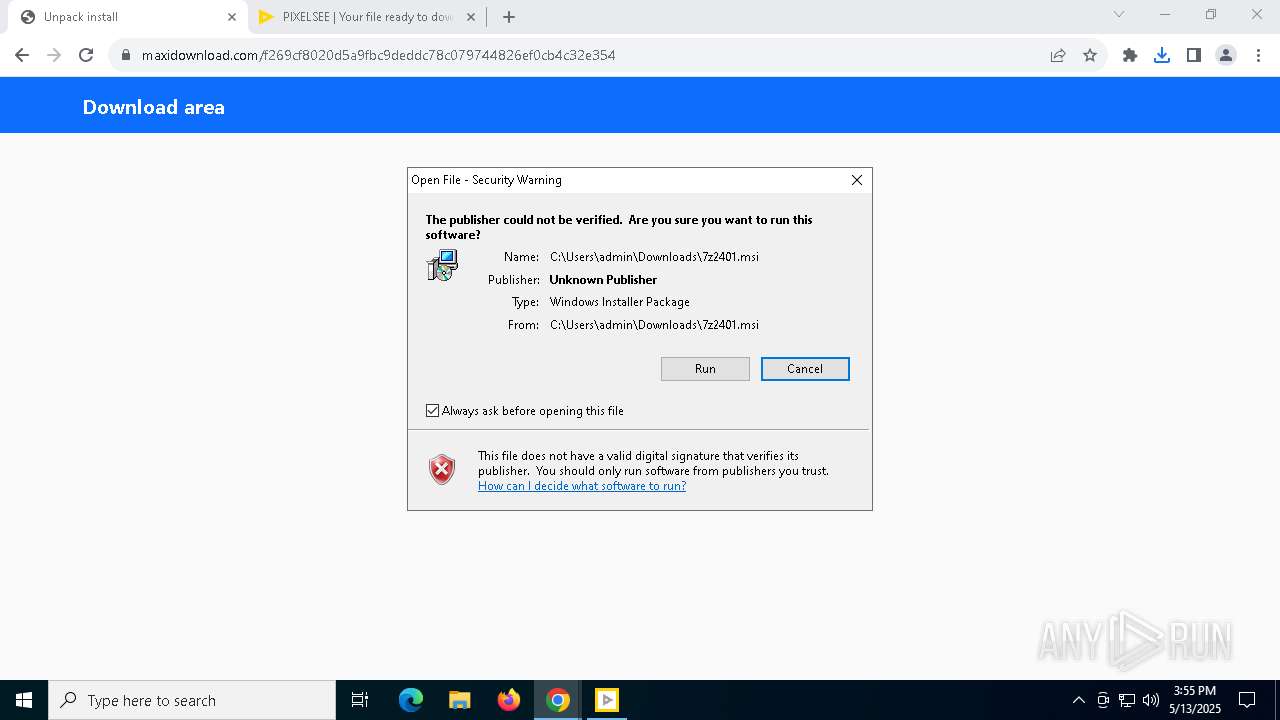
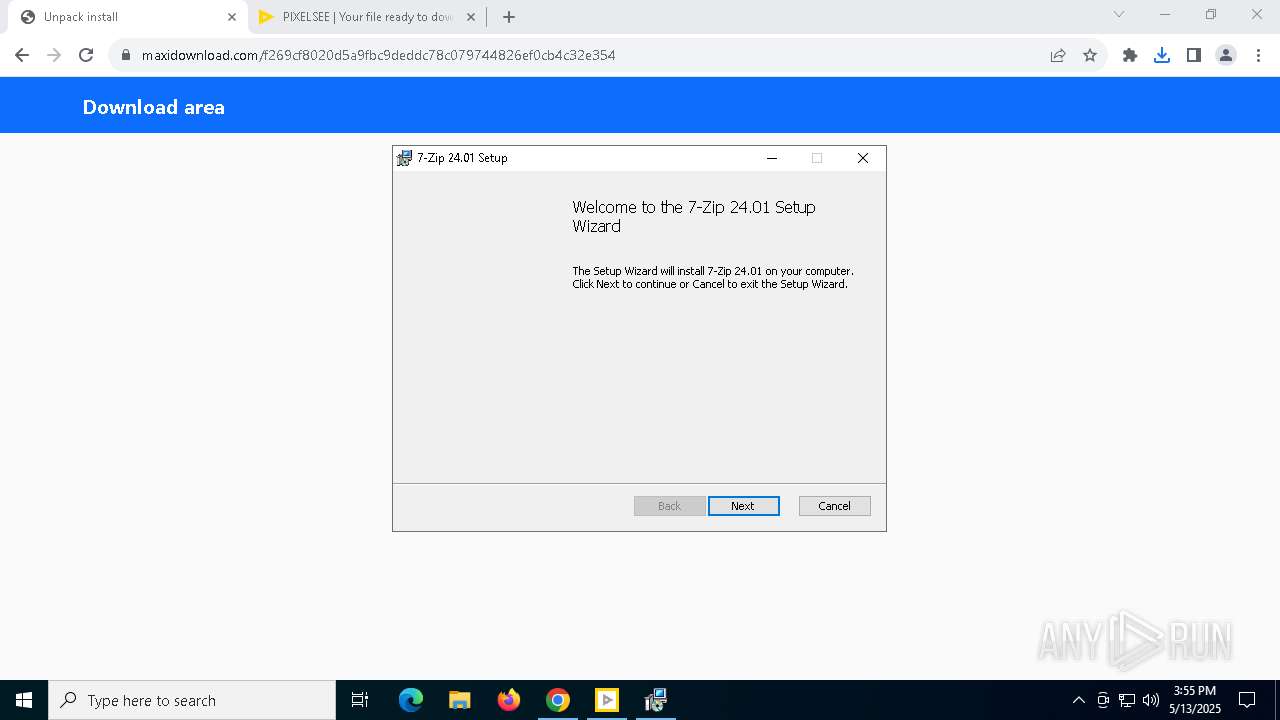
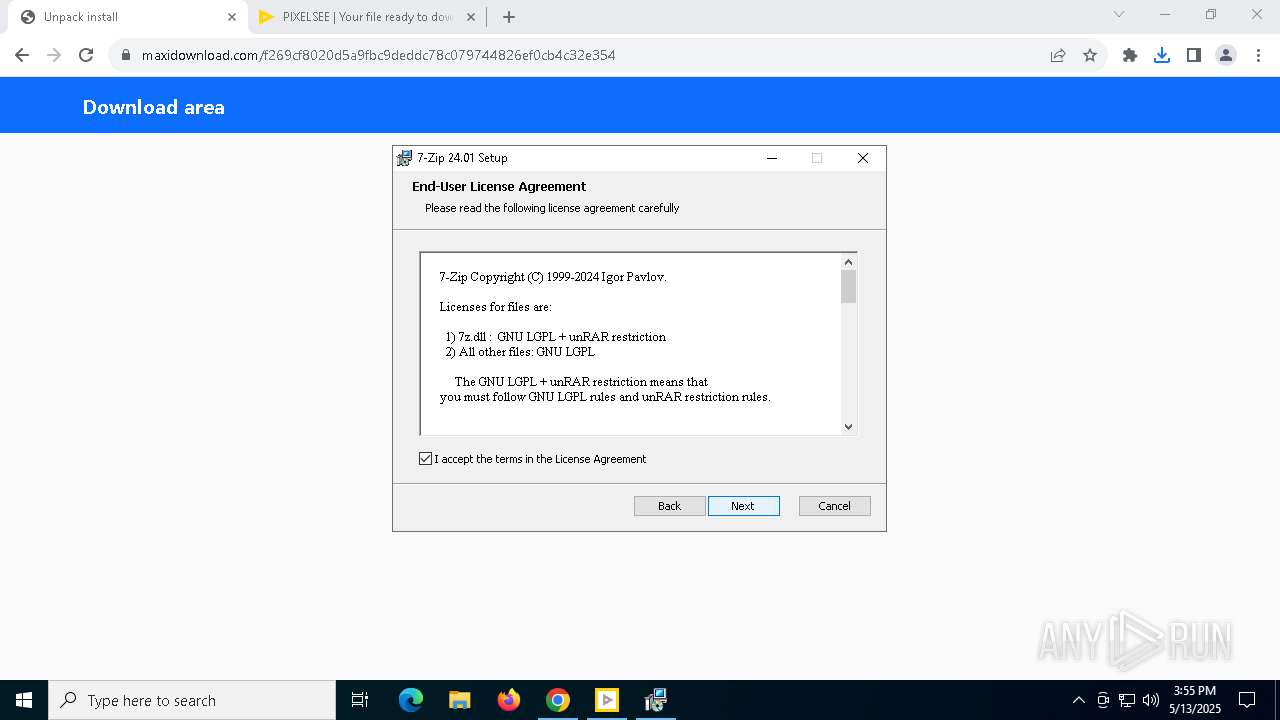
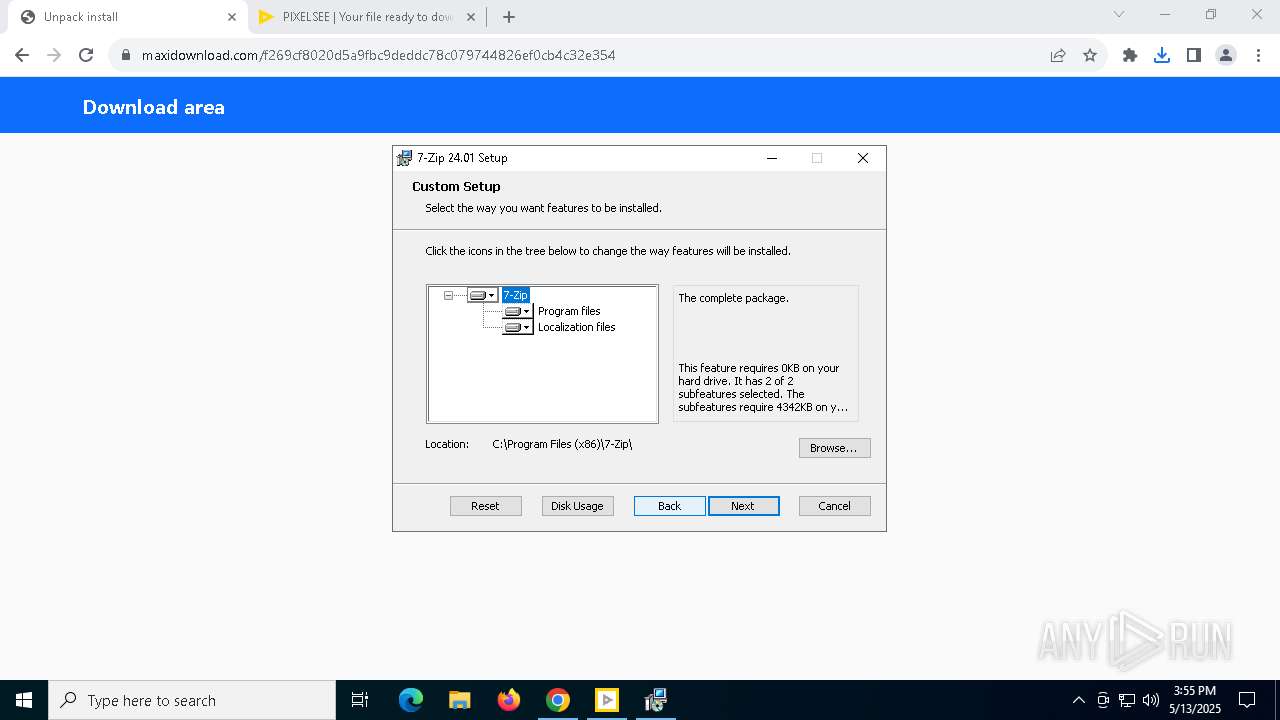
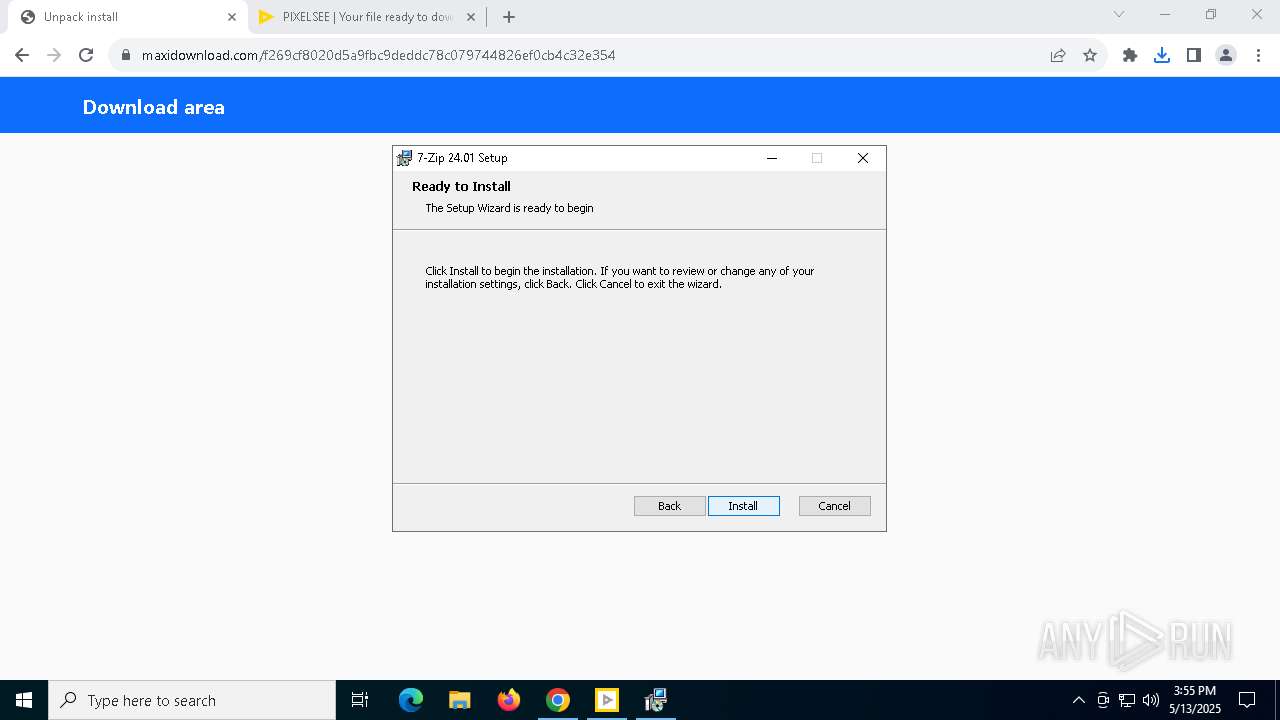
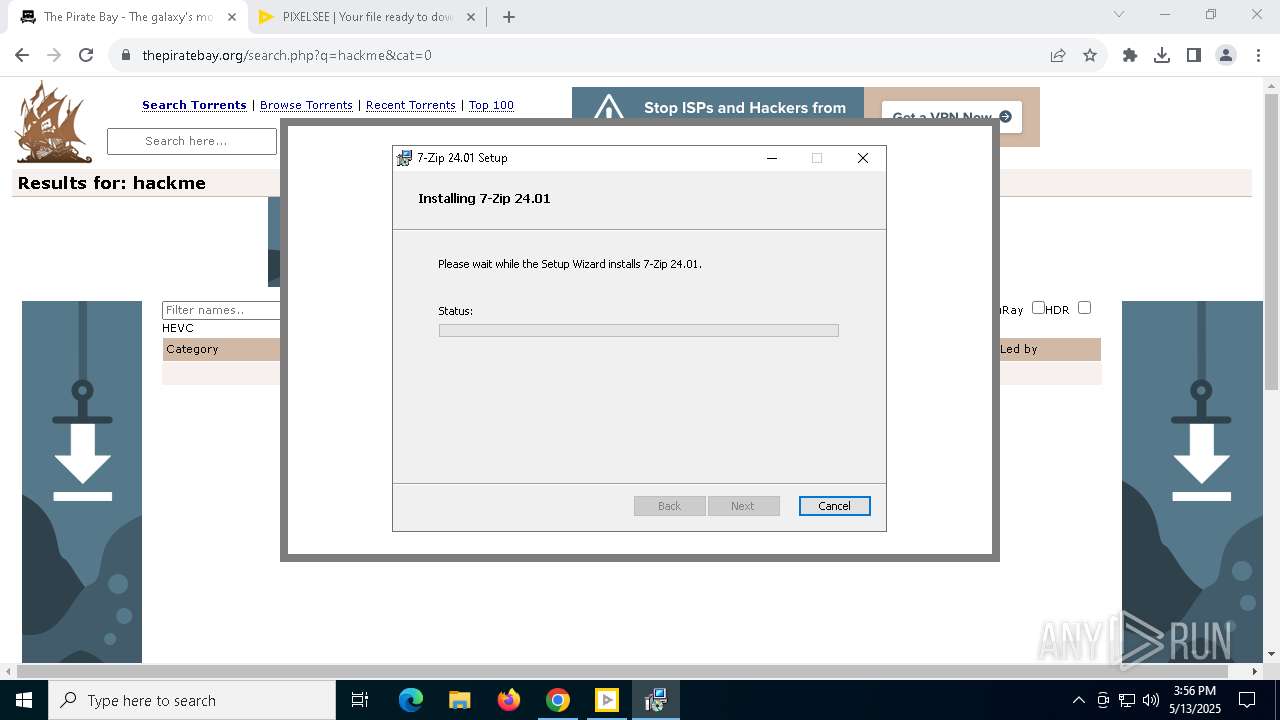
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 7868)
- 360TS_Setup.exe (PID: 8468)
Uses NETSH.EXE to add a firewall rule or allowed programs
- PixelSee_id781848id.exe (PID: 4608)
- PixelSee_id782110id.exe (PID: 4008)
Checks for external IP
- net_updater32.exe (PID: 5740)
Application launched itself
- setup.exe (PID: 7628)
- assistant_installer.exe (PID: 1676)
- setup.exe (PID: 8212)
Starts itself from another location
- setup.exe (PID: 7628)
- 360TS_Setup.exe (PID: 9124)
Potential Corporate Privacy Violation
- antivirus360.exe (PID: 6572)
Process requests binary or script from the Internet
- antivirus360.exe (PID: 6572)
- antivirus360.exe (PID: 540)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 7672)
- msiexec.exe (PID: 7868)
- chrome.exe (PID: 8708)
The sample compiled with english language support
- chrome.exe (PID: 7672)
- PixelSee_id781848id.exe (PID: 4608)
- lum_inst.tmp (PID: 7796)
- msiexec.exe (PID: 7868)
- antivirus360.exe (PID: 6572)
- luminati-m-controller.exe (PID: 8184)
- opera_binst.exe (PID: 6252)
- setup.exe (PID: 728)
- setup.exe (PID: 7628)
- setup.exe (PID: 6820)
- setup.exe (PID: 8212)
- setup.exe (PID: 8256)
- chrome.exe (PID: 8708)
- Assistant_118.0.5461.41_Setup.exe_sfx.exe (PID: 8380)
- 360TS_Setup.exe (PID: 8468)
- PixelSee_id782110id.exe (PID: 4008)
- antivirus360.exe (PID: 540)
Connects to unusual port
- chrome.exe (PID: 7940)
Application launched itself
- chrome.exe (PID: 7672)
Checks supported languages
- PixelSee_id781848id.exe (PID: 4608)
- msiexec.exe (PID: 7868)
Reads the computer name
- PixelSee_id781848id.exe (PID: 4608)
- msiexec.exe (PID: 7868)
Create files in a temporary directory
- PixelSee_id781848id.exe (PID: 4608)
Checks proxy server information
- PixelSee_id781848id.exe (PID: 4608)
- slui.exe (PID: 7236)
Reads the software policy settings
- slui.exe (PID: 7604)
- slui.exe (PID: 7236)
Reads Microsoft Office registry keys
- chrome.exe (PID: 7672)
Manages system restore points
- SrTasks.exe (PID: 5668)
The sample compiled with russian language support
- msiexec.exe (PID: 7868)
The sample compiled with chinese language support
- 360TS_Setup.exe (PID: 9124)
- 360TS_Setup.exe (PID: 8468)
- 360TS_Setup.exe (PID: 3708)
The sample compiled with turkish language support
- 360TS_Setup.exe (PID: 8468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
242
Monitored processes
96
Malicious processes
3
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6900 --field-trial-handle=2036,i,15497075509577548404,267944448666667789,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | ||||
| 540 | "C:\Users\admin\AppData\Local\Temp\antivirus360\antivirus360.exe" /s | C:\Users\admin\AppData\Local\Temp\antivirus360\antivirus360.exe | PixelSee_id782110id.exe | |
User: admin Company: Qihoo 360 Technology Co. Ltd. Integrity Level: HIGH Description: 360 Total Security Online Installer Exit code: 1 Version: 6, 6, 0, 1060 | ||||
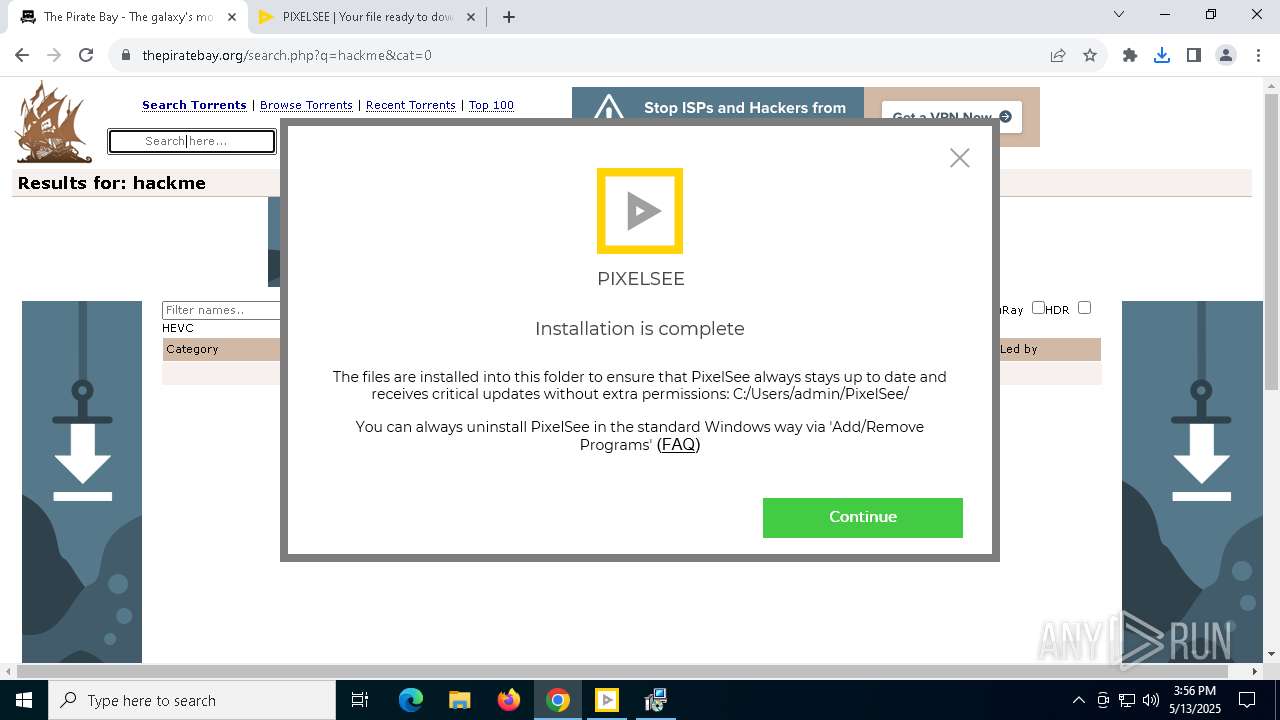
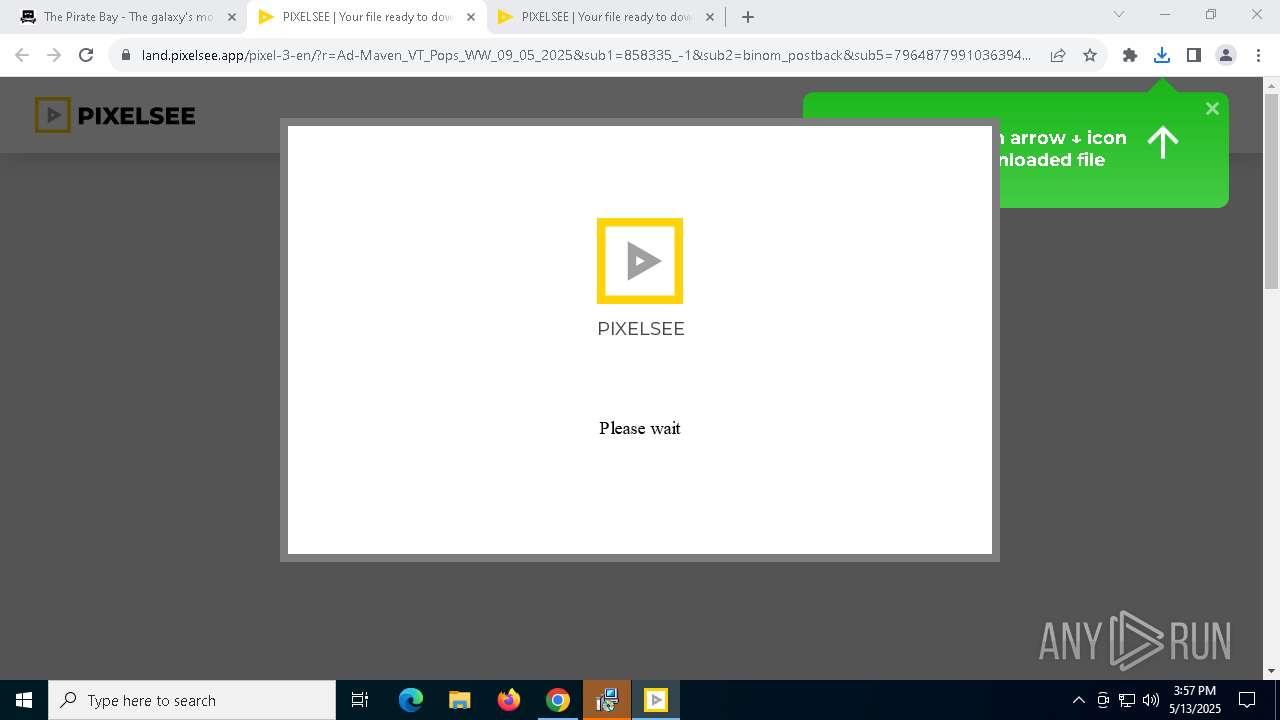
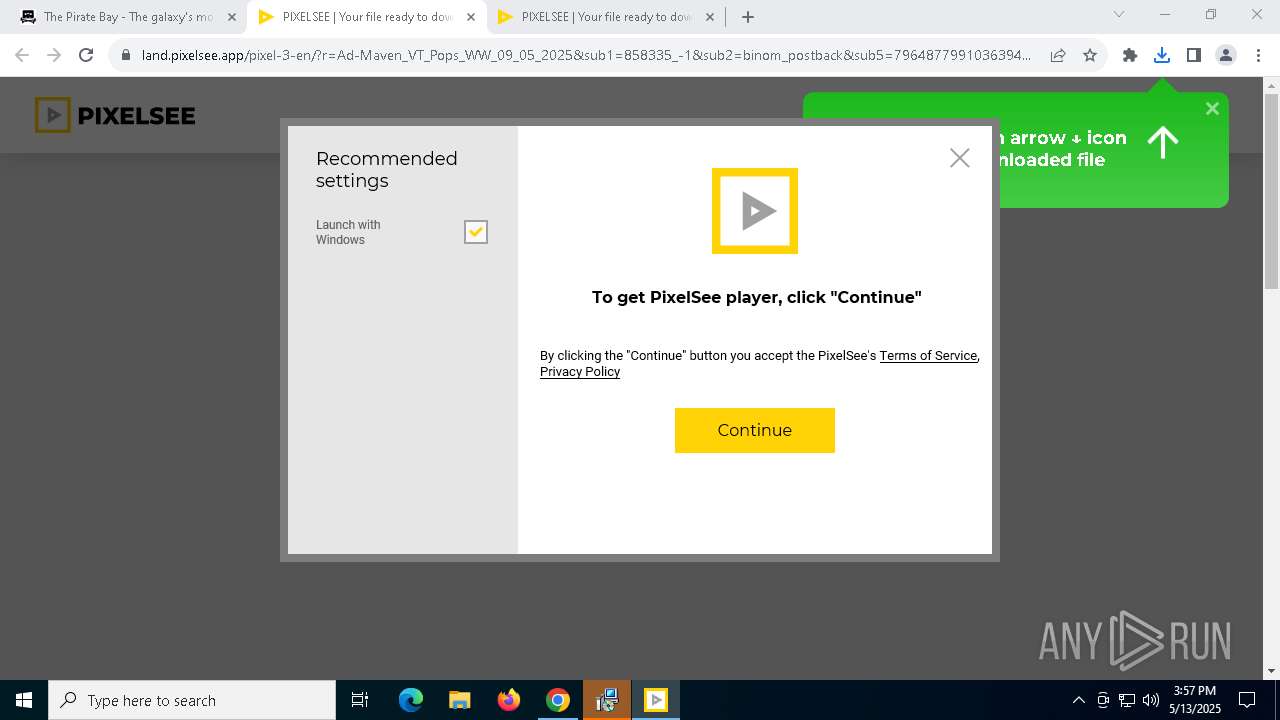
| 720 | "C:\Users\admin\PixelSee\pixelsee.exe" --installer | C:\Users\admin\PixelSee\pixelsee.exe | PixelSee_id781848id.exe | |
User: admin Company: SIA Circle Solutions Integrity Level: HIGH Description: PixelSee Player Exit code: 0 Version: 14.0.0.0 | ||||
| 728 | "C:\Users\admin\AppData\Local\Temp\.opera\Opera Installer Temp\setup.exe" --version | C:\Users\admin\AppData\Local\Temp\.opera\Opera Installer Temp\setup.exe | setup.exe | |
User: admin Company: Opera Software Integrity Level: HIGH Description: Opera Installer Exit code: 0 Version: 119.0.5497.29 | ||||
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=7080 --field-trial-handle=2036,i,15497075509577548404,267944448666667789,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | ||||
| 732 | C:\ProgramData\BrightData\b85f5ef603041f1fc4e7f943c177a0d440a01266\idle_report.exe --id 38158 | C:\ProgramData\BrightData\b85f5ef603041f1fc4e7f943c177a0d440a01266\idle_report.exe | — | net_updater32.exe |
User: admin Company: BrightData Ltd. Integrity Level: MEDIUM Description: idle_report Exit code: 0 Version: 1.474.630 | ||||
| 812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --mojo-platform-channel-handle=6664 --field-trial-handle=2036,i,15497075509577548404,267944448666667789,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | ||||
| 1004 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net_updater32.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6784 --field-trial-handle=2036,i,15497075509577548404,267944448666667789,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
650
Suspicious files
905
Text files
495
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10e0ec.TMP | — | |
MD5:— | SHA256:— | |||
| 7672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10e0ec.TMP | — | |
MD5:— | SHA256:— | |||
| 7672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10e0fb.TMP | — | |
MD5:— | SHA256:— | |||
| 7672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10e0fb.TMP | — | |
MD5:— | SHA256:— | |||
| 7672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10e0fb.TMP | — | |
MD5:— | SHA256:— | |||
| 7672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
347
DNS requests
242
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7240 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1228 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
1228 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
1228 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
7240 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1228 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
1228 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
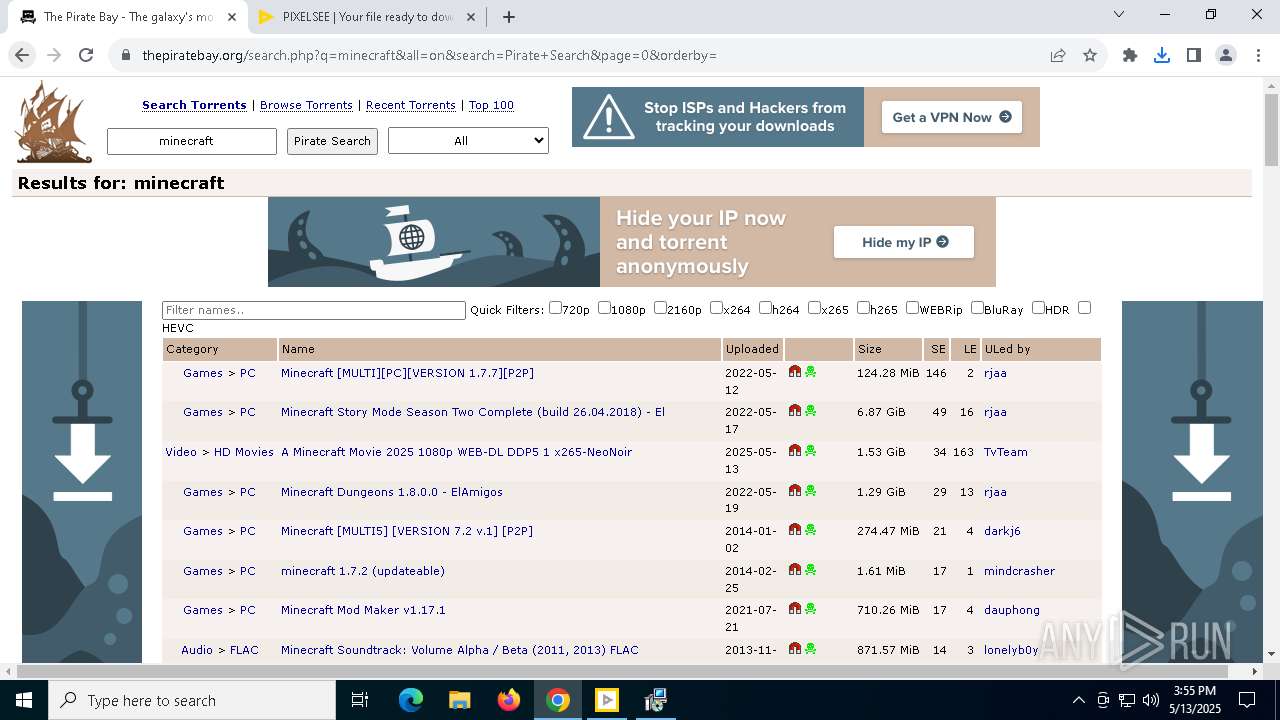
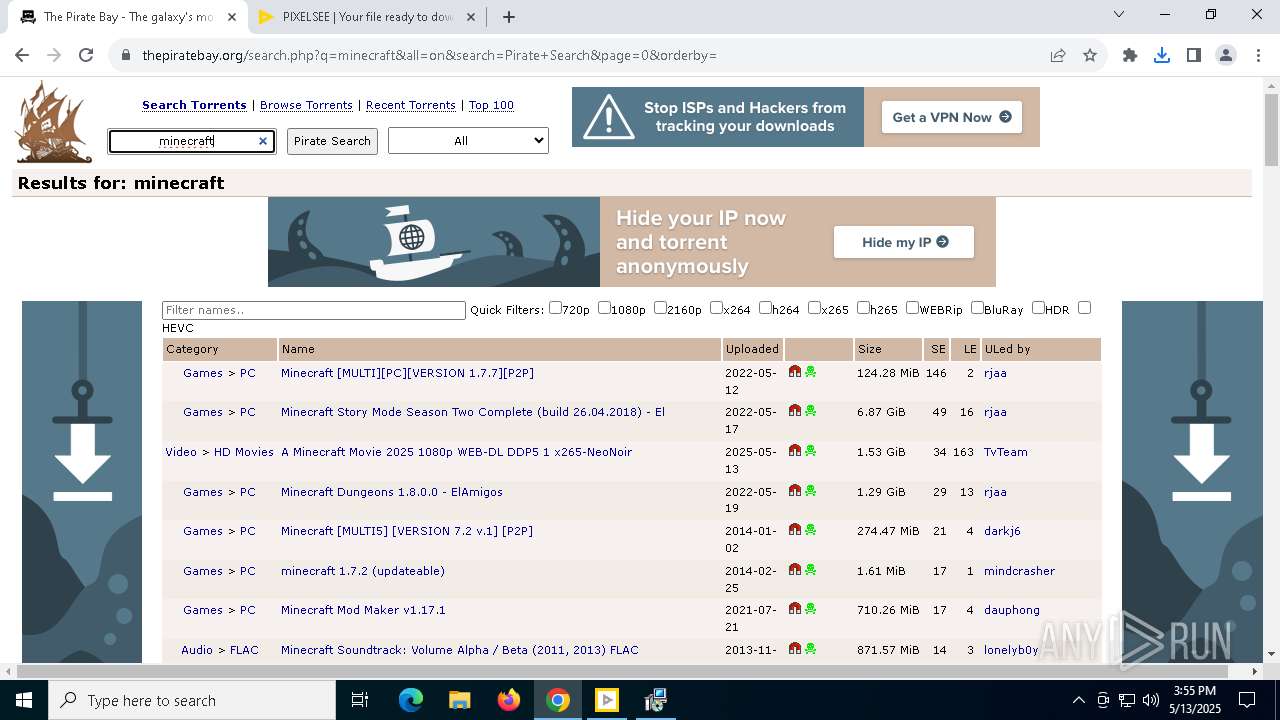
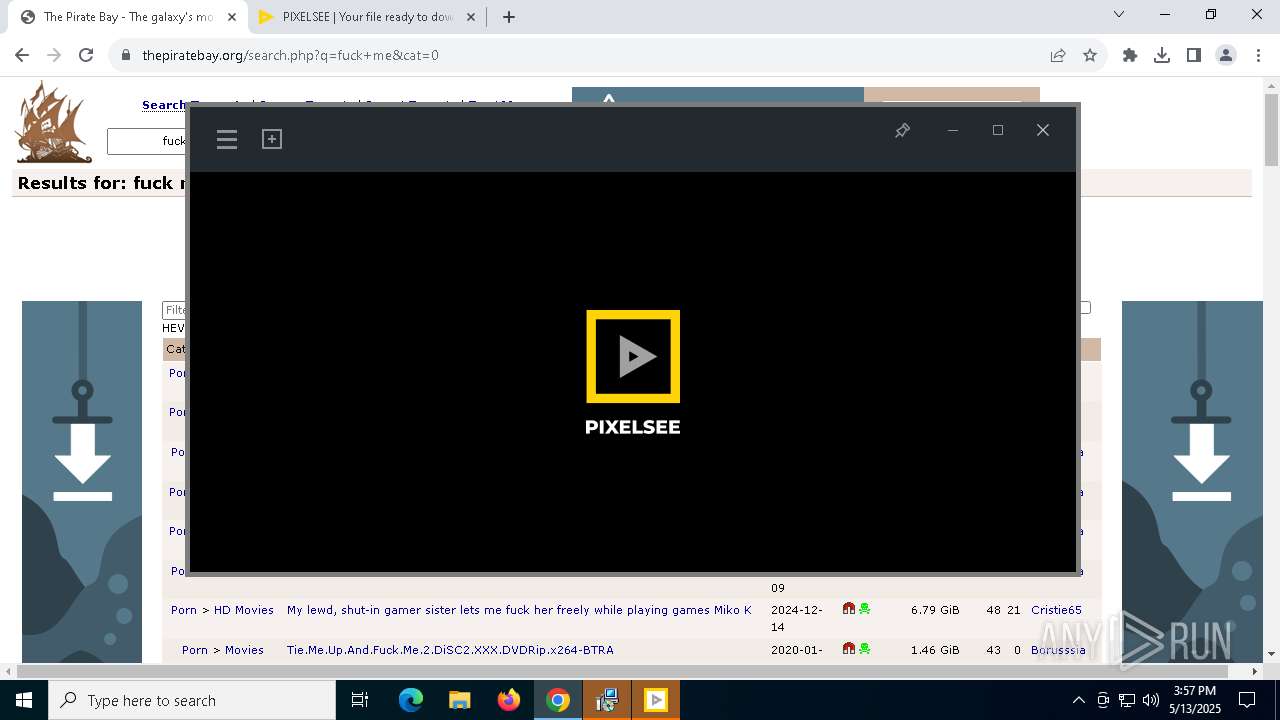
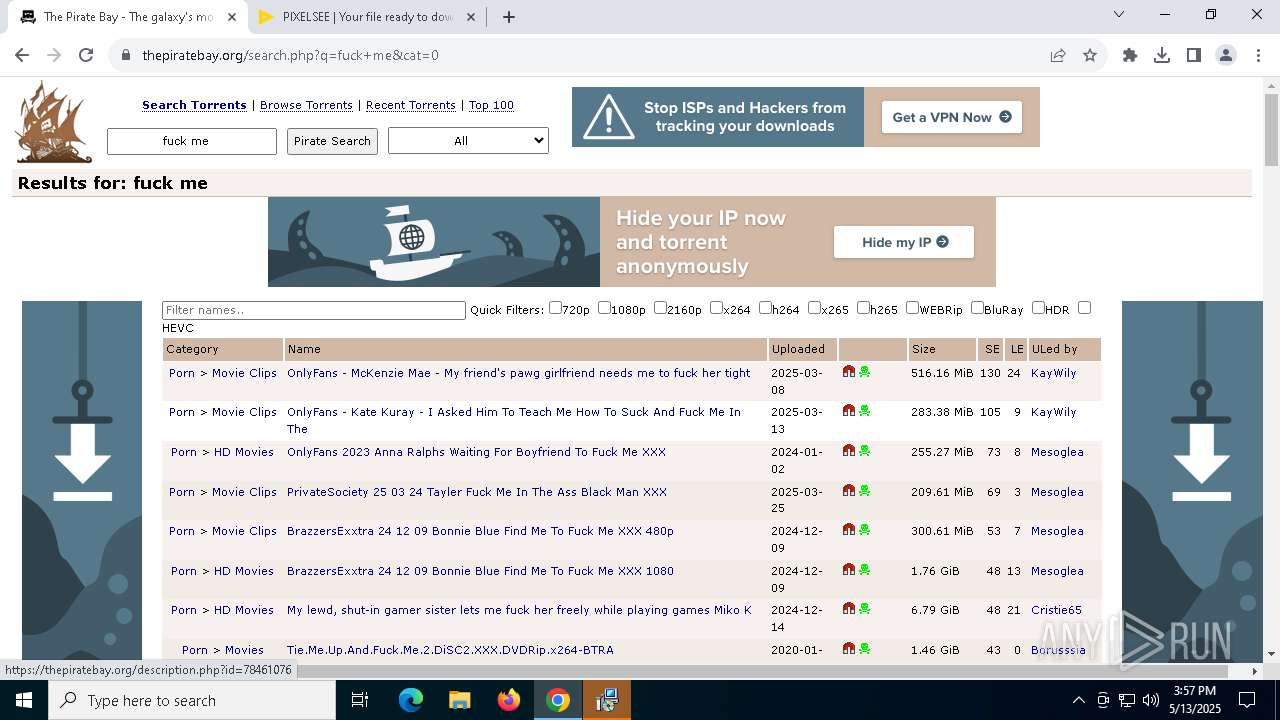
7940 | chrome.exe | 162.159.136.6:443 | thepiratebay.org | CLOUDFLARENET | — | whitelisted |
7672 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7940 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
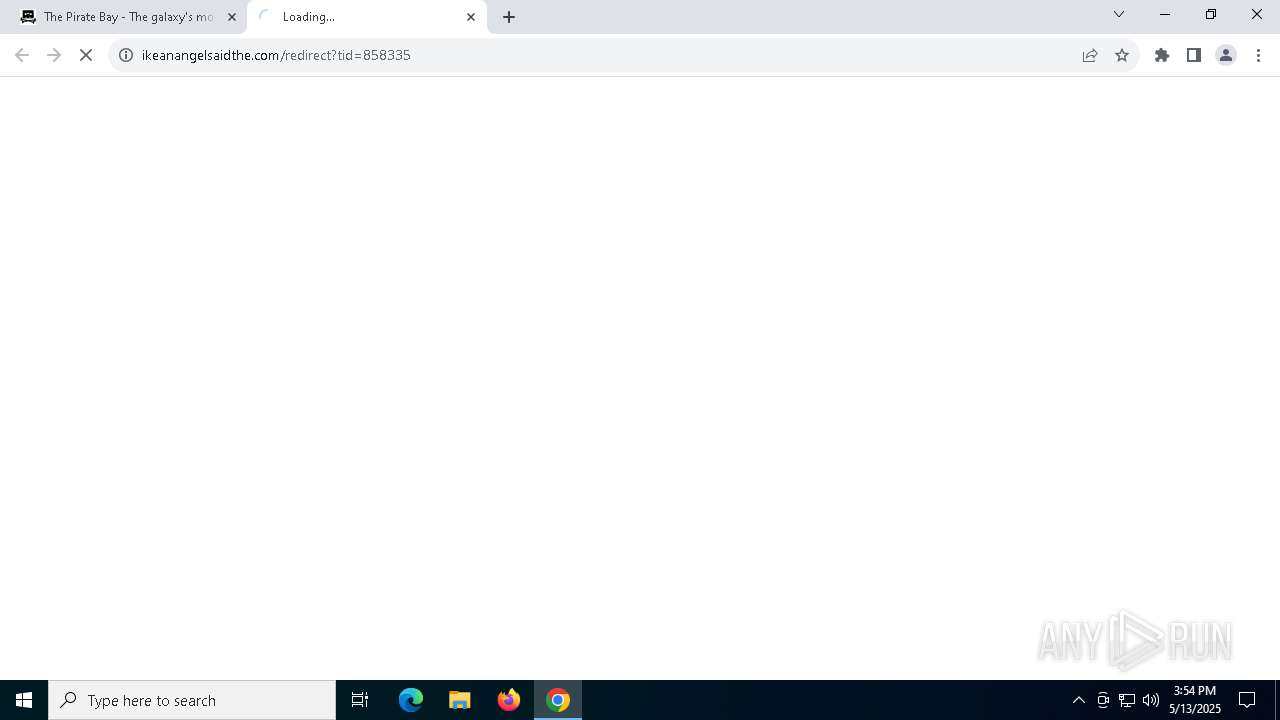
7940 | chrome.exe | 104.21.70.143:443 | torrindex.net | CLOUDFLARENET | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
thepiratebay.org |
| whitelisted |
accounts.google.com |
| whitelisted |
torrindex.net |
| unknown |
unhappyweakness.com |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7940 | chrome.exe | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
7940 | chrome.exe | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
7940 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7940 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7940 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7940 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7940 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7940 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7940 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7940 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |