| File name: | dom1.msi |
| Full analysis: | https://app.any.run/tasks/53a057d6-5a49-4b8b-b6d0-c6319d1bbdef |
| Verdict: | Malicious activity |
| Threats: | FlawedAmmmyy is a RAT type malware that can be used to perform actions remotely on an infected PC. This malware is well known for being featured in especially large campaigns with wide target demographics. |
| Analysis date: | April 24, 2019, 00:15:42 |
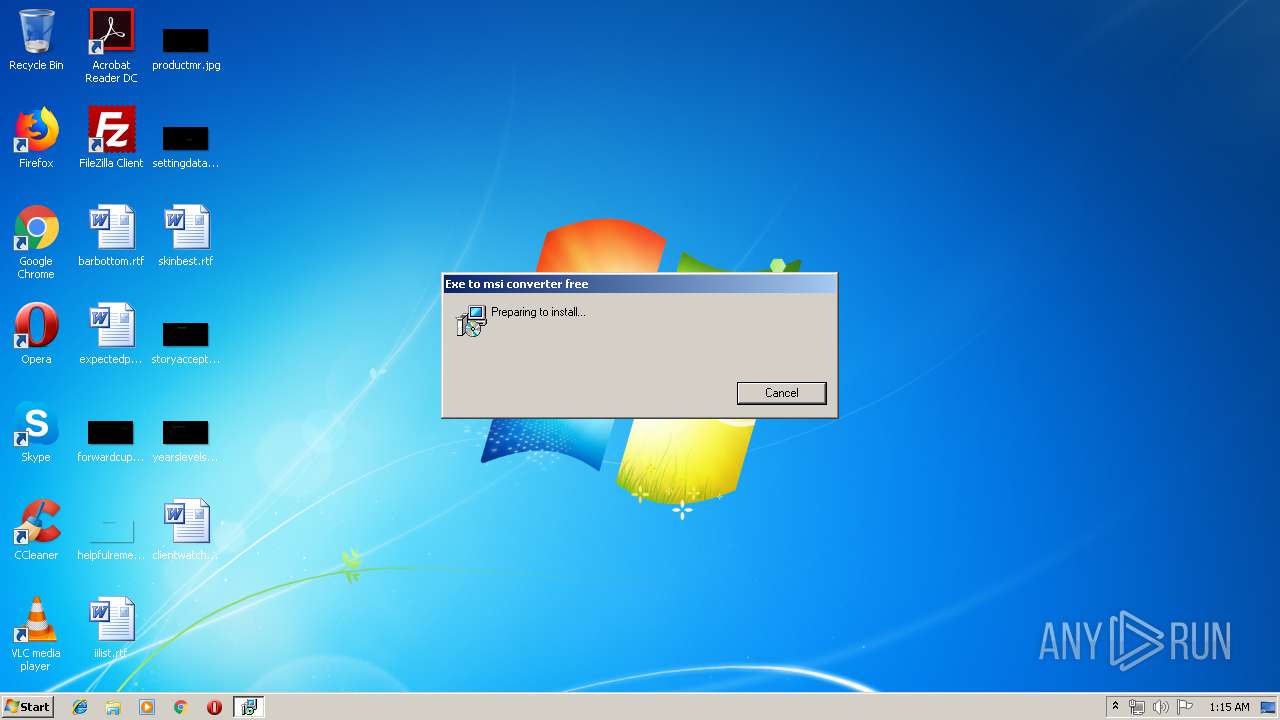
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 1252, Last Printed: Fri Sep 21 10:56:09 2012, Create Time/Date: Fri Sep 21 10:56:09 2012, Name of Creating Application: Windows Installer, Title: Exe to msi converter free, Author: www.exetomsi.com, Template: ;0, Last Saved By: devuser, Revision Number: {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E}, Last Saved Time/Date: Tue May 21 12:56:44 2013, Number of Pages: 100, Number of Words: 0, Security: 0 |
| MD5: | 15524A83BFD4D2FDEE1239CC63113850 |
| SHA1: | 1DC87EE1C638A19F248F18770C04DAEDF76DAE3F |
| SHA256: | 50F300BF2E87A2063EEE32867B1D7F41F55F67CEC0B2F26D2D6766DCF7C459A6 |
| SSDEEP: | 3072:PEPHxd8I0CzoaKeRuZHlSTfQCayLCw3aTXN9GwjF:PEPoIJk+zCnr7R |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 2604)
- cmd.exe (PID: 3592)
- cmd.exe (PID: 2188)
AMMYY was detected
- wsus.exe (PID: 2456)
FLAWEDAMMYY was detected
- wsus.exe (PID: 2456)
Connects to CnC server
- wsus.exe (PID: 2456)
Application was dropped or rewritten from another process
- wsus.exe (PID: 3440)
- wsus.exe (PID: 2456)
SUSPICIOUS
Drop ExeToMSI Application
- msiexec.exe (PID: 2396)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2396)
- MSI9D3E.tmp (PID: 3264)
Starts CMD.EXE for commands execution
- MSI9D3E.tmp (PID: 3264)
Starts SC.EXE for service management
- cmd.exe (PID: 2888)
- cmd.exe (PID: 3856)
- cmd.exe (PID: 3064)
Creates files in the program directory
- MSI9D3E.tmp (PID: 3264)
Application launched itself
- wsus.exe (PID: 3440)
INFO
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3812)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2156)
Searches for installed software
- msiexec.exe (PID: 2396)
Changes settings of System certificates
- DrvInst.exe (PID: 3812)
Starts application with an unusual extension
- msiexec.exe (PID: 2396)
Application was dropped or rewritten from another process
- MSI9D3E.tmp (PID: 3264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| LastPrinted: | 2012:09:21 09:56:09 |
| CreateDate: | 2012:09:21 09:56:09 |
| Software: | Windows Installer |
| Title: | Exe to msi converter free |
| Subject: | - |
| Author: | www.exetomsi.com |
| Keywords: | - |
| Comments: | - |
| Template: | ;0 |
| LastModifiedBy: | devuser |
| RevisionNumber: | {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E} |
| ModifyDate: | 2013:05:21 11:56:44 |
| Pages: | 100 |
| Words: | - |
| Security: | None |
Total processes
60
Monitored processes
22
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\Windows\system32\net1 stop foundation | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1012 | C:\Windows\system32\net1 stop foundation | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1352 | C:\Windows\system32\net1 start foundation y | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1476 | net.exe stop foundation | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2188 | "C:\Windows\System32\cmd.exe" /C net.exe start foundation y | C:\Windows\System32\cmd.exe | MSI9D3E.tmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2332 | net.exe stop foundation | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2456 | "C:\ProgramData\Microsofts HeIp\wsus.exe" -nogui | C:\ProgramData\Microsofts HeIp\wsus.exe | wsus.exe | ||||||||||||
User: SYSTEM Company: Gravity Integrity Level: SYSTEM Description: Gravity Protect Exit code: 0 Version: 7.3.1.1 Modules
| |||||||||||||||
| 2604 | "C:\Windows\System32\cmd.exe" /C net.exe stop foundation | C:\Windows\System32\cmd.exe | MSI9D3E.tmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
616
Read events
436
Write events
180
Delete events
0
Modification events
| (PID) Process: | (2396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000A01C1FE432FAD4015C090000400E0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000A01C1FE432FAD4015C090000400E0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (2396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000002CA366E432FAD4015C090000400E0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000860569E432FAD4015C090000E8060000E8030000010000000000000000000000ED4D08967F1C22449E5125E1C95CE9210000000000000000 | |||
| (PID) Process: | (2156) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EE8E72E432FAD4016C0800006C060000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2156) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EE8E72E432FAD4016C080000F00C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2156) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EE8E72E432FAD4016C080000E40C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2156) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EE8E72E432FAD4016C0800004C040000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2156) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000FCB579E432FAD4016C080000E40C0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
3
Suspicious files
8
Text files
60
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2396 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2396 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF9CD1400620257485.TMP | — | |
MD5:— | SHA256:— | |||
| 2156 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2396 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 3264 | MSI9D3E.tmp | C:\ProgramData\Microsofts HeIp\template_107b318.DATAHASH | binary | |
MD5:— | SHA256:— | |||
| 3264 | MSI9D3E.tmp | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\1[1].tmp | binary | |
MD5:— | SHA256:— | |||
| 2396 | msiexec.exe | C:\Windows\Installer\MSI9C13.tmp | binary | |
MD5:— | SHA256:— | |||
| 2396 | msiexec.exe | C:\Windows\Installer\MSI9D3E.tmp | executable | |
MD5:— | SHA256:— | |||
| 3264 | MSI9D3E.tmp | C:\ProgramData\Microsofts HeIp\wsus.exe | executable | |
MD5:— | SHA256:— | |||
| 2396 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{96084ded-1c7f-4422-9e51-25e1c95ce921}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
0
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3264 | MSI9D3E.tmp | GET | 200 | 160.202.162.147:80 | http://160.202.162.147/1.tmp | KR | binary | 627 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 160.202.162.147:80 | — | Korea Telecom | KR | suspicious |
2456 | wsus.exe | 169.239.128.119:80 | — | Zappie Host LLC | ZA | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3264 | MSI9D3E.tmp | A Network Trojan was detected | ET CURRENT_EVENTS MalDoc Request for Payload (TA505 Related) |
2456 | wsus.exe | A Network Trojan was detected | MALWARE [PTsecurity] FlawedAmmyy.RAT |
2456 | wsus.exe | A Network Trojan was detected | MALWARE [PTsecurity] AMMYY RAT |
2456 | wsus.exe | A Network Trojan was detected | ET TROJAN Win32/FlawedAmmyy RAT CnC Checkin |
2456 | wsus.exe | A Network Trojan was detected | MALWARE [PTsecurity] FlawedAmmyy.RAT Checkin |
Process | Message |
|---|---|
MSI9D3E.tmp | C:\ProgramData\Microsofts HeIp\template_107b318.DATAHASH |
MSI9D3E.tmp | 1 |
MSI9D3E.tmp | /C sc create foundation binPath= "C:\ProgramData\Microsofts HeIp\wsus.exe -service" type= own start= auto error= ignore |