| File name: | file.exe |
| Full analysis: | https://app.any.run/tasks/33ac0cdb-e3df-4130-bd79-2c0c3d7fb28e |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
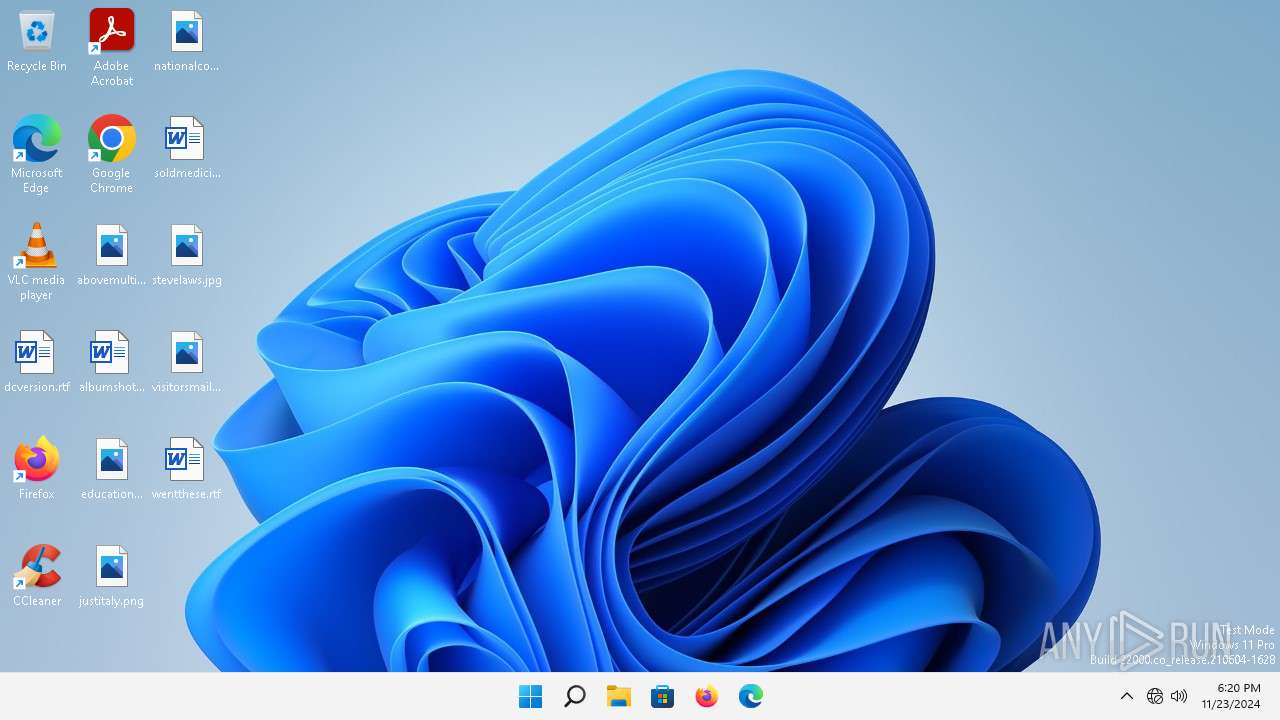
| Analysis date: | November 23, 2024, 18:20:36 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 4CECB04D97630CC2D5CCE80368B87FDD |
| SHA1: | 4F693736497E06C820B91597AF84C6FECE13408B |
| SHA256: | 51698570A9C637EC0C9BC2B3CA6ACB7EDF3D7804C49B8EED33E82573950877DD |
| SSDEEP: | 98304:kvrA8weLeVCH0N256o3+Fo4BVRs5y+r0e1C0wM5kLLQOMV1GPNPd9UCPyNNvz8xM:j2R1ya |
MALICIOUS
RHADAMANTHYS has been detected (YARA)
- svchost.exe (PID: 1472)
SUSPICIOUS
Reads the BIOS version
- file.exe (PID: 6956)
The process checks if it is being run in the virtual environment
- svchost.exe (PID: 1472)
Connects to unusual port
- svchost.exe (PID: 1472)
INFO
Manual execution by a user
- svchost.exe (PID: 1472)
Checks supported languages
- file.exe (PID: 6956)
Sends debugging messages
- file.exe (PID: 6956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:05:13 11:58:23+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 228352 |
| InitializedDataSize: | 220672 |
| UninitializedDataSize: | 65536 |
| EntryPoint: | 0x4bb000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.0.0 |
| ProductVersionNumber: | 8.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Daniel Pistelli |
| FileDescription: | Common File Format Explorer |
| FileVersion: | 8.0.0.0 |
| InternalName: | CFF Explorer.exe |
| LegalCopyright: | ? 2012 Daniel Pistelli. All rights reserved. |
| OriginalFileName: | CFF Explorer.exe |
| ProductName: | CFF Explorer |
| ProductVersion: | 8.0.0.0 |
Total processes
120
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1472 | "C:\Windows\System32\svchost.exe" | C:\Windows\SysWOW64\svchost.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6956 | "C:\Users\admin\Desktop\file.exe" | C:\Users\admin\Desktop\file.exe | explorer.exe | ||||||||||||
User: admin Company: Daniel Pistelli Integrity Level: MEDIUM Description: Common File Format Explorer Version: 8.0.0.0 Modules
| |||||||||||||||
Total events
486
Read events
485
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6956) file.exe | Key: | HKEY_CURRENT_USER\Software\SibCode |
| Operation: | write | Name: | sn3 |
Value: E6F6F68A7CA3A55AB69713F50FB62779DE46F43192ADD42D2AD2241C9DBEC516A2EBD80AFB255CE4AFB0B1EE90AFFCB94666B19E396E1381C750A5D0EAA27DF5 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
51
DNS requests
36
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6848 | rundll32.exe | GET | 304 | 88.221.110.106:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c1fd398a593704ee | unknown | — | — | whitelisted |
5488 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
5488 | firefox.exe | POST | 200 | 95.101.54.131:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5488 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
5488 | firefox.exe | POST | 200 | 95.101.54.211:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
1296 | svchost.exe | GET | 200 | 23.55.161.193:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.213.164.137:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
6688 | MoUsoCoreWorker.exe | GET | 304 | 88.221.110.106:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7186fbe7c9da15cf | unknown | — | — | whitelisted |
2860 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?bdb78aa50ddaee77 | unknown | — | — | whitelisted |
3460 | svchost.exe | GET | 304 | 88.221.110.106:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?26abb5ca7fe49d8d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6848 | rundll32.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5052 | OfficeC2RClient.exe | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
5488 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
5488 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
1296 | svchost.exe | 23.55.161.193:80 | — | Akamai International B.V. | DE | unknown |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6848 | rundll32.exe | 88.221.110.106:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
5052 | OfficeC2RClient.exe | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5488 | firefox.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ecs.office.com |
| whitelisted |
r10.o.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1296 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
Process | Message |
|---|---|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|