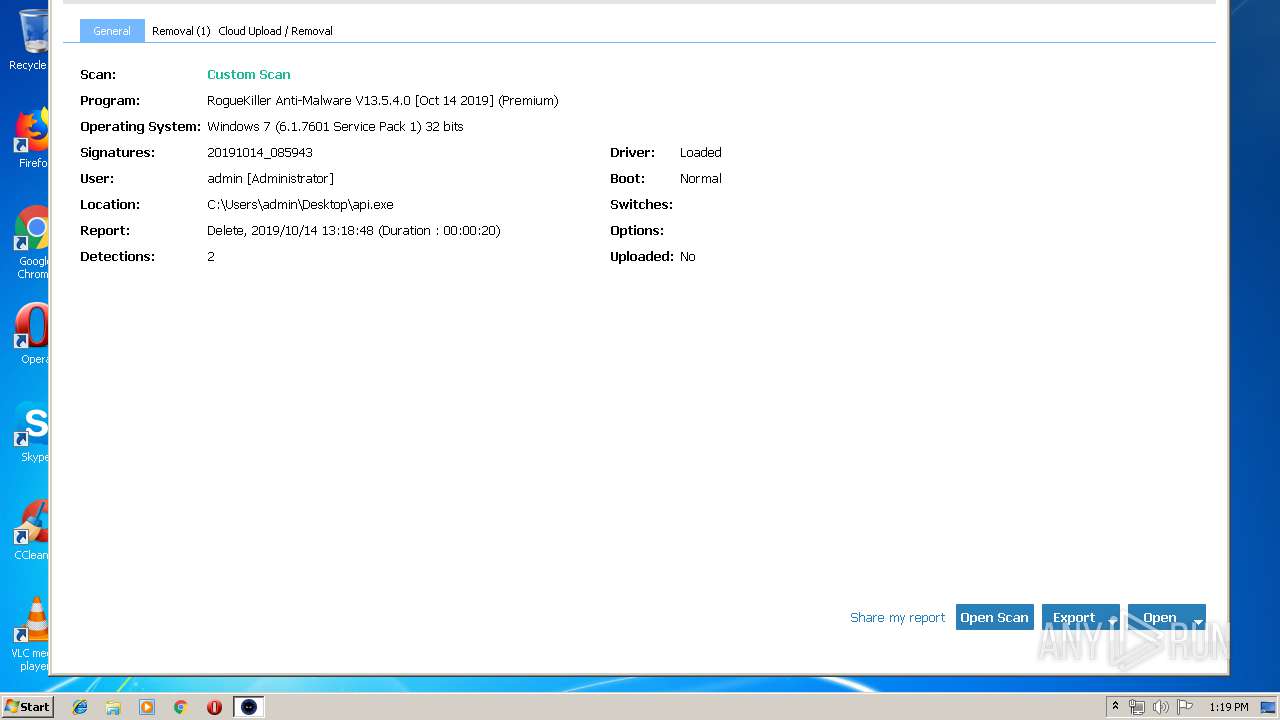
| download: | api |
| Full analysis: | https://app.any.run/tasks/a2d60a92-6312-46ed-8d7a-3a8329381f85 |
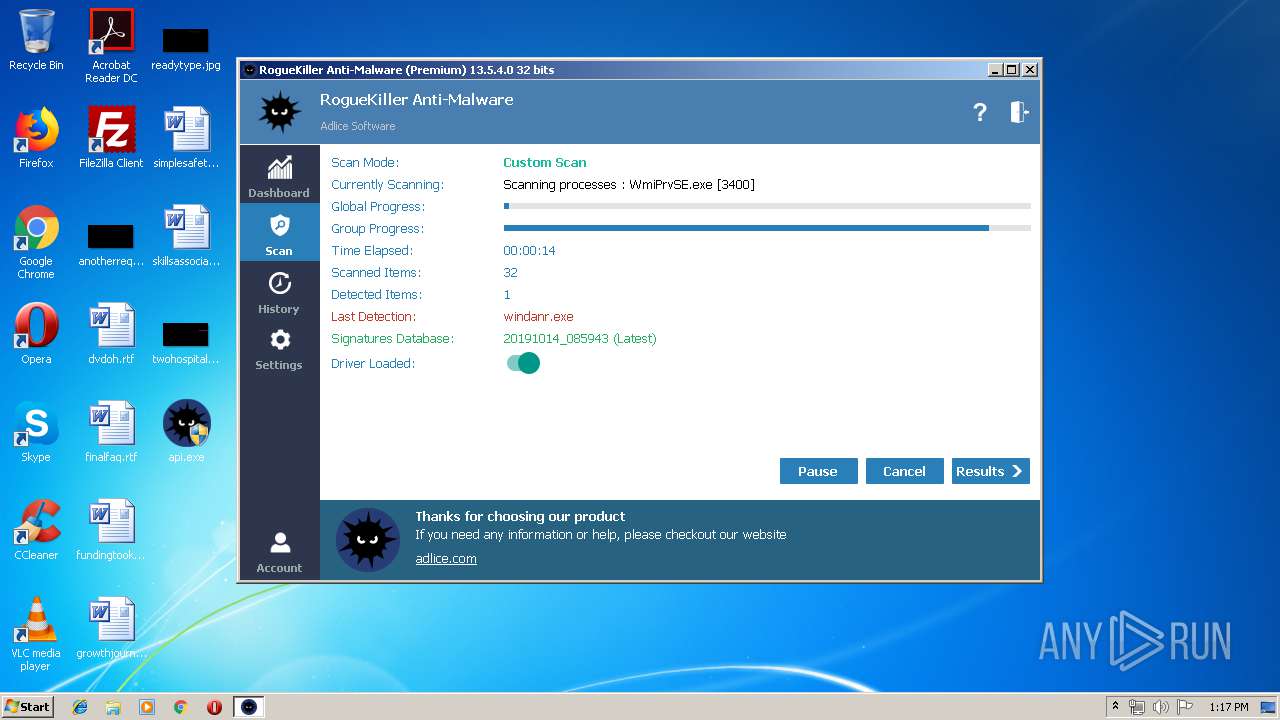
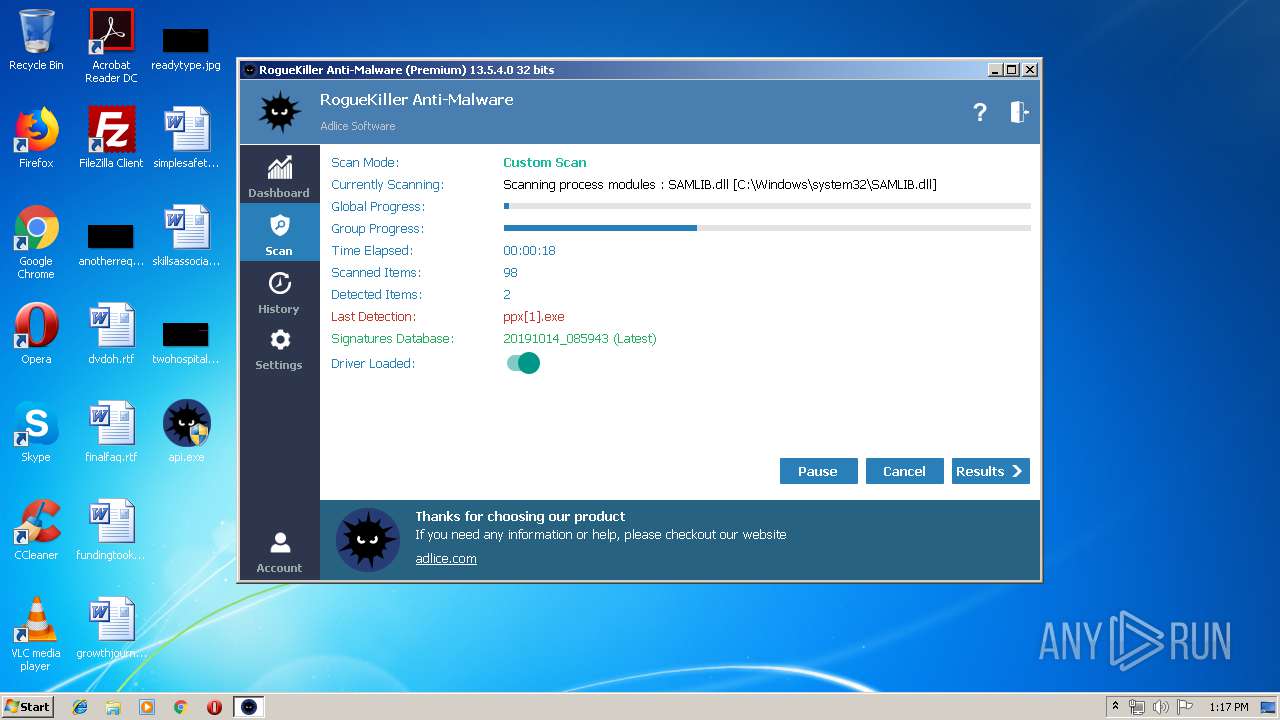
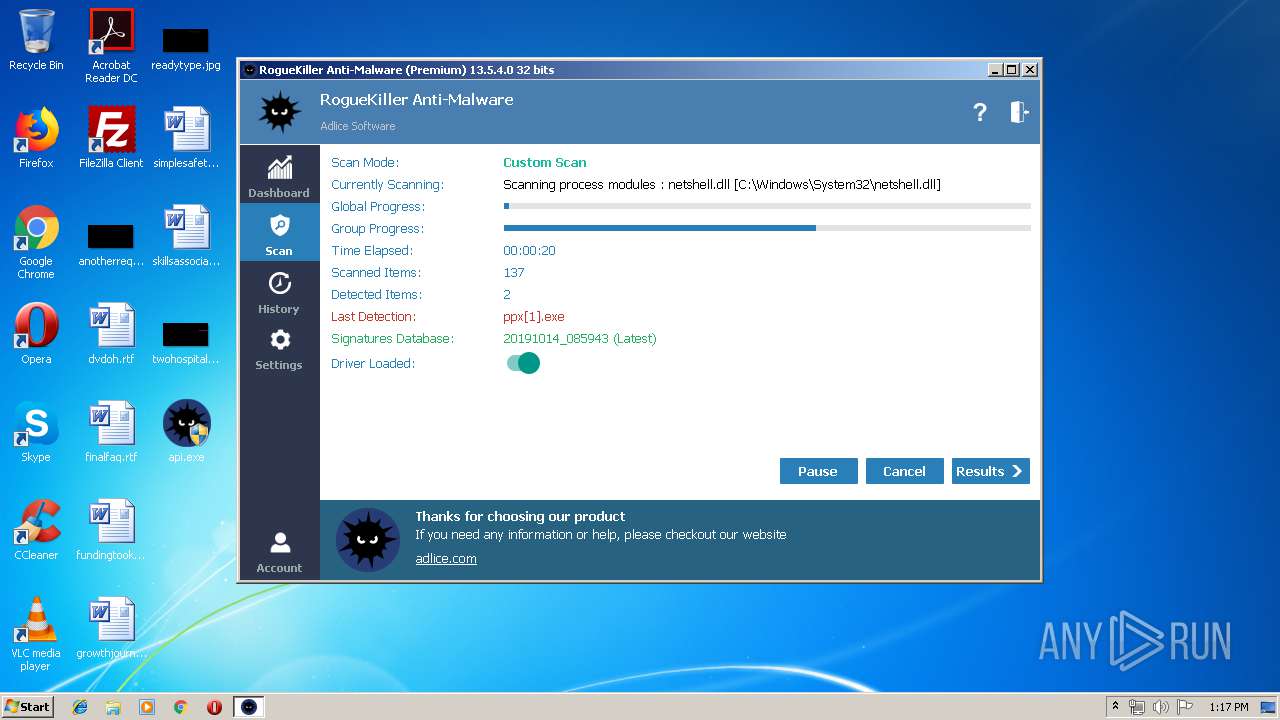
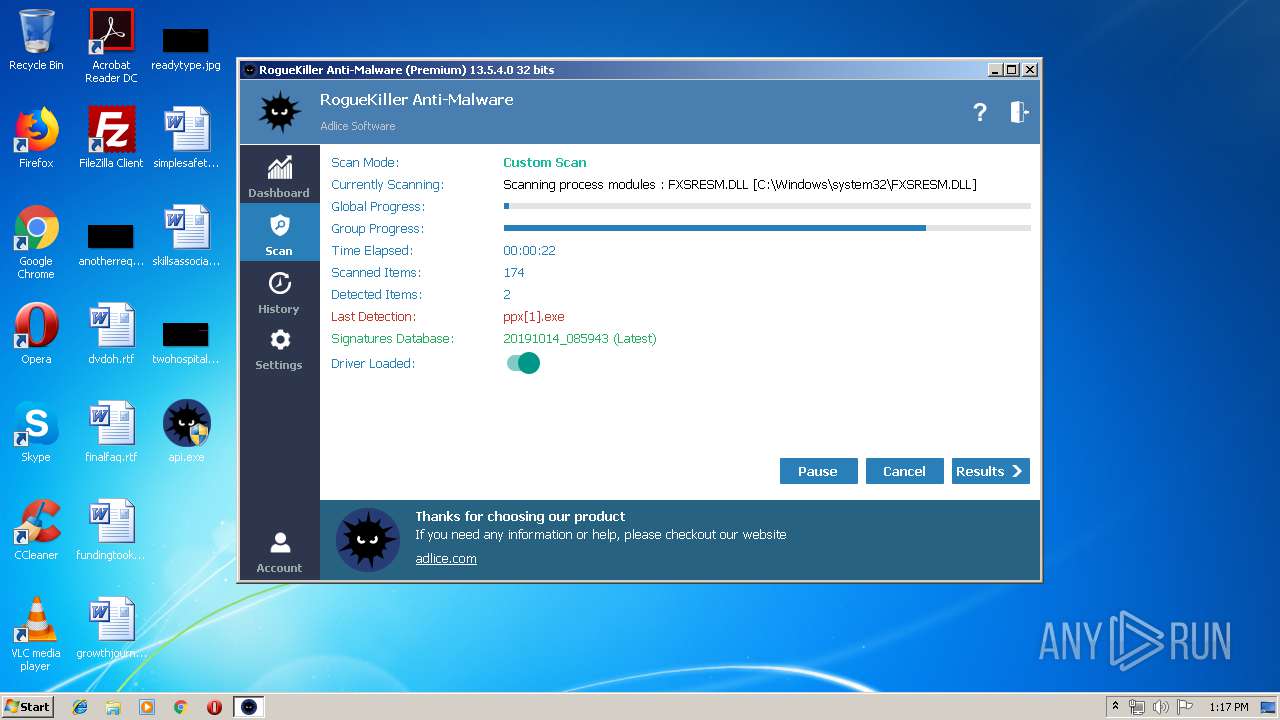
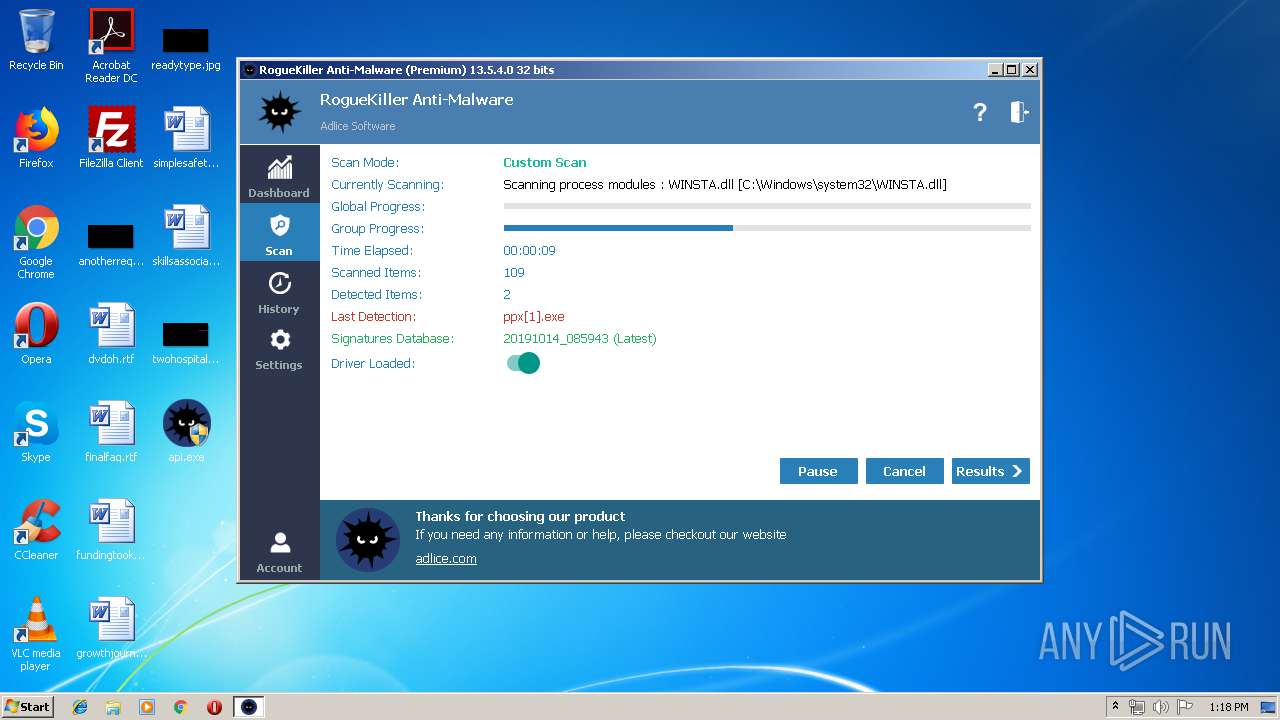
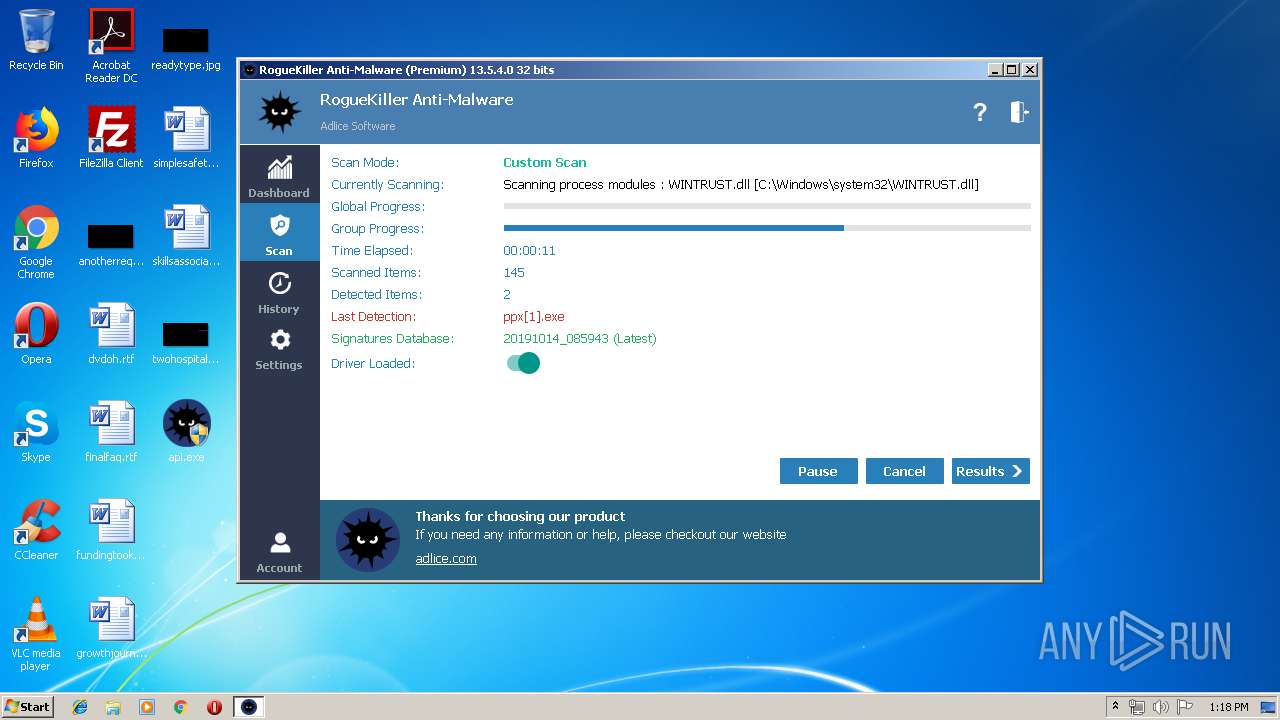
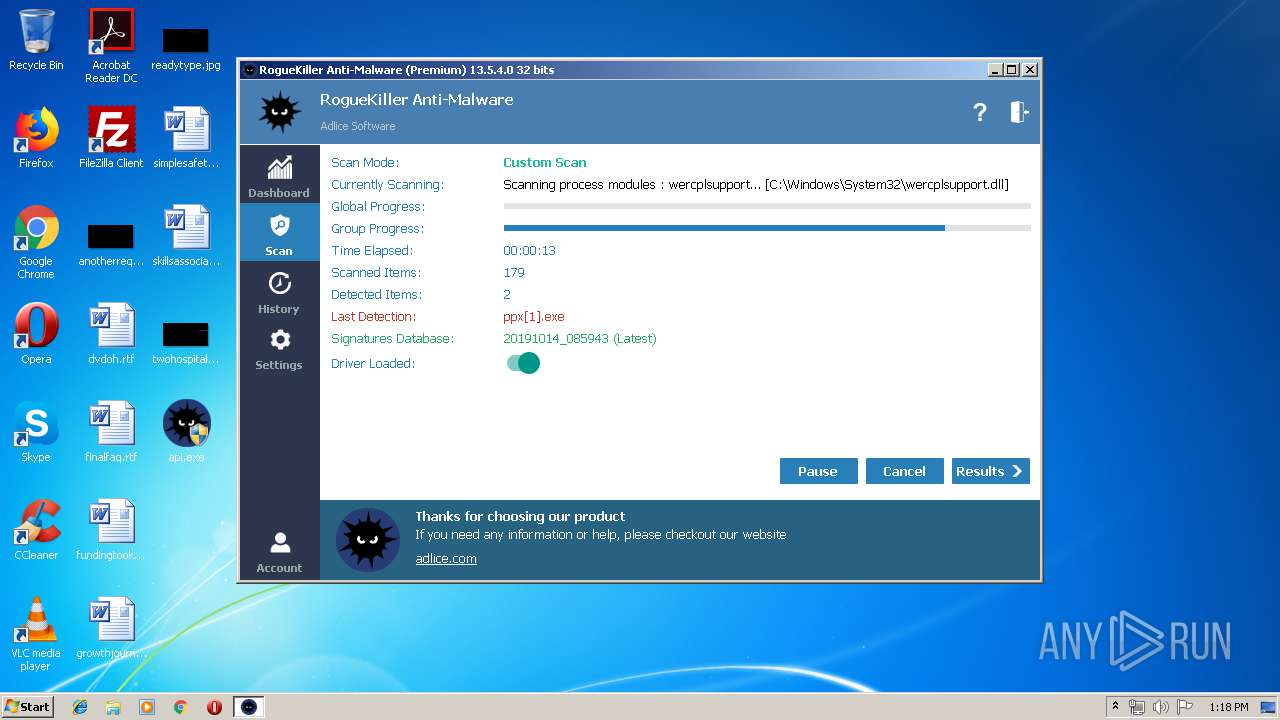
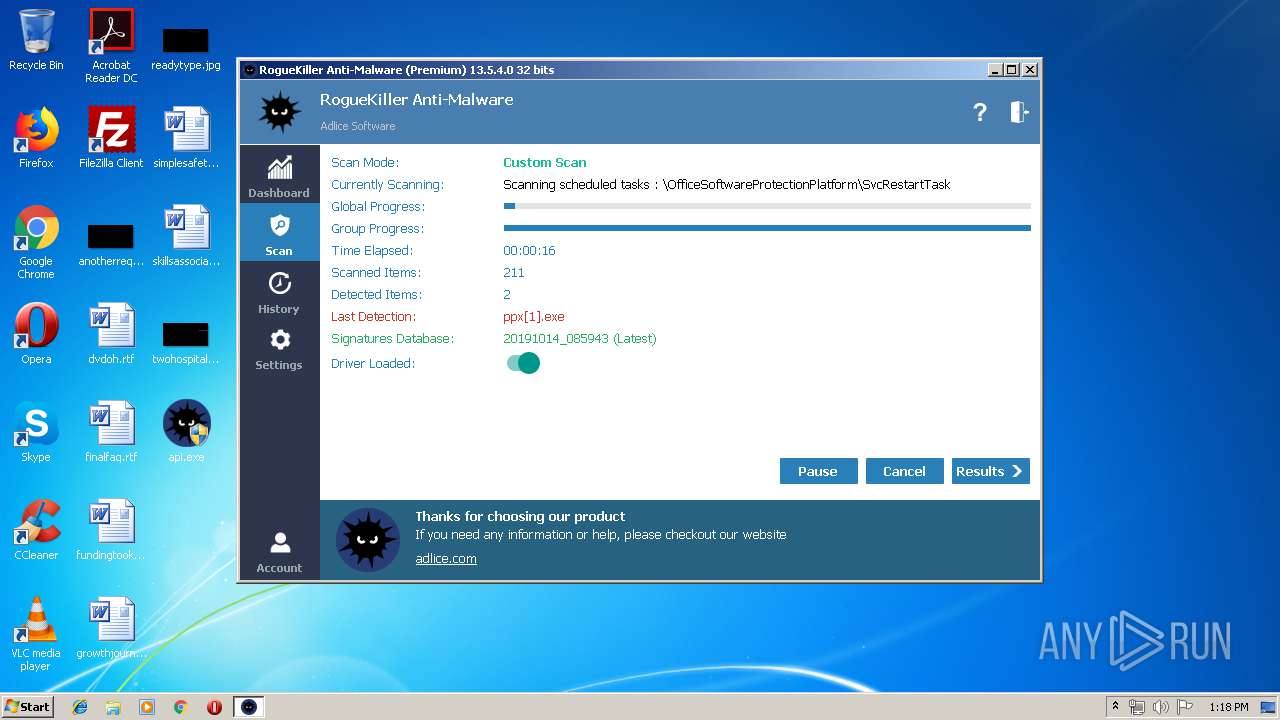
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | October 14, 2019, 12:14:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C348621CA796B09FB51FBAF6DDD9DA9B |
| SHA1: | 7B1AC92B87901AACE2C067DC9792140D618B795B |
| SHA256: | 50DB34CD43FF22F4F804F73FC890F5B4B709D526DEE6100BAA8ACC9CF281D3FF |
| SSDEEP: | 393216:Vb34D51pmVV+oGRy7yiRDapcXObcwH+yGGJsv6tWKFdu9CYQUearRAVuHw/P/:Vz+1poV+oGR2PXObXKAVuu3 |
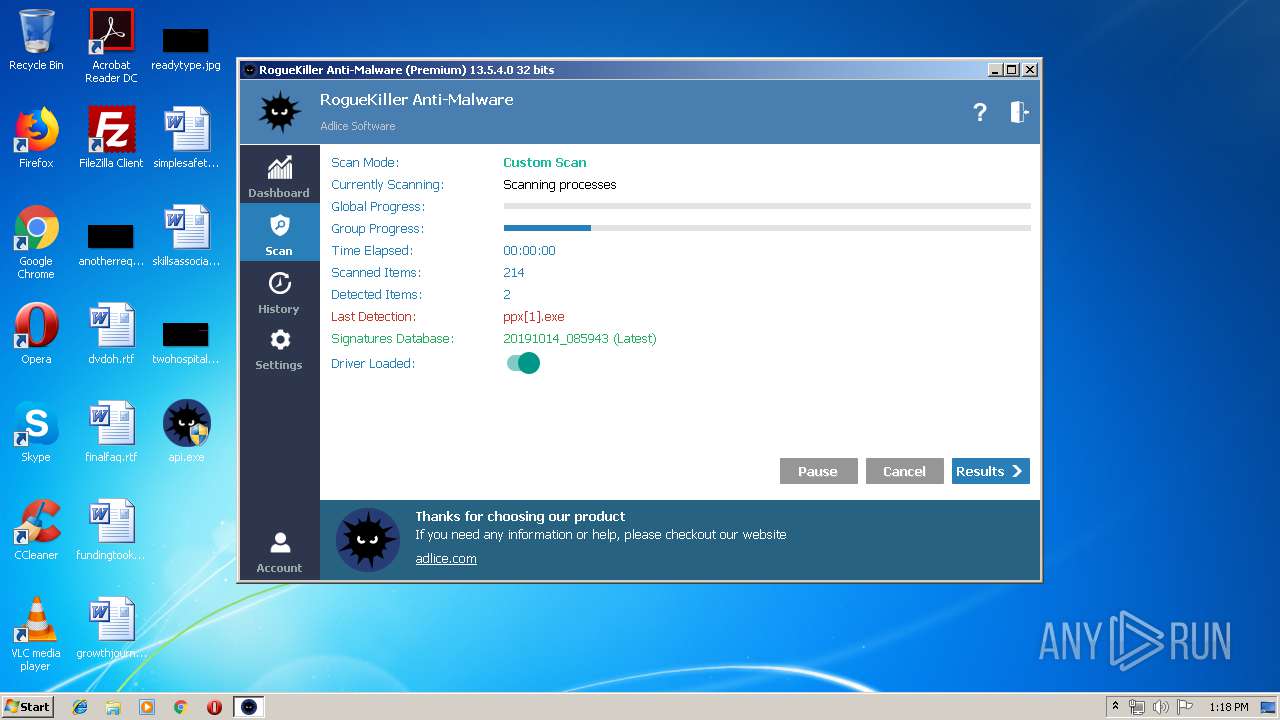
MALICIOUS
Loads the Task Scheduler DLL interface
- api.exe (PID: 1944)
Loads the Task Scheduler COM API
- api.exe (PID: 1944)
Changes settings of System certificates
- MSBuild.exe (PID: 1160)
Stealing of credential data
- MSBuild.exe (PID: 1160)
- NETSTAT.EXE (PID: 3824)
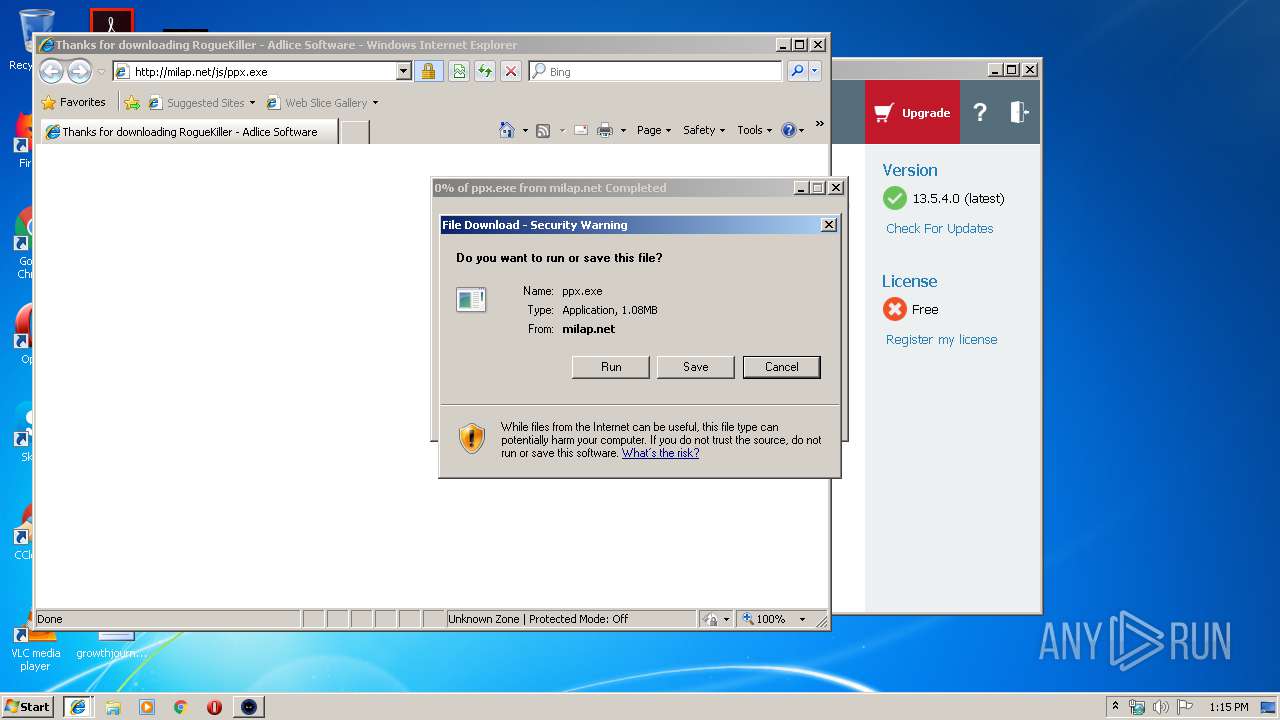
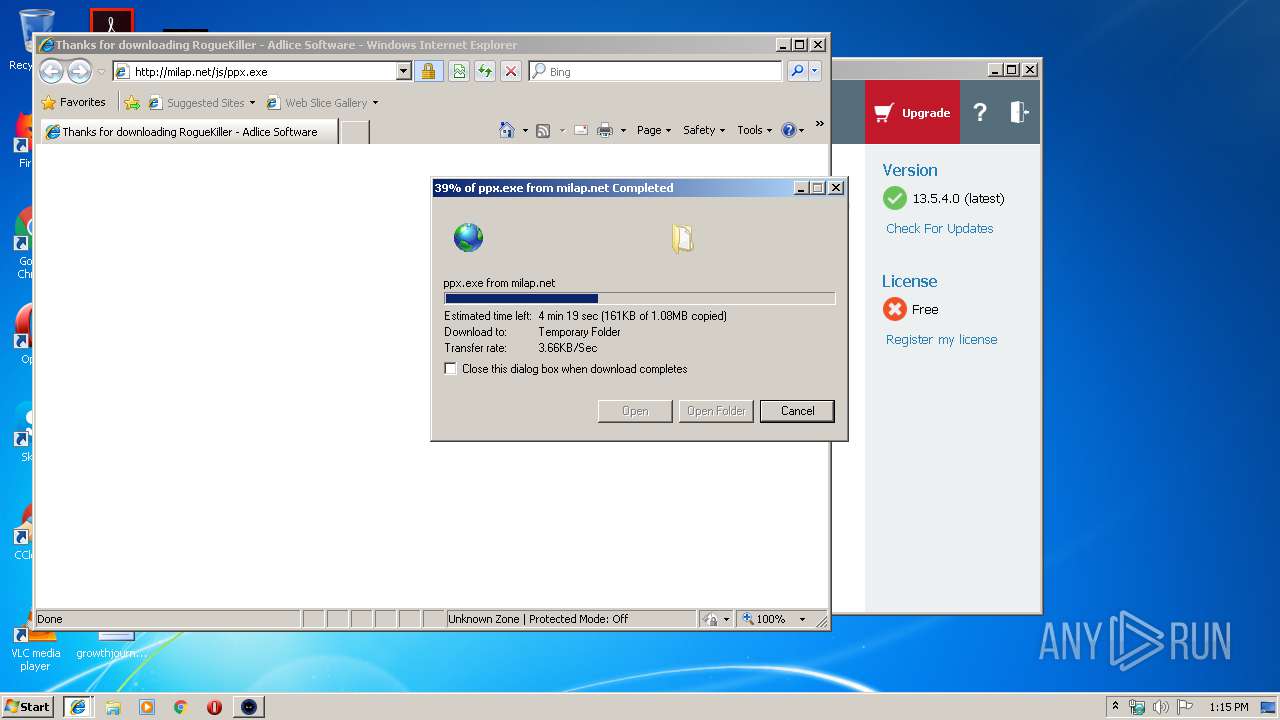
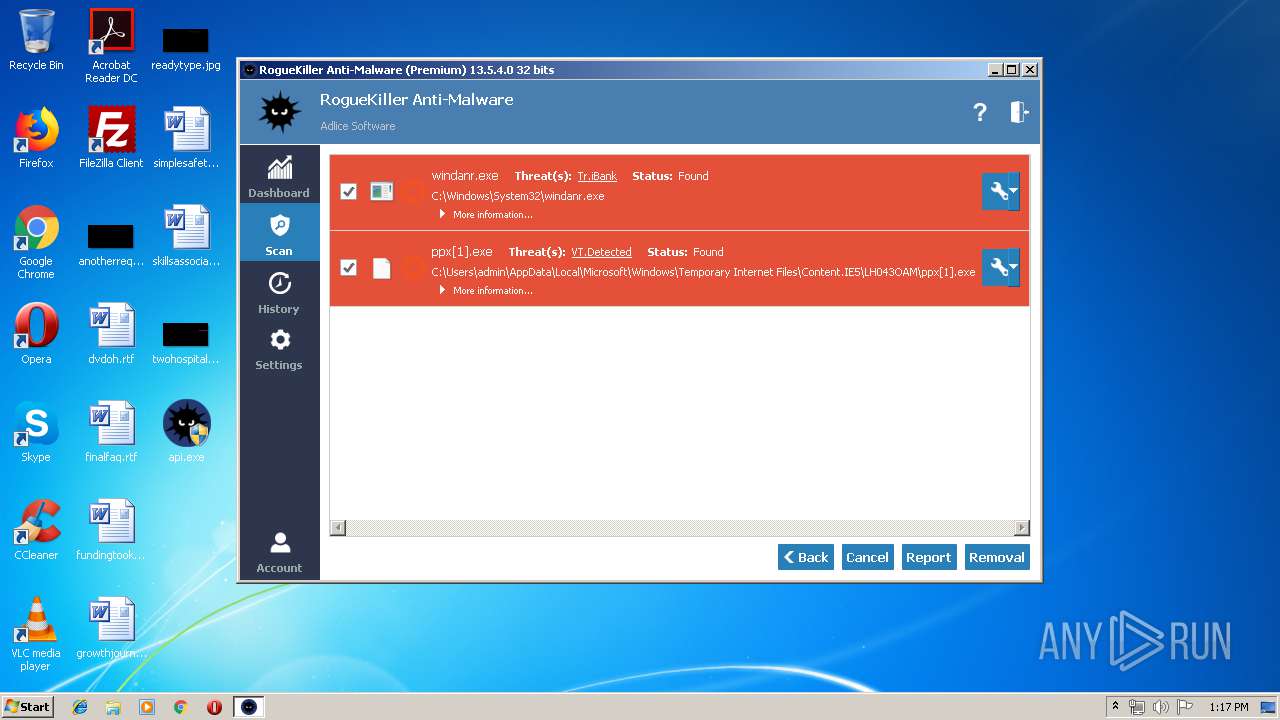
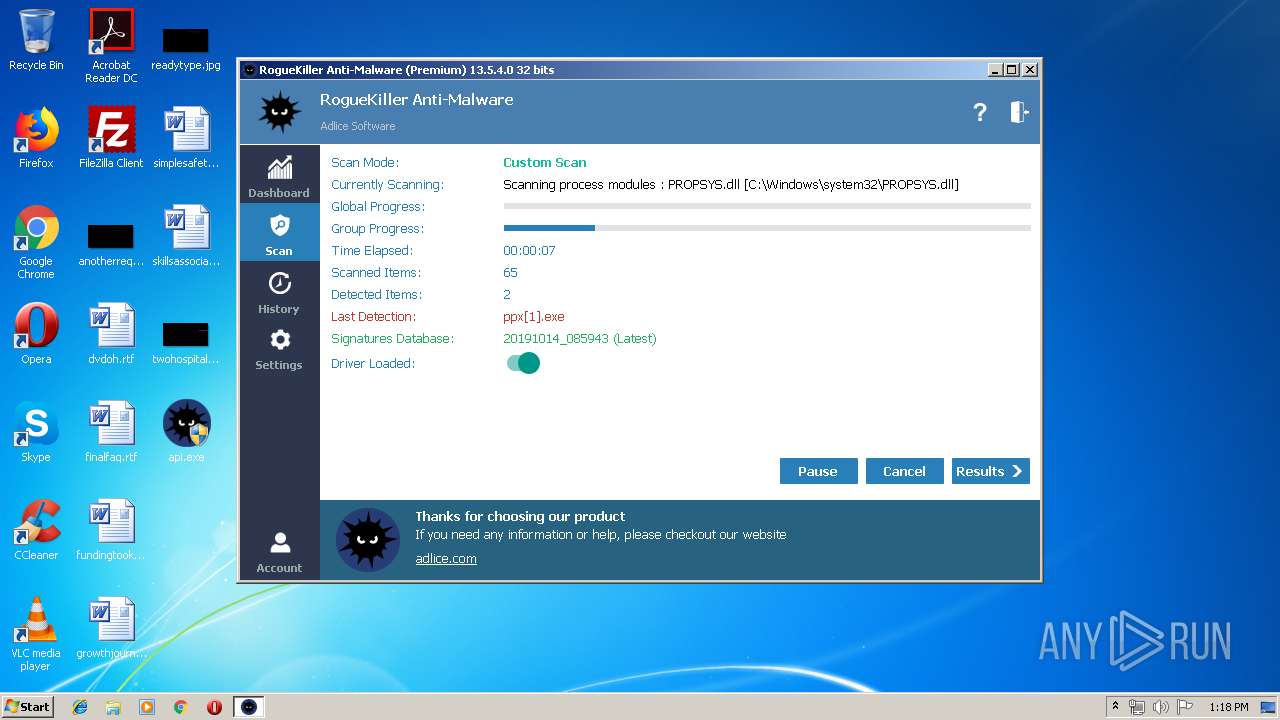
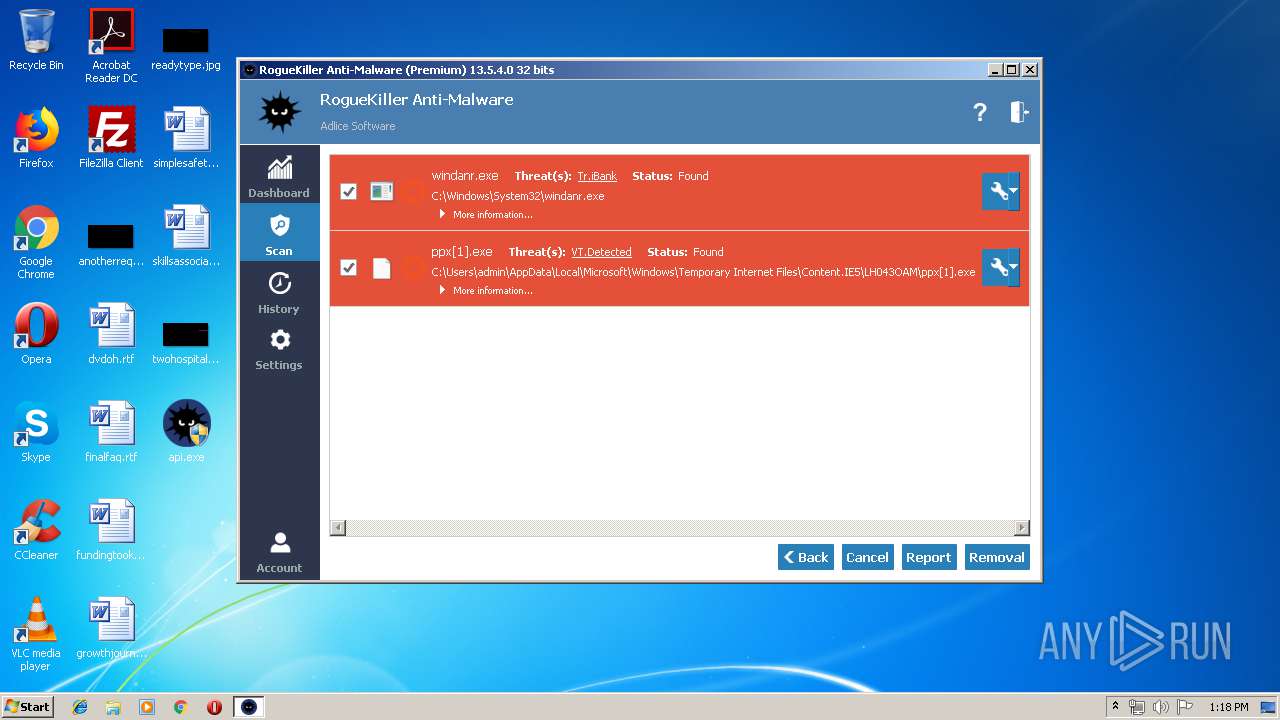
Application was dropped or rewritten from another process
- ppx[1].exe (PID: 2644)
- ssdrs[1].exe (PID: 3624)
- odo[1].exe (PID: 2064)
- odo[1].exe (PID: 2532)
- ssdrs[1].exe (PID: 3068)
- 2drlgx4ad6t.exe (PID: 2084)
- 2drlgx4ad6t.exe (PID: 3656)
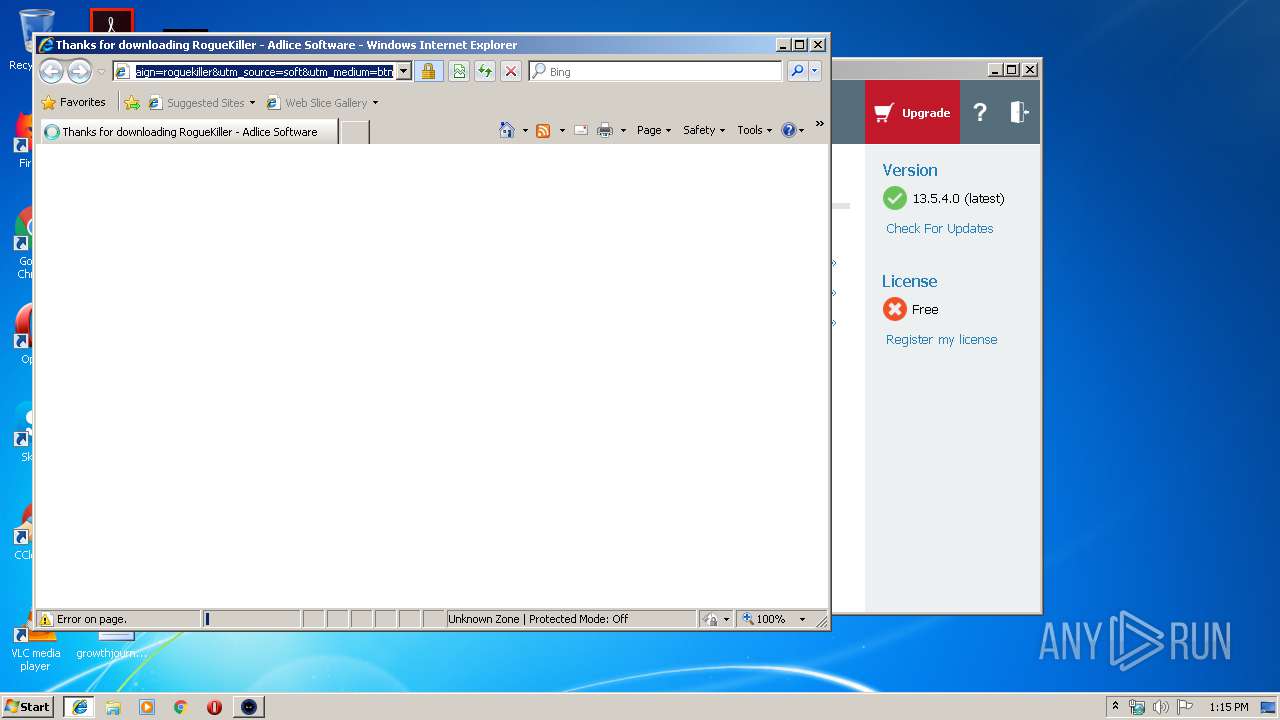
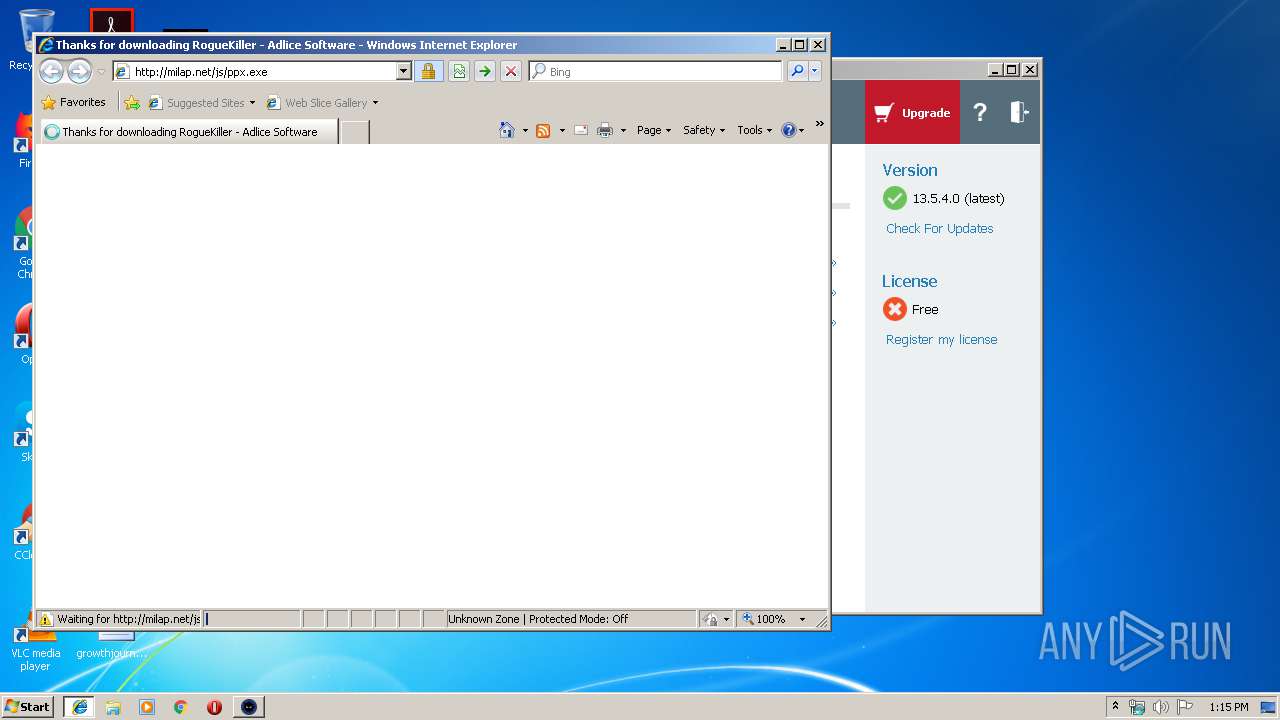
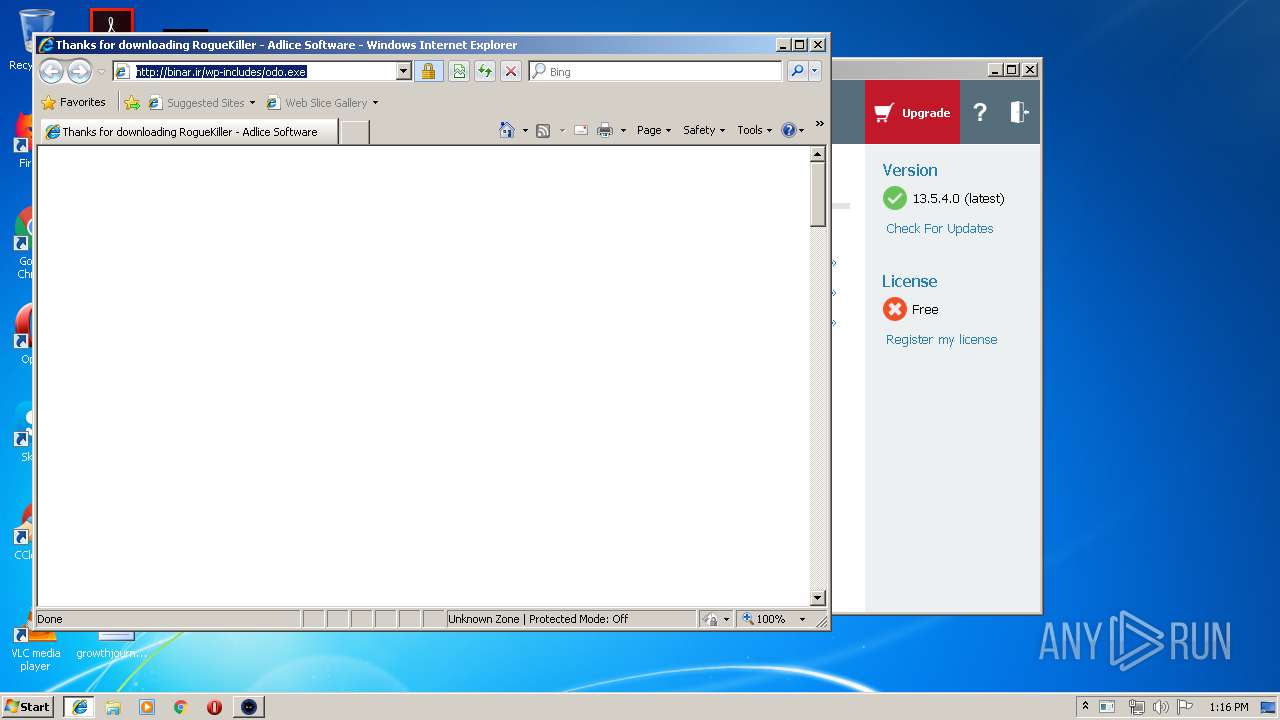
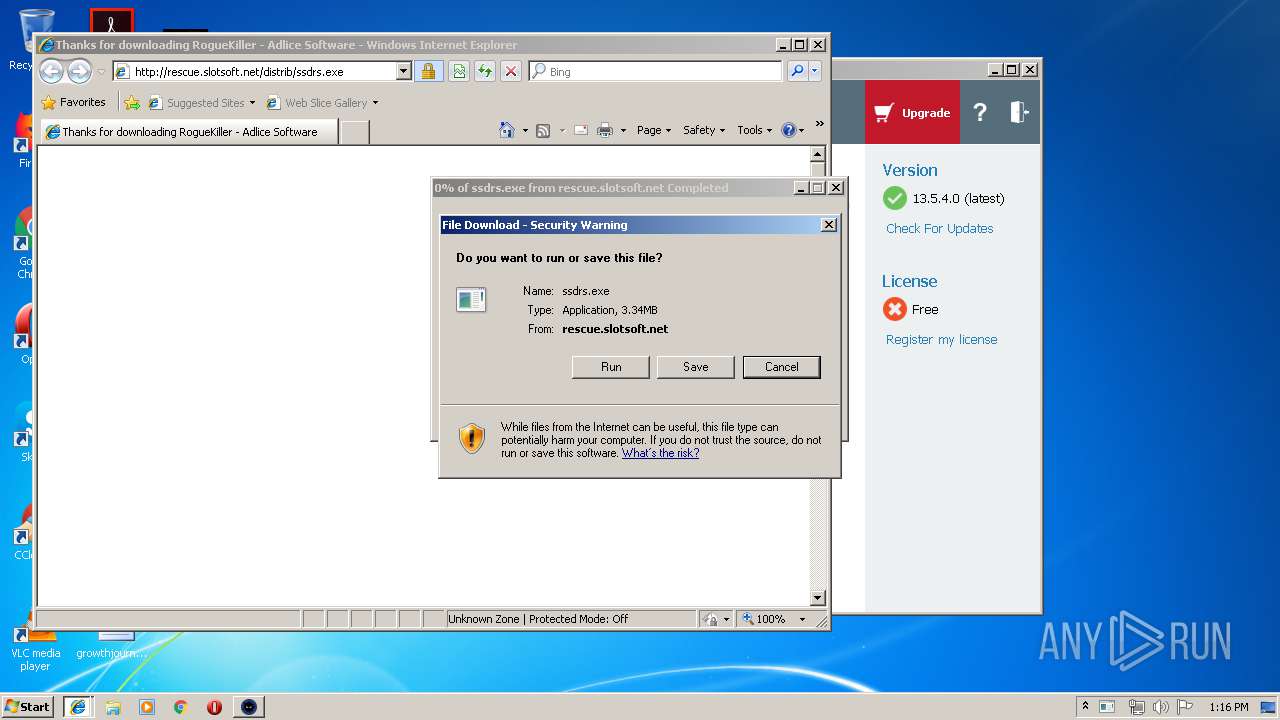
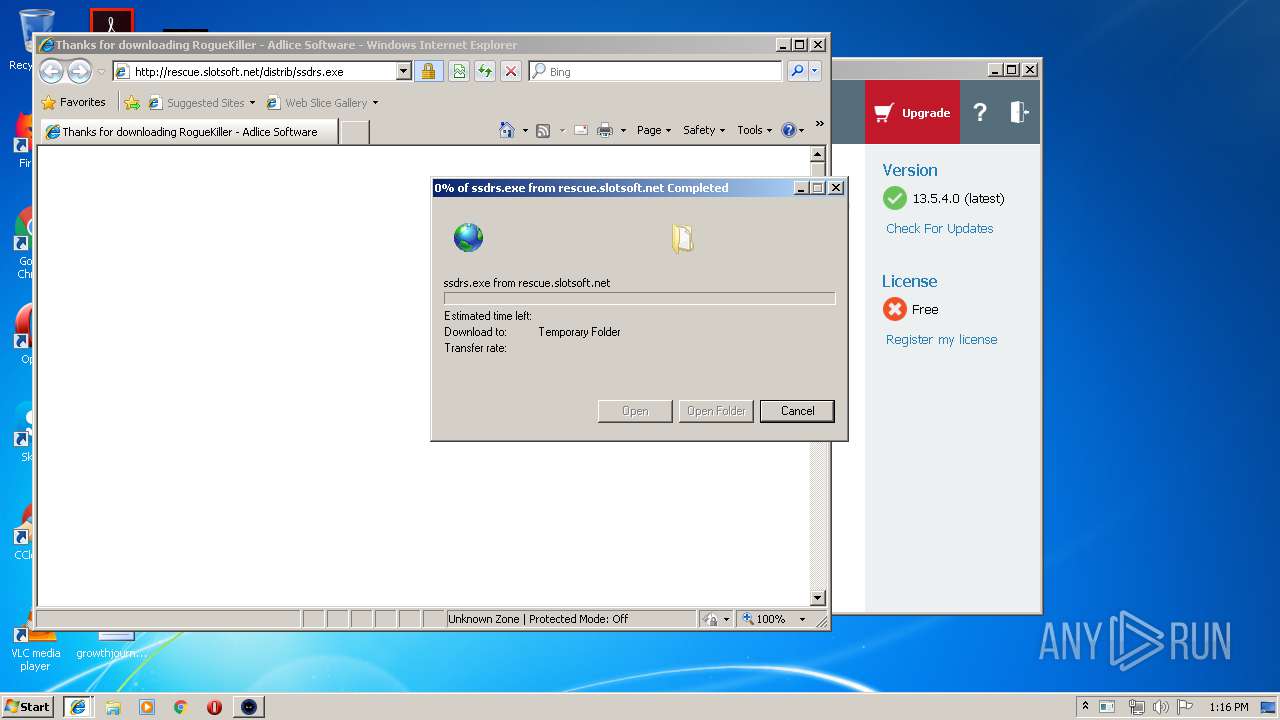
Downloads executable files from the Internet
- iexplore.exe (PID: 2720)
Connects to CnC server
- explorer.exe (PID: 352)
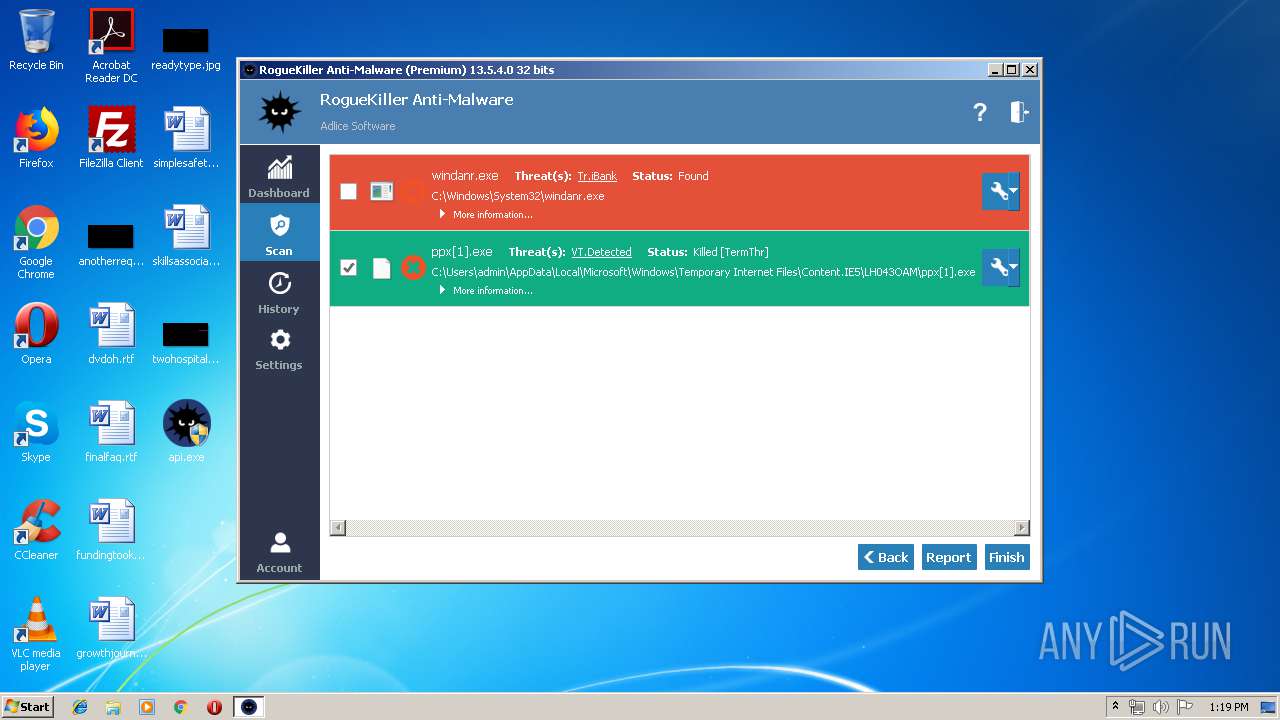
FORMBOOK was detected
- explorer.exe (PID: 352)
- NETSTAT.EXE (PID: 3824)
- Firefox.exe (PID: 2932)
Changes the autorun value in the registry
- NETSTAT.EXE (PID: 3824)
Actions looks like stealing of personal data
- NETSTAT.EXE (PID: 3824)
SUSPICIOUS
Creates files in the program directory
- api.exe (PID: 1944)
- DllHost.exe (PID: 1608)
Low-level read access rights to disk partition
- api.exe (PID: 1944)
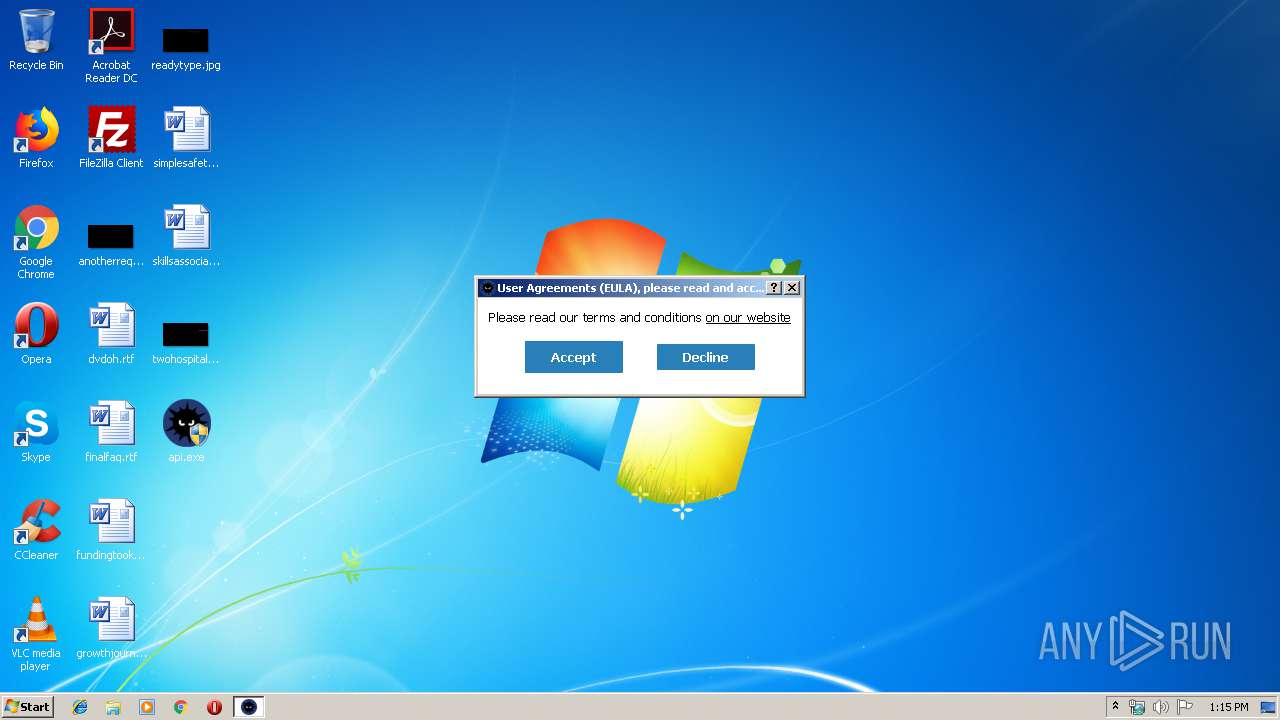
Starts Internet Explorer
- api.exe (PID: 1944)
Reads Internet Cache Settings
- explorer.exe (PID: 352)
Checks for external IP
- MSBuild.exe (PID: 1160)
Adds / modifies Windows certificates
- MSBuild.exe (PID: 1160)
Connects to SMTP port
- MSBuild.exe (PID: 1160)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2720)
- api.exe (PID: 1944)
- explorer.exe (PID: 352)
- DllHost.exe (PID: 1608)
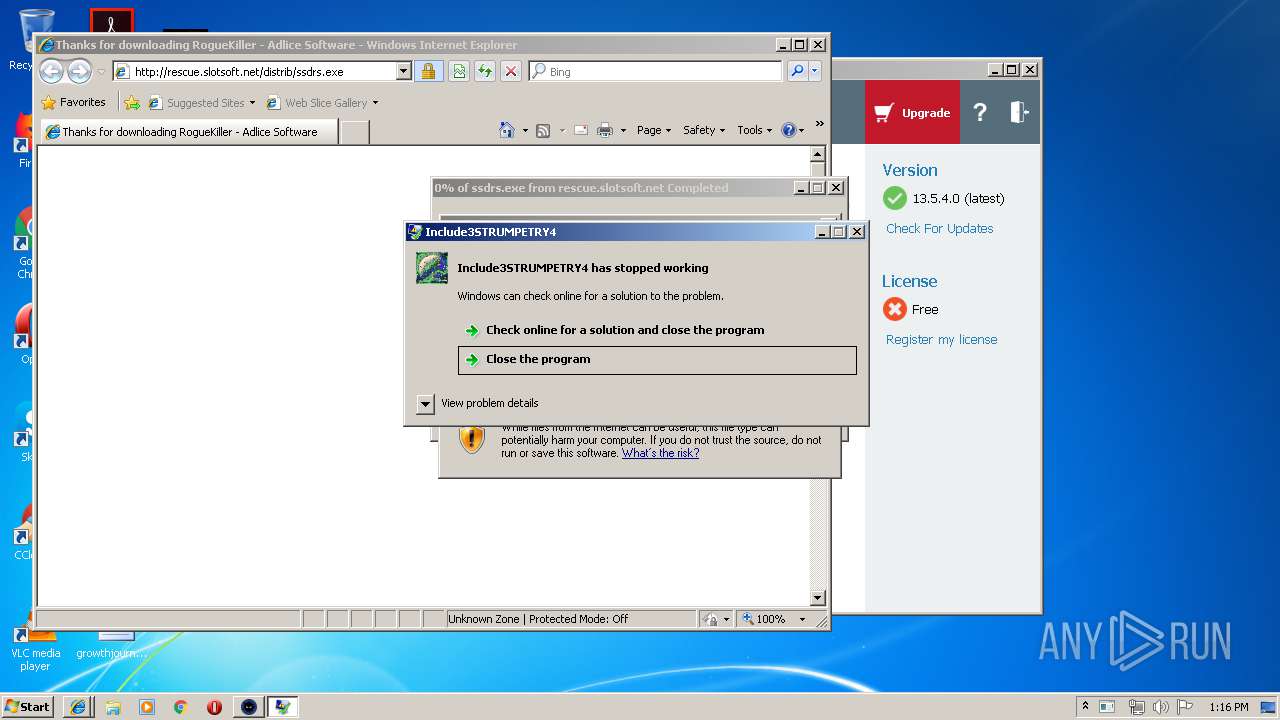
Application launched itself
- odo[1].exe (PID: 2532)
- 2drlgx4ad6t.exe (PID: 3656)
Starts CMD.EXE for commands execution
- NETSTAT.EXE (PID: 3824)
Uses NETSTAT.EXE to discover network connections
- explorer.exe (PID: 352)
Loads DLL from Mozilla Firefox
- NETSTAT.EXE (PID: 3824)
Creates files in the user directory
- NETSTAT.EXE (PID: 3824)
Creates files in the Windows directory
- api.exe (PID: 1944)
Creates or modifies windows services
- api.exe (PID: 1944)
Removes files from Windows directory
- api.exe (PID: 1944)
Executed via COM
- DllHost.exe (PID: 1608)
Creates files in the driver directory
- api.exe (PID: 1944)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2092)
Creates files in the user directory
- iexplore.exe (PID: 2720)
- iexplore.exe (PID: 2092)
- Firefox.exe (PID: 2932)
Reads settings of System Certificates
- MSBuild.exe (PID: 1160)
Application launched itself
- iexplore.exe (PID: 2092)
Reads Internet Cache Settings
- iexplore.exe (PID: 2720)
Reads internet explorer settings
- iexplore.exe (PID: 2720)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2720)
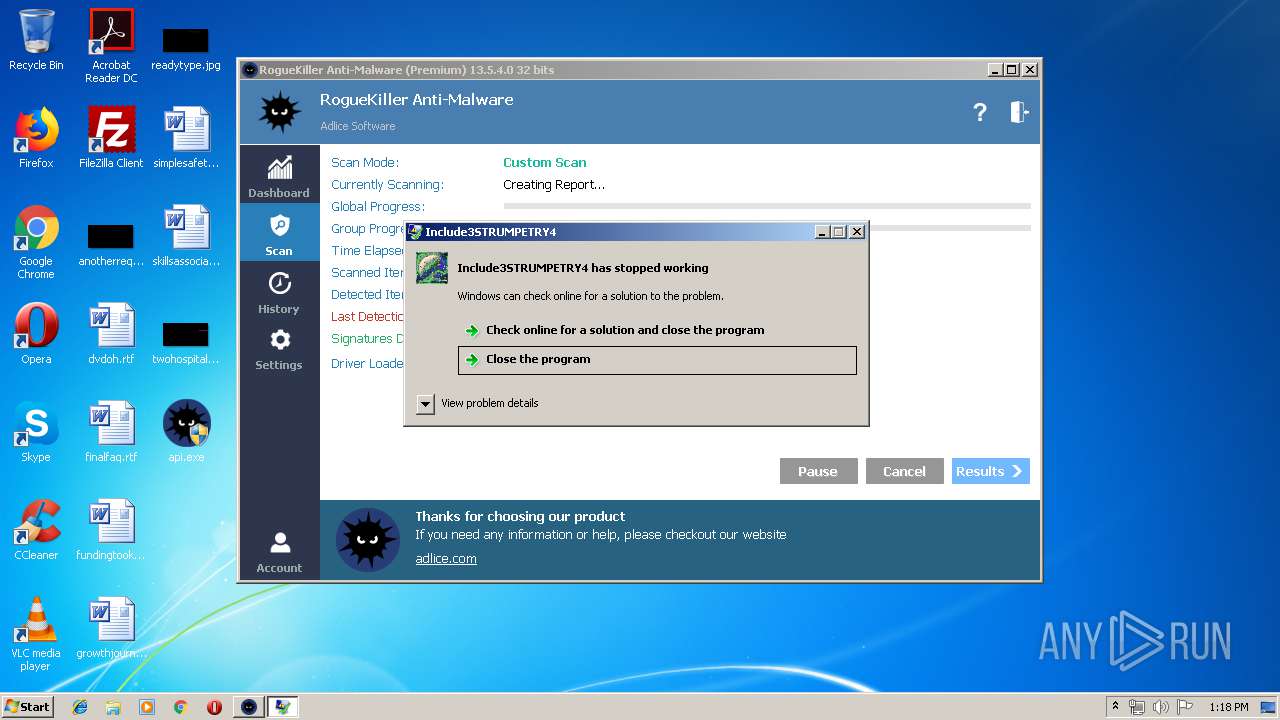
Application was crashed
- odo[1].exe (PID: 2532)
- 2drlgx4ad6t.exe (PID: 3656)
Manual execution by user
- NETSTAT.EXE (PID: 3824)
Reads the hosts file
- NETSTAT.EXE (PID: 3824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:14 12:05:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 16879104 |
| InitializedDataSize: | 11647488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd59514 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
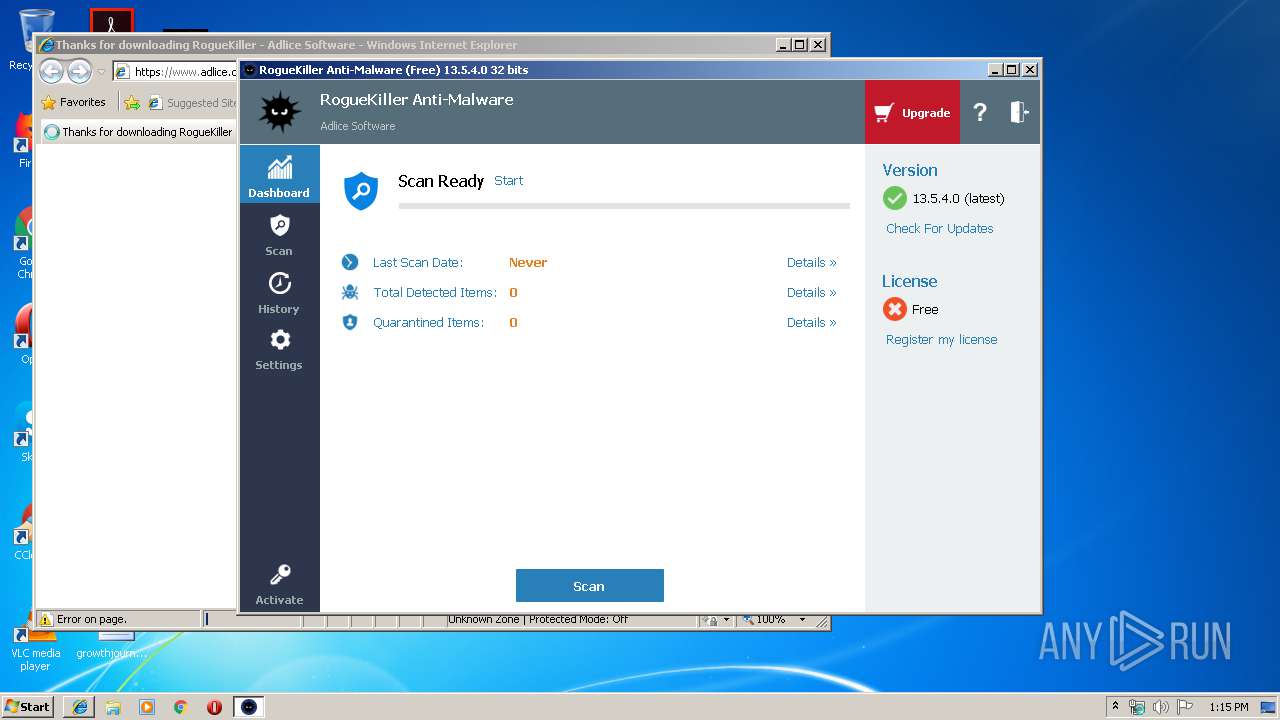
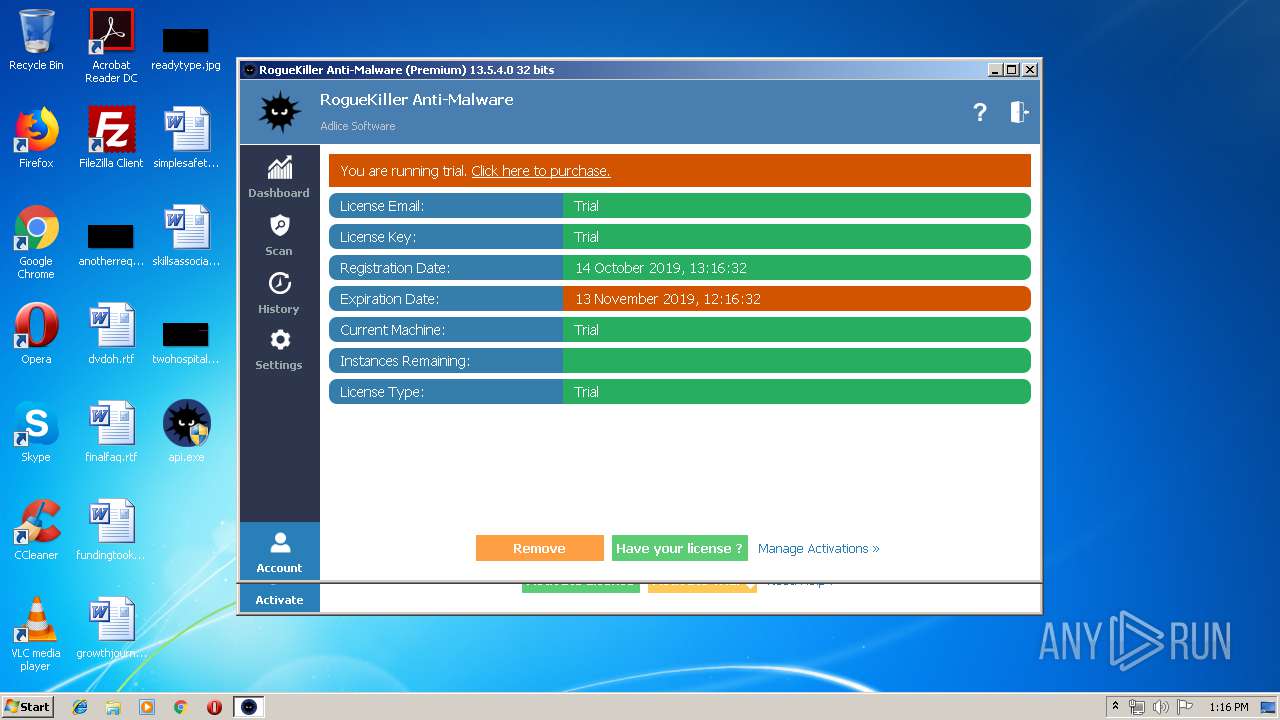
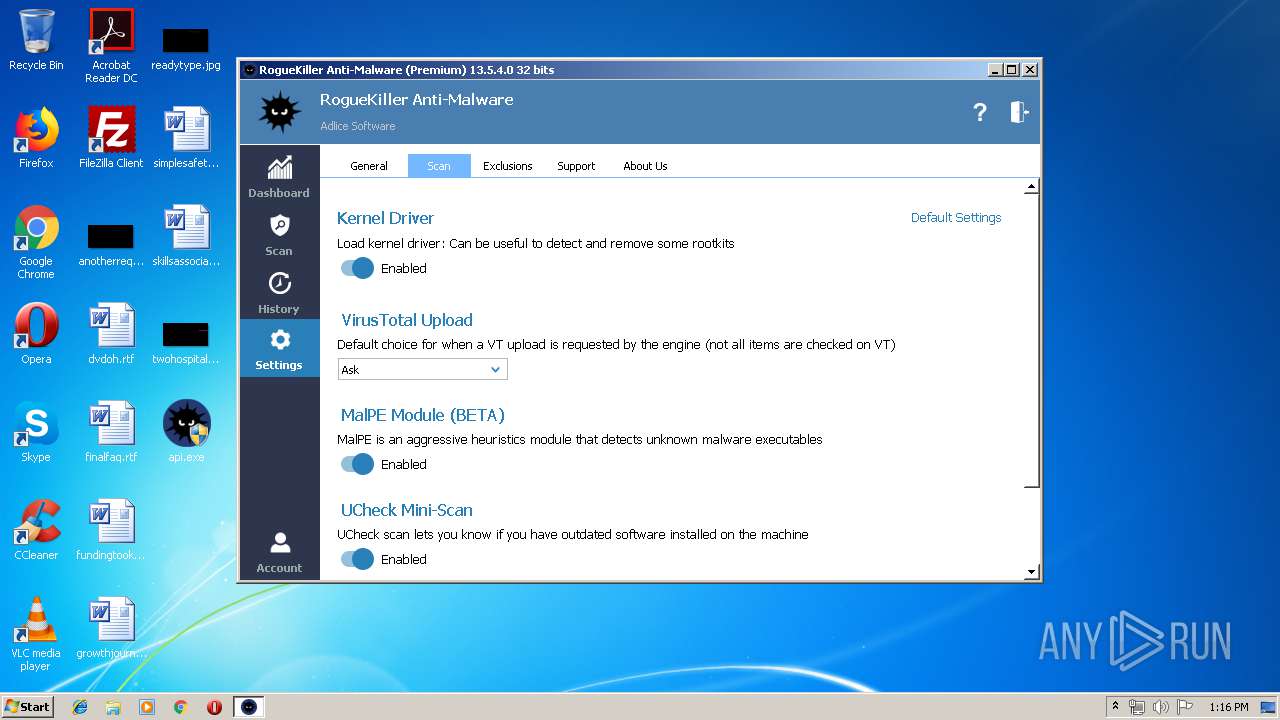
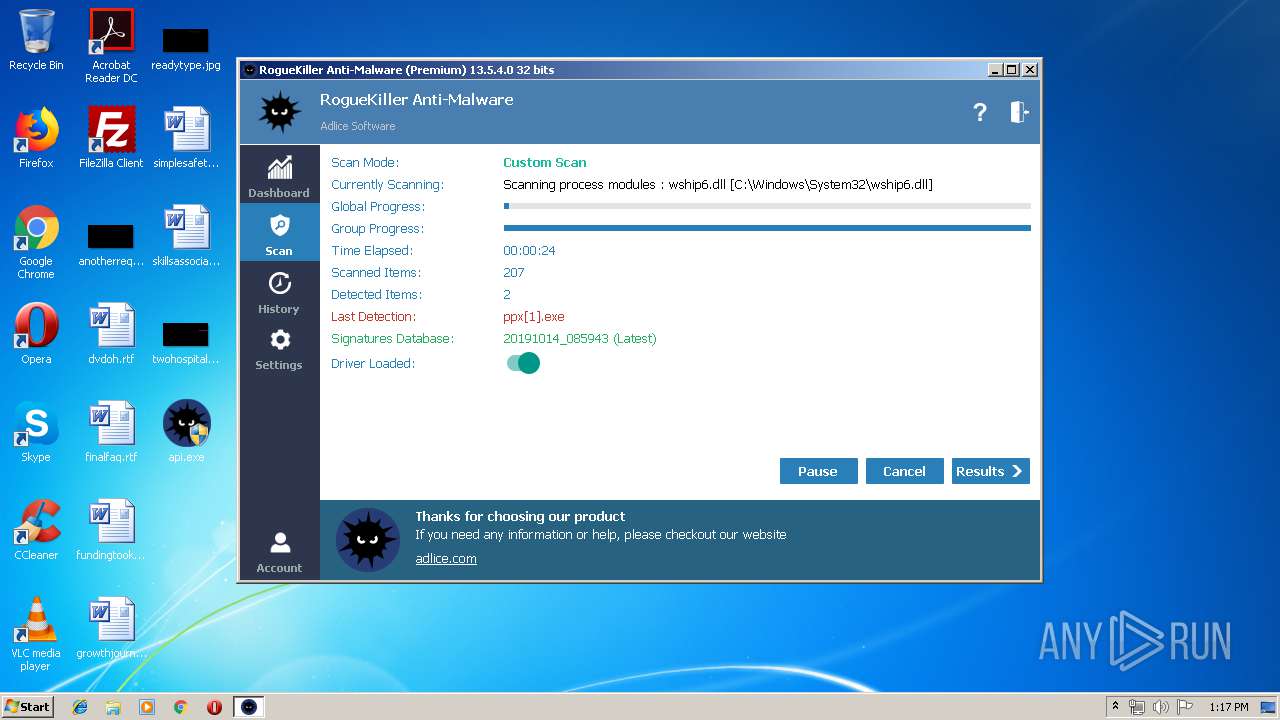
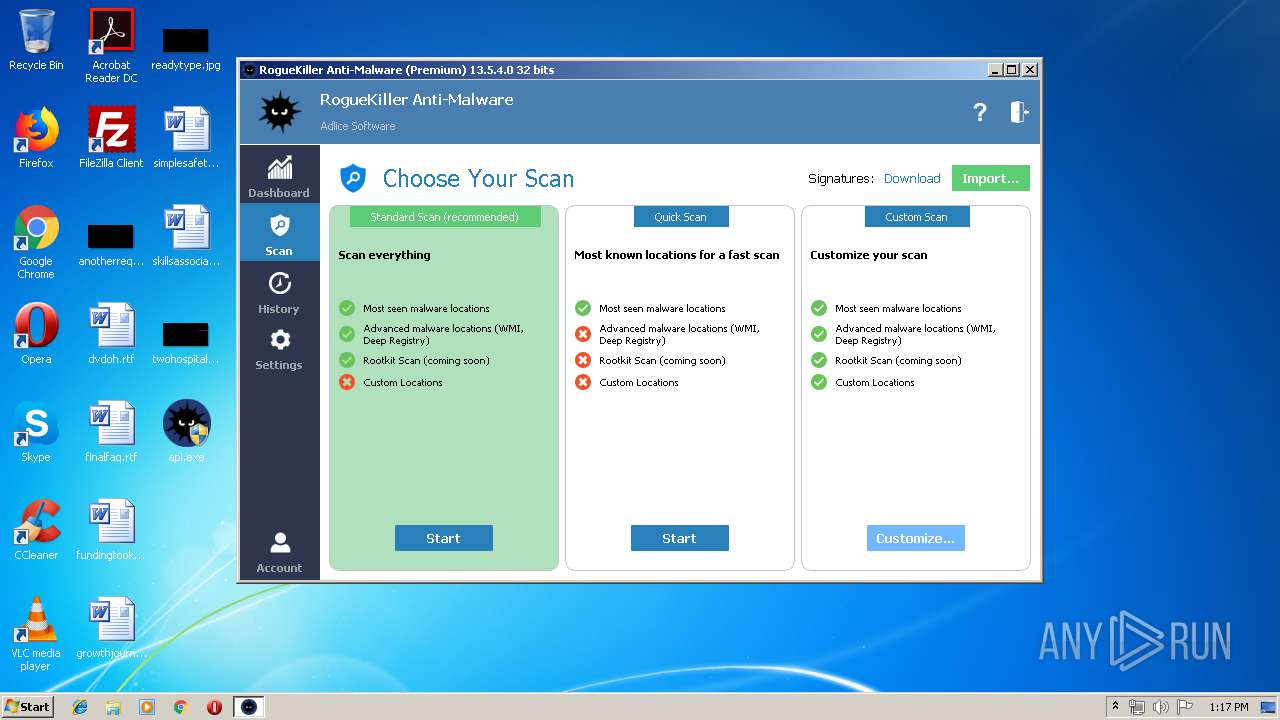
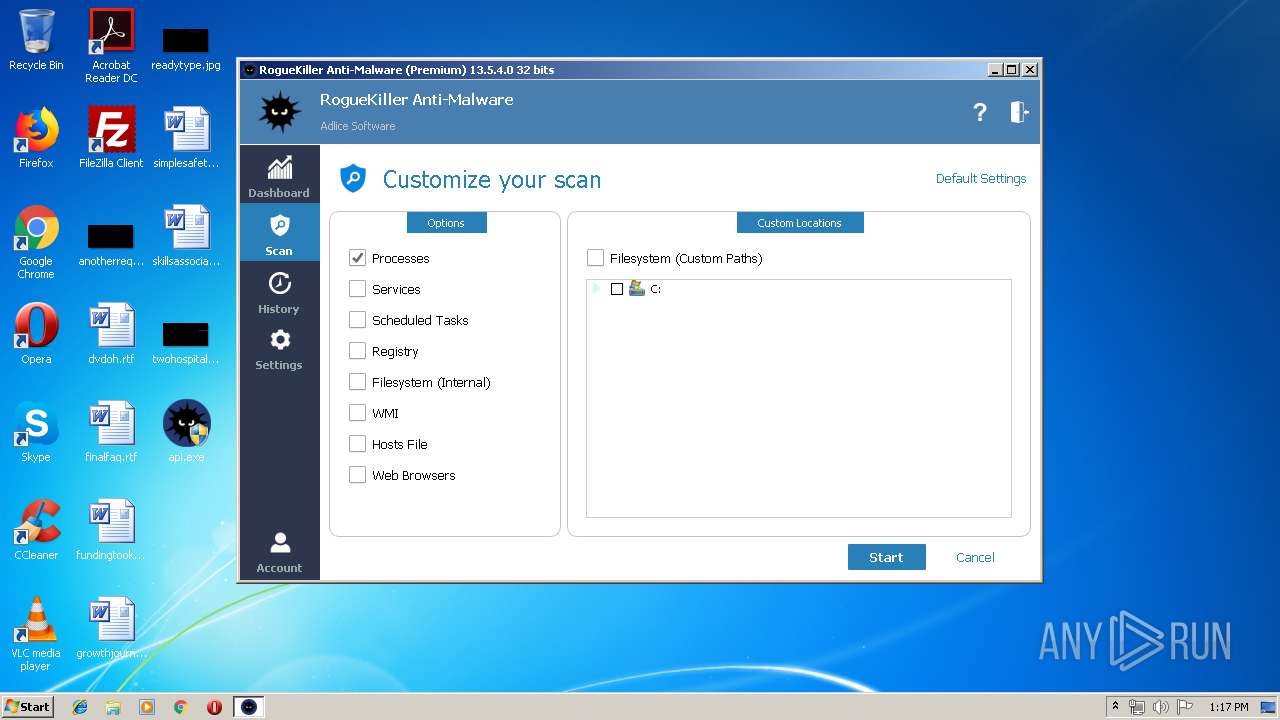
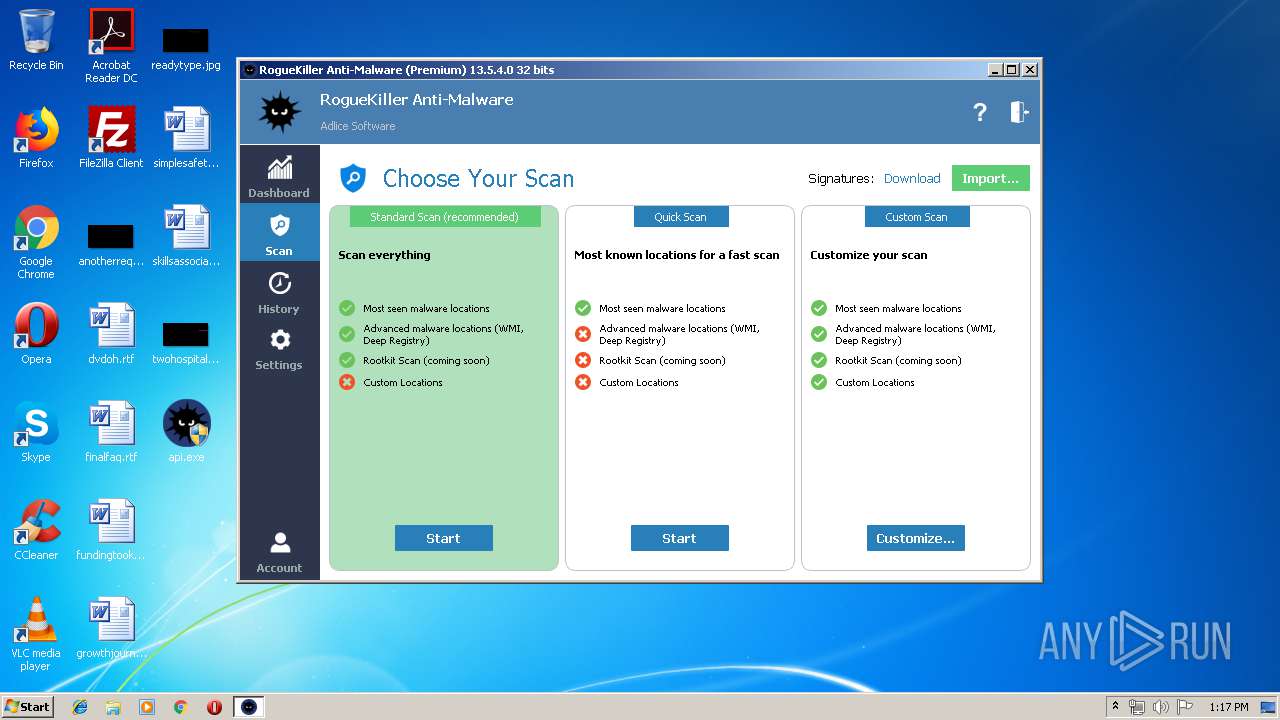
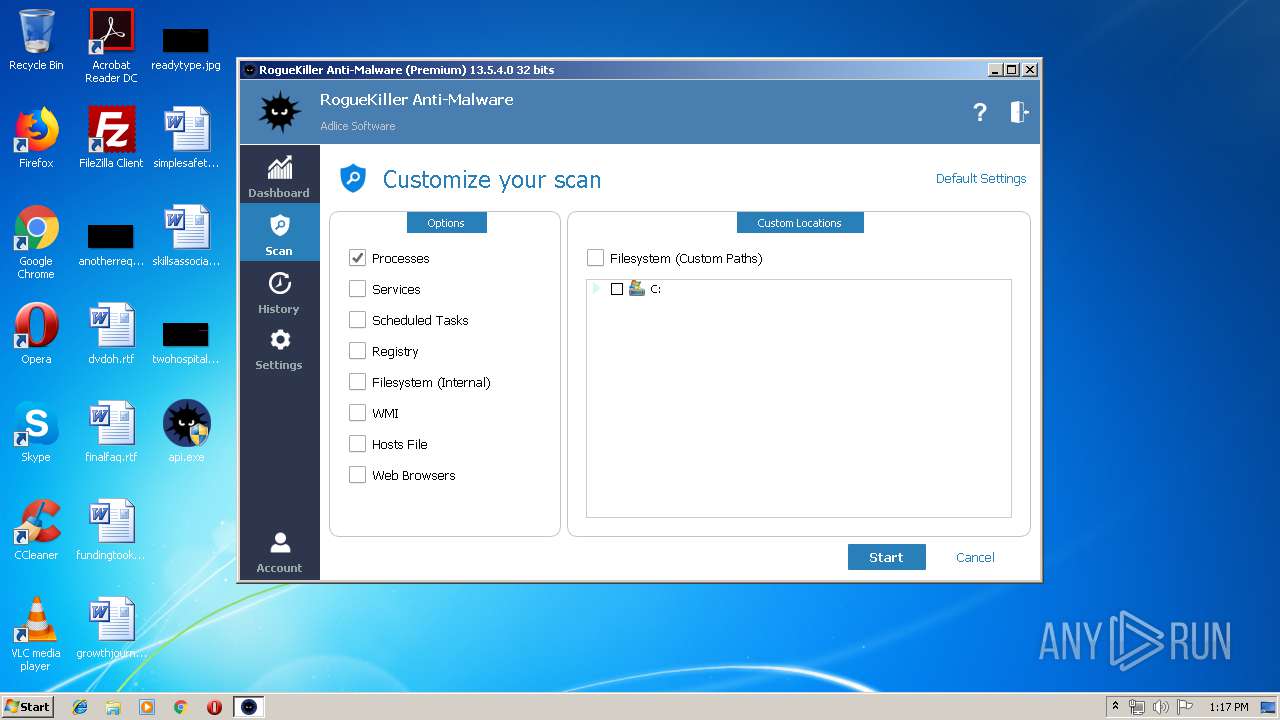
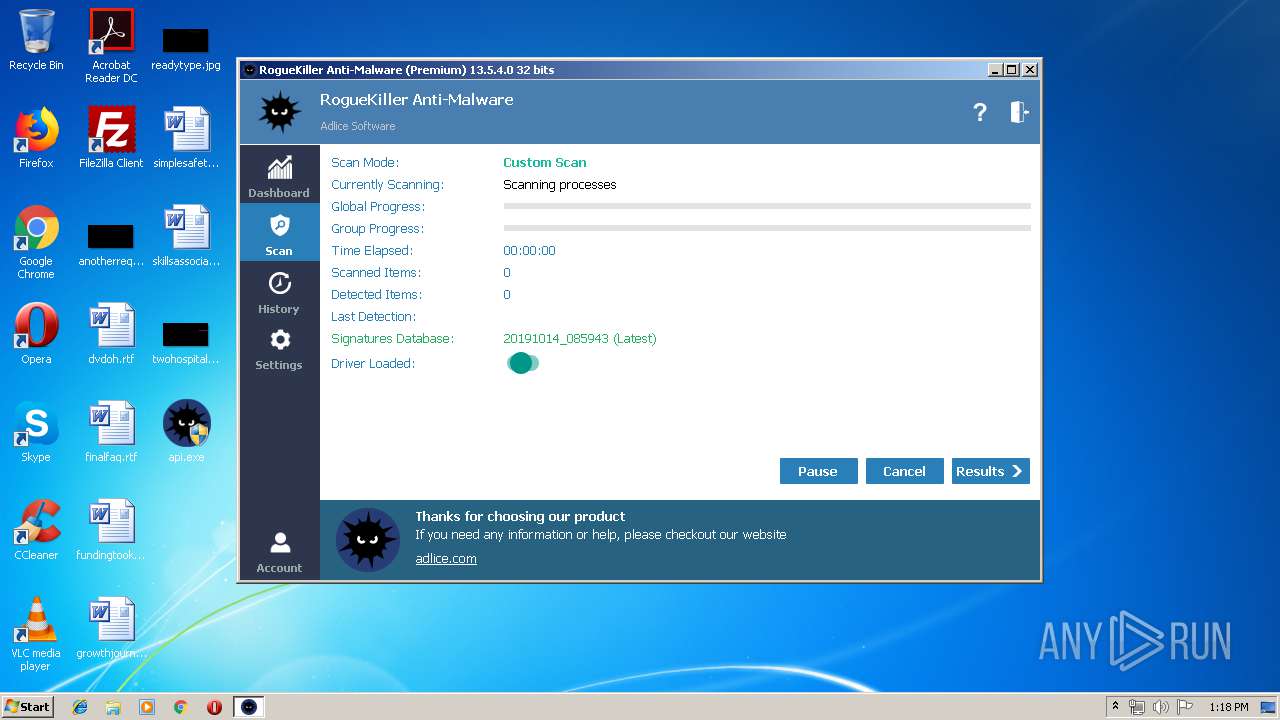
| FileVersionNumber: | 13.5.4.0 |
| ProductVersionNumber: | 13.5.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
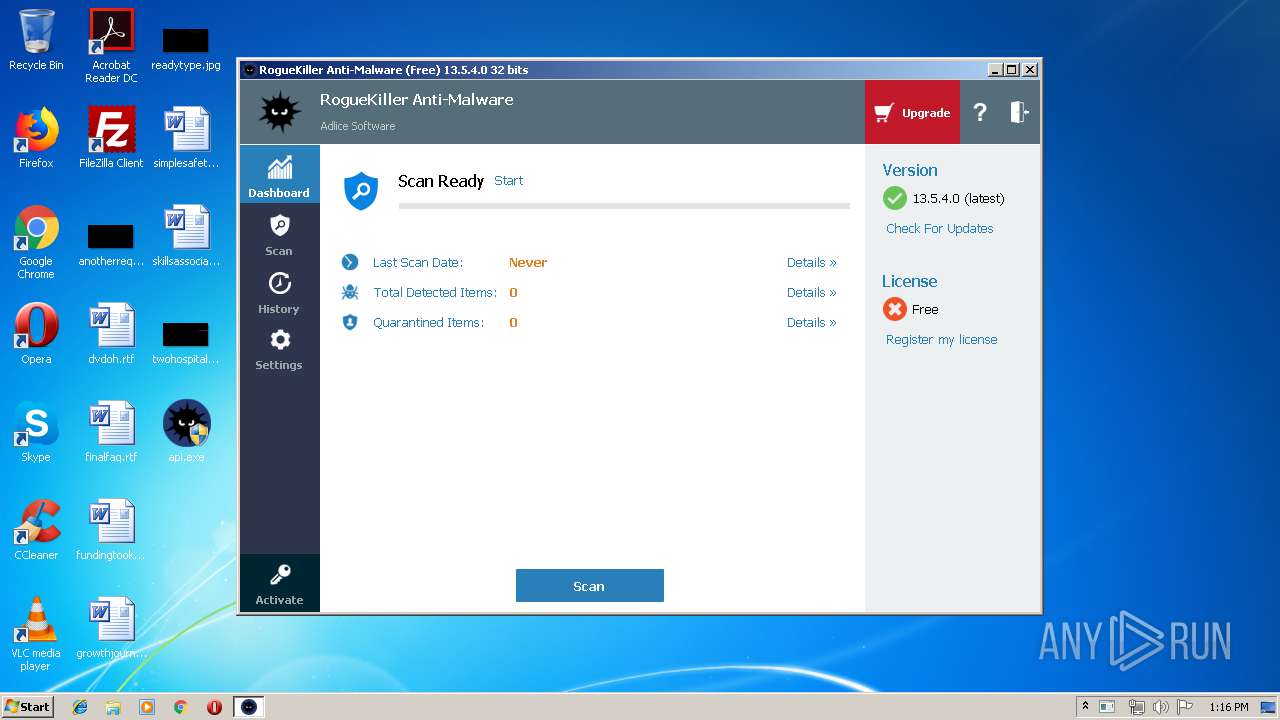
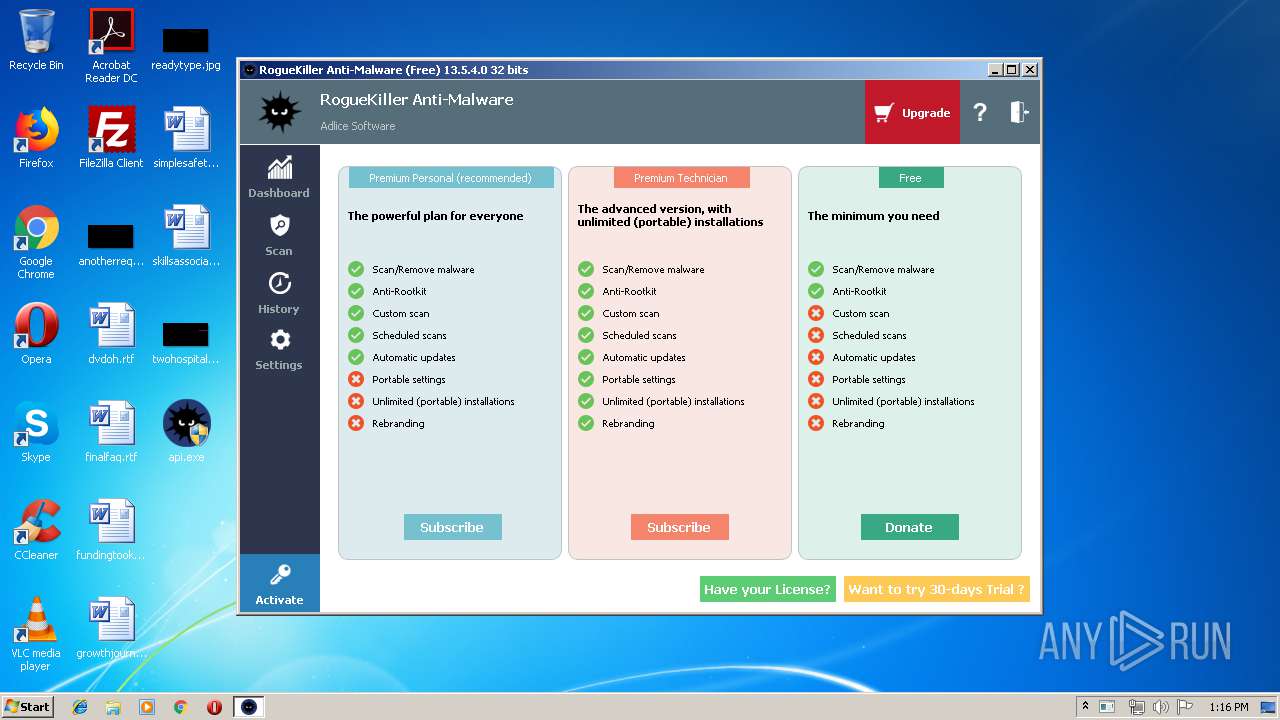
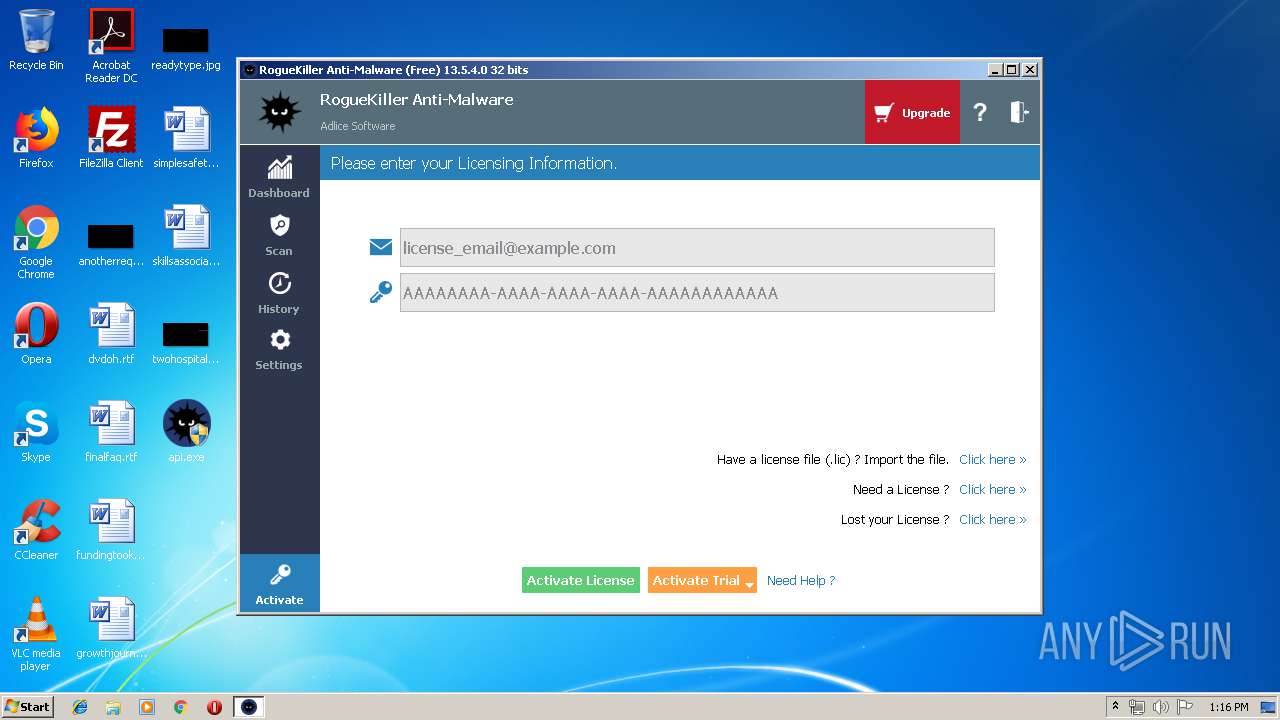
| CompanyName: | Adlice Software |
| FileDescription: | Anti-Malware Scan and Removal |
| FileVersion: | 13.5.4.0 |
| InternalName: | RogueKiller Anti-Malware |
| LegalCopyright: | Copyright Adlice Software(C) 2019 |
| LegalTrademarks1: | Adlice Software |
| LegalTrademarks2: | Adlice Software |
| OriginalFileName: | RogueKiller Anti-Malware |
| ProductName: | RogueKiller Anti-Malware |
| ProductVersion: | 13.5.4.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Oct-2019 10:05:43 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Adlice Software |
| FileDescription: | Anti-Malware Scan and Removal |
| FileVersion: | 13.5.4.0 |
| InternalName: | RogueKiller Anti-Malware |
| LegalCopyright: | Copyright Adlice Software(C) 2019 |
| LegalTrademarks1: | Adlice Software |
| LegalTrademarks2: | Adlice Software |
| OriginalFilename: | RogueKiller Anti-Malware |
| ProductName: | RogueKiller Anti-Malware |
| ProductVersion: | 13.5.4.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000160 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 14-Oct-2019 10:05:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x01018C40 | 0x01018E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60269 |
.rdata | 0x0101A000 | 0x004E6BB4 | 0x004E6C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.35077 |
.data | 0x01501000 | 0x00052440 | 0x00031400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.89602 |
.tls | 0x01554000 | 0x0000000D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.qtmetadL\x02 | 0x01555000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.15593 |
.gfids | 0x01556000 | 0x00000770 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.97983 |
_RDATA | 0x01557000 | 0x00000124 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.51793 |
.rsrc | 0x01558000 | 0x00533D50 | 0x00533E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.88516 |
.reloc | 0x01A8C000 | 0x000AD8A0 | 0x000ADA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64635 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21878 | 667 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.08492 | 296 | UNKNOWN | English - United States | RT_ICON |
3 | 4.32673 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.69 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.96085 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 7.96471 | 21897 | UNKNOWN | English - United States | RT_ICON |
7 | 3.53747 | 16936 | UNKNOWN | English - United States | RT_ICON |
8 | 3.87766 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 4.07378 | 6760 | UNKNOWN | English - United States | RT_ICON |
10 | 4.36584 | 4264 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
OPENGL32.dll |
PSAPI.DLL |
Total processes
65
Monitored processes
18
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1160 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v4.0.30319\\\\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | ppx[1].exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 1608 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1944 | "C:\Users\admin\Desktop\api.exe" | C:\Users\admin\Desktop\api.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\odo[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\odo[1].exe | — | odo[1].exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.09.0003 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Espx8rn\2drlgx4ad6t.exe" | C:\Program Files\Espx8rn\2drlgx4ad6t.exe | — | 2drlgx4ad6t.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.09.0003 Modules
| |||||||||||||||
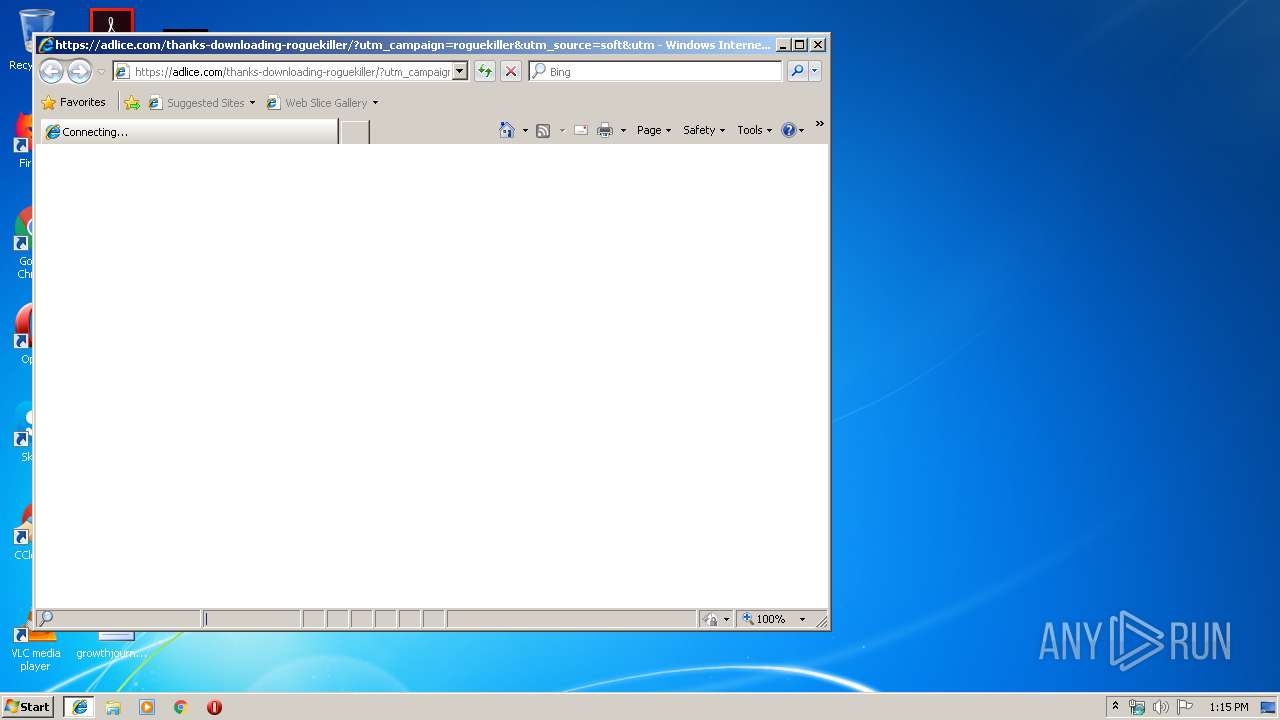
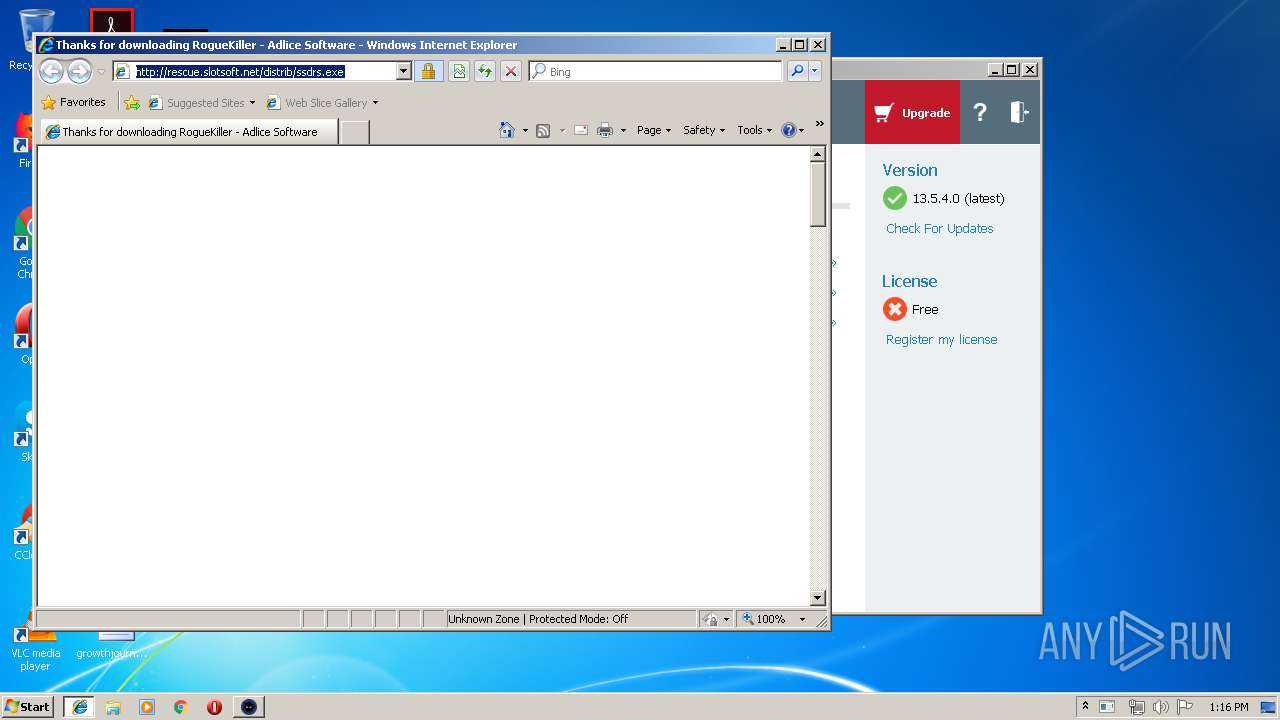
| 2092 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://adlice.com/thanks-downloading-roguekiller/?utm_campaign=roguekiller&utm_source=soft&utm_medium=btn" | C:\Program Files\Internet Explorer\iexplore.exe | api.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | "C:\Windows\System32\help.exe" | C:\Windows\System32\help.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Help Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | "C:\Users\admin\Desktop\api.exe" | C:\Users\admin\Desktop\api.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 | |||||||||||||||
| 2472 | /c del "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\odo[1].exe" | C:\Windows\System32\cmd.exe | — | NETSTAT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 958
Read events
1 740
Write events
216
Delete events
2
Modification events
| (PID) Process: | (1944) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1944) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1944) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1944) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1944) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1944) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1944) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1944) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1944) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1944) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
7
Suspicious files
109
Text files
106
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\thanks-downloading-roguekiller[1].txt | — | |
MD5:— | SHA256:— | |||
| 1944 | api.exe | C:\ProgramData\RogueKiller\Debug\RogueKiller Anti-Malware_debug.log | text | |
MD5:— | SHA256:— | |||
| 1944 | api.exe | C:\ProgramData\RogueKiller\scheduler | text | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\thanks-downloading-roguekiller[1].htm | html | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@www.adlice[1].txt | text | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@adlice[1].txt | text | |
MD5:— | SHA256:— | |||
| 1944 | api.exe | C:\ProgramData\RogueKiller\advert | text | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\wp-review-2c1e1d637abcf6b366bb979cf8727271[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
76
DNS requests
34
Threats
59
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | explorer.exe | GET | — | 199.192.25.235:80 | http://www.moraxy.com/y00/?GX=i4BOXk/Xe46odwxF56aarnhHHL0HSDKheDxJPoPHHOsFUVfohqOXhRE48+RAtyKXnfdhxQ==&uFO4=XPxDeFaPj | US | — | — | malicious |
352 | explorer.exe | GET | — | 23.227.38.64:80 | http://www.simplycitystore.com/y00/?uFO4=XPxDeFaPj&GX=jTnSyqkhbUqkPi81/jAZr150p6mMk6KO2otj7gnsDXCmyot9frb9xkwS95dAD7bHxA0skA== | CA | — | — | malicious |
352 | explorer.exe | GET | — | 157.7.134.248:80 | http://www.fire-wing.net/y00/?GX=SRbXy3vvOTn/nK7ZexqLbZ5dRDT1AxavuiKDFh811MUAWToECvwAM/7mI4pCeWiUrDXdPA==&uFO4=XPxDeFaPj&sql=1 | JP | — | — | malicious |
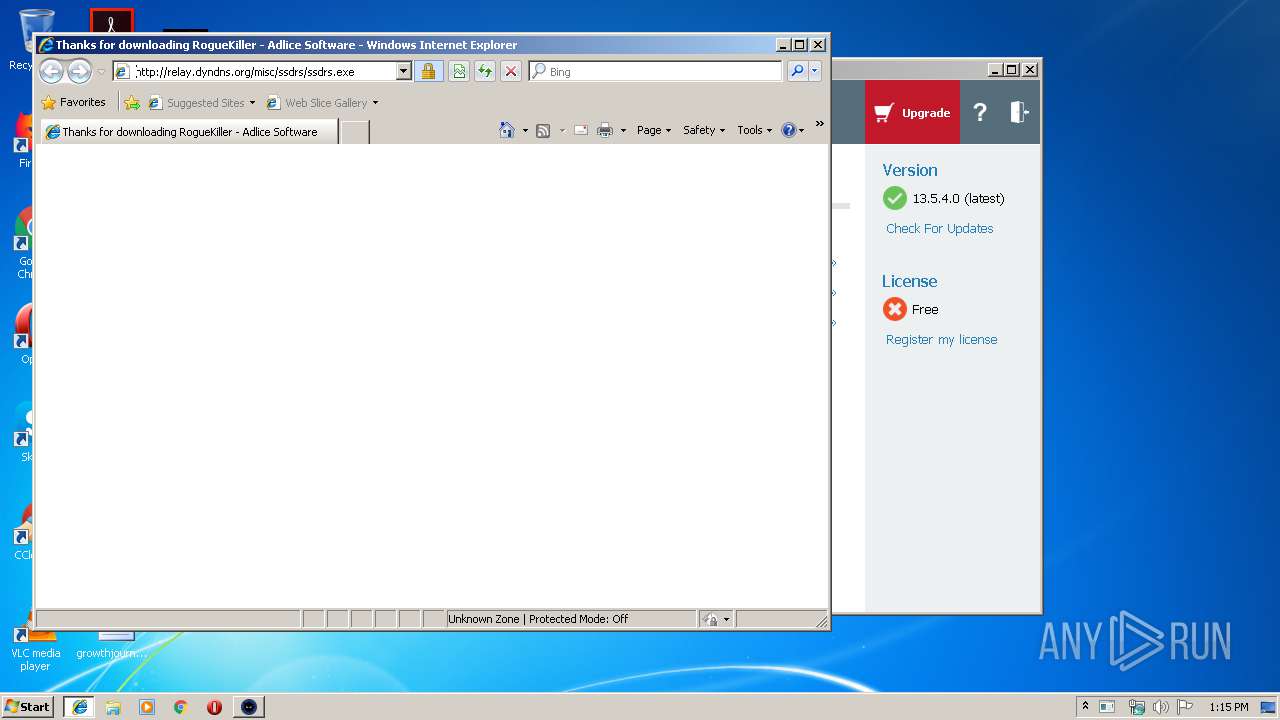
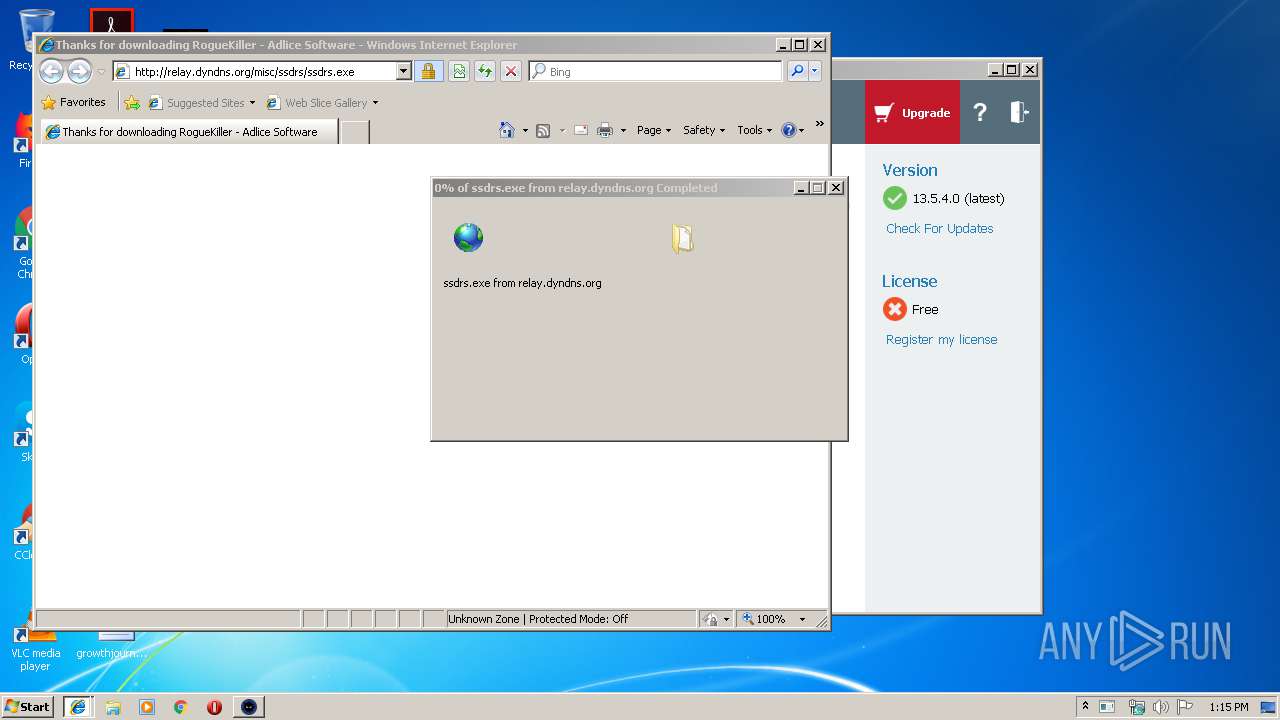
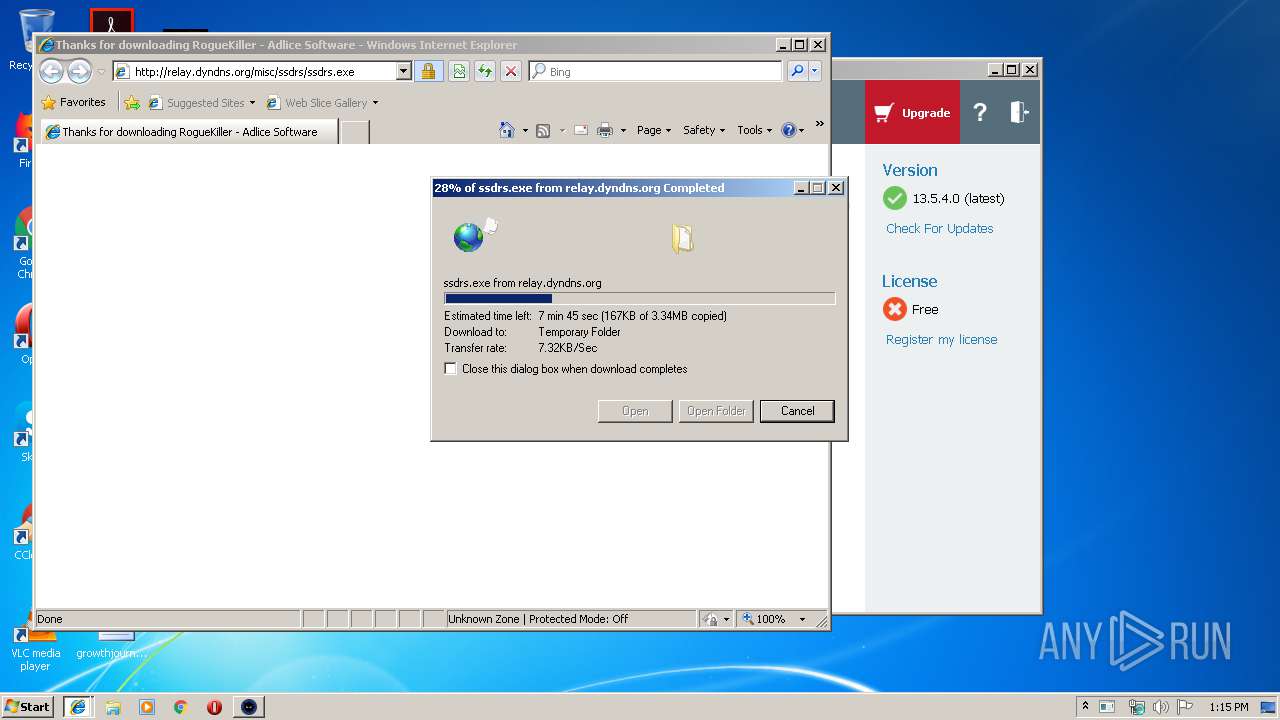
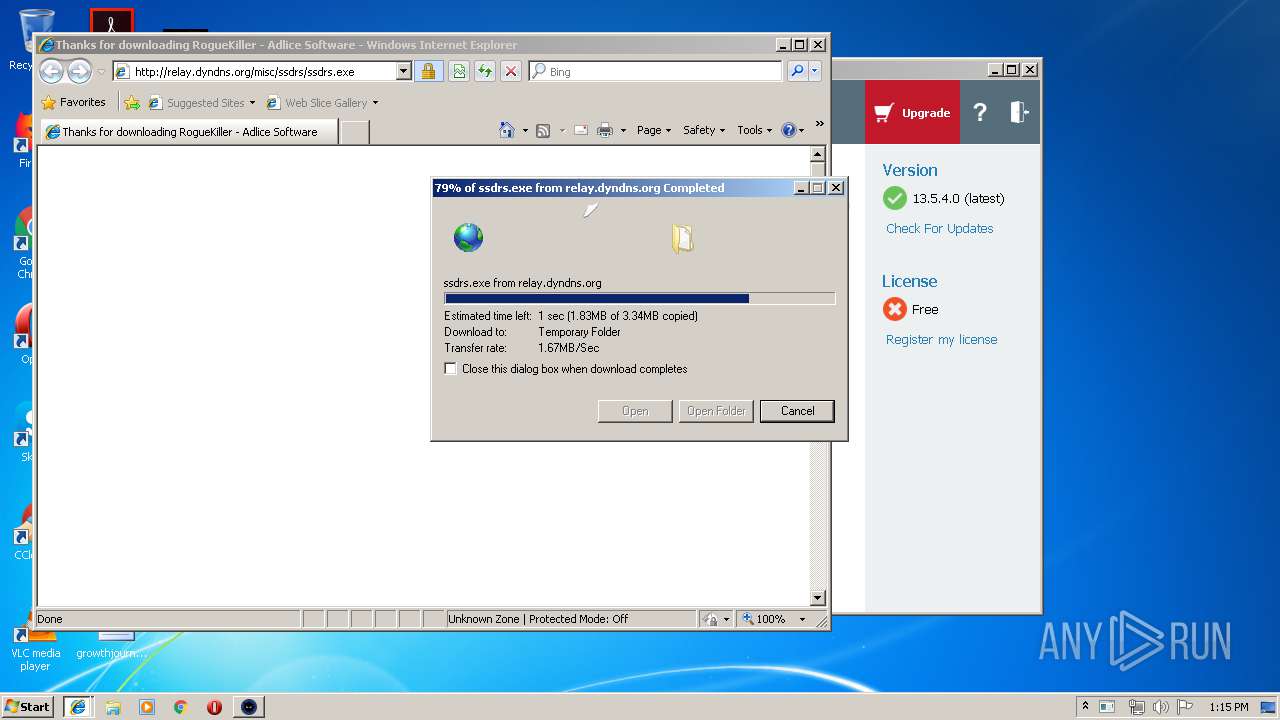
2720 | iexplore.exe | GET | 200 | 159.69.44.217:80 | http://relay.dyndns.org/misc/ssdrs/ssdrs.exe | US | executable | 3.35 Mb | suspicious |
352 | explorer.exe | GET | 302 | 74.208.215.128:80 | http://www.islamicityindex.com/y00/?GX=UpOPcfCINmnx65uKk8n7YGp2/m9GD3f6moCMlfFb7uKrY81qk7TnuhQjZNoXkVbCG2CdQQ==&uFO4=XPxDeFaPj&sql=1 | US | html | 211 b | malicious |
1160 | MSBuild.exe | GET | 200 | 216.239.32.21:80 | http://ifconfig.me/ip | US | text | 12 b | shared |
2720 | iexplore.exe | GET | 200 | 185.43.210.27:80 | http://rescue.slotsoft.net/distrib/ssdrs.exe | GB | executable | 3.35 Mb | suspicious |
352 | explorer.exe | POST | — | 74.208.215.128:80 | http://www.islamicityindex.com/y00/ | US | — | — | malicious |
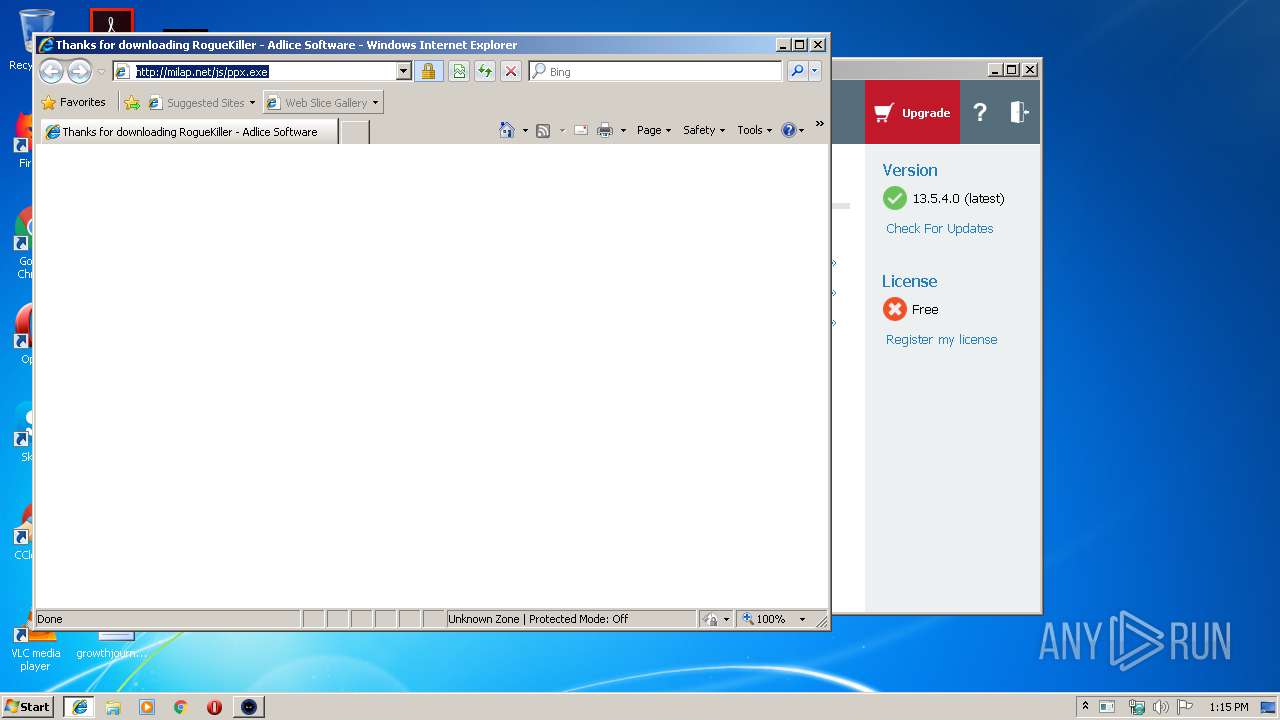
2720 | iexplore.exe | GET | 200 | 208.115.234.234:80 | http://milap.net/js/ppx.exe | US | executable | 1.09 Mb | malicious |
352 | explorer.exe | POST | — | 74.208.215.128:80 | http://www.islamicityindex.com/y00/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1944 | api.exe | 178.33.106.117:443 | download.adlice.com | OVH SAS | FR | suspicious |
2720 | iexplore.exe | 104.27.164.26:443 | adlice.com | Cloudflare Inc | US | shared |
2720 | iexplore.exe | 104.27.165.26:443 | adlice.com | Cloudflare Inc | US | shared |
2092 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2720 | iexplore.exe | 104.19.199.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
2720 | iexplore.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2720 | iexplore.exe | 172.217.16.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2720 | iexplore.exe | 172.217.22.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2720 | iexplore.exe | 216.58.207.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2720 | iexplore.exe | 173.194.76.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.adlice.com |
| whitelisted |
adflux.adlice.com |
| whitelisted |
adlice.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.adlice.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2720 | iexplore.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2720 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1160 | MSBuild.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (ifconfig .me) |
1160 | MSBuild.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ifconfig. me) |
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
1080 | svchost.exe | Misc activity | AV INFO DYNAMIC_DNS Query to *.dyndns. Domain |
2720 | iexplore.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to a *.dyndns.* domain |
2720 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2720 | iexplore.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
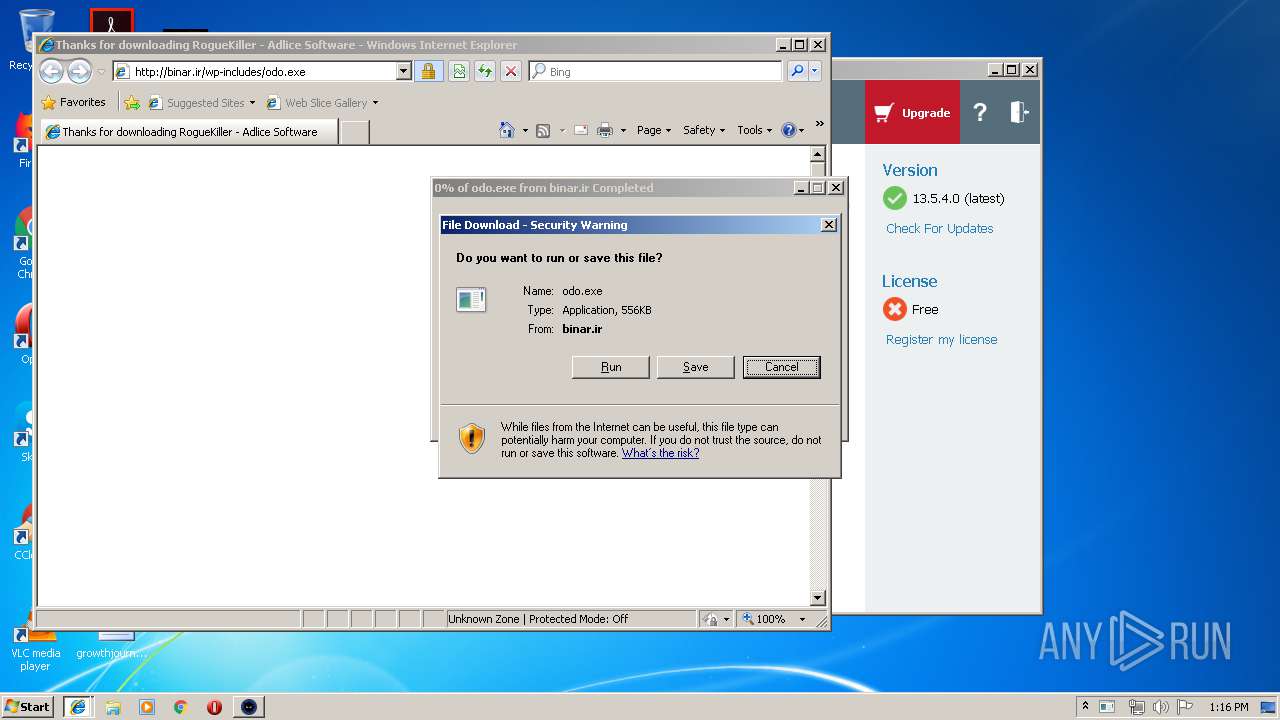
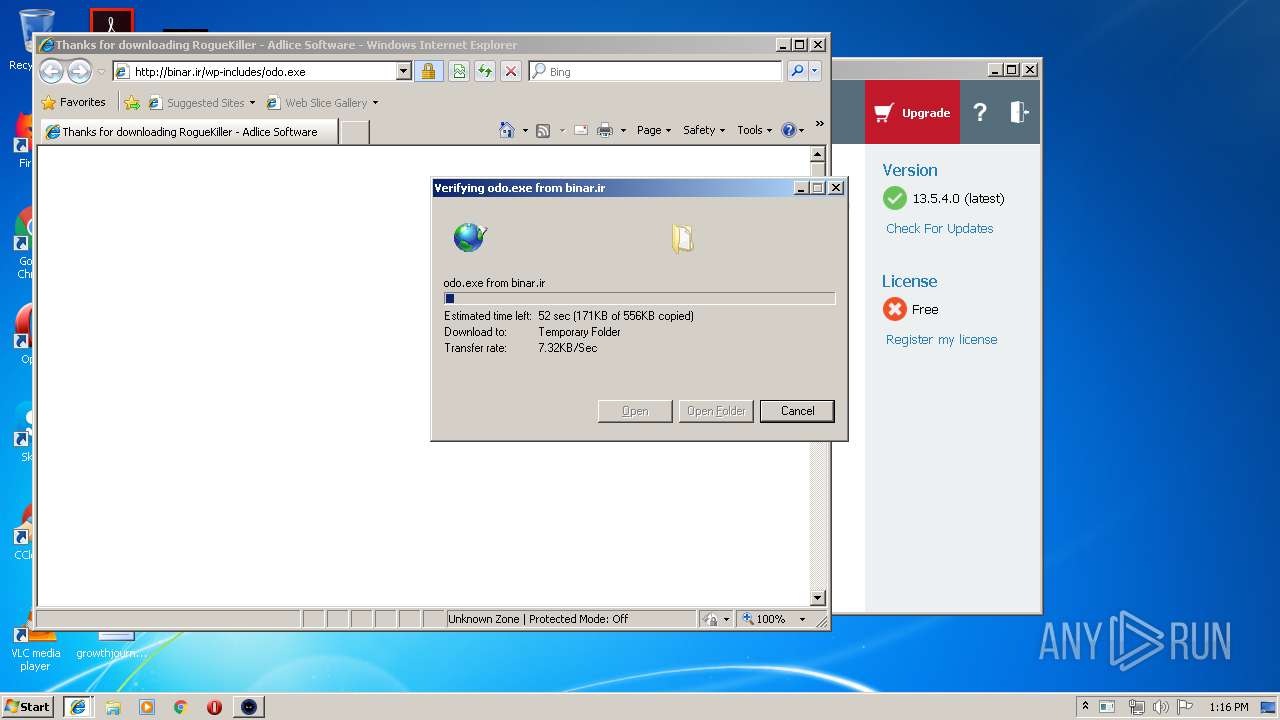
2720 | iexplore.exe | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
19 ETPRO signatures available at the full report
Process | Message |
|---|---|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|