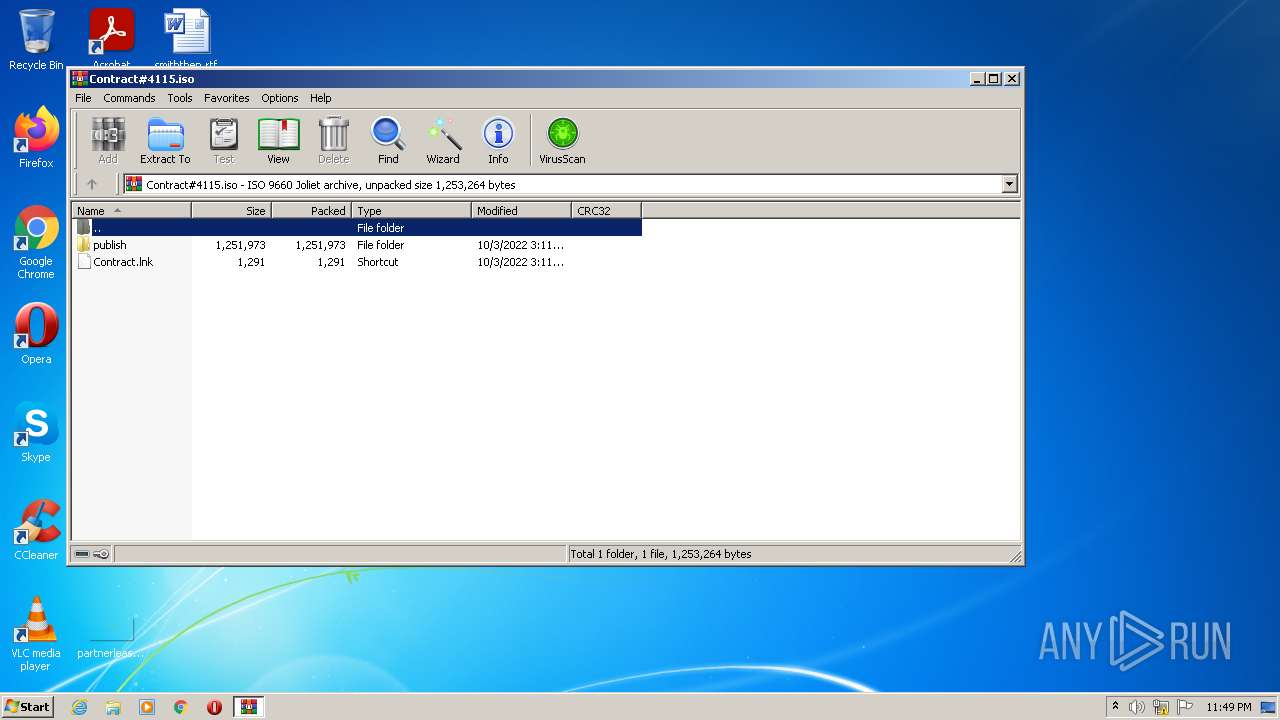
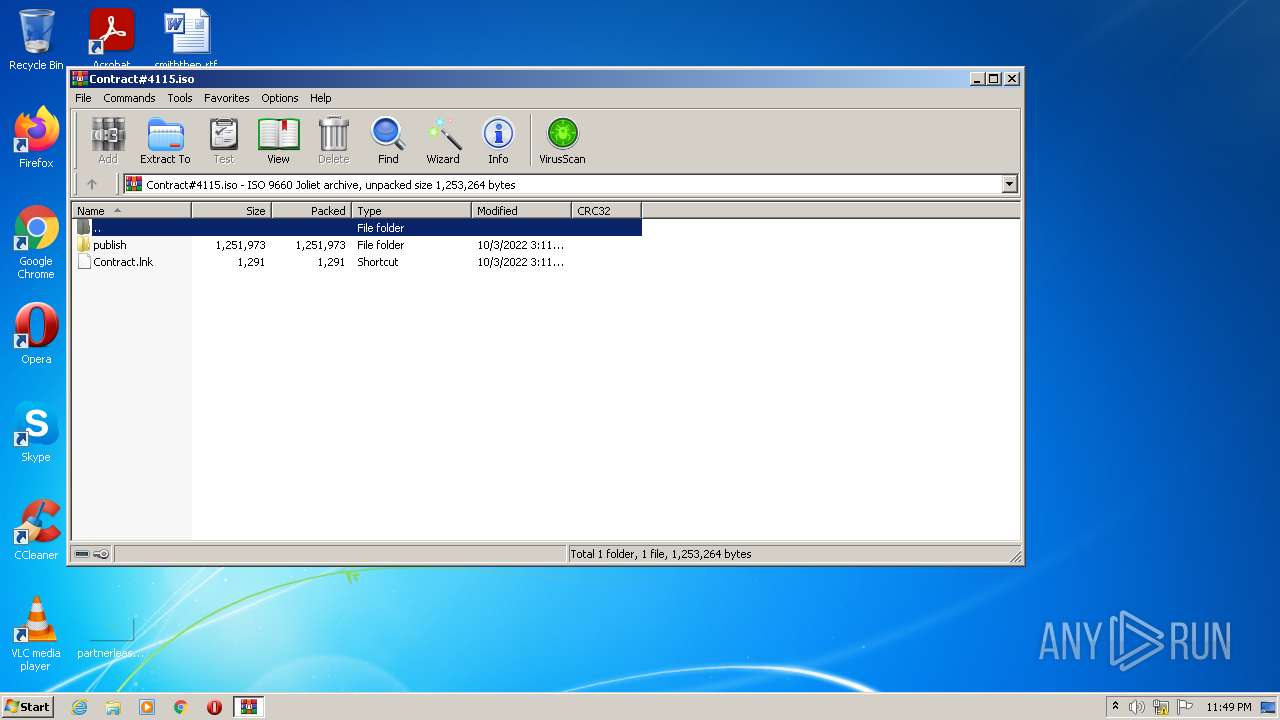
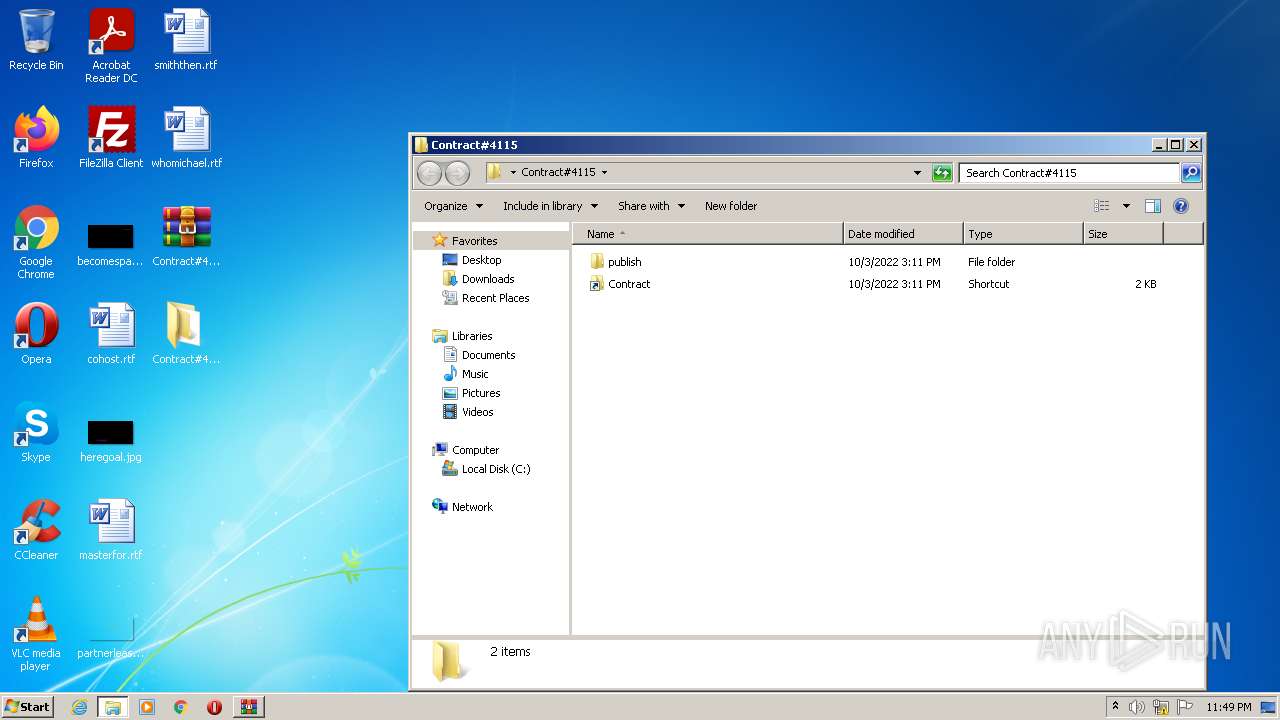
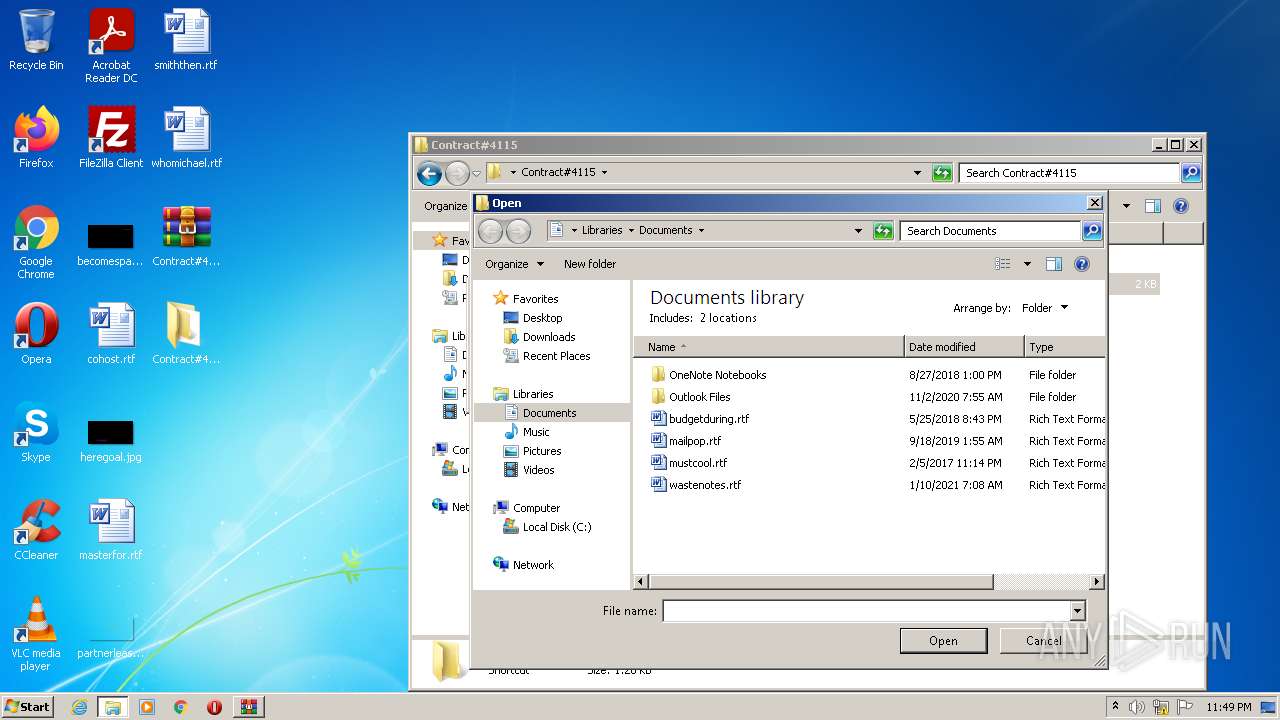
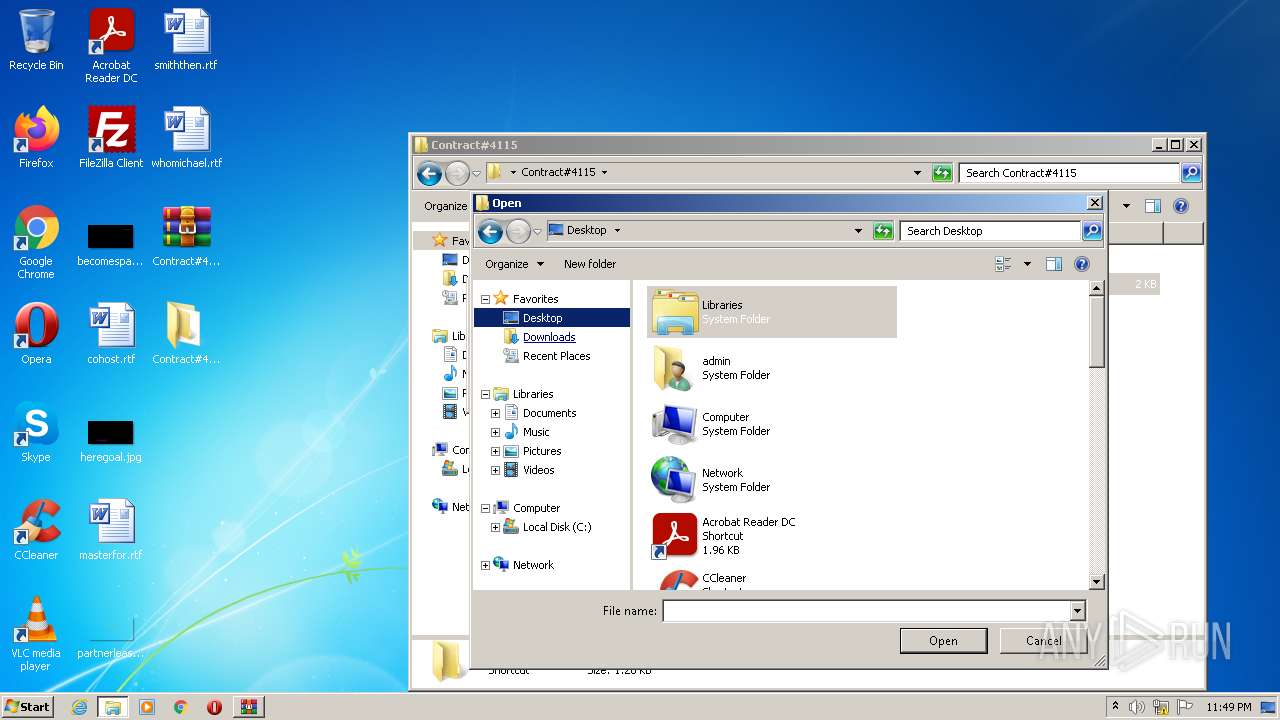
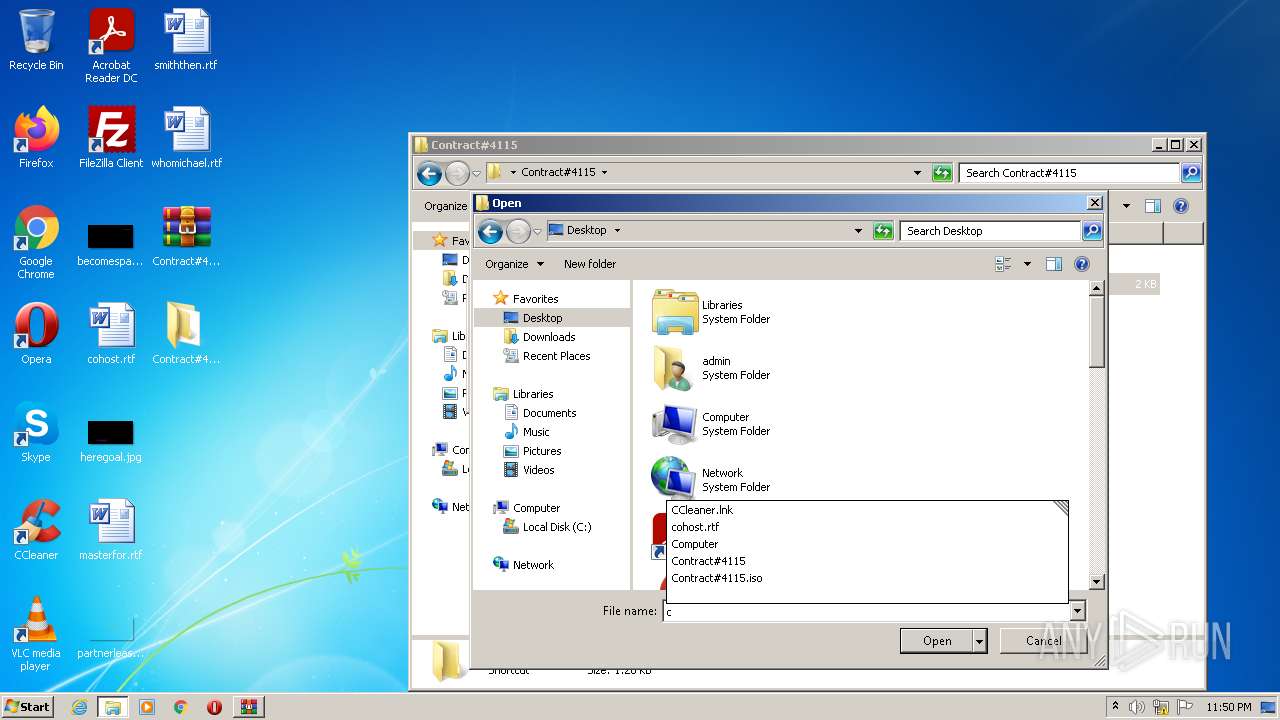
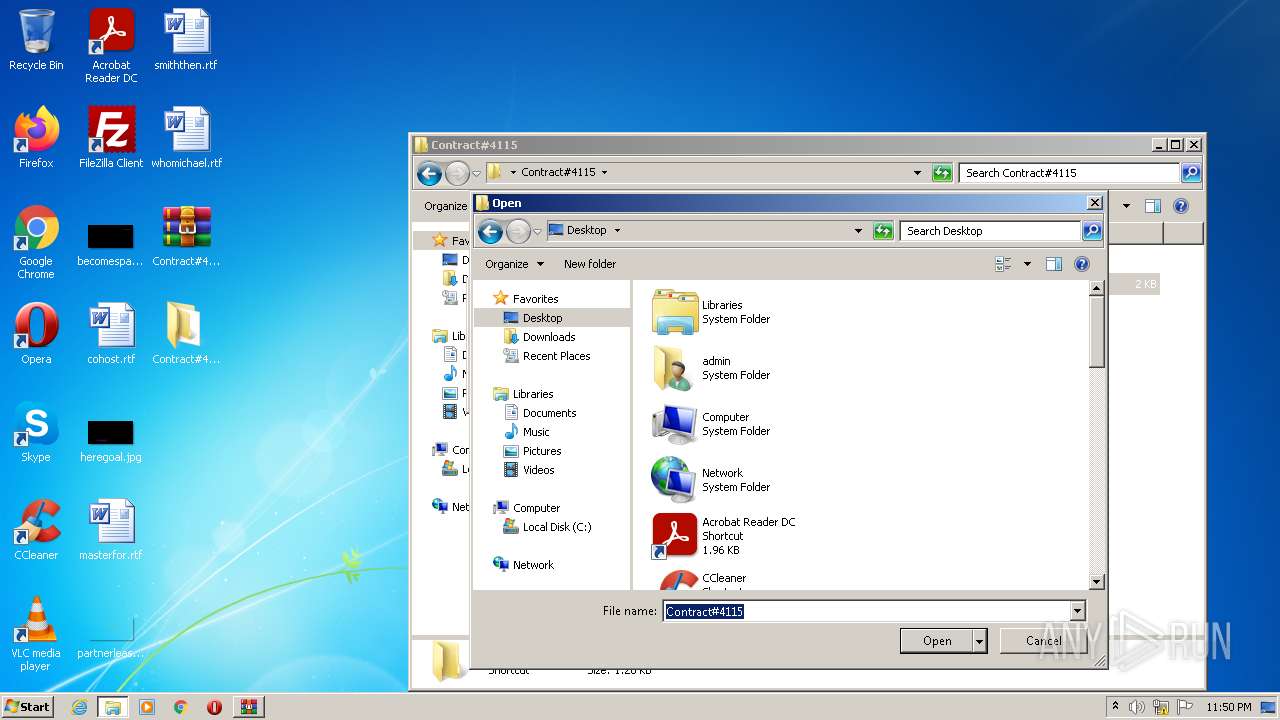
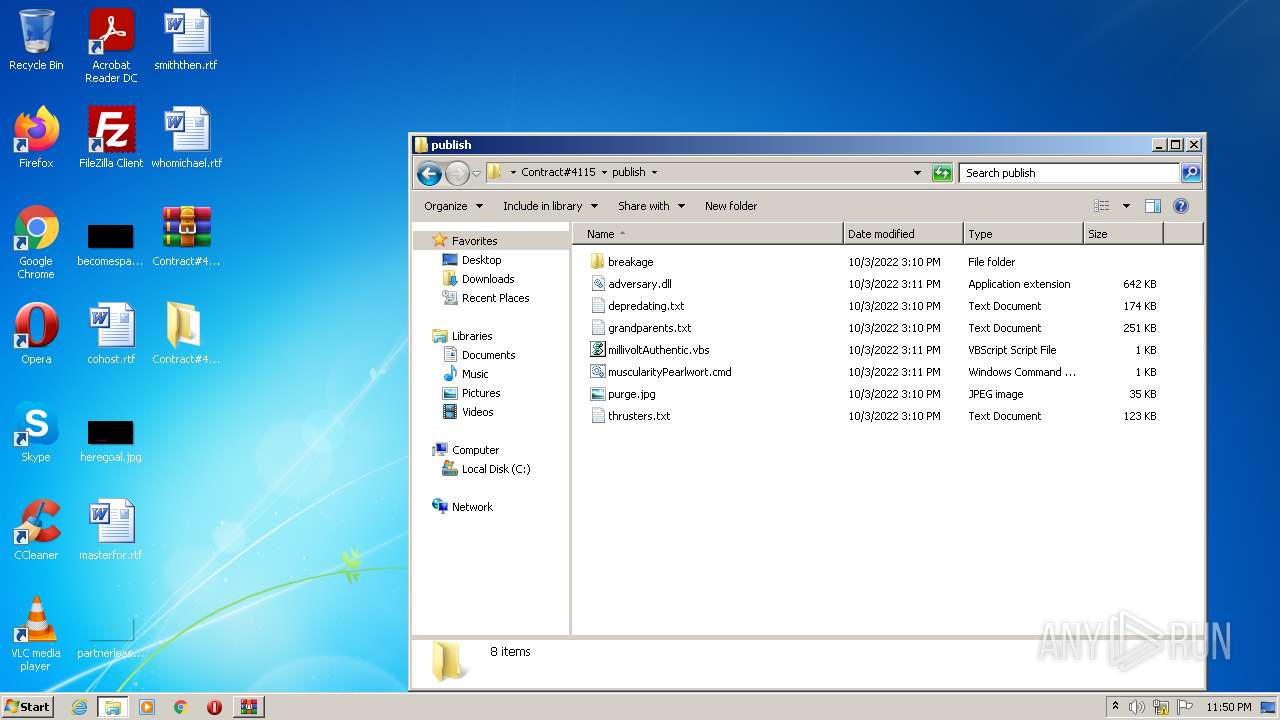
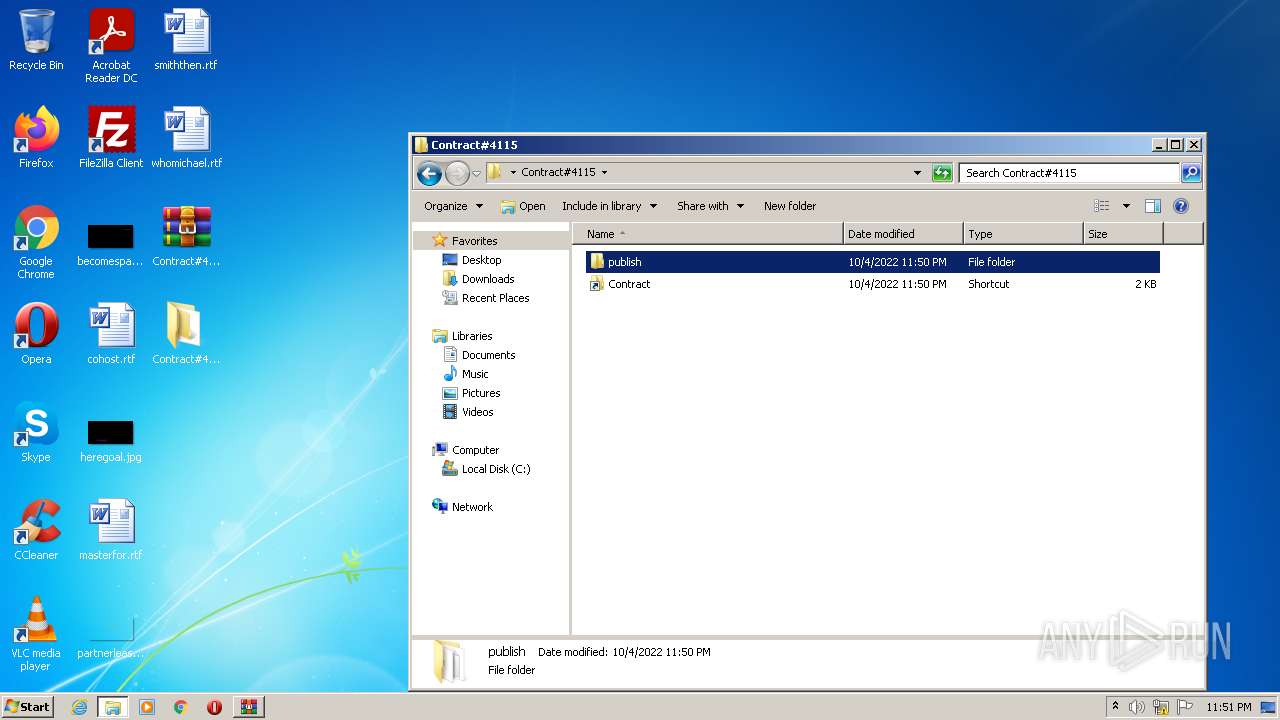
| File name: | Contract#4115.iso |
| Full analysis: | https://app.any.run/tasks/8ccd8e73-383c-4bb7-9562-34a418f3ef33 |
| Verdict: | Malicious activity |
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
| Analysis date: | October 04, 2022, 22:49:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-iso9660-image |
| File info: | ISO 9660 CD-ROM filesystem data 'CD_ROM' |
| MD5: | 255E8EB50654B3413D3025AB46C112C7 |
| SHA1: | BBAFF6350C529B92BD6030B010D5F9698A0F6E7B |
| SHA256: | 5140F0D1ED4BF989558F4DB7E1F385AE4DE5E9082E7203F36505E3F6BE4FD728 |
| SSDEEP: | 24576:X2j1do5WFEJ4B38MPwFOHrwcwjHmvwiK7Jb0y/cT5SL8uj3HH:X5lJI3BwFOHrwcwjHmvwiKb1/cT5S53n |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 3232)
- Explorer.EXE (PID: 1488)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3884)
- Explorer.EXE (PID: 1488)
- rundll32.exe (PID: 2200)
QBOT detected by memory dumps
- wermgr.exe (PID: 3256)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3232)
- Explorer.EXE (PID: 1488)
Creates files in the user directory
- Explorer.EXE (PID: 1488)
Reads the computer name
- WinRAR.exe (PID: 3232)
- WScript.exe (PID: 1388)
- WScript.exe (PID: 416)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3232)
- Explorer.EXE (PID: 1488)
Checks supported languages
- WinRAR.exe (PID: 3232)
- WScript.exe (PID: 1388)
- WScript.exe (PID: 416)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 1568)
Executes scripts
- Explorer.EXE (PID: 1488)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 1388)
- WScript.exe (PID: 416)
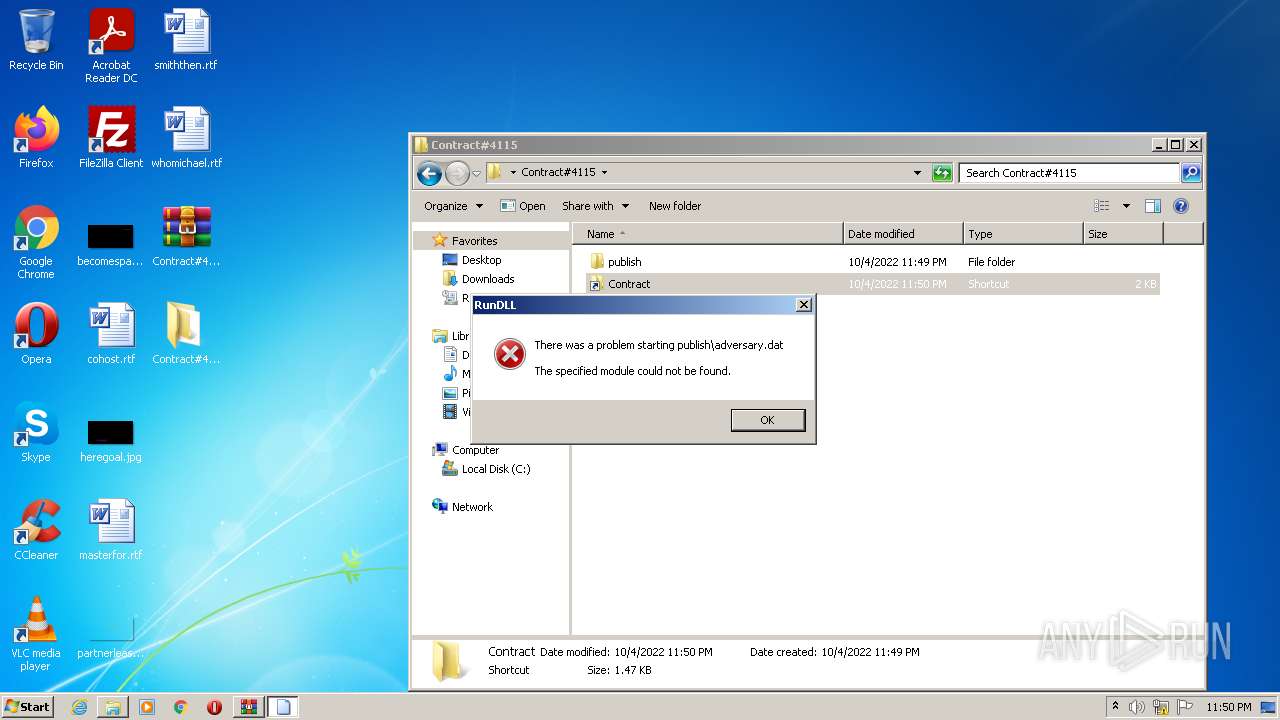
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 3820)
- Explorer.EXE (PID: 1488)
- cmd.exe (PID: 1568)
INFO
Checks Windows Trust Settings
- WScript.exe (PID: 1388)
- WScript.exe (PID: 416)
Checks supported languages
- rundll32.exe (PID: 3260)
- rundll32.exe (PID: 2200)
- wermgr.exe (PID: 3256)
- rundll32.exe (PID: 2084)
Reads the computer name
- rundll32.exe (PID: 2200)
- rundll32.exe (PID: 3260)
- wermgr.exe (PID: 3256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .iso | | | ISO 9660 CD image (27.6) |
|---|---|---|
| .atn | | | Photoshop Action (27.1) |
| .gmc | | | Game Music Creator Music (6.1) |
Total processes
55
Monitored processes
11
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
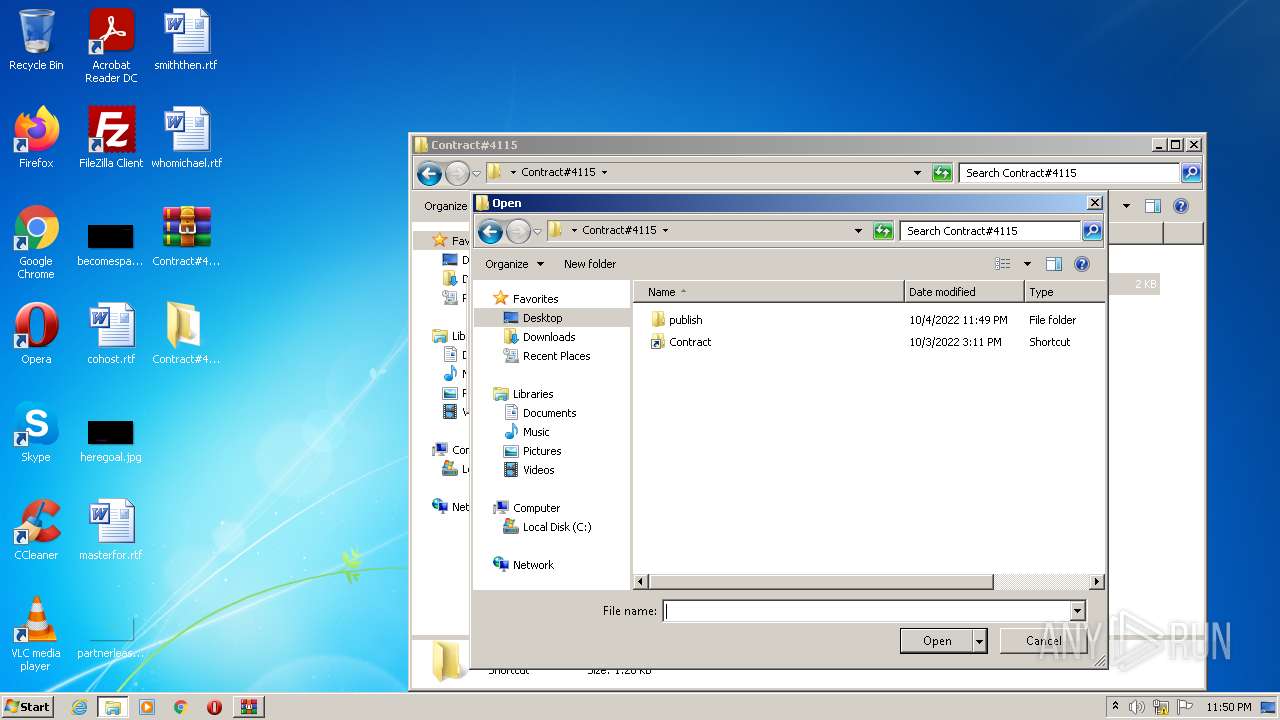
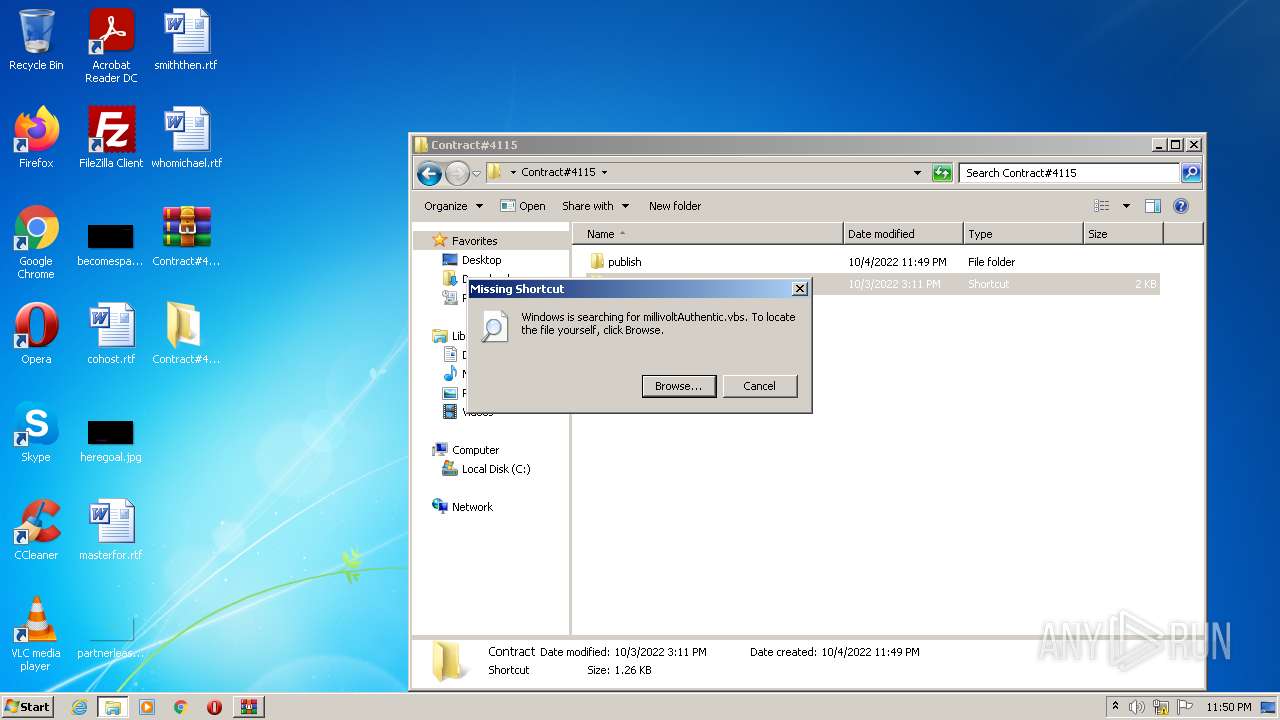
| 416 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Contract#4115\publish\millivoltAuthentic.vbs" | C:\Windows\System32\WScript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1388 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Contract#4115\publish\millivoltAuthentic.vbs" | C:\Windows\System32\WScript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1488 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
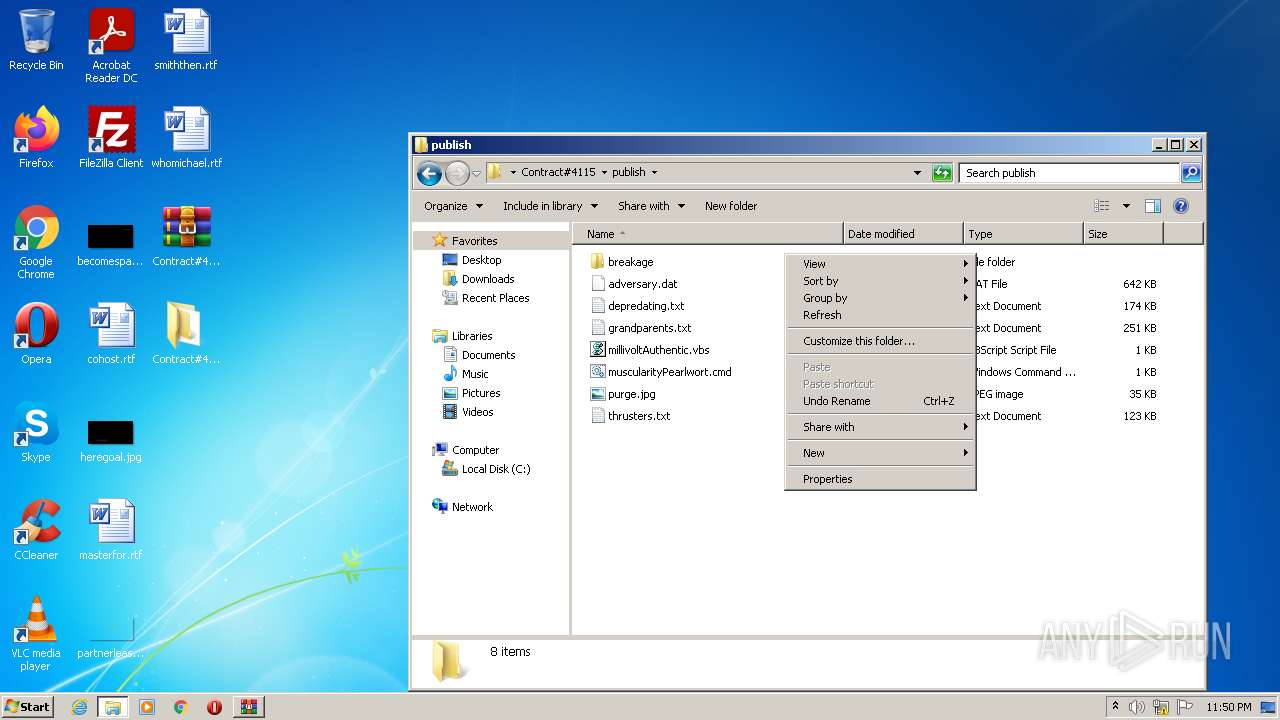
| 1568 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Contract#4115\publish\muscularityPearlwort.cmd" rund" | C:\Windows\system32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
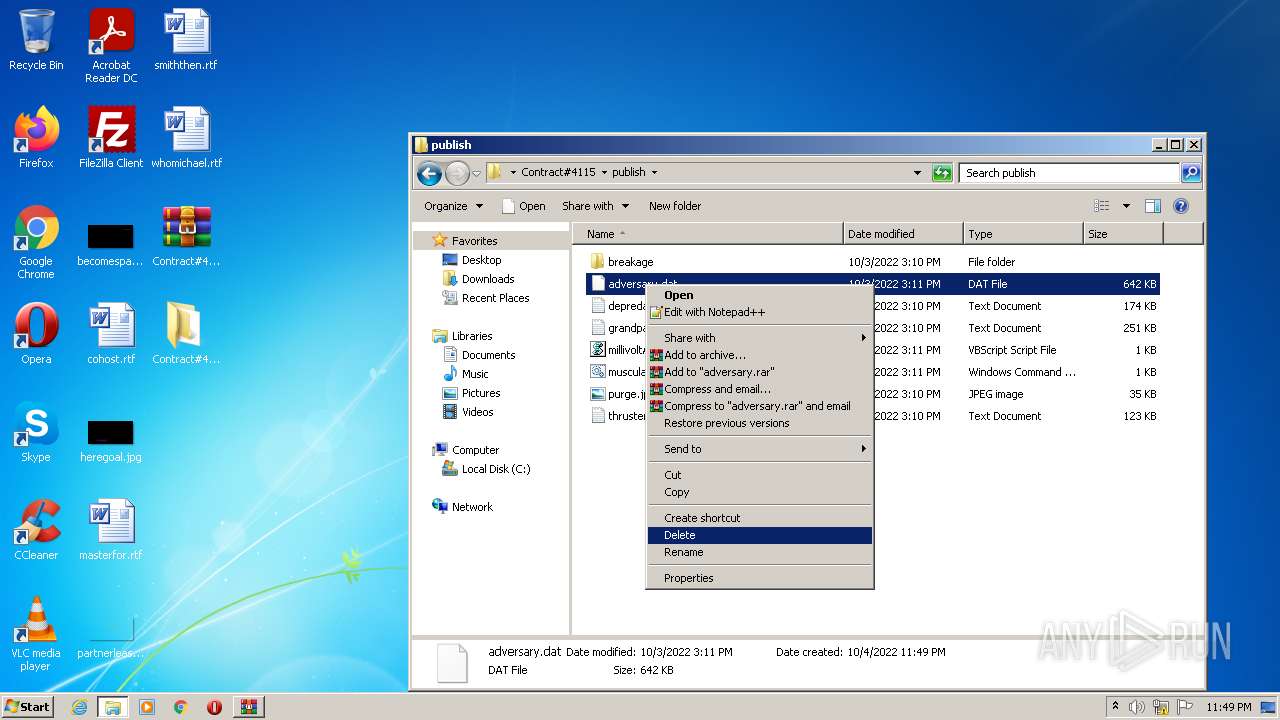
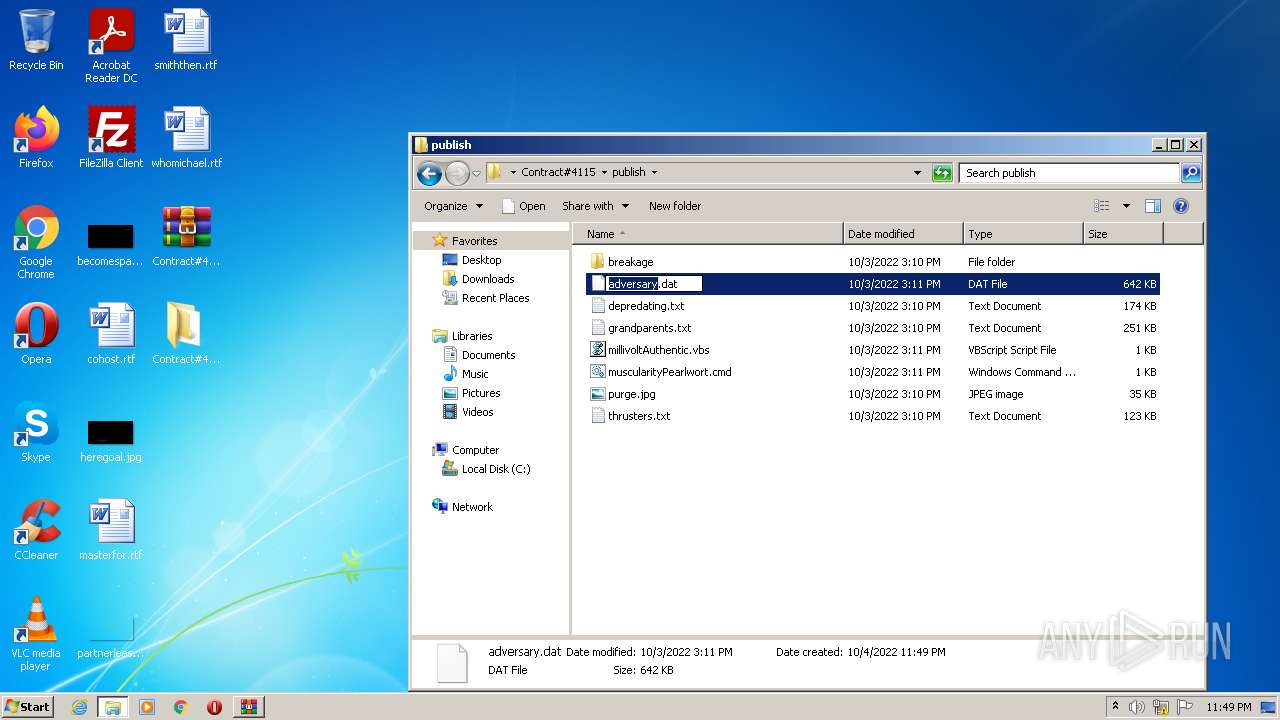
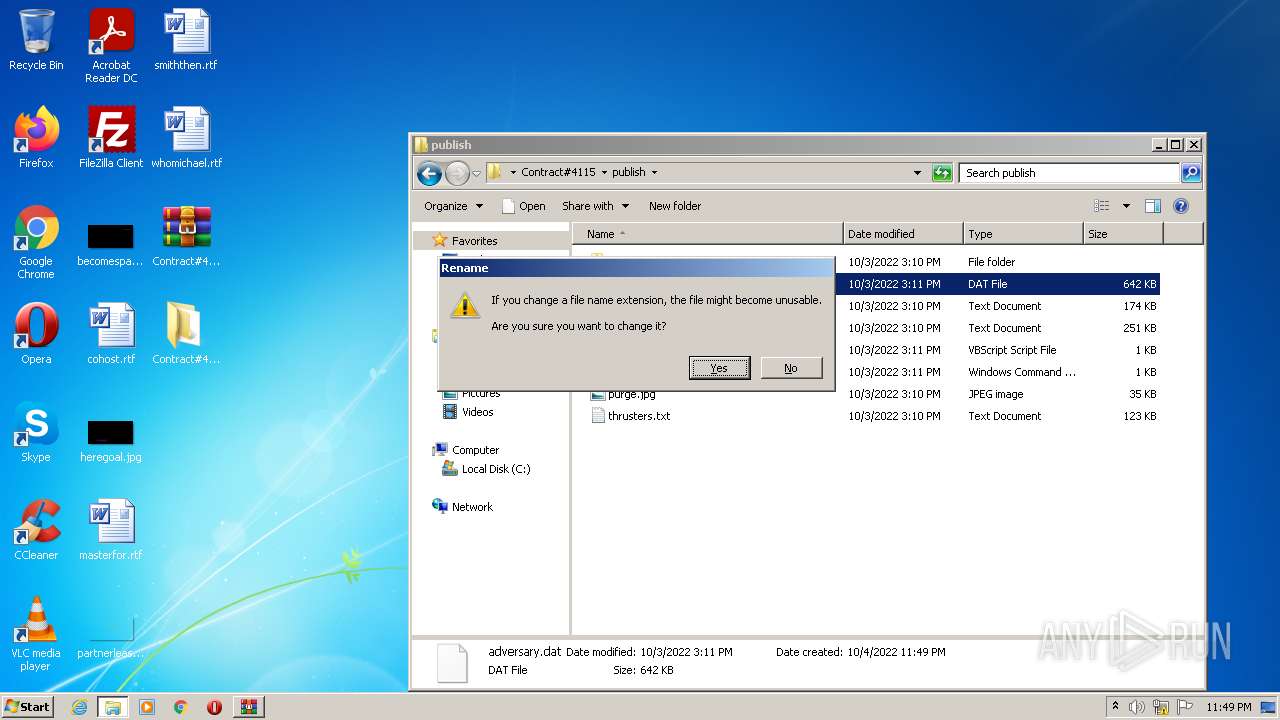
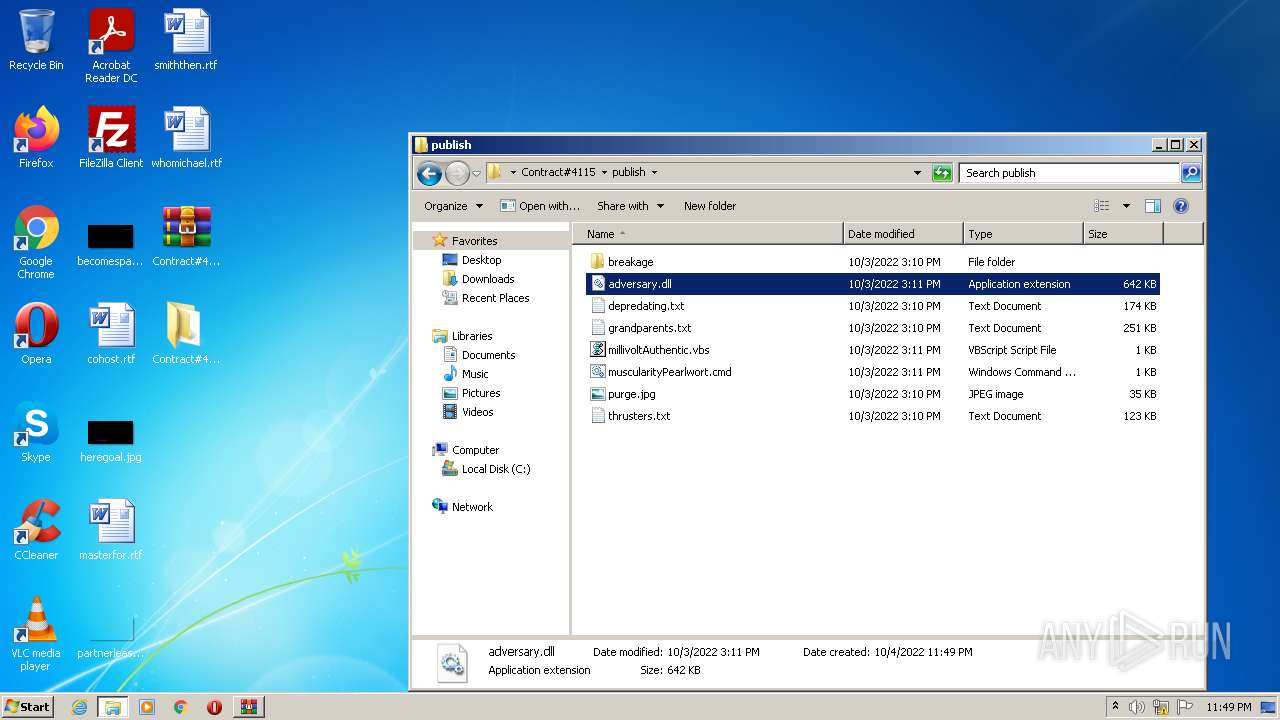
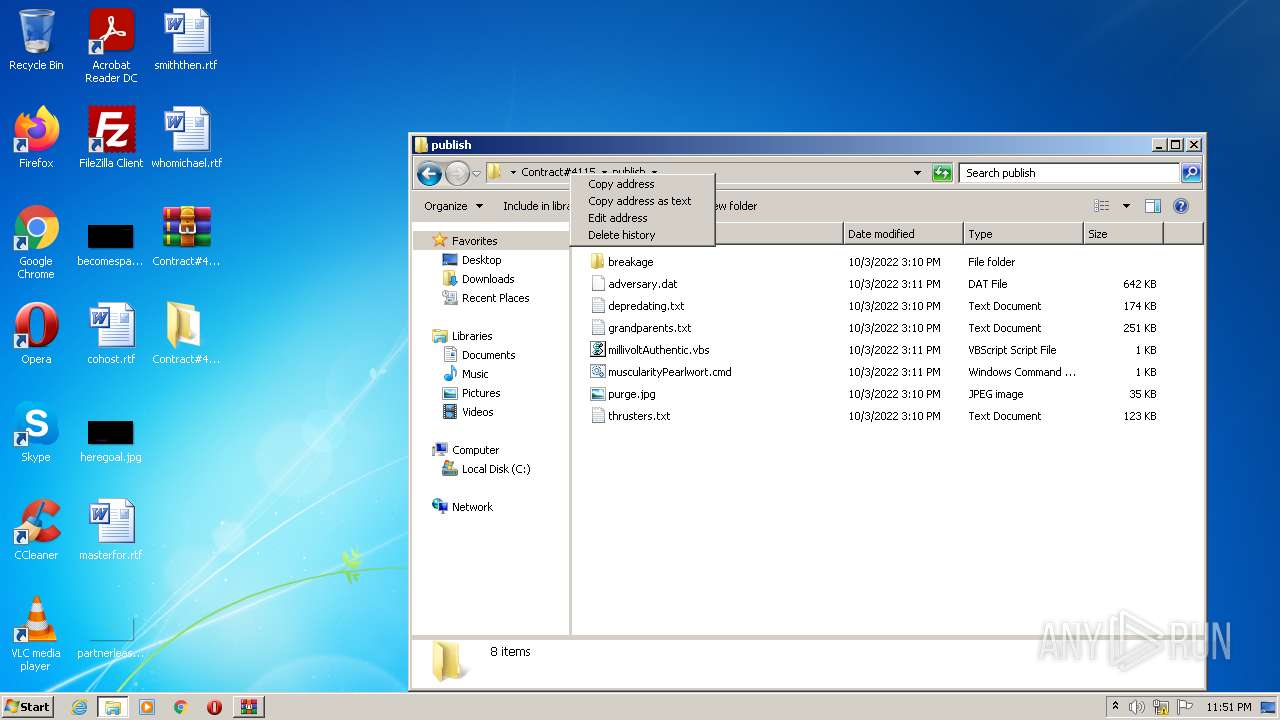
| 2084 | rundll32 publish\adversary.dat,DllRegisterServer | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | rundll32 publish\adversary.dat,DllRegisterServer | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3232 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Contract#4115.iso" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3256 | C:\Windows\System32\wermgr.exe | C:\Windows\System32\wermgr.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7601.24521 (win7sp1_ldr_escrow.190909-1704) Modules
| |||||||||||||||
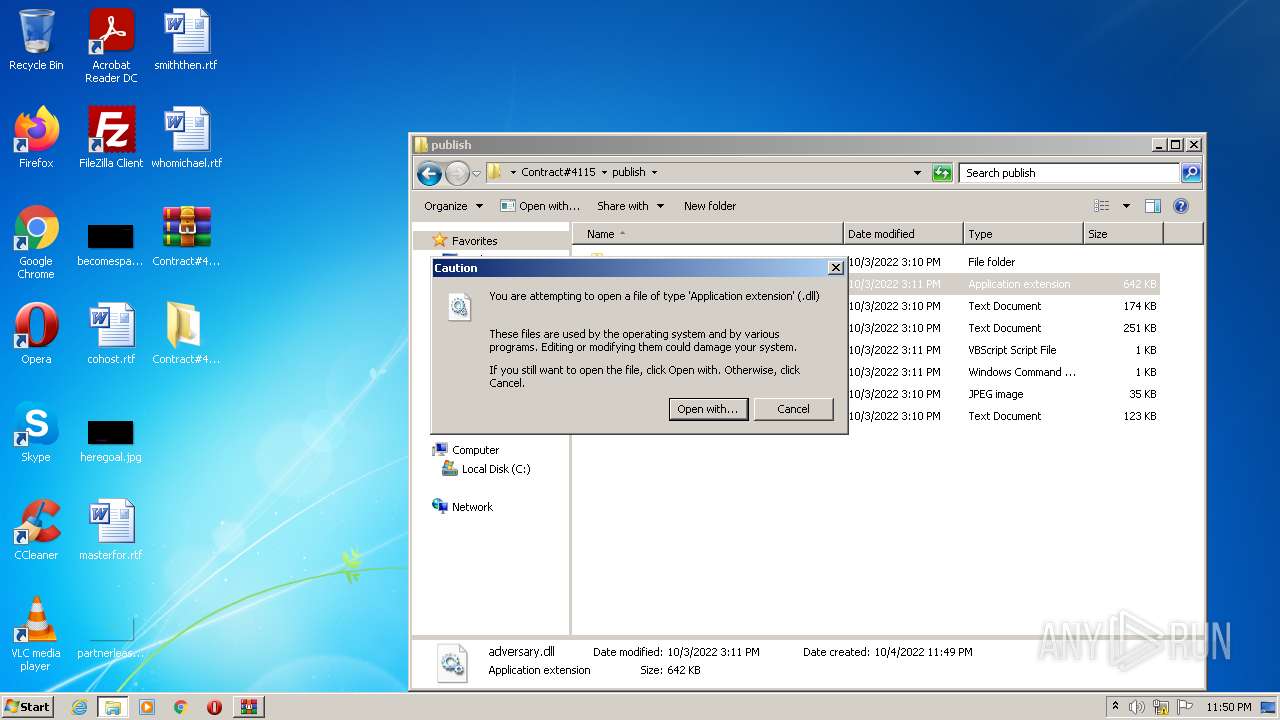
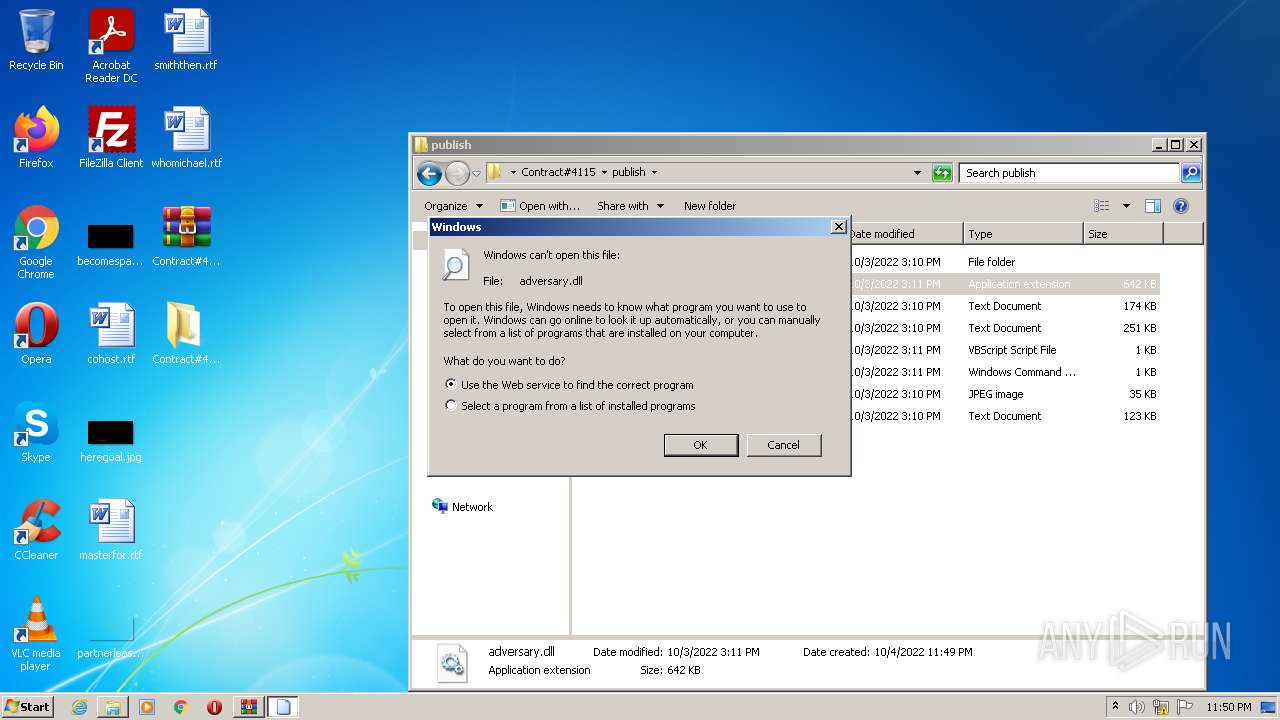
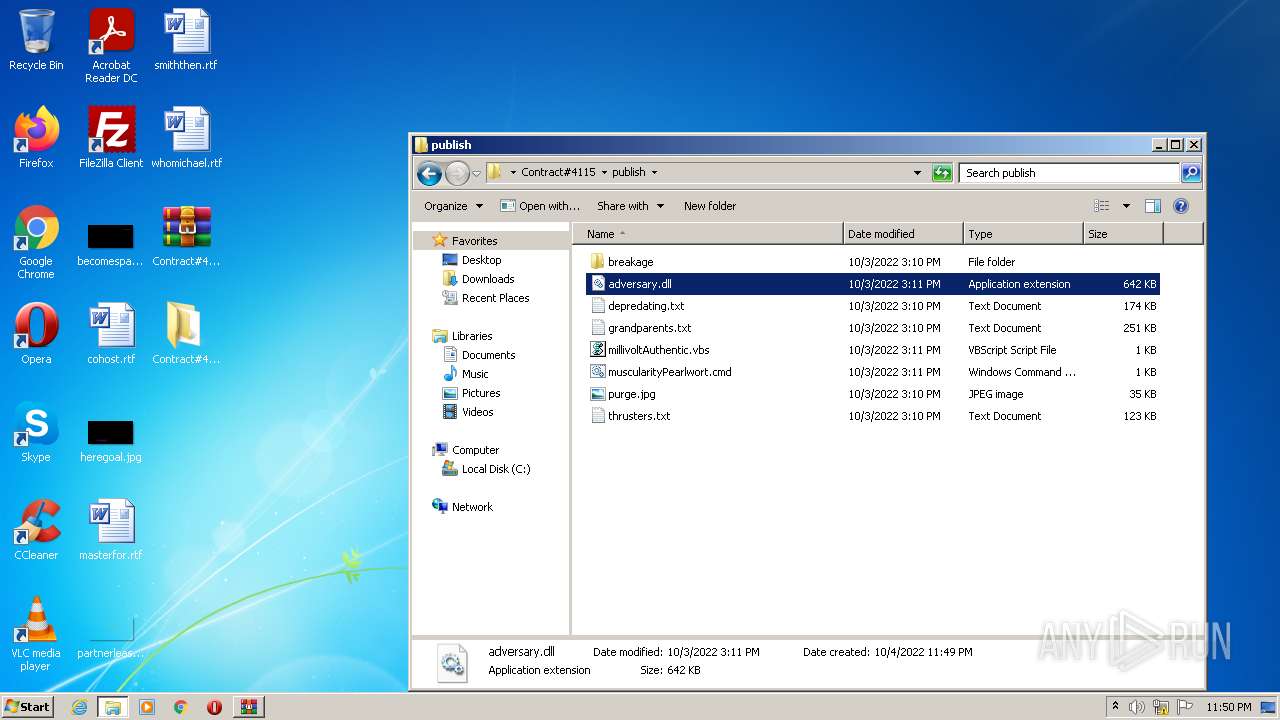
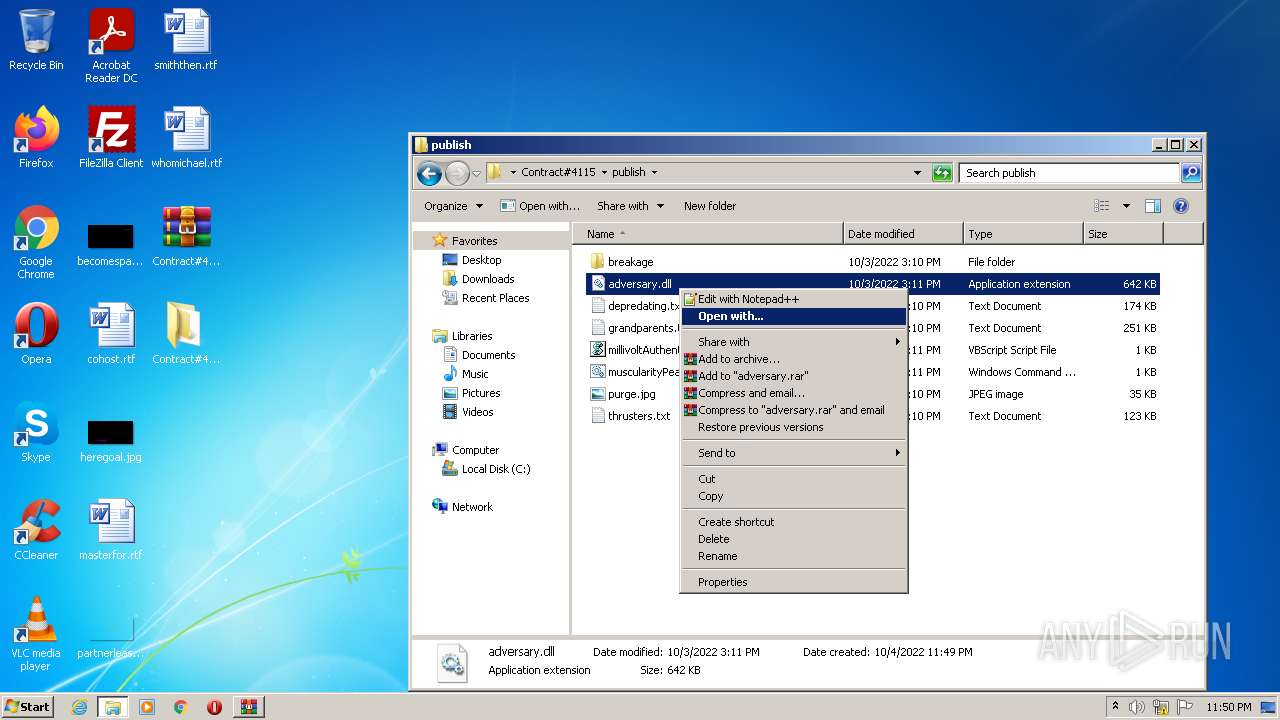
| 3260 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\Contract#4115\publish\adversary.dll | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3820 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Contract#4115\publish\muscularityPearlwort.cmd" rund" | C:\Windows\system32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
12 511
Read events
12 033
Write events
473
Delete events
5
Modification events
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Contract#4115.iso | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
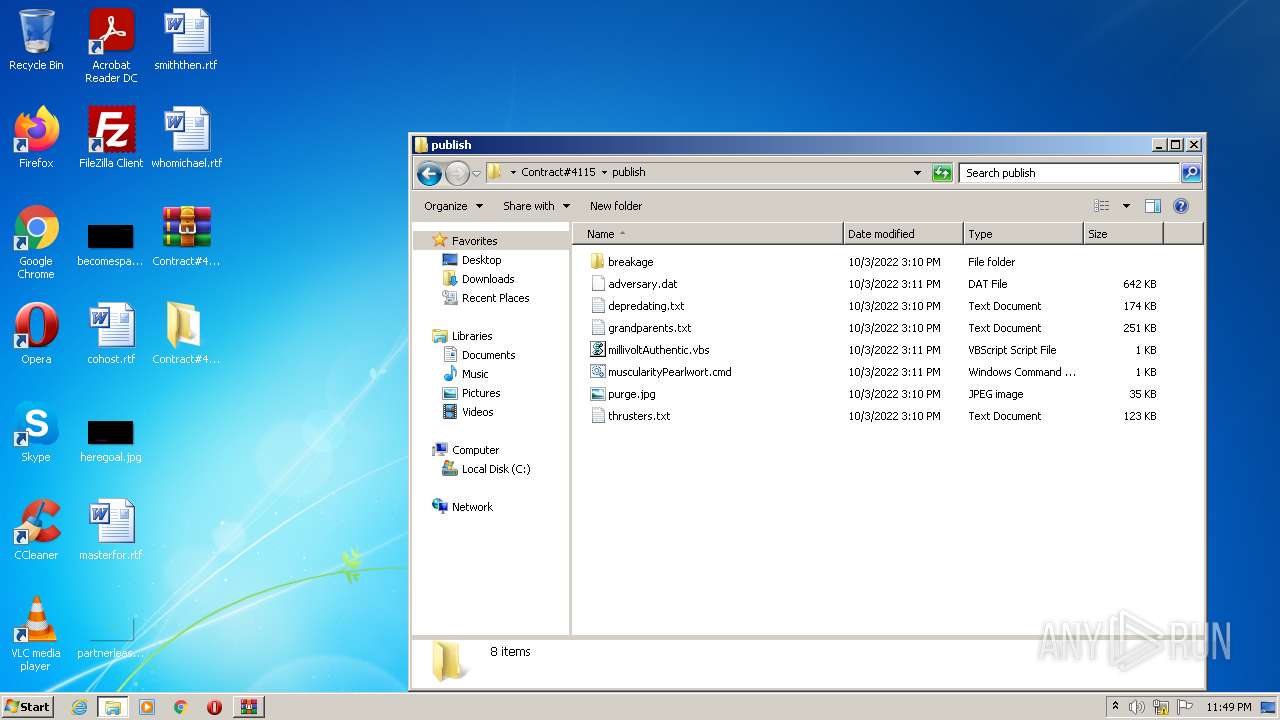
Executable files
3
Suspicious files
0
Text files
6
Unknown types
9
Dropped files
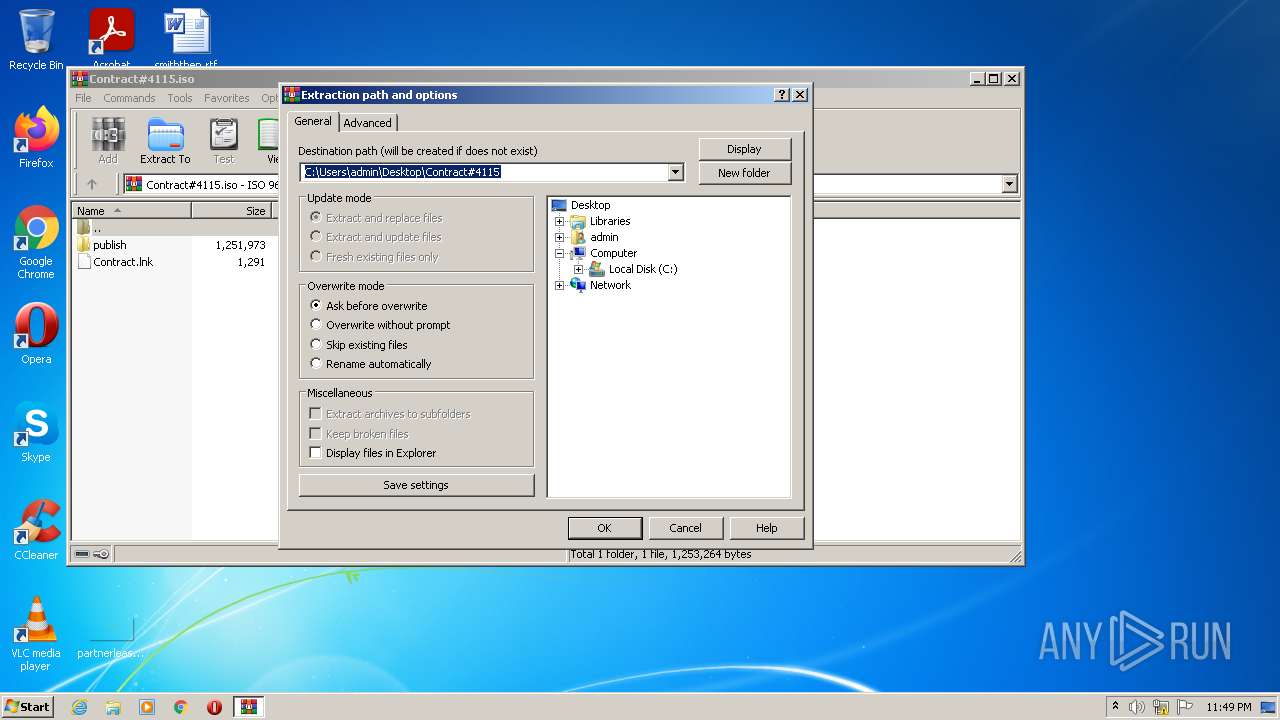
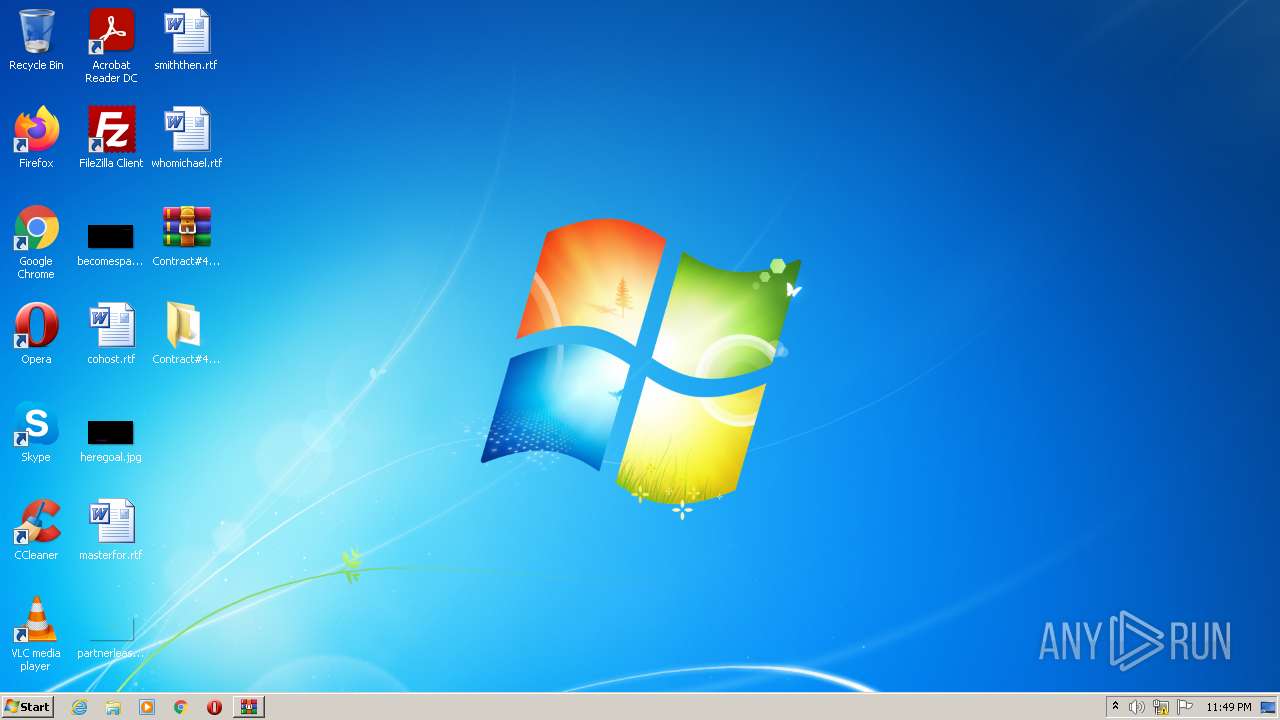
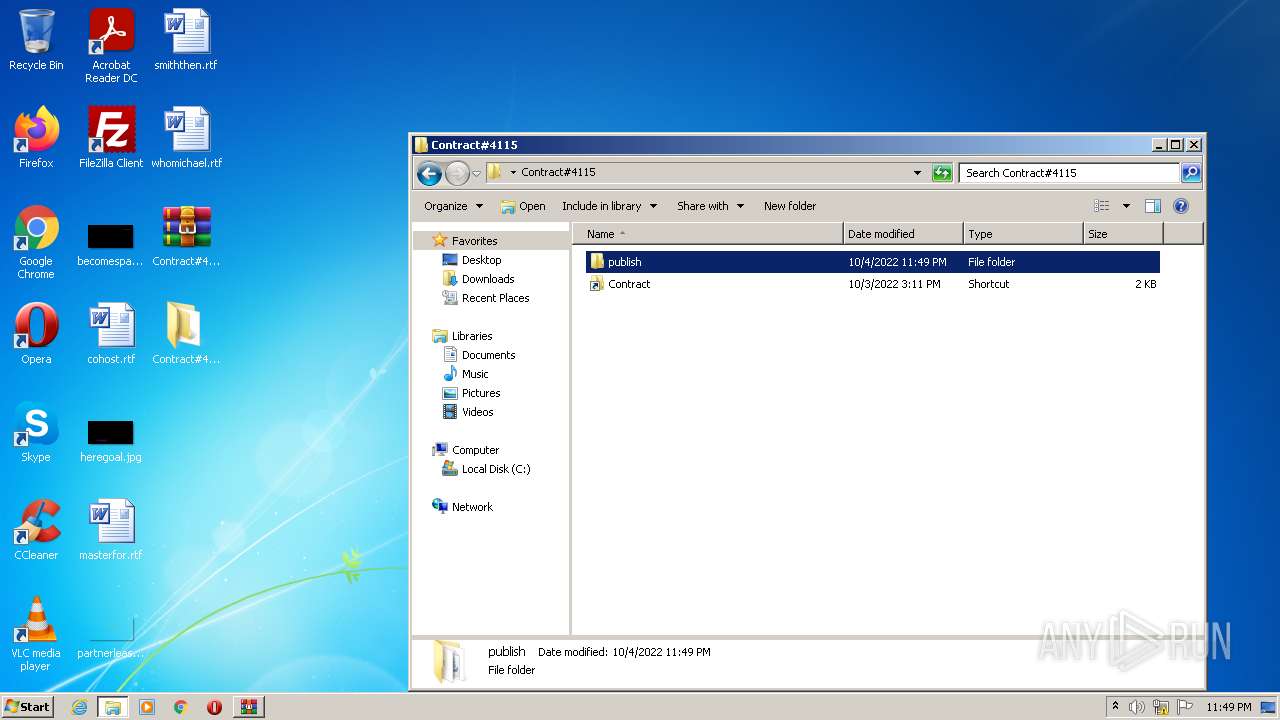
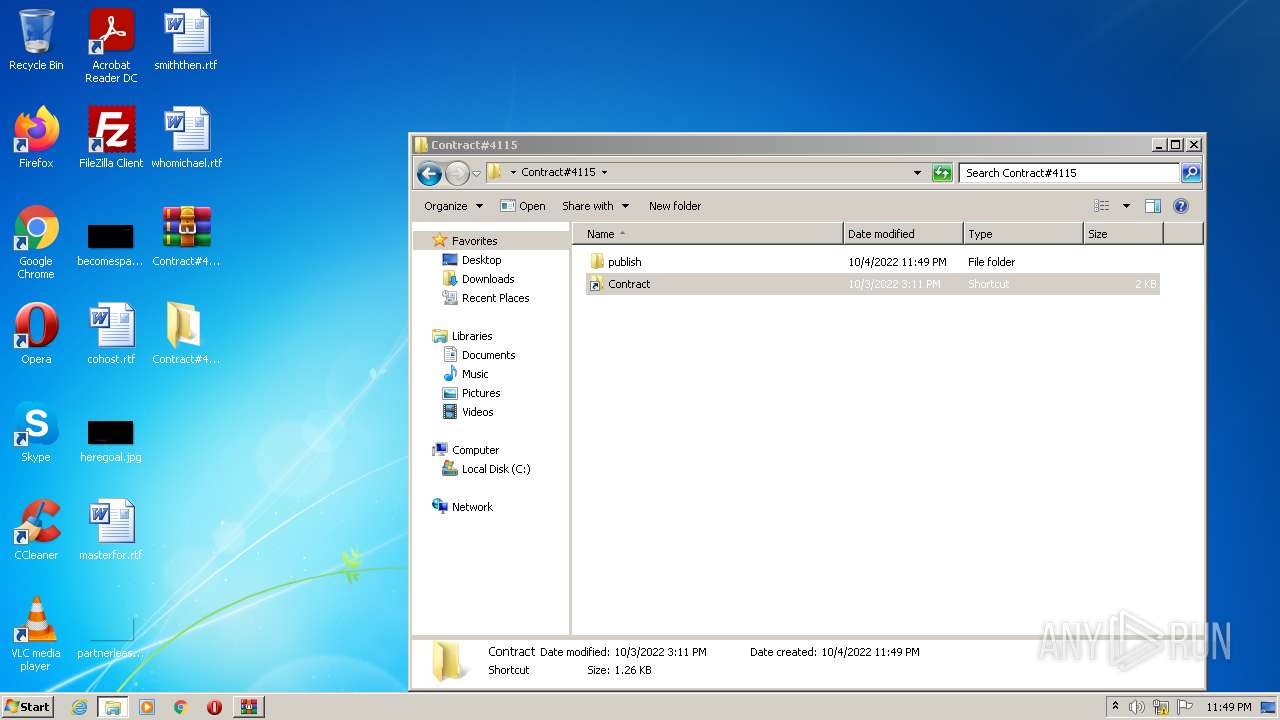
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1488 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 1488 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
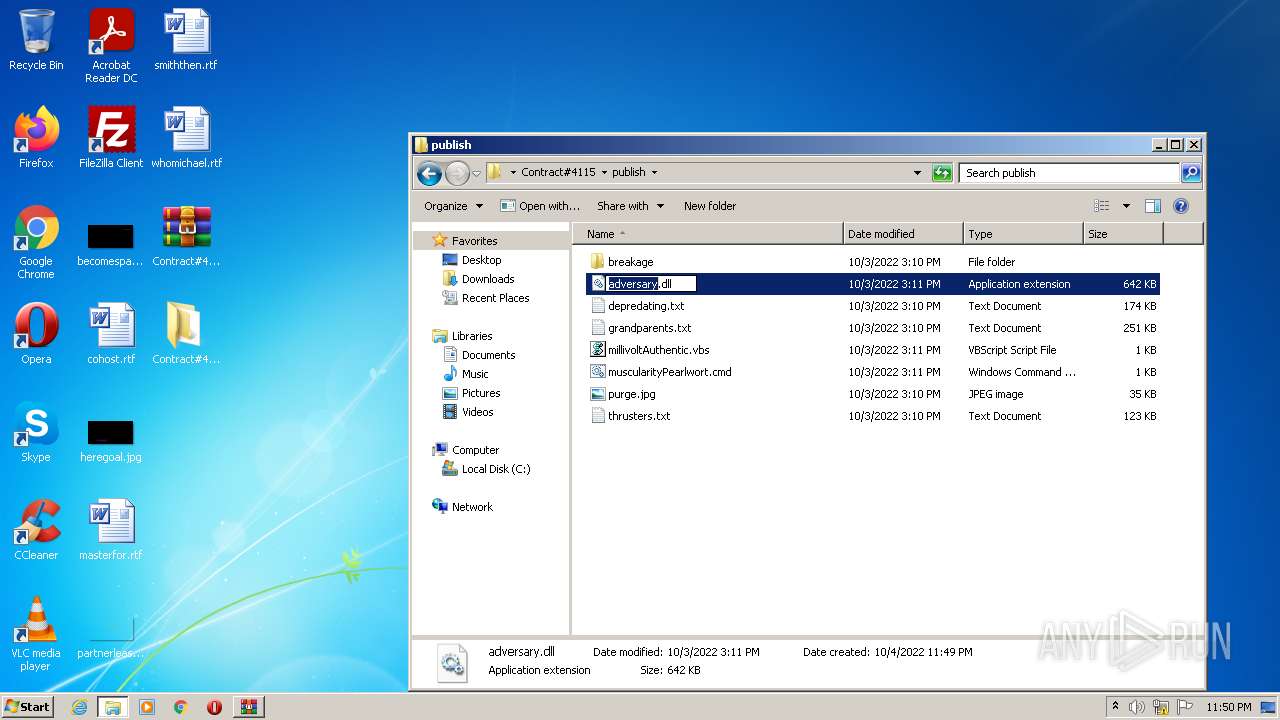
| 3232 | WinRAR.exe | C:\Users\admin\Desktop\Contract#4115\publish\grandparents.txt | text | |
MD5:— | SHA256:— | |||
| 1488 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Contract#4115.iso.lnk | lnk | |
MD5:— | SHA256:— | |||
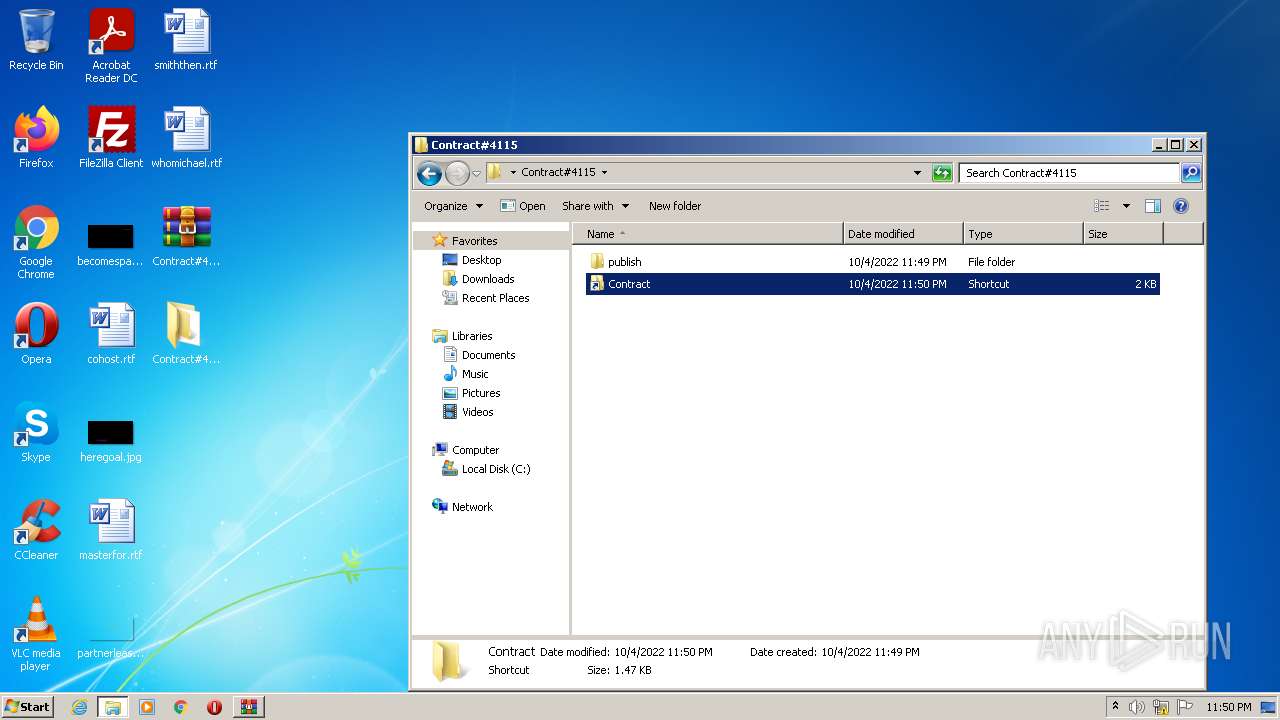
| 1488 | Explorer.EXE | C:\Users\admin\Desktop\Contract#4115\publish\adversary.dll | executable | |
MD5:— | SHA256:— | |||
| 3232 | WinRAR.exe | C:\Users\admin\Desktop\Contract#4115\publish\purge.jpg | image | |
MD5:— | SHA256:— | |||
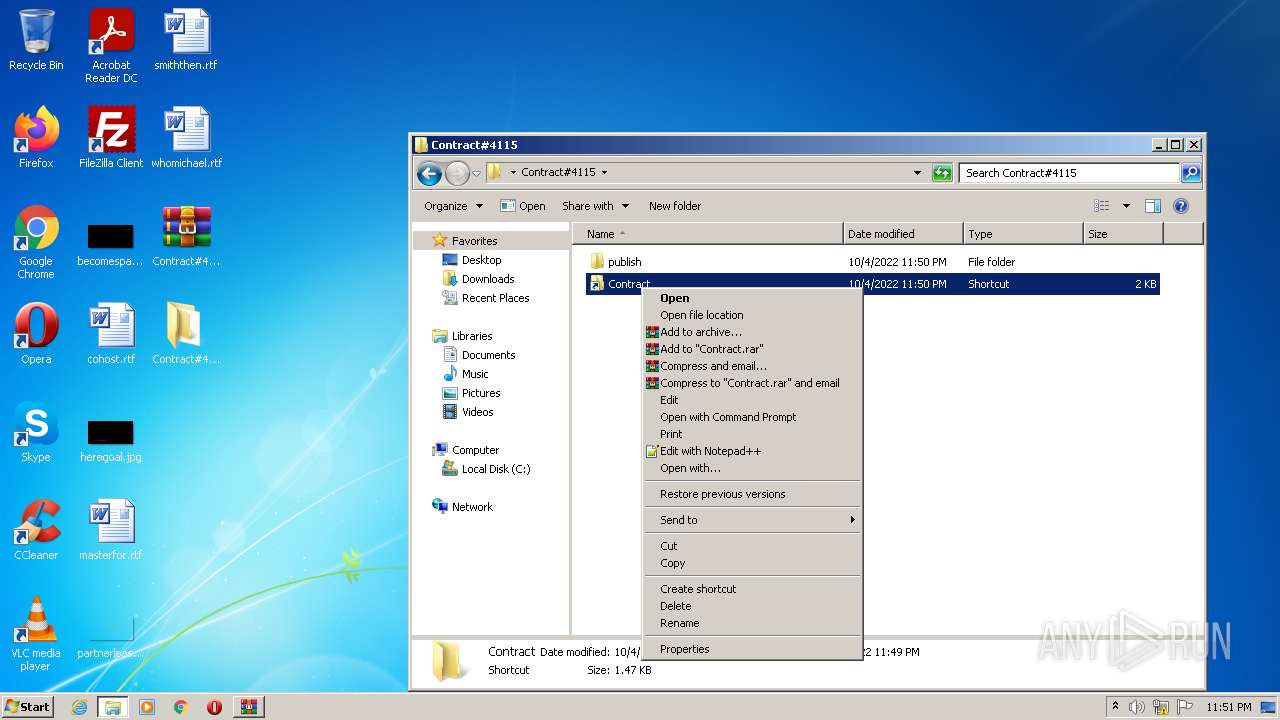
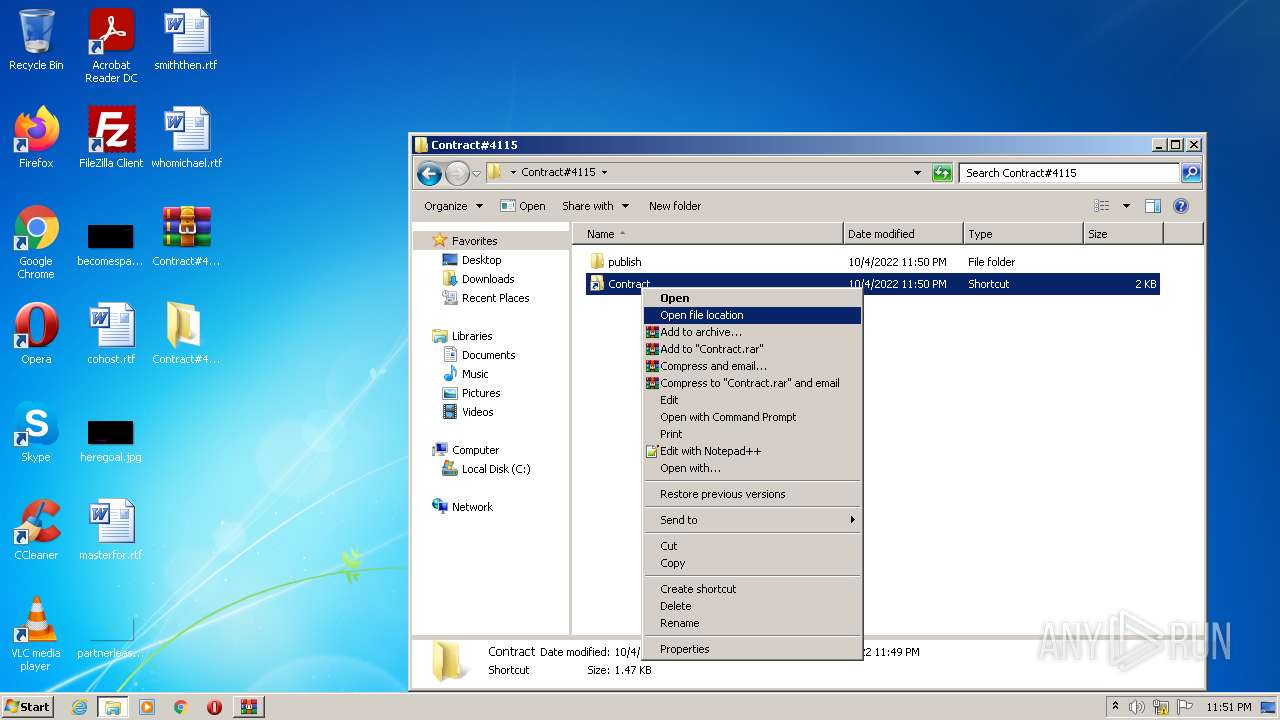
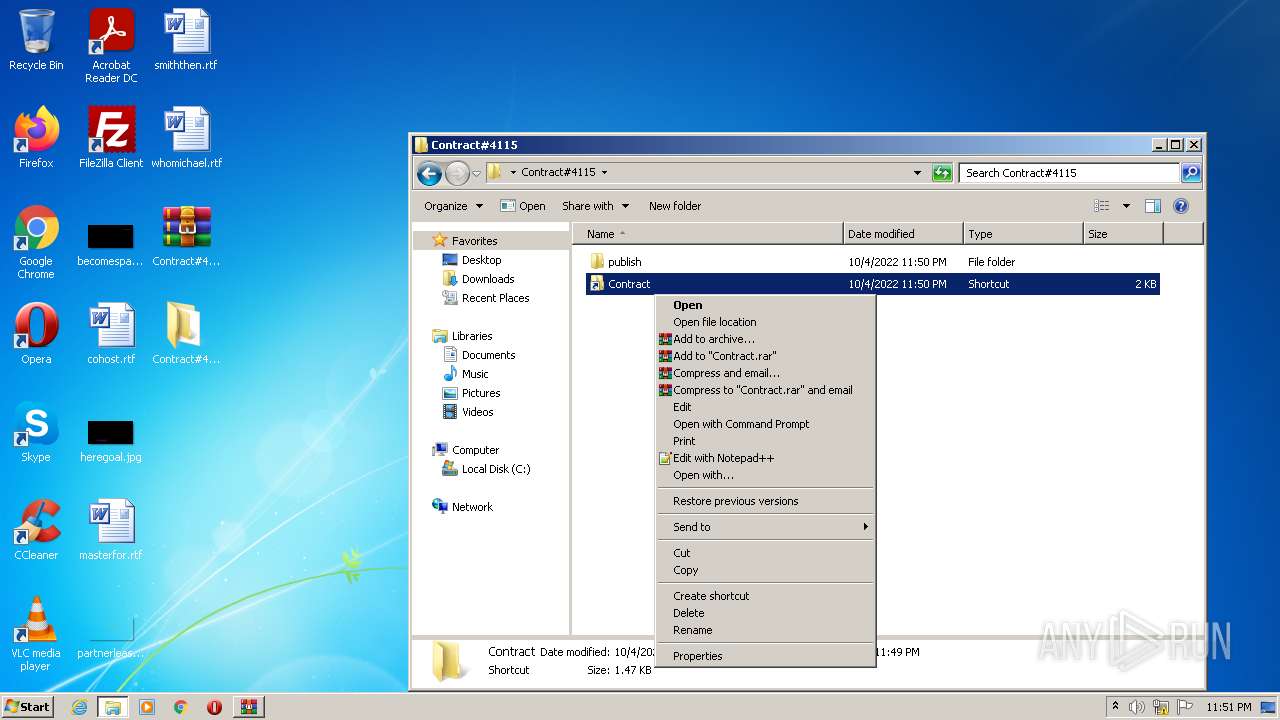
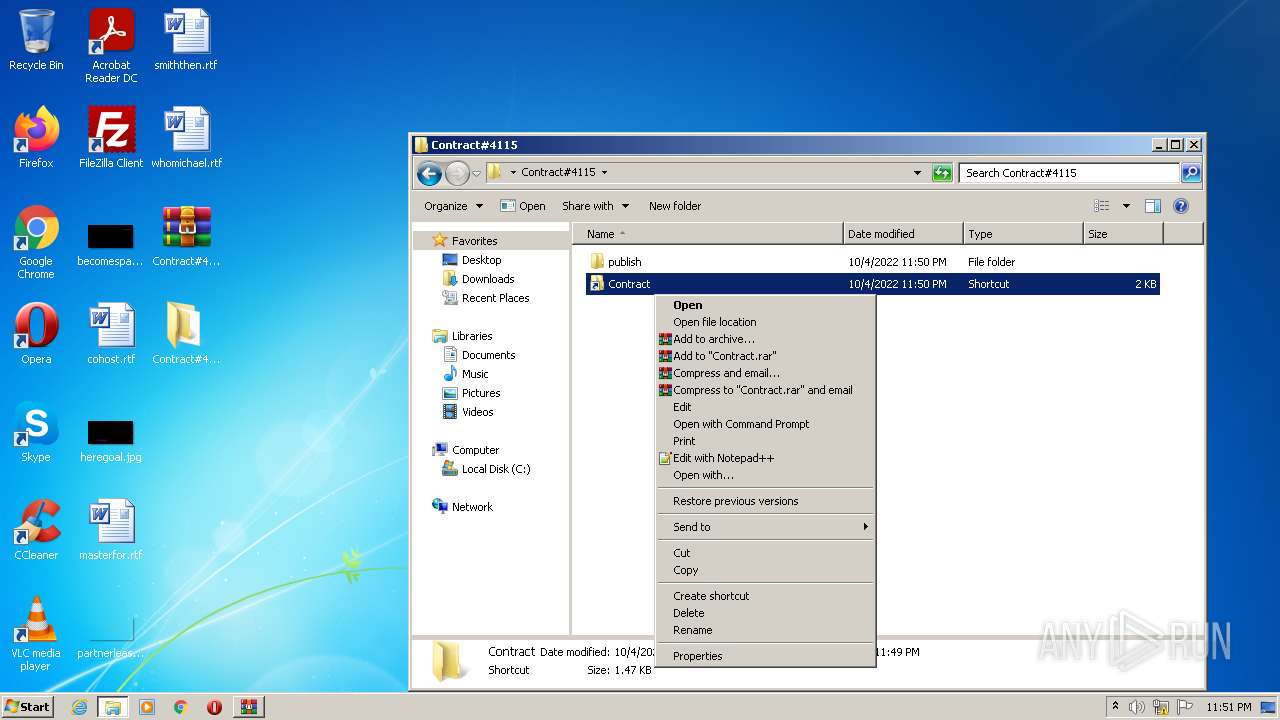
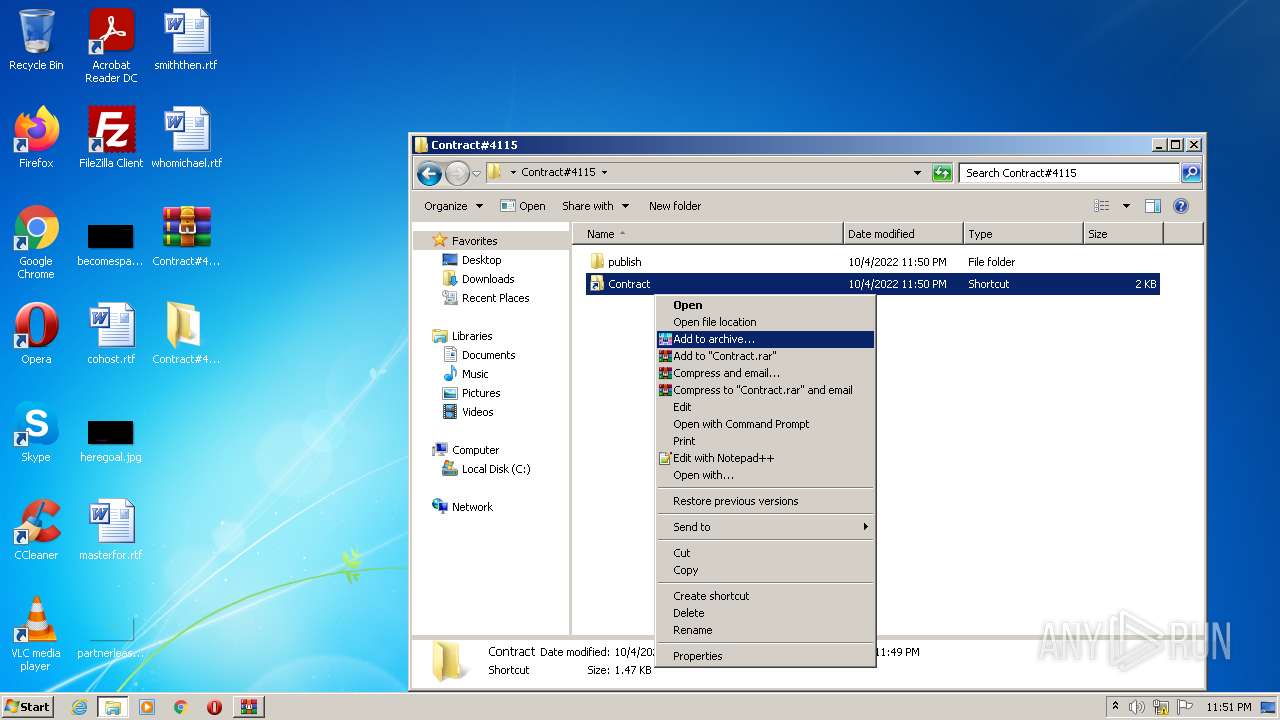
| 3232 | WinRAR.exe | C:\Users\admin\Desktop\Contract#4115\Contract.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3232 | WinRAR.exe | C:\Users\admin\Desktop\Contract#4115\publish\muscularityPearlwort.cmd | text | |
MD5:— | SHA256:— | |||
| 1488 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\millivoltAuthentic.vbs.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1488 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\954ea5f70258b502.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |