| File name: | Ransomware.Unnamed_0.exe |
| Full analysis: | https://app.any.run/tasks/ebc8b3bf-bafa-44b3-9dfc-4819f3dae421 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | August 18, 2019, 00:05:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 96AFC9CDEF3C623E0C5420E339C57283 |
| SHA1: | CCBDFF85419E61987FDB7291F9966A046B0E4B25 |
| SHA256: | 517AC5506A5488A1193686F66CB57AD3288C2258C510004EDB2F361B674526CC |
| SSDEEP: | 24576:COMJ1lwizdSdyqtnhCJfmuEEQJt7NVpjbWy:TQl3wZCfKXJt7NrjbW |
MALICIOUS
Writes to a start menu file
- Ransomware.Unnamed_0.exe (PID: 3300)
Starts Visual C# compiler
- Ransomware.Unnamed_0.exe (PID: 3300)
Runs injected code in another process
- vbc.exe (PID: 2464)
MINER was detected
- wuapp.exe (PID: 2084)
- wuapp.exe (PID: 2152)
- wuapp.exe (PID: 3084)
- wuapp.exe (PID: 3512)
Application was injected by another process
- explorer.exe (PID: 276)
Connects to CnC server
- wuapp.exe (PID: 2084)
- wuapp.exe (PID: 2152)
- wuapp.exe (PID: 3084)
- wuapp.exe (PID: 3512)
Changes the autorun value in the registry
- vbc.exe (PID: 2464)
SUSPICIOUS
Executable content was dropped or overwritten
- Ransomware.Unnamed_0.exe (PID: 3300)
Creates files in the user directory
- Ransomware.Unnamed_0.exe (PID: 3300)
Executes scripts
- Ransomware.Unnamed_0.exe (PID: 3300)
INFO
Manual execution by user
- wuapp.exe (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:31 10:48:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 84992 |
| InitializedDataSize: | 838656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16b4e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | Ea6dq8F1DhAt0XmH.MZVgFJNgR2Tj7eIu.exe |
| LegalCopyright: | |
| OriginalFileName: | Ea6dq8F1DhAt0XmH.MZVgFJNgR2Tj7eIu.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Mar-2018 08:48:55 |
| Detected languages: |
|
| FileDescription: | - |
| FileVersion: | 0.0.0.0 |
| InternalName: | Ea6dq8F1DhAt0XmH.MZVgFJNgR2Tj7eIu.exe |
| LegalCopyright: | - |
| OriginalFilename: | Ea6dq8F1DhAt0XmH.MZVgFJNgR2Tj7eIu.exe |
| ProductVersion: | 0.0.0.0 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 31-Mar-2018 08:48:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00014B54 | 0x00014C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.0367 |
.rsrc | 0x00018000 | 0x000CC810 | 0x000CCA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99651 |
.reloc | 0x000E6000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 4.50808 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
138 | 7.99869 | 831811 | Latin 1 / Western European | German - Germany | RT_HTML |
32512 | 1.94375 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
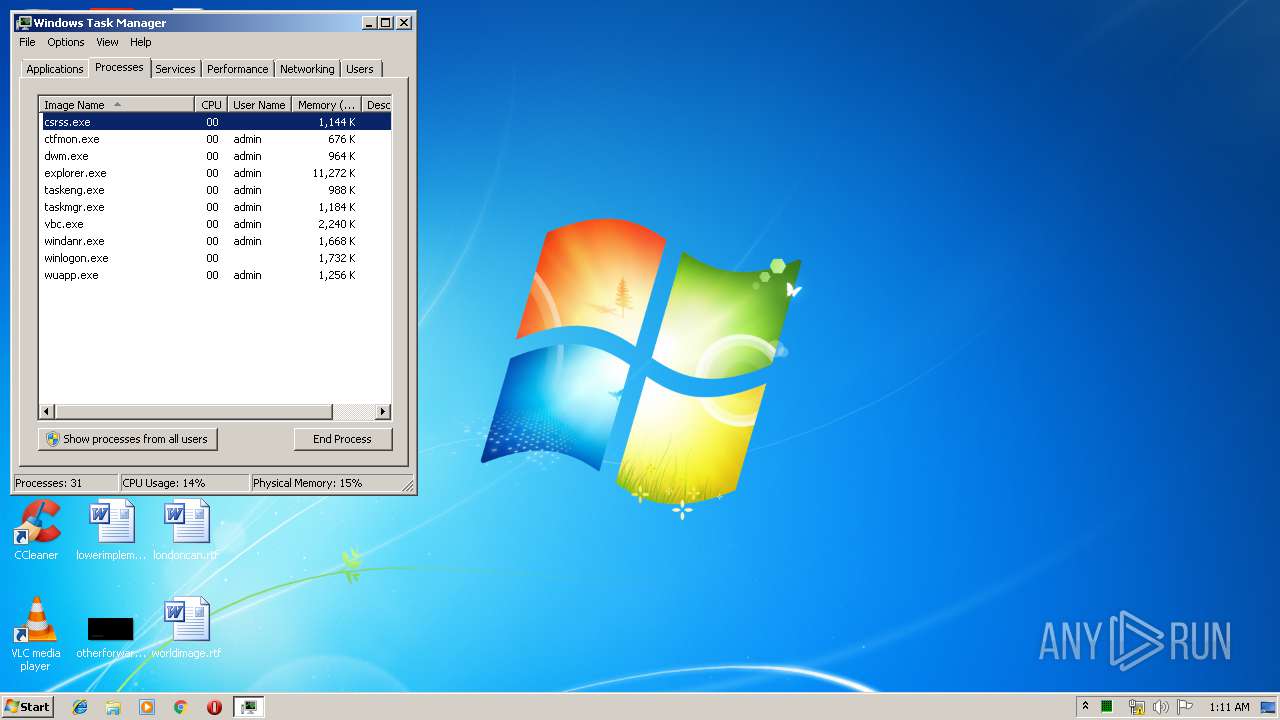
Total processes
41
Monitored processes
10
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1640 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | "C:\Windows\System32\wuapp.exe" -c "C:\Users\admin\AppData\Local\JesYXqkYNx\cfgi" | C:\Windows\System32\wuapp.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Application Launcher Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2152 | "C:\Windows\System32\wuapp.exe" -c "C:\Users\admin\AppData\Local\JesYXqkYNx\cfg" | C:\Windows\System32\wuapp.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Application Launcher Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2356 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\wa2yxemq.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | Ransomware.Unnamed_0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2464 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | Ransomware.Unnamed_0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3084 | "C:\Windows\System32\wuapp.exe" -c "C:\Users\admin\AppData\Local\JesYXqkYNx\cfgi" | C:\Windows\System32\wuapp.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Application Launcher Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3300 | "C:\Windows\Ransomware.Unnamed_0.exe" | C:\Windows\Ransomware.Unnamed_0.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3468 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES9D8D.tmp" "c:\Users\admin\AppData\Local\Temp\CSCB1539DCBE4164B66B777822543F26B95.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 12.00.52519.0 built by: VSWINSERVICING Modules
| |||||||||||||||
| 3512 | "C:\Windows\System32\wuapp.exe" -c "C:\Users\admin\AppData\Local\JesYXqkYNx\cfg" | C:\Windows\System32\wuapp.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Application Launcher Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
913
Read events
904
Write events
9
Delete events
0
Modification events
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2464) vbc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | waLPMrixgj |
Value: "C:\Users\admin\AppData\Local\JESYXQ~1\DHSDHC~1.EXE" | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\gnfxzte.rkr |
Value: 000000000000000001000000DD170000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000001C0000002500000043900C00090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
Executable files
1
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3300 | Ransomware.Unnamed_0.exe | C:\Users\admin\AppData\Local\Temp\wa2yxemq.0.cs | — | |
MD5:— | SHA256:— | |||
| 3300 | Ransomware.Unnamed_0.exe | C:\Users\admin\AppData\Local\Temp\wa2yxemq.cmdline | — | |
MD5:— | SHA256:— | |||
| 2356 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCB1539DCBE4164B66B777822543F26B95.TMP | — | |
MD5:— | SHA256:— | |||
| 2356 | csc.exe | C:\Users\admin\AppData\Local\Temp\wa2yxemq.pdb | — | |
MD5:— | SHA256:— | |||
| 2356 | csc.exe | C:\Users\admin\AppData\Local\Temp\wa2yxemq.dll | — | |
MD5:— | SHA256:— | |||
| 3468 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES9D8D.tmp | — | |
MD5:— | SHA256:— | |||
| 2356 | csc.exe | C:\Users\admin\AppData\Local\Temp\wa2yxemq.out | — | |
MD5:— | SHA256:— | |||
| 2464 | vbc.exe | C:\Users\admin\AppData\Local\JesYXqkYNx\dhsdhchqsh.exe | — | |
MD5:— | SHA256:— | |||
| 3300 | Ransomware.Unnamed_0.exe | C:\Users\admin\Ransomware.Unnamed_0.exe | executable | |
MD5:96AFC9CDEF3C623E0C5420E339C57283 | SHA256:517AC5506A5488A1193686F66CB57AD3288C2258C510004EDB2F361B674526CC | |||
| 3300 | Ransomware.Unnamed_0.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\rTErod.url | text | |
MD5:61C7CB625E4C41E6E8E6744288764F98 | SHA256:CB042B44183FB13DBE9DBD3D1EC36D1EF99BF8A8308DDAF231974D8C6976A2EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
12
DNS requests
1
Threats
58
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2084 | wuapp.exe | 136.243.102.154:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | malicious |
2084 | wuapp.exe | 88.99.142.163:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | malicious |
2084 | wuapp.exe | 94.130.143.162:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | malicious |
3084 | wuapp.exe | 136.243.102.154:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | malicious |
2084 | wuapp.exe | 136.243.102.167:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | malicious |
3084 | wuapp.exe | 88.99.142.163:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | malicious |
2152 | wuapp.exe | 136.243.102.167:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | malicious |
3084 | wuapp.exe | 136.243.102.167:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | malicious |
3512 | wuapp.exe | 136.243.102.167:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xmr.pool.minergate.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | A Network Trojan was detected | ET POLICY Monero Mining Pool DNS Lookup |
2084 | wuapp.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
2084 | wuapp.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
2084 | wuapp.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
2084 | wuapp.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
2084 | wuapp.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
2084 | wuapp.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
2084 | wuapp.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
2084 | wuapp.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
2084 | wuapp.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
22 ETPRO signatures available at the full report