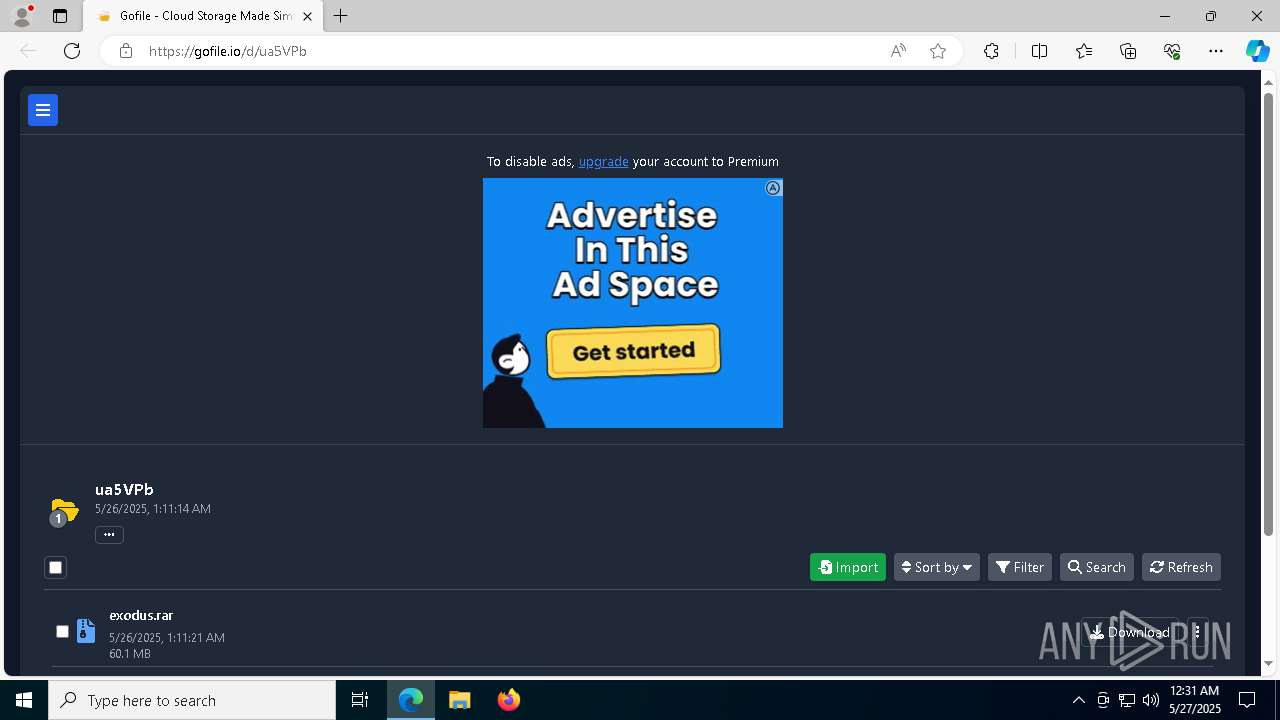
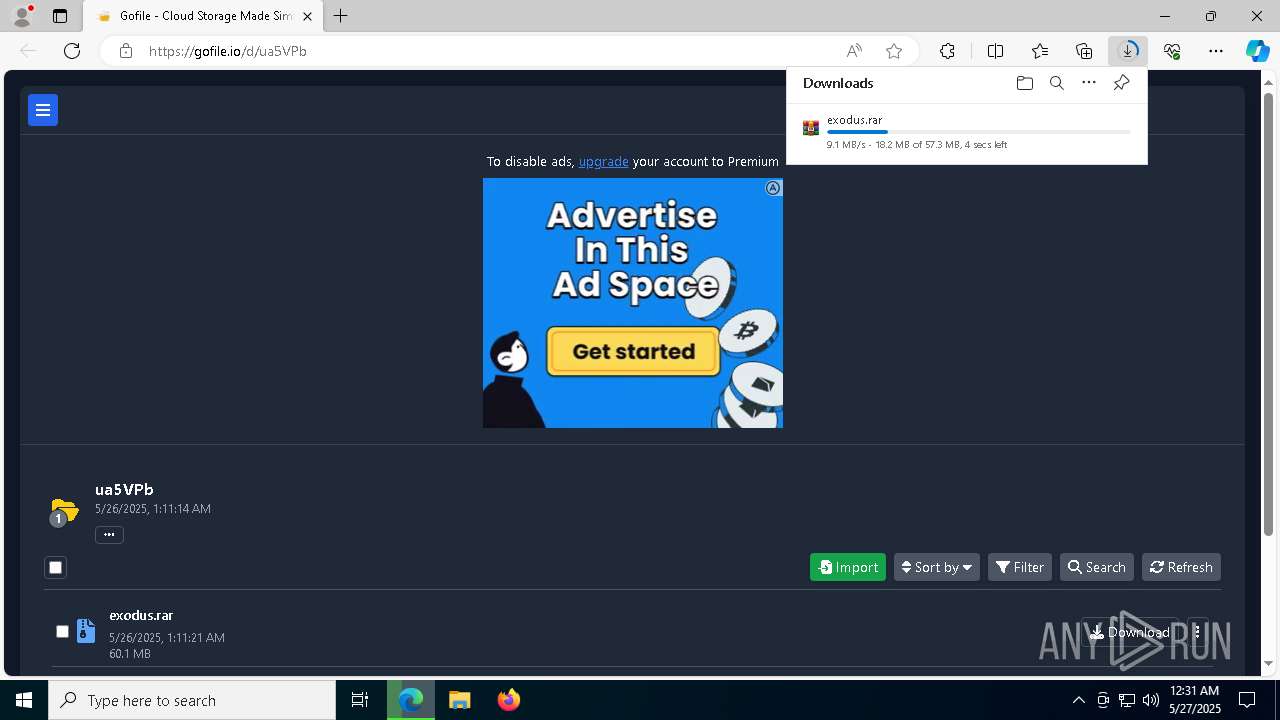
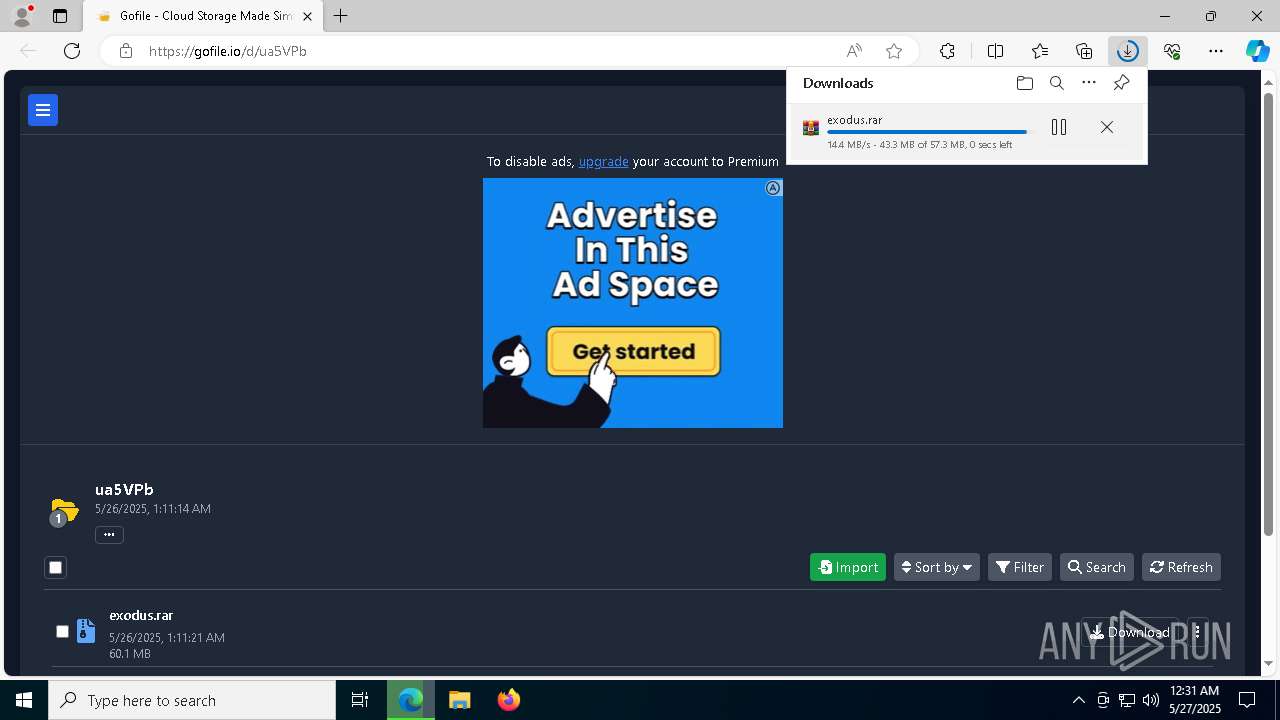
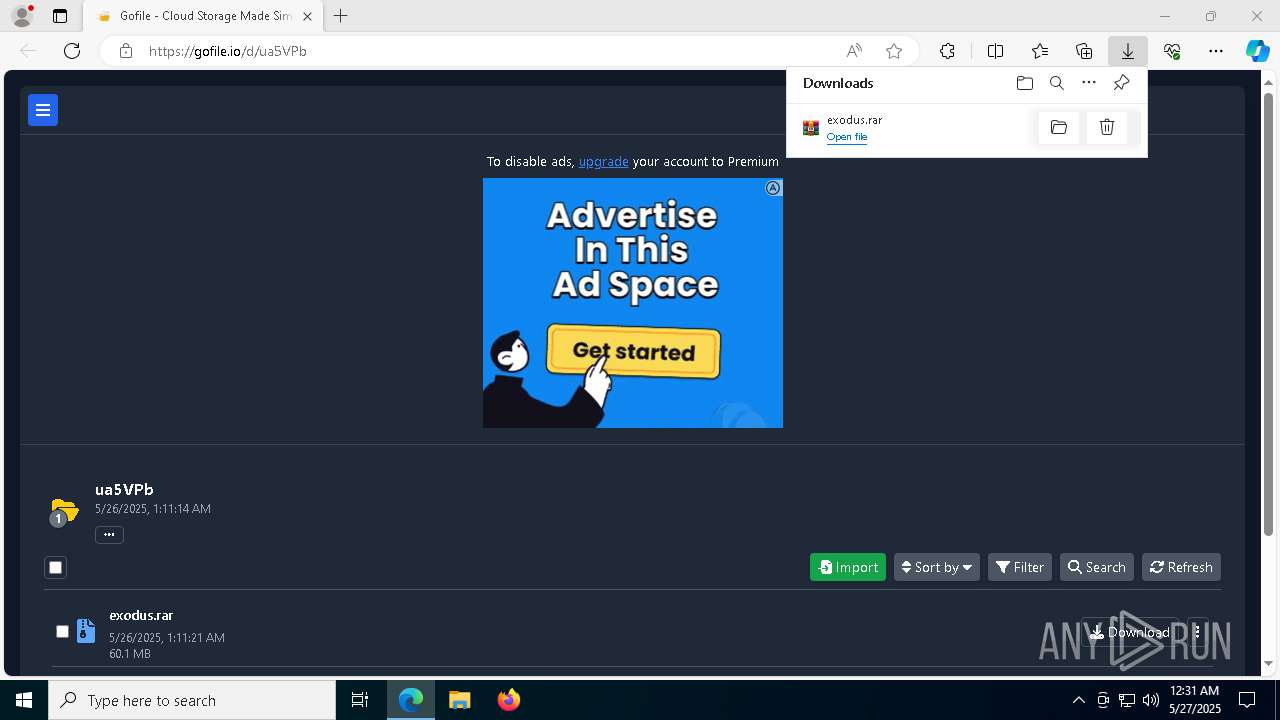
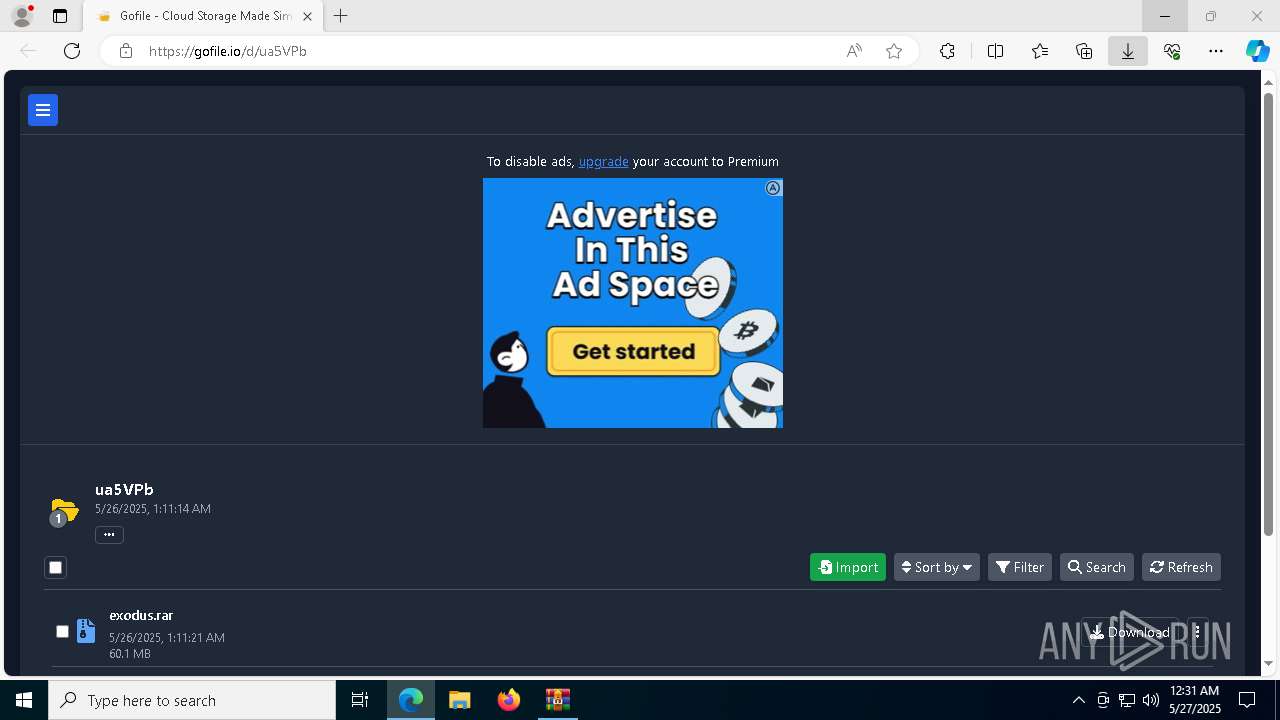
| URL: | https://gofile.io/d/ua5VPb |
| Full analysis: | https://app.any.run/tasks/d77c145b-9cde-48cb-a070-f634f7bc31b2 |
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
| Analysis date: | May 27, 2025, 00:31:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 47B4A94DC53A73C1207604000BB5B7DA |
| SHA1: | 24CD4C8317430AD58CDBC45FD8711E5BB9794B39 |
| SHA256: | 5118E7ECB64B542352952957487B8B65ED9552E960679C596E6A647499E2EE41 |
| SSDEEP: | 3:N8rxL1UN:2Zs |
MALICIOUS
Changes the autorun value in the registry
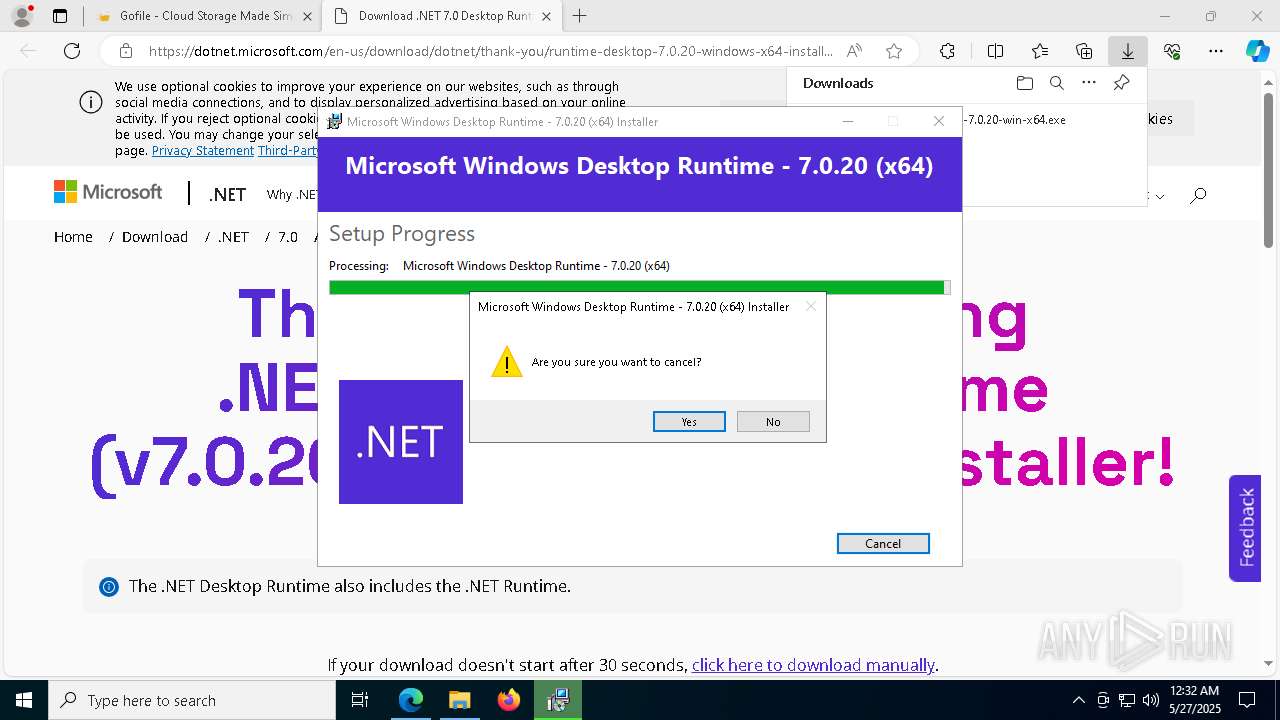
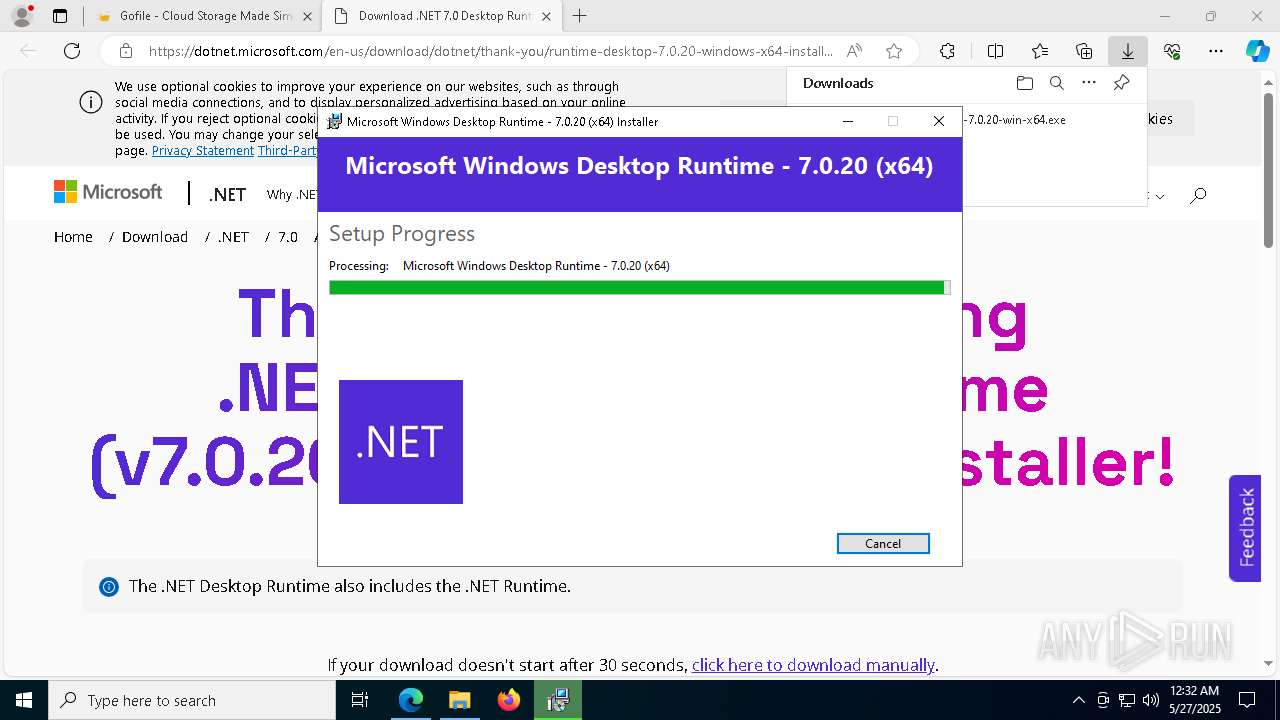
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
Executing a file with an untrusted certificate
- Built.exe (PID: 8512)
- Built.exe (PID: 9180)
- Built.exe (PID: 4228)
- Built.exe (PID: 8416)
Adds path to the Windows Defender exclusion list
- Built.exe (PID: 8416)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 6576)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 4428)
Changes Windows Defender settings
- cmd.exe (PID: 4428)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 6576)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 8656)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 8656)
Changes Controlled Folder Access settings
- powershell.exe (PID: 8656)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 8656)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 8656)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 8656)
Changes settings for real-time protection
- powershell.exe (PID: 8656)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 6960)
Bypass execution policy to execute commands
- powershell.exe (PID: 7812)
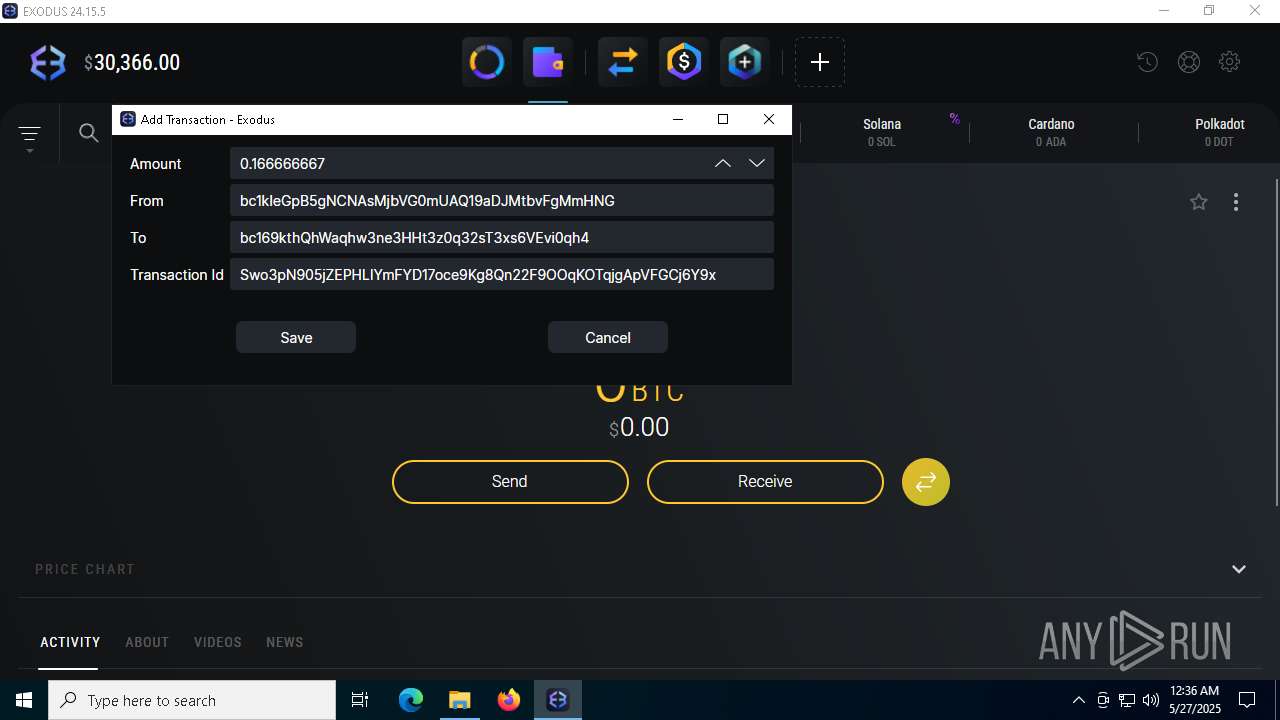
BLANKGRABBER has been detected (SURICATA)
- Built.exe (PID: 8416)
XRED has been detected (YARA)
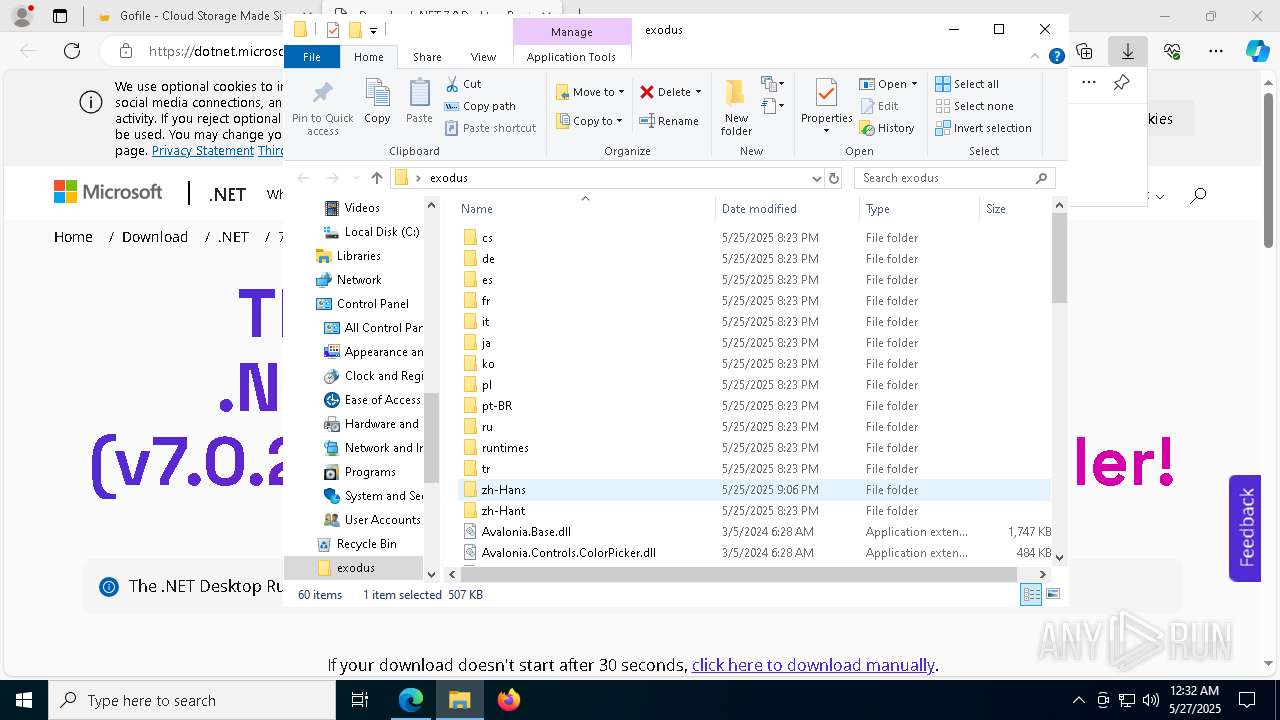
- Synaptics.exe (PID: 716)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 8196)
SUSPICIOUS
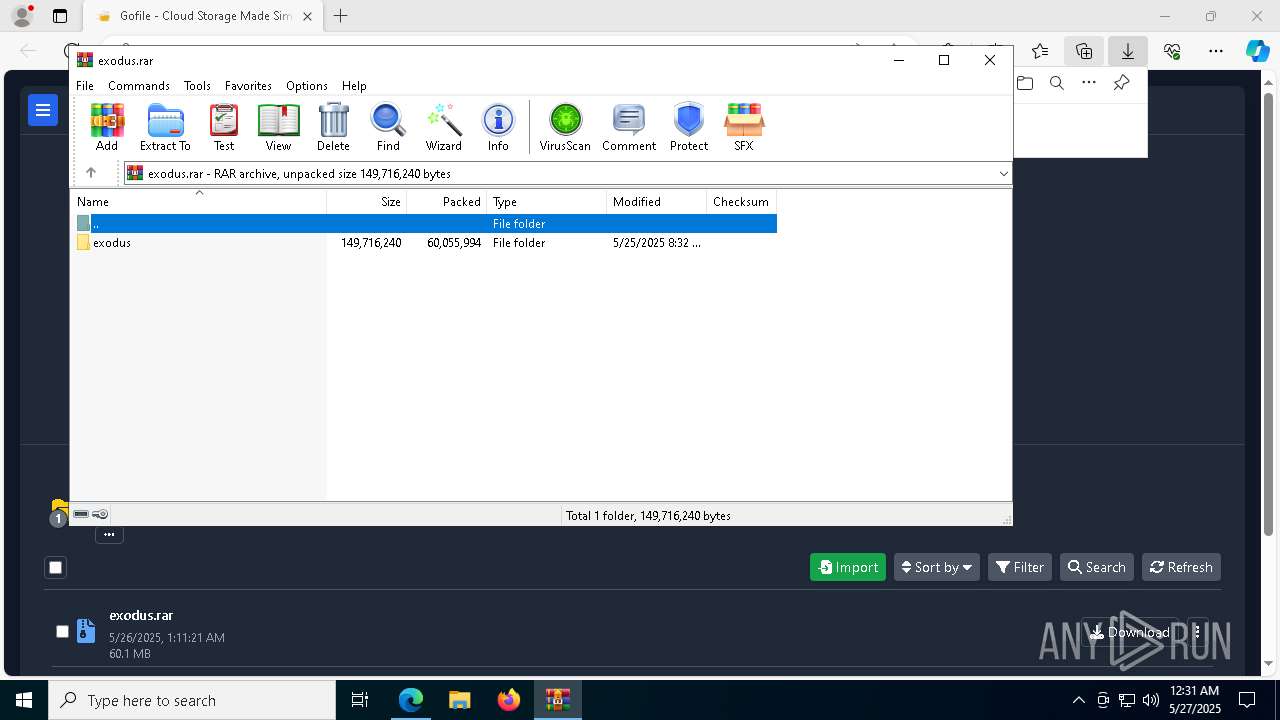
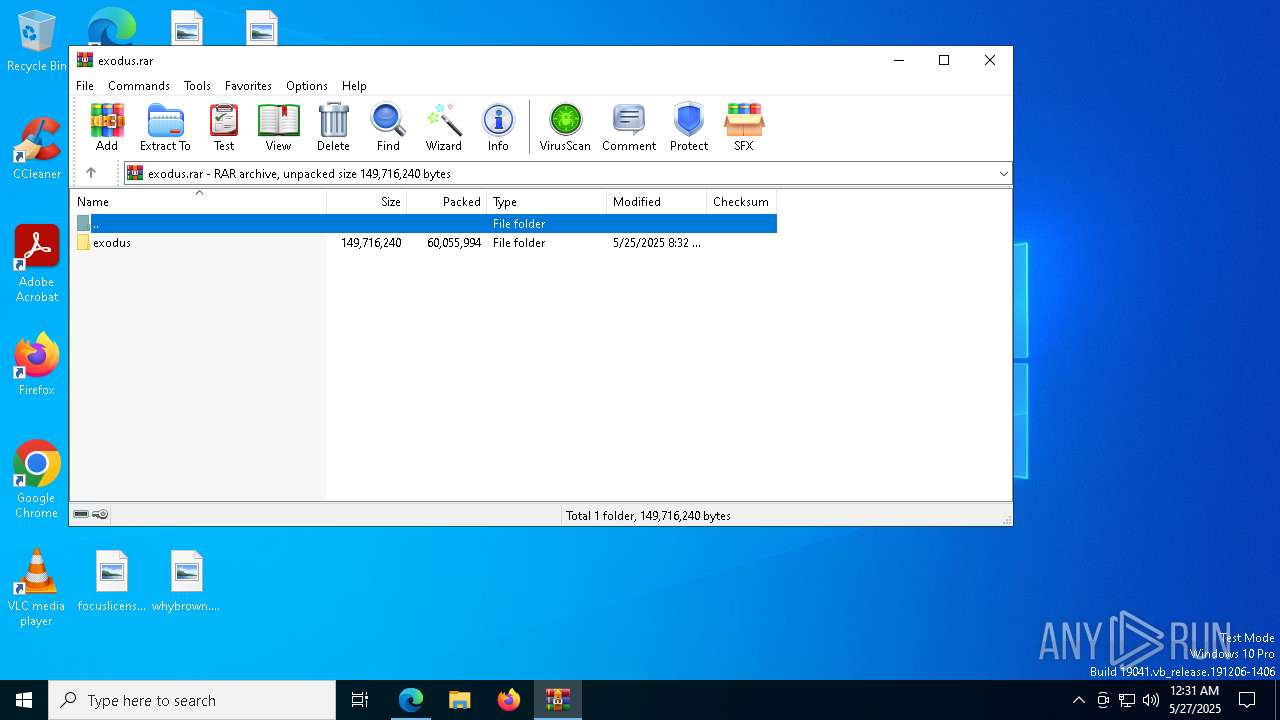
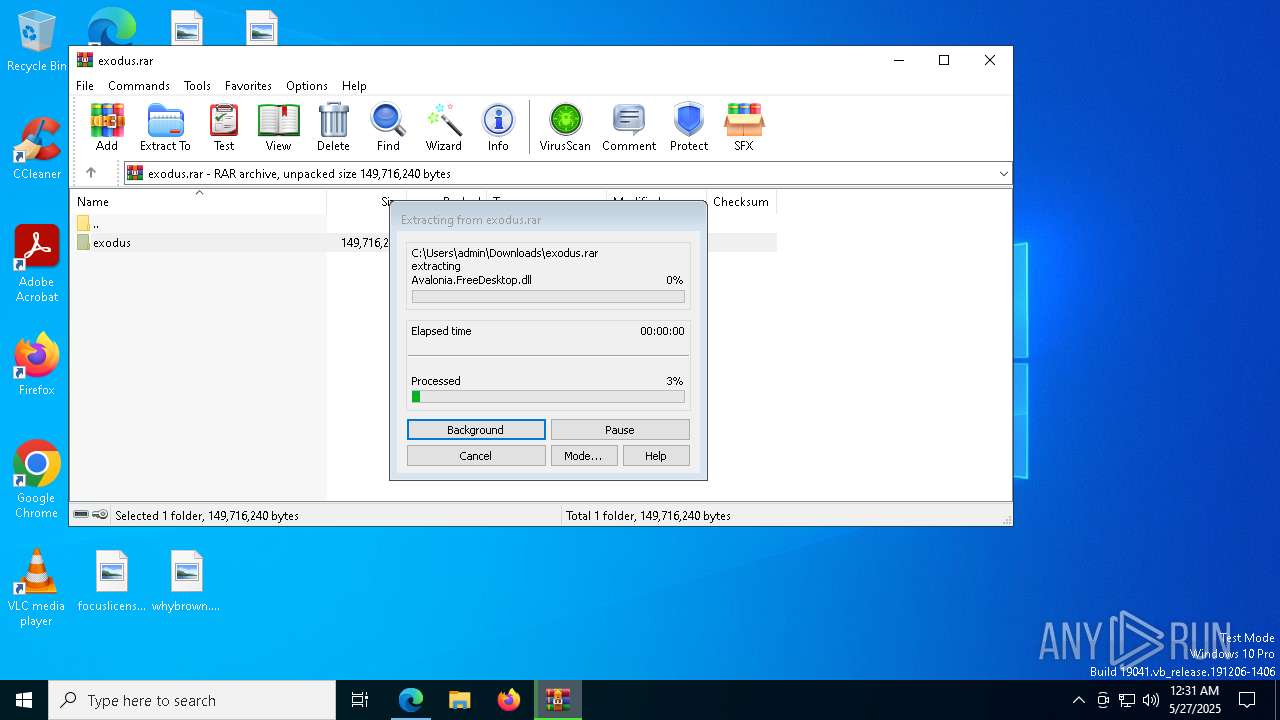
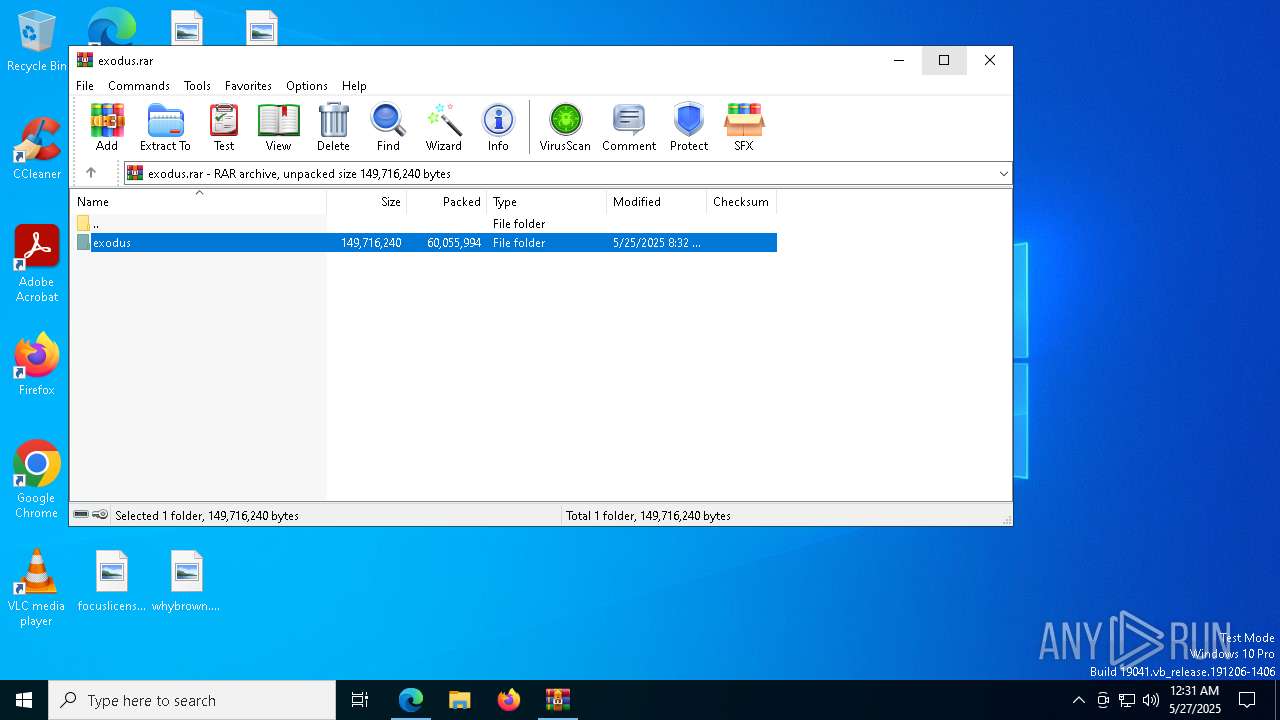
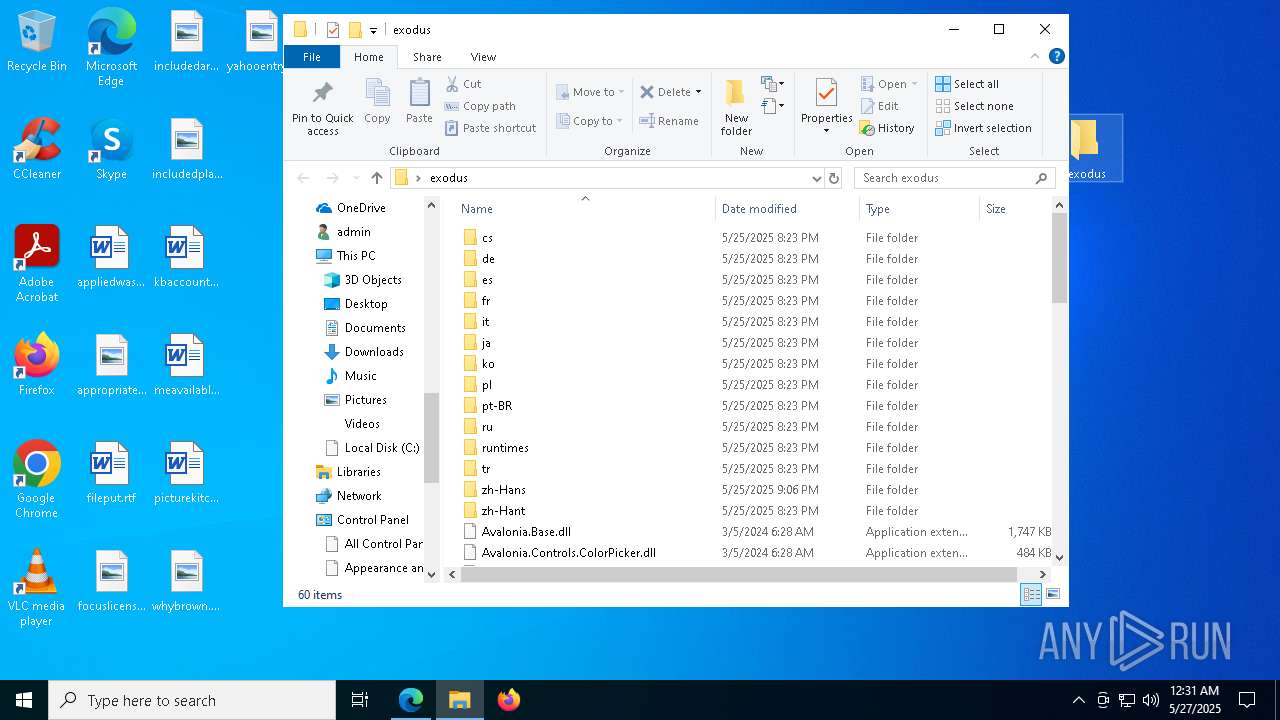
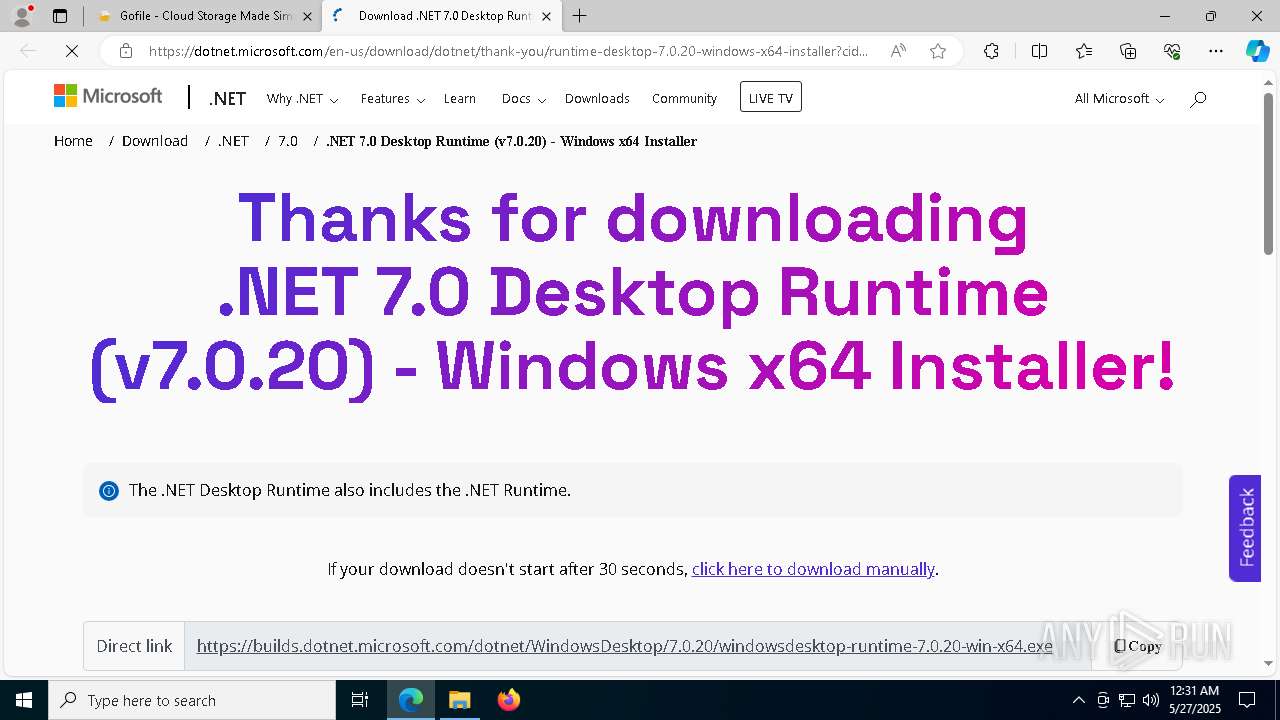
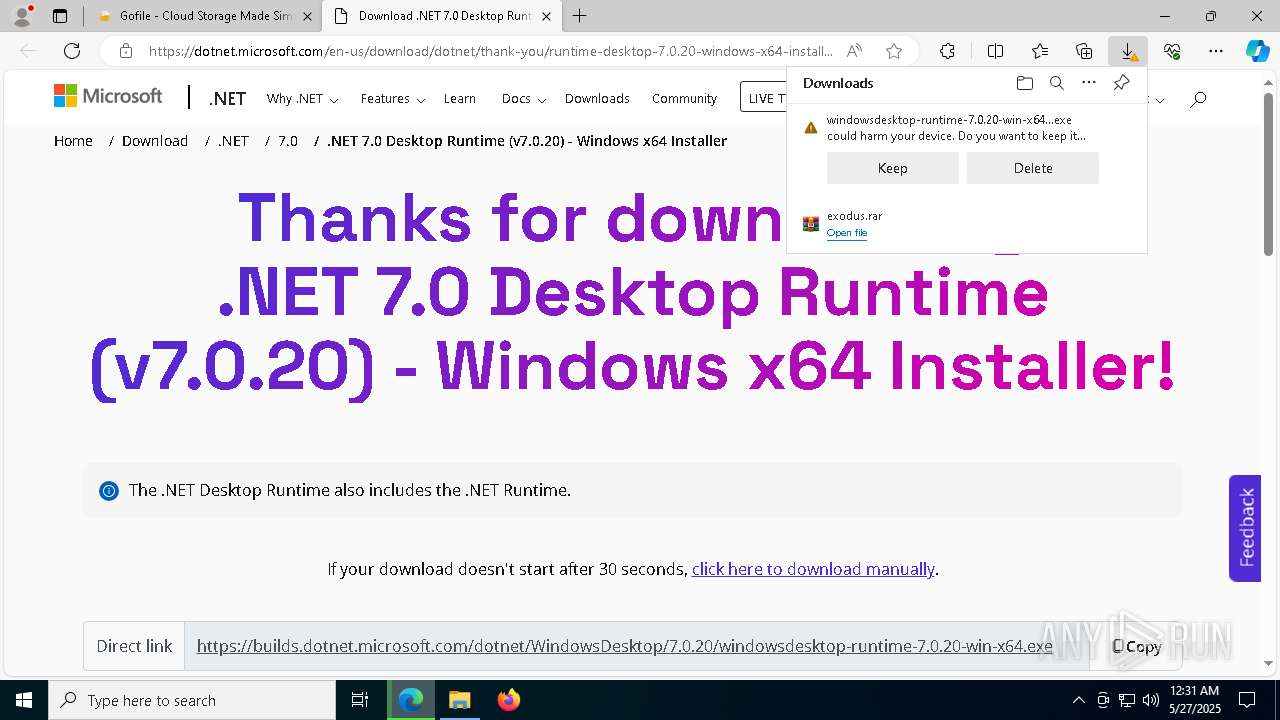
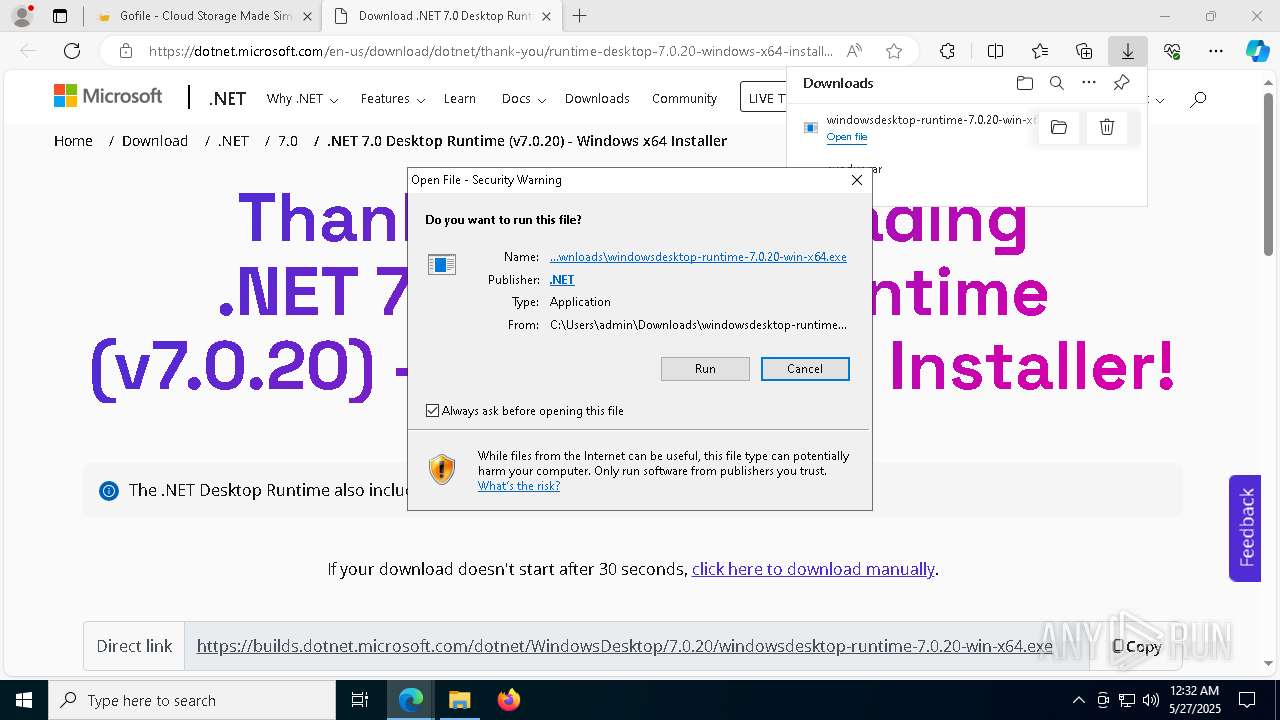
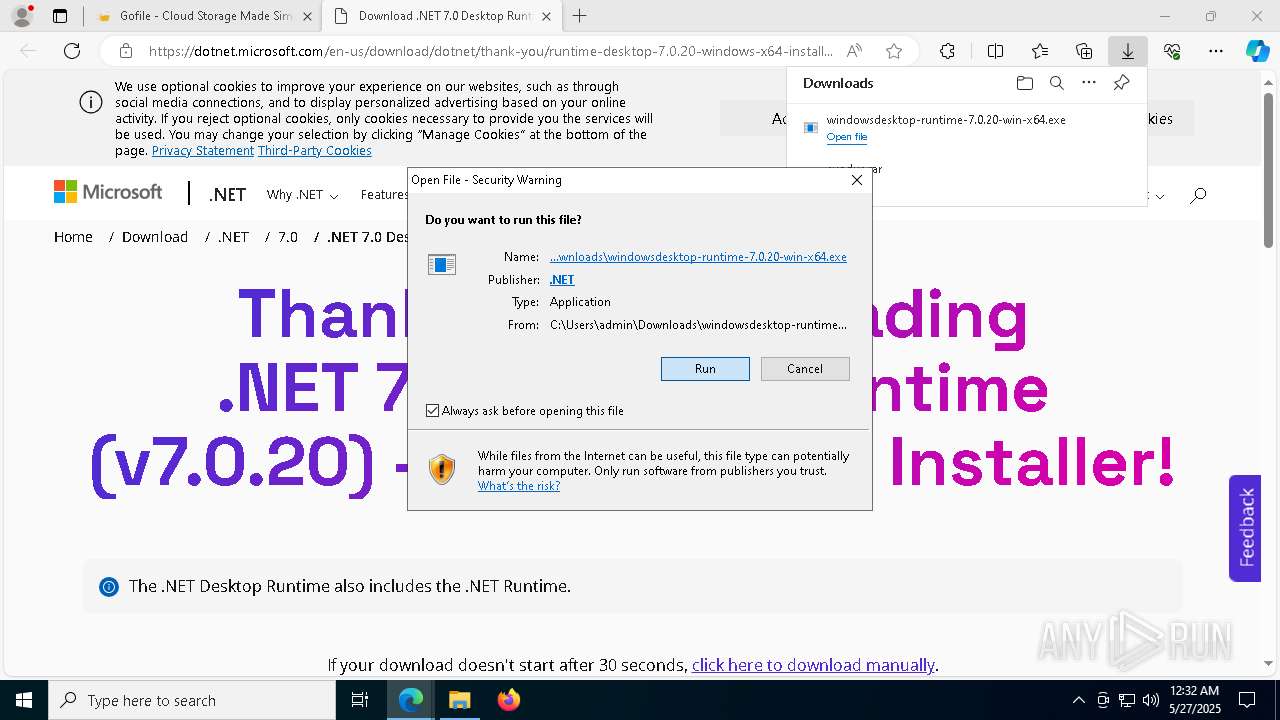
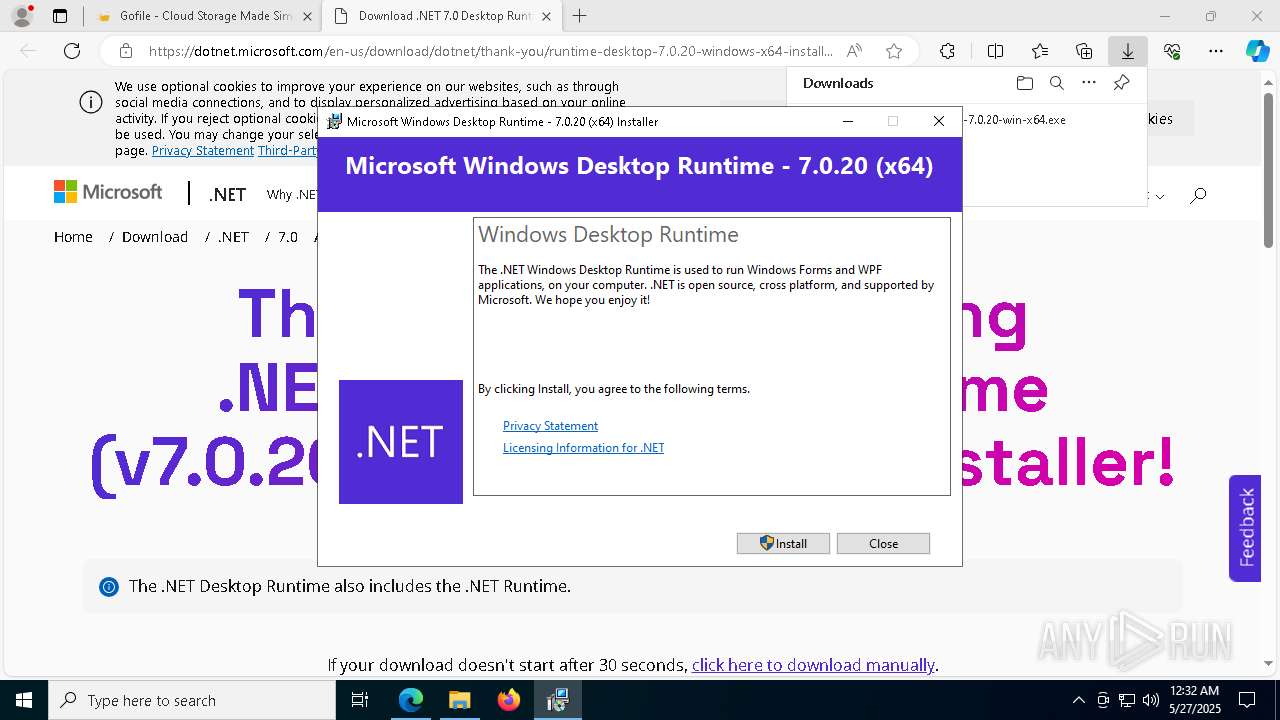
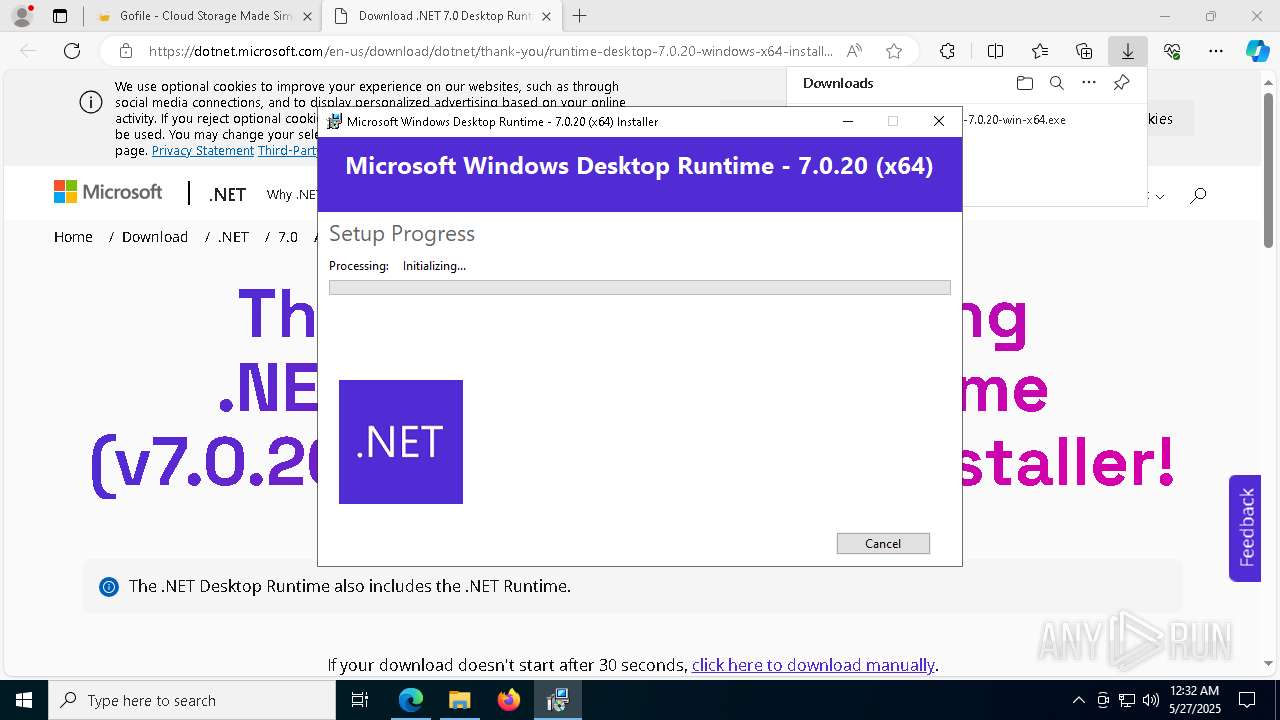
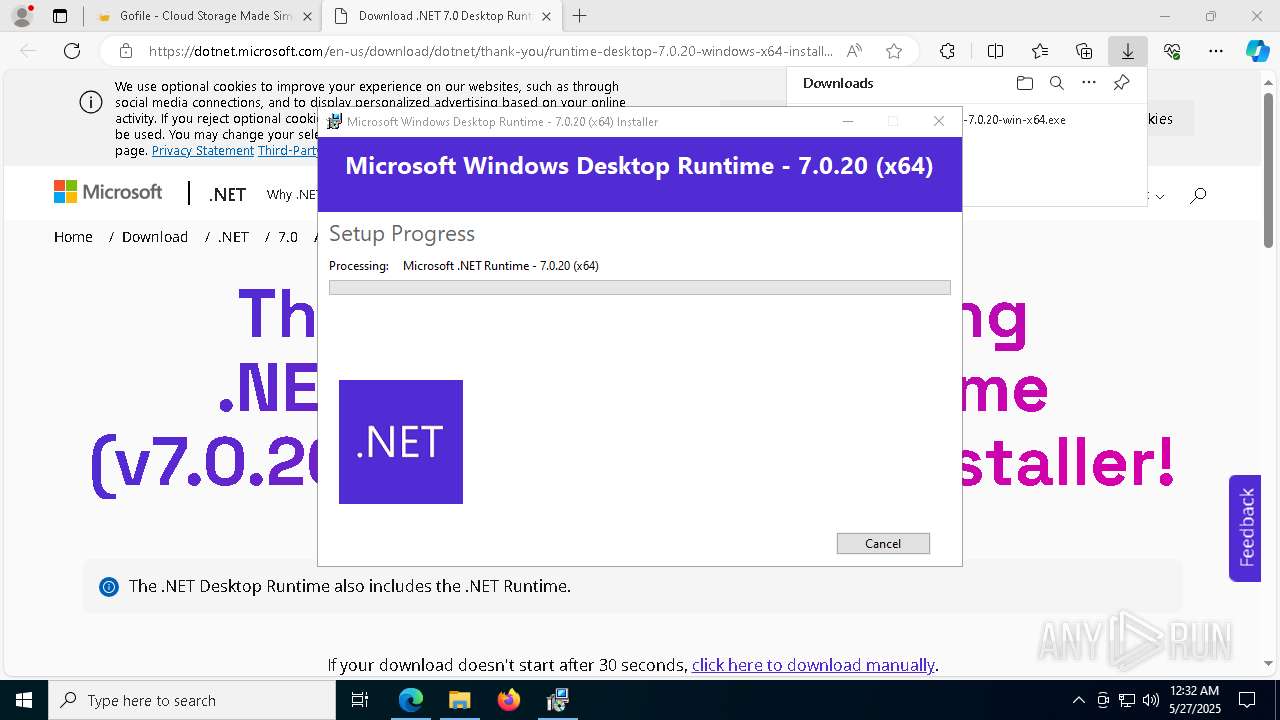
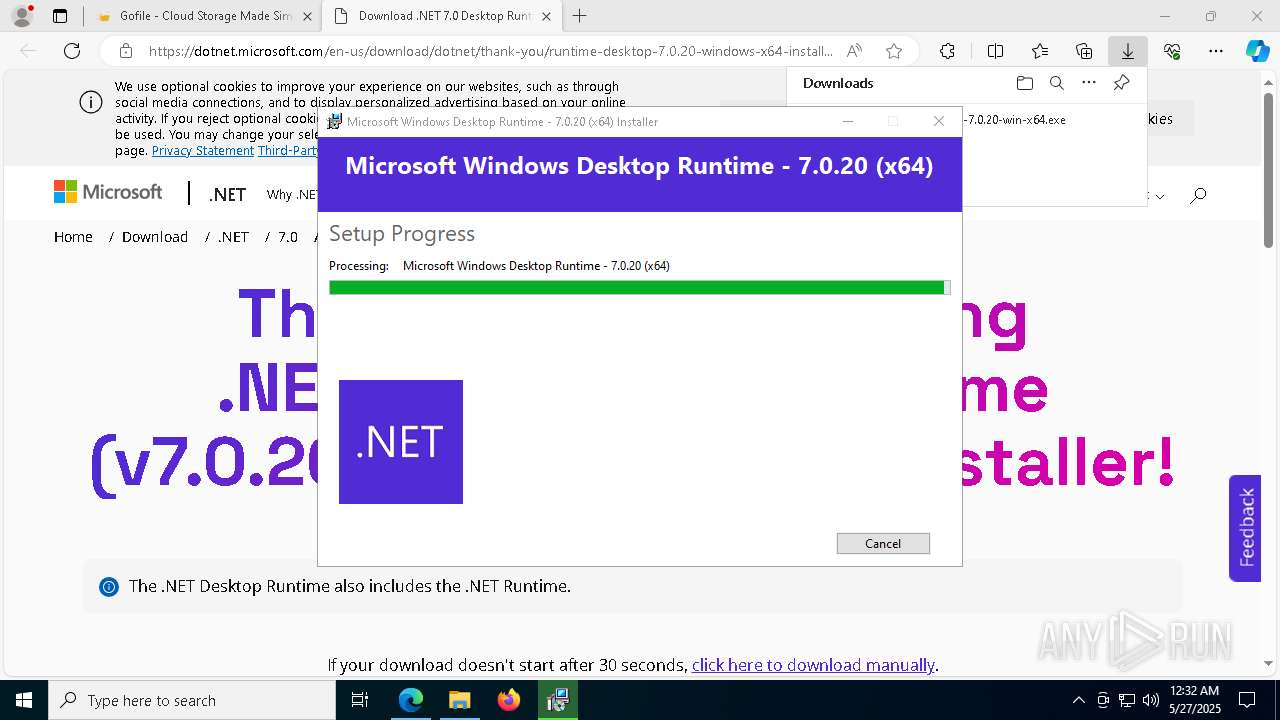
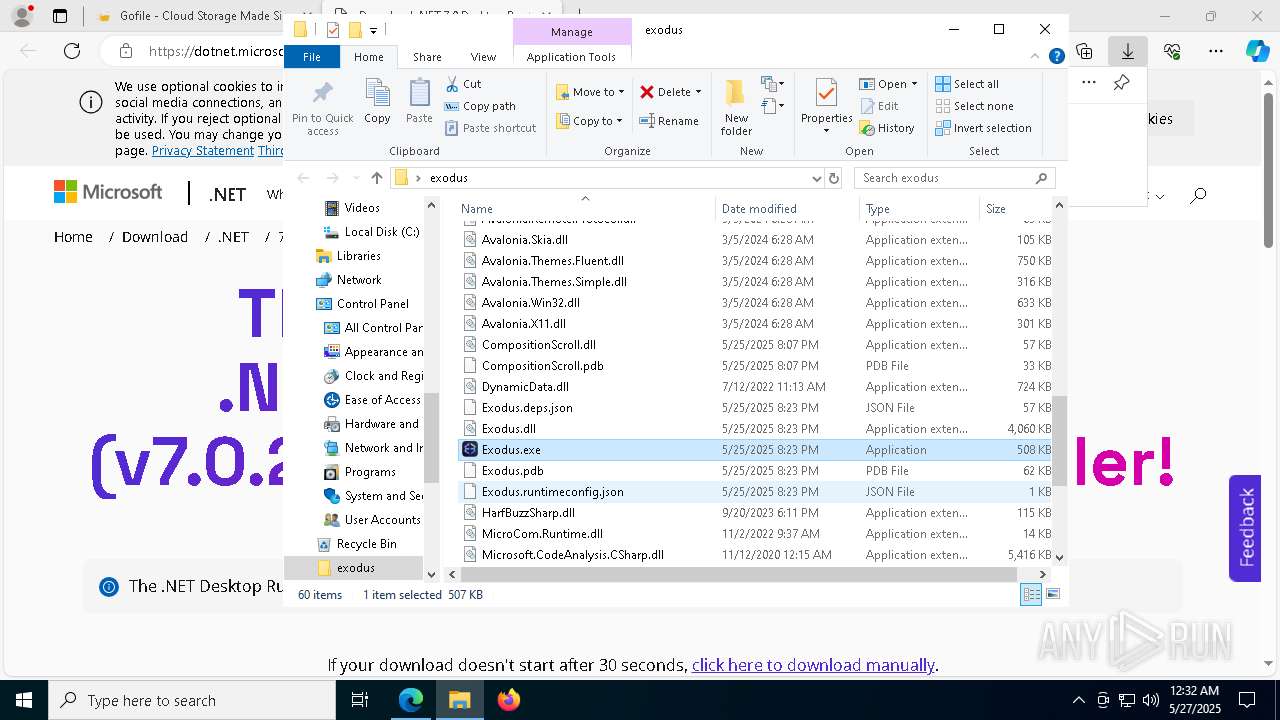
Process drops legitimate windows executable
- WinRAR.exe (PID: 8580)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 4336)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
- msiexec.exe (PID: 5720)
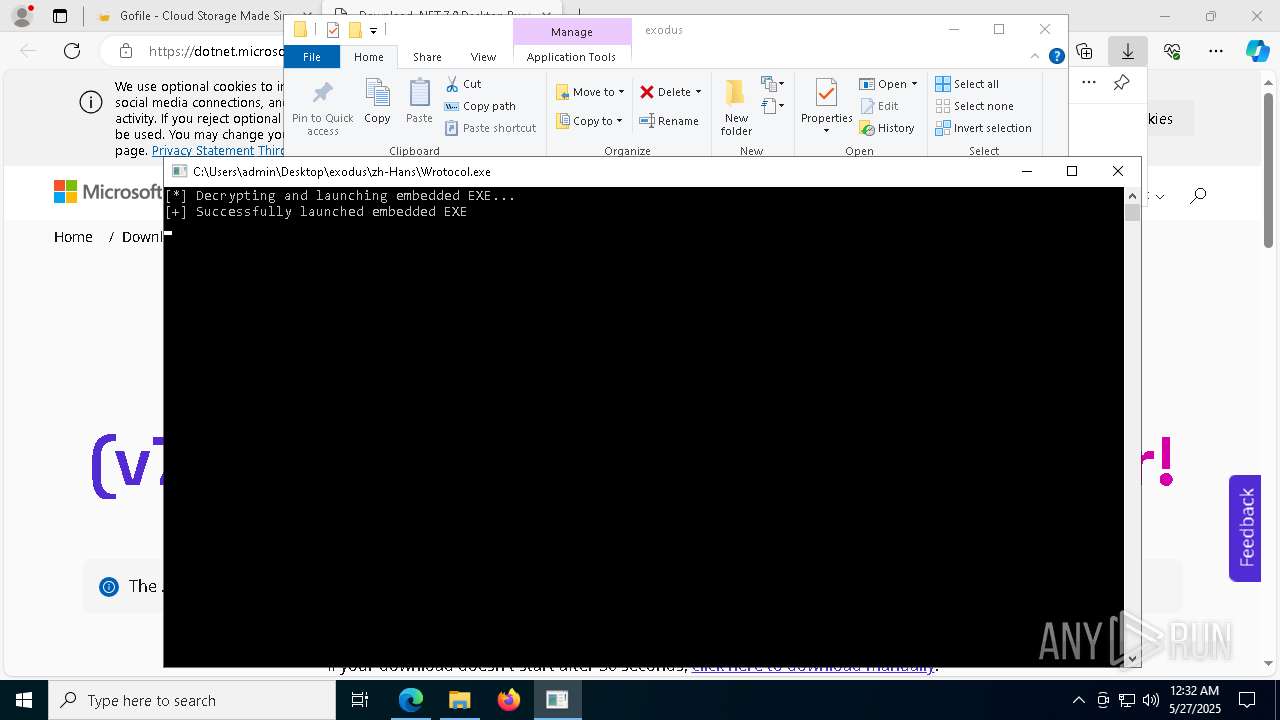
- Wrotocol.exe (PID: 3996)
- ._cache_tool.exe (PID: 8996)
- Built.exe (PID: 4228)
- Built.exe (PID: 8512)
- Built.exe (PID: 8416)
Reads security settings of Internet Explorer
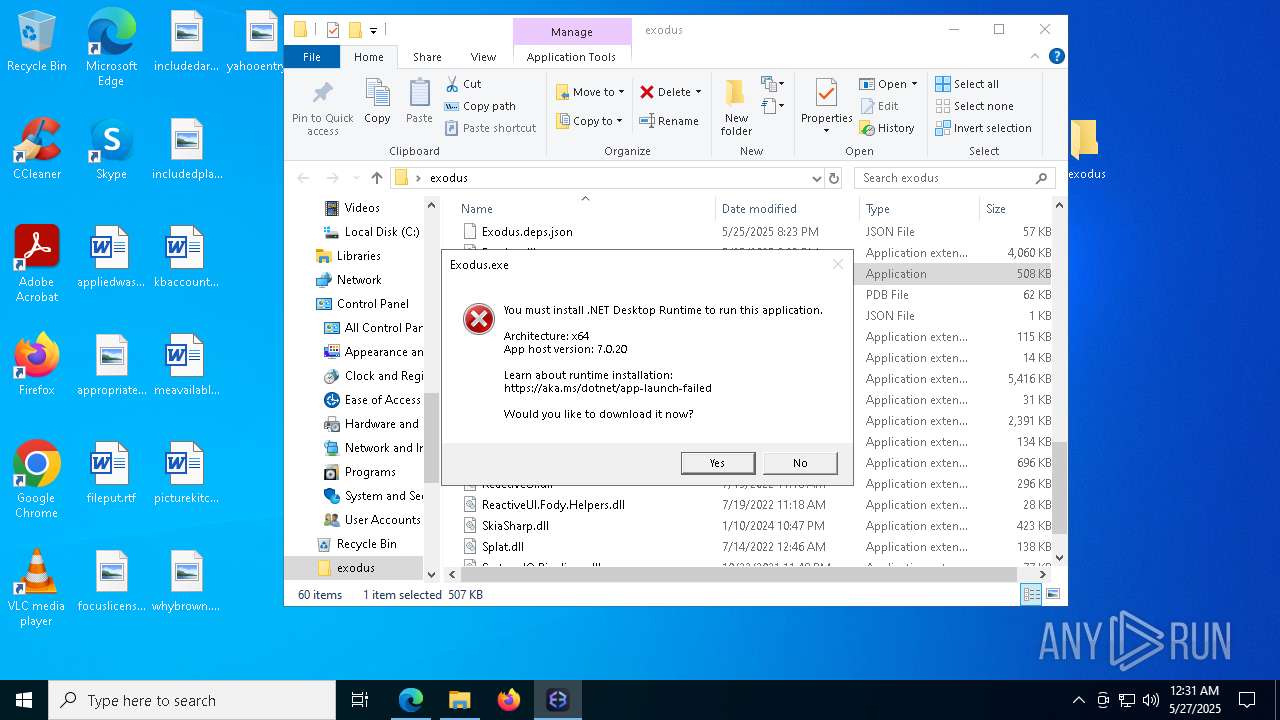
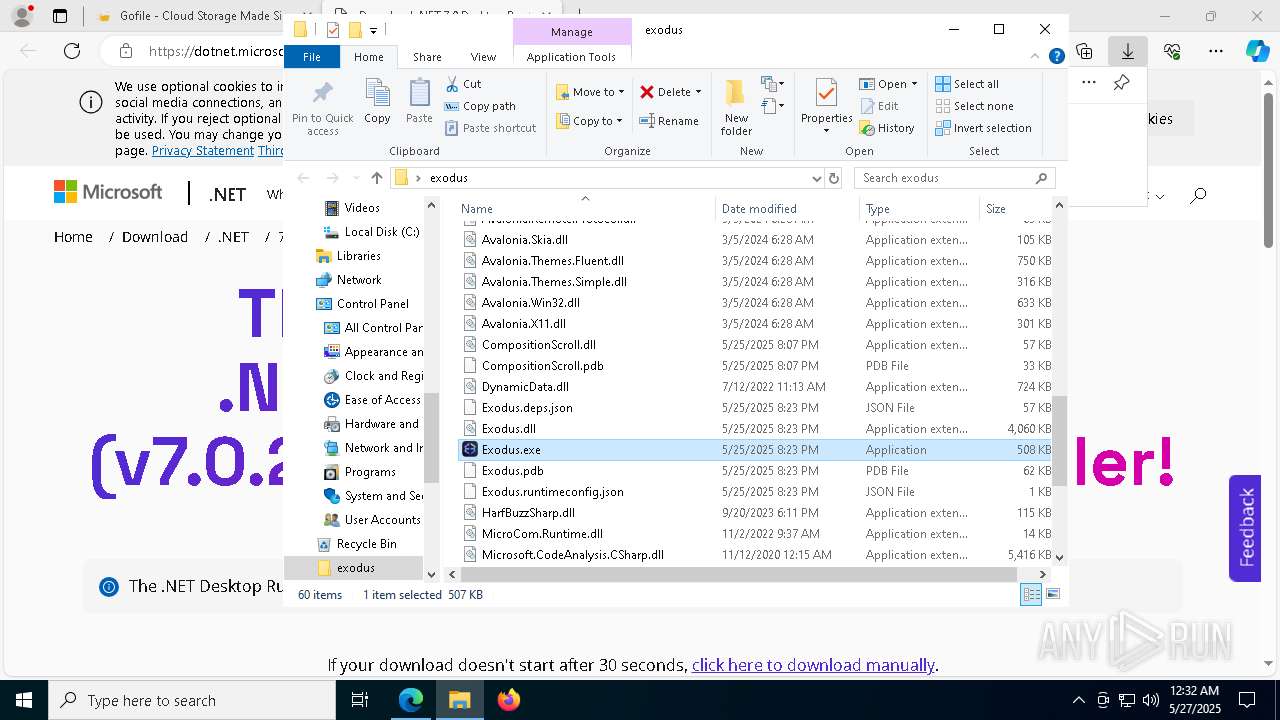
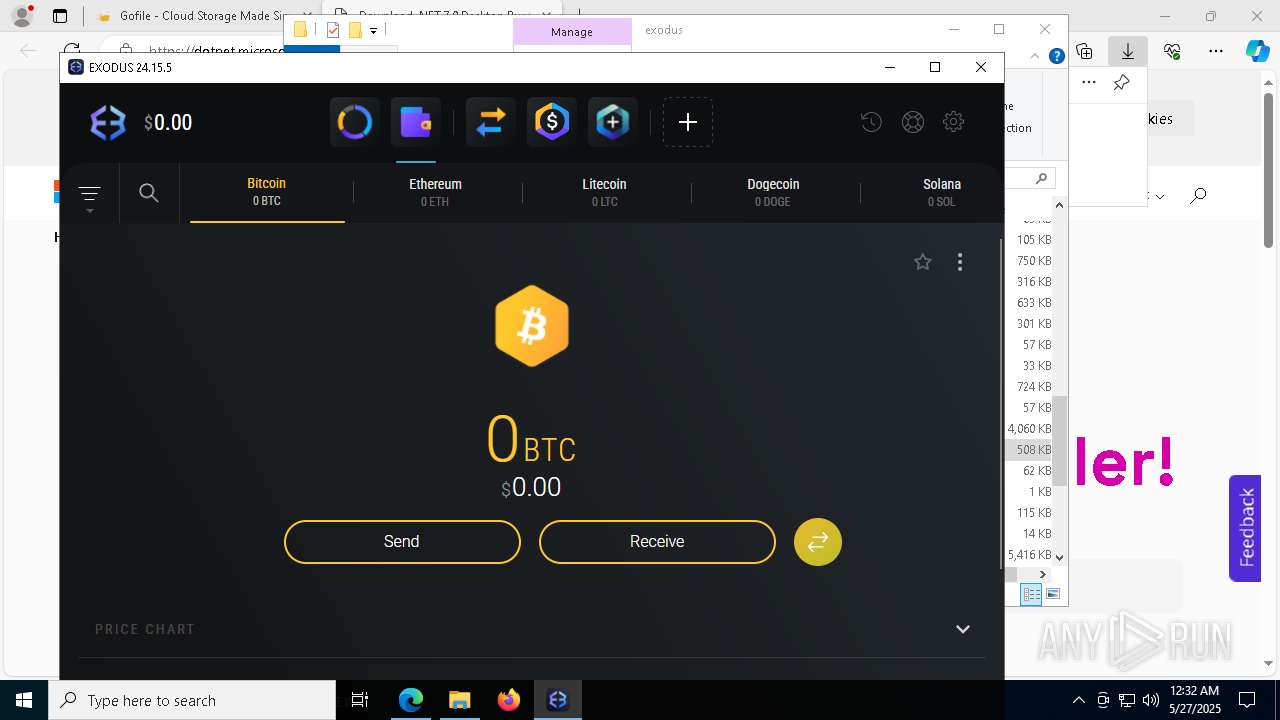
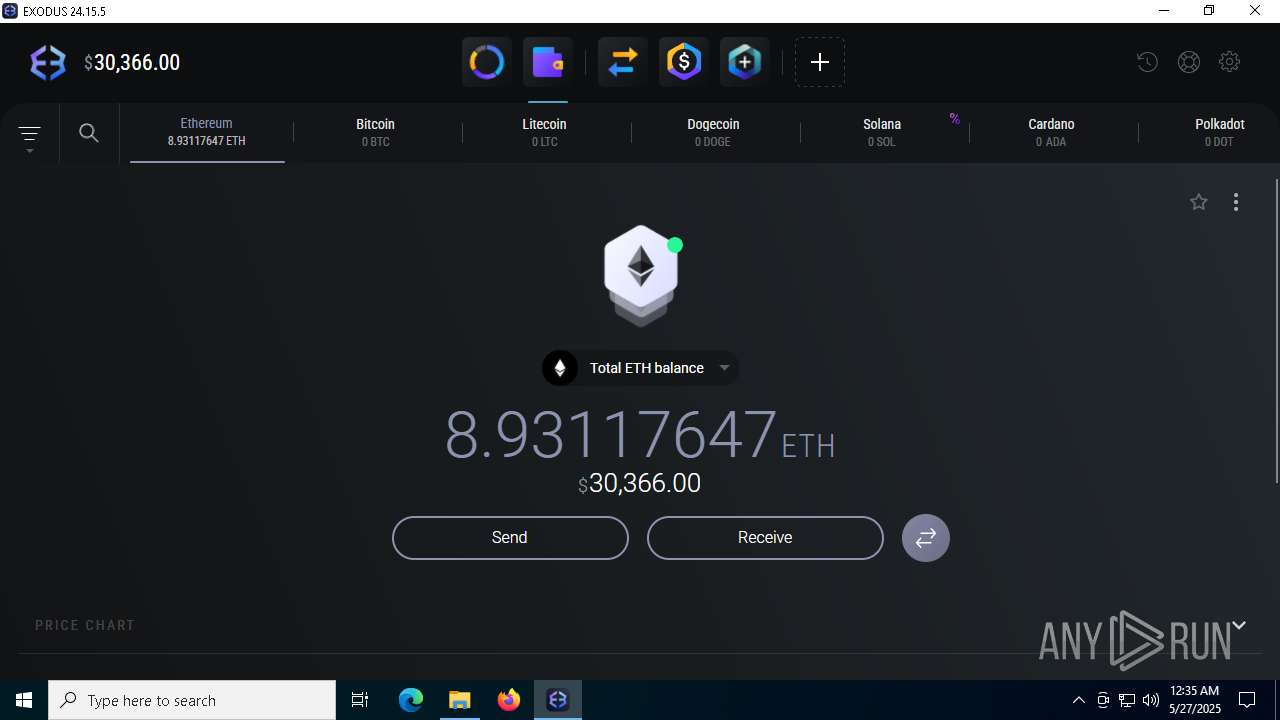
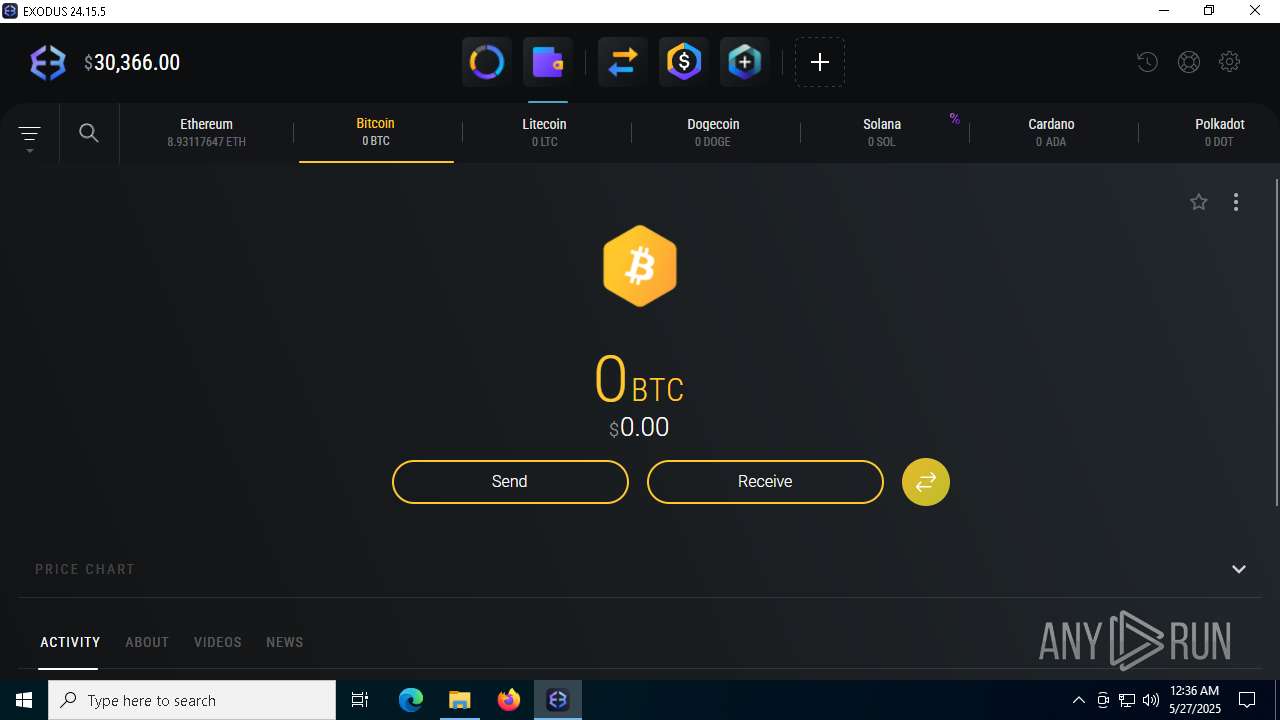
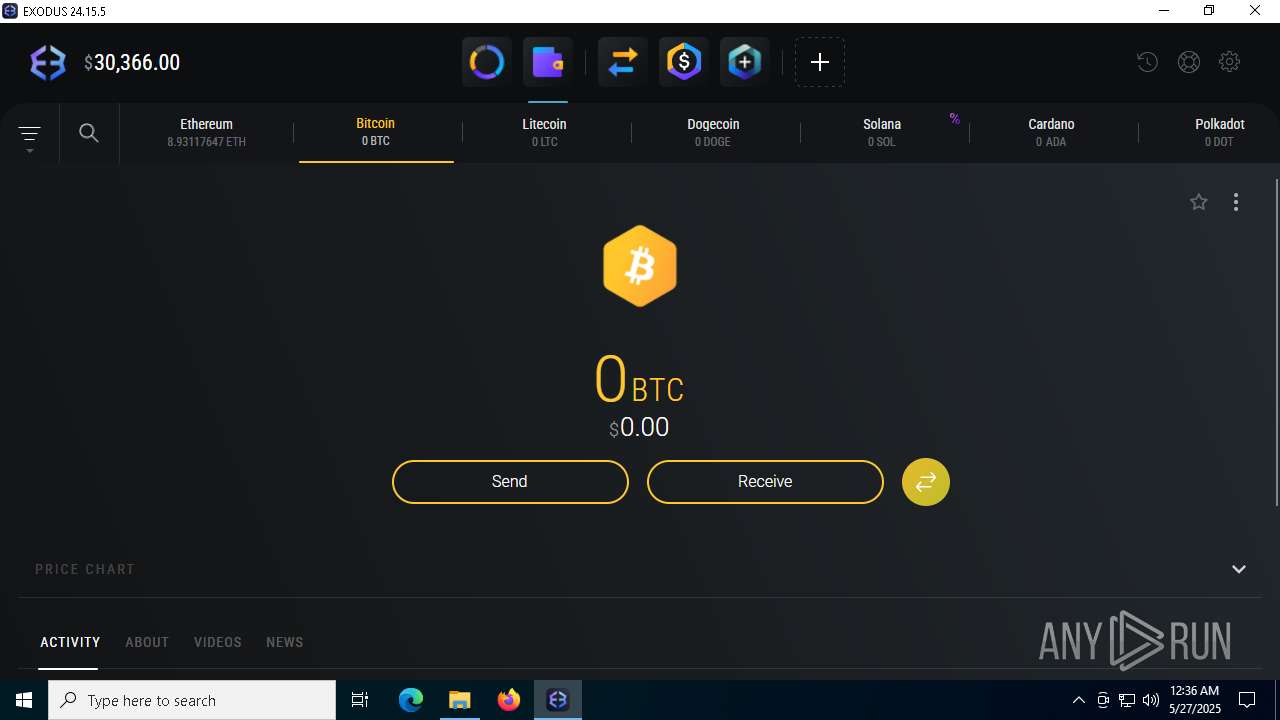
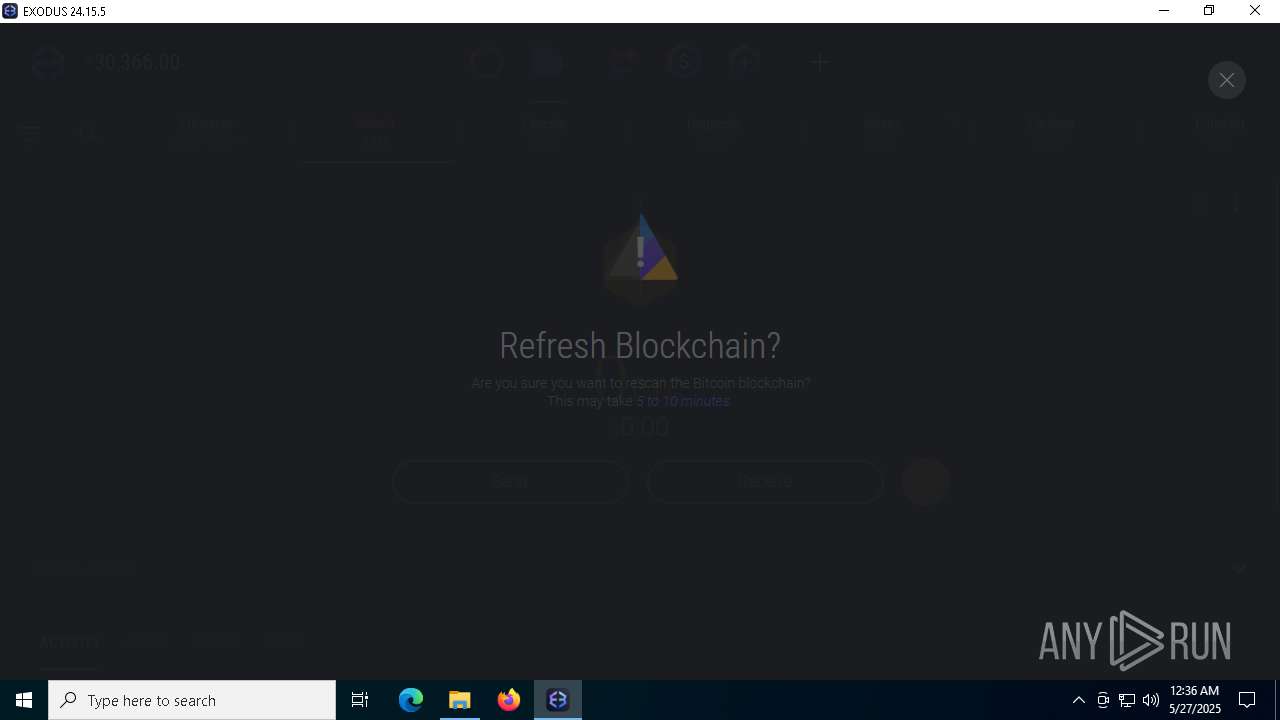
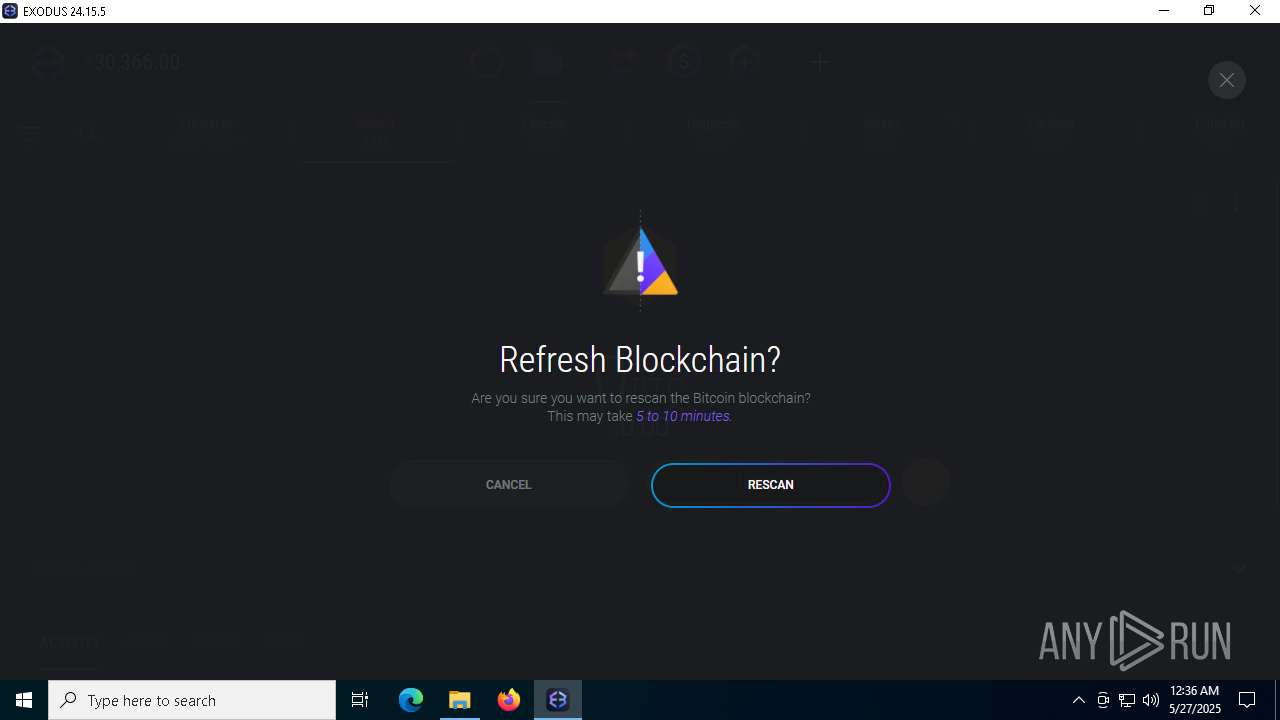
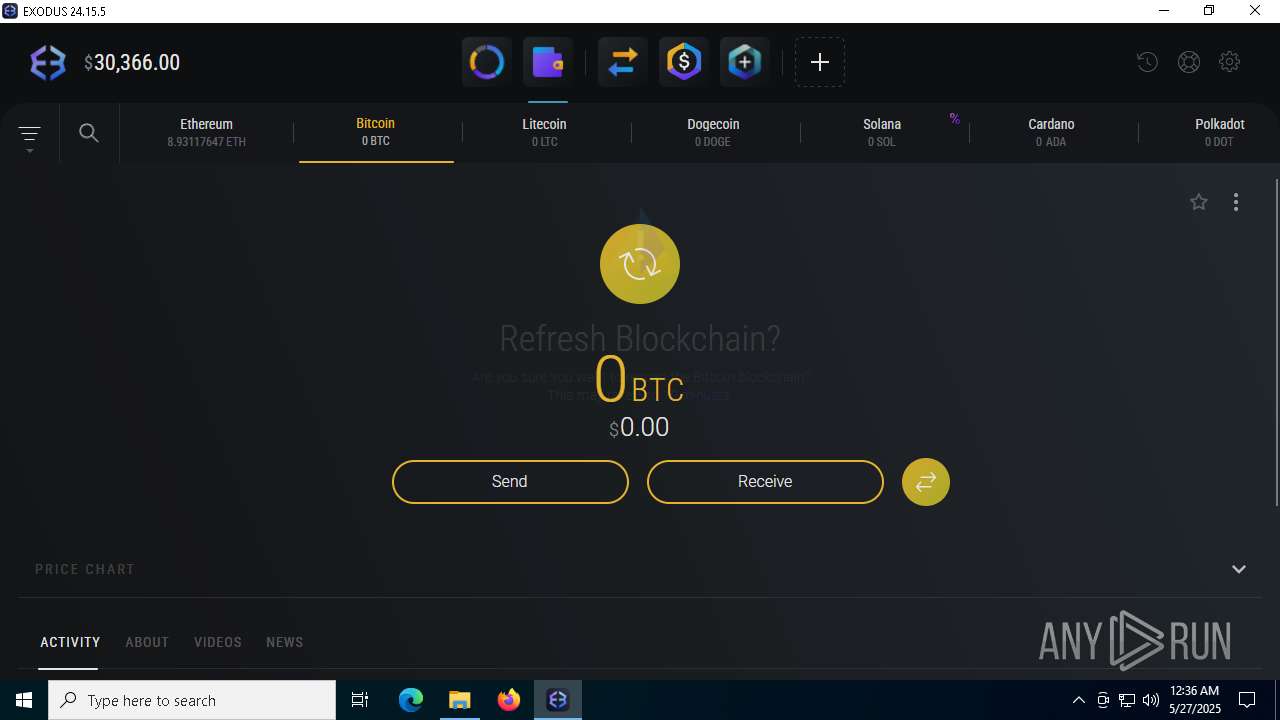
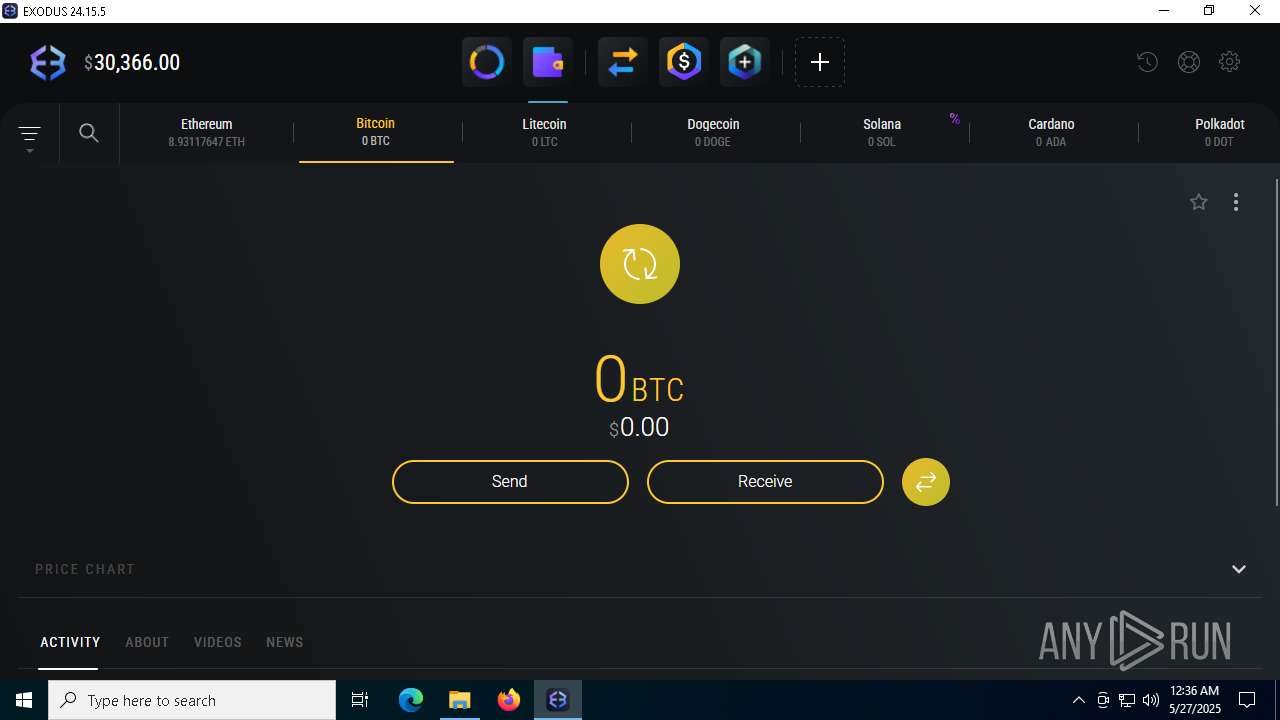
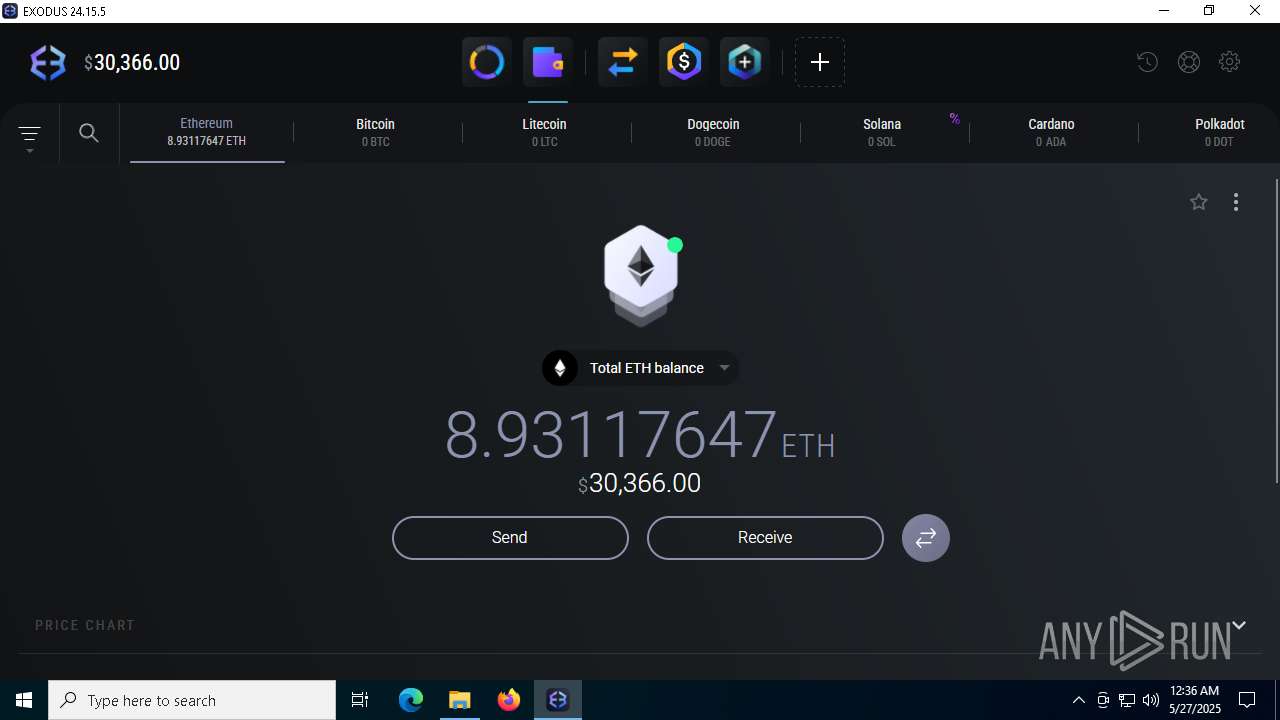
- Exodus.exe (PID: 8824)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
Executable content was dropped or overwritten
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 4336)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
- tool.exe (PID: 6496)
- Wrotocol.exe (PID: 3996)
- Wrotocol.exe (PID: 8048)
- Synaptics.exe (PID: 716)
- ._cache_tool.exe (PID: 8996)
- Built.exe (PID: 8512)
- Built.exe (PID: 4228)
- Built.exe (PID: 8416)
- csc.exe (PID: 976)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
- Built.exe (PID: 8512)
- Built.exe (PID: 9180)
- Built.exe (PID: 4228)
- Built.exe (PID: 8416)
Searches for installed software
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
Starts itself from another location
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5720)
The process drops C-runtime libraries
- msiexec.exe (PID: 5720)
- Wrotocol.exe (PID: 3996)
- Built.exe (PID: 4228)
- Built.exe (PID: 8512)
Creates a software uninstall entry
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
Process drops python dynamic module
- Wrotocol.exe (PID: 3996)
- Built.exe (PID: 8512)
- Built.exe (PID: 4228)
Application launched itself
- Wrotocol.exe (PID: 3996)
- Built.exe (PID: 8512)
- Built.exe (PID: 9180)
- Built.exe (PID: 4228)
Starts CMD.EXE for commands execution
- Built.exe (PID: 8416)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4244)
- cmd.exe (PID: 4428)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5864)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 3896)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 4244)
- cmd.exe (PID: 6576)
Found strings related to reading or modifying Windows Defender settings
- Built.exe (PID: 8416)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 4428)
Script disables Windows Defender's IPS
- cmd.exe (PID: 4428)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 516)
- cmd.exe (PID: 7392)
Starts application with an unusual extension
- cmd.exe (PID: 8168)
- cmd.exe (PID: 7912)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 1696)
- cmd.exe (PID: 8208)
- cmd.exe (PID: 8228)
Get information on the list of running processes
- cmd.exe (PID: 2908)
- cmd.exe (PID: 8584)
- Built.exe (PID: 8416)
- cmd.exe (PID: 2040)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 6816)
CSC.EXE is used to compile C# code
- csc.exe (PID: 976)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 6960)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6960)
Base64-obfuscated command line is found
- cmd.exe (PID: 6960)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8140)
- cmd.exe (PID: 8496)
- cmd.exe (PID: 632)
- cmd.exe (PID: 9004)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 5864)
- cmd.exe (PID: 4448)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 6564)
- cmd.exe (PID: 2772)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 6828)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 5728)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6708)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 4724)
Checks for external IP
- Built.exe (PID: 8416)
- svchost.exe (PID: 2196)
There is functionality for taking screenshot (YARA)
- Synaptics.exe (PID: 716)
- Exodus.exe (PID: 6032)
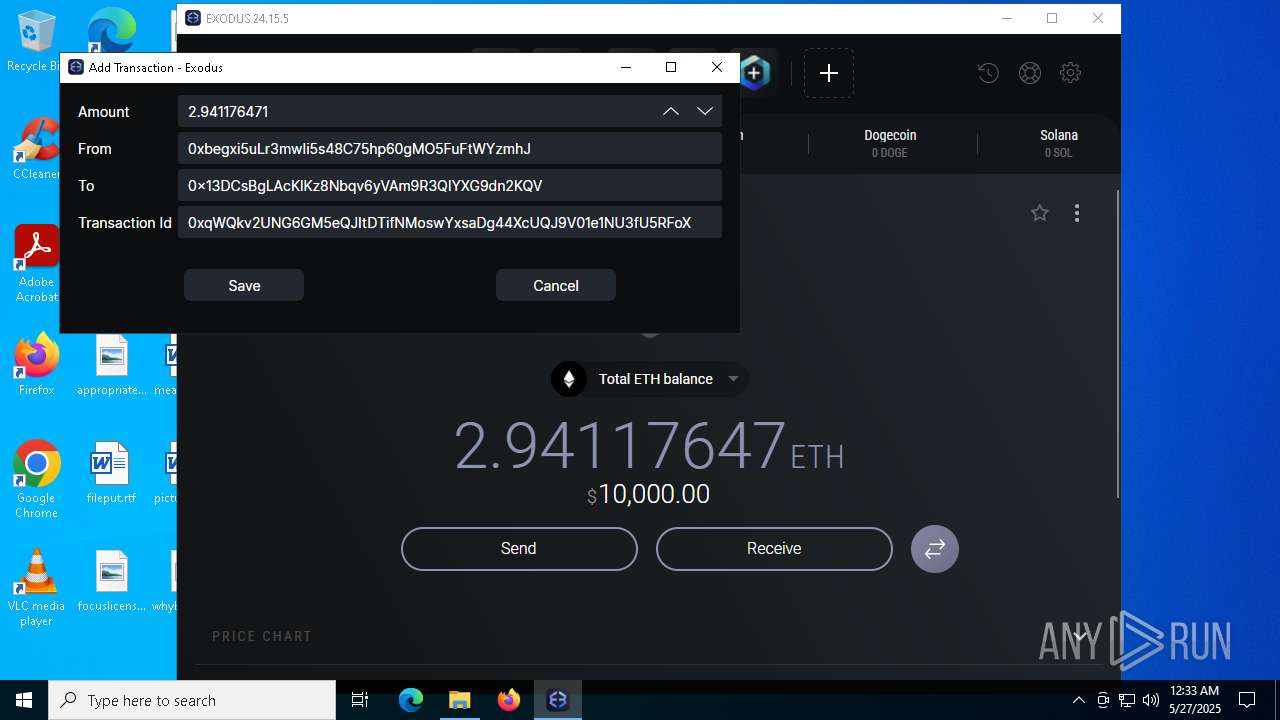
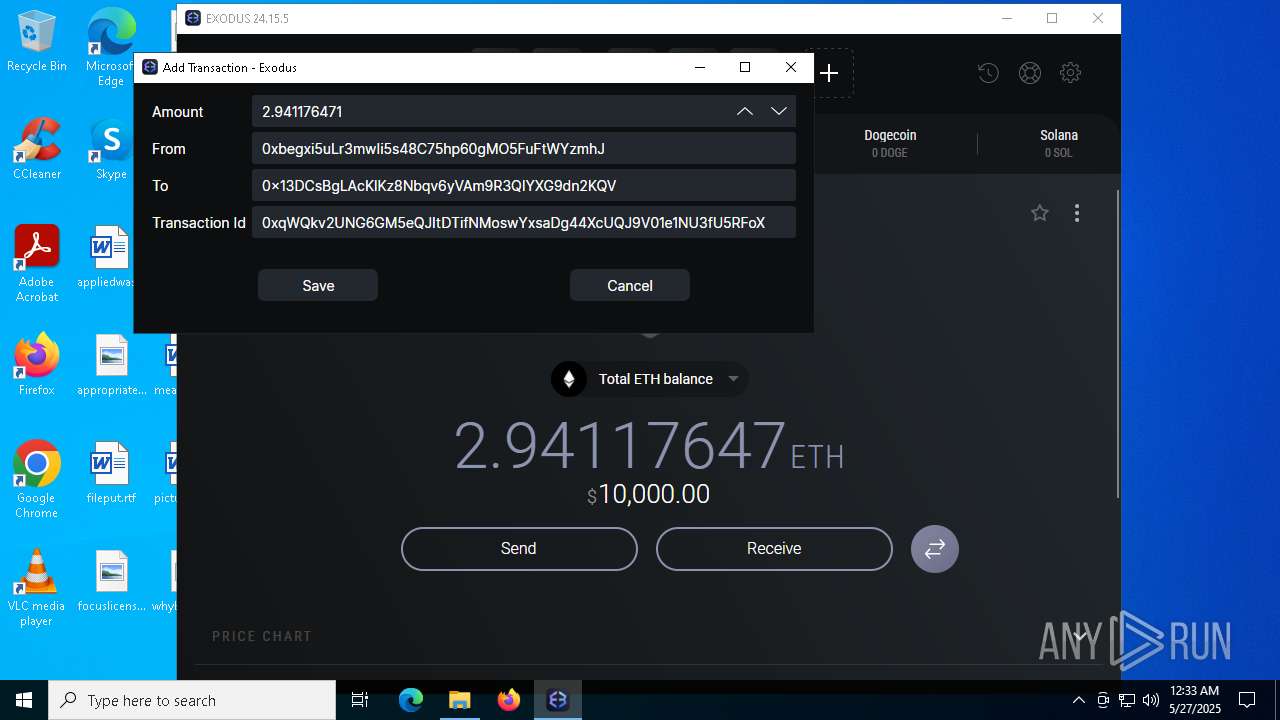
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Built.exe (PID: 8416)
There is functionality for communication over UDP network (YARA)
- Synaptics.exe (PID: 716)
There is functionality for communication dyndns network (YARA)
- Synaptics.exe (PID: 716)
INFO
Checks supported languages
- identity_helper.exe (PID: 2420)
- Exodus.exe (PID: 8824)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 4336)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
- msiexec.exe (PID: 5720)
- msiexec.exe (PID: 5984)
Application launched itself
- msedge.exe (PID: 5776)
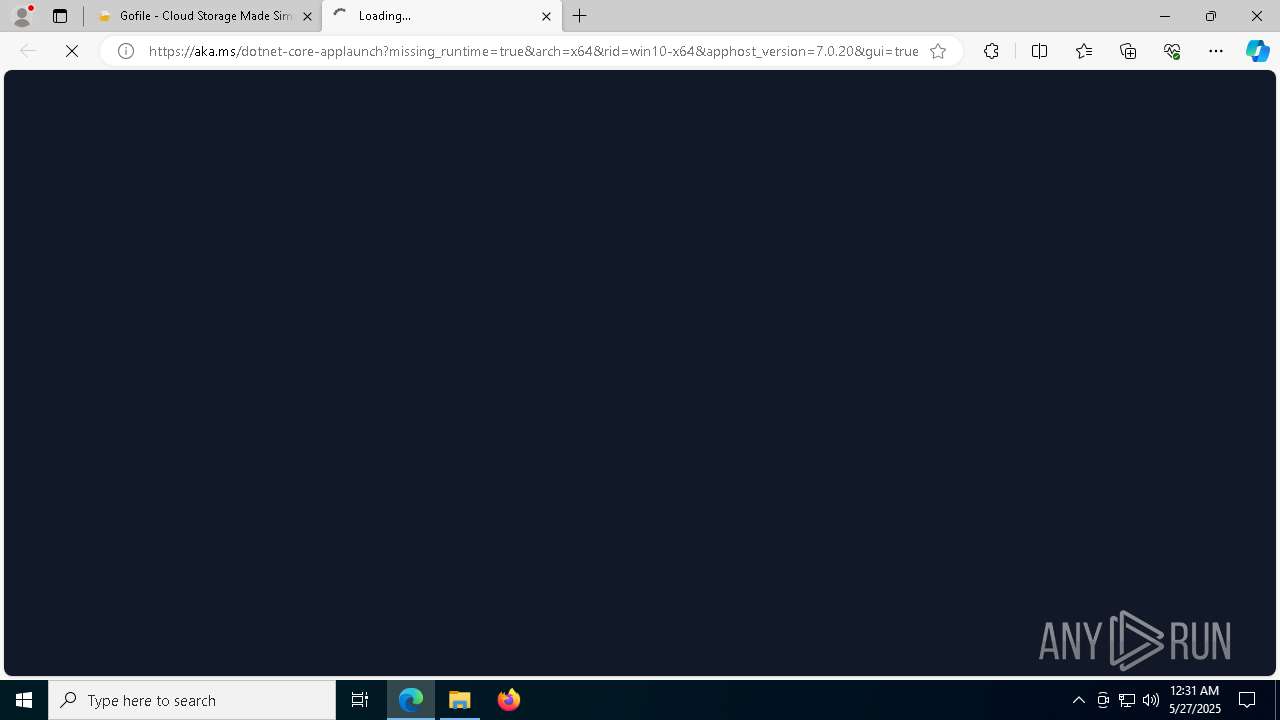
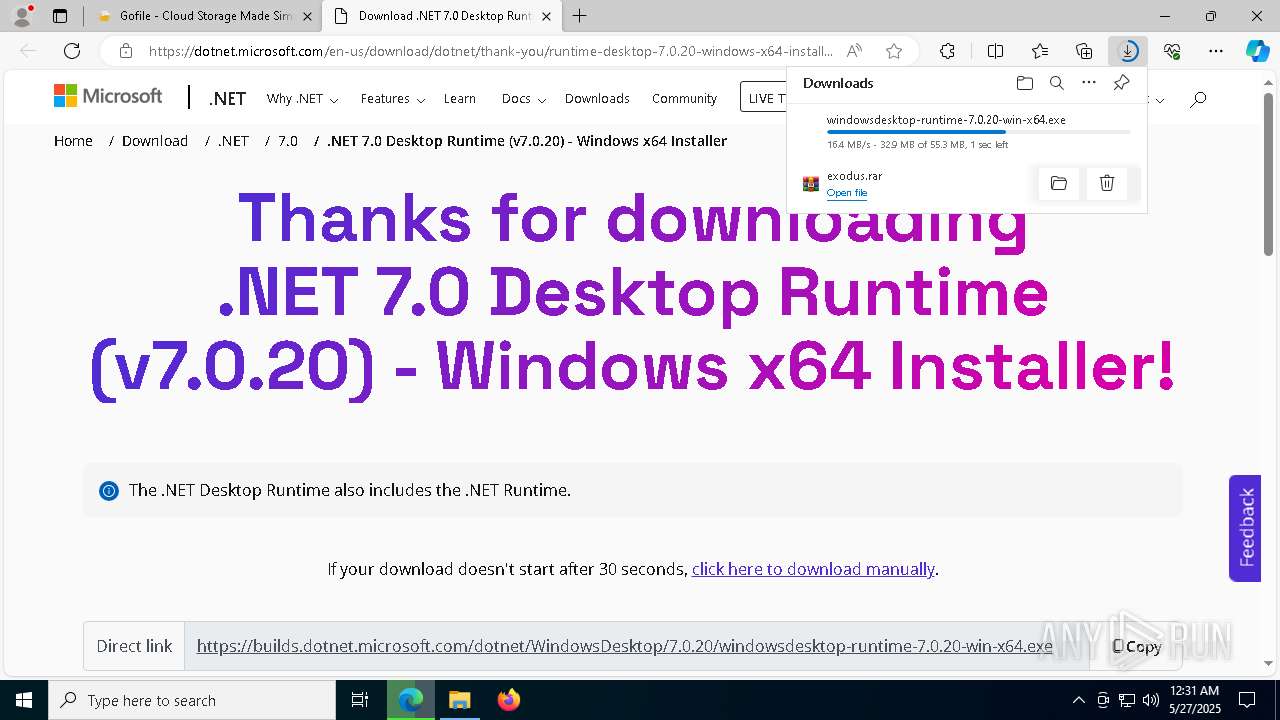
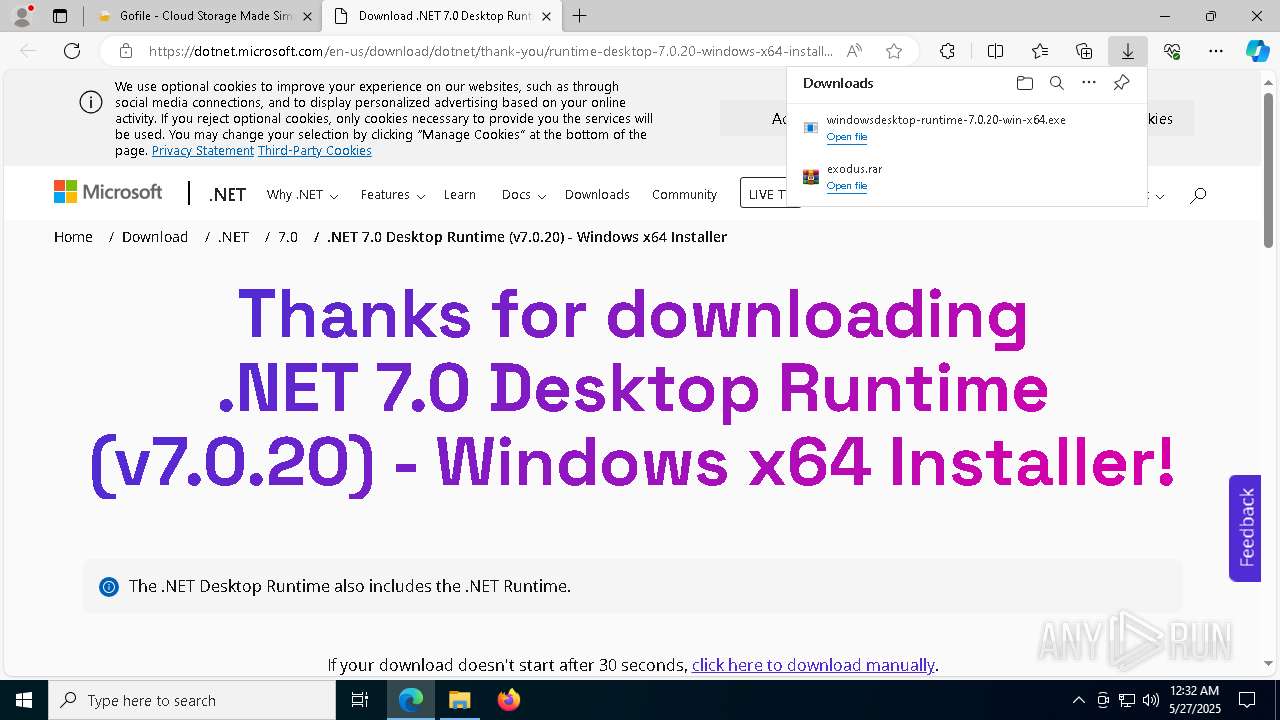
Attempting to use file storage service
- msedge.exe (PID: 7208)
Reads Environment values
- identity_helper.exe (PID: 2420)
Reads the computer name
- identity_helper.exe (PID: 2420)
- Exodus.exe (PID: 8824)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
- msiexec.exe (PID: 5720)
- msiexec.exe (PID: 5984)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8580)
- msedge.exe (PID: 5776)
- msiexec.exe (PID: 5720)
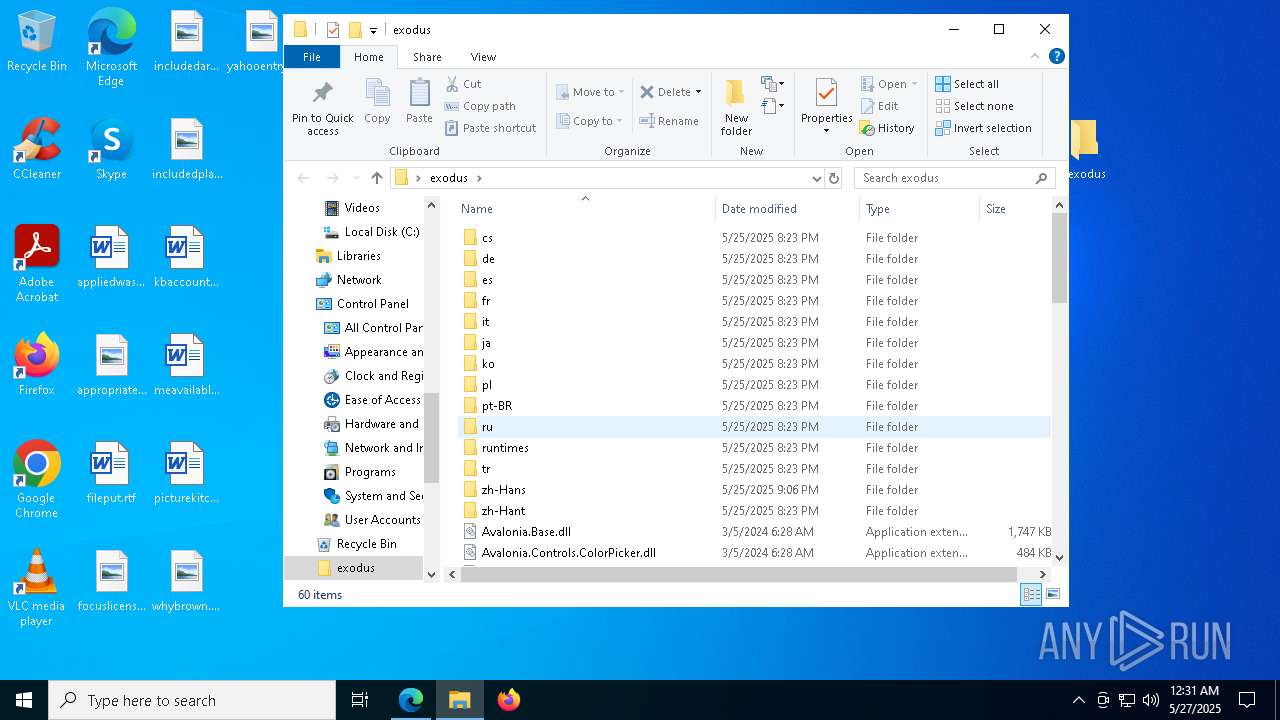
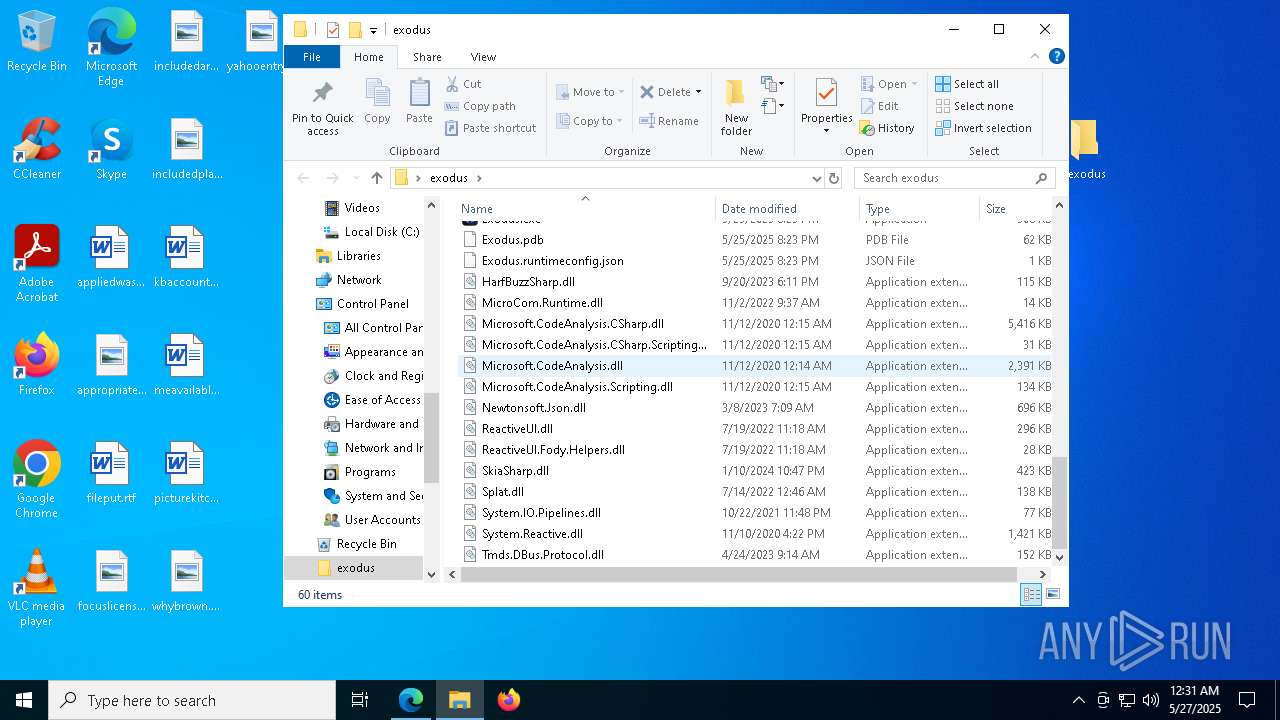
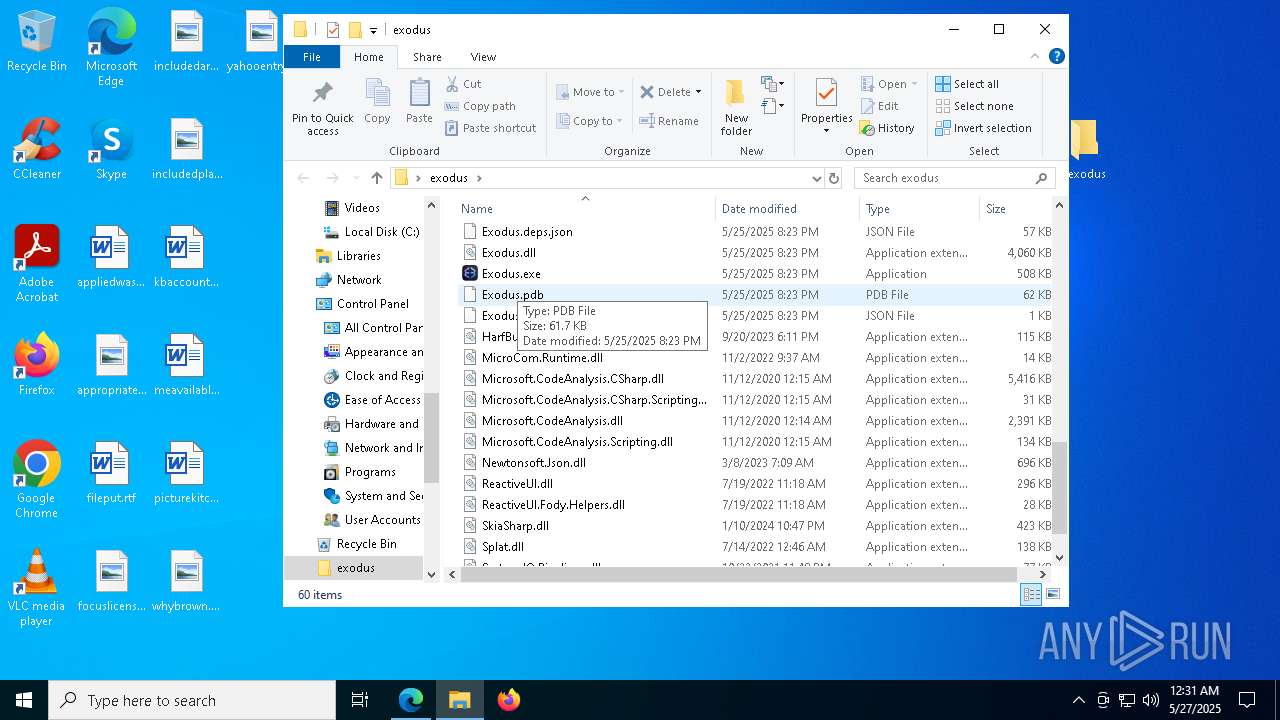
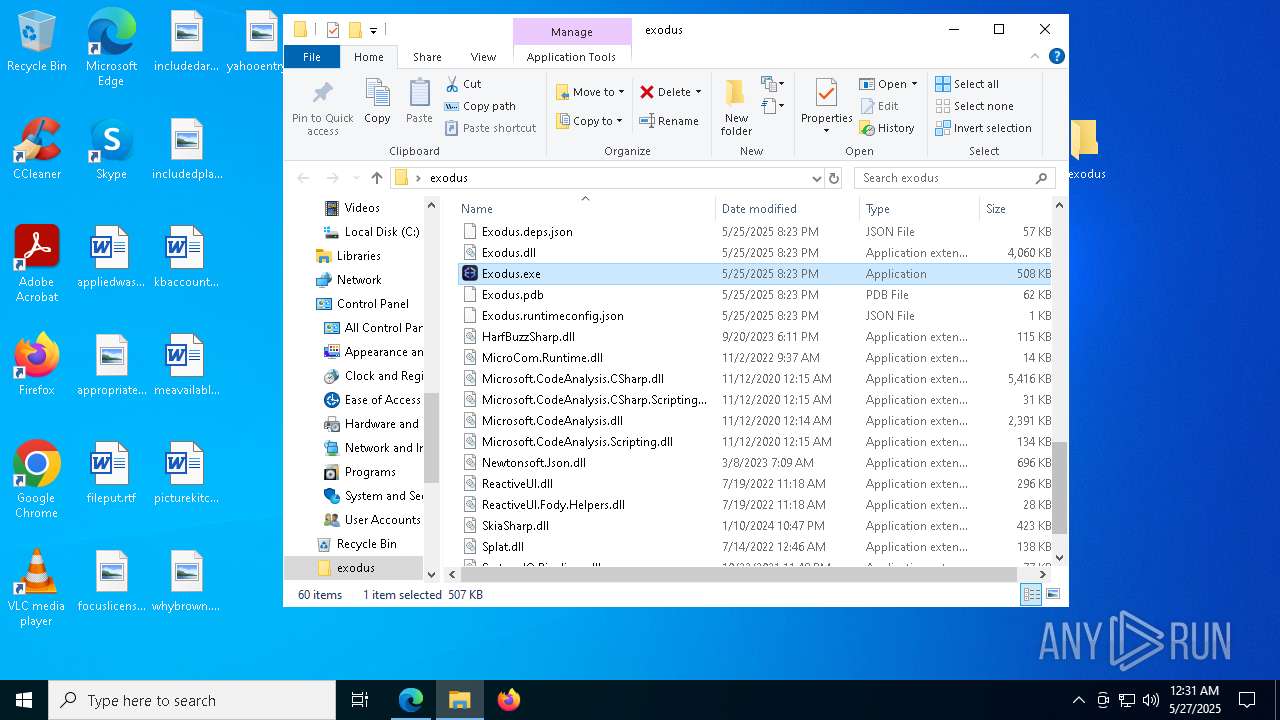
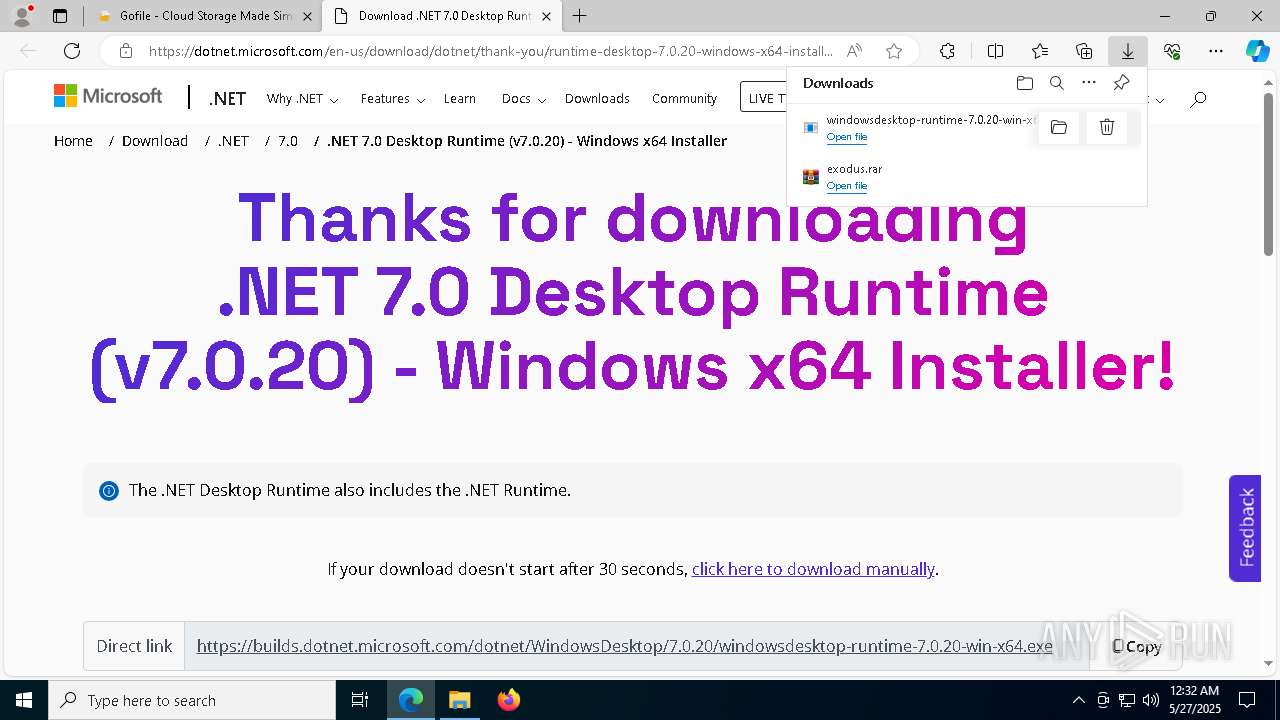
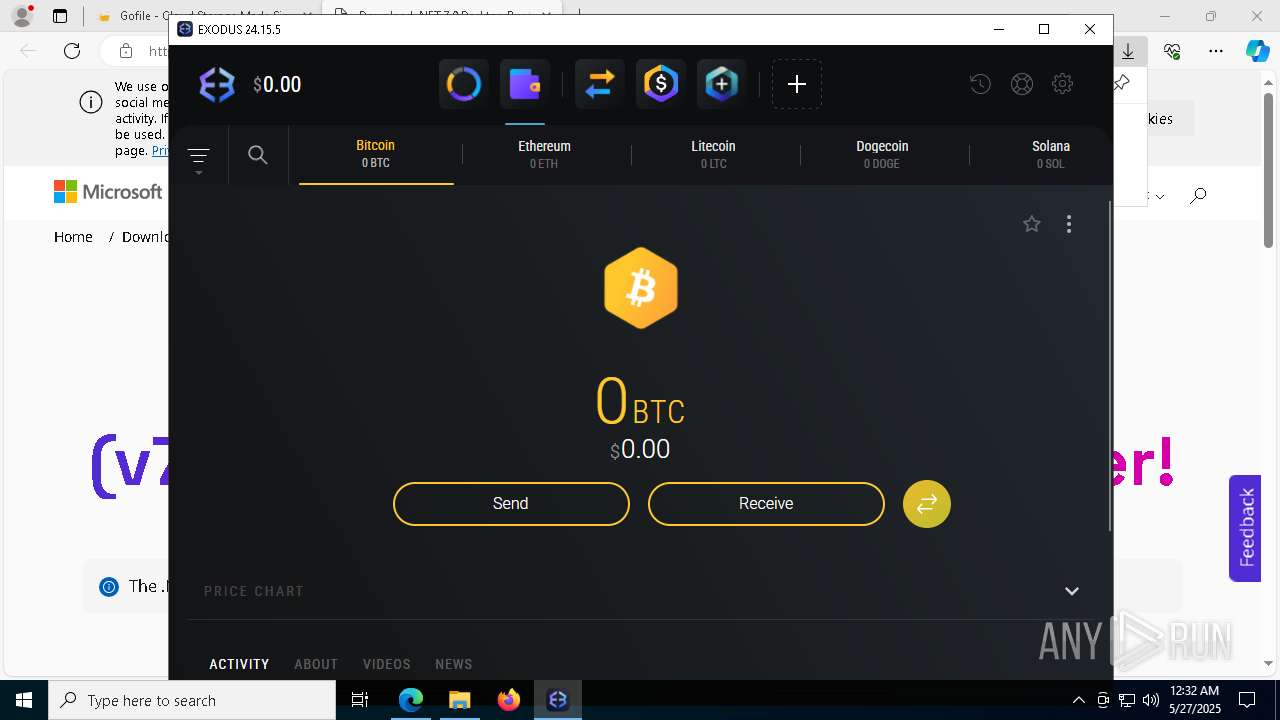
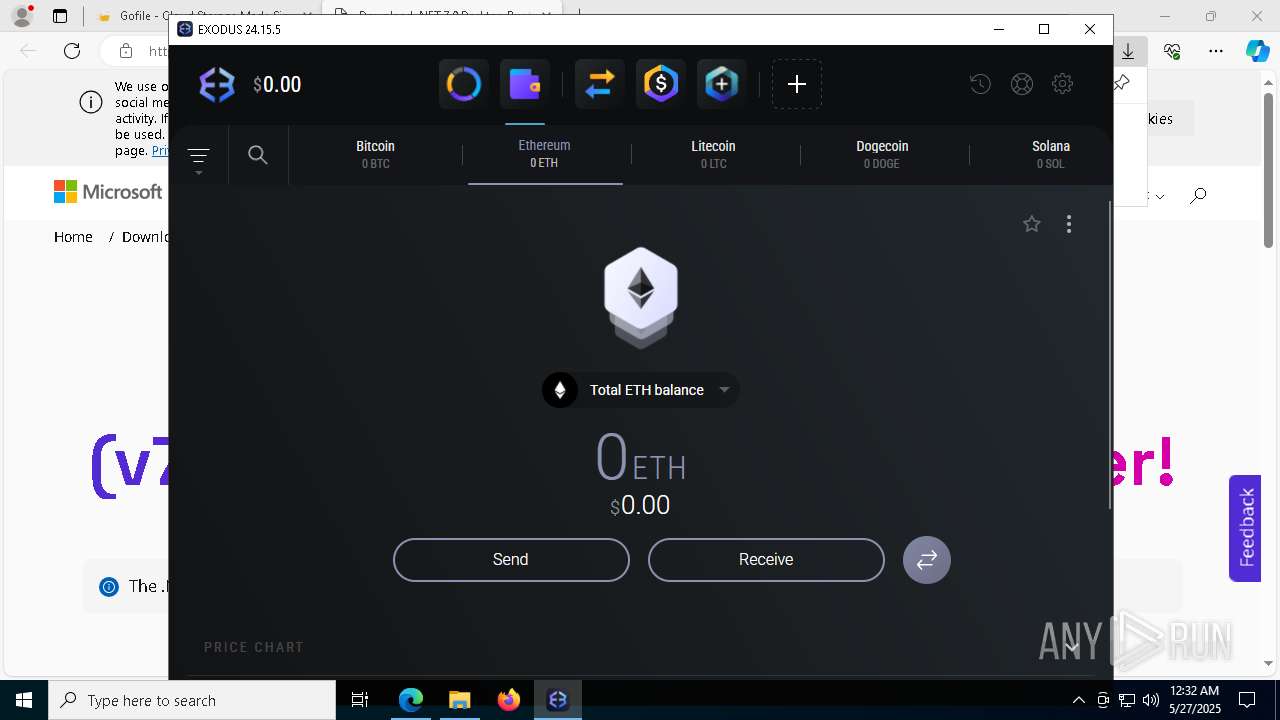
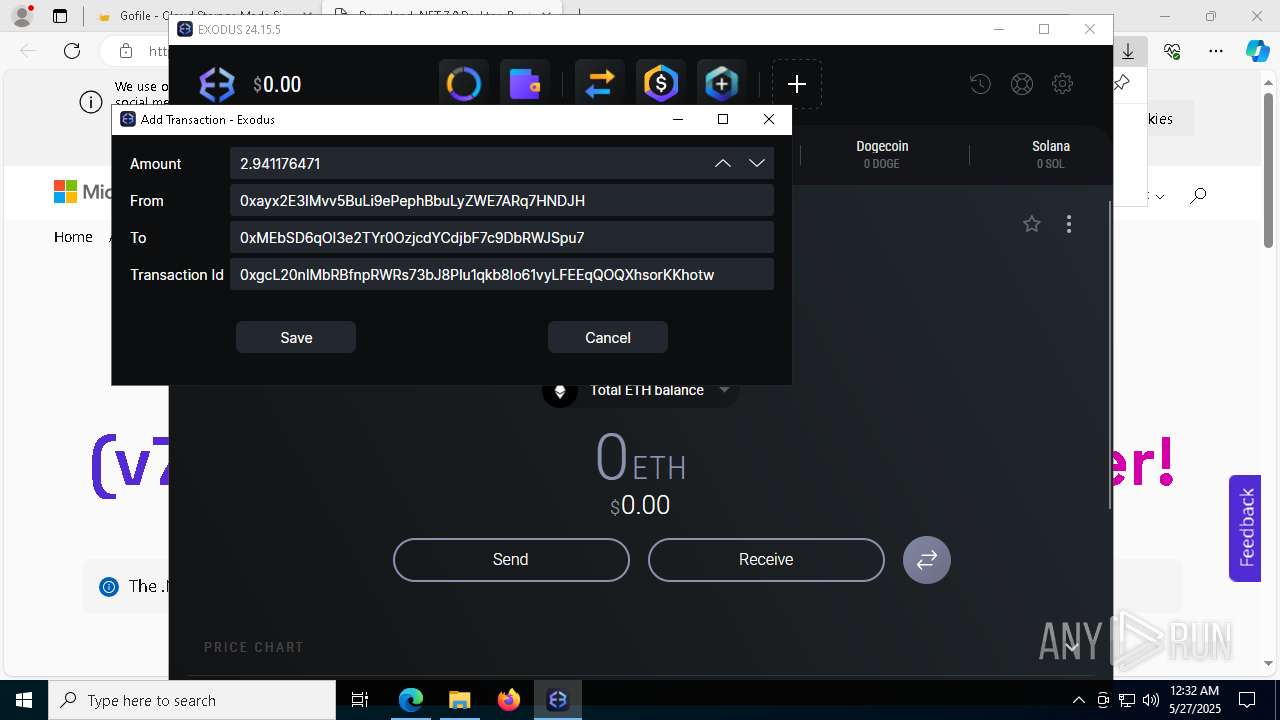
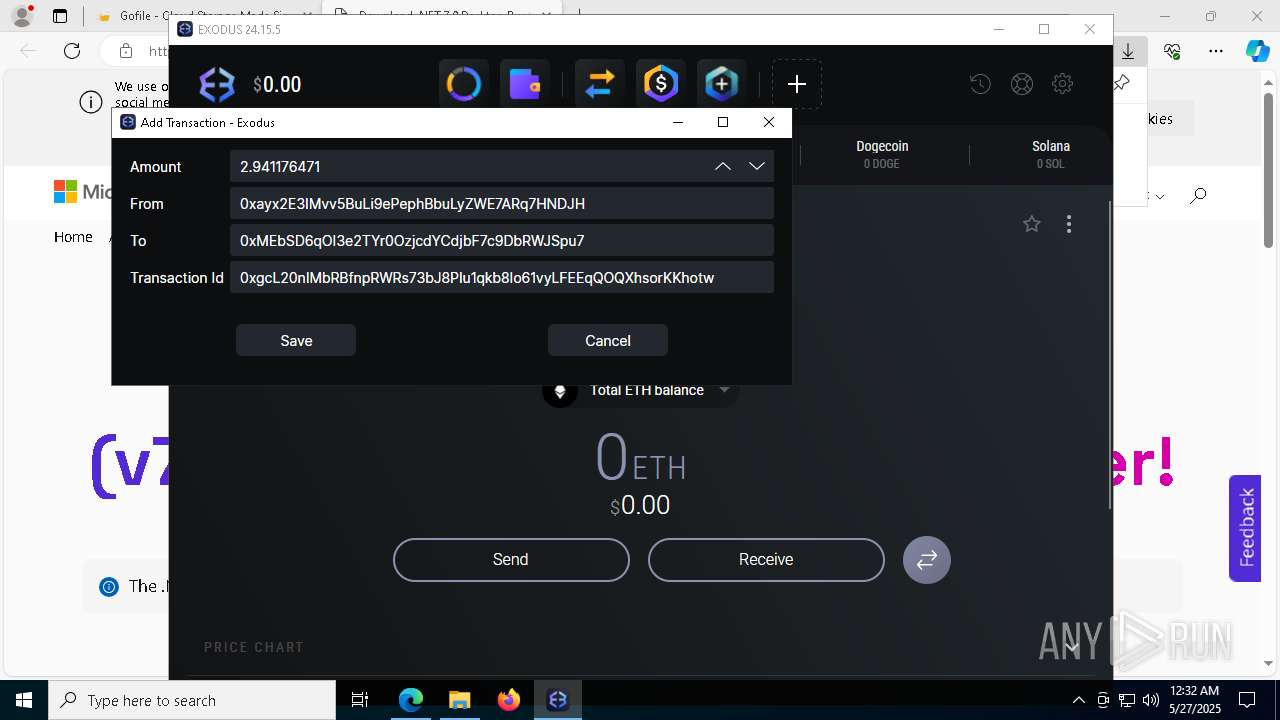
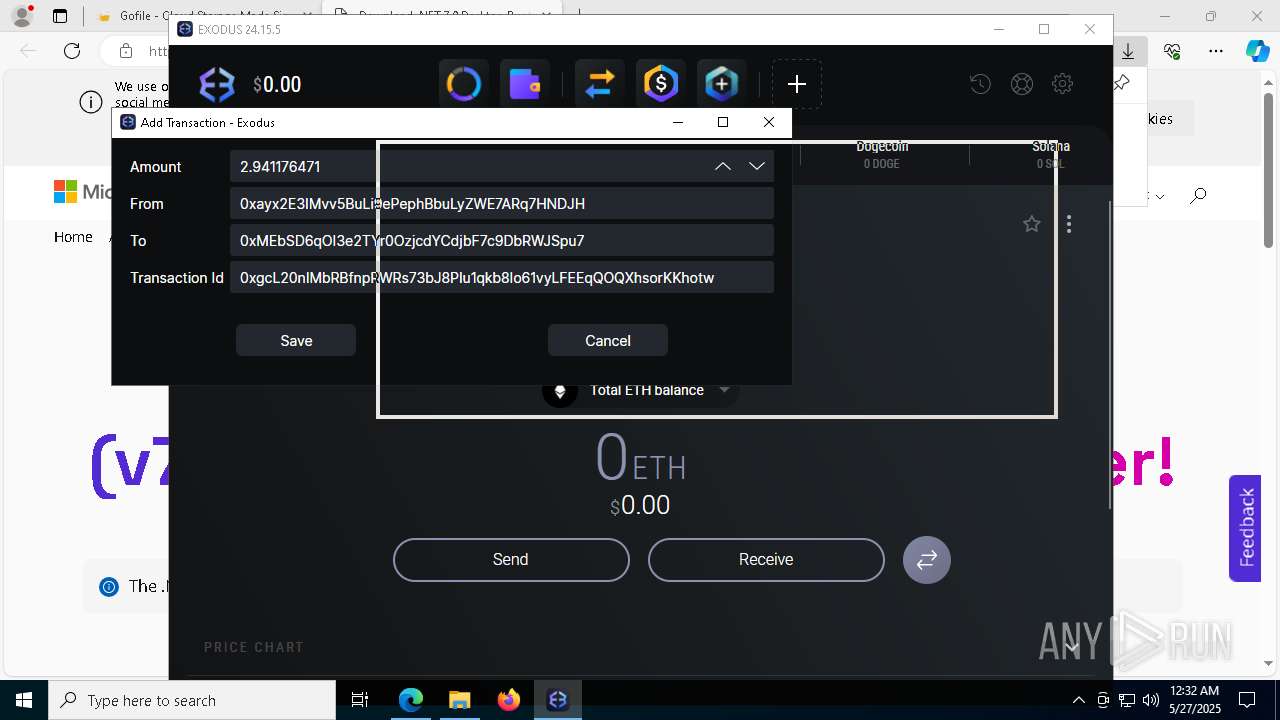
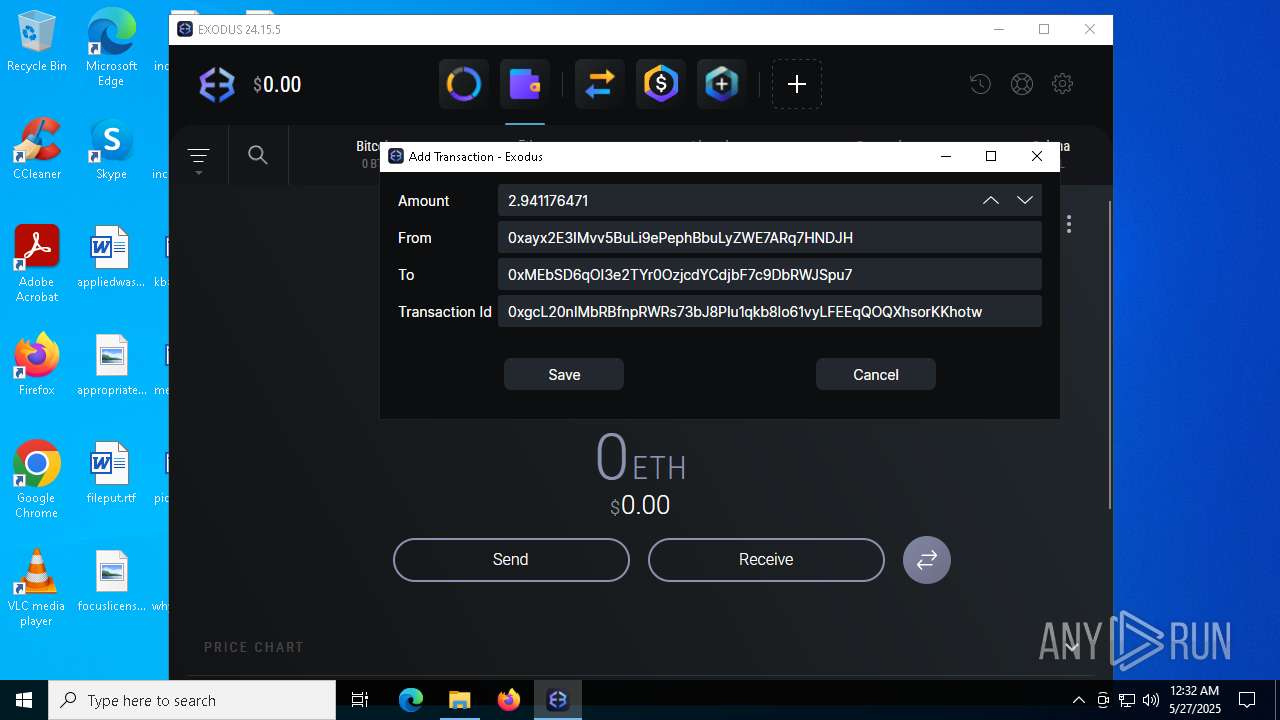
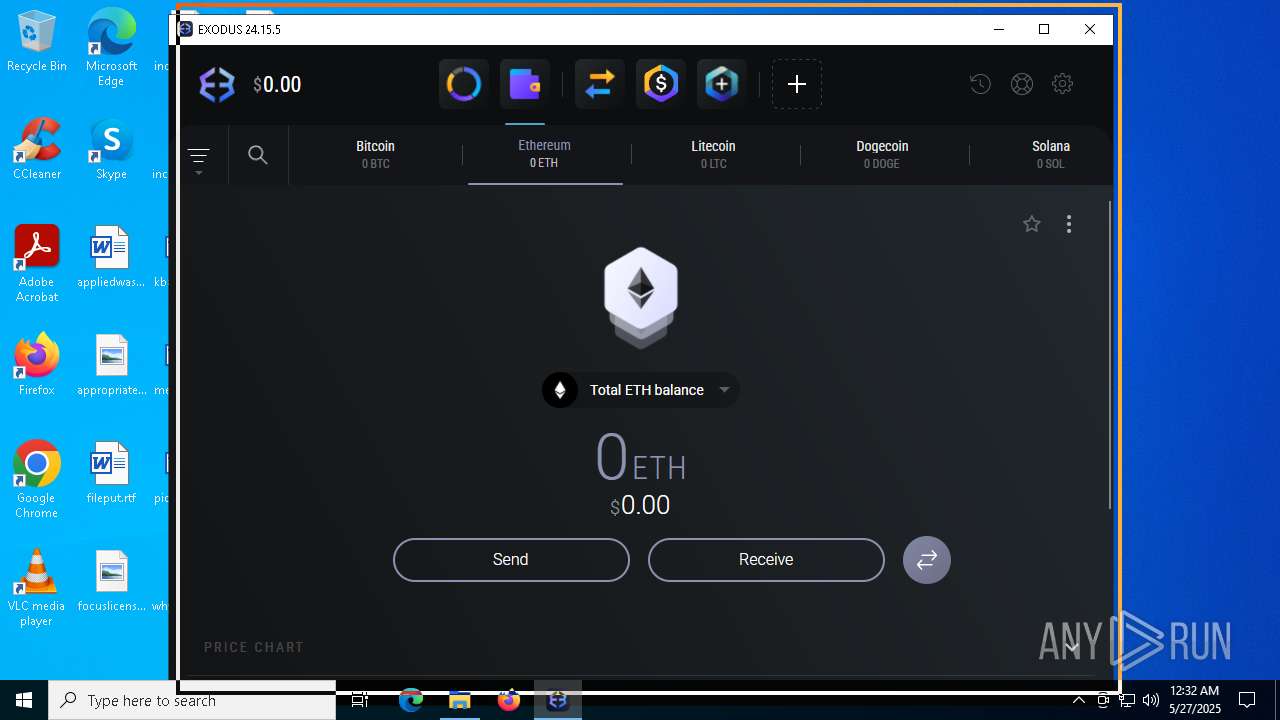
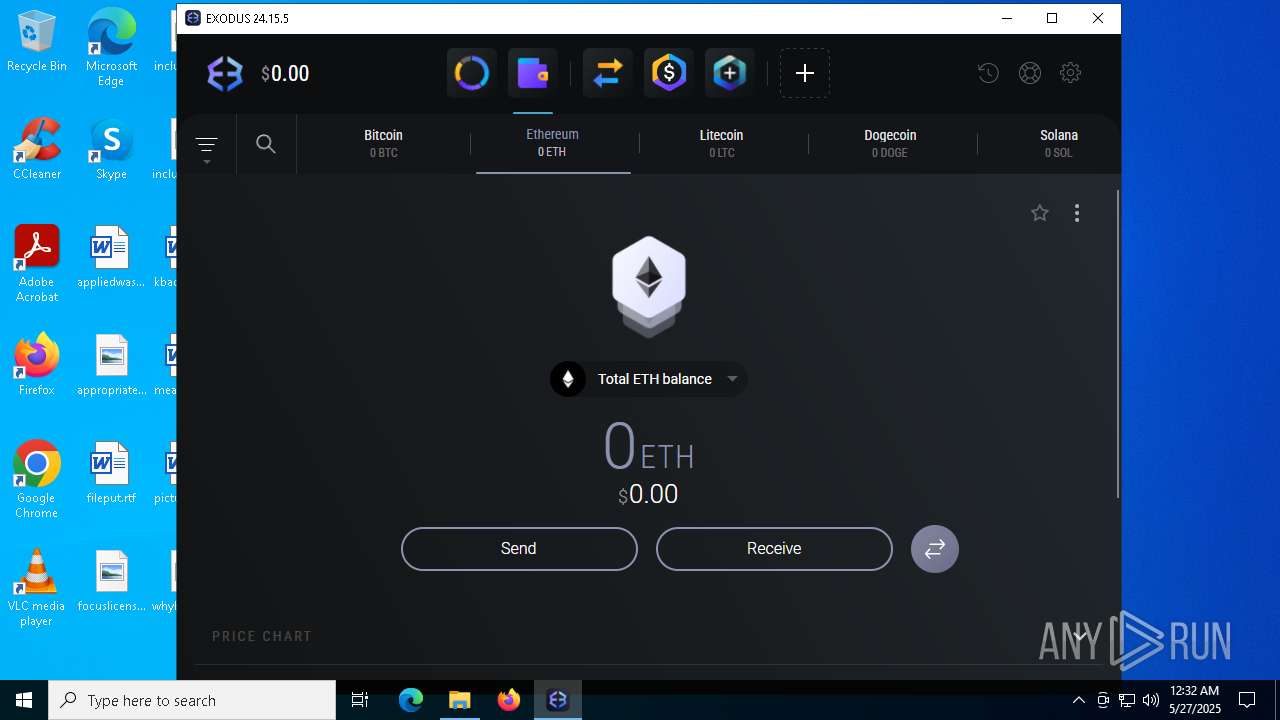
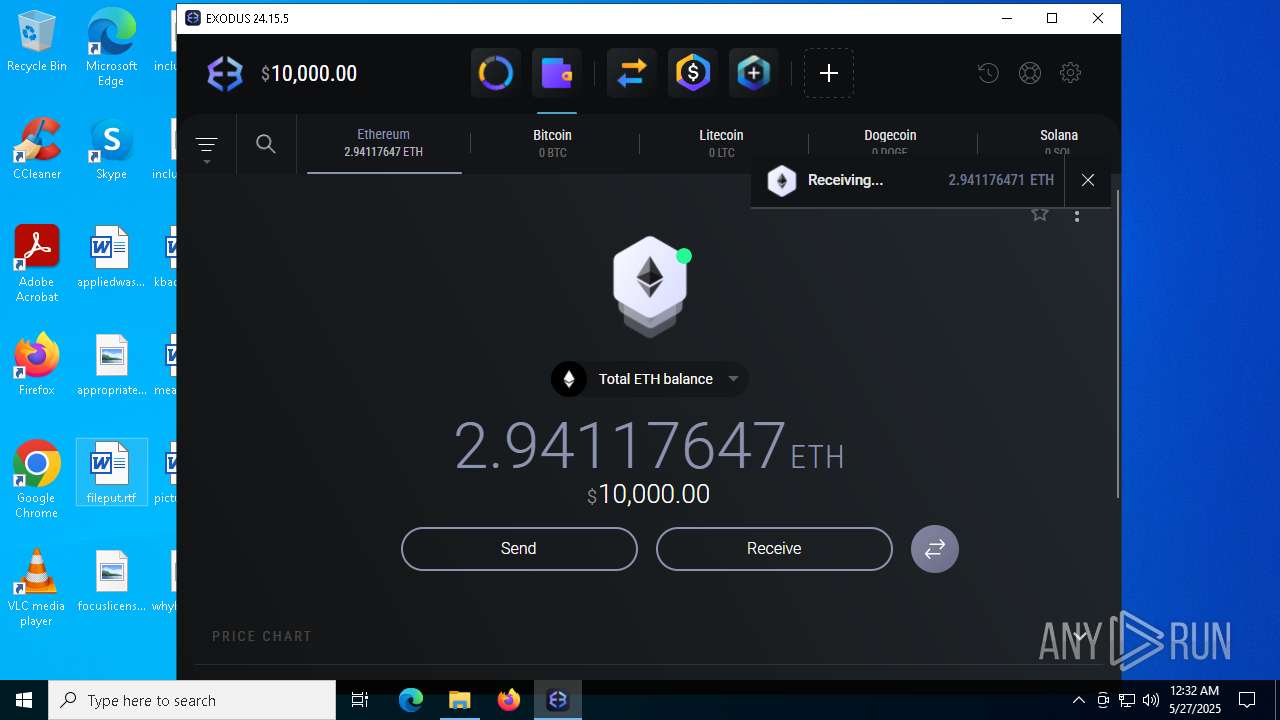
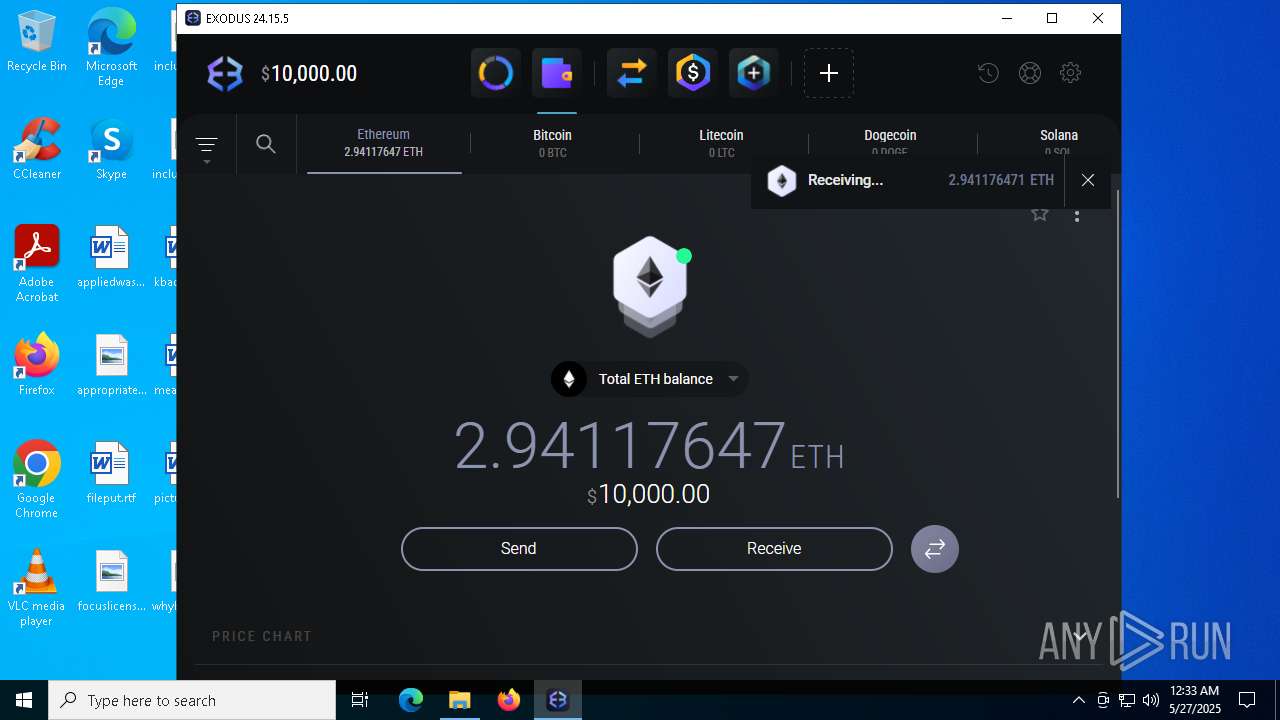
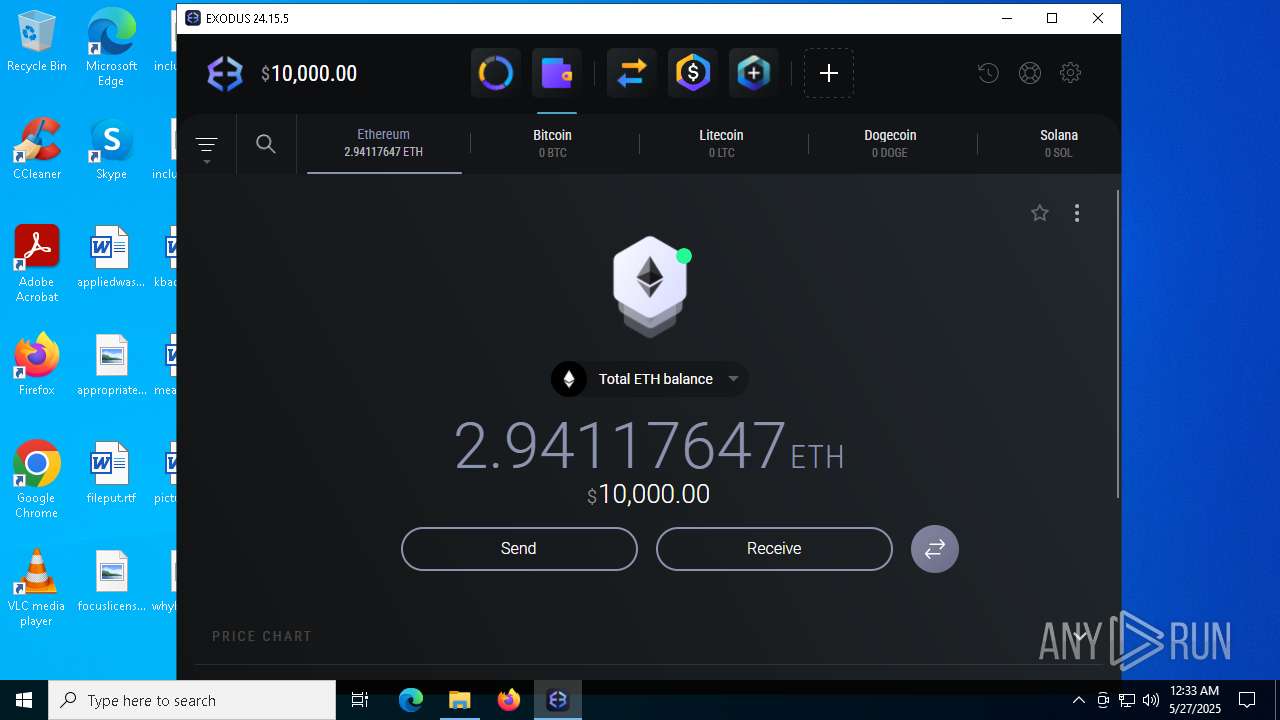
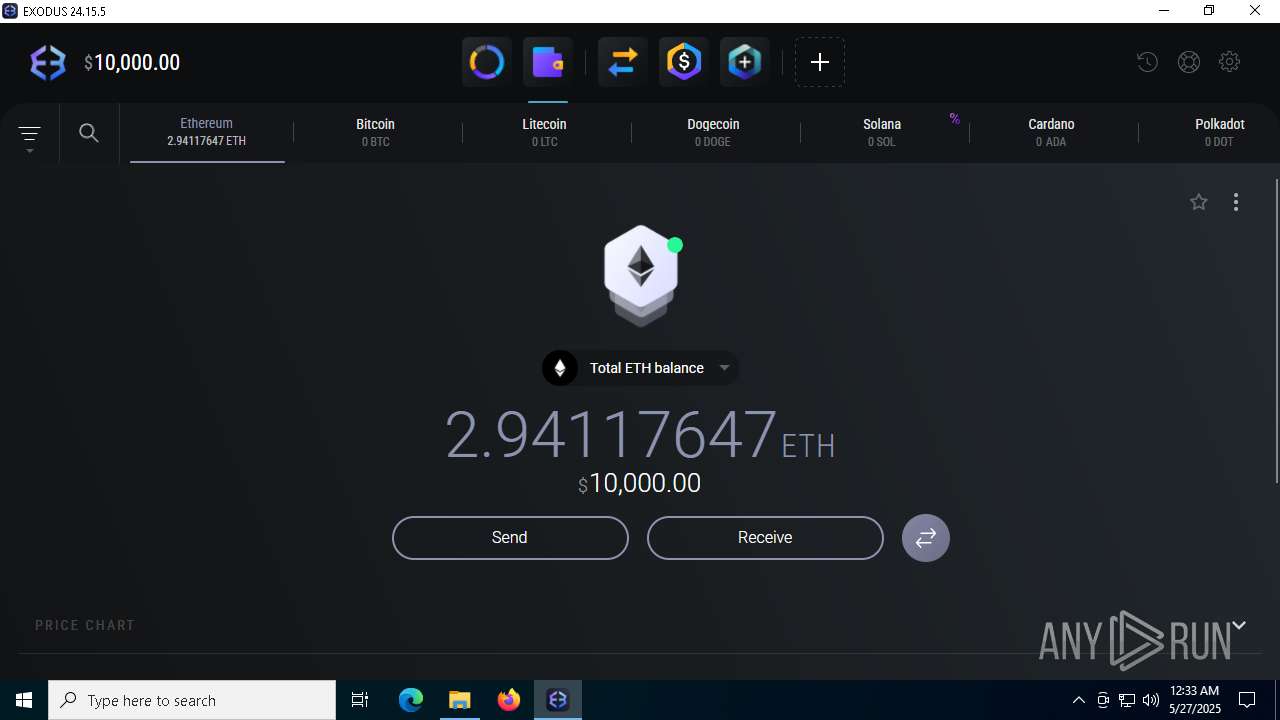
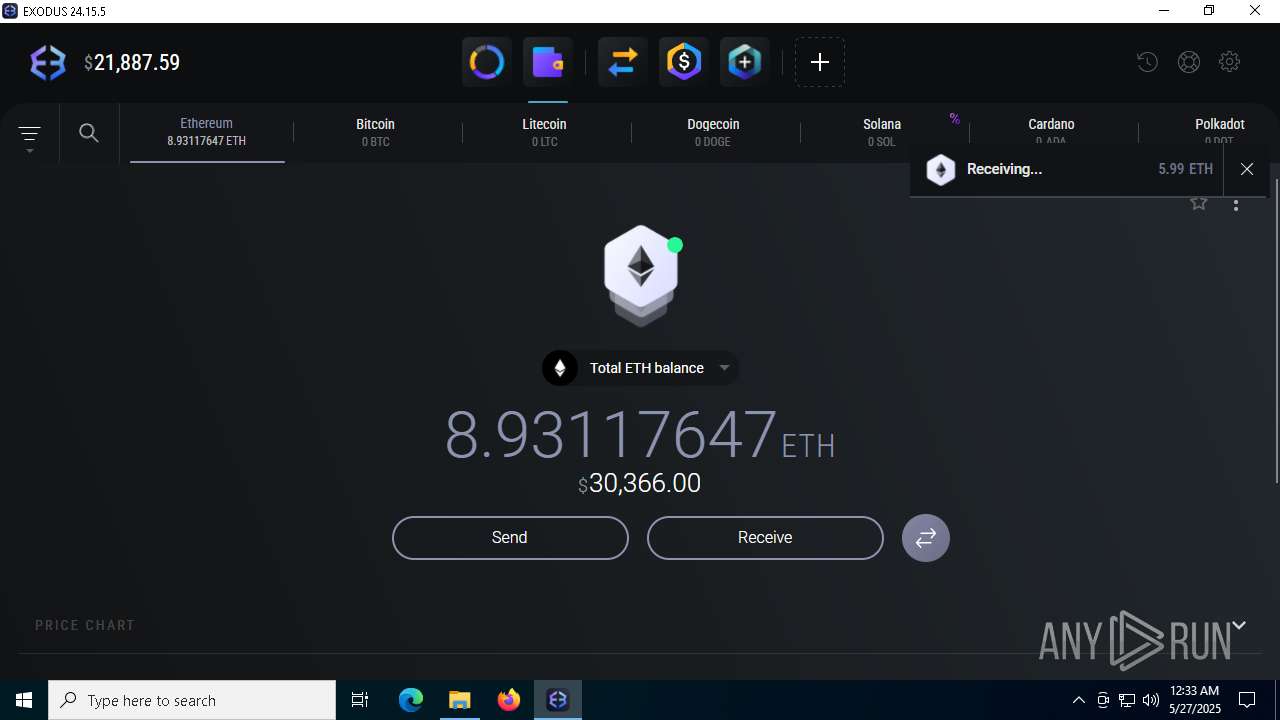
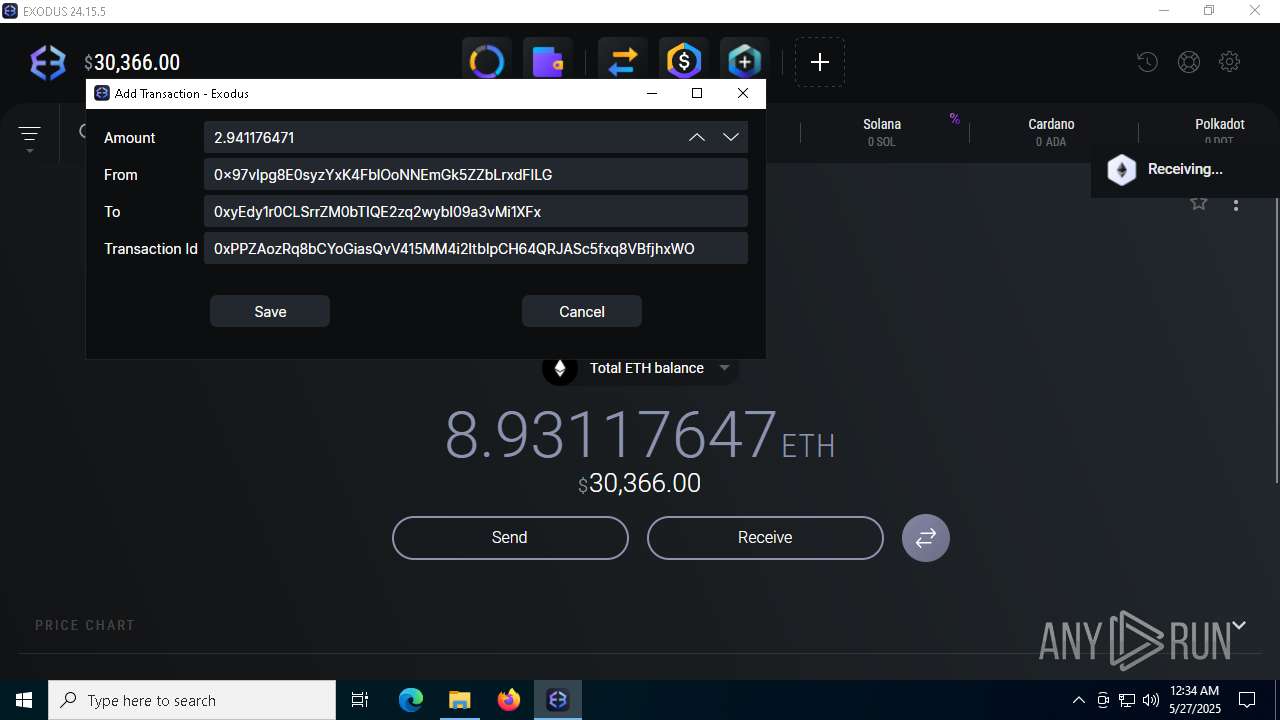
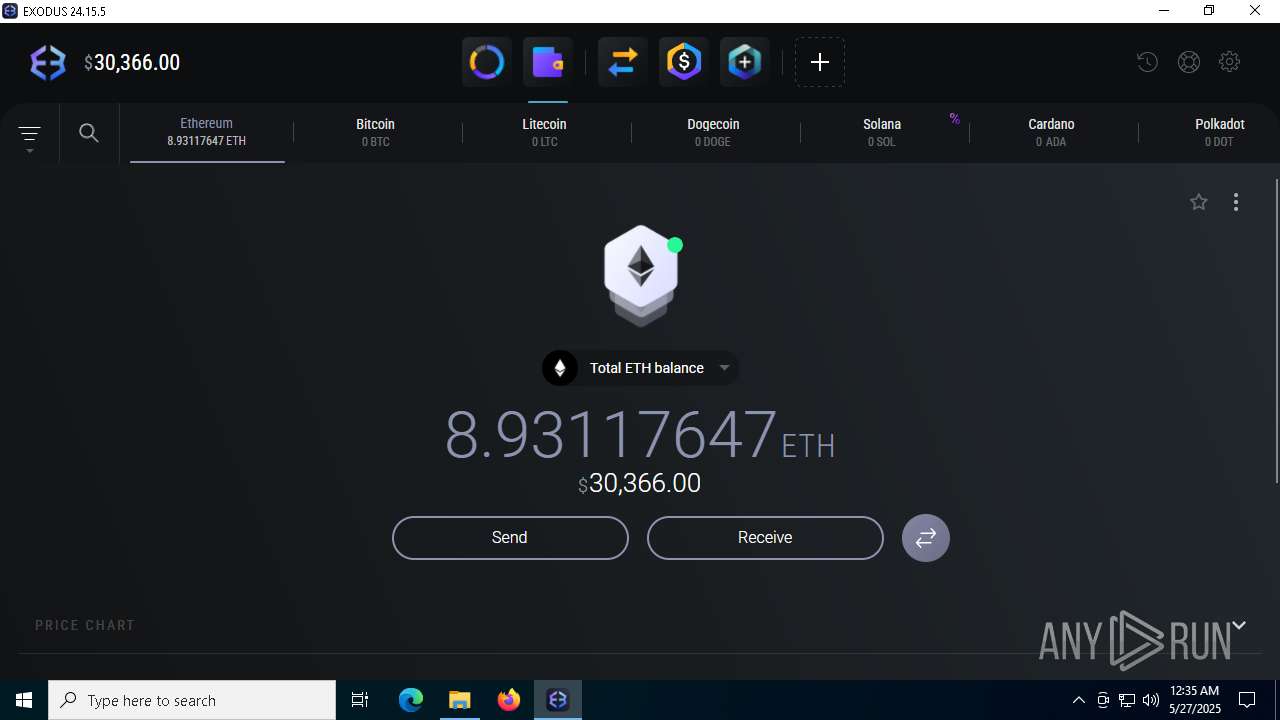
Manual execution by a user
- Exodus.exe (PID: 8824)
- Exodus.exe (PID: 6032)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5776)
The sample compiled with english language support
- WinRAR.exe (PID: 8580)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 4336)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
- msiexec.exe (PID: 5720)
- Wrotocol.exe (PID: 3996)
- ._cache_tool.exe (PID: 8996)
- Built.exe (PID: 8512)
- Built.exe (PID: 4228)
- Built.exe (PID: 8416)
Launch of the file from Downloads directory
- msedge.exe (PID: 8496)
- msedge.exe (PID: 8548)
Create files in a temporary directory
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 4336)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
Process checks computer location settings
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 8216)
Reads the machine GUID from the registry
- msiexec.exe (PID: 5720)
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
Reads the software policy settings
- msiexec.exe (PID: 5720)
Creates files in the program directory
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
Launch of the file from Registry key
- windowsdesktop-runtime-7.0.20-win-x64.exe (PID: 6960)
The sample compiled with turkish language support
- tool.exe (PID: 6496)
- Wrotocol.exe (PID: 8048)
- Synaptics.exe (PID: 716)
The Powershell gets current clipboard
- powershell.exe (PID: 4448)
Checks the directory tree
- tree.com (PID: 7808)
- tree.com (PID: 8464)
- tree.com (PID: 8544)
- tree.com (PID: 8148)
- tree.com (PID: 8512)
- tree.com (PID: 8512)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 5344)
Compiled with Borland Delphi (YARA)
- slui.exe (PID: 5972)
- Exodus.exe (PID: 6032)
- Synaptics.exe (PID: 716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
329
Monitored processes
186
Malicious processes
20
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | C:\Windows\syswow64\MsiExec.exe -Embedding F94B112547BBDA1267699BEEF6E12D17 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | C:\WINDOWS\system32\cmd.exe /c "WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntivirusProduct Get displayName" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | taskkill /F /PID 8796 | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\WINDOWS\system32\cmd.exe /c "taskkill /F /PID 7328" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7156 --field-trial-handle=2272,i,16556765789136241720,11007766523652613092,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 716 | "C:\ProgramData\Synaptics\Synaptics.exe" InjUpdate | C:\ProgramData\Synaptics\Synaptics.exe | tool.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: HIGH Description: Synaptics Pointing Device Driver Version: 1.0.0.4 Modules
| |||||||||||||||
| 976 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\pa1itnr5\pa1itnr5.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1012 | C:\WINDOWS\system32\cmd.exe /c "taskkill /F /PID 8796" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5536 --field-trial-handle=2272,i,16556765789136241720,11007766523652613092,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
77 969
Read events
76 999
Write events
924
Delete events
46
Modification events
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8430D377A9942F00 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {78234325-1C0E-4EC1-8483-66B6636B3D6A} | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A5BC8A3D-EF6F-4FBC-88ED-78C3A8DD1782} | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {51FC0701-E38E-4B47-94FA-03C77A4C2F86} | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B93BCD77A9942F00 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B139A3EE-44A4-476C-9CAF-88003124C373} | |||
Executable files
652
Suspicious files
263
Text files
125
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10a6a2.TMP | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10a6b2.TMP | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10a6b2.TMP | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10a6c1.TMP | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10a6c1.TMP | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
86
DNS requests
105
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5796 | svchost.exe | GET | 304 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8992 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8992 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5776 | msedge.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5776 | msedge.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
2564 | svchost.exe | HEAD | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748410064&P2=404&P3=2&P4=AA8OSaPD7EVXSLjFWuTZSCUyXzD0dH%2bNIeJxJy1K6FeGla7urSwutJFJYvPt6XVDI1%2fQhoqn2jsOu%2fwhMxzKFg%3d%3d | unknown | — | — | whitelisted |
2564 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748410064&P2=404&P3=2&P4=AA8OSaPD7EVXSLjFWuTZSCUyXzD0dH%2bNIeJxJy1K6FeGla7urSwutJFJYvPt6XVDI1%2fQhoqn2jsOu%2fwhMxzKFg%3d%3d | unknown | — | — | whitelisted |
2564 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748410064&P2=404&P3=2&P4=AA8OSaPD7EVXSLjFWuTZSCUyXzD0dH%2bNIeJxJy1K6FeGla7urSwutJFJYvPt6XVDI1%2fQhoqn2jsOu%2fwhMxzKFg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1244 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5796 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5776 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7208 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7208 | msedge.exe | 45.112.123.126:443 | gofile.io | AMAZON-02 | SG | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
gofile.io |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7208 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7208 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7208 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7208 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7208 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7208 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7208 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7208 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7208 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7208 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |